diff --git a/404.html b/404.html
index 56f6c30..3c3801b 100644
--- a/404.html
+++ b/404.html
@@ -91,7 +91,7 @@
diff --git a/approved/0001-agile-coretime.html b/approved/0001-agile-coretime.html
index 10db1d5..0b46c87 100644
--- a/approved/0001-agile-coretime.html
+++ b/approved/0001-agile-coretime.html
@@ -90,7 +90,7 @@
diff --git a/approved/0005-coretime-interface.html b/approved/0005-coretime-interface.html
index 69416e2..dfa9ac9 100644
--- a/approved/0005-coretime-interface.html
+++ b/approved/0005-coretime-interface.html
@@ -90,7 +90,7 @@
diff --git a/approved/0007-system-collator-selection.html b/approved/0007-system-collator-selection.html
index 225f4be..ae26903 100644
--- a/approved/0007-system-collator-selection.html
+++ b/approved/0007-system-collator-selection.html
@@ -90,7 +90,7 @@
diff --git a/approved/0008-parachain-bootnodes-dht.html b/approved/0008-parachain-bootnodes-dht.html
index 3f3b6da..9e98e15 100644
--- a/approved/0008-parachain-bootnodes-dht.html
+++ b/approved/0008-parachain-bootnodes-dht.html
@@ -90,7 +90,7 @@
diff --git a/approved/0010-burn-coretime-revenue.html b/approved/0010-burn-coretime-revenue.html
index 9063257..85464b0 100644
--- a/approved/0010-burn-coretime-revenue.html
+++ b/approved/0010-burn-coretime-revenue.html
@@ -90,7 +90,7 @@
diff --git a/approved/0012-process-for-adding-new-collectives.html b/approved/0012-process-for-adding-new-collectives.html
index 8001f17..4249433 100644
--- a/approved/0012-process-for-adding-new-collectives.html
+++ b/approved/0012-process-for-adding-new-collectives.html
@@ -90,7 +90,7 @@
diff --git a/approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html b/approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html
index e75ff56..1ee80fb 100644
--- a/approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html
+++ b/approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html
@@ -90,7 +90,7 @@
diff --git a/approved/0014-improve-locking-mechanism-for-parachains.html b/approved/0014-improve-locking-mechanism-for-parachains.html
index 503eeb2..9f4469b 100644
--- a/approved/0014-improve-locking-mechanism-for-parachains.html
+++ b/approved/0014-improve-locking-mechanism-for-parachains.html
@@ -90,7 +90,7 @@
diff --git a/approved/0022-adopt-encointer-runtime.html b/approved/0022-adopt-encointer-runtime.html
index 040cd9d..de22000 100644
--- a/approved/0022-adopt-encointer-runtime.html
+++ b/approved/0022-adopt-encointer-runtime.html
@@ -90,7 +90,7 @@
diff --git a/approved/0026-sassafras-consensus.html b/approved/0026-sassafras-consensus.html
index 885bccf..06792f7 100644
--- a/approved/0026-sassafras-consensus.html
+++ b/approved/0026-sassafras-consensus.html
@@ -90,7 +90,7 @@
diff --git a/approved/0032-minimal-relay.html b/approved/0032-minimal-relay.html
index eccbe76..34bbe8b 100644
--- a/approved/0032-minimal-relay.html
+++ b/approved/0032-minimal-relay.html
@@ -90,7 +90,7 @@
diff --git a/approved/0042-extrinsics-state-version.html b/approved/0042-extrinsics-state-version.html
index d90383a..42803cb 100644
--- a/approved/0042-extrinsics-state-version.html
+++ b/approved/0042-extrinsics-state-version.html
@@ -90,7 +90,7 @@
diff --git a/approved/0043-storage-proof-size-hostfunction.html b/approved/0043-storage-proof-size-hostfunction.html
index 3b7272c..2ed25b7 100644
--- a/approved/0043-storage-proof-size-hostfunction.html
+++ b/approved/0043-storage-proof-size-hostfunction.html
@@ -90,7 +90,7 @@
diff --git a/approved/0045-nft-deposits-asset-hub.html b/approved/0045-nft-deposits-asset-hub.html
index 9ffa48f..f82fca0 100644
--- a/approved/0045-nft-deposits-asset-hub.html
+++ b/approved/0045-nft-deposits-asset-hub.html
@@ -90,7 +90,7 @@
diff --git a/approved/0047-assignment-of-availability-chunks.html b/approved/0047-assignment-of-availability-chunks.html
index 8be965f..b3286c4 100644
--- a/approved/0047-assignment-of-availability-chunks.html
+++ b/approved/0047-assignment-of-availability-chunks.html
@@ -90,7 +90,7 @@
diff --git a/approved/0048-session-keys-runtime-api.html b/approved/0048-session-keys-runtime-api.html
index 02b8088..39913fc 100644
--- a/approved/0048-session-keys-runtime-api.html
+++ b/approved/0048-session-keys-runtime-api.html
@@ -90,7 +90,7 @@
diff --git a/approved/0050-fellowship-salaries.html b/approved/0050-fellowship-salaries.html
index 112f099..23947da 100644
--- a/approved/0050-fellowship-salaries.html
+++ b/approved/0050-fellowship-salaries.html
@@ -90,7 +90,7 @@
diff --git a/approved/0056-one-transaction-per-notification.html b/approved/0056-one-transaction-per-notification.html
index a271c9d..617127d 100644
--- a/approved/0056-one-transaction-per-notification.html
+++ b/approved/0056-one-transaction-per-notification.html
@@ -90,7 +90,7 @@
diff --git a/approved/0059-nodes-capabilities-discovery.html b/approved/0059-nodes-capabilities-discovery.html
index a0162c4..41e81fb 100644
--- a/approved/0059-nodes-capabilities-discovery.html
+++ b/approved/0059-nodes-capabilities-discovery.html
@@ -90,7 +90,7 @@
diff --git a/approved/0078-merkleized-metadata.html b/approved/0078-merkleized-metadata.html
index a36170f..d11179c 100644
--- a/approved/0078-merkleized-metadata.html
+++ b/approved/0078-merkleized-metadata.html
@@ -90,7 +90,7 @@
diff --git a/approved/0084-general-transaction-extrinsic-format.html b/approved/0084-general-transaction-extrinsic-format.html
index a591b80..f690115 100644
--- a/approved/0084-general-transaction-extrinsic-format.html
+++ b/approved/0084-general-transaction-extrinsic-format.html
@@ -90,7 +90,7 @@
diff --git a/approved/0091-dht-record-creation-time.html b/approved/0091-dht-record-creation-time.html
index 6520bf1..b438443 100644
--- a/approved/0091-dht-record-creation-time.html
+++ b/approved/0091-dht-record-creation-time.html
@@ -90,7 +90,7 @@
diff --git a/approved/0097-unbonding_queue.html b/approved/0097-unbonding_queue.html
index 350c441..37e555c 100644
--- a/approved/0097-unbonding_queue.html
+++ b/approved/0097-unbonding_queue.html
@@ -90,7 +90,7 @@
diff --git a/approved/0099-transaction-extension-version.html b/approved/0099-transaction-extension-version.html
index 2c90b71..9edd9e3 100644
--- a/approved/0099-transaction-extension-version.html
+++ b/approved/0099-transaction-extension-version.html
@@ -90,7 +90,7 @@
diff --git a/approved/0100-xcm-multi-type-asset-transfer.html b/approved/0100-xcm-multi-type-asset-transfer.html
index 420e078..5483b13 100644
--- a/approved/0100-xcm-multi-type-asset-transfer.html
+++ b/approved/0100-xcm-multi-type-asset-transfer.html
@@ -90,7 +90,7 @@
diff --git a/approved/0101-xcm-transact-remove-max-weight-param.html b/approved/0101-xcm-transact-remove-max-weight-param.html
index 1fa0207..a718e1e 100644
--- a/approved/0101-xcm-transact-remove-max-weight-param.html
+++ b/approved/0101-xcm-transact-remove-max-weight-param.html
@@ -90,7 +90,7 @@
diff --git a/approved/0103-introduce-core-index-commitment.html b/approved/0103-introduce-core-index-commitment.html
index b01de9d..3f1ac73 100644
--- a/approved/0103-introduce-core-index-commitment.html
+++ b/approved/0103-introduce-core-index-commitment.html
@@ -90,7 +90,7 @@
diff --git a/approved/0105-xcm-improved-fee-mechanism.html b/approved/0105-xcm-improved-fee-mechanism.html
index a64427c..695252e 100644
--- a/approved/0105-xcm-improved-fee-mechanism.html
+++ b/approved/0105-xcm-improved-fee-mechanism.html
@@ -90,7 +90,7 @@
diff --git a/approved/0107-xcm-execution-hints.html b/approved/0107-xcm-execution-hints.html
index 8e4c2a5..bcab16a 100644
--- a/approved/0107-xcm-execution-hints.html
+++ b/approved/0107-xcm-execution-hints.html
@@ -90,7 +90,7 @@
diff --git a/approved/0108-xcm-remove-testnet-ids.html b/approved/0108-xcm-remove-testnet-ids.html
index a974ad3..50be58e 100644
--- a/approved/0108-xcm-remove-testnet-ids.html
+++ b/approved/0108-xcm-remove-testnet-ids.html
@@ -90,7 +90,7 @@
diff --git a/approved/0122-alias-origin-on-asset-transfers.html b/approved/0122-alias-origin-on-asset-transfers.html
index 0ccf25e..32c2e89 100644
--- a/approved/0122-alias-origin-on-asset-transfers.html
+++ b/approved/0122-alias-origin-on-asset-transfers.html
@@ -90,7 +90,7 @@
diff --git a/index.html b/index.html
index ca84c0d..7e36894 100644
--- a/index.html
+++ b/index.html
@@ -90,7 +90,7 @@
diff --git a/introduction.html b/introduction.html
index ca84c0d..7e36894 100644
--- a/introduction.html
+++ b/introduction.html
@@ -90,7 +90,7 @@
diff --git a/new/0125-xcm-asset-metadata.html b/new/0125-xcm-asset-metadata.html
index c332d1a..d66392b 100644
--- a/new/0125-xcm-asset-metadata.html
+++ b/new/0125-xcm-asset-metadata.html
@@ -90,7 +90,7 @@
diff --git a/new/0126-introduce-xcq.html b/new/0126-introduce-xcq.html
index 87cd2c4..fe4c036 100644
--- a/new/0126-introduce-xcq.html
+++ b/new/0126-introduce-xcq.html
@@ -90,7 +90,7 @@
diff --git a/new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html b/new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html
index f51f87a..6aa29b2 100644
--- a/new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html
+++ b/new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html
@@ -90,7 +90,7 @@
diff --git a/print.html b/print.html
index 305bcf8..2f7fe60 100644
--- a/print.html
+++ b/print.html
@@ -91,7 +91,7 @@
@@ -1706,186 +1706,6 @@ how to avoid getting bricked
of the paras, the locked/unlocked state, and the manager info.
-
(source)
-Table of Contents
-
-
-Start Date 22 March 2024 Description Proposal to decide polls after confirm period via a mechanism similar to a candle auction Authors Pablo Dorado, Daniel Olano
-
In an attempt to mitigate risks derived from unwanted behaviours around long decision periods on
-referenda, this proposal describes how to finalize and decide a result of a poll via a
-mechanism similar to candle auctions.
-Referenda protocol provide permissionless and efficient mechanisms to enable governance actors to
-decide the future of the blockchains around Polkadot network. However, they pose a series of risks
-derived from the game theory perspective around these mechanisms. One of them being where an actor
-uses the the public nature of the tally of a poll as a way of determining the best point in time to
-alter a poll in a meaningful way.
-While this behaviour is expected based on the current design of the referenda logic, given the
-recent extension of ongoing times (up to 1 month), the incentives for a bad actor to cause losses
-on a proposer, reflected as wasted cost of opportunity increase, and thus, this otherwise
-reasonable outcome becomes an attack vector, a potential risk to mitigate, especially when such
-attack can compromise critical guarantees of the protocol (such as its upgradeability).
-To mitigate this, the referenda underlying mechanisms should incentive actors to cast their votes
-on a poll as early as possible. This proposal's approach suggests using a Candle Auction that will
-be determined right after the confirm period finishes, thus decreasing the chances of actors to
-alter the results of a poll on confirming state, and instead incentivizing them to cast their votes
-earlier, on deciding state.
-
-Governance actors : Tokenholders and Collectives that vote on polls that have this mechanism
-enabled should be aware this change affects the outcome of failing a poll on its confirm period.Runtime Developers : This change requires runtime developers to change configuration
-parameters for the Referenda Pallet.Tooling and UI developers : Applications that interact with referenda must update to reflect
-the new Finalizing state.
-Currently, the process of a referendum/poll is defined as an sequence between an ongoing state
-(where accounts can vote), comprised by a with a preparation period, a decision period, and a
-confirm period. If the poll is passing before the decision period ends, it's possible to push
-forward to confirm period, and still, go back in case the poll fails. Once the decision period
-ends, a failure of the poll in the confirm period will lead to the poll to ultimately be rejected.
-stateDiagram-v2
- sb: Submission
- pp: Preparation Period
- dp: Decision Period
- cp: Confirmation Period
- state dpd <<choice>>
- state ps <<choice>>
- cf: Approved
- rj: Rejected
-
- [*] --> sb
- sb --> pp
- pp --> dp: decision period starts
- dp --> cp: poll is passing
- dp --> ps: decision period ends
- ps --> cp: poll is passing
- cp --> dpd: poll fails
- dpd --> dp: decision period not deadlined
- ps --> rj: poll is failing
- dpd --> rj: decision period deadlined
- cp --> cf
- cf --> [*]
- rj --> [*]
-This specification proposes three changes to implement this candle mechanism:
-
-
-This mechanism MUST be enabled via a configuration parameter. Once enabled, the referenda system
-MAY record the next poll ID from which to start enabling this mechanism. This is to preserve
-backwards compatibility with currently ongoing polls.
-
-
-A record of the poll status (whether it is passing or not) is stored once the decision period is
-finished.
-
-
-Including a Finalization period as part of the ongoing state. From this point, the poll MUST
-be immutable at this point.
-This period begins the moment after confirm period ends, and extends the decision for a couple
-of blocks, until the VRF seed used to determine the candle block can be considered
-"good enough" . This is, not known before the ongoing period (decision/confirmation) was over.
-Once that happens, a random block within the confirm period is chosen, and the decision of
-approving or rejecting the poll is based on the status immediately before the block where the
-candle was "lit-off" .
-
-
-When enabled, the state diagram for the referenda system is the following:
-stateDiagram-v2
- sb: Submission
- pp: Preparation Period
- dp: Decision Period
- cp: Confirmation Period
- cds: Finalization
- state dpd <<choice>>
- state ps <<choice>>
- state cd <<choice>>
- cf: Approved
- rj: Rejected
-
- [*] --> sb
- sb --> pp
- pp --> dp: decision period starts
- dp --> cp: poll is passing
- ps --> cp: poll is passing
- dp --> ps: decision period ends
- ps --> rj: poll is failing
- cp --> dpd: poll fails
- dpd --> cp: decision period over
- dpd --> dp: decision period not over
- cp --> cds: confirmation period ends
- cds --> cd: define moment when candle lit-off
- cd --> cf: poll passed
- cd --> rj: poll failed
- cf --> [*]
- rj --> [*]
-This approach doesn't include a mechanism to determine whether a change of the poll status in the
-confirming period is due to a legitimate change of mind of the voters, or an exploitation of its
-aforementioned vulnerabilities (like a sniping attack), instead treating all of them as potential
-attacks.
-This is an issue that can be addressed by additional mechanisms, and heuristics that can help
-determine the probability of a change of poll status to happen as a result of a legitimate behaviour.
-The implementation of this RFC will be tested on testnets (Paseo and Westend) first. Furthermore, it
-should be enabled in a canary network (like Kusama) to ensure the behaviours it is trying to address
-is indeed avoided.
-An audit will be required to ensure the implementation doesn't introduce unwanted side effects.
-There are no privacy related concerns.
-
-
-The added steps imply pessimization, necessary to meet the expected changes. An implementation MUST
-exit from the Finalization period as early as possible to minimize this impact.
-This proposal does not alter the already exposed interfaces or developers or end users. However, they
-must be aware of the changes in the additional overhead the new period might incur (these depend on the
-implemented VRF).
-This proposal does not break compatibility with existing interfaces, older versions, but it alters the
-previous implementation of the referendum processing algorithm.
-An acceptable upgrade strategy that can be applied is defining a point in time (block number, poll index)
-from which to start applying the new mechanism, thus, not affecting the already ongoing referenda.
-
-How to determine in a statistically meaningful way that a change in the poll status corresponds to an
-organic behaviour, and not an unwanted, malicious behaviour?
-
-
-A proposed implementation of this change can be seen on this Pull Request .
(source)
Table of Contents
@@ -1917,12 +1737,12 @@ organic behaviour, and not an unwanted, malicious behaviour?
Authors Pablo Dorado, Daniel Olano The protocol change introduces flexibility in the governance structure by enabling the referenda
track list to be modified dynamically at runtime. This is achieved by replacing static slices in
TracksInfo with iterators, facilitating storage-based track management. As a result, governance
tracks can be modified or added based on real-time decisions and without requiring runtime upgrades.
-Polkadot's governance system is designed to be adaptive and decentralized, but modifying the
referenda tracks (which determine decision-making paths for proposals) has historically required
runtime upgrades. This poses an operational challenge, delaying governance changes until an upgrade
@@ -1930,12 +1750,12 @@ is scheduled and executed. The new system provides the flexibility needed to adj
dynamically, reflecting real-time changes in governance needs without the latency and risks
associated with runtime upgrades. This reduces governance bottlenecks and allows for quicker
adaptation to emergent scenarios.
-
Network stakeholders : the change means reduced coordination effort for track adjustments.Governance participants : this enables more responsive decision-making pathways.
-The protocol modification replaces the current static slice method used for storing referenda tracks
with an iterator-based approach that allows tracks to be managed dynamically using chain storage.
Governance participants can define and modify referenda tracks as needed, which are then accessed
@@ -1947,12 +1767,12 @@ rather enhances them by increasing adaptability.
to alter track configurations based on storage data rather than static definitions. This opens up
possibilities for new track types and governance configurations to be deployed without the need for
upgrades that might take up weeks.
-The most significant drawback is the increased complexity for developers managing track configurations
via storage-based iterators, which require careful handling to avoid misuse or inefficiencies.
Additionally, this flexibility could introduce risks if track configurations are modified improperly
during runtime, potentially leading to governance instabilities.
-To ensure security, the change must be tested in testnet environments first (Paseo, Westend),
particularly in scenarios where multiple track changes happen concurrently. Potential
vulnerabilities in governance adjustments must be addressed to prevent abuse.
@@ -1960,27 +1780,27 @@ vulnerabilities in governance adjustments must be addressed to prevent abuse.
Comprehensive tests should be conducted to validate correct track modifications in different
governance scenarios.
-
-
+
+
The proposal optimizes governance track management by avoiding the overhead of runtime upgrades,
reducing downtime, and eliminating the need for full consensus on upgrades. However, there is a
slight performance cost related to runtime access to storage-based iterators, though this is
mitigated by the overall system efficiency gains.
-Developers and governance actors benefit from simplified governance processes but must account for
the technical complexity of managing iterator-based track configurations.
Tools may need to be developed to help streamline track adjustments in runtime.
-The change is backward compatible with existing governance operations, and does not require developers
to adjust how they interact with referenda tracks.
A migration is required to convert existing statically-defined tracks to dynamic storage-based
configurations without disruption.
-This dynamic governance track approach builds on previous work around Polkadot's on-chain governance
and leverages standard iterator patterns in Rust programming to improve runtime flexibility.
Comparable solutions in other governance networks were examined, but this proposal uniquely tailors
them to Polkadot’s decentralized, runtime-upgradable architecture.
-
How to handle governance transitions for currently ongoing referenda when changing configuration
parameters of an existing track? Ideally, most tracks should not have to go through this change,
@@ -1988,7 +1808,7 @@ but some tactics might be applied (like a proposal that reduces the ongoing queu
change and then executes the change, after a reasonable period of time has elapsed and no ongoing
referenda exists for that track).
-
+
There are already two proposed solutions for both the implementation and
This Pull Request proposes changing pallet-referenda's TracksInfo to make tracks
@@ -2026,39 +1846,39 @@ stores the configurations, and implements TracksInfo using the iter
Authors Bastian Köcher The code of a runtime is stored in its own state, and when performing a runtime upgrade, this code is replaced. The new runtime can contain runtime migrations that adapt the state to the state layout as defined by the runtime code. This runtime migration is executed when building the first block with the new runtime code. Anything that interacts with the runtime state uses the state layout as defined by the runtime code. So, when trying to load something from the state in the block that applied the runtime upgrade, it will use the new state layout but will decode the data from the non-migrated state. In the worst case, the data is incorrectly decoded, which may lead to crashes or halting of the chain.
This RFC proposes to store the new runtime code under a different storage key when applying a runtime upgrade. This way, all the off-chain logic can still load the old runtime code under the default storage key and decode the state correctly. The block producer is then required to use this new runtime code to build the next block. While building the next block, the runtime is executing the migrations and moves the new runtime code to the default runtime code location. So, the runtime code found under the default location is always the correct one to decode the state from which the runtime code was loaded.
-While the issue of having undecodable state only exists for the one block in which the runtime upgrade was applied, it still impacts anything that reads state data, like block explorers, UIs, nodes, etc. For block explorers, the issue mainly results in indexing invalid data and UIs may show invalid data to the user. For nodes, reading incorrect data may lead to a performance degradation of the network . There are also ways to prevent certain decoding issues from happening, but it requires that developers are aware of this issue and also requires introducing extra code, which could introduce further bugs down the line.
So, this RFC tries to solve these issues by fixing the underlying problem of having temporary undecodable state.
-
Relay chain/Parachain node developers
Relay chain/Parachain node operators
-The runtime code is stored under the special key :code in the state. Nodes and other tooling read the runtime code under this storage key when they want to interact with the runtime for e.g., building/importing blocks or getting the metadata to read the state. To update the runtime code the runtime overwrites the value at :code, and then from the next block on, the new runtime will be loaded.
This RFC proposes to first store the new runtime code under :pending_code in the state for one block. When the next block is being built, the block builder first needs to check if :pending_code is set, and if so, it needs to load the runtime from this storage key. While building the block the runtime will move :pending_code to :code to have the runtime code at the default location. Nodes importing the block will also need to load :pending_code if it exists to ensure that the correct runtime code is used. By doing it this way, the runtime code found at :code in the state of a block will always be able to decode the state.
Furthermore, this RFC proposes to introduce system_version: 3. The system_version was introduced in RFC423 would then enable the usage of :pending_code when applying a runtime code upgrade. This way, the feature can be introduced first and enabled later when the majority of the nodes have upgraded.
-Because the first block built with the new runtime code will move the runtime code from :pending_code to :code, the runtime code will need to be loaded. This means the runtime code will appear in the proof of validity of a parachain for the first block built with the new runtime code. Generally this is not a problem as the runtime code is also loaded by the parachain when setting the new runtime code.
There is still the possibility of having state that is not migrated even when following the proposal as presented by this RFC. The issue is that if the amount of data to be migrated is too big, not all of it can be migrated in one block, because either it takes more time than there is assigned for a block or parachains for example have a fixed budget for their proof of validity. To solve this issue there already exist multi-block migrations that can chunk the migration across multiple blocks. Consensus-critical data needs to be migrated in the first block to ensure that block production etc., can continue. For the other data being migrated by multi-block migrations the migrations could for example expose to the outside which keys are being migrated and should not be indexed until the migration is finished.
-Testing should be straightforward and most of the existing testing should already be good enough. Extending with some checks that :pending_code is moved to :code.
-
-
+
+
The performance should not be impacted besides requiring loading the runtime code in the first block being built with the new runtime code.
-It only alters the way blocks are produced and imported after applying a runtime upgrade. This means that only nodes need to be adapted to the changes of this RFC.
-The change will require that the nodes are upgraded before the runtime starts using this feature. Otherwise they will fail to import the block build by :pending_code.
For Polkadot/Kusama this means that also the parachain nodes need to be running with a relay chain node version that supports this new feature. Otherwise the parachains will stop producing/finalizing nodes as they can not sync the relay chain any more.
-The issue initially reported a bug that led to this RFC. It also discusses multiple solutions for the problem.
-None
-
+
Solve the issue of requiring loading the entire runtime code to move it into a different location by introducing a low-level move function. When using the V1 trie layout every value bigger than 32 bytes is put into the db separately. This means a low level move function would only need to move the hash of the runtime code from :code to :pending_code.
@@ -2100,17 +1920,17 @@ For Polkadot/Kusama this means that also the parachain nodes need to be running
Authors George Pisaltu This RFC proposes the definition of version 5 extrinsics along with changes to the specification and encoding from version 4.
-RFC84 introduced the specification of General transactions, a new type of extrinsic besides the Signed and Unsigned variants available previously in version 4. Additionally, RFC99 introduced versioning of transaction extensions through an extra byte in the extrinsic encoding. Both of these changes require an extrinsic format version bump as both the semantics around extensions as well as the actual encoding of extrinsics need to change to accommodate these new features.
-
Runtime users
Runtime devs
Wallet devs
-The introduction of General transactions allows the authorization of any and all origins through
extensions. This means that, with the appropriate extension, General transactions are capable of
@@ -2179,31 +1999,31 @@ consumers downstream in the transition period between these extrinsic versions,
Add the General variant starting with v5 extrinsics
Enable runtimes to support both v4 and v5 extrinsics
-The metadata will have to accommodate two distinct extrinsic format versions at a given point in
time in order to provide the new functionality in a non-breaking way for users and tooling.
-There is no impact on testing, security or privacy.
-
+
This change makes the authorization through signatures configurable by runtime devs in version 5
extrinsics, as opposed to version 4 where the signing payload algorithm and signatures were
hardcoded. This moves the responsibility of ensuring proper authentication through
TransactionExtension to the runtime devs, but a sensible default which closely resembles the
present day behavior will be provided in VerifySignature.
-
+
There is no performance impact.
-Tooling will have to adapt to be able to tell which authorization scheme is used by a particular
transaction by decoding the extension and checking which particular TransactionExtension in the pipeline is enabled to do the origin authorization. Previously, this was done by simply checking whether the transaction is signed or unsigned, as there was only one method of authentication.
-As long as extrinsic version 4 is still exposed in the metadata when version 5 will be introduced,
the changes will not break existing infrastructure. This should give enough time for tooling to
support version 5 and to remove version 4 in the future.
-This is a result of the work in Extrinsic
Horizon and
RFC99 .
-There is no clear way to expose two different extrinsic versions in the current metadata framework.
A non-exhaustive list of options discussed so far:
@@ -2212,7 +2032,7 @@ A non-exhaustive list of options discussed so far:
Create a new trait similar to ExtrinsicMetadata, but for future versions of the extrinsic
format and add it to the metadata.
-
+
Following this change, extrinsic version 5 will be introduced as part of the Extrinsic
Horizon effort, which will shape future
work.
@@ -2246,7 +2066,7 @@ work.
Authors Leemo / ChaosDAO This RFC proposes to change the duration of the Confirmation Period for the Big Tipper and Small Tipper tracks in Polkadot OpenGov:
-Currently, these are the durations of treasury tracks in Polkadot OpenGov. Confirmation periods for the Spender tracks were adjusted based on RFC20 and its related conversation.
Track Description Confirmation Period Duration
Treasurer 7 Days You can see that there is a general trend on the Spender track that when the privilege level (the amount the track can spend) the confirmation period approximately doubles.
I believe that the Big Tipper and Small Tipper track's confirmation periods should be adjusted to match this trend.
In the current state it is possible to somewhat positively snipe these tracks, and whilst the power/privilege level of these tracks is very low (they cannot spend a large amount of funds), I believe we should increase the confirmation periods to something higher. This is backed up by the recent sentiment in the greater community regarding referendums submitted on these tracks. The parameters of Polkadot OpenGov can be adjusted based on the general sentiment of token holders when necessary.
-The primary stakeholders of this RFC are:
– DOT token holders – as this affects the protocol's treasury
– Entities wishing to submit a referendum on these tracks – as this affects the referendum's timeline
– Projects with governance app integrations – see Performance, Ergonomics and Compatibility section below
-This RFC proposes to change the duration of the confirmation period for both the Big Tipper and Small Tipper tracks. To achieve this the confirm_period parameter for those tracks should be changed.
You can see the lines of code that need to be adjusted here:
@@ -2287,12 +2107,12 @@ work.
This RFC proposes to change the confirm_period for the Big Tipper track to DAYS (i.e. 1 Day) and the confirm_period for the Small Tipper track to 12 * HOURS (i.e. 12 Hours).
-The drawback of changing these confirmation periods is that the lifecycle of referenda submitted on those tracks would be ultimately longer, and it would add a greater potential to negatively "snipe" referenda on those tracks by knocking the referendum out of its confirmation period once the decision period has ended. This can be a good or a bad thing depending on your outlook of positive vs negative sniping.
-This referendum will enhance the security of the protocol as it relates to its treasury. The confirmation period is one of the last lines of defense for the Polkadot token holder DAO to react to a potentially bad referendum and vote NAY in order for its confirmation period to be aborted.
-
-
+
+
This is a simple change (code wise) that should not affect the performance of the Polkadot protocol, outside of increasing the duration of the confirmation periods for these 2 tracks.
As per the implementation of changes described in RFC-20, it was identified that governance UIs automatically update to meet the new parameters:
@@ -2301,11 +2121,11 @@ work.
Polkassembly - directly uses on-chain data via rpc to fetch trackInfo so the change will be automatically reflected.
SubSquare - scan script will update their app to the latest parameters and it will be automatically reflected in their app.
-N/A
-Some token holders may want these confirmation periods to remain as they are currently and for them not to increase. If this is something that the Polkadot Technical Fellowship considers to be an issue to implement into a runtime upgrade then I can create a Wish For Change to obtain token holder approval.
-
+
The parameters of Polkadot OpenGov will likely continue to change over time, there are additional discussions in the community regarding adjusting the min_support for some tracks so that it does not trend towards 0%, similar to the current state of the Whitelisted Caller track. This is outside of the scope of this RFC and requires a lot more discussion.
(source)
Table of Contents
@@ -2347,9 +2167,9 @@ work.
Authors Gavin Wood
This proposes a periodic, sale-based method for assigning Polkadot Coretime, the analogue of "block space" within the Polkadot Network. The method takes into account the need for long-term capital expenditure planning for teams building on Polkadot, yet also provides a means to allow Polkadot to capture long-term value in the resource which it sells. It supports the possibility of building rich and dynamic secondary markets to optimize resource allocation and largely avoids the need for parameterization.
-The Polkadot Ubiquitous Computer , or just Polkadot UC , represents the public service provided by the Polkadot Network. It is a trust-free, WebAssembly-based, multicore, internet-native omnipresent virtual machine which is highly resilient to interference and corruption.
The present system of allocating the limited resources of the Polkadot Ubiquitous Computer is through a process known as parachain slot auctions . This is a parachain-centric paradigm whereby a single core is long-term allocated to a single parachain which itself implies a Substrate/Cumulus-based chain secured and connected via the Relay-chain. Slot auctions are on-chain candle auctions which proceed for several days and result in the core being assigned to the parachain for six months at a time up to 24 months in advance. Practically speaking, we only see two year periods being bid upon and leased.
@@ -2370,7 +2190,7 @@ work.
The solution SHOULD avoid creating additional dependencies on functionality which the Relay-chain need not strictly provide for the delivery of the Polkadot UC.
Furthermore, the design SHOULD be implementable and deployable in a timely fashion; three months from the acceptance of this RFC should not be unreasonable.
-Primary stakeholder sets are:
Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division.
@@ -2379,7 +2199,7 @@ work.
Socialization:
The essensials of this proposal were presented at Polkadot Decoded 2023 Copenhagen on the Main Stage. A small amount of socialization at the Parachain Summit preceeded it and some substantial discussion followed it. Parity Ecosystem team is currently soliciting views from ecosystem teams who would be key stakeholders.
-Upon implementation of this proposal, the parachain-centric slot auctions and associated crowdloans cease. Instead, Coretime on the Polkadot UC is sold by the Polkadot System in two separate formats: Bulk Coretime and Instantaneous Coretime .
When a Polkadot Core is utilized, we say it is dedicated to a Task rather than a "parachain". The Task to which a Core is dedicated may change at every Relay-chain block and while one predominant type of Task is to secure a Cumulus-based blockchain (i.e. a parachain), other types of Tasks are envisioned.
@@ -2811,16 +2631,16 @@ InstaPoolHistory: (empty)
Governance upgrade proposal(s).
Monitoring of the upgrade process.
-
+
No specific considerations.
Parachains already deployed into the Polkadot UC must have a clear plan of action to migrate to an agile Coretime market.
While this proposal does not introduce documentable features per se, adequate documentation must be provided to potential purchasers of Polkadot Coretime. This SHOULD include any alterations to the Polkadot-SDK software collection.
-Regular testing through unit tests, integration tests, manual testnet tests, zombie-net tests and fuzzing SHOULD be conducted.
A regular security review SHOULD be conducted prior to deployment through a review by the Web3 Foundation economic research group.
Any final implementation MUST pass a professional external security audit.
The proposal introduces no new privacy concerns.
-
+
RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain.
RFC-5 proposes the API for interacting with Relay-chain.
Additional work should specify the interface for the instantaneous market revenue so that the Coretime-chain can ensure Bulk Coretime placed in the instantaneous market is properly compensated.
@@ -2836,7 +2656,7 @@ InstaPoolHistory: (empty)
The percentage of cores to be sold as Bulk Coretime.
The fate of revenue collected.
-Robert Habermeier initially wrote on the subject of Polkadot blockspace-centric in the article Polkadot Blockspace over Blockchains . While not going into details, the article served as an early reframing piece for moving beyond one-slot-per-chain models and building out secondary market infrastructure for resource allocation.
(source)
Table of Contents
@@ -2869,10 +2689,10 @@ InstaPoolHistory: (empty)
Authors Gavin Wood, Robert Habermeier In the Agile Coretime model of the Polkadot Ubiquitous Computer, as proposed in RFC-1 and RFC-3, it is necessary for the allocating parachain (envisioned to be one or more pallets on a specialised Brokerage System Chain) to communicate the core assignments to the Relay-chain, which is responsible for ensuring those assignments are properly enacted.
This is a proposal for the interface which will exist around the Relay-chain in order to communicate this information and instructions.
-The background motivation for this interface is splitting out coretime allocation functions and secondary markets from the Relay-chain onto System parachains. A well-understood and general interface is necessary for ensuring the Relay-chain receives coretime allocation instructions from one or more System chains without introducing dependencies on the implementation details of either side.
@@ -2884,7 +2704,7 @@ InstaPoolHistory: (empty)
The interface MUST allow for the allocating chain to instruct changes to the number of cores which it is able to allocate.
The interface MUST allow for the allocating chain to be notified of changes to the number of cores which are able to be allocated by the allocating chain.
-Primary stakeholder sets are:
Developers of the Relay-chain core-management logic.
@@ -2892,7 +2712,7 @@ InstaPoolHistory: (empty)
Socialization:
This content of this RFC was discussed in the Polkdot Fellows channel.
-The interface has two sections: The messages which the Relay-chain is able to receive from the allocating parachain (the UMP message types ), and messages which the Relay-chain is able to send to the allocating parachain (the DMP message types ). These messages are expected to be able to be implemented in a well-known pallet and called with the XCM Transact instruction.
Future work may include these messages being introduced into the XCM standard.
For request_revenue_info, a successful request should be possible if when is no less than the Relay-chain block number on arrival of the message less 100,000.
For assign_core, a successful request should be possible if begin is no less than the Relay-chain block number on arrival of the message plus 10 and workload contains no more than 100 items.
-
+
No specific considerations.
-Standard Polkadot testing and security auditing applies.
The proposal introduces no new privacy concerns.
-
+
RFC-1 proposes a means of determining allocation of Coretime using this interface.
RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain.
None at present.
-None.
(source)
Table of Contents
@@ -3023,13 +2843,13 @@ assert_eq!(targets.iter().map(|x| x.1).sum(), 57600);
Authors Joe Petrowski As core functionality moves from the Relay Chain into system chains, so increases the reliance on
the liveness of these chains for the use of the network. It is not economically scalable, nor
necessary from a game-theoretic perspective, to pay collators large rewards. This RFC proposes a
mechanism -- part technical and part social -- for ensuring reliable collator sets that are
resilient to attemps to stop any subsytem of the Polkadot protocol.
-In order to guarantee access to Polkadot's system, the collators on its system chains must propose
blocks (provide liveness) and allow all transactions to eventually be included. That is, some
collators may censor transactions, but there must exist one collator in the set who will include a
@@ -3065,12 +2885,12 @@ to censor any subset of transactions.
Collators selected by governance SHOULD have a reasonable expectation that the Treasury will
reimburse their operating costs.
-
Infrastructure providers (people who run validator/collator nodes)
Polkadot Treasury
-This protocol builds on the existing
Collator Selection pallet
and its notion of Invulnerables. Invulnerables are collators (identified by their AccountIds) who
@@ -3106,27 +2926,27 @@ approximately:
of which 15 are Invulnerable, and
five are elected by bond.
-The primary drawback is a reliance on governance for continued treasury funding of infrastructure
costs for Invulnerable collators.
-The vast majority of cases can be covered by unit testing. Integration test should ensure that the
Collator Selection UpdateOrigin, which has permission to modify the Invulnerables and desired
number of Candidates, can handle updates over XCM from the system's governance location.
-
+
This proposal has very little impact on most users of Polkadot, and should improve the performance
of system chains by reducing the number of missed blocks.
-
+
As chains have strict PoV size limits, care must be taken in the PoV impact of the session manager.
Appropriate benchmarking and tests should ensure that conservative limits are placed on the number
of Invulnerables and Candidates.
-The primary group affected is Candidate collators, who, after implementation of this RFC, will need
to compete in a bond-based election rather than a race to claim a Candidate spot.
-This RFC is compatible with the existing implementation and can be handled via upgrades and
migration.
-
GitHub: Collator Selection Roadmap SR Labs Auditors
Current collators including Paranodes, Stake Plus, Turboflakes, Peter Mensik, SIK, and many more.
-None at this time.
-
+
There may exist in the future system chains for which this model of collator selection is not
appropriate. These chains should be evaluated on a case-by-case basis.
(source)
@@ -3182,10 +3002,10 @@ appropriate. These chains should be evaluated on a case-by-case basis.
Authors Pierre Krieger The full nodes of the Polkadot peer-to-peer network maintain a distributed hash table (DHT), which is currently used for full nodes discovery and validators discovery purposes.
This RFC proposes to extend this DHT to be used to discover full nodes of the parachains of Polkadot.
-The maintenance of bootnodes has long been an annoyance for everyone.
When a bootnode is newly-deployed or removed, every chain specification must be updated in order to take the update into account. This has lead to various non-optimal solutions, such as pulling chain specifications from GitHub repositories.
When it comes to RPC nodes, UX developers often have trouble finding up-to-date addresses of parachain RPC nodes. With the ongoing migration from RPC nodes to light clients, similar problems would happen with chain specifications as well.
@@ -3194,9 +3014,9 @@ When it comes to RPC nodes, UX developers often have trouble finding up-to-date
Because the list of bootnodes in chain specifications is so annoying to modify, the consequence is that the number of bootnodes is rather low (typically between 2 and 15). In order to better resist downtimes and DoS attacks, a better solution would be to use every node of a certain chain as potential bootnode, rather than special-casing some specific nodes.
While this RFC doesn't solve these problems for relay chains, it aims at solving it for parachains by storing the list of all the full nodes of a parachain on the relay chain DHT.
Assuming that this RFC is implemented, and that light clients are used, deploying a parachain wouldn't require more work than registering it onto the relay chain and starting the collators. There wouldn't be any need for special infrastructure nodes anymore.
-This RFC has been opened on my own initiative because I think that this is a good technical solution to a usability problem that many people are encountering and that they don't realize can be solved.
-The content of this RFC only applies for parachains and parachain nodes that are "Substrate-compatible". It is in no way mandatory for parachains to comply to this RFC.
Note that "Substrate-compatible" is very loosely defined as "implements the same mechanisms and networking protocols as Substrate". The author of this RFC believes that "Substrate-compatible" should be very precisely specified, but there is controversy on this topic.
While a lot of this RFC concerns the implementation of parachain nodes, it makes use of the resources of the Polkadot chain, and as such it is important to describe them in the Polkadot specification.
@@ -3233,10 +3053,10 @@ message Response {
The maximum size of a response is set to an arbitrary 16kiB. The responding side should make sure to conform to this limit. Given that fork_id is typically very small and that the only variable-length field is addrs, this is easily achieved by limiting the number of addresses.
Implementers should be aware that addrs might be very large, and are encouraged to limit the number of addrs to an implementation-defined value.
-The peer_id and addrs fields are in theory not strictly needed, as the PeerId and addresses could be always equal to the PeerId and addresses of the node being registered as the provider and serving the response. However, the Cumulus implementation currently uses two different networking stacks, one of the parachain and one for the relay chain, using two separate PeerIds and addresses, and as such the PeerId and addresses of the other networking stack must be indicated. Asking them to use only one networking stack wouldn't feasible in a realistic time frame.
The values of the genesis_hash and fork_id fields cannot be verified by the requester and are expected to be unused at the moment. Instead, a client that desires connecting to a parachain is expected to obtain the genesis hash and fork ID of the parachain from the parachain chain specification. These fields are included in the networking protocol nonetheless in case an acceptable solution is found in the future, and in order to allow use cases such as discovering parachains in a not-strictly-trusted way.
-Because not all nodes want to be used as bootnodes, implementers are encouraged to provide a way to disable this mechanism. However, it is very much encouraged to leave this mechanism on by default for all parachain nodes.
This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms.
However, if the principle of chain specification bootnodes is entirely replaced with the mechanism described in this RFC (which is the objective), then it becomes important whether the mechanism in this RFC can be abused in order to make a parachain unreachable.
@@ -3245,22 +3065,22 @@ Furthermore, when a large number of providers (here, a provider is a bootnode) a
For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target parachain. They are then in control of the parachain bootnodes.
Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term.
Furthermore, parachain clients are expected to cache a list of known good nodes on their disk. If the mechanism described in this RFC went down, it would only prevent new nodes from accessing the parachain, while clients that have connected before would not be affected.
-
-
+
+
The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours.
Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode.
Assuming 1000 parachain full nodes, the 20 Polkadot full nodes corresponding to a specific parachain will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a parachain full node registers itself to be the provider of the key corresponding to BabeApi_next_epoch.
Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the bootnodes of a parachain. Light clients are generally encouraged to cache the peers that they use between restarts, so they should only query these 20 Polkadot full nodes at their first initialization.
If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.
-Irrelevant.
-Irrelevant.
-None.
-While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?
-
+
It is possible that in the future a client could connect to a parachain without having to rely on a trusted parachain specification.
(source)
Table of Contents
@@ -3281,13 +3101,13 @@ If this every becomes a problem, this value of 20 is an arbitrary constant that
Authors Jonas Gehrlein The Polkadot UC will generate revenue from the sale of available Coretime. The question then arises: how should we handle these revenues? Broadly, there are two reasonable paths – burning the revenue and thereby removing it from total issuance or divert it to the Treasury. This Request for Comment (RFC) presents arguments favoring burning as the preferred mechanism for handling revenues from Coretime sales.
-How to handle the revenue accrued from Coretime sales is an important economic question that influences the value of DOT and should be properly discussed before deciding for either of the options. Now is the best time to start this discussion.
-Polkadot DOT token holders.
-This RFC discusses potential benefits of burning the revenue accrued from Coretime sales instead of diverting them to Treasury. Here are the following arguments for it.
It's in the interest of the Polkadot community to have a consistent and predictable Treasury income, because volatility in the inflow can be damaging, especially in situations when it is insufficient. As such, this RFC operates under the presumption of a steady and sustainable Treasury income flow, which is crucial for the Polkadot community's stability. The assurance of a predictable Treasury income, as outlined in a prior discussion here , or through other equally effective measures, serves as a baseline assumption for this argument.
Consequently, we need not concern ourselves with this particular issue here. This naturally begs the question - why should we introduce additional volatility to the Treasury by aligning it with the variable Coretime sales? It's worth noting that Coretime revenues often exhibit an inverse relationship with periods when Treasury spending should ideally be ramped up. During periods of low Coretime utilization (indicated by lower revenue), Treasury should spend more on projects and endeavours to increase the demand for Coretime. This pattern underscores that Coretime sales, by their very nature, are an inconsistent and unpredictable source of funding for the Treasury. Given the importance of maintaining a steady and predictable inflow, it's unnecessary to rely on another volatile mechanism. Some might argue that we could have both: a steady inflow (from inflation) and some added bonus from Coretime sales, but burning the revenue would offer further benefits as described below.
@@ -3330,13 +3150,13 @@ If this every becomes a problem, this value of 20 is an arbitrary constant that
Authors Joe Petrowski Since the introduction of the Collectives parachain, many groups have expressed interest in forming
new -- or migrating existing groups into -- on-chain collectives. While adding a new collective is
relatively simple from a technical standpoint, the Fellowship will need to merge new pallets into
the Collectives parachain for each new collective. This RFC proposes a means for the network to
ratify a new collective, thus instructing the Fellowship to instate it in the runtime.
-Many groups have expressed interest in representing collectives on-chain. Some of these include:
Parachain technical fellowship (new)
@@ -3352,12 +3172,12 @@ path to having its collective accepted on-chain as part of the protocol. Accepta
the Fellowship to include the new collective with a given initial configuration into the runtime.
However, the network, not the Fellowship, should ultimately decide which collectives are in the
interest of the network.
-
Polkadot stakeholders who would like to organize on-chain.
Technical Fellowship, in its role of maintaining system runtimes.
-The group that wishes to operate an on-chain collective should publish the following information:
Charter, including the collective's mandate and how it benefits Polkadot. This would be similar
@@ -3391,22 +3211,22 @@ Fellowship would help them identify the pallet indices associated with a given c
or not the Fellowship member agrees with removal.
Collective removal may also come with other governance calls, for example voiding any scheduled
Treasury spends that would fund the given collective.
-Passing a Root origin referendum is slow. However, given the network's investment (in terms of code
maintenance and salaries) in a new collective, this is an appropriate step.
-No impacts.
-
+
Generally all new collectives will be in the Collectives parachain. Thus, performance impacts
should strictly be limited to this parachain and not affect others. As the majority of logic for
collectives is generalized and reusable, we expect most collectives to be instances of similar
subsets of modules. That is, new collectives should generally be compatible with UIs and other
services that provide collective-related functionality, with little modifications to support new
ones.
-The launch of the Technical Fellowship, see the
initial forum post .
-None at this time.
(source)
Table of Contents
@@ -3443,13 +3263,13 @@ ones.
Authors Oliver Tale-Yazdi Introduces breaking changes to the Core runtime API by letting Core::initialize_block return an enum. The versions of Core is bumped from 4 to 5.
-The main feature that motivates this RFC are Multi-Block-Migrations (MBM); these make it possible to split a migration over multiple blocks.poll, that runs at the beginning of the block when there are no MBMs and has access to AllPalletsWithSystem. This hook can then be used to replace the use of on_initialize and on_finalize for non-deadline critical logic.System::PostInherents callback that always runs after all inherents were applied.
-
Substrate Maintainers: They have to implement this, including tests, audit and
maintenance burden.
@@ -3457,7 +3277,7 @@ maintenance burden.
Polkadot Parachain Teams: They have to adapt to the breaking changes but then eventually have
multi-block migrations available.
-This runtime API function is changed from returning () to ExtrinsicInclusionMode:
fn initialize_block(header: &<Block as BlockT>::Header)
@@ -3478,23 +3298,23 @@ multi-block migrations available.
1. Multi-Block-Migrations : The runtime is being put into lock-down mode for the duration of the migration process by returning OnlyInherents from initialize_block. This ensures that no user provided transaction can interfere with the migration process. It is absolutely necessary to ensure this, otherwise a transaction could call into un-migrated storage and violate storage invariants.
2. poll is possible by using apply_extrinsic as entry-point and not hindered by this approach. It would not be possible to use a pallet inherent like System::last_inherent to achieve this for two reasons: First is that pallets do not have access to AllPalletsWithSystem which is required to invoke the poll hook on all pallets. Second is that the runtime does currently not enforce an order of inherents.
3. System::PostInherents can be done in the same manner as poll.
-The previous drawback of cementing the order of inherents has been addressed and removed by redesigning the approach. No further drawbacks have been identified thus far.
-The new logic of initialize_block can be tested by checking that the block-builder will skip transactions when OnlyInherents is returned.
Security: n/a
Privacy: n/a
-
-
+
+
The performance overhead is minimal in the sense that no clutter was added after fulfilling the
requirements. The only performance difference is that initialize_block also returns an enum that needs to be passed through the WASM boundary. This should be negligible.
-The new interface allows for more extensible runtime logic. In the future, this will be utilized for
multi-block-migrations which should be a huge ergonomic advantage for parachain developers.
-The advice here is OPTIONAL and outside of the RFC. To not degrade
user experience, it is recommended to ensure that an updated node can still import historic blocks.
-The RFC is currently being implemented in polkadot-sdk#1781 (formerly substrate#14275 ). Related issues and merge
requests:
-Please suggest a better name for BlockExecutiveMode. We already tried: RuntimeExecutiveMode,
ExtrinsicInclusionMode. The names of the modes Normal and Minimal were also called
AllExtrinsics and OnlyInherents, so if you have naming preferences; please post them.ExtrinsicInclusionMode
Is post_inherents more consistent instead of last_inherent? Then we should change it.=> renamed to last_inherent
-
+
The long-term future here is to move the block building logic into the runtime. Currently there is a tight dance between the block author and the runtime; the author has to call into different runtime functions in quick succession and exact order. Any misstep causes the block to be invalid.
(source)
@@ -3548,14 +3368,14 @@ This can be unified and simplified by moving both parts into the runtime.
Authors Bryan Chen This RFC proposes a set of changes to the parachain lock mechanism. The goal is to allow a parachain manager to self-service the parachain without root track governance action.
This is achieved by remove existing lock conditions and only lock a parachain when:
A parachain manager explicitly lock the parachain
OR a parachain block is produced successfully
-The manager of a parachain has permission to manage the parachain when the parachain is unlocked. Parachains are by default locked when onboarded to a slot. This requires the parachain wasm/genesis must be valid, otherwise a root track governance action on relaychain is required to update the parachain.
The current reliance on root track governance actions for managing parachains can be time-consuming and burdensome. This RFC aims to address this technical difficulty by allowing parachain managers to take self-service actions, rather than relying on general public voting.
The key scenarios this RFC seeks to improve are:
@@ -3574,12 +3394,12 @@ This can be unified and simplified by moving both parts into the runtime.
A parachain SHOULD be locked when it successfully produced the first block.
A parachain manager MUST be able to perform lease swap without having a running parachain.
-
Parachain teams
Parachain users
-A parachain can either be locked or unlocked. With parachain locked, the parachain manager does not have any privileges. With parachain unlocked, the parachain manager can perform following actions with the paras_registrar pallet:
@@ -3619,31 +3439,31 @@ This can be unified and simplified by moving both parts into the runtime.
Parachain never produced a block. Including from expired leases.
Parachain manager never explicitly lock the parachain.
-Parachain locks are designed in such way to ensure the decentralization of parachains. If parachains are not locked when it should be, it could introduce centralization risk for new parachains.
For example, one possible scenario is that a collective may decide to launch a parachain fully decentralized. However, if the parachain is unable to produce block, the parachain manager will be able to replace the wasm and genesis without the consent of the collective.
It is considered this risk is tolerable as it requires the wasm/genesis to be invalid at first place. It is not yet practically possible to develop a parachain without any centralized risk currently.
Another case is that a parachain team may decide to use crowdloan to help secure a slot lease. Previously, creating a crowdloan will lock a parachain. This means crowdloan participants will know exactly the genesis of the parachain for the crowdloan they are participating. However, this actually providers little assurance to crowdloan participants. For example, if the genesis block is determined before a crowdloan is started, it is not possible to have onchain mechanism to enforce reward distributions for crowdloan participants. They always have to rely on the parachain team to fulfill the promise after the parachain is alive.
Existing operational parachains will not be impacted.
-The implementation of this RFC will be tested on testnets (Rococo and Westend) first.
An audit maybe required to ensure the implementation does not introduce unwanted side effects.
There is no privacy related concerns.
-
+
This RFC should not introduce any performance impact.
-This RFC should improve the developer experiences for new and existing parachain teams
-This RFC is fully compatibility with existing interfaces.
-
Parachain Slot Extension Story: https://github.com/paritytech/polkadot/issues/4758
Allow parachain to renew lease without actually run another parachain: https://github.com/paritytech/polkadot/issues/6685
Always treat parachain that never produced block for a significant amount of time as unlocked: https://github.com/paritytech/polkadot/issues/7539
-None at this stage.
-
+
This RFC is only intended to be a short term solution. Slots will be removed in future and lock mechanism is likely going to be replaced with a more generalized parachain manage & recovery system in future. Therefore long term impacts of this RFC are not considered.
-Encointer is a system chain on Kusama since Jan 2022 and has been developed and maintained by the Encointer association. This RFC proposes to treat Encointer like any other system chain and include it in the fellowship repo with this PR .
-Encointer does not seek to be in control of its runtime repository. As a decentralized system, the fellowship has a more suitable structure to maintain a system chain runtime repo than the Encointer association does.
Also, Encointer aims to update its runtime in batches with other system chains in order to have consistency for interoperability across system chains.
-
Fellowship: Will continue to take upon them the review and auditing work for the Encointer runtime, but the process is streamlined with other system chains and therefore less time-consuming compared to the separate repo and CI process we currently have.
Kusama Network: Tokenholders can easily see the changes of all system chains in one place.
Encointer Association: Further decentralization of the Encointer Network necessities like devops.
Encointer devs: Being able to work directly in the Fellowship runtimes repo to streamline and synergize with other developers.
-Our PR has all details about our runtime and how we would move it into the fellowship repo.
Noteworthy: All Encointer-specific pallets will still be located in encointer's repo for the time being: https://github.com/encointer/pallets
It will still be the duty of the Encointer team to keep its runtime up to date and provide adequate test fixtures. Frequent dependency bumps with Polkadot releases would be beneficial for interoperability and could be streamlined with other system chains but that will not be a duty of fellowship. Whenever possible, all system chains could be upgraded jointly (including Encointer) with a batch referendum.
@@ -3698,17 +3518,17 @@ This can be unified and simplified by moving both parts into the runtime.
Encointer will publish all its crates crates.io
Encointer does not carry out external auditing of its runtime nor pallets. It would be beneficial but not a requirement from our side if Encointer could join the auditing process of other system chains.
-Other than all other system chains, development and maintenance of the Encointer Network is mainly financed by the KSM Treasury and possibly the DOT Treasury in the future. Encointer is dedicated to maintaining its network and runtime code for as long as possible, but there is a dependency on funding which is not in the hands of the fellowship. The only risk in the context of funding, however, is that the Encointer runtime will see less frequent updates if there's less funding.
-No changes to the existing system are proposed. Only changes to how maintenance is organized.
-
+
No changes
-Existing Encointer runtime repo
-None identified
-
+
More info on Encointer: encointer.org
(source)
Table of Contents
@@ -4628,11 +4448,11 @@ other privacy-enhancing mechanisms to address this concern.
Authors Joe Petrowski, Gavin Wood The Relay Chain contains most of the core logic for the Polkadot network. While this was necessary
prior to the launch of parachains and development of XCM, most of this logic can exist in
parachains. This is a proposal to migrate several subsystems into system parachains.
-Polkadot's scaling approach allows many distinct state machines (known generally as parachains) to
operate with common guarantees about the validity and security of their state transitions. Polkadot
provides these common guarantees by executing the state transitions on a strict subset (a backing
@@ -4644,13 +4464,13 @@ blockspace) to the network.
By minimising state transition logic on the Relay Chain by migrating it into "system chains" -- a
set of parachains that, with the Relay Chain, make up the Polkadot protocol -- the Polkadot
Ubiquitous Computer can maximise its primary offering: secure blockspace.
-
Parachains that interact with affected logic on the Relay Chain;
Core protocol and XCM format developers;
Tooling, block explorer, and UI developers.
-The following pallets and subsystems are good candidates to migrate from the Relay Chain:
Identity
@@ -4796,36 +4616,36 @@ sensible to rehearse a migration.
Staking is the subsystem most constrained by PoV limits. Ensuring that elections, payouts, session
changes, offences/slashes, etc. work in a parachain on Kusama -- with its larger validator set --
will give confidence to the chain's robustness on Polkadot.
-These subsystems will have reduced resources in cores than on the Relay Chain. Staking in particular
may require some optimizations to deal with constraints.
-Standard audit/review requirements apply. More powerful multi-chain integration test tools would be
useful in developement.
-
+
Describe the impact of the proposal on the exposed functionality of Polkadot.
-
+
This is an optimization. The removal of public/user transactions on the Relay Chain ensures that its
primary resources are allocated to system performance.
-This proposal alters very little for coretime users (e.g. parachain developers). Application
developers will need to interact with multiple chains, making ergonomic light client tools
particularly important for application development.
For existing parachains that interact with these subsystems, they will need to configure their
runtimes to recognize the new locations in the network.
-Implementing this proposal will require some changes to pallet APIs and/or a pub-sub protocol.
Application developers will need to interact with multiple chains in the network.
-There remain some implementation questions, like how to use balances for both Staking and
Governance. See, for example, Moving Staking off the Relay
Chain .
-
+
Ideally the Relay Chain becomes transactionless, such that not even balances are represented there.
With Staking and Governance off the Relay Chain, this is not an unreasonable next step.
With Identity on Polkadot, Kusama may opt to drop its People Chain.
@@ -4860,13 +4680,13 @@ With Staking and Governance off the Relay Chain, this is not an unreasonable nex
Authors Vedhavyas Singareddi At the moment, we have system_version field on RuntimeVersion that derives which state version is used for the
Storage.
We have a use case where we want extrinsics root is derived using StateVersion::V1. Without defining a new field
under RuntimeVersion,
we would like to propose adding system_version that can be used to derive both storage and extrinsic state version.
-Since the extrinsic state version is always StateVersion::V0, deriving extrinsic root requires full extrinsic data.
This would be problematic when we need to verify the extrinsics root if the extrinsic sizes are bigger. This problem is
further explored in https://github.com/polkadot-fellows/RFCs/issues/19
@@ -4878,11 +4698,11 @@ One of the main challenge here is some extrinsics could be big enough that this
included in the Consensus block due to Block's weight restriction.
If the extrinsic root is derived using StateVersion::V1, then we do not need to pass the full extrinsic data but
rather at maximum, 32 byte of extrinsic data.
-
Technical Fellowship, in its role of maintaining system runtimes.
-In order to use project specific StateVersion for extrinsic roots, we proposed
an implementation that introduced
parameter to frame_system::Config but that unfortunately did not feel correct.
@@ -4908,26 +4728,26 @@ pub const VERSION: RuntimeVersion = RuntimeVersion {
system_version: 1,
};
}
There should be no drawbacks as it would replace state_version with same behavior but documentation should be updated
so that chains know which system_version to use.
-AFAIK, should not have any impact on the security or privacy.
-
+
These changes should be compatible for existing chains if they use state_version value for system_verision.
-
+
I do not believe there is any performance hit with this change.
-This does not break any exposed Apis.
-This change should not break any compatibility.
-We proposed introducing a similar change by introducing a
parameter to frame_system::Config but did not feel that
is the correct way of introducing this change.
-I do not have any specific questions about this change at the moment.
-
+
IMO, this change is pretty self-contained and there won't be any future work necessary.
(source)
Table of Contents
@@ -4956,9 +4776,9 @@ is the correct way of introducing this change.
Authors Sebastian Kunert This RFC proposes a new host function for parachains, storage_proof_size. It shall provide the size of the currently recorded storage proof to the runtime. Runtime authors can use the proof size to improve block utilization by retroactively reclaiming unused storage weight.
-The number of extrinsics that are included in a parachain block is limited by two constraints: execution time and proof size. FRAME weights cover both concepts, and block-builders use them to decide how many extrinsics to include in a block. However, these weights are calculated ahead of time by benchmarking on a machine with reference hardware. The execution-time properties of the state-trie and its storage items are unknown at benchmarking time. Therefore, we make some assumptions about the state-trie:
Trie Depth: We assume a trie depth to account for intermediary nodes.These pessimistic assumptions lead to an overestimation of storage weight, negatively impacting block utilization on parachains.
In addition, the current model does not account for multiple accesses to the same storage items. While these repetitive accesses will not increase storage-proof size, the runtime-side weight monitoring will account for them multiple times. Since the proof size is completely opaque to the runtime, we can not implement retroactive storage weight correction.
A solution must provide a way for the runtime to track the exact storage-proof size consumed on a per-extrinsic basis.
-
Parachain Teams: They MUST include this host function in their runtime and node.Light-client Implementors: They SHOULD include this host function in their runtime and node.
-This RFC proposes a new host function that exposes the storage-proof size to the runtime. As a result, runtimes can implement storage weight reclaiming mechanisms that improve block utilization.
This RFC proposes the following host function signature:
#![allow(unused)]
@@ -4980,14 +4800,14 @@ is the correct way of introducing this change.
fn ext_storage_proof_size_version_1() -> u64;
} The host function MUST return an unsigned 64-bit integer value representing the current proof size. In block-execution and block-import contexts, this function MUST return the current size of the proof. To achieve this, parachain node implementors need to enable proof recording for block imports. In other contexts, this function MUST return 18446744073709551615 (u64::MAX), which represents disabled proof recording.
-
-
+
+
Parachain nodes need to enable proof recording during block import to correctly implement the proposed host function. Benchmarking conducted with balance transfers has shown a performance reduction of around 0.6% when proof recording is enabled.
-The host function proposed in this RFC allows parachain runtime developers to keep track of the proof size. Typical usage patterns would be to keep track of the overall proof size or the difference between subsequent calls to the host function.
-Parachain teams will need to include this host function to upgrade.
-
Pull Request including proposed host function: PoV Reclaim (Clawback) Node Side .
Issue with discussion: [FRAME core] Clawback PoV Weights For Dispatchables
@@ -5041,12 +4861,12 @@ is the correct way of introducing this change.
Authors Aurora Poppyseed , Just_Luuuu , Viki Val , Joe Petrowski This RFC proposes changing the current deposit requirements on the Polkadot and Kusama Asset Hub for
creating an NFT collection, minting an individual NFT, and lowering its corresponding metadata and
attribute deposits. The objective is to lower the barrier to entry for NFT creators, fostering a
more inclusive and vibrant ecosystem while maintaining network integrity and preventing spam.
-The current deposit of 10 DOT for collection creation (along with 0.01 DOT for item deposit and 0.2
DOT for metadata and attribute deposits) on the Polkadot Asset Hub and 0.1 KSM on Kusama Asset Hub
presents a significant financial barrier for many NFT creators. By lowering the deposit
@@ -5063,7 +4883,7 @@ low.
Deposits SHOULD be derived from deposit function, adjusted by correspoding pricing mechansim.
-
NFT Creators : Primary beneficiaries of the proposed change, particularly those who found the
current deposit requirements prohibitive.Previous discussions have been held within the Polkadot
Forum , with
artists expressing their concerns about the deposit amounts.
-This RFC proposes a revision of the deposit constants in the configuration of the NFTs pallet on the
Polkadot Asset Hub. The new deposit amounts would be determined by a standard deposit formula.
As of v1.1.1, the Collection Deposit is 10 DOT and the Item Deposit is 0.01 DOT (see
@@ -5148,7 +4968,7 @@ application to avoid sudden rate changes, as in:
where the constant a moves the inflection to lower or higher x values, the constant b adjusts
the rate of the deposit increase, and the independent variable x is the number of collections or
items, depending on application.
-Modifying deposit requirements necessitates a balanced assessment of the potential drawbacks.
Highlighted below are cogent points extracted from the discourse on the Polkadot Forum
conversation ,
@@ -5177,22 +4997,22 @@ stakeholders wouldn't be much affected. As of date 9th January 2024 there are 42
Polkadot Asset Hub and 191 on Kusama Asset Hub with a relatively low volume.
-As noted above, state bloat is a security concern. In the case of abuse, governance could adapt by
increasing deposit rates and/or using forceDestroy on collections agreed to be spam.
-
-
+
+
The primary performance consideration stems from the potential for state bloat due to increased
activity from lower deposit requirements. It's vital to monitor and manage this to avoid any
negative impact on the chain's performance. Strategies for mitigating state bloat, including
efficient data management and periodic reviews of storage requirements, will be essential.
-The proposed change aims to enhance the user experience for artists, traders, and utilizers of
Kusama and Polkadot Asset Hubs, making Polkadot and Kusama more accessible and user-friendly.
-The change does not impact compatibility as a redeposit function is already implemented.
-If this RFC is accepted, there should not be any unresolved questions regarding how to adapt the
implementation of deposits for NFT collections.
Authors Alin Dima Propose a way of permuting the availability chunk indices assigned to validators, in the context of
recovering available data from systematic chunks , with the
purpose of fairly distributing network bandwidth usage.
-Currently, the ValidatorIndex is always identical to the ChunkIndex. Since the validator array is only shuffled once
per session, naively using the ValidatorIndex as the ChunkIndex would pose an unreasonable stress on the first N/3
validators during an entire session, when favouring availability recovery from systematic chunks.
@@ -5292,9 +5112,9 @@ validators during an entire session, when favouring availability recovery from s
systematic availability chunks to different validators, based on the relay chain block and core.
The main purpose is to ensure fair distribution of network bandwidth usage for availability recovery in general and in
particular for systematic chunk holders.
-Relay chain node core developers.
-An erasure coding algorithm is considered systematic if it preserves the original unencoded data as part of the
resulting code.
@@ -5448,7 +5268,7 @@ struct (added in https://github.com/paritytech/polkadot-sdk/pull/2177Configuration::set_node_feature extrinsic. Once the feature is enabled and new configuration is live, the
validator->chunk mapping ceases to be a 1:1 mapping and systematic recovery may begin.
-
Getting access to the core_index that used to be occupied by a candidate in some parts of the dispute protocol is
very complicated (See appendix A ). This RFC assumes that availability-recovery processes initiated during
@@ -5458,28 +5278,28 @@ mitigate this problem and will likely be needed in the future for CoreJam and/or
Related discussion about updating CandidateReceipt
It's a breaking change that requires all validators and collators to upgrade their node version at least once.
-Extensive testing will be conducted - both automated and manual.
This proposal doesn't affect security or privacy.
-
-
+
+
This is a necessary data availability optimisation, as reed-solomon erasure coding has proven to be a top consumer of
CPU time in polkadot as we scale up the parachain block size and number of availability cores.
With this optimisation, preliminary performance results show that CPU time used for reed-solomon coding/decoding can be
halved and total POV recovery time decrease by 80% for large POVs. See more
here .
-Not applicable.
-This is a breaking change. See upgrade path section above.
All validators and collators need to have upgraded their node versions before the feature will be enabled via a
governance call.
-See comments on the tracking issue and the
in-progress PR
-Not applicable.
-
+
This enables future optimisations for the performance of availability recovery, such as retrieving batched systematic
chunks from backers/approval-checkers.
Authors Bastian Köcher This RFC proposes to changes the SessionKeys::generate_session_keys runtime api interface. This runtime api is used by validator operators to
generate new session keys on a node. The public session keys are then registered manually on chain by the validator operator.
Before this RFC it was not possible by the on chain logic to ensure that the account setting the public session keys is also in
@@ -5562,7 +5382,7 @@ possession of the private session keys. To solve this the RFC proposes to pass t
registration on chain to generate_session_keys. Further this RFC proposes to change the return value of the generate_session_keys
function also to not only return the public session keys, but also the proof of ownership for the private session keys. The
validator operator will then need to send the public session keys and the proof together when registering new session keys on chain.
-When submitting the new public session keys to the on chain logic there doesn't exist any verification of possession of the private session keys.
This means that users can basically register any kind of public session keys on chain. While the on chain logic ensures that there are
no duplicate keys, someone could try to prevent others from registering new session keys by setting them first. While this wouldn't bring
@@ -5570,13 +5390,13 @@ the "attacker" any kind of advantage, more like disadvantages (potenti
e.g. changing its session key in the event of a private session key leak.
After this RFC this kind of attack would not be possible anymore, because the on chain logic can verify that the sending account
is in ownership of the private session keys.
-
Polkadot runtime implementors
Polkadot node implementors
Validator operators
-We are first going to explain the proof format being used:
#![allow(unused)]
fn main() {
@@ -5610,31 +5430,31 @@ actual exported function signature looks like:
already gets the proof passed as Vec<u8>. This proof needs to be decoded to
the actual Proof type as explained above. The proof and the SCALE encoded
account_id of the sender are used to verify the ownership of the SessionKeys.
-Validator operators need to pass the their account id when rotating their session keys in a node.
This will require updating some high level docs and making users familiar with the slightly changed ergonomics.
-Testing of the new changes only requires passing an appropriate owner for the current testing context.
The changes to the proof generation and verification got audited to ensure they are correct.
-
-
+
+
The session key generation is an offchain process and thus, doesn't influence the performance of the
chain. Verifying the proof is done on chain as part of the transaction logic for setting the session keys.
The verification of the proof is a signature verification number of individual session keys times. As setting
the session keys is happening quite rarely, it should not influence the overall system performance.
-The interfaces have been optimized to make it as easy as possible to generate the ownership proof.
-Introduces a new version of the SessionKeys runtime api. Thus, nodes should be updated before
a runtime is enacted that contains these changes otherwise they will fail to generate session keys.
The RPC that exists around this runtime api needs to be updated to support passing the account id
and for returning the ownership proof alongside the public session keys.
UIs would need to be updated to support the new RPC and the changed on chain logic.
-None.
-None.
-
+
Substrate implementation of the RFC .
(source)
Table of Contents
@@ -5672,10 +5492,10 @@ and for returning the ownership proof alongside the public session keys.
Authors Joe Petrowski, Gavin Wood The Fellowship Manifesto states that members should receive a monthly allowance on par with gross
income in OECD countries. This RFC proposes concrete amounts.
-One motivation for the Technical Fellowship is to provide an incentive mechanism that can induct and
retain technical talent for the continued progress of the network.
In order for members to uphold their commitment to the network, they should receive support to
@@ -5685,12 +5505,12 @@ on par with a full-time job. Providing a livable wage to those making such contr
pragmatic to work full-time on Polkadot.
Note: Goals of the Fellowship, expectations for each Dan, and conditions for promotion and demotion
are all explained in the Manifesto. This RFC is only to propose concrete values for allowances.
-
Fellowship members
Polkadot Treasury
-This RFC proposes agreeing on salaries relative to a single level, the III Dan. As such, changes to
the amount or asset used would only be on a single value, and all others would adjust relatively. A
III Dan is someone whose contributions match the expectations of a full-time individual contributor.
@@ -5750,19 +5570,19 @@ other hand, more people will likely join the Fellowship in the coming years.
Updates to these levels, whether relative ratios, the asset used, or the amount, shall be done via
RFC.
-By not using DOT for payment, the protocol relies on the stability of other assets and the ability
to acquire them. However, the asset of choice can be changed in the future.
-N/A.
-
-
+
+
N/A
-N/A
-N/A
-None at present.
(source)
Table of Contents
@@ -5803,11 +5623,11 @@ States
Authors Pierre Krieger When two peers connect to each other, they open (amongst other things) a so-called "notifications protocol" substream dedicated to gossiping transactions to each other.
Each notification on this substream currently consists in a SCALE-encoded Vec<Transaction> where Transaction is defined in the runtime.
This RFC proposes to modify the format of the notification to become (Compact(1), Transaction). This maintains backwards compatibility, as this new format decodes as a Vec of length equal to 1.
-There exists three motivations behind this change:
@@ -5820,9 +5640,9 @@ States
It makes the implementation way more straight-forward by not having to repeat code related to back-pressure. See explanations below.
-Low-level developers.
-To give an example, if you send one notification with three transactions, the bytes that are sent on the wire are:
concat(
leb128(total-size-in-bytes-of-the-rest),
@@ -5842,23 +5662,23 @@ A SCALE-compact encoded 1 is one byte of value 4. In o
This is equivalent to forcing the Vec<Transaction> to always have a length of 1, and I expect the Substrate implementation to simply modify the sending side to add a for loop that sends one notification per item in the Vec.
As explained in the motivation section, this allows extracting scale(transaction) items without having to know how to decode them.
By "flattening" the two-steps hierarchy, an implementation only needs to back-pressure individual notifications rather than back-pressure notifications and transactions within notifications.
-This RFC chooses to maintain backwards compatibility at the cost of introducing a very small wart (the Compact(1)).
An alternative could be to introduce a new version of the transactions notifications protocol that sends one Transaction per notification, but this is significantly more complicated to implement and can always be done later in case the Compact(1) is bothersome.
-Irrelevant.
-
-
+
+
Irrelevant.
-Irrelevant.
-The change is backwards compatible if done in two steps: modify the sender to always send one transaction per notification, then, after a while, modify the receiver to enforce the new format.
-Irrelevant.
-None.
-
+
None. This is a simple isolated change.
(source)
Table of Contents
@@ -5898,20 +5718,20 @@ This is equivalent to forcing the Vec<Transaction> to always
Authors Pierre Krieger This RFC proposes to make the mechanism of RFC #8 more generic by introducing the concept of "capabilities".
Implementations can implement certain "capabilities", such as serving old block headers or being a parachain bootnode.
The discovery mechanism of RFC #8 is extended to be able to discover nodes of specific capabilities.
-The Polkadot peer-to-peer network is made of nodes. Not all these nodes are equal. Some nodes store only the headers of recent blocks, some nodes store all the block headers and bodies since the genesis, some nodes store the storage of all blocks since the genesis, and so on.
It is currently not possible to know ahead of time (without connecting to it and asking) which nodes have which data available, and it is not easily possible to build a list of nodes that have a specific piece of data available.
If you want to download for example the header of block 500, you have to connect to a randomly-chosen node, ask it for block 500, and if it says that it doesn't have the block, disconnect and try another randomly-chosen node.
In certain situations such as downloading the storage of old blocks, nodes that have the information are relatively rare, and finding through trial and error a node that has the data can take a long time.
This RFC attempts to solve this problem by giving the possibility to build a list of nodes that are capable of serving specific data.
-Low-level client developers.
People interested in accessing the archive of the chain.
-Reading RFC #8 first might help with comprehension, as this RFC is very similar.
Please keep in mind while reading that everything below applies for both relay chains and parachains, except mentioned otherwise.
Implementations that have the head of the chain provider capability do not register themselves as providers, but instead are the nodes that participate in the main DHT. In other words, they are the nodes that serve requests of the /<genesis_hash>/kad protocol.
Any implementation that isn't a head of the chain provider (read: light clients) must not participate in the main DHT. This is already presently the case.
Implementations must not participate in the main DHT if they don't fulfill the capability yet. For example, a node that is still in the process of warp syncing must not participate in the main DHT. However, assuming that warp syncing doesn't last more than a few seconds, it is acceptable to ignore this requirement in order to avoid complicating implementations too much.
-None that I can see.
-The content of this section is basically the same as the one in RFC 8.
This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms.
Due to the way Kademlia works, it would become the responsibility of the 20 Polkadot nodes whose sha256(peer_id) is closest to the key (described in the explanations section) to store the list of nodes that have specific capabilities.
Furthermore, when a large number of providers are registered, only the providers closest to the key are kept, up to a certain implementation-defined limit.
For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target capability. They are then in control of the list of nodes with that capability. While doing this can in no way be actually harmful, it could lead to eclipse attacks.
Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term.
-
-
+
+
The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours.
Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode.
Assuming 1000 nodes with a specific capability, the 20 Polkadot full nodes corresponding to that capability will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a node registers itself to be the provider of the key corresponding to BabeApi_next_epoch.
Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the nodes with a capability. If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.
-Irrelevant.
-Irrelevant.
-Unknown.
-While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?
-
+
This RFC would make it possible to reliably discover archive nodes, which would make it possible to reliably send archive node requests, something that isn't currently possible. This could solve the problem of finding archive RPC node providers by migrating archive-related request to using the native peer-to-peer protocol rather than JSON-RPC.
If we ever decide to break backwards compatibility, we could divide the "history" and "archive" capabilities in two, between nodes capable of serving older blocks and nodes capable of serving newer blocks.
We could even add to the peer-to-peer network nodes that are only capable of serving older blocks (by reading from a database) but do not participate in the head of the chain, and that just exist for historical purposes.
@@ -6019,12 +5839,12 @@ We could even add to the peer-to-peer network nodes that are only capable of ser
Authors Zondax AG, Parity Technologies To interact with chains in the Polkadot ecosystem it is required to know how transactions are encoded and how to read state. For doing this, Polkadot-SDK, the framework used by most of the chains in the Polkadot ecosystem, exposes metadata about the runtime to the outside. UIs, wallets, and others can use this metadata to interact with these chains. This makes the metadata a crucial piece of the transaction encoding as users are relying on the interacting software to encode the transactions in the correct format.
It gets even more important when the user signs the transaction in an offline wallet, as the device by its nature cannot get access to the metadata without relying on the online wallet to provide it. This makes it so that the offline wallet needs to trust an online party, deeming the security assumptions of the offline devices, mute.
This RFC proposes a way for offline wallets to leverage metadata, within the constraints of these. The design idea is that the metadata is chunked and these chunks are put into a merkle tree. The root hash of this merkle tree represents the metadata. The offline wallets can use the root hash to decode transactions by getting proofs for the individual chunks of the metadata. This root hash is also included in the signed data of the transaction (but not sent as part of the transaction). The runtime is then including its known metadata root hash when verifying the transaction. If the metadata root hash known by the runtime differs from the one that the offline wallet used, it very likely means that the online wallet provided some fake data and the verification of the transaction fails.
Users depend on offline wallets to correctly display decoded transactions before signing. With merkleized metadata, they can be assured of the transaction's legitimacy, as incorrect transactions will be rejected by the runtime.
-Polkadot's innovative design (both relay chain and parachains) present the ability to developers to upgrade their network as frequently as they need. These systems manage to have integrations working after the upgrades with the help of FRAME Metadata. This Metadata, which is in the order of half a MiB for most Polkadot-SDK chains, completely describes chain interfaces and properties. Securing this metadata is key for users to be able to interact with the Polkadot-SDK chain in the expected way.
On the other hand, offline wallets provide a secure way for Blockchain users to hold their own keys (some do a better job than others). These devices seldomly get upgraded, usually account for one particular network and hold very small internal memories. Currently in the Polkadot ecosystem there is no secure way of having these offline devices know the latest Metadata of the Polkadot-SDK chain they are interacting with. This results in a plethora of similar yet slightly different offline wallets for all different Polkadot-SDK chains, as well as the impediment of keeping these regularly updated, thus not fully leveraging Polkadot-SDK’s unique forkless upgrade feature.
The two main reasons why this is not possible today are:
@@ -6051,14 +5871,14 @@ We could even add to the peer-to-peer network nodes that are only capable of ser
Chunks handling mechanism SHOULD support chunks being sent in any order without memory utilization overhead;
Unused enum variants MUST be stripped (this has great impact on transmitted metadata size; examples: era enum, enum with all calls for call batching).
-
Runtime implementors
UI/wallet implementors
Offline wallet implementors
The idea for this RFC was brought up by runtime implementors and was extensively discussed with offline wallet implementors. It was designed in such a way that it can work easily with the existing offline wallet solutions in the Polkadot ecosystem.
-The FRAME metadata provides a wide range of information about a FRAME based runtime. It contains information about the pallets, the calls per pallet, the storage entries per pallet, runtime APIs, and type information about most of the types that are used in the runtime. For decoding extrinsics on an offline wallet, what is mainly required is type information. Most of the other information in the FRAME metadata is actually not required for decoding extrinsics and thus it can be removed. Therefore, the following is a proposal on a custom representation of the metadata and how this custom metadata is chunked, ensuring that only the needed chunks required for decoding a particular extrinsic are sent to the offline wallet. The necessary information to transform the FRAME metadata type information into the type information presented in this RFC will be provided. However, not every single detail on how to convert from FRAME metadata into the RFC type information is described.
First, the MetadataDigest is introduced. After that, ExtrinsicMetadata is covered and finally the actual format of the type information. Then pruning of unrelated type information is covered and how to generate the TypeRefs. In the latest step, merkle tree calculation is explained.
@@ -6329,23 +6149,23 @@ nodes: [[[2, 3], [4, 5]], [0, 1]]
Included in the extrinsic is u8, the "mode". The mode is either 0 which means to not include the metadata hash in the signed data or the mode is 1 to include the metadata hash in V1.
Included in the signed data is an Option<[u8; 32]>. Depending on the mode the value is either None or Some(metadata_hash).
-The chunking may not be the optimal case for every kind of offline wallet.
-All implementations are required to strictly follow the RFC to generate the metadata hash. This includes which hash function to use and how to construct the metadata types tree. So, all implementations are following the same security criteria. As the chains will calculate the metadata hash at compile time, the build process needs to be trusted. However, this is already a solved problem in the Polkadot ecosystem by using reproducible builds. So, anyone can rebuild a chain runtime to ensure that a proposal is actually containing the changes as advertised.
Implementations can also be tested easily against each other by taking some metadata and ensuring that they all come to the same metadata hash.
Privacy of users should also not be impacted. This assumes that wallets will generate the metadata hash locally and don't leak any information to third party services about which chunks a user will send to their offline wallet. Besides that, there is no leak of private information as getting the raw metadata from the chain is an operation that is done by almost everyone.
-
-
+
+
There should be no measurable impact on performance to Polkadot or any other chain using this feature. The metadata root hash is calculated at compile time and at runtime it is optionally used when checking the signature of a transaction. This means that at runtime no performance heavy operations are done.
The proposal alters the way a transaction is built, signed, and verified. So, this imposes some required changes to any kind of developer who wants to construct transactions for Polkadot or any chain using this feature. As the developer can pass 0 for disabling the verification of the metadata root hash, it can be easily ignored.
-RFC 46 produced by the Alzymologist team is a previous work reference that goes in this direction as well.
On other ecosystems, there are other solutions to the problem of trusted signing. Cosmos for example has a standardized way of transforming a transaction into some textual representation and this textual representation is included in the signed data. Basically achieving the same as what the RFC proposes, but it requires that for every transaction applied in a block, every node in the network always has to generate this textual representation to ensure the transaction signature is valid.
-None.
-
+
Does it work with all kind of offline wallets?
Generic types currently appear multiple times in the metadata with each instantiation. It could be may be useful to have generic type only once in the metadata and declare the generic parameters at their instantiation.
@@ -6383,20 +6203,20 @@ nodes: [[[2, 3], [4, 5]], [0, 1]]
Authors George Pisaltu This RFC proposes a change to the extrinsic format to incorporate a new transaction type, the "general" transaction.
-"General" transactions, a new type of transaction that this RFC aims to support, are transactions which obey the runtime's extensions and have according extension data yet do not have hard-coded signatures. They are first described in Extrinsic Horizon and supported in 3685 . They enable users to authorize origins in new, more flexible ways (e.g. ZK proofs, mutations over pre-authenticated origins). As of now, all transactions are limited to the account signing model for origin authorization and any additional origin changes happen in extrinsic logic, which cannot leverage the validation process of extensions.
An example of a use case for such an extension would be sponsoring the transaction fee for some other user. A new extension would be put in place to verify that a part of the initial payload was signed by the author under who the extrinsic should run and change the origin, but the payment for the whole transaction should be handled under a sponsor's account. A POC for this can be found in 3712 .
The new "general" transaction type would coexist with both current transaction types for a while and, therefore, the current number of supported transaction types, capped at 2, is insufficient. A new extrinsic type must be introduced alongside the current signed and unsigned types. Currently, an encoded extrinsic's first byte indicate the type of extrinsic using the most significant bit - 0 for unsigned, 1 for signed - and the 7 following bits indicate the extrinsic format version , which has been equal to 4 for a long time.
By taking one bit from the extrinsic format version encoding, we can support 2 additional extrinsic types while also having a minimal impact on our capability to extend and change the extrinsic format in the future.
-
Runtime users
Runtime devs
Wallet devs
-An extrinsic is currently encoded as one byte to identify the extrinsic type and version. This RFC aims to change the interpretation of this byte regarding the reserved bits for the extrinsic type and version. In the following explanation, bits represented using T make up the extrinsic type and bits represented using V make up the extrinsic version.
Currently, the bit allocation within the leading encoded byte is 0bTVVV_VVVV. In practice in the Polkadot ecosystem, the leading byte would be 0bT000_0100 as the version has been equal to 4 for a long time.
This RFC proposes for the bit allocation to change to 0bTTVV_VVVV. As a result, the extrinsic format version will be bumped to 5 and the extrinsic type bit representation would change as follows:
@@ -6407,23 +6227,23 @@ nodes: [[[2, 3], [4, 5]], [0, 1]]
11 reserved This change would reduce the maximum possible transaction version from the current 127 to 63. In order to bypass the new, lower limit, the extrinsic format would have to change again.
-There is no impact on testing, security or privacy.
-
+
This change would allow Polkadot to support new types of transactions, with the specific "general" transaction type in mind at the time of writing this proposal.
-
+
There is no performance impact.
-The impact to developers and end-users is minimal as it would just be a bitmask update on their part for parsing the extrinsic type along with the version.
-This change breaks backwards compatiblity because any transaction that is neither signed nor unsigned, but a new transaction type, would be interpreted as having a future extrinsic format version.
-The original design was originally proposed in the TransactionExtension PR
-None.
-
+
Following this change, the "general" transaction type will be introduced as part of the Extrinsic Horizon effort, which will shape future work.
(source)
Table of Contents
@@ -6456,16 +6276,16 @@ nodes: [[[2, 3], [4, 5]], [0, 1]]
Authors Alex Gheorghe (alexggh) Extend the DHT authority discovery records with a signed creation time, so that nodes can determine which record is newer and always decide to prefer the newer records to the old ones.
-Currently, we use the Kademlia DHT for storing records regarding the p2p address of an authority discovery key, the problem is that if the nodes decide to change its PeerId/Network key it will publish a new record, however because of the distributed and replicated nature of the DHT there is no way to tell which record is newer so both old PeerId and the new PeerId will live in the network until the old one expires(36h), that creates all sort of problem and leads to the node changing its address not being properly connected for up to 36h.
After this RFC, nodes are extended to decide to keep the new record and propagate the new record to nodes that have the old record stored, so in the end all the nodes will converge faster to the new record(in the order of minutes, not 36h)
Implementation of the rfc: https://github.com/paritytech/polkadot-sdk/pull/3786.
Current issue without this enhacement: https://github.com/paritytech/polkadot-sdk/issues/3673
-Polkadot node developers.
-This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot.
You can find a link to the specification here .
In a nutshell, on a specific node the current authority-discovery protocol publishes Kademila DHT records at startup and periodically. The records contain the full address of the node for each authorithy key it owns. The node tries also to find the full address of all authorities in the network by querying the DHT and picking up the first record it finds for each of the authority id it found on chain.
@@ -6498,24 +6318,24 @@ You can find a link to the specification In theory the new protocol creates a bit more traffic on the DHT network, because it waits for DHT records to be received from more than one node, while in the current implementation we just take the first record that we receive and cancel all in-flight requests to other peers. However, because the redundancy factor will be relatively small and this operation happens rarerly, every 10min, this cost is negligible.
-This RFC's implementation https://github.com/paritytech/polkadot-sdk/pull/3786 had been tested on various local test networks and versi.
With regard to security the creation time is wrapped inside SignedAuthorityRecord wo it will be signed with the authority id key, so there is no way for other malicious nodes to manipulate this field without the received node observing.
-
+
Irrelevant.
-
+
Irrelevant.
-Irrelevant.
-The changes are backwards compatible with the existing protocol, so nodes with both the old protocol and newer protocol can exist in the network, this is achieved by the fact that we use protobuf for serializing and deserializing the records, so new fields will be ignore when deserializing with the older protocol and vice-versa when deserializing an old record with the new protocol the new field will be None and the new code accepts this record as being valid.
-The enhancements have been inspired by the algorithm specified in here
-N/A
-
+
N/A
(source)
Table of Contents
@@ -6561,23 +6381,23 @@ in order to speed up the time until all nodes have the newest record, nodes can
Authors Jonas Gehrlein & Alistair Stewart This RFC proposes a flexible unbonding mechanism for tokens that are locked from staking on the Relay Chain (DOT/KSM), aiming to enhance user convenience without compromising system security.
Locking tokens for staking ensures that Polkadot is able to slash tokens backing misbehaving validators. With changing the locking period, we still need to make sure that Polkadot can slash enough tokens to deter misbehaviour. This means that not all tokens can be unbonded immediately, however we can still allow some tokens to be unbonded quickly.
The new mechanism leads to a signficantly reduced unbonding time on average, by queuing up new unbonding requests and scaling their unbonding duration relative to the size of the queue. New requests are executed with a minimum of 2 days, when the queue is comparatively empty, to the conventional 28 days, if the sum of requests (in terms of stake) exceed some threshold. In scenarios between these two bounds, the unbonding duration scales proportionately. The new mechanism will never be worse than the current fixed 28 days.
In this document we also present an empirical analysis by retrospectively fitting the proposed mechanism to the historic unbonding timeline and show that the average unbonding duration would drastically reduce, while still being sensitive to large unbonding events. Additionally, we discuss implications for UI, UX, and conviction voting.
Note: Our proposition solely focuses on the locks imposed from staking. Other locks, such as governance, remain unchanged. Also, this mechanism should not be confused with the already existing feature of FastUnstake , which lets users unstake tokens immediately that have not received rewards for 28 days or longer.
As an initial step to gauge its effectiveness and stability, it is recommended to implement and test this model on Kusama before considering its integration into Polkadot, with appropriate adjustments to the parameters. In the following, however, we limit our discussion to Polkadot.
-Polkadot has one of the longest unbonding periods among all Proof-of-Stake protocols, because security is the most important goal. Staking on Polkadot is still attractive compared to other protocols because of its above-average staking APY. However the long unbonding period harms usability and deters potential participants that want to contribute to the security of the network.
The current length of the unbonding period imposes significant costs for any entity that even wants to perform basic tasks such as a reorganization / consolidation of their stashes, or updating their private key infrastructure. It also limits participation of users that have a large preference for liquidity.
The combination of long unbonding periods and high returns has lead to the proliferation of liquid staking , where parachains or centralised exchanges offer users their staked tokens before the 28 days unbonding period is over either in original DOT/KSM form or derivative tokens. Liquid staking is harmless if few tokens are involved but it could result in many validators being selected by a few entities if a large fraction of DOTs were involved. This may lead to centralization (see here for more discussion on threats of liquid staking) and an opportunity for attacks.
The new mechanism greatly increases the competitiveness of Polkadot, while maintaining sufficient security.
-
Every DOT/KSM token holder
-Before diving into the details of how to implement the unbonding queue, we give readers context about why Polkadot has a 28-day unbonding period in the first place. The reason for it is to prevent long-range attacks (LRA) that becomes theoretically possible if more than 1/3 of validators collude. In essence, a LRA describes the inability of users, who disconnect from the consensus at time t0 and reconnects later, to realize that validators which were legitimate at a certain time, say t0 but dropped out in the meantime, are not to be trusted anymore. That means, for example, a user syncing the state could be fooled by trusting validators that fell outside the active set of validators after t0, and are building a competitive and malicious chain (fork).
LRAs of longer than 28 days are mitigated by the use of trusted checkpoints, which are assumed to be no more than 28 days old. A new node that syncs Polkadot will start at the checkpoint and look for proofs of finality of later blocks, signed by 2/3 of the validators. In an LRA fork, some of the validator sets may be different but only if 2/3 of some validator set in the last 28 days signed something incorrect.
If we detect an LRA of no more than 28 days with the current unbonding period, then we should be able to detect misbehaviour from over 1/3 of validators whose nominators are still bonded. The stake backing these validators is considerable fraction of the total stake (empirically it is 0.287 or so). If we allowed more than this stake to unbond, without checking who it was backing, then the LRA attack might be free of cost for an attacker. The proposed mechansim allows up to half this stake to unbond within 28 days. This halves the amount of tokens that can be slashed, but this is still very high in absolute terms. For example, at the time of writing (19.06.2024) this would translate to around 120 millions DOTs.
@@ -6635,23 +6455,23 @@ The analysis can be reproduced or changed to other parameters using In addition to a simple queue, we could add a market component that lets users always unbond from staking at the minimum possible waiting time)(== LOWER_BOUND, e.g., 2 days), by paying a variable fee. To achieve this, it is reasonable to split the total unbonding capacity into two chunks, with the first capacity for the simple queue and the remaining capacity for the fee-based unbonding. By doing so, we allow users to choose whether they want the quickest unbond and paying a dynamic fee or join the simple queue. Setting a capacity restriction for both queues enables us to guarantee a predictable unbonding time in the simple queue, while allowing users with the respective willingness to pay to get out even earlier. The fees are dynamically adjusted and are proportional to the unbonding stake (and thereby expressed in a percentage of the requested unbonding stake). In contrast to a unified queue, this prevents the issue that users paying a fee jump in front of other users not paying a fee, pushing their unbonding time back (which would be bad for UX). The revenue generated could be burned.
This extension and further specifications are left out of this RFC, because it adds further complexity and the empirical analysis above suggests that average unbonding times will already be close the LOWER_BOUND, making a more complex design unnecessary. We advise to first implement the discussed mechanism and assess after some experience whether an extension is desirable.
-
Lower security for LRAs: Without a doubt, the theoretical security against LRAs decreases. But, as we argue, the attack is still costly enough to deter attacks and the attack is sufficiently theoretical. Here, the benefits outweigh the costs.Griefing attacks: A large holder could pretend to unbond a large amount of their tokens to prevent other users to exit the network earlier. This would, however be costly due to the fact that the holder loses out on staking rewards. The larger the impact on the queue, the higher the costs. In any case it must be noted that the UPPER_BOUND is still 28 days, which means that nominators are never left with a longer unbonding period than currently. There is not enough gain for the attacker to endure this cost.Challenge for Custodians and Liquid Staking Providers : Changing the unbonding time, especially making it flexible, requires entities that offer staking derivatives to rethink and rework their products.
-NA
-
+
NA
-
+
The authors cannot see any potential impact on performance.
-The authors cannot see any potential impact on ergonomics for developers. We discussed potential impact on UX/UI for users above.
-The authors cannot see any potential impact on compatibility. This should be assessed by the technical fellows.
-
Ethereum proposed a similar solution
Alistair did some initial write-up
@@ -6688,20 +6508,20 @@ The analysis can be reproduced or changed to other parameters using This RFC proposes a change to the extrinsic format to include a transaction extension version.
-The extrinsic format supports to be extended with transaction extensions. These transaction extensions are runtime specific and can be different per chain. Each transaction extension can add data to the extrinsic itself or extend the signed payload.
This means that adding a transaction extension is breaking the chain specific extrinsic format. A recent example was the introduction of the CheckMetadatHash
-
Runtime users
Runtime devs
Wallet devs
-RFC84 introduced the extrinsic format 5. The idea is to piggyback onto this change of the extrinsic format to add the extra version for the transaction extensions. If required, this could also come
as extrinsic format 6, but 5 is not yet deployed anywhere.
The extrinsic format supports the following types of transactions:
@@ -6717,25 +6537,25 @@ as extrinsic format 6, but 5 is not yet deployed anywh
The Version being a SCALE encoded u8 representing the version of the transaction extensions.
In the chain runtime the version can be used to determine which set of transaction extensions should be used to decode and to validate the transaction.
-This adds one byte more to each signed transaction.
-There is no impact on testing, security or privacy.
-
+
This will ensure that changes to the transactions extensions can be done in a backwards compatible way.
-
+
There is no performance impact.
-Runtime developers need to take care of the versioning and ensure to bump as required, so that there are no compatibility breaking changes without a bump of the version. It will also add a little bit more code in the runtime
to decode these old versions, but this should be neglectable.
-When introduced together with extrinsic format version 5 from RFC84 , it can be implemented in a backwards compatible way. So, transactions can still be send using the
old extrinsic format and decoded by the runtime.
-None.
-None.
-
+
None.
(source)
Table of Contents
@@ -6772,14 +6592,14 @@ old extrinsic format and decoded by the runtime.
Authors Adrian Catangiu This RFC proposes a new instruction that provides a way to initiate on remote chains, asset transfers which
transfer multiple types (teleports, local-reserve, destination-reserve) of assets, using XCM alone.
The currently existing instructions are too opinionated and force each XCM asset transfer to a single
transfer type (teleport, local-reserve, destination-reserve). This results in inability to combine different
types of transfers in single transfer which results in overall poor UX when trying to move assets across
chains.
-XCM is the de-facto cross-chain messaging protocol within the Polkadot ecosystem, and cross-chain
assets transfers is one of its main use-cases. Unfortunately, in its current spec, it does not support
initiating on a remote chain, one or more transfers that combine assets with different transfer types.ParaP on Polkadot.
With current XCM, we are limited to doing multiple independent transfers for each individual hop in order to
move both "interesting" assets, but also "supporting" assets (used to pay fees).
-
Runtime users
Runtime devs
Wallet devs
dApps devs
-A new instruction InitiateAssetsTransfer is introduced that initiates an assets transfer from the
chain it is executed on, to another chain. The executed transfer is point-to-point (chain-to-chain)
with all of the transfer properties specified in the instruction parameters. The instruction also
@@ -6996,9 +6816,9 @@ by executing a single XCM message, even though we'll be mixing multiple
).unwrap();
})
}
No drawbacks identified.
-There should be no security risks related to the new instruction from the XCVM perspective. It follows the same
pattern as with single-type asset transfers, only now it allows combining multiple types at once.
Improves security by enabling
@@ -7007,16 +6827,16 @@ which minimizes the potential free/unpaid work that a receiving chain has to do.
required execution fee payment, part of the instruction logic through the remote_fees: Option<AssetTransferFilter>
parameter, which will make sure the remote XCM starts with a single-asset-holding-loading-instruction,
immediately followed by a BuyExecution using said asset.
-
+
This brings no impact to the rest of the XCM spec. It is a new, independent instruction, no changes to existing instructions.
Enhances the exposed functionality of Polkadot. Will allow multi-chain transfers that are currently forced to happen in
multiple programs per asset per "hop", to be possible in a single XCM program.
-
+
No performance changes/implications.
-The proposal enhances developers' and users' cross-chain asset transfer capabilities. This enhancement is optimized for XCM
programs transferring multiple assets, needing to run their logic across multiple chains.
-Does this proposal break compatibility with existing interfaces, older versions of implementations? Summarize necessary
migrations or upgrade strategies, if any.
This enhancement is compatible with all existing XCM programs and versions.
@@ -7025,11 +6845,11 @@ success.
A program where the new instruction is used to initiate multiple types of asset transfers, cannot be downgraded to older
XCM versions, because there is no equivalent capability there.
Such conversion attempts will explicitly fail.
-None.
-None.
-
+
None.
(source)
Table of Contents
@@ -7062,10 +6882,10 @@ Such conversion attempts will explicitly fail.
Authors Adrian Catangiu The Transact XCM instruction currently forces the user to set a specific maximum weight allowed to the inner call and then also pay for that much weight regardless of how much the call actually needs in practice.
This RFC proposes improving the usability of Transact by removing that parameter and instead get and charge the actual weight of the inner call from its dispatch info on the remote chain.
-The UX of using Transact is poor because of having to guess/estimate the require_weight_at_most weight used by the inner call on the target.
We've seen multiple Transact on-chain failures caused by guessing wrong values for this require_weight_at_most even though the rest of the XCM program would have worked.
In practice, this parameter only adds UX overhead with no real practical value. Use cases fall in one of two categories:
@@ -7078,40 +6898,40 @@ weight limit parameter.
We've had multiple OpenGov root/whitelisted_caller proposals initiated by core-devs completely or partially fail
because of incorrect configuration of require_weight_at_most parameter. This is a strong indication that the
instruction is hard to use.
-
Runtime Users,
Runtime Devs,
Wallets,
dApps,
-The proposed enhancement is simple: remove require_weight_at_most parameter from the instruction:
- Transact { origin_kind: OriginKind, require_weight_at_most: Weight, call: DoubleEncoded<Call> },
+ Transact { origin_kind: OriginKind, call: DoubleEncoded<Call> },
The XCVM implementation shall no longer use require_weight_at_most for weighing. Instead, it shall weigh the Transact instruction by decoding and weighing the inner call.
-No drawbacks, existing scenarios work as before, while this also allows new/easier flows.
-Currently, an XCVM implementation can weigh a message just by looking at the decoded instructions without decoding the Transact's call, but assuming require_weight_at_most weight for it. With the new version it has to decode the inner call to know its actual weight.
But this does not actually change the security considerations, as can be seen below.
With the new Transact the weighing happens after decoding the inner call. The entirety of the XCM program containing this Transact needs to be either covered by enough bought weight using a BuyExecution, or the origin has to be allowed to do free execution.
The security considerations around how much can someone execute for free are the same for
both this new version and the old. In both cases, an "attacker" can do the XCM decoding (including Transact inner calls) for free by adding a large enough BuyExecution without actually having the funds available.
In both cases, decoding is done for free, but in both cases execution fails early on BuyExecution.
-
-
+
+
No performance change.
-Ergonomics are slightly improved by simplifying Transact API.
-Compatible with previous XCM programs.
-None.
-None.
-
+
None.
(source)
Table of Contents
@@ -7155,13 +6975,13 @@ both this new version and the old. In both cases, an "attacker" can do
Authors Andrei Sandu Elastic scaling is not resilient against griefing attacks without a way for a PoV (Proof of Validity)
to commit to the particular core index it was intended for. This RFC proposes a way to include
core index information in the candidate commitments and the CandidateDescriptor data structure
in a backward compatible way. Additionally, it proposes the addition of a SessionIndex field in
the CandidateDescriptor to make dispute resolution more secure and robust.
-This RFC proposes a way to solve two different problems:
For Elastic Scaling, it prevents anyone who has acquired a valid collation to DoS the parachain
@@ -7176,14 +6996,14 @@ dispute. The dispute may concern a relay chain block not yet imported by a
validator. In this case, validators can safely assume the session index refers to the session
the candidate has appeared in, otherwise, the chain would have rejected the candidate.
-
Polkadot core developers.
Cumulus node developers.
Tooling, block explorer developers.
This approach and alternatives have been considered and discussed in this issue .
-The approach proposed below was chosen primarily because it minimizes the number of breaking
changes, the complexity and takes less implementation and testing time. The proposal is to change
the existing primitives while keeping binary compatibility with the older versions. We repurpose
@@ -7329,28 +7149,28 @@ A candidate must not be backed if any of the following are true:
as backers did off-chain. It currently stores the claim queue at the newest allowed
relay parent corresponding to the claim queue offset 0. The runtime needs to be changed to store
a claim queue snapshot at all allowed relay parents.
-The only drawback is that further additions to the descriptor are limited to the amount of
remaining unused space.
-Standard testing (unit tests, CI zombienet tests) for functionality and mandatory security audit
to ensure the implementation does not introduce any new security issues.
Backward compatibility of the implementation will be tested on testnets (Versi and Westend).
There is no impact on privacy.
-
+
Overall performance will be improved by not checking the collator signatures in runtime and nodes.
The impact on the UMP queue and candidate receipt processing is negligible.
The ClaimQueueOffset along with the relay parent choice allows parachains to optimize their
block production for either throughput or lower XCM message processing latency. A value of 0
with the newest relay parent provides the best latency while picking older relay parents avoids
re-orgs.
-It is mandatory for elastic parachains to switch to the new receipt format and commit to a
core by sending the UMPSignal::SelectCore message. It is optional but desired that all
parachains switch to the new receipts for providing the session index for disputes.
The implementation of this RFC itself must not introduce any breaking changes for the parachain
runtime or collator nodes.
-The proposed changes are not fully backward compatible, because older validators verify the
collator signature of candidate descriptors.
Additional care must be taken before enabling the new descriptors by waiting for at least
@@ -7375,12 +7195,12 @@ present in the receipt.
Any tooling that decodes UMP XCM messages needs an update to support or ignore the new UMP
messages, but they should be fine to decode the regular XCM messages that come before the
separator.
-Forum discussion about a new CandidateReceipt format:
https://forum.polkadot.network/t/pre-rfc-discussion-candidate-receipt-format-v2/3738
-N/A
-
+
The implementation is extensible and future-proof to some extent. With minimal or no breaking
changes, additional fields can be added in the candidate descriptor until the reserved space is
exhausted
@@ -7422,7 +7242,7 @@ by using the version field of the descriptor introduced in this RFC
Authors Francisco Aguirre XCM already handles execution fees in an effective and efficient manner using the BuyExecution instruction.
However, other types of fees are not handled as effectively -- for example, delivery fees.
Fees exist that can't be measured using Weight -- as execution fees can -- so a new method should be thought up for those cases.
@@ -7431,7 +7251,7 @@ This RFC proposes making the fee handling system simpler and more general, by do
Adding a fees register
Deprecating BuyExecution and adding a new instruction PayFees with new semantics to ultimately replace it.
-Execution fees are handled correctly by XCM right now.
However, the addition of extra fees, like for message delivery, result in awkward ways of integrating them into the XCVM implementation.
This is because these types of fees are not included in the language.
@@ -7439,14 +7259,14 @@ The standard should have a way to correctly deal with these implementation speci
The new instruction moves the specified amount of fees from the holding register to a dedicated fees register that the XCVM can use in flexible ways depending on its implementation.
The XCVM implementation is free to use these fees to pay for execution fees, transport fees, or any other type of fee that might be necessary.
This moves the specifics of fees further away from the XCM standard, and more into the actual underlying XCVM implementation, which is a good thing.
-
Runtime Users
Runtime Devs
Wallets
dApps
-The new instruction that will replace BuyExecution is a much simpler and general version: PayFees.
This instruction takes one Asset, takes it from the holding register, and puts it into a new fees register.
The XCVM implementation can now use this Asset to make sure every necessary fee is paid for, this includes execution fees, delivery fees, and any other type of fee
@@ -7477,27 +7297,27 @@ BuyExecution { asset, weight_limit }
PayFees { asset }
// ...rest
}
-
There needs to be an explicit change from BuyExecution to PayFees, most often accompanied by a reduction in the assets passed in.
-It might become a security concern if leftover fees are trapped, since a lot of them are expected.
-
-
+
+
There should be no performance downsides to this approach.
The fees register is a simplification that may actually result in better performance, in the case an implementation is doing a workaround to achieve what this RFC proposes.
-The interface is going to be very similar to the already existing one.
Even simpler since PayFees will only receive one asset.
That asset will allow users to limit the amount of fees they are willing to pay.
-This RFC can't just change the semantics of the BuyExecution instruction since that instruction accepts any funds, uses what it needs and returns the rest immediately.
The new proposed instruction, PayFees, doesn't return the leftover immediately, it keeps it in the fees register.
In practice, the deprecated BuyExecution needs to be slowly rolled out in favour of PayFees.
-The closed RFC PR on the xcm-format repository, before XCM RFCs got moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/53.
-None
-
+
This proposal would greatly benefit from an improved asset trapping system.
CustomAssetClaimer is also related, as it directly improves the ergonomics of this proposal.
LeftoverAssetsDestination execution hint would also similarly improve the ergonomics.
@@ -7533,12 +7353,12 @@ In practice, the deprecated BuyExecution needs to be slowly rolled
Authors Francisco Aguirre A previous XCM RFC (https://github.com/polkadot-fellows/xcm-format/pull/37) introduced a SetAssetClaimer instruction.
This idea of instructing the XCVM to change some implementation-specific behavior is useful.
In order to generalize this mechanism, this RFC introduces a new instruction SetHints
and makes the SetAssetClaimer be just one of many possible execution hints.
-There is a need for specifying how certain implementation-specific things should behave.
Things like who can claim the assets or what can be done instead of trapping assets.
Another idea for a hint:
@@ -7546,13 +7366,13 @@ Another idea for a hint:
AssetForFees: to signify to the executor what asset the user prefers to use for fees.LeftoverAssetsDestination: for depositing leftover assets to a destination instead of trapping them
Runtime devs
Wallets
dApps
-A new instruction, SetHints, will be added.
This instruction will take a single parameter of type Hint, an enumeration.
The first variant for this enum is AssetClaimer, which allows to specify a location that should be able to claim trapped assets.
@@ -7573,27 +7393,27 @@ enum Hint {
type NumVariants = /* Number of variants of the `Hint` enum */;
}
-
The SetHints instruction might be hard to benchmark, since we should look into the actual hints being set to know how much weight to attribute to it.
-Hints are specified on a per-message basis, so they have to be specified at the beginning of a message.
If they were to be specified at the end, hints like AssetClaimer would be useless if an error occurs beforehand and assets get trapped before ever reaching the hint.
The instruction takes a bounded vector of hints so as to not force barriers to allow an arbitrary number of SetHint instructions.
-
-
+
+
None.
-The SetHints instruction provides a better integration with barriers.
If we had to add one barrier for SetAssetClaimer and another for each new hint that's added, barriers would need to be changed all the time.
Also, this instruction would make it simpler to write XCM programs.
You only need to specify the hints you want in one single instruction at the top of your program.
-None.
-The previous RFC PR in the xcm-format repository before XCM RFCs moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/59.
-None.
-
+
None.
(source)
Table of Contents
@@ -7626,36 +7446,36 @@ You only need to specify the hints you want in one single instruction at the top
Authors This RFC aims to remove the NetworkIds of Westend and Rococo, arguing that testnets shouldn't go in the language.
-We've already seen the plans to phase out Rococo and Paseo has appeared.
Instead of constantly changing the testnets included in the language, we should favor specifying them via their genesis hash,
using NetworkId::ByGenesis.
-
Runtime devs
Wallets
dApps
-Remove Westend and Rococo from the included NetworkIds in the language.
-This RFC will make it less convenient to specify a testnet, but not by a large amount.
-None.
-
-
+
+
None.
-It will very slightly reduce the ergonomics of testnet developers but improve the stability of the language.
-NetworkId::Rococo and NetworkId::Westend can just use NetworkId::ByGenesis, as can other testnets.
-A previous attempt to add NetworkId::Paseo: https://github.com/polkadot-fellows/xcm-format/pull/58.
-None.
-
+
None.
(source)
Table of Contents
@@ -7694,11 +7514,11 @@ using NetworkId::ByGenesis.
Authors Adrian Catangiu XCM programs generated by the InitiateAssetTransfer instruction shall have the option to carry over the original origin all the way to the final destination. They shall do so by internally making use of AliasOrigin or ClearOrigin depending on given parameters.
This allows asset transfers to retain their original origin even across multiple hops.
Ecosystem chains would have to change their trusted aliasing rules to effectively make use of this feature.
-Currently, all XCM asset transfer instructions ultimately clear the origin in the remote XCM message by use of the ClearOrigin instruction. This is done for security considerations to ensure that subsequent (user-controlled) instructions cannot command the authority of the sending chain.
The problem with this approach is that it limits what can be achieved on remote chains through XCM. Most XCM operations require having an origin, and following any asset transfer the origin is lost, meaning not much can be done other than depositing the transferred assets to some local account or transferring them onward to another chain.
For example, we cannot transfer some funds for buying execution, then do a Transact (all in the same XCM message).
@@ -7706,9 +7526,9 @@ using NetworkId::ByGenesis.
Transact XCM programs today require a two step process:
And we want to be able to do it using a single XCM program.
-Runtime Users, Runtime Devs, wallets, cross-chain dApps.
-In the case of XCM programs going from source-chain directly to dest-chain without an intermediary hop, we can enable scenarios such as above by using the AliasOrigin instruction instead of the ClearOrigin instruction.
Instead of clearing the source-chain origin, the destination chain shall attempt to alias source-chain to "original origin" on the source chain.
Most common such origin aliasing would be X1(Parachain(source-chain)) -> X2(Parachain(source-chain), AccountId32(origin-account)) for the case of a single hop transfer where the initiator is a (signed/pure/proxy) account origin-account on source-chain.
@@ -7758,35 +7578,35 @@ involved chains.
user on ParaA on Polkdaot calls function on Ethereum, pays with ETH,
In terms of ergonomics and user experience, this support for combining an asset transfer with a subsequent action (like Transact) is a net positive.
In terms of performance, and privacy, this is neutral with no changes.
In terms of security, the feature by itself is also neutral because it allows preserve_origin: false usage for operating with no extra trust assumptions. When wanting to support preserving origin, chains need to configure secure origin aliasing filters. The one suggested in this RFC should be the right choice for the majority of chains, but each chain will ultimately choose depending on their business model and logic (e.g. chain does not plan to integrate with Asset Hub). It is up to the individual chains to configure accordingly.
-Barriers should now allow AliasOrigin, DescendOrigin or ClearOrigin.
Normally, XCM program builders should audit their programs and eliminate assumptions of "no origin" on remote side of this instruction. In this case, the InitiateAssetsTransfer has not been released yet, it will be part of XCMv5, and we can make this change part of the same XCMv5 so that there isn't even the possibility of someone in the wild having built XCM programs using this instruction on those wrong assumptions.
The working assumption going forward is that the origin on the remote side can either be cleared or it can be the local origin's reanchored location. This assumption is in line with the current behavior of remote XCM programs sent over using pallet_xcm::send.
The existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear origin same as before for compatibility reasons.
-
-
+
+
No impact.
-Improves ergonomics by allowing the local origin to operate on the remote chain even when the XCM program includes an asset transfer.
-At the executor-level this change is backwards and forwards compatible. Both types of programs can be executed on new and old versions of XCM with no changes in behavior.
New version of the InitiateAssetsTransfer instruction acts same as before when used with preserve_origin: false.
For using the new capabilities, the XCM builder has to verify that the involved chains have the required origin-aliasing filters configured and use some new version of Barriers aware of AliasOrigin as an allowed alternative to ClearOrigin.
For compatibility reasons, this RFC proposes this mechanism be added as an enhancement to the yet unreleased InitiateAssetsTransfer instruction, thus eliminating possibilities of XCM logic breakages in the wild.
Following the same logic, the existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear the origin same as before for compatibility reasons.
Any one of DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions can be replaced with a InitiateAssetsTransfer instruction with or without origin aliasing, thus providing a clean and clear upgrade path for opting-in this new feature.
-None
-
+
(source)
Table of Contents
@@ -7831,16 +7651,16 @@ Following the same logic, the existing DepositReserveAsset, I
Authors Jeff Burdges, ... An off-chain approximation protocol should assign rewards based upon the approvals and availability work done by validators.
All validators track which approval votes they actually use, reporting the aggregate, after which an on-chain median computation gives a good approximation under byzantine assumptions. Approval checkers report aggregate information about which availability chunks they use too, but in availability we need a tit-for-tat game to enforce honesty, because approval committees could often bias results thanks to their small size.
-We want all polkadot subsystems be profitable for validataors, because otherwise operators might profit from running modified code. In particular, almost all rewards in Kusama/Polkadot should come from work done securing parachains, primarily approval checking, but also backing, availability, and support of XCMP.
Among these task, our highest priorities must be approval checks, which ensure soundness, and sending availability chunks to approval checkers. We prove backers must be paid strictly less than approval checkers.
At present though, validators' rewards have relatively little relationship to validators operating costs, in terms of bandwidth and CPU time. Worse, polkadot's scaling makes us particular vulnerable "no-shows" caused by validators skipping their approval checks.
We're particularly concernned about hardware specks impact upon the number of parachain cores. We've requested relatively low spec machines so far, only four physical CPU cores, although some run even lower specs like only two physical CPU cores. Alone, rewards cannot fix our low speced validator problem, but rewards and outreach together should far more impact than either alone.
In future, we'll further increase validator spec requirements, which directly improve polkadot's throughput, and which repeats this dynamic of purging underspeced nodes, except outreach becomes more important because de facto too many slow validators can "out vote" the faster ones
-We alter the validators rewards protocol, but with negligable impact upon rewards for honest validators who comply with hardware and bandwidth recommendations.
We shall still reward participation in relay chain concensus of course, which de facto means block production but not finality, but these current reward levels shall wind up greatly reduced. Any validators who manipulate block rewards now could lose rewards here, simply because of rewards being shifted from block production to availability, but this sounds desirable.
We've discussed roughly this rewards protocol in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF and https://github.com/paritytech/polkadot-sdk/issues/1811 as well as related topics like https://github.com/paritytech/polkadot-sdk/issues/5122
@@ -7926,7 +7746,7 @@ for (mmu,atm) in my_missing_uploads.iter_mut().zip(approvals_tally_messages) {
We distribute rewards on-chain using approval_usages_medians and reweighted_total_used_downloads. Approval checkers could later change from who they download chunks using my_missing_uploads.
In theory, validators could adopt whatever strategy they like to penalize validators who stiff them on availability redistribution rewards, except they should not stiff back, only choose other availability providers. We discuss one good strategy below, but initially this could go unimplemented.
-Polkadot's efficency creates subtle liveness concerns: Anytime one node cannot perform one of its approval checks then Polkadot loses in expectation 3.25 approval checks, or 0.10833 parablocks. This makes back pressure essential.
We cannot throttle approval checks securely either, so reactive off-chain back pressure only makes sense during or before the backing phase. In other words, if nodes feel overworked themselves, or perhaps beleive others to be, then they should drop backing checks, never approval checks. It follows backing work must be rewarded less well and less reliably than approvals, as otherwise validators could benefit from behavior that harms the network.
@@ -7977,7 +7797,7 @@ At this point, we compute $\beta\prime_w = \sum_v \beta\prime_{w,v}$ on-chain fo
We discuss approvals being considered by the tit-for-tat in earlier drafts. An adversary who successfuly manipulates the rewards median votes would've alraedy violated polkadot's security assumptions though, which requires a hard fork and correcting the dot allocation. Incorrect report wrong approval_usages remain interesting statistics though.
Adversarial validators could manipulates their availability votes though, even without being a supermajority. If they still download honestly, then this costs them more rewards than they earn. We do not prevent validators from preferentially obtaining their pieces from their friends though. We should analyze, or at least observe, the long-term consequences.
A priori, whale nominator's validators could stiff validators but then rotate their validators quickly enough so that they never suffered being skipped back. We discuss several possible solution, and their difficulties, under "Rob's nominator-wise skipping" in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF but overall less seems like more here. Also frequent validator rotation could be penalized elsewhere.
-
+
We operate off-chain except for final rewards votes and median tallies. We expect lower overhead rewards protocols would lack information, thereby admitting easier cheating.
Initially, we designed the ELVES approval gadget to allow on-chain operation, in part for rewards computation, but doing so looks expensive. Also, on-chain rewards computaiton remains only an approximation too, but could even be biased more easily than our off-chain protocol presented here.
@@ -7985,11 +7805,11 @@ At this point, we compute $\beta\prime_w = \sum_v \beta\prime_{w,v}$ on-chain fo
We alraedy teach validators about missed parachain blocks, but we'll teach approval checking more going forwards, because current efforts focus more upon backing.
JAM's block exports should not complicate availability rewards, but could impact some alternative schemes.
-None
-Provide specific questions to discuss and address before the RFC is voted on by the Fellowship. This should include, for example, alternatives to aspects of the proposed design where the appropriate trade-off to make is unclear.
-
+
Any rewards protocol could simply be "out voted" by too many slow validators: An increase the number of parachain cores increases more workload, but this creates no-shows if too few validators could handle this workload.
We could add a synthetic parachain flag, only settable by governance, which treats no-shows as positive approval votes for that parachain, but without adding rewards. We should never enable this for real parachains, only for synthetic ones like gluttons. We should not enable the synthetic parachain flag long-term even for gluttonsm, because validators could easily modify their code. Yet, synthetic approval checks might enable pushing the hardware upgrades more agressively over the short-term.
@@ -8021,16 +7841,16 @@ At this point, we compute $\beta\prime_w = \sum_v \beta\prime_{w,v}$ on-chain fo
Authors Pierre Krieger Update the runtime-host interface to no longer make use of a host-side allocator.
-The heap allocation of the runtime is currently controlled by the host using a memory allocator on the host side.
The API of many host functions consists in allocating a buffer. For example, when calling ext_hashing_twox_256_version_1, the host allocates a 32 bytes buffer using the host allocator, and returns a pointer to this buffer to the runtime. The runtime later has to call ext_allocator_free_version_1 on this pointer in order to free the buffer.
Even though no benchmark has been done, it is pretty obvious that this design is very inefficient. To continue with the example of ext_hashing_twox_256_version_1, it would be more efficient to instead write the output hash to a buffer that was allocated by the runtime on its stack and passed by pointer to the function. Allocating a buffer on the stack in the worst case scenario simply consists in decreasing a number, and in the best case scenario is free. Doing so would save many Wasm memory reads and writes by the allocator, and would save a function call to ext_allocator_free_version_1.
Furthermore, the existence of the host-side allocator has become questionable over time. It is implemented in a very naive way, and for determinism and backwards compatibility reasons it needs to be implemented exactly identically in every client implementation. Runtimes make substantial use of heap memory allocations, and each allocation needs to go twice through the runtime <-> host boundary (once for allocating and once for freeing). Moving the allocator to the runtime side, while it would increase the size of the runtime, would be a good idea. But before the host-side allocator can be deprecated, all the host functions that make use of it need to be updated to not use it.
-No attempt was made at convincing stakeholders.
-This section contains a list of new host functions to introduce.
(func $ext_storage_read_version_2
@@ -8233,11 +8053,11 @@ The following other host functions are similarly also considered deprecated:
ext_allocator_free_version_1ext_offchain_network_state_version_1
-This RFC might be difficult to implement in Substrate due to the internal code design. It is not clear to the author of this RFC how difficult it would be.
The API of these new functions was heavily inspired by API used by the C programming language.
-The changes in this RFC would need to be benchmarked. This involves implementing the RFC and measuring the speed difference.
It is expected that most host functions are faster or equal speed to their deprecated counterparts, with the following exceptions:
@@ -8294,10 +8114,10 @@ This would remove the possibility to synchronize older blocks, which is probably
License MIT This RFC proposes a dynamic pricing model for the sale of Bulk Coretime on the Polkadot UC. The proposed model updates the regular price of cores for each sale period, by taking into account the number of cores sold in the previous sale, as well as a limit of cores and a target number of cores sold. It ensures a minimum price and limits price growth to a maximum price increase factor, while also giving govenance control over the steepness of the price change curve. It allows governance to address challenges arising from changing market conditions and should offer predictable and controlled price adjustments.
Accompanying visualizations are provided at [1].
-RFC-1 proposes periodic Bulk Coretime Sales as a mechanism to sell continouos regions of blockspace (suggested to be 4 weeks in length). A number of Blockspace Regions (compare RFC-1 & RFC-3) are provided for sale to the Broker-Chain each period and shall be sold in a way that provides value-capture for the Polkadot network. The exact pricing mechanism is out of scope for RFC-1 and shall be provided by this RFC.
A dynamic pricing model is needed. A limited number of Regions are offered for sale each period. The model needs to find the price for a period based on supply and demand of the previous period.
The model shall give Coretime consumers predictability about upcoming price developments and confidence that Polkadot governance can adapt the pricing model to changing market conditions.
@@ -8309,7 +8129,7 @@ This would remove the possibility to synchronize older blocks, which is probably
The solution SHOULD provide a maximum factor of price increase should the limit of Regions sold per period be reached.
The solution should allow governance to control the steepness of the price function
-The primary stakeholders of this RFC are:
Protocol researchers and evelopers
@@ -8317,7 +8137,7 @@ This would remove the possibility to synchronize older blocks, which is probably
Polkadot parachains teams
Brokers involved in the trade of Bulk Coretime
-The dynamic pricing model sets the new price based on supply and demand in the previous period. The model is a function of the number of Regions sold, piecewise-defined by two power functions.
@@ -8416,9 +8236,9 @@ SCALE_DOWN = 1
SCALE_UP = 1
OLD_PRICE = 1000
-None at present.
-This pricing model is based on the requirements from the basic linear solution proposed in RFC-1, which is a simple dynamic pricing model and only used as proof. The present model adds additional considerations to make the model more adaptable under real conditions.
This RFC, if accepted, shall be implemented in conjunction with RFC-1.
@@ -8457,9 +8277,9 @@ OLD_PRICE = 1000
Authors Pierre Krieger Improve the networking messages that query storage items from the remote, in order to reduce the bandwidth usage and number of round trips of light clients.
-Clients on the Polkadot peer-to-peer network can be divided into two categories: full nodes and light clients. So-called full nodes are nodes that store the content of the chain locally on their disk, while light clients are nodes that don't. In order to access for example the balance of an account, a full node can do a disk read, while a light client needs to send a network message to a full node and wait for the full node to reply with the desired value. This reply is in the form of a Merkle proof, which makes it possible for the light client to verify the exactness of the value.
Unfortunately, this network protocol is suffering from some issues:
@@ -8469,9 +8289,9 @@ OLD_PRICE = 1000
Once Polkadot and Kusama will have transitioned to state_version = 1, which modifies the format of the trie entries, it will be possible to generate Merkle proofs that contain only the hashes of values in the storage. Thanks to this, it is already possible to prove the existence of a key without sending its entire value (only its hash), or to prove that a value has changed or not between two blocks (by sending just their hashes).
Thus, the only reason why aforementioned issues exist is because the existing networking messages don't give the possibility for the querier to query this. This is what this proposal aims at fixing.
-This is the continuation of https://github.com/w3f/PPPs/pull/10, which itself is the continuation of https://github.com/w3f/PPPs/pull/5.
-The protobuf schema of the networking protocol can be found here: https://github.com/paritytech/substrate/blob/5b6519a7ff4a2d3cc424d78bc4830688f3b184c0/client/network/light/src/schema/light.v1.proto
The proposal is to modify this protocol in this way:
@@ -11,6 +11,7 @@ message Request {
@@ -8529,26 +8349,26 @@ An alternative could have been to specify the child_trie_info for e
Also note that child tries aren't considered as descendants of the main trie when it comes to the includeDescendants flag. In other words, if the request concerns the main trie, no content coming from child tries is ever sent back.
This protocol keeps the same maximum response size limit as currently exists (16 MiB). It is not possible for the querier to know in advance whether its query will lead to a reply that exceeds the maximum size. If the reply is too large, the replier should send back only a limited number (but at least one) of requested items in the proof. The querier should then send additional requests for the rest of the items. A response containing none of the requested items is invalid.
The server is allowed to silently discard some keys of the request if it judges that the number of requested keys is too high. This is in line with the fact that the server might truncate the response.
-This proposal doesn't handle one specific situation: what if a proof containing a single specific item would exceed the response size limit? For example, if the response size limit was 1 MiB, querying the runtime code (which is typically 1.0 to 1.5 MiB) would be impossible as it's impossible to generate a proof less than 1 MiB. The response size limit is currently 16 MiB, meaning that no single storage item must exceed 16 MiB.
Unfortunately, because it's impossible to verify a Merkle proof before having received it entirely, parsing the proof in a streaming way is also not possible.
A way to solve this issue would be to Merkle-ize large storage items, so that a proof could include only a portion of a large storage item. Since this would require a change to the trie format, it is not realistically feasible in a short time frame.
-The main security consideration concerns the size of replies and the resources necessary to generate them. It is for example easily possible to ask for all keys and values of the chain, which would take a very long time to generate. Since responses to this networking protocol have a maximum size, the replier should truncate proofs that would lead to the response being too large. Note that it is already possible to send a query that would lead to a very large reply with the existing network protocol. The only thing that this proposal changes is that it would make it less complicated to perform such an attack.
Implementers of the replier side should be careful to detect early on when a reply would exceed the maximum reply size, rather than inconditionally generate a reply, as this could take a very large amount of CPU, disk I/O, and memory. Existing implementations might currently be accidentally protected from such an attack thanks to the fact that requests have a maximum size, and thus that the list of keys in the query was bounded. After this proposal, this accidental protection would no longer exist.
Malicious server nodes might truncate Merkle proofs even when they don't strictly need to, and it is not possible for the client to (easily) detect this situation. However, malicious server nodes can already do undesirable things such as throttle down their upload bandwidth or simply not respond. There is no need to handle unnecessarily truncated Merkle proofs any differently than a server simply not answering the request.
-
-
+
+
It is unclear to the author of the RFC what the performance implications are. Servers are supposed to have limits to the amount of resources they use to respond to requests, and as such the worst that can happen is that light client requests become a bit slower than they currently are.
-Irrelevant.
-The prior networking protocol is maintained for now. The older version of this protocol could get removed in a long time.
-None. This RFC is a clean-up of an existing mechanism.
-None
-
+
The current networking protocol could be deprecated in a long time. Additionally, the current "state requests" protocol (used for warp syncing) could also be deprecated in favor of this one.
(source)
Table of Contents
@@ -8578,9 +8398,9 @@ Also note that child tries aren't considered as descendants of the main trie whe
Authors Jonas Gehrlein This document is a proposal for restructuring the bulk markets in the Polkadot UC's coretime allocation system to improve efficiency and fairness. The proposal suggests separating the BULK_PERIOD into MARKET_PERIOD and RENEWAL_PERIOD, allowing for a market-driven price discovery through a clearing price Dutch auction during the MARKET_PERIOD followed by renewal offers at the MARKET_PRICE during the RENEWAL_PERIOD. The new system ensures synchronicity between renewal and market prices, fairness among all current tenants, and efficient price discovery, while preserving price caps to provide security for current tenants. It seeks to start a discussion about the possibility of long-term leases.
-While the initial RFC-1 has provided a robust framework for Coretime allocation within the Polkadot UC, this proposal builds upon its strengths and uses many provided building blocks to address some areas that could be further improved.
In particular, this proposal introduces the following changes:
@@ -8600,14 +8420,14 @@ Also note that child tries aren't considered as descendants of the main trie whe
The premise of this proposal is to reduce complexity by introducing a common price (that develops releative to capacity consumption of Polkadot UC), while still allowing for market forces to add efficiency. Longterm lease owners still receive priority IF they can pay (close to) the market price. This prevents a situation where the renewal price significantly diverges from renewal prices which allows for core captures. While maximum price increase certainty might seem contradictory to efficient price discovery, the proposed model aims to balance these elements, utilizing market forces to determine the price and allocate cores effectively within certain bounds. It must be stated, that potential price increases remain predictable (in the worst-case) but could be higher than in the originally proposed design. The argument remains, however, that we need to allow market forces to affect all prices for an efficient Coretime pricing and allocation.
Ultimately, this the framework proposed here adheres to all requirements stated in RFC-1.
-Primary stakeholder sets are:
Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division.
Polkadot Parachain teams both present and future, and their users.
Polkadot DOT token holders.
-The BULK_PERIOD has been restructured into two primary segments: the MARKET_PERIOD and RENEWAL_PERIOD, along with an auxiliary SETTLEMENT_PERIOD. This latter period doesn't necessitate any actions from the coretime system chain, but it facilitates a more efficient allocation of coretime in secondary markets. A significant departure from the original proposal lies in the timing of renewals, which now occur post-market phase. This adjustment aims to harmonize renewal prices with their market counterparts, ensuring a more consistent and equitable pricing model.
Long-term Coretime : The Polkadot UC is undergoing a transition from two-year leases without an instantaneous market to a model encompassing instantaneous and one-month leases. This shift seems to pivot from one extreme to another. While the introduction of short-term leases, both instantaneous and for one month, is a constructive move to lower barriers to entry and promote experimentation, it seems to be the case that established projects might benefit from more extended lease options. We could consider offering another product, such as a six-month Coretime lease, using the same mechanism described herein. Although the majority of leases would still be sold on a one-month basis, the addition of this option would enhance market efficiency as it would strengthen the impact of a secondary market .
-There are trade-offs that arise from this proposal, compared to the initial model. The most notable one is that here, I prioritize requirement 6 over requirement 2. The price, in the very "worst-case" (meaning a huge explosion in demand for coretime) could lead to a much larger increase of prices in Coretime. From an economic perspective, this (rare edgecase) would also mean that we'd vastly underprice Coretime in the original model, leading to highly inefficient allocations.
-This RFC builds extensively on the available ideas put forward in RFC-1 .
Additionally, I want to express a special thanks to Samuel Haefner and Shahar Dobzinski for fruitful discussions and helping me structure my thoughts.
-The technical feasability needs to be assessed.
(source)
Table of Contents
@@ -8691,16 +8511,16 @@ Also note that child tries aren't considered as descendants of the main trie whe
Authors Gabriel Facco de Arruda This RFC proposes changes that enable the use of absolute locations in AccountId derivations, which allows protocols built using XCM to have static account derivations in any runtime, regardless of its position in the family hierarchy.
-These changes would allow protocol builders to leverage absolute locations to maintain the exact same derived account address across all networks in the ecosystem, thus enhancing user experience.
One such protocol, that is the original motivation for this proposal, is InvArch's Saturn Multisig, which gives users a unifying multisig and DAO experience across all XCM connected chains.
-This proposal aims to make it possible to derive accounts for absolute locations, enabling protocols that require the ability to maintain the same derived account in any runtime. This is done by deriving accounts from the hash of described absolute locations, which are static across different destinations.
The same location can be represented in relative form and absolute form like so:
#![allow(unused)]
@@ -8757,25 +8577,25 @@ Also note that child tries aren't considered as descendants of the main trie whe
The DescribeFamily location descriptor is part of the HashedDescription MultiLocation hashing system and exists to describe locations in an easy format for encoding and hashing, so that an AccountId can be derived from this MultiLocation.
This implementation contains a match statement that does not match against absolute locations, so changes to it involve matching against absolute locations and providing appropriate descriptions for hashing.
-No drawbacks have been identified with this proposal.
-Tests can be done using simple unit tests, as this is not a change to XCM itself but rather to types defined in xcm-builder.
Security considerations should be taken with the implementation to make sure no unwanted behavior is introduced.
This proposal does not introduce any privacy considerations.
-
-
+
+
Depending on the final implementation, this proposal should not introduce much overhead to performance.
-The ergonomics of this proposal depend on the final implementation details.
-Backwards compatibility should remain unchanged, although that depend on the final implementation.
-
DescirbeFamily type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/location_conversion.rs#L122WithComputedOrigin type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/barriers.rs#L153
-Implementation details and overall code is still up to discussion.
(source)
Table of Contents
@@ -8807,7 +8627,7 @@ Also note that child tries aren't considered as descendants of the main trie whe
ChaosDAO This RFC proposes to make modifications to voting power delegations as part of the Conviction Voting pallet. The changes being proposed include:
Allow a Delegator to vote independently of their Delegate if they so desire.
@@ -8815,7 +8635,7 @@ Also note that child tries aren't considered as descendants of the main trie whe
Make a change so that when a delegate votes abstain their delegated votes also vote abstain.
Allow a Delegator to delegate/ undelegate their votes for all tracks with a single call.
-It has become clear since the launch of OpenGov that there are a few common tropes which pop up time and time again:
The frequency of referenda is often too high for network participants to have sufficient time to review, comprehend, and ultimately vote on each individual referendum. This means that these network participants end up being inactive in on-chain governance.
@@ -8823,13 +8643,13 @@ Also note that child tries aren't considered as descendants of the main trie whe
Delegating votes for all tracks currently requires long batched calls which result in high fees for the Delegator - resulting in a reluctance from many to delegate their votes.
We believe (based on feedback from token holders with a larger stake in the network) that if there were some changes made to delegation mechanics, these larger stake holders would be more likely to delegate their voting power to active network participants – thus greatly increasing the support turnout.
-The primary stakeholders of this RFC are:
The Polkadot Technical Fellowship who will have to research and implement the technical aspects of this RFC
DOT token holders in general
-This RFC proposes to make 4 changes to the convictionVoting pallet logic in order to improve the user experience of those delegating their voting power to another account.
@@ -8845,21 +8665,21 @@ Also note that child tries aren't considered as descendants of the main trie whe
Allow a Delegator to delegate/ undelegate their votes for all tracks with a single call - in order to delegate votes across all tracks, a user must batch 15 calls - resulting in high costs for delegation. A single call for delegate_all/ undelegate_all would reduce the complexity and therefore costs of delegations considerably for prospective Delegators.
-We do not foresee any drawbacks by implementing these changes. If anything we believe that this should help to increase overall voter turnout (via the means of delegation) which we see as a net positive.
-We feel that the Polkadot Technical Fellowship would be the most competent collective to identify the testing requirements for the ideas presented in this RFC.
-
-
+
+
This change may add extra chain storage requirements on Polkadot, especially with respect to nested delegations.
The change to add nested delegations may affect governance interfaces such as Nova Wallet who will have to apply changes to their indexers to support nested delegations. It may also affect the Polkadot Delegation Dashboard as well as Polkassembly & SubSquare.
We want to highlight the importance for ecosystem builders to create a mechanism for indexers and wallets to be able to understand that changes have occurred such as increasing the pallet version, etc.
-N/A
-N/A
-
+
Additionally we would like to re-open the conversation about the potential for there to be free delegations. This was discussed by Dr Gavin Wood at Sub0 2022 and we feel like this would go a great way towards increasing the amount of network participants that are delegating: https://youtu.be/hSoSA6laK3Q?t=526
Overall, we strongly feel that delegations are a great way to increase voter turnout, and the ideas presented in this RFC would hopefully help in that aspect.
(source)
@@ -8901,9 +8721,9 @@ Also note that child tries aren't considered as descendants of the main trie whe
Authors Sergej Sakac This RFC proposes a new model for a sustainable on-demand parachain registration, involving a smaller initial deposit and periodic rent payments. The new model considers that on-demand chains may be unregistered and later re-registered. The proposed solution also ensures a quick startup for on-demand chains on Polkadot in such cases.
-With the support of on-demand parachains on Polkadot, there is a need to explore a new, more cost-effective model for registering validation code. In the current model, the parachain manager is responsible for reserving a unique ParaId and covering the cost of storing the validation code of the parachain. These costs can escalate, particularly if the validation code is large. We need a better, sustainable model for registering on-demand parachains on Polkadot to help smaller teams deploy more easily.
This RFC suggests a new payment model to create a more financially viable approach to on-demand parachain registration. In this model, a lower initial deposit is required, followed by recurring payments upon parachain registration.
This new model will coexist with the existing one-time deposit payment model, offering teams seeking to deploy on-demand parachains on Polkadot a more cost-effective alternative.
@@ -8917,11 +8737,11 @@ Also note that child tries aren't considered as descendants of the main trie whe
The solution MUST allow anyone to pay the rent.
The solution MUST prevent the removal of validation code if it could still be required for disputes or approval checking.
-
Future Polkadot on-demand Parachains
-This RFC proposes a set of changes that will enable the new rent based approach to registering and storing validation code on-chain.
The new model, compared to the current one, will require periodic rent payments. The parachain won't be pruned automatically if the rent is not paid, but by permitting anyone to prune the parachain and rewarding the caller, there will be an incentive for the removal of the validation code.
On-demand parachains should still be able to utilize the current one-time payment model. However, given the size of the deposit required, it's highly likely that most on-demand parachains will opt for the new rent-based model.
@@ -9028,27 +8848,27 @@ pub(super) type CheckedCodeHash<T: Config> =
StorageMap<_, Twox64Concat, ParaId, ValidationCodeHash>;
} To enable parachain re-registration, we should introduce a new extrinsic in the paras-registrar pallet that allows this. The logic of this extrinsic will be same as regular registration, with the distinction that it can be called by anyone, and the required deposit will be smaller since it only has to cover for the storage of the validation code.
-This RFC does not alter the process of reserving a ParaId, and therefore, it does not propose reducing it, even though such a reduction could be beneficial.
Even though this RFC doesn't delve into the specifics of the configuration values for parachain registration but rather focuses on the mechanism, configuring it carelessly could lead to potential problems.
Since the validation code hash and head data are not removed when the parachain is pruned but only when the deregister extrinsic is called, the T::DataDepositPerByte must be set to a higher value to create a strong enough incentive for removing it from the state.
-The implementation of this RFC will be tested on Rococo first.
Proper research should be conducted on setting the configuration values of the new system since these values can have great impact on the network.
An audit is required to ensure the implementation's correctness.
The proposal introduces no new privacy concerns.
-
-
+
+
This RFC should not introduce any performance impact.
-This RFC does not affect the current parachains, nor the parachains that intend to use the one-time payment model for parachain registration.
-This RFC does not break compatibility.
-Prior discussion on this topic: https://github.com/paritytech/polkadot-sdk/issues/1796
-None at this time.
-
+
As noted in this GitHub issue , we want to raise the per-byte cost of on-chain data storage. However, a substantial increase in this cost would make it highly impractical for on-demand parachains to register on Polkadot.
This RFC offers an alternative solution for on-demand parachains, ensuring that the per-byte cost increase doesn't overly burden the registration process.
(source)
@@ -9082,16 +8902,16 @@ This RFC offers an alternative solution for on-demand parachains, ensuring that
Authors Pierre Krieger Rather than enforce a limit to the total memory consumption on the client side by loading the value at :heappages, enforce that limit on the runtime side.
-From the early days of Substrate up until recently, the runtime was present in two forms: the wasm runtime (wasm bytecode passed through an interpreter) and the native runtime (native code directly run by the client).
Since the wasm runtime has a lower amount of available memory (4 GiB maximum) compared to the native runtime, and in order to ensure sure that the wasm and native runtimes always produce the same outcome, it was necessary to clamp the amount of memory available to both runtimes to the same value.
In order to achieve this, a special storage key (a "well-known" key) :heappages was introduced and represents the number of "wasm pages" (one page equals 64kiB) of memory that are available to the memory allocator of the runtimes. If this storage key is absent, it defaults to 2048, which is 128 MiB.
The native runtime has since then been disappeared, but the concept of "heap pages" still exists. This RFC proposes a simplification to the design of Polkadot by removing the concept of "heap pages" as is currently known, and proposes alternative ways to achieve the goal of limiting the amount of memory available.
-Client implementers and low-level runtime developers.
-This RFC proposes the following changes to the client:
The client no longer considers :heappages as special.
@@ -9117,27 +8937,27 @@ This RFC offers an alternative solution for on-demand parachains, ensuring that
Each parachain can choose the option that they prefer, but the author of this RFC strongly suggests either option C or B.
-In case of path A, there is one situation where the behaviour pre-RFC is not equivalent to the one post-RFC: when a host function that performs an allocation (for example ext_storage_get) is called, without this RFC this allocation might fail due to reaching the maximum heap pages, while after this RFC this will always succeed.
This is most likely not a problem, as storage values aren't supposed to be larger than a few megabytes at the very maximum.
In the unfortunate event where the runtime runs out of memory, path B would make it more difficult to relax the memory limit, as we would need to re-upload the entire Wasm, compared to updating only :heappages in path A or before this RFC.
In the case where the runtime runs out of memory only in the specific event where the Wasm runtime is modified, this could brick the chain. However, this situation is no different than the thousands of other ways that a bug in the runtime can brick a chain, and there's no reason to be particularily worried about this situation in particular.
-This RFC would reduce the chance of a consensus issue between clients.
The :heappages are a rather obscure feature, and it is not clear what happens in some corner cases such as the value being too large (error? clamp?) or malformed. This RFC would completely erase these questions.
-
-
+
+
In case of path A, it is unclear how performances would be affected. Path A consists in moving client-side operations to the runtime without changing these operations, and as such performance differences are expected to be minimal. Overall, we're talking about one addition/subtraction per malloc and per free, so this is more than likely completely negligible.
In case of path B and C, the performance gain would be a net positive, as this RFC strictly removes things.
-This RFC would isolate the client and runtime more from each other, making it a bit easier to reason about the client or the runtime in isolation.
-Not a breaking change. The runtime-side changes can be applied immediately (without even having to wait for changes in the client), then as soon as the runtime is updated, the client can be updated without any transition period. One can even consider updating the client before the runtime, as it corresponds to path C.
-None.
-None.
-
+
This RFC follows the same path as https://github.com/polkadot-fellows/RFCs/pull/4 by scoping everything related to memory allocations to the runtime.
(source)
Table of Contents
@@ -9175,7 +8995,7 @@ The :heappages are a rather obscure feature, and it is not clear wh
Author Adam Clay Steeber This RFC proposes adding a trivial governance track on Kusama to facilitate X (formerly known as Twitter) posts on the @kusamanetwork account. The technical aspect
of implementing this in the runtime is very inconsequential and straight-forward, though it might get more technical if the Fellowship wants to regulate this track
with a non-existent permission set. If this is implemented it would need to be followed up with:
@@ -9183,7 +9003,7 @@ with a non-existent permission set. If this is implemented it would need to be f
the establishment of specifications for proposing X posts via this track, and
the development of tools/processes to ensure that the content contained in referenda enacted in this track would be automatically posted on X.
-The overall motivation for this RFC is to decentralize the management of the Kusama brand/communication channel to KSM holders. This is necessary in my opinion primarily
because of the inactivity of the account in recent history, with posts spanning weeks or months apart. I am currently unaware of who/what entity manages the Kusama
X account, but if they are affiliated with Parity or W3F this proposed solution could also offload some of the legal ramifications of making (or not making)
@@ -9193,11 +9013,11 @@ and the community becomes totally autonomous in the management of Kusama's X pos
that could be offloaded to openGov, provided this proof-of-concept is successful.
Finally, this RFC is the epitome of experimentation that Kusama is ideal for. This proposal may spark newfound excitement for Kusama and help us realize Kusama's potential
for pushing boundaries and trying new unconventional ideas.
-This idea has not been formalized by any individual (or group of) KSM holder(s). To my knowledge the socialization of this idea is contained
entirely in my recent X post here , but it is possible that an idea like this one has been discussed in
other places. It appears to me that the ecosystem would welcome a change like this which is why I am taking action to formalize the discussion.
-The implementation of this idea can be broken down into 3 primary phases:
First, we begin with this RFC to ensure all feedback can be discussed and implemented in the proposal. After the Fellowship and the community come to a reasonable
@@ -9250,7 +9070,7 @@ to implement them. Here's what would be needed:
a UI to allow layman users to propose referenda on this track
After everything is complete, we can update the Kusama wiki to include documentation on the X post specifications and include links to the tools/UI.
-The main drawback to this change is that it requires a lot of off-chain coordination. It's easy enough to include the track on Kusama but it's a totally different
challenge to make it function as intended. The tools need to be built and the auth tokens need to be managed. It would certainly add an administrative burden to whoever
manages the X account since they would either need to run the tools themselves or manage auth tokens.
@@ -9262,28 +9082,28 @@ If that happens, we risk getting Kusama banned on X!
agency to manage posts. It wouldn't be decentralized but it would probably be more effective in terms of creating good content.
Finally, this solution is merely pseudo-decentralization since the X account manager would still have ultimate control of the account. It's decentralized insofar as
the auth tokens are given to people actually running the tools; a house of cards is required to facilitate X posts via this track. Not ideal.
-There's major precedent for configuring tracks on openGov given the amount of power tracks have, so it shouldn't be hard to come up with a sound configuration.
That's why I recommend restricting permissions of this track to remarks and batches of remarks, or something equally inconsequential.
Building the tools for this implementation is really straight-forward and could be audited by Fellowship members, and the community at large, on Github.
The largest security concern would be the management of Kusama's X account's auth tokens. We would need to ensure that they aren't compromised.
-
-
+
+
If a track on Kusama promises users that compliant referenda enacted therein would be posted on Kusama's X account, users would expect that track to perform as promised.
If the house of cards tumbles down and a compliant referendum doesn't actually get anything posted, users might think that Kusama is broken or unreliable. This
could be damaging to Kusama's image and cause people to question the soundness of other features on Kusama.
As mentioned in the drawbacks, the performance of this feature would depend on off-chain coordinations. We can reduce the administrative burden of these coordinations
by funding third parties with the Treasury to deal with it, but then we're relying on trusting these parties.
-By adding a new track to Kusama, governance platforms like Polkassembly or Nova Wallet would need to include it on their applications. This shouldn't be too
much of a burden or overhead since they've already built the infrastructure for other openGov tracks.
-This change wouldn't break any compatibility as far as I know.
One reference to a similar feature requiring on-chain/off-chain coordination would be the Kappa-Sigma-Mu Society. Nothing on-chain necessarily enforces the rules
or facilitates bids, challenges, defenses, etc. However, the Society has managed to maintain itself with integrity to its rules. So I don't think this is totally
out of Kusama's scope. But it will require some off-chain effort to maintain.
-
Who will develop the tools necessary to implement this feature? How do we select them?
How can this idea be better implemented with on-chain/substrate features?
@@ -9322,11 +9142,11 @@ out of Kusama's scope. But it will require some off-chain effort to maintain.Authors JelliedOwl
-The current size of the decision deposit on some tracks is too high for many proposers. As a result, those needing to use it have to find someone else willing to put up the deposit for them - and a number of legitimate attempts to use the root track have timed out. This track would provide a more affordable (though slower) route for these holders to use the root track.
-There have been recent attempts to use the Kusama root track which have timed out with no decision deposit placed. Usually, these referenda have been related to parachain registration related issues.
-Propose to address this by adding a new referendum track [22] Referendum Deposit
[Referenda Pallet] Modify the placeDecisionDesposit function to additionally allow it to be called by root, with root call bypassing the requirements for a deposit payment.
@@ -9350,23 +9170,23 @@ out of Kusama's scope. But it will require some off-chain effort to maintain.Approval & Support curves : As per the root track, timed to match the decision period
Maximum deciding : 10
-This track would provide a route to starting a root referendum with a much-reduced slashable deposit. This might be undesirable but, assuming the decision deposit cost for this track is still high enough, slashing would still act as a disincentive.
An alternative to this might be to reduce the decision deposit size some of the more expensive tracks. However, part of the purpose of the high deposit - at least on the root track - is to prevent spamming the limited queue with junk referenda.
-Will need additional tests case for the modified pallet and runtime. No security or privacy issues.
-
-
+
+
No significant performance impact.
-Only changes related to adding the track. Existing functionality is unchanged.
-No compatibility issues.
-Feedback on whether my proposed implementation of this is the best way to address the issue - including which calls the track should be allowed to make. Are the track parameters correct or should be use something different? Alternative would be welcome.
(source)
Table of Contents
@@ -9411,7 +9231,7 @@ out of Kusama's scope. But it will require some off-chain effort to maintain.Authors Abdelrahman Soliman (Boda)
-A pallet to facilitate enhanced multisig accounts. The main enhancement is that we store a multisig account in the state with related info (signers, threshold,..etc). The module affords enhanced control over administrative operations such as adding/removing signers, changing the threshold, account deletion, canceling an existing proposal. Each signer can approve/reject a proposal while still exists. The proposal is not intended for migrating or getting rid of existing multisig. It's to allow both options to coexist.
For the rest of the RFC We use the following terms:
@@ -9419,7 +9239,7 @@ out of Kusama's scope. But it will require some off-chain effort to maintain.Stateful Multisig to refer to the proposed pallet.
Stateless Multisig to refer to the current multisig pallet in polkadot-sdk.
-Entities in the Polkadot ecosystem need to have a way to manage their funds and other operations in a secure and efficient way. Multisig accounts are a common way to achieve this. Entities by definition change over time, members of the entity may change, threshold requirements may change, and the multisig account may need to be deleted. For even more enhanced hierarchical control, the multisig account may need to be controlled by other multisig accounts.
Current native solutions for multisig operations are less optimal, performance-wise (as we'll explain later in the RFC), and lack fine-grained control over the multisig account.
@@ -9461,12 +9281,12 @@ DAOs can utilize multisig accounts to ensure that decisions are made collectivel
and much more...
-
Polkadot holders
Polkadot developers
-I've created the stateful multisig pallet during my studies in Polkadot Blockchain Academy under supervision from @shawntabrizi and @ank4n. After that, I've enhanced it to be fully functional and this is a draft PR#3300 in polkadot-sdk. I'll list all the details and design decisions in the following sections. Note that the PR is not 1-1 exactly to the current RFC as the RFC is a more polished version of the PR after updating based on the feedback and discussions.
Let's start with a sequence diagram to illustrate the main operations of the Stateful Multisig.
@@ -9879,14 +9699,14 @@ pub type PendingProposals<T: Config> = StorageDoubleMap<
In case threshold is lower than the number of approvers then the proposal is still valid.
In case threshold is higher than the number of approvers then we catch it during execute proposal and error.
-Standard audit/review requirements apply.
-
-
+
+
Doing back of the envelop calculation to proof that the stateful multisig is more efficient than the stateless multisig given it's smaller footprint size on blocks.
Quick review over the extrinsics for both as it affects the block size:
Stateless Multisig:
@@ -9950,17 +9770,17 @@ We have the following extrinsics:
| Stateless | N^2 | Nil |
| Stateful | N | N |
So even though the stateful multisig has a larger state size, it's still more efficient in terms of block size and total footprint on the blockchain.
-The Stateful Multisig will have better ergonomics for managing multisig accounts for both developers and end-users.
-This RFC is compatible with the existing implementation and can be handled via upgrades and migration. It's not intended to replace the existing multisig pallet.
-multisig pallet in polkadot-sdk
-
On account deletion, should we transfer remaining deposits to treasury or remove signers' addition deposits completely and consider it as fees to start with?
-
+
Authors Luke Schoen This proposes to increase the maximum length of PGP Fingerprint values from a 20 bytes/chars limit to a 40 bytes/chars limit.
-Pretty Good Privacy (PGP) Fingerprints are shorter versions of their corresponding Public Key that may be printed on a business card.
They may be used by someone to validate the correct corresponding Public Key.
@@ -10026,7 +9846,7 @@ Implement call filters. This will allow multisig accounts to only accept certain
The maximum length of identity PGP Fingerprint values should be increased from the current 20 bytes/chars limit at least a 40 bytes/chars limit to support PGP Fingerprints and GPG Fingerprints.
-
Any Polkadot account holder wishing to use a Polkadot on-chain identity for their:
@@ -10035,30 +9855,30 @@ Implement call filters. This will allow multisig accounts to only accept certain
-If a user tries to setting an on-chain identity by creating an extrinsic using Polkadot.js with identity > setIdentity(info), then if they try to provide their 40 character long PGP Fingerprint or GPG Fingerprint, which is longer than the maximum length of 20 bytes/chars [u8;20], then they will encounter this error:
createType(Call):: Call: failed decoding identity.setIdentity:: Struct: failed on args: {...}:: Struct: failed on pgpFingerprint: Option<[u8;20]>:: Expected input with 20 bytes (160 bits), found 40 bytes
Increasing maximum length of identity PGP Fingerprint values from the current 20 bytes/chars limit to at least a 40 bytes/chars limit would overcome these errors and support PGP Fingerprints and GPG Fingerprints, satisfying the solution requirements.
-No drawbacks have been identified.
-Implementations would be tested for adherance by checking that 40 bytes/chars PGP Fingerprints are supported.
No effect on security or privacy has been identified than already exists.
No implementation pitfalls have been identified.
-
-
+
+
It would be an optimization, since the associated exposed interfaces to developers and end-users could start being used.
To minimize additional overhead the proposal suggests a 40 bytes/chars limit since that would at least provide support for PGP Fingerprints, satisfying the solution requirements.
-No potential ergonomic optimizations have been identified.
-Updates to Polkadot.js Apps, API and its documentation and those referring to it may be required.
-No prior articles or references.
-No further questions at this stage.
-
+
Relates to RFC entitled "Increase maximum length of identity raw data values from 32 bytes".
(source)
Table of Contents
@@ -10104,10 +9924,10 @@ Implement call filters. This will allow multisig accounts to only accept certain
Authors Luke Schoen This proposes to require a slashable deposit in the broker pallet when initially purchasing or renewing Bulk Coretime or Instantaneous Coretime cores.
Additionally, it proposes to record a reputational status based on the behavior of the purchaser, as it relates to their use of Kusama Coretime cores that they purchase, and to possibly reserve a proportion of the cores for prospective purchasers that have an on-chain identity.
-There are sales of Kusama Coretime cores that are scheduled to occur later this month by Coretime Marketplace Lastic.xyz initially in limited quantities, and potentially also by RegionX in future that is subject to their Polkadot referendum #582 . This poses a risk in that some Kusama Coretime core purchasers may buy Kusama Coretime cores when they have no intention of actually placing a workload on them or leasing them out, which would prevent those that wish to purchase and actually use Kusama Coretime cores from being able to use any at cores at all.
Reputation . To disincentivise certain behaviours, a reputational status indicator could be used to record the historic behavior of the purchaser and whether on-chain judgement has determined they have adequately rectified that behaviour, as it relates to their usage of Kusama Coretime cores that they purchase.
-
Any Kusama account holder wishing to use the Broker pallet in any upcoming Kusama Coretime sales.
Any prospective Kusama Coretime purchaser, developer, and user.
KSM holders.
-The slashable deposit if set too high, may result in an economic impact, where less Kusama Coretime core sales are purchased.
-Lack of a slashable deposit in the Broker pallet is a security concern, since it exposes Kusama Coretime sales to potential abuse.
Reserving a proportion of Kusama Coretime sales cores for those with on-chain identities should not be to the exclusion of accounts that wish to remain anonymous or cause cores to be wasted unnecessarily. As such, if cores that are reserved for on-chain identities remain unsold then they should be released to anonymous accounts that are on a waiting list.
No implementation pitfalls have been identified.
-
-
+
+
It should improve performance as it reduces the potential for state bloat since there is less risk of undesirable Kusama Coretime sales activity that would be apparent with no requirement for a slashable deposit or there being no reputational risk to purchasers that waste or misuse Kusama Coretime cores.
The solution proposes to minimize the risk of some Kusama Coretime cores not even being used or leased to perform any tasks at all.
It will be important to monitor and manage the slashable deposits, purchaser reputations, and utilization of the proportion of cores that are reserved for accounts with an on-chain identity.
-The mechanism for setting a slashable deposit amount, should avoid undue complexity for users.
-Updates to Polkadot.js Apps, API and its documentation and those referring to it may be required.
-No prior articles.
-None
-
+
None
(source)
Table of Contents
@@ -10199,7 +10019,7 @@ Implement call filters. This will allow multisig accounts to only accept certain
Authors Kian Paimani This RFC proposes a new pallet_inflation to be added to the Polkadot runtime, which improves
inflation machinery of the Polkadot relay chain in a number of ways:
@@ -10209,7 +10029,7 @@ inflation machinery of the Polkadot relay chain in a number of ways:
systems, as proposed
RFC32 .
-The existing inflation logic in the relay chain suffers from a number of drawbacks:
-First, let's further elaborate on the existing order. The current inflation logic is deeply nested
in pallet_staking, and pallet_staking::Config::EraPayout interface. Through this trait, the
@@ -10375,7 +10195,7 @@ prefixed by dynamic_params.
Whereby FixedAnnualInflationAmount is the fixed absolute value (as opposed to ratio ) by
which the chain inflates annually, for example 100m DOTs.
-The following drawbacks are noted:
The solution provided here is possibly an over-engineering, if we want to achieve the goal of
@@ -10389,24 +10209,24 @@ of the inflation amount being reliant on eg. the staking-rate. We acknowledge th
but given that many PoS inflationary systems rely on the staking rate, we believe it is a
reasonable compromise. Such parameters can be ignored if the implementation does not need them.
-The new pallet_inflation, among its integration into pallet_staking must be thoroughly audited
and reviewed by fellows. We also emphasize on simulating the actual inflation logic using the real
polkadot state with Chopsticks and try-runtime.
-
+
The proposed system in this RFC implies a handful of extra storage reads and writes "per inflation
cycle", but given that a reasonable instance of this pallet would probably decide to inflation eg.
once per day, the performance impact is negligible.
The drawback section above noted some ergonomic concerns.
The "New Order" section above notes the compatibility notes with the existing staking
and inflation system.
-
Previous updates to the inflation system:
pallet_parametershttps://forum.polkadot.network/t/adjusting-the-current-inflation-model-to-sustain-treasury-inflow/3301
-
Whether the design proposed in this RFC is worthy of the complexity implementing and integrating
it? Note that a draft implementation already exists, yet the amount of further work needed to
@@ -10417,7 +10237,7 @@ timestamps must be provided to the pallet in order to function, possibly being s
relay-chain. @ggwpez has explored issues related to on-demand core-time and time-based systems
here .
-
+
If initial reaction is positive researchers and economic experts should formulate their desired
inflation parameters and systems, such that we can be sure the pallet is flexible enough in
@@ -10461,13 +10281,13 @@ the pallet design as it stands, this is very unlikely.
Authors Aurora Poppyseed , Philip Lucsok This RFC proposes the addition of a secondary market feature to either the broker pallet or as a separate pallet maintained by Lastic, enabling users to list and purchase regions. This includes creating, purchasing, and removing listings, as well as emitting relevant events and handling associated errors.
-Currently, the broker pallet lacks functionality for a secondary market, which limits users' ability to freely trade regions. This RFC aims to introduce a secure and straightforward mechanism for users to list regions they own for sale and allow other users to purchase these regions.
While integrating this functionality directly into the broker pallet is one option, another viable approach is to implement it as a separate pallet maintained by Lastic. This separate pallet would have access to the broker pallet and add minimal functionality necessary to support the secondary market.
Adding smart contracts to the Coretime chain could also address this need; however, this process is expected to be lengthy and complex. We cannot afford to wait for this extended timeline to enable basic secondary market functionality. By proposing either integration into the broker pallet or the creation of a dedicated pallet, we can quickly enhance the flexibility and utility of the broker pallet, making it more user-friendly and valuable.
-Primary stakeholders include:
Developers working on the broker pallet.
@@ -10475,7 +10295,7 @@ the pallet design as it stands, this is very unlikely.
Users who own regions and wish to trade them.
Community members interested in enhancing the broker pallet’s capabilities.
-This RFC introduces the following key features:
@@ -10516,10 +10336,10 @@ the pallet design as it stands, this is very unlikely.
-The main drawback of adding the additional complexity directly to the broker pallet is the potential increase in maintenance overhead. Therefore, we propose adding additional functionality as a separate pallet on the Coretime chain. To take the pressure off from implementing these features, implementation along with unit tests would be taken care of by Lastic (Aurora Makovac, Philip Lucsok).
There are potential risks of security vulnerabilities in the new market functionalities, such as unauthorized region transfers or incorrect balance adjustments. Therefore, extensive security measures would have to be implemented.
-
Comprehensive unit tests need to be provided to ensure the correctness of the new functionalities.
@@ -10535,31 +10355,31 @@ the pallet design as it stands, this is very unlikely.
The proposal does not introduce new privacy concerns as it only affects region trading functionality within the existing framework.
-
-
+
+
This feature is expected to introduce minimal overhead since it primarily involves read and write operations to storage maps.
Efforts will be made to optimize the code to prevent unnecessary computational costs.
-
The new functions are designed to be intuitive and easy to use, providing clear feedback through events and errors.
Documentation and examples will be provided to assist developers and users.
-
This proposal does not break compatibility with existing interfaces or previous versions.
No migrations are necessary as it introduces new functionality without altering existing features.
-
All related discussions are going to be under this PR.
-
Are there additional security measures needed to prevent potential abuses of the new functionalities?
-
+
Integration with external NFT marketplaces for more robust trading options.
Development of user interfaces to interact with the new marketplace features seamlessly.
@@ -10602,12 +10422,12 @@ the pallet design as it stands, this is very unlikely.
Authors Aurora Poppyseed , Phil Lucksok This RFC proposes the integration of smart contracts on the Coretime chain to enhance flexibility and enable complex decentralized applications, including secondary market functionalities.
-Currently, the Coretime chain lacks the capability to support smart contracts, which limits the range of decentralized applications that can be developed and deployed. By enabling smart contracts, the Coretime chain can facilitate more sophisticated functionalities such as automated region trading, dynamic pricing mechanisms, and other decentralized applications that require programmable logic. This will enhance the utility of the Coretime chain, attract more developers, and create more opportunities for innovation.
Additionally, while there is a proposal (#885) to allow EVM-compatible contracts on Polkadot’s Asset Hub, the implementation of smart contracts directly on the Coretime chain will provide synchronous interactions and avoid the complexities of asynchronous operations via XCM.
-Primary stakeholders include:
Developers working on the Coretime chain.
@@ -10615,7 +10435,7 @@ the pallet design as it stands, this is very unlikely.
Community members interested in expanding the capabilities of the Coretime chain.
Secondary Coretime marketplaces.
-This RFC introduces the following key components:
@@ -10647,14 +10467,14 @@ the pallet design as it stands, this is very unlikely.
-There are several drawbacks to consider:
Complexity : Adding smart contracts introduces significant complexity to the Coretime chain, which may increase maintenance overhead and the potential for bugs.Performance : The execution of smart contracts can be resource-intensive, potentially affecting the performance of the Coretime chain.Security : Smart contracts are prone to vulnerabilities and exploits, necessitating rigorous security measures and continuous monitoring.
-
Comprehensive unit tests and integration tests should be developed to ensure the correct functionality of smart contracts.
@@ -10670,36 +10490,36 @@ the pallet design as it stands, this is very unlikely.
The proposal does not introduce new privacy concerns as it extends existing functionalities with programmable logic.
-
-
+
+
The introduction of smart contracts may impact performance due to the additional computational overhead.
Optimization techniques, such as efficient gas fee mechanisms and resource management, should be employed to minimize performance degradation.
-
The new functionality should be designed to be intuitive and easy to use for developers, with comprehensive documentation and examples.
Provide developer tools and SDKs to facilitate the creation and deployment of smart contracts.
-
This proposal should maintain compatibility with existing interfaces and functionalities of the Coretime chain.
Ensure backward compatibility and provide migration paths if necessary.
-
Ethereum’s implementation of smart contracts using Solidity.
Polkadot’s Ink! smart contract platform.
Existing decentralized applications and use cases on other blockchain platforms.
Proposal #885: EVM-compatible contracts on Asset Hub, which highlights the community's interest in integrating smart contracts within the Polkadot ecosystem.
-
What specific security measures should be implemented to prevent smart contract vulnerabilities?
How can we ensure optimal performance while supporting complex smart contracts?
What are the best practices for integrating smart contracts with existing pallets on the Coretime chain?
-
+
Further enhancements could include advanced developer tools and SDKs for smart contract development.
Integration with external decentralized applications and platforms to expand the ecosystem.
@@ -10738,52 +10558,52 @@ the pallet design as it stands, this is very unlikely.
Authors Francisco Aguirre The SetFeesMode instruction and the fees_mode register allow for the existence of JIT withdrawal.
JIT withdrawal complicates the fee mechanism and leads to bugs and unexpected behaviour.
The proposal is to remove said functionality.
Another effort to simplify fee handling in XCM.
-The JIT withdrawal mechanism creates bugs such as not being able to get fees when all assets are put into holding and none left in the origin location.
This is a confusing behavior, since there are funds for fees, just not where the XCVM wants them.
The XCVM should have only one entrypoint to fee payment, the holding register.
That way there is also less surface for bugs.
-
Runtime Users
Runtime Devs
Wallets
dApps
-The SetFeesMode instruction will be removed.
The Fees Mode register will be removed.
-Users will have to make sure to put enough assets in WithdrawAsset when
previously some things might have been charged directly from their accounts.
This leads to a more predictable behaviour though so it will only be
a drawback for the minority of users.
-Implementations and benchmarking must change for most existing pallet calls
that send XCMs to other locations.
-
-
+
+
Performance will be improved since unnecessary checks will be avoided.
-JIT withdrawal was a way of side-stepping the regular flow of XCM programs.
By removing it, the spec is simplified but now old use-cases have to work with
the original intended behaviour, which may result in more implementation work.
Ergonomics for users will undoubtedly improve since the system is more predictable.
-Existing programs in the ecosystem will break.
The instruction should be deprecated as soon as this RFC is approved
(but still fully supported), then removed in a subsequent XCM version
(probably deprecate in v5, remove in v6).
-The previous RFC PR on the xcm-format repo, before XCM RFCs were moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/57.
-None.
-
+
The new generic fees mechanism is related to this proposal and further stimulates it as the JIT withdraw fees mechanism will become useless anyway.
(source)
Table of Contents
@@ -10816,20 +10636,20 @@ The instruction should be deprecated as soon as this RFC is approved
Authors Liu-Cheng Xu This RFC proposes compressing the state response message during the state syncing process to reduce the amount of data transferred.
-State syncing can require downloading several gigabytes of data, particularly for blockchains with large state sizes, such as Astar, which
has a state size exceeding 5 GiB (https://github.com/AstarNetwork/Astar/issues/1110). This presents a significant
challenge for nodes with slower network connections. Additionally, the current state sync implementation lacks a persistence feature (https://github.com/paritytech/polkadot-sdk/issues/4),
meaning any network disruption forces the node to re-download the entire state, making the process even more difficult.
-This RFC benefits all projects utilizing the Substrate framework, specifically in improving the efficiency of state syncing.
Node Operators.
Substrate Users.
-The largest portion of the state response message consists of either CompactProof or Vec<KeyValueStateEntry>, depending on whether a proof is requested (source ):
CompactProof: When proof is requested, compression yields a lower ratio but remains beneficial, as shown in warp sync tests in the Performance section below.
-None identified.
-The code changes required for this RFC are straightforward: compress the state response on the sender side and decompress it on the receiver side. Existing sync tests should ensure functionality remains intact.
-
-
+
+
This RFC optimizes network bandwidth usage during state syncing, particularly for blockchains with gigabyte-sized states, while introducing negligible CPU overhead for compression and decompression. For example, compressing the state response during a recent Polkadot warp sync (around height #22076653) reduces the data transferred from 530,310,121 bytes to 352,583,455 bytes — a 33% reduction, saving approximately 169 MiB of data.
Performance data is based on this patch , with logs available here .
-None.
-No compatibility issues identified.
+None.
+None.
+
+None.
+
(source)
+Table of Contents
+
+
+Start Date 22 March 2024 Description Proposal to decide polls after confirm period via a mechanism similar to a candle auction Authors Pablo Dorado, Daniel Olano
+
In an attempt to mitigate risks derived from unwanted behaviours around long decision periods on
+referenda, this proposal describes how to finalize and decide a result of a poll via a
+mechanism similar to candle auctions.
+Referenda protocol provide permissionless and efficient mechanisms to enable governance actors to
+decide the future of the blockchains around Polkadot network. However, they pose a series of risks
+derived from the game theory perspective around these mechanisms. One of them being where an actor
+uses the the public nature of the tally of a poll as a way of determining the best point in time to
+alter a poll in a meaningful way.
+While this behaviour is expected based on the current design of the referenda logic, given the
+recent extension of ongoing times (up to 1 month), the incentives for a bad actor to cause losses
+on a proposer, reflected as wasted cost of opportunity increase, and thus, this otherwise
+reasonable outcome becomes an attack vector, a potential risk to mitigate, especially when such
+attack can compromise critical guarantees of the protocol (such as its upgradeability).
+To mitigate this, the referenda underlying mechanisms should incentive actors to cast their votes
+on a poll as early as possible. This proposal's approach suggests using a Candle Auction that will
+be determined right after the confirm period finishes, thus decreasing the chances of actors to
+alter the results of a poll on confirming state, and instead incentivizing them to cast their votes
+earlier, on deciding state.
+
+Governance actors : Tokenholders and Collectives that vote on polls that have this mechanism
+enabled should be aware this change affects the outcome of failing a poll on its confirm period.Runtime Developers : This change requires runtime developers to change configuration
+parameters for the Referenda Pallet.Tooling and UI developers : Applications that interact with referenda must update to reflect
+the new Finalizing state.
+Currently, the process of a referendum/poll is defined as an sequence between an ongoing state
+(where accounts can vote), comprised by a with a preparation period, a decision period, and a
+confirm period. If the poll is passing before the decision period ends, it's possible to push
+forward to confirm period, and still, go back in case the poll fails. Once the decision period
+ends, a failure of the poll in the confirm period will lead to the poll to ultimately be rejected.
+ stateDiagram-v2
+ sb: Submission
+ pp: Preparation Period
+ dp: Decision Period
+ cp: Confirmation Period
+ state dpd <<choice>>
+ state ps <<choice>>
+ cf: Approved
+ rj: Rejected
+
+ [*] --> sb
+ sb --> pp
+ pp --> dp: decision period starts
+ dp --> cp: poll is passing
+ dp --> ps: decision period ends
+ ps --> cp: poll is passing
+ cp --> dpd: poll fails
+ dpd --> dp: decision period not deadlined
+ ps --> rj: poll is failing
+ dpd --> rj: decision period deadlined
+ cp --> cf
+ cf --> [*]
+ rj --> [*]
+This specification proposes three changes to implement this candle mechanism:
+
+
+This mechanism MUST be enabled via a configuration parameter. Once enabled, the referenda system
+MAY record the next poll ID from which to start enabling this mechanism. This is to preserve
+backwards compatibility with currently ongoing polls.
+
+
+A record of the poll status (whether it is passing or not) is stored once the decision period is
+finished.
+
+
+Including a Finalization period as part of the ongoing state. From this point, the poll MUST
+be immutable at this point.
+This period begins the moment after confirm period ends, and extends the decision for a couple
+of blocks, until the VRF seed used to determine the candle block can be considered
+"good enough" . This is, not known before the ongoing period (decision/confirmation) was over.
+Once that happens, a random block within the confirm period is chosen, and the decision of
+approving or rejecting the poll is based on the status immediately before the block where the
+candle was "lit-off" .
+
+
+When enabled, the state diagram for the referenda system is the following:
+stateDiagram-v2
+ sb: Submission
+ pp: Preparation Period
+ dp: Decision Period
+ cp: Confirmation Period
+ cds: Finalization
+ state dpd <<choice>>
+ state ps <<choice>>
+ state cd <<choice>>
+ cf: Approved
+ rj: Rejected
+
+ [*] --> sb
+ sb --> pp
+ pp --> dp: decision period starts
+ dp --> cp: poll is passing
+ ps --> cp: poll is passing
+ dp --> ps: decision period ends
+ ps --> rj: poll is failing
+ cp --> dpd: poll fails
+ dpd --> cp: decision period over
+ dpd --> dp: decision period not over
+ cp --> cds: confirmation period ends
+ cds --> cd: define moment when candle lit-off
+ cd --> cf: poll passed
+ cd --> rj: poll failed
+ cf --> [*]
+ rj --> [*]
+This approach doesn't include a mechanism to determine whether a change of the poll status in the
+confirming period is due to a legitimate change of mind of the voters, or an exploitation of its
+aforementioned vulnerabilities (like a sniping attack), instead treating all of them as potential
+attacks.
+This is an issue that can be addressed by additional mechanisms, and heuristics that can help
+determine the probability of a change of poll status to happen as a result of a legitimate behaviour.
+The implementation of this RFC will be tested on testnets (Paseo and Westend) first. Furthermore, it
+should be enabled in a canary network (like Kusama) to ensure the behaviours it is trying to address
+is indeed avoided.
+An audit will be required to ensure the implementation doesn't introduce unwanted side effects.
+There are no privacy related concerns.
+
+
+The added steps imply pessimization, necessary to meet the expected changes. An implementation MUST
+exit from the Finalization period as early as possible to minimize this impact.
+This proposal does not alter the already exposed interfaces or developers or end users. However, they
+must be aware of the changes in the additional overhead the new period might incur (these depend on the
+implemented VRF).
+This proposal does not break compatibility with existing interfaces, older versions, but it alters the
+previous implementation of the referendum processing algorithm.
+An acceptable upgrade strategy that can be applied is defining a point in time (block number, poll index)
+from which to start applying the new mechanism, thus, not affecting the already ongoing referenda.
None.
+
None.
+
+How to determine in a statistically meaningful way that a change in the poll status corresponds to an
+organic behaviour, and not an unwanted, malicious behaviour?
+
-None.
+A proposed implementation of this change can be seen on this Pull Request .
(source)
Table of Contents
diff --git a/proposed/0102-offchain-parachain-runtime-upgrades.html b/proposed/0102-offchain-parachain-runtime-upgrades.html
index d999723..4400548 100644
--- a/proposed/0102-offchain-parachain-runtime-upgrades.html
+++ b/proposed/0102-offchain-parachain-runtime-upgrades.html
@@ -90,7 +90,7 @@
diff --git a/proposed/0111-pure-proxy-replication.html b/proposed/0111-pure-proxy-replication.html
index 0dc4042..11cb3eb 100644
--- a/proposed/0111-pure-proxy-replication.html
+++ b/proposed/0111-pure-proxy-replication.html
@@ -90,7 +90,7 @@
diff --git a/proposed/0114-secp256r1-hostfunction.html b/proposed/0114-secp256r1-hostfunction.html
index 93f01a8..381d756 100644
--- a/proposed/0114-secp256r1-hostfunction.html
+++ b/proposed/0114-secp256r1-hostfunction.html
@@ -90,7 +90,7 @@
diff --git a/proposed/0117-unbrick-collective.html b/proposed/0117-unbrick-collective.html
index d840236..5404bf2 100644
--- a/proposed/0117-unbrick-collective.html
+++ b/proposed/0117-unbrick-collective.html
@@ -90,7 +90,7 @@
@@ -359,7 +359,7 @@ of the paras, the locked/unlocked state, and the manager info.
+
@@ -373,7 +373,7 @@ of the paras, the locked/unlocked state, and the manager info.
+
diff --git a/proposed/0121-iterable-referenda-tracks.html b/proposed/0121-iterable-referenda-tracks.html
index b5d033d..8e9929d 100644
--- a/proposed/0121-iterable-referenda-tracks.html
+++ b/proposed/0121-iterable-referenda-tracks.html
@@ -90,7 +90,7 @@
@@ -289,7 +289,7 @@ stores the configurations, and implements TracksInfo using the iter
-
+
@@ -303,7 +303,7 @@ stores the configurations, and implements TracksInfo using the iter
-
+
diff --git a/proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html b/proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html
index 5f2b9ca..28a6c6d 100644
--- a/proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html
+++ b/proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html
@@ -90,7 +90,7 @@
diff --git a/proposed/0124-extrinsic-version-5.html b/proposed/0124-extrinsic-version-5.html
index 0d05b05..0a0a09f 100644
--- a/proposed/0124-extrinsic-version-5.html
+++ b/proposed/0124-extrinsic-version-5.html
@@ -90,7 +90,7 @@
diff --git a/proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html b/proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html
index a2ebc1c..7d221c6 100644
--- a/proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html
+++ b/proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html
@@ -90,7 +90,7 @@
diff --git a/searchindex.js b/searchindex.js
index f7f9f3e..d3017c6 100644
--- a/searchindex.js
+++ b/searchindex.js
@@ -1 +1 @@
-Object.assign(window.search, {"doc_urls":["introduction.html#introduction","new/0125-xcm-asset-metadata.html#rfc-0125-xcm-asset-metadata","new/0125-xcm-asset-metadata.html#summary","new/0125-xcm-asset-metadata.html#motivation","new/0125-xcm-asset-metadata.html#stakeholders","new/0125-xcm-asset-metadata.html#explanation","new/0125-xcm-asset-metadata.html#new-instructions","new/0125-xcm-asset-metadata.html#repurposing-assetinstanceundefined","new/0125-xcm-asset-metadata.html#drawbacks","new/0125-xcm-asset-metadata.html#testing-security-and-privacy","new/0125-xcm-asset-metadata.html#performance-ergonomics-and-compatibility","new/0125-xcm-asset-metadata.html#performance","new/0125-xcm-asset-metadata.html#ergonomics","new/0125-xcm-asset-metadata.html#compatibility","new/0125-xcm-asset-metadata.html#prior-art-and-references","new/0125-xcm-asset-metadata.html#unresolved-questions","new/0125-xcm-asset-metadata.html#future-directions-and-related-material","new/0126-introduce-xcq.html#rfc-0126-introduce-xcqcross-consensus-query","new/0126-introduce-xcq.html#summary","new/0126-introduce-xcq.html#motivation","new/0126-introduce-xcq.html#stakeholders","new/0126-introduce-xcq.html#explanation","new/0126-introduce-xcq.html#xcq-runtime-api","new/0126-introduce-xcq.html#xcq-executor","new/0126-introduce-xcq.html#xcq-extension","new/0126-introduce-xcq.html#xcq-program-structure","new/0126-introduce-xcq.html#xcq-program-execution-flow","new/0126-introduce-xcq.html#drawbacks","new/0126-introduce-xcq.html#performance-issues","new/0126-introduce-xcq.html#user-experience-issues","new/0126-introduce-xcq.html#testing-security-and-privacy","new/0126-introduce-xcq.html#performance-ergonomics-and-compatibility","new/0126-introduce-xcq.html#performance","new/0126-introduce-xcq.html#ergonomics","new/0126-introduce-xcq.html#compatibility","new/0126-introduce-xcq.html#prior-art-and-references","new/0126-introduce-xcq.html#unresolved-questions","new/0126-introduce-xcq.html#future-directions-and-related-material","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#rfc-0127-jam-service-for-validating-ethereum-optimistic-rollups","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#background","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#motivation","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#requirements","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#stakeholders","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#jam-service-design","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#overview","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#refine","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#key-validation-process-storage-proofs","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#accumulate","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#transfer","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#beefy","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#service-poc-implementation","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#gas--storage-considerations","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#compatibility","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#testing-security-and-privacy","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#future-directions-and-related-material","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#drawbacks-alternatives-and-unknowns","proposed/0102-offchain-parachain-runtime-upgrades.html#rfc-0000-feature-name-here","proposed/0102-offchain-parachain-runtime-upgrades.html#summary","proposed/0102-offchain-parachain-runtime-upgrades.html#motivation","proposed/0102-offchain-parachain-runtime-upgrades.html#stakeholders","proposed/0102-offchain-parachain-runtime-upgrades.html#explanation","proposed/0102-offchain-parachain-runtime-upgrades.html#introduce-a-new-ump-message-type-requestcodeupgrade","proposed/0102-offchain-parachain-runtime-upgrades.html#handle-requestcodeupgrade-on-backers","proposed/0102-offchain-parachain-runtime-upgrades.html#get-the-new-code-to-all-validators","proposed/0102-offchain-parachain-runtime-upgrades.html#on-chain-code-upgrade-process","proposed/0102-offchain-parachain-runtime-upgrades.html#handling-new-validators","proposed/0102-offchain-parachain-runtime-upgrades.html#how-do-other-parties-get-hold-of-the-pvf","proposed/0102-offchain-parachain-runtime-upgrades.html#pruning","proposed/0102-offchain-parachain-runtime-upgrades.html#drawbacks","proposed/0102-offchain-parachain-runtime-upgrades.html#testing-security-and-privacy","proposed/0102-offchain-parachain-runtime-upgrades.html#performance-ergonomics-and-compatibility","proposed/0102-offchain-parachain-runtime-upgrades.html#performance","proposed/0102-offchain-parachain-runtime-upgrades.html#ergonomics","proposed/0102-offchain-parachain-runtime-upgrades.html#compatibility","proposed/0102-offchain-parachain-runtime-upgrades.html#prior-art-and-references","proposed/0102-offchain-parachain-runtime-upgrades.html#unresolved-questions","proposed/0102-offchain-parachain-runtime-upgrades.html#future-directions-and-related-material","proposed/0102-offchain-parachain-runtime-upgrades.html#further-hardening","proposed/0102-offchain-parachain-runtime-upgrades.html#generalize-this-off-chain-storage-mechanism","proposed/0111-pure-proxy-replication.html#rfc-0111-pure-proxy-replication","proposed/0111-pure-proxy-replication.html#summary","proposed/0111-pure-proxy-replication.html#motivation","proposed/0111-pure-proxy-replication.html#stakeholders","proposed/0111-pure-proxy-replication.html#explanation","proposed/0111-pure-proxy-replication.html#drawbacks","proposed/0111-pure-proxy-replication.html#testing-security-and-privacy","proposed/0111-pure-proxy-replication.html#performance-ergonomics-and-compatibility","proposed/0111-pure-proxy-replication.html#performance","proposed/0111-pure-proxy-replication.html#ergonomics","proposed/0111-pure-proxy-replication.html#compatibility","proposed/0111-pure-proxy-replication.html#prior-art-and-references","proposed/0111-pure-proxy-replication.html#unresolved-questions","proposed/0111-pure-proxy-replication.html#future-directions-and-related-material","proposed/0114-secp256r1-hostfunction.html#rfc-0114-introduce-secp256r1_ecdsa_verify_prehashed-host-function-to-verify-nist-p256-elliptic-curve-signatures","proposed/0114-secp256r1-hostfunction.html#summary","proposed/0114-secp256r1-hostfunction.html#motivation","proposed/0114-secp256r1-hostfunction.html#stakeholders","proposed/0114-secp256r1-hostfunction.html#explanation","proposed/0114-secp256r1-hostfunction.html#drawbacks","proposed/0114-secp256r1-hostfunction.html#testing-security-and-privacy","proposed/0114-secp256r1-hostfunction.html#security","proposed/0114-secp256r1-hostfunction.html#performance-ergonomics-and-compatibility","proposed/0114-secp256r1-hostfunction.html#performance","proposed/0114-secp256r1-hostfunction.html#ergonomics","proposed/0114-secp256r1-hostfunction.html#compatibility","proposed/0114-secp256r1-hostfunction.html#prior-art-and-references","proposed/0117-unbrick-collective.html#rfc-0117-the-unbrick-collective","proposed/0117-unbrick-collective.html#summary","proposed/0117-unbrick-collective.html#motivation","proposed/0117-unbrick-collective.html#stakeholders","proposed/0117-unbrick-collective.html#explanation","proposed/0117-unbrick-collective.html#the-collective","proposed/0117-unbrick-collective.html#the-unbrick-process","proposed/0117-unbrick-collective.html#belonging-to-the-collective","proposed/0117-unbrick-collective.html#drawbacks","proposed/0117-unbrick-collective.html#testing-security-and-privacy","proposed/0117-unbrick-collective.html#performance-ergonomics-and-compatibility","proposed/0117-unbrick-collective.html#performance","proposed/0117-unbrick-collective.html#ergonomics","proposed/0117-unbrick-collective.html#compatibility","proposed/0117-unbrick-collective.html#prior-art-and-references","proposed/0117-unbrick-collective.html#unresolved-questions","proposed/0120-referenda-confirmation-by-candle-mechanism.html#rfc-0120-referenda-confirmation-by-candle-mechanism","proposed/0120-referenda-confirmation-by-candle-mechanism.html#summary","proposed/0120-referenda-confirmation-by-candle-mechanism.html#motivation","proposed/0120-referenda-confirmation-by-candle-mechanism.html#stakeholders","proposed/0120-referenda-confirmation-by-candle-mechanism.html#explanation","proposed/0120-referenda-confirmation-by-candle-mechanism.html#drawbacks","proposed/0120-referenda-confirmation-by-candle-mechanism.html#testing-security-and-privacy","proposed/0120-referenda-confirmation-by-candle-mechanism.html#performance-ergonomics-and-compatibility","proposed/0120-referenda-confirmation-by-candle-mechanism.html#performance","proposed/0120-referenda-confirmation-by-candle-mechanism.html#ergonomics","proposed/0120-referenda-confirmation-by-candle-mechanism.html#compatibility","proposed/0120-referenda-confirmation-by-candle-mechanism.html#prior-art-and-references","proposed/0120-referenda-confirmation-by-candle-mechanism.html#unresolved-questions","proposed/0120-referenda-confirmation-by-candle-mechanism.html#future-directions-and-related-material","proposed/0121-iterable-referenda-tracks.html#rfc-0121-iterable-referenda-tracks","proposed/0121-iterable-referenda-tracks.html#summary","proposed/0121-iterable-referenda-tracks.html#motivation","proposed/0121-iterable-referenda-tracks.html#stakeholders","proposed/0121-iterable-referenda-tracks.html#explanation","proposed/0121-iterable-referenda-tracks.html#drawbacks","proposed/0121-iterable-referenda-tracks.html#testing-security-and-privacy","proposed/0121-iterable-referenda-tracks.html#performance-ergonomics-and-compatibility","proposed/0121-iterable-referenda-tracks.html#performance","proposed/0121-iterable-referenda-tracks.html#ergonomics","proposed/0121-iterable-referenda-tracks.html#compatibility","proposed/0121-iterable-referenda-tracks.html#prior-art-and-references","proposed/0121-iterable-referenda-tracks.html#unresolved-questions","proposed/0121-iterable-referenda-tracks.html#future-directions-and-related-material","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#rfc-0123-introduce-pending_code-as-intermediate-storage-key-for-the-runtime-code","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#summary","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#motivation","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#stakeholders","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#explanation","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#drawbacks","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#testing-security-and-privacy","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#performance-ergonomics-and-compatibility","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#performance","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#ergonomics","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#compatibility","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#prior-art-and-references","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#unresolved-questions","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#future-directions-and-related-material","proposed/0124-extrinsic-version-5.html#rfc-0124-extrinsic-version-5","proposed/0124-extrinsic-version-5.html#summary","proposed/0124-extrinsic-version-5.html#motivation","proposed/0124-extrinsic-version-5.html#stakeholders","proposed/0124-extrinsic-version-5.html#explanation","proposed/0124-extrinsic-version-5.html#changes-to-extrinsic-authorization","proposed/0124-extrinsic-version-5.html#encoding-format-for-version-5","proposed/0124-extrinsic-version-5.html#signatures-on-polkadot-in-general-transactions","proposed/0124-extrinsic-version-5.html#summary-of-changes-in-version-5","proposed/0124-extrinsic-version-5.html#drawbacks","proposed/0124-extrinsic-version-5.html#testing-security-and-privacy","proposed/0124-extrinsic-version-5.html#performance-ergonomics-and-compatibility","proposed/0124-extrinsic-version-5.html#performance","proposed/0124-extrinsic-version-5.html#ergonomics","proposed/0124-extrinsic-version-5.html#compatibility","proposed/0124-extrinsic-version-5.html#prior-art-and-references","proposed/0124-extrinsic-version-5.html#unresolved-questions","proposed/0124-extrinsic-version-5.html#future-directions-and-related-material","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#rfc-114-adjust-tipper-track-confirmation-periods","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#summary","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#motivation","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#stakeholders","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#explanation","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#drawbacks","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#testing-security-and-privacy","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#performance-ergonomics-and-compatibility","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#performance","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#ergonomics--compatibility","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#prior-art-and-references","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#unresolved-questions","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#future-directions-and-related-material","approved/0001-agile-coretime.html#rfc-1-agile-coretime","approved/0001-agile-coretime.html#summary","approved/0001-agile-coretime.html#motivation","approved/0001-agile-coretime.html#present-system","approved/0001-agile-coretime.html#problems","approved/0001-agile-coretime.html#requirements","approved/0001-agile-coretime.html#stakeholders","approved/0001-agile-coretime.html#explanation","approved/0001-agile-coretime.html#overview","approved/0001-agile-coretime.html#detail","approved/0001-agile-coretime.html#specific-functions-of-the-coretime-chain","approved/0001-agile-coretime.html#notes-on-the-instantaneous-coretime-market","approved/0001-agile-coretime.html#notes-on-economics","approved/0001-agile-coretime.html#notes-on-types","approved/0001-agile-coretime.html#rollout","approved/0001-agile-coretime.html#performance-ergonomics-and-compatibility","approved/0001-agile-coretime.html#testing-security-and-privacy","approved/0001-agile-coretime.html#future-directions-and-related-material","approved/0001-agile-coretime.html#drawbacks-alternatives-and-unknowns","approved/0001-agile-coretime.html#prior-art-and-references","approved/0005-coretime-interface.html#rfc-5-coretime-interface","approved/0005-coretime-interface.html#summary","approved/0005-coretime-interface.html#motivation","approved/0005-coretime-interface.html#requirements","approved/0005-coretime-interface.html#stakeholders","approved/0005-coretime-interface.html#explanation","approved/0005-coretime-interface.html#ump-message-types","approved/0005-coretime-interface.html#dmp-message-types","approved/0005-coretime-interface.html#realistic-limits-of-the-usage","approved/0005-coretime-interface.html#performance-ergonomics-and-compatibility","approved/0005-coretime-interface.html#testing-security-and-privacy","approved/0005-coretime-interface.html#future-directions-and-related-material","approved/0005-coretime-interface.html#drawbacks-alternatives-and-unknowns","approved/0005-coretime-interface.html#prior-art-and-references","approved/0007-system-collator-selection.html#rfc-0007-system-collator-selection","approved/0007-system-collator-selection.html#summary","approved/0007-system-collator-selection.html#motivation","approved/0007-system-collator-selection.html#requirements","approved/0007-system-collator-selection.html#stakeholders","approved/0007-system-collator-selection.html#explanation","approved/0007-system-collator-selection.html#set-size","approved/0007-system-collator-selection.html#drawbacks","approved/0007-system-collator-selection.html#testing-security-and-privacy","approved/0007-system-collator-selection.html#performance-ergonomics-and-compatibility","approved/0007-system-collator-selection.html#performance","approved/0007-system-collator-selection.html#ergonomics","approved/0007-system-collator-selection.html#compatibility","approved/0007-system-collator-selection.html#prior-art-and-references","approved/0007-system-collator-selection.html#written-discussions","approved/0007-system-collator-selection.html#prior-feedback-and-input-from","approved/0007-system-collator-selection.html#unresolved-questions","approved/0007-system-collator-selection.html#future-directions-and-related-material","approved/0008-parachain-bootnodes-dht.html#rfc-0008-store-parachain-bootnodes-in-relay-chain-dht","approved/0008-parachain-bootnodes-dht.html#summary","approved/0008-parachain-bootnodes-dht.html#motivation","approved/0008-parachain-bootnodes-dht.html#stakeholders","approved/0008-parachain-bootnodes-dht.html#explanation","approved/0008-parachain-bootnodes-dht.html#dht-provider-registration","approved/0008-parachain-bootnodes-dht.html#new-networking-protocol","approved/0008-parachain-bootnodes-dht.html#drawbacks","approved/0008-parachain-bootnodes-dht.html#testing-security-and-privacy","approved/0008-parachain-bootnodes-dht.html#performance-ergonomics-and-compatibility","approved/0008-parachain-bootnodes-dht.html#performance","approved/0008-parachain-bootnodes-dht.html#ergonomics","approved/0008-parachain-bootnodes-dht.html#compatibility","approved/0008-parachain-bootnodes-dht.html#prior-art-and-references","approved/0008-parachain-bootnodes-dht.html#unresolved-questions","approved/0008-parachain-bootnodes-dht.html#future-directions-and-related-material","approved/0010-burn-coretime-revenue.html#rfc-0010-burn-coretime-revenue","approved/0010-burn-coretime-revenue.html#summary","approved/0010-burn-coretime-revenue.html#motivation","approved/0010-burn-coretime-revenue.html#stakeholders","approved/0010-burn-coretime-revenue.html#explanation","approved/0012-process-for-adding-new-collectives.html#rfc-0012-process-for-adding-new-system-collectives","approved/0012-process-for-adding-new-collectives.html#summary","approved/0012-process-for-adding-new-collectives.html#motivation","approved/0012-process-for-adding-new-collectives.html#stakeholders","approved/0012-process-for-adding-new-collectives.html#explanation","approved/0012-process-for-adding-new-collectives.html#removing-collectives","approved/0012-process-for-adding-new-collectives.html#drawbacks","approved/0012-process-for-adding-new-collectives.html#testing-security-and-privacy","approved/0012-process-for-adding-new-collectives.html#performance-ergonomics-and-compatibility","approved/0012-process-for-adding-new-collectives.html#prior-art-and-references","approved/0012-process-for-adding-new-collectives.html#unresolved-questions","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#rfc-0013-prepare-core-runtime-api-for-mbms","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#summary","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#motivation","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#stakeholders","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#explanation","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#coreinitialize_block","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#drawbacks","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#testing-security-and-privacy","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#performance-ergonomics-and-compatibility","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#performance","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#ergonomics","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#compatibility","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#prior-art-and-references","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#unresolved-questions","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#future-directions-and-related-material","approved/0014-improve-locking-mechanism-for-parachains.html#rfc-0014-improve-locking-mechanism-for-parachains","approved/0014-improve-locking-mechanism-for-parachains.html#summary","approved/0014-improve-locking-mechanism-for-parachains.html#motivation","approved/0014-improve-locking-mechanism-for-parachains.html#requirements","approved/0014-improve-locking-mechanism-for-parachains.html#stakeholders","approved/0014-improve-locking-mechanism-for-parachains.html#explanation","approved/0014-improve-locking-mechanism-for-parachains.html#status-quo","approved/0014-improve-locking-mechanism-for-parachains.html#proposed-changes","approved/0014-improve-locking-mechanism-for-parachains.html#migration","approved/0014-improve-locking-mechanism-for-parachains.html#drawbacks","approved/0014-improve-locking-mechanism-for-parachains.html#testing-security-and-privacy","approved/0014-improve-locking-mechanism-for-parachains.html#performance","approved/0014-improve-locking-mechanism-for-parachains.html#ergonomics","approved/0014-improve-locking-mechanism-for-parachains.html#compatibility","approved/0014-improve-locking-mechanism-for-parachains.html#prior-art-and-references","approved/0014-improve-locking-mechanism-for-parachains.html#unresolved-questions","approved/0014-improve-locking-mechanism-for-parachains.html#future-directions-and-related-material","approved/0022-adopt-encointer-runtime.html#rfc-0022-adopt-encointer-runtime","approved/0022-adopt-encointer-runtime.html#summary","approved/0022-adopt-encointer-runtime.html#motivation","approved/0022-adopt-encointer-runtime.html#stakeholders","approved/0022-adopt-encointer-runtime.html#explanation","approved/0022-adopt-encointer-runtime.html#drawbacks","approved/0022-adopt-encointer-runtime.html#testing-security-and-privacy","approved/0022-adopt-encointer-runtime.html#performance-ergonomics-and-compatibility","approved/0022-adopt-encointer-runtime.html#prior-art-and-references","approved/0022-adopt-encointer-runtime.html#unresolved-questions","approved/0022-adopt-encointer-runtime.html#future-directions-and-related-material","approved/0026-sassafras-consensus.html#rfc-0026-sassafras-consensus-protocol","approved/0026-sassafras-consensus.html#abstract","approved/0026-sassafras-consensus.html#1-motivation","approved/0026-sassafras-consensus.html#11-relevance-to-implementors","approved/0026-sassafras-consensus.html#12-supporting-sassafras-for-polkadot","approved/0026-sassafras-consensus.html#2-stakeholders","approved/0026-sassafras-consensus.html#21-blockchain-core-developers","approved/0026-sassafras-consensus.html#22-polkadot-ecosystem-contributors","approved/0026-sassafras-consensus.html#3-notation","approved/0026-sassafras-consensus.html#31-data-structures-definitions","approved/0026-sassafras-consensus.html#32-types-alias","approved/0026-sassafras-consensus.html#32-pseudo-code","approved/0026-sassafras-consensus.html#33-incremental-introduction-of-types-and-functions","approved/0026-sassafras-consensus.html#4-protocol-introduction","approved/0026-sassafras-consensus.html#41-submission-of-candidate-tickets","approved/0026-sassafras-consensus.html#42-validation-of-candidate-tickets","approved/0026-sassafras-consensus.html#43-tickets-slots-binding","approved/0026-sassafras-consensus.html#44-claim-of-ticket-ownership","approved/0026-sassafras-consensus.html#5-bandersnatch-vrfs-cryptographic-primitives","approved/0026-sassafras-consensus.html#51-bare-vrf-interface","approved/0026-sassafras-consensus.html#6-sassafras-protocol","approved/0026-sassafras-consensus.html#62-header-digest-log","approved/0026-sassafras-consensus.html#63-on-chain-randomness","approved/0026-sassafras-consensus.html#64-epoch-change-signal","approved/0026-sassafras-consensus.html#65-tickets-creation-and-submission","approved/0026-sassafras-consensus.html#66-on-chain-tickets-validation","approved/0026-sassafras-consensus.html#67-ticket-slot-binding","approved/0026-sassafras-consensus.html#68-slot-claim","approved/0026-sassafras-consensus.html#69-slot-claim-verification","approved/0026-sassafras-consensus.html#691-primary-method","approved/0026-sassafras-consensus.html#610-randomness-accumulator","approved/0026-sassafras-consensus.html#7-drawbacks","approved/0026-sassafras-consensus.html#8-testing-security-and-privacy","approved/0026-sassafras-consensus.html#9-performance-ergonomics-and-compatibility","approved/0026-sassafras-consensus.html#91-performance","approved/0026-sassafras-consensus.html#92-ergonomics","approved/0026-sassafras-consensus.html#93-compatibility","approved/0026-sassafras-consensus.html#10-prior-art-and-references","approved/0026-sassafras-consensus.html#11-unresolved-questions","approved/0026-sassafras-consensus.html#12-future-directions-and-related-material","approved/0026-sassafras-consensus.html#121-interactions-with-on-chain-code","approved/0026-sassafras-consensus.html#122-deployment-strategies","approved/0026-sassafras-consensus.html#123-zk-snark-parameters","approved/0026-sassafras-consensus.html#124-anonymous-submission-of-tickets","approved/0032-minimal-relay.html#rfc-0032-minimal-relay","approved/0032-minimal-relay.html#summary","approved/0032-minimal-relay.html#motivation","approved/0032-minimal-relay.html#stakeholders","approved/0032-minimal-relay.html#explanation","approved/0032-minimal-relay.html#migrations","approved/0032-minimal-relay.html#interfaces","approved/0032-minimal-relay.html#functional-architecture","approved/0032-minimal-relay.html#resource-allocation","approved/0032-minimal-relay.html#deployment","approved/0032-minimal-relay.html#kusama","approved/0032-minimal-relay.html#drawbacks","approved/0032-minimal-relay.html#testing-security-and-privacy","approved/0032-minimal-relay.html#performance-ergonomics-and-compatibility","approved/0032-minimal-relay.html#performance","approved/0032-minimal-relay.html#ergonomics","approved/0032-minimal-relay.html#compatibility","approved/0032-minimal-relay.html#prior-art-and-references","approved/0032-minimal-relay.html#unresolved-questions","approved/0032-minimal-relay.html#future-directions-and-related-material","approved/0042-extrinsics-state-version.html#rfc-0042-add-system-version-that-replaces-stateversion-on-runtimeversion","approved/0042-extrinsics-state-version.html#summary","approved/0042-extrinsics-state-version.html#motivation","approved/0042-extrinsics-state-version.html#stakeholders","approved/0042-extrinsics-state-version.html#explanation","approved/0042-extrinsics-state-version.html#drawbacks","approved/0042-extrinsics-state-version.html#testing-security-and-privacy","approved/0042-extrinsics-state-version.html#performance-ergonomics-and-compatibility","approved/0042-extrinsics-state-version.html#performance","approved/0042-extrinsics-state-version.html#ergonomics","approved/0042-extrinsics-state-version.html#compatibility","approved/0042-extrinsics-state-version.html#prior-art-and-references","approved/0042-extrinsics-state-version.html#unresolved-questions","approved/0042-extrinsics-state-version.html#future-directions-and-related-material","approved/0043-storage-proof-size-hostfunction.html#rfc-0043-introduce-storage_proof_size-host-function-for-improved-parachain-block-utilization","approved/0043-storage-proof-size-hostfunction.html#summary","approved/0043-storage-proof-size-hostfunction.html#motivation","approved/0043-storage-proof-size-hostfunction.html#stakeholders","approved/0043-storage-proof-size-hostfunction.html#explanation","approved/0043-storage-proof-size-hostfunction.html#performance-ergonomics-and-compatibility","approved/0043-storage-proof-size-hostfunction.html#performance","approved/0043-storage-proof-size-hostfunction.html#ergonomics","approved/0043-storage-proof-size-hostfunction.html#compatibility","approved/0043-storage-proof-size-hostfunction.html#prior-art-and-references","approved/0045-nft-deposits-asset-hub.html#rfc-0045-lowering-nft-deposits-on-asset-hub","approved/0045-nft-deposits-asset-hub.html#summary","approved/0045-nft-deposits-asset-hub.html#motivation","approved/0045-nft-deposits-asset-hub.html#requirements","approved/0045-nft-deposits-asset-hub.html#stakeholders","approved/0045-nft-deposits-asset-hub.html#explanation","approved/0045-nft-deposits-asset-hub.html#enhanced-approach-to-further-lower-barriers-for-entry","approved/0045-nft-deposits-asset-hub.html#short--and-long-term-plans","approved/0045-nft-deposits-asset-hub.html#drawbacks","approved/0045-nft-deposits-asset-hub.html#testing-security-and-privacy","approved/0045-nft-deposits-asset-hub.html#security-concerns","approved/0045-nft-deposits-asset-hub.html#performance-ergonomics-and-compatibility","approved/0045-nft-deposits-asset-hub.html#performance","approved/0045-nft-deposits-asset-hub.html#ergonomics","approved/0045-nft-deposits-asset-hub.html#compatibility","approved/0045-nft-deposits-asset-hub.html#unresolved-questions","approved/0045-nft-deposits-asset-hub.html#addendum","approved/0045-nft-deposits-asset-hub.html#enhanced-weak-governance-origin-model","approved/0045-nft-deposits-asset-hub.html#function-based-pricing-model","approved/0045-nft-deposits-asset-hub.html#linking-deposit-to-usdx-value","approved/0047-assignment-of-availability-chunks.html#rfc-0047-assignment-of-availability-chunks-to-validators","approved/0047-assignment-of-availability-chunks.html#summary","approved/0047-assignment-of-availability-chunks.html#motivation","approved/0047-assignment-of-availability-chunks.html#stakeholders","approved/0047-assignment-of-availability-chunks.html#explanation","approved/0047-assignment-of-availability-chunks.html#systematic-erasure-codes","approved/0047-assignment-of-availability-chunks.html#availability-recovery-at-present","approved/0047-assignment-of-availability-chunks.html#availability-recovery-from-systematic-chunks","approved/0047-assignment-of-availability-chunks.html#chunk-assignment-function","approved/0047-assignment-of-availability-chunks.html#network-protocol","approved/0047-assignment-of-availability-chunks.html#upgrade-path","approved/0047-assignment-of-availability-chunks.html#drawbacks","approved/0047-assignment-of-availability-chunks.html#testing-security-and-privacy","approved/0047-assignment-of-availability-chunks.html#performance-ergonomics-and-compatibility","approved/0047-assignment-of-availability-chunks.html#performance","approved/0047-assignment-of-availability-chunks.html#ergonomics","approved/0047-assignment-of-availability-chunks.html#compatibility","approved/0047-assignment-of-availability-chunks.html#prior-art-and-references","approved/0047-assignment-of-availability-chunks.html#unresolved-questions","approved/0047-assignment-of-availability-chunks.html#future-directions-and-related-material","approved/0047-assignment-of-availability-chunks.html#appendix-a","approved/0048-session-keys-runtime-api.html#rfc-0048-generate-ownership-proof-for-sessionkeys","approved/0048-session-keys-runtime-api.html#summary","approved/0048-session-keys-runtime-api.html#motivation","approved/0048-session-keys-runtime-api.html#stakeholders","approved/0048-session-keys-runtime-api.html#explanation","approved/0048-session-keys-runtime-api.html#drawbacks","approved/0048-session-keys-runtime-api.html#testing-security-and-privacy","approved/0048-session-keys-runtime-api.html#performance-ergonomics-and-compatibility","approved/0048-session-keys-runtime-api.html#performance","approved/0048-session-keys-runtime-api.html#ergonomics","approved/0048-session-keys-runtime-api.html#compatibility","approved/0048-session-keys-runtime-api.html#prior-art-and-references","approved/0048-session-keys-runtime-api.html#unresolved-questions","approved/0048-session-keys-runtime-api.html#future-directions-and-related-material","approved/0050-fellowship-salaries.html#rfc-0050-fellowship-salaries","approved/0050-fellowship-salaries.html#summary","approved/0050-fellowship-salaries.html#motivation","approved/0050-fellowship-salaries.html#stakeholders","approved/0050-fellowship-salaries.html#explanation","approved/0050-fellowship-salaries.html#salary-asset","approved/0050-fellowship-salaries.html#projections","approved/0050-fellowship-salaries.html#updates","approved/0050-fellowship-salaries.html#drawbacks","approved/0050-fellowship-salaries.html#testing-security-and-privacy","approved/0050-fellowship-salaries.html#performance-ergonomics-and-compatibility","approved/0050-fellowship-salaries.html#performance","approved/0050-fellowship-salaries.html#ergonomics","approved/0050-fellowship-salaries.html#compatibility","approved/0050-fellowship-salaries.html#prior-art-and-references","approved/0050-fellowship-salaries.html#unresolved-questions","approved/0056-one-transaction-per-notification.html#rfc-0056-enforce-only-one-transaction-per-notification","approved/0056-one-transaction-per-notification.html#summary","approved/0056-one-transaction-per-notification.html#motivation","approved/0056-one-transaction-per-notification.html#stakeholders","approved/0056-one-transaction-per-notification.html#explanation","approved/0056-one-transaction-per-notification.html#drawbacks","approved/0056-one-transaction-per-notification.html#testing-security-and-privacy","approved/0056-one-transaction-per-notification.html#performance-ergonomics-and-compatibility","approved/0056-one-transaction-per-notification.html#performance","approved/0056-one-transaction-per-notification.html#ergonomics","approved/0056-one-transaction-per-notification.html#compatibility","approved/0056-one-transaction-per-notification.html#prior-art-and-references","approved/0056-one-transaction-per-notification.html#unresolved-questions","approved/0056-one-transaction-per-notification.html#future-directions-and-related-material","approved/0059-nodes-capabilities-discovery.html#rfc-0059-add-a-discovery-mechanism-for-nodes-based-on-their-capabilities","approved/0059-nodes-capabilities-discovery.html#summary","approved/0059-nodes-capabilities-discovery.html#motivation","approved/0059-nodes-capabilities-discovery.html#stakeholders","approved/0059-nodes-capabilities-discovery.html#explanation","approved/0059-nodes-capabilities-discovery.html#capabilities","approved/0059-nodes-capabilities-discovery.html#dht-provider-registration","approved/0059-nodes-capabilities-discovery.html#secondary-dhts","approved/0059-nodes-capabilities-discovery.html#head-of-the-chain-providers","approved/0059-nodes-capabilities-discovery.html#drawbacks","approved/0059-nodes-capabilities-discovery.html#testing-security-and-privacy","approved/0059-nodes-capabilities-discovery.html#performance-ergonomics-and-compatibility","approved/0059-nodes-capabilities-discovery.html#performance","approved/0059-nodes-capabilities-discovery.html#ergonomics","approved/0059-nodes-capabilities-discovery.html#compatibility","approved/0059-nodes-capabilities-discovery.html#prior-art-and-references","approved/0059-nodes-capabilities-discovery.html#unresolved-questions","approved/0059-nodes-capabilities-discovery.html#future-directions-and-related-material","approved/0078-merkleized-metadata.html#rfc-0078-merkleized-metadata","approved/0078-merkleized-metadata.html#summary","approved/0078-merkleized-metadata.html#motivation","approved/0078-merkleized-metadata.html#requirements","approved/0078-merkleized-metadata.html#reduce-metadata-size","approved/0078-merkleized-metadata.html#stakeholders","approved/0078-merkleized-metadata.html#explanation","approved/0078-merkleized-metadata.html#metadata-digest","approved/0078-merkleized-metadata.html#extrinsic-metadata","approved/0078-merkleized-metadata.html#type-information","approved/0078-merkleized-metadata.html#prune-unrelated-types","approved/0078-merkleized-metadata.html#generating-typeref","approved/0078-merkleized-metadata.html#building-the-merkle-tree-root","approved/0078-merkleized-metadata.html#inclusion-in-an-extrinsic","approved/0078-merkleized-metadata.html#drawbacks","approved/0078-merkleized-metadata.html#testing-security-and-privacy","approved/0078-merkleized-metadata.html#performance-ergonomics-and-compatibility","approved/0078-merkleized-metadata.html#performance","approved/0078-merkleized-metadata.html#ergonomics--compatibility","approved/0078-merkleized-metadata.html#prior-art-and-references","approved/0078-merkleized-metadata.html#unresolved-questions","approved/0078-merkleized-metadata.html#future-directions-and-related-material","approved/0084-general-transaction-extrinsic-format.html#rfc-0084-general-transactions-in-extrinsic-format","approved/0084-general-transaction-extrinsic-format.html#summary","approved/0084-general-transaction-extrinsic-format.html#motivation","approved/0084-general-transaction-extrinsic-format.html#stakeholders","approved/0084-general-transaction-extrinsic-format.html#explanation","approved/0084-general-transaction-extrinsic-format.html#drawbacks","approved/0084-general-transaction-extrinsic-format.html#testing-security-and-privacy","approved/0084-general-transaction-extrinsic-format.html#performance-ergonomics-and-compatibility","approved/0084-general-transaction-extrinsic-format.html#performance","approved/0084-general-transaction-extrinsic-format.html#ergonomics","approved/0084-general-transaction-extrinsic-format.html#compatibility","approved/0084-general-transaction-extrinsic-format.html#prior-art-and-references","approved/0084-general-transaction-extrinsic-format.html#unresolved-questions","approved/0084-general-transaction-extrinsic-format.html#future-directions-and-related-material","approved/0091-dht-record-creation-time.html#rfc-0091-dht-authority-discovery-record-creation-time","approved/0091-dht-record-creation-time.html#summary","approved/0091-dht-record-creation-time.html#motivation","approved/0091-dht-record-creation-time.html#stakeholders","approved/0091-dht-record-creation-time.html#explanation","approved/0091-dht-record-creation-time.html#drawbacks","approved/0091-dht-record-creation-time.html#testing-security-and-privacy","approved/0091-dht-record-creation-time.html#performance-ergonomics-and-compatibility","approved/0091-dht-record-creation-time.html#performance","approved/0091-dht-record-creation-time.html#ergonomics","approved/0091-dht-record-creation-time.html#compatibility","approved/0091-dht-record-creation-time.html#prior-art-and-references","approved/0091-dht-record-creation-time.html#unresolved-questions","approved/0091-dht-record-creation-time.html#future-directions-and-related-material","approved/0097-unbonding_queue.html#rfc-0097-unbonding-queue","approved/0097-unbonding_queue.html#summary","approved/0097-unbonding_queue.html#motivation","approved/0097-unbonding_queue.html#stakeholders","approved/0097-unbonding_queue.html#explanation","approved/0097-unbonding_queue.html#mechanism","approved/0097-unbonding_queue.html#proposed-parameters","approved/0097-unbonding_queue.html#rebonding","approved/0097-unbonding_queue.html#empirical-analysis","approved/0097-unbonding_queue.html#additional-considerations","approved/0097-unbonding_queue.html#deferred-slashing","approved/0097-unbonding_queue.html#uxui","approved/0097-unbonding_queue.html#conviction-voting","approved/0097-unbonding_queue.html#potential-extension","approved/0097-unbonding_queue.html#drawbacks","approved/0097-unbonding_queue.html#testing-security-and-privacy","approved/0097-unbonding_queue.html#performance-ergonomics-and-compatibility","approved/0097-unbonding_queue.html#performance","approved/0097-unbonding_queue.html#ergonomics","approved/0097-unbonding_queue.html#compatibility","approved/0097-unbonding_queue.html#prior-art-and-references","approved/0099-transaction-extension-version.html#rfc-0099-introduce-a-transaction-extension-version","approved/0099-transaction-extension-version.html#summary","approved/0099-transaction-extension-version.html#motivation","approved/0099-transaction-extension-version.html#stakeholders","approved/0099-transaction-extension-version.html#explanation","approved/0099-transaction-extension-version.html#drawbacks","approved/0099-transaction-extension-version.html#testing-security-and-privacy","approved/0099-transaction-extension-version.html#performance-ergonomics-and-compatibility","approved/0099-transaction-extension-version.html#performance","approved/0099-transaction-extension-version.html#ergonomics","approved/0099-transaction-extension-version.html#compatibility","approved/0099-transaction-extension-version.html#prior-art-and-references","approved/0099-transaction-extension-version.html#unresolved-questions","approved/0099-transaction-extension-version.html#future-directions-and-related-material","approved/0100-xcm-multi-type-asset-transfer.html#rfc-0100-new-xcm-instruction-initiateassetstransfer","approved/0100-xcm-multi-type-asset-transfer.html#summary","approved/0100-xcm-multi-type-asset-transfer.html#motivation","approved/0100-xcm-multi-type-asset-transfer.html#stakeholders","approved/0100-xcm-multi-type-asset-transfer.html#explanation","approved/0100-xcm-multi-type-asset-transfer.html#example-usage-transferring-2-different-asset-types-across-3-chains","approved/0100-xcm-multi-type-asset-transfer.html#drawbacks","approved/0100-xcm-multi-type-asset-transfer.html#testing-security-and-privacy","approved/0100-xcm-multi-type-asset-transfer.html#performance-ergonomics-and-compatibility","approved/0100-xcm-multi-type-asset-transfer.html#performance","approved/0100-xcm-multi-type-asset-transfer.html#ergonomics","approved/0100-xcm-multi-type-asset-transfer.html#compatibility","approved/0100-xcm-multi-type-asset-transfer.html#prior-art-and-references","approved/0100-xcm-multi-type-asset-transfer.html#unresolved-questions","approved/0100-xcm-multi-type-asset-transfer.html#future-directions-and-related-material","approved/0101-xcm-transact-remove-max-weight-param.html#rfc-0101-xcm-transact-remove-require_weight_at_most-parameter","approved/0101-xcm-transact-remove-max-weight-param.html#summary","approved/0101-xcm-transact-remove-max-weight-param.html#motivation","approved/0101-xcm-transact-remove-max-weight-param.html#stakeholders","approved/0101-xcm-transact-remove-max-weight-param.html#explanation","approved/0101-xcm-transact-remove-max-weight-param.html#drawbacks","approved/0101-xcm-transact-remove-max-weight-param.html#testing-security-and-privacy","approved/0101-xcm-transact-remove-max-weight-param.html#performance-ergonomics-and-compatibility","approved/0101-xcm-transact-remove-max-weight-param.html#performance","approved/0101-xcm-transact-remove-max-weight-param.html#ergonomics","approved/0101-xcm-transact-remove-max-weight-param.html#compatibility","approved/0101-xcm-transact-remove-max-weight-param.html#prior-art-and-references","approved/0101-xcm-transact-remove-max-weight-param.html#unresolved-questions","approved/0101-xcm-transact-remove-max-weight-param.html#future-directions-and-related-material","approved/0103-introduce-core-index-commitment.html#rfc-0103--introduce-a-coreindex-commitment-and-a-sessionindex-field-in-candidate-receipts","approved/0103-introduce-core-index-commitment.html#summary","approved/0103-introduce-core-index-commitment.html#motivation","approved/0103-introduce-core-index-commitment.html#stakeholders","approved/0103-introduce-core-index-commitment.html#explanation","approved/0103-introduce-core-index-commitment.html#reclaiming-unused-space-in-the-descriptor","approved/0103-introduce-core-index-commitment.html#ump-transport","approved/0103-introduce-core-index-commitment.html#polkadot-primitive-changes","approved/0103-introduce-core-index-commitment.html#backwards-compatibility","approved/0103-introduce-core-index-commitment.html#parachain-block-validation","approved/0103-introduce-core-index-commitment.html#on-chain-backing","approved/0103-introduce-core-index-commitment.html#drawbacks","approved/0103-introduce-core-index-commitment.html#testing-security-and-privacy","approved/0103-introduce-core-index-commitment.html#performance","approved/0103-introduce-core-index-commitment.html#ergonomics","approved/0103-introduce-core-index-commitment.html#compatibility","approved/0103-introduce-core-index-commitment.html#relay-chain-runtime","approved/0103-introduce-core-index-commitment.html#validators","approved/0103-introduce-core-index-commitment.html#tooling","approved/0103-introduce-core-index-commitment.html#prior-art-and-references","approved/0103-introduce-core-index-commitment.html#unresolved-questions","approved/0103-introduce-core-index-commitment.html#future-directions-and-related-material","approved/0105-xcm-improved-fee-mechanism.html#rfc-0105-xcm-improved-fee-mechanism","approved/0105-xcm-improved-fee-mechanism.html#summary","approved/0105-xcm-improved-fee-mechanism.html#motivation","approved/0105-xcm-improved-fee-mechanism.html#stakeholders","approved/0105-xcm-improved-fee-mechanism.html#explanation","approved/0105-xcm-improved-fee-mechanism.html#examples","approved/0105-xcm-improved-fee-mechanism.html#drawbacks","approved/0105-xcm-improved-fee-mechanism.html#testing-security-and-privacy","approved/0105-xcm-improved-fee-mechanism.html#performance-ergonomics-and-compatibility","approved/0105-xcm-improved-fee-mechanism.html#performance","approved/0105-xcm-improved-fee-mechanism.html#ergonomics","approved/0105-xcm-improved-fee-mechanism.html#compatibility","approved/0105-xcm-improved-fee-mechanism.html#prior-art-and-references","approved/0105-xcm-improved-fee-mechanism.html#unresolved-questions","approved/0105-xcm-improved-fee-mechanism.html#future-directions-and-related-material","approved/0107-xcm-execution-hints.html#rfc-0107-xcm-execution-hints","approved/0107-xcm-execution-hints.html#summary","approved/0107-xcm-execution-hints.html#motivation","approved/0107-xcm-execution-hints.html#stakeholders","approved/0107-xcm-execution-hints.html#explanation","approved/0107-xcm-execution-hints.html#drawbacks","approved/0107-xcm-execution-hints.html#testing-security-and-privacy","approved/0107-xcm-execution-hints.html#performance-ergonomics-and-compatibility","approved/0107-xcm-execution-hints.html#performance","approved/0107-xcm-execution-hints.html#ergonomics","approved/0107-xcm-execution-hints.html#compatibility","approved/0107-xcm-execution-hints.html#prior-art-and-references","approved/0107-xcm-execution-hints.html#unresolved-questions","approved/0107-xcm-execution-hints.html#future-directions-and-related-material","approved/0108-xcm-remove-testnet-ids.html#rfc-0108-remove-xcm-testnet-networkids","approved/0108-xcm-remove-testnet-ids.html#summary","approved/0108-xcm-remove-testnet-ids.html#motivation","approved/0108-xcm-remove-testnet-ids.html#stakeholders","approved/0108-xcm-remove-testnet-ids.html#explanation","approved/0108-xcm-remove-testnet-ids.html#drawbacks","approved/0108-xcm-remove-testnet-ids.html#testing-security-and-privacy","approved/0108-xcm-remove-testnet-ids.html#performance-ergonomics-and-compatibility","approved/0108-xcm-remove-testnet-ids.html#performance","approved/0108-xcm-remove-testnet-ids.html#ergonomics","approved/0108-xcm-remove-testnet-ids.html#compatibility","approved/0108-xcm-remove-testnet-ids.html#prior-art-and-references","approved/0108-xcm-remove-testnet-ids.html#unresolved-questions","approved/0108-xcm-remove-testnet-ids.html#future-directions-and-related-material","approved/0122-alias-origin-on-asset-transfers.html#rfc-0122-asset-transfers-can-alias-xcm-origin-on-destination-to-original-origin","approved/0122-alias-origin-on-asset-transfers.html#summary","approved/0122-alias-origin-on-asset-transfers.html#motivation","approved/0122-alias-origin-on-asset-transfers.html#stakeholders","approved/0122-alias-origin-on-asset-transfers.html#explanation","approved/0122-alias-origin-on-asset-transfers.html#trust-assumptions","approved/0122-alias-origin-on-asset-transfers.html#xcm-initiateassetstransfer-instruction-changes","approved/0122-alias-origin-on-asset-transfers.html#example-scenarios","approved/0122-alias-origin-on-asset-transfers.html#drawbacks","approved/0122-alias-origin-on-asset-transfers.html#testing-security-and-privacy","approved/0122-alias-origin-on-asset-transfers.html#performance-ergonomics-and-compatibility","approved/0122-alias-origin-on-asset-transfers.html#performance","approved/0122-alias-origin-on-asset-transfers.html#ergonomics","approved/0122-alias-origin-on-asset-transfers.html#compatibility","approved/0122-alias-origin-on-asset-transfers.html#prior-art-and-references","approved/0122-alias-origin-on-asset-transfers.html#unresolved-questions","approved/0122-alias-origin-on-asset-transfers.html#future-directions-and-related-material","stale/0000-rewards.html#rfc-0000-validator-rewards","stale/0000-rewards.html#summary","stale/0000-rewards.html#motivation","stale/0000-rewards.html#stakeholders","stale/0000-rewards.html#logic","stale/0000-rewards.html#categories","stale/0000-rewards.html#collection","stale/0000-rewards.html#messages","stale/0000-rewards.html#rewards-compoutation","stale/0000-rewards.html#strategies","stale/0000-rewards.html#explanation","stale/0000-rewards.html#backing","stale/0000-rewards.html#approvals","stale/0000-rewards.html#availability-redistribution","stale/0000-rewards.html#tit-for-tat","stale/0000-rewards.html#concerns-drawbacks-testing-security-and-privacy","stale/0000-rewards.html#performance-ergonomics-and-compatibility","stale/0000-rewards.html#prior-art-and-references","stale/0000-rewards.html#unresolved-questions","stale/0000-rewards.html#future-directions-and-related-material","stale/0000-rewards.html#synthetic-parachain-flag","stale/0004-remove-unnecessary-allocator-usage.html#rfc-0004-remove-the-host-side-runtime-memory-allocator","stale/0004-remove-unnecessary-allocator-usage.html#summary","stale/0004-remove-unnecessary-allocator-usage.html#motivation","stale/0004-remove-unnecessary-allocator-usage.html#stakeholders","stale/0004-remove-unnecessary-allocator-usage.html#explanation","stale/0004-remove-unnecessary-allocator-usage.html#new-host-functions","stale/0004-remove-unnecessary-allocator-usage.html#other-changes","stale/0004-remove-unnecessary-allocator-usage.html#drawbacks","stale/0004-remove-unnecessary-allocator-usage.html#prior-art","stale/0004-remove-unnecessary-allocator-usage.html#unresolved-questions","stale/0004-remove-unnecessary-allocator-usage.html#future-possibilities","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#rfc-0006-dynamic-pricing-for-bulk-coretime-sales","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#summary","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#motivation","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#requirements","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#stakeholders","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#explanation","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#overview","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#parameters","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#function","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#pseudo-code","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#properties-of-the-curve","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#example-configurations","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#drawbacks","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#prior-art-and-references","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#future-possibilities","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#references","stale/0009-improved-net-light-client-requests.html#rfc-0009-improved-light-client-requests-networking-protocol","stale/0009-improved-net-light-client-requests.html#summary","stale/0009-improved-net-light-client-requests.html#motivation","stale/0009-improved-net-light-client-requests.html#stakeholders","stale/0009-improved-net-light-client-requests.html#explanation","stale/0009-improved-net-light-client-requests.html#drawbacks","stale/0009-improved-net-light-client-requests.html#testing-security-and-privacy","stale/0009-improved-net-light-client-requests.html#performance-ergonomics-and-compatibility","stale/0009-improved-net-light-client-requests.html#performance","stale/0009-improved-net-light-client-requests.html#ergonomics","stale/0009-improved-net-light-client-requests.html#compatibility","stale/0009-improved-net-light-client-requests.html#prior-art-and-references","stale/0009-improved-net-light-client-requests.html#unresolved-questions","stale/0009-improved-net-light-client-requests.html#future-directions-and-related-material","stale/0015-market-design-revisit.html#rfc-0015-market-design-revisit","stale/0015-market-design-revisit.html#summary","stale/0015-market-design-revisit.html#motivation","stale/0015-market-design-revisit.html#stakeholders","stale/0015-market-design-revisit.html#explanation","stale/0015-market-design-revisit.html#bulk-markets","stale/0015-market-design-revisit.html#benefits-of-this-system","stale/0015-market-design-revisit.html#further-discussion-points","stale/0015-market-design-revisit.html#drawbacks","stale/0015-market-design-revisit.html#prior-art-and-references","stale/0015-market-design-revisit.html#unresolved-questions","stale/0034-xcm-absolute-location-account-derivation.html#rfc-34-xcm-absolute-location-account-derivation","stale/0034-xcm-absolute-location-account-derivation.html#summary","stale/0034-xcm-absolute-location-account-derivation.html#motivation","stale/0034-xcm-absolute-location-account-derivation.html#stakeholders","stale/0034-xcm-absolute-location-account-derivation.html#explanation","stale/0034-xcm-absolute-location-account-derivation.html#drawbacks","stale/0034-xcm-absolute-location-account-derivation.html#testing-security-and-privacy","stale/0034-xcm-absolute-location-account-derivation.html#performance-ergonomics-and-compatibility","stale/0034-xcm-absolute-location-account-derivation.html#performance","stale/0034-xcm-absolute-location-account-derivation.html#ergonomics","stale/0034-xcm-absolute-location-account-derivation.html#compatibility","stale/0034-xcm-absolute-location-account-derivation.html#prior-art-and-references","stale/0034-xcm-absolute-location-account-derivation.html#unresolved-questions","stale/0035-conviction-voting-delegation-modifications.html#rfc-0035-conviction-voting-delegation-modifications","stale/0035-conviction-voting-delegation-modifications.html#summary","stale/0035-conviction-voting-delegation-modifications.html#motivation","stale/0035-conviction-voting-delegation-modifications.html#stakeholders","stale/0035-conviction-voting-delegation-modifications.html#explanation","stale/0035-conviction-voting-delegation-modifications.html#drawbacks","stale/0035-conviction-voting-delegation-modifications.html#testing-security-and-privacy","stale/0035-conviction-voting-delegation-modifications.html#performance-ergonomics-and-compatibility","stale/0035-conviction-voting-delegation-modifications.html#performance","stale/0035-conviction-voting-delegation-modifications.html#ergonomics--compatibility","stale/0035-conviction-voting-delegation-modifications.html#prior-art-and-references","stale/0035-conviction-voting-delegation-modifications.html#unresolved-questions","stale/0035-conviction-voting-delegation-modifications.html#future-directions-and-related-material","stale/0044-rent-based-registration.html#rfc-0044-rent-based-registration-model","stale/0044-rent-based-registration.html#summary","stale/0044-rent-based-registration.html#motivation","stale/0044-rent-based-registration.html#requirements","stale/0044-rent-based-registration.html#stakeholders","stale/0044-rent-based-registration.html#explanation","stale/0044-rent-based-registration.html#registering-an-on-demand-parachain","stale/0044-rent-based-registration.html#on-demand-parachain-pruning","stale/0044-rent-based-registration.html#ensuring-rent-is-paid","stale/0044-rent-based-registration.html#on-demand-para-re-registration","stale/0044-rent-based-registration.html#drawbacks","stale/0044-rent-based-registration.html#testing-security-and-privacy","stale/0044-rent-based-registration.html#performance-ergonomics-and-compatibility","stale/0044-rent-based-registration.html#performance","stale/0044-rent-based-registration.html#ergonomics","stale/0044-rent-based-registration.html#compatibility","stale/0044-rent-based-registration.html#prior-art-and-references","stale/0044-rent-based-registration.html#unresolved-questions","stale/0044-rent-based-registration.html#future-directions-and-related-material","stale/0054-remove-heap-pages.html#rfc-0054-remove-the-concept-of-heap-pages-from-the-client","stale/0054-remove-heap-pages.html#summary","stale/0054-remove-heap-pages.html#motivation","stale/0054-remove-heap-pages.html#stakeholders","stale/0054-remove-heap-pages.html#explanation","stale/0054-remove-heap-pages.html#drawbacks","stale/0054-remove-heap-pages.html#testing-security-and-privacy","stale/0054-remove-heap-pages.html#performance-ergonomics-and-compatibility","stale/0054-remove-heap-pages.html#performance","stale/0054-remove-heap-pages.html#ergonomics","stale/0054-remove-heap-pages.html#compatibility","stale/0054-remove-heap-pages.html#prior-art-and-references","stale/0054-remove-heap-pages.html#unresolved-questions","stale/0054-remove-heap-pages.html#future-directions-and-related-material","stale/0070-x-track-kusamanetwork.html#rfc-0070-x-track-for--kusamanetwork","stale/0070-x-track-kusamanetwork.html#summary","stale/0070-x-track-kusamanetwork.html#motivation","stale/0070-x-track-kusamanetwork.html#stakeholders","stale/0070-x-track-kusamanetwork.html#explanation","stale/0070-x-track-kusamanetwork.html#phase-1---track-configurations","stale/0070-x-track-kusamanetwork.html#phase-2---establish-specs-for-x-post-track-referenda","stale/0070-x-track-kusamanetwork.html#phase-3---release-tooling--documentation","stale/0070-x-track-kusamanetwork.html#drawbacks","stale/0070-x-track-kusamanetwork.html#testing-security-and-privacy","stale/0070-x-track-kusamanetwork.html#performance-ergonomics-and-compatibility","stale/0070-x-track-kusamanetwork.html#performance","stale/0070-x-track-kusamanetwork.html#ergonomics","stale/0070-x-track-kusamanetwork.html#compatibility","stale/0070-x-track-kusamanetwork.html#references","stale/0070-x-track-kusamanetwork.html#unresolved-questions","stale/0073-referedum-deposit-track.html#rfc-0073-decision-deposit-referendum-track","stale/0073-referedum-deposit-track.html#summary","stale/0073-referedum-deposit-track.html#motivation","stale/0073-referedum-deposit-track.html#explanation","stale/0073-referedum-deposit-track.html#referendum-track-parameters---polkadot","stale/0073-referedum-deposit-track.html#referendum-track-parameters---kusama","stale/0073-referedum-deposit-track.html#drawbacks","stale/0073-referedum-deposit-track.html#testing-security-and-privacy","stale/0073-referedum-deposit-track.html#performance-ergonomics-and-compatibility","stale/0073-referedum-deposit-track.html#performance","stale/0073-referedum-deposit-track.html#ergonomics","stale/0073-referedum-deposit-track.html#compatibility","stale/0073-referedum-deposit-track.html#prior-art-and-references","stale/0073-referedum-deposit-track.html#unresolved-questions","stale/0074-stateful-multisig-pallet.html#rfc-0074-stateful-multisig-pallet","stale/0074-stateful-multisig-pallet.html#summary","stale/0074-stateful-multisig-pallet.html#motivation","stale/0074-stateful-multisig-pallet.html#problem","stale/0074-stateful-multisig-pallet.html#requirements","stale/0074-stateful-multisig-pallet.html#use-cases","stale/0074-stateful-multisig-pallet.html#stakeholders","stale/0074-stateful-multisig-pallet.html#explanation","stale/0074-stateful-multisig-pallet.html#state-transition-functions","stale/0074-stateful-multisig-pallet.html#storagestate","stale/0074-stateful-multisig-pallet.html#considerations--edge-cases","stale/0074-stateful-multisig-pallet.html#drawbacks","stale/0074-stateful-multisig-pallet.html#testing-security-and-privacy","stale/0074-stateful-multisig-pallet.html#performance-ergonomics-and-compatibility","stale/0074-stateful-multisig-pallet.html#performance","stale/0074-stateful-multisig-pallet.html#ergonomics","stale/0074-stateful-multisig-pallet.html#compatibility","stale/0074-stateful-multisig-pallet.html#prior-art-and-references","stale/0074-stateful-multisig-pallet.html#unresolved-questions","stale/0074-stateful-multisig-pallet.html#future-directions-and-related-material","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#rfc-0077-increase-maximum-length-of-identity-pgp-fingerprint-values-from-20-bytes","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#summary","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#motivation","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#background","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#problem","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#solution-requirements","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#stakeholders","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#explanation","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#drawbacks","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#testing-security-and-privacy","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#performance-ergonomics-and-compatibility","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#performance","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#ergonomics","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#compatibility","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#prior-art-and-references","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#unresolved-questions","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#future-directions-and-related-material","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#rfc-0088-add-slashable-locked-deposit-purchaser-reputation-and-reserved-cores-for-on-chain-identities-to-broker-pallet","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#summary","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#motivation","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#background","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#problem","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#solution-requirements","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#stakeholders","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#drawbacks","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#testing-security-and-privacy","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance-ergonomics-and-compatibility","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance-1","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#ergonomics","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#compatibility","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#prior-art-and-references","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#prior-art","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#unresolved-questions","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#future-directions-and-related-material","stale/0089-flexible-inflation.html#rfc-0089-flexible-inflation","stale/0089-flexible-inflation.html#summary","stale/0089-flexible-inflation.html#motivation","stale/0089-flexible-inflation.html#stakeholders","stale/0089-flexible-inflation.html#explanation","stale/0089-flexible-inflation.html#existing-order","stale/0089-flexible-inflation.html#new-order","stale/0089-flexible-inflation.html#proposed-implementation","stale/0089-flexible-inflation.html#drawbacks","stale/0089-flexible-inflation.html#testing-security-and-privacy","stale/0089-flexible-inflation.html#performance-ergonomics-and-compatibility","stale/0089-flexible-inflation.html#prior-art-and-references","stale/0089-flexible-inflation.html#unresolved-questions","stale/0089-flexible-inflation.html#future-directions-and-related-material","stale/00xx-secondary-marketplace-for-regions.html#rfc-0001-secondary-market-for-regions","stale/00xx-secondary-marketplace-for-regions.html#summary","stale/00xx-secondary-marketplace-for-regions.html#motivation","stale/00xx-secondary-marketplace-for-regions.html#stakeholders","stale/00xx-secondary-marketplace-for-regions.html#explanation","stale/00xx-secondary-marketplace-for-regions.html#drawbacks","stale/00xx-secondary-marketplace-for-regions.html#testing-security-and-privacy","stale/00xx-secondary-marketplace-for-regions.html#testing","stale/00xx-secondary-marketplace-for-regions.html#security","stale/00xx-secondary-marketplace-for-regions.html#privacy","stale/00xx-secondary-marketplace-for-regions.html#performance-ergonomics-and-compatibility","stale/00xx-secondary-marketplace-for-regions.html#performance","stale/00xx-secondary-marketplace-for-regions.html#ergonomics","stale/00xx-secondary-marketplace-for-regions.html#compatibility","stale/00xx-secondary-marketplace-for-regions.html#prior-art-and-references","stale/00xx-secondary-marketplace-for-regions.html#unresolved-questions","stale/00xx-secondary-marketplace-for-regions.html#future-directions-and-related-material","stale/00xx-smart-contracts-coretime-chain.html#rfc-0002-smart-contracts-on-the-coretime-chain","stale/00xx-smart-contracts-coretime-chain.html#summary","stale/00xx-smart-contracts-coretime-chain.html#motivation","stale/00xx-smart-contracts-coretime-chain.html#stakeholders","stale/00xx-smart-contracts-coretime-chain.html#explanation","stale/00xx-smart-contracts-coretime-chain.html#drawbacks","stale/00xx-smart-contracts-coretime-chain.html#testing-security-and-privacy","stale/00xx-smart-contracts-coretime-chain.html#testing","stale/00xx-smart-contracts-coretime-chain.html#security","stale/00xx-smart-contracts-coretime-chain.html#privacy","stale/00xx-smart-contracts-coretime-chain.html#performance-ergonomics-and-compatibility","stale/00xx-smart-contracts-coretime-chain.html#performance","stale/00xx-smart-contracts-coretime-chain.html#ergonomics","stale/00xx-smart-contracts-coretime-chain.html#compatibility","stale/00xx-smart-contracts-coretime-chain.html#prior-art-and-references","stale/00xx-smart-contracts-coretime-chain.html#unresolved-questions","stale/00xx-smart-contracts-coretime-chain.html#future-directions-and-related-material","stale/0106-xcm-remove-fees-mode.html#rfc-0106-remove-xcm-fees-mode","stale/0106-xcm-remove-fees-mode.html#summary","stale/0106-xcm-remove-fees-mode.html#motivation","stale/0106-xcm-remove-fees-mode.html#stakeholders","stale/0106-xcm-remove-fees-mode.html#explanation","stale/0106-xcm-remove-fees-mode.html#drawbacks","stale/0106-xcm-remove-fees-mode.html#testing-security-and-privacy","stale/0106-xcm-remove-fees-mode.html#performance-ergonomics-and-compatibility","stale/0106-xcm-remove-fees-mode.html#performance","stale/0106-xcm-remove-fees-mode.html#ergonomics","stale/0106-xcm-remove-fees-mode.html#compatibility","stale/0106-xcm-remove-fees-mode.html#prior-art-and-references","stale/0106-xcm-remove-fees-mode.html#unresolved-questions","stale/0106-xcm-remove-fees-mode.html#future-directions-and-related-material","stale/0112-compress-state-response-message-in-state-sync.html#rfc-0112-compress-the-state-response-message-in-state-sync","stale/0112-compress-state-response-message-in-state-sync.html#summary","stale/0112-compress-state-response-message-in-state-sync.html#motivation","stale/0112-compress-state-response-message-in-state-sync.html#stakeholders","stale/0112-compress-state-response-message-in-state-sync.html#explanation","stale/0112-compress-state-response-message-in-state-sync.html#drawbacks","stale/0112-compress-state-response-message-in-state-sync.html#testing-security-and-privacy","stale/0112-compress-state-response-message-in-state-sync.html#performance-ergonomics-and-compatibility","stale/0112-compress-state-response-message-in-state-sync.html#performance","stale/0112-compress-state-response-message-in-state-sync.html#ergonomics","stale/0112-compress-state-response-message-in-state-sync.html#compatibility","stale/0112-compress-state-response-message-in-state-sync.html#prior-art-and-references","stale/0112-compress-state-response-message-in-state-sync.html#unresolved-questions","stale/0112-compress-state-response-message-in-state-sync.html#future-directions-and-related-material","stale/TODO-stale-nomination-reward-curve.html#rfc-todo-stale-nomination-reward-curve","stale/TODO-stale-nomination-reward-curve.html#summary","stale/TODO-stale-nomination-reward-curve.html#motivation","stale/TODO-stale-nomination-reward-curve.html#stakeholders","stale/TODO-stale-nomination-reward-curve.html#explanation","stale/TODO-stale-nomination-reward-curve.html#drawbacks","stale/TODO-stale-nomination-reward-curve.html#testing-security-and-privacy","stale/TODO-stale-nomination-reward-curve.html#performance-ergonomics-and-compatibility","stale/TODO-stale-nomination-reward-curve.html#performance","stale/TODO-stale-nomination-reward-curve.html#ergonomics","stale/TODO-stale-nomination-reward-curve.html#compatibility","stale/TODO-stale-nomination-reward-curve.html#prior-art-and-references","stale/TODO-stale-nomination-reward-curve.html#unresolved-questions","stale/TODO-stale-nomination-reward-curve.html#future-directions-and-related-material"],"index":{"documentStore":{"docInfo":{"0":{"body":16,"breadcrumbs":2,"title":1},"1":{"body":52,"breadcrumbs":10,"title":5},"10":{"body":0,"breadcrumbs":8,"title":3},"100":{"body":10,"breadcrumbs":13,"title":1},"1000":{"body":1,"breadcrumbs":10,"title":2},"1001":{"body":1,"breadcrumbs":12,"title":4},"1002":{"body":48,"breadcrumbs":12,"title":6},"1003":{"body":34,"breadcrumbs":7,"title":1},"1004":{"body":101,"breadcrumbs":7,"title":1},"1005":{"body":4,"breadcrumbs":7,"title":1},"1006":{"body":22,"breadcrumbs":7,"title":1},"1007":{"body":16,"breadcrumbs":7,"title":1},"1008":{"body":22,"breadcrumbs":9,"title":3},"1009":{"body":6,"breadcrumbs":9,"title":3},"101":{"body":0,"breadcrumbs":15,"title":3},"1010":{"body":8,"breadcrumbs":7,"title":1},"1011":{"body":11,"breadcrumbs":7,"title":1},"1012":{"body":13,"breadcrumbs":7,"title":1},"1013":{"body":8,"breadcrumbs":9,"title":3},"1014":{"body":19,"breadcrumbs":8,"title":2},"1015":{"body":17,"breadcrumbs":10,"title":4},"102":{"body":1,"breadcrumbs":13,"title":1},"103":{"body":17,"breadcrumbs":13,"title":1},"104":{"body":7,"breadcrumbs":13,"title":1},"105":{"body":16,"breadcrumbs":15,"title":3},"106":{"body":53,"breadcrumbs":8,"title":4},"107":{"body":29,"breadcrumbs":5,"title":1},"108":{"body":110,"breadcrumbs":5,"title":1},"109":{"body":8,"breadcrumbs":5,"title":1},"11":{"body":2,"breadcrumbs":6,"title":1},"110":{"body":0,"breadcrumbs":5,"title":1},"111":{"body":107,"breadcrumbs":5,"title":1},"112":{"body":116,"breadcrumbs":6,"title":2},"113":{"body":72,"breadcrumbs":6,"title":2},"114":{"body":32,"breadcrumbs":5,"title":1},"115":{"body":19,"breadcrumbs":7,"title":3},"116":{"body":0,"breadcrumbs":7,"title":3},"117":{"body":4,"breadcrumbs":5,"title":1},"118":{"body":12,"breadcrumbs":5,"title":1},"119":{"body":5,"breadcrumbs":5,"title":1},"12":{"body":25,"breadcrumbs":6,"title":1},"120":{"body":14,"breadcrumbs":7,"title":3},"121":{"body":96,"breadcrumbs":6,"title":2},"122":{"body":53,"breadcrumbs":12,"title":6},"123":{"body":22,"breadcrumbs":7,"title":1},"124":{"body":124,"breadcrumbs":7,"title":1},"125":{"body":38,"breadcrumbs":7,"title":1},"126":{"body":301,"breadcrumbs":7,"title":1},"127":{"body":40,"breadcrumbs":7,"title":1},"128":{"body":30,"breadcrumbs":9,"title":3},"129":{"body":0,"breadcrumbs":9,"title":3},"13":{"body":6,"breadcrumbs":6,"title":1},"130":{"body":16,"breadcrumbs":7,"title":1},"131":{"body":18,"breadcrumbs":7,"title":1},"132":{"body":33,"breadcrumbs":7,"title":1},"133":{"body":15,"breadcrumbs":9,"title":3},"134":{"body":13,"breadcrumbs":8,"title":2},"135":{"body":6,"breadcrumbs":10,"title":4},"136":{"body":53,"breadcrumbs":10,"title":5},"137":{"body":37,"breadcrumbs":6,"title":1},"138":{"body":56,"breadcrumbs":6,"title":1},"139":{"body":17,"breadcrumbs":6,"title":1},"14":{"body":4,"breadcrumbs":8,"title":3},"140":{"body":88,"breadcrumbs":6,"title":1},"141":{"body":32,"breadcrumbs":6,"title":1},"142":{"body":48,"breadcrumbs":8,"title":3},"143":{"body":0,"breadcrumbs":8,"title":3},"144":{"body":31,"breadcrumbs":6,"title":1},"145":{"body":23,"breadcrumbs":6,"title":1},"146":{"body":25,"breadcrumbs":6,"title":1},"147":{"body":33,"breadcrumbs":8,"title":3},"148":{"body":35,"breadcrumbs":7,"title":2},"149":{"body":30,"breadcrumbs":9,"title":4},"15":{"body":10,"breadcrumbs":7,"title":2},"150":{"body":49,"breadcrumbs":18,"title":9},"151":{"body":132,"breadcrumbs":10,"title":1},"152":{"body":72,"breadcrumbs":10,"title":1},"153":{"body":8,"breadcrumbs":10,"title":1},"154":{"body":126,"breadcrumbs":10,"title":1},"155":{"body":107,"breadcrumbs":10,"title":1},"156":{"body":12,"breadcrumbs":12,"title":3},"157":{"body":0,"breadcrumbs":12,"title":3},"158":{"body":14,"breadcrumbs":10,"title":1},"159":{"body":14,"breadcrumbs":10,"title":1},"16":{"body":37,"breadcrumbs":9,"title":4},"160":{"body":37,"breadcrumbs":10,"title":1},"161":{"body":10,"breadcrumbs":12,"title":3},"162":{"body":1,"breadcrumbs":11,"title":2},"163":{"body":38,"breadcrumbs":13,"title":4},"164":{"body":60,"breadcrumbs":10,"title":5},"165":{"body":12,"breadcrumbs":6,"title":1},"166":{"body":47,"breadcrumbs":6,"title":1},"167":{"body":6,"breadcrumbs":6,"title":1},"168":{"body":0,"breadcrumbs":6,"title":1},"169":{"body":58,"breadcrumbs":8,"title":3},"17":{"body":67,"breadcrumbs":12,"title":6},"170":{"body":115,"breadcrumbs":9,"title":4},"171":{"body":113,"breadcrumbs":9,"title":4},"172":{"body":34,"breadcrumbs":9,"title":4},"173":{"body":19,"breadcrumbs":6,"title":1},"174":{"body":4,"breadcrumbs":8,"title":3},"175":{"body":37,"breadcrumbs":8,"title":3},"176":{"body":2,"breadcrumbs":6,"title":1},"177":{"body":28,"breadcrumbs":6,"title":1},"178":{"body":25,"breadcrumbs":6,"title":1},"179":{"body":5,"breadcrumbs":8,"title":3},"18":{"body":78,"breadcrumbs":7,"title":1},"180":{"body":44,"breadcrumbs":7,"title":2},"181":{"body":13,"breadcrumbs":9,"title":4},"182":{"body":49,"breadcrumbs":14,"title":7},"183":{"body":25,"breadcrumbs":8,"title":1},"184":{"body":111,"breadcrumbs":8,"title":1},"185":{"body":27,"breadcrumbs":8,"title":1},"186":{"body":50,"breadcrumbs":8,"title":1},"187":{"body":37,"breadcrumbs":8,"title":1},"188":{"body":26,"breadcrumbs":10,"title":3},"189":{"body":0,"breadcrumbs":10,"title":3},"19":{"body":90,"breadcrumbs":7,"title":1},"190":{"body":15,"breadcrumbs":8,"title":1},"191":{"body":45,"breadcrumbs":9,"title":2},"192":{"body":1,"breadcrumbs":10,"title":3},"193":{"body":24,"breadcrumbs":9,"title":2},"194":{"body":30,"breadcrumbs":11,"title":4},"195":{"body":65,"breadcrumbs":8,"title":4},"196":{"body":50,"breadcrumbs":5,"title":1},"197":{"body":0,"breadcrumbs":5,"title":1},"198":{"body":124,"breadcrumbs":6,"title":2},"199":{"body":153,"breadcrumbs":5,"title":1},"2":{"body":18,"breadcrumbs":6,"title":1},"20":{"body":4,"breadcrumbs":7,"title":1},"200":{"body":90,"breadcrumbs":5,"title":1},"201":{"body":54,"breadcrumbs":5,"title":1},"202":{"body":0,"breadcrumbs":5,"title":1},"203":{"body":438,"breadcrumbs":5,"title":1},"204":{"body":562,"breadcrumbs":5,"title":1},"205":{"body":630,"breadcrumbs":8,"title":4},"206":{"body":103,"breadcrumbs":8,"title":4},"207":{"body":410,"breadcrumbs":6,"title":2},"208":{"body":905,"breadcrumbs":6,"title":2},"209":{"body":52,"breadcrumbs":5,"title":1},"21":{"body":40,"breadcrumbs":7,"title":1},"210":{"body":33,"breadcrumbs":7,"title":3},"211":{"body":40,"breadcrumbs":7,"title":3},"212":{"body":35,"breadcrumbs":8,"title":4},"213":{"body":49,"breadcrumbs":7,"title":3},"214":{"body":34,"breadcrumbs":7,"title":3},"215":{"body":55,"breadcrumbs":8,"title":4},"216":{"body":43,"breadcrumbs":5,"title":1},"217":{"body":37,"breadcrumbs":5,"title":1},"218":{"body":73,"breadcrumbs":5,"title":1},"219":{"body":21,"breadcrumbs":5,"title":1},"22":{"body":175,"breadcrumbs":9,"title":3},"220":{"body":39,"breadcrumbs":5,"title":1},"221":{"body":235,"breadcrumbs":7,"title":3},"222":{"body":86,"breadcrumbs":7,"title":3},"223":{"body":32,"breadcrumbs":7,"title":3},"224":{"body":2,"breadcrumbs":7,"title":3},"225":{"body":11,"breadcrumbs":7,"title":3},"226":{"body":20,"breadcrumbs":8,"title":4},"227":{"body":2,"breadcrumbs":7,"title":3},"228":{"body":1,"breadcrumbs":7,"title":3},"229":{"body":53,"breadcrumbs":10,"title":5},"23":{"body":42,"breadcrumbs":8,"title":2},"230":{"body":40,"breadcrumbs":6,"title":1},"231":{"body":203,"breadcrumbs":6,"title":1},"232":{"body":34,"breadcrumbs":6,"title":1},"233":{"body":8,"breadcrumbs":6,"title":1},"234":{"body":176,"breadcrumbs":6,"title":1},"235":{"body":18,"breadcrumbs":7,"title":2},"236":{"body":11,"breadcrumbs":6,"title":1},"237":{"body":25,"breadcrumbs":8,"title":3},"238":{"body":14,"breadcrumbs":8,"title":3},"239":{"body":21,"breadcrumbs":6,"title":1},"24":{"body":293,"breadcrumbs":8,"title":2},"240":{"body":16,"breadcrumbs":6,"title":1},"241":{"body":8,"breadcrumbs":6,"title":1},"242":{"body":0,"breadcrumbs":8,"title":3},"243":{"body":16,"breadcrumbs":7,"title":2},"244":{"body":21,"breadcrumbs":8,"title":3},"245":{"body":2,"breadcrumbs":7,"title":2},"246":{"body":13,"breadcrumbs":9,"title":4},"247":{"body":57,"breadcrumbs":16,"title":8},"248":{"body":29,"breadcrumbs":9,"title":1},"249":{"body":185,"breadcrumbs":9,"title":1},"25":{"body":83,"breadcrumbs":9,"title":3},"250":{"body":15,"breadcrumbs":9,"title":1},"251":{"body":60,"breadcrumbs":9,"title":1},"252":{"body":110,"breadcrumbs":11,"title":3},"253":{"body":153,"breadcrumbs":11,"title":3},"254":{"body":96,"breadcrumbs":9,"title":1},"255":{"body":144,"breadcrumbs":11,"title":3},"256":{"body":0,"breadcrumbs":11,"title":3},"257":{"body":110,"breadcrumbs":9,"title":1},"258":{"body":1,"breadcrumbs":9,"title":1},"259":{"body":1,"breadcrumbs":9,"title":1},"26":{"body":83,"breadcrumbs":10,"title":4},"260":{"body":1,"breadcrumbs":11,"title":3},"261":{"body":21,"breadcrumbs":10,"title":2},"262":{"body":11,"breadcrumbs":12,"title":4},"263":{"body":23,"breadcrumbs":10,"title":5},"264":{"body":36,"breadcrumbs":6,"title":1},"265":{"body":21,"breadcrumbs":6,"title":1},"266":{"body":4,"breadcrumbs":6,"title":1},"267":{"body":290,"breadcrumbs":6,"title":1},"268":{"body":44,"breadcrumbs":14,"title":7},"269":{"body":43,"breadcrumbs":8,"title":1},"27":{"body":0,"breadcrumbs":7,"title":1},"270":{"body":81,"breadcrumbs":8,"title":1},"271":{"body":10,"breadcrumbs":8,"title":1},"272":{"body":101,"breadcrumbs":8,"title":1},"273":{"body":70,"breadcrumbs":9,"title":2},"274":{"body":16,"breadcrumbs":8,"title":1},"275":{"body":1,"breadcrumbs":10,"title":3},"276":{"body":39,"breadcrumbs":10,"title":3},"277":{"body":7,"breadcrumbs":10,"title":3},"278":{"body":2,"breadcrumbs":9,"title":2},"279":{"body":51,"breadcrumbs":14,"title":7},"28":{"body":46,"breadcrumbs":8,"title":2},"280":{"body":15,"breadcrumbs":8,"title":1},"281":{"body":50,"breadcrumbs":8,"title":1},"282":{"body":27,"breadcrumbs":8,"title":1},"283":{"body":0,"breadcrumbs":8,"title":1},"284":{"body":117,"breadcrumbs":8,"title":1},"285":{"body":14,"breadcrumbs":8,"title":1},"286":{"body":15,"breadcrumbs":10,"title":3},"287":{"body":0,"breadcrumbs":10,"title":3},"288":{"body":19,"breadcrumbs":8,"title":1},"289":{"body":17,"breadcrumbs":8,"title":1},"29":{"body":32,"breadcrumbs":9,"title":3},"290":{"body":16,"breadcrumbs":8,"title":1},"291":{"body":26,"breadcrumbs":10,"title":3},"292":{"body":30,"breadcrumbs":9,"title":2},"293":{"body":35,"breadcrumbs":11,"title":4},"294":{"body":48,"breadcrumbs":12,"title":6},"295":{"body":35,"breadcrumbs":7,"title":1},"296":{"body":152,"breadcrumbs":7,"title":1},"297":{"body":32,"breadcrumbs":7,"title":1},"298":{"body":4,"breadcrumbs":7,"title":1},"299":{"body":0,"breadcrumbs":7,"title":1},"3":{"body":243,"breadcrumbs":6,"title":1},"30":{"body":93,"breadcrumbs":9,"title":3},"300":{"body":92,"breadcrumbs":8,"title":2},"301":{"body":52,"breadcrumbs":8,"title":2},"302":{"body":32,"breadcrumbs":7,"title":1},"303":{"body":111,"breadcrumbs":7,"title":1},"304":{"body":19,"breadcrumbs":9,"title":3},"305":{"body":4,"breadcrumbs":7,"title":1},"306":{"body":8,"breadcrumbs":7,"title":1},"307":{"body":5,"breadcrumbs":7,"title":1},"308":{"body":26,"breadcrumbs":9,"title":3},"309":{"body":2,"breadcrumbs":8,"title":2},"31":{"body":0,"breadcrumbs":9,"title":3},"310":{"body":34,"breadcrumbs":10,"title":4},"311":{"body":48,"breadcrumbs":10,"title":5},"312":{"body":20,"breadcrumbs":6,"title":1},"313":{"body":30,"breadcrumbs":6,"title":1},"314":{"body":52,"breadcrumbs":6,"title":1},"315":{"body":73,"breadcrumbs":6,"title":1},"316":{"body":38,"breadcrumbs":6,"title":1},"317":{"body":7,"breadcrumbs":8,"title":3},"318":{"body":1,"breadcrumbs":8,"title":3},"319":{"body":4,"breadcrumbs":8,"title":3},"32":{"body":7,"breadcrumbs":7,"title":1},"320":{"body":2,"breadcrumbs":7,"title":2},"321":{"body":4,"breadcrumbs":9,"title":4},"322":{"body":168,"breadcrumbs":10,"title":5},"323":{"body":38,"breadcrumbs":6,"title":1},"324":{"body":34,"breadcrumbs":7,"title":2},"325":{"body":22,"breadcrumbs":8,"title":3},"326":{"body":23,"breadcrumbs":9,"title":4},"327":{"body":9,"breadcrumbs":7,"title":2},"328":{"body":10,"breadcrumbs":9,"title":4},"329":{"body":9,"breadcrumbs":9,"title":4},"33":{"body":32,"breadcrumbs":7,"title":1},"330":{"body":9,"breadcrumbs":7,"title":2},"331":{"body":21,"breadcrumbs":9,"title":4},"332":{"body":67,"breadcrumbs":8,"title":3},"333":{"body":99,"breadcrumbs":8,"title":3},"334":{"body":11,"breadcrumbs":10,"title":5},"335":{"body":36,"breadcrumbs":8,"title":3},"336":{"body":19,"breadcrumbs":9,"title":4},"337":{"body":17,"breadcrumbs":9,"title":4},"338":{"body":18,"breadcrumbs":9,"title":4},"339":{"body":19,"breadcrumbs":9,"title":4},"34":{"body":9,"breadcrumbs":7,"title":1},"340":{"body":68,"breadcrumbs":10,"title":5},"341":{"body":167,"breadcrumbs":9,"title":4},"342":{"body":98,"breadcrumbs":8,"title":3},"343":{"body":117,"breadcrumbs":9,"title":4},"344":{"body":89,"breadcrumbs":8,"title":3},"345":{"body":130,"breadcrumbs":9,"title":4},"346":{"body":372,"breadcrumbs":9,"title":4},"347":{"body":171,"breadcrumbs":9,"title":4},"348":{"body":100,"breadcrumbs":9,"title":4},"349":{"body":262,"breadcrumbs":8,"title":3},"35":{"body":69,"breadcrumbs":9,"title":3},"350":{"body":117,"breadcrumbs":9,"title":4},"351":{"body":43,"breadcrumbs":8,"title":3},"352":{"body":23,"breadcrumbs":8,"title":3},"353":{"body":1,"breadcrumbs":7,"title":2},"354":{"body":16,"breadcrumbs":9,"title":4},"355":{"body":0,"breadcrumbs":9,"title":4},"356":{"body":31,"breadcrumbs":7,"title":2},"357":{"body":2,"breadcrumbs":7,"title":2},"358":{"body":23,"breadcrumbs":7,"title":2},"359":{"body":28,"breadcrumbs":9,"title":4},"36":{"body":0,"breadcrumbs":8,"title":2},"360":{"body":1,"breadcrumbs":8,"title":3},"361":{"body":14,"breadcrumbs":10,"title":5},"362":{"body":43,"breadcrumbs":9,"title":4},"363":{"body":19,"breadcrumbs":8,"title":3},"364":{"body":30,"breadcrumbs":9,"title":4},"365":{"body":26,"breadcrumbs":9,"title":4},"366":{"body":54,"breadcrumbs":8,"title":4},"367":{"body":22,"breadcrumbs":5,"title":1},"368":{"body":85,"breadcrumbs":5,"title":1},"369":{"body":16,"breadcrumbs":5,"title":1},"37":{"body":10,"breadcrumbs":10,"title":4},"370":{"body":42,"breadcrumbs":5,"title":1},"371":{"body":62,"breadcrumbs":5,"title":1},"372":{"body":62,"breadcrumbs":5,"title":1},"373":{"body":127,"breadcrumbs":6,"title":2},"374":{"body":101,"breadcrumbs":6,"title":2},"375":{"body":324,"breadcrumbs":5,"title":1},"376":{"body":117,"breadcrumbs":5,"title":1},"377":{"body":12,"breadcrumbs":5,"title":1},"378":{"body":13,"breadcrumbs":7,"title":3},"379":{"body":6,"breadcrumbs":7,"title":3},"38":{"body":126,"breadcrumbs":16,"title":8},"380":{"body":12,"breadcrumbs":5,"title":1},"381":{"body":35,"breadcrumbs":5,"title":1},"382":{"body":17,"breadcrumbs":5,"title":1},"383":{"body":7,"breadcrumbs":7,"title":3},"384":{"body":14,"breadcrumbs":6,"title":2},"385":{"body":23,"breadcrumbs":8,"title":4},"386":{"body":49,"breadcrumbs":16,"title":8},"387":{"body":33,"breadcrumbs":9,"title":1},"388":{"body":94,"breadcrumbs":9,"title":1},"389":{"body":6,"breadcrumbs":9,"title":1},"39":{"body":119,"breadcrumbs":9,"title":1},"390":{"body":97,"breadcrumbs":9,"title":1},"391":{"body":11,"breadcrumbs":9,"title":1},"392":{"body":4,"breadcrumbs":11,"title":3},"393":{"body":8,"breadcrumbs":11,"title":3},"394":{"body":4,"breadcrumbs":9,"title":1},"395":{"body":3,"breadcrumbs":9,"title":1},"396":{"body":3,"breadcrumbs":9,"title":1},"397":{"body":12,"breadcrumbs":11,"title":3},"398":{"body":4,"breadcrumbs":10,"title":2},"399":{"body":9,"breadcrumbs":12,"title":4},"4":{"body":8,"breadcrumbs":6,"title":1},"40":{"body":72,"breadcrumbs":9,"title":1},"400":{"body":42,"breadcrumbs":20,"title":10},"401":{"body":28,"breadcrumbs":11,"title":1},"402":{"body":121,"breadcrumbs":11,"title":1},"403":{"body":15,"breadcrumbs":11,"title":1},"404":{"body":70,"breadcrumbs":11,"title":1},"405":{"body":0,"breadcrumbs":13,"title":3},"406":{"body":26,"breadcrumbs":11,"title":1},"407":{"body":26,"breadcrumbs":11,"title":1},"408":{"body":7,"breadcrumbs":11,"title":1},"409":{"body":19,"breadcrumbs":13,"title":3},"41":{"body":17,"breadcrumbs":9,"title":1},"410":{"body":78,"breadcrumbs":14,"title":7},"411":{"body":37,"breadcrumbs":8,"title":1},"412":{"body":101,"breadcrumbs":8,"title":1},"413":{"body":8,"breadcrumbs":8,"title":1},"414":{"body":67,"breadcrumbs":8,"title":1},"415":{"body":98,"breadcrumbs":8,"title":1},"416":{"body":111,"breadcrumbs":13,"title":6},"417":{"body":112,"breadcrumbs":11,"title":4},"418":{"body":154,"breadcrumbs":8,"title":1},"419":{"body":0,"breadcrumbs":10,"title":3},"42":{"body":27,"breadcrumbs":9,"title":1},"420":{"body":19,"breadcrumbs":9,"title":2},"421":{"body":0,"breadcrumbs":10,"title":3},"422":{"body":35,"breadcrumbs":8,"title":1},"423":{"body":20,"breadcrumbs":8,"title":1},"424":{"body":7,"breadcrumbs":8,"title":1},"425":{"body":10,"breadcrumbs":9,"title":2},"426":{"body":26,"breadcrumbs":8,"title":1},"427":{"body":77,"breadcrumbs":12,"title":5},"428":{"body":60,"breadcrumbs":11,"title":4},"429":{"body":87,"breadcrumbs":11,"title":4},"43":{"body":0,"breadcrumbs":11,"title":3},"430":{"body":67,"breadcrumbs":12,"title":6},"431":{"body":20,"breadcrumbs":7,"title":1},"432":{"body":66,"breadcrumbs":7,"title":1},"433":{"body":5,"breadcrumbs":7,"title":1},"434":{"body":0,"breadcrumbs":7,"title":1},"435":{"body":77,"breadcrumbs":9,"title":3},"436":{"body":94,"breadcrumbs":9,"title":3},"437":{"body":82,"breadcrumbs":10,"title":4},"438":{"body":99,"breadcrumbs":9,"title":3},"439":{"body":261,"breadcrumbs":8,"title":2},"44":{"body":123,"breadcrumbs":9,"title":1},"440":{"body":172,"breadcrumbs":8,"title":2},"441":{"body":59,"breadcrumbs":7,"title":1},"442":{"body":11,"breadcrumbs":9,"title":3},"443":{"body":0,"breadcrumbs":9,"title":3},"444":{"body":45,"breadcrumbs":7,"title":1},"445":{"body":1,"breadcrumbs":7,"title":1},"446":{"body":19,"breadcrumbs":7,"title":1},"447":{"body":6,"breadcrumbs":9,"title":3},"448":{"body":1,"breadcrumbs":8,"title":2},"449":{"body":13,"breadcrumbs":10,"title":4},"45":{"body":224,"breadcrumbs":9,"title":1},"450":{"body":217,"breadcrumbs":7,"title":1},"451":{"body":51,"breadcrumbs":12,"title":6},"452":{"body":82,"breadcrumbs":7,"title":1},"453":{"body":73,"breadcrumbs":7,"title":1},"454":{"body":8,"breadcrumbs":7,"title":1},"455":{"body":136,"breadcrumbs":7,"title":1},"456":{"body":21,"breadcrumbs":7,"title":1},"457":{"body":17,"breadcrumbs":9,"title":3},"458":{"body":0,"breadcrumbs":9,"title":3},"459":{"body":39,"breadcrumbs":7,"title":1},"46":{"body":199,"breadcrumbs":13,"title":5},"460":{"body":8,"breadcrumbs":7,"title":1},"461":{"body":46,"breadcrumbs":7,"title":1},"462":{"body":1,"breadcrumbs":9,"title":3},"463":{"body":1,"breadcrumbs":8,"title":2},"464":{"body":3,"breadcrumbs":10,"title":4},"465":{"body":48,"breadcrumbs":8,"title":4},"466":{"body":16,"breadcrumbs":5,"title":1},"467":{"body":70,"breadcrumbs":5,"title":1},"468":{"body":4,"breadcrumbs":5,"title":1},"469":{"body":78,"breadcrumbs":5,"title":1},"47":{"body":211,"breadcrumbs":9,"title":1},"470":{"body":92,"breadcrumbs":6,"title":2},"471":{"body":67,"breadcrumbs":5,"title":1},"472":{"body":12,"breadcrumbs":5,"title":1},"473":{"body":13,"breadcrumbs":5,"title":1},"474":{"body":1,"breadcrumbs":7,"title":3},"475":{"body":0,"breadcrumbs":7,"title":3},"476":{"body":1,"breadcrumbs":5,"title":1},"477":{"body":1,"breadcrumbs":5,"title":1},"478":{"body":1,"breadcrumbs":5,"title":1},"479":{"body":12,"breadcrumbs":7,"title":3},"48":{"body":53,"breadcrumbs":9,"title":1},"480":{"body":2,"breadcrumbs":6,"title":2},"481":{"body":51,"breadcrumbs":14,"title":7},"482":{"body":44,"breadcrumbs":8,"title":1},"483":{"body":100,"breadcrumbs":8,"title":1},"484":{"body":3,"breadcrumbs":8,"title":1},"485":{"body":121,"breadcrumbs":8,"title":1},"486":{"body":33,"breadcrumbs":8,"title":1},"487":{"body":1,"breadcrumbs":10,"title":3},"488":{"body":0,"breadcrumbs":10,"title":3},"489":{"body":1,"breadcrumbs":8,"title":1},"49":{"body":68,"breadcrumbs":9,"title":1},"490":{"body":1,"breadcrumbs":8,"title":1},"491":{"body":19,"breadcrumbs":8,"title":1},"492":{"body":1,"breadcrumbs":10,"title":3},"493":{"body":1,"breadcrumbs":9,"title":2},"494":{"body":4,"breadcrumbs":11,"title":4},"495":{"body":60,"breadcrumbs":16,"title":8},"496":{"body":32,"breadcrumbs":9,"title":1},"497":{"body":98,"breadcrumbs":9,"title":1},"498":{"body":9,"breadcrumbs":9,"title":1},"499":{"body":23,"breadcrumbs":9,"title":1},"5":{"body":124,"breadcrumbs":6,"title":1},"50":{"body":57,"breadcrumbs":11,"title":3},"500":{"body":232,"breadcrumbs":9,"title":1},"501":{"body":125,"breadcrumbs":11,"title":3},"502":{"body":44,"breadcrumbs":10,"title":2},"503":{"body":65,"breadcrumbs":11,"title":3},"504":{"body":2,"breadcrumbs":9,"title":1},"505":{"body":94,"breadcrumbs":11,"title":3},"506":{"body":0,"breadcrumbs":11,"title":3},"507":{"body":91,"breadcrumbs":9,"title":1},"508":{"body":1,"breadcrumbs":9,"title":1},"509":{"body":1,"breadcrumbs":9,"title":1},"51":{"body":79,"breadcrumbs":11,"title":3},"510":{"body":1,"breadcrumbs":11,"title":3},"511":{"body":21,"breadcrumbs":10,"title":2},"512":{"body":74,"breadcrumbs":12,"title":4},"513":{"body":72,"breadcrumbs":8,"title":4},"514":{"body":165,"breadcrumbs":5,"title":1},"515":{"body":189,"breadcrumbs":5,"title":1},"516":{"body":86,"breadcrumbs":5,"title":1},"517":{"body":69,"breadcrumbs":7,"title":3},"518":{"body":29,"breadcrumbs":5,"title":1},"519":{"body":106,"breadcrumbs":5,"title":1},"52":{"body":50,"breadcrumbs":9,"title":1},"520":{"body":143,"breadcrumbs":6,"title":2},"521":{"body":222,"breadcrumbs":6,"title":2},"522":{"body":401,"breadcrumbs":6,"title":2},"523":{"body":87,"breadcrumbs":7,"title":3},"524":{"body":152,"breadcrumbs":6,"title":2},"525":{"body":196,"breadcrumbs":8,"title":4},"526":{"body":130,"breadcrumbs":6,"title":2},"527":{"body":6,"breadcrumbs":5,"title":1},"528":{"body":92,"breadcrumbs":7,"title":3},"529":{"body":0,"breadcrumbs":7,"title":3},"53":{"body":40,"breadcrumbs":11,"title":3},"530":{"body":25,"breadcrumbs":5,"title":1},"531":{"body":28,"breadcrumbs":6,"title":2},"532":{"body":48,"breadcrumbs":7,"title":3},"533":{"body":1,"breadcrumbs":6,"title":2},"534":{"body":68,"breadcrumbs":8,"title":4},"535":{"body":48,"breadcrumbs":12,"title":6},"536":{"body":11,"breadcrumbs":7,"title":1},"537":{"body":166,"breadcrumbs":7,"title":1},"538":{"body":6,"breadcrumbs":7,"title":1},"539":{"body":85,"breadcrumbs":7,"title":1},"54":{"body":92,"breadcrumbs":12,"title":4},"540":{"body":18,"breadcrumbs":7,"title":1},"541":{"body":4,"breadcrumbs":9,"title":3},"542":{"body":15,"breadcrumbs":9,"title":3},"543":{"body":2,"breadcrumbs":7,"title":1},"544":{"body":13,"breadcrumbs":7,"title":1},"545":{"body":16,"breadcrumbs":7,"title":1},"546":{"body":9,"breadcrumbs":9,"title":3},"547":{"body":1,"breadcrumbs":8,"title":2},"548":{"body":13,"breadcrumbs":10,"title":4},"549":{"body":51,"breadcrumbs":16,"title":8},"55":{"body":48,"breadcrumbs":11,"title":3},"550":{"body":19,"breadcrumbs":9,"title":1},"551":{"body":85,"breadcrumbs":9,"title":1},"552":{"body":3,"breadcrumbs":9,"title":1},"553":{"body":177,"breadcrumbs":9,"title":1},"554":{"body":36,"breadcrumbs":9,"title":1},"555":{"body":31,"breadcrumbs":11,"title":3},"556":{"body":1,"breadcrumbs":11,"title":3},"557":{"body":1,"breadcrumbs":9,"title":1},"558":{"body":1,"breadcrumbs":9,"title":1},"559":{"body":42,"breadcrumbs":9,"title":1},"56":{"body":73,"breadcrumbs":10,"title":5},"560":{"body":5,"breadcrumbs":11,"title":3},"561":{"body":1,"breadcrumbs":10,"title":2},"562":{"body":1,"breadcrumbs":12,"title":4},"563":{"body":81,"breadcrumbs":8,"title":4},"564":{"body":183,"breadcrumbs":5,"title":1},"565":{"body":124,"breadcrumbs":5,"title":1},"566":{"body":3,"breadcrumbs":5,"title":1},"567":{"body":231,"breadcrumbs":5,"title":1},"568":{"body":146,"breadcrumbs":5,"title":1},"569":{"body":70,"breadcrumbs":6,"title":2},"57":{"body":27,"breadcrumbs":6,"title":1},"570":{"body":63,"breadcrumbs":5,"title":1},"571":{"body":206,"breadcrumbs":6,"title":2},"572":{"body":0,"breadcrumbs":6,"title":2},"573":{"body":219,"breadcrumbs":6,"title":2},"574":{"body":54,"breadcrumbs":5,"title":1},"575":{"body":110,"breadcrumbs":6,"title":2},"576":{"body":141,"breadcrumbs":6,"title":2},"577":{"body":89,"breadcrumbs":5,"title":1},"578":{"body":1,"breadcrumbs":7,"title":3},"579":{"body":1,"breadcrumbs":7,"title":3},"58":{"body":88,"breadcrumbs":6,"title":1},"580":{"body":5,"breadcrumbs":5,"title":1},"581":{"body":12,"breadcrumbs":5,"title":1},"582":{"body":8,"breadcrumbs":5,"title":1},"583":{"body":13,"breadcrumbs":7,"title":3},"584":{"body":45,"breadcrumbs":12,"title":6},"585":{"body":9,"breadcrumbs":7,"title":1},"586":{"body":75,"breadcrumbs":7,"title":1},"587":{"body":6,"breadcrumbs":7,"title":1},"588":{"body":73,"breadcrumbs":7,"title":1},"589":{"body":7,"breadcrumbs":7,"title":1},"59":{"body":11,"breadcrumbs":6,"title":1},"590":{"body":4,"breadcrumbs":9,"title":3},"591":{"body":8,"breadcrumbs":9,"title":3},"592":{"body":2,"breadcrumbs":7,"title":1},"593":{"body":25,"breadcrumbs":7,"title":1},"594":{"body":20,"breadcrumbs":7,"title":1},"595":{"body":1,"breadcrumbs":9,"title":3},"596":{"body":1,"breadcrumbs":8,"title":2},"597":{"body":1,"breadcrumbs":10,"title":4},"598":{"body":61,"breadcrumbs":12,"title":6},"599":{"body":56,"breadcrumbs":7,"title":1},"6":{"body":331,"breadcrumbs":7,"title":2},"60":{"body":111,"breadcrumbs":6,"title":1},"600":{"body":187,"breadcrumbs":7,"title":1},"601":{"body":8,"breadcrumbs":7,"title":1},"602":{"body":509,"breadcrumbs":7,"title":1},"603":{"body":222,"breadcrumbs":15,"title":9},"604":{"body":2,"breadcrumbs":7,"title":1},"605":{"body":61,"breadcrumbs":9,"title":3},"606":{"body":32,"breadcrumbs":9,"title":3},"607":{"body":2,"breadcrumbs":7,"title":1},"608":{"body":21,"breadcrumbs":7,"title":1},"609":{"body":53,"breadcrumbs":7,"title":1},"61":{"body":49,"breadcrumbs":11,"title":6},"610":{"body":1,"breadcrumbs":9,"title":3},"611":{"body":1,"breadcrumbs":8,"title":2},"612":{"body":1,"breadcrumbs":10,"title":4},"613":{"body":47,"breadcrumbs":14,"title":7},"614":{"body":39,"breadcrumbs":8,"title":1},"615":{"body":90,"breadcrumbs":8,"title":1},"616":{"body":6,"breadcrumbs":8,"title":1},"617":{"body":35,"breadcrumbs":8,"title":1},"618":{"body":8,"breadcrumbs":8,"title":1},"619":{"body":94,"breadcrumbs":10,"title":3},"62":{"body":57,"breadcrumbs":8,"title":3},"620":{"body":0,"breadcrumbs":10,"title":3},"621":{"body":2,"breadcrumbs":8,"title":1},"622":{"body":6,"breadcrumbs":8,"title":1},"623":{"body":4,"breadcrumbs":8,"title":1},"624":{"body":1,"breadcrumbs":10,"title":3},"625":{"body":1,"breadcrumbs":9,"title":2},"626":{"body":1,"breadcrumbs":11,"title":4},"627":{"body":69,"breadcrumbs":18,"title":9},"628":{"body":43,"breadcrumbs":10,"title":1},"629":{"body":93,"breadcrumbs":10,"title":1},"63":{"body":168,"breadcrumbs":8,"title":3},"630":{"body":15,"breadcrumbs":10,"title":1},"631":{"body":40,"breadcrumbs":10,"title":1},"632":{"body":74,"breadcrumbs":13,"title":4},"633":{"body":218,"breadcrumbs":11,"title":2},"634":{"body":164,"breadcrumbs":12,"title":3},"635":{"body":60,"breadcrumbs":11,"title":2},"636":{"body":34,"breadcrumbs":12,"title":3},"637":{"body":39,"breadcrumbs":11,"title":2},"638":{"body":9,"breadcrumbs":10,"title":1},"639":{"body":26,"breadcrumbs":12,"title":3},"64":{"body":62,"breadcrumbs":9,"title":4},"640":{"body":46,"breadcrumbs":10,"title":1},"641":{"body":32,"breadcrumbs":10,"title":1},"642":{"body":36,"breadcrumbs":10,"title":1},"643":{"body":28,"breadcrumbs":12,"title":3},"644":{"body":61,"breadcrumbs":10,"title":1},"645":{"body":20,"breadcrumbs":10,"title":1},"646":{"body":12,"breadcrumbs":12,"title":3},"647":{"body":1,"breadcrumbs":11,"title":2},"648":{"body":39,"breadcrumbs":13,"title":4},"649":{"body":47,"breadcrumbs":12,"title":6},"65":{"body":38,"breadcrumbs":8,"title":3},"650":{"body":57,"breadcrumbs":7,"title":1},"651":{"body":77,"breadcrumbs":7,"title":1},"652":{"body":6,"breadcrumbs":7,"title":1},"653":{"body":109,"breadcrumbs":7,"title":1},"654":{"body":28,"breadcrumbs":7,"title":1},"655":{"body":9,"breadcrumbs":7,"title":1},"656":{"body":8,"breadcrumbs":9,"title":3},"657":{"body":0,"breadcrumbs":9,"title":3},"658":{"body":17,"breadcrumbs":7,"title":1},"659":{"body":21,"breadcrumbs":7,"title":1},"66":{"body":20,"breadcrumbs":8,"title":3},"660":{"body":34,"breadcrumbs":7,"title":1},"661":{"body":15,"breadcrumbs":9,"title":3},"662":{"body":1,"breadcrumbs":8,"title":2},"663":{"body":25,"breadcrumbs":10,"title":4},"664":{"body":46,"breadcrumbs":10,"title":5},"665":{"body":32,"breadcrumbs":6,"title":1},"666":{"body":32,"breadcrumbs":6,"title":1},"667":{"body":4,"breadcrumbs":6,"title":1},"668":{"body":48,"breadcrumbs":6,"title":1},"669":{"body":13,"breadcrumbs":6,"title":1},"67":{"body":49,"breadcrumbs":6,"title":1},"670":{"body":33,"breadcrumbs":8,"title":3},"671":{"body":0,"breadcrumbs":8,"title":3},"672":{"body":1,"breadcrumbs":6,"title":1},"673":{"body":35,"breadcrumbs":6,"title":1},"674":{"body":1,"breadcrumbs":6,"title":1},"675":{"body":15,"breadcrumbs":8,"title":3},"676":{"body":1,"breadcrumbs":7,"title":2},"677":{"body":1,"breadcrumbs":9,"title":4},"678":{"body":44,"breadcrumbs":12,"title":6},"679":{"body":11,"breadcrumbs":7,"title":1},"68":{"body":22,"breadcrumbs":6,"title":1},"680":{"body":22,"breadcrumbs":7,"title":1},"681":{"body":4,"breadcrumbs":7,"title":1},"682":{"body":6,"breadcrumbs":7,"title":1},"683":{"body":8,"breadcrumbs":7,"title":1},"684":{"body":1,"breadcrumbs":9,"title":3},"685":{"body":0,"breadcrumbs":9,"title":3},"686":{"body":1,"breadcrumbs":7,"title":1},"687":{"body":9,"breadcrumbs":7,"title":1},"688":{"body":5,"breadcrumbs":7,"title":1},"689":{"body":7,"breadcrumbs":9,"title":3},"69":{"body":73,"breadcrumbs":8,"title":3},"690":{"body":1,"breadcrumbs":8,"title":2},"691":{"body":1,"breadcrumbs":10,"title":4},"692":{"body":62,"breadcrumbs":20,"title":10},"693":{"body":42,"breadcrumbs":11,"title":1},"694":{"body":88,"breadcrumbs":11,"title":1},"695":{"body":8,"breadcrumbs":11,"title":1},"696":{"body":117,"breadcrumbs":11,"title":1},"697":{"body":213,"breadcrumbs":12,"title":2},"698":{"body":56,"breadcrumbs":14,"title":4},"699":{"body":44,"breadcrumbs":12,"title":2},"7":{"body":50,"breadcrumbs":7,"title":2},"70":{"body":0,"breadcrumbs":8,"title":3},"700":{"body":68,"breadcrumbs":11,"title":1},"701":{"body":84,"breadcrumbs":13,"title":3},"702":{"body":0,"breadcrumbs":13,"title":3},"703":{"body":1,"breadcrumbs":11,"title":1},"704":{"body":14,"breadcrumbs":11,"title":1},"705":{"body":107,"breadcrumbs":11,"title":1},"706":{"body":12,"breadcrumbs":13,"title":3},"707":{"body":1,"breadcrumbs":12,"title":2},"708":{"body":0,"breadcrumbs":14,"title":4},"709":{"body":57,"breadcrumbs":8,"title":4},"71":{"body":68,"breadcrumbs":6,"title":1},"710":{"body":51,"breadcrumbs":5,"title":1},"711":{"body":145,"breadcrumbs":5,"title":1},"712":{"body":66,"breadcrumbs":5,"title":1},"713":{"body":0,"breadcrumbs":5,"title":1},"714":{"body":74,"breadcrumbs":5,"title":1},"715":{"body":125,"breadcrumbs":5,"title":1},"716":{"body":44,"breadcrumbs":5,"title":1},"717":{"body":88,"breadcrumbs":6,"title":2},"718":{"body":25,"breadcrumbs":5,"title":1},"719":{"body":0,"breadcrumbs":5,"title":1},"72":{"body":70,"breadcrumbs":6,"title":1},"720":{"body":164,"breadcrumbs":5,"title":1},"721":{"body":252,"breadcrumbs":5,"title":1},"722":{"body":239,"breadcrumbs":6,"title":2},"723":{"body":149,"breadcrumbs":6,"title":2},"724":{"body":139,"breadcrumbs":9,"title":5},"725":{"body":74,"breadcrumbs":7,"title":3},"726":{"body":1,"breadcrumbs":7,"title":3},"727":{"body":19,"breadcrumbs":6,"title":2},"728":{"body":0,"breadcrumbs":8,"title":4},"729":{"body":67,"breadcrumbs":7,"title":3},"73":{"body":84,"breadcrumbs":6,"title":1},"730":{"body":45,"breadcrumbs":16,"title":8},"731":{"body":10,"breadcrumbs":9,"title":1},"732":{"body":156,"breadcrumbs":9,"title":1},"733":{"body":4,"breadcrumbs":9,"title":1},"734":{"body":0,"breadcrumbs":9,"title":1},"735":{"body":1723,"breadcrumbs":11,"title":3},"736":{"body":52,"breadcrumbs":9,"title":1},"737":{"body":12,"breadcrumbs":9,"title":1},"738":{"body":10,"breadcrumbs":10,"title":2},"739":{"body":71,"breadcrumbs":10,"title":2},"74":{"body":26,"breadcrumbs":8,"title":3},"740":{"body":26,"breadcrumbs":10,"title":2},"741":{"body":54,"breadcrumbs":14,"title":7},"742":{"body":68,"breadcrumbs":8,"title":1},"743":{"body":87,"breadcrumbs":8,"title":1},"744":{"body":59,"breadcrumbs":8,"title":1},"745":{"body":18,"breadcrumbs":8,"title":1},"746":{"body":0,"breadcrumbs":8,"title":1},"747":{"body":64,"breadcrumbs":8,"title":1},"748":{"body":66,"breadcrumbs":8,"title":1},"749":{"body":142,"breadcrumbs":8,"title":1},"75":{"body":68,"breadcrumbs":7,"title":2},"750":{"body":19,"breadcrumbs":9,"title":2},"751":{"body":104,"breadcrumbs":9,"title":2},"752":{"body":151,"breadcrumbs":9,"title":2},"753":{"body":2,"breadcrumbs":8,"title":1},"754":{"body":28,"breadcrumbs":10,"title":3},"755":{"body":7,"breadcrumbs":9,"title":2},"756":{"body":10,"breadcrumbs":8,"title":1},"757":{"body":52,"breadcrumbs":16,"title":8},"758":{"body":16,"breadcrumbs":9,"title":1},"759":{"body":224,"breadcrumbs":9,"title":1},"76":{"body":0,"breadcrumbs":9,"title":4},"760":{"body":5,"breadcrumbs":9,"title":1},"761":{"body":482,"breadcrumbs":9,"title":1},"762":{"body":87,"breadcrumbs":9,"title":1},"763":{"body":137,"breadcrumbs":11,"title":3},"764":{"body":0,"breadcrumbs":11,"title":3},"765":{"body":23,"breadcrumbs":9,"title":1},"766":{"body":1,"breadcrumbs":9,"title":1},"767":{"body":11,"breadcrumbs":9,"title":1},"768":{"body":6,"breadcrumbs":11,"title":3},"769":{"body":1,"breadcrumbs":10,"title":2},"77":{"body":86,"breadcrumbs":7,"title":2},"770":{"body":17,"breadcrumbs":12,"title":4},"771":{"body":48,"breadcrumbs":10,"title":5},"772":{"body":65,"breadcrumbs":6,"title":1},"773":{"body":190,"breadcrumbs":6,"title":1},"774":{"body":25,"breadcrumbs":6,"title":1},"775":{"body":0,"breadcrumbs":6,"title":1},"776":{"body":367,"breadcrumbs":7,"title":2},"777":{"body":218,"breadcrumbs":7,"title":2},"778":{"body":80,"breadcrumbs":8,"title":3},"779":{"body":46,"breadcrumbs":6,"title":1},"78":{"body":158,"breadcrumbs":9,"title":4},"780":{"body":23,"breadcrumbs":8,"title":3},"781":{"body":4,"breadcrumbs":7,"title":2},"782":{"body":45,"breadcrumbs":14,"title":7},"783":{"body":22,"breadcrumbs":8,"title":1},"784":{"body":37,"breadcrumbs":8,"title":1},"785":{"body":2,"breadcrumbs":8,"title":1},"786":{"body":202,"breadcrumbs":8,"title":1},"787":{"body":3,"breadcrumbs":8,"title":1},"788":{"body":26,"breadcrumbs":10,"title":3},"789":{"body":0,"breadcrumbs":10,"title":3},"79":{"body":47,"breadcrumbs":10,"title":5},"790":{"body":8,"breadcrumbs":8,"title":1},"791":{"body":6,"breadcrumbs":8,"title":1},"792":{"body":8,"breadcrumbs":8,"title":1},"793":{"body":10,"breadcrumbs":10,"title":3},"794":{"body":7,"breadcrumbs":9,"title":2},"795":{"body":40,"breadcrumbs":12,"title":6},"796":{"body":61,"breadcrumbs":7,"title":1},"797":{"body":101,"breadcrumbs":7,"title":1},"798":{"body":15,"breadcrumbs":7,"title":1},"799":{"body":187,"breadcrumbs":7,"title":1},"8":{"body":32,"breadcrumbs":6,"title":1},"80":{"body":37,"breadcrumbs":6,"title":1},"800":{"body":17,"breadcrumbs":7,"title":1},"801":{"body":12,"breadcrumbs":9,"title":3},"802":{"body":0,"breadcrumbs":9,"title":3},"803":{"body":11,"breadcrumbs":7,"title":1},"804":{"body":40,"breadcrumbs":8,"title":2},"805":{"body":1,"breadcrumbs":9,"title":3},"806":{"body":1,"breadcrumbs":8,"title":2},"807":{"body":39,"breadcrumbs":10,"title":4},"808":{"body":61,"breadcrumbs":12,"title":6},"809":{"body":34,"breadcrumbs":7,"title":1},"81":{"body":177,"breadcrumbs":6,"title":1},"810":{"body":92,"breadcrumbs":7,"title":1},"811":{"body":67,"breadcrumbs":7,"title":1},"812":{"body":4,"breadcrumbs":7,"title":1},"813":{"body":77,"breadcrumbs":7,"title":1},"814":{"body":237,"breadcrumbs":9,"title":3},"815":{"body":124,"breadcrumbs":9,"title":3},"816":{"body":41,"breadcrumbs":9,"title":3},"817":{"body":106,"breadcrumbs":10,"title":4},"818":{"body":51,"breadcrumbs":7,"title":1},"819":{"body":27,"breadcrumbs":9,"title":3},"82":{"body":8,"breadcrumbs":6,"title":1},"820":{"body":0,"breadcrumbs":9,"title":3},"821":{"body":4,"breadcrumbs":7,"title":1},"822":{"body":13,"breadcrumbs":7,"title":1},"823":{"body":3,"breadcrumbs":7,"title":1},"824":{"body":5,"breadcrumbs":9,"title":3},"825":{"body":2,"breadcrumbs":8,"title":2},"826":{"body":37,"breadcrumbs":10,"title":4},"827":{"body":49,"breadcrumbs":14,"title":7},"828":{"body":14,"breadcrumbs":8,"title":1},"829":{"body":113,"breadcrumbs":8,"title":1},"83":{"body":223,"breadcrumbs":6,"title":1},"830":{"body":6,"breadcrumbs":8,"title":1},"831":{"body":180,"breadcrumbs":8,"title":1},"832":{"body":91,"breadcrumbs":8,"title":1},"833":{"body":25,"breadcrumbs":10,"title":3},"834":{"body":0,"breadcrumbs":10,"title":3},"835":{"body":44,"breadcrumbs":8,"title":1},"836":{"body":13,"breadcrumbs":8,"title":1},"837":{"body":31,"breadcrumbs":8,"title":1},"838":{"body":1,"breadcrumbs":10,"title":3},"839":{"body":1,"breadcrumbs":9,"title":2},"84":{"body":128,"breadcrumbs":6,"title":1},"840":{"body":12,"breadcrumbs":11,"title":4},"841":{"body":60,"breadcrumbs":10,"title":5},"842":{"body":55,"breadcrumbs":6,"title":1},"843":{"body":103,"breadcrumbs":6,"title":1},"844":{"body":28,"breadcrumbs":6,"title":1},"845":{"body":7,"breadcrumbs":6,"title":1},"846":{"body":125,"breadcrumbs":9,"title":4},"847":{"body":83,"breadcrumbs":13,"title":8},"848":{"body":149,"breadcrumbs":10,"title":5},"849":{"body":148,"breadcrumbs":6,"title":1},"85":{"body":86,"breadcrumbs":8,"title":3},"850":{"body":52,"breadcrumbs":8,"title":3},"851":{"body":0,"breadcrumbs":8,"title":3},"852":{"body":61,"breadcrumbs":6,"title":1},"853":{"body":22,"breadcrumbs":6,"title":1},"854":{"body":6,"breadcrumbs":6,"title":1},"855":{"body":38,"breadcrumbs":6,"title":1},"856":{"body":11,"breadcrumbs":7,"title":2},"857":{"body":50,"breadcrumbs":12,"title":6},"858":{"body":37,"breadcrumbs":7,"title":1},"859":{"body":18,"breadcrumbs":7,"title":1},"86":{"body":0,"breadcrumbs":8,"title":3},"860":{"body":42,"breadcrumbs":7,"title":1},"861":{"body":29,"breadcrumbs":10,"title":4},"862":{"body":29,"breadcrumbs":10,"title":4},"863":{"body":43,"breadcrumbs":7,"title":1},"864":{"body":10,"breadcrumbs":9,"title":3},"865":{"body":0,"breadcrumbs":9,"title":3},"866":{"body":3,"breadcrumbs":7,"title":1},"867":{"body":7,"breadcrumbs":7,"title":1},"868":{"body":2,"breadcrumbs":7,"title":1},"869":{"body":14,"breadcrumbs":9,"title":3},"87":{"body":14,"breadcrumbs":6,"title":1},"870":{"body":21,"breadcrumbs":8,"title":2},"871":{"body":58,"breadcrumbs":10,"title":5},"872":{"body":77,"breadcrumbs":6,"title":1},"873":{"body":0,"breadcrumbs":6,"title":1},"874":{"body":185,"breadcrumbs":6,"title":1},"875":{"body":60,"breadcrumbs":6,"title":1},"876":{"body":63,"breadcrumbs":7,"title":2},"877":{"body":4,"breadcrumbs":6,"title":1},"878":{"body":121,"breadcrumbs":6,"title":1},"879":{"body":865,"breadcrumbs":8,"title":3},"88":{"body":13,"breadcrumbs":6,"title":1},"880":{"body":224,"breadcrumbs":6,"title":1},"881":{"body":139,"breadcrumbs":8,"title":3},"882":{"body":3,"breadcrumbs":6,"title":1},"883":{"body":4,"breadcrumbs":8,"title":3},"884":{"body":0,"breadcrumbs":8,"title":3},"885":{"body":243,"breadcrumbs":6,"title":1},"886":{"body":11,"breadcrumbs":6,"title":1},"887":{"body":14,"breadcrumbs":6,"title":1},"888":{"body":4,"breadcrumbs":8,"title":3},"889":{"body":14,"breadcrumbs":7,"title":2},"89":{"body":1,"breadcrumbs":6,"title":1},"890":{"body":23,"breadcrumbs":9,"title":4},"891":{"body":59,"breadcrumbs":22,"title":11},"892":{"body":13,"breadcrumbs":12,"title":1},"893":{"body":0,"breadcrumbs":12,"title":1},"894":{"body":37,"breadcrumbs":12,"title":1},"895":{"body":150,"breadcrumbs":12,"title":1},"896":{"body":19,"breadcrumbs":13,"title":2},"897":{"body":18,"breadcrumbs":12,"title":1},"898":{"body":73,"breadcrumbs":12,"title":1},"899":{"body":2,"breadcrumbs":12,"title":1},"9":{"body":18,"breadcrumbs":8,"title":3},"90":{"body":1,"breadcrumbs":8,"title":3},"900":{"body":18,"breadcrumbs":14,"title":3},"901":{"body":0,"breadcrumbs":14,"title":3},"902":{"body":25,"breadcrumbs":12,"title":1},"903":{"body":4,"breadcrumbs":12,"title":1},"904":{"body":8,"breadcrumbs":12,"title":1},"905":{"body":3,"breadcrumbs":14,"title":3},"906":{"body":3,"breadcrumbs":13,"title":2},"907":{"body":12,"breadcrumbs":15,"title":4},"908":{"body":67,"breadcrumbs":28,"title":14},"909":{"body":36,"breadcrumbs":15,"title":1},"91":{"body":1,"breadcrumbs":7,"title":2},"910":{"body":0,"breadcrumbs":15,"title":1},"911":{"body":49,"breadcrumbs":15,"title":1},"912":{"body":226,"breadcrumbs":15,"title":1},"913":{"body":115,"breadcrumbs":16,"title":2},"914":{"body":19,"breadcrumbs":15,"title":1},"915":{"body":0,"breadcrumbs":15,"title":1},"916":{"body":13,"breadcrumbs":15,"title":1},"917":{"body":46,"breadcrumbs":17,"title":3},"918":{"body":0,"breadcrumbs":17,"title":3},"919":{"body":53,"breadcrumbs":15,"title":1},"92":{"body":6,"breadcrumbs":9,"title":4},"920":{"body":9,"breadcrumbs":15,"title":1},"921":{"body":8,"breadcrumbs":15,"title":1},"922":{"body":0,"breadcrumbs":17,"title":3},"923":{"body":2,"breadcrumbs":16,"title":2},"924":{"body":1,"breadcrumbs":16,"title":2},"925":{"body":1,"breadcrumbs":18,"title":4},"926":{"body":52,"breadcrumbs":8,"title":4},"927":{"body":37,"breadcrumbs":5,"title":1},"928":{"body":184,"breadcrumbs":5,"title":1},"929":{"body":42,"breadcrumbs":5,"title":1},"93":{"body":50,"breadcrumbs":24,"title":12},"930":{"body":0,"breadcrumbs":5,"title":1},"931":{"body":99,"breadcrumbs":6,"title":2},"932":{"body":287,"breadcrumbs":6,"title":2},"933":{"body":161,"breadcrumbs":6,"title":2},"934":{"body":80,"breadcrumbs":5,"title":1},"935":{"body":20,"breadcrumbs":7,"title":3},"936":{"body":43,"breadcrumbs":7,"title":3},"937":{"body":12,"breadcrumbs":7,"title":3},"938":{"body":59,"breadcrumbs":6,"title":2},"939":{"body":31,"breadcrumbs":8,"title":4},"94":{"body":43,"breadcrumbs":13,"title":1},"940":{"body":51,"breadcrumbs":10,"title":5},"941":{"body":29,"breadcrumbs":6,"title":1},"942":{"body":92,"breadcrumbs":6,"title":1},"943":{"body":21,"breadcrumbs":6,"title":1},"944":{"body":92,"breadcrumbs":6,"title":1},"945":{"body":55,"breadcrumbs":6,"title":1},"946":{"body":0,"breadcrumbs":8,"title":3},"947":{"body":26,"breadcrumbs":6,"title":1},"948":{"body":16,"breadcrumbs":6,"title":1},"949":{"body":12,"breadcrumbs":6,"title":1},"95":{"body":181,"breadcrumbs":13,"title":1},"950":{"body":0,"breadcrumbs":8,"title":3},"951":{"body":20,"breadcrumbs":6,"title":1},"952":{"body":18,"breadcrumbs":6,"title":1},"953":{"body":16,"breadcrumbs":6,"title":1},"954":{"body":5,"breadcrumbs":8,"title":3},"955":{"body":9,"breadcrumbs":7,"title":2},"956":{"body":37,"breadcrumbs":9,"title":4},"957":{"body":51,"breadcrumbs":12,"title":6},"958":{"body":17,"breadcrumbs":7,"title":1},"959":{"body":71,"breadcrumbs":7,"title":1},"96":{"body":2,"breadcrumbs":13,"title":1},"960":{"body":24,"breadcrumbs":7,"title":1},"961":{"body":90,"breadcrumbs":7,"title":1},"962":{"body":40,"breadcrumbs":7,"title":1},"963":{"body":0,"breadcrumbs":9,"title":3},"964":{"body":22,"breadcrumbs":7,"title":1},"965":{"body":23,"breadcrumbs":7,"title":1},"966":{"body":10,"breadcrumbs":7,"title":1},"967":{"body":0,"breadcrumbs":9,"title":3},"968":{"body":22,"breadcrumbs":7,"title":1},"969":{"body":19,"breadcrumbs":7,"title":1},"97":{"body":40,"breadcrumbs":13,"title":1},"970":{"body":15,"breadcrumbs":7,"title":1},"971":{"body":34,"breadcrumbs":9,"title":3},"972":{"body":24,"breadcrumbs":8,"title":2},"973":{"body":62,"breadcrumbs":10,"title":4},"974":{"body":47,"breadcrumbs":12,"title":6},"975":{"body":26,"breadcrumbs":7,"title":1},"976":{"body":31,"breadcrumbs":7,"title":1},"977":{"body":6,"breadcrumbs":7,"title":1},"978":{"body":7,"breadcrumbs":7,"title":1},"979":{"body":20,"breadcrumbs":7,"title":1},"98":{"body":1,"breadcrumbs":13,"title":1},"980":{"body":9,"breadcrumbs":9,"title":3},"981":{"body":0,"breadcrumbs":9,"title":3},"982":{"body":5,"breadcrumbs":7,"title":1},"983":{"body":31,"breadcrumbs":7,"title":1},"984":{"body":21,"breadcrumbs":7,"title":1},"985":{"body":15,"breadcrumbs":9,"title":3},"986":{"body":1,"breadcrumbs":8,"title":2},"987":{"body":15,"breadcrumbs":10,"title":4},"988":{"body":54,"breadcrumbs":16,"title":8},"989":{"body":14,"breadcrumbs":9,"title":1},"99":{"body":0,"breadcrumbs":15,"title":3},"990":{"body":51,"breadcrumbs":9,"title":1},"991":{"body":15,"breadcrumbs":9,"title":1},"992":{"body":54,"breadcrumbs":9,"title":1},"993":{"body":2,"breadcrumbs":9,"title":1},"994":{"body":20,"breadcrumbs":11,"title":3},"995":{"body":0,"breadcrumbs":11,"title":3},"996":{"body":52,"breadcrumbs":9,"title":1},"997":{"body":1,"breadcrumbs":9,"title":1},"998":{"body":3,"breadcrumbs":9,"title":1},"999":{"body":1,"breadcrumbs":11,"title":3}},"docs":{"0":{"body":"This book contains the Polkadot Fellowship Requests for Comments (RFCs) detailing proposed changes to the technical implementation of the Polkadot network. polkadot-fellows/RFCs","breadcrumbs":"Introduction » Introduction","id":"0","title":"Introduction"},"1":{"body":"(source) Table of Contents RFC-0125: XCM Asset Metadata Summary Motivation Stakeholders Explanation New instructions Repurposing AssetInstance::Undefined Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 22 Oct 2024 Description XCM Asset Metadata definition and a way of communicating it via XCM Authors Daniel Shiposha","breadcrumbs":"RFC-0125: XCM Asset Metadata » RFC-0125: XCM Asset Metadata","id":"1","title":"RFC-0125: XCM Asset Metadata"},"10":{"body":"","breadcrumbs":"RFC-0125: XCM Asset Metadata » Performance, Ergonomics, and Compatibility","id":"10","title":"Performance, Ergonomics, and Compatibility"},"100":{"body":"The changes are not directly affecting the protocol security, parachains are not enforced to use the host function.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Security","id":"100","title":"Security"},"1000":{"body":"None.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Unresolved Questions","id":"1000","title":"Unresolved Questions"},"1001":{"body":"None.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Future Directions and Related Material","id":"1001","title":"Future Directions and Related Material"},"1002":{"body":"(source) Table of Contents RFC-TODO: Stale Nomination Reward Curve Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 10 July 2024 Description Introduce a decaying reward curve for stale nominations in staking. Authors Shawn Tabrizi","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » RFC-TODO: Stale Nomination Reward Curve","id":"1002","title":"RFC-TODO: Stale Nomination Reward Curve"},"1003":{"body":"This is a proposal to reduce the impact of stale nominations in the Polkadot staking system. With this proposal, nominators are incentivized to update or renew their selected validators once per time period. Nominators that do not update or renew their selected validators would be considered stale, and a decaying multiplier would be applied to their nominations, reducing the weight of their nomination and rewards.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Summary","id":"1003","title":"Summary"},"1004":{"body":"Longer motivation behind the content of the RFC, presented as a combination of both problems and requirements for the solution. One of Polkadot's primary utilities is providing a high quality security layer for applications built on top of it. To achieve this, Polkadot runs a Nominated Proof-of-Stake system, allowing nominators to vote on who they think are the best validators for Polkadot. This system functions best when nominators and validators are active participants in the network. Nominators should consistently evaluate the quality and preferences of validators, and adjust their nominations accordingly. Unfortunately, many Polkadot nominators do not play an active role in the NPoS system. For many, they set their nominations, and then seldomly look back at the. This can lead to many negative behaviors: Incumbents who received early nominations basically achieve tenure. Validator quality and performance can decrease without recourse. The validator set are not the optimal for Polkadot. New validators have a harder time entering the active set. Validators are able to \"sneakily\" increase their commission.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Motivation","id":"1004","title":"Motivation"},"1005":{"body":"Primary stakeholders are: Nominators Validators","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Stakeholders","id":"1005","title":"Stakeholders"},"1006":{"body":"Detail-heavy explanation of the RFC, suitable for explanation to an implementer of the changeset. This should address corner cases in detail and provide justification behind decisions, and provide rationale for how the design meets the solution requirements.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Explanation","id":"1006","title":"Explanation"},"1007":{"body":"Description of recognized drawbacks to the approach given in the RFC. Non-exhaustively, drawbacks relating to performance, ergonomics, user experience, security, or privacy.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Drawbacks","id":"1007","title":"Drawbacks"},"1008":{"body":"Describe the the impact of the proposal on these three high-importance areas - how implementations can be tested for adherence, effects that the proposal has on security and privacy per-se, as well as any possible implementation pitfalls which should be clearly avoided.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Testing, Security, and Privacy","id":"1008","title":"Testing, Security, and Privacy"},"1009":{"body":"Describe the impact of the proposal on the exposed functionality of Polkadot.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Performance, Ergonomics, and Compatibility","id":"1009","title":"Performance, Ergonomics, and Compatibility"},"101":{"body":"","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Performance, Ergonomics, and Compatibility","id":"101","title":"Performance, Ergonomics, and Compatibility"},"1010":{"body":"Is this an optimization or a necessary pessimization? What steps have been taken to minimize additional overhead?","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Performance","id":"1010","title":"Performance"},"1011":{"body":"If the proposal alters exposed interfaces to developers or end-users, which types of usage patterns have been optimized for?","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Ergonomics","id":"1011","title":"Ergonomics"},"1012":{"body":"Does this proposal break compatibility with existing interfaces, older versions of implementations? Summarize necessary migrations or upgrade strategies, if any.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Compatibility","id":"1012","title":"Compatibility"},"1013":{"body":"Provide references to either prior art or other relevant research for the submitted design.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Prior Art and References","id":"1013","title":"Prior Art and References"},"1014":{"body":"Provide specific questions to discuss and address before the RFC is voted on by the Fellowship. This should include, for example, alternatives to aspects of the proposed design where the appropriate trade-off to make is unclear.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Unresolved Questions","id":"1014","title":"Unresolved Questions"},"1015":{"body":"Describe future work which could be enabled by this RFC, if it were accepted, as well as related RFCs. This is a place to brain-dump and explore possibilities, which themselves may become their own RFCs.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Future Directions and Related Material","id":"1015","title":"Future Directions and Related Material"},"102":{"body":"N/A","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Performance","id":"102","title":"Performance"},"103":{"body":"The host function proposed in this RFC allows parachain runtime developers to use a more efficient verification mechanism for \"secp256r1\" elliptic curve signatures.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Ergonomics","id":"103","title":"Ergonomics"},"104":{"body":"Parachain teams will need to include this host function to upgrade.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Compatibility","id":"104","title":"Compatibility"},"105":{"body":"Pull Request including RIP-7212 in Moonbeam: Add secp256r1 precompile . Pull Request including proposed host function: IN PROGRESS .","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Prior Art and References","id":"105","title":"Prior Art and References"},"106":{"body":"(source) Table of Contents RFC-0117: The Unbrick Collective Summary Motivation Stakeholders Explanation The Collective The Unbrick Process Belonging to the Collective Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 22 August 2024 Description The Unbrick Collective aims to help teams rescuing a para once it stops producing blocks Authors Bryan Chen, Pablo Dorado","breadcrumbs":"RFC-0117: The Unbrick Collective » RFC-0117: The Unbrick Collective","id":"106","title":"RFC-0117: The Unbrick Collective"},"107":{"body":"A followup of the RFC-0014 . This RFC proposes adding a new collective to the Polkadot Collectives Chain: The Unbrick Collective, as well as improvements in the mechanisms that will allow teams operating paras that had stopped producing blocks to be assisted, in order to restore the production of blocks of these paras.","breadcrumbs":"RFC-0117: The Unbrick Collective » Summary","id":"107","title":"Summary"},"108":{"body":"Since the initial launch of Polkadot parachains, there has been many incidients causing parachains to stop producing new blocks (therefore, being bricked ) and many occurrences that required Polkadot governance to update the parachain head state/wasm. This can be due to many reasons range from incorrectly registering the initial head state, inability to use sudo key, bad runtime migration, bad weight configuration, and bugs in the development of the Polkadot SDK. Currently, when the para is not unlocked in the paras registrar [1] , the Root origin is required to perform such actions, involving the governance process to invoke this origin, which can be very resource expensive for the teams. The long voting and enactment times also could result significant damage to the parachain and users. Finally, other instances of governance that might enact a call using the Root origin (like the Polkadot Fellowship), due to the nature of their mission, are not fit to carry these kind of tasks. In consequence, the idea of a Unbrick Collective that can provide assistance to para teams when they brick and further protection against future halts is reasonable enough.","breadcrumbs":"RFC-0117: The Unbrick Collective » Motivation","id":"108","title":"Motivation"},"109":{"body":"Parachain teams Parachain users OpenGov users Polkadot Fellowship","breadcrumbs":"RFC-0117: The Unbrick Collective » Stakeholders","id":"109","title":"Stakeholders"},"11":{"body":"No significant impact.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Performance","id":"11","title":"Performance"},"110":{"body":"","breadcrumbs":"RFC-0117: The Unbrick Collective » Explanation","id":"110","title":"Explanation"},"111":{"body":"The Unbrick Collective is defined as an unranked collective of members, not paid by the Polkadot Treasury. Its main goal is to serve as a point of contact and assistance for enacting the actions needed to unbrick a para. Such actions are: Updating the Parachain Verification Function (a.k.a. a new WASM) of a para. Updating the head state of a para. A combination of the above. In order to ensure these changes are safe enough for the network, actions enacted by the Unbrick Collective must be whitelisted via similar mechanisms followed by collectives like the Polkadot Fellowship. This will prevent unintended, not overseen changes on other paras to occur. Also, teams might opt-in to delegate handling their para in the registry to the Collective. This allows to perform similar actions using the paras registrar , allowing for a shorter path to unbrick a para. Initially, the unbrick collective has powers similar to a parachains own sudo, but permits more decentralized control. In the future, Polkadot shall provide functionality like SPREE or JAM that exceeds sudo permissions, so the unbrick collective cannot modify those state roots or code.","breadcrumbs":"RFC-0117: The Unbrick Collective » The Collective","id":"111","title":"The Collective"},"112":{"body":"flowchart TD A[Start] A -- Bricked --> C[Request para unlock via Root] C -- Approved --> Y C -- Rejected --> A D[unbrick call proposal on WhitelistedUnbrickCaller] E[whitelist call proposal on the Unbrick governance] E -- call whitelisted --> F[unbrick call enacted] D -- unbrick called --> F F --> Y A -- Not bricked --> O[Opt-in to the Collective] O -- Bricked --> D O -- Bricked --> E Y[update PVF / head state] -- Unbricked --> Z[End] Initially, a para team has two paths to handle a potential unbrick of their para in the case it stops producing blocks. Opt-in to the Unbrick Collective : This is done by delegating the handling of the para in the paras registrar to an origin related to the Collective. This doesn't require unlocking the para. This way, the collective is enabled to perform changes in the paras module, after the Unbrick Process proceeds. Request a Para Unlock : In case the para hasn't delegated its handling in the paras registrar , it'll be still possible for the para team to submit a proposal to unlock the para, which can be assisted by the Collective. However, this involves submitting a proposal to the Root governance origin.","breadcrumbs":"RFC-0117: The Unbrick Collective » The Unbrick Process","id":"112","title":"The Unbrick Process"},"113":{"body":"The collective will be initially created without members (no seeding). There will be additional governance proposals to setup the seed members. The origins able to modify the members of the collective are: The Fellows track in the Polkadot Fellowship. Root track in the Relay. More than two thirds of the existing Unbrick Collective. The members are responsible to verify the technical details of the unbrick requests (i.e. the hash of the new PVF being set). Therefore, they must have the technical capacity to perform such tasks. Suggested requirements to become a member are the following: Rank 3 or above in the Polkadot Fellowship. Being a CTO or Technical Lead in a para team that has opted-in to delegate the Unbrick Collective to manage the PVF/head state of the para.","breadcrumbs":"RFC-0117: The Unbrick Collective » Belonging to the Collective","id":"113","title":"Belonging to the Collective"},"114":{"body":"The ability to modify the Head State and/or the PVF of a para means a possibility to perform arbitrary modifications of it (i.e. take control the native parachain token or any bridged assets in the para). This could introduce a new attack vector, and therefore, such great power needs to be handled carefully.","breadcrumbs":"RFC-0117: The Unbrick Collective » Drawbacks","id":"114","title":"Drawbacks"},"115":{"body":"The implementation of this RFC will be tested on testnets (Rococo and Westend) first. An audit will be required to ensure the implementation doesn't introduce unwanted side effects. There are no privacy related concerns.","breadcrumbs":"RFC-0117: The Unbrick Collective » Testing, Security, and Privacy","id":"115","title":"Testing, Security, and Privacy"},"116":{"body":"","breadcrumbs":"RFC-0117: The Unbrick Collective » Performance, Ergonomics, and Compatibility","id":"116","title":"Performance, Ergonomics, and Compatibility"},"117":{"body":"This RFC should not introduce any performance impact.","breadcrumbs":"RFC-0117: The Unbrick Collective » Performance","id":"117","title":"Performance"},"118":{"body":"This RFC should improve the experience for new and existing parachain teams, lowering the barrier to unbrick a stalled para.","breadcrumbs":"RFC-0117: The Unbrick Collective » Ergonomics","id":"118","title":"Ergonomics"},"119":{"body":"This RFC is fully compatible with existing interfaces.","breadcrumbs":"RFC-0117: The Unbrick Collective » Compatibility","id":"119","title":"Compatibility"},"12":{"body":"Introducing a standard metadata format and a way of communicating it is a valuable addition to the XCM format that potentially increases cross-chain interoperability without the need to form ad-hoc chain-to-chain integrations via Transact.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Ergonomics","id":"12","title":"Ergonomics"},"120":{"body":"RFC-0014: Improve Locking Mechanisms for Parachains How to Recover a Parachain, Polkadot Forum Unbrick Collective, Polkadot Forum","breadcrumbs":"RFC-0117: The Unbrick Collective » Prior Art and References","id":"120","title":"Prior Art and References"},"121":{"body":"What are the parameters for the WhitelistedUnbrickCaller track? Any other methods that shall be updated to accept Unbrick origin? Any other requirements to become a member? We would like to keep this simple, so no funding support from the Polkadot treasury. But do we want to compensate the members somehow? i.e. Allow parachain teams to donate to the collective. We hope SPREE/JAM would be carefully audited for miss-use risks before being provided to parachain teams, but could the unbrick collective have an elections that warranted trust beyond sudo powers? An auditing framework/collective makes sense parachain code upgrades, but could also strengthen the unbrick collective. Do we want to have this collective offer additional technical support to help bricked parachains? i.e. help debug the code, create the rescue plan, create postmortem report, provide resources on how to avoid getting bricked The paras registrar refers to a pallet in the Relay, responsible to gather registration info of the paras, the locked/unlocked state, and the manager info.","breadcrumbs":"RFC-0117: The Unbrick Collective » Unresolved Questions","id":"121","title":"Unresolved Questions"},"122":{"body":"(source) Table of Contents RFC-0120: Referenda Confirmation by Candle Mechanism Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 22 March 2024 Description Proposal to decide polls after confirm period via a mechanism similar to a candle auction Authors Pablo Dorado, Daniel Olano","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » RFC-0120: Referenda Confirmation by Candle Mechanism","id":"122","title":"RFC-0120: Referenda Confirmation by Candle Mechanism"},"123":{"body":"In an attempt to mitigate risks derived from unwanted behaviours around long decision periods on referenda, this proposal describes how to finalize and decide a result of a poll via a mechanism similar to candle auctions.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Summary","id":"123","title":"Summary"},"124":{"body":"Referenda protocol provide permissionless and efficient mechanisms to enable governance actors to decide the future of the blockchains around Polkadot network. However, they pose a series of risks derived from the game theory perspective around these mechanisms. One of them being where an actor uses the the public nature of the tally of a poll as a way of determining the best point in time to alter a poll in a meaningful way. While this behaviour is expected based on the current design of the referenda logic, given the recent extension of ongoing times (up to 1 month), the incentives for a bad actor to cause losses on a proposer, reflected as wasted cost of opportunity increase, and thus, this otherwise reasonable outcome becomes an attack vector, a potential risk to mitigate, especially when such attack can compromise critical guarantees of the protocol (such as its upgradeability). To mitigate this, the referenda underlying mechanisms should incentive actors to cast their votes on a poll as early as possible. This proposal's approach suggests using a Candle Auction that will be determined right after the confirm period finishes, thus decreasing the chances of actors to alter the results of a poll on confirming state, and instead incentivizing them to cast their votes earlier, on deciding state.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Motivation","id":"124","title":"Motivation"},"125":{"body":"Governance actors : Tokenholders and Collectives that vote on polls that have this mechanism enabled should be aware this change affects the outcome of failing a poll on its confirm period. Runtime Developers : This change requires runtime developers to change configuration parameters for the Referenda Pallet. Tooling and UI developers : Applications that interact with referenda must update to reflect the new Finalizing state.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Stakeholders","id":"125","title":"Stakeholders"},"126":{"body":"Currently, the process of a referendum/poll is defined as an sequence between an ongoing state (where accounts can vote), comprised by a with a preparation period, a decision period, and a confirm period. If the poll is passing before the decision period ends, it's possible to push forward to confirm period, and still, go back in case the poll fails. Once the decision period ends, a failure of the poll in the confirm period will lead to the poll to ultimately be rejected. stateDiagram-v2 sb: Submission pp: Preparation Period dp: Decision Period cp: Confirmation Period state dpd <> state ps <> cf: Approved rj: Rejected [*] --> sb sb --> pp pp --> dp: decision period starts dp --> cp: poll is passing dp --> ps: decision period ends ps --> cp: poll is passing cp --> dpd: poll fails dpd --> dp: decision period not deadlined ps --> rj: poll is failing dpd --> rj: decision period deadlined cp --> cf cf --> [*] rj --> [*] This specification proposes three changes to implement this candle mechanism: This mechanism MUST be enabled via a configuration parameter. Once enabled, the referenda system MAY record the next poll ID from which to start enabling this mechanism. This is to preserve backwards compatibility with currently ongoing polls. A record of the poll status (whether it is passing or not) is stored once the decision period is finished. Including a Finalization period as part of the ongoing state. From this point, the poll MUST be immutable at this point. This period begins the moment after confirm period ends, and extends the decision for a couple of blocks, until the VRF seed used to determine the candle block can be considered \"good enough\" . This is, not known before the ongoing period (decision/confirmation) was over. Once that happens, a random block within the confirm period is chosen, and the decision of approving or rejecting the poll is based on the status immediately before the block where the candle was \"lit-off\" . When enabled, the state diagram for the referenda system is the following: stateDiagram-v2 sb: Submission pp: Preparation Period dp: Decision Period cp: Confirmation Period cds: Finalization state dpd <> state ps <> state cd <> cf: Approved rj: Rejected [*] --> sb sb --> pp pp --> dp: decision period starts dp --> cp: poll is passing ps --> cp: poll is passing dp --> ps: decision period ends ps --> rj: poll is failing cp --> dpd: poll fails dpd --> cp: decision period over dpd --> dp: decision period not over cp --> cds: confirmation period ends cds --> cd: define moment when candle lit-off cd --> cf: poll passed cd --> rj: poll failed cf --> [*] rj --> [*]","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Explanation","id":"126","title":"Explanation"},"127":{"body":"This approach doesn't include a mechanism to determine whether a change of the poll status in the confirming period is due to a legitimate change of mind of the voters, or an exploitation of its aforementioned vulnerabilities (like a sniping attack), instead treating all of them as potential attacks. This is an issue that can be addressed by additional mechanisms, and heuristics that can help determine the probability of a change of poll status to happen as a result of a legitimate behaviour.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Drawbacks","id":"127","title":"Drawbacks"},"128":{"body":"The implementation of this RFC will be tested on testnets (Paseo and Westend) first. Furthermore, it should be enabled in a canary network (like Kusama) to ensure the behaviours it is trying to address is indeed avoided. An audit will be required to ensure the implementation doesn't introduce unwanted side effects. There are no privacy related concerns.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Testing, Security, and Privacy","id":"128","title":"Testing, Security, and Privacy"},"129":{"body":"","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Performance, Ergonomics, and Compatibility","id":"129","title":"Performance, Ergonomics, and Compatibility"},"13":{"body":"This RFC proposes new functionality, so there are no compatibility issues.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Compatibility","id":"13","title":"Compatibility"},"130":{"body":"The added steps imply pessimization, necessary to meet the expected changes. An implementation MUST exit from the Finalization period as early as possible to minimize this impact.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Performance","id":"130","title":"Performance"},"131":{"body":"This proposal does not alter the already exposed interfaces or developers or end users. However, they must be aware of the changes in the additional overhead the new period might incur (these depend on the implemented VRF).","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Ergonomics","id":"131","title":"Ergonomics"},"132":{"body":"This proposal does not break compatibility with existing interfaces, older versions, but it alters the previous implementation of the referendum processing algorithm. An acceptable upgrade strategy that can be applied is defining a point in time (block number, poll index) from which to start applying the new mechanism, thus, not affecting the already ongoing referenda.","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Compatibility","id":"132","title":"Compatibility"},"133":{"body":"Auctions pallet in polkadot-runtime-commont : Defines the mechanism of candle auctions. PBA Book : A good place to read about VRFs .","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Prior Art and References","id":"133","title":"Prior Art and References"},"134":{"body":"How to determine in a statistically meaningful way that a change in the poll status corresponds to an organic behaviour, and not an unwanted, malicious behaviour?","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Unresolved Questions","id":"134","title":"Unresolved Questions"},"135":{"body":"A proposed implementation of this change can be seen on this Pull Request .","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Future Directions and Related Material","id":"135","title":"Future Directions and Related Material"},"136":{"body":"(source) Table of Contents RFC-0121: Iterable Referenda Tracks Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 17 September 2024 Description Allow dynamic modifications of referenda tracks at runtime without the need for a full runtime upgrade. Authors Pablo Dorado, Daniel Olano","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » RFC-0121: Iterable Referenda Tracks","id":"136","title":"RFC-0121: Iterable Referenda Tracks"},"137":{"body":"The protocol change introduces flexibility in the governance structure by enabling the referenda track list to be modified dynamically at runtime. This is achieved by replacing static slices in TracksInfo with iterators, facilitating storage-based track management. As a result, governance tracks can be modified or added based on real-time decisions and without requiring runtime upgrades.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Summary","id":"137","title":"Summary"},"138":{"body":"Polkadot's governance system is designed to be adaptive and decentralized, but modifying the referenda tracks (which determine decision-making paths for proposals) has historically required runtime upgrades. This poses an operational challenge, delaying governance changes until an upgrade is scheduled and executed. The new system provides the flexibility needed to adjust tracks dynamically, reflecting real-time changes in governance needs without the latency and risks associated with runtime upgrades. This reduces governance bottlenecks and allows for quicker adaptation to emergent scenarios.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Motivation","id":"138","title":"Motivation"},"139":{"body":"Network stakeholders : the change means reduced coordination effort for track adjustments. Governance participants : this enables more responsive decision-making pathways.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Stakeholders","id":"139","title":"Stakeholders"},"14":{"body":"RFC: XCM Asset Metadata","breadcrumbs":"RFC-0125: XCM Asset Metadata » Prior Art and References","id":"14","title":"Prior Art and References"},"140":{"body":"The protocol modification replaces the current static slice method used for storing referenda tracks with an iterator-based approach that allows tracks to be managed dynamically using chain storage. Governance participants can define and modify referenda tracks as needed, which are then accessed through runtime rather than being hardcoded in the protocol. This system ensures that tracks are adjustable at any time, reducing upgrade-related complexities and introducing agility in how governance tracks are applied. This modification does not disrupt existing governance mechanisms but rather enhances them by increasing adaptability. In terms of technical structure, TracksInfo::tracks will now return iterators, making it possible to alter track configurations based on storage data rather than static definitions. This opens up possibilities for new track types and governance configurations to be deployed without the need for upgrades that might take up weeks.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Explanation","id":"140","title":"Explanation"},"141":{"body":"The most significant drawback is the increased complexity for developers managing track configurations via storage-based iterators, which require careful handling to avoid misuse or inefficiencies. Additionally, this flexibility could introduce risks if track configurations are modified improperly during runtime, potentially leading to governance instabilities.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Drawbacks","id":"141","title":"Drawbacks"},"142":{"body":"To ensure security, the change must be tested in testnet environments first (Paseo, Westend), particularly in scenarios where multiple track changes happen concurrently. Potential vulnerabilities in governance adjustments must be addressed to prevent abuse. The proposal doesn't introduce privacy risks but increases the need for ensuring that any runtime changes do not inadvertently lead to insecure governance structures. Comprehensive tests should be conducted to validate correct track modifications in different governance scenarios.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Testing, Security, and Privacy","id":"142","title":"Testing, Security, and Privacy"},"143":{"body":"","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Performance, Ergonomics, and Compatibility","id":"143","title":"Performance, Ergonomics, and Compatibility"},"144":{"body":"The proposal optimizes governance track management by avoiding the overhead of runtime upgrades, reducing downtime, and eliminating the need for full consensus on upgrades. However, there is a slight performance cost related to runtime access to storage-based iterators, though this is mitigated by the overall system efficiency gains.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Performance","id":"144","title":"Performance"},"145":{"body":"Developers and governance actors benefit from simplified governance processes but must account for the technical complexity of managing iterator-based track configurations. Tools may need to be developed to help streamline track adjustments in runtime.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Ergonomics","id":"145","title":"Ergonomics"},"146":{"body":"The change is backward compatible with existing governance operations, and does not require developers to adjust how they interact with referenda tracks. A migration is required to convert existing statically-defined tracks to dynamic storage-based configurations without disruption.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Compatibility","id":"146","title":"Compatibility"},"147":{"body":"This dynamic governance track approach builds on previous work around Polkadot's on-chain governance and leverages standard iterator patterns in Rust programming to improve runtime flexibility. Comparable solutions in other governance networks were examined, but this proposal uniquely tailors them to Polkadot’s decentralized, runtime-upgradable architecture.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Prior Art and References","id":"147","title":"Prior Art and References"},"148":{"body":"How to handle governance transitions for currently ongoing referenda when changing configuration parameters of an existing track? Ideally, most tracks should not have to go through this change, but some tactics might be applied (like a proposal that reduces the ongoing queue before a major change and then executes the change, after a reasonable period of time has elapsed and no ongoing referenda exists for that track).","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Unresolved Questions","id":"148","title":"Unresolved Questions"},"149":{"body":"There are already two proposed solutions for both the implementation and This Pull Request proposes changing pallet-referenda's TracksInfo to make tracks return an iterator. There is already a proposed implementation of pallet-referenda-tracks , which stores the configurations, and implements TracksInfo using the iterator approach.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Future Directions and Related Material","id":"149","title":"Future Directions and Related Material"},"15":{"body":"Should the MetadataMap and MetadataKeys be bounded, or is it enough to rely on the fact that every XCM message is itself bounded?","breadcrumbs":"RFC-0125: XCM Asset Metadata » Unresolved Questions","id":"15","title":"Unresolved Questions"},"150":{"body":"(source) Table of Contents RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 14.10.2024 Description Store a runtime upgrade in :pending_code before moving it to :code. Authors Bastian Köcher","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code","id":"150","title":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code"},"151":{"body":"The code of a runtime is stored in its own state, and when performing a runtime upgrade, this code is replaced. The new runtime can contain runtime migrations that adapt the state to the state layout as defined by the runtime code. This runtime migration is executed when building the first block with the new runtime code. Anything that interacts with the runtime state uses the state layout as defined by the runtime code. So, when trying to load something from the state in the block that applied the runtime upgrade, it will use the new state layout but will decode the data from the non-migrated state. In the worst case, the data is incorrectly decoded, which may lead to crashes or halting of the chain. This RFC proposes to store the new runtime code under a different storage key when applying a runtime upgrade. This way, all the off-chain logic can still load the old runtime code under the default storage key and decode the state correctly. The block producer is then required to use this new runtime code to build the next block. While building the next block, the runtime is executing the migrations and moves the new runtime code to the default runtime code location. So, the runtime code found under the default location is always the correct one to decode the state from which the runtime code was loaded.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Summary","id":"151","title":"Summary"},"152":{"body":"While the issue of having undecodable state only exists for the one block in which the runtime upgrade was applied, it still impacts anything that reads state data, like block explorers, UIs, nodes, etc. For block explorers, the issue mainly results in indexing invalid data and UIs may show invalid data to the user. For nodes, reading incorrect data may lead to a performance degradation of the network . There are also ways to prevent certain decoding issues from happening, but it requires that developers are aware of this issue and also requires introducing extra code, which could introduce further bugs down the line. So, this RFC tries to solve these issues by fixing the underlying problem of having temporary undecodable state.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Motivation","id":"152","title":"Motivation"},"153":{"body":"Relay chain/Parachain node developers Relay chain/Parachain node operators","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Stakeholders","id":"153","title":"Stakeholders"},"154":{"body":"The runtime code is stored under the special key :code in the state. Nodes and other tooling read the runtime code under this storage key when they want to interact with the runtime for e.g., building/importing blocks or getting the metadata to read the state. To update the runtime code the runtime overwrites the value at :code, and then from the next block on, the new runtime will be loaded. This RFC proposes to first store the new runtime code under :pending_code in the state for one block. When the next block is being built, the block builder first needs to check if :pending_code is set, and if so, it needs to load the runtime from this storage key. While building the block the runtime will move :pending_code to :code to have the runtime code at the default location. Nodes importing the block will also need to load :pending_code if it exists to ensure that the correct runtime code is used. By doing it this way, the runtime code found at :code in the state of a block will always be able to decode the state. Furthermore, this RFC proposes to introduce system_version: 3. The system_version was introduced in RFC42 . Version 3 would then enable the usage of :pending_code when applying a runtime code upgrade. This way, the feature can be introduced first and enabled later when the majority of the nodes have upgraded.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Explanation","id":"154","title":"Explanation"},"155":{"body":"Because the first block built with the new runtime code will move the runtime code from :pending_code to :code, the runtime code will need to be loaded. This means the runtime code will appear in the proof of validity of a parachain for the first block built with the new runtime code. Generally this is not a problem as the runtime code is also loaded by the parachain when setting the new runtime code. There is still the possibility of having state that is not migrated even when following the proposal as presented by this RFC. The issue is that if the amount of data to be migrated is too big, not all of it can be migrated in one block, because either it takes more time than there is assigned for a block or parachains for example have a fixed budget for their proof of validity. To solve this issue there already exist multi-block migrations that can chunk the migration across multiple blocks. Consensus-critical data needs to be migrated in the first block to ensure that block production etc., can continue. For the other data being migrated by multi-block migrations the migrations could for example expose to the outside which keys are being migrated and should not be indexed until the migration is finished.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Drawbacks","id":"155","title":"Drawbacks"},"156":{"body":"Testing should be straightforward and most of the existing testing should already be good enough. Extending with some checks that :pending_code is moved to :code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Testing, Security, and Privacy","id":"156","title":"Testing, Security, and Privacy"},"157":{"body":"","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Performance, Ergonomics, and Compatibility","id":"157","title":"Performance, Ergonomics, and Compatibility"},"158":{"body":"The performance should not be impacted besides requiring loading the runtime code in the first block being built with the new runtime code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Performance","id":"158","title":"Performance"},"159":{"body":"It only alters the way blocks are produced and imported after applying a runtime upgrade. This means that only nodes need to be adapted to the changes of this RFC.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Ergonomics","id":"159","title":"Ergonomics"},"16":{"body":"The original RFC draft contained additional metadata instructions. Though they could be useful, they're clearly outside the basic logic. So, this RFC version omits them to make the metadata discussion more focused on the core things. Nonetheless, there is hope that metadata approval instructions might be useful in the future, so they are mentioned here. You can read about the details in the original draft .","breadcrumbs":"RFC-0125: XCM Asset Metadata » Future Directions and Related Material","id":"16","title":"Future Directions and Related Material"},"160":{"body":"The change will require that the nodes are upgraded before the runtime starts using this feature. Otherwise they will fail to import the block build by :pending_code. For Polkadot/Kusama this means that also the parachain nodes need to be running with a relay chain node version that supports this new feature. Otherwise the parachains will stop producing/finalizing nodes as they can not sync the relay chain any more.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Compatibility","id":"160","title":"Compatibility"},"161":{"body":"The issue initially reported a bug that led to this RFC. It also discusses multiple solutions for the problem.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Prior Art and References","id":"161","title":"Prior Art and References"},"162":{"body":"None","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Unresolved Questions","id":"162","title":"Unresolved Questions"},"163":{"body":"Solve the issue of requiring loading the entire runtime code to move it into a different location by introducing a low-level move function. When using the V1 trie layout every value bigger than 32 bytes is put into the db separately. This means a low level move function would only need to move the hash of the runtime code from :code to :pending_code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Future Directions and Related Material","id":"163","title":"Future Directions and Related Material"},"164":{"body":"(source) Table of Contents RFC-0124: Extrinsic version 5 Summary Motivation Stakeholders Explanation Changes to extrinsic authorization Encoding format for version 5 Signatures on Polkadot in General transactions Summary of changes in version 5 Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 18 October 2024 Description Definition and specification of version 5 extrinsics Authors George Pisaltu","breadcrumbs":"RFC-0124: Extrinsic version 5 » RFC-0124: Extrinsic version 5","id":"164","title":"RFC-0124: Extrinsic version 5"},"165":{"body":"This RFC proposes the definition of version 5 extrinsics along with changes to the specification and encoding from version 4.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Summary","id":"165","title":"Summary"},"166":{"body":"RFC84 introduced the specification of General transactions, a new type of extrinsic besides the Signed and Unsigned variants available previously in version 4. Additionally, RFC99 introduced versioning of transaction extensions through an extra byte in the extrinsic encoding. Both of these changes require an extrinsic format version bump as both the semantics around extensions as well as the actual encoding of extrinsics need to change to accommodate these new features.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Motivation","id":"166","title":"Motivation"},"167":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0124: Extrinsic version 5 » Stakeholders","id":"167","title":"Stakeholders"},"168":{"body":"","breadcrumbs":"RFC-0124: Extrinsic version 5 » Explanation","id":"168","title":"Explanation"},"169":{"body":"The introduction of General transactions allows the authorization of any and all origins through extensions. This means that, with the appropriate extension, General transactions are capable of replicating the same behavior present day v4 Signed transactions. Specifically for Polkadot chains, an example implementation for such an extension is VerifySignature , introduced in the Transaction Extension PR3685 . Other extensions can be inserted into the extension pipeline to authorize different custom origins. Therefore, a Signed extrinsic variant is redundant to a General one strictly in terms of functionality available to users and would eventually need to be deprecated and removed.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Changes to extrinsic authorization","id":"169","title":"Changes to extrinsic authorization"},"17":{"body":"(source) Table of Contents RFC-0126: Introduce XCQ(Cross Consensus Query) Summary Motivation Stakeholders Explanation XCQ Runtime API XCQ Executor XCQ Extension XCQ Program Structure XCQ Program Execution Flow Drawbacks Performance issues User experience issues Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date Oct 25 2024 Description Introduce XCQ (Cross Consensus Query) Authors Bryan Chen, Jiyuan Zheng","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » RFC-0126: Introduce XCQ(Cross Consensus Query)","id":"17","title":"RFC-0126: Introduce XCQ(Cross Consensus Query)"},"170":{"body":"As with version 4, the encoded v5 extrinsics will still be an array of SCALE encoded bytes, starting with the encoded length of the following bytes. The leading byte will determine the version and type of extrinsic, as specified by RFC84 , with the addition that the Signed variant will not be supported for v5 extrinsics, for reasons mentioned above. NOTE: For Bare extrinsics, the following bytes will just be the encoded call and nothing else. For General transactions, as stated in RFC99 , an extension version byte must be added in the next extrinsic version. This byte should allow runtimes to expose more than one set of extensions which can be used for a transaction. As far as the v5 extrinsic encoding is concerned, this extension byte should be encoded immediately after the leading encoding byte. The extension version byte should be included in payloads to be signed by all extensions configured by runtime devs to ensure a user's extension version choice cannot be altered by third parties. After the extension version byte, the extensions will be encoded next, followed by the call itself. A quick visualization of the encoding: Bare extrinsics: (extrinsic_encoded_len, 0b0000_0101, call) General transactions: (extrinsic_encoded_len, , 0b0100_0101, extension_version_byte, extension, call)","breadcrumbs":"RFC-0124: Extrinsic version 5 » Encoding format for version 5","id":"170","title":"Encoding format for version 5"},"171":{"body":"As stated before, PR3685 comes with a Transaction Extension which replicates the current Signed transactions in v5 extrinsics, namely VerifySignature . This extension leverages the new inherited implication functionality introduced in TransactionExtension and creates a payload to be signed using the data of all extensions after itself in the extension pipeline. In order to run a transaction with a signed origin, a user must create the transaction with an instance of the extension which provides a signature. Alternatively, if users want to use some other origin, they should create the transaction with this particular extension disabled. More on this behavior in the extension documentation. This extension can be configured to accept a MultiSignature, which makes it compatible with all signature types currently used in Polkadot. To generate the payload to be signed: The extension version byte, call, extension and extension implicit should be encoded; The result of the encoding should then be hashed using the BLAKE2_256 hasher; The result of the hash should then be signed with the signature type specified in the extension definition. // Step 1: encode the bytes\nlet encoded = (extension_version_byte, call, transaction_extension, transaction_extension_implicit).encode();\n// Step 2: hash them\nlet payload = blake2_256(&encoded[..]);\n// Step 3: sign the payload\nlet signature = keyring.sign(&payload[..]);","breadcrumbs":"RFC-0124: Extrinsic version 5 » Signatures on Polkadot in General transactions","id":"171","title":"Signatures on Polkadot in General transactions"},"172":{"body":"In order to minimize the number of changes to the extrinsic format version and also to help all consumers downstream in the transition period between these extrinsic versions, we should: Remove the Signed variant starting with v5 extrinsics Add the General variant starting with v5 extrinsics Enable runtimes to support both v4 and v5 extrinsics","breadcrumbs":"RFC-0124: Extrinsic version 5 » Summary of changes in version 5","id":"172","title":"Summary of changes in version 5"},"173":{"body":"The metadata will have to accommodate two distinct extrinsic format versions at a given point in time in order to provide the new functionality in a non-breaking way for users and tooling.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Drawbacks","id":"173","title":"Drawbacks"},"174":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Testing, Security, and Privacy","id":"174","title":"Testing, Security, and Privacy"},"175":{"body":"This change makes the authorization through signatures configurable by runtime devs in version 5 extrinsics, as opposed to version 4 where the signing payload algorithm and signatures were hardcoded. This moves the responsibility of ensuring proper authentication through TransactionExtension to the runtime devs, but a sensible default which closely resembles the present day behavior will be provided in VerifySignature.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Performance, Ergonomics, and Compatibility","id":"175","title":"Performance, Ergonomics, and Compatibility"},"176":{"body":"There is no performance impact.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Performance","id":"176","title":"Performance"},"177":{"body":"Tooling will have to adapt to be able to tell which authorization scheme is used by a particular transaction by decoding the extension and checking which particular TransactionExtension in the pipeline is enabled to do the origin authorization. Previously, this was done by simply checking whether the transaction is signed or unsigned, as there was only one method of authentication.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Ergonomics","id":"177","title":"Ergonomics"},"178":{"body":"As long as extrinsic version 4 is still exposed in the metadata when version 5 will be introduced, the changes will not break existing infrastructure. This should give enough time for tooling to support version 5 and to remove version 4 in the future.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Compatibility","id":"178","title":"Compatibility"},"179":{"body":"This is a result of the work in Extrinsic Horizon and RFC99 .","breadcrumbs":"RFC-0124: Extrinsic version 5 » Prior Art and References","id":"179","title":"Prior Art and References"},"18":{"body":"This proposal introduces XCQ (Cross Consensus Query), which aims to serve as an intermediary layer between different chain runtime implementations and tools/UIs, to provide a unified interface for cross-chain queries. XCQ abstracts away concrete implementations across chains and supports custom query computations. Use cases benefiting from XCQ include: XCM bridge UI: Query asset balances Query XCM weight and fee from hop and dest chains Wallets: Query asset balances Query weights and fees for operations across chains Universal dApp that supports all the parachains: Perform Feature discovery Query pallet-specific features Construct extrinsics by querying pallet index, call index, etc","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Summary","id":"18","title":"Summary"},"180":{"body":"There is no clear way to expose two different extrinsic versions in the current metadata framework. A non-exhaustive list of options discussed so far: Change the ExtrinsicMetadata trait to specify a list of versions instead of a single version. Use the custom fields in the metadata to specify the details of the version 5. Create a new trait similar to ExtrinsicMetadata, but for future versions of the extrinsic format and add it to the metadata.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Unresolved Questions","id":"180","title":"Unresolved Questions"},"181":{"body":"Following this change, extrinsic version 5 will be introduced as part of the Extrinsic Horizon effort, which will shape future work.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Future Directions and Related Material","id":"181","title":"Future Directions and Related Material"},"182":{"body":"(source) Table of Contents RFC-114: Adjust Tipper Track Confirmation Periods Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics & Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 17-Aug-24 Description Big and Small Tipper Track Conformation Period Modification Authors Leemo / ChaosDAO","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » RFC-114: Adjust Tipper Track Confirmation Periods","id":"182","title":"RFC-114: Adjust Tipper Track Confirmation Periods"},"183":{"body":"This RFC proposes to change the duration of the Confirmation Period for the Big Tipper and Small Tipper tracks in Polkadot OpenGov: Small Tipper: 10 Minutes -> 12 Hours Big Tipper: 1 Hour -> 1 Day","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Summary","id":"183","title":"Summary"},"184":{"body":"Currently, these are the durations of treasury tracks in Polkadot OpenGov. Confirmation periods for the Spender tracks were adjusted based on RFC20 and its related conversation. Track Description Confirmation Period Duration Treasurer 7 Days Big Spender 7 Days Medium Spender 4 Days Small Spender 2 Days Big Tipper 1 Hour Small Tipper 10 Minutes You can see that there is a general trend on the Spender track that when the privilege level (the amount the track can spend) the confirmation period approximately doubles. I believe that the Big Tipper and Small Tipper track's confirmation periods should be adjusted to match this trend. In the current state it is possible to somewhat positively snipe these tracks, and whilst the power/privilege level of these tracks is very low (they cannot spend a large amount of funds), I believe we should increase the confirmation periods to something higher. This is backed up by the recent sentiment in the greater community regarding referendums submitted on these tracks. The parameters of Polkadot OpenGov can be adjusted based on the general sentiment of token holders when necessary.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Motivation","id":"184","title":"Motivation"},"185":{"body":"The primary stakeholders of this RFC are: – DOT token holders – as this affects the protocol's treasury – Entities wishing to submit a referendum on these tracks – as this affects the referendum's timeline – Projects with governance app integrations – see Performance, Ergonomics and Compatibility section below","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Stakeholders","id":"185","title":"Stakeholders"},"186":{"body":"This RFC proposes to change the duration of the confirmation period for both the Big Tipper and Small Tipper tracks. To achieve this the confirm_period parameter for those tracks should be changed. You can see the lines of code that need to be adjusted here: Big Tipper: https://github.com/polkadot-fellows/runtimes/blob/f4c5d272d4672387771fb038ef52ca36f3429096/relay/polkadot/src/governance/tracks.rs#L245 Small Tipper: https://github.com/polkadot-fellows/runtimes/blob/f4c5d272d4672387771fb038ef52ca36f3429096/relay/polkadot/src/governance/tracks.rs#L231 This RFC proposes to change the confirm_period for the Big Tipper track to DAYS (i.e. 1 Day) and the confirm_period for the Small Tipper track to 12 * HOURS (i.e. 12 Hours).","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Explanation","id":"186","title":"Explanation"},"187":{"body":"The drawback of changing these confirmation periods is that the lifecycle of referenda submitted on those tracks would be ultimately longer, and it would add a greater potential to negatively \"snipe\" referenda on those tracks by knocking the referendum out of its confirmation period once the decision period has ended. This can be a good or a bad thing depending on your outlook of positive vs negative sniping.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Drawbacks","id":"187","title":"Drawbacks"},"188":{"body":"This referendum will enhance the security of the protocol as it relates to its treasury. The confirmation period is one of the last lines of defense for the Polkadot token holder DAO to react to a potentially bad referendum and vote NAY in order for its confirmation period to be aborted.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Testing, Security, and Privacy","id":"188","title":"Testing, Security, and Privacy"},"189":{"body":"","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Performance, Ergonomics, and Compatibility","id":"189","title":"Performance, Ergonomics, and Compatibility"},"19":{"body":"In Substrate, runtime APIs facilitate off-chain clients in reading the state of the consensus system. However, different chains may expose different APIs for a similar query or have varying data types, such as doing custom transformations on direct data, or differing AccountId types. This diversity also extends to client-side, which may require custom computations over runtime APIs in various use cases. Therefore, tools and UI developers often access storage directly and reimplement custom computations to convert data into user-friendly representations, leading to duplicated code between Rust runtime logic and UI JS/TS logic. This duplication increases workload and potential for bugs. Therefore, A system is needed to serve as an intermediary layer between concrete chain runtime implementations and tools/UIs, to provide a unified interface for cross-chain queries.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Motivation","id":"19","title":"Motivation"},"190":{"body":"This is a simple change (code wise) that should not affect the performance of the Polkadot protocol, outside of increasing the duration of the confirmation periods for these 2 tracks.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Performance","id":"190","title":"Performance"},"191":{"body":"As per the implementation of changes described in RFC-20, it was identified that governance UIs automatically update to meet the new parameters: Nova Wallet - directly uses on-chain data, and change will be automatically reflected. Polkassembly - directly uses on-chain data via rpc to fetch trackInfo so the change will be automatically reflected. SubSquare - scan script will update their app to the latest parameters and it will be automatically reflected in their app.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Ergonomics & Compatibility","id":"191","title":"Ergonomics & Compatibility"},"192":{"body":"N/A","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Prior Art and References","id":"192","title":"Prior Art and References"},"193":{"body":"Some token holders may want these confirmation periods to remain as they are currently and for them not to increase. If this is something that the Polkadot Technical Fellowship considers to be an issue to implement into a runtime upgrade then I can create a Wish For Change to obtain token holder approval.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Unresolved Questions","id":"193","title":"Unresolved Questions"},"194":{"body":"The parameters of Polkadot OpenGov will likely continue to change over time, there are additional discussions in the community regarding adjusting the min_support for some tracks so that it does not trend towards 0%, similar to the current state of the Whitelisted Caller track. This is outside of the scope of this RFC and requires a lot more discussion.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Future Directions and Related Material","id":"194","title":"Future Directions and Related Material"},"195":{"body":"(source) Table of Contents RFC-1: Agile Coretime Summary Motivation Present System Problems Requirements Stakeholders Explanation Overview Detail Specific functions of the Coretime-chain Notes on the Instantaneous Coretime Market Notes on Economics Notes on Types Rollout Performance, Ergonomics and Compatibility Testing, Security and Privacy Future Directions and Related Material Drawbacks, Alternatives and Unknowns Prior Art and References Start Date 30 June 2023 Description Agile periodic-sale-based model for assigning Coretime on the Polkadot Ubiquitous Computer. Authors Gavin Wood","breadcrumbs":"RFC-1: Agile Coretime » RFC-1: Agile Coretime","id":"195","title":"RFC-1: Agile Coretime"},"196":{"body":"This proposes a periodic, sale-based method for assigning Polkadot Coretime, the analogue of \"block space\" within the Polkadot Network. The method takes into account the need for long-term capital expenditure planning for teams building on Polkadot, yet also provides a means to allow Polkadot to capture long-term value in the resource which it sells. It supports the possibility of building rich and dynamic secondary markets to optimize resource allocation and largely avoids the need for parameterization.","breadcrumbs":"RFC-1: Agile Coretime » Summary","id":"196","title":"Summary"},"197":{"body":"","breadcrumbs":"RFC-1: Agile Coretime » Motivation","id":"197","title":"Motivation"},"198":{"body":"The Polkadot Ubiquitous Computer , or just Polkadot UC , represents the public service provided by the Polkadot Network. It is a trust-free, WebAssembly-based, multicore, internet-native omnipresent virtual machine which is highly resilient to interference and corruption. The present system of allocating the limited resources of the Polkadot Ubiquitous Computer is through a process known as parachain slot auctions . This is a parachain-centric paradigm whereby a single core is long-term allocated to a single parachain which itself implies a Substrate/Cumulus-based chain secured and connected via the Relay-chain. Slot auctions are on-chain candle auctions which proceed for several days and result in the core being assigned to the parachain for six months at a time up to 24 months in advance. Practically speaking, we only see two year periods being bid upon and leased. Funds behind the bids made in the slot auctions are merely locked, they are not consumed or paid and become unlocked and returned to the bidder on expiry of the lease period. A means of sharing the deposit trustlessly known as a crowdloan is available allowing token holders to contribute to the overall deposit of a chain without any counterparty risk.","breadcrumbs":"RFC-1: Agile Coretime » Present System","id":"198","title":"Present System"},"199":{"body":"The present system is based on a model of one-core-per-parachain. This is a legacy interpretation of the Polkadot platform and is not a reflection of its present capabilities. By restricting ownership and usage to this model, more dynamic and resource-efficient means of utilizing the Polkadot Ubiquitous Computer are lost. More specifically, it is impossible to lease out cores at anything less than six months, and apparently unrealistic to do so at anything less than two years. This removes the ability to dynamically manage the underlying resource, and generally experimentation, iteration and innovation suffer. It bakes into the platform an assumption of permanence for anything deployed into it and restricts the market's ability to find a more optimal allocation of the finite resource. There is no ability to determine capital requirements for hosting a parachain beyond two years from the point of its initial deployment onto Polkadot. While it would be unreasonable to have perfect and indefinite cost predictions for any real-world platform, not having any clarity whatsoever beyond \"market rates\" two years hence can be a very off-putting prospect for teams to buy into. However, quite possibly the most substantial problem is both a perceived and often real high barrier to entry of the Polkadot ecosystem. By forcing innovators to either raise seven-figure sums through investors or appeal to the wider token-holding community, Polkadot makes it difficult for a small band of innovators to deploy their technology into Polkadot. While not being actually permissioned, it is also far from the barrierless, permissionless ideal which an innovation platform such as Polkadot should be striving for.","breadcrumbs":"RFC-1: Agile Coretime » Problems","id":"199","title":"Problems"},"2":{"body":"This RFC proposes a metadata format for XCM-identifiable assets (i.e., for fungible/non-fungible collections and non-fungible tokens) and a set of instructions to communicate it across chains.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Summary","id":"2","title":"Summary"},"20":{"body":"Runtime Developers Tools/UI Developers","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Stakeholders","id":"20","title":"Stakeholders"},"200":{"body":"The solution SHOULD provide an acceptable value-capture mechanism for the Polkadot network. The solution SHOULD allow parachains and other projects deployed on to the Polkadot UC to make long-term capital expenditure predictions for the cost of ongoing deployment. The solution SHOULD minimize the barriers to entry in the ecosystem. The solution SHOULD work well when the Polkadot UC has up to 1,000 cores. The solution SHOULD work when the number of cores which the Polkadot UC can support changes over time. The solution SHOULD facilitate the optimal allocation of work to cores of the Polkadot UC, including by facilitating the trade of regular core assignment at various intervals and for various spans. The solution SHOULD avoid creating additional dependencies on functionality which the Relay-chain need not strictly provide for the delivery of the Polkadot UC. Furthermore, the design SHOULD be implementable and deployable in a timely fashion; three months from the acceptance of this RFC should not be unreasonable.","breadcrumbs":"RFC-1: Agile Coretime » Requirements","id":"200","title":"Requirements"},"201":{"body":"Primary stakeholder sets are: Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division. Polkadot Parachain teams both present and future, and their users. Polkadot DOT token holders. Socialization: The essensials of this proposal were presented at Polkadot Decoded 2023 Copenhagen on the Main Stage. A small amount of socialization at the Parachain Summit preceeded it and some substantial discussion followed it. Parity Ecosystem team is currently soliciting views from ecosystem teams who would be key stakeholders.","breadcrumbs":"RFC-1: Agile Coretime » Stakeholders","id":"201","title":"Stakeholders"},"202":{"body":"","breadcrumbs":"RFC-1: Agile Coretime » Explanation","id":"202","title":"Explanation"},"203":{"body":"Upon implementation of this proposal, the parachain-centric slot auctions and associated crowdloans cease. Instead, Coretime on the Polkadot UC is sold by the Polkadot System in two separate formats: Bulk Coretime and Instantaneous Coretime . When a Polkadot Core is utilized, we say it is dedicated to a Task rather than a \"parachain\". The Task to which a Core is dedicated may change at every Relay-chain block and while one predominant type of Task is to secure a Cumulus-based blockchain (i.e. a parachain), other types of Tasks are envisioned. Bulk Coretime is sold periodically on a specialised system chain known as the Coretime-chain and allocated in advance of its usage, whereas Instantaneous Coretime is sold on the Relay-chain immediately prior to usage on a block-by-block basis. This proposal does not fix what should be done with revenue from sales of Coretime and leaves it for a further RFC process. Owners of Bulk Coretime are tracked on the Coretime-chain and the ownership status and properties of the owned Coretime are exposed over XCM as a non-fungible asset. At the request of the owner, the Coretime-chain allows a single Bulk Coretime asset, known as a Region , to be used in various ways including transferal to another owner, allocated to a particular task (e.g. a parachain) or placed in the Instantaneous Coretime Pool. Regions can also be split out, either into non-overlapping sub-spans or exactly-overlapping spans with less regularity. The Coretime-Chain periodically instructs the Relay-chain to assign its cores to alternative tasks as and when Core allocations change due to new Regions coming into effect. Renewal and Migration There is a renewal system which allows a Bulk Coretime assignment of a single core to be renewed unchanged with a known price increase from month to month. Renewals are processed in a period prior to regular purchases, effectively giving them precedence over a fixed number of cores available. Renewals are only enabled when a core's assignment does not include an Instantaneous Coretime allocation and has not been split into shorter segments. Thus, renewals are designed to ensure only that committed parachains get some guarantees about price for predicting future costs. This price-capped renewal system only allows cores to be reused for their same tasks from month to month. In any other context, Bulk Coretime would need to be purchased regularly. As a migration mechanism, pre-existing leases (from the legacy lease/slots/crowdloan framework) are initialized into the Coretime-chain and cores assigned to them prior to Bulk Coretime sales. In the sale where the lease expires, the system offers a renewal, as above, to allow a priority sale of Bulk Coretime and ensure that the Parachain suffers no downtime when transitioning from the legacy framework. Instantaneous Coretime Processing of Instantaneous Coretime happens in part on the Polkadot Relay-chain. Credit is purchased on the Coretime-chain for regular DOT tokens, and this results in a DOT-denominated Instantaneous Coretime Credit account on the Relay-chain being credited for the same amount. Though the Instantaneous Coretime Credit account records a balance for an account identifier (very likely controlled by a collator), it is non-transferable and non-refundable . It can only be consumed in order to purchase some Instantaneous Coretime with immediate availability. The Relay-chain reports this usage back to the Coretime-chain in order to allow it to reward the providers of the underlying Coretime, either the Polkadot System or owners of Bulk Coretime who contributed to the Instantaneous Coretime Pool. Specifically the Relay-chain is expected to be responsible for: holding non-transferable, non-refundable DOT-denominated Instantaneous Coretime Credit balance information. setting and adjusting the price of Instantaneous Coretime based on usage. allowing collators to consume their Instantaneous Coretime Credit at the current pricing in exchange for the ability to schedule one PoV for near-immediate usage. ensuring the Coretime-Chain has timely accounting information on Instantaneous Coretime Sales revenue. Coretime-chain The Coretime-chain is a new system parachain. It has the responsibility of providing the Relay-chain via UMP with information of: The number of cores which should be made available. Which tasks should be running on which cores and in what ratios. Accounting information for Instantaneous Coretime Credit. It also expects information from the Relay-chain via DMP: The number of cores available to be scheduled. Account information on Instantaneous Coretime Sales. The specific interface is properly described in RFC-5.","breadcrumbs":"RFC-1: Agile Coretime » Overview","id":"203","title":"Overview"},"204":{"body":"Parameters This proposal includes a number of parameters which need not necessarily be fixed. Their usage is explained below, but their values are suggested or specified in the later section Parameter Values . Reservations and Leases The Coretime-chain includes some governance-set reservations of Coretime; these cover every System-chain. Additionally, governance is expected to initialize details of the pre-existing leased chains. Regions A Region is an assignable period of Coretime with a known regularity. All Regions are associated with a unique Core Index , to identify which core the assignment of which ownership of the Region controls. All Regions are also associated with a Core Mask , an 80-bit bitmap, to denote the regularity at which it may be scheduled on the core. If all bits are set in the Core Mask value, it is said to be Complete . 80 is selected since this results in the size of the datatype used to identify any Region of Polkadot Coretime to be a very convenient 128-bit. Additionally, if TIMESLICE (the number of Relay-chain blocks in a Timeslice) is 80, then a single bit in the Core Mask bitmap represents exactly one Core for one Relay-chain block in one Timeslice. All Regions have a span. Region spans are quantized into periods of TIMESLICE blocks; BULK_PERIOD divides into TIMESLICE a whole number of times. The Timeslice type is a u32 which can be multiplied by TIMESLICE to give a BlockNumber value representing the same quantity in terms of Relay-chain blocks. Regions can be tasked to a TaskId (aka ParaId) or pooled into the Instantaneous Coretime Pool. This process can be Provisional or Final . If done only provisionally or not at all then they are fresh and have an Owner which is able to manipulate them further including reassignment. Once Final , then all ownership information is discarded and they cannot be manipulated further. Renewal is not possible when only provisionally tasked/pooled. Bulk Sales A sale of Bulk Coretime occurs on the Coretime-chain every BULK_PERIOD blocks. In every sale, a BULK_LIMIT of individual Regions are offered for sale. Each Region offered for sale has a different Core Index, ensuring that they each represent an independently allocatable resource on the Polkadot UC. The Regions offered for sale have the same span: they last exactly BULK_PERIOD blocks, and begin immediately following the span of the previous Sale's Regions. The Regions offered for sale also have the complete, non-interlaced, Core Mask. The Sale Period ends immediately as soon as span of the Coretime Regions that are being sold begins. At this point, the next Sale Price is set according to the previous Sale Price together with the number of Regions sold compared to the desired and maximum amount of Regions to be sold. See Price Setting for additional detail on this point. Following the end of the previous Sale Period, there is an Interlude Period lasting INTERLUDE_PERIOD of blocks. After this period is elapsed, regular purchasing begins with the Purchasing Period . This is designed to give at least two weeks worth of time for the purchased regions to be partitioned, interlaced, traded and allocated. The Interlude The Interlude period is a period prior to Regular Purchasing where renewals are allowed to happen. This has the effect of ensuring existing long-term tasks/parachains have a chance to secure their Bulk Coretime for a well-known price prior to general sales. Regular Purchasing Any account may purchase Regions of Bulk Coretime if they have the appropriate funds in place during the Purchasing Period, which is from INTERLUDE_PERIOD blocks after the end of the previous sale until the beginning of the Region of the Bulk Coretime which is for sale as long as there are Regions of Bulk Coretime left for sale (i.e. no more than BULK_LIMIT have already been sold in the Bulk Coretime Sale). The Purchasing Period is thus roughly BULK_PERIOD - INTERLUDE_PERIOD blocks in length. The Sale Price varies during an initial portion of the Purchasing Period called the Leadin Period and then stays stable for the remainder. This initial portion is LEADIN_PERIOD blocks in duration. During the Leadin Period the price decreases towards the Sale Price, which it lands at by the end of the Leadin Period. The actual curve by which the price starts and descends to the Sale Price is outside the scope of this RFC, though a basic suggestion is provided in the Price Setting Notes, below. Renewals At any time when there are remaining Regions of Bulk Coretime to be sold, including during the Interlude Period , then certain Bulk Coretime assignmnents may be Renewed . This is similar to a purchase in that funds must be paid and it consumes one of the Regions of Bulk Coretime which would otherwise be placed for purchase. However there are two key differences. Firstly, the price paid is the minimum of RENEWAL_PRICE_CAP more than what the purchase/renewal price was in the previous renewal and the current (or initial, if yet to begin) regular Sale Price. Secondly, the purchased Region comes preassigned with exactly the same workload as before. It cannot be traded, repartitioned, interlaced or exchanged. As such unlike regular purchasing the Region never has an owner. Renewal is only possible for either cores which have been assigned as a result of a previous renewal, which are migrating from legacy slot leases, or which fill their Bulk Coretime with an unsegmented, fully and finally assigned workload which does not include placement in the Instantaneous Coretime Pool. The renewed workload will be the same as this initial workload. Manipulation Regions may be manipulated in various ways by its owner: Transferred in ownership. Partitioned into quantized, non-overlapping segments of Bulk Coretime with the same ownership. Interlaced into multiple Regions over the same period whose eventual assignments take turns to be scheduled. Assigned to a single, specific task (identified by TaskId aka ParaId). This may be either provisional or final . Pooled into the Instantaneous Coretime Pool, in return for a pro-rata amount of the revenue from the Instantaneous Coretime Sales over its period. Enactment","breadcrumbs":"RFC-1: Agile Coretime » Detail","id":"204","title":"Detail"},"205":{"body":"Several functions of the Coretime-chain SHALL be exposed through dispatchables and/or a nonfungible trait implementation integrated into XCM: 1. transfer Regions may have their ownership transferred. A transfer(region: RegionId, new_owner: AccountId) dispatchable shall have the effect of altering the current owner of the Region identified by region from the signed origin to new_owner. An implementation of the nonfungible trait SHOULD include equivalent functionality. RegionId SHOULD be used for the AssetInstance value. 2. partition Regions may be split apart into two non-overlapping interior Regions of the same Core Mask which together concatenate to the original Region. A partition(region: RegionId, pivot: Timeslice) dispatchable SHALL have the effect of removing the Region identified by region and adding two new Regions of the same owner and Core Mask. One new Region will begin at the same point of the old Region but end at pivot timeslices into the Region, whereas the other will begin at this point and end at the end point of the original Region. Also: owner field of region must the equal to the Signed origin. pivot must equal neither the begin nor end fields of the region. 3. interlace Regions may be decomposed into two Regions of the same span whose eventual assignments take turns on the core by virtue of having complementary Core Masks. An interlace(region: RegionId, mask: CoreMask) dispatchable shall have the effect of removing the Region identified by region and creating two new Regions. The new Regions will each have the same span and owner of the original Region, but one Region will have a Core Mask equal to mask and the other will have Core Mask equal to the XOR of mask and the Core Mask of the original Region. Also: owner field of region must the equal to the Signed origin. mask must have some bits set AND must not equal the Core Mask of the old Region AND must only have bits set which are also set in the old Region's' Core Mask. 4. assign Regions may be assigned to a core. A assign(region: RegionId, target: TaskId, finality: Finality) dispatchable shall have the effect of placing an item in the workplan corresponding to the region's properties and assigned to the target task. If the region's end has already passed (taking into account any advance notice requirements) then this operation is a no-op. If the region's begining has already passed, then it is effectively altered to become the next schedulable timeslice. finality may have the value of either Final or Provisional. If Final, then the operation is free, the region record is removed entirely from storage and renewal may be possible: if the Region's span is the entire BULK_PERIOD, then the Coretime-chain records in storage that the allocation happened during this period in order to facilitate the possibility for a renewal. (Renewal only becomes possible when the full Core Mask of a core is finally assigned for the full BULK_PERIOD.) Also: owner field of region must the equal to the Signed origin. 5. pool Regions may be consumed in exchange for a pro rata portion of the Instantaneous Coretime Sales Revenue from its period and regularity. A pool(region: RegionId, beneficiary: AccountId, finality: Finality) dispatchable shall have the effect of placing an item in the workplan corresponding to the region's properties and assigned to the Instantaneous Coretime Pool. The details of the region will be recorded in order to allow for a pro rata share of the Instantaneous Coretime Sales Revenue at the time of the Region relative to any other providers in the Pool. If the region's end has already passed (taking into account any advance notice requirements) then this operation is a no-op. If the region's begining has already passed, then it is effectively altered to become the next schedulable timeslice. finality may have the value of either Final or Provisional. If Final, then the operation is free and the region record is removed entirely from storage. Also: owner field of region must the equal to the Signed origin. 6. Purchases A dispatchable purchase(price_limit: Balance) shall be provided. Any account may call purchase to purchase Bulk Coretime at the maximum price of price_limit. This may be called successfully only: during the regular Purchasing Period; when the caller is a Signed origin and their account balance is reducible by the current sale price; when the current sale price is no greater than price_limit; and when the number of cores already sold is less than BULK_LIMIT. If successful, the caller's account balance is reduced by the current sale price and a new Region item for the following Bulk Coretime span is issued with the owner equal to the caller's account. 7. Renewals A dispatchable renew(core: CoreIndex) shall be provided. Any account may call renew to purchase Bulk Coretime and renew an active allocation for the given core. This may be called during the Interlude Period as well as the regular Purchasing Period and has the same effect as purchase followed by assign, except that: The price of the sale is the Renewal Price (see next). The Region is allocated exactly the given core is currently allocated for the present Region. Renewal is only valid where a Region's span is assigned to Tasks (not placed in the Instantaneous Coretime Pool) for the entire unsplit BULK_PERIOD over all of the Core Mask and with Finality. There are thus three possibilities of a renewal being allowed: Purchased unsplit Coretime with final assignment to tasks over the full Core Mask. Renewed Coretime. A legacy lease which is ending. Renewal Price The Renewal Price is the minimum of the current regular Sale Price (or the initial Sale Price if in the Interlude Period) and: If the workload being renewed came to be through the Purchase and Assignment of Bulk Coretime, then the price paid during that Purchase operation. If the workload being renewed was previously renewed, then the price paid during this previous Renewal operation plus RENEWAL_PRICE_CAP. If the workload being renewed is a migation from a legacy slot auction lease, then the nominal price for a Regular Purchase (outside of the Lead-in Period) of the Sale during which the legacy lease expires. 8. Instantaneous Coretime Credits A dispatchable purchase_credit(amount: Balance, beneficiary: RelayChainAccountId) shall be provided. Any account with at least amount spendable funds may call this. This increases the Instantaneous Coretime Credit balance on the Relay-chain of the beneficiary by the given amount. This Credit is consumable on the Relay-chain as part of the Task scheduling system and its specifics are out of the scope of this proposal. When consumed, revenue is recorded and provided to the Coretime-chain for proper distribution. The API for doing this is specified in RFC-5.","breadcrumbs":"RFC-1: Agile Coretime » Specific functions of the Coretime-chain","id":"205","title":"Specific functions of the Coretime-chain"},"206":{"body":"For an efficient market to form around the provision of Bulk-purchased Cores into the pool of cores available for Instantaneous Coretime purchase, it is crucial to ensure that price changes for the purchase of Instantaneous Coretime are reflected well in the revenues of private Coretime providers during the same period. In order to ensure this, then it is crucial that Instantaneous Coretime, once purchased, cannot be held indefinitely prior to eventual use since, if this were the case, a nefarious collator could purchase Coretime when cheap and utilize it some time later when expensive and deprive private Coretime providers of their revenue. It must therefore be assumed that Instantaneous Coretime, once purchased, has a definite and short \"shelf-life\", after which it becomes unusable. This incentivizes collators to avoid purchasing Coretime unless they expect to utilize it imminently and thus helps create an efficient market-feedback mechanism whereby a higher price will actually result in material revenues for private Coretime providers who contribute to the pool of Cores available to service Instantaneous Coretime purchases.","breadcrumbs":"RFC-1: Agile Coretime » Notes on the Instantaneous Coretime Market","id":"206","title":"Notes on the Instantaneous Coretime Market"},"207":{"body":"The specific pricing mechanisms are out of scope for the present proposal. Proposals on economics should be properly described and discussed in another RFC. However, for the sake of completeness, I provide some basic illustration of how price setting could potentially work. Bulk Price Progression The present proposal assumes the existence of a price-setting mechanism which takes into account several parameters: OLD_PRICE: The price of the previous sale. BULK_TARGET: the target number of cores to be purchased as Bulk Coretime Regions or renewed during the previous sale. BULK_LIMIT: the maximum number of cores which could have been purchased/renewed during the previous sale. CORES_SOLD: the actual number of cores purchased/renewed in the previous sale. SELLOUT_PRICE: the price at which the most recent Bulk Coretime was purchased ( not renewed) prior to selling more cores than BULK_TARGET (or immediately after, if none were purchased before). This may not have a value if no Bulk Coretime was purchased. In general we would expect the price to increase the closer CORES_SOLD gets to BULK_LIMIT and to decrease the closer it gets to zero. If it is exactly equal to BULK_TARGET, then we would expect the price to remain the same. In the edge case that no cores were purchased yet more cores were sold (through renewals) than the target, then we would also avoid altering the price. A simple example of this would be the formula: IF SELLOUT_PRICE == NULL AND CORES_SOLD > BULK_TARGET THEN RETURN OLD_PRICE\nEND IF\nEFFECTIVE_PRICE := IF CORES_SOLD > BULK_TARGET THEN SELLOUT_PRICE\nELSE OLD_PRICE\nEND IF\nNEW_PRICE := IF CORES_SOLD < BULK_TARGET THEN EFFECTIVE_PRICE * MAX(CORES_SOLD, 1) / BULK_TARGET\nELSE EFFECTIVE_PRICE + EFFECTIVE_PRICE * (CORES_SOLD - BULK_TARGET) / (BULK_LIMIT - BULK_TARGET)\nEND IF This exists only as a trivial example to demonstrate a basic solution exists, and should not be intended as a concrete proposal. Intra-Leadin Price-decrease During the Leadin Period of a sale, the effective price starts higher than the Sale Price and falls to end at the Sale Price at the end of the Leadin Period. The price can thus be defined as a simple factor above one on which the Sale Price is multiplied. A function which returns this factor would accept a factor between zero and one specifying the portion of the Leadin Period which has passed. Thus we assume SALE_PRICE, then we can define PRICE as: PRICE := SALE_PRICE * FACTOR((NOW - LEADIN_BEGIN) / LEADIN_PERIOD) We can define a very simple progression where the price decreases monotonically from double the Sale Price at the beginning of the Leadin Period. FACTOR(T) := 2 - T Parameter Values Parameters are either suggested or specified . If suggested , it is non-binding and the proposal should not be judged on the value since other RFCs and/or the governance mechanism of Polkadot is expected to specify/maintain it. If specified , then the proposal should be judged on the merit of the value as-is. Name Value BULK_PERIOD 28 * DAYS specified INTERLUDE_PERIOD 7 * DAYS specified LEADIN_PERIOD 7 * DAYS specified TIMESLICE 8 * MINUTES specified BULK_TARGET 30 suggested BULK_LIMIT 45 suggested RENEWAL_PRICE_CAP Perbill::from_percent(2) suggested Instantaneous Price Progression This proposal assumes the existence of a Relay-chain-based price-setting mechanism for the Instantaneous Coretime Market which alters from block to block, taking into account several parameters: the last price, the size of the Instantaneous Coretime Pool (in terms of cores per Relay-chain block) and the amount of Instantaneous Coretime waiting for processing (in terms of Core-blocks queued). The ideal situation is to have the size of the Instantaneous Coretime Pool be equal to some factor of the Instantaneous Coretime waiting. This allows all Instantaneous Coretime sales to be processed with some limited latency while giving limited flexibility over ordering to the Relay-chain apparatus which is needed for efficient operation. If we set a factor of three, and thus aim to retain a queue of Instantaneous Coretime Sales which can be processed within three Relay-chain blocks, then we would increase the price if the queue goes above three times the amount of cores available, and decrease if it goes under. Let us assume the values OLD_PRICE, FACTOR, QUEUE_SIZE and POOL_SIZE. A simple definition of the NEW_PRICE would be thus: NEW_PRICE := IF QUEUE_SIZE < POOL_SIZE * FACTOR THEN OLD_PRICE * 0.95\nELSE OLD_PRICE / 0.95\nEND IF This exists only as a trivial example to demonstrate a basic solution exists, and should not be intended as a concrete proposal.","breadcrumbs":"RFC-1: Agile Coretime » Notes on Economics","id":"207","title":"Notes on Economics"},"208":{"body":"This exists only as a short illustration of a potential technical implementation and should not be treated as anything more. Regions This data schema achieves a number of goals: Coretime can be individually traded at a level of a single usage of a single core. Coretime Regions, of arbitrary span and up to 1/80th interlacing can be exposed as NFTs and exchanged. Any Coretime Region can be contributed to the Instantaneous Coretime Pool. Unlimited number of individual Coretime contributors to the Instantaneous Coretime Pool. (Effectively limited only in number of cores and interlacing level; with current values this would allow 80,000 individual payees per timeslice). All keys are self-describing. Workload to communicate core (re-)assignments is well-bounded and low in weight. All mandatory bookkeeping workload is well-bounded in weight. type Timeslice = u32; // 80 block amounts.\ntype CoreIndex = u16;\ntype CoreMask = [u8; 10]; // 80-bit bitmap. // 128-bit (16 bytes)\nstruct RegionId { begin: Timeslice, core: CoreIndex, mask: CoreMask,\n}\n// 296-bit (37 bytes)\nstruct RegionRecord { end: Timeslice, owner: AccountId,\n} map Regions = Map; // 40-bit (5 bytes). Could be 32-bit with a more specialised type.\nenum CoreTask { Off, Assigned { target: TaskId }, InstaPool,\n}\n// 120-bit (15 bytes). Could be 14 bytes with a specialised 32-bit `CoreTask`.\nstruct ScheduleItem { mask: CoreMask, // 80 bit task: CoreTask, // 40 bit\n} /// The work we plan on having each core do at a particular time in the future.\ntype Workplan = Map<(Timeslice, CoreIndex), BoundedVec>;\n/// The current workload of each core. This gets updated with workplan as timeslices pass.\ntype Workload = Map>; enum Contributor { System, Private(AccountId),\n} struct ContributionRecord { begin: Timeslice, end: Timeslice, core: CoreIndex, mask: CoreMask, payee: Contributor,\n}\ntype InstaPoolContribution = Map; type SignedTotalMaskBits = u32;\ntype InstaPoolIo = Map; type PoolSize = Value; /// Counter for the total CoreMask which could be dedicated to a pool. `u32` so we don't ever get\n/// an overflow.\ntype TotalMaskBits = u32;\nstruct InstaPoolHistoryRecord { total_contributions: TotalMaskBits, maybe_payout: Option,\n}\n/// Total InstaPool rewards for each Timeslice and the number of core Mask which contributed.\ntype InstaPoolHistory = Map; CoreMask tracks unique \"parts\" of a single core. It is used with interlacing in order to give a unique identifier to each component of any possible interlacing configuration of a core, allowing for simple self-describing keys for all core ownership and allocation information. It also allows for each core's workload to be tracked and updated progressively, keeping ongoing compute costs well-bounded and low. Regions are issued into the Regions map and can be transferred, partitioned and interlaced as the owner desires. Regions can only be tasked if they begin after the current scheduling deadline (if they have missed this, then the region can be auto-trimmed until it is). Once tasked, they are removed from there and a record is placed in Workplan. In addition, if they are contributed to the Instantaneous Coretime Pool, then an entry is placing in InstaPoolContribution and InstaPoolIo. Each timeslice, InstaPoolIo is used to update the current value of PoolSize. A new entry in InstaPoolHistory is inserted, with the total_contributions field of InstaPoolHistoryRecord being informed by the PoolSize value. Each core's has its Workload mutated according to its Workplan for the upcoming timeslice. When Instantaneous Coretime Market Revenues are reported for a particular timeslice from the Relay-chain, this information gets placed in the maybe_payout field of the relevant record of InstaPoolHistory. Payments can be requested made for any records in InstaPoolContribution whose begin is the key for a value in InstaPoolHistory whose maybe_payout is Some. In this case, the total_contributions is reduced by the ContributionRecord's mask and a pro rata amount paid. The ContributionRecord is mutated by incrementing begin, or removed if begin becomes equal to end. Example: // Simple example with a `u16` `CoreMask` and bulk sold in 100 timeslices.\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// First split @ 50\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_1111_1111u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Share half of first 50 blocks\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Sell half of them to Bob\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob splits first 10 and assigns them to himself.\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 110u32, owner: Bob };\n{ core: 0u16, begin: 110, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob shares first 10 3 ways and sells smaller shares to Charlie and Dave\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1100_0000u16 } => { end: 110u32, owner: Charlie };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_0011_0000u16 } => { end: 110u32, owner: Dave };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_0000_1111u16 } => { end: 110u32, owner: Bob };\n{ core: 0u16, begin: 110, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob assigns to his para B, Charlie and Dave assign to their paras C and D; Alice assigns first 50 to A\nRegions:\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\nWorkplan:\n(100, 0) => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\n(110, 0) => vec![{ mask: 0b0000_0000_1111_1111u16, task: Assigned(B) }]\n// Alice assigns her remaining 50 timeslices to the InstaPool paying herself:\nRegions: (empty)\nWorkplan:\n(100, 0) => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\n(110, 0) => vec![{ mask: 0b0000_0000_1111_1111u16, task: Assigned(B) }]\n(150, 0) => vec![{ mask: 0b1111_1111_1111_1111u16, task: InstaPool }]\nInstaPoolContribution:\n{ begin: 150, end: 200, core: 0, mask: 0b1111_1111_1111_1111u16, payee: Alice }\nInstaPoolIo:\n150 => 16\n200 => -16\n// Actual notifications to relay chain.\n// Assumes:\n// - Timeslice is 10 blocks.\n// - Timeslice 0 begins at block #1000.\n// - Relay needs 10 blocks notice of change.\n//\nWorkload: 0 => vec![]\nPoolSize: 0 // Block 990:\nRelay <= assign_core(core: 0u16, begin: 1000, assignment: vec![(A, 8), (C, 2), (D, 2), (B, 4)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\nPoolSize: 0 // Block 1090:\nRelay <= assign_core(core: 0u16, begin: 1100, assignment: vec![(A, 8), (B, 8)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1111_1111u16, task: Assigned(B) },\n]\nPoolSize: 0 // Block 1490:\nRelay <= assign_core(core: 0u16, begin: 1500, assignment: vec![(Pool, 16)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_1111_1111u16, task: InstaPool },\n]\nPoolSize: 16\nInstaPoolIo:\n200 => -16\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: None } // Sometime after block 1500:\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: Some(P) } // Sometime after block 1990:\nInstaPoolIo: (empty)\nPoolSize: 0\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: Some(P0) }\n151 => { total_contributions: 16, maybe_payout: Some(P1) }\n152 => { total_contributions: 16, maybe_payout: Some(P2) }\n...\n199 => { total_contributions: 16, maybe_payout: Some(P49) } // Sometime later still Alice calls for a payout\nInstaPoolContribution: (empty)\nInstaPoolHistory: (empty)\n// Alice gets rewarded P0 + P1 + ... P49.","breadcrumbs":"RFC-1: Agile Coretime » Notes on Types","id":"208","title":"Notes on Types"},"209":{"body":"Rollout of this proposal comes in several phases: Finalise the specifics of implementation; this may be done through a design document or through a well-documented prototype implementation. Implement the design, including all associated aspects such as unit tests, benchmarks and any support software needed. If any new parachain is required, launch of this. Formal audit of the implementation and any manual testing. Announcement to the various stakeholders of the imminent changes. Software integration and release. Governance upgrade proposal(s). Monitoring of the upgrade process.","breadcrumbs":"RFC-1: Agile Coretime » Rollout","id":"209","title":"Rollout"},"21":{"body":"The overall query pattern of the XCQ consists of three components: Runtime: View-functions across different pallets are amalgamated through an extension-based system. XCQ query: Custom computations over view-function results are encapsulated via PolkaVM programs. XCQ query arguments: Query arguments like accounts to be queried are also passed together with the query program.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Explanation","id":"21","title":"Explanation"},"210":{"body":"No specific considerations. Parachains already deployed into the Polkadot UC must have a clear plan of action to migrate to an agile Coretime market. While this proposal does not introduce documentable features per se, adequate documentation must be provided to potential purchasers of Polkadot Coretime. This SHOULD include any alterations to the Polkadot-SDK software collection.","breadcrumbs":"RFC-1: Agile Coretime » Performance, Ergonomics and Compatibility","id":"210","title":"Performance, Ergonomics and Compatibility"},"211":{"body":"Regular testing through unit tests, integration tests, manual testnet tests, zombie-net tests and fuzzing SHOULD be conducted. A regular security review SHOULD be conducted prior to deployment through a review by the Web3 Foundation economic research group. Any final implementation MUST pass a professional external security audit. The proposal introduces no new privacy concerns.","breadcrumbs":"RFC-1: Agile Coretime » Testing, Security and Privacy","id":"211","title":"Testing, Security and Privacy"},"212":{"body":"RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain. RFC-5 proposes the API for interacting with Relay-chain. Additional work should specify the interface for the instantaneous market revenue so that the Coretime-chain can ensure Bulk Coretime placed in the instantaneous market is properly compensated.","breadcrumbs":"RFC-1: Agile Coretime » Future Directions and Related Material","id":"212","title":"Future Directions and Related Material"},"213":{"body":"Unknowns include the economic and resource parameterisations: The initial price of Bulk Coretime. The price-change algorithm between Bulk Coretime sales. The price increase per Bulk Coretime period for renewals. The price decrease graph in the Leadin period for Bulk Coretime sales. The initial price of Instantaneous Coretime. The price-change algorithm for Instantaneous Coretime sales. The percentage of cores to be sold as Bulk Coretime. The fate of revenue collected.","breadcrumbs":"RFC-1: Agile Coretime » Drawbacks, Alternatives and Unknowns","id":"213","title":"Drawbacks, Alternatives and Unknowns"},"214":{"body":"Robert Habermeier initially wrote on the subject of Polkadot blockspace-centric in the article Polkadot Blockspace over Blockchains . While not going into details, the article served as an early reframing piece for moving beyond one-slot-per-chain models and building out secondary market infrastructure for resource allocation.","breadcrumbs":"RFC-1: Agile Coretime » Prior Art and References","id":"214","title":"Prior Art and References"},"215":{"body":"(source) Table of Contents RFC-5: Coretime Interface Summary Motivation Requirements Stakeholders Explanation UMP Message Types DMP Message Types Realistic Limits of the Usage Performance, Ergonomics and Compatibility Testing, Security and Privacy Future Directions and Related Material Drawbacks, Alternatives and Unknowns Prior Art and References Start Date 06 July 2023 Description Interface for manipulating the usage of cores on the Polkadot Ubiquitous Computer. Authors Gavin Wood, Robert Habermeier","breadcrumbs":"RFC-5: Coretime Interface » RFC-5: Coretime Interface","id":"215","title":"RFC-5: Coretime Interface"},"216":{"body":"In the Agile Coretime model of the Polkadot Ubiquitous Computer, as proposed in RFC-1 and RFC-3, it is necessary for the allocating parachain (envisioned to be one or more pallets on a specialised Brokerage System Chain) to communicate the core assignments to the Relay-chain, which is responsible for ensuring those assignments are properly enacted. This is a proposal for the interface which will exist around the Relay-chain in order to communicate this information and instructions.","breadcrumbs":"RFC-5: Coretime Interface » Summary","id":"216","title":"Summary"},"217":{"body":"The background motivation for this interface is splitting out coretime allocation functions and secondary markets from the Relay-chain onto System parachains. A well-understood and general interface is necessary for ensuring the Relay-chain receives coretime allocation instructions from one or more System chains without introducing dependencies on the implementation details of either side.","breadcrumbs":"RFC-5: Coretime Interface » Motivation","id":"217","title":"Motivation"},"218":{"body":"The interface MUST allow the Relay-chain to be scheduled on a low-latency basis. Individual cores MUST be schedulable, both in full to a single task (a ParaId or the Instantaneous Coretime Pool) or to many unique tasks in differing ratios. Typical usage of the interface SHOULD NOT overload the VMP message system. The interface MUST allow for the allocating chain to be notified of all accounting information relevant for making accurate rewards for contributing to the Instantaneous Coretime Pool. The interface MUST allow for Instantaneous Coretime Market Credits to be communicated. The interface MUST allow for the allocating chain to instruct changes to the number of cores which it is able to allocate. The interface MUST allow for the allocating chain to be notified of changes to the number of cores which are able to be allocated by the allocating chain.","breadcrumbs":"RFC-5: Coretime Interface » Requirements","id":"218","title":"Requirements"},"219":{"body":"Primary stakeholder sets are: Developers of the Relay-chain core-management logic. Developers of the Brokerage System Chain and its pallets. Socialization: This content of this RFC was discussed in the Polkdot Fellows channel.","breadcrumbs":"RFC-5: Coretime Interface » Stakeholders","id":"219","title":"Stakeholders"},"22":{"body":"The runtime API for off-chain query usage includes two methods: execute_query: Executes the query and returns the result. It takes the query, input, and weight limit as arguments. The query is the query program in PolkaVM program binary format. The input is the query arguments that is SCALE-encoded. The weight limit is the maximum weight allowed for the query execution. metadata: Return metadata of supported extensions (introduced in later section) and methods, serving as a feature discovery functionality Example XCQ Runtime API : decl_runtime_apis! { pub trait XcqApi { fn execute_query(query: Vec, input: Vec, weight_limit: u64) -> XcqResult; fn metadata() -> Vec; }\n}\ntype XcqResult = Result;\ntype XcqResponse = Vec;\nenum XcqError { Custom(String),\n} Example metadata : Metadata { extensions: vec![ ExtensionMetadata { name: \"ExtensionCore\", methods: vec![MethodMetadata { name: \"has_extension\", inputs: vec![MethodParamMetadata { name: \"id\", ty: XcqType::Primitive(PrimitiveType::U64) }], output: XcqType::Primitive(PrimitiveType::Bool) }] }, ExtensionMetadata { name: \"ExtensionFungibles\", methods: vec![ MethodMetadata { name: \"total_supply\", inputs: vec![MethodParamMetadata { name: \"asset\", ty: XcqType::Primitive(PrimitiveType::U32) }], output: XcqType::Primitive(PrimitiveType::U64) }, MethodMetadata { name: \"balance\", inputs: vec![ MethodParamMetadata { name: \"asset\", ty: XcqType::Primitive(PrimitiveType::U32) }, MethodParamMetadata { name: \"who\", ty: XcqType::Primitive(PrimitiveType::H256) } ], output: XcqType::Primitive(PrimitiveType::U64) } ] } ]\n} Note: ty is represented by a meta-type system called xcq-types xcq-types xcq-types is a meta-type system similar to scale-info but simpler. It enables different chains with different type definitions to work via a common operation. Front-end codes constructs call data to XCQ programs according to metadata provided by different chains.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Runtime API","id":"22","title":"XCQ Runtime API"},"220":{"body":"The interface has two sections: The messages which the Relay-chain is able to receive from the allocating parachain (the UMP message types ), and messages which the Relay-chain is able to send to the allocating parachain (the DMP message types ). These messages are expected to be able to be implemented in a well-known pallet and called with the XCM Transact instruction. Future work may include these messages being introduced into the XCM standard.","breadcrumbs":"RFC-5: Coretime Interface » Explanation","id":"220","title":"Explanation"},"221":{"body":"request_core_count Prototype: fn request_core_count( count: u16,\n) Requests the Relay-chain to alter the number of schedulable cores to count. Under normal operation, the Relay-chain SHOULD send a notify_core_count(count) message back. request_revenue_info_at Prototype: fn request_revenue_at( when: BlockNumber,\n) Requests that the Relay-chain send a notify_revenue message back at or soon after Relay-chain block number when whose until parameter is equal to when. The period in to the past which when is allowed to be may be limited; if so the limit should be understood on a channel outside of this proposal. In the case that the request cannot be serviced because when is too old a block then a notify_revenue message must still be returned, but its revenue field may be None. credit_account Prototype: fn credit_account( who: AccountId, amount: Balance,\n) Instructs the Relay-chain to add the amount of DOT to the Instantaneous Coretime Market Credit account of who. It is expected that Instantaneous Coretime Market Credit on the Relay-chain is NOT transferrable and only redeemable when used to assign cores in the Instantaneous Coretime Pool. assign_core Prototype: type PartsOf57600 = u16;\nenum CoreAssignment { InstantaneousPool, Task(ParaId),\n}\nfn assign_core( core: CoreIndex, begin: BlockNumber, assignment: Vec<(CoreAssignment, PartsOf57600)>, end_hint: Option,\n) Requirements: assert!(core < core_count);\nassert!(targets.iter().map(|x| x.0).is_sorted());\nassert_eq!(targets.iter().map(|x| x.0).unique().count(), targets.len());\nassert_eq!(targets.iter().map(|x| x.1).sum(), 57600); Where: core_count is assumed to be the sole parameter in the last received notify_core_count message. Instructs the Relay-chain to ensure that the core indexed as core is utilised for a number of assignments in specific ratios given by assignment starting as soon after begin as possible. Core assignments take the form of a CoreAssignment value which can either task the core to a ParaId value or indicate that the core should be used in the Instantaneous Pool. Each assignment comes with a ratio value, represented as the numerator of the fraction with a denominator of 57,600. If end_hint is Some and the inner is greater than the current block number, then the Relay-chain should optimize in the expectation of receiving a new assign_core(core, ...) message at or prior to the block number of the inner value. Specific functionality should remain unchanged regardless of the end_hint value. On the choice of denominator: 57,600 is a very composite number which factors into: 2 ** 8, 3 ** 2, 5 ** 2. By using it as the denominator we allow for various useful fractions to be perfectly represented including thirds, quarters, fifths, tenths, 80ths, percent and 256ths.","breadcrumbs":"RFC-5: Coretime Interface » UMP Message Types","id":"221","title":"UMP Message Types"},"222":{"body":"notify_core_count Prototype: fn notify_core_count( count: u16,\n) Indicate that from this block onwards, the range of acceptable values of the core parameter of assign_core message is [0, count). assign_core will be a no-op if provided with a value for core outside of this range. notify_revenue_info Prototype: fn notify_revenue_info( until: BlockNumber, revenue: Option,\n) Provide the amount of revenue accumulated from Instantaneous Coretime Sales from Relay-chain block number last_until to until, not including until itself. last_until is defined as being the until argument of the last notify_revenue message sent, or zero for the first call. If revenue is None, this indicates that the information is no longer available. This explicitly disregards the possibility of multiple parachains requesting and being notified of revenue information. The Relay-chain must be configured to ensure that only a single revenue information destination exists.","breadcrumbs":"RFC-5: Coretime Interface » DMP Message Types","id":"222","title":"DMP Message Types"},"223":{"body":"For request_revenue_info, a successful request should be possible if when is no less than the Relay-chain block number on arrival of the message less 100,000. For assign_core, a successful request should be possible if begin is no less than the Relay-chain block number on arrival of the message plus 10 and workload contains no more than 100 items.","breadcrumbs":"RFC-5: Coretime Interface » Realistic Limits of the Usage","id":"223","title":"Realistic Limits of the Usage"},"224":{"body":"No specific considerations.","breadcrumbs":"RFC-5: Coretime Interface » Performance, Ergonomics and Compatibility","id":"224","title":"Performance, Ergonomics and Compatibility"},"225":{"body":"Standard Polkadot testing and security auditing applies. The proposal introduces no new privacy concerns.","breadcrumbs":"RFC-5: Coretime Interface » Testing, Security and Privacy","id":"225","title":"Testing, Security and Privacy"},"226":{"body":"RFC-1 proposes a means of determining allocation of Coretime using this interface. RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain.","breadcrumbs":"RFC-5: Coretime Interface » Future Directions and Related Material","id":"226","title":"Future Directions and Related Material"},"227":{"body":"None at present.","breadcrumbs":"RFC-5: Coretime Interface » Drawbacks, Alternatives and Unknowns","id":"227","title":"Drawbacks, Alternatives and Unknowns"},"228":{"body":"None.","breadcrumbs":"RFC-5: Coretime Interface » Prior Art and References","id":"228","title":"Prior Art and References"},"229":{"body":"(source) Table of Contents RFC-0007: System Collator Selection Summary Motivation Requirements Stakeholders Explanation Set Size Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Written Discussions Prior Feedback and Input From Unresolved Questions Future Directions and Related Material Start Date 07 July 2023 Description Mechanism for selecting collators of system chains. Authors Joe Petrowski","breadcrumbs":"RFC-0007: System Collator Selection » RFC-0007: System Collator Selection","id":"229","title":"RFC-0007: System Collator Selection"},"23":{"body":"An XCQ executor is a runtime module that executes XCQ queries. It has a core method execute that takes a PolkaVM program binary, method name of the exported functions in the PolkaVM program, input arguments, and weight limit that the PolkaVM program can consume. pub fn execute( &mut self, raw_blob: &[u8], method: &str, input: &[u8], weight_limit: u64,\n) -> Result, XcqExecutorError> {...}","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Executor","id":"23","title":"XCQ Executor"},"230":{"body":"As core functionality moves from the Relay Chain into system chains, so increases the reliance on the liveness of these chains for the use of the network. It is not economically scalable, nor necessary from a game-theoretic perspective, to pay collators large rewards. This RFC proposes a mechanism -- part technical and part social -- for ensuring reliable collator sets that are resilient to attemps to stop any subsytem of the Polkadot protocol.","breadcrumbs":"RFC-0007: System Collator Selection » Summary","id":"230","title":"Summary"},"231":{"body":"In order to guarantee access to Polkadot's system, the collators on its system chains must propose blocks (provide liveness) and allow all transactions to eventually be included. That is, some collators may censor transactions, but there must exist one collator in the set who will include a given transaction. In fact, all collators may censor varying subsets of transactions, but as long as no transaction is in the intersection of every subset, it will eventually be included. The objective of this RFC is to propose a mechanism to select such a set on each system chain. While the network as a whole uses staking (and inflationary rewards) to attract validators, collators face different challenges in scale and have lower security assumptions than validators. Regarding scale, there exist many system chains, and it is economically expensive to pay collators a premium. Likewise, any staked DOT for collation is not staked for validation. Since collator sets do not need to meet Byzantine Fault Tolerance criteria, staking as the primary mechanism for collator selection would remove stake that is securing BFT assumptions, making the network less secure. Another problem with economic scalability relates to the increasing number of system chains, and corresponding increase in need for collators (i.e., increase in collator slots). \"Good\" (highly available, non-censoring) collators will not want to compete in elections on many chains when they could use their resources to compete in the more profitable validator election. Such dilution decreases the required bond on each chain, leaving them vulnerable to takeover by hostile collator groups. This RFC proposes a system whereby collation is primarily an infrastructure service, with the on-chain Treasury reimbursing costs of semi-trusted node operators, referred to as \"Invulnerables\". The system need not trust the individual operators, only that as a set they would be resilient to coordinated attempts to stop a single chain from halting or to censor a particular subset of transactions. In the case that users do not trust this set, this RFC also proposes that each chain always have available collator positions that can be acquired by anyone by placing a bond.","breadcrumbs":"RFC-0007: System Collator Selection » Motivation","id":"231","title":"Motivation"},"232":{"body":"System MUST have at least one valid collator for every chain. System MUST allow anyone to become a collator, provided they reserve/hold enough DOT. System SHOULD select a set of collators with reasonable expectation that the set will not collude to censor any subset of transactions. Collators selected by governance SHOULD have a reasonable expectation that the Treasury will reimburse their operating costs.","breadcrumbs":"RFC-0007: System Collator Selection » Requirements","id":"232","title":"Requirements"},"233":{"body":"Infrastructure providers (people who run validator/collator nodes) Polkadot Treasury","breadcrumbs":"RFC-0007: System Collator Selection » Stakeholders","id":"233","title":"Stakeholders"},"234":{"body":"This protocol builds on the existing Collator Selection pallet and its notion of Invulnerables. Invulnerables are collators (identified by their AccountIds) who will be selected as part of the collator set every session. Operations relating to the management of the Invulnerables are done through privileged, governance origins. The implementation should maintain an API for adding and removing Invulnerable collators. In addition to Invulnerables, there are also open slots for \"Candidates\". Anyone can register as a Candidate by placing a fixed bond. However, with a fixed bond and fixed number of slots, there is an obvious selection problem: The slots fill up without any logic to replace their occupants. This RFC proposes that the collator selection protocol allow Candidates to increase (and decrease) their individual bonds, sort the Candidates according to bond, and select the top N Candidates. The selection and changeover should be coordinated by the session manager. A FRAME pallet already exists for sorting (\"bagging\") \"top N\" groups, the Bags List pallet . This pallet's SortedListProvider should be integrated into the session manager of the Collator Selection pallet. Despite the lack of apparent economic incentives (i.e., inflation), several reasons exist why one may want to bond funds to participate in the Candidates election, for example: They want to build credibility to be selected as Invulnerable; They want to ensure availability of an application, e.g. a stablecoin issuer might run a collator on Asset Hub to ensure transactions in its asset are included in blocks; They fear censorship themselves, e.g. a voter might think their votes are being censored from governance, so they run a collator on the governance chain to include their votes. Unlike the fixed-bond mechanism that fills up its Candidates, the election mechanism ensures that anyone can join the collator set by placing the Nth highest bond.","breadcrumbs":"RFC-0007: System Collator Selection » Explanation","id":"234","title":"Explanation"},"235":{"body":"In order to achieve the requirements listed under Motivation , it is reasonable to have approximately: 20 collators per system chain, of which 15 are Invulnerable, and five are elected by bond.","breadcrumbs":"RFC-0007: System Collator Selection » Set Size","id":"235","title":"Set Size"},"236":{"body":"The primary drawback is a reliance on governance for continued treasury funding of infrastructure costs for Invulnerable collators.","breadcrumbs":"RFC-0007: System Collator Selection » Drawbacks","id":"236","title":"Drawbacks"},"237":{"body":"The vast majority of cases can be covered by unit testing. Integration test should ensure that the Collator Selection UpdateOrigin, which has permission to modify the Invulnerables and desired number of Candidates, can handle updates over XCM from the system's governance location.","breadcrumbs":"RFC-0007: System Collator Selection » Testing, Security, and Privacy","id":"237","title":"Testing, Security, and Privacy"},"238":{"body":"This proposal has very little impact on most users of Polkadot, and should improve the performance of system chains by reducing the number of missed blocks.","breadcrumbs":"RFC-0007: System Collator Selection » Performance, Ergonomics, and Compatibility","id":"238","title":"Performance, Ergonomics, and Compatibility"},"239":{"body":"As chains have strict PoV size limits, care must be taken in the PoV impact of the session manager. Appropriate benchmarking and tests should ensure that conservative limits are placed on the number of Invulnerables and Candidates.","breadcrumbs":"RFC-0007: System Collator Selection » Performance","id":"239","title":"Performance"},"24":{"body":"An extension-based design is essential for several reasons: Different chains may have different data types for semantically similar queries, making it challenging to standardize function calls across them. An extension-based design with optional associated types allows these diverse data types to be specified and utilized effectively. Function calls distributed across various pallets can be amalgamated into a single extension, simplifying the development process and ensuring a more cohesive and maintainable codebase. New functionalities can be added without upgrading the core part of the XCQ. Ensure the core part is in a minimal scope. Essential components of an XCQ extension system include: A hash-based extension id generation mechanism for addressing and versioning . The hash value derives from the extension name and its method sets. Any update to an extension is treated as a new extension. decl_extension macro: Defines an extension as a Rust trait with optional associated types. Example usage : use xcq_extension::decl_extension; pub trait Config { type AssetId: Codec; type AccountId: Codec; type Balance: Codec;\n}\ndecl_extension! { pub trait ExtensionFungibles { type Config: Config; fn total_supply(asset: ::AssetId) -> ::Balance; fn balance(asset: ::AssetId, who: ::AccountId) -> ::Balance; }\n} impl_extensions macro: Generates extension implementations and extension-level metadata. Example Usage : // ExtensionImpl is an aggregate struct to impl different extensions\nstruct ExtensionImpl;\nimpl extension_fungibles::Config for ExtensionImpl { type AssetId = u32; type AccountId = [u8; 32]; type Balance = u64;\n}\nimpl_extensions! { impl extension_core::ExtensionCore for ExtensionImpl { type Config = ExtensionImpl; fn has_extension(id: ::ExtensionId) -> bool { matches!(id, 0 | 1) } } impl extension_fungibles::ExtensionFungibles for ExtensionImpl { type Config = ExtensionImpl; #[allow(unused_variables)] fn total_supply(asset: ::AssetId) -> ::Balance { 200 } #[allow(unused_variables)] fn balance(asset: ::AssetId, who: ::AccountId) -> ::Balance { 100 } }\n} ExtensionExecutor: Connects extension implementations and xcq-executor. All methods of all extensions that a chain supports are amalgamated into a single host_call entry. Then this entry is registered as a typed function entry in PolkaVM Linker within the xcq-executor. Given the extension ID and call data encoded in SCALE format, call requests from the guest XCQ program are dispatched to corresponding extensions: linker .define_typed( \"host_call\", move |caller: Caller<'_, Self::UserData>, extension_id: u64, call_ptr: u32, call_len: u32| -> Result { ... }); PermController: Filters guest XCQ program calling requests, useful for host chains to disable some queries by filtering invoking sources. pub trait PermController { fn is_allowed(extension_id: ExtensionIdTy, call: &[u8], source: InvokeSource) -> bool;\n}\n#[derive(Copy, Clone)]\npub enum InvokeSource { RuntimeAPI, XCM, Extrinsic, Runtime,\n}","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Extension","id":"24","title":"XCQ Extension"},"240":{"body":"The primary group affected is Candidate collators, who, after implementation of this RFC, will need to compete in a bond-based election rather than a race to claim a Candidate spot.","breadcrumbs":"RFC-0007: System Collator Selection » Ergonomics","id":"240","title":"Ergonomics"},"241":{"body":"This RFC is compatible with the existing implementation and can be handled via upgrades and migration.","breadcrumbs":"RFC-0007: System Collator Selection » Compatibility","id":"241","title":"Compatibility"},"242":{"body":"","breadcrumbs":"RFC-0007: System Collator Selection » Prior Art and References","id":"242","title":"Prior Art and References"},"243":{"body":"GitHub: Collator Selection Roadmap GitHub: Revisit Collator Selection Mechanism Polkadot Forum: Economic Model for System Para Collators","breadcrumbs":"RFC-0007: System Collator Selection » Written Discussions","id":"243","title":"Written Discussions"},"244":{"body":"Kian Paimani Jeff Burdges Rob Habermeier SR Labs Auditors Current collators including Paranodes, Stake Plus, Turboflakes, Peter Mensik, SIK, and many more.","breadcrumbs":"RFC-0007: System Collator Selection » Prior Feedback and Input From","id":"244","title":"Prior Feedback and Input From"},"245":{"body":"None at this time.","breadcrumbs":"RFC-0007: System Collator Selection » Unresolved Questions","id":"245","title":"Unresolved Questions"},"246":{"body":"There may exist in the future system chains for which this model of collator selection is not appropriate. These chains should be evaluated on a case-by-case basis.","breadcrumbs":"RFC-0007: System Collator Selection » Future Directions and Related Material","id":"246","title":"Future Directions and Related Material"},"247":{"body":"(source) Table of Contents RFC-0008: Store parachain bootnodes in relay chain DHT Summary Motivation Stakeholders Explanation DHT provider registration New networking protocol Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-07-14 Description Parachain bootnodes shall register themselves in the DHT of the relay chain Authors Pierre Krieger","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » RFC-0008: Store parachain bootnodes in relay chain DHT","id":"247","title":"RFC-0008: Store parachain bootnodes in relay chain DHT"},"248":{"body":"The full nodes of the Polkadot peer-to-peer network maintain a distributed hash table (DHT), which is currently used for full nodes discovery and validators discovery purposes. This RFC proposes to extend this DHT to be used to discover full nodes of the parachains of Polkadot.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Summary","id":"248","title":"Summary"},"249":{"body":"The maintenance of bootnodes has long been an annoyance for everyone. When a bootnode is newly-deployed or removed, every chain specification must be updated in order to take the update into account. This has lead to various non-optimal solutions, such as pulling chain specifications from GitHub repositories. When it comes to RPC nodes, UX developers often have trouble finding up-to-date addresses of parachain RPC nodes. With the ongoing migration from RPC nodes to light clients, similar problems would happen with chain specifications as well. Furthermore, there exists multiple different possible variants of a certain chain specification: with the non-raw storage, with the raw storage, with just the genesis trie root hash, with or without checkpoint, etc. All of this creates confusion. Removing the need for parachain developers to be aware of and manage these different versions would be beneficial. Since the PeerId and addresses of bootnodes needs to be stable, extra maintenance work is required from the chain maintainers. For example, they need to be extra careful when migrating nodes within their infrastructure. In some situations, bootnodes are put behind domain names, which also requires maintenance work. Because the list of bootnodes in chain specifications is so annoying to modify, the consequence is that the number of bootnodes is rather low (typically between 2 and 15). In order to better resist downtimes and DoS attacks, a better solution would be to use every node of a certain chain as potential bootnode, rather than special-casing some specific nodes. While this RFC doesn't solve these problems for relay chains, it aims at solving it for parachains by storing the list of all the full nodes of a parachain on the relay chain DHT. Assuming that this RFC is implemented, and that light clients are used, deploying a parachain wouldn't require more work than registering it onto the relay chain and starting the collators. There wouldn't be any need for special infrastructure nodes anymore.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Motivation","id":"249","title":"Motivation"},"25":{"body":"An XCQ program is structured as a PolkaVM program with the following key components: Imported Functions: host_call: Dispatches call requests to the XCQ Extension Executor. #[polkavm_derive::polkavm_import]\nextern \"C\" { fn host_call(extension_id: u64, call_ptr: u32, call_len: u32) -> u64;\n} Results are SCALE-encoded bytes, with the pointer address (lower 32 bits) and length (higher 32 bits) packed into a u64. return_ty: Returns the type of the function call result. #[polkavm_derive::polkavm_import]\nextern \"C\" { fn return_ty(extension_id: u64, call_index: u32) -> u64;\n} Results are SCALE-encoded bytes, with the pointer address and length packed similarly to host_call. Exported Functions: main: The entry point of the XCQ program. It performs type checking, arguments and results passing and executes the query.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Program Structure","id":"25","title":"XCQ Program Structure"},"250":{"body":"This RFC has been opened on my own initiative because I think that this is a good technical solution to a usability problem that many people are encountering and that they don't realize can be solved.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Stakeholders","id":"250","title":"Stakeholders"},"251":{"body":"The content of this RFC only applies for parachains and parachain nodes that are \"Substrate-compatible\". It is in no way mandatory for parachains to comply to this RFC. Note that \"Substrate-compatible\" is very loosely defined as \"implements the same mechanisms and networking protocols as Substrate\". The author of this RFC believes that \"Substrate-compatible\" should be very precisely specified, but there is controversy on this topic. While a lot of this RFC concerns the implementation of parachain nodes, it makes use of the resources of the Polkadot chain, and as such it is important to describe them in the Polkadot specification. This RFC adds two mechanisms: a registration in the DHT, and a new networking protocol.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Explanation","id":"251","title":"Explanation"},"252":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . Full nodes of a parachain registered on Polkadot should register themselves onto the Polkadot DHT as the providers of a key corresponding to the parachain that they are serving, as described in the Content provider advertisement section of the specification. This uses the ADD_PROVIDER system of libp2p-kademlia. This key is: sha256(concat(scale_compact(para_id), randomness)) where the value of randomness can be found in the randomness field when calling the BabeApi_currentEpoch function. For example, for a para_id equal to 1000, and at the time of writing of this RFC (July 14th 2023 at 09:13 UTC), it is sha(0xa10f12872447958d50aa7b937b0106561a588e0e2628d33f81b5361b13dbcf8df708), which is equal to 0x483dd8084d50dbbbc962067f216c37b627831d9339f5a6e426a32e3076313d87. In order to avoid downtime when the key changes, parachain full nodes should also register themselves as a secondary key that uses a value of randomness equal to the randomness field when calling BabeApi_nextEpoch. Implementers should be aware that their implementation of Kademlia might already hash the key before XOR'ing it. The key is not meant to be hashed twice. The compact SCALE encoding has been chosen in order to avoid problems related to the number of bytes and endianness of the para_id.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » DHT provider registration","id":"252","title":"DHT provider registration"},"253":{"body":"A new request-response protocol should be added, whose name is /91b171bb158e2d3848fa23a9f1c25182fb8e20313b2c1eb49219da7a70ce90c3/paranode (that hexadecimal number is the genesis hash of the Polkadot chain, and should be adjusted appropriately for Kusama and others). The request consists in a SCALE-compact-encoded para_id. For example, for a para_id equal to 1000, this is 0xa10f. Note that because this is a request-response protocol, the request is always prefixed with its length in bytes. While the body of the request is simply the SCALE-compact-encoded para_id, the data actually sent onto the substream is both the length and body. The response consists in a protobuf struct, defined as: syntax = \"proto2\"; message Response { // Peer ID of the node on the parachain side. bytes peer_id = 1; // Multiaddresses of the parachain side of the node. The list and format are the same as for the `listenAddrs` field of the `identify` protocol. repeated bytes addrs = 2; // Genesis hash of the parachain. Used to determine the name of the networking protocol to connect to the parachain. Untrusted. bytes genesis_hash = 3; // So-called \"fork ID\" of the parachain. Used to determine the name of the networking protocol to connect to the parachain. Untrusted. optional string fork_id = 4;\n}; The maximum size of a response is set to an arbitrary 16kiB. The responding side should make sure to conform to this limit. Given that fork_id is typically very small and that the only variable-length field is addrs, this is easily achieved by limiting the number of addresses. Implementers should be aware that addrs might be very large, and are encouraged to limit the number of addrs to an implementation-defined value.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » New networking protocol","id":"253","title":"New networking protocol"},"254":{"body":"The peer_id and addrs fields are in theory not strictly needed, as the PeerId and addresses could be always equal to the PeerId and addresses of the node being registered as the provider and serving the response. However, the Cumulus implementation currently uses two different networking stacks, one of the parachain and one for the relay chain, using two separate PeerIds and addresses, and as such the PeerId and addresses of the other networking stack must be indicated. Asking them to use only one networking stack wouldn't feasible in a realistic time frame. The values of the genesis_hash and fork_id fields cannot be verified by the requester and are expected to be unused at the moment. Instead, a client that desires connecting to a parachain is expected to obtain the genesis hash and fork ID of the parachain from the parachain chain specification. These fields are included in the networking protocol nonetheless in case an acceptable solution is found in the future, and in order to allow use cases such as discovering parachains in a not-strictly-trusted way.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Drawbacks","id":"254","title":"Drawbacks"},"255":{"body":"Because not all nodes want to be used as bootnodes, implementers are encouraged to provide a way to disable this mechanism. However, it is very much encouraged to leave this mechanism on by default for all parachain nodes. This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms. However, if the principle of chain specification bootnodes is entirely replaced with the mechanism described in this RFC (which is the objective), then it becomes important whether the mechanism in this RFC can be abused in order to make a parachain unreachable. Due to the way Kademlia works, it would become the responsibility of the 20 Polkadot nodes whose sha256(peer_id) is closest to the key (described in the explanations section) to store the list of bootnodes of each parachain. Furthermore, when a large number of providers (here, a provider is a bootnode) are registered, only the providers closest to the key are kept, up to a certain implementation-defined limit. For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target parachain. They are then in control of the parachain bootnodes. Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term. Furthermore, parachain clients are expected to cache a list of known good nodes on their disk. If the mechanism described in this RFC went down, it would only prevent new nodes from accessing the parachain, while clients that have connected before would not be affected.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Testing, Security, and Privacy","id":"255","title":"Testing, Security, and Privacy"},"256":{"body":"","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Performance, Ergonomics, and Compatibility","id":"256","title":"Performance, Ergonomics, and Compatibility"},"257":{"body":"The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours. Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode. Assuming 1000 parachain full nodes, the 20 Polkadot full nodes corresponding to a specific parachain will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a parachain full node registers itself to be the provider of the key corresponding to BabeApi_next_epoch. Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the bootnodes of a parachain. Light clients are generally encouraged to cache the peers that they use between restarts, so they should only query these 20 Polkadot full nodes at their first initialization. If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Performance","id":"257","title":"Performance"},"258":{"body":"Irrelevant.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Ergonomics","id":"258","title":"Ergonomics"},"259":{"body":"Irrelevant.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Compatibility","id":"259","title":"Compatibility"},"26":{"body":"The interaction between an XCQ program and the XCQ Extension Executor follows these steps: Program Loading: The Executor loads the PolkaVM program binary. Environment Setup: The Executor configures the PolkaVM environment, registering host functions like host_call and return_ty. Main Function Execution: The Executor calls the program's main function, passing serialized query arguments. Program Execution: Type Checking: The program uses the return_ty function to ensure compatibility with supported chain extensions. Query Execution: The program executes the query using host_call and performs custom computations. Result Serialization: The program serializes the result, writes it to shared memory, and returns the pointer and length to the executor. Result Retrieval: The Executor reads the result from shared memory and returns it to the caller.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Program Execution Flow","id":"26","title":"XCQ Program Execution Flow"},"260":{"body":"None.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Prior Art and References","id":"260","title":"Prior Art and References"},"261":{"body":"While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Unresolved Questions","id":"261","title":"Unresolved Questions"},"262":{"body":"It is possible that in the future a client could connect to a parachain without having to rely on a trusted parachain specification.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Future Directions and Related Material","id":"262","title":"Future Directions and Related Material"},"263":{"body":"(source) Table of Contents RFC-0010: Burn Coretime Revenue Summary Motivation Stakeholders Explanation Start Date 19.07.2023 Description Revenue from Coretime sales should be burned Authors Jonas Gehrlein","breadcrumbs":"RFC-0010: Burn Coretime Revenue » RFC-0010: Burn Coretime Revenue","id":"263","title":"RFC-0010: Burn Coretime Revenue"},"264":{"body":"The Polkadot UC will generate revenue from the sale of available Coretime. The question then arises: how should we handle these revenues? Broadly, there are two reasonable paths – burning the revenue and thereby removing it from total issuance or divert it to the Treasury. This Request for Comment (RFC) presents arguments favoring burning as the preferred mechanism for handling revenues from Coretime sales.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Summary","id":"264","title":"Summary"},"265":{"body":"How to handle the revenue accrued from Coretime sales is an important economic question that influences the value of DOT and should be properly discussed before deciding for either of the options. Now is the best time to start this discussion.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Motivation","id":"265","title":"Motivation"},"266":{"body":"Polkadot DOT token holders.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Stakeholders","id":"266","title":"Stakeholders"},"267":{"body":"This RFC discusses potential benefits of burning the revenue accrued from Coretime sales instead of diverting them to Treasury. Here are the following arguments for it. It's in the interest of the Polkadot community to have a consistent and predictable Treasury income, because volatility in the inflow can be damaging, especially in situations when it is insufficient. As such, this RFC operates under the presumption of a steady and sustainable Treasury income flow, which is crucial for the Polkadot community's stability. The assurance of a predictable Treasury income, as outlined in a prior discussion here , or through other equally effective measures, serves as a baseline assumption for this argument. Consequently, we need not concern ourselves with this particular issue here. This naturally begs the question - why should we introduce additional volatility to the Treasury by aligning it with the variable Coretime sales? It's worth noting that Coretime revenues often exhibit an inverse relationship with periods when Treasury spending should ideally be ramped up. During periods of low Coretime utilization (indicated by lower revenue), Treasury should spend more on projects and endeavours to increase the demand for Coretime. This pattern underscores that Coretime sales, by their very nature, are an inconsistent and unpredictable source of funding for the Treasury. Given the importance of maintaining a steady and predictable inflow, it's unnecessary to rely on another volatile mechanism. Some might argue that we could have both: a steady inflow (from inflation) and some added bonus from Coretime sales, but burning the revenue would offer further benefits as described below. Balancing Inflation: While DOT as a utility token inherently profits from a (reasonable) net inflation, it also benefits from a deflationary force that functions as a counterbalance to the overall inflation. Right now, the only mechanism on Polkadot that burns fees is the one for underutilized DOT in the Treasury. Finding other, more direct target for burns makes sense and the Coretime market is a good option. Clear incentives: By burning the revenue accrued on Coretime sales, prices paid by buyers are clearly costs. This removes distortion from the market that might arise when the paid tokens occur on some other places within the network. In that case, some actors might have secondary motives of influencing the price of Coretime sales, because they benefit down the line. For example, actors that actively participate in the Coretime sales are likely to also benefit from a higher Treasury balance, because they might frequently request funds for their projects. While those effects might appear far-fetched, they could accumulate. Burning the revenues makes sure that the prices paid are clearly costs to the actors themselves. Collective Value Accrual: Following the previous argument, burning the revenue also generates some externality, because it reduces the overall issuance of DOT and thereby increases the value of each remaining token. In contrast to the aforementioned argument, this benefits all token holders collectively and equally. Therefore, I'd consider this as the preferrable option, because burns lets all token holders participate at Polkadot's success as Coretime usage increases.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Explanation","id":"267","title":"Explanation"},"268":{"body":"(source) Table of Contents RFC-0012: Process for Adding New System Collectives Summary Motivation Stakeholders Explanation Removing Collectives Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Start Date 24 July 2023 Description A process for adding new (and removing existing) system collectives. Authors Joe Petrowski","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » RFC-0012: Process for Adding New System Collectives","id":"268","title":"RFC-0012: Process for Adding New System Collectives"},"269":{"body":"Since the introduction of the Collectives parachain, many groups have expressed interest in forming new -- or migrating existing groups into -- on-chain collectives. While adding a new collective is relatively simple from a technical standpoint, the Fellowship will need to merge new pallets into the Collectives parachain for each new collective. This RFC proposes a means for the network to ratify a new collective, thus instructing the Fellowship to instate it in the runtime.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Summary","id":"269","title":"Summary"},"27":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Drawbacks","id":"27","title":"Drawbacks"},"270":{"body":"Many groups have expressed interest in representing collectives on-chain. Some of these include: Parachain technical fellowship (new) Fellowship(s) for media, education, and evangelism (new) Polkadot Ambassador Program (existing) Anti-Scam Team (existing) Collectives that form part of the core Polkadot protocol should have a mandate to serve the Polkadot network. However, as part of the Polkadot protocol, the Fellowship, in its capacity of maintaining system runtimes, will need to include modules and configurations for each collective. Once a group has developed a value proposition for the Polkadot network, it should have a clear path to having its collective accepted on-chain as part of the protocol. Acceptance should direct the Fellowship to include the new collective with a given initial configuration into the runtime. However, the network, not the Fellowship, should ultimately decide which collectives are in the interest of the network.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Motivation","id":"270","title":"Motivation"},"271":{"body":"Polkadot stakeholders who would like to organize on-chain. Technical Fellowship, in its role of maintaining system runtimes.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Stakeholders","id":"271","title":"Stakeholders"},"272":{"body":"The group that wishes to operate an on-chain collective should publish the following information: Charter, including the collective's mandate and how it benefits Polkadot. This would be similar to the Fellowship Manifesto . Seeding recommendation. Member types, i.e. should members be individuals or organizations. Member management strategy, i.e. how do members join and get promoted, if applicable. How much, if at all, members should get paid in salary. Any special origins this Collective should have outside its self. For example, the Fellowship can whitelist calls for referenda via the WhitelistOrigin. This information could all be in a single document or, for example, a GitHub repository. After publication, members should seek feedback from the community and Technical Fellowship, and make any revisions needed. When the collective believes the proposal is ready, they should bring a remark with the text APPROVE_COLLECTIVE(\"{collective name}, {commitment}\") to a Root origin referendum. The proposer should provide instructions for generating commitment. The passing of this referendum would be unequivocal direction to the Fellowship that this collective should be part of the Polkadot runtime. Note: There is no need for a REJECT referendum. Proposals that have not been approved are simply not included in the runtime.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Explanation","id":"272","title":"Explanation"},"273":{"body":"If someone believes that an existing collective is not acting in the interest of the network or in accordance with its charter, they should likewise have a means to instruct the Fellowship to remove that collective from Polkadot. An on-chain remark from the Root origin with the text REMOVE_COLLECTIVE(\"{collective name}, {para ID}, [{pallet indices}]\") would instruct the Fellowship to remove the collective via the listed pallet indices on paraId. Should someone want to construct such a remark, they should have a reasonable expectation that a member of the Fellowship would help them identify the pallet indices associated with a given collective, whether or not the Fellowship member agrees with removal. Collective removal may also come with other governance calls, for example voiding any scheduled Treasury spends that would fund the given collective.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Removing Collectives","id":"273","title":"Removing Collectives"},"274":{"body":"Passing a Root origin referendum is slow. However, given the network's investment (in terms of code maintenance and salaries) in a new collective, this is an appropriate step.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Drawbacks","id":"274","title":"Drawbacks"},"275":{"body":"No impacts.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Testing, Security, and Privacy","id":"275","title":"Testing, Security, and Privacy"},"276":{"body":"Generally all new collectives will be in the Collectives parachain. Thus, performance impacts should strictly be limited to this parachain and not affect others. As the majority of logic for collectives is generalized and reusable, we expect most collectives to be instances of similar subsets of modules. That is, new collectives should generally be compatible with UIs and other services that provide collective-related functionality, with little modifications to support new ones.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Performance, Ergonomics, and Compatibility","id":"276","title":"Performance, Ergonomics, and Compatibility"},"277":{"body":"The launch of the Technical Fellowship, see the initial forum post .","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Prior Art and References","id":"277","title":"Prior Art and References"},"278":{"body":"None at this time.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Unresolved Questions","id":"278","title":"Unresolved Questions"},"279":{"body":"(source) Table of Contents RFC-0013: Prepare Core runtime API for MBMs Summary Motivation Stakeholders Explanation Core::initialize_block Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date July 24, 2023 Description Prepare the Core Runtime API for Multi-Block-Migrations Authors Oliver Tale-Yazdi","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » RFC-0013: Prepare Core runtime API for MBMs","id":"279","title":"RFC-0013: Prepare Core runtime API for MBMs"},"28":{"body":"XCQ Query Program Size: The size of XCQ query programs should be optimized to ensure efficient storage and transmission via XCMP/HRMP. Some strategies to address this issue include: Exploring modular program structures that allow for separate storage and transmission of core logic and supporting elements. PolkaVM supports spliting the program into multiple modules. Establishing guidelines for optimizing dynamic memory usage within query programs","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance issues","id":"28","title":"Performance issues"},"280":{"body":"Introduces breaking changes to the Core runtime API by letting Core::initialize_block return an enum. The versions of Core is bumped from 4 to 5.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Summary","id":"280","title":"Summary"},"281":{"body":"The main feature that motivates this RFC are Multi-Block-Migrations (MBM); these make it possible to split a migration over multiple blocks. Further it would be nice to not hinder the possibility of implementing a new hook poll, that runs at the beginning of the block when there are no MBMs and has access to AllPalletsWithSystem. This hook can then be used to replace the use of on_initialize and on_finalize for non-deadline critical logic. In a similar fashion, it should not hinder the future addition of a System::PostInherents callback that always runs after all inherents were applied.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Motivation","id":"281","title":"Motivation"},"282":{"body":"Substrate Maintainers: They have to implement this, including tests, audit and maintenance burden. Polkadot Runtime developers: They will have to adapt the runtime files to this breaking change. Polkadot Parachain Teams: They have to adapt to the breaking changes but then eventually have multi-block migrations available.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Stakeholders","id":"282","title":"Stakeholders"},"283":{"body":"","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Explanation","id":"283","title":"Explanation"},"284":{"body":"This runtime API function is changed from returning () to ExtrinsicInclusionMode: fn initialize_block(header: &::Header)\n+ -> ExtrinsicInclusionMode; With ExtrinsicInclusionMode is defined as: enum ExtrinsicInclusionMode { /// All extrinsics are allowed in this block. AllExtrinsics, /// Only inherents are allowed in this block. OnlyInherents,\n} A block author MUST respect the ExtrinsicInclusionMode that is returned by initialize_block. The runtime MUST reject blocks that have non-inherent extrinsics in them while OnlyInherents was returned. Coming back to the motivations and how they can be implemented with this runtime API change: 1. Multi-Block-Migrations : The runtime is being put into lock-down mode for the duration of the migration process by returning OnlyInherents from initialize_block. This ensures that no user provided transaction can interfere with the migration process. It is absolutely necessary to ensure this, otherwise a transaction could call into un-migrated storage and violate storage invariants. 2. poll is possible by using apply_extrinsic as entry-point and not hindered by this approach. It would not be possible to use a pallet inherent like System::last_inherent to achieve this for two reasons: First is that pallets do not have access to AllPalletsWithSystem which is required to invoke the poll hook on all pallets. Second is that the runtime does currently not enforce an order of inherents. 3. System::PostInherents can be done in the same manner as poll.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Core::initialize_block","id":"284","title":"Core::initialize_block"},"285":{"body":"The previous drawback of cementing the order of inherents has been addressed and removed by redesigning the approach. No further drawbacks have been identified thus far.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Drawbacks","id":"285","title":"Drawbacks"},"286":{"body":"The new logic of initialize_block can be tested by checking that the block-builder will skip transactions when OnlyInherents is returned. Security: n/a Privacy: n/a","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Testing, Security, and Privacy","id":"286","title":"Testing, Security, and Privacy"},"287":{"body":"","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Performance, Ergonomics, and Compatibility","id":"287","title":"Performance, Ergonomics, and Compatibility"},"288":{"body":"The performance overhead is minimal in the sense that no clutter was added after fulfilling the requirements. The only performance difference is that initialize_block also returns an enum that needs to be passed through the WASM boundary. This should be negligible.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Performance","id":"288","title":"Performance"},"289":{"body":"The new interface allows for more extensible runtime logic. In the future, this will be utilized for multi-block-migrations which should be a huge ergonomic advantage for parachain developers.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Ergonomics","id":"289","title":"Ergonomics"},"29":{"body":"Debugging: Currently, there is no full-fledged debuggers for PolkaVM programs. The only debugging approach is to set the PolkaVM backend in interpreter mode and then log the operations at the assembly level, which is too low-level to debug efficiently. Gas computation: According to this issue , the gas cost model of PolkaVM is not accurate for now.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » User experience issues","id":"29","title":"User experience issues"},"290":{"body":"The advice here is OPTIONAL and outside of the RFC. To not degrade user experience, it is recommended to ensure that an updated node can still import historic blocks.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Compatibility","id":"290","title":"Compatibility"},"291":{"body":"The RFC is currently being implemented in polkadot-sdk#1781 (formerly substrate#14275 ). Related issues and merge requests: Simple multi block migrations Execute a hook after inherent but before transactions There is no module hook after inherents and before transactions","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Prior Art and References","id":"291","title":"Prior Art and References"},"292":{"body":"Please suggest a better name for BlockExecutiveMode. We already tried: RuntimeExecutiveMode, ExtrinsicInclusionMode. The names of the modes Normal and Minimal were also called AllExtrinsics and OnlyInherents, so if you have naming preferences; please post them. => renamed to ExtrinsicInclusionMode Is post_inherents more consistent instead of last_inherent? Then we should change it. => renamed to last_inherent","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Unresolved Questions","id":"292","title":"Unresolved Questions"},"293":{"body":"The long-term future here is to move the block building logic into the runtime. Currently there is a tight dance between the block author and the runtime; the author has to call into different runtime functions in quick succession and exact order. Any misstep causes the block to be invalid. This can be unified and simplified by moving both parts into the runtime.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Future Directions and Related Material","id":"293","title":"Future Directions and Related Material"},"294":{"body":"(source) Table of Contents RFC-0014: Improve locking mechanism for parachains Summary Motivation Requirements Stakeholders Explanation Status quo Proposed changes Migration Drawbacks Testing, Security, and Privacy Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date July 25, 2023 Description Improve locking mechanism for parachains Authors Bryan Chen","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » RFC-0014: Improve locking mechanism for parachains","id":"294","title":"RFC-0014: Improve locking mechanism for parachains"},"295":{"body":"This RFC proposes a set of changes to the parachain lock mechanism. The goal is to allow a parachain manager to self-service the parachain without root track governance action. This is achieved by remove existing lock conditions and only lock a parachain when: A parachain manager explicitly lock the parachain OR a parachain block is produced successfully","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Summary","id":"295","title":"Summary"},"296":{"body":"The manager of a parachain has permission to manage the parachain when the parachain is unlocked. Parachains are by default locked when onboarded to a slot. This requires the parachain wasm/genesis must be valid, otherwise a root track governance action on relaychain is required to update the parachain. The current reliance on root track governance actions for managing parachains can be time-consuming and burdensome. This RFC aims to address this technical difficulty by allowing parachain managers to take self-service actions, rather than relying on general public voting. The key scenarios this RFC seeks to improve are: Rescue a parachain with invalid wasm/genesis. While we have various resources and templates to build a new parachain, it is still not a trivial task. It is very easy to make a mistake and resulting an invalid wasm/genesis. With lack of tools to help detect those issues [1] , it is very likely that the issues are only discovered after the parachain is onboarded on a slot. In this case, the parachain is locked and the parachain team has to go through a lengthy governance process to rescue the parachain. Perform lease renewal for an existing parachain. One way to perform lease renewal for a parachain is by doing a least swap with another parachain with a longer lease. This requires the other parachain must be operational and able to perform XCM transact call into relaychain to dispatch the swap call. Combined with the overhead of setting up a new parachain, this is an time consuming and expensive process. Ideally, the parachain manager should be able to perform the lease swap call without having a running parachain [2] .","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Motivation","id":"296","title":"Motivation"},"297":{"body":"A parachain manager SHOULD be able to rescue a parachain by updating the wasm/genesis without root track governance action. A parachain manager MUST NOT be able to update the wasm/genesis if the parachain is locked. A parachain SHOULD be locked when it successfully produced the first block. A parachain manager MUST be able to perform lease swap without having a running parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Requirements","id":"297","title":"Requirements"},"298":{"body":"Parachain teams Parachain users","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Stakeholders","id":"298","title":"Stakeholders"},"299":{"body":"","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Explanation","id":"299","title":"Explanation"},"3":{"body":"Currently, there is no way to communicate metadata of an asset (or an asset instance) via XCM. The ability to query and modify the metadata is useful for two kinds of entities: Asset collections (both fungible and nonfungible). Any collection has some metadata, such as the name of the collection. The standard way of communicating metadata could help with registering foreign assets within a consensus system. Therefore, this RFC could complement or supersede the RFC for initializing fully-backed derivatives (note that this RFC is related to the old XCM RFC process; it's not the Fellowship RFC and hasn't been migrated yet). NFTs (i.e., asset instances). The metadata is the crucial aspect of any nonfungible object since metadata assigns meaning to such an object. The metadata for NFTs is just as important as the notion of \"amount\" for fungibles (there is no sense in fungibles if they have no amount). An NFT is always a representation of some object. The metadata describes the object represented by the NFT. NFTs can be transferred to another chain via XCM. However, there are limitations due to the inability to communicate its metadata: Teleports are inherently impossible because they imply the complete transfer of an NFT, including its metadata, which can't be done via XCM now. Reserve-based transfers currently have limited use-case scenarios if the reserve chain provides a way of modifying metadata for its users (usually, the token's owner has privileged rights to modify a specific metadata subset). When a user transfers an NFT using this model to another chain, the NFT owner-related metadata can't be updated anymore because another chain's sovereign account owns the original token, and another chain cannot modify the metadata. However, if it were possible to update NFT metadata in the standard XCM way, another chain could offer additional metadata-related logic. For instance, it could provide a facade logic to metadata modification (i.e., provide permission-based modification authorization, new value format check, etc.). Besides metadata modification, the ability to read it is also valuable. On-chain logic can interpret the NFT metadata, i.e., the metadata could have not only the media meaning but also a utility function within a consensus system. Currently, such a way of using NFT metadata is possible only within one consensus system. This RFC proposes making it possible between different systems via XCM so different chains can fetch and analyze the asset metadata from other chains.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Motivation","id":"3","title":"Motivation"},"30":{"body":"Testing: A comprehensive test suite should be developed to cover various scenarios: Positive test cases: Basic queries with various extensions, data types, return values, custom computations, etc. Accurate conversion between given weight limit and the gas limit of PolkaVM Negative test cases: Queries exceeding weight limits Invoking queries from unauthorized sources Edge cases: Queries with minimal or maximum allowed input sizes Integration tests to ensure proper interaction with off-chain wallets/UI and on-chain XCM, including the aforementioned use cases in Motivation section. Security: The XCQ system must enforce a strict read-only policy for all query operations. A mechanism should be implemented to prevent any state-changing operations within XCQ queries. Clear guidelines and best practices should be provided for parachain developers to ensure secure implementation.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Testing, Security, and Privacy","id":"30","title":"Testing, Security, and Privacy"},"300":{"body":"A parachain can either be locked or unlocked [3] . With parachain locked, the parachain manager does not have any privileges. With parachain unlocked, the parachain manager can perform following actions with the paras_registrar pallet: deregister: Deregister a Para Id, freeing all data and returning any deposit. swap: Initiate or confirm lease swap with another parachain. add_lock: Lock the parachain. schedule_code_upgrade: Schedule a parachain upgrade to update parachain wasm. set_current_head: Set the parachain's current head. Currently, a parachain can be locked with following conditions: From add_lock call, which can be dispatched by relaychain Root origin, the parachain, or the parachain manager. When a parachain is onboarded on a slot [4] . When a crowdloan is created. Only the relaychain Root origin or the parachain itself can unlock the lock [5] . This creates an issue that if the parachain is unable to produce block, the parachain manager is unable to do anything and have to rely on relaychain Root origin to manage the parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Status quo","id":"300","title":"Status quo"},"301":{"body":"This RFC proposes to change the lock and unlock conditions. A parachain can be locked only with following conditions: Relaychain governance MUST be able to lock any parachain. A parachain MUST be able to lock its own lock. A parachain manager SHOULD be able to lock the parachain. A parachain SHOULD be locked when it successfully produced a block for the first time. A parachain can be unlocked only with following conditions: Relaychain governance MUST be able to unlock any parachain. A parachain MUST be able to unlock its own lock. Note that create crowdloan MUST NOT lock the parachain and onboard a parachain SHOULD NOT lock it until a new block is successfully produced.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Proposed changes","id":"301","title":"Proposed changes"},"302":{"body":"A one off migration is proposed in order to apply this change retrospectively so that existing parachains can also be benefited from this RFC. This migration will unlock parachains that confirms with following conditions: Parachain is locked. Parachain never produced a block. Including from expired leases. Parachain manager never explicitly lock the parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Migration","id":"302","title":"Migration"},"303":{"body":"Parachain locks are designed in such way to ensure the decentralization of parachains. If parachains are not locked when it should be, it could introduce centralization risk for new parachains. For example, one possible scenario is that a collective may decide to launch a parachain fully decentralized. However, if the parachain is unable to produce block, the parachain manager will be able to replace the wasm and genesis without the consent of the collective. It is considered this risk is tolerable as it requires the wasm/genesis to be invalid at first place. It is not yet practically possible to develop a parachain without any centralized risk currently. Another case is that a parachain team may decide to use crowdloan to help secure a slot lease. Previously, creating a crowdloan will lock a parachain. This means crowdloan participants will know exactly the genesis of the parachain for the crowdloan they are participating. However, this actually providers little assurance to crowdloan participants. For example, if the genesis block is determined before a crowdloan is started, it is not possible to have onchain mechanism to enforce reward distributions for crowdloan participants. They always have to rely on the parachain team to fulfill the promise after the parachain is alive. Existing operational parachains will not be impacted.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Drawbacks","id":"303","title":"Drawbacks"},"304":{"body":"The implementation of this RFC will be tested on testnets (Rococo and Westend) first. An audit maybe required to ensure the implementation does not introduce unwanted side effects. There is no privacy related concerns.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Testing, Security, and Privacy","id":"304","title":"Testing, Security, and Privacy"},"305":{"body":"This RFC should not introduce any performance impact.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Performance","id":"305","title":"Performance"},"306":{"body":"This RFC should improve the developer experiences for new and existing parachain teams","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Ergonomics","id":"306","title":"Ergonomics"},"307":{"body":"This RFC is fully compatibility with existing interfaces.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Compatibility","id":"307","title":"Compatibility"},"308":{"body":"Parachain Slot Extension Story: https://github.com/paritytech/polkadot/issues/4758 Allow parachain to renew lease without actually run another parachain: https://github.com/paritytech/polkadot/issues/6685 Always treat parachain that never produced block for a significant amount of time as unlocked: https://github.com/paritytech/polkadot/issues/7539","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Prior Art and References","id":"308","title":"Prior Art and References"},"309":{"body":"None at this stage.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Unresolved Questions","id":"309","title":"Unresolved Questions"},"31":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance, Ergonomics, and Compatibility","id":"31","title":"Performance, Ergonomics, and Compatibility"},"310":{"body":"This RFC is only intended to be a short term solution. Slots will be removed in future and lock mechanism is likely going to be replaced with a more generalized parachain manage & recovery system in future. Therefore long term impacts of this RFC are not considered. https://github.com/paritytech/cumulus/issues/377 [2] : https://github.com/paritytech/polkadot/issues/6685 [3] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L51-L52C15 [4] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L473-L475 [5] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L333-L340","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Future Directions and Related Material","id":"310","title":"Future Directions and Related Material"},"311":{"body":"(source) Table of Contents RFC-0022: Adopt Encointer Runtime Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date Aug 22nd 2023 Description Permanently move the Encointer runtime into the Fellowship runtimes repo. Authors @brenzi for Encointer Association, 8000 Zurich, Switzerland","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » RFC-0022: Adopt Encointer Runtime","id":"311","title":"RFC-0022: Adopt Encointer Runtime"},"312":{"body":"Encointer is a system chain on Kusama since Jan 2022 and has been developed and maintained by the Encointer association. This RFC proposes to treat Encointer like any other system chain and include it in the fellowship repo with this PR .","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Summary","id":"312","title":"Summary"},"313":{"body":"Encointer does not seek to be in control of its runtime repository. As a decentralized system, the fellowship has a more suitable structure to maintain a system chain runtime repo than the Encointer association does. Also, Encointer aims to update its runtime in batches with other system chains in order to have consistency for interoperability across system chains.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Motivation","id":"313","title":"Motivation"},"314":{"body":"Fellowship: Will continue to take upon them the review and auditing work for the Encointer runtime, but the process is streamlined with other system chains and therefore less time-consuming compared to the separate repo and CI process we currently have. Kusama Network: Tokenholders can easily see the changes of all system chains in one place. Encointer Association: Further decentralization of the Encointer Network necessities like devops. Encointer devs: Being able to work directly in the Fellowship runtimes repo to streamline and synergize with other developers.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Stakeholders","id":"314","title":"Stakeholders"},"315":{"body":"Our PR has all details about our runtime and how we would move it into the fellowship repo. Noteworthy: All Encointer-specific pallets will still be located in encointer's repo for the time being: https://github.com/encointer/pallets It will still be the duty of the Encointer team to keep its runtime up to date and provide adequate test fixtures. Frequent dependency bumps with Polkadot releases would be beneficial for interoperability and could be streamlined with other system chains but that will not be a duty of fellowship. Whenever possible, all system chains could be upgraded jointly (including Encointer) with a batch referendum. Further notes: Encointer will publish all its crates crates.io Encointer does not carry out external auditing of its runtime nor pallets. It would be beneficial but not a requirement from our side if Encointer could join the auditing process of other system chains.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Explanation","id":"315","title":"Explanation"},"316":{"body":"Other than all other system chains, development and maintenance of the Encointer Network is mainly financed by the KSM Treasury and possibly the DOT Treasury in the future. Encointer is dedicated to maintaining its network and runtime code for as long as possible, but there is a dependency on funding which is not in the hands of the fellowship. The only risk in the context of funding, however, is that the Encointer runtime will see less frequent updates if there's less funding.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Drawbacks","id":"316","title":"Drawbacks"},"317":{"body":"No changes to the existing system are proposed. Only changes to how maintenance is organized.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Testing, Security, and Privacy","id":"317","title":"Testing, Security, and Privacy"},"318":{"body":"No changes","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Performance, Ergonomics, and Compatibility","id":"318","title":"Performance, Ergonomics, and Compatibility"},"319":{"body":"Existing Encointer runtime repo","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Prior Art and References","id":"319","title":"Prior Art and References"},"32":{"body":"It's a new functionality, which doesn't modify the existing implementations.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance","id":"32","title":"Performance"},"320":{"body":"None identified","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Unresolved Questions","id":"320","title":"Unresolved Questions"},"321":{"body":"More info on Encointer: encointer.org","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Future Directions and Related Material","id":"321","title":"Future Directions and Related Material"},"322":{"body":"(source) Table of Contents RFC-0026: Sassafras Consensus Protocol Abstract 1. Motivation 1.1. Relevance to Implementors 1.2. Supporting Sassafras for Polkadot 2. Stakeholders 2.1. Blockchain Core Developers 2.2. Polkadot Ecosystem Contributors 3. Notation 3.1. Data Structures Definitions 3.2. Types Alias 3.2. Pseudo-Code 3.3. Incremental Introduction of Types and Functions 4. Protocol Introduction 4.1. Submission of Candidate Tickets 4.2. Validation of Candidate Tickets 4.3. Tickets Slots Binding 4.4. Claim of Ticket Ownership 5. Bandersnatch VRFs Cryptographic Primitives 5.1 Bare VRF Interface 6. Sassafras Protocol 6.2. Header Digest Log 6.3. On-Chain Randomness 6.4. Epoch Change Signal 6.5. Tickets Creation and Submission 6.6. On-chain Tickets Validation 6.7. Ticket-Slot Binding 6.8. Slot Claim 6.9. Slot Claim Verification 6.9.1. Primary Method 6.10. Randomness Accumulator 7. Drawbacks 8. Testing, Security, and Privacy 9. Performance, Ergonomics, and Compatibility 9.1. Performance 9.2. Ergonomics 9.3. Compatibility 10. Prior Art and References 11. Unresolved Questions 12. Future Directions and Related Material 12.1. Interactions with On-Chain Code 12.2. Deployment Strategies 12.3. ZK-SNARK Parameters 12.4. Anonymous Submission of Tickets. Start Date September 06, 2023 Description Sassafras consensus protocol specification Authors Davide Galassi","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » RFC-0026: Sassafras Consensus Protocol","id":"322","title":"RFC-0026: Sassafras Consensus Protocol"},"323":{"body":"Sassafras is a novel consensus protocol designed to address the recurring fork-related challenges encountered in other lottery-based protocols. The protocol aims to create a mapping between each epoch's slots and the authorities set while ensuring that the identity of authorities assigned to the slots remains undisclosed until the slot is actively claimed during block production.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » Abstract","id":"323","title":"Abstract"},"324":{"body":"Sassafras Protocol has been rigorously described in a comprehensive research paper authored by the Web3 Foundation research team. This RFC is primarily intended to detail the critical implementation aspects vital for ensuring interoperability and to clarify certain aspects that are left open by the research paper and thus subject to interpretation during implementation.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1. Motivation","id":"324","title":"1. Motivation"},"325":{"body":"This RFC focuses on providing implementors with the necessary insights into the core protocol's operation. In instances of inconsistency between this document and the research paper, this RFC should be considered authoritative to eliminate ambiguities and ensure interoperability.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1.1. Relevance to Implementors","id":"325","title":"1.1. Relevance to Implementors"},"326":{"body":"Beyond promoting interoperability, this RFC also aims to facilitate the implementation of Sassafras within the greater Polkadot ecosystem. Although the specifics of deployment strategies are beyond the scope of this document, it lays the groundwork for the integration of Sassafras.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1.2. Supporting Sassafras for Polkadot","id":"326","title":"1.2. Supporting Sassafras for Polkadot"},"327":{"body":"The protocol has a central role in the next generation block authoring consensus systems.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2. Stakeholders","id":"327","title":"2. Stakeholders"},"328":{"body":"Developers responsible for creating blockchains who intend to leverage the benefits offered by the Sassafras Protocol.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2.1. Blockchain Core Developers","id":"328","title":"2.1. Blockchain Core Developers"},"329":{"body":"Developers contributing to the Polkadot ecosystem, both relay-chain and para-chains.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2.2. Polkadot Ecosystem Contributors","id":"329","title":"2.2. Polkadot Ecosystem Contributors"},"33":{"body":"The proposal facilitate the wallets and dApps developers. Developers no longer need to examine every concrete implementation to support conceptually similar operations across different chains. Additionally, they gain a more modular development experience through encapsulating custom computations over the exposed APIs in PolkaVM programs.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Ergonomics","id":"33","title":"Ergonomics"},"330":{"body":"This section outlines the notation adopted throughout this document to ensure clarity and consistency.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3. Notation","id":"330","title":"3. Notation"},"331":{"body":"Data structures are mostly defined using standard ASN.1 syntax with few exceptions. To ensure interoperability of serialized structures, the order of the fields must match the definitions found within this specification.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.1. Data Structures Definitions","id":"331","title":"3.1. Data Structures Definitions"},"332":{"body":"Unsigned integer: Unsigned ::= INTEGER (0..MAX) n-bit unsigned integer: Unsigned ::= INTEGER (0..2^n - 1) 8-bit unsigned integer (octet) Unsigned8 ::= Unsigned<8> 32-bit unsigned integer: Unsigned32 ::= Unsigned<32> 64-bit unsigned integer: Unsigned64 ::= Unsigned<64> Non-homogeneous sequence (struct/tuple): Sequence ::= SEQUENCE Variable length homogeneous sequence (vector): Sequence ::= SEQUENCE OF T Fixed length homogeneous sequence (array): Sequence ::= Sequence (SIZE(n)) Variable length octet-string: OctetString ::= Sequence Fixed length octet-string: OctetString ::= Sequence","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.2. Types Alias","id":"332","title":"3.2. Types Alias"},"333":{"body":"It is convenient to make use of code snippets as part of the protocol description. As a convention, the code is formatted in a style similar to Rust , and can make use of the following set of predefined procedures: Sequences CONCAT(x₀: OctetString, ..., xₖ: OctetString) -> OctetString: Concatenates the input octet-strings as a new octet string. LENGTH(s: Sequence) -> Unsigned: The number of elements in the sequence s. GET(s: Sequence, i: Unsigned) -> T: The i-th element of the sequence s. PUSH(s: Sequence, x: T): Appends x as the new last element of the sequence s. POP(s: Sequence) -> T: extract and returns the last element of the sequence s. Codec ENCODE(x: T) -> OctetString: Encodes x as an OctetString according to SCALE codec. DECODE(x: OctetString) -> T: Decodes x as a type T object according to SCALE codec. Other BLAKE2(x: OctetString) -> OctetString<32>: Standard Blake2b hash of x with 256-bit digest.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.2. Pseudo-Code","id":"333","title":"3.2. Pseudo-Code"},"334":{"body":"More types and helper functions are introduced incrementally as they become relevant within the document's context.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.3. Incremental Introduction of Types and Functions","id":"334","title":"3.3. Incremental Introduction of Types and Functions"},"335":{"body":"The timeline is segmented into a sequentially ordered sequence of slots . This entire sequence of slots is further partitioned into distinct segments known as epochs . Sassafras aims to map each slot within a target epoch to the authorities scheduled for that epoch, utilizing a ticketing system. The core protocol operation can be roughly divided into four phases.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4. Protocol Introduction","id":"335","title":"4. Protocol Introduction"},"336":{"body":"Each authority scheduled for the target epoch generates and shares a set of candidate tickets. Every ticket has an unbiasable pseudo random score and is bundled with an anonymous proof of validity.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.1. Submission of Candidate Tickets","id":"336","title":"4.1. Submission of Candidate Tickets"},"337":{"body":"Each candidate ticket undergoes a validation process for the associated validity proof and compliance with other protocol-specific constraints. Valid tickets are persisted on-chain.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.2. Validation of Candidate Tickets","id":"337","title":"4.2. Validation of Candidate Tickets"},"338":{"body":"After collecting all valid candidate tickets and before the beginning of the target epoch , a deterministic method is used to uniquely associate a subset of these tickets to the slots of the target epoch .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.3. Tickets Slots Binding","id":"338","title":"4.3. Tickets Slots Binding"},"339":{"body":"During block production phase of target epoch , the author is required to prove ownership of the ticket associated to the block's slot. This step discloses the identity of the ticket owner.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.4. Claim of Ticket Ownership","id":"339","title":"4.4. Claim of Ticket Ownership"},"34":{"body":"The proposal defines new apis, which doesn't break compatibility with existing interfaces.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Compatibility","id":"34","title":"Compatibility"},"340":{"body":"This section is not intended to serve as an exhaustive exploration of the mathematically intensive foundations of the cryptographic primitive. Rather, its primary aim is to offer a concise and accessible explanation of the primitives role and interface which is relevant within the scope of the protocol. For a more detailed explanation, refer to the Bandersnatch VRFs technical specification Bandersnatch VRF comes in two variants: Bare VRF: Extension to the IETF ECVRF RFC 9381 , Ring VRF: Anonymous signatures leveraging zk-SNARK . Together with the input , which determines the VRF output , both variants offer the capability to sign some arbitrary additional data ( extra ) which doesn't contribute to the VRF output.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 5. Bandersnatch VRFs Cryptographic Primitives","id":"340","title":"5. Bandersnatch VRFs Cryptographic Primitives"},"341":{"body":"VRF signature construction. fn vrf_sign( secret: SecretKey, input: OctetString, extra: OctetString, ) -> VrfSignature VRF signature verification. Returns a Boolean indicating the validity of the signature (1 on success). fn vrf_verify( public: PublicKey, input: OctetString, extra: OctetString, signature: VrfSignature ) -> Unsigned<1>; VRF output derivation from input and secret . fn vrf_output( secret: SecretKey, input: OctetString, ) -> OctetString<32>; VRF output derivation from a VRF signature. fn vrf_signed_output( signature: VrfSignature, ) -> OctetString<32>; The following condition is always satisfied: let signature = vrf_sign(secret, input, extra); vrf_output(secret, input) == vrf_signed_output(signature) SecretKey, PublicKey and VrfSignature types are intentionally left undefined. Their definitions can be found in the Bandersnatch VRF specification and related documents. 5.4.2. Ring VRF Interface Ring VRF signature construction. fn ring_vrf_sign( secret: SecretKey, prover: RingProver, input: OctetString, extra: OctetString, ) -> RingVrfSignature; Ring VRF signature verification. Returns a Boolean indicating the validity of the signature (1 on success). Note that verification doesn't require the signer's public key. fn ring_vrf_verify( verifier: RingVerifier, input: OctetString, extra: OctetString, signature: RingVrfSignature, ) -> Unsigned<1>; VRF output derivation from a ring VRF signature . fn ring_vrf_signed_output( signature: RingVrfSignature, ) -> OctetString<32>; The following condition is always satisfied: let signature = vrf_sign(secret, input, extra); let ring_signature = ring_vrf_sign(secret, prover, input, extra); vrf_signed_output(signature) == ring_vrf_signed_output(ring_signature); RingProver, RingVerifier, and RingVrfSignature are intentionally left undefined. Their definitions can be found in the Bandersnatch VRF specification and related documents.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 5.1 Bare VRF Interface","id":"341","title":"5.1 Bare VRF Interface"},"342":{"body":"6.1. Protocol Configuration The ProtocolConfiguration type contains some parameters to tweak the protocol behavior and primarily influences certain checks carried out during tickets validation. It is defined as: ProtocolConfiguration ::= Sequence { epoch_length: Unsigned32, attempts_number: Unsigned8, redundancy_factor: Unsigned8, } Where: epoch_length: Number of slots for each epoch. attempts_number: Maximum number of tickets that each authority is allowed to submit. redundancy_factor: Expected ratio between the cumulative number of valid tickets which can be submitted by the scheduled authorities and the epoch's duration in slots. The attempts_number influences the anonymity of block producers. As all published tickets have a public attempt number less than attempts_number, all the tickets which share the attempt number value must belong to different block producers, which reduces anonymity late as we approach the epoch tail. Bigger values guarantee more anonymity but also more computation. Details about how these parameters drive the tickets validity probability can be found in section 6.5.2 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6. Sassafras Protocol","id":"342","title":"6. Sassafras Protocol"},"343":{"body":"Each block header contains a Digest log, which is defined as an ordered sequence of DigestItems: DigestItem ::= Sequence { id: OctetString<4>, data: OctetString } Digest ::= Sequence The Digest sequence is used to propagate information required for the correct protocol progress. Outside the protocol's context, the information within each DigestItem is opaque and maps to some SCALE-encoded protocol-specific structure. For Sassafras related items, the DiegestItems id is set to the ASCII string \"SASS\" Possible digest items for Sassafras: Epoch change signal: Information about next epoch. This is mandatory for the first block of a new epoch. Epoch tickets signal: Sequence of tickets for claiming slots in the next epoch. This is mandatory for the first block in the epoch's tail Slot claim info: Additional data required for block verification. This is mandatory for each block and must be the second-to-last entry in the log. Seal: Block signature added by the block author. This is mandatory for each block and must be the last entry in the log. If any digest entry is unexpected, not found where mandatory or found in the wrong position, then the block is considered invalid.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.2. Header Digest Log","id":"343","title":"6.2. Header Digest Log"},"344":{"body":"A sequence of four randomness entries is maintained on-chain. RandomnessBuffer ::= Sequence, 4> During epoch N: The first entry is the current randomness accumulator and incorporates verifiable random elements from all previously executed blocks. The accumulation procedure is described in section 6.10 . The second entry is the snapshot of the accumulator before the execution of the first block of epoch N. This is the randomness used for tickets targeting epoch N+2. The third entry is the snapshot of the accumulator before the execution of the first block of epoch N-1. This is the randomness used for tickets targeting epoch N+1 (the next epoch). The third entry is the snapshot of the accumulator before the execution of the first block of epoch N-2. This is the randomness used for tickets targeting epoch N (the current epoch). The buffer's entries are updated after each block execution.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.3. On-Chain Randomness","id":"344","title":"6.3. On-Chain Randomness"},"345":{"body":"The first block produced during epoch N must include a descriptor for some of the parameters to be used by the subsequent epoch (N+1). This signal descriptor is defined as: NextEpochDescriptor ::= Sequence { randomness: OctetString<32>, authorities: Sequence, } Where: randomness: Randomness accumulator snapshot relevant for validation of next epoch blocks. In other words, randomness used to construct the tickets targeting epoch N+1. authorities: List of authorities scheduled for next epoch. This descriptor is SCALE encoded and embedded in a DigestItem. 6.4.1. Startup Parameters Some of the initial parameters used by the first epoch (#0), are set through the genesis configuration, which is defined as: GenesisConfig ::= Sequence { authorities: Sequence, } The on-chain RandomnessBuffer is initialized after the genesis block construction. The first buffer entry is set as the Blake2b hash of the genesis block, each of the other entries is set as the Blake2b hash of the previous entry. Since block #0 is generated by each node as part of the genesis process, the first block that an authority explicitly produces for epoch #0 is block #1. Therefore, block #1 is required to contain the NextEpochDescriptor for the following epoch. NextEpochDescriptor for epoch #1: randomness: Third entry (index 2) of the randomness buffer. authorities: The same sequence as specified in the genesis configuration.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.4. Epoch Change Signal","id":"345","title":"6.4. Epoch Change Signal"},"346":{"body":"During epoch N, each authority scheduled for epoch N+2 constructs a set of tickets which may be eligible ( 6.5.2 ) for on-chain submission. These tickets are constructed using the on-chain randomness snapshot taken before the execution of the first block of epoch N together with other parameters and aims to secure ownership of one or more slots of epoch N+2 ( target epoch ). Each authority is allowed to submit a maximum number of tickets, constrained by attempts_number field of the ProtocolConfiguration. The ideal timing for the candidate authority to start constructing the tickets is subject to strategy. A recommended approach is to initiate tickets creation once the last block of epoch N-1 is either probabilistically or, even better, deterministically finalized. This delay is suggested to prevent wasting resources creating tickets that will be unusable if a different chain branch is chosen as canonical. Tickets generated during epoch N are shared with the tickets relayers , which are the authorities scheduled for epoch N+1. Relayers validate and collect (off-chain) the tickets targeting epoch N+2. When epoch N+1 starts, collected tickets are submitted on-chain by relayers as inherent extrinsics , a special type of transaction inserted by the block author at the beginning of the block's transactions sequence. 6.5.1. Ticket Identifier Each ticket has an associated identifier defined as: TicketId ::= OctetString<32>; The value of TicketId is completely determined by the output of Bandersnatch VRFs given the following unbiasable input: let ticket_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(attempt) ); let ticket_id = vrf_output(authority_secret_key, ticket_vrf_input); Where: target_epoch_randomness: element of RandomnessBuffer which contains the randomness for the epoch the ticket is targeting. attempt: value going from 0 to the configured attempts_number - 1. 6.5.2. Tickets Threshold A ticket is valid for on-chain submission if its TicketId value, when interpreted as a big-endian 256-bit integer normalized as a float within the range [0..1], is less than the ticket threshold computed as: T = (r·s)/(a·v) Where: v: epoch's authorities number s: epoch's slots number r: redundancy factor a: attempts number In an epoch with s slots, the goal is to achieve an expected number of valid tickets equal to r·s. It's crucial to ensure that the probability of having fewer than s winning tickets is very low, even in scenarios where up to 1/3 of the authorities might be offline. To accomplish this, we first define the winning probability of a single ticket as T = (r·s)/(a·v). Let n be the actual number of participating authorities, where v·2/3 ≤ n ≤ v. These n authorities each make a attempts, for a total of a·n attempts. Let X be the random variable associated to the number of winning tickets, then its expected value is E[X] = T·a·n = (r·s·n)/v. By setting r = 2, we get s·4/3 ≤ E[X] ≤ s·2. Using Bernestein's inequality we get Pr[X < s] ≤ e^(-s/21). For instance, with s = 600 this results in Pr[X < s] < 4·10⁻¹³. Consequently, this approach offers considerable tolerance for offline nodes and ensures that all slots are likely to be filled with tickets. For more details about threshold formula refer to probabilities and parameters paragraph in the Web3 Foundation description of the protocol. 6.5.3. Ticket Envelope Each ticket candidate is represented by a TicketEnvelope: TicketEnvelope ::= Sequence { attempt: Unsigned8, extra: OctetString, signature: RingVrfSignature } Where: attempt: Index associated to the ticket. extra: Additional data available for user-defined applications. signature: Ring VRF signature of the envelope data (attempt and extra). Envelope data is signed using Bandersnatch Ring VRF ( 5.4.2 ). let signature = ring_vrf_sign( secret_key, ring_prover ticket_vrf_input, extra, ); With ticket_vrf_input defined as in 6.5.1 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.5. Tickets Creation and Submission","id":"346","title":"6.5. Tickets Creation and Submission"},"347":{"body":"Validation rules: Ring VRF signature is verified using the ring_verifier derived by the constant ring context parameters (SNARK SRS) and the next epoch authorities public keys. TicketId is locally computed from the RingVrfSignature and its value is checked to be less than tickets' threshold. On-chain tickets submission can't occur within a block part of the epoch's tail , which encompasses a configurable number of slots at the end of the epoch. This constraint is to give time to persisted on-chain tickets to be probabilistically (or even better deterministically) finalized and thus to further reduce the fork chances at the beginning of the target epoch. All tickets which are proposed within a block must be valid and all of them must end up being persisted on-chain. Because the total number of tickets persisted on-chain is limited by to the epoch's length, this may require to drop some of the previously persisted tickets. We remove tickets with greater TicketId value first. No tickets duplicates are allowed. If at least one of the checks fails then the block must be considered invalid. Pseudo-code for ticket validation for steps 1 and 2: let ticket_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(envelope.attempt) ); let result = ring_vrf_verify( ring_verifier, ticket_vrf_input, envelope.extra, envelope.ring_signature ); ASSERT(result == 1); let ticket_id = ring_vrf_signed_output(envelope.ring_signature); ASSERT(ticket_id < ticket_threshold); Valid tickets are persisted on-chain in a bounded sorted sequence of TicketBody objects. Items within this sequence are sorted according to their TicketId, interpreted as a 256-bit big-endian unsigned integer. TicketBody ::= Sequence { id: TicketId, attempt: Unsigned8, extra: OctetString, } Tickets ::= Sequence The on-chain tickets sequence length bound is set equal to the epoch length in slots according to the protocol configuration.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.6. On-chain Tickets Validation","id":"347","title":"6.6. On-chain Tickets Validation"},"348":{"body":"Before the beginning of the target epoch , the on-chain sequence of tickets must be associated to epoch's slots such that there is at most one ticket per slot. Given an ordered sequence of tickets [t₀, t₁, ..., tₙ], the tickets are associated according to the following outside-in strategy: slot_index : [ 0, 1, 2, 3 , ... ] tickets : [ t₀, tₙ, t₁, tₙ₋₁, ... ] Here slot_index is the slot number relative to the epoch's first slot: slot_index = slot - epoch_first_slot. The association between tickets and a slots is recorded on-chain and thus is public. What remains confidential is the ticket's author identity, and consequently, who is enabled to claim the corresponding slot. This information is known only to the ticket's author. If the number of published tickets is less than the number of epoch's slots, some orphan slots at the end of the epoch will remain unbounded to any ticket. For orphan slots claiming strategy refer to 6.8.2 . Note that this fallback situation always apply to the first two epochs after genesis.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.7. Ticket-Slot Binding","id":"348","title":"6.7. Ticket-Slot Binding"},"349":{"body":"With tickets bounded to the target epoch slots, every designated authority acquires the information about the slots for which they are required to produce a block. The procedure for slot claiming depends on whether a given slot has an associated ticket according to the on-chain state. If a slot has an associated ticket, then the primary authoring method is used. Conversely, the protocol resorts to the secondary method as a fallback. 6.8.1. Primary Method An authority, can claim a slot using the primary method if it is the legit owner of the ticket associated to the given slot. Let target_epoch_randomness be the entry in RandomnessBuffer relative to the epoch the block is targeting and attempt be the attempt used to construct the ticket associated to the slot to claim, the VRF input for slot claiming is constructed as: let seal_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(attempt) ); The seal_vrf_input, when signed with the correct authority secret key, must generate the same TicketId which has been associated to the target slot according to the on-chain state. 6.8.2. Secondary Method Given that the authorities scheduled for the target epoch are kept on-chain in an ordered sequence, the index of the authority which has the privilege to claim an orphan slot is given by the following procedure: let hash_input = CONCAT( target_epoch_randomness, ENCODE(relative_slot_index), ); let hash = BLAKE2(hash_input); let index_bytes = CONCAT(GET(hash, 0), GET(hash, 1), GET(hash, 2), GET(hash, 3)); let index = DECODE(index_bytes) % LENGTH(authorities); With relative_slot_index the slot offset relative to the target epoch's start and authorities the sequence of target epoch authorities. let seal_vrf_input = CONCAT( BYTES(\"sassafras_fallback_seal\"), target_epoch_randomness ); 6.8.3. Claim Data ClaimData is a digest entry which contains additional information required by the protocol to verify the block: ClaimData ::= Sequence { slot: Unsigned32, authority_index: Unsigned32, randomness_source: VrfSignature, } slot: The slot number authority_index: Block's author index relative to the on-chain authorities sequence. randomness_source: VRF signature used to generate per-block randomness. Given the seal_vrf_input constructed using the primary or secondary method, the randomness source signature is generated as follows: let randomness_vrf_input = CONCAT( BYTES(\"sassafras_randomness\"), vrf_output(authority_secret_key, seal_vrf_input) ); let randomness_source = vrf_sign( authority_secret_key, randomness_vrf_input, [] ); let claim = SlotClaim { slot, authority_index, randomness_source }; PUSH(block_header.digest, ENCODE(claim)); The ClaimData object is SCALE encoded and pushed as the second-to-last element of the header digest log. 6.8.4. Block Seal A block is finally sealed as follows: let unsealed_header_byets = ENCODE(block_header); let seal = vrf_sign( authority_secret_key, seal_vrf_input, unsealed_header_bytes ); PUSH(block_header.digest, ENCODE(seal)); With block_header the block's header without the seal digest log entry. The seal object is a VrfSignature, which is SCALE encoded and pushed as the last entry of the header digest log.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.8. Slot Claim","id":"349","title":"6.8. Slot Claim"},"35":{"body":"There are several discussions related to the proposal, including: https://forum.polkadot.network/t/wasm-view-functions/1045 is the original discussion about having a mechanism to avoid code duplications between the runtime and front-ends/wallets. In the original design, the custom computations are compiled as a wasm function. https://github.com/paritytech/polkadot-sdk/issues/216 is the issue tracking the view functions implementation in runtime implementations https://github.com/paritytech/polkadot-sdk/pull/4722 is the on-going view function pull request. It works at pallet level. If two chains use two different pallets to provide similar functionalities, like pallet-assets and pallet-erc20, we still need to have different codes to support. Therefore, it doesn't conflict with XCQ, and can be utilized by XCQ.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Prior Art and References","id":"35","title":"Prior Art and References"},"350":{"body":"The last entry is extracted from the header digest log, and is SCALE decoded as a VrfSignature object. The unsealed header is then SCALE encoded in order to be verified. The next entry is extracted from the header digest log, and is SCALE decoded as a ClaimData object. The validity of the two signatures is assessed using as the authority public key corresponding to the authority_index found in the ClaimData, together with the VRF input (which depends on primary/secondary method) and additional data used by the block author. let seal_signature = DECODE(POP(header.digest)); let unsealed_header_bytes = ENCODE(header); let claim_data = DECODE(POP(header.digest)); let authority_public_key = GET(authorities, claim_data.authority_index); // Verify seal signature let result = vrf_verify( authority_public_key, seal_vrf_input, unsealed_header_bytes, seal_signature ); ASSERT(result == 1); let randomness_vrf_input = CONCAT( BYTES(\"sassafras_randomness\"), vrf_signed_output(seal_signature) ); // Verify per-block entropy source signature let result = vrf_verify( authority_public_key, randomness_vrf_input, [], claim_data.randomness_source ); ASSERT(result == 1); With: header: The block's header. authorities: Sequence of authorities for the target epoch, as recorded on-chain. seal_vrf_input: VRF input data constructed as specified in 6.8 . If signatures verification is successful, then the verification process diverges based on whether the slot is associated with a ticket according to the on-chain state.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.9. Slot Claim Verification","id":"350","title":"6.9. Slot Claim Verification"},"351":{"body":"For slots tied to a ticket, the primary verification method is employed. This method verifies ticket ownership using the TicketId associated to the slot. let ticket_id = vrf_signed_output(seal_signature); ASSERT(ticket_id == expected_ticket_id); With expected_ticket_id the ticket identifier committed on-chain in the associated TicketBody. 6.9.2. Secondary Method If the slot doesn't have any associated ticket, then the authority_index contained in the ClaimData must match the one returned by the procedure outlined in section 6.8.2 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.9.1. Primary Method","id":"351","title":"6.9.1. Primary Method"},"352":{"body":"The randomness accumulator is updated using the randomness_source signature found within the ClaimData object. In particular, fresh randomness is derived and accumulated after block execution as follows: let fresh_randomness = vrf_signed_output(claim.randomness_source); randomness_buffer[0] = BLAKE2(CONCAT(randomness_buffer[0], fresh_randomness));","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.10. Randomness Accumulator","id":"352","title":"6.10. Randomness Accumulator"},"353":{"body":"None","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 7. Drawbacks","id":"353","title":"7. Drawbacks"},"354":{"body":"It is critical that implementations of this RFC undergo thorough rigorous testing. A security audit may be desirable to ensure the implementation does not introduce emergent side effects.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 8. Testing, Security, and Privacy","id":"354","title":"8. Testing, Security, and Privacy"},"355":{"body":"","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9. Performance, Ergonomics, and Compatibility","id":"355","title":"9. Performance, Ergonomics, and Compatibility"},"356":{"body":"Adopting Sassafras consensus marks a significant improvement in reducing the frequency of short-lived forks which are eliminated by design. Forks may only result from network disruption or protocol attacks. In such cases, the choice of which fork to follow upon recovery is clear-cut, with only one valid option.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.1. Performance","id":"356","title":"9.1. Performance"},"357":{"body":"No specific considerations.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.2. Ergonomics","id":"357","title":"9.2. Ergonomics"},"358":{"body":"The adoption of Sassafras affects the native client and thus can't be introduced via a \"simple\" runtime upgrade. A deployment strategy should be carefully engineered for live networks. This subject is left open for a dedicated RFC.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.3. Compatibility","id":"358","title":"9.3. Compatibility"},"359":{"body":"Sassafras layman introduction Sassafras research paper Bandersnatch VRFs specification Bandersnatch VRFs reference implementation W3F Ring VRF research paper Sassafras reference implementation tracking issue Sassafras reference implementation main PR","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 10. Prior Art and References","id":"359","title":"10. Prior Art and References"},"36":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Unresolved Questions","id":"36","title":"Unresolved Questions"},"360":{"body":"None","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 11. Unresolved Questions","id":"360","title":"11. Unresolved Questions"},"361":{"body":"While this RFC lays the groundwork and outlines the core aspects of the protocol, several crucial topics remain to be addressed in future RFCs.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12. Future Directions and Related Material","id":"361","title":"12. Future Directions and Related Material"},"362":{"body":"Storage : Types, organization and genesis configuration. Host interface : Interface that the hosting environment exposes to on-chain code (also known as host functions ). Unrecorded on-chain interface . Interface that on-chain code exposes to the hosting environment (also known as runtime API ). Transactional on-chain interface . Interface that on-chain code exposes to the World to alter the state (also known as transactions or extrinsics in the Polkadot ecosystem).","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.1. Interactions with On-Chain Code","id":"362","title":"12.1. Interactions with On-Chain Code"},"363":{"body":"Protocol Migration . Investigate of how Sassafras can seamlessly replace an already operational instance of another protocol. Future RFCs may focus on deployment strategies to facilitate a smooth transition.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.2. Deployment Strategies","id":"363","title":"12.2. Deployment Strategies"},"364":{"body":"Parameters Setup : Determine the setup procedure for the zk-SNARK SRS (Structured Reference String) initialization. Future RFCs may provide insights into whether this process should include an ad-hoc initialization ceremony or if we can reuse an SRS from another ecosystem (e.g. Zcash or Ethereum).","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.3. ZK-SNARK Parameters","id":"364","title":"12.3. ZK-SNARK Parameters"},"365":{"body":"Mixnet Integration : Submitting tickets directly to the relay can pose a risk of potential deanonymization through traffic analysis. Subsequent RFCs may investigate the potential for incorporating mix network protocol or other privacy-enhancing mechanisms to address this concern.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.4. Anonymous Submission of Tickets.","id":"365","title":"12.4. Anonymous Submission of Tickets."},"366":{"body":"(source) Table of Contents RFC-0032: Minimal Relay Summary Motivation Stakeholders Explanation Migrations Interfaces Functional Architecture Resource Allocation Deployment Kusama Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 20 September 2023 Description Proposal to minimise Relay Chain functionality. Authors Joe Petrowski, Gavin Wood","breadcrumbs":"RFC-0032: Minimal Relay » RFC-0032: Minimal Relay","id":"366","title":"RFC-0032: Minimal Relay"},"367":{"body":"The Relay Chain contains most of the core logic for the Polkadot network. While this was necessary prior to the launch of parachains and development of XCM, most of this logic can exist in parachains. This is a proposal to migrate several subsystems into system parachains.","breadcrumbs":"RFC-0032: Minimal Relay » Summary","id":"367","title":"Summary"},"368":{"body":"Polkadot's scaling approach allows many distinct state machines (known generally as parachains) to operate with common guarantees about the validity and security of their state transitions. Polkadot provides these common guarantees by executing the state transitions on a strict subset (a backing group) of the Relay Chain's validator set. However, state transitions on the Relay Chain need to be executed by all validators. If any of those state transitions can occur on parachains, then the resources of the complement of a single backing group could be used to offer more cores. As in, they could be offering more coretime (a.k.a. blockspace) to the network. By minimising state transition logic on the Relay Chain by migrating it into \"system chains\" -- a set of parachains that, with the Relay Chain, make up the Polkadot protocol -- the Polkadot Ubiquitous Computer can maximise its primary offering: secure blockspace.","breadcrumbs":"RFC-0032: Minimal Relay » Motivation","id":"368","title":"Motivation"},"369":{"body":"Parachains that interact with affected logic on the Relay Chain; Core protocol and XCM format developers; Tooling, block explorer, and UI developers.","breadcrumbs":"RFC-0032: Minimal Relay » Stakeholders","id":"369","title":"Stakeholders"},"37":{"body":"Since XCQ are supported both in off-chain and on-chain, a related XCM-Format RFC should be proposed.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Future Directions and Related Material","id":"37","title":"Future Directions and Related Material"},"370":{"body":"The following pallets and subsystems are good candidates to migrate from the Relay Chain: Identity Balances Staking Staking Election Provider Bags List NIS Nomination Pools Fast Unstake Governance Treasury and Bounties Conviction Voting Referenda Note: The Auctions and Crowdloan pallets will be replaced by Coretime, its system chain and interface described in RFC-1 and RFC-5, respectively.","breadcrumbs":"RFC-0032: Minimal Relay » Explanation","id":"370","title":"Explanation"},"371":{"body":"Some subsystems are simpler to move than others. For example, migrating Identity can be done by simply preventing state changes in the Relay Chain, using the Identity-related state as the genesis for a new chain, and launching that new chain with the genesis and logic (pallet) needed. Other subsystems cannot experience any downtime like this because they are essential to the network's functioning, like Staking and Governance. However, these can likely coexist with a similarly-permissioned system chain for some time, much like how \"Gov1\" and \"OpenGov\" coexisted at the latter's introduction. Specific migration plans will be included in release notes of runtimes from the Polkadot Fellowship when beginning the work of migrating a particular subsystem.","breadcrumbs":"RFC-0032: Minimal Relay » Migrations","id":"371","title":"Migrations"},"372":{"body":"The Relay Chain, in many cases, will still need to interact with these subsystems, especially Staking and Governance. These subsystems will require making some APIs available either via dispatchable calls accessible to XCM Transact or possibly XCM Instructions in future versions. For example, Staking provides a pallet-API to register points (e.g. for block production) and offences (e.g. equivocation). With Staking in a system chain, that chain would need to allow the Relay Chain to update validator points periodically so that it can correctly calculate rewards. A pub-sub protocol may also lend itself to these types of interactions.","breadcrumbs":"RFC-0032: Minimal Relay » Interfaces","id":"372","title":"Interfaces"},"373":{"body":"This RFC proposes that system chains form individual components within the system's architecture and that these components are chosen as functional groups. This approach allows synchronous composibility where it is most valuable, but isolates logic in such a way that provides flexibility for optimal resource allocation (see Resource Allocation ). For the subsystems discussed in this RFC, namely Identity, Governance, and Staking, this would mean: People Chain, for identity and personhood logic, providing functionality related to the attributes of single actors; Governance Chain, for governance and system collectives, providing functionality for pluralities to express their voices within the system; Staking Chain, for Polkadot's staking system, including elections, nominations, reward distribution, slashing, and non-interactive staking; and Asset Hub, for fungible and non-fungible assets, including DOT. The Collectives chain and Asset Hub already exist, so implementation of this RFC would mean two new chains (People and Staking), with Governance moving to the currently-known-as Collectives chain and Asset Hub being increasingly used for DOT over the Relay Chain. Note that one functional group will likely include many pallets, as we do not know how pallet configurations and interfaces will evolve over time.","breadcrumbs":"RFC-0032: Minimal Relay » Functional Architecture","id":"373","title":"Functional Architecture"},"374":{"body":"The system should minimise wasted blockspace. These three (and other) subsystems may not each consistently require a dedicated core. However, core scheduling is far more agile than functional grouping. While migrating functionality from one chain to another can be a multi-month endeavour, cores can be rescheduled almost on-the-fly. Migrations are also breaking changes to some use cases, for example other parachains that need to route XCM programs to particular chains. It is thus preferable to do them a single time in migrating off the Relay Chain, reducing the risk of needing parachain splits in the future. Therefore, chain boundaries should be based on functional grouping where synchronous composibility is most valuable; and efficient resource allocation should be managed by the core scheduling protocol. Many of these system chains (including Asset Hub) could often share a single core in a semi-round robin fashion (the coretime may not be uniform). When needed, for example during NPoS elections or slashing events, the scheduler could allocate a dedicated core to the chain in need of more throughput.","breadcrumbs":"RFC-0032: Minimal Relay » Resource Allocation","id":"374","title":"Resource Allocation"},"375":{"body":"Actual migrations should happen based on some prioritization. This RFC proposes to migrate Identity, Staking, and Governance as the systems to work on first. A brief discussion on the factors involved in each one: Identity Identity will be one of the simpler pallets to migrate into a system chain, as its logic is largely self-contained and it does not \"share\" balances with other subsystems. As in, any DOT is held in reserve as a storage deposit and cannot be simultaneously used the way locked DOT can be locked for multiple purposes. Therefore, migration can take place as follows: The pallet can be put in a locked state, blocking most calls to the pallet and preventing updates to identity info. The frozen state will form the genesis of a new system parachain. Functions will be added to the pallet that allow migrating the deposit to the parachain. The parachain deposit is on the order of 1/100th of the Relay Chain's. Therefore, this will result in freeing up Relay State as well as most of each user's reserved balance. The pallet and any leftover state can be removed from the Relay Chain. User interfaces that render Identity information will need to source their data from the new system parachain. Note: In the future, it may make sense to decommission Kusama's Identity chain and do all account identities via Polkadot's. However, the Kusama chain will serve as a dress rehearsal for Polkadot. Staking Migrating the staking subsystem will likely be the most complex technical undertaking, as the Staking system cannot stop (the system MUST always have a validator set) nor run in parallel (the system MUST have only one validator set) and the subsystem itself is made up of subsystems in the runtime and the node. For example, if offences are reported to the Staking parachain, validator nodes will need to submit their reports there. Handling balances also introduces complications. The same balance can be used for staking and governance. Ideally, all balances stay on Asset Hub, and only report \"credits\" to system chains like Staking and Governance. However, staking mutates balances by issuing new DOT on era changes and for rewards. Allowing DOT directly on the Staking parachain would simplify staking changes. Given the complexity, it would be pragmatic to include the Balances pallet in the Staking parachain in its first version. Any other systems that use overlapping locks, most notably governance, will need to recognise DOT held on both Asset Hub and the Staking parachain. There is more discussion about staking in a parachain in Moving Staking off the Relay Chain . Governance Migrating governance into a parachain will be less complicated than staking. Most of the primitives needed for the migration already exist. The Treasury supports spending assets on remote chains and collectives like the Polkadot Technical Fellowship already function in a parachain. That is, XCM already provides the ability to express system origins across chains. Therefore, actually moving the governance logic into a parachain will be simple. It can run in parallel with the Relay Chain's governance, which can be removed when the parachain has demonstrated sufficient functionality. It's possible that the Relay Chain maintain a Root-level emergency track for situations like parachains halting . The only complication arises from the fact that both Asset Hub and the Staking parachain will have DOT balances; therefore, the Governance chain will need to be able to credit users' voting power based on balances from both locations. This is not expected to be difficult to handle.","breadcrumbs":"RFC-0032: Minimal Relay » Deployment","id":"375","title":"Deployment"},"376":{"body":"Although Polkadot and Kusama both have system chains running, they have to date only been used for introducing new features or bodies, for example fungible assets or the Technical Fellowship. There has not yet been a migration of logic/state from the Relay Chain into a parachain. Given its more realistic network conditions than testnets, Kusama is the best stage for rehearsal. In the case of identity, Polkadot's system may be sufficient for the ecosystem. Therefore, Kusama should be used to test the migration of logic and state from Relay Chain to parachain, but these features may be (at the will of Kusama's governance) dropped from Kusama entirely after a successful migration on Polkadot. For Governance, Polkadot already has the Collectives parachain, which would become the Governance parachain. The entire group of DOT holders is itself a collective (the legislative body), and governance provides the means to express voice. Launching a Kusama Governance chain would be sensible to rehearse a migration. The Staking subsystem is perhaps where Kusama would provide the most value in its canary capacity. Staking is the subsystem most constrained by PoV limits. Ensuring that elections, payouts, session changes, offences/slashes, etc. work in a parachain on Kusama -- with its larger validator set -- will give confidence to the chain's robustness on Polkadot.","breadcrumbs":"RFC-0032: Minimal Relay » Kusama","id":"376","title":"Kusama"},"377":{"body":"These subsystems will have reduced resources in cores than on the Relay Chain. Staking in particular may require some optimizations to deal with constraints.","breadcrumbs":"RFC-0032: Minimal Relay » Drawbacks","id":"377","title":"Drawbacks"},"378":{"body":"Standard audit/review requirements apply. More powerful multi-chain integration test tools would be useful in developement.","breadcrumbs":"RFC-0032: Minimal Relay » Testing, Security, and Privacy","id":"378","title":"Testing, Security, and Privacy"},"379":{"body":"Describe the impact of the proposal on the exposed functionality of Polkadot.","breadcrumbs":"RFC-0032: Minimal Relay » Performance, Ergonomics, and Compatibility","id":"379","title":"Performance, Ergonomics, and Compatibility"},"38":{"body":"(source) Table of Contents RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups Background Motivation Requirements Stakeholders JAM Service Design Overview Refine: Key Validation Process: Storage Proofs Accumulate Transfer Beefy Service PoC Implementation Gas + Storage Considerations Compatibility Testing, Security, and Privacy Future Directions and Related Material Drawbacks, Alternatives, and Unknowns Start Date 26 October 2024 Description JAM Service for Securing Ethereum Optimistic Rollups Authors Sourabh Niyogi Abstract JAM's rollup host function can be extended from Polkadot rollups to non-Polkadot rollups. We outline the design of a JAM service capable of securing Ethereum optimistic rollups, such as OP Stack and ArbOS. This service transforms optimistic rollups to cynical rollups, allowing users to benefit from the finality and high throughput of JAM, alongside JAM's anticipated messaging service. This JAM service's competitive advantage enables rollup operators to choose JAM/Polkadot over Ethereum or other rollup providers. A precise design for the service's refine-accumulate function is outlined, using tools already available.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups","id":"38","title":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups"},"380":{"body":"This is an optimization. The removal of public/user transactions on the Relay Chain ensures that its primary resources are allocated to system performance.","breadcrumbs":"RFC-0032: Minimal Relay » Performance","id":"380","title":"Performance"},"381":{"body":"This proposal alters very little for coretime users (e.g. parachain developers). Application developers will need to interact with multiple chains, making ergonomic light client tools particularly important for application development. For existing parachains that interact with these subsystems, they will need to configure their runtimes to recognize the new locations in the network.","breadcrumbs":"RFC-0032: Minimal Relay » Ergonomics","id":"381","title":"Ergonomics"},"382":{"body":"Implementing this proposal will require some changes to pallet APIs and/or a pub-sub protocol. Application developers will need to interact with multiple chains in the network.","breadcrumbs":"RFC-0032: Minimal Relay » Compatibility","id":"382","title":"Compatibility"},"383":{"body":"Transactionless Relay-chain Moving Staking off the Relay Chain","breadcrumbs":"RFC-0032: Minimal Relay » Prior Art and References","id":"383","title":"Prior Art and References"},"384":{"body":"There remain some implementation questions, like how to use balances for both Staking and Governance. See, for example, Moving Staking off the Relay Chain .","breadcrumbs":"RFC-0032: Minimal Relay » Unresolved Questions","id":"384","title":"Unresolved Questions"},"385":{"body":"Ideally the Relay Chain becomes transactionless, such that not even balances are represented there. With Staking and Governance off the Relay Chain, this is not an unreasonable next step. With Identity on Polkadot, Kusama may opt to drop its People Chain.","breadcrumbs":"RFC-0032: Minimal Relay » Future Directions and Related Material","id":"385","title":"Future Directions and Related Material"},"386":{"body":"(source) Table of Contents RFC-0042: Add System version that replaces StateVersion on RuntimeVersion Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 25th October 2023 Description Add System Version and remove State Version Authors Vedhavyas Singareddi","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » RFC-0042: Add System version that replaces StateVersion on RuntimeVersion","id":"386","title":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion"},"387":{"body":"At the moment, we have system_version field on RuntimeVersion that derives which state version is used for the Storage. We have a use case where we want extrinsics root is derived using StateVersion::V1. Without defining a new field under RuntimeVersion, we would like to propose adding system_version that can be used to derive both storage and extrinsic state version.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Summary","id":"387","title":"Summary"},"388":{"body":"Since the extrinsic state version is always StateVersion::V0, deriving extrinsic root requires full extrinsic data. This would be problematic when we need to verify the extrinsics root if the extrinsic sizes are bigger. This problem is further explored in https://github.com/polkadot-fellows/RFCs/issues/19 For Subspace project, we have an enshrined rollups called Domain with optimistic verification and Fraud proofs are used to detect malicious behavior. One of the Fraud proof variant is to derive Domain block extrinsic root on Subspace's consensus chain. Since StateVersion::V0 requires full extrinsic data, we are forced to pass all the extrinsics through the Fraud proof. One of the main challenge here is some extrinsics could be big enough that this variant of Fraud proof may not be included in the Consensus block due to Block's weight restriction. If the extrinsic root is derived using StateVersion::V1, then we do not need to pass the full extrinsic data but rather at maximum, 32 byte of extrinsic data.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Motivation","id":"388","title":"Motivation"},"389":{"body":"Technical Fellowship, in its role of maintaining system runtimes.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Stakeholders","id":"389","title":"Stakeholders"},"39":{"body":"The Gray Paper suggests a design for applying the same audit protocol from Polkadot's parachain validation service to ETH rollups: \" Smart-contract state may be held in a coherent format on the JAM chain so long as any updates are made through the 15kb/core/sec work results, which would need to contain only the hashes of the altered contracts’ state roots . \" This proposal concretely addresses two top non-Polkadot optimistic rollup platforms: OP Stack and ArbOS . Optimistic rollups use centralized sequencers and have no forks, creating an illusion of fast finality while actually relying on delayed fraud proofs. Optimistic rollups are termed \"optimistic\" because they assume transactions are valid by default, requiring fraud proofs on Ethereum L1 if a dispute arises. Currently, ORUs store L2 data on ETH L1, using EIP-4844's blob transactions or similar DA alternatives, just long enough to allow for fraud proof submission. This approach, however, incurs a cost: a 7-day exit window to accommodate fraud proofs. JAM Service can eliminate this long exit window by validating optimistic rollups.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Background","id":"39","title":"Background"},"390":{"body":"In order to use project specific StateVersion for extrinsic roots, we proposed an implementation that introduced parameter to frame_system::Config but that unfortunately did not feel correct. So we would like to propose adding this change to the RuntimeVersion object. The system version, if introduced, will be used to derive both storage and extrinsic state version. If system version is 0, then both Storage and Extrinsic State version would use V0. If system version is 1, then Storage State version would use V1 and Extrinsic State version would use V0. If system version is 2, then both Storage and Extrinsic State version would use V1. If implemented, the new RuntimeVersion definition would look something similar to /// Runtime version (Rococo).\n#[sp_version::runtime_version]\npub const VERSION: RuntimeVersion = RuntimeVersion { spec_name: create_runtime_str!(\"rococo\"), impl_name: create_runtime_str!(\"parity-rococo-v2.0\"), authoring_version: 0, spec_version: 10020, impl_version: 0, apis: RUNTIME_API_VERSIONS, transaction_version: 22, system_version: 1, };","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Explanation","id":"390","title":"Explanation"},"391":{"body":"There should be no drawbacks as it would replace state_version with same behavior but documentation should be updated so that chains know which system_version to use.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Drawbacks","id":"391","title":"Drawbacks"},"392":{"body":"AFAIK, should not have any impact on the security or privacy.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Testing, Security, and Privacy","id":"392","title":"Testing, Security, and Privacy"},"393":{"body":"These changes should be compatible for existing chains if they use state_version value for system_verision.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Performance, Ergonomics, and Compatibility","id":"393","title":"Performance, Ergonomics, and Compatibility"},"394":{"body":"I do not believe there is any performance hit with this change.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Performance","id":"394","title":"Performance"},"395":{"body":"This does not break any exposed Apis.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Ergonomics","id":"395","title":"Ergonomics"},"396":{"body":"This change should not break any compatibility.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Compatibility","id":"396","title":"Compatibility"},"397":{"body":"We proposed introducing a similar change by introducing a parameter to frame_system::Config but did not feel that is the correct way of introducing this change.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Prior Art and References","id":"397","title":"Prior Art and References"},"398":{"body":"I do not have any specific questions about this change at the moment.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Unresolved Questions","id":"398","title":"Unresolved Questions"},"399":{"body":"IMO, this change is pretty self-contained and there won't be any future work necessary.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Future Directions and Related Material","id":"399","title":"Future Directions and Related Material"},"4":{"body":"Runtime users, Runtime devs, Cross-chain dApps, Wallets.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Stakeholders","id":"4","title":"Stakeholders"},"40":{"body":"JAM is intended to host rollups rather than serve end users directly. A secure JAM service for Optimistic Rollups will expand JAM's service scope to include optimistic rollups and enhance their appeal with JAM's finality. This expanded focus on rollups will increase CoreTime demand, making JAM attractive to both existing and new optimistic rollups by reducing exit windows. This JAM Service converts optimistic rollups into cynical rollups, delivering a user experience advantage that is marketable. With popular CEXes (Coinbase, Kraken) adopting OP Stack, this improvement is highly visible to retail users, turning ORUs into CRUs \"Secured by JAM\" for a competitive edge.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Motivation","id":"40","title":"Motivation"},"400":{"body":"(source) Table of Contents RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization Summary Motivation Stakeholders Explanation Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Start Date 30 October 2023 Description Host function to provide the storage proof size to runtimes. Authors Sebastian Kunert","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization","id":"400","title":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization"},"401":{"body":"This RFC proposes a new host function for parachains, storage_proof_size. It shall provide the size of the currently recorded storage proof to the runtime. Runtime authors can use the proof size to improve block utilization by retroactively reclaiming unused storage weight.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Summary","id":"401","title":"Summary"},"402":{"body":"The number of extrinsics that are included in a parachain block is limited by two constraints: execution time and proof size. FRAME weights cover both concepts, and block-builders use them to decide how many extrinsics to include in a block. However, these weights are calculated ahead of time by benchmarking on a machine with reference hardware. The execution-time properties of the state-trie and its storage items are unknown at benchmarking time. Therefore, we make some assumptions about the state-trie: Trie Depth: We assume a trie depth to account for intermediary nodes. Storage Item Size: We make a pessimistic assumption based on the MaxEncodedLen trait. These pessimistic assumptions lead to an overestimation of storage weight, negatively impacting block utilization on parachains. In addition, the current model does not account for multiple accesses to the same storage items. While these repetitive accesses will not increase storage-proof size, the runtime-side weight monitoring will account for them multiple times. Since the proof size is completely opaque to the runtime, we can not implement retroactive storage weight correction. A solution must provide a way for the runtime to track the exact storage-proof size consumed on a per-extrinsic basis.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Motivation","id":"402","title":"Motivation"},"403":{"body":"Parachain Teams: They MUST include this host function in their runtime and node. Light-client Implementors: They SHOULD include this host function in their runtime and node.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Stakeholders","id":"403","title":"Stakeholders"},"404":{"body":"This RFC proposes a new host function that exposes the storage-proof size to the runtime. As a result, runtimes can implement storage weight reclaiming mechanisms that improve block utilization. This RFC proposes the following host function signature: fn ext_storage_proof_size_version_1() -> u64; The host function MUST return an unsigned 64-bit integer value representing the current proof size. In block-execution and block-import contexts, this function MUST return the current size of the proof. To achieve this, parachain node implementors need to enable proof recording for block imports. In other contexts, this function MUST return 18446744073709551615 (u64::MAX), which represents disabled proof recording.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Explanation","id":"404","title":"Explanation"},"405":{"body":"","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Performance, Ergonomics, and Compatibility","id":"405","title":"Performance, Ergonomics, and Compatibility"},"406":{"body":"Parachain nodes need to enable proof recording during block import to correctly implement the proposed host function. Benchmarking conducted with balance transfers has shown a performance reduction of around 0.6% when proof recording is enabled.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Performance","id":"406","title":"Performance"},"407":{"body":"The host function proposed in this RFC allows parachain runtime developers to keep track of the proof size. Typical usage patterns would be to keep track of the overall proof size or the difference between subsequent calls to the host function.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Ergonomics","id":"407","title":"Ergonomics"},"408":{"body":"Parachain teams will need to include this host function to upgrade.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Compatibility","id":"408","title":"Compatibility"},"409":{"body":"Pull Request including proposed host function: PoV Reclaim (Clawback) Node Side . Issue with discussion: [FRAME core] Clawback PoV Weights For Dispatchables","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Prior Art and References","id":"409","title":"Prior Art and References"},"41":{"body":"Securing optimistic rollups with a JAM Service should be practical and require minimal changes by the ORU operator. Securing Polkadot rollups with a JAM Service should not be affected.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Requirements","id":"41","title":"Requirements"},"410":{"body":"(source) Table of Contents RFC-0045: Lowering NFT Deposits on Asset Hub Summary Motivation Requirements Stakeholders Explanation Enhanced Approach to Further Lower Barriers for Entry Short- and Long-Term Plans Drawbacks Testing, Security, and Privacy Security concerns Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Unresolved Questions Addendum Enhanced Weak Governance Origin Model Function-Based Pricing Model Linking Deposit to USD(x) Value Start Date 2 November 2023 Description A proposal to reduce the minimum deposit required for collection creation on the Polkadot and Kusama Asset Hubs. Authors Aurora Poppyseed , Just_Luuuu , Viki Val , Joe Petrowski","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » RFC-0045: Lowering NFT Deposits on Asset Hub","id":"410","title":"RFC-0045: Lowering NFT Deposits on Asset Hub"},"411":{"body":"This RFC proposes changing the current deposit requirements on the Polkadot and Kusama Asset Hub for creating an NFT collection, minting an individual NFT, and lowering its corresponding metadata and attribute deposits. The objective is to lower the barrier to entry for NFT creators, fostering a more inclusive and vibrant ecosystem while maintaining network integrity and preventing spam.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Summary","id":"411","title":"Summary"},"412":{"body":"The current deposit of 10 DOT for collection creation (along with 0.01 DOT for item deposit and 0.2 DOT for metadata and attribute deposits) on the Polkadot Asset Hub and 0.1 KSM on Kusama Asset Hub presents a significant financial barrier for many NFT creators. By lowering the deposit requirements, we aim to encourage more NFT creators to participate in the Polkadot NFT ecosystem, thereby enriching the diversity and vibrancy of the community and its offerings. The initial introduction of a 10 DOT deposit was an arbitrary starting point that does not consider the actual storage footprint of an NFT collection. This proposal aims to adjust the deposit first to a value based on the deposit function, which calculates a deposit based on the number of keys introduced to storage and the size of corresponding values stored. Further, it suggests a direction for a future of calculating deposits variably based on adoption and/or market conditions. There is a discussion on tradeoffs of setting deposits too high or too low.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Motivation","id":"412","title":"Motivation"},"413":{"body":"Deposits SHOULD be derived from deposit function, adjusted by correspoding pricing mechansim.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Requirements","id":"413","title":"Requirements"},"414":{"body":"NFT Creators : Primary beneficiaries of the proposed change, particularly those who found the current deposit requirements prohibitive. NFT Platforms : As the facilitator of artists' relations, NFT marketplaces have a vested interest in onboarding new users and making their platforms more accessible. dApp Developers : Making the blockspace more accessible will encourage developers to create and build unique dApps in the Polkadot ecosystem. Polkadot Community : Stands to benefit from an influx of artists, creators, and diverse NFT collections, enhancing the overall ecosystem. Previous discussions have been held within the Polkadot Forum , with artists expressing their concerns about the deposit amounts.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Stakeholders","id":"414","title":"Stakeholders"},"415":{"body":"This RFC proposes a revision of the deposit constants in the configuration of the NFTs pallet on the Polkadot Asset Hub. The new deposit amounts would be determined by a standard deposit formula. As of v1.1.1, the Collection Deposit is 10 DOT and the Item Deposit is 0.01 DOT (see here ). Based on the storage footprint of these items, this RFC proposes changing them to: pub const NftsCollectionDeposit: Balance = system_para_deposit(1, 130);\npub const NftsItemDeposit: Balance = system_para_deposit(1, 164); This results in the following deposits (calculted using this repository ): Polkadot Name Current Rate (DOT) Calculated with Function (DOT) collectionDeposit 10 0.20064 itemDeposit 0.01 0.20081 metadataDepositBase 0.20129 0.20076 attributeDepositBase 0.2 0.2 Similarly, the prices for Kusama were calculated as: Kusama: Name Current Rate (KSM) Calculated with Function (KSM) collectionDeposit 0.1 0.006688 itemDeposit 0.001 0.000167 metadataDepositBase 0.006709666617 0.0006709666617 attributeDepositBase 0.00666666666 0.000666666666","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Explanation","id":"415","title":"Explanation"},"416":{"body":"This RFC proposes further lowering these deposits below the rate normally charged for such a storage footprint. This is based on the economic argument that sub-rate deposits are a subsididy for growth and adoption of a specific technology. If the NFT functionality on Polkadot gains adoption, it makes it more attractive for future entrants, who would be willing to pay the non-subsidized rate because of the existing community. Proposed Rate Adjustments parameter_types! { pub const NftsCollectionDeposit: Balance = system_para_deposit(1, 130); pub const NftsItemDeposit: Balance = system_para_deposit(1, 164) / 40; pub const NftsMetadataDepositBase: Balance = system_para_deposit(1, 129) / 10; pub const NftsAttributeDepositBase: Balance = system_para_deposit(1, 0) / 10; pub const NftsDepositPerByte: Balance = system_para_deposit(0, 1);\n} This adjustment would result in the following DOT and KSM deposit values: Name Proposed Rate Polkadot Proposed Rate Kusama collectionDeposit 0.20064 DOT 0.006688 KSM itemDeposit 0.005 DOT 0.000167 KSM metadataDepositBase 0.002 DOT 0.0006709666617 KSM attributeDepositBase 0.002 DOT 0.000666666666 KSM","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Enhanced Approach to Further Lower Barriers for Entry","id":"416","title":"Enhanced Approach to Further Lower Barriers for Entry"},"417":{"body":"The plan presented above is recommended as an immediate step to make Polkadot a more attractive place to launch NFTs, although one would note that a forty fold reduction in the Item Deposit is just as arbitrary as the value it was replacing. As explained earlier, this is meant as a subsidy to gain more momentum for NFTs on Polkadot. In the long term, an implementation should account for what should happen to the deposit rates assuming that the subsidy is successful and attracts a lot of deployments. Many options are discussed in the Addendum . The deposit should be calculated as a function of the number of existing collections with maximum DOT and stablecoin values limiting the amount. With asset rates available via the Asset Conversion pallet, the system could take the lower value required. A sigmoid curve would make sense for this application to avoid sudden rate changes, as in: $$ minDeposit + \\frac{\\mathrm{min(DotDeposit, StableDeposit) - minDeposit} }{\\mathrm{1 + e^{a - b * x}} }$$ where the constant a moves the inflection to lower or higher x values, the constant b adjusts the rate of the deposit increase, and the independent variable x is the number of collections or items, depending on application.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Short- and Long-Term Plans","id":"417","title":"Short- and Long-Term Plans"},"418":{"body":"Modifying deposit requirements necessitates a balanced assessment of the potential drawbacks. Highlighted below are cogent points extracted from the discourse on the Polkadot Forum conversation , which provide critical perspectives on the implications of such changes. Adjusting NFT deposit requirements on Polkadot and Kusama Asset Hubs involves key challenges: State Growth and Technical Concerns : Lowering deposit requirements can lead to increased blockchain state size, potentially causing state bloat. This growth needs to be managed to prevent strain on the network's resources and maintain operational efficiency. As stated earlier, the deposit levels proposed here are intentionally low with the thesis that future participants would pay the standard rate. Network Security and Market Response : Adapting to the cryptocurrency market's volatility is crucial. The mechanism for setting deposit amounts must be responsive yet stable, avoiding undue complexity for users. Economic Impact on Previous Stakeholders : The change could have varied economic effects on previous (before the change) creators, platform operators, and investors. Balancing these interests is essential to ensure the adjustment benefits the ecosystem without negatively impacting its value dynamics. However in the particular case of Polkadot and Kusama Asset Hub this does not pose a concern since there are very few collections currently and thus previous stakeholders wouldn't be much affected. As of date 9th January 2024 there are 42 collections on Polkadot Asset Hub and 191 on Kusama Asset Hub with a relatively low volume.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Drawbacks","id":"418","title":"Drawbacks"},"419":{"body":"","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Testing, Security, and Privacy","id":"419","title":"Testing, Security, and Privacy"},"42":{"body":"Optimistic Rollup Operators seeking shorter exit windows, lower costs, higher scalability, and DA. Web3 developers wanting to create applications on cynical rollups secured by JAM. DOT Holders aiming to increase CoreTime demand.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Stakeholders","id":"42","title":"Stakeholders"},"420":{"body":"As noted above, state bloat is a security concern. In the case of abuse, governance could adapt by increasing deposit rates and/or using forceDestroy on collections agreed to be spam.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Security concerns","id":"420","title":"Security concerns"},"421":{"body":"","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Performance, Ergonomics, and Compatibility","id":"421","title":"Performance, Ergonomics, and Compatibility"},"422":{"body":"The primary performance consideration stems from the potential for state bloat due to increased activity from lower deposit requirements. It's vital to monitor and manage this to avoid any negative impact on the chain's performance. Strategies for mitigating state bloat, including efficient data management and periodic reviews of storage requirements, will be essential.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Performance","id":"422","title":"Performance"},"423":{"body":"The proposed change aims to enhance the user experience for artists, traders, and utilizers of Kusama and Polkadot Asset Hubs, making Polkadot and Kusama more accessible and user-friendly.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Ergonomics","id":"423","title":"Ergonomics"},"424":{"body":"The change does not impact compatibility as a redeposit function is already implemented.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Compatibility","id":"424","title":"Compatibility"},"425":{"body":"If this RFC is accepted, there should not be any unresolved questions regarding how to adapt the implementation of deposits for NFT collections.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Unresolved Questions","id":"425","title":"Unresolved Questions"},"426":{"body":"Several innovative proposals have been considered to enhance the network's adaptability and manage deposit requirements more effectively. The RFC recommends a mixture of the function-based model and the stablecoin model, but some tradeoffs of each are maintained here for those interested.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Addendum","id":"426","title":"Addendum"},"427":{"body":"The concept of a weak governance origin, controlled by a consortium like a system collective, has been proposed. This model would allow for dynamic adjustments of NFT deposit requirements in response to market conditions, adhering to storage deposit norms. Responsiveness : To address concerns about delayed responses, the model could incorporate automated triggers based on predefined market indicators, ensuring timely adjustments. Stability vs. Flexibility : Balancing stability with the need for flexibility is challenging. To mitigate the issue of frequent changes in DOT-based deposits, a mechanism for gradual and predictable adjustments could be introduced. Scalability : The model's scalability is a concern, given the numerous deposits across the system. A more centralized approach to deposit management might be needed to avoid constant, decentralized adjustments.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Enhanced Weak Governance Origin Model","id":"427","title":"Enhanced Weak Governance Origin Model"},"428":{"body":"Another proposal is to use a mathematical function to regulate deposit prices, initially allowing low prices to encourage participation, followed by a gradual increase to prevent network bloat. Choice of Function : A logarithmic or sigmoid function is favored over an exponential one, as these functions increase prices at a rate that encourages participation while preventing prohibitive costs. Adjustment of Constants : To finely tune the pricing rise, one of the function's constants could correlate with the total number of NFTs on Asset Hub. This would align the deposit requirements with the actual usage and growth of the network.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Function-Based Pricing Model","id":"428","title":"Function-Based Pricing Model"},"429":{"body":"This approach suggests pegging the deposit value to a stable currency like the USD, introducing predictability and stability for network users. Market Dynamics : One perspective is that fluctuations in native currency value naturally balance user participation and pricing, deterring network spam while encouraging higher-value collections. Conversely, there's an argument for allowing broader participation if the DOT/KSM value increases. Complexity and Risks : Implementing a USD-based pricing system could add complexity and potential risks. The implementation needs to be carefully designed to avoid unintended consequences, such as excessive reliance on external financial systems or currencies. Each of these proposals offers unique advantages and challenges. The optimal approach may involve a combination of these ideas, carefully adjusted to address the specific needs and dynamics of the Polkadot and Kusama networks.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Linking Deposit to USD(x) Value","id":"429","title":"Linking Deposit to USD(x) Value"},"43":{"body":"","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » JAM Service Design","id":"43","title":"JAM Service Design"},"430":{"body":"(source) Table of Contents RFC-0047: Assignment of availability chunks to validators Summary Motivation Stakeholders Explanation Systematic erasure codes Availability recovery at present Availability recovery from systematic chunks Chunk assignment function Network protocol Upgrade path Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Appendix A Start Date 03 November 2023 Description An evenly-distributing indirection layer between availability chunks and validators. Authors Alin Dima","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » RFC-0047: Assignment of availability chunks to validators","id":"430","title":"RFC-0047: Assignment of availability chunks to validators"},"431":{"body":"Propose a way of permuting the availability chunk indices assigned to validators, in the context of recovering available data from systematic chunks , with the purpose of fairly distributing network bandwidth usage.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Summary","id":"431","title":"Summary"},"432":{"body":"Currently, the ValidatorIndex is always identical to the ChunkIndex. Since the validator array is only shuffled once per session, naively using the ValidatorIndex as the ChunkIndex would pose an unreasonable stress on the first N/3 validators during an entire session, when favouring availability recovery from systematic chunks. Therefore, the relay chain node needs a deterministic way of evenly distributing the first ~(N_VALIDATORS / 3) systematic availability chunks to different validators, based on the relay chain block and core. The main purpose is to ensure fair distribution of network bandwidth usage for availability recovery in general and in particular for systematic chunk holders.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Motivation","id":"432","title":"Motivation"},"433":{"body":"Relay chain node core developers.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Stakeholders","id":"433","title":"Stakeholders"},"434":{"body":"","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Explanation","id":"434","title":"Explanation"},"435":{"body":"An erasure coding algorithm is considered systematic if it preserves the original unencoded data as part of the resulting code. The implementation of the erasure coding algorithm used for polkadot's availability data is systematic. Roughly speaking, the first N_VALIDATORS/3 chunks of data can be cheaply concatenated to retrieve the original data, without running the resource-intensive and time-consuming reconstruction algorithm. You can find the concatenation procedure of systematic chunks for polkadot's erasure coding algorithm here In a nutshell, it performs a column-wise concatenation with 2-byte chunks. The output could be zero-padded at the end, so scale decoding must be aware of the expected length in bytes and ignore trailing zeros (this assertion is already being made for regular reconstruction).","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Systematic erasure codes","id":"435","title":"Systematic erasure codes"},"436":{"body":"According to the polkadot protocol spec : A validator should request chunks by picking peers randomly and must recover at least f+1 chunks, where n=3f+k and k in {1,2,3}. For parity's polkadot node implementation, the process was further optimised. At this moment, it works differently based on the estimated size of the available data: (a) for small PoVs (up to 128 Kib), sequentially try requesting the unencoded data from the backing group, in a random order. If this fails, fallback to option (b). (b) for large PoVs (over 128 Kib), launch N parallel requests for the erasure coded chunks (currently, N has an upper limit of 50), until enough chunks were recovered. Validators are tried in a random order. Then, reconstruct the original data. All options require that after reconstruction, validators then re-encode the data and re-create the erasure chunks trie in order to check the erasure root.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Availability recovery at present","id":"436","title":"Availability recovery at present"},"437":{"body":"As part of the effort of increasing polkadot's resource efficiency, scalability and performance , work is under way to modify the Availability Recovery protocol by leveraging systematic chunks. See this comment for preliminary performance results. In this scheme, the relay chain node will first attempt to retrieve the ~N/3 systematic chunks from the validators that should hold them, before falling back to recovering from regular chunks, as before. A re-encoding step is still needed for verifying the erasure root, so the erasure coding overhead cannot be completely brought down to 0. Not being able to retrieve even one systematic chunk would make systematic reconstruction impossible. Therefore, backers can be used as a backup to retrieve a couple of missing systematic chunks, before falling back to retrieving regular chunks.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Availability recovery from systematic chunks","id":"437","title":"Availability recovery from systematic chunks"},"438":{"body":"Properties The function that decides the chunk index for a validator will be parameterized by at least (validator_index, core_index) and have the following properties: deterministic relatively quick to compute and resource-efficient. when considering a fixed core_index, the function should describe a permutation of the chunk indices the validators that map to the first N/3 chunk indices should have as little overlap as possible for different cores. In other words, we want a uniformly distributed, deterministic mapping from ValidatorIndex to ChunkIndex per core. It's desirable to not embed this function in the runtime, for performance and complexity reasons. However, this means that the function needs to be kept very simple and with minimal or no external dependencies. Any change to this function could result in parachains being stalled and needs to be coordinated via a runtime upgrade or governance call. Proposed function Pseudocode: pub fn get_chunk_index( n_validators: u32, validator_index: ValidatorIndex, core_index: CoreIndex\n) -> ChunkIndex { let threshold = systematic_threshold(n_validators); // Roughly n_validators/3 let core_start_pos = core_index * threshold; (core_start_pos + validator_index) % n_validators\n}","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Chunk assignment function","id":"438","title":"Chunk assignment function"},"439":{"body":"The request-response /req_chunk protocol will be bumped to a new version (from v1 to v2). For v1, the request and response payloads are: /// Request an availability chunk.\npub struct ChunkFetchingRequest { /// Hash of candidate we want a chunk for. pub candidate_hash: CandidateHash, /// The index of the chunk to fetch. pub index: ValidatorIndex,\n} /// Receive a requested erasure chunk.\npub enum ChunkFetchingResponse { /// The requested chunk data. Chunk(ChunkResponse), /// Node was not in possession of the requested chunk. NoSuchChunk,\n} /// This omits the chunk's index because it is already known by\n/// the requester and by not transmitting it, we ensure the requester is going to use his index\n/// value for validating the response, thus making sure he got what he requested.\npub struct ChunkResponse { /// The erasure-encoded chunk of data belonging to the candidate block. pub chunk: Vec, /// Proof for this chunk's branch in the Merkle tree. pub proof: Proof,\n} Version 2 will add an index field to ChunkResponse: #[derive(Debug, Clone, Encode, Decode)]\npub struct ChunkResponse { /// The erasure-encoded chunk of data belonging to the candidate block. pub chunk: Vec, /// Proof for this chunk's branch in the Merkle tree. pub proof: Proof, /// Chunk index. pub index: ChunkIndex\n} An important thing to note is that in version 1, the ValidatorIndex value is always equal to the ChunkIndex. Until the chunk rotation feature is enabled, this will also be true for version 2. However, after the feature is enabled, this will generally not be true. The requester will send the request to validator with index V. The responder will map the V validator index to the C chunk index and respond with the C-th chunk. This mapping can be seamless, by having each validator store their chunk by ValidatorIndex (just as before). The protocol implementation MAY check the returned ChunkIndex against the expected mapping to ensure that it received the right chunk. In practice, this is desirable during availability-distribution and systematic chunk recovery. However, regular recovery may not check this index, which is particularly useful when participating in disputes that don't allow for easy access to the validator->chunk mapping. See Appendix A for more details. In any case, the requester MUST verify the chunk's proof using the provided index. During availability-recovery, given that the requester may not know (if the mapping is not available) whether the received chunk corresponds to the requested validator index, it has to keep track of received chunk indices and ignore duplicates. Such duplicates should be considered the same as an invalid/garbage response (drop it and move on to the next validator - we can't punish via reputation changes, because we don't know which validator misbehaved).","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Network protocol","id":"439","title":"Network protocol"},"44":{"body":"Rollups produce a sequence of blocks ${\\bf B}$ with headers ${\\bf H}$. The header ${\\bf H}$ contains a parent header hash ${\\bf H} p$ and a state root ${\\bf H} {r}$, which represents the global state after applying all block transactions. The transactions trie root is unnecessary here; validating the state trie root alone is sufficient for securing rollups. This JAM Service strategy, as hinted in the JAM Gray Paper, aggregates storage proofs of altered smart account/contract states into a chain of work packages. These validate an uninterrupted chain of an optimistic rollup's blocks against the state root ${\\bf H}_r$. Instead of relying on a promise that the state root is correct unless proven otherwise, JAM validates it using storage proofs for each contract update across $N$ blocks. The rollup operator submits headers and Merkle proofs in a chain of work packages $..., p_{n-1}, p_{n}, p_{n+1}, ...$ corresponding to the rollup chain, grouping $N$ blocks of data in each package. Typically, each work package $p_n$ requires a prerequisite work package $p_{n-1}$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Overview","id":"44","title":"Overview"},"440":{"body":"Step 1: Enabling new network protocol In the beginning, both /req_chunk/1 and /req_chunk/2 will be supported, until all validators and collators have upgraded to use the new version. V1 will be considered deprecated. During this step, the mapping will still be 1:1 (ValidatorIndex == ChunkIndex), regardless of protocol. Once all nodes are upgraded, a new release will be cut that removes the v1 protocol. Only once all nodes have upgraded to this version will step 2 commence. Step 2: Enabling the new validator->chunk mapping Considering that the Validator->Chunk mapping is critical to para consensus, the change needs to be enacted atomically via governance, only after all validators have upgraded the node to a version that is aware of this mapping, functionality-wise. It needs to be explicitly stated that after the governance enactment, validators that run older client versions that don't support this mapping will not be able to participate in parachain consensus. Additionally, an error will be logged when starting a validator with an older version, after the feature was enabled. On the other hand, collators will not be required to upgrade in this step (but are still require to upgrade for step 1), as regular chunk recovery will work as before, granted that version 1 of the networking protocol has been removed. Note that collators only perform availability-recovery in rare, adversarial scenarios, so it is fine to not optimise for this case and let them upgrade at their own pace. To support enabling this feature via the runtime, we will use the NodeFeatures bitfield of the HostConfiguration struct (added in https://github.com/paritytech/polkadot-sdk/pull/2177). Adding and enabling a feature with this scheme does not require a runtime upgrade, but only a referendum that issues a Configuration::set_node_feature extrinsic. Once the feature is enabled and new configuration is live, the validator->chunk mapping ceases to be a 1:1 mapping and systematic recovery may begin.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Upgrade path","id":"440","title":"Upgrade path"},"441":{"body":"Getting access to the core_index that used to be occupied by a candidate in some parts of the dispute protocol is very complicated (See appendix A ). This RFC assumes that availability-recovery processes initiated during disputes will only use regular recovery, as before. This is acceptable since disputes are rare occurrences in practice and is something that can be optimised later, if need be. Adding the core_index to the CandidateReceipt would mitigate this problem and will likely be needed in the future for CoreJam and/or Elastic scaling. Related discussion about updating CandidateReceipt It's a breaking change that requires all validators and collators to upgrade their node version at least once.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Drawbacks","id":"441","title":"Drawbacks"},"442":{"body":"Extensive testing will be conducted - both automated and manual. This proposal doesn't affect security or privacy.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Testing, Security, and Privacy","id":"442","title":"Testing, Security, and Privacy"},"443":{"body":"","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Performance, Ergonomics, and Compatibility","id":"443","title":"Performance, Ergonomics, and Compatibility"},"444":{"body":"This is a necessary data availability optimisation, as reed-solomon erasure coding has proven to be a top consumer of CPU time in polkadot as we scale up the parachain block size and number of availability cores. With this optimisation, preliminary performance results show that CPU time used for reed-solomon coding/decoding can be halved and total POV recovery time decrease by 80% for large POVs. See more here .","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Performance","id":"444","title":"Performance"},"445":{"body":"Not applicable.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Ergonomics","id":"445","title":"Ergonomics"},"446":{"body":"This is a breaking change. See upgrade path section above. All validators and collators need to have upgraded their node versions before the feature will be enabled via a governance call.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Compatibility","id":"446","title":"Compatibility"},"447":{"body":"See comments on the tracking issue and the in-progress PR","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Prior Art and References","id":"447","title":"Prior Art and References"},"448":{"body":"Not applicable.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Unresolved Questions","id":"448","title":"Unresolved Questions"},"449":{"body":"This enables future optimisations for the performance of availability recovery, such as retrieving batched systematic chunks from backers/approval-checkers.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Future Directions and Related Material","id":"449","title":"Future Directions and Related Material"},"45":{"body":"Key Input: Work Packages In JAM's refine code, work package content is as follows: JAM Refine Content Work Package $p_n \\in \\mathbb{P}$ Data submitted by ORU operator for validation of blocks $i$ through $j$ Payload ${\\bf y}$ Chain ID (e.g., 10, 42161, etc.), start and end block numbers expected in extrinsics Imported Data Segment ${\\bf i}$ Last ${\\bf H}$ validated by the service in the previous work package $p_{n-1}$ Extrinsics $\\bar{{\\bf x}}$ Header ${\\bf H}$, block hash $H({\\bf B})$, and Merkle proofs $\\Pi$ detailed below Work Items ${\\bf w} \\in \\mathbb{I}$ Summary of the first and last blocks ($i$ to $j$) Exported Data Segment ${\\bf e}$ Last validated ${\\bf H}$, used in the next work package $p_{n+1}$ Work Result ${\\bf r}$ $N$ header hashes $H({\\bf H})$ and $N$ block hashes $H({\\bf B})$ Refine's operations: Check for authorization ${\\bf o}$. Perform historical_lookup to fetch the last on-chain state in the anchor block. Import the last header ${\\bf H}$ and confirm that the imported data segment ${\\bf i}$ matches the historical_lookup. For each extrinsic header in ${\\bf H}$: Ensure that each header forms a chain, with ${\\bf H}_p$ matching the previous extrinsic $H({\\bf H})$, except for the first header, which must match the previous 2. Using the state root ${\\bf H}_r$, validate all Merkle proofs. Export the header of the last extrinsic successfully validated. Output the work result, up to $2(j-i+1)$ hashes: two hashes per extrinsic, $H({\\bf H})$ and $H({\\bf B})$. The refine process uses 3 host functions, with the main computation focused on Merkle proof validation. As detailed in GP, work results in guaranteed work reports are assured, audited, and judged following the ELVES protocol. JAM finalizes its audited blocks via GRANDPA voting, ensuring the rollup’s state can be trusted for subsequent operations.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Refine:","id":"45","title":"Refine:"},"450":{"body":"This appendix details the intricacies of getting access to the core index of a candidate in parity's polkadot node. Here, core_index refers to the index of the core that a candidate was occupying while it was pending availability (from backing to inclusion). Availability-recovery can currently be triggered by the following phases in the polkadot protocol: During the approval voting process. By other collators of the same parachain. During disputes. Getting the right core index for a candidate can be troublesome. Here's a breakdown of how different parts of the node implementation can get access to it: The approval-voting process for a candidate begins after observing that the candidate was included. Therefore, the node has easy access to the block where the candidate got included (and also the core that it occupied). The pov_recovery task of the collators starts availability recovery in response to noticing a candidate getting backed, which enables easy access to the core index the candidate started occupying. Disputes may be initiated on a number of occasions: 3.a. is initiated by the validator as a result of finding an invalid candidate while participating in the approval-voting protocol. In this case, availability-recovery is not needed, since the validator already issued their vote. 3.b is initiated by the validator noticing dispute votes recorded on-chain. In this case, we can safely assume that the backing event for that candidate has been recorded and kept in memory. 3.c is initiated as a result of getting a dispute statement from another validator. It is possible that the dispute is happening on a fork that was not yet imported by this validator, so the subsystem may not have seen this candidate being backed. A naive attempt of solving 3.c would be to add a new version for the disputes request-response networking protocol. Blindly passing the core index in the network payload would not work, since there is no way of validating that the reported core_index was indeed the one occupied by the candidate at the respective relay parent. Another attempt could be to include in the message the relay block hash where the candidate was included. This information would be used in order to query the runtime API and retrieve the core index that the candidate was occupying. However, considering it's part of an unimported fork, the validator cannot call a runtime API on that block. Adding the core_index to the CandidateReceipt would solve this problem and would enable systematic recovery for all dispute scenarios.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Appendix A","id":"450","title":"Appendix A"},"451":{"body":"(source) Table of Contents RFC-0048: Generate ownership proof for SessionKeys Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 13 November 2023 Description Change SessionKeys runtime api to support generating an ownership proof for the on chain registration. Authors Bastian Köcher","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » RFC-0048: Generate ownership proof for SessionKeys","id":"451","title":"RFC-0048: Generate ownership proof for SessionKeys"},"452":{"body":"This RFC proposes to changes the SessionKeys::generate_session_keys runtime api interface. This runtime api is used by validator operators to generate new session keys on a node. The public session keys are then registered manually on chain by the validator operator. Before this RFC it was not possible by the on chain logic to ensure that the account setting the public session keys is also in possession of the private session keys. To solve this the RFC proposes to pass the account id of the account doing the registration on chain to generate_session_keys. Further this RFC proposes to change the return value of the generate_session_keys function also to not only return the public session keys, but also the proof of ownership for the private session keys. The validator operator will then need to send the public session keys and the proof together when registering new session keys on chain.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Summary","id":"452","title":"Summary"},"453":{"body":"When submitting the new public session keys to the on chain logic there doesn't exist any verification of possession of the private session keys. This means that users can basically register any kind of public session keys on chain. While the on chain logic ensures that there are no duplicate keys, someone could try to prevent others from registering new session keys by setting them first. While this wouldn't bring the \"attacker\" any kind of advantage, more like disadvantages (potential slashes on their account), it could prevent someone from e.g. changing its session key in the event of a private session key leak. After this RFC this kind of attack would not be possible anymore, because the on chain logic can verify that the sending account is in ownership of the private session keys.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Motivation","id":"453","title":"Motivation"},"454":{"body":"Polkadot runtime implementors Polkadot node implementors Validator operators","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Stakeholders","id":"454","title":"Stakeholders"},"455":{"body":"We are first going to explain the proof format being used: type Proof = (Signature, Signature, ..); The proof being a SCALE encoded tuple over all signatures of each private session key signing the account_id. The actual type of each signature depends on the corresponding session key cryptographic algorithm. The order of the signatures in the proof is the same as the order of the session keys in the SessionKeys type declared in the runtime. The version of the SessionKeys needs to be bumped to 1 to reflect the changes to the signature of SessionKeys_generate_session_keys: pub struct OpaqueGeneratedSessionKeys { pub keys: Vec, pub proof: Vec,\n} fn SessionKeys_generate_session_keys(account_id: Vec, seed: Option>) -> OpaqueGeneratedSessionKeys; The default calling convention for runtime apis is applied, meaning the parameters passed as SCALE encoded array and the length of the encoded array. The return value being the SCALE encoded return value as u64 (array_ptr | length << 32). So, the actual exported function signature looks like: fn SessionKeys_generate_session_keys(array: *const u8, len: usize) -> u64; The on chain logic for setting the SessionKeys needs to be changed as well. It already gets the proof passed as Vec. This proof needs to be decoded to the actual Proof type as explained above. The proof and the SCALE encoded account_id of the sender are used to verify the ownership of the SessionKeys.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Explanation","id":"455","title":"Explanation"},"456":{"body":"Validator operators need to pass the their account id when rotating their session keys in a node. This will require updating some high level docs and making users familiar with the slightly changed ergonomics.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Drawbacks","id":"456","title":"Drawbacks"},"457":{"body":"Testing of the new changes only requires passing an appropriate owner for the current testing context. The changes to the proof generation and verification got audited to ensure they are correct.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Testing, Security, and Privacy","id":"457","title":"Testing, Security, and Privacy"},"458":{"body":"","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Performance, Ergonomics, and Compatibility","id":"458","title":"Performance, Ergonomics, and Compatibility"},"459":{"body":"The session key generation is an offchain process and thus, doesn't influence the performance of the chain. Verifying the proof is done on chain as part of the transaction logic for setting the session keys. The verification of the proof is a signature verification number of individual session keys times. As setting the session keys is happening quite rarely, it should not influence the overall system performance.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Performance","id":"459","title":"Performance"},"46":{"body":"Optimistic rollups, including OP Stack and ArbOS, use Ethereum's Merkle Patricia Trie to commit to state data on each block. See this architecture diagram for an overview. The state root ${\\bf H}_r$ is a cryptographic commitment to the entire rollup state at that block height. Notably, validation does not calculate the state root ${\\bf H_r}$ based on block transactions , which would necessitate the entire state of the rollup. Instead, storage proofs (or \"witness data\") enable the ORU to prove that specific storage values exist within a particular state root. Only the last witness per contract address is needed in a work package of $N$ blocks. The central assumption is that if the work package proves all account/contract storage items over $N$ of blocks, which are guaranteed/assured/audited by a subset of JAM validators, then the sequence of state transitions in these blocks is valid. This chaining of state roots ensures continuity and trust in the rollup secured by this JAM Service: Each block’s state root can be verified against the previous state, allowing nodes to validate state changes trustlessly. Inclusion in Parent Block Hash: Since each block header ${\\bf H}$ includes the previous header hash ${\\bf H}_p$ and indirectly references the previous state root ${\\bf H}_r$, each block and header also serves as a cryptographic reference to the prior state. The core operation verifies proofs against the state root, enabling efficient, trustless block sequence validation based solely on headers, which are much smaller than full transaction blocks. For now, we consider 100% of storage keys and values output by the trace of a block. A more sophisticated approach to sample the set of storage keys based on JAM's public entropy $\\eta_3$ may be warranted to limit work packages to within JAM's limits, made available through historical_lookup operations.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Key Validation Process: Storage Proofs","id":"46","title":"Key Validation Process: Storage Proofs"},"460":{"body":"The interfaces have been optimized to make it as easy as possible to generate the ownership proof.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Ergonomics","id":"460","title":"Ergonomics"},"461":{"body":"Introduces a new version of the SessionKeys runtime api. Thus, nodes should be updated before a runtime is enacted that contains these changes otherwise they will fail to generate session keys. The RPC that exists around this runtime api needs to be updated to support passing the account id and for returning the ownership proof alongside the public session keys. UIs would need to be updated to support the new RPC and the changed on chain logic.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Compatibility","id":"461","title":"Compatibility"},"462":{"body":"None.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Prior Art and References","id":"462","title":"Prior Art and References"},"463":{"body":"None.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Unresolved Questions","id":"463","title":"Unresolved Questions"},"464":{"body":"Substrate implementation of the RFC .","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Future Directions and Related Material","id":"464","title":"Future Directions and Related Material"},"465":{"body":"(source) Table of Contents RFC-0050: Fellowship Salaries Summary Motivation Stakeholders Explanation Salary Asset Projections Updates Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 15 November 2023 Description Proposal to set rank-based Fellowship salary levels. Authors Joe Petrowski, Gavin Wood","breadcrumbs":"RFC-0050: Fellowship Salaries » RFC-0050: Fellowship Salaries","id":"465","title":"RFC-0050: Fellowship Salaries"},"466":{"body":"The Fellowship Manifesto states that members should receive a monthly allowance on par with gross income in OECD countries. This RFC proposes concrete amounts.","breadcrumbs":"RFC-0050: Fellowship Salaries » Summary","id":"466","title":"Summary"},"467":{"body":"One motivation for the Technical Fellowship is to provide an incentive mechanism that can induct and retain technical talent for the continued progress of the network. In order for members to uphold their commitment to the network, they should receive support to ensure that their needs are met such that they have the time to dedicate to their work on Polkadot. Given the high expectations of Fellows, it is reasonable to consider contributions and requirements on par with a full-time job. Providing a livable wage to those making such contributions makes it pragmatic to work full-time on Polkadot. Note: Goals of the Fellowship, expectations for each Dan, and conditions for promotion and demotion are all explained in the Manifesto. This RFC is only to propose concrete values for allowances.","breadcrumbs":"RFC-0050: Fellowship Salaries » Motivation","id":"467","title":"Motivation"},"468":{"body":"Fellowship members Polkadot Treasury","breadcrumbs":"RFC-0050: Fellowship Salaries » Stakeholders","id":"468","title":"Stakeholders"},"469":{"body":"This RFC proposes agreeing on salaries relative to a single level, the III Dan. As such, changes to the amount or asset used would only be on a single value, and all others would adjust relatively. A III Dan is someone whose contributions match the expectations of a full-time individual contributor. The salary at this level should be reasonably close to averages in OECD countries. Dan Factor I 0.125 II 0.25 III 1 IV 1.5 V 2.0 VI 2.5 VII 2.5 VIII 2.5 IX 2.5 Note that there is a sizable increase between II Dan (Proficient) and III Dan (Fellow). By the third Dan, it is generally expected that one is working on Polkadot as their primary focus in a full-time capacity.","breadcrumbs":"RFC-0050: Fellowship Salaries » Explanation","id":"469","title":"Explanation"},"47":{"body":"The accumulate process ensures that all rollup data necessary to validate the rollup is available in JAM DA. Accumulate is an entirely synchronous on-chain operation performed by all JAM Validators (rather than in-core as with Refine). Computation is carried out first by the JAM Block Author and the newly authored block sent to all Validators. On-chain Storage of Rollup State The service maintains a summary of fully validated blocks of each chain in 3 service storage keys: the first block number $a$ validated with data fully available the last block number $b$ validated with data fully available a window parameter $w$, modeling the maximum $b-a$ For every block number in this range, the block number has its own key to store the header hash and the block hash. The function of this data storage represents both of the following: the refine validation has been completed and the block and header preimages are available in JAM's DA Key Process JAM Accumulate Content Wrangled Work Results Chain ID (e.g., 10, 42161, etc.), block number start $i$ and end $j$ followed by pairs of $H({\\bf H})$ and $H({\\bf B})$ read fetch $a, b, w$ based on Chain ID. Validate that $i=b+1$. solicit is called for both hashes in the wrangled work results. Advance $b$ by 1 if: both ${\\bf a}_l(H({\\bf B}))$ and ${\\bf a}_l(H({\\bf H}))$ are \"available\" the header ${\\bf H}$ is contained with ${\\bf B}$ If $b-a$ exceeds the window $w$, advance $a$ by 1 if both ${\\bf a}_l(H({\\bf B}))$ and ${\\bf a}_l(H({\\bf H}))$ are \"forget\". write $a$ and $b$ back to storage. Necessarily, the ORU operator must provide both preimages for the chain to be considered valid. If any block or header is not made available by the ORU operator, $b$ will not advance. Under normal operations, the above process will result in a full set of blocks and header preimages being in JAM's DA layer. Moreover, the forget operation ensures that storage is bounded by $w$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Accumulate","id":"47","title":"Accumulate"},"470":{"body":"Although the Manifesto (Section 8) specifies a monthly allowance in DOT, this RFC proposes the use of USDT instead. The allowance is meant to provide members stability in meeting their day-to-day needs and recognize contributions. Using USDT provides more stability and less speculation. This RFC proposes that a III Dan earn 80,000 USDT per year. The salary at this level is commensurate with average salaries in OECD countries (note: 77,000 USD in the U.S., with an average engineer at 100,000 USD). The other ranks would thus earn: Dan Annual Salary I 10,000 II 20,000 III 80,000 IV 120,000 V 160,000 VI 200,000 VII 200,000 VIII 200,000 IX 200,000 The salary levels for Architects (IV, V, and VI Dan) are typical of senior engineers. Allowances will be managed by the Salary pallet.","breadcrumbs":"RFC-0050: Fellowship Salaries » Salary Asset","id":"470","title":"Salary Asset"},"471":{"body":"Based on the current membership, the maximum yearly and monthly costs are shown below: Dan Salary Members Yearly Monthly I 10,000 27 270,000 22,500 II 20,000 11 220,000 18,333 III 80,000 8 640,000 53,333 IV 120,000 3 360,000 30,000 V 160,000 5 800,000 66,667 VI 200,000 3 600,000 50,000 > VI 200,000 0 0 0 Total 2,890,000 240,833 Note that these are the maximum amounts; members may choose to take a passive (lower) level. On the other hand, more people will likely join the Fellowship in the coming years.","breadcrumbs":"RFC-0050: Fellowship Salaries » Projections","id":"471","title":"Projections"},"472":{"body":"Updates to these levels, whether relative ratios, the asset used, or the amount, shall be done via RFC.","breadcrumbs":"RFC-0050: Fellowship Salaries » Updates","id":"472","title":"Updates"},"473":{"body":"By not using DOT for payment, the protocol relies on the stability of other assets and the ability to acquire them. However, the asset of choice can be changed in the future.","breadcrumbs":"RFC-0050: Fellowship Salaries » Drawbacks","id":"473","title":"Drawbacks"},"474":{"body":"N/A.","breadcrumbs":"RFC-0050: Fellowship Salaries » Testing, Security, and Privacy","id":"474","title":"Testing, Security, and Privacy"},"475":{"body":"","breadcrumbs":"RFC-0050: Fellowship Salaries » Performance, Ergonomics, and Compatibility","id":"475","title":"Performance, Ergonomics, and Compatibility"},"476":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Performance","id":"476","title":"Performance"},"477":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Ergonomics","id":"477","title":"Ergonomics"},"478":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Compatibility","id":"478","title":"Compatibility"},"479":{"body":"The Polkadot Fellowship Manifesto OECD Average Wages Indeed: Average Salary for Engineers, United States","breadcrumbs":"RFC-0050: Fellowship Salaries » Prior Art and References","id":"479","title":"Prior Art and References"},"48":{"body":"Transfer details concerning fees of storage balance are not considered at this time. A full model appears to necessitate a clear interface between JAM and CoreTime as well as a model of how this service can support a single vs. multiple Chain IDs. Naturally, all service fees would be in DOT rather than ETH on L2. Multiple service instantiations under different CoreTime leases may be envisioned for each rollup, but a set of homogenous ORU rollups to support sync/async models by the same ORU operator could also be supported.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Transfer","id":"48","title":"Transfer"},"480":{"body":"None at present.","breadcrumbs":"RFC-0050: Fellowship Salaries » Unresolved Questions","id":"480","title":"Unresolved Questions"},"481":{"body":"(source) Table of Contents RFC-0056: Enforce only one transaction per notification Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-11-30 Description Modify the transactions notifications protocol to always send only one transaction at a time Authors Pierre Krieger","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » RFC-0056: Enforce only one transaction per notification","id":"481","title":"RFC-0056: Enforce only one transaction per notification"},"482":{"body":"When two peers connect to each other, they open (amongst other things) a so-called \"notifications protocol\" substream dedicated to gossiping transactions to each other. Each notification on this substream currently consists in a SCALE-encoded Vec where Transaction is defined in the runtime. This RFC proposes to modify the format of the notification to become (Compact(1), Transaction). This maintains backwards compatibility, as this new format decodes as a Vec of length equal to 1.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Summary","id":"482","title":"Summary"},"483":{"body":"There exists three motivations behind this change: It is technically impossible to decode a SCALE-encoded Vec into a list of SCALE-encoded transactions without knowing how to decode a Transaction. That's because a Vec consists in several Transactions one after the other in memory, without any delimiter that indicates the end of a transaction and the start of the next. Unfortunately, the format of a Transaction is runtime-specific. This means that the code that receives notifications is necessarily tied to a specific runtime, and it is not possible to write runtime-agnostic code. Notifications protocols are already designed to be optimized to send many items. Currently, when it comes to transactions, each item is a Vec that consists in multiple sub-items of type Transaction. This two-steps hierarchy is completely unnecessary, and was originally written at a time when the networking protocol of Substrate didn't have proper multiplexing. It makes the implementation way more straight-forward by not having to repeat code related to back-pressure. See explanations below.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Motivation","id":"483","title":"Motivation"},"484":{"body":"Low-level developers.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Stakeholders","id":"484","title":"Stakeholders"},"485":{"body":"To give an example, if you send one notification with three transactions, the bytes that are sent on the wire are: concat( leb128(total-size-in-bytes-of-the-rest), scale(compact(3)), scale(transaction1), scale(transaction2), scale(transaction3)\n) But you can also send three notifications of one transaction each, in which case it is: concat( leb128(size(scale(transaction1)) + 1), scale(compact(1)), scale(transaction1), leb128(size(scale(transaction2)) + 1), scale(compact(1)), scale(transaction2), leb128(size(scale(transaction3)) + 1), scale(compact(1)), scale(transaction3)\n) Right now the sender can choose which of the two encoding to use. This RFC proposes to make the second encoding mandatory. The format of the notification would become a SCALE-encoded (Compact(1), Transaction). A SCALE-compact encoded 1 is one byte of value 4. In other words, the format of the notification would become concat(&[4], scale_encoded_transaction). This is equivalent to forcing the Vec to always have a length of 1, and I expect the Substrate implementation to simply modify the sending side to add a for loop that sends one notification per item in the Vec. As explained in the motivation section, this allows extracting scale(transaction) items without having to know how to decode them. By \"flattening\" the two-steps hierarchy, an implementation only needs to back-pressure individual notifications rather than back-pressure notifications and transactions within notifications.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Explanation","id":"485","title":"Explanation"},"486":{"body":"This RFC chooses to maintain backwards compatibility at the cost of introducing a very small wart (the Compact(1)). An alternative could be to introduce a new version of the transactions notifications protocol that sends one Transaction per notification, but this is significantly more complicated to implement and can always be done later in case the Compact(1) is bothersome.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Drawbacks","id":"486","title":"Drawbacks"},"487":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Testing, Security, and Privacy","id":"487","title":"Testing, Security, and Privacy"},"488":{"body":"","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Performance, Ergonomics, and Compatibility","id":"488","title":"Performance, Ergonomics, and Compatibility"},"489":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Performance","id":"489","title":"Performance"},"49":{"body":"Following the BEEFY protocol, JAM's own state trie aggregates work packages' accumulate roots into its own recent history $\\beta$, signed by JAM validators. BEEFY’s model allows JAM's state to be verified on Ethereum and other external chains without needing all JAM Chain data on the external chain. All rollups, whether built on Substrate or optimistic turned cynical, are committed into this state, supporting cross-ecosystem proofs using Merkle trees as today. To support this goal, the accumulate result is the last block hash, last header hash, or last state root as suitable to match Polkadot rollup behavior.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Beefy","id":"49","title":"Beefy"},"490":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Ergonomics","id":"490","title":"Ergonomics"},"491":{"body":"The change is backwards compatible if done in two steps: modify the sender to always send one transaction per notification, then, after a while, modify the receiver to enforce the new format.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Compatibility","id":"491","title":"Compatibility"},"492":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Prior Art and References","id":"492","title":"Prior Art and References"},"493":{"body":"None.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Unresolved Questions","id":"493","title":"Unresolved Questions"},"494":{"body":"None. This is a simple isolated change.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Future Directions and Related Material","id":"494","title":"Future Directions and Related Material"},"495":{"body":"(source) Table of Contents RFC-0059: Add a discovery mechanism for nodes based on their capabilities Summary Motivation Stakeholders Explanation Capabilities DHT provider registration Secondary DHTs Head of the chain providers Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-12-18 Description Nodes having certain capabilities register themselves in the DHT to be discoverable Authors Pierre Krieger","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » RFC-0059: Add a discovery mechanism for nodes based on their capabilities","id":"495","title":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities"},"496":{"body":"This RFC proposes to make the mechanism of RFC #8 more generic by introducing the concept of \"capabilities\". Implementations can implement certain \"capabilities\", such as serving old block headers or being a parachain bootnode. The discovery mechanism of RFC #8 is extended to be able to discover nodes of specific capabilities.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Summary","id":"496","title":"Summary"},"497":{"body":"The Polkadot peer-to-peer network is made of nodes. Not all these nodes are equal. Some nodes store only the headers of recent blocks, some nodes store all the block headers and bodies since the genesis, some nodes store the storage of all blocks since the genesis, and so on. It is currently not possible to know ahead of time (without connecting to it and asking) which nodes have which data available, and it is not easily possible to build a list of nodes that have a specific piece of data available. If you want to download for example the header of block 500, you have to connect to a randomly-chosen node, ask it for block 500, and if it says that it doesn't have the block, disconnect and try another randomly-chosen node. In certain situations such as downloading the storage of old blocks, nodes that have the information are relatively rare, and finding through trial and error a node that has the data can take a long time. This RFC attempts to solve this problem by giving the possibility to build a list of nodes that are capable of serving specific data.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Motivation","id":"497","title":"Motivation"},"498":{"body":"Low-level client developers. People interested in accessing the archive of the chain.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Stakeholders","id":"498","title":"Stakeholders"},"499":{"body":"Reading RFC #8 first might help with comprehension, as this RFC is very similar. Please keep in mind while reading that everything below applies for both relay chains and parachains, except mentioned otherwise.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Explanation","id":"499","title":"Explanation"},"5":{"body":"The Asset Metadata is information bound to an asset class (fungible or NFT collection) or an asset instance (an NFT). The Asset Metadata could be represented differently on different chains (or in other consensus entities). However, to communicate metadata between consensus entities via XCM, we need a general format so that any consensus entity can make sense of such information. We can name this format \"XCM Asset Metadata\". This RFC proposes: Using key-value pairs as XCM Asset Metadata since it is a general concept useful for both structured and unstructured data. Both key and value can be raw bytes with interpretation up to the communicating entities. The XCM Asset Metadata should be represented as a map SCALE-encoded equivalent to the BTreeMap. Let's call the type of the XCM Asset Metadata map MetadataMap. Communicating only the demanded part of the metadata, not the whole metadata. A consensus entity should be able to query the values of interested keys to read the metadata. To specify the keys to read, we need a set-like type. Let's call that type MetadataKeys and make its instance a SCALE-encoded equivalent to the BTreeSet. A consensus entity should be able to write the values for specified keys. New XCM instructions to communicate the metadata.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Explanation","id":"5","title":"Explanation"},"50":{"body":"This JAM Service can be implemented in Rust using polkatool and tested on a JAM Testnet by JAM implementers. A Keccak256 host function is used for expedience, and the preimage hash function will be adjusted to this for PoC. Real-world work packages can be developed for OP Stack chains like Base and Optimism (currently with 30 blocks/minute) and Arbitrum, which operates at 150 blocks/minute. The results of \"trace_block\" JSON-RPC calls enable 3 x 1440 work packages per day for these top 3 ETH rollups. This is ample for PoC.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Service PoC Implementation","id":"50","title":"Service PoC Implementation"},"500":{"body":"This RFC defines a list of so-called capabilities : Head of chain provider . An implementation with this capability must be able to serve to other nodes block headers, block bodies, justifications, calls proofs, and storage proofs of \"recent\" (see below) blocks, and, for relay chains, to serve to other nodes warp sync proofs where the starting block is a session change block and must participate in Grandpa and Beefy gossip. History provider . An implementation with this capability must be able to serve to other nodes block headers and block bodies of any block since the genesis, and must be able to serve to other nodes justifications of any session change block since the genesis up until and including their currently finalized block. Archive provider . This capability is a superset of History provider . In addition to the requirements of History provider , an implementation with this capability must be able to serve call proofs and storage proof requests of any block since the genesis up until and including their currently finalized block. Parachain bootnode (only for relay chains). An implementation with this capability must be able to serve the network request described in RFC 8. More capabilities might be added in the future. In the context of the head of chain provider , the word \"recent\" means: any not-finalized-yet block that is equal to or an ancestor of a block that it has announced through a block announce, and any finalized block whose height is superior to its current finalized block minus 16 . This does not include blocks that have been pruned because they're not a descendant of its current finalized block. In other words, blocks that aren't a descendant of the current finalized block can be thrown away. A gap of blocks is required due to race conditions: when a node finalizes a block, it takes some time for its peers to be made aware of this, during which they might send requests concerning older blocks. The choice of the number of blocks in this gap is arbitrary. Substrate is currently by default a head of chain provider provider. After it has finished warp syncing, it downloads the list of old blocks, after which it becomes a history provider . If Substrate is instead configured as an archive node, then it downloads all blocks since the genesis and builds their state, after which it becomes an archive provider , history provider , and head of chain provider . If blocks pruning is enabled and the chain is a relay chain, then Substrate unfortunately doesn't implement any of these capabilities, not even head of chain provider . This is considered as a bug that should be fixed, see https://github.com/paritytech/polkadot-sdk/issues/2733 .","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Capabilities","id":"500","title":"Capabilities"},"501":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . Implementations that have the history provider capability should register themselves as providers under the key sha256(concat(\"history\", randomness)). Implementations that have the archive provider capability should register themselves as providers under the key sha256(concat(\"archive\", randomness)). Implementations that have the parachain bootnode capability should register themselves as provider under the key sha256(concat(scale_compact(para_id), randomness)), as described in RFC 8. \"Register themselves as providers\" consists in sending ADD_PROVIDER requests to nodes close to the key, as described in the Content provider advertisement section of the specification. The value of randomness can be found in the randomness field when calling the BabeApi_currentEpoch function. In order to avoid downtimes when the key changes, nodes should also register themselves as a secondary key that uses a value of randomness equal to the randomness field when calling BabeApi_nextEpoch. Implementers should be aware that their implementation of Kademlia might already hash the key before XOR'ing it. The key is not meant to be hashed twice. Implementations must not register themselves if they don't fulfill the capability yet . For example, a node configured to be an archive node but that is still building its archive state in the background must register itself only after it has finished building its archive.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » DHT provider registration","id":"501","title":"DHT provider registration"},"502":{"body":"Implementations that have the history provider capability must also participate in a secondary DHT that comprises only of nodes with that capability. The protocol name of that secondary DHT must be //kad/history. Similarly, implementations that have the archive provider capability must also participate in a secondary DHT that comprises only of nodes with that capability and whose protocol name is //kad/archive. Just like implementations must not register themselves if they don't fulfill their capability yet, they must also not participate in the secondary DHT if they don't fulfill their capability yet.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Secondary DHTs","id":"502","title":"Secondary DHTs"},"503":{"body":"Implementations that have the head of the chain provider capability do not register themselves as providers, but instead are the nodes that participate in the main DHT. In other words, they are the nodes that serve requests of the //kad protocol. Any implementation that isn't a head of the chain provider (read: light clients) must not participate in the main DHT. This is already presently the case. Implementations must not participate in the main DHT if they don't fulfill the capability yet. For example, a node that is still in the process of warp syncing must not participate in the main DHT. However, assuming that warp syncing doesn't last more than a few seconds, it is acceptable to ignore this requirement in order to avoid complicating implementations too much.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Head of the chain providers","id":"503","title":"Head of the chain providers"},"504":{"body":"None that I can see.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Drawbacks","id":"504","title":"Drawbacks"},"505":{"body":"The content of this section is basically the same as the one in RFC 8. This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms. Due to the way Kademlia works, it would become the responsibility of the 20 Polkadot nodes whose sha256(peer_id) is closest to the key (described in the explanations section) to store the list of nodes that have specific capabilities. Furthermore, when a large number of providers are registered, only the providers closest to the key are kept, up to a certain implementation-defined limit. For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target capability. They are then in control of the list of nodes with that capability. While doing this can in no way be actually harmful, it could lead to eclipse attacks. Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Testing, Security, and Privacy","id":"505","title":"Testing, Security, and Privacy"},"506":{"body":"","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Performance, Ergonomics, and Compatibility","id":"506","title":"Performance, Ergonomics, and Compatibility"},"507":{"body":"The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours. Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode. Assuming 1000 nodes with a specific capability, the 20 Polkadot full nodes corresponding to that capability will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a node registers itself to be the provider of the key corresponding to BabeApi_next_epoch. Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the nodes with a capability. If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Performance","id":"507","title":"Performance"},"508":{"body":"Irrelevant.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Ergonomics","id":"508","title":"Ergonomics"},"509":{"body":"Irrelevant.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Compatibility","id":"509","title":"Compatibility"},"51":{"body":"JAM's gas parameters for PVM instructions and host calls have not been fully developed yet. Combining Polkadot and non-Polkadot rollup services will provide valuable data for determining these parameters. The gas required for refine is proportional to the number of storage proofs submitted in a work package and the average size of each proof. To upper-bound storage proofs, sampling using an entropy state variable $\\eta_3$ may be necessary, although accessing it remains unclear. The gas required for accumulate is proportional to the number of solicit and forget operations. It is believed that accumulate's gas cost is nominal and poses no significant issue. However, the storage rent model common to all blockchain storage applies to the preimage, which is explicitly tallied. Fortunately, this is upper-bounded by $w$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Gas + Storage Considerations","id":"51","title":"Gas + Storage Considerations"},"510":{"body":"Unknown.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Prior Art and References","id":"510","title":"Prior Art and References"},"511":{"body":"While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Unresolved Questions","id":"511","title":"Unresolved Questions"},"512":{"body":"This RFC would make it possible to reliably discover archive nodes, which would make it possible to reliably send archive node requests, something that isn't currently possible. This could solve the problem of finding archive RPC node providers by migrating archive-related request to using the native peer-to-peer protocol rather than JSON-RPC. If we ever decide to break backwards compatibility, we could divide the \"history\" and \"archive\" capabilities in two, between nodes capable of serving older blocks and nodes capable of serving newer blocks. We could even add to the peer-to-peer network nodes that are only capable of serving older blocks (by reading from a database) but do not participate in the head of the chain, and that just exist for historical purposes.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Future Directions and Related Material","id":"512","title":"Future Directions and Related Material"},"513":{"body":"(source) Table of Contents RFC-0078: Merkleized Metadata Summary Motivation Requirements Reduce metadata size Stakeholders Explanation Metadata digest Extrinsic metadata Type Information Prune unrelated Types Generating TypeRef Building the Merkle Tree Root Inclusion in an Extrinsic Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics & Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 22 February 2024 Description Include merkleized metadata hash in extrinsic signature for trust-less metadata verification. Authors Zondax AG, Parity Technologies","breadcrumbs":"RFC-0078: Merkleized Metadata » RFC-0078: Merkleized Metadata","id":"513","title":"RFC-0078: Merkleized Metadata"},"514":{"body":"To interact with chains in the Polkadot ecosystem it is required to know how transactions are encoded and how to read state. For doing this, Polkadot-SDK, the framework used by most of the chains in the Polkadot ecosystem, exposes metadata about the runtime to the outside. UIs, wallets, and others can use this metadata to interact with these chains. This makes the metadata a crucial piece of the transaction encoding as users are relying on the interacting software to encode the transactions in the correct format. It gets even more important when the user signs the transaction in an offline wallet, as the device by its nature cannot get access to the metadata without relying on the online wallet to provide it. This makes it so that the offline wallet needs to trust an online party, deeming the security assumptions of the offline devices, mute. This RFC proposes a way for offline wallets to leverage metadata, within the constraints of these. The design idea is that the metadata is chunked and these chunks are put into a merkle tree. The root hash of this merkle tree represents the metadata. The offline wallets can use the root hash to decode transactions by getting proofs for the individual chunks of the metadata. This root hash is also included in the signed data of the transaction (but not sent as part of the transaction). The runtime is then including its known metadata root hash when verifying the transaction. If the metadata root hash known by the runtime differs from the one that the offline wallet used, it very likely means that the online wallet provided some fake data and the verification of the transaction fails. Users depend on offline wallets to correctly display decoded transactions before signing. With merkleized metadata, they can be assured of the transaction's legitimacy, as incorrect transactions will be rejected by the runtime.","breadcrumbs":"RFC-0078: Merkleized Metadata » Summary","id":"514","title":"Summary"},"515":{"body":"Polkadot's innovative design (both relay chain and parachains) present the ability to developers to upgrade their network as frequently as they need. These systems manage to have integrations working after the upgrades with the help of FRAME Metadata. This Metadata, which is in the order of half a MiB for most Polkadot-SDK chains, completely describes chain interfaces and properties. Securing this metadata is key for users to be able to interact with the Polkadot-SDK chain in the expected way. On the other hand, offline wallets provide a secure way for Blockchain users to hold their own keys (some do a better job than others). These devices seldomly get upgraded, usually account for one particular network and hold very small internal memories. Currently in the Polkadot ecosystem there is no secure way of having these offline devices know the latest Metadata of the Polkadot-SDK chain they are interacting with. This results in a plethora of similar yet slightly different offline wallets for all different Polkadot-SDK chains, as well as the impediment of keeping these regularly updated, thus not fully leveraging Polkadot-SDK’s unique forkless upgrade feature. The two main reasons why this is not possible today are: Metadata is too large for offline devices . Currently Polkadot-SDK metadata is on average 500 KiB, which is more than what the mostly adopted offline devices can hold. Metadata is not authenticated . Even if there was enough space on offline devices to hold the metadata, the user would be trusting the entity providing this metadata to the hardware wallet. In the Polkadot ecosystem, this is how currently Polkadot Vault works. This RFC proposes a solution to make FRAME Metadata compatible with offline signers in a secure way. As it leverages FRAME Metadata, it does not only ensure that offline devices can always keep up to date with every FRAME based chain, but also that every offline wallet will be compatible with all FRAME based chains, avoiding the need of per-chain implementations.","breadcrumbs":"RFC-0078: Merkleized Metadata » Motivation","id":"515","title":"Motivation"},"516":{"body":"Metadata's integrity MUST be preserved. If any compromise were to happen, extrinsics sent with compromised metadata SHOULD fail. Metadata information that could be used in signable extrinsic decoding MAY be included in digest, yet its inclusion MUST be indicated in signed extensions. Digest MUST be deterministic with respect to metadata. Digest MUST be cryptographically strong against pre-image, both first (finding an input that results in given digest) and second (finding an input that results in same digest as some other input given). Extra-metadata information necessary for extrinsic decoding and constant within runtime version MUST be included in digest. It SHOULD be possible to quickly withdraw offline signing mechanism without access to cold signing devices. Digest format SHOULD be versioned. Work necessary for proving metadata authenticity MAY be omitted at discretion of signer device design (to support automation tools).","breadcrumbs":"RFC-0078: Merkleized Metadata » Requirements","id":"516","title":"Requirements"},"517":{"body":"Metadata should be stripped from parts that are not necessary to parse a signable extrinsic, then it should be separated into a finite set of self-descriptive chunks. Thus, a subset of chunks necessary for signable extrinsic decoding and rendering could be sent, possibly in small portions (ultimately, one at a time), to cold devices together with the proof. Single chunk with proof payload size SHOULD fit within few kB; Chunks handling mechanism SHOULD support chunks being sent in any order without memory utilization overhead; Unused enum variants MUST be stripped (this has great impact on transmitted metadata size; examples: era enum, enum with all calls for call batching).","breadcrumbs":"RFC-0078: Merkleized Metadata » Reduce metadata size","id":"517","title":"Reduce metadata size"},"518":{"body":"Runtime implementors UI/wallet implementors Offline wallet implementors The idea for this RFC was brought up by runtime implementors and was extensively discussed with offline wallet implementors. It was designed in such a way that it can work easily with the existing offline wallet solutions in the Polkadot ecosystem.","breadcrumbs":"RFC-0078: Merkleized Metadata » Stakeholders","id":"518","title":"Stakeholders"},"519":{"body":"The FRAME metadata provides a wide range of information about a FRAME based runtime. It contains information about the pallets, the calls per pallet, the storage entries per pallet, runtime APIs, and type information about most of the types that are used in the runtime. For decoding extrinsics on an offline wallet, what is mainly required is type information. Most of the other information in the FRAME metadata is actually not required for decoding extrinsics and thus it can be removed. Therefore, the following is a proposal on a custom representation of the metadata and how this custom metadata is chunked, ensuring that only the needed chunks required for decoding a particular extrinsic are sent to the offline wallet. The necessary information to transform the FRAME metadata type information into the type information presented in this RFC will be provided. However, not every single detail on how to convert from FRAME metadata into the RFC type information is described. First, the MetadataDigest is introduced. After that, ExtrinsicMetadata is covered and finally the actual format of the type information. Then pruning of unrelated type information is covered and how to generate the TypeRefs. In the latest step, merkle tree calculation is explained.","breadcrumbs":"RFC-0078: Merkleized Metadata » Explanation","id":"519","title":"Explanation"},"52":{"body":"CoreTime Instead of ETH, rollups would require DOT for CoreTime to secure their rollup. However, rollups are not locked into JAM and may freely enter and exit the JAM ecosystem since work packages do not need to start at genesis. Different rollups may need to scale their core usage based on rollup activity. JAM's connectivity to CoreTime is expected to handle this effectively. Hashing Currently, preimages are specified to use the Blake2b hash, while Ethereum rollup block hashes utilize Keccak256.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Compatibility","id":"52","title":"Compatibility"},"520":{"body":"The metadata digest is the compact representation of the metadata. The hash of this digest is the metadata hash . Below the type declaration of the Hash type and the MetadataDigest itself can be found: type Hash = [u8; 32]; enum MetadataDigest { #[index = 1] V1 { type_information_tree_root: Hash, extrinsic_metadata_hash: Hash, spec_version: u32, spec_name: String, base58_prefix: u16, decimals: u8, token_symbol: String, },\n} The Hash is 32 bytes long and blake3 is used for calculating it. The hash of the MetadataDigest is calculated by blake3(SCALE(MetadataDigest)). Therefore, MetadataDigest is at first SCALE encoded, and then those bytes are hashed. The MetadataDigest itself is represented as an enum. This is done to make it future proof, because a SCALE encoded enum is prefixed by the index of the variant. This index represents the version of the digest. As seen above, there is no index zero and it starts directly with one. Version one of the digest contains the following elements: type_information_tree_root: The root of the merkleized type information tree. extrinsic_metadata_hash: The hash of the extrinsic metadata . spec_version: The spec_version of the runtime as found in the RuntimeVersion when generating the metadata. While this information can also be found in the metadata, it is hidden in a big blob of data. To avoid transferring this big blob of data, we directly add this information here. spec_name: Similar to spec_version, but being the spec_name found in the RuntimeVersion. ss58_prefix: The SS58 prefix used for address encoding. decimals: The number of decimals for the token. token_symbol: The symbol of the token.","breadcrumbs":"RFC-0078: Merkleized Metadata » Metadata digest","id":"520","title":"Metadata digest"},"521":{"body":"For decoding an extrinsic, more information on what types are being used is required. The actual format of the extrinsic is the format as described in the Polkadot specification . The metadata for an extrinsic is as follows: struct ExtrinsicMetadata { version: u8, address_ty: TypeRef, call_ty: TypeRef, signature_ty: TypeRef, signed_extensions: Vec,\n} struct SignedExtensionMetadata { identifier: String, included_in_extrinsic: TypeRef, included_in_signed_data: TypeRef,\n} To begin with, TypeRef. This is a unique identifier for a type as found in the type information. Using this TypeRef, it is possible to look up the type in the type information tree. More details on this process can be found in the section Generating TypeRef . The actual ExtrinsicMetadata contains the following information: version: The version of the extrinsic format. As of writing this, the latest version is 4. address_ty: The address type used by the chain. call_ty: The call type used by the chain. The call in FRAME based runtimes represents the type of transaction being executed on chain. It references the actual function to execute and the parameters of this function. signature_ty: The signature type used by the chain. signed_extensions: FRAME based runtimes can extend the base extrinsic with extra information. This extra information that is put into an extrinsic is called \"signed extensions\". These extensions offer the runtime developer the possibility to include data directly into the extrinsic, like nonce, tip, amongst others. This means that the this data is sent alongside the extrinsic to the runtime. The other possibility these extensions offer is to include extra information only in the signed data that is signed by the sender. This means that this data needs to be known by both sides, the signing side and the verification side. An example for this kind of data is the genesis hash that ensures that extrinsics are unique per chain. Another example is the metadata hash itself that will also be included in the signed data. The offline wallets need to know which signed extensions are present in the chain and this is communicated to them using this field. The SignedExtensionMetadata provides information about a signed extension: identifier: The identifier of the signed extension. An identifier is required to be unique in the Polkadot ecosystem as otherwise extrinsics are maybe built incorrectly. included_in_extrinsic: The type that will be included in the extrinsic by this signed extension. included_in_signed_data: The type that will be included in the signed data by this signed extension.","breadcrumbs":"RFC-0078: Merkleized Metadata » Extrinsic metadata","id":"521","title":"Extrinsic metadata"},"522":{"body":"As SCALE is not self descriptive like JSON, a decoder always needs to know the format of the type to decode it properly. This is where the type information comes into play. The format of the extrinsic is fixed as described above and ExtrinsicMetadata provides information on which type information is required for which part of the extrinsic. So, offline wallets only need access to the actual type information. It is a requirement that the type information can be chunked into logical pieces to reduce the amount of data that is sent to the offline wallets for decoding the extrinsics. So, the type information is structured in the following way: struct Type { path: Vec, type_def: TypeDef, type_id: Compact,\n} enum TypeDef { Composite(Vec), Enumeration(EnumerationVariant), Sequence(TypeRef), Array(Array), Tuple(Vec), BitSequence(BitSequence),\n} struct Field { name: Option, ty: TypeRef, type_name: Option,\n} struct Array { len: u32, type_param: TypeRef,\n} struct BitSequence { num_bytes: u8, least_significant_bit_first: bool,\n} struct EnumerationVariant { name: String, fields: Vec, index: Compact,\n} enum TypeRef { Bool, Char, Str, U8, U16, U32, U64, U128, U256, I8, I16, I32, I64, I128, I256, CompactU8, CompactU16, CompactU32, CompactU64, CompactU128, CompactU256, Void, PerId(Compact),\n} The Type declares the structure of a type. The type has the following fields: path: A path declares the position of a type locally to the place where it is defined. The path is not globally unique, this means that there can be multiple types with the same path. type_def: The high-level type definition, e.g. the type is a composition of fields where each field has a type, the type is a composition of different types as tuple etc. type_id: The unique identifier of this type. Every Type is composed of multiple different types. Each of these \"sub types\" can reference either a full Type again or reference one of the primitive types. This is where TypeRef becomes relevant as the type referencing information. To reference a Type in the type information, a unique identifier is used. As primitive types can be represented using a single byte, they are not put as separate types into the type information. Instead the primitive types are directly part of TypeRef to not require the overhead of referencing them in an extra Type. The special primitive type Void represents a type that encodes to nothing and can be decoded from nothing. As FRAME doesn't support Compact as primitive type it requires a more involved implementation to convert a FRAME type to a Compact primitive type. SCALE only supports u8, u16, u32, u64 and u128 as Compact which maps onto the primitive type declaration in the RFC. One special case is a Compact that wraps an empty Tuple which is expressed as primitive type Void. The TypeDef variants have the following meaning: Composite: A struct like type that is composed of multiple different fields. Each Field can have its own type. The order of the fields is significant. A Composite with no fields is expressed as primitive type Void. Enumeration: Stores a EnumerationVariant. A EnumerationVariant is a struct that is described by a name, an index and a vector of Fields, each of which can have it's own type. Typically Enumerations have more than just one variant, and in those cases Enumeration will appear multiple times, each time with a different variant, in the type information. Enumerations can become quite large, yet usually for decoding a type only one variant is required, therefore this design brings optimizations and helps reduce the size of the proof. An Enumeration with no variants is expressed as primitive type Void. Sequence: A vector like type wrapping the given type. BitSequence: A vector storing bits. num_bytes represents the size in bytes of the internal storage. If least_significant_bit_first is true the least significant bit is first, otherwise the most significant bit is first. Array: A fixed-length array of a specific type. Tuple: A composition of multiple types. A Tuple that is composed of no types is expressed as primitive type Void. Using the type information together with the SCALE specification provides enough information on how to decode types.","breadcrumbs":"RFC-0078: Merkleized Metadata » Type Information","id":"522","title":"Type Information"},"523":{"body":"The FRAME metadata contains not only the type information for decoding extrinsics, but it also contains type information about storage types. The scope of the RFC is only about decoding transactions on offline wallets. Thus, a lot of type information can be pruned. To know which type information are required to decode all possible extrinsics, ExtrinsicMetadata has been defined. The extrinsic metadata contains all the types that define the layout of an extrinsic. Therefore, all the types that are accessible from the types declared in the extrinsic metadata can be collected. To collect all accessible types, it requires to recursively iterate over all types starting from the types in ExtrinsicMetadata. Note that some types are accessible, but they don't appear in the final type information and thus, can be pruned as well. These are for example inner types of Compact or the types referenced by BitSequence. The result of collecting these accessible types is a list of all the types that are required to decode each possible extrinsic.","breadcrumbs":"RFC-0078: Merkleized Metadata » Prune unrelated Types","id":"523","title":"Prune unrelated Types"},"524":{"body":"Each TypeRef basically references one of the following types: One of the primitive types. All primitive types can be represented by 1 byte and thus, they are directly part of the TypeRef itself to remove an extra level of indirection. A Type using its unique identifier. In FRAME metadata a primitive type is represented like any other type. So, the first step is to remove all the primitive only types from the list of types that were generated in the previous section. The resulting list of types is sorted using the id provided by FRAME metadata. In the last step the TypeRefs are created. Each reference to a primitive type is replaced by one of the corresponding TypeRef primitive type variants and every other reference is replaced by the type's unique identifier. The unique identifier of a type is the index of the type in our sorted list. For Enumerations all variants have the same unique identifier, while they are represented as multiple type information. All variants need to have the same unique identifier as the reference doesn't know which variant will appear in the actual encoded data. let pruned_types = get_pruned_types(); for ty in pruned_types { if ty.is_primitive_type() { pruned_types.remove(ty); }\n} pruned_types.sort(|(left, right)| if left.frame_metadata_id() == right.frame_metadata_id() { left.variant_index() < right.variant_index() } else { left.frame_metadata_id() < right.frame_metadata_id() }\n); fn generate_type_ref(ty, ty_list) -> TypeRef { if ty.is_primitive_type() { TypeRef::primtive_from_ty(ty) } TypeRef::from_id( // Determine the id by using the position of the type in the // list of unique frame metadata ids. ty_list.position_by_frame_metadata_id(ty.frame_metadata_id()) )\n} fn replace_all_sub_types_with_type_refs(ty, ty_list) -> Type { for sub_ty in ty.sub_types() { replace_all_sub_types_with_type_refs(sub_ty, ty_list); sub_ty = generate_type_ref(sub_ty, ty_list) } ty\n} let final_ty_list = Vec::new();\nfor ty in pruned_types { final_ty_list.push(replace_all_sub_types_with_type_refs(ty, ty_list))\n}","breadcrumbs":"RFC-0078: Merkleized Metadata » Generating TypeRef","id":"524","title":"Generating TypeRef"},"525":{"body":"A complete binary merkle tree with blake3 as the hashing function is proposed. For building the merkle tree root, the initial data has to be hashed as a first step. This initial data is referred to as the leaves of the merkle tree. The leaves need to be sorted to make the tree root deterministic. The type information is sorted using their unique identifiers and for the Enumeration, variants are sort using their index. After sorting and hashing all leaves, two leaves have to be combined to one hash. The combination of these of two hashes is referred to as a node . let nodes = leaves;\nwhile nodes.len() > 1 { let right = nodes.pop_back(); let left = nodes.pop_back(); nodes.push_front(blake3::hash(scale::encode((left, right))));\n} let merkle_tree_root = if nodes.is_empty() { [0u8; 32] } else { nodes.back() }; The merkle_tree_root in the end is the last node left in the list of nodes. If there are no nodes in the list left, it means that the initial data set was empty. In this case, all zeros hash is used to represent the empty tree. Building a tree with 5 leaves (numbered 0 to 4): nodes: 0 1 2 3 4 nodes: [3, 4] 0 1 2 nodes: [1, 2] [3, 4] 0 nodes: [[3, 4], 0] [1, 2] nodes: [[[3, 4], 0], [1, 2]] The resulting tree visualized: [root] / \\ * * / \\ / \\ * 0 1 2 / \\\n3 4 Building a tree with 6 leaves (numbered 0 to 5): nodes: 0 1 2 3 4 5 nodes: [4, 5] 0 1 2 3 nodes: [2, 3] [4, 5] 0 1 nodes: [0, 1] [2, 3] [4, 5] nodes: [[2, 3], [4, 5]] [0, 1] nodes: [[[2, 3], [4, 5]], [0, 1]] The resulting tree visualized: [root] / \\ * * / \\ / \\ * * 0 1 / \\ / \\\n2 3 4 5","breadcrumbs":"RFC-0078: Merkleized Metadata » Building the Merkle Tree Root","id":"525","title":"Building the Merkle Tree Root"},"526":{"body":"To ensure that the offline wallet used the correct metadata to show the extrinsic to the user the metadata hash needs to be included in the extrinsic. The metadata hash is generated by hashing the SCALE encoded MetadataDigest: blake3::hash(SCALE::encode(MetadataDigest::V1 { .. })) For the runtime the metadata hash is generated at compile time. Wallets will have to generate the hash using the FRAME metadata. The signing side should control whether it wants to add the metadata hash or if it wants to omit it. To accomplish this it is required to add one extra byte to the extrinsic itself. If this byte is 0 the metadata hash is not required and if the byte is 1 the metadata hash is added using V1 of the MetadataDigest. This leaves room for future versions of the MetadataDigest format. When the metadata hash should be included, it is only added to the data that is signed. This brings the advantage of not requiring to include 32 bytes into the extrinsic itself, because the runtime knows the metadata hash as well and can add it to the signed data as well if required. This is similar to the genesis hash, while this isn't added conditionally to the signed data. So, to recap: Included in the extrinsic is u8, the \"mode\". The mode is either 0 which means to not include the metadata hash in the signed data or the mode is 1 to include the metadata hash in V1. Included in the signed data is an Option<[u8; 32]>. Depending on the mode the value is either None or Some(metadata_hash).","breadcrumbs":"RFC-0078: Merkleized Metadata » Inclusion in an Extrinsic","id":"526","title":"Inclusion in an Extrinsic"},"527":{"body":"The chunking may not be the optimal case for every kind of offline wallet.","breadcrumbs":"RFC-0078: Merkleized Metadata » Drawbacks","id":"527","title":"Drawbacks"},"528":{"body":"All implementations are required to strictly follow the RFC to generate the metadata hash. This includes which hash function to use and how to construct the metadata types tree. So, all implementations are following the same security criteria. As the chains will calculate the metadata hash at compile time, the build process needs to be trusted. However, this is already a solved problem in the Polkadot ecosystem by using reproducible builds. So, anyone can rebuild a chain runtime to ensure that a proposal is actually containing the changes as advertised. Implementations can also be tested easily against each other by taking some metadata and ensuring that they all come to the same metadata hash. Privacy of users should also not be impacted. This assumes that wallets will generate the metadata hash locally and don't leak any information to third party services about which chunks a user will send to their offline wallet. Besides that, there is no leak of private information as getting the raw metadata from the chain is an operation that is done by almost everyone.","breadcrumbs":"RFC-0078: Merkleized Metadata » Testing, Security, and Privacy","id":"528","title":"Testing, Security, and Privacy"},"529":{"body":"","breadcrumbs":"RFC-0078: Merkleized Metadata » Performance, Ergonomics, and Compatibility","id":"529","title":"Performance, Ergonomics, and Compatibility"},"53":{"body":"The described service requires expert attention from security experts familiar with JAM, ELVES, and Ethereum. The ELVES and JAM protocols are expected to undergo audit with the 1.0 ratification of JAM. The proposal introduces no new privacy concerns. Raw PVM assembly may be preferred in a production implementation, along with a host function for Keccak256 to minimize issues related to compiler bugs.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Testing, Security, and Privacy","id":"53","title":"Testing, Security, and Privacy"},"530":{"body":"There should be no measurable impact on performance to Polkadot or any other chain using this feature. The metadata root hash is calculated at compile time and at runtime it is optionally used when checking the signature of a transaction. This means that at runtime no performance heavy operations are done.","breadcrumbs":"RFC-0078: Merkleized Metadata » Performance","id":"530","title":"Performance"},"531":{"body":"The proposal alters the way a transaction is built, signed, and verified. So, this imposes some required changes to any kind of developer who wants to construct transactions for Polkadot or any chain using this feature. As the developer can pass 0 for disabling the verification of the metadata root hash, it can be easily ignored.","breadcrumbs":"RFC-0078: Merkleized Metadata » Ergonomics & Compatibility","id":"531","title":"Ergonomics & Compatibility"},"532":{"body":"RFC 46 produced by the Alzymologist team is a previous work reference that goes in this direction as well. On other ecosystems, there are other solutions to the problem of trusted signing. Cosmos for example has a standardized way of transforming a transaction into some textual representation and this textual representation is included in the signed data. Basically achieving the same as what the RFC proposes, but it requires that for every transaction applied in a block, every node in the network always has to generate this textual representation to ensure the transaction signature is valid.","breadcrumbs":"RFC-0078: Merkleized Metadata » Prior Art and References","id":"532","title":"Prior Art and References"},"533":{"body":"None.","breadcrumbs":"RFC-0078: Merkleized Metadata » Unresolved Questions","id":"533","title":"Unresolved Questions"},"534":{"body":"Does it work with all kind of offline wallets? Generic types currently appear multiple times in the metadata with each instantiation. It could be may be useful to have generic type only once in the metadata and declare the generic parameters at their instantiation. The metadata doesn't contain any kind of semantic information. This means that the offline wallet for example doesn't know what is a balance etc. The current solution for this problem is to match on the type name, but this isn't a sustainable solution. MetadataDigest only provides one token and decimal. However, chains support a lot of chains support multiple tokens for paying fees etc. Probably more a question of having semantic information as mentioned above.","breadcrumbs":"RFC-0078: Merkleized Metadata » Future Directions and Related Material","id":"534","title":"Future Directions and Related Material"},"535":{"body":"(source) Table of Contents RFC-0084: General transactions in extrinsic format Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 12 March 2024 Description Support more extrinsic types by updating the extrinsic format Authors George Pisaltu","breadcrumbs":"RFC-0084: General transactions in extrinsic format » RFC-0084: General transactions in extrinsic format","id":"535","title":"RFC-0084: General transactions in extrinsic format"},"536":{"body":"This RFC proposes a change to the extrinsic format to incorporate a new transaction type, the \"general\" transaction.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Summary","id":"536","title":"Summary"},"537":{"body":"\"General\" transactions, a new type of transaction that this RFC aims to support, are transactions which obey the runtime's extensions and have according extension data yet do not have hard-coded signatures. They are first described in Extrinsic Horizon and supported in 3685 . They enable users to authorize origins in new, more flexible ways (e.g. ZK proofs, mutations over pre-authenticated origins). As of now, all transactions are limited to the account signing model for origin authorization and any additional origin changes happen in extrinsic logic, which cannot leverage the validation process of extensions. An example of a use case for such an extension would be sponsoring the transaction fee for some other user. A new extension would be put in place to verify that a part of the initial payload was signed by the author under who the extrinsic should run and change the origin, but the payment for the whole transaction should be handled under a sponsor's account. A POC for this can be found in 3712 . The new \"general\" transaction type would coexist with both current transaction types for a while and, therefore, the current number of supported transaction types, capped at 2, is insufficient. A new extrinsic type must be introduced alongside the current signed and unsigned types. Currently, an encoded extrinsic's first byte indicate the type of extrinsic using the most significant bit - 0 for unsigned, 1 for signed - and the 7 following bits indicate the extrinsic format version , which has been equal to 4 for a long time. By taking one bit from the extrinsic format version encoding, we can support 2 additional extrinsic types while also having a minimal impact on our capability to extend and change the extrinsic format in the future.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Motivation","id":"537","title":"Motivation"},"538":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Stakeholders","id":"538","title":"Stakeholders"},"539":{"body":"An extrinsic is currently encoded as one byte to identify the extrinsic type and version. This RFC aims to change the interpretation of this byte regarding the reserved bits for the extrinsic type and version. In the following explanation, bits represented using T make up the extrinsic type and bits represented using V make up the extrinsic version. Currently, the bit allocation within the leading encoded byte is 0bTVVV_VVVV. In practice in the Polkadot ecosystem, the leading byte would be 0bT000_0100 as the version has been equal to 4 for a long time. This RFC proposes for the bit allocation to change to 0bTTVV_VVVV. As a result, the extrinsic format version will be bumped to 5 and the extrinsic type bit representation would change as follows: bits type 00 unsigned 10 signed 01 reserved 11 reserved","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Explanation","id":"539","title":"Explanation"},"54":{"body":"Solutions to model other elements in the state trie (account balances and nonces) are not covered in this service design yet. As JAM implementers move towards conformant implementations in 2025, which support gas modeling and justify performance improvements, a proper model of storage costs and fees will be necessary. JAM enables a semi-coherent model for non-Polkadot rollups, starting with optimistic rollups as described here. A similar service may be envisioned for mature ZK rollup ecosystems. An interoperable JAM messaging service between both kinds of non-Polkadot rollups and Polkadot rollups would be highly desirable. The growth of optimistic rollup platforms, led by OP Stack with CEXes (Coinbase and Kraken) and ArbOS, threatens JAM's viability as a rollup host. Achieving JAM's rollup host goals may require urgency to match the speed at which these network effects emerge.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Future Directions and Related Material","id":"54","title":"Future Directions and Related Material"},"540":{"body":"This change would reduce the maximum possible transaction version from the current 127 to 63. In order to bypass the new, lower limit, the extrinsic format would have to change again.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Drawbacks","id":"540","title":"Drawbacks"},"541":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Testing, Security, and Privacy","id":"541","title":"Testing, Security, and Privacy"},"542":{"body":"This change would allow Polkadot to support new types of transactions, with the specific \"general\" transaction type in mind at the time of writing this proposal.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Performance, Ergonomics, and Compatibility","id":"542","title":"Performance, Ergonomics, and Compatibility"},"543":{"body":"There is no performance impact.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Performance","id":"543","title":"Performance"},"544":{"body":"The impact to developers and end-users is minimal as it would just be a bitmask update on their part for parsing the extrinsic type along with the version.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Ergonomics","id":"544","title":"Ergonomics"},"545":{"body":"This change breaks backwards compatiblity because any transaction that is neither signed nor unsigned, but a new transaction type, would be interpreted as having a future extrinsic format version.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Compatibility","id":"545","title":"Compatibility"},"546":{"body":"The original design was originally proposed in the TransactionExtension PR , which is also the motivation behind this effort.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Prior Art and References","id":"546","title":"Prior Art and References"},"547":{"body":"None.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Unresolved Questions","id":"547","title":"Unresolved Questions"},"548":{"body":"Following this change, the \"general\" transaction type will be introduced as part of the Extrinsic Horizon effort, which will shape future work.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Future Directions and Related Material","id":"548","title":"Future Directions and Related Material"},"549":{"body":"(source) Table of Contents RFC-0091: DHT Authority discovery record creation time Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2024-05-20 Description Add creation time for DHT authority discovery records Authors Alex Gheorghe (alexggh)","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » RFC-0091: DHT Authority discovery record creation time","id":"549","title":"RFC-0091: DHT Authority discovery record creation time"},"55":{"body":"Alongside Ethereum DA (via EIP-4844), numerous DA alternatives for rollups exist: Avail, Celestia, Eigenlayer. ORUs rely primarily on fraud proofs, but they require a lengthy 7-day window for these \"fraud proofs.\" The cynical rollup model offers significant UX improvements by eliminating this \"exit window,\" commonly 7 days. None of these alternatives provide the same UX enhancement enabled by \"cynical\" rollups.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Drawbacks, Alternatives, and Unknowns","id":"55","title":"Drawbacks, Alternatives, and Unknowns"},"550":{"body":"Extend the DHT authority discovery records with a signed creation time, so that nodes can determine which record is newer and always decide to prefer the newer records to the old ones.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Summary","id":"550","title":"Summary"},"551":{"body":"Currently, we use the Kademlia DHT for storing records regarding the p2p address of an authority discovery key, the problem is that if the nodes decide to change its PeerId/Network key it will publish a new record, however because of the distributed and replicated nature of the DHT there is no way to tell which record is newer so both old PeerId and the new PeerId will live in the network until the old one expires(36h), that creates all sort of problem and leads to the node changing its address not being properly connected for up to 36h. After this RFC, nodes are extended to decide to keep the new record and propagate the new record to nodes that have the old record stored, so in the end all the nodes will converge faster to the new record(in the order of minutes, not 36h) Implementation of the rfc: https://github.com/paritytech/polkadot-sdk/pull/3786. Current issue without this enhacement: https://github.com/paritytech/polkadot-sdk/issues/3673","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Motivation","id":"551","title":"Motivation"},"552":{"body":"Polkadot node developers.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Stakeholders","id":"552","title":"Stakeholders"},"553":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . In a nutshell, on a specific node the current authority-discovery protocol publishes Kademila DHT records at startup and periodically. The records contain the full address of the node for each authorithy key it owns. The node tries also to find the full address of all authorities in the network by querying the DHT and picking up the first record it finds for each of the authority id it found on chain. The authority discovery DHT records use the protobuf protocol and the current format is specified here . This RFC proposese extending the schema in a backwards compatible manner by adding a new optional creation_time field to AuthorityRecord and nodes can use this information to determine which of the record is newer. Diff of dht-v3.proto vs dht-v2.proto @@ -1,10 +1,10 @@ syntax = \"proto3\"; -package authority_discovery_v2;\n+package authority_discovery_v3; // First we need to serialize the addresses in order to be able to sign them. message AuthorityRecord { repeated bytes addresses = 1;\n+\t// Time since UNIX_EPOCH in nanoseconds, scale encoded\n+\tTimestampInfo creation_time = 2; } message PeerSignature {\n@@ -13,11 +15,17 @@ bytes public_key = 2; } +// Information regarding the creation data of the record\n+message TimestampInfo {\n+ // Time since UNIX_EPOCH in nanoseconds, scale encoded\n+ bytes timestamp = 1;\n+}\n+ Each time a node wants to resolve an authorithy ID it will issue a query with a certain redundancy factor, and from all the results it receives it will decide to pick only the newest record. Additionally, in order to speed up the time until all nodes have the newest record, nodes can optionaly implement a logic where they send the new record to nodes that answered with the older record.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Explanation","id":"553","title":"Explanation"},"554":{"body":"In theory the new protocol creates a bit more traffic on the DHT network, because it waits for DHT records to be received from more than one node, while in the current implementation we just take the first record that we receive and cancel all in-flight requests to other peers. However, because the redundancy factor will be relatively small and this operation happens rarerly, every 10min, this cost is negligible.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Drawbacks","id":"554","title":"Drawbacks"},"555":{"body":"This RFC's implementation https://github.com/paritytech/polkadot-sdk/pull/3786 had been tested on various local test networks and versi. With regard to security the creation time is wrapped inside SignedAuthorityRecord wo it will be signed with the authority id key, so there is no way for other malicious nodes to manipulate this field without the received node observing.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Testing, Security, and Privacy","id":"555","title":"Testing, Security, and Privacy"},"556":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Performance, Ergonomics, and Compatibility","id":"556","title":"Performance, Ergonomics, and Compatibility"},"557":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Performance","id":"557","title":"Performance"},"558":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Ergonomics","id":"558","title":"Ergonomics"},"559":{"body":"The changes are backwards compatible with the existing protocol, so nodes with both the old protocol and newer protocol can exist in the network, this is achieved by the fact that we use protobuf for serializing and deserializing the records, so new fields will be ignore when deserializing with the older protocol and vice-versa when deserializing an old record with the new protocol the new field will be None and the new code accepts this record as being valid.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Compatibility","id":"559","title":"Compatibility"},"56":{"body":"(source) Table of Contents RFC-0000: Feature Name Here Summary Motivation Stakeholders Explanation Introduce a new UMP message type RequestCodeUpgrade Handle RequestCodeUpgrade on backers Get the new code to all validators On-chain code upgrade process Handling new validators How do other parties get hold of the PVF? Pruning Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Further Hardening Generalize this off-chain storage mechanism? Start Date 13 July 2024 Description Implement off-chain parachain runtime upgrades Authors eskimor","breadcrumbs":"RFC-0000: Feature Name Here » RFC-0000: Feature Name Here","id":"56","title":"RFC-0000: Feature Name Here"},"560":{"body":"The enhancements have been inspired by the algorithm specified in here","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Prior Art and References","id":"560","title":"Prior Art and References"},"561":{"body":"N/A","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Unresolved Questions","id":"561","title":"Unresolved Questions"},"562":{"body":"N/A","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Future Directions and Related Material","id":"562","title":"Future Directions and Related Material"},"563":{"body":"(source) Table of Contents RFC-0097: Unbonding Queue Summary Motivation Stakeholders Explanation Mechanism Proposed Parameters Rebonding Empirical Analysis Additional Considerations Deferred slashing UX/UI Conviction voting Potential Extension Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Date 19.06.2024 Description This RFC proposes a safe mechanism to scale the unbonding time from staking on the Relay Chain proportionally to the overall unbonding stake. This approach significantly reduces the expected duration for unbonding, while ensuring that a substantial portion of the stake is always available to slash of validators behaving maliciously within a 28-day window. Authors Jonas Gehrlein & Alistair Stewart","breadcrumbs":"RFC-0097: Unbonding Queue » RFC-0097: Unbonding Queue","id":"563","title":"RFC-0097: Unbonding Queue"},"564":{"body":"This RFC proposes a flexible unbonding mechanism for tokens that are locked from staking on the Relay Chain (DOT/KSM), aiming to enhance user convenience without compromising system security. Locking tokens for staking ensures that Polkadot is able to slash tokens backing misbehaving validators. With changing the locking period, we still need to make sure that Polkadot can slash enough tokens to deter misbehaviour. This means that not all tokens can be unbonded immediately, however we can still allow some tokens to be unbonded quickly. The new mechanism leads to a signficantly reduced unbonding time on average, by queuing up new unbonding requests and scaling their unbonding duration relative to the size of the queue. New requests are executed with a minimum of 2 days, when the queue is comparatively empty, to the conventional 28 days, if the sum of requests (in terms of stake) exceed some threshold. In scenarios between these two bounds, the unbonding duration scales proportionately. The new mechanism will never be worse than the current fixed 28 days. In this document we also present an empirical analysis by retrospectively fitting the proposed mechanism to the historic unbonding timeline and show that the average unbonding duration would drastically reduce, while still being sensitive to large unbonding events. Additionally, we discuss implications for UI, UX, and conviction voting. Note: Our proposition solely focuses on the locks imposed from staking. Other locks, such as governance, remain unchanged. Also, this mechanism should not be confused with the already existing feature of FastUnstake , which lets users unstake tokens immediately that have not received rewards for 28 days or longer. As an initial step to gauge its effectiveness and stability, it is recommended to implement and test this model on Kusama before considering its integration into Polkadot, with appropriate adjustments to the parameters. In the following, however, we limit our discussion to Polkadot.","breadcrumbs":"RFC-0097: Unbonding Queue » Summary","id":"564","title":"Summary"},"565":{"body":"Polkadot has one of the longest unbonding periods among all Proof-of-Stake protocols, because security is the most important goal. Staking on Polkadot is still attractive compared to other protocols because of its above-average staking APY. However the long unbonding period harms usability and deters potential participants that want to contribute to the security of the network. The current length of the unbonding period imposes significant costs for any entity that even wants to perform basic tasks such as a reorganization / consolidation of their stashes, or updating their private key infrastructure. It also limits participation of users that have a large preference for liquidity. The combination of long unbonding periods and high returns has lead to the proliferation of liquid staking , where parachains or centralised exchanges offer users their staked tokens before the 28 days unbonding period is over either in original DOT/KSM form or derivative tokens. Liquid staking is harmless if few tokens are involved but it could result in many validators being selected by a few entities if a large fraction of DOTs were involved. This may lead to centralization (see here for more discussion on threats of liquid staking) and an opportunity for attacks. The new mechanism greatly increases the competitiveness of Polkadot, while maintaining sufficient security.","breadcrumbs":"RFC-0097: Unbonding Queue » Motivation","id":"565","title":"Motivation"},"566":{"body":"Every DOT/KSM token holder","breadcrumbs":"RFC-0097: Unbonding Queue » Stakeholders","id":"566","title":"Stakeholders"},"567":{"body":"Before diving into the details of how to implement the unbonding queue, we give readers context about why Polkadot has a 28-day unbonding period in the first place. The reason for it is to prevent long-range attacks (LRA) that becomes theoretically possible if more than 1/3 of validators collude. In essence, a LRA describes the inability of users, who disconnect from the consensus at time t0 and reconnects later, to realize that validators which were legitimate at a certain time, say t0 but dropped out in the meantime, are not to be trusted anymore. That means, for example, a user syncing the state could be fooled by trusting validators that fell outside the active set of validators after t0, and are building a competitive and malicious chain (fork). LRAs of longer than 28 days are mitigated by the use of trusted checkpoints, which are assumed to be no more than 28 days old. A new node that syncs Polkadot will start at the checkpoint and look for proofs of finality of later blocks, signed by 2/3 of the validators. In an LRA fork, some of the validator sets may be different but only if 2/3 of some validator set in the last 28 days signed something incorrect. If we detect an LRA of no more than 28 days with the current unbonding period, then we should be able to detect misbehaviour from over 1/3 of validators whose nominators are still bonded. The stake backing these validators is considerable fraction of the total stake (empirically it is 0.287 or so). If we allowed more than this stake to unbond, without checking who it was backing, then the LRA attack might be free of cost for an attacker. The proposed mechansim allows up to half this stake to unbond within 28 days. This halves the amount of tokens that can be slashed, but this is still very high in absolute terms. For example, at the time of writing (19.06.2024) this would translate to around 120 millions DOTs. Attacks other than an LRA, such as backing incorrect parachain blocks, should be detected and slashed within 2 days. This is why the mechanism has a minimum unbonding period. In practice an LRA does not affect clients who follow consensus more frequently than every 2 days, such as running nodes or bridges. However any time a node syncs Polkadot if an attacker is able to connect to it first, it could be misled. In short, in the light of the huge benefits obtained, we are fine by only keeping a fraction of the total stake of validators slashable against LRAs at any given time.","breadcrumbs":"RFC-0097: Unbonding Queue » Explanation","id":"567","title":"Explanation"},"568":{"body":"When a user ( nominator or validator) decides to unbond their tokens, they don't become instantly available. Instead, they enter an unbonding queue . The following specification illustrates how the queue works, given a user wants to unbond some portion of their stake denoted as new_unbonding_stake. We also store a variable, max_unstake that tracks how much stake we allow to unbond potentially earlier than 28 eras (28 days on Polkadot and 7 days on Kusama). To calculate max_unstake, we record for each era how much stake was used to back the lowest-backed 1/3 of validators. We store this information for the last 28 eras and let min_lowest_third_stake be the minimum of this over the last 28 eras. max_unstake is determined by MIN_SLASHABLE_SHARE x min_lowest_third_stake. In addition, we can use UPPER_BOUND and LOWER_BOUND as variables to scale the unbonding duration of the queue. At any time we store back_of_unbonding_queue_block_number which expresses the block number when all the existing unbonders have unbonded. Let's assume a user wants to unbond some of their stake, i.e., new_unbonding_stake, and issues the request at some arbitrary block number denoted as current_block. Then: unbonding_time_delta = new_unbonding_stake / max_unstake * UPPER_BOUND This number needs to be added to the back_of_unbonding_queue_block_number under the conditions that it does not undercut current_block + LOWER_BOUND or exceed current_block + UPPER_BOUND. back_of_unbonding_queue_block_number = max(current_block_number, back_of_unbonding_queue_block_number) + unbonding_time_delta This determines at which block the user has their tokens unbonded, making sure that it is in the limit of LOWER_BOUND and UPPER_BOUND. unbonding_block_number = min(UPPER_BOUND, max(back_of_unbonding_queue_block_number - current_block_number, LOWER_BOUND)) + current_block_number Ultimately, the user's token are unbonded at unbonding_block_number.","breadcrumbs":"RFC-0097: Unbonding Queue » Mechanism","id":"568","title":"Mechanism"},"569":{"body":"There are a few constants to be exogenously set. They are up for discussion, but we make the following recommendation: MIN_SLASHABLE_SHARE: 1/2 - This is the share of stake backing the lowest 1/3 of validators that is slashable at any point in time. It offers a trade-off between security and unbonding time. Half is a sensible choice. Here, we have sufficient stake to slash while allowing for a short average unbonding time. LOWER_BOUND: 28800 blocks (or 2 eras): This value resembles a minimum unbonding time for any stake of 2 days. UPPER_BOUND: 403200 blocks (or 28 eras): This value resembles the maximum time a user faces in their unbonding time. It equals to the current unbonding time and should be familiar to users.","breadcrumbs":"RFC-0097: Unbonding Queue » Proposed Parameters","id":"569","title":"Proposed Parameters"},"57":{"body":"Change the upgrade process of a parachain runtime upgrade to become an off-chain process with regards to the relay chain. Upgrades are still contained in parachain blocks, but will no longer need to end up in relay chain blocks nor in relay chain state.","breadcrumbs":"RFC-0000: Feature Name Here » Summary","id":"57","title":"Summary"},"570":{"body":"Users that chose to unbond might want to cancel their request and rebond. There is no security loss in doing this, but with the scheme above, it could imply that a large unbond increases the unbonding time for everyone else later in the queue. When the large stake is rebonded, however, the participants later in the queue move forward and can unbond more quickly than originally estimated. It would require an additional extrinsic by the user though. Thus, we should store the unbonding_time_delta with the unbonding account. If it rebonds when it is still unbonding, then this value should be subtracted from back_of_unbonding_queue_block_number. So unbonding and rebonding leaves this number unaffected. Note that we must store unbonding_time_delta, because in later eras max_unstake might have changed and we cannot recompute it.","breadcrumbs":"RFC-0097: Unbonding Queue » Rebonding","id":"570","title":"Rebonding"},"571":{"body":"We can use the proposed unbonding queue calculation, with the recommended parameters, and simulate the queue over the course of Polkadot's unbonding history. Instead of doing the analysis on a per-block basis, we calculate it on a daily basis. To simulate the unbonding queue, we require the ratio between the daily total stake of the lowest third backed validators and the daily total stake (which determines the max_unstake) and the sum of daily and newly unbonded tokens. Due to the NPoS algorithm , the first number has only small variations and we used a constant as approximation (0.287) determined by sampling a bunch of empirical eras. At this point, we want to thank Parity's Data team for allowing us to leverage their data infrastructure in these analyses. The following graph plots said statistics. The abovementioned graph combines two metrics into a single graph. Unbonded Amount: The number of daily and newly unbonded token over time scaled to the y-axis of 28 days. In particular its normalized by daily_unbonded / max(daily_unbonded) * 28. Unbonding Days: The daily expected unbonding days given the history of daily_unbonded. We can observe that historical unbonds only trigger an unbonding time larger than LOWER_BOUND in situations with extensive and/or clustered unbonding amounts. The average unbonding time across the whole timeseries is ~2.67 days. We can, however, see it taking effect pushing unbonding times up during large unbonding events. In the largest events, we hit a maximum of 28 days. This gives us reassurance that it is sufficiently sensitive and it makes sense to match the UPPER_BOUND with the historically largest unbonds. The main parameter affecting the situation is the max_unstake. The relationship is obvious: decreasing the max_unstake makes the queue more sensitive, i.e., having it spike more quickly and higher with unbonding events. Given that these events historically were mostly associated with parachain auctions, we can assume that, in the absence of major systemic events, users will experience drastically reduced unbonding times. The analysis can be reproduced or changed to other parameters using this repository .","breadcrumbs":"RFC-0097: Unbonding Queue » Empirical Analysis","id":"571","title":"Empirical Analysis"},"572":{"body":"","breadcrumbs":"RFC-0097: Unbonding Queue » Additional Considerations","id":"572","title":"Additional Considerations"},"573":{"body":"Currently we defer applying many slashes until around 28 days have passed. This was implemented so we can conveniently cancel slashes via governance in the case that the slashing was due to a bug. While rare on Polkadot, such bugs cause a significant fraction of slashes. This includes slashing for attacks other than LRAs for which we've assumed that 2 days is enough to slash. But 2 days in not enough to cancel slashes via OpenGov. Owing to the way exposures, which nominators back validators with how many tokens, are stored, it is hard to search for whether a nominator has deferred slashes that need to be applied to them on chain as of now. So we cannot simply check when a nominator attempts to withdraw their bond. We can solve this by freezing the unbonding queue while there are pending slashes in the staking system. In the worst case, where the slash is applied, we would forced all members of the queue to unbond with 28 days minus the days since they are in the queue (i.e., nobody ever needs to wait more than 28 days) and pause the unbonding queue until there are no deferred slashes in the system. This solution is potentially easier to implement but could cause disruptions for unbonding stakers that are not slashed, because they do not benefit from the queue. It is crucial to note that unbonding is still always possible for all stakers in the usual 28 days. Since slashes should occur rarely, this should not cause distruptions in reality too often. In addition, we could further complement the solution by adding a new extrinsic where any account is allowed to point out the unbonding accounts with the deferred slashes. Then, the chain would set the unbonding_block_number of the affected accounts to after the time when the slash would be applied, which will be no more than 28 days from the time the staker unbonded. After removing the offenders from the queue, we could unfreeze the unbonding queue and restore operation for unslashed accounts immediately. To find nominators with deferred slashes it is required, however, to iterate through all nominators, which is only feasible to do off chain. There should be plenty of incentive to do so by the non-slashed unbonding accounts that seek to reduce the opportunity costs of being forced wait potentially much longer than necessary. This solution achieves resolve the situation securely and, in the worst case where no user submits the extrinsic, no staker would exceed an unbonding duration of the usual 28 days and apply all slashes as intended.","breadcrumbs":"RFC-0097: Unbonding Queue » Deferred slashing","id":"573","title":"Deferred slashing"},"574":{"body":"As per the nature of the unbonding queue, the more a user slices up their stake to be unbonded, the quicker they find their expected unbonding time. This, however, comes at the cost of creating more and/or larger transactions, i.e., incurring higher transactions costs. We leave it to UI implementations to provide a good UX to inform users about this trade-off and help them find their individual willingness to pay to unbond even faster. For most users, splitting up their stake will not lead to any meaningful advantage because their effect on the queue is neglible.","breadcrumbs":"RFC-0097: Unbonding Queue » UX/UI","id":"574","title":"UX/UI"},"575":{"body":"Changing the (expected) unbonding period has an indirect impact on conviction voting, because the governance locks do not stack with the staking locks. In other words, if a user is already being locked in staking, they can, for free, choose a conviction vote that is lower or equal to that locking time. Currently and with an unbonding period of a fixed 28 days, that means, the 3x conviction vote comes essentially for free. There has been discussions to rescale the conviction weights to improved parametrization. But, the transition between the old locks and new locks pose significant challenges. We argue, that under our unbonding queue, the current conviction voting scheme logically better aligns with their impact on governance, avoiding an expensive solution to migrate existing locks to a new scheme. For example, if the average unbonding period is around 2 days from staking, locking tokens for an additional 26 days justifies a higher weight (in that regard of3x). Voters that seek maximum liquidity are free to do so but it is fair to be weighted less in governance decisions that are naturally affecting the long-term success of Polkadot.","breadcrumbs":"RFC-0097: Unbonding Queue » Conviction voting","id":"575","title":"Conviction voting"},"576":{"body":"In addition to a simple queue, we could add a market component that lets users always unbond from staking at the minimum possible waiting time)(== LOWER_BOUND, e.g., 2 days), by paying a variable fee. To achieve this, it is reasonable to split the total unbonding capacity into two chunks, with the first capacity for the simple queue and the remaining capacity for the fee-based unbonding. By doing so, we allow users to choose whether they want the quickest unbond and paying a dynamic fee or join the simple queue. Setting a capacity restriction for both queues enables us to guarantee a predictable unbonding time in the simple queue, while allowing users with the respective willingness to pay to get out even earlier. The fees are dynamically adjusted and are proportional to the unbonding stake (and thereby expressed in a percentage of the requested unbonding stake). In contrast to a unified queue, this prevents the issue that users paying a fee jump in front of other users not paying a fee, pushing their unbonding time back (which would be bad for UX). The revenue generated could be burned. This extension and further specifications are left out of this RFC, because it adds further complexity and the empirical analysis above suggests that average unbonding times will already be close the LOWER_BOUND, making a more complex design unnecessary. We advise to first implement the discussed mechanism and assess after some experience whether an extension is desirable.","breadcrumbs":"RFC-0097: Unbonding Queue » Potential Extension","id":"576","title":"Potential Extension"},"577":{"body":"Lower security for LRAs: Without a doubt, the theoretical security against LRAs decreases. But, as we argue, the attack is still costly enough to deter attacks and the attack is sufficiently theoretical. Here, the benefits outweigh the costs. Griefing attacks: A large holder could pretend to unbond a large amount of their tokens to prevent other users to exit the network earlier. This would, however be costly due to the fact that the holder loses out on staking rewards. The larger the impact on the queue, the higher the costs. In any case it must be noted that the UPPER_BOUND is still 28 days, which means that nominators are never left with a longer unbonding period than currently. There is not enough gain for the attacker to endure this cost. Challenge for Custodians and Liquid Staking Providers : Changing the unbonding time, especially making it flexible, requires entities that offer staking derivatives to rethink and rework their products.","breadcrumbs":"RFC-0097: Unbonding Queue » Drawbacks","id":"577","title":"Drawbacks"},"578":{"body":"NA","breadcrumbs":"RFC-0097: Unbonding Queue » Testing, Security, and Privacy","id":"578","title":"Testing, Security, and Privacy"},"579":{"body":"NA","breadcrumbs":"RFC-0097: Unbonding Queue » Performance, Ergonomics, and Compatibility","id":"579","title":"Performance, Ergonomics, and Compatibility"},"58":{"body":"Having parachain runtime upgrades go through the relay chain has always been seen as a scalability concern. Due to optimizations in statement distribution and asynchronous backing it became less crucial and got de-prioritized, the original issue can be found here . With the introduction of Agile Coretime and in general our efforts to reduce barrier to entry more for Polkadot more, the issue becomes more relevant again: We would like to reduce the required storage deposit for PVF registration, with the aim to not only make it cheaper to run a parachain (bulk + on-demand coretime), but also reduce the amount of capital required for the deposit. With this we would hope for far more parachains to get registered, thousands potentially even ten thousands. With so many PVFs registered, updates are expected to become more frequent and even attacks on service quality for other parachains would become a higher risk.","breadcrumbs":"RFC-0000: Feature Name Here » Motivation","id":"58","title":"Motivation"},"580":{"body":"The authors cannot see any potential impact on performance.","breadcrumbs":"RFC-0097: Unbonding Queue » Performance","id":"580","title":"Performance"},"581":{"body":"The authors cannot see any potential impact on ergonomics for developers. We discussed potential impact on UX/UI for users above.","breadcrumbs":"RFC-0097: Unbonding Queue » Ergonomics","id":"581","title":"Ergonomics"},"582":{"body":"The authors cannot see any potential impact on compatibility. This should be assessed by the technical fellows.","breadcrumbs":"RFC-0097: Unbonding Queue » Compatibility","id":"582","title":"Compatibility"},"583":{"body":"Ethereum proposed a similar solution Alistair did some initial write-up There are other solutions that further mitigate the risk of LRAs.","breadcrumbs":"RFC-0097: Unbonding Queue » Prior Art and References","id":"583","title":"Prior Art and References"},"584":{"body":"(source) Table of Contents RFC-0099: Introduce a transaction extension version Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 03 July 2024 Description Introduce a versioning for transaction extensions. Authors Bastian Köcher","breadcrumbs":"RFC-0099: Introduce a transaction extension version » RFC-0099: Introduce a transaction extension version","id":"584","title":"RFC-0099: Introduce a transaction extension version"},"585":{"body":"This RFC proposes a change to the extrinsic format to include a transaction extension version.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Summary","id":"585","title":"Summary"},"586":{"body":"The extrinsic format supports to be extended with transaction extensions. These transaction extensions are runtime specific and can be different per chain. Each transaction extension can add data to the extrinsic itself or extend the signed payload. This means that adding a transaction extension is breaking the chain specific extrinsic format. A recent example was the introduction of the CheckMetadatHash to Polkadot and all its system chains. As the extension was adding one byte to the extrinsic, it broke a lot of tooling. By introducing an extra version for the transaction extensions it will be possible to introduce changes to these transaction extensions while still being backwards compatible. Based on the version of the transaction extensions, each chain runtime could decode the extrinsic correctly and also create the correct signed payload.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Motivation","id":"586","title":"Motivation"},"587":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Stakeholders","id":"587","title":"Stakeholders"},"588":{"body":"RFC84 introduced the extrinsic format 5. The idea is to piggyback onto this change of the extrinsic format to add the extra version for the transaction extensions. If required, this could also come as extrinsic format 6, but 5 is not yet deployed anywhere. The extrinsic format supports the following types of transactions: Bare: Does not add anything to the extrinsic. Signed: (Address, Signature, Extensions) General: Extensions The Signed and General transaction would change to: Signed: (Address, Signature, Version, Extensions) General: (Version, Extensions) The Version being a SCALE encoded u8 representing the version of the transaction extensions. In the chain runtime the version can be used to determine which set of transaction extensions should be used to decode and to validate the transaction.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Explanation","id":"588","title":"Explanation"},"589":{"body":"This adds one byte more to each signed transaction.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Drawbacks","id":"589","title":"Drawbacks"},"59":{"body":"Parachain Teams Relay Chain Node implementation teams Relay Chain runtime developers","breadcrumbs":"RFC-0000: Feature Name Here » Stakeholders","id":"59","title":"Stakeholders"},"590":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Testing, Security, and Privacy","id":"590","title":"Testing, Security, and Privacy"},"591":{"body":"This will ensure that changes to the transactions extensions can be done in a backwards compatible way.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Performance, Ergonomics, and Compatibility","id":"591","title":"Performance, Ergonomics, and Compatibility"},"592":{"body":"There is no performance impact.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Performance","id":"592","title":"Performance"},"593":{"body":"Runtime developers need to take care of the versioning and ensure to bump as required, so that there are no compatibility breaking changes without a bump of the version. It will also add a little bit more code in the runtime to decode these old versions, but this should be neglectable.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Ergonomics","id":"593","title":"Ergonomics"},"594":{"body":"When introduced together with extrinsic format version 5 from RFC84 , it can be implemented in a backwards compatible way. So, transactions can still be send using the old extrinsic format and decoded by the runtime.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Compatibility","id":"594","title":"Compatibility"},"595":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Prior Art and References","id":"595","title":"Prior Art and References"},"596":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Unresolved Questions","id":"596","title":"Unresolved Questions"},"597":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Future Directions and Related Material","id":"597","title":"Future Directions and Related Material"},"598":{"body":"(source) Table of Contents RFC-0100: New XCM instruction: InitiateAssetsTransfer Summary Motivation Stakeholders Explanation Example usage: transferring 2 different asset types across 3 chains Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 11 July 2024 Description Add new XCM instruction: InitiateAssetsTransfer for mixing asset transfer types in same XCM Authors Adrian Catangiu","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » RFC-0100: New XCM instruction: InitiateAssetsTransfer","id":"598","title":"RFC-0100: New XCM instruction: InitiateAssetsTransfer"},"599":{"body":"This RFC proposes a new instruction that provides a way to initiate on remote chains, asset transfers which transfer multiple types (teleports, local-reserve, destination-reserve) of assets, using XCM alone. The currently existing instructions are too opinionated and force each XCM asset transfer to a single transfer type (teleport, local-reserve, destination-reserve). This results in inability to combine different types of transfers in single transfer which results in overall poor UX when trying to move assets across chains.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Summary","id":"599","title":"Summary"},"6":{"body":"ReportMetadata The ReportMetadata is a new instruction to query metadata information. It can be used to query metadata key list or to query values of interested keys. This instruction allows querying the metadata of: a collection (fungible or nonfungible) an NFT If an asset (or an asset instance) for which the query is made doesn't exist, the Response::Null should be reported via the existing QueryResponse instruction. The ReportMetadata can be used without origin (i.e., following the ClearOrigin instruction) since it only reads state. Safety: The reporter origin should be trusted to hold the true metadata. If the reserve-based model is considered, the asset's reserve location must be viewed as the only source of truth about the metadata. The use case for this instruction is when the metadata information of a foreign asset (or asset instance) is used in the logic of a consensus entity that requested it. /// An instruction to query metadata of an asset or an asset instance.\nReportMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the metadata of the collection is reported. instance: AssetInstance, /// See `MetadataQueryKind` below. query_kind: MetadataQueryKind, /// The usual field for Report XCM instructions. /// /// Information regarding the query response. /// The `QueryResponseInfo` type is already defined in the XCM spec. response_info: QueryResponseInfo,\n} Where the MetadataQueryKind is: enum MetadataQueryKind { /// Query metadata key list. KeyList, /// Query values of the specified keys. Values(MetadataKeys),\n} The QueryMetadata works in conjunction with the existing QueryResponse instruction. The Response type should be modified accordingly: we need to add a new AssetMetadata variant to it. /// The struct used in the existing `QueryResponse` instruction.\npub enum Response { // ... snip, existing variants ... /// The metadata info. AssetMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the reported metadata is related to the collection, not a token. instance: AssetInstance, /// See `MetadataResponseData` below. data: MetadataResponseData, }\n} pub enum MetadataResponseData { /// The metadata key list to be reported /// in response to the `KeyList` metadata query kind. KeyList(MetadataKeys), /// The values of the keys that were specified in the /// `Values` variant of the metadata query kind. Values(MetadataMap),\n} ModifyMetadata The ModifyMetadata is a new instruction to request a remote chain to modify the values of the specified keys. This instruction can be used to update the metadata of a collection (fungible or nonfungible) or of an NFT. The remote chain handles the modification request and may reject it based on its internal rules. The request can only be executed or rejected in its entirety. It must not be executed partially. To execute the ModifyMetadata, an origin is required so that the handling logic can authorize the metadata modification request from a known source. Since this instruction requires an origin, the assets used to cover the execution fees must be transferred in a way that preserves the origin. For instance, one can use the approach described in RFC #122 if the handling chain configured aliasing rules accordingly. The example use case of this instruction is to ask the reserve location of the asset to modify the metadata. So that, the original asset's metadata is updated according to the reserve location's rules. ModifyMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the modification request targets the collection, not a token. instance: AssetInstance, /// The map contains the keys mapped to the requested new values. modification: MetadataMap,\n}","breadcrumbs":"RFC-0125: XCM Asset Metadata » New instructions","id":"6","title":"New instructions"},"60":{"body":"The issues with on-chain runtime upgrades are: Needlessly costly. A single runtime upgrade more or less occupies an entire relay chain block, thus it might affect also other parachains, especially if their candidates are also not negligible due to messages for example or they want to uprade their runtime at the same time. The signalling of the parachain to notify the relay chain of an upcoming runtime upgrade already contains the upgrade. Therefore the only way to rate limit upgrades is to drop an already distributed update in the size of megabytes: With the result that the parachain missed a block and more importantly it will try again with the very next block, until it finally succeeds. If we imagine to reduce capacity of runtime upgrades to let's say 1 every 100 relay chain blocks, this results in lot's of wasted effort and lost blocks. We discussed introducing a separate signalling before submitting the actual runtime, but I think we should just go one step further and make upgrades fully off-chain. Which also helps bringing down deposit costs in a secure way, as we are also actually reducing costs for the network.","breadcrumbs":"RFC-0000: Feature Name Here » Explanation","id":"60","title":"Explanation"},"600":{"body":"XCM is the de-facto cross-chain messaging protocol within the Polkadot ecosystem, and cross-chain assets transfers is one of its main use-cases. Unfortunately, in its current spec, it does not support initiating on a remote chain, one or more transfers that combine assets with different transfer types. For example, ParachainA cannot instruct AssetHub to teleport ForeignAssetX to ParachainX alongside USDT (which has to be reserve transferred) using current XCM specification. There currently exist DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions that initiate asset transfers on execution, but they are opinionated in the type of transfer to use. Combining them is also not possible, because as a result of their individual execution, a message containing a ClearOrigin instruction is sent to the destination chain, making subsequent transfers impossible after the first instruction is executed. The new instruction proposed by this RFC allows an XCM program to describe multiple asset transfer types, then execute them in one shot with a single remote_xcm program sent to the target chain to effect the transfer and subsequently clear origin. Multi-hop asset transfers will benefit from this change by allowing single XCM program to handle multiple types of transfers and reduce complexity. Bridge asset transfers greatly benefit from this change by allowing building XCM programs to transfer multiple assets across multiple hops in a single pseudo-atomic action. For example, allows single XCM program execution to transfer multiple assets from ParaK on Kusama, through Kusama Asset Hub, over the bridge through Polkadot Asset Hub with final destination ParaP on Polkadot. With current XCM, we are limited to doing multiple independent transfers for each individual hop in order to move both \"interesting\" assets, but also \"supporting\" assets (used to pay fees).","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Motivation","id":"600","title":"Motivation"},"601":{"body":"Runtime users Runtime devs Wallet devs dApps devs","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Stakeholders","id":"601","title":"Stakeholders"},"602":{"body":"A new instruction InitiateAssetsTransfer is introduced that initiates an assets transfer from the chain it is executed on, to another chain. The executed transfer is point-to-point (chain-to-chain) with all of the transfer properties specified in the instruction parameters. The instruction also allows specifying another XCM program to be executed on the remote chain. If a transfer requires going through multiple hops, an XCM program can compose this instruction to be used at every chain along the path, on each hop describing that specific leg of the transfer. Note: Transferring assets that require different paths (chains along the way) is not supported within same XCM because of the async nature of cross chain messages. This new instruction, however, enables initiating transfers for multiple assets that take the same path even if they require different transfer types along that path. The usage and composition model of InitiateAssetsTransfer is the same as with existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions. The main difference comes from the ability to handle assets that have different point-to-point transfer type between A and B. The other benefit is that it also allows specifying remote fee payment and transparently appends the required remote fees logic to the remote XCM. We can specify the desired transfer type for some asset(s) using: /// Specify which type of asset transfer is required for a particular `(asset, dest)` combination.\npub enum AssetTransferFilter { /// teleport assets matching `AssetFilter` to `dest` Teleport(AssetFilter), /// reserve-transfer assets matching `AssetFilter` to `dest`, using the local chain as reserve ReserveDeposit(AssetFilter), /// reserve-transfer assets matching `AssetFilter` to `dest`, using `dest` as reserve ReserveWithdraw(AssetFilter),\n} This RFC proposes 1 new XCM instruction: /// Cross-chain transfer matching `assets` in the holding register as follows:\n///\n/// Assets in the holding register are matched using the given list of `AssetTransferFilter`s,\n/// they are then transferred based on their specified transfer type:\n///\n/// - teleport: burn local assets and append a `ReceiveTeleportedAsset` XCM instruction to\n/// the XCM program to be sent onward to the `dest` location,\n///\n/// - reserve deposit: place assets under the ownership of `dest` within this consensus system\n/// (i.e. its sovereign account), and append a `ReserveAssetDeposited` XCM instruction\n/// to the XCM program to be sent onward to the `dest` location,\n///\n/// - reserve withdraw: burn local assets and append a `WithdrawAsset` XCM instruction\n/// to the XCM program to be sent onward to the `dest` location,\n///\n/// The onward XCM is then appended a `ClearOrigin` to allow safe execution of any following\n/// custom XCM instructions provided in `remote_xcm`.\n///\n/// The onward XCM also potentially contains a `BuyExecution` instruction based on the presence\n/// of the `remote_fees` parameter (see below).\n///\n/// If a transfer requires going through multiple hops, an XCM program can compose this instruction\n/// to be used at every chain along the path, describing that specific leg of the transfer.\n///\n/// Parameters:\n/// - `dest`: The location of the transfer next hop.\n/// - `remote_fees`: If set to `Some(asset_xfer_filter)`, the single asset matching\n/// `asset_xfer_filter` in the holding register will be transferred first in the remote XCM\n/// program, followed by a `BuyExecution(fee)`, then rest of transfers follow.\n/// This guarantees `remote_xcm` will successfully pass a `AllowTopLevelPaidExecutionFrom` barrier.\n/// - `remote_xcm`: Custom instructions that will be executed on the `dest` chain. Note that\n/// these instructions will be executed after a `ClearOrigin` so their origin will be `None`.\n///\n/// Safety: No concerns.\n///\n/// Kind: *Command*.\n///\nInitiateAssetsTransfer { destination: Location, assets: Vec, remote_fees: Option, remote_xcm: Xcm<()>,\n} An InitiateAssetsTransfer { .. } instruction shall transfer to dest, all assets in the holding register that match the provided assets and remote_fees filters. These filters identify the assets to be transferred as well as the transfer type to be used for transferring them. It shall handle the local side of the transfer, then forward an onward XCM to dest for handling the remote side of the transfer. It should do so using same mechanisms as existing DepositReserveAsset, InitiateReserveWithdraw, InitiateTeleport instructions but practically combining all required XCM instructions to be remotely executed into a single remote XCM program to be sent over to dest. Furthermore, through remote_fees: Option, it shall allow specifying a single asset to be used for fees on dest chain. This single asset shall be remotely handled/received by the first instruction in the onward XCM and shall be followed by a BuyExecution instruction using it. If remote_fees is set to None, the first instruction in the onward XCM shall be a UnpaidExecution instruction. The rest of the assets shall be handled by subsequent instructions, thus also finally allowing single asset buy execution barrier security recommendation. The BuyExecution appended to the onward XCM specifies WeightLimit::Unlimited, thus being limited only by the remote_fees asset \"amount\". This is a deliberate decision for enhancing UX - in practice, people/dApps care about limiting the amount of fee asset used and not the actually used weight. The onward XCM, following the assets transfers instructions, ClearOrigin or DescendOrigin instructions shall be appended to stop acting on behalf of the source chain, then the caller-provided remote_xcm shall also be appended, allowing the caller to control what to do with the transferred assets.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Explanation","id":"602","title":"Explanation"},"603":{"body":"Transferring ROCs as the native asset of RococoAssetHub and PENs as the native asset of Penpal, Transfer origin is Penpal (on Rococo) and the destination is WestendAssetHub (across the bridge), ROCs are native to RococoAssetHub and are registered as trust-backed assets on Penpal and WestendAssetHub, PENs are native to Penpal and are registered as teleportable assets on RococoAssetHub and as foreign assets on WestendAssetHub, Fees on RococoAssetHub and WestendAssetHub are paid using ROCs. We can transfer them from Penpal (Rococo), through RococoAssetHub, over the bridge to WestendAssetHub by executing a single XCM message, even though we'll be mixing multiple types of transfers along the path: 1st leg of the transfer: Penpal -> Rococo Asset Hub: teleport PENs reserve withdraw ROCs 2nd leg of the transfer: Rococo Asset Hub -> Westend Asset Hub: reserve deposit both PENs and ROCs Penpal::execute_with(|| { let destination = Location::new(2, (GlobalConsensus(Westend), Parachain(1000)).into()); let rocs_id: AssetId = Parent.into(); let rocs: Asset = (rocs_id.clone(), rocs_amount).into(); let pens: Asset = (pens_id, pens_amount).into(); let assets: Assets = vec![rocs.clone(), pens.clone()].into(); // XCM to be executed at dest (Westend Asset Hub) let xcm_on_dest = Xcm(vec![DepositAsset { assets: Wild(All), beneficiary: beneficiary.clone() }]); // XCM to be executed at Rococo Asset Hub let context = PenpalUniversalLocation::get(); let reanchored_assets = assets.clone().reanchored(&local_asset_hub, &context).unwrap(); let reanchored_dest = destination.clone().reanchored(&local_asset_hub, &context).unwrap(); let reanchored_rocs_id = rocs_id.clone().reanchored(&local_asset_hub, &context).unwrap(); // from AHR, both ROCs and PENs are local-reserve transferred to Westend Asset Hub let assets_filter = vec![ AssetTransferFilter::ReserveDeposit(reanchored_assets.clone().into()) ]; // we want to pay with ROCs on WAH let remote_fees = Some(AssetTransferFilter::ReserveDeposit( AssetFilter::Wild(AllOf { id: reanchored_rocs_id.into(), fun: WildFungibility::Fungible })) ); let xcm_on_ahr = Xcm(vec![ InitiateAssetsTransfer { dest: reanchored_dest, assets: assets_filter, remote_fees: Some(), remote_xcm: xcm_on_dest, }, ]); // pay remote fees with ROCs let remote_fees = Some( AssetTransferFilter::ReserveWithdraw( AssetFilter::Wild(AllOf { id: rocs_id.into(), fun: WildFungibility::Fungible }) ) ); // XCM to be executed locally let xcm = Xcm::(vec![ // Withdraw both ROCs and PENs from origin account WithdrawAsset(assets.clone().into()), // Execute the transfers while paying remote fees with ROCs InitiateAssetsTransfer { dest: local_asset_hub, assets: vec![ // ROCs are reserve-withdrawn on AHR ReserveWithdraw(rocs.into()), // PENs are teleported to AHR Teleport(pens.into()), ], remote_fees, remote_xcm: xcm_on_ahr, }, ]); ::PolkadotXcm::execute( signed_origin, bx!(xcm::VersionedXcm::V4(xcm.into())), Weight::MAX, ).unwrap();\n})","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Example usage: transferring 2 different asset types across 3 chains","id":"603","title":"Example usage: transferring 2 different asset types across 3 chains"},"604":{"body":"No drawbacks identified.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Drawbacks","id":"604","title":"Drawbacks"},"605":{"body":"There should be no security risks related to the new instruction from the XCVM perspective. It follows the same pattern as with single-type asset transfers, only now it allows combining multiple types at once. Improves security by enabling enforcement of single asset for buying execution , which minimizes the potential free/unpaid work that a receiving chain has to do. It does so, by making the required execution fee payment, part of the instruction logic through the remote_fees: Option parameter, which will make sure the remote XCM starts with a single-asset-holding-loading-instruction, immediately followed by a BuyExecution using said asset.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Testing, Security, and Privacy","id":"605","title":"Testing, Security, and Privacy"},"606":{"body":"This brings no impact to the rest of the XCM spec. It is a new, independent instruction, no changes to existing instructions. Enhances the exposed functionality of Polkadot. Will allow multi-chain transfers that are currently forced to happen in multiple programs per asset per \"hop\", to be possible in a single XCM program.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Performance, Ergonomics, and Compatibility","id":"606","title":"Performance, Ergonomics, and Compatibility"},"607":{"body":"No performance changes/implications.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Performance","id":"607","title":"Performance"},"608":{"body":"The proposal enhances developers' and users' cross-chain asset transfer capabilities. This enhancement is optimized for XCM programs transferring multiple assets, needing to run their logic across multiple chains.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Ergonomics","id":"608","title":"Ergonomics"},"609":{"body":"Does this proposal break compatibility with existing interfaces, older versions of implementations? Summarize necessary migrations or upgrade strategies, if any. This enhancement is compatible with all existing XCM programs and versions. New (XCMv5) programs using this instruction shall be best-effort downgraded to an older XCM version, but cannot guarantee success. A program where the new instruction is used to initiate multiple types of asset transfers, cannot be downgraded to older XCM versions, because there is no equivalent capability there. Such conversion attempts will explicitly fail.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Compatibility","id":"609","title":"Compatibility"},"61":{"body":"As part of elastic scaling we are already planning to increase flexibility of UMP messages , we can now use this to our advantage and introduce another UMP message: enum UMPSignal { // For elastic scaling OnCore(CoreIndex), // For off-chain upgrades RequestCodeUpgrade(Hash),\n} We could also make that new message a regular XCM, calling an extrinsic on the relay chain, but we will want to look into that message right after validation on the backers on the node side, making a straight forward semantic message more apt for the purpose.","breadcrumbs":"RFC-0000: Feature Name Here » Introduce a new UMP message type RequestCodeUpgrade","id":"61","title":"Introduce a new UMP message type RequestCodeUpgrade"},"610":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Prior Art and References","id":"610","title":"Prior Art and References"},"611":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Unresolved Questions","id":"611","title":"Unresolved Questions"},"612":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Future Directions and Related Material","id":"612","title":"Future Directions and Related Material"},"613":{"body":"(source) Table of Contents RFC-0101: XCM Transact remove require_weight_at_most parameter Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 12 July 2024 Description Remove require_weight_at_most parameter from XCM Transact Authors Adrian Catangiu","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » RFC-0101: XCM Transact remove require_weight_at_most parameter","id":"613","title":"RFC-0101: XCM Transact remove require_weight_at_most parameter"},"614":{"body":"The Transact XCM instruction currently forces the user to set a specific maximum weight allowed to the inner call and then also pay for that much weight regardless of how much the call actually needs in practice. This RFC proposes improving the usability of Transact by removing that parameter and instead get and charge the actual weight of the inner call from its dispatch info on the remote chain.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Summary","id":"614","title":"Summary"},"615":{"body":"The UX of using Transact is poor because of having to guess/estimate the require_weight_at_most weight used by the inner call on the target. We've seen multiple Transact on-chain failures caused by guessing wrong values for this require_weight_at_most even though the rest of the XCM program would have worked. In practice, this parameter only adds UX overhead with no real practical value. Use cases fall in one of two categories: Unpaid execution of Transacts - in these cases the require_weight_at_most is not really useful, caller doesn't have to pay for it, and on the call site it either fits the block or not; Paid execution of single Transact - the weight to be spent by the Transact is already covered by the BuyExecution weight limit parameter. We've had multiple OpenGov root/whitelisted_caller proposals initiated by core-devs completely or partially fail because of incorrect configuration of require_weight_at_most parameter. This is a strong indication that the instruction is hard to use.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Motivation","id":"615","title":"Motivation"},"616":{"body":"Runtime Users, Runtime Devs, Wallets, dApps,","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Stakeholders","id":"616","title":"Stakeholders"},"617":{"body":"The proposed enhancement is simple: remove require_weight_at_most parameter from the instruction: - Transact { origin_kind: OriginKind, require_weight_at_most: Weight, call: DoubleEncoded },\n+ Transact { origin_kind: OriginKind, call: DoubleEncoded }, The XCVM implementation shall no longer use require_weight_at_most for weighing. Instead, it shall weigh the Transact instruction by decoding and weighing the inner call.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Explanation","id":"617","title":"Explanation"},"618":{"body":"No drawbacks, existing scenarios work as before, while this also allows new/easier flows.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Drawbacks","id":"618","title":"Drawbacks"},"619":{"body":"Currently, an XCVM implementation can weigh a message just by looking at the decoded instructions without decoding the Transact's call, but assuming require_weight_at_most weight for it. With the new version it has to decode the inner call to know its actual weight. But this does not actually change the security considerations, as can be seen below. With the new Transact the weighing happens after decoding the inner call. The entirety of the XCM program containing this Transact needs to be either covered by enough bought weight using a BuyExecution, or the origin has to be allowed to do free execution. The security considerations around how much can someone execute for free are the same for both this new version and the old. In both cases, an \"attacker\" can do the XCM decoding (including Transact inner calls) for free by adding a large enough BuyExecution without actually having the funds available. In both cases, decoding is done for free, but in both cases execution fails early on BuyExecution.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Testing, Security, and Privacy","id":"619","title":"Testing, Security, and Privacy"},"62":{"body":"We will introduce a new request/response protocol for both collators and validators, with the following request/response: struct RequestBlob { blob_hash: Hash,\n} struct BlobResponse { blob: Vec\n} This protocol will be used by backers to request the PVF from collators in the following conditions: They received a collation sending RequestCodeUpgrade. They received a collation, but they don't yet have the code that was previously registered on the relaychain. (E.g. disk pruned, new validator) In case they received the collation via PoV distribution instead of from the collator itself, they will use the exact same message to fetch from the valiator they got the PoV from.","breadcrumbs":"RFC-0000: Feature Name Here » Handle RequestCodeUpgrade on backers","id":"62","title":"Handle RequestCodeUpgrade on backers"},"620":{"body":"","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Performance, Ergonomics, and Compatibility","id":"620","title":"Performance, Ergonomics, and Compatibility"},"621":{"body":"No performance change.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Performance","id":"621","title":"Performance"},"622":{"body":"Ergonomics are slightly improved by simplifying Transact API.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Ergonomics","id":"622","title":"Ergonomics"},"623":{"body":"Compatible with previous XCM programs.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Compatibility","id":"623","title":"Compatibility"},"624":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Prior Art and References","id":"624","title":"Prior Art and References"},"625":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Unresolved Questions","id":"625","title":"Unresolved Questions"},"626":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Future Directions and Related Material","id":"626","title":"Future Directions and Related Material"},"627":{"body":"(source) Table of Contents RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts Summary Motivation Stakeholders Explanation Reclaiming unused space in the descriptor UMP transport Polkadot Primitive changes Backwards compatibility Parachain block validation On-chain backing Drawbacks Testing, Security, and Privacy Performance Ergonomics Compatibility Relay chain runtime Validators Tooling Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 15 July 2024 Description Constrain parachain block validity to a specific core and session Authors Andrei Sandu","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts","id":"627","title":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts"},"628":{"body":"Elastic scaling is not resilient against griefing attacks without a way for a PoV (Proof of Validity) to commit to the particular core index it was intended for. This RFC proposes a way to include core index information in the candidate commitments and the CandidateDescriptor data structure in a backward compatible way. Additionally, it proposes the addition of a SessionIndex field in the CandidateDescriptor to make dispute resolution more secure and robust.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Summary","id":"628","title":"Summary"},"629":{"body":"This RFC proposes a way to solve two different problems: For Elastic Scaling, it prevents anyone who has acquired a valid collation to DoS the parachain by providing the same collation to all backing groups assigned to the parachain. This can happen before the next valid parachain block is authored and will prevent the chain of candidates from being formed, reducing the throughput of the parachain to a single core. The dispute protocol relies on validators trusting the session index provided by other validators when initiating and participating in disputes. It is used to look up validator keys and check dispute vote signatures. By adding a SessionIndex in the CandidateDescriptor, validators no longer have to trust the Sessionindex provided by the validator raising a dispute. The dispute may concern a relay chain block not yet imported by a validator. In this case, validators can safely assume the session index refers to the session the candidate has appeared in, otherwise, the chain would have rejected the candidate.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Motivation","id":"629","title":"Motivation"},"63":{"body":"Once the candidate issuing RequestCodeUpgrade got backed on chain, validators will start fetching the code from the backers as part of availability distribution. To mitigate attack vectors we should make sure that serving requests for code can be treated as low priority requests. Thus I am suggesting the following scheme: Validators will notice via a runtime API (TODO: Define) that a new code has been requested, the API will return the Hash and a counter, which starts at some configurable value e.g. 10. The validators are now aware of the new hash and start fetching, but they don't have to wait for the fetch to succeed to sign their bitfield. Then on each further candidate from that chain that counter gets decremented. Validators which have not yet succeeded fetching will now try again. This game continues until the counter reached 0. Now it is mandatory to have to code in order to sign a 1 in the bitfield. PVF pre-checking will happen after the candidate which brought the counter to 0 has been successfully included and thus is also able to assume that 2/3 of the validators have the code. This scheme serves two purposes: Fetching can happen over a longer period of time with low priority. E.g. if we waited for the PVF at the very first avaialbility distribution, this might actually affect liveness of other chains on the same core. Distributing megabytes of data to a thousand validators, might take a bit. Thus this helps isolating parachains from each other. By configuring the initial counter value we can affect how much an upgrade costs. E.g. forcing the parachain to produce 10 blocks, means 10x the cost for issuing an update. If too frequent upgrades ever become a problem for the system, we have a knob to make them more costly.","breadcrumbs":"RFC-0000: Feature Name Here » Get the new code to all validators","id":"63","title":"Get the new code to all validators"},"630":{"body":"Polkadot core developers. Cumulus node developers. Tooling, block explorer developers. This approach and alternatives have been considered and discussed in this issue .","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Stakeholders","id":"630","title":"Stakeholders"},"631":{"body":"The approach proposed below was chosen primarily because it minimizes the number of breaking changes, the complexity and takes less implementation and testing time. The proposal is to change the existing primitives while keeping binary compatibility with the older versions. We repurpose unused fields to introduce core index and a session index information in the CandidateDescriptor and extend the UMP to transport non-XCM messages.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Explanation","id":"631","title":"Explanation"},"632":{"body":"The CandidateDescriptor includes collator and signature fields. The collator includes a signature on the following descriptor fields: parachain id, relay parent, validation data hash, validation code hash, and the PoV hash. However, in practice, having a collator signature in the receipt on the relay chain does not provide any benefits as there is no mechanism to punish or reward collators that have provided bad parachain blocks. This proposal aims to remove the collator signature and all the logic that checks the collator signatures of candidate receipts. We use the first 7 reclaimed bytes to represent the version, the core, session index, and fill the rest with zeroes. So, there is no change in the layout and length of the receipt. The new primitive is binary-compatible with the old one.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Reclaiming unused space in the descriptor","id":"632","title":"Reclaiming unused space in the descriptor"},"633":{"body":"CandidateCommitments remains unchanged as we will store scale encoded UMPSignal messages directly in the parachain UMP queue by outputting them in upward_messages . The UMP queue layout is changed to allow the relay chain to receive both the XCM messages and UMPSignal messages. An empty message (empty Vec) is used to mark the end of XCM messages and the start of UMPSignal messages. The UMPSignal is optional and can be omitted by parachains not using elastic scaling. This way of representing the new messages has been chosen over introducing an enum wrapper to minimize breaking changes of XCM message decoding in tools like Subscan for example. Example: [ XCM message1, XCM message2, ..., EMPTY message, UMPSignal::SelectCore ] UMPSignal messages /// The selector that determines the core index.\npub struct CoreSelector(pub u8); /// The offset in the relay chain claim queue.\n///\n/// The state of the claim queue is given by the relay chain block\n/// that is used as context for the `PoV`. pub struct ClaimQueueOffset(pub u8); /// Signals sent by a parachain to the relay chain.\npub enum UMPSignal { /// A message sent by a parachain to select the core the candidate is committed to. /// Relay chain validators, in particular backers, use the `CoreSelector` and `ClaimQueueOffset` /// to compute the index of the core the candidate has committed to. SelectCore(CoreSelector, ClaimQueueOffset),\n} The CoreSelector together with the ClaimQueueOffset are used to index the claim queue. This way the validators can compute the CoreIndex and ensure that the collator put the correct CoreIndex into the CandidateDescriptor. Example: cq_offset = 1 and core_selector = 3 The table below represents a snapshot of the claim queue: offset = 0 offset = 1 offset = 2 Core 1 Para A Para A Para A Core 2 Para A Para B Para A Core 3 Para B Para A Para A The purpose of ClaimQueueOffset is to select the column from the above table. For cq_offset = 1 we get [Para A, Para B, Para A] and use as input to create a sorted vec with the cores A is assigned to: [Core 1, Core 3] and call it para_assigned_cores. We use core_selector and determine the committed core index is Core 3 like this: let committed_core_index = para_assigned_cores[core_selector % para_assigned_cores.len()];","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » UMP transport","id":"633","title":"UMP transport"},"634":{"body":"New CandidateDescriptor reclaim 32 bytes from collator: CollatorId and 64 bytes from signature: CollatorSignature and rename to reserved1 and reserved2 fields. take 1 bytes from reserved1 for a new version: u8 field. take 2 bytes from reserved1 for a new core_index: u16 field. take 4 bytes from reserved1 for a new session_index: u32 field. the remaining reserved1 and reserved2 fields are zeroed The new primitive will look like this: pub struct CandidateDescriptorV2 { /// The ID of the para this is a candidate for. para_id: ParaId, /// The hash of the relay-chain block this is executed in the context of. relay_parent: H, /// Version field. The raw value here is not exposed, instead, it is used /// to determine the `CandidateDescriptorVersion` version: InternalVersion, /// The core index where the candidate is backed. core_index: u16, /// The session in which the candidate is backed. session_index: SessionIndex, /// Reserved bytes. reserved1: [u8; 25], /// The blake2-256 hash of the persisted validation data. This is extra data derived from /// relay-chain state which may vary based on bitfields included before the candidate. /// Thus it cannot be derived entirely from the relay parent. persisted_validation_data_hash: Hash, /// The blake2-256 hash of the PoV. pov_hash: Hash, /// The root of a block's erasure encoding Merkle tree. erasure_root: Hash, /// Reserved bytes. reserved2: [u8; 64], /// Hash of the para header that is being generated by this candidate. para_head: Hash, /// The blake2-256 hash of the validation code bytes. validation_code_hash: ValidationCodeHash,\n} In future format versions, parts of the reserved1 and reserved2 bytes can be used to include additional information in the descriptor.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Polkadot Primitive changes","id":"634","title":"Polkadot Primitive changes"},"635":{"body":"Two flavors of candidate receipts are used in network protocols, runtime and node implementation: CommittedCandidateReceipt which includes the CandidateDescriptor and the CandidateCommitments CandidateReceipt which includes the CandidateDescriptor and just a hash of the commitments We want to support both the old and new versions in the runtime and node, so the implementation must be able to detect the version of a given candidate receipt. The version of the descriptor is detected by checking the reserved fields. If they are not zeroed, it means it is a version 1 descriptor. Otherwise the version field is used further to determine the version. It should be 0 for version 2 descriptors. If it is not the descriptor has an unknown version and should be considered invalid.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Backwards compatibility","id":"635","title":"Backwards compatibility"},"636":{"body":"If the candidate descriptor is version 1, there are no changes. Backers must check the validity of core_index and session_index fields. A candidate must not be backed if any of the following are true: the core_index in the descriptor does not match the core the backer is assigned to the session_index is not equal to the session index the candidate is backed in the core_index in the descriptor does not match the one determined by the UMPSignal::SelectCore message","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Parachain block validation","id":"636","title":"Parachain block validation"},"637":{"body":"If the candidate descriptor is version 1, there are no changes. For version 2 descriptors the runtime will determine the core_index using the same inputs as backers did off-chain. It currently stores the claim queue at the newest allowed relay parent corresponding to the claim queue offset 0. The runtime needs to be changed to store a claim queue snapshot at all allowed relay parents.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » On-chain backing","id":"637","title":"On-chain backing"},"638":{"body":"The only drawback is that further additions to the descriptor are limited to the amount of remaining unused space.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Drawbacks","id":"638","title":"Drawbacks"},"639":{"body":"Standard testing (unit tests, CI zombienet tests) for functionality and mandatory security audit to ensure the implementation does not introduce any new security issues. Backward compatibility of the implementation will be tested on testnets (Versi and Westend). There is no impact on privacy.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Testing, Security, and Privacy","id":"639","title":"Testing, Security, and Privacy"},"64":{"body":"First when a candidate is backed we need to make the new hash available (together with a counter) via a runtime API so validators in availability distribution can check for it and fetch it if changed (see previous section). For performance reasons, I think we should not do an additional call, but replace the existing one with one containing the new additional information (Option<(Hash, Counter)>). Once the candidate gets included (counter 0), the hash is given to pre-checking and only after pre-checking succeeded (and a full session passed) it is finally enacted and the parachain can switch to the new code. (Same process as it used to be.)","breadcrumbs":"RFC-0000: Feature Name Here » On-chain code upgrade process","id":"64","title":"On-chain code upgrade process"},"640":{"body":"Overall performance will be improved by not checking the collator signatures in runtime and nodes. The impact on the UMP queue and candidate receipt processing is negligible. The ClaimQueueOffset along with the relay parent choice allows parachains to optimize their block production for either throughput or lower XCM message processing latency. A value of 0 with the newest relay parent provides the best latency while picking older relay parents avoids re-orgs.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Performance","id":"640","title":"Performance"},"641":{"body":"It is mandatory for elastic parachains to switch to the new receipt format and commit to a core by sending the UMPSignal::SelectCore message. It is optional but desired that all parachains switch to the new receipts for providing the session index for disputes. The implementation of this RFC itself must not introduce any breaking changes for the parachain runtime or collator nodes.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Ergonomics","id":"641","title":"Ergonomics"},"642":{"body":"The proposed changes are not fully backward compatible, because older validators verify the collator signature of candidate descriptors. Additional care must be taken before enabling the new descriptors by waiting for at least 2/3 + 1 validators to upgrade. Validators that have not upgraded will not back candidates using the new descriptor format and will also initiate disputes against these candidates.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Compatibility","id":"642","title":"Compatibility"},"643":{"body":"The first step is to remove collator signature checking logic in the runtime but keep the node side collator signature checks. The runtime must be upgraded to support the new primitives before any collator or node is allowed to use the new candidate receipts format.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Relay chain runtime","id":"643","title":"Relay chain runtime"},"644":{"body":"To ensure a smooth launch, a new node feature is required. The feature acts as a signal for supporting the new candidate receipts on the node side and can only be safely enabled if at least 2/3 + 1 of the validators are upgraded. Node implementations need to decode the new candidate descriptor once the feature is enabled otherwise they might raise disputes and get slashed. Once the feature is enabled, the validators will skip checking the collator signature when processing the candidate receipts and verify the CoreIndex and SessionIndex fields if present in the receipt. No new implementation of networking protocol versions for collation and validation is required.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Validators","id":"644","title":"Validators"},"645":{"body":"Any tooling that decodes UMP XCM messages needs an update to support or ignore the new UMP messages, but they should be fine to decode the regular XCM messages that come before the separator.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Tooling","id":"645","title":"Tooling"},"646":{"body":"Forum discussion about a new CandidateReceipt format: https://forum.polkadot.network/t/pre-rfc-discussion-candidate-receipt-format-v2/3738","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Prior Art and References","id":"646","title":"Prior Art and References"},"647":{"body":"N/A","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Unresolved Questions","id":"647","title":"Unresolved Questions"},"648":{"body":"The implementation is extensible and future-proof to some extent. With minimal or no breaking changes, additional fields can be added in the candidate descriptor until the reserved space is exhausted At this point, there is a simple way to determine the version of the receipt, by testing for zeroed reserved bytes in the descriptor. Future versions of the receipt can be implemented and identified by using the version field of the descriptor introduced in this RFC.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Future Directions and Related Material","id":"648","title":"Future Directions and Related Material"},"649":{"body":"(source) Table of Contents RFC-0105: XCM improved fee mechanism Summary Motivation Stakeholders Explanation Examples Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Allow multiple types of fees to be paid Authors Francisco Aguirre","breadcrumbs":"RFC-0105: XCM improved fee mechanism » RFC-0105: XCM improved fee mechanism","id":"649","title":"RFC-0105: XCM improved fee mechanism"},"65":{"body":"Backers If a backer receives a collation for a parachain it does not yet have the code as enacted on chain (see \"On-chain code upgrade process\"), it will use above request/response protocol to fetch it from whom it received the collation. Availablity Distribution Validators in availability distribution will be changed to only sign a 1 in the bitfield of a candidate if they not only have the chunk, but also the currently active PVF. They will fetch it from backers in case they don't have it yet.","breadcrumbs":"RFC-0000: Feature Name Here » Handling new validators","id":"65","title":"Handling new validators"},"650":{"body":"XCM already handles execution fees in an effective and efficient manner using the BuyExecution instruction. However, other types of fees are not handled as effectively -- for example, delivery fees. Fees exist that can't be measured using Weight -- as execution fees can -- so a new method should be thought up for those cases. This RFC proposes making the fee handling system simpler and more general, by doing two things: Adding a fees register Deprecating BuyExecution and adding a new instruction PayFees with new semantics to ultimately replace it.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Summary","id":"650","title":"Summary"},"651":{"body":"Execution fees are handled correctly by XCM right now. However, the addition of extra fees, like for message delivery, result in awkward ways of integrating them into the XCVM implementation. This is because these types of fees are not included in the language. The standard should have a way to correctly deal with these implementation specific fees, that might not exist in every system that uses XCM. The new instruction moves the specified amount of fees from the holding register to a dedicated fees register that the XCVM can use in flexible ways depending on its implementation. The XCVM implementation is free to use these fees to pay for execution fees, transport fees, or any other type of fee that might be necessary. This moves the specifics of fees further away from the XCM standard, and more into the actual underlying XCVM implementation, which is a good thing.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Motivation","id":"651","title":"Motivation"},"652":{"body":"Runtime Users Runtime Devs Wallets dApps","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Stakeholders","id":"652","title":"Stakeholders"},"653":{"body":"The new instruction that will replace BuyExecution is a much simpler and general version: PayFees. This instruction takes one Asset, takes it from the holding register, and puts it into a new fees register. The XCVM implementation can now use this Asset to make sure every necessary fee is paid for, this includes execution fees, delivery fees, and any other type of fee necessary for the program to execute successfully. PayFees { asset: Asset } This new instruction will reserve the entirety of the asset operand for fee payment. There is not concept of returning the leftover fees to the holding register, to allow for the implementation to charge fees at different points during execution. Because of this, the asset passed in can't be used for anything else during the entirety of the program. This is different from the current semantics of BuyExecution. If not all Asset in the fees register is used when the execution ends, then we trap them alongside any possible leftover assets from the holding register. RefundSurplus can be used to move all leftover fees from the fees register to the holding register. Care must be taken that this is used only after all possible instructions which might charge fees, else execution will fail.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Explanation","id":"653","title":"Explanation"},"654":{"body":"Most XCM programs that pay for execution are written like so: // Instruction that loads the holding register\nBuyExecution { asset, weight_limit }\n// ...rest With this RFC, the structure would be the same, but using the new instruction, that has different semantics: // Instruction that loads the holding register\nPayFees { asset }\n// ...rest","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Examples","id":"654","title":"Examples"},"655":{"body":"There needs to be an explicit change from BuyExecution to PayFees, most often accompanied by a reduction in the assets passed in.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Drawbacks","id":"655","title":"Drawbacks"},"656":{"body":"It might become a security concern if leftover fees are trapped, since a lot of them are expected.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Testing, Security, and Privacy","id":"656","title":"Testing, Security, and Privacy"},"657":{"body":"","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Performance, Ergonomics, and Compatibility","id":"657","title":"Performance, Ergonomics, and Compatibility"},"658":{"body":"There should be no performance downsides to this approach. The fees register is a simplification that may actually result in better performance, in the case an implementation is doing a workaround to achieve what this RFC proposes.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Performance","id":"658","title":"Performance"},"659":{"body":"The interface is going to be very similar to the already existing one. Even simpler since PayFees will only receive one asset. That asset will allow users to limit the amount of fees they are willing to pay.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Ergonomics","id":"659","title":"Ergonomics"},"66":{"body":"Two ways: Discover collators via relay chain DHT and request from them: Preferred way, as it is less load on validators. Request from validators, which will serve on a best effort basis.","breadcrumbs":"RFC-0000: Feature Name Here » How do other parties get hold of the PVF?","id":"66","title":"How do other parties get hold of the PVF?"},"660":{"body":"This RFC can't just change the semantics of the BuyExecution instruction since that instruction accepts any funds, uses what it needs and returns the rest immediately. The new proposed instruction, PayFees, doesn't return the leftover immediately, it keeps it in the fees register. In practice, the deprecated BuyExecution needs to be slowly rolled out in favour of PayFees.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Compatibility","id":"660","title":"Compatibility"},"661":{"body":"The closed RFC PR on the xcm-format repository, before XCM RFCs got moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/53.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Prior Art and References","id":"661","title":"Prior Art and References"},"662":{"body":"None","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Unresolved Questions","id":"662","title":"Unresolved Questions"},"663":{"body":"This proposal would greatly benefit from an improved asset trapping system. CustomAssetClaimer is also related, as it directly improves the ergonomics of this proposal. LeftoverAssetsDestination execution hint would also similarly improve the ergonomics. Removal of JIT fees is also related, they are useless with this proposal.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Future Directions and Related Material","id":"663","title":"Future Directions and Related Material"},"664":{"body":"(source) Table of Contents RFC-0107: XCM Execution hints Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Add a mechanism for configuring particular XCM executions Authors Francisco Aguirre","breadcrumbs":"RFC-0107: XCM Execution hints » RFC-0107: XCM Execution hints","id":"664","title":"RFC-0107: XCM Execution hints"},"665":{"body":"A previous XCM RFC (https://github.com/polkadot-fellows/xcm-format/pull/37) introduced a SetAssetClaimer instruction. This idea of instructing the XCVM to change some implementation-specific behavior is useful. In order to generalize this mechanism, this RFC introduces a new instruction SetHints and makes the SetAssetClaimer be just one of many possible execution hints.","breadcrumbs":"RFC-0107: XCM Execution hints » Summary","id":"665","title":"Summary"},"666":{"body":"There is a need for specifying how certain implementation-specific things should behave. Things like who can claim the assets or what can be done instead of trapping assets. Another idea for a hint: AssetForFees: to signify to the executor what asset the user prefers to use for fees. LeftoverAssetsDestination: for depositing leftover assets to a destination instead of trapping them","breadcrumbs":"RFC-0107: XCM Execution hints » Motivation","id":"666","title":"Motivation"},"667":{"body":"Runtime devs Wallets dApps","breadcrumbs":"RFC-0107: XCM Execution hints » Stakeholders","id":"667","title":"Stakeholders"},"668":{"body":"A new instruction, SetHints, will be added. This instruction will take a single parameter of type Hint, an enumeration. The first variant for this enum is AssetClaimer, which allows to specify a location that should be able to claim trapped assets. This means the instruction SetAssetClaimer would also be removed, in favor of this. In Rust, the new definitions would look as follows: enum Instruction { // ...snip... SetHints(BoundedVec), // ...snip...\n} enum Hint { AssetClaimer(Location), // more can be added\n} type NumVariants = /* Number of variants of the `Hint` enum */;","breadcrumbs":"RFC-0107: XCM Execution hints » Explanation","id":"668","title":"Explanation"},"669":{"body":"The SetHints instruction might be hard to benchmark, since we should look into the actual hints being set to know how much weight to attribute to it.","breadcrumbs":"RFC-0107: XCM Execution hints » Drawbacks","id":"669","title":"Drawbacks"},"67":{"body":"We covered how validators get hold of new code, but when can they prune old ones? In principle it is not an issue, if some validors prune code, because: We changed it so that a candidate is not deemed available if validators were not able to fetch the PVF. Backers can always fetch the PVF from collators as part of the collation fetching. But the majority of validators should always keep the latest code of any parachain and only prune the previous one, once the first candidate using the new code got finalized. This ensures that disputes will always be able to resolve.","breadcrumbs":"RFC-0000: Feature Name Here » Pruning","id":"67","title":"Pruning"},"670":{"body":"Hints are specified on a per-message basis, so they have to be specified at the beginning of a message. If they were to be specified at the end, hints like AssetClaimer would be useless if an error occurs beforehand and assets get trapped before ever reaching the hint. The instruction takes a bounded vector of hints so as to not force barriers to allow an arbitrary number of SetHint instructions.","breadcrumbs":"RFC-0107: XCM Execution hints » Testing, Security, and Privacy","id":"670","title":"Testing, Security, and Privacy"},"671":{"body":"","breadcrumbs":"RFC-0107: XCM Execution hints » Performance, Ergonomics, and Compatibility","id":"671","title":"Performance, Ergonomics, and Compatibility"},"672":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Performance","id":"672","title":"Performance"},"673":{"body":"The SetHints instruction provides a better integration with barriers. If we had to add one barrier for SetAssetClaimer and another for each new hint that's added, barriers would need to be changed all the time. Also, this instruction would make it simpler to write XCM programs. You only need to specify the hints you want in one single instruction at the top of your program.","breadcrumbs":"RFC-0107: XCM Execution hints » Ergonomics","id":"673","title":"Ergonomics"},"674":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Compatibility","id":"674","title":"Compatibility"},"675":{"body":"The previous RFC PR in the xcm-format repository before XCM RFCs moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/59.","breadcrumbs":"RFC-0107: XCM Execution hints » Prior Art and References","id":"675","title":"Prior Art and References"},"676":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Unresolved Questions","id":"676","title":"Unresolved Questions"},"677":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Future Directions and Related Material","id":"677","title":"Future Directions and Related Material"},"678":{"body":"(source) Table of Contents RFC-0108: Remove XCM testnet NetworkIds Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Remove the NetworkIds for testnets Westend and Rococo Authors","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » RFC-0108: Remove XCM testnet NetworkIds","id":"678","title":"RFC-0108: Remove XCM testnet NetworkIds"},"679":{"body":"This RFC aims to remove the NetworkIds of Westend and Rococo, arguing that testnets shouldn't go in the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Summary","id":"679","title":"Summary"},"68":{"body":"The major drawback of this solution is the same as any solution the moves work off-chain, it adds complexity to the node. E.g. nodes needing the PVF, need to store them separately, together with their own pruning strategy as well.","breadcrumbs":"RFC-0000: Feature Name Here » Drawbacks","id":"68","title":"Drawbacks"},"680":{"body":"We've already seen the plans to phase out Rococo and Paseo has appeared. Instead of constantly changing the testnets included in the language, we should favor specifying them via their genesis hash, using NetworkId::ByGenesis.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Motivation","id":"680","title":"Motivation"},"681":{"body":"Runtime devs Wallets dApps","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Stakeholders","id":"681","title":"Stakeholders"},"682":{"body":"Remove Westend and Rococo from the included NetworkIds in the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Explanation","id":"682","title":"Explanation"},"683":{"body":"This RFC will make it less convenient to specify a testnet, but not by a large amount.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Drawbacks","id":"683","title":"Drawbacks"},"684":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Testing, Security, and Privacy","id":"684","title":"Testing, Security, and Privacy"},"685":{"body":"","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Performance, Ergonomics, and Compatibility","id":"685","title":"Performance, Ergonomics, and Compatibility"},"686":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Performance","id":"686","title":"Performance"},"687":{"body":"It will very slightly reduce the ergonomics of testnet developers but improve the stability of the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Ergonomics","id":"687","title":"Ergonomics"},"688":{"body":"NetworkId::Rococo and NetworkId::Westend can just use NetworkId::ByGenesis, as can other testnets.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Compatibility","id":"688","title":"Compatibility"},"689":{"body":"A previous attempt to add NetworkId::Paseo: https://github.com/polkadot-fellows/xcm-format/pull/58.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Prior Art and References","id":"689","title":"Prior Art and References"},"69":{"body":"Implementations adhering to this RFC, will respond to PVF requests with the actual PVF, if they have it. Requesters will persist received PVFs on disk for as long as they are replaced by a new one. Implementations must not be lazy here, if validators only fetched the PVF when needed, they can be prevented from participating in disputes. Validators should treat incoming requests for PVFs in general with rather low priority, but should prefer fetches from other validators over requests from random peers. Given that we are altering what set bits in the availability bitfields mean (not only chunk, but also PVF available), it is important to have enough validators upgraded, before we allow collators to make use of the new runtime upgrade mechanism. Otherwise we would risk disputes to not being able to succeed. This RFC has no impact on privacy.","breadcrumbs":"RFC-0000: Feature Name Here » Testing, Security, and Privacy","id":"69","title":"Testing, Security, and Privacy"},"690":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Unresolved Questions","id":"690","title":"Unresolved Questions"},"691":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Future Directions and Related Material","id":"691","title":"Future Directions and Related Material"},"692":{"body":"(source) Table of Contents RFC-0122: Asset transfers can alias XCM origin on destination to original origin Summary Motivation Stakeholders Explanation Trust assumptions XCM InitiateAssetsTransfer instruction changes Example scenarios Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 01 Sep 2024. Description Single and Multi-hop asset transfers should be able to carry over original origin Authors Adrian Catangiu","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » RFC-0122: Asset transfers can alias XCM origin on destination to original origin","id":"692","title":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin"},"693":{"body":"XCM programs generated by the InitiateAssetTransfer instruction shall have the option to carry over the original origin all the way to the final destination. They shall do so by internally making use of AliasOrigin or ClearOrigin depending on given parameters. This allows asset transfers to retain their original origin even across multiple hops. Ecosystem chains would have to change their trusted aliasing rules to effectively make use of this feature.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Summary","id":"693","title":"Summary"},"694":{"body":"Currently, all XCM asset transfer instructions ultimately clear the origin in the remote XCM message by use of the ClearOrigin instruction. This is done for security considerations to ensure that subsequent (user-controlled) instructions cannot command the authority of the sending chain. The problem with this approach is that it limits what can be achieved on remote chains through XCM. Most XCM operations require having an origin, and following any asset transfer the origin is lost, meaning not much can be done other than depositing the transferred assets to some local account or transferring them onward to another chain. For example, we cannot transfer some funds for buying execution, then do a Transact (all in the same XCM message). The above example is a basic, core building block for cross-chain interactions and we should support it. Transact XCM programs today require a two step process: And we want to be able to do it using a single XCM program.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Motivation","id":"694","title":"Motivation"},"695":{"body":"Runtime Users, Runtime Devs, wallets, cross-chain dApps.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Stakeholders","id":"695","title":"Stakeholders"},"696":{"body":"In the case of XCM programs going from source-chain directly to dest-chain without an intermediary hop, we can enable scenarios such as above by using the AliasOrigin instruction instead of the ClearOrigin instruction. Instead of clearing the source-chain origin, the destination chain shall attempt to alias source-chain to \"original origin\" on the source chain. Most common such origin aliasing would be X1(Parachain(source-chain)) -> X2(Parachain(source-chain), AccountId32(origin-account)) for the case of a single hop transfer where the initiator is a (signed/pure/proxy) account origin-account on source-chain. This is equivalent to using the DescendOrigin instruction in this case, but also usable in the multi hop case. This allows an actor on chain A to Transact on chain B without having to prefund its SA account on chain B, instead they can simply transfer the required fees in the same XCM program as the Transact. As long as the asset transfer has the same XCM route/hops as the rest of the program, this pattern of usage can be composed across multiple hops, to ultimately Transact on the final hop using the original origin on the source chain, effectively abstracting away any intermediary hops.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Explanation","id":"696","title":"Explanation"},"697":{"body":"The model described above works between chains that configure certain aliasing rules. Origin aliasing is highly customizable at the runtime level, so that chains can define coarse filters or granular pairs of (source, target) locations aliasing. This RFC suggests a coarse set of aliasing rules that chains can use for allowing the vast majority of Transact usecases in a \"one-click\" manner (single user signature), without practically lowering their security posture. Suggested Aliasing Rules: Any chain allows aliasing origin into a child location. Equivalent to DescendOrigin into an interior location. Parachains allow Asset Hub root location to alias into any other origin. The first rule is allowing use of AliasOrigin with same effect as doing a DescendOrigin, so it is absolutely not controversial. Now, the second rule as defined above in its most generic form might seem \"dangerous\" at first, but in practical terms if Asset Hub Root gets compromised and can access arbitrary sovereign accounts on Asset Hub and/or send arbitrary XCMs, the blast radius and potential damage to other chains is already so large that it is not relevantly impacted by this aliasing rule. A compromised system chain root would already be by itself an \"apocalypse\" scenario for the whole Polkadot Ecosystem. It's important noting that the aliasing rules above are a suggestion only, ultimately they are chain specific configuration. Therefore, each chain can tighten them to their own liking. For example, use stricter range of locations that Asset Hub can alias like: \"allow Asset Hub root to alias Ethereum locations\" - which enables support for Transact over the Ethereum Snowbridge (but doesn't support sibling parachain to Transact through Asset Hub), \"allow Asset Hub root to alias Kusama locations\" \"allow Asset Hub root to alias specific pallet or smart contract on Chain X\" Please note that Bridge Hub already does something similar today: Bridge Hub root is allowed/trusted to UniversalOrigin+DescendOrigin into any external location in order to impersonate/proxy external locations.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Trust assumptions","id":"697","title":"Trust assumptions"},"698":{"body":"A new parameter preserve_origin to be added to the InitiateAssetsTransfer XCM instruction that specifies if the original origin should be preserved or cleared. InitiateAssetsTransfer { destination: Location, assets: Vec, remote_fees: Option,\n+\tpreserve_origin: bool, remote_xcm: Xcm<()>,\n} This parameter is explicitly necessary because the instruction should be usable between any two chains regardless of their origin-aliasing trust relationship. Preserving the origin requires some level of trust, while clearing it works regardless of that relationship. Specifying preserve_origin: false will always work regardless of the configured alias filters of the involved chains.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » XCM InitiateAssetsTransfer instruction changes","id":"698","title":"XCM InitiateAssetsTransfer instruction changes"},"699":{"body":"Transact within the ecosytem: between two chains using an asset native to either one of them for paying for Transact, between two chains using an Asset Hub asset (e.g. USDT) for paying for Transact, Transact over Snowbridge (same for other bridges): user on Ethereum calls function in Parachain A on Polkadot, pays with ETH, user on ParaA on Polkdaot calls function on Ethereum, pays with ETH,","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Example scenarios","id":"699","title":"Example scenarios"},"7":{"body":"As the new instructions show, this RFC reframes the purpose of the Undefined variant of the AssetInstance enum. This RFC proposes to use the Undefined variant of a collection identified by an AssetId as a synonym of the collection itself. I.e., an asset Asset { id: , fun: Undefined } is considered an NFT representing the collection itself. As a singleton non-fungible instance is barely distinguishable from its collection, this convention shouldn't cause any problems. Thus, the AssetInstance docs must be updated accordingly in the implementations.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Repurposing AssetInstance::Undefined","id":"7","title":"Repurposing AssetInstance::Undefined"},"70":{"body":"","breadcrumbs":"RFC-0000: Feature Name Here » Performance, Ergonomics, and Compatibility","id":"70","title":"Performance, Ergonomics, and Compatibility"},"700":{"body":"In terms of ergonomics and user experience, this support for combining an asset transfer with a subsequent action (like Transact) is a net positive. In terms of performance, and privacy, this is neutral with no changes. In terms of security, the feature by itself is also neutral because it allows preserve_origin: false usage for operating with no extra trust assumptions. When wanting to support preserving origin, chains need to configure secure origin aliasing filters. The one suggested in this RFC should be the right choice for the majority of chains, but each chain will ultimately choose depending on their business model and logic (e.g. chain does not plan to integrate with Asset Hub). It is up to the individual chains to configure accordingly.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Drawbacks","id":"700","title":"Drawbacks"},"701":{"body":"Barriers should now allow AliasOrigin, DescendOrigin or ClearOrigin. Normally, XCM program builders should audit their programs and eliminate assumptions of \"no origin\" on remote side of this instruction. In this case, the InitiateAssetsTransfer has not been released yet, it will be part of XCMv5, and we can make this change part of the same XCMv5 so that there isn't even the possibility of someone in the wild having built XCM programs using this instruction on those wrong assumptions. The working assumption going forward is that the origin on the remote side can either be cleared or it can be the local origin's reanchored location. This assumption is in line with the current behavior of remote XCM programs sent over using pallet_xcm::send. The existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear origin same as before for compatibility reasons.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Testing, Security, and Privacy","id":"701","title":"Testing, Security, and Privacy"},"702":{"body":"","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Performance, Ergonomics, and Compatibility","id":"702","title":"Performance, Ergonomics, and Compatibility"},"703":{"body":"No impact.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Performance","id":"703","title":"Performance"},"704":{"body":"Improves ergonomics by allowing the local origin to operate on the remote chain even when the XCM program includes an asset transfer.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Ergonomics","id":"704","title":"Ergonomics"},"705":{"body":"At the executor-level this change is backwards and forwards compatible. Both types of programs can be executed on new and old versions of XCM with no changes in behavior. New version of the InitiateAssetsTransfer instruction acts same as before when used with preserve_origin: false. For using the new capabilities, the XCM builder has to verify that the involved chains have the required origin-aliasing filters configured and use some new version of Barriers aware of AliasOrigin as an allowed alternative to ClearOrigin. For compatibility reasons, this RFC proposes this mechanism be added as an enhancement to the yet unreleased InitiateAssetsTransfer instruction, thus eliminating possibilities of XCM logic breakages in the wild. Following the same logic, the existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear the origin same as before for compatibility reasons. Any one of DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions can be replaced with a InitiateAssetsTransfer instruction with or without origin aliasing, thus providing a clean and clear upgrade path for opting-in this new feature.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Compatibility","id":"705","title":"Compatibility"},"706":{"body":"RFC: InitiateAssetsTransfer for complex asset transfers RFC: Descend XCM origin instead of clearing it where possible","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Prior Art and References","id":"706","title":"Prior Art and References"},"707":{"body":"None","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Unresolved Questions","id":"707","title":"Unresolved Questions"},"708":{"body":"","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Future Directions and Related Material","id":"708","title":"Future Directions and Related Material"},"709":{"body":"(source) Table of Contents RFC-0000: Validator Rewards Summary Motivation Stakeholders Logic Categories Collection Messages Rewards compoutation Strategies Explanation Backing Approvals Availability redistribution Tit-for-tat Concerns: Drawbacks, Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Synthetic parachain flag Start Date Date of initial proposal Description Rewards protocol for Polkadot validators Authors Jeff Burdges, ...","breadcrumbs":"RFC-0000: Validator Rewards » RFC-0000: Validator Rewards","id":"709","title":"RFC-0000: Validator Rewards"},"71":{"body":"This proposal lightens the load on the relay chain and is thus in general beneficial for the performance of the network, this is achieved by the following: Code upgrades are still propagated to all validators, but only once, not twice (First statements, then via the containing relay chain block). Code upgrades are only communicated to validators and other nodes which are interested, not any full node as it has been before. Relay chain block space is preserved. Previously we could only do one runtime upgrade per relay chain block, occupying almost all of the blockspace. Signalling an upgrade no longer contains the upgrade, hence if we need to push back on an upgrade for whatever reason, no network bandwidth and core time gets wasted because of this.","breadcrumbs":"RFC-0000: Feature Name Here » Performance","id":"71","title":"Performance"},"710":{"body":"An off-chain approximation protocol should assign rewards based upon the approvals and availability work done by validators. All validators track which approval votes they actually use, reporting the aggregate, after which an on-chain median computation gives a good approximation under byzantine assumptions. Approval checkers report aggregate information about which availability chunks they use too, but in availability we need a tit-for-tat game to enforce honesty, because approval committees could often bias results thanks to their small size.","breadcrumbs":"RFC-0000: Validator Rewards » Summary","id":"710","title":"Summary"},"711":{"body":"We want all polkadot subsystems be profitable for validataors, because otherwise operators might profit from running modified code. In particular, almost all rewards in Kusama/Polkadot should come from work done securing parachains, primarily approval checking, but also backing, availability, and support of XCMP. Among these task, our highest priorities must be approval checks, which ensure soundness, and sending availability chunks to approval checkers. We prove backers must be paid strictly less than approval checkers. At present though, validators' rewards have relatively little relationship to validators operating costs, in terms of bandwidth and CPU time. Worse, polkadot's scaling makes us particular vulnerable \"no-shows\" caused by validators skipping their approval checks. We're particularly concernned about hardware specks impact upon the number of parachain cores. We've requested relatively low spec machines so far, only four physical CPU cores, although some run even lower specs like only two physical CPU cores. Alone, rewards cannot fix our low speced validator problem, but rewards and outreach together should far more impact than either alone. In future, we'll further increase validator spec requirements, which directly improve polkadot's throughput, and which repeats this dynamic of purging underspeced nodes, except outreach becomes more important because de facto too many slow validators can \"out vote\" the faster ones","breadcrumbs":"RFC-0000: Validator Rewards » Motivation","id":"711","title":"Motivation"},"712":{"body":"We alter the validators rewards protocol, but with negligable impact upon rewards for honest validators who comply with hardware and bandwidth recommendations. We shall still reward participation in relay chain concensus of course, which de facto means block production but not finality, but these current reward levels shall wind up greatly reduced. Any validators who manipulate block rewards now could lose rewards here, simply because of rewards being shifted from block production to availability, but this sounds desirable. We've discussed roughly this rewards protocol in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF and https://github.com/paritytech/polkadot-sdk/issues/1811 as well as related topics like https://github.com/paritytech/polkadot-sdk/issues/5122","breadcrumbs":"RFC-0000: Validator Rewards » Stakeholders","id":"712","title":"Stakeholders"},"713":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Logic","id":"713","title":"Logic"},"714":{"body":"We alter the current rewards scheme by reducing to roughly these proportions of total rewards: 15-20% - Relay chain block production and uncle logic 5% - Rnything else related to relay chain finality, primarily beefy proving, but maybe other tasts exist. Any existing rewards for on-chain validity statements would only cover backers, so those rewards must be removed. We add roughly these proportions of total rewards covering parachain work: 70-75% - approval and backing validity checks, with the backing rewards being required to be less than approval rewards. 5-10% - Availability redistribution from availability providers to approval checkers. We do not reward for availability distribution from backers to availability providers.","breadcrumbs":"RFC-0000: Validator Rewards » Categories","id":"714","title":"Categories"},"715":{"body":"We track this data for each candidate during the approvals process: /// Our subjective record of out availability transfers for this candidate.\nCandidateRewards { /// Anyone who backed this parablock backers: [AuthorityId; NumBackers], /// Anyone who sent us chunks for this candidate downloaded_from: HashMap, /// Anyone to whome we sent chunks for this candidate uploaded_to: HashMap,\n} We no longer require this data during disputes. After we approve a relay chain block, then we collect all its CandidateRewards into an ApprovalsTally, with one ApprovalTallyRecord for each validator. In this, we compute approval_usages from the final run of the approvals loop, plus 0.8 for each backer. /// Our subjective record of what we used from, and provided to, all other validators on the finalized chain\npub struct ApprovalsTally(Vec); /// Our subjective record of what we used from, and provided to, all one other validators on the finalized chain\npub struct ApprovalTallyLine { /// Approvals by this validator which our approvals gadget used in marking candidates approved. approval_usages: u32, /// Availability chunks we downloaded from this validator for our approval checks we used. used_downloads: u32, /// Availability chunks we uploaded to this validator which whose approval checks we used. used_uploads: u32,\n} At finality we sum these ApprovalsTally for one for the whole epoch so far, into another ApprovalsTally. We can optionally sum them earlier at chain heads, but this requires mutablity.","breadcrumbs":"RFC-0000: Validator Rewards » Collection","id":"715","title":"Collection"},"716":{"body":"After the epoch is finalized, we share the first two lines of its ApprovalTally. /// Our subjective record of what we used from some other validator on the finalized chain\npub struct ApprovalTallyMessageLine { /// Approvals by this validator which our approvals gadget used in marking candidates approved. approval_usages: u32, /// Availability chunks we downloaded from this validator for our approval checks we used. used_downloads: u32,\n} /// Our subjective record of what we used from all other validators on the finalized chain\npub struct ApprovalsTallyMessage(Vec);","breadcrumbs":"RFC-0000: Validator Rewards » Messages","id":"716","title":"Messages"},"717":{"body":"We compute the approvals rewards by taking the median of the approval_usages fields for each validator across all validators ApprovalsTallyMessages. let mut approval_usages_medians = Vec::new(); for i in 0..num_validators { let mut v: Vec = approvals_tally_messages.iter().map(|atm| atm.0[i].approval_usages); v.sort(); approval_usages_medians.push(v[num_validators/2]);\n} Assuming more than 50% honersty, these median tell us how many approval votes form each validator We re-weight the used_downloads from the ith validator by their median times their expected f+1 chunks and divided by how many chunks downloads they claimed, and sum them #[cfg(offchain)]\nlet mut my_missing_uploads = my_approvals_tally.iter().map(|l| l.used_uploads).collect();\nlet mut reweighted_total_used_downloads = vec[0u64; num_validators];\nfor (mmu,atm) in my_missing_uploads.iter_mut().zip(approvals_tally_messages) { let d = atm.0.iter().map(|l| l.used_downloads).sum(); for i in 0..num_validators { let atm_from_i = approval_usages_medians[i] * (f+1) / d; #[cfg(offchain)] if i == me { mmu -= atm_from_i }; reweighted_total_used_downloads[i] += atm_from_i; }\n} We distribute rewards on-chain using approval_usages_medians and reweighted_total_used_downloads. Approval checkers could later change from who they download chunks using my_missing_uploads.","breadcrumbs":"RFC-0000: Validator Rewards » Rewards compoutation","id":"717","title":"Rewards compoutation"},"718":{"body":"In theory, validators could adopt whatever strategy they like to penalize validators who stiff them on availability redistribution rewards, except they should not stiff back, only choose other availability providers. We discuss one good strategy below, but initially this could go unimplemented.","breadcrumbs":"RFC-0000: Validator Rewards » Strategies","id":"718","title":"Strategies"},"719":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Explanation","id":"719","title":"Explanation"},"72":{"body":"End users are only affected by better performance and more stable block times. Parachains will need to implement the introduced request/response protocol and adapt to the new signalling mechanism via an UMP message, instead of sending the code upgrade directly. For parachain operators we should emit events on initiated runtime upgrade and each block reporting the current counter and how many blocks to go until the upgrade gets passed to pre-checking. This is especially important for on-demand chains or bulk users not occupying a full core. Further more that behaviour of requiring multiple blocks to fully initiate a runtime upgrade needs to be well documented.","breadcrumbs":"RFC-0000: Feature Name Here » Ergonomics","id":"72","title":"Ergonomics"},"720":{"body":"Polkadot's efficency creates subtle liveness concerns: Anytime one node cannot perform one of its approval checks then Polkadot loses in expectation 3.25 approval checks, or 0.10833 parablocks. This makes back pressure essential. We cannot throttle approval checks securely either, so reactive off-chain back pressure only makes sense during or before the backing phase. In other words, if nodes feel overworked themselves, or perhaps beleive others to be, then they should drop backing checks, never approval checks. It follows backing work must be rewarded less well and less reliably than approvals, as otherwise validators could benefit from behavior that harms the network. We propose that one backing statement be rewarded at 80% of one approval statement, so backers earn only 80% of what approval checkers earn. We omit rewards for availability distribution, so backers spend more on bandwidth too. Approval checkers always fetch chunks first from backers though, so good backers earn roughly 7% there, meaning backing checks earn roughly 13% less than approval checks. We should lower this 80% if we ever increase availability redistribution rewards. Although imperfect, we believe this simplifies implementation, and provides robustness against mistakes elsewhere, including by governance mistakes, but incurs minimal risk. In principle, backer might not distribute systemic chunks, but approval checkers fetch systemic chunks from backers first anyways, so likely this yields negligable gains. As always we require that backers' rewards covers their operational costs plus some profit, but approval checks must be more profitable.","breadcrumbs":"RFC-0000: Validator Rewards » Backing","id":"720","title":"Backing"},"721":{"body":"In polkadot, all validators run an approval assignment loop for each candidate, in which the validator listens to other approval checkers assignments and approval statements/votes, with which it marks checkers no-show or done, and marks candidates approved. Also, this loop determines and announces validators' own approval checker assignments. Any validator should always conclude whatever approval checks it begins, but our approval assignment loop ignore some approval checks, either because they were announced too soon or because an earlier no-show delivered its approval vote before the final approval. We say a validator $u$ uses an approval vote by a validator $v$ on a candidate $c$ if the approval assignments loop by $u$ counted the vote by $v$ towards approving the candidate $c$. We should not rewards votes announced too soon, so we unavoidably omit rewards for some honest no-show replacements too. We expect the 80% discount for backing covers these losses, so approval checks remain more profitable than backing. We propose a simple approximate solution based upon computing medians across validators for used votes. In an epoch $e$, each validator $u$ counts of the number $\\alpha_{u,v}$ of votes they used from each validator $v$, including themselves. Any time a validator marks a candidate approved, they increment these counts appropriately. After epoch $e$'s last block gets finalized, all validators of epoch $e$ submit an approvals tally message ApprovalsTallyMessage that reveals their number $\\alpha_{u,v}$ of useful approvals they saw from each validator $v$ on candidates that became available in epoch $n$. We do not send $\\alpha_{u,u}$ for tit-for-tat reasons discussed below, not for bias concerns. We record these approvals tally messages on-chain. After some delay, we compute on-chain the median $\\alpha_v := \\textrm{median} { \\alpha_{u,v} : u }$ used approvals statements for each validator $v$. As discussed in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF we could compute these medians using the on-line algorithm if substrate had a nice priority queue. We never achieve true consensus on approval checkers and their approval votes. Yet, our approval assignment loop gives a rough concensus, under our Byzantine assumption and some synchrony assumption. It then follows that miss-reporting by malicious validators should not appreciably alter the median $\\alpha_v$ and hence rewards. We never tally used approval assignments to candidate equivocations or other forks. Any validator should always conclude whatever approval checks it begins, even on other forks, but we expect relay chain equivocations should be vanishingly rare, and sassafras should make forks uncommon.","breadcrumbs":"RFC-0000: Validator Rewards » Approvals","id":"721","title":"Approvals"},"722":{"body":"As approval checkers could easily perform useless checks, we shall reward availability providers for the availability chunks they provide that resulted in useful approval checks. We enforce honesty using a tit-for-tat mechanism because chunk transfers are inherently subjective. An approval checker reconstructs the full parachain block by downloading distinct $f+1$ chunks from other validators, where at most $f$ validators are byzantine, out of the $n \\ge 3 f + 1$ total validators. In downloading chunks, validators prefer the $f+1$ systemic chunks over the non-systemic chunks, and prefer fetching from validators who already voted valid, like backing checkers. It follows some validators should recieve credit for more than one chunk per candidate. We expect a validator $v$ has actually performed more approval checks $\\omega_v$ than the median $\\alpha_v$ for which they actually received credit. In fact, approval checkers even ignore some of their own approval checks, meaning $\\alpha_{v,v} \\le \\omega_v$ too. Alongside approvals count for epoch $e$, approval checker $v$ computes the counts $\\beta_{u,v}$ of the number of chunks they downloaded from each availability provider $u$, excluding themselves, for which they percieve the approval check turned out useful, meaning their own approval counts in $\\alpha_{v,v}$. Approval checkers publish $\\beta_{u,v}$ alongside $\\alpha_{u,v}$ in the approvals tally message ApprovalsTallyMessage. We originally proposed include the self availability usage $\\beta_{v,v}$ here, but this should not matter, and excluding simplifies the code. Symmetrically, availability provider $u$ computes the counts $\\gamma_{u,v}$ of the number of chunks they uploaded to each approval checker $v$, again including themselves, again for which they percieve the approval check turned out useful. Availability provider $u$ never reveal its $\\gamma_{u,v}$ however. At this point, $\\alpha_v$, $\\alpha_{v,v}$, and $\\alpha_{u,v}$ all potentially differ. We established consensus upon $\\alpha_v$ above however, with which we avoid approval checkers printing unearned availability provider rewards: After receiving \"all\" pairs $(\\alpha_{u,v},\\beta_{u,v})$, validator $w$ re-weights the $\\beta_{u,v}$ and their own $\\gamma_{w,v}$. $$ \\begin{aligned} \\beta\\prime_{w,v} &= {(f+1) \\alpha_v \\over \\sum_u \\beta_{u,v}} \\beta_{w,v} \\ \\gamma\\prime_{w,v} &= {(f+1) \\alpha_w \\over \\sum_v \\gamma_{w,v}} \\gamma_{w,v} \\ \\end{aligned} $$ At this point, we compute $\\beta\\prime_w = \\sum_v \\beta\\prime_{w,v}$ on-chain for each $w$ and reward $w$ proportionally.","breadcrumbs":"RFC-0000: Validator Rewards » Availability redistribution","id":"722","title":"Availability redistribution"},"723":{"body":"We employ a tit-for-tat strategy to punish validators who lie about from whome they obtain availability chunks. We only alter validators future choices in from whom they obtain availability chunks, and never punish by lying ourselves, so nothing here breaks polkadot, but not having roughly this strategy enables cheating. An availability provider $w$ defines $\\delta\\prime_{w,v} := \\gamma\\prime_{w,v} - \\beta\\prime_{w,v}$ to be the re-weighted number of chunks by which $v$ stiffed $w$. Now $w$ increments their cumulative stiffing perception $\\eta_{w,v}$ from $v$ by the value $\\delta\\prime_{w,v}$, so $\\eta_{w,v} \\mathrel{+}= \\delta\\prime_{w,v}$ In future, anytime $w$ seeks chunks in reconstruction $w$ skips $v$ proportional to $\\eta_{w,v} / \\sum_u \\eta_{w,u}$, with each skip reducing $\\eta_{w,u}$ by 1. We expect honest accedental availability stiffs have only small $\\delta\\prime_{w,v}$, so they clear out quickly, but intentional skips add up more quickly. We keep $\\gamma_{w,v}$ and $\\alpha_{u,u}$ secret so that approval checkers cannot really know others stiffing perceptions, although $\\alpha_{u,v}$ leaks some relevant information. We expect this secrecy keeps skips secret and thus prevents the tit-for-tat escalating beyond one round, which hopefully creates a desirable Nash equilibrium. We favor skiping systematic chunks to reduce reconstructon costs, so we face costs when skipping them. We could however fetch systematic chunks from availability providers as well as backers, or even other approval checkers, so this might not become problematic in practice.","breadcrumbs":"RFC-0000: Validator Rewards » Tit-for-tat","id":"723","title":"Tit-for-tat"},"724":{"body":"We do not pay backers individually for availability distribution per se. We could only do so by including this information into the availability bitfields, which complicates on-chain computation. Also, if one of the two backers does not distribute then the availability core should remain occupied longer, meaning the lazy backer loses some rewards too. It's likely future protocol improbvements change this, so we should monitor for lazy backers outside the rewards system. We discuss approvals being considered by the tit-for-tat in earlier drafts. An adversary who successfuly manipulates the rewards median votes would've alraedy violated polkadot's security assumptions though, which requires a hard fork and correcting the dot allocation. Incorrect report wrong approval_usages remain interesting statistics though. Adversarial validators could manipulates their availability votes though, even without being a supermajority. If they still download honestly, then this costs them more rewards than they earn. We do not prevent validators from preferentially obtaining their pieces from their friends though. We should analyze, or at least observe, the long-term consequences. A priori, whale nominator's validators could stiff validators but then rotate their validators quickly enough so that they never suffered being skipped back. We discuss several possible solution, and their difficulties, under \"Rob's nominator-wise skipping\" in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF but overall less seems like more here. Also frequent validator rotation could be penalized elsewhere.","breadcrumbs":"RFC-0000: Validator Rewards » Concerns: Drawbacks, Testing, Security, and Privacy","id":"724","title":"Concerns: Drawbacks, Testing, Security, and Privacy"},"725":{"body":"We operate off-chain except for final rewards votes and median tallies. We expect lower overhead rewards protocols would lack information, thereby admitting easier cheating. Initially, we designed the ELVES approval gadget to allow on-chain operation, in part for rewards computation, but doing so looks expensive. Also, on-chain rewards computaiton remains only an approximation too, but could even be biased more easily than our off-chain protocol presented here. We alraedy teach validators about missed parachain blocks, but we'll teach approval checking more going forwards, because current efforts focus more upon backing. JAM's block exports should not complicate availability rewards, but could impact some alternative schemes.","breadcrumbs":"RFC-0000: Validator Rewards » Performance, Ergonomics, and Compatibility","id":"725","title":"Performance, Ergonomics, and Compatibility"},"726":{"body":"None","breadcrumbs":"RFC-0000: Validator Rewards » Prior Art and References","id":"726","title":"Prior Art and References"},"727":{"body":"Provide specific questions to discuss and address before the RFC is voted on by the Fellowship. This should include, for example, alternatives to aspects of the proposed design where the appropriate trade-off to make is unclear.","breadcrumbs":"RFC-0000: Validator Rewards » Unresolved Questions","id":"727","title":"Unresolved Questions"},"728":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Future Directions and Related Material","id":"728","title":"Future Directions and Related Material"},"729":{"body":"Any rewards protocol could simply be \"out voted\" by too many slow validators: An increase the number of parachain cores increases more workload, but this creates no-shows if too few validators could handle this workload. We could add a synthetic parachain flag, only settable by governance, which treats no-shows as positive approval votes for that parachain, but without adding rewards. We should never enable this for real parachains, only for synthetic ones like gluttons. We should not enable the synthetic parachain flag long-term even for gluttonsm, because validators could easily modify their code. Yet, synthetic approval checks might enable pushing the hardware upgrades more agressively over the short-term.","breadcrumbs":"RFC-0000: Validator Rewards » Synthetic parachain flag","id":"729","title":"Synthetic parachain flag"},"73":{"body":"We will continue to support the old mechanism for code upgrades for a while, but will start to impose stricter limits over time, with the number of registered parachains going up. With those limits in place parachains not migrating to the new scheme might be having a harder time upgrading and will miss more blocks. I guess we can be lenient for a while still, so the upgrade path for parachains should be rather smooth. In total the protocol changes we need are: For validators and collators: New request/response protocol for fetching PVF data from collators and validators. New UMP message type for signalling a runtime upgrade. Only for validators: New runtime API for determining to be enacted code upgrades. Different behaviour of bitfields (only sign a 1 bit, if validator has chunk + \"hot\" PVF). Altered behaviour in availability-distribution: Fetch missing PVFS.","breadcrumbs":"RFC-0000: Feature Name Here » Compatibility","id":"73","title":"Compatibility"},"730":{"body":"(source) Table of Contents RFC-0004: Remove the host-side runtime memory allocator Summary Motivation Stakeholders Explanation New host functions Other changes Drawbacks Prior Art Unresolved Questions Future Possibilities Start Date 2023-07-04 Description Update the runtime-host interface to no longer make use of a host-side allocator Authors Pierre Krieger","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » RFC-0004: Remove the host-side runtime memory allocator","id":"730","title":"RFC-0004: Remove the host-side runtime memory allocator"},"731":{"body":"Update the runtime-host interface to no longer make use of a host-side allocator.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Summary","id":"731","title":"Summary"},"732":{"body":"The heap allocation of the runtime is currently controlled by the host using a memory allocator on the host side. The API of many host functions consists in allocating a buffer. For example, when calling ext_hashing_twox_256_version_1, the host allocates a 32 bytes buffer using the host allocator, and returns a pointer to this buffer to the runtime. The runtime later has to call ext_allocator_free_version_1 on this pointer in order to free the buffer. Even though no benchmark has been done, it is pretty obvious that this design is very inefficient. To continue with the example of ext_hashing_twox_256_version_1, it would be more efficient to instead write the output hash to a buffer that was allocated by the runtime on its stack and passed by pointer to the function. Allocating a buffer on the stack in the worst case scenario simply consists in decreasing a number, and in the best case scenario is free. Doing so would save many Wasm memory reads and writes by the allocator, and would save a function call to ext_allocator_free_version_1. Furthermore, the existence of the host-side allocator has become questionable over time. It is implemented in a very naive way, and for determinism and backwards compatibility reasons it needs to be implemented exactly identically in every client implementation. Runtimes make substantial use of heap memory allocations, and each allocation needs to go twice through the runtime <-> host boundary (once for allocating and once for freeing). Moving the allocator to the runtime side, while it would increase the size of the runtime, would be a good idea. But before the host-side allocator can be deprecated, all the host functions that make use of it need to be updated to not use it.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Motivation","id":"732","title":"Motivation"},"733":{"body":"No attempt was made at convincing stakeholders.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Stakeholders","id":"733","title":"Stakeholders"},"734":{"body":"","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Explanation","id":"734","title":"Explanation"},"735":{"body":"This section contains a list of new host functions to introduce. (func $ext_storage_read_version_2 (param $key i64) (param $value_out i64) (param $offset i32) (result i64))\n(func $ext_default_child_storage_read_version_2 (param $child_storage_key i64) (param $key i64) (param $value_out i64) (param $offset i32) (result i64)) The signature and behaviour of ext_storage_read_version_2 and ext_default_child_storage_read_version_2 is identical to their version 1 counterparts, but the return value has a different meaning. The new functions directly return the number of bytes that were written in the value_out buffer. If the entry doesn't exist, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in value_out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. The runtime execution stops with an error if value_out is outside of the range of the memory of the virtual machine, even if the size of the buffer is 0 or if the amount of data to write would be 0 bytes. (func $ext_storage_next_key_version_2 (param $key i64) (param $out i64) (return i32))\n(func $ext_default_child_storage_next_key_version_2 (param $child_storage_key i64) (param $key i64) (param $out i64) (return i32)) The behaviour of these functions is identical to their version 1 counterparts. Instead of allocating a buffer, writing the next key to it, and returning a pointer to it, the new version of these functions accepts an out parameter containing a pointer-size to the memory location where the host writes the output. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. These functions return the size, in bytes, of the next key, or 0 if there is no next key. If the size of the next key is larger than the buffer in out, the bytes of the key that fit the buffer are written to out and any extra byte that doesn't fit is discarded. Some notes: It is never possible for the next key to be an empty buffer, because an empty key has no preceding key. For this reason, a return value of 0 can unambiguously be used to indicate the lack of next key. The ext_storage_next_key_version_2 and ext_default_child_storage_next_key_version_2 are typically used in order to enumerate keys that starts with a certain prefix. Given that storage keys are constructed by concatenating hashes, the runtime is expected to know the size of the next key and can allocate a buffer that can fit said key. When the next key doesn't belong to the desired prefix, it might not fit the buffer, but given that the start of the key is written to the buffer anyway this can be detected in order to avoid calling the function a second time with a larger buffer. (func $ext_hashing_keccak_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_keccak_512_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_sha2_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_blake2_128_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_blake2_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_64_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_128_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_256_version_2 (param $data i64) (param $out i32))\n(func $ext_trie_blake2_256_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_blake2_256_ordered_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_keccak_256_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_keccak_256_ordered_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_default_child_storage_root_version_3 (param $child_storage_key i64) (param $out i32))\n(func $ext_crypto_ed25519_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32))\n(func $ext_crypto_sr25519_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32) (return i32))\n(func $ext_crypto_ecdsa_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32) (return i32)) The behaviour of these functions is identical to their version 1 or version 2 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new version of these functions accepts an out parameter containing the memory location where the host writes the output. The output is always of a size known at compilation time. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. (func $ext_default_child_storage_root_version_3 (param $child_storage_key i64) (param $out i32))\n(func $ext_storage_root_version_3 (param $out i32)) The behaviour of these functions is identical to their version 1 and version 2 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new versions of these functions accepts an out parameter containing the memory location where the host writes the output. The output is always of a size known at compilation time. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. I have taken the liberty to take the version 1 of these functions as a base rather than the version 2, as a PPP deprecating the version 2 of these functions has previously been accepted: https://github.com/w3f/PPPs/pull/6 . (func $ext_storage_clear_prefix_version_3 (param $prefix i64) (param $limit i64) (param $removed_count_out i32) (return i32))\n(func $ext_default_child_storage_clear_prefix_version_3 (param $child_storage_key i64) (param $prefix i64) (param $limit i64) (param $removed_count_out i32) (return i32))\n(func $ext_default_child_storage_kill_version_4 (param $child_storage_key i64) (param $limit i64) (param $removed_count_out i32) (return i32)) The behaviour of these functions is identical to their version 2 and 3 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the version 3 and 4 of these functions accepts a removed_count_out parameter containing the memory location to a 8 bytes buffer where the host writes the number of keys that were removed in little endian. The runtime execution stops with an error if removed_count_out is outside of the range of the memory of the virtual machine. The functions return 1 to indicate that there are keys remaining, and 0 to indicate that all keys have been removed. Note that there is an alternative proposal to add new host functions with the same names: https://github.com/w3f/PPPs/pull/7 . This alternative doesn't conflict with this one except for the version number. One proposal or the other will have to use versions 4 and 5 rather than 3 and 4. (func $ext_crypto_ed25519_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\n(func $ext_crypto_sr25519_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\nfunc $ext_crypto_ecdsa_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\n(func $ext_crypto_ecdsa_sign_prehashed_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i64)) The behaviour of these functions is identical to their version 1 counterparts. The new versions of these functions accept an out parameter containing the memory location where the host writes the signature. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. The signatures are always of a size known at compilation time. On success, these functions return 0. If the public key can't be found in the keystore, these functions return 1 and do not write anything to out. Note that the return value is 0 on success and 1 on failure, while the previous version of these functions write 1 on success (as it represents a SCALE-encoded Some) and 0 on failure (as it represents a SCALE-encoded None). Returning 0 on success and non-zero on failure is consistent with common practices in the C programming language and is less surprising than the opposite. (func $ext_crypto_secp256k1_ecdsa_recover_version_3 (param $sig i32) (param $msg i32) (param $out i32) (return i64))\n(func $ext_crypto_secp256k1_ecdsa_recover_compressed_version_3 (param $sig i32) (param $msg i32) (param $out i32) (return i64)) The behaviour of these functions is identical to their version 2 counterparts. The new versions of these functions accept an out parameter containing the memory location where the host writes the signature. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. The signatures are always of a size known at compilation time. On success, these functions return 0. On failure, these functions return a non-zero value and do not write anything to out. The non-zero value written on failure is: 1: incorrect value of R or S 2: incorrect value of V 3: invalid signature These values are equal to the values returned on error by the version 2 (see https://spec.polkadot.network/chap-host-api#defn-ecdsa-verify-error ), but incremented by 1 in order to reserve 0 for success. (func $ext_crypto_ed25519_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_ed25519_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32))\n(func $ext_crypto_sr25519_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_sr25519_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32))\n(func $ext_crypto_ecdsa_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_ecdsa_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32)) The functions superceded the ext_crypto_ed25519_public_key_version_1, ext_crypto_sr25519_public_key_version_1, and ext_crypto_ecdsa_public_key_version_1 host functions. Instead of calling ext_crypto_ed25519_public_key_version_1 in order to obtain the list of all keys at once, the runtime should instead call ext_crypto_ed25519_num_public_keys_version_1 in order to obtain the number of public keys available, then ext_crypto_ed25519_public_key_version_2 repeatedly. The ext_crypto_ed25519_public_key_version_2 function writes the public key of the given key_index to the memory location designated by out. The key_index must be between 0 (included) and n (excluded), where n is the value returned by ext_crypto_ed25519_num_public_keys_version_1. Execution must trap if n is out of range. The same explanations apply for ext_crypto_sr25519_public_key_version_1 and ext_crypto_ecdsa_public_key_version_1. Host implementers should be aware that the list of public keys (including their ordering) must not change while the runtime is running. This is most likely done by copying the list of all available keys either at the start of the execution or the first time the list is accessed. (func $ext_offchain_http_request_start_version_2 (param $method i64) (param $uri i64) (param $meta i64) (result i32)) The behaviour of this function is identical to its version 1 counterpart. Instead of allocating a buffer, writing the request identifier in it, and returning a pointer to it, the version 2 of this function simply returns the newly-assigned identifier to the HTTP request. On failure, this function returns -1. An identifier of -1 is invalid and is reserved to indicate failure. (func $ext_offchain_http_request_write_body_version_2 (param $method i64) (param $uri i64) (param $meta i64) (result i32))\n(func $ext_offchain_http_response_read_body_version_2 (param $request_id i32) (param $buffer i64) (param $deadline i64) (result i64)) The behaviour of these functions is identical to their version 1 counterpart. Instead of allocating a buffer, writing two bytes in it, and returning a pointer to it, the new version of these functions simply indicates what happened: For ext_offchain_http_request_write_body_version_2, 0 on success. For ext_offchain_http_response_read_body_version_2, 0 or a non-zero number of bytes on success. -1 if the deadline was reached. -2 if there was an I/O error while processing the request. -3 if the identifier of the request is invalid. These values are equal to the values returned on error by the version 1 (see https://spec.polkadot.network/chap-host-api#defn-http-error ), but tweaked in order to reserve positive numbers for success. When it comes to ext_offchain_http_response_read_body_version_2, the host implementers must not read too much data at once in order to not create ambiguity in the returned value. Given that the size of the buffer is always inferior or equal to 4 GiB, this is not a problem. (func $ext_offchain_http_response_wait_version_2 (param $ids i64) (param $deadline i64) (param $out i32)) The behaviour of this function is identical to its version 1 counterpart. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new version of this function accepts an out parameter containing the memory location where the host writes the output. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. The encoding of the response code is also modified compared to its version 1 counterpart and each response code now encodes to 4 little endian bytes as described below: 100-999: the request has finished with the given HTTP status code. -1 if the deadline was reached. -2 if there was an I/O error while processing the request. -3 if the identifier of the request is invalid. The buffer passed to out must always have a size of 4 * n where n is the number of elements in the ids. (func $ext_offchain_http_response_header_name_version_1 (param $request_id i32) (param $header_index i32) (param $out i64) (result i64))\n(func $ext_offchain_http_response_header_value_version_1 (param $request_id i32) (param $header_index i32) (param $out i64) (result i64)) These functions supercede the ext_offchain_http_response_headers_version_1 host function. Contrary to ext_offchain_http_response_headers_version_1, only one header indicated by header_index can be read at a time. Instead of calling ext_offchain_http_response_headers_version_1 once, the runtime should call ext_offchain_http_response_header_name_version_1 and ext_offchain_http_response_header_value_version_1 multiple times with an increasing header_index, until a value of -1 is returned. These functions accept an out parameter containing a pointer-size to the memory location where the header name or value should be written. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. These functions return the size, in bytes, of the header name or header value. If request doesn't exist or is in an invalid state (as documented for ext_offchain_http_response_headers_version_1) or the header_index is out of range, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. If the buffer in out is too small to fit the entire header name of value, only the bytes that fit are written and the rest are discarded. (func $ext_offchain_submit_transaction_version_2 (param $data i64) (return i32))\n(func $ext_offchain_http_request_add_header_version_2 (param $request_id i32) (param $name i64) (param $value i64) (result i32)) Instead of allocating a buffer, writing 1 or 0 in it, and returning a pointer to it, the version 2 of these functions return 0 or 1, where 0 indicates success and 1 indicates failure. The runtime must interpret any non-0 value as failure, but the client must always return 1 in case of failure. (func $ext_offchain_local_storage_read_version_1 (param $kind i32) (param $key i64) (param $value_out i64) (param $offset i32) (result i64)) This function supercedes the ext_offchain_local_storage_get_version_1 host function, and uses an API and logic similar to ext_storage_read_version_2. It reads the offchain local storage key indicated by kind and key starting at the byte indicated by offset, and writes the value to the pointer-size indicated by value_out. The function returns the number of bytes that were written in the value_out buffer. If the entry doesn't exist, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in value_out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. The runtime execution stops with an error if value_out is outside of the range of the memory of the virtual machine, even if the size of the buffer is 0 or if the amount of data to write would be 0 bytes. (func $ext_offchain_network_peer_id_version_1 (param $out i64)) This function writes the PeerId of the local node to the memory location indicated by out. A PeerId is always 38 bytes long. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. (func $ext_input_size_version_1 (return i64))\n(func $ext_input_read_version_1 (param $offset i64) (param $out i64)) When a runtime function is called, the host uses the allocator to allocate memory within the runtime where to write some input data. These two new host functions provide an alternative way to access the input that doesn't make use of the allocator. The ext_input_size_version_1 host function returns the size in bytes of the input data. The ext_input_read_version_1 host function copies some data from the input data to the memory of the runtime. The offset parameter indicates the offset within the input data where to start copying, and must be inferior or equal to the value returned by ext_input_size_version_1. The out parameter is a pointer-size containing the buffer where to write to. The runtime execution stops with an error if offset is strictly superior to the size of the input data, or if out is outside of the range of the memory of the virtual machine, even if the amount of data to copy would be 0 bytes.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » New host functions","id":"735","title":"New host functions"},"736":{"body":"In addition to the new host functions, this RFC proposes two changes to the runtime-host interface: The following function signature is now also accepted for runtime entry points: (func (result i64)). Runtimes no longer need to expose a constant named __heap_base. All the host functions that are being superceded by new host functions are now considered deprecated and should no longer be used. The following other host functions are similarly also considered deprecated: ext_storage_get_version_1 ext_default_child_storage_get_version_1 ext_allocator_malloc_version_1 ext_allocator_free_version_1 ext_offchain_network_state_version_1","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Other changes","id":"736","title":"Other changes"},"737":{"body":"This RFC might be difficult to implement in Substrate due to the internal code design. It is not clear to the author of this RFC how difficult it would be.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Drawbacks","id":"737","title":"Drawbacks"},"738":{"body":"The API of these new functions was heavily inspired by API used by the C programming language.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Prior Art","id":"738","title":"Prior Art"},"739":{"body":"The changes in this RFC would need to be benchmarked. This involves implementing the RFC and measuring the speed difference. It is expected that most host functions are faster or equal speed to their deprecated counterparts, with the following exceptions: ext_input_size_version_1/ext_input_read_version_1 is inherently slower than obtaining a buffer with the entire data due to the two extra function calls and the extra copying. However, given that this only happens once per runtime call, the cost is expected to be negligible. The ext_crypto_*_public_keys, ext_offchain_network_state, and ext_offchain_http_* host functions are likely slightly slower than their deprecated counterparts, but given that they are used only in offchain workers this is acceptable. It is unclear how replacing ext_storage_get with ext_storage_read and ext_default_child_storage_get with ext_default_child_storage_read will impact performances. It is unclear how the changes to ext_storage_next_key and ext_default_child_storage_next_key will impact performances.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Unresolved Questions","id":"739","title":"Unresolved Questions"},"74":{"body":"Off-chain runtime upgrades have been discussed before, the architecture described here is simpler though as it piggybacks on already existing features, namely: availability-distribution: No separate I have code messages anymore. Existing pre-checking. https://github.com/paritytech/polkadot-sdk/issues/971","breadcrumbs":"RFC-0000: Feature Name Here » Prior Art and References","id":"74","title":"Prior Art and References"},"740":{"body":"After this RFC, we can remove from the source code of the host the allocator altogether in a future version, by removing support for all the deprecated host functions. This would remove the possibility to synchronize older blocks, which is probably controversial and requires a some preparations that are out of scope of this RFC.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Future Possibilities","id":"740","title":"Future Possibilities"},"741":{"body":"(source) Table of Contents RFC-0006: Dynamic Pricing for Bulk Coretime Sales Summary Motivation Requirements Stakeholders Explanation Overview Parameters Function Pseudo-code Properties of the Curve Example Configurations Drawbacks Prior Art and References Future Possibilities References Start Date July 09, 2023 Description A dynamic pricing model to adapt the regular price for bulk coretime sales Authors Tommi Enenkel (Alice und Bob) License MIT","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » RFC-0006: Dynamic Pricing for Bulk Coretime Sales","id":"741","title":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales"},"742":{"body":"This RFC proposes a dynamic pricing model for the sale of Bulk Coretime on the Polkadot UC. The proposed model updates the regular price of cores for each sale period, by taking into account the number of cores sold in the previous sale, as well as a limit of cores and a target number of cores sold. It ensures a minimum price and limits price growth to a maximum price increase factor, while also giving govenance control over the steepness of the price change curve. It allows governance to address challenges arising from changing market conditions and should offer predictable and controlled price adjustments. Accompanying visualizations are provided at [1].","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Summary","id":"742","title":"Summary"},"743":{"body":"RFC-1 proposes periodic Bulk Coretime Sales as a mechanism to sell continouos regions of blockspace (suggested to be 4 weeks in length). A number of Blockspace Regions (compare RFC-1 & RFC-3) are provided for sale to the Broker-Chain each period and shall be sold in a way that provides value-capture for the Polkadot network. The exact pricing mechanism is out of scope for RFC-1 and shall be provided by this RFC. A dynamic pricing model is needed. A limited number of Regions are offered for sale each period. The model needs to find the price for a period based on supply and demand of the previous period. The model shall give Coretime consumers predictability about upcoming price developments and confidence that Polkadot governance can adapt the pricing model to changing market conditions.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Motivation","id":"743","title":"Motivation"},"744":{"body":"The solution SHOULD provide a dynamic pricing model that increases price with growing demand and reduces price with shrinking demand. The solution SHOULD have a slow rate of change for price if the number of Regions sold is close to a given sales target and increase the rate of change as the number of sales deviates from the target. The solution SHOULD provide the possibility to always have a minimum price per Region. The solution SHOULD provide a maximum factor of price increase should the limit of Regions sold per period be reached. The solution should allow governance to control the steepness of the price function","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Requirements","id":"744","title":"Requirements"},"745":{"body":"The primary stakeholders of this RFC are: Protocol researchers and evelopers Polkadot DOT token holders Polkadot parachains teams Brokers involved in the trade of Bulk Coretime","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Stakeholders","id":"745","title":"Stakeholders"},"746":{"body":"","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Explanation","id":"746","title":"Explanation"},"747":{"body":"The dynamic pricing model sets the new price based on supply and demand in the previous period. The model is a function of the number of Regions sold, piecewise-defined by two power functions. The left side ranges from 0 to the target. It represents situations where demand was lower than the target. The right side ranges from the target to limit. It represents situations where demand was higher than the target. The curve of the function forms a plateau around the target and then falls off to the left and rises up to the right. The shape of the plateau can be controlled via a scale factor for the left side and right side of the function respectively.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Overview","id":"747","title":"Overview"},"748":{"body":"From here on, we will also refer to Regions sold as 'cores' to stay congruent with RFC-1. Name Suggested Value Description Constraints BULK_LIMIT 45 The maximum number of cores being sold 0 < BULK_LIMIT BULK_TARGET 30 The target number of cores being sold 0 < BULK_TARGET <= BULK_LIMIT MIN_PRICE 1 The minimum price a core will always cost. 0 < MIN_PRICE MAX_PRICE_INCREASE_FACTOR 2 The maximum factor by which the price can change. 1 < MAX_PRICE_INCREASE_FACTOR SCALE_DOWN 2 The steepness of the left side of the function. 0 < SCALE_DOWN SCALE_UP 2 The steepness of the right side of the function. 0 < SCALE_UP","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Parameters","id":"748","title":"Parameters"},"749":{"body":"P(n) = \\begin{cases} (P_{\\text{old}} - P_{\\text{min}}) \\left(1 - \\left(\\frac{T - n}{T}\\right)^d\\right) + P_{\\text{min}} & \\text{if } n \\leq T \\\\ ((F - 1) \\cdot P_{\\text{old}} \\cdot \\left(\\frac{n - T}{L - T}\\right)^u) + P_{\\text{old}} & \\text{if } n > T \\end{cases} $P_{\\text{old}}$ is the old_price, the price of a core in the previous period. $P_{\\text{min}}$ is the MIN_PRICE, the minimum price a core will always cost. $F$ is the MAX_PRICE_INCREASE_FACTOR, the factor by which the price maximally can change from one period to another. $d$ is the SCALE_DOWN, the steepness of the left side of the function. $u$ is the SCALE_UP, the steepness of the right side of the function. $T$ is the BULK_TARGET, the target number of cores being sold. $L$ is the BULK_LIMIT, the maximum number of cores being sold. $n$ is cores_sold, the number of cores being sold. Left side The left side is a power function that describes an increasing concave downward curvature that approaches old_price. We realize this by using the form $y = a(1 - x^d)$, usually used as a downward sloping curve, but in our case flipped horizontally by letting the argument $x = \\frac{T-n}{T}$ decrease with $n$, doubly inversing the curve. This approach is chosen over a decaying exponential because it let's us a better control the shape of the plateau, especially allowing us to get a straight line by setting SCALE_DOWN to $1$. Ride side The right side is a power function of the form $y = a(x^u)$.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Function","id":"749","title":"Function"},"75":{"body":"What about the initial runtime, shall we make that off-chain as well? Good news, at least after the first upgrade, no code will be stored on chain any more, this means that we also have to redefine the storage deposit now. We no longer charge for chain storage, but validator disk storage -> Should be cheaper. Solution to this: Not only store the hash on chain, but also the size of the data. Then define a price per byte and charge that, but: how do we charge - I guess deposit has to be provided via other means, runtime upgrade fails if not provided. how do we signal to the chain that the code is too large for it to reject the upgrade? Easy: Make available and vote nay in pre-checking. TODO: Fully resolve these questions and incorporate in RFC text.","breadcrumbs":"RFC-0000: Feature Name Here » Unresolved Questions","id":"75","title":"Unresolved Questions"},"750":{"body":"NEW_PRICE := IF CORES_SOLD <= BULK_TARGET THEN (OLD_PRICE - MIN_PRICE) * (1 - ((BULK_TARGET - CORES_SOLD)^SCALE_DOWN / BULK_TARGET^SCALE_DOWN)) + MIN_PRICE\nELSE ((MAX_PRICE_INCREASE_FACTOR - 1) * OLD_PRICE * ((CORES_SOLD - BULK_TARGET)^SCALE_UP / (BULK_LIMIT - BULK_TARGET)^SCALE_UP)) + OLD_PRICE\nEND IF","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Pseudo-code","id":"750","title":"Pseudo-code"},"751":{"body":"Minimum Price We introduce MIN_PRICE to control the minimum price. The left side of the function shall be allowed to come close to 0 if cores sold approaches 0. The rationale is that if there are actually 0 cores sold, the previous sale price was too high and the price needs to adapt quickly. Price forms a plateau around the target If the number of cores is close to BULK_TARGET, less extreme price changes might be sensible. This ensures that a drop in sold cores or an increase doesn’t lead to immediate price changes, but rather slowly adapts. Only if more extreme changes in the number of sold cores occur, does the price slope increase. We introduce SCALE_DOWN and SCALE_UP to control for the steepness of the left and the right side of the function respectively. Max price increase factor We introduce MAX_PRICE_INCREASE_FACTOR as the factor that controls how much the price may increase from one period to another. Introducing this variable gives governance an additional control lever and avoids the necessity for a future runtime upgrade.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Properties of the Curve","id":"751","title":"Properties of the Curve"},"752":{"body":"Baseline This example proposes the baseline parameters. If not mentioned otherwise, other examples use these values. The minimum price of a core is 1 DOT, the price can double every 4 weeks. Price change around BULK_TARGET is dampened slightly. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 2\nSCALE_DOWN = 2\nSCALE_UP = 2\nOLD_PRICE = 1000 More aggressive pricing We might want to have a more aggressive price growth, allowing the price to triple every 4 weeks and have a linear increase in price on the right side. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 3\nSCALE_DOWN = 2\nSCALE_UP = 1\nOLD_PRICE = 1000 Conservative pricing to ensure quick corrections in an affluent market If governance considers the risk that a sudden surge in DOT price might price chains out from bulk coretime markets, it can ensure the model quickly reacts to a quick drop in demand, by setting 0 < SCALE_DOWN < 1 and setting the max price increase factor more conservatively. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 1.5\nSCALE_DOWN = 0.5\nSCALE_UP = 2\nOLD_PRICE = 1000 Linear pricing By setting the scaling factors to 1 and potentially adapting the max price increase, we can achieve a linear function BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 1.5\nSCALE_DOWN = 1\nSCALE_UP = 1\nOLD_PRICE = 1000","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Example Configurations","id":"752","title":"Example Configurations"},"753":{"body":"None at present.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Drawbacks","id":"753","title":"Drawbacks"},"754":{"body":"This pricing model is based on the requirements from the basic linear solution proposed in RFC-1, which is a simple dynamic pricing model and only used as proof. The present model adds additional considerations to make the model more adaptable under real conditions.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Prior Art and References","id":"754","title":"Prior Art and References"},"755":{"body":"This RFC, if accepted, shall be implemented in conjunction with RFC-1.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Future Possibilities","id":"755","title":"Future Possibilities"},"756":{"body":"[1] Polkadot forum post with visualizations: Dynamic Pricing for Bulk Coretime Sales","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » References","id":"756","title":"References"},"757":{"body":"(source) Table of Contents RFC-0009: Improved light client requests networking protocol Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-07-19 Description Modify the networking storage read requests to solve some problems with the existing one Authors Pierre Krieger","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » RFC-0009: Improved light client requests networking protocol","id":"757","title":"RFC-0009: Improved light client requests networking protocol"},"758":{"body":"Improve the networking messages that query storage items from the remote, in order to reduce the bandwidth usage and number of round trips of light clients.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Summary","id":"758","title":"Summary"},"759":{"body":"Clients on the Polkadot peer-to-peer network can be divided into two categories: full nodes and light clients. So-called full nodes are nodes that store the content of the chain locally on their disk, while light clients are nodes that don't. In order to access for example the balance of an account, a full node can do a disk read, while a light client needs to send a network message to a full node and wait for the full node to reply with the desired value. This reply is in the form of a Merkle proof, which makes it possible for the light client to verify the exactness of the value. Unfortunately, this network protocol is suffering from some issues: It is not possible for the querier to check whether a key exists in the storage of the chain except by querying the value of that key. The reply will thus include the value of the key, only for that value to be discarded by the querier that isn't interested by it. This is a waste of bandwidth. It is not possible for the querier to know whether a value in the storage of the chain has been modified between two blocks except by querying this value for both blocks and comparing them. Only a few storage values get modified in a block, and thus most of the time the comparison will be equal. This leads to a waste of bandwidth as the values have to be transferred. While it is possible to ask for multiple specific storage keys at the same time, it is not possible to ask for a list of keys that start with a certain prefix. Due to the way FRAME works, storage keys are grouped by \"prefix\", for example all account balances start with the same prefix. It is thus a common necessity for a light client to obtain the list of all keys (and possibly their values) that start with a specific prefix. This is currently not possible except by performing multiple queries serially that \"walk down\" the trie. Once Polkadot and Kusama will have transitioned to state_version = 1, which modifies the format of the trie entries, it will be possible to generate Merkle proofs that contain only the hashes of values in the storage. Thanks to this, it is already possible to prove the existence of a key without sending its entire value (only its hash), or to prove that a value has changed or not between two blocks (by sending just their hashes). Thus, the only reason why aforementioned issues exist is because the existing networking messages don't give the possibility for the querier to query this. This is what this proposal aims at fixing.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Motivation","id":"759","title":"Motivation"},"76":{"body":"","breadcrumbs":"RFC-0000: Feature Name Here » Future Directions and Related Material","id":"76","title":"Future Directions and Related Material"},"760":{"body":"This is the continuation of https://github.com/w3f/PPPs/pull/10, which itself is the continuation of https://github.com/w3f/PPPs/pull/5.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Stakeholders","id":"760","title":"Stakeholders"},"761":{"body":"The protobuf schema of the networking protocol can be found here: https://github.com/paritytech/substrate/blob/5b6519a7ff4a2d3cc424d78bc4830688f3b184c0/client/network/light/src/schema/light.v1.proto The proposal is to modify this protocol in this way: @@ -11,6 +11,7 @@ message Request { RemoteReadRequest remote_read_request = 2; RemoteReadChildRequest remote_read_child_request = 4; // Note: ids 3 and 5 were used in the past. It would be preferable to not re-use them.\n+ RemoteReadRequestV2 remote_read_request_v2 = 6; } } @@ -48,6 +49,21 @@ message RemoteReadRequest { repeated bytes keys = 3; } +message RemoteReadRequestV2 {\n+ required bytes block = 1;\n+ optional ChildTrieInfo child_trie_info = 2; // Read from the main trie if missing.\n+ repeated Key keys = 3;\n+ optional bytes onlyKeysAfter = 4;\n+ optional bool onlyKeysAfterIgnoreLastNibble = 5;\n+}\n+\n+message ChildTrieInfo {\n+ enum ChildTrieNamespace {\n+ DEFAULT = 1;\n+ }\n+\n+ required bytes hash = 1;\n+ required ChildTrieNamespace namespace = 2;\n+}\n+ // Remote read response. message RemoteReadResponse { // Read proof. If missing, indicates that the remote couldn't answer, for example because\n@@ -65,3 +81,8 @@ message RemoteReadChildRequest { // Storage keys. repeated bytes keys = 6; }\n+\n+message Key {\n+ required bytes key = 1;\n+ optional bool skipValue = 2; // Defaults to `false` if missing\n+ optional bool includeDescendants = 3; // Defaults to `false` if missing\n+} Note that the field names aren't very important as they are not sent over the wire. They can be changed at any time without any consequence. I would invite people to not discuss these field names as they are implementation details. This diff adds a new type of request (RemoteReadRequestV2). The new child_trie_info field in the request makes it possible to specify which trie is concerned by the request. The current networking protocol uses two different structs (RemoteReadRequest and RemoteReadChildRequest) for main trie and child trie queries, while this new request would make it possible to query either. This change doesn't fix any of the issues mentioned in the previous section, but is a side change that has been done for simplicity. An alternative could have been to specify the child_trie_info for each individual Key. However this would make it necessary to send the child trie hash many times over the network, which leads to a waste of bandwidth, and in my opinion makes things more complicated for no actual gain. If a querier would like to access more than one trie at the same time, it is always possible to send one query per trie. If skipValue is true for a Key, then the value associated with this key isn't important to the querier, and the replier is encouraged to replace the value with its hash provided that the storage item has a state_version equal to 1. If the storage value has a state_version equal to 0, then the optimization isn't possible and the replier should behave as if skipValue was false. If includeDescendants is true for a Key, then the replier must also include in the proof all keys that are descendant of the given key (in other words, its children, children of children, children of children of children, etc.). It must do so even if key itself doesn't have any storage value associated to it. The values of all of these descendants are replaced with their hashes if skipValue is true, similarly to key itself. The optional onlyKeysAfter and onlyKeysAfterIgnoreLastNibble fields can provide a lower bound for the keys contained in the proof. The responder must not include in its proof any node whose key is strictly inferior to the value in onlyKeysAfter. If onlyKeysAfterIgnoreLastNibble is provided, then the last 4 bits for onlyKeysAfter must be ignored. This makes it possible to represent a trie branch node that doesn't have an even number of nibbles. If no onlyKeysAfter is provided, it is equivalent to being empty, meaning that the response must start with the root node of the trie. If onlyKeysAfterIgnoreLastNibble is missing, it is equivalent to false. If onlyKeysAfterIgnoreLastNibble is true and onlyKeysAfter is missing or empty, then the request is invalid. For the purpose of this networking protocol, it should be considered as if the main trie contained an entry for each default child trie whose key is concat(\":child_storage:default:\", child_trie_hash) and whose value is equal to the trie root hash of that default child trie. This behavior is consistent with what the host functions observe when querying the storage. This behavior is present in the existing networking protocol, in other words this proposal doesn't change anything to the situation, but it is worth mentioning. Also note that child tries aren't considered as descendants of the main trie when it comes to the includeDescendants flag. In other words, if the request concerns the main trie, no content coming from child tries is ever sent back. This protocol keeps the same maximum response size limit as currently exists (16 MiB). It is not possible for the querier to know in advance whether its query will lead to a reply that exceeds the maximum size. If the reply is too large, the replier should send back only a limited number (but at least one) of requested items in the proof. The querier should then send additional requests for the rest of the items. A response containing none of the requested items is invalid. The server is allowed to silently discard some keys of the request if it judges that the number of requested keys is too high. This is in line with the fact that the server might truncate the response.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Explanation","id":"761","title":"Explanation"},"762":{"body":"This proposal doesn't handle one specific situation: what if a proof containing a single specific item would exceed the response size limit? For example, if the response size limit was 1 MiB, querying the runtime code (which is typically 1.0 to 1.5 MiB) would be impossible as it's impossible to generate a proof less than 1 MiB. The response size limit is currently 16 MiB, meaning that no single storage item must exceed 16 MiB. Unfortunately, because it's impossible to verify a Merkle proof before having received it entirely, parsing the proof in a streaming way is also not possible. A way to solve this issue would be to Merkle-ize large storage items, so that a proof could include only a portion of a large storage item. Since this would require a change to the trie format, it is not realistically feasible in a short time frame.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Drawbacks","id":"762","title":"Drawbacks"},"763":{"body":"The main security consideration concerns the size of replies and the resources necessary to generate them. It is for example easily possible to ask for all keys and values of the chain, which would take a very long time to generate. Since responses to this networking protocol have a maximum size, the replier should truncate proofs that would lead to the response being too large. Note that it is already possible to send a query that would lead to a very large reply with the existing network protocol. The only thing that this proposal changes is that it would make it less complicated to perform such an attack. Implementers of the replier side should be careful to detect early on when a reply would exceed the maximum reply size, rather than inconditionally generate a reply, as this could take a very large amount of CPU, disk I/O, and memory. Existing implementations might currently be accidentally protected from such an attack thanks to the fact that requests have a maximum size, and thus that the list of keys in the query was bounded. After this proposal, this accidental protection would no longer exist. Malicious server nodes might truncate Merkle proofs even when they don't strictly need to, and it is not possible for the client to (easily) detect this situation. However, malicious server nodes can already do undesirable things such as throttle down their upload bandwidth or simply not respond. There is no need to handle unnecessarily truncated Merkle proofs any differently than a server simply not answering the request.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Testing, Security, and Privacy","id":"763","title":"Testing, Security, and Privacy"},"764":{"body":"","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Performance, Ergonomics, and Compatibility","id":"764","title":"Performance, Ergonomics, and Compatibility"},"765":{"body":"It is unclear to the author of the RFC what the performance implications are. Servers are supposed to have limits to the amount of resources they use to respond to requests, and as such the worst that can happen is that light client requests become a bit slower than they currently are.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Performance","id":"765","title":"Performance"},"766":{"body":"Irrelevant.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Ergonomics","id":"766","title":"Ergonomics"},"767":{"body":"The prior networking protocol is maintained for now. The older version of this protocol could get removed in a long time.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Compatibility","id":"767","title":"Compatibility"},"768":{"body":"None. This RFC is a clean-up of an existing mechanism.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Prior Art and References","id":"768","title":"Prior Art and References"},"769":{"body":"None","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Unresolved Questions","id":"769","title":"Unresolved Questions"},"77":{"body":"By no longer having code upgrade go through the relay chain, occupying a full relay chain block, the impact on other parachains is already greatly reduced, if we make distribution and PVF pre-checking low-priority processes on validators. The only thing attackers might be able to do is delay upgrades of other parachains. Which seems like a problem to be solved once we actually see it as a problem in the wild (and can already be mitigated by adjusting the counter). The good thing is that we have all the ingredients to go further if need be. Signalling no longer actually includes the code, hence there is no need to reject the candidate: The parachain can make progress even if we choose not to immediately act on the request and no relay chain resources are wasted either. We could for example introduce another UMP Signalling message RequestCodeUpgradeWithPriority which not just requests a code upgrade, but also offers some DOT to get ranked up in a queue.","breadcrumbs":"RFC-0000: Feature Name Here » Further Hardening","id":"77","title":"Further Hardening"},"770":{"body":"The current networking protocol could be deprecated in a long time. Additionally, the current \"state requests\" protocol (used for warp syncing) could also be deprecated in favor of this one.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Future Directions and Related Material","id":"770","title":"Future Directions and Related Material"},"771":{"body":"(source) Table of Contents RFC-0015: Market Design Revisit Summary Motivation Stakeholders Explanation Bulk Markets Benefits of this system Further Discussion Points Drawbacks Prior Art and References Unresolved Questions Start Date 05.08.2023 Description This RFC refines the previously proposed mechanisms involving the various Coretime markets and presents an integrated framework for harmonious interaction between all markets. Authors Jonas Gehrlein","breadcrumbs":"RFC-0015: Market Design Revisit » RFC-0015: Market Design Revisit","id":"771","title":"RFC-0015: Market Design Revisit"},"772":{"body":"This document is a proposal for restructuring the bulk markets in the Polkadot UC's coretime allocation system to improve efficiency and fairness. The proposal suggests separating the BULK_PERIOD into MARKET_PERIOD and RENEWAL_PERIOD, allowing for a market-driven price discovery through a clearing price Dutch auction during the MARKET_PERIOD followed by renewal offers at the MARKET_PRICE during the RENEWAL_PERIOD. The new system ensures synchronicity between renewal and market prices, fairness among all current tenants, and efficient price discovery, while preserving price caps to provide security for current tenants. It seeks to start a discussion about the possibility of long-term leases.","breadcrumbs":"RFC-0015: Market Design Revisit » Summary","id":"772","title":"Summary"},"773":{"body":"While the initial RFC-1 has provided a robust framework for Coretime allocation within the Polkadot UC, this proposal builds upon its strengths and uses many provided building blocks to address some areas that could be further improved. In particular, this proposal introduces the following changes: It introduces a RESERVE_PRICE that anchors all markets, promoting price synchronicity within the Bulk markets (flexible + renewals). This reduces complexity. This makes sure all consumers pay a closely correlated price for coretime within a BULK_PERIOD. It reverses the order of the market and renewal phase. This allows to fine-tune the price through market forces. It exposes the renewal prices, while still being beneficial for longterm tenants, more to market forces. It removes the LeadIn period and introduces a (from the perspective of the coretime systemchain) passive Settlement Phase, that allows the secondary market to exert it's force. The premise of this proposal is to reduce complexity by introducing a common price (that develops releative to capacity consumption of Polkadot UC), while still allowing for market forces to add efficiency. Longterm lease owners still receive priority IF they can pay (close to) the market price. This prevents a situation where the renewal price significantly diverges from renewal prices which allows for core captures. While maximum price increase certainty might seem contradictory to efficient price discovery, the proposed model aims to balance these elements, utilizing market forces to determine the price and allocate cores effectively within certain bounds. It must be stated, that potential price increases remain predictable (in the worst-case) but could be higher than in the originally proposed design. The argument remains, however, that we need to allow market forces to affect all prices for an efficient Coretime pricing and allocation. Ultimately, this the framework proposed here adheres to all requirements stated in RFC-1.","breadcrumbs":"RFC-0015: Market Design Revisit » Motivation","id":"773","title":"Motivation"},"774":{"body":"Primary stakeholder sets are: Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division. Polkadot Parachain teams both present and future, and their users. Polkadot DOT token holders.","breadcrumbs":"RFC-0015: Market Design Revisit » Stakeholders","id":"774","title":"Stakeholders"},"775":{"body":"","breadcrumbs":"RFC-0015: Market Design Revisit » Explanation","id":"775","title":"Explanation"},"776":{"body":"The BULK_PERIOD has been restructured into two primary segments: the MARKET_PERIOD and RENEWAL_PERIOD, along with an auxiliary SETTLEMENT_PERIOD. This latter period doesn't necessitate any actions from the coretime system chain, but it facilitates a more efficient allocation of coretime in secondary markets. A significant departure from the original proposal lies in the timing of renewals, which now occur post-market phase. This adjustment aims to harmonize renewal prices with their market counterparts, ensuring a more consistent and equitable pricing model. Market Period (14 days) During the market period, core sales are conducted through a well-established clearing price Dutch auction that features a RESERVE_PRICE. The price initiates at a premium, designated as PRICE_PREMIUM (for instance, 30%) and descends linearly to the RESERVE_PRICE throughout the duration of the MARKET_PERIOD. Each bidder is expected to submit both their desired price and the quantity (that is, the amount of Coretime) they wish to purchase. To secure these acquisitions, bidders must make a deposit equivalent to their bid multiplied by the chosen quantity, in DOT. The market achieves resolution once all quantities have been sold, or the RESERVE_PRICE has been reached. This situation leads to determining the MARKET_PRICE either by the lowest bid that was successful in clearing the entire market or by the RESERVE_PRICE. This mechanism yields a uniform price, shaped by market forces (refer to the following discussion for an explanation of its benefits). In other words, all buyers pay the same price (per unit of Coretime). Further down the benefits of this variant of a Dutch auction is discussed. Note: In cases where some cores remain unsold in the market, all buyers are obligated to pay the RESERVE_PRICE. Renewal Period (7 days) As the RENEWAL_PERIOD commences, all current tenants are granted the opportunity to renew their cores at a slight discount of MARKET_PRICE * RENEWAL_DISCOUNT (for instance, 10%). This provision affords marginal benefits to existing tenants, balancing out the non-transferability aspect of renewals. At the end of the period, all available cores are allocated to the current tenants who have opted for renewal and the participants who placed bids during the market period. If the demand for cores exceeds supply, the cores left unclaimed from renewals may be awarded to bidders who placed their bids early in the auction, thereby subtly incentivizing early participation. If the supply exceeds the demand, all unsold cores are transferred to the Instantanous Market. Reserve Price Adjustment After all cores are allocated, the RESERVE_PRICE is adjusted following the process described in RFC-1 and serves as baseline price in the next BULK_PERIOD. Note: The particular price curve is outside the scope of the proposal. The MARKET_PRICE (as a function of RESERVE_PRICE), however, is able to capture higher demand very well while being capped downwards. That means, the curve that adjusts the RESERVE_PRICE should be more sensitive to undercapacity. Price Predictability Tasks that are in the \"renewal-pipeline\" can determine the upper bound for the price they will pay in any future period. The main driver of any price increase over time is the adjustment of the RESERVE_PRICE, that occurs at the end of each BULK_PERIOD after determining the capacity fillment of Polkadot UC. To calculate the maximum price in some future period, a task could assume maximum capacity in all upcoming periods and track the resulting price increase of RESERVE_PRICE. In the final period, that price can get a maximum premium of PRICE_PREMIUM and after deducting a potential RENEWAL_DISCOUNT, the maximum price can be determined. Settlement Period (7 days) During the settlement period, participants have ample time to trade Coretime on secondary markets before the onset of the next BULK_PERIOD. This allows for trading with full Coretime availability. Trading transferrable Coretime naturally continues during each BULK_PERIOD, albeit with cores already in use.","breadcrumbs":"RFC-0015: Market Design Revisit » Bulk Markets","id":"776","title":"Bulk Markets"},"777":{"body":"The introduction of a single price, the RESERVE_PRICE, provides an anchor for all Coretime markets. This is a preventative measure against the possible divergence and mismatch of prices, which could inadvertently lead to a situation where existing tenants secure cores at significantly below-market rates. With a more market-responsive pricing system, we can achieve a more efficient price discovery process. Any price increases will be less arbitrary and more dynamic. The ideal strategy for existing tenants is to maintain passivity, i.e., refrain from active market participation and simply accept the offer presented to them during the renewal phase. This approach lessens the organizational overhead for long-term projects. In the two-week market phase, the maximum price increase is known well in advance, providing ample time for tenants to secure necessary funds to meet the potential price escalation. All existing tenants pay an equal amount for Coretime, reflecting our intent to price the Coretime itself and not the relative timing of individual projects. Discussion: Clearing Price Dutch Auctions Having all bidders pay the market clearing price offers some benefits and disadvantages. Advantages: Fairness : All bidders pay the same price. Active participation : Because bidders are protected from overbidding (winner's curse), they are more likely to engage and reveal their true valuations. Simplicity : A single price is easier to work with for pricing renewals later. Truthfulness : There is no need to try to game the market by waiting with bidding. Bidders can just bid their valuations. Disadvantages: (Potentially) Lower Revenue : While the theory predicts revenue-equivalence between a uniform price and pay-as-bid type of auction, slightly lower revenue for the former type is observed empirically. Arguably, revenue maximization (i.e., squeezing out the maximum willingness to pay from bidders) is not the priority for Polkadot UC. Instead, it is interested in efficient allocation and the other benefits illustrated above. (Technical) Complexity : Instead of making a final purchase within the auction, the bid is only a deposit. Some refunds might happen after the auction is finished. This might pose additional challenges from the technical side (e.g., storage requirements).","breadcrumbs":"RFC-0015: Market Design Revisit » Benefits of this system","id":"777","title":"Benefits of this system"},"778":{"body":"Long-term Coretime : The Polkadot UC is undergoing a transition from two-year leases without an instantaneous market to a model encompassing instantaneous and one-month leases. This shift seems to pivot from one extreme to another. While the introduction of short-term leases, both instantaneous and for one month, is a constructive move to lower barriers to entry and promote experimentation, it seems to be the case that established projects might benefit from more extended lease options. We could consider offering another product, such as a six-month Coretime lease, using the same mechanism described herein. Although the majority of leases would still be sold on a one-month basis, the addition of this option would enhance market efficiency as it would strengthen the impact of a secondary market .","breadcrumbs":"RFC-0015: Market Design Revisit » Further Discussion Points","id":"778","title":"Further Discussion Points"},"779":{"body":"There are trade-offs that arise from this proposal, compared to the initial model. The most notable one is that here, I prioritize requirement 6 over requirement 2. The price, in the very \"worst-case\" (meaning a huge explosion in demand for coretime) could lead to a much larger increase of prices in Coretime. From an economic perspective, this (rare edgecase) would also mean that we'd vastly underprice Coretime in the original model, leading to highly inefficient allocations.","breadcrumbs":"RFC-0015: Market Design Revisit » Drawbacks","id":"779","title":"Drawbacks"},"78":{"body":"Making this storage mechanism more general purpose is worth thinking about. E.g. by resolving above \"fee\" question, we might also be able to resolve the pruning question in a more generic way and thus could indeed open this storage facility for other purposes as well. E.g. smart contracts, so the PoV would only need to reference contracts by hash and the actual PoV is stored on validators and collators and thus no longer needs to be part of the PoV. A possible avenue would be to change the response to: enum BlobResponse { Blob(Vec), Blobs(MerkleTree),\n} With this the hash specified in the request can also be a merkle root and the responder will respond with the entire merkle tree (only hashes, no payload). Then the requester can traverse the leaf hashes and use the same request response protocol to request any locally missing blobs in that tree. One leaf would for example be the PVF others could be smart contracts. With a properly specified format (e.g. which leaf is the PVF?), what we got here is that a parachain can not only update its PVF, but additional data, incrementally. E.g. adding another smart contract, does not require resubmitting the entire PVF to validators, only the root hash on the relay chain gets updated, then validators fetch the merkle tree and only fetch any missing leaves. That additional data could be made available to the PVF via a to be added host function. The nice thing about this approach is, that while we can upgrade incrementally, lifetime is still tied to the PVF and we get all the same guarantees. Assuming the validators store blobs by hash, we even get disk sharing if multiple parachains use the same data (e.g. same smart contracts).","breadcrumbs":"RFC-0000: Feature Name Here » Generalize this off-chain storage mechanism?","id":"78","title":"Generalize this off-chain storage mechanism?"},"780":{"body":"This RFC builds extensively on the available ideas put forward in RFC-1 . Additionally, I want to express a special thanks to Samuel Haefner and Shahar Dobzinski for fruitful discussions and helping me structure my thoughts.","breadcrumbs":"RFC-0015: Market Design Revisit » Prior Art and References","id":"780","title":"Prior Art and References"},"781":{"body":"The technical feasability needs to be assessed.","breadcrumbs":"RFC-0015: Market Design Revisit » Unresolved Questions","id":"781","title":"Unresolved Questions"},"782":{"body":"(source) Table of Contents RFC-34: XCM Absolute Location Account Derivation Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 05 October 2023 Description XCM Absolute Location Account Derivation Authors Gabriel Facco de Arruda","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » RFC-34: XCM Absolute Location Account Derivation","id":"782","title":"RFC-34: XCM Absolute Location Account Derivation"},"783":{"body":"This RFC proposes changes that enable the use of absolute locations in AccountId derivations, which allows protocols built using XCM to have static account derivations in any runtime, regardless of its position in the family hierarchy.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Summary","id":"783","title":"Summary"},"784":{"body":"These changes would allow protocol builders to leverage absolute locations to maintain the exact same derived account address across all networks in the ecosystem, thus enhancing user experience. One such protocol, that is the original motivation for this proposal, is InvArch's Saturn Multisig, which gives users a unifying multisig and DAO experience across all XCM connected chains.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Motivation","id":"784","title":"Motivation"},"785":{"body":"Ecosystem developers","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Stakeholders","id":"785","title":"Stakeholders"},"786":{"body":"This proposal aims to make it possible to derive accounts for absolute locations, enabling protocols that require the ability to maintain the same derived account in any runtime. This is done by deriving accounts from the hash of described absolute locations, which are static across different destinations. The same location can be represented in relative form and absolute form like so: // Relative location (from own perspective)\n{ parents: 0, interior: Here\n} // Relative location (from perspective of parent)\n{ parents: 0, interior: [Parachain(1000)]\n} // Relative location (from perspective of sibling)\n{ parents: 1, interior: [Parachain(1000)]\n} // Absolute location\n[GlobalConsensus(Kusama), Parachain(1000)] Using DescribeFamily, the above relative locations would be described like so: // Relative location (from own perspective)\n// Not possible. // Relative location (from perspective of parent)\n(b\"ChildChain\", Compact::::from(*index)).encode() // Relative location (from perspective of sibling)\n(b\"SiblingChain\", Compact::::from(*index)).encode() The proposed description for absolute location would follow the same pattern, like so: ( b\"GlobalConsensus\", network_id, b\"Parachain\", Compact::::from(para_id), tail\n).encode() This proposal requires the modification of two XCM types defined in the xcm-builder crate: The WithComputedOrigin barrier and the DescribeFamily MultiLocation descriptor. WithComputedOrigin The WtihComputedOrigin barrier serves as a wrapper around other barriers, consuming origin modification instructions and applying them to the message origin before passing to the inner barriers. One of the origin modifying instructions is UniversalOrigin, which serves the purpose of signaling that the origin should be a Universal Origin that represents the location as an absolute path prefixed by the GlobalConsensus junction. In it's current state the barrier transforms locations with the UniversalOrigin instruction into relative locations, so the proposed changes aim to make it return absolute locations instead. DescribeFamily The DescribeFamily location descriptor is part of the HashedDescription MultiLocation hashing system and exists to describe locations in an easy format for encoding and hashing, so that an AccountId can be derived from this MultiLocation. This implementation contains a match statement that does not match against absolute locations, so changes to it involve matching against absolute locations and providing appropriate descriptions for hashing.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Explanation","id":"786","title":"Explanation"},"787":{"body":"No drawbacks have been identified with this proposal.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Drawbacks","id":"787","title":"Drawbacks"},"788":{"body":"Tests can be done using simple unit tests, as this is not a change to XCM itself but rather to types defined in xcm-builder. Security considerations should be taken with the implementation to make sure no unwanted behavior is introduced. This proposal does not introduce any privacy considerations.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Testing, Security, and Privacy","id":"788","title":"Testing, Security, and Privacy"},"789":{"body":"","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Performance, Ergonomics, and Compatibility","id":"789","title":"Performance, Ergonomics, and Compatibility"},"79":{"body":"(source) Table of Contents RFC-0111: Pure Proxy Replication Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 12 Aug 2024. Description Replication of pure proxy account ownership to a remote chain Authors @muharem @xlc","breadcrumbs":"RFC-0111: Pure Proxy Replication » RFC-0111: Pure Proxy Replication","id":"79","title":"RFC-0111: Pure Proxy Replication"},"790":{"body":"Depending on the final implementation, this proposal should not introduce much overhead to performance.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Performance","id":"790","title":"Performance"},"791":{"body":"The ergonomics of this proposal depend on the final implementation details.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Ergonomics","id":"791","title":"Ergonomics"},"792":{"body":"Backwards compatibility should remain unchanged, although that depend on the final implementation.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Compatibility","id":"792","title":"Compatibility"},"793":{"body":"DescirbeFamily type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/location_conversion.rs#L122 WithComputedOrigin type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/barriers.rs#L153","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Prior Art and References","id":"793","title":"Prior Art and References"},"794":{"body":"Implementation details and overall code is still up to discussion.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Unresolved Questions","id":"794","title":"Unresolved Questions"},"795":{"body":"(source) Table of Contents RFC-0035: Conviction Voting Delegation Modifications Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics & Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material October 10, 2023 Conviction Voting Delegation Modifications ChaosDAO","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » RFC-0035: Conviction Voting Delegation Modifications","id":"795","title":"RFC-0035: Conviction Voting Delegation Modifications"},"796":{"body":"This RFC proposes to make modifications to voting power delegations as part of the Conviction Voting pallet. The changes being proposed include: Allow a Delegator to vote independently of their Delegate if they so desire. Allow nested delegations – for example Charlie delegates to Bob who delegates to Alice – when Alice votes then both Bob and Charlie vote alongside Alice (in the current implementation Charlie will not vote when Alice votes). Make a change so that when a delegate votes abstain their delegated votes also vote abstain. Allow a Delegator to delegate/ undelegate their votes for all tracks with a single call.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Summary","id":"796","title":"Summary"},"797":{"body":"It has become clear since the launch of OpenGov that there are a few common tropes which pop up time and time again: The frequency of referenda is often too high for network participants to have sufficient time to review, comprehend, and ultimately vote on each individual referendum. This means that these network participants end up being inactive in on-chain governance. There are active network participants who are reviewing every referendum and are providing feedback in an attempt to help make the network thrive – but often time these participants do not control enough voting power to influence the network with their positive efforts. Delegating votes for all tracks currently requires long batched calls which result in high fees for the Delegator - resulting in a reluctance from many to delegate their votes. We believe (based on feedback from token holders with a larger stake in the network) that if there were some changes made to delegation mechanics, these larger stake holders would be more likely to delegate their voting power to active network participants – thus greatly increasing the support turnout.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Motivation","id":"797","title":"Motivation"},"798":{"body":"The primary stakeholders of this RFC are: The Polkadot Technical Fellowship who will have to research and implement the technical aspects of this RFC DOT token holders in general","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Stakeholders","id":"798","title":"Stakeholders"},"799":{"body":"This RFC proposes to make 4 changes to the convictionVoting pallet logic in order to improve the user experience of those delegating their voting power to another account. Allow a Delegator to vote independently of their Delegate if they so desire – this would empower network participants to more actively delegate their voting power to active voters, removing the tedious steps of having to undelegate across an entire track every time they do not agree with their delegate's voting direction for a particular referendum. Allow nested delegations – for example Charlie delegates to Bob who delegates to Alice – when Alice votes then both Bob and Charlie vote alongside Alice (in the current runtime Charlie will not vote when Alice votes) – This would allow network participants who control multiple (possibly derived) accounts to be able to delegate all of their voting power to a single account under their control, which would in turn delegate to a more active voting participant. Then if the delegator wishes to vote independently of their delegate they can control all of their voting power from a single account, which again removes the pain point of having to issue multiple undelegate extrinsics in the event that they disagree with their delegate. Have delegated votes follow their delegates abstain votes – there are times where delegates may vote abstain on a particular referendum and adding this functionality will increase the support of a particular referendum. It has a secondary benefit of meaning that Validators who are delegating their voting power do not lose points in the 1KV program in the event that their delegate votes abstain (another pain point which may be preventing those network participants from delegating). Allow a Delegator to delegate/ undelegate their votes for all tracks with a single call - in order to delegate votes across all tracks, a user must batch 15 calls - resulting in high costs for delegation. A single call for delegate_all/ undelegate_all would reduce the complexity and therefore costs of delegations considerably for prospective Delegators.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Explanation","id":"799","title":"Explanation"},"8":{"body":"Regarding ergonomics, no drawbacks were noticed. As for the user experience, it could discover new cross-chain use cases involving asset collections and NFTs, indicating a positive impact. There are no security concerns except for the ReportMetadata instruction, which implies that the source of the information must be trusted. In terms of performance and privacy, there will be no changes.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Drawbacks","id":"8","title":"Drawbacks"},"80":{"body":"This RFC proposes a solution to replicate an existing pure proxy from one chain to others. The aim is to address the current limitations where pure proxy accounts, which are keyless, cannot have their proxy relationships recreated on different chains. This leads to issues where funds or permissions transferred to the same keyless account address on chains other than its origin chain become inaccessible.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Summary","id":"80","title":"Summary"},"800":{"body":"We do not foresee any drawbacks by implementing these changes. If anything we believe that this should help to increase overall voter turnout (via the means of delegation) which we see as a net positive.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Drawbacks","id":"800","title":"Drawbacks"},"801":{"body":"We feel that the Polkadot Technical Fellowship would be the most competent collective to identify the testing requirements for the ideas presented in this RFC.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Testing, Security, and Privacy","id":"801","title":"Testing, Security, and Privacy"},"802":{"body":"","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Performance, Ergonomics, and Compatibility","id":"802","title":"Performance, Ergonomics, and Compatibility"},"803":{"body":"This change may add extra chain storage requirements on Polkadot, especially with respect to nested delegations.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Performance","id":"803","title":"Performance"},"804":{"body":"The change to add nested delegations may affect governance interfaces such as Nova Wallet who will have to apply changes to their indexers to support nested delegations. It may also affect the Polkadot Delegation Dashboard as well as Polkassembly & SubSquare. We want to highlight the importance for ecosystem builders to create a mechanism for indexers and wallets to be able to understand that changes have occurred such as increasing the pallet version, etc.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Ergonomics & Compatibility","id":"804","title":"Ergonomics & Compatibility"},"805":{"body":"N/A","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Prior Art and References","id":"805","title":"Prior Art and References"},"806":{"body":"N/A","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Unresolved Questions","id":"806","title":"Unresolved Questions"},"807":{"body":"Additionally we would like to re-open the conversation about the potential for there to be free delegations. This was discussed by Dr Gavin Wood at Sub0 2022 and we feel like this would go a great way towards increasing the amount of network participants that are delegating: https://youtu.be/hSoSA6laK3Q?t=526 Overall, we strongly feel that delegations are a great way to increase voter turnout, and the ideas presented in this RFC would hopefully help in that aspect.","breadcrumbs":"RFC-0035: Conviction Voting Delegation Modifications » Future Directions and Related Material","id":"807","title":"Future Directions and Related Material"},"808":{"body":"(source) Table of Contents RFC-0044: Rent based registration model Summary Motivation Requirements Stakeholders Explanation Registering an on-demand parachain On-demand parachain pruning Ensuring rent is paid On-demand para re-registration Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 6 November 2023 Description A new rent based parachain registration model Authors Sergej Sakac","breadcrumbs":"RFC-0044: Rent based registration model » RFC-0044: Rent based registration model","id":"808","title":"RFC-0044: Rent based registration model"},"809":{"body":"This RFC proposes a new model for a sustainable on-demand parachain registration, involving a smaller initial deposit and periodic rent payments. The new model considers that on-demand chains may be unregistered and later re-registered. The proposed solution also ensures a quick startup for on-demand chains on Polkadot in such cases.","breadcrumbs":"RFC-0044: Rent based registration model » Summary","id":"809","title":"Summary"},"81":{"body":"A pure proxy is a new account created by a primary account. The primary account is set as a proxy for the pure proxy account, managing it. Pure proxies are keyless and non-reproducible, meaning they lack a private key and have an address derived from a preimage determined by on-chain logic. More on pure proxies can be found here . For the purpose of this document, we define a keyless account as a \"pure account\", the controlling account as a \"proxy account\", and the entire relationship as a \"pure proxy\". The relationship between a pure account (e.g., account ID: pure1) and its proxy (e.g., account ID: alice) is stored on-chain (e.g., parachain A) and currently cannot be replicated to another chain (e.g., parachain B). Because the account pure1 is keyless and its proxy relationship with alice is not replicable from the parachain A to the parachain B, alice does not control the pure1 account on the parachain B. Although this behaviour is not promised, users and clients often mistakenly expect alice to control the same pure1 account on the parachain B. As a result, assets transferred to the account or permissions granted for it are inaccessible. Several factors contribute to this misuse: regular accounts on different parachains with the same account ID are typically accessible for the owner and controlled by the same private key (e.g., within System Parachains); users and clients do not distinguish between keyless and regular accounts; members using the multisig account ID across different chains, where a member of a multisig is a pure account; users may prefer an account with a registered identity (e.g. for cross-chain treasury spend proposal), even if the account is keyless; Given that these mistakes are likely, it is necessary to provide a solution to either prevent them or enable access to a pure account on a target chain.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Motivation","id":"81","title":"Motivation"},"810":{"body":"With the support of on-demand parachains on Polkadot, there is a need to explore a new, more cost-effective model for registering validation code. In the current model, the parachain manager is responsible for reserving a unique ParaId and covering the cost of storing the validation code of the parachain. These costs can escalate, particularly if the validation code is large. We need a better, sustainable model for registering on-demand parachains on Polkadot to help smaller teams deploy more easily. This RFC suggests a new payment model to create a more financially viable approach to on-demand parachain registration. In this model, a lower initial deposit is required, followed by recurring payments upon parachain registration. This new model will coexist with the existing one-time deposit payment model, offering teams seeking to deploy on-demand parachains on Polkadot a more cost-effective alternative.","breadcrumbs":"RFC-0044: Rent based registration model » Motivation","id":"810","title":"Motivation"},"811":{"body":"The solution SHOULD NOT affect the current model for registering validation code. The solution SHOULD offer an easily configurable way for governance to adjust the initial deposit and recurring rent cost. The solution SHOULD provide an incentive to prune validation code for which rent is not paid. The solution SHOULD allow anyone to re-register validation code under the same ParaId without the need for redundant pre-checking if it was already verified before. The solution MUST be compatible with the Agile Coretime model, as described in RFC#0001 The solution MUST allow anyone to pay the rent. The solution MUST prevent the removal of validation code if it could still be required for disputes or approval checking.","breadcrumbs":"RFC-0044: Rent based registration model » Requirements","id":"811","title":"Requirements"},"812":{"body":"Future Polkadot on-demand Parachains","breadcrumbs":"RFC-0044: Rent based registration model » Stakeholders","id":"812","title":"Stakeholders"},"813":{"body":"This RFC proposes a set of changes that will enable the new rent based approach to registering and storing validation code on-chain. The new model, compared to the current one, will require periodic rent payments. The parachain won't be pruned automatically if the rent is not paid, but by permitting anyone to prune the parachain and rewarding the caller, there will be an incentive for the removal of the validation code. On-demand parachains should still be able to utilize the current one-time payment model. However, given the size of the deposit required, it's highly likely that most on-demand parachains will opt for the new rent-based model. Importantly, this solution doesn't require any storage migrations in the current system nor does it introduce any breaking changes. The following provides a detailed description of this solution.","breadcrumbs":"RFC-0044: Rent based registration model » Explanation","id":"813","title":"Explanation"},"814":{"body":"In the current implementation of the registrar pallet, there are two constants that specify the necessary deposit for parachains to register and store their validation code: trait Config { // -- snip -- /// The deposit required for reserving a `ParaId`. #[pallet::constant] type ParaDeposit: Get>; /// The deposit to be paid per byte stored on chain. #[pallet::constant] type DataDepositPerByte: Get>;\n} This RFC proposes the addition of three new constants that will determine the payment amount and the frequency of the recurring rent payment: trait Config { // -- snip -- /// Defines how frequently the rent needs to be paid. /// /// The duration is set in sessions instead of block numbers. #[pallet::constant] type RentDuration: Get; /// The initial deposit amount for registering validation code. /// /// This is defined as a proportion of the deposit that would be required in the regular /// model. #[pallet::constant] type RentalDepositProportion: Get; /// The recurring rental cost defined as a proportion of the initial rental registration deposit. #[pallet::constant] type RentalRecurringProportion: Get;\n} Users will be able to reserve a ParaId and register their validation code for a proportion of the regular deposit required. However, they must also make additional rent payments at intervals of T::RentDuration. For registering using the new rental system we will have to make modifications to the paras-registrar pallet. We should expose two new extrinsics for this: mod pallet { // -- snip -- pub fn register_rental( origin: OriginFor, id: ParaId, genesis_head: HeadData, validation_code: ValidationCode, ) -> DispatchResult { /* ... */ } pub fn pay_rent(origin: OriginFor, id: ParaId) -> DispatchResult { /* ... */ }\n} A call to register_rental will require the reservation of only a percentage of the deposit that would otherwise be required to register the validation code when using the regular model. As described later in the Quick para re-registering section below, we will also store the code hash of each parachain to enable faster re-registration after a parachain has been pruned. For this reason the total initial deposit amount is increased to account for that. // The logic for calculating the initial deposit for parachain registered with the // new rent-based model: let validation_code_deposit = per_byte_fee.saturating_mul((validation_code.0.len() as u32).into()); let head_deposit = per_byte_fee.saturating_mul((genesis_head.0.len() as u32).into())\nlet hash_deposit = per_byte_fee.saturating_mul(HASH_SIZE); let deposit = T::RentalDepositProportion::get().mul_ceil(validation_code_deposit) .saturating_add(T::ParaDeposit::get()) .saturating_add(head_deposit) .saturating_add(hash_deposit) Once the ParaId is reserved and the validation code is registered the rent must be periodically paid to ensure the on-demand parachain doesn't get removed from the state. The pay_rent extrinsic should be callable by anyone, removing the need for the parachain to depend on the parachain manager for rent payments.","breadcrumbs":"RFC-0044: Rent based registration model » Registering an on-demand parachain","id":"814","title":"Registering an on-demand parachain"},"815":{"body":"If the rent is not paid, anyone has the option to prune the on-demand parachain and claim a portion of the initial deposit reserved for storing the validation code. This type of 'light' pruning only removes the validation code, while the head data and validation code hash are retained. The validation code hash is stored to allow anyone to register it again as well as to enable quicker re-registration by skipping the pre-checking process. The moment the rent is no longer paid, the parachain won't be able to purchase on-demand access, meaning no new blocks are allowed. This stage is called the \"hibernation\" stage, during which all the parachain-related data is still stored on-chain, but new blocks are not permitted. The reason for this is to ensure that the validation code is available in case it is needed in the dispute or approval checking subsystems. Waiting for one entire session will be enough to ensure it is safe to deregister the parachain. This means that anyone can prune the parachain only once the \"hibernation\" stage is over, which lasts for an entire session after the moment that the rent is not paid. The pruning described here is a light form of pruning, since it only removes the validation code. As with all parachains, the parachain or para manager can use the deregister extrinsic to remove all associated state.","breadcrumbs":"RFC-0044: Rent based registration model » On-demand parachain pruning","id":"815","title":"On-demand parachain pruning"},"816":{"body":"The paras pallet will be loosely coupled with the para-registrar pallet. This approach enables all the pallets tightly coupled with the paras pallet to have access to the rent status information. Once the validation code is stored without having its rent paid the assigner_on_demand pallet will ensure that an order for that parachain cannot be placed. This is easily achievable given that the assigner_on_demand pallet is tightly coupled with the paras pallet.","breadcrumbs":"RFC-0044: Rent based registration model » Ensuring rent is paid","id":"816","title":"Ensuring rent is paid"},"817":{"body":"If the rent isn't paid on time, and the parachain gets pruned, the new model should provide a quick way to re-register the same validation code under the same ParaId. This can be achieved by skipping the pre-checking process, as the validation code hash will be stored on-chain, allowing us to easily verify that the uploaded code remains unchanged. /// Stores the validation code hash for parachains that successfully completed the /// pre-checking process.\n///\n/// This is stored to enable faster on-demand para re-registration in case its pvf has been earlier\n/// registered and checked.\n///\n/// NOTE: During a runtime upgrade where the pre-checking rules change this storage map should be\n/// cleared appropriately.\n#[pallet::storage]\npub(super) type CheckedCodeHash = StorageMap<_, Twox64Concat, ParaId, ValidationCodeHash>; To enable parachain re-registration, we should introduce a new extrinsic in the paras-registrar pallet that allows this. The logic of this extrinsic will be same as regular registration, with the distinction that it can be called by anyone, and the required deposit will be smaller since it only has to cover for the storage of the validation code.","breadcrumbs":"RFC-0044: Rent based registration model » On-demand para re-registration","id":"817","title":"On-demand para re-registration"},"818":{"body":"This RFC does not alter the process of reserving a ParaId, and therefore, it does not propose reducing it, even though such a reduction could be beneficial. Even though this RFC doesn't delve into the specifics of the configuration values for parachain registration but rather focuses on the mechanism, configuring it carelessly could lead to potential problems. Since the validation code hash and head data are not removed when the parachain is pruned but only when the deregister extrinsic is called, the T::DataDepositPerByte must be set to a higher value to create a strong enough incentive for removing it from the state.","breadcrumbs":"RFC-0044: Rent based registration model » Drawbacks","id":"818","title":"Drawbacks"},"819":{"body":"The implementation of this RFC will be tested on Rococo first. Proper research should be conducted on setting the configuration values of the new system since these values can have great impact on the network. An audit is required to ensure the implementation's correctness. The proposal introduces no new privacy concerns.","breadcrumbs":"RFC-0044: Rent based registration model » Testing, Security, and Privacy","id":"819","title":"Testing, Security, and Privacy"},"82":{"body":"Runtime Users, Runtime Devs, wallets, cross-chain dApps.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Stakeholders","id":"82","title":"Stakeholders"},"820":{"body":"","breadcrumbs":"RFC-0044: Rent based registration model » Performance, Ergonomics, and Compatibility","id":"820","title":"Performance, Ergonomics, and Compatibility"},"821":{"body":"This RFC should not introduce any performance impact.","breadcrumbs":"RFC-0044: Rent based registration model » Performance","id":"821","title":"Performance"},"822":{"body":"This RFC does not affect the current parachains, nor the parachains that intend to use the one-time payment model for parachain registration.","breadcrumbs":"RFC-0044: Rent based registration model » Ergonomics","id":"822","title":"Ergonomics"},"823":{"body":"This RFC does not break compatibility.","breadcrumbs":"RFC-0044: Rent based registration model » Compatibility","id":"823","title":"Compatibility"},"824":{"body":"Prior discussion on this topic: https://github.com/paritytech/polkadot-sdk/issues/1796","breadcrumbs":"RFC-0044: Rent based registration model » Prior Art and References","id":"824","title":"Prior Art and References"},"825":{"body":"None at this time.","breadcrumbs":"RFC-0044: Rent based registration model » Unresolved Questions","id":"825","title":"Unresolved Questions"},"826":{"body":"As noted in this GitHub issue , we want to raise the per-byte cost of on-chain data storage. However, a substantial increase in this cost would make it highly impractical for on-demand parachains to register on Polkadot. This RFC offers an alternative solution for on-demand parachains, ensuring that the per-byte cost increase doesn't overly burden the registration process.","breadcrumbs":"RFC-0044: Rent based registration model » Future Directions and Related Material","id":"826","title":"Future Directions and Related Material"},"827":{"body":"(source) Table of Contents RFC-0054: Remove the concept of \"heap pages\" from the client Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-11-24 Description Remove the concept of heap pages from the client and move it to the runtime. Authors Pierre Krieger","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » RFC-0054: Remove the concept of \"heap pages\" from the client","id":"827","title":"RFC-0054: Remove the concept of \"heap pages\" from the client"},"828":{"body":"Rather than enforce a limit to the total memory consumption on the client side by loading the value at :heappages, enforce that limit on the runtime side.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Summary","id":"828","title":"Summary"},"829":{"body":"From the early days of Substrate up until recently, the runtime was present in two forms: the wasm runtime (wasm bytecode passed through an interpreter) and the native runtime (native code directly run by the client). Since the wasm runtime has a lower amount of available memory (4 GiB maximum) compared to the native runtime, and in order to ensure sure that the wasm and native runtimes always produce the same outcome, it was necessary to clamp the amount of memory available to both runtimes to the same value. In order to achieve this, a special storage key (a \"well-known\" key) :heappages was introduced and represents the number of \"wasm pages\" (one page equals 64kiB) of memory that are available to the memory allocator of the runtimes. If this storage key is absent, it defaults to 2048, which is 128 MiB. The native runtime has since then been disappeared, but the concept of \"heap pages\" still exists. This RFC proposes a simplification to the design of Polkadot by removing the concept of \"heap pages\" as is currently known, and proposes alternative ways to achieve the goal of limiting the amount of memory available.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Motivation","id":"829","title":"Motivation"},"83":{"body":"One possible solution is to allow a proxy to create or replicate a pure proxy relationship for the same pure account on a target chain. For example, Alice, as the proxy of the pure1 pure account on parachain A, should be able to set a proxy for the same pure1 account on parachain B. To minimise security risks, the parachain B should grant the parachain A the least amount of permission necessary for the replication. First, Parachain A claims to Parachain B that the operation is commanded by the pure account, and thus by its proxy, and second, provides proof that the account is keyless. The replication process will be facilitated by XCM, with the first claim made using the DescendOrigin instruction. The replication call on parachain A would require a signed origin by the pure account and construct an XCM program for parachain B, where it first descends the origin, resulting in the ParachainA/AccountId32(pure1) origin location on the receiving side. To prove that the pure account is keyless, the client must provide the initial preimage used by the chain to derive the pure account. Parachain A verifies it and sends it to parachain B with the replication request. We can draft a pallet extension for the proxy pallet, which needs to be initialised on both sides to enable replication: // Simplified version to illustrate the concept.\nmod pallet_proxy_replica { /// The part of the pure account preimage that has to be provided by a client. struct Witness { /// Pure proxy swapner spawner: AccountId, /// Disambiguation index index: u16, /// The block height and extrinsic index of when the pure account was created. block_number: BlockNumber, /// The extrinsic index. ext_index: u32, // Part of the preimage, but constant. // proxy_type: ProxyType::Any, } // ... /// The replication call to be initiated on the source chain. // Simplified version, the XCM part will be abstracted by the `Config` trait. fn replicate(origin: SignedOrigin, witness: Witness, proxy: xcm::Location) -> ... { let pure = ensure_signed(origin); ensure!(pure == proxy_pallet::derive_pure_account(witness), Error::NotPureAccount); let xcm = vec![ DescendOrigin(who), Transact( // … origin_kind: OriginKind::Xcm, call: pallet_proxy_replica::create(witness, proxy).encode(), ) ]; xcmTransport::send(xcm)?; } // … /// The call initiated by the source chain on the receiving chain. // `Config::CreateOrigin` - generally open for whitelisted parachain IDs and // converts `Origin::Xcm(ParachainA/AccountId32(pure1))` to `AccountID(pure1)`. fn create(origin: Config::CreateOrigin, witness: Witness, proxy: xcm::Location) -> ... { let pure = T::CreateOrigin::ensure_origin(origin); ensure!(pure == proxy_pallet::derive_pure_account(witness), Error::NotPureAccount); proxy_pallet::create_pure_proxy(pure, proxy); }\n}","breadcrumbs":"RFC-0111: Pure Proxy Replication » Explanation","id":"83","title":"Explanation"},"830":{"body":"Client implementers and low-level runtime developers.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Stakeholders","id":"830","title":"Stakeholders"},"831":{"body":"This RFC proposes the following changes to the client: The client no longer considers :heappages as special. The memory allocator of the runtime is no longer bounded by the value of :heappages. With these changes, the memory available to the runtime is now only bounded by the available memory space (4 GiB), and optionally by the maximum amount of memory specified in the Wasm binary (see https://webassembly.github.io/spec/core/bikeshed/#memories%E2%91%A0). In Rust, the latter can be controlled during compilation with the flag -Clink-arg=--max-memory=.... Since the client-side change is strictly more tolerant than before, we can perform the change immediately after the runtime has been updated, and without having to worry about backwards compatibility. This RFC proposes three alternative paths (different chains might choose to follow different paths): Path A: add back the same memory limit to the runtime, like so: At initialization, the runtime loads the value of :heappages from the storage (using ext_storage_get or similar), and sets a global variable to the decoded value. The runtime tracks the total amount of memory that it has allocated using its instance of #[global_allocator] (https://github.com/paritytech/polkadot-sdk/blob/e3242d2c1e2018395c218357046cc88caaed78f3/substrate/primitives/io/src/lib.rs#L1748-L1762). This tracking should also be added around the host functions that perform allocations. If an allocation is attempted that would go over the value in the global variable, the memory allocation fails. Path B: define the memory limit using the -Clink-arg=--max-memory=... flag. Path C: don't add anything to the runtime. This is effectively the same as setting the memory limit to ~4 GiB (compared to the current default limit of 128 MiB). This solution is viable only because we're compiling for 32bits wasm rather than for example 64bits wasm. If we ever compile for 64bits wasm, this would need to be revisited. Each parachain can choose the option that they prefer, but the author of this RFC strongly suggests either option C or B.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Explanation","id":"831","title":"Explanation"},"832":{"body":"In case of path A, there is one situation where the behaviour pre-RFC is not equivalent to the one post-RFC: when a host function that performs an allocation (for example ext_storage_get) is called, without this RFC this allocation might fail due to reaching the maximum heap pages, while after this RFC this will always succeed. This is most likely not a problem, as storage values aren't supposed to be larger than a few megabytes at the very maximum. In the unfortunate event where the runtime runs out of memory, path B would make it more difficult to relax the memory limit, as we would need to re-upload the entire Wasm, compared to updating only :heappages in path A or before this RFC. In the case where the runtime runs out of memory only in the specific event where the Wasm runtime is modified, this could brick the chain. However, this situation is no different than the thousands of other ways that a bug in the runtime can brick a chain, and there's no reason to be particularily worried about this situation in particular.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Drawbacks","id":"832","title":"Drawbacks"},"833":{"body":"This RFC would reduce the chance of a consensus issue between clients. The :heappages are a rather obscure feature, and it is not clear what happens in some corner cases such as the value being too large (error? clamp?) or malformed. This RFC would completely erase these questions.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Testing, Security, and Privacy","id":"833","title":"Testing, Security, and Privacy"},"834":{"body":"","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Performance, Ergonomics, and Compatibility","id":"834","title":"Performance, Ergonomics, and Compatibility"},"835":{"body":"In case of path A, it is unclear how performances would be affected. Path A consists in moving client-side operations to the runtime without changing these operations, and as such performance differences are expected to be minimal. Overall, we're talking about one addition/subtraction per malloc and per free, so this is more than likely completely negligible. In case of path B and C, the performance gain would be a net positive, as this RFC strictly removes things.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Performance","id":"835","title":"Performance"},"836":{"body":"This RFC would isolate the client and runtime more from each other, making it a bit easier to reason about the client or the runtime in isolation.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Ergonomics","id":"836","title":"Ergonomics"},"837":{"body":"Not a breaking change. The runtime-side changes can be applied immediately (without even having to wait for changes in the client), then as soon as the runtime is updated, the client can be updated without any transition period. One can even consider updating the client before the runtime, as it corresponds to path C.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Compatibility","id":"837","title":"Compatibility"},"838":{"body":"None.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Prior Art and References","id":"838","title":"Prior Art and References"},"839":{"body":"None.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Unresolved Questions","id":"839","title":"Unresolved Questions"},"84":{"body":"There are two disadvantages to this approach: The receiving chain has to trust the sending chain's claim that the account controlling the pure account has commanded the replication. Clients must obtain witness data. We could eliminate the first disadvantage by allowing only the spawner of the pure proxy to recreate the pure proxies, if they sign the transaction on a remote chain and supply the witness/preimage. Since the preimage of a pure account includes the account ID of the spawner, we can verify that the account signing the transaction is indeed the spawner of the given pure account. However, this approach would grant exclusive rights to the spawner over the pure account, which is not a property of pure proxies at present. This is why it's not an option for us. As an alternative to requiring clients to provide a witness data, we could label pure accounts on the source chain and trust it on the receiving chain. However, this would require the receiving chain to place greater trust in the source chain. If the source chain is compromised, any type of account on the trusting chain could also be compromised. A conceptually different solution would be to not implement replication of pure proxies and instead inform users that ownership of a pure proxy on one chain does not imply ownership of the same account on another chain. This solution seems complex, as it would require UIs and clients to adapt to this understanding. Moreover, mistakes would likely remain unavoidable.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Drawbacks","id":"84","title":"Drawbacks"},"840":{"body":"This RFC follows the same path as https://github.com/polkadot-fellows/RFCs/pull/4 by scoping everything related to memory allocations to the runtime.","breadcrumbs":"RFC-0054: Remove the concept of \"heap pages\" from the client » Future Directions and Related Material","id":"840","title":"Future Directions and Related Material"},"841":{"body":"(source) Table of Contents RFC-0070: X Track for @kusamanetwork Summary Motivation Stakeholders Explanation Phase 1 - Track configurations Phase 2 - Establish Specs for X Post Track Referenda Phase 3 - Release, Tooling, & Documentation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility References Unresolved Questions Start Date January 29, 2024 Description Add a governance track to facilitate posts on the @kusamanetwork's X account Author Adam Clay Steeber","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » RFC-0070: X Track for @kusamanetwork","id":"841","title":"RFC-0070: X Track for @kusamanetwork"},"842":{"body":"This RFC proposes adding a trivial governance track on Kusama to facilitate X (formerly known as Twitter) posts on the @kusamanetwork account. The technical aspect of implementing this in the runtime is very inconsequential and straight-forward, though it might get more technical if the Fellowship wants to regulate this track with a non-existent permission set. If this is implemented it would need to be followed up with: the establishment of specifications for proposing X posts via this track, and the development of tools/processes to ensure that the content contained in referenda enacted in this track would be automatically posted on X.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Summary","id":"842","title":"Summary"},"843":{"body":"The overall motivation for this RFC is to decentralize the management of the Kusama brand/communication channel to KSM holders. This is necessary in my opinion primarily because of the inactivity of the account in recent history, with posts spanning weeks or months apart. I am currently unaware of who/what entity manages the Kusama X account, but if they are affiliated with Parity or W3F this proposed solution could also offload some of the legal ramifications of making (or not making) announcements to the public regarding Kusama. While centralized control of the X account would still be present, it could become totally moot if this RFC is implemented and the community becomes totally autonomous in the management of Kusama's X posts. This solution does not cover every single communication front for Kusama, but it does cover one of the largest. It also establishes a precedent for other communication channels that could be offloaded to openGov, provided this proof-of-concept is successful. Finally, this RFC is the epitome of experimentation that Kusama is ideal for. This proposal may spark newfound excitement for Kusama and help us realize Kusama's potential for pushing boundaries and trying new unconventional ideas.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Motivation","id":"843","title":"Motivation"},"844":{"body":"This idea has not been formalized by any individual (or group of) KSM holder(s). To my knowledge the socialization of this idea is contained entirely in my recent X post here , but it is possible that an idea like this one has been discussed in other places. It appears to me that the ecosystem would welcome a change like this which is why I am taking action to formalize the discussion.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Stakeholders","id":"844","title":"Stakeholders"},"845":{"body":"The implementation of this idea can be broken down into 3 primary phases:","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Explanation","id":"845","title":"Explanation"},"846":{"body":"First, we begin with this RFC to ensure all feedback can be discussed and implemented in the proposal. After the Fellowship and the community come to a reasonable agreement on the changes necessary to make this happen, the Fellowship can merge changes into Kusama's runtime to include this new track with appropriate track configurations. As a starting point, I recommend the following track configurations: const APP_X_POST: Curve = Curve::make_linear(7, 28, percent(50), percent(100));\nconst SUP_X_POST: Curve = Curve::make_reciprocal(?, ?, percent(?), percent(?), percent(?)); // I don't know how to configure the make_reciprocal variables to get what I imagine for support,\n// but I recommend starting at 50% support and sharply decreasing such that 1% is sufficient quarterway\n// through the decision period and hitting 0% at the end of the decision period, or something like that. ( 69, pallet_referenda::TrackInfo { name: \"x_post\", max_deciding: 50, decision_deposit: 1 * UNIT, prepare_period: 10 * MINUTES, decision_period: 4 * DAYS, confirm_period: 10 * MINUTES, min_enactment_period: 1 * MINUTES, min_approval: APP_X_POST, min_support: SUP_X_POST, }, ), I also recommend restricting permissions of this track to only submitting remarks or batches of remarks - that's all we'll need for its purpose. I'm not sure how easy that is to configure, but it is important since we don't want such an agile track to be able to make highly consequential calls.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Phase 1 - Track configurations","id":"846","title":"Phase 1 - Track configurations"},"847":{"body":"It is important that we establish the specifications of referenda that will be submitted in this track to ensure that whatever automation tool is built can easily make posts once a referendum is enacted. As stated above, we really only need a system.remark (or batch of remarks) to indicate the contents of a proposed X post. The most straight-forward way to do this is to require remarks to adhere to X's requirements for making posts via their API . For example, if I wanted to propose a post that contained the text \"Hello World!\" I would propose a referendum in the X post track that contains the following call data: 0x0000607b2274657874223a202248656c6c6f20576f726c6421227d (i.e. system.remark('{\"text\": \"Hello World!\"}')). At first, we could support text posts only to prove the concept. Later on we could expand this spec to add support for media, likes, retweets, replies, polls, and whatever other X features we want.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Phase 2 - Establish Specs for X Post Track Referenda","id":"847","title":"Phase 2 - Establish Specs for X Post Track Referenda"},"848":{"body":"Once we agree on track configurations and specs for referenda in this track, the Fellowship can move forward with merging these changes into Kusama's runtime and include them in its next release. We could also move forward with developing the necessary tools that would listen for enacted referenda to post automatically on X. This would require coordination with whoever controls the X account; they would either need to run the tools themselves or add a third party as an authorized user to run the tools to make posts on the account's behalf. This is a bottleneck for decentralization, but as long as the tools are run by the X account manager or by a trusted third party it should be fine. I'm open to more decentralized solutions, but those always come at a cost of complexity. For the tools themselves, we could open a bounty on Kusama for developers/teams to bid on. We could also just ask the community to step up with a Treasury proposal to have anyone fund the build. Or, the Fellowship could make the release of these changes contingent on their endorsement of developers/teams to build these tools. Lots of options! For the record, me and my team could develop all the necessary tools, but all because I'm proposing these changes doesn't entitle me to funds to build the tools needed to implement them. Here's what would be needed: a listener tool that would listen for enacted referenda in this track, verify the format of the remark(s), and submit to X's API with authenticating credentials a UI to allow layman users to propose referenda on this track After everything is complete, we can update the Kusama wiki to include documentation on the X post specifications and include links to the tools/UI.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Phase 3 - Release, Tooling, & Documentation","id":"848","title":"Phase 3 - Release, Tooling, & Documentation"},"849":{"body":"The main drawback to this change is that it requires a lot of off-chain coordination. It's easy enough to include the track on Kusama but it's a totally different challenge to make it function as intended. The tools need to be built and the auth tokens need to be managed. It would certainly add an administrative burden to whoever manages the X account since they would either need to run the tools themselves or manage auth tokens. This change also introduces on-going costs to the Treasury since it would need to compensate people to support the tools necessary to facilitate this idea. The ultimate question is whether these on-going costs would be worth the ability for KSM holders to make posts on Kusama's X account. There's also the risk of misconfiguring the track to make referenda too easy to pass, potentially allowing a malicious actor to get content posted on X that violates X's ToS. If that happens, we risk getting Kusama banned on X! This change might also be outside the scope of the Fellowship/openGov. Perhaps the best solution for the X account is to have the Treasury pay for a professional agency to manage posts. It wouldn't be decentralized but it would probably be more effective in terms of creating good content. Finally, this solution is merely pseudo-decentralization since the X account manager would still have ultimate control of the account. It's decentralized insofar as the auth tokens are given to people actually running the tools; a house of cards is required to facilitate X posts via this track. Not ideal.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Drawbacks","id":"849","title":"Drawbacks"},"85":{"body":"Each chain expressly authorizes another chain to replicate its pure proxies, accepting the inherent risk of that chain potentially being compromised. This authorization allows a malicious actor from the compromised chain to take control of any pure proxy account on the chain that granted the authorization. However, this is limited to pure proxies that originated from the compromised chain if they have a chain-specific seed within the preimage. There is a security issue, not introduced by the proposed solution but worth mentioning. The same spawner can create the pure accounts on different chains controlled by the different accounts. This is possible because the current preimage version of the proxy pallet does not include any non-reproducible, chain-specific data, and elements like block numbers and extrinsic indexes can be reproduced with some effort. This issue could be addressed by adding a chain-specific seed into the preimages of pure accounts.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Testing, Security, and Privacy","id":"85","title":"Testing, Security, and Privacy"},"850":{"body":"There's major precedent for configuring tracks on openGov given the amount of power tracks have, so it shouldn't be hard to come up with a sound configuration. That's why I recommend restricting permissions of this track to remarks and batches of remarks, or something equally inconsequential. Building the tools for this implementation is really straight-forward and could be audited by Fellowship members, and the community at large, on Github. The largest security concern would be the management of Kusama's X account's auth tokens. We would need to ensure that they aren't compromised.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Testing, Security, and Privacy","id":"850","title":"Testing, Security, and Privacy"},"851":{"body":"","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Performance, Ergonomics, and Compatibility","id":"851","title":"Performance, Ergonomics, and Compatibility"},"852":{"body":"If a track on Kusama promises users that compliant referenda enacted therein would be posted on Kusama's X account, users would expect that track to perform as promised. If the house of cards tumbles down and a compliant referendum doesn't actually get anything posted, users might think that Kusama is broken or unreliable. This could be damaging to Kusama's image and cause people to question the soundness of other features on Kusama. As mentioned in the drawbacks, the performance of this feature would depend on off-chain coordinations. We can reduce the administrative burden of these coordinations by funding third parties with the Treasury to deal with it, but then we're relying on trusting these parties.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Performance","id":"852","title":"Performance"},"853":{"body":"By adding a new track to Kusama, governance platforms like Polkassembly or Nova Wallet would need to include it on their applications. This shouldn't be too much of a burden or overhead since they've already built the infrastructure for other openGov tracks.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Ergonomics","id":"853","title":"Ergonomics"},"854":{"body":"This change wouldn't break any compatibility as far as I know.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Compatibility","id":"854","title":"Compatibility"},"855":{"body":"One reference to a similar feature requiring on-chain/off-chain coordination would be the Kappa-Sigma-Mu Society. Nothing on-chain necessarily enforces the rules or facilitates bids, challenges, defenses, etc. However, the Society has managed to maintain itself with integrity to its rules. So I don't think this is totally out of Kusama's scope. But it will require some off-chain effort to maintain.","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » References","id":"855","title":"References"},"856":{"body":"Who will develop the tools necessary to implement this feature? How do we select them? How can this idea be better implemented with on-chain/substrate features?","breadcrumbs":"RFC-0070: X Track for @kusamanetwork » Unresolved Questions","id":"856","title":"Unresolved Questions"},"857":{"body":"(source) Table of Contents RFC-0073: Decision Deposit Referendum Track Summary Motivation Explanation Referendum track parameters - Polkadot Referendum track parameters - Kusama Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 12 February 2024 Description Add a referendum track which can place the decision deposit on any other track Authors JelliedOwl","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » RFC-0073: Decision Deposit Referendum Track","id":"857","title":"RFC-0073: Decision Deposit Referendum Track"},"858":{"body":"The current size of the decision deposit on some tracks is too high for many proposers. As a result, those needing to use it have to find someone else willing to put up the deposit for them - and a number of legitimate attempts to use the root track have timed out. This track would provide a more affordable (though slower) route for these holders to use the root track.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Summary","id":"858","title":"Summary"},"859":{"body":"There have been recent attempts to use the Kusama root track which have timed out with no decision deposit placed. Usually, these referenda have been related to parachain registration related issues.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Motivation","id":"859","title":"Motivation"},"86":{"body":"","breadcrumbs":"RFC-0111: Pure Proxy Replication » Performance, Ergonomics, and Compatibility","id":"86","title":"Performance, Ergonomics, and Compatibility"},"860":{"body":"Propose to address this by adding a new referendum track [22] Referendum Deposit which can place the decision deposit on another referendum. This would require the following changes: [Referenda Pallet] Modify the placeDecisionDesposit function to additionally allow it to be called by root, with root call bypassing the requirements for a deposit payment. [Runtime] Add a new referendum track which can only call referenda->placeDecisionDeposit and the utility functions.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Explanation","id":"860","title":"Explanation"},"861":{"body":"Decision deposit : 1000 DOT Decision period : 14 days Confirmation period : 12 hours Enactment period : 2 hour Approval & Support curves : As per the root track, timed to match the decision period Maximum deciding : 10","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Referendum track parameters - Polkadot","id":"861","title":"Referendum track parameters - Polkadot"},"862":{"body":"Decision deposit : 33.333333 KSM Decision period : 7 days Confirmation period : 6 hours Enactment period : 1 hour Approval & Support curves : As per the root track, timed to match the decision period Maximum deciding : 10","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Referendum track parameters - Kusama","id":"862","title":"Referendum track parameters - Kusama"},"863":{"body":"This track would provide a route to starting a root referendum with a much-reduced slashable deposit. This might be undesirable but, assuming the decision deposit cost for this track is still high enough, slashing would still act as a disincentive. An alternative to this might be to reduce the decision deposit size some of the more expensive tracks. However, part of the purpose of the high deposit - at least on the root track - is to prevent spamming the limited queue with junk referenda.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Drawbacks","id":"863","title":"Drawbacks"},"864":{"body":"Will need additional tests case for the modified pallet and runtime. No security or privacy issues.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Testing, Security, and Privacy","id":"864","title":"Testing, Security, and Privacy"},"865":{"body":"","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Performance, Ergonomics, and Compatibility","id":"865","title":"Performance, Ergonomics, and Compatibility"},"866":{"body":"No significant performance impact.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Performance","id":"866","title":"Performance"},"867":{"body":"Only changes related to adding the track. Existing functionality is unchanged.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Ergonomics","id":"867","title":"Ergonomics"},"868":{"body":"No compatibility issues.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Compatibility","id":"868","title":"Compatibility"},"869":{"body":"Recent discussion / referendum for an alternative way to address this issue: Kusama Referendum 340 - Funding a Decision Deposit Sponsor","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Prior Art and References","id":"869","title":"Prior Art and References"},"87":{"body":"The replication is facilitated by XCM, which adds some additional load to the communication channel. However, since the number of replications is not expected to be large, the impact is minimal.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Performance","id":"87","title":"Performance"},"870":{"body":"Feedback on whether my proposed implementation of this is the best way to address the issue - including which calls the track should be allowed to make. Are the track parameters correct or should be use something different? Alternative would be welcome.","breadcrumbs":"RFC-0073: Decision Deposit Referendum Track » Unresolved Questions","id":"870","title":"Unresolved Questions"},"871":{"body":"(source) Table of Contents RFC-0074: Stateful Multisig Pallet Summary Motivation Problem Requirements Use Cases Stakeholders Explanation State Transition Functions Storage/State Considerations & Edge cases Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 15 February 2024 Description Add Enhanced Multisig Pallet to System chains Authors Abdelrahman Soliman (Boda)","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » RFC-0074: Stateful Multisig Pallet","id":"871","title":"RFC-0074: Stateful Multisig Pallet"},"872":{"body":"A pallet to facilitate enhanced multisig accounts. The main enhancement is that we store a multisig account in the state with related info (signers, threshold,..etc). The module affords enhanced control over administrative operations such as adding/removing signers, changing the threshold, account deletion, canceling an existing proposal. Each signer can approve/reject a proposal while still exists. The proposal is not intended for migrating or getting rid of existing multisig. It's to allow both options to coexist. For the rest of the RFC We use the following terms: proposal to refer to an extrinsic that is to be dispatched from a multisig account after getting enough approvals. Stateful Multisig to refer to the proposed pallet. Stateless Multisig to refer to the current multisig pallet in polkadot-sdk.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Summary","id":"872","title":"Summary"},"873":{"body":"","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Motivation","id":"873","title":"Motivation"},"874":{"body":"Entities in the Polkadot ecosystem need to have a way to manage their funds and other operations in a secure and efficient way. Multisig accounts are a common way to achieve this. Entities by definition change over time, members of the entity may change, threshold requirements may change, and the multisig account may need to be deleted. For even more enhanced hierarchical control, the multisig account may need to be controlled by other multisig accounts. Current native solutions for multisig operations are less optimal, performance-wise (as we'll explain later in the RFC), and lack fine-grained control over the multisig account. Stateless Multisig We refer to current multisig pallet in polkadot-sdk because the multisig account is only derived and not stored in the state. Although deriving the account is determinsitc as it relies on exact users (sorted) and thershold to derive it. This does not allow for control over the multisig account. It's also tightly coupled to exact users and threshold. This makes it hard for an organization to manage existing accounts and to change the threshold or add/remove signers. We believe as well that the stateless multisig is not efficient in terms of block footprint as we'll show in the performance section. Pure Proxy Pure proxy can achieve having a stored and determinstic multisig account from different users but it's unneeded complexity as a way around the limitations of the current multisig pallet. It doesn't also have the same fine grained control over the multisig account. Other points mentioned by @tbaut pure proxies aren't (yet) a thing cross chain the end user complexity is much much higher with pure proxies, also for new users smart contract multisig are widely known while pure proxies are obscure. you can shoot yourself in the foot by deleting the proxy, and effectively loosing access to funds with pure proxies.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Problem","id":"874","title":"Problem"},"875":{"body":"Basic requirements for the Stateful Multisig are: The ability to have concrete and permanent (unless deleted) multisig accounts in the state. The ability to add/remove signers from an existing multisig account by the multisig itself. The ability to change the threshold of an existing multisig account by the multisig itself. The ability to delete an existing multisig account by the multisig itself. The ability to cancel an existing proposal by the multisig itself. Signers of multisig account can start a proposal on behalf of the multisig account which will be dispatched after getting enough approvals. Signers of multisig account can approve/reject a proposal while still exists.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Requirements","id":"875","title":"Requirements"},"876":{"body":"Corporate Governance: In a corporate setting, multisig accounts can be employed for decision-making processes. For example, a company may require the approval of multiple executives to initiate significant financial transactions. Joint Accounts: Multisig accounts can be used for joint accounts where multiple individuals need to authorize transactions. This is particularly useful in family finances or shared business accounts. Decentralized Autonomous Organizations (DAOs): DAOs can utilize multisig accounts to ensure that decisions are made collectively. Multiple key holders can be required to approve changes to the organization's rules or the allocation of funds. and much more...","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Use Cases","id":"876","title":"Use Cases"},"877":{"body":"Polkadot holders Polkadot developers","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Stakeholders","id":"877","title":"Stakeholders"},"878":{"body":"I've created the stateful multisig pallet during my studies in Polkadot Blockchain Academy under supervision from @shawntabrizi and @ank4n. After that, I've enhanced it to be fully functional and this is a draft PR#3300 in polkadot-sdk. I'll list all the details and design decisions in the following sections. Note that the PR is not 1-1 exactly to the current RFC as the RFC is a more polished version of the PR after updating based on the feedback and discussions. Let's start with a sequence diagram to illustrate the main operations of the Stateful Multisig. multisig operations Notes on above diagram: It's a 3 step process to execute a proposal. (Start Proposal --> Approvals --> Execute Proposal) Execute is an explicit extrinsic for a simpler API. It can be optimized to be executed automatically after getting enough approvals. Any user can create a multisig account and they don't need to be part of it. (Alice in the diagram) A proposal is any extrinsic including control extrinsics (e.g. add/remove signer, change threshold,..etc). Any multisig account signer can start a proposal on behalf of the multisig account. (Bob in the diagram) Any multisig account owener can execute proposal if it's approved by enough signers. (Dave in the diagram)","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Explanation","id":"878","title":"Explanation"},"879":{"body":"having the following enum to store the call or the hash: enum CallOrHash { Call(::RuntimeCall), Hash(T::Hash),\n} create_multisig - Create a multisig account with a given threshold and initial signers. (Needs Deposit) /// Creates a new multisig account and attach signers with a threshold to it. /// /// The dispatch origin for this call must be _Signed_. It is expected to be a nomral AccountId and not a /// Multisig AccountId. /// /// T::BaseCreationDeposit + T::PerSignerDeposit * signers.len() will be held from the caller's account. /// /// # Arguments /// /// - `signers`: Initial set of accounts to add to the multisig. These may be updated later via `add_signer` /// and `remove_signer`. /// - `threshold`: The threshold number of accounts required to approve an action. Must be greater than 0 and /// less than or equal to the total number of signers. /// /// # Errors /// /// * `TooManySignatories` - The number of signatories exceeds the maximum allowed. /// * `InvalidThreshold` - The threshold is greater than the total number of signers. pub fn create_multisig( origin: OriginFor, signers: BoundedBTreeSet, threshold: u32, ) -> DispatchResult start_proposal - Start a multisig proposal. (Needs Deposit) /// Starts a new proposal for a dispatchable call for a multisig account. /// The caller must be one of the signers of the multisig account. /// T::ProposalDeposit will be held from the caller's account. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// * `call_or_hash` - The enum having the call or the hash of the call to be approved and executed later. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `UnAuthorizedSigner` - The caller is not an signer of the multisig account. /// * `TooManySignatories` - The number of signatories exceeds the maximum allowed. (shouldn't really happen as it's the first approval) pub fn start_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) -> DispatchResult approve - Approve a multisig proposal. /// Approves a proposal for a dispatchable call for a multisig account. /// The caller must be one of the signers of the multisig account. /// /// If a signer did approve -> reject -> approve, the proposal will be approved. /// If a signer did approve -> reject, the proposal will be rejected. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// * `call_or_hash` - The enum having the call or the hash of the call to be approved. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `UnAuthorizedSigner` - The caller is not an signer of the multisig account. /// * `TooManySignatories` - The number of signatories exceeds the maximum allowed. /// This shouldn't really happen as it's an approval, not an addition of a new signer. pub fn approve( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) -> DispatchResult reject - Reject a multisig proposal. /// Rejects a proposal for a multisig account. /// The caller must be one of the signers of the multisig account. /// /// Between approving and rejecting, last call wins. /// If a signer did approve -> reject -> approve, the proposal will be approved. /// If a signer did approve -> reject, the proposal will be rejected. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// * `call_or_hash` - The enum having the call or the hash of the call to be rejected. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `UnAuthorizedSigner` - The caller is not an signer of the multisig account. /// * `SignerNotFound` - The caller has not approved the proposal. #[pallet::call_index(3)] #[pallet::weight(Weight::default())] pub fn reject( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) -> DispatchResult execute_proposal - Execute a multisig proposal. (Releases Deposit) /// Executes a proposal for a dispatchable call for a multisig account. /// Poropsal needs to be approved by enough signers (exceeds or equal multisig threshold) before it can be executed. /// The caller must be one of the signers of the multisig account. /// /// This function does an extra check to make sure that all approvers still exist in the multisig account. /// That is to make sure that the multisig account is not compromised by removing an signer during an active proposal. /// /// Once finished, the withheld deposit will be returned to the proposal creator. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// * `call_or_hash` - We should have gotten the RuntimeCall (preimage) and stored it in the proposal by the time the extrinsic is called. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `UnAuthorizedSigner` - The caller is not an signer of the multisig account. /// * `NotEnoughApprovers` - approvers don't exceed the threshold. /// * `ProposalNotFound` - The proposal does not exist. /// * `CallPreImageNotFound` - The proposal doesn't have the preimage of the call in the state. pub fn execute_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) -> DispatchResult cancel_proposal - Cancel a multisig proposal. (Releases Deposit) /// Cancels an existing proposal for a multisig account. /// Poropsal needs to be rejected by enough signers (exceeds or equal multisig threshold) before it can be executed. /// The caller must be one of the signers of the multisig account. /// /// This function does an extra check to make sure that all rejectors still exist in the multisig account. /// That is to make sure that the multisig account is not compromised by removing an signer during an active proposal. /// /// Once finished, the withheld deposit will be returned to the proposal creator./ /// /// # Arguments /// /// * `origin` - The origin multisig account who wants to cancel the proposal. /// * `call_or_hash` - The call or hash of the call to be canceled. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `ProposalNotFound` - The proposal does not exist. pub fn cancel_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash) -> DispatchResult cancel_own_proposal - Cancel a multisig proposal started by the caller in case no other signers approved it yet. (Releases Deposit) /// Cancels an existing proposal for a multisig account Only if the proposal doesn't have approvers other than /// the proposer. /// ///\tThis function needs to be called from a the proposer of the proposal as the origin. /// /// The withheld deposit will be returned to the proposal creator. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// * `call_or_hash` - The hash of the call to be canceled. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `ProposalNotFound` - The proposal does not exist. pub fn cancel_own_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) -> DispatchResult cleanup_proposals - Cleanup proposals of a multisig account. (Releases Deposit) /// Cleanup proposals of a multisig account. This function will iterate over a max limit per extrinsic to ensure /// we don't have unbounded iteration over the proposals. /// /// The withheld deposit will be returned to the proposal creator. /// /// # Arguments /// /// * `multisig_account` - The multisig account ID. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `ProposalNotFound` - The proposal does not exist. pub fn cleanup_proposals( origin: OriginFor, multisig_account: T::AccountId, ) -> DispatchResult Note: Next functions need to be called from the multisig account itself. Deposits are reserved from the multisig account as well. add_signer - Add a new signer to a multisig account. (Needs Deposit) /// Adds a new signer to the multisig account. /// This function needs to be called from a Multisig account as the origin. /// Otherwise it will fail with MultisigNotFound error. /// /// T::PerSignerDeposit will be held from the multisig account. /// /// # Arguments /// /// * `origin` - The origin multisig account who wants to add a new signer to the multisig account. /// * `new_signer` - The AccountId of the new signer to be added. /// * `new_threshold` - The new threshold for the multisig account after adding the new signer. /// /// # Errors /// * `MultisigNotFound` - The multisig account does not exist. /// * `InvalidThreshold` - The threshold is greater than the total number of signers or is zero. /// * `TooManySignatories` - The number of signatories exceeds the maximum allowed. pub fn add_signer( origin: OriginFor, new_signer: T::AccountId, new_threshold: u32, ) -> DispatchResult remove_signer - Remove an signer from a multisig account. (Releases Deposit) /// Removes an signer from the multisig account. /// This function needs to be called from a Multisig account as the origin. /// Otherwise it will fail with MultisigNotFound error. /// If only one signer exists and is removed, the multisig account and any pending proposals for this account will be deleted from the state. /// /// # Arguments /// /// * `origin` - The origin multisig account who wants to remove an signer from the multisig account. /// * `signer_to_remove` - The AccountId of the signer to be removed. /// * `new_threshold` - The new threshold for the multisig account after removing the signer. Accepts zero if /// the signer is the only one left.kkk /// /// # Errors /// /// This function can return the following errors: /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `InvalidThreshold` - The new threshold is greater than the total number of signers or is zero. /// * `UnAuthorizedSigner` - The caller is not an signer of the multisig account. pub fn remove_signer( origin: OriginFor, signer_to_remove: T::AccountId, new_threshold: u32, ) -> DispatchResult set_threshold - Change the threshold of a multisig account. /// Sets a new threshold for a multisig account. ///\tThis function needs to be called from a Multisig account as the origin. /// Otherwise it will fail with MultisigNotFound error. /// /// # Arguments /// /// * `origin` - The origin multisig account who wants to set the new threshold. /// * `new_threshold` - The new threshold to be set. /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. /// * `InvalidThreshold` - The new threshold is greater than the total number of signers or is zero. set_threshold(origin: OriginFor, new_threshold: u32) -> DispatchResult delete_multisig - Delete a multisig account. (Releases Deposit) /// Deletes a multisig account and all related proposals. /// ///\tThis function needs to be called from a Multisig account as the origin. /// Otherwise it will fail with MultisigNotFound error. /// /// # Arguments /// /// * `origin` - The origin multisig account who wants to cancel the proposal. /// /// # Errors /// /// * `MultisigNotFound` - The multisig account does not exist. pub fn delete_account(origin: OriginFor) -> DispatchResult","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » State Transition Functions","id":"879","title":"State Transition Functions"},"88":{"body":"The proposed solution does not alter any existing interfaces. It does require clients to obtain the witness data which should not be an issue with support of an indexer.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Ergonomics","id":"88","title":"Ergonomics"},"880":{"body":"Use 2 main storage maps to store mutlisig accounts and proposals. #[pallet::storage] pub type MultisigAccount = StorageMap<_, Twox64Concat, T::AccountId, MultisigAccountDetails>; /// The set of open multisig proposals. A proposal is uniquely identified by the multisig account and the call hash.\n/// (maybe a nonce as well in the future)\n#[pallet::storage]\npub type PendingProposals = StorageDoubleMap< _, Twox64Concat, T::AccountId, // Multisig Account Blake2_128Concat, T::Hash, // Call Hash MultisigProposal,\n>; As for the values: pub struct MultisigAccountDetails { /// The signers of the multisig account. This is a BoundedBTreeSet to ensure faster operations (add, remove). /// As well as lookups and faster set operations to ensure approvers is always a subset from signers. (e.g. in case of removal of an signer during an active proposal) pub signers: BoundedBTreeSet, /// The threshold of approvers required for the multisig account to be able to execute a call. pub threshold: u32, pub deposit: BalanceOf,\n} pub struct MultisigProposal { /// Proposal creator. pub creator: T::AccountId, pub creation_deposit: BalanceOf, /// The extrinsic when the multisig operation was opened. pub when: Timepoint>, /// The approvers achieved so far, including the depositor. /// The approvers are stored in a BoundedBTreeSet to ensure faster lookup and operations (approve, reject). /// It's also bounded to ensure that the size don't go over the required limit by the Runtime. pub approvers: BoundedBTreeSet, /// The rejectors for the proposal so far. /// The rejectors are stored in a BoundedBTreeSet to ensure faster lookup and operations (approve, reject). /// It's also bounded to ensure that the size don't go over the required limit by the Runtime. pub rejectors: BoundedBTreeSet, /// The block number until which this multisig operation is valid. None means no expiry. pub expire_after: Option>,\n} For optimization we're using BoundedBTreeSet to allow for efficient lookups and removals. Especially in the case of approvers, we need to be able to remove an approver from the list when they reject their approval. (which we do lazily when execute_proposal is called). There's an extra storage map for the deposits of the multisig accounts per signer added. This is to ensure that we can release the deposits when the multisig removes them even if the constant deposit per signer changed in the runtime later on.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Storage/State","id":"880","title":"Storage/State"},"881":{"body":"Removing an signer from the multisig account during an active proposal We need to ensure that the approvers are always a subset from signers. This is also partially why we're using BoundedBTreeSet for signers and approvers. Once execute proposal is called we ensure that the proposal is still valid and the approvers are still a subset from current signers. Multisig account deletion and cleaning up existing proposals Once the last signer of a multisig account is removed or the multisig approved the account deletion we delete the multisig accound from the state and keep the proposals until someone calls cleanup_proposals multiple times which iterates over a max limit per extrinsic. This is to ensure we don't have unbounded iteration over the proposals. Users are already incentivized to call cleanup_proposals to get their deposits back. Multisig account deletion and existing deposits We currently just delete the account without checking for deposits (Would like to hear your thoughts here). We can either Don't make deposits to begin with and make it a fee. Transfer to treasury. Error on deletion. (don't like this) Approving a proposal after the threshold is changed We always use latest threshold and don't store each proposal with different threshold. This allows the following: In case threshold is lower than the number of approvers then the proposal is still valid. In case threshold is higher than the number of approvers then we catch it during execute proposal and error.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Considerations & Edge cases","id":"881","title":"Considerations & Edge cases"},"882":{"body":"New pallet to maintain.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Drawbacks","id":"882","title":"Drawbacks"},"883":{"body":"Standard audit/review requirements apply.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Testing, Security, and Privacy","id":"883","title":"Testing, Security, and Privacy"},"884":{"body":"","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Performance, Ergonomics, and Compatibility","id":"884","title":"Performance, Ergonomics, and Compatibility"},"885":{"body":"Doing back of the envelop calculation to proof that the stateful multisig is more efficient than the stateless multisig given it's smaller footprint size on blocks. Quick review over the extrinsics for both as it affects the block size: Stateless Multisig: Both as_multi and approve_as_multi has a similar parameters: origin: OriginFor,\nthreshold: u16,\nother_signatories: Vec,\nmaybe_timepoint: Option>>,\ncall_hash: [u8; 32],\nmax_weight: Weight, Stateful Multisig: We have the following extrinsics: pub fn start_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) pub fn approve( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) pub fn execute_proposal( origin: OriginFor, multisig_account: T::AccountId, call_or_hash: CallOrHash, ) The main takeway is that we don't need to pass the threshold and other signatories in the extrinsics. This is because we already have the threshold and signatories in the state (only once). So now for the caclulations, given the following: K is the number of multisig accounts. N is number of signers in each multisig account. For each proposal we need to have 2N/3 approvals. The table calculates if each of the K multisig accounts has one proposal and it gets approved by the 2N/3 and then executed. How much did the total Blocks and States sizes increased by the end of the day. Note: We're not calculating the cost of proposal as both in statefull and stateless multisig they're almost the same and gets cleaned up from the state once the proposal is executed or canceled. Stateless effect on blocksizes = 2/3 K N^2 (as each user of the 2/3 users will need to call approve_as_multi with all the other signatories(N) in extrinsic body) Stateful effect on blocksizes = K * N (as each user will need to call approve with the multisig account only in extrinsic body) Stateless effect on statesizes = Nil (as the multisig account is not stored in the state) Stateful effect on statesizes = K*N (as each multisig account (K) will be stored with all the signers (K) in the state) Pallet Block Size State Size Stateless 2/3 K N^2 Nil Stateful K*N K*N Simplified table removing K from the equation: | Pallet | Block Size | State Size | |----------------|:-------------:|-----------:| | Stateless | N^2 | Nil | | Stateful | N | N | So even though the stateful multisig has a larger state size, it's still more efficient in terms of block size and total footprint on the blockchain.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Performance","id":"885","title":"Performance"},"886":{"body":"The Stateful Multisig will have better ergonomics for managing multisig accounts for both developers and end-users.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Ergonomics","id":"886","title":"Ergonomics"},"887":{"body":"This RFC is compatible with the existing implementation and can be handled via upgrades and migration. It's not intended to replace the existing multisig pallet.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Compatibility","id":"887","title":"Compatibility"},"888":{"body":"multisig pallet in polkadot-sdk","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Prior Art and References","id":"888","title":"Prior Art and References"},"889":{"body":"On account deletion, should we transfer remaining deposits to treasury or remove signers' addition deposits completely and consider it as fees to start with?","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Unresolved Questions","id":"889","title":"Unresolved Questions"},"89":{"body":"None.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Compatibility","id":"89","title":"Compatibility"},"890":{"body":"Batch addition/removal of signers. Add expiry to proposals. After a certain time, proposals will not accept any more approvals or executions and will be deleted. Implement call filters. This will allow multisig accounts to only accept certain calls.","breadcrumbs":"RFC-0074: Stateful Multisig Pallet » Future Directions and Related Material","id":"890","title":"Future Directions and Related Material"},"891":{"body":"(source) Table of Contents RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes Summary Motivation Background Problem Solution Requirements Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 20 Feb 2024 Description Increase the maximum length of identity PGP fingerprint values from 20 bytes Authors Luke Schoen","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes","id":"891","title":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes"},"892":{"body":"This proposes to increase the maximum length of PGP Fingerprint values from a 20 bytes/chars limit to a 40 bytes/chars limit.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Summary","id":"892","title":"Summary"},"893":{"body":"","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Motivation","id":"893","title":"Motivation"},"894":{"body":"Pretty Good Privacy (PGP) Fingerprints are shorter versions of their corresponding Public Key that may be printed on a business card. They may be used by someone to validate the correct corresponding Public Key. It should be possible to add PGP Fingerprints to Polkadot on-chain identities. GNU Privacy Guard (GPG) is compliant with PGP and the two acronyms are used interchangeably.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Background","id":"894","title":"Background"},"895":{"body":"If you want to set a Polkadot on-chain identity, users may provide a PGP Fingerprint value in the \"pgpFingerprint\" field, which may be longer than 20 bytes/chars (e.g. PGP Fingerprints are 40 bytes/chars long), however that field can only store a maximum length of 20 bytes/chars of information. Possible disadvantages of the current 20 bytes/chars limitation: Discourages users from using the \"pgpFingerprint\" field. Discourages users from using Polkadot on-chain identities for Web2 and Web3 dApp software releases where the latest \"pgpFingerprint\" field could be used to verify the correct PGP Fingerprint that has been used to sign the software releases so users that download the software know that it was from a trusted source. Encourages dApps to link to Web2 sources to allow their users verify the correct fingerprint associated with software releases, rather than to use the Web3 Polkadot on-chain identity \"pgpFingerprint\" field of the releaser of the software, since it may be the case that the \"pgpFingerprint\" field of most on-chain identities is not widely used due to the maximum length of 20 bytes/chars restriction. Discourages users from setting an on-chain identity by creating an extrinsic using Polkadot.js with identity > setIdentity(info), since if they try to provide their 40 character long PGP Fingerprint or GPG Fingerprint, which is longer than the maximum length of 20 bytes/chars, they will encounter an error. Discourages users from using on-chain Web3 registrars to judge on-chain identity fields, where the shortest value they are able to generate for a \"pgpFingerprint\" is not less than or equal to the maximum length of 20 bytes.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Problem","id":"895","title":"Problem"},"896":{"body":"The maximum length of identity PGP Fingerprint values should be increased from the current 20 bytes/chars limit at least a 40 bytes/chars limit to support PGP Fingerprints and GPG Fingerprints.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Solution Requirements","id":"896","title":"Solution Requirements"},"897":{"body":"Any Polkadot account holder wishing to use a Polkadot on-chain identity for their: PGP Fingerprints that are longer than 32 characters GPG Fingerprints that are longer than 32 characters","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Stakeholders","id":"897","title":"Stakeholders"},"898":{"body":"If a user tries to setting an on-chain identity by creating an extrinsic using Polkadot.js with identity > setIdentity(info), then if they try to provide their 40 character long PGP Fingerprint or GPG Fingerprint, which is longer than the maximum length of 20 bytes/chars [u8;20], then they will encounter this error: createType(Call):: Call: failed decoding identity.setIdentity:: Struct: failed on args: {...}:: Struct: failed on pgpFingerprint: Option<[u8;20]>:: Expected input with 20 bytes (160 bits), found 40 bytes Increasing maximum length of identity PGP Fingerprint values from the current 20 bytes/chars limit to at least a 40 bytes/chars limit would overcome these errors and support PGP Fingerprints and GPG Fingerprints, satisfying the solution requirements.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Explanation","id":"898","title":"Explanation"},"899":{"body":"No drawbacks have been identified.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Drawbacks","id":"899","title":"Drawbacks"},"9":{"body":"The implementations must honor the contract for the new instructions. Namely, if the instance field has the value of AssetInstance::Undefined, the metadata must relate to the asset collection but not to a non-fungible token inside it.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Testing, Security, and Privacy","id":"9","title":"Testing, Security, and Privacy"},"90":{"body":"None.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Prior Art and References","id":"90","title":"Prior Art and References"},"900":{"body":"Implementations would be tested for adherance by checking that 40 bytes/chars PGP Fingerprints are supported. No effect on security or privacy has been identified than already exists. No implementation pitfalls have been identified.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Testing, Security, and Privacy","id":"900","title":"Testing, Security, and Privacy"},"901":{"body":"","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Performance, Ergonomics, and Compatibility","id":"901","title":"Performance, Ergonomics, and Compatibility"},"902":{"body":"It would be an optimization, since the associated exposed interfaces to developers and end-users could start being used. To minimize additional overhead the proposal suggests a 40 bytes/chars limit since that would at least provide support for PGP Fingerprints, satisfying the solution requirements.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Performance","id":"902","title":"Performance"},"903":{"body":"No potential ergonomic optimizations have been identified.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Ergonomics","id":"903","title":"Ergonomics"},"904":{"body":"Updates to Polkadot.js Apps, API and its documentation and those referring to it may be required.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Compatibility","id":"904","title":"Compatibility"},"905":{"body":"No prior articles or references.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Prior Art and References","id":"905","title":"Prior Art and References"},"906":{"body":"No further questions at this stage.","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Unresolved Questions","id":"906","title":"Unresolved Questions"},"907":{"body":"Relates to RFC entitled \"Increase maximum length of identity raw data values from 32 bytes\".","breadcrumbs":"RFC-0077: Increase maximum length of identity PGP fingerprint values from 20 bytes » Future Directions and Related Material","id":"907","title":"Future Directions and Related Material"},"908":{"body":"(source) Table of Contents RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet Summary Motivation Background Problem Solution Requirements Stakeholders Drawbacks Performance Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Prior Art Unresolved Questions Future Directions and Related Material Start Date 25 Apr 2024 Description Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet Authors Luke Schoen","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet","id":"908","title":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet"},"909":{"body":"This proposes to require a slashable deposit in the broker pallet when initially purchasing or renewing Bulk Coretime or Instantaneous Coretime cores. Additionally, it proposes to record a reputational status based on the behavior of the purchaser, as it relates to their use of Kusama Coretime cores that they purchase, and to possibly reserve a proportion of the cores for prospective purchasers that have an on-chain identity.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Summary","id":"909","title":"Summary"},"91":{"body":"None.","breadcrumbs":"RFC-0111: Pure Proxy Replication » Unresolved Questions","id":"91","title":"Unresolved Questions"},"910":{"body":"","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Motivation","id":"910","title":"Motivation"},"911":{"body":"There are sales of Kusama Coretime cores that are scheduled to occur later this month by Coretime Marketplace Lastic.xyz initially in limited quantities, and potentially also by RegionX in future that is subject to their Polkadot referendum #582 . This poses a risk in that some Kusama Coretime core purchasers may buy Kusama Coretime cores when they have no intention of actually placing a workload on them or leasing them out, which would prevent those that wish to purchase and actually use Kusama Coretime cores from being able to use any at cores at all.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Background","id":"911","title":"Background"},"912":{"body":"The types of purchasers may include: Collectors (e.g. purchase a significant core such as the first core that is sold just to increase their likelihood of receiving an NFT airdrop for being one of the first purchasers). Resellers (e.g. purchase a core that may be used at a popular period of time to resell closer to the date to realise a profit) Market makers (e.g. buy cores just to change the floor price or volume). Anti-competitive (e.g. competitor to Polkadot ecosystem purchases cores possibly in violation of anti-trust laws just to restrict access to prospective Kusama Coretime sales cores by the Kusama community that wish to do business in the Polkadot ecosystem). Chaoatic repurcussions could include the following: Generation of \"white elephant\" Kusama Coretime cores, similar to \"white elephant\" properties in the real-estate industry that never actually get used, leased or tenanted. Kusama Coretime core resellers scalping the core time faster than the average core time consumer, and then choosing to use dynamic pricing that causes prices to fluctuate based on demand. Resellers that own the Kusama Coretime scalping organisations may actually turn out to be the Official Kusama Coretime sellers. Official Kusama Coretime sellers may establish a monopoly on the market and abuse that power by charging exhorbitant additional charge fees for each purchase, since they could then increase their floor prices even more, pretending that there are fewer cores available and more demand to make extra profits from their scalping organisations, similar to how it occurred in these concert ticket sales . This could caused Kusama Coretime costs to be no longer be affordable to the Kusama community. Official Kusama Coretime sellers may run pre-sale events, but their websites may not be able to unable to handle the traffic and crash multiple times, causing them to end up cancelling those pre-sales and the pre-sale registrants missing out on getting a core that way, which would then cause available Kusama Coretime cores to be bought and resold at a higher price on third-party sites. The scalping activity may be illegal in some jurisdictions and raise anti-trust issues similar to the Taylor Swift debacle over concert tickets.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Problem","id":"912","title":"Problem"},"913":{"body":"On-chain identity . It may be possible to circumvent bots and scalpers to an extent by requiring a proportion of Kusama Coretime purchasers to have an on-chain identity. As such, a possible solution could be to allow the configuration of a threshold in the Broker pallet that reserves a proportion of the cores for accounts that have an on-chain identity, that reverts to a waiting list of anonymous account purchasers if the reserved proportion of cores remain unsold. Slashable deposit . A viable solution could be to require a slashable deposit to be locked prior to the purchase or renewal of a core, similar to how decision deposits are used in OpenGov to prevent spam, but where if you buy a Kusama Coretime core you could be challenged by one of more collectives of fishermen to provide proof against certain criteria of how you used it, and if you fail to provide adequate evidence in response to that scrutiny, then you would lose a proportion of that deposit and face restrictions on purchasing or renewing cores in future that may also be configured on-chain. Reputation . To disincentivise certain behaviours, a reputational status indicator could be used to record the historic behavior of the purchaser and whether on-chain judgement has determined they have adequately rectified that behaviour, as it relates to their usage of Kusama Coretime cores that they purchase.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Solution Requirements","id":"913","title":"Solution Requirements"},"914":{"body":"Any Kusama account holder wishing to use the Broker pallet in any upcoming Kusama Coretime sales. Any prospective Kusama Coretime purchaser, developer, and user. KSM holders.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Stakeholders","id":"914","title":"Stakeholders"},"915":{"body":"","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Drawbacks","id":"915","title":"Drawbacks"},"916":{"body":"The slashable deposit if set too high, may result in an economic impact, where less Kusama Coretime core sales are purchased.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Performance","id":"916","title":"Performance"},"917":{"body":"Lack of a slashable deposit in the Broker pallet is a security concern, since it exposes Kusama Coretime sales to potential abuse. Reserving a proportion of Kusama Coretime sales cores for those with on-chain identities should not be to the exclusion of accounts that wish to remain anonymous or cause cores to be wasted unnecessarily. As such, if cores that are reserved for on-chain identities remain unsold then they should be released to anonymous accounts that are on a waiting list. No implementation pitfalls have been identified.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Testing, Security, and Privacy","id":"917","title":"Testing, Security, and Privacy"},"918":{"body":"","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Performance, Ergonomics, and Compatibility","id":"918","title":"Performance, Ergonomics, and Compatibility"},"919":{"body":"It should improve performance as it reduces the potential for state bloat since there is less risk of undesirable Kusama Coretime sales activity that would be apparent with no requirement for a slashable deposit or there being no reputational risk to purchasers that waste or misuse Kusama Coretime cores. The solution proposes to minimize the risk of some Kusama Coretime cores not even being used or leased to perform any tasks at all. It will be important to monitor and manage the slashable deposits, purchaser reputations, and utilization of the proportion of cores that are reserved for accounts with an on-chain identity.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Performance","id":"919","title":"Performance"},"92":{"body":"Pure Proxy documentation - https://wiki.polkadot.network/docs/learn-proxies-pure","breadcrumbs":"RFC-0111: Pure Proxy Replication » Future Directions and Related Material","id":"92","title":"Future Directions and Related Material"},"920":{"body":"The mechanism for setting a slashable deposit amount, should avoid undue complexity for users.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Ergonomics","id":"920","title":"Ergonomics"},"921":{"body":"Updates to Polkadot.js Apps, API and its documentation and those referring to it may be required.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Compatibility","id":"921","title":"Compatibility"},"922":{"body":"","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Prior Art and References","id":"922","title":"Prior Art and References"},"923":{"body":"No prior articles.","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Prior Art","id":"923","title":"Prior Art"},"924":{"body":"None","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Unresolved Questions","id":"924","title":"Unresolved Questions"},"925":{"body":"None","breadcrumbs":"RFC-0088: Add slashable locked deposit, purchaser reputation, and reserved cores for on-chain identities to broker pallet » Future Directions and Related Material","id":"925","title":"Future Directions and Related Material"},"926":{"body":"(source) Table of Contents RFC-0089: Flexible Inflation Summary Motivation Stakeholders Explanation Existing Order New Order Proposed Implementation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date May 6 2024 Description Revise the inflation logic in the runtime such that it can be parameterized and tweaked in an easier and more transparent way. Authors Kian Paimani","breadcrumbs":"RFC-0089: Flexible Inflation » RFC-0089: Flexible Inflation","id":"926","title":"RFC-0089: Flexible Inflation"},"927":{"body":"This RFC proposes a new pallet_inflation to be added to the Polkadot runtime, which improves inflation machinery of the Polkadot relay chain in a number of ways: More transparent and easier to understand inflation logic Easier parameterization through governance Decoupled from the staking logic, should inflation and staking happen in two disjoint consensus systems, as proposed RFC32 .","breadcrumbs":"RFC-0089: Flexible Inflation » Summary","id":"927","title":"Summary"},"928":{"body":"The existing inflation logic in the relay chain suffers from a number of drawbacks: It is dated, as the number of parachain slots (and consequently auctions) will soon no longer be a factor in determining the inflation rate. Is hard to parameterize through on-chain governance, as the only way to tweak the inflation amount is through changing a particular function directly in the source code ( example in Polkadot runtime ). Is deeply intertwined with the staking system, which is not an ideal design. For example, if one wishes to know the inflation amount, an Event from the staking system has to be interpreted, which is counter-intuitive. Given all of this complexity, implementing an alteration which suggested a fixed percentage of the inflation to go to the treasury was also not possible in an ergonomic way . This RFC, as iterated above, proposes a new pallet_inflation that addresses all of the named problems. However, this RFC does not propose any changes to the actual inflation rate , but rather provide a new technical substrate (pun intended), upon which token holders can decide on the future of the DOT token's inflation in a more clear and transparent way. We argue that one reason why the inflation rate of Polkadot has not significantly change in ~4 years has been the complicated process of updating it. We hope that with the tools provided in this RFC, stakeholders can experiment with the inflation rate in a more ergonomic way. Finally, this experimentation can be considered useful as a final step toward fixing the economics of DOT in JAM, as proposed in the JAM graypaper. Within the scope of this RFC, we suggest deploying the new inflation pallet in a backwards compatible way, such that the inflation model does not change in practice, and leave the actual changes to the token holders and researchers and further governance proposals. While mainly intended for Polkadot, the system proposed in this RFC is general enough such that it can be interpreted as a \"general inflation system pallet\", and can be used in newly onboarding parachain.","breadcrumbs":"RFC-0089: Flexible Inflation » Motivation","id":"928","title":"Motivation"},"929":{"body":"This RFC is relevant to the following stakeholders, listed from high to low impact: All token holders who participate in governance, as they can possibly now propose (some degree of) changes to the inflation model without any coding required. Depending on the parameters, these changes may or may not require a particular governance track. Validators and all other stakers, as the staking rate of the chain might possibly change through the means that this pallet provides. All other token holders.","breadcrumbs":"RFC-0089: Flexible Inflation » Stakeholders","id":"929","title":"Stakeholders"},"93":{"body":"(source) Table of Contents RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Security Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Start Date 16 August 2024 Description Host function to verify NIST-P256 elliptic curve signatures. Authors Rodrigo Quelhas","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures","id":"93","title":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures"},"930":{"body":"","breadcrumbs":"RFC-0089: Flexible Inflation » Explanation","id":"930","title":"Explanation"},"931":{"body":"First, let's further elaborate on the existing order. The current inflation logic is deeply nested in pallet_staking, and pallet_staking::Config::EraPayout interface. Through this trait, the staking pallet is informed how many new tokens should possibly be minted. This amount is divided into two parts: an amount allocated to staking. This amount is not minted right away, and is instead minted when the staking rewards are paid out. an amount allocated to pallet_staking::Config::RewardRemainder, which is configured to forward the amount to the treasury. As it stands now the implementation of EraPayout which specifies the two amounts above lives in the respective runtime, and uses the original proposed inflation rate proposed by W3F for Polkadot. Read more about this model here . At present, the inflation always happens at the end of an era , which is a concept know by the staking system. The duration of an era is recorded in pallet_staking as milliseconds (as recorded by the standard pallet_timestamp), is passed to EraPayout as an input, as is measured against the full year to determine how much should be inflated.","breadcrumbs":"RFC-0089: Flexible Inflation » Existing Order","id":"931","title":"Existing Order"},"932":{"body":"The naming used in this section is tentative, based on a WIP implementation, and subject to change before finalization of this RFC. The new order splits the process for inflation into two steps: Sourcing the inflation amount: This step merely specifies by how much the chain intends to inflate its token. This amount is not minted right away, and is instead passed over to the next step for distribution . Distributing the aforementioned amount: A sequence of functions that decide what needs to be done with the sourced inflation amount. This process is expected to transfer the inflation amount to any account that should receive it. This implies that the staking system should, similar to treasury, have a key-less account that will act as a temporary pot for the inflation amount. In very abstract terms, an example of the above process can be: The chain inflates its token by a fixed 10% per year, an amount called i. Pay out 20% of i to the treasury account. Pay out 10% of what is left of i to the fellowship account. Pay out up to 70% of what is left of i to staking, depending on the staking rate. Burn anything that is left. A proper configuration of this pallet should use pallet_parameters where possible to allow for any of the actual values used to specify Sourcing and Distribution to be changed via on-chain governance. Please see the example configurations section for more details. In the new model, inflation can happen at any point in time. Since now a new pallet is dedicated to inflation, and it can internally store the timestamp of the last inflation point, and always inflate the correct amount. This means that while the duration of a staking era is 1 day, the inflation process can happen eg. every hour. The opposite is also possible, although more complicated: The staking/treasury system can possibly receive their corresponding income on a weekly basis, while the era duration is still 1 day. That being said, we don't recommend using this flexibility as it brings no clear advantage, and is only extra complexity. We recommend the inflation to still happen shortly before the end of the staking era. This means that if the inflation sourcing or distribution is a function of the staking rate, it can reliably use the staking rate of the last era. Finally, as noted above, this RFC implies a new accounting system for staking to keep track of its staking reward. In short, the new process is as follows: pallet_inflation will mint the staking portion of inflation directly into a key-less account controlled by pallet_staking. At the end of each era, pallet_staking will inspect this account, and move whatever amount is paid out into it to another key-less account associated with the era number. The actual payouts, initiated by stakers, will transfer from this era account into the corresponding stakers' account. Interestingly, this means that any account can possibly contribute to staking rewards by transferring DOTs to the key-less parent account controlled by the staking system.","breadcrumbs":"RFC-0089: Flexible Inflation » New Order","id":"932","title":"New Order"},"933":{"body":"A candidate implementation of this RFC can be found in this branch of the polkadot-sdk repository. Please note the changes to: substrate/frame/inflation to see the new pallet. substrate/frame/staking to see the integration with the staking pallet. substrate/bin/runtime to see how the pallet can be configured into a runtime. Example Configurations The following are working examples from the above implementation candidate, highlighting some of the outcomes that can be achieved. First, to parameterize the existing proposed implementation to replicate what Polkadot does today, assuming we incorporate the fixed 2% treasury income, the outcome would be: parameter_types! { pub Distribution: Vec> = vec![ // 2% goes to treasury, no questions asked. Box::new(pay::), // from whatever is left, staking gets all the rest, based on the staking rate. Box::new(polkadot_staking_income::< Runtime, dynamic_params::staking::IdealStakingRate, dynamic_params::staking::Falloff, StakingIncomeAccount >), // Burn anything that is left. Box::new(burn::), ];\n} impl pallet_inflation::Config for Runtime { /// Fixed 10% annual inflation. type InflationSource = pallet_inflation::FixedRatioAnnualInflation; type Distribution = Distribution;\n} In this snippet, we use a number of components provided by pallet_inflation, namely pay, polkadot_staking_income, burn and FixedRatioAnnualInflation. Yet, crucially, these components are fed parameters that are all backed by an instance of the pallet_parameters, namely everything prefixed by dynamic_params. The above is a purely inflationary system. If one wants to change the inflation to dis-inflationary , another pre-made component of pallet_inflation can be used: impl pallet_inflation::Config for Runtime {\n-\t/// Fixed 10% annual inflation.\n-\ttype InflationSource =\n- pallet_inflation::FixedRatioAnnualInflation;\n+\ttype InflationSource = pallet_inflation::FixedAnnualInflation<\n+ Runtime,\n+ dynamic_params::staking::FixedAnnualInflationAmount,\n+\t>;\n} Whereby FixedAnnualInflationAmount is the fixed absolute value (as opposed to ratio ) by which the chain inflates annually, for example 100m DOTs.","breadcrumbs":"RFC-0089: Flexible Inflation » Proposed Implementation","id":"933","title":"Proposed Implementation"},"934":{"body":"The following drawbacks are noted: The solution provided here is possibly an over-engineering, if we want to achieve the goal of making the existing formula parameterize-able. In that case, we can merely add an instance of the pallet_parameters to the runtime and make the existing formula's ratios be provided by governance-controlled parameters. Although, this shortsighted but simpler solution fails to decouple the staking and inflation logic. This will be an issue depending on whether staking lives in AssetHub, or its independent parachain. Some of the interfaces proposed in the draft implementation still leak the implementation detail of the inflation amount being reliant on eg. the staking-rate. We acknowledge this as a drawback, but given that many PoS inflationary systems rely on the staking rate, we believe it is a reasonable compromise. Such parameters can be ignored if the implementation does not need them.","breadcrumbs":"RFC-0089: Flexible Inflation » Drawbacks","id":"934","title":"Drawbacks"},"935":{"body":"The new pallet_inflation, among its integration into pallet_staking must be thoroughly audited and reviewed by fellows. We also emphasize on simulating the actual inflation logic using the real polkadot state with Chopsticks and try-runtime.","breadcrumbs":"RFC-0089: Flexible Inflation » Testing, Security, and Privacy","id":"935","title":"Testing, Security, and Privacy"},"936":{"body":"The proposed system in this RFC implies a handful of extra storage reads and writes \"per inflation cycle\", but given that a reasonable instance of this pallet would probably decide to inflation eg. once per day, the performance impact is negligible. The drawback section above noted some ergonomic concerns. The \"New Order\" section above notes the compatibility notes with the existing staking and inflation system.","breadcrumbs":"RFC-0089: Flexible Inflation » Performance, Ergonomics, and Compatibility","id":"936","title":"Performance, Ergonomics, and Compatibility"},"937":{"body":"Previous updates to the inflation system: pallet_parameters https://forum.polkadot.network/t/adjusting-the-current-inflation-model-to-sustain-treasury-inflow/3301","breadcrumbs":"RFC-0089: Flexible Inflation » Prior Art and References","id":"937","title":"Prior Art and References"},"938":{"body":"Whether the design proposed in this RFC is worthy of the complexity implementing and integrating it? Note that a draft implementation already exists, yet the amount of further work needed to integrate it is non-negligible. Given that this pallet is general enough to also be used by parachain, the usage of timestamp poses risks with regard to agile-coretime, and parachains that only use on-demand cores. Accurate timestamps must be provided to the pallet in order to function, possibly being sourced from the relay-chain. @ggwpez has explored issues related to on-demand core-time and time-based systems here .","breadcrumbs":"RFC-0089: Flexible Inflation » Unresolved Questions","id":"938","title":"Unresolved Questions"},"939":{"body":"If initial reaction is positive researchers and economic experts should formulate their desired inflation parameters and systems, such that we can be sure the pallet is flexible enough in possibly fulfilling them without an extensive amount of work needed. Given the high flexibility of the pallet design as it stands, this is very unlikely.","breadcrumbs":"RFC-0089: Flexible Inflation » Future Directions and Related Material","id":"939","title":"Future Directions and Related Material"},"94":{"body":"This RFC proposes a new host function, secp256r1_ecdsa_verify_prehashed, for verifying NIST-P256 signatures. The function takes as input the message hash, r and s components of the signature, and the x and y coordinates of the public key. By providing this function, runtime authors can leverage a more efficient verification mechanism for \"secp256r1\" elliptic curve signatures, reducing computational costs and improving overall performance.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Summary","id":"94","title":"Summary"},"940":{"body":"(source) Table of Contents RFC-0001: Secondary Market for Regions Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Testing Security Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2024-06-09 Description Implement a secondary market for region listings and sales Authors Aurora Poppyseed , Philip Lucsok","breadcrumbs":"RFC-0001: Secondary Market for Regions » RFC-0001: Secondary Market for Regions","id":"940","title":"RFC-0001: Secondary Market for Regions"},"941":{"body":"This RFC proposes the addition of a secondary market feature to either the broker pallet or as a separate pallet maintained by Lastic, enabling users to list and purchase regions. This includes creating, purchasing, and removing listings, as well as emitting relevant events and handling associated errors.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Summary","id":"941","title":"Summary"},"942":{"body":"Currently, the broker pallet lacks functionality for a secondary market, which limits users' ability to freely trade regions. This RFC aims to introduce a secure and straightforward mechanism for users to list regions they own for sale and allow other users to purchase these regions. While integrating this functionality directly into the broker pallet is one option, another viable approach is to implement it as a separate pallet maintained by Lastic. This separate pallet would have access to the broker pallet and add minimal functionality necessary to support the secondary market. Adding smart contracts to the Coretime chain could also address this need; however, this process is expected to be lengthy and complex. We cannot afford to wait for this extended timeline to enable basic secondary market functionality. By proposing either integration into the broker pallet or the creation of a dedicated pallet, we can quickly enhance the flexibility and utility of the broker pallet, making it more user-friendly and valuable.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Motivation","id":"942","title":"Motivation"},"943":{"body":"Primary stakeholders include: Developers working on the broker pallet. Secondary Coretime marketplaces. Users who own regions and wish to trade them. Community members interested in enhancing the broker pallet’s capabilities.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Stakeholders","id":"943","title":"Stakeholders"},"944":{"body":"This RFC introduces the following key features: Storage Changes : Addition of Listings storage map to keep track of regions listed for sale and their prices. New Dispatchable Functions : create_listing: Allows a region owner to list a region for sale. purchase_listing: Allows a user to purchase a listed region. remove_listing: Allows a region owner to remove their listing. Events : ListingCreated: Emitted when a new listing is created. RegionSold: Emitted when a region is sold. ListingRemoved: Emitted when a listing is removed. Error Handling : ExpiredRegion: The region has expired and cannot be listed or sold. UnknownListing: The listing does not exist. InvalidPrice: The listing price is invalid. NotOwner: The caller is not the owner of the region. Testing : Comprehensive tests to verify the correct functionality of the new features, including listing creation, purchase, removal, and handling of edge cases such as expired regions and unauthorized actions.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Explanation","id":"944","title":"Explanation"},"945":{"body":"The main drawback of adding the additional complexity directly to the broker pallet is the potential increase in maintenance overhead. Therefore, we propose adding additional functionality as a separate pallet on the Coretime chain. To take the pressure off from implementing these features, implementation along with unit tests would be taken care of by Lastic (Aurora Makovac, Philip Lucsok). There are potential risks of security vulnerabilities in the new market functionalities, such as unauthorized region transfers or incorrect balance adjustments. Therefore, extensive security measures would have to be implemented.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Drawbacks","id":"945","title":"Drawbacks"},"946":{"body":"","breadcrumbs":"RFC-0001: Secondary Market for Regions » Testing, Security, and Privacy","id":"946","title":"Testing, Security, and Privacy"},"947":{"body":"Comprehensive unit tests need to be provided to ensure the correctness of the new functionalities. Scenarios tested should include successful and failed listing creation, purchases, and removals, as well as edge cases like expired regions and non-owner actions.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Testing","id":"947","title":"Testing"},"948":{"body":"Security audits should be performed to identify any vulnerabilities. Ensure that only region owners can create or remove listings. Validate all inputs to prevent invalid operations.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Security","id":"948","title":"Security"},"949":{"body":"The proposal does not introduce new privacy concerns as it only affects region trading functionality within the existing framework.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Privacy","id":"949","title":"Privacy"},"95":{"body":"“secp256r1” elliptic curve is a standardized curve by NIST which has the same calculations by different input parameters with “secp256k1” elliptic curve. The cost of combined attacks and the security conditions are almost the same for both curves. Adding a host function can provide signature verifications using the “secp256r1” elliptic curve in the runtime and multi-faceted benefits can occur. One important factor is that this curve is widely used and supported in many modern devices such as Apple’s Secure Enclave, Webauthn, Android Keychain which proves the user adoption. Additionally, the introduction of this host function could enable valuable features in the account abstraction which allows more efficient and flexible management of accounts by transaction signs in mobile devices. Most of the modern devices and applications rely on the “secp256r1” elliptic curve. The addition of this host function enables a more efficient verification of device native transaction signing mechanisms. For example: Apple's Secure Enclave: There is a separate “Trusted Execution Environment” in Apple hardware which can sign arbitrary messages and can only be accessed by biometric identification. Webauthn: Web Authentication (WebAuthn) is a web standard published by the World Wide Web Consortium (W3C). WebAuthn aims to standardize an interface for authenticating users to web-based applications and services using public-key cryptography. It is being used by almost all of the modern web browsers. Android Keystore: Android Keystore is an API that manages the private keys and signing methods. The private keys are not processed while using Keystore as the applications’ signing method. Also, it can be done in the “Trusted Execution Environment” in the microchip. Passkeys: Passkeys is utilizing FIDO Alliance and W3C standards. It replaces passwords with cryptographic key-pairs which is also can be used for the elliptic curve cryptography.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Motivation","id":"95","title":"Motivation"},"950":{"body":"","breadcrumbs":"RFC-0001: Secondary Market for Regions » Performance, Ergonomics, and Compatibility","id":"950","title":"Performance, Ergonomics, and Compatibility"},"951":{"body":"This feature is expected to introduce minimal overhead since it primarily involves read and write operations to storage maps. Efforts will be made to optimize the code to prevent unnecessary computational costs.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Performance","id":"951","title":"Performance"},"952":{"body":"The new functions are designed to be intuitive and easy to use, providing clear feedback through events and errors. Documentation and examples will be provided to assist developers and users.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Ergonomics","id":"952","title":"Ergonomics"},"953":{"body":"This proposal does not break compatibility with existing interfaces or previous versions. No migrations are necessary as it introduces new functionality without altering existing features.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Compatibility","id":"953","title":"Compatibility"},"954":{"body":"All related discussions are going to be under this PR.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Prior Art and References","id":"954","title":"Prior Art and References"},"955":{"body":"Are there additional security measures needed to prevent potential abuses of the new functionalities?","breadcrumbs":"RFC-0001: Secondary Market for Regions » Unresolved Questions","id":"955","title":"Unresolved Questions"},"956":{"body":"Integration with external NFT marketplaces for more robust trading options. Development of user interfaces to interact with the new marketplace features seamlessly. Exploration of adding smart contracts to the Coretime chain, which would provide greater flexibility and functionality for the secondary market and other decentralized applications. This would require a longer time for implementation, so this proposes an intermediary solution.","breadcrumbs":"RFC-0001: Secondary Market for Regions » Future Directions and Related Material","id":"956","title":"Future Directions and Related Material"},"957":{"body":"(source) Table of Contents RFC-0002: Smart Contracts on the Coretime Chain Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Testing Security Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2024-06-09 Description Implement smart contracts on the Coretime chain Authors Aurora Poppyseed , Phil Lucksok","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » RFC-0002: Smart Contracts on the Coretime Chain","id":"957","title":"RFC-0002: Smart Contracts on the Coretime Chain"},"958":{"body":"This RFC proposes the integration of smart contracts on the Coretime chain to enhance flexibility and enable complex decentralized applications, including secondary market functionalities.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Summary","id":"958","title":"Summary"},"959":{"body":"Currently, the Coretime chain lacks the capability to support smart contracts, which limits the range of decentralized applications that can be developed and deployed. By enabling smart contracts, the Coretime chain can facilitate more sophisticated functionalities such as automated region trading, dynamic pricing mechanisms, and other decentralized applications that require programmable logic. This will enhance the utility of the Coretime chain, attract more developers, and create more opportunities for innovation. Additionally, while there is a proposal (#885) to allow EVM-compatible contracts on Polkadot’s Asset Hub, the implementation of smart contracts directly on the Coretime chain will provide synchronous interactions and avoid the complexities of asynchronous operations via XCM.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Motivation","id":"959","title":"Motivation"},"96":{"body":"Runtime Authors","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Stakeholders","id":"96","title":"Stakeholders"},"960":{"body":"Primary stakeholders include: Developers working on the Coretime chain. Users who want to deploy decentralized applications on the Coretime chain. Community members interested in expanding the capabilities of the Coretime chain. Secondary Coretime marketplaces.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Stakeholders","id":"960","title":"Stakeholders"},"961":{"body":"This RFC introduces the following key components: Smart Contract Support : Integrate support for deploying and executing smart contracts on the Coretime chain. Use a well-established smart contract platform, such as Ethereum’s Solidity or Polkadot's Ink!, to ensure compatibility and ease of use. Storage and Execution : Define a storage structure for smart contracts and their associated data. Ensure efficient and secure execution of smart contracts, with proper resource management and gas fee mechanisms. Integration with Existing Pallets : Ensure that smart contracts can interact with existing pallets on the Coretime chain, such as the broker pallet. Provide APIs and interfaces for seamless integration and interaction. Security and Auditing : Implement robust security measures to prevent vulnerabilities and exploits in smart contracts. Conduct thorough security audits and testing before deployment.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Explanation","id":"961","title":"Explanation"},"962":{"body":"There are several drawbacks to consider: Complexity : Adding smart contracts introduces significant complexity to the Coretime chain, which may increase maintenance overhead and the potential for bugs. Performance : The execution of smart contracts can be resource-intensive, potentially affecting the performance of the Coretime chain. Security : Smart contracts are prone to vulnerabilities and exploits, necessitating rigorous security measures and continuous monitoring.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Drawbacks","id":"962","title":"Drawbacks"},"963":{"body":"","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Testing, Security, and Privacy","id":"963","title":"Testing, Security, and Privacy"},"964":{"body":"Comprehensive unit tests and integration tests should be developed to ensure the correct functionality of smart contracts. Test scenarios should include various use cases and edge cases to validate the robustness of the implementation.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Testing","id":"964","title":"Testing"},"965":{"body":"Security audits should be performed to identify and mitigate vulnerabilities. Implement best practices for smart contract development to minimize the risk of exploits. Continuous monitoring and updates will be necessary to address new security threats.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Security","id":"965","title":"Security"},"966":{"body":"The proposal does not introduce new privacy concerns as it extends existing functionalities with programmable logic.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Privacy","id":"966","title":"Privacy"},"967":{"body":"","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Performance, Ergonomics, and Compatibility","id":"967","title":"Performance, Ergonomics, and Compatibility"},"968":{"body":"The introduction of smart contracts may impact performance due to the additional computational overhead. Optimization techniques, such as efficient gas fee mechanisms and resource management, should be employed to minimize performance degradation.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Performance","id":"968","title":"Performance"},"969":{"body":"The new functionality should be designed to be intuitive and easy to use for developers, with comprehensive documentation and examples. Provide developer tools and SDKs to facilitate the creation and deployment of smart contracts.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Ergonomics","id":"969","title":"Ergonomics"},"97":{"body":"This RFC proposes a new host function for runtime authors to leverage a more efficient verification mechanism for \"secp256r1\" elliptic curve signatures. Proposed host function signature: fn ext_secp256r1_ecdsa_verify_prehashed_version_1( sig: &[u8; 64], msg: &[u8; 32], pub_key: &[u8; 64],\n) -> bool; The host function MUST return true if the signature is valid or false otherwise.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Explanation","id":"97","title":"Explanation"},"970":{"body":"This proposal should maintain compatibility with existing interfaces and functionalities of the Coretime chain. Ensure backward compatibility and provide migration paths if necessary.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Compatibility","id":"970","title":"Compatibility"},"971":{"body":"Ethereum’s implementation of smart contracts using Solidity. Polkadot’s Ink! smart contract platform. Existing decentralized applications and use cases on other blockchain platforms. Proposal #885: EVM-compatible contracts on Asset Hub, which highlights the community's interest in integrating smart contracts within the Polkadot ecosystem.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Prior Art and References","id":"971","title":"Prior Art and References"},"972":{"body":"What specific security measures should be implemented to prevent smart contract vulnerabilities? How can we ensure optimal performance while supporting complex smart contracts? What are the best practices for integrating smart contracts with existing pallets on the Coretime chain?","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Unresolved Questions","id":"972","title":"Unresolved Questions"},"973":{"body":"Further enhancements could include advanced developer tools and SDKs for smart contract development. Integration with external decentralized applications and platforms to expand the ecosystem. Continuous updates and improvements to the smart contract platform based on community feedback and emerging best practices. Exploration of additional use cases for smart contracts on the Coretime chain, such as decentralized finance (DeFi) applications, voting systems, and more. By enabling smart contracts on the Coretime chain, we can significantly expand its capabilities and attract a wider range of developers and users, fostering innovation and growth in the ecosystem.","breadcrumbs":"RFC-0002: Smart Contracts on the Coretime Chain » Future Directions and Related Material","id":"973","title":"Future Directions and Related Material"},"974":{"body":"(source) Table of Contents RFC-0106: Remove XCM fees mode Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Remove the SetFeesMode instruction and fees_mode register from XCM Authors Francisco Aguirre","breadcrumbs":"RFC-0106: Remove XCM fees mode » RFC-0106: Remove XCM fees mode","id":"974","title":"RFC-0106: Remove XCM fees mode"},"975":{"body":"The SetFeesMode instruction and the fees_mode register allow for the existence of JIT withdrawal. JIT withdrawal complicates the fee mechanism and leads to bugs and unexpected behaviour. The proposal is to remove said functionality. Another effort to simplify fee handling in XCM.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Summary","id":"975","title":"Summary"},"976":{"body":"The JIT withdrawal mechanism creates bugs such as not being able to get fees when all assets are put into holding and none left in the origin location. This is a confusing behavior, since there are funds for fees, just not where the XCVM wants them. The XCVM should have only one entrypoint to fee payment, the holding register. That way there is also less surface for bugs.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Motivation","id":"976","title":"Motivation"},"977":{"body":"Runtime Users Runtime Devs Wallets dApps","breadcrumbs":"RFC-0106: Remove XCM fees mode » Stakeholders","id":"977","title":"Stakeholders"},"978":{"body":"The SetFeesMode instruction will be removed. The Fees Mode register will be removed.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Explanation","id":"978","title":"Explanation"},"979":{"body":"Users will have to make sure to put enough assets in WithdrawAsset when previously some things might have been charged directly from their accounts. This leads to a more predictable behaviour though so it will only be a drawback for the minority of users.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Drawbacks","id":"979","title":"Drawbacks"},"98":{"body":"N/A","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Drawbacks","id":"98","title":"Drawbacks"},"980":{"body":"Implementations and benchmarking must change for most existing pallet calls that send XCMs to other locations.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Testing, Security, and Privacy","id":"980","title":"Testing, Security, and Privacy"},"981":{"body":"","breadcrumbs":"RFC-0106: Remove XCM fees mode » Performance, Ergonomics, and Compatibility","id":"981","title":"Performance, Ergonomics, and Compatibility"},"982":{"body":"Performance will be improved since unnecessary checks will be avoided.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Performance","id":"982","title":"Performance"},"983":{"body":"JIT withdrawal was a way of side-stepping the regular flow of XCM programs. By removing it, the spec is simplified but now old use-cases have to work with the original intended behaviour, which may result in more implementation work. Ergonomics for users will undoubtedly improve since the system is more predictable.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Ergonomics","id":"983","title":"Ergonomics"},"984":{"body":"Existing programs in the ecosystem will break. The instruction should be deprecated as soon as this RFC is approved (but still fully supported), then removed in a subsequent XCM version (probably deprecate in v5, remove in v6).","breadcrumbs":"RFC-0106: Remove XCM fees mode » Compatibility","id":"984","title":"Compatibility"},"985":{"body":"The previous RFC PR on the xcm-format repo, before XCM RFCs were moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/57.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Prior Art and References","id":"985","title":"Prior Art and References"},"986":{"body":"None.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Unresolved Questions","id":"986","title":"Unresolved Questions"},"987":{"body":"The new generic fees mechanism is related to this proposal and further stimulates it as the JIT withdraw fees mechanism will become useless anyway.","breadcrumbs":"RFC-0106: Remove XCM fees mode » Future Directions and Related Material","id":"987","title":"Future Directions and Related Material"},"988":{"body":"(source) Table of Contents RFC-0112: Compress the State Response Message in State Sync Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 14 August 2024 Description Compress the state response message to reduce the data transfer during the state syncing Authors Liu-Cheng Xu","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » RFC-0112: Compress the State Response Message in State Sync","id":"988","title":"RFC-0112: Compress the State Response Message in State Sync"},"989":{"body":"This RFC proposes compressing the state response message during the state syncing process to reduce the amount of data transferred.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Summary","id":"989","title":"Summary"},"99":{"body":"","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Testing, Security, and Privacy","id":"99","title":"Testing, Security, and Privacy"},"990":{"body":"State syncing can require downloading several gigabytes of data, particularly for blockchains with large state sizes, such as Astar, which has a state size exceeding 5 GiB (https://github.com/AstarNetwork/Astar/issues/1110). This presents a significant challenge for nodes with slower network connections. Additionally, the current state sync implementation lacks a persistence feature (https://github.com/paritytech/polkadot-sdk/issues/4), meaning any network disruption forces the node to re-download the entire state, making the process even more difficult.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Motivation","id":"990","title":"Motivation"},"991":{"body":"This RFC benefits all projects utilizing the Substrate framework, specifically in improving the efficiency of state syncing. Node Operators. Substrate Users.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Stakeholders","id":"991","title":"Stakeholders"},"992":{"body":"The largest portion of the state response message consists of either CompactProof or Vec, depending on whether a proof is requested ( source ): CompactProof: When proof is requested, compression yields a lower ratio but remains beneficial, as shown in warp sync tests in the Performance section below. Vec: Without proof, this is theoretically compressible because the entries are generated by iterating the storage sequentially starting from an empty storage key, which means many entries in the message share the same storage prefix, making it ideal for compression.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Explanation","id":"992","title":"Explanation"},"993":{"body":"None identified.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Drawbacks","id":"993","title":"Drawbacks"},"994":{"body":"The code changes required for this RFC are straightforward: compress the state response on the sender side and decompress it on the receiver side. Existing sync tests should ensure functionality remains intact.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Testing, Security, and Privacy","id":"994","title":"Testing, Security, and Privacy"},"995":{"body":"","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Performance, Ergonomics, and Compatibility","id":"995","title":"Performance, Ergonomics, and Compatibility"},"996":{"body":"This RFC optimizes network bandwidth usage during state syncing, particularly for blockchains with gigabyte-sized states, while introducing negligible CPU overhead for compression and decompression. For example, compressing the state response during a recent Polkadot warp sync (around height #22076653) reduces the data transferred from 530,310,121 bytes to 352,583,455 bytes — a 33% reduction, saving approximately 169 MiB of data. Performance data is based on this patch , with logs available here .","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Performance","id":"996","title":"Performance"},"997":{"body":"None.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Ergonomics","id":"997","title":"Ergonomics"},"998":{"body":"No compatibility issues identified.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Compatibility","id":"998","title":"Compatibility"},"999":{"body":"None.","breadcrumbs":"RFC-0112: Compress the State Response Message in State Sync » Prior Art and References","id":"999","title":"Prior Art and References"}},"length":1016,"save":true},"fields":["title","body","breadcrumbs"],"index":{"body":{"root":{"0":{".":{".":{"1":{"df":1,"docs":{"346":{"tf":1.0}}},"2":{"^":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"0":{"0":{"0":{"1":{"6":{"7":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"0":{"9":{"6":{"6":{"6":{"6":{"1":{"7":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":1,"docs":{"415":{"tf":1.0}}},"2":{"df":1,"docs":{"416":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"416":{"tf":1.0}}},"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"8":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"0":{"9":{"6":{"6":{"6":{"6":{"1":{"7":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"1":{"0":{"8":{"3":{"3":{"df":1,"docs":{"720":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"df":1,"docs":{"469":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.0}}},"2":{"0":{"0":{"6":{"4":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"7":{"6":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"8":{"1":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"2":{"9":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"df":1,"docs":{"469":{"tf":1.0}}},"8":{"7":{"df":2,"docs":{"567":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"752":{"tf":1.0}}},"6":{"df":1,"docs":{"406":{"tf":1.0}}},"8":{"df":1,"docs":{"715":{"tf":1.0}}},"9":{"5":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"0":{"0":{"df":2,"docs":{"56":{"tf":1.4142135623730951},"709":{"tf":1.4142135623730951}}},"1":{"df":1,"docs":{"940":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"957":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"730":{"tf":1.4142135623730951}}},"6":{"df":1,"docs":{"741":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"229":{"tf":1.4142135623730951}}},"8":{"df":1,"docs":{"247":{"tf":1.4142135623730951}}},"9":{"df":1,"docs":{"757":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"1":{"0":{"df":1,"docs":{"263":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"268":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"279":{"tf":1.4142135623730951}}},"4":{"df":3,"docs":{"107":{"tf":1.0},"120":{"tf":1.0},"294":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"771":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"2":{"2":{"df":1,"docs":{"311":{"tf":1.4142135623730951}}},"6":{"df":1,"docs":{"322":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"366":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"795":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"4":{"2":{"df":1,"docs":{"386":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"400":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"808":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"410":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"430":{"tf":1.4142135623730951}}},"8":{"df":1,"docs":{"451":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"5":{"0":{"df":1,"docs":{"465":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"827":{"tf":1.4142135623730951}}},"6":{"df":1,"docs":{"481":{"tf":1.4142135623730951}}},"9":{"df":1,"docs":{"495":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"7":{"0":{"df":1,"docs":{"841":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"857":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"871":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"891":{"tf":1.4142135623730951}}},"8":{"df":1,"docs":{"513":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"8":{"4":{"df":1,"docs":{"535":{"tf":1.4142135623730951}}},"8":{"df":1,"docs":{"908":{"tf":1.4142135623730951}}},"9":{"df":1,"docs":{"926":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"9":{"1":{"df":1,"docs":{"549":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"563":{"tf":1.4142135623730951}}},"9":{"df":1,"docs":{"584":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":1,"docs":{"539":{"tf":1.0}}},"1":{"0":{"0":{"df":1,"docs":{"598":{"tf":1.4142135623730951}}},"1":{"df":1,"docs":{"613":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"627":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"649":{"tf":1.4142135623730951}}},"6":{"df":1,"docs":{"974":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"664":{"tf":1.4142135623730951}}},"8":{"df":1,"docs":{"678":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"1":{"1":{"df":1,"docs":{"79":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"988":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"93":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"106":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"2":{"0":{"df":1,"docs":{"122":{"tf":1.4142135623730951}}},"1":{"df":1,"docs":{"136":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"692":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"150":{"tf":1.4142135623730951}}},"4":{"df":1,"docs":{"164":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"1":{"tf":1.4142135623730951}}},"6":{"df":1,"docs":{"17":{"tf":1.4142135623730951}}},"7":{"df":1,"docs":{"38":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":2,"docs":{"539":{"tf":1.0},"692":{"tf":1.0}}},"3":{"df":2,"docs":{"430":{"tf":1.0},"584":{"tf":1.0}}},"4":{"df":1,"docs":{"730":{"tf":1.0}}},"5":{".":{"0":{"8":{".":{"2":{"0":{"2":{"3":{"df":1,"docs":{"771":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"549":{"tf":1.0},"782":{"tf":1.0}}},"6":{"df":4,"docs":{"215":{"tf":1.0},"322":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}},"7":{"df":4,"docs":{"229":{"tf":1.0},"247":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0}}},"9":{":":{"1":{"3":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":3,"docs":{"741":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}},"b":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"1":{"df":1,"docs":{"170":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"0":{"_":{"0":{"1":{"0":{"1":{"df":1,"docs":{"170":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"1":{"1":{"_":{"1":{"1":{"1":{"1":{"_":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"1":{"1":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":3.3166247903554}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"t":{"0":{"0":{"0":{"_":{"0":{"1":{"0":{"0":{"df":1,"docs":{"539":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"t":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":1,"docs":{"539":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":1,"docs":{"539":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":31,"docs":{"194":{"tf":1.0},"208":{"tf":3.872983346207417},"222":{"tf":1.0},"24":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.7320508075688772},"416":{"tf":1.0},"437":{"tf":1.0},"471":{"tf":1.7320508075688772},"525":{"tf":3.872983346207417},"526":{"tf":1.4142135623730951},"531":{"tf":1.0},"537":{"tf":1.0},"63":{"tf":1.4142135623730951},"633":{"tf":1.0},"635":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.0},"735":{"tf":4.58257569495584},"747":{"tf":1.0},"748":{"tf":2.23606797749979},"751":{"tf":1.7320508075688772},"752":{"tf":1.0},"761":{"tf":1.0},"786":{"tf":1.4142135623730951},"846":{"tf":1.0},"879":{"tf":1.0}},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":4.795831523312719}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"525":{"tf":1.0}}},"df":0,"docs":{}},"x":{"0":{"0":{"0":{"0":{"6":{"0":{"7":{"b":{"2":{"2":{"7":{"4":{"6":{"5":{"7":{"8":{"7":{"4":{"2":{"2":{"3":{"a":{"2":{"0":{"2":{"2":{"4":{"8":{"6":{"5":{"6":{"c":{"6":{"c":{"6":{"df":0,"docs":{},"f":{"2":{"0":{"5":{"7":{"6":{"df":0,"docs":{},"f":{"7":{"2":{"6":{"c":{"6":{"4":{"2":{"1":{"2":{"2":{"7":{"d":{"df":1,"docs":{"847":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"8":{"3":{"d":{"d":{"8":{"0":{"8":{"4":{"d":{"5":{"0":{"d":{"b":{"b":{"b":{"c":{"9":{"6":{"2":{"0":{"6":{"7":{"df":0,"docs":{},"f":{"2":{"1":{"6":{"c":{"3":{"7":{"b":{"6":{"2":{"7":{"8":{"3":{"1":{"d":{"9":{"3":{"3":{"9":{"df":0,"docs":{},"f":{"5":{"a":{"6":{"df":0,"docs":{},"e":{"4":{"2":{"6":{"a":{"3":{"2":{"df":0,"docs":{},"e":{"3":{"0":{"7":{"6":{"3":{"1":{"3":{"d":{"8":{"7":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"1":{"0":{"df":0,"docs":{},"f":{"df":1,"docs":{"253":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"1":{",":{"0":{"0":{"0":{"df":1,"docs":{"200":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"2":{",":{"3":{"df":1,"docs":{"436":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},".":{"0":{"df":2,"docs":{"53":{"tf":1.0},"762":{"tf":1.0}}},"1":{"df":2,"docs":{"322":{"tf":1.0},"325":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"326":{"tf":1.0}}},"5":{"df":3,"docs":{"469":{"tf":1.0},"752":{"tf":1.4142135623730951},"762":{"tf":1.0}}},"df":0,"docs":{}},"/":{"1":{"0":{"0":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"375":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"df":1,"docs":{"569":{"tf":1.0}}},"3":{"df":4,"docs":{"346":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.0},"569":{"tf":1.0}}},"8":{"0":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"223":{"tf":1.0},"470":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":7,"docs":{"208":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"507":{"tf":1.0},"752":{"tf":2.0},"861":{"tf":1.0}}},"2":{"0":{"df":1,"docs":{"390":{"tf":1.0}}},"df":0,"docs":{}},"df":6,"docs":{"208":{"tf":3.872983346207417},"223":{"tf":1.0},"24":{"tf":1.0},"46":{"tf":1.0},"60":{"tf":1.0},"735":{"tf":1.0}},"m":{"df":1,"docs":{"933":{"tf":1.0}}}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":22,"docs":{"1002":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":1.0},"208":{"tf":2.23606797749979},"223":{"tf":1.0},"322":{"tf":1.0},"359":{"tf":1.0},"412":{"tf":1.4142135623730951},"415":{"tf":1.4142135623730951},"416":{"tf":1.4142135623730951},"45":{"tf":1.0},"47":{"tf":1.0},"539":{"tf":1.0},"63":{"tf":1.4142135623730951},"714":{"tf":1.0},"776":{"tf":1.0},"795":{"tf":1.0},"846":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"554":{"tf":1.0}}}}},"x":{"df":1,"docs":{"63":{"tf":1.0}}}},"1":{",":{"6":{"df":1,"docs":{"761":{"tf":1.0}}},"7":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"0":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":2.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"4":{"df":1,"docs":{"182":{"tf":1.4142135623730951}}},"df":7,"docs":{"322":{"tf":1.0},"360":{"tf":1.0},"471":{"tf":1.0},"481":{"tf":1.0},"539":{"tf":1.0},"598":{"tf":1.0},"827":{"tf":1.0}}},"2":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"362":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"363":{"tf":1.0}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"364":{"tf":1.0}}},"4":{"df":2,"docs":{"322":{"tf":1.0},"365":{"tf":1.0}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"208":{"tf":1.0},"567":{"tf":1.0}}},"2":{"df":1,"docs":{"6":{"tf":1.0}}},"7":{"df":1,"docs":{"540":{"tf":1.0}}},"8":{"df":5,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"436":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":1.0}}},"9":{"df":1,"docs":{"416":{"tf":1.0}}},"df":10,"docs":{"183":{"tf":1.0},"186":{"tf":1.4142135623730951},"322":{"tf":1.0},"361":{"tf":1.0},"495":{"tf":1.0},"535":{"tf":1.0},"613":{"tf":1.0},"79":{"tf":1.0},"857":{"tf":1.0},"861":{"tf":1.0}}},"3":{",":{"1":{"1":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":3,"docs":{"451":{"tf":1.0},"56":{"tf":1.0},"720":{"tf":1.0}}},"4":{".":{"1":{"0":{".":{"2":{"0":{"2":{"4":{"df":1,"docs":{"150":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"0":{"df":1,"docs":{"50":{"tf":1.0}}},"df":0,"docs":{}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":5,"docs":{"208":{"tf":1.0},"247":{"tf":1.0},"776":{"tf":1.0},"861":{"tf":1.0},"988":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"252":{"tf":1.0}}}}},"5":{",":{"1":{"7":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"0":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":2,"docs":{"208":{"tf":3.4641016151377544},"50":{"tf":1.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":3.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"df":1,"docs":{"208":{"tf":1.0}}},"df":8,"docs":{"208":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.0},"465":{"tf":1.0},"627":{"tf":1.0},"714":{"tf":1.0},"799":{"tf":1.0},"871":{"tf":1.0}},"k":{"b":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"39":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"6":{"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"898":{"tf":1.0}}},"4":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"9":{"df":1,"docs":{"996":{"tf":1.0}}},"df":5,"docs":{"208":{"tf":3.4641016151377544},"500":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"93":{"tf":1.0}},"k":{"df":0,"docs":{},"i":{"b":{"df":1,"docs":{"253":{"tf":1.0}}},"df":0,"docs":{}}}},"7":{"df":2,"docs":{"136":{"tf":1.0},"182":{"tf":1.0}}},"8":{",":{"3":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"4":{"6":{"7":{"4":{"4":{"0":{"7":{"3":{"7":{"0":{"9":{"5":{"5":{"1":{"6":{"1":{"5":{"df":1,"docs":{"404":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"164":{"tf":1.0},"495":{"tf":1.0}}},"9":{".":{"0":{"6":{".":{"2":{"0":{"2":{"4":{"df":2,"docs":{"563":{"tf":1.0},"567":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{".":{"2":{"0":{"2":{"3":{"df":1,"docs":{"263":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":1,"docs":{"418":{"tf":1.0}}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"757":{"tf":1.0}}},":":{"1":{"df":1,"docs":{"440":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":80,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"171":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.0},"186":{"tf":1.0},"195":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.0},"216":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"322":{"tf":1.0},"324":{"tf":1.0},"332":{"tf":1.0},"341":{"tf":1.4142135623730951},"344":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"370":{"tf":1.0},"390":{"tf":1.4142135623730951},"416":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.4142135623730951},"440":{"tf":1.7320508075688772},"45":{"tf":1.0},"455":{"tf":1.0},"469":{"tf":1.0},"47":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":2.23606797749979},"520":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":3.7416573867739413},"526":{"tf":1.4142135623730951},"537":{"tf":1.0},"553":{"tf":1.4142135623730951},"60":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":2.23606797749979},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":5.656854249492381},"742":{"tf":1.0},"743":{"tf":1.7320508075688772},"748":{"tf":1.7320508075688772},"749":{"tf":1.4142135623730951},"750":{"tf":1.4142135623730951},"752":{"tf":3.1622776601683795},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.23606797749979},"762":{"tf":1.4142135623730951},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"780":{"tf":1.0},"786":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":2.0},"862":{"tf":1.0},"878":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"v":{"df":1,"docs":{"799":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}},"2":{"(":{"df":0,"docs":{},"j":{"df":1,"docs":{"45":{"tf":1.0}}}},",":{"8":{"9":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},".":{"0":{"df":1,"docs":{"469":{"tf":1.0}}},"1":{"df":2,"docs":{"322":{"tf":1.0},"328":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"329":{"tf":1.0}}},"5":{"df":1,"docs":{"469":{"tf":2.0}}},"6":{"7":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"3":{"df":5,"docs":{"567":{"tf":1.4142135623730951},"63":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":2.0},"471":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"208":{"tf":1.7320508075688772},"24":{"tf":1.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":2.6457513110645907}}},"df":0,"docs":{}},"df":0,"docs":{}}},"2":{"2":{"df":2,"docs":{"312":{"tf":1.0},"807":{"tf":1.0}}},"3":{"df":27,"docs":{"195":{"tf":1.0},"201":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"782":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0}}},"4":{"df":33,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"38":{"tf":1.0},"418":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"79":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}},"5":{"df":1,"docs":{"54":{"tf":1.0}}},"df":0,"docs":{}},"4":{"8":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}},"df":15,"docs":{"191":{"tf":1.0},"235":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":2.0},"366":{"tf":1.0},"505":{"tf":1.4142135623730951},"507":{"tf":1.7320508075688772},"549":{"tf":1.0},"714":{"tf":1.0},"891":{"tf":2.0},"892":{"tf":1.0},"895":{"tf":2.449489742783178},"896":{"tf":1.0},"898":{"tf":1.7320508075688772},"932":{"tf":1.0}}},"2":{",":{"5":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"6":{"6":{"5":{"3":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"1":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"390":{"tf":1.0},"513":{"tf":1.0},"860":{"tf":1.0}},"n":{"d":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}}},"3":{"df":4,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"974":{"tf":1.0}}},"4":{"0":{",":{"8":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":7,"docs":{"182":{"tf":1.0},"198":{"tf":1.0},"257":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"507":{"tf":1.0},"827":{"tf":1.0}}},"5":{"6":{"df":4,"docs":{"333":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"634":{"tf":1.7320508075688772}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":4,"docs":{"17":{"tf":1.0},"294":{"tf":1.0},"634":{"tf":1.0},"908":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"386":{"tf":1.0}}}}},"6":{"df":2,"docs":{"38":{"tf":1.0},"575":{"tf":1.0}}},"7":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"471":{"tf":1.0}}},"8":{"8":{"0":{"0":{"df":1,"docs":{"569":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":12,"docs":{"207":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":2.449489742783178},"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.7320508075688772},"573":{"tf":2.449489742783178},"575":{"tf":1.0},"577":{"tf":1.0},"846":{"tf":1.0}}},"9":{"6":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"841":{"tf":1.0}}},"df":51,"docs":{"171":{"tf":1.0},"184":{"tf":1.0},"190":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":1.7320508075688772},"249":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"327":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.0},"410":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"45":{"tf":1.0},"525":{"tf":3.605551275463989},"537":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.4142135623730951},"569":{"tf":1.4142135623730951},"573":{"tf":1.4142135623730951},"575":{"tf":1.0},"576":{"tf":1.0},"598":{"tf":1.0},"603":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":1.0},"637":{"tf":1.0},"735":{"tf":3.4641016151377544},"748":{"tf":1.7320508075688772},"752":{"tf":2.23606797749979},"761":{"tf":2.0},"779":{"tf":1.0},"841":{"tf":1.0},"847":{"tf":1.0},"861":{"tf":1.0},"880":{"tf":1.0},"933":{"tf":1.4142135623730951}},"n":{"/":{"3":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"3":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"331":{"tf":1.0}}},"2":{"5":{"df":1,"docs":{"720":{"tf":1.0}}},"df":3,"docs":{"322":{"tf":1.4142135623730951},"332":{"tf":1.0},"333":{"tf":1.0}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"334":{"tf":1.0}}},"a":{"df":1,"docs":{"450":{"tf":1.0}}},"b":{"df":1,"docs":{"450":{"tf":1.0}}},"c":{"df":1,"docs":{"450":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":8,"docs":{"195":{"tf":1.0},"207":{"tf":1.0},"400":{"tf":1.0},"481":{"tf":1.0},"50":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":2.0},"776":{"tf":1.0}}},"2":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"831":{"tf":1.0}}}}},"df":17,"docs":{"163":{"tf":1.0},"208":{"tf":1.4142135623730951},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"332":{"tf":1.0},"388":{"tf":1.0},"455":{"tf":1.0},"520":{"tf":1.4142135623730951},"525":{"tf":1.0},"526":{"tf":1.4142135623730951},"634":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"885":{"tf":1.0},"897":{"tf":1.4142135623730951},"907":{"tf":1.0},"97":{"tf":1.0}}},"3":{".":{"3":{"3":{"3":{"3":{"3":{"3":{"df":1,"docs":{"862":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"996":{"tf":1.0}}},"4":{"0":{"df":1,"docs":{"869":{"tf":1.0}}},"df":1,"docs":{"782":{"tf":1.4142135623730951}}},"5":{"2":{",":{"5":{"8":{"3":{",":{"4":{"5":{"5":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"5":{"df":1,"docs":{"537":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"df":1,"docs":{"551":{"tf":1.4142135623730951}}}},"7":{"1":{"2":{"df":1,"docs":{"537":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"208":{"tf":1.0}}},"8":{"df":1,"docs":{"735":{"tf":1.0}}},"df":35,"docs":{"113":{"tf":1.0},"154":{"tf":1.4142135623730951},"171":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"216":{"tf":1.0},"221":{"tf":1.0},"226":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"330":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"432":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.4142135623730951},"50":{"tf":1.4142135623730951},"525":{"tf":3.605551275463989},"598":{"tf":1.0},"603":{"tf":1.0},"633":{"tf":2.0},"722":{"tf":1.0},"735":{"tf":2.449489742783178},"743":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":2.0},"841":{"tf":1.0},"845":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0}},"x":{"df":1,"docs":{"575":{"tf":1.0}}}},"4":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"336":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"337":{"tf":1.0}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"338":{"tf":1.0}}},"4":{"df":2,"docs":{"322":{"tf":1.0},"339":{"tf":1.0}}},"df":0,"docs":{}},"0":{"3":{"2":{"0":{"0":{"df":1,"docs":{"569":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":8,"docs":{"208":{"tf":1.4142135623730951},"416":{"tf":1.0},"892":{"tf":1.0},"895":{"tf":1.4142135623730951},"896":{"tf":1.0},"898":{"tf":1.7320508075688772},"900":{"tf":1.0},"902":{"tf":1.0}}},"2":{"1":{"6":{"1":{"df":2,"docs":{"45":{"tf":1.0},"47":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"418":{"tf":1.0}}},"5":{"df":3,"docs":{"207":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":2.0}}},"6":{"df":1,"docs":{"532":{"tf":1.0}}},"8":{",":{"6":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"4":{"4":{"'":{"df":1,"docs":{"39":{"tf":1.0}}},"df":1,"docs":{"55":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{",":{"2":{"1":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":30,"docs":{"165":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.4142135623730951},"184":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"280":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"335":{"tf":1.0},"344":{"tf":1.0},"485":{"tf":1.0},"521":{"tf":1.0},"525":{"tf":3.7416573867739413},"537":{"tf":1.0},"539":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":2.449489742783178},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"761":{"tf":1.7320508075688772},"799":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.4142135623730951},"846":{"tf":1.0},"928":{"tf":1.0}},"·":{"1":{"0":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"5":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"341":{"tf":1.0}}},"4":{".":{"2":{"df":2,"docs":{"341":{"tf":1.0},"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":2,"docs":{"497":{"tf":1.4142135623730951},"515":{"tf":1.0}}},"df":6,"docs":{"208":{"tf":2.0},"257":{"tf":1.0},"436":{"tf":1.0},"507":{"tf":1.0},"717":{"tf":1.0},"846":{"tf":1.4142135623730951}}},"3":{",":{"3":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"3":{"1":{"0":{",":{"1":{"2":{"1":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{",":{"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"2":{"df":1,"docs":{"911":{"tf":1.0}}},"df":0,"docs":{}},"df":29,"docs":{"164":{"tf":2.23606797749979},"165":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.4142135623730951},"180":{"tf":1.0},"181":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.4142135623730951},"221":{"tf":1.0},"280":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"340":{"tf":1.0},"370":{"tf":1.0},"471":{"tf":1.0},"525":{"tf":3.0},"539":{"tf":1.0},"588":{"tf":1.4142135623730951},"594":{"tf":1.0},"714":{"tf":1.4142135623730951},"735":{"tf":1.0},"761":{"tf":1.4142135623730951},"990":{"tf":1.0}}},"6":{".":{"1":{"0":{"df":3,"docs":{"322":{"tf":1.0},"344":{"tf":1.0},"352":{"tf":1.0}}},"df":1,"docs":{"342":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"343":{"tf":1.0}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"344":{"tf":1.0}}},"4":{".":{"1":{"df":1,"docs":{"345":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"345":{"tf":1.0}}},"5":{".":{"1":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"342":{"tf":1.0},"346":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"346":{"tf":1.0}}},"6":{"df":2,"docs":{"322":{"tf":1.0},"347":{"tf":1.0}}},"7":{"df":2,"docs":{"322":{"tf":1.0},"348":{"tf":1.0}}},"8":{".":{"1":{"df":1,"docs":{"349":{"tf":1.0}}},"2":{"df":3,"docs":{"348":{"tf":1.0},"349":{"tf":1.0},"351":{"tf":1.0}}},"3":{"df":1,"docs":{"349":{"tf":1.0}}},"4":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":3,"docs":{"322":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0}}},"9":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"351":{"tf":1.0}}},"2":{"df":1,"docs":{"351":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"350":{"tf":1.0}}},"df":0,"docs":{}},"0":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"3":{"df":1,"docs":{"540":{"tf":1.0}}},"4":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"735":{"tf":1.7320508075688772},"831":{"tf":1.4142135623730951}}}}},"df":4,"docs":{"332":{"tf":1.0},"404":{"tf":1.0},"634":{"tf":1.4142135623730951},"97":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"i":{"b":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}}}},"5":{",":{"3":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{",":{"6":{"6":{"7":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"df":1,"docs":{"846":{"tf":1.0}}},"df":10,"docs":{"205":{"tf":1.0},"322":{"tf":1.0},"342":{"tf":1.0},"525":{"tf":1.0},"588":{"tf":1.0},"761":{"tf":1.4142135623730951},"779":{"tf":1.0},"808":{"tf":1.0},"862":{"tf":1.0},"926":{"tf":1.0}}},"7":{"0":{"df":2,"docs":{"714":{"tf":1.0},"932":{"tf":1.0}}},"2":{"1":{"2":{"df":1,"docs":{"105":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"df":1,"docs":{"714":{"tf":1.0}}},"7":{",":{"0":{"0":{"0":{"df":1,"docs":{"470":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":13,"docs":{"184":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"322":{"tf":1.0},"353":{"tf":1.0},"39":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.4142135623730951},"568":{"tf":1.0},"632":{"tf":1.0},"720":{"tf":1.0},"776":{"tf":1.4142135623730951},"862":{"tf":1.0}}},"8":{"0":{",":{"0":{"0":{"0":{"df":3,"docs":{"208":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}},"df":5,"docs":{"204":{"tf":1.7320508075688772},"208":{"tf":2.23606797749979},"444":{"tf":1.0},"720":{"tf":1.7320508075688772},"721":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"1":{",":{"8":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"5":{"df":2,"docs":{"959":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{}},"df":15,"docs":{"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.7320508075688772},"221":{"tf":1.0},"322":{"tf":1.0},"332":{"tf":1.0},"354":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"496":{"tf":1.4142135623730951},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"735":{"tf":1.0}}},"9":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"356":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"357":{"tf":1.0}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"358":{"tf":1.0}}},"df":0,"docs":{}},"1":{"b":{"1":{"7":{"1":{"b":{"b":{"1":{"5":{"8":{"df":0,"docs":{},"e":{"2":{"d":{"3":{"8":{"4":{"8":{"df":0,"docs":{},"f":{"a":{"2":{"3":{"a":{"9":{"df":0,"docs":{},"f":{"1":{"c":{"2":{"5":{"1":{"8":{"2":{"df":0,"docs":{},"f":{"b":{"8":{"df":0,"docs":{},"e":{"2":{"0":{"3":{"1":{"3":{"b":{"2":{"c":{"1":{"df":0,"docs":{},"e":{"b":{"4":{"9":{"2":{"1":{"9":{"d":{"a":{"7":{"a":{"7":{"0":{"c":{"df":0,"docs":{},"e":{"9":{"0":{"c":{"3":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"253":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"8":{"1":{"df":1,"docs":{"340":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"9":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"355":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"418":{"tf":1.0}}}}},"_":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"_":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"736":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":1,"docs":{"880":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"a":{"(":{"1":{"df":1,"docs":{"749":{"tf":1.0}}},"df":0,"docs":{},"x":{"^":{"df":0,"docs":{},"u":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}}},".":{"df":0,"docs":{},"k":{".":{"a":{"df":2,"docs":{"111":{"tf":1.0},"368":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"[":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{}}}},"b":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"871":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":12,"docs":{"114":{"tf":1.0},"199":{"tf":1.7320508075688772},"203":{"tf":1.0},"3":{"tf":1.4142135623730951},"375":{"tf":1.0},"473":{"tf":1.0},"515":{"tf":1.0},"602":{"tf":1.0},"786":{"tf":1.0},"849":{"tf":1.0},"875":{"tf":2.23606797749979},"942":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"188":{"tf":1.0}}}},"v":{"df":33,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"170":{"tf":1.0},"203":{"tf":1.0},"207":{"tf":1.4142135623730951},"417":{"tf":1.0},"420":{"tf":1.0},"446":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"534":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"576":{"tf":1.0},"581":{"tf":1.0},"633":{"tf":1.0},"65":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.7320508075688772},"722":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"847":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"571":{"tf":1.0}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"829":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":8,"docs":{"284":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"782":{"tf":1.7320508075688772},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":3.0},"933":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"796":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772}}}}},"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"18":{"tf":1.0},"322":{"tf":1.0},"323":{"tf":1.0},"38":{"tf":1.0},"696":{"tf":1.0},"83":{"tf":1.0},"932":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"s":{"df":7,"docs":{"142":{"tf":1.0},"255":{"tf":1.4142135623730951},"420":{"tf":1.0},"505":{"tf":1.0},"912":{"tf":1.0},"917":{"tf":1.0},"955":{"tf":1.0}}}}},"c":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"723":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":22,"docs":{"1015":{"tf":1.0},"121":{"tf":1.0},"132":{"tf":1.0},"171":{"tf":1.0},"200":{"tf":1.4142135623730951},"207":{"tf":1.0},"222":{"tf":1.0},"254":{"tf":1.0},"270":{"tf":1.4142135623730951},"425":{"tf":1.0},"441":{"tf":1.0},"503":{"tf":1.0},"559":{"tf":1.0},"660":{"tf":1.0},"735":{"tf":3.0},"736":{"tf":1.0},"739":{"tf":1.0},"755":{"tf":1.0},"777":{"tf":1.0},"85":{"tf":1.0},"879":{"tf":1.0},"890":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"s":{"df":32,"docs":{"140":{"tf":1.0},"144":{"tf":1.0},"19":{"tf":1.0},"231":{"tf":1.0},"255":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":1.0},"340":{"tf":1.0},"372":{"tf":1.0},"402":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"423":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":2.0},"498":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":2.0},"697":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":1.0},"874":{"tf":1.0},"912":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"763":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":3,"docs":{"166":{"tf":1.0},"173":{"tf":1.0},"39":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":2,"docs":{"655":{"tf":1.0},"742":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"346":{"tf":1.0},"526":{"tf":1.0}}}}}}}},"r":{"d":{"df":14,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"22":{"tf":1.0},"234":{"tf":1.0},"273":{"tf":1.0},"29":{"tf":1.0},"333":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"436":{"tf":1.0},"537":{"tf":1.0},"6":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"1004":{"tf":1.0},"6":{"tf":1.4142135623730951},"7":{"tf":1.0},"700":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"881":{"tf":1.0}}},"df":0,"docs":{},"t":{"'":{"df":2,"docs":{"848":{"tf":1.0},"850":{"tf":1.0}}},"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"44":{"tf":1.0},"46":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"455":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":69,"docs":{"126":{"tf":1.0},"145":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.0},"205":{"tf":2.8284271247461903},"207":{"tf":1.4142135623730951},"21":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":1.0},"375":{"tf":1.0},"402":{"tf":1.7320508075688772},"417":{"tf":1.0},"452":{"tf":1.7320508075688772},"453":{"tf":1.4142135623730951},"456":{"tf":1.0},"461":{"tf":1.0},"515":{"tf":1.0},"537":{"tf":1.4142135623730951},"54":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":2.23606797749979},"602":{"tf":1.0},"603":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":2.0},"697":{"tf":1.0},"742":{"tf":1.0},"759":{"tf":1.4142135623730951},"782":{"tf":1.7320508075688772},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.7320508075688772},"79":{"tf":1.0},"799":{"tf":2.0},"80":{"tf":1.4142135623730951},"81":{"tf":4.795831523312719},"814":{"tf":1.0},"83":{"tf":3.1622776601683795},"84":{"tf":3.1622776601683795},"841":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":1.7320508075688772},"848":{"tf":1.4142135623730951},"849":{"tf":2.23606797749979},"85":{"tf":2.0},"852":{"tf":1.0},"872":{"tf":2.0},"874":{"tf":3.3166247903554},"875":{"tf":2.6457513110645907},"876":{"tf":2.449489742783178},"878":{"tf":2.0},"879":{"tf":8.426149773176359},"880":{"tf":2.449489742783178},"881":{"tf":2.449489742783178},"885":{"tf":2.449489742783178},"886":{"tf":1.0},"889":{"tf":1.0},"890":{"tf":1.0},"897":{"tf":1.0},"913":{"tf":1.4142135623730951},"914":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.0},"932":{"tf":3.4641016151377544},"95":{"tf":1.4142135623730951},"979":{"tf":1.0}},"i":{"d":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"3":{"2":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"696":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":10,"docs":{"19":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"221":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"783":{"tf":1.0},"786":{"tf":1.0},"83":{"tf":1.0},"879":{"tf":2.0}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":2,"docs":{"265":{"tf":1.0},"267":{"tf":1.4142135623730951}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"51":{"tf":1.0}}},"df":0,"docs":{}}}},"df":10,"docs":{"222":{"tf":1.0},"267":{"tf":1.0},"322":{"tf":1.0},"344":{"tf":2.23606797749979},"345":{"tf":1.0},"352":{"tf":1.7320508075688772},"38":{"tf":1.4142135623730951},"47":{"tf":2.0},"49":{"tf":1.4142135623730951},"51":{"tf":1.0}}}}},"r":{"df":4,"docs":{"218":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"938":{"tf":1.0}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":29,"docs":{"1004":{"tf":1.4142135623730951},"137":{"tf":1.0},"186":{"tf":1.0},"208":{"tf":1.0},"235":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"295":{"tf":1.0},"346":{"tf":1.0},"404":{"tf":1.0},"532":{"tf":1.0},"54":{"tf":1.0},"559":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"658":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.0},"721":{"tf":1.0},"752":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"829":{"tf":1.4142135623730951},"874":{"tf":1.4142135623730951},"880":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"934":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":4,"docs":{"231":{"tf":1.0},"349":{"tf":1.0},"473":{"tf":1.0},"629":{"tf":1.0}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"894":{"tf":1.0}}}}}}},"t":{"df":7,"docs":{"273":{"tf":1.0},"602":{"tf":1.0},"644":{"tf":1.0},"705":{"tf":1.0},"77":{"tf":1.0},"863":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":14,"docs":{"108":{"tf":1.0},"111":{"tf":2.0},"210":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"300":{"tf":1.0},"600":{"tf":1.0},"700":{"tf":1.0},"776":{"tf":1.0},"844":{"tf":1.0},"879":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0}}}},"v":{"df":16,"docs":{"1004":{"tf":1.7320508075688772},"205":{"tf":1.0},"267":{"tf":1.0},"323":{"tf":1.0},"422":{"tf":1.0},"52":{"tf":1.0},"567":{"tf":1.0},"65":{"tf":1.0},"777":{"tf":1.4142135623730951},"797":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":8,"docs":{"124":{"tf":2.23606797749979},"125":{"tf":1.0},"145":{"tf":1.0},"267":{"tf":1.7320508075688772},"373":{"tf":1.0},"696":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":43,"docs":{"166":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"39":{"tf":1.0},"412":{"tf":1.0},"428":{"tf":1.0},"455":{"tf":1.7320508075688772},"505":{"tf":1.0},"519":{"tf":1.4142135623730951},"521":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"528":{"tf":1.0},"60":{"tf":1.4142135623730951},"602":{"tf":1.0},"614":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"63":{"tf":1.0},"651":{"tf":1.0},"658":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.4142135623730951},"751":{"tf":1.0},"761":{"tf":1.0},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"911":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"935":{"tf":1.0}}}},"df":0,"docs":{}}}},"d":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"841":{"tf":1.0}}},"p":{"df":0,"docs":{},"t":{"df":17,"docs":{"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"151":{"tf":1.0},"159":{"tf":1.0},"177":{"tf":1.0},"282":{"tf":1.4142135623730951},"418":{"tf":1.0},"420":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"72":{"tf":1.0},"741":{"tf":1.0},"743":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":1.0},"84":{"tf":1.0}}}}},"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":3,"docs":{"874":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.0}}}}}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"300":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.7320508075688772}}}}}}},"df":57,"docs":{"105":{"tf":1.0},"172":{"tf":1.0},"180":{"tf":1.0},"187":{"tf":1.0},"221":{"tf":1.0},"251":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"386":{"tf":1.7320508075688772},"429":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"485":{"tf":1.0},"495":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"512":{"tf":1.0},"520":{"tf":1.0},"526":{"tf":1.7320508075688772},"549":{"tf":1.0},"576":{"tf":1.4142135623730951},"586":{"tf":1.0},"588":{"tf":1.4142135623730951},"589":{"tf":1.0},"593":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"664":{"tf":1.0},"673":{"tf":1.0},"68":{"tf":1.0},"689":{"tf":1.0},"714":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"773":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"831":{"tf":1.4142135623730951},"841":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"857":{"tf":1.0},"860":{"tf":1.0},"87":{"tf":1.0},"871":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0},"890":{"tf":1.0},"894":{"tf":1.0},"908":{"tf":1.7320508075688772},"934":{"tf":1.0},"942":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":3,"docs":{"410":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"872":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"t":{"df":60,"docs":{"1010":{"tf":1.0},"113":{"tf":1.0},"12":{"tf":1.0},"121":{"tf":1.0},"127":{"tf":1.0},"131":{"tf":1.0},"16":{"tf":1.0},"170":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.0},"281":{"tf":1.0},"3":{"tf":1.0},"340":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"402":{"tf":1.0},"500":{"tf":1.0},"537":{"tf":1.4142135623730951},"563":{"tf":1.0},"568":{"tf":1.0},"570":{"tf":1.0},"572":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"628":{"tf":1.0},"634":{"tf":1.0},"638":{"tf":1.0},"64":{"tf":1.4142135623730951},"642":{"tf":1.0},"648":{"tf":1.0},"651":{"tf":1.0},"736":{"tf":1.0},"751":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"864":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":1.0},"889":{"tf":1.0},"902":{"tf":1.0},"912":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.4142135623730951},"95":{"tf":1.0},"955":{"tf":1.0},"968":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"890":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"835":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":16,"docs":{"141":{"tf":1.0},"166":{"tf":1.0},"204":{"tf":1.4142135623730951},"33":{"tf":1.0},"440":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"628":{"tf":1.0},"770":{"tf":1.0},"780":{"tf":1.0},"807":{"tf":1.0},"860":{"tf":1.0},"909":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}}}}},"r":{"df":2,"docs":{"253":{"tf":2.0},"254":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"df":38,"docs":{"1006":{"tf":1.0},"1014":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"253":{"tf":1.0},"254":{"tf":2.0},"28":{"tf":1.0},"285":{"tf":1.0},"296":{"tf":1.0},"323":{"tf":1.0},"361":{"tf":1.0},"365":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"46":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":2.0},"588":{"tf":1.4142135623730951},"727":{"tf":1.0},"742":{"tf":1.0},"773":{"tf":1.0},"784":{"tf":1.0},"80":{"tf":1.4142135623730951},"81":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"928":{"tf":1.0},"942":{"tf":1.0},"965":{"tf":1.0}}}}}}},"df":52,"docs":{"107":{"tf":1.0},"12":{"tf":1.0},"130":{"tf":1.0},"137":{"tf":1.0},"170":{"tf":1.0},"205":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.7320508075688772},"269":{"tf":1.0},"288":{"tf":1.0},"343":{"tf":1.0},"364":{"tf":1.0},"375":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.0},"440":{"tf":1.4142135623730951},"441":{"tf":1.0},"450":{"tf":1.0},"500":{"tf":1.0},"526":{"tf":1.7320508075688772},"553":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.0},"586":{"tf":1.4142135623730951},"619":{"tf":1.0},"629":{"tf":1.0},"648":{"tf":1.0},"650":{"tf":1.4142135623730951},"668":{"tf":1.4142135623730951},"673":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"729":{"tf":1.0},"78":{"tf":1.4142135623730951},"799":{"tf":1.0},"831":{"tf":1.0},"842":{"tf":1.0},"85":{"tf":1.0},"853":{"tf":1.0},"860":{"tf":1.0},"867":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"927":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.4142135623730951},"95":{"tf":1.0},"956":{"tf":1.0},"962":{"tf":1.0}},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":3,"docs":{"210":{"tf":1.0},"315":{"tf":1.0},"913":{"tf":1.4142135623730951}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"1008":{"tf":1.0},"427":{"tf":1.0},"69":{"tf":1.0},"773":{"tf":1.0},"847":{"tf":1.0},"900":{"tf":1.0}}}}},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":30,"docs":{"1004":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"142":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"182":{"tf":1.4142135623730951},"184":{"tf":1.7320508075688772},"186":{"tf":1.0},"194":{"tf":1.0},"203":{"tf":1.0},"253":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"416":{"tf":1.4142135623730951},"417":{"tf":1.0},"418":{"tf":1.4142135623730951},"427":{"tf":2.0},"428":{"tf":1.0},"429":{"tf":1.0},"469":{"tf":1.0},"50":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"77":{"tf":1.0},"776":{"tf":2.23606797749979},"811":{"tf":1.0},"945":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":3,"docs":{"849":{"tf":1.0},"852":{"tf":1.0},"872":{"tf":1.0}}}}}}},"t":{"df":1,"docs":{"725":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":10,"docs":{"311":{"tf":1.4142135623730951},"330":{"tf":1.0},"356":{"tf":1.0},"358":{"tf":1.0},"40":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.4142135623730951},"515":{"tf":1.0},"718":{"tf":1.0},"95":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"598":{"tf":1.0},"613":{"tf":1.0},"692":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"a":{"df":0,"docs":{},"n":{"c":{"df":7,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"761":{"tf":1.0},"777":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"g":{"df":10,"docs":{"289":{"tf":1.0},"38":{"tf":1.0},"40":{"tf":1.0},"429":{"tf":1.0},"453":{"tf":1.0},"526":{"tf":1.0},"574":{"tf":1.0},"61":{"tf":1.0},"777":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"440":{"tf":1.0},"724":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":3,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"528":{"tf":1.0}}}}}}},"i":{"c":{"df":1,"docs":{"290":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":1,"docs":{"576":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":1,"docs":{"392":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":28,"docs":{"100":{"tf":1.0},"125":{"tf":1.0},"132":{"tf":1.0},"185":{"tf":1.4142135623730951},"190":{"tf":1.0},"240":{"tf":1.0},"255":{"tf":1.0},"276":{"tf":1.0},"358":{"tf":1.0},"369":{"tf":1.0},"41":{"tf":1.0},"418":{"tf":1.0},"442":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.4142135623730951},"72":{"tf":1.0},"773":{"tf":1.0},"804":{"tf":1.4142135623730951},"811":{"tf":1.0},"822":{"tf":1.0},"835":{"tf":1.0},"885":{"tf":1.0},"949":{"tf":1.0},"962":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"843":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"752":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"d":{"df":5,"docs":{"776":{"tf":1.0},"858":{"tf":1.0},"872":{"tf":1.0},"912":{"tf":1.0},"942":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"127":{"tf":1.0},"267":{"tf":1.0},"30":{"tf":1.0},"759":{"tf":1.0},"932":{"tf":1.0}}}}}}}}}},"g":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":11,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"522":{"tf":1.0},"540":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"722":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"815":{"tf":1.0}},"s":{"df":0,"docs":{},"t":{"df":15,"docs":{"108":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"528":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.0},"628":{"tf":1.0},"642":{"tf":1.0},"720":{"tf":1.0},"777":{"tf":1.0},"786":{"tf":1.4142135623730951},"913":{"tf":1.0},"931":{"tf":1.0}}}}}}},"df":1,"docs":{"513":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"849":{"tf":1.0}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":4,"docs":{"24":{"tf":1.0},"44":{"tf":1.0},"49":{"tf":1.0},"710":{"tf":1.4142135623730951}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"752":{"tf":1.4142135623730951}}}}}}},"i":{"df":0,"docs":{},"l":{"df":9,"docs":{"140":{"tf":1.0},"195":{"tf":1.7320508075688772},"210":{"tf":1.0},"216":{"tf":1.0},"374":{"tf":1.0},"58":{"tf":1.0},"811":{"tf":1.0},"846":{"tf":1.0},"938":{"tf":1.0}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":5,"docs":{"273":{"tf":1.0},"420":{"tf":1.0},"469":{"tf":1.0},"799":{"tf":1.0},"848":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"729":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":3,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"974":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":2,"docs":{"402":{"tf":1.0},"497":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":1,"docs":{"603":{"tf":1.7320508075688772}}}},"i":{"df":0,"docs":{},"m":{"df":27,"docs":{"106":{"tf":1.0},"18":{"tf":1.0},"207":{"tf":1.0},"249":{"tf":1.0},"296":{"tf":1.0},"313":{"tf":1.0},"323":{"tf":1.0},"326":{"tf":1.0},"335":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"412":{"tf":1.4142135623730951},"42":{"tf":1.0},"423":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"564":{"tf":1.0},"58":{"tf":1.0},"632":{"tf":1.0},"679":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.4142135623730951},"80":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}},"r":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{}}},"k":{"a":{"df":1,"docs":{"204":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"l":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"549":{"tf":1.0}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"549":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"df":8,"docs":{"132":{"tf":1.0},"175":{"tf":1.0},"213":{"tf":1.4142135623730951},"435":{"tf":2.0},"455":{"tf":1.0},"560":{"tf":1.0},"571":{"tf":1.0},"721":{"tf":1.0}}}}}}}}},"i":{"a":{"df":6,"docs":{"322":{"tf":1.0},"332":{"tf":1.0},"692":{"tf":1.4142135623730951},"696":{"tf":1.0},"697":{"tf":2.23606797749979},"698":{"tf":1.0}},"s":{"df":8,"docs":{"6":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":2.8284271247461903},"698":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.7320508075688772}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0}}}}}}}}}},"c":{"df":7,"docs":{"208":{"tf":4.242640687119285},"741":{"tf":1.0},"796":{"tf":2.0},"799":{"tf":2.0},"81":{"tf":2.0},"83":{"tf":1.0},"878":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"267":{"tf":1.0},"428":{"tf":1.0},"575":{"tf":1.0}}}},"n":{"df":1,"docs":{"430":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":2,"docs":{"563":{"tf":1.0},"583":{"tf":1.0}}}}},"df":0,"docs":{}}},"v":{"df":1,"docs":{"303":{"tf":1.0}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"284":{"tf":1.0},"292":{"tf":1.0}}}}}}}}},"i":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}},"df":37,"docs":{"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"204":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.0},"212":{"tf":1.0},"214":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":2.449489742783178},"220":{"tf":1.4142135623730951},"226":{"tf":1.4142135623730951},"366":{"tf":1.0},"373":{"tf":1.4142135623730951},"374":{"tf":1.7320508075688772},"380":{"tf":1.0},"539":{"tf":1.4142135623730951},"724":{"tf":1.0},"730":{"tf":1.7320508075688772},"731":{"tf":1.0},"732":{"tf":3.7416573867739413},"735":{"tf":3.4641016151377544},"740":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.7320508075688772},"776":{"tf":1.7320508075688772},"777":{"tf":1.0},"779":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":2.23606797749979},"832":{"tf":1.4142135623730951},"840":{"tf":1.0},"876":{"tf":1.0},"931":{"tf":1.4142135623730951}}},"df":0,"docs":{},"w":{"(":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":124,"docs":{"1004":{"tf":1.0},"103":{"tf":1.0},"107":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0},"136":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":2.23606797749979},"22":{"tf":1.0},"221":{"tf":1.4142135623730951},"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"254":{"tf":1.0},"28":{"tf":1.0},"284":{"tf":1.4142135623730951},"289":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.0},"308":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"38":{"tf":1.0},"39":{"tf":1.0},"407":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"46":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"470":{"tf":1.7320508075688772},"485":{"tf":1.0},"49":{"tf":1.0},"542":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"6":{"tf":1.0},"600":{"tf":2.0},"602":{"tf":2.449489742783178},"605":{"tf":1.0},"606":{"tf":1.0},"614":{"tf":1.0},"618":{"tf":1.0},"619":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.4142135623730951},"640":{"tf":1.0},"643":{"tf":1.0},"649":{"tf":1.0},"653":{"tf":1.0},"659":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":2.6457513110645907},"700":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":2.23606797749979},"776":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"796":{"tf":1.7320508075688772},"799":{"tf":2.0},"811":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"83":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"870":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0},"881":{"tf":1.0},"890":{"tf":1.0},"895":{"tf":1.0},"913":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.7320508075688772},"95":{"tf":1.0},"959":{"tf":1.0},"975":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"281":{"tf":1.0},"284":{"tf":1.0}}}}}}}}}}}}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"44":{"tf":1.0},"599":{"tf":1.0},"711":{"tf":1.4142135623730951}},"g":{"df":9,"docs":{"165":{"tf":1.0},"412":{"tf":1.0},"53":{"tf":1.0},"544":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.0},"640":{"tf":1.0},"776":{"tf":1.0},"945":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"d":{"df":10,"docs":{"38":{"tf":1.0},"461":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.0},"600":{"tf":1.0},"653":{"tf":1.0},"722":{"tf":1.4142135623730951},"796":{"tf":1.0},"799":{"tf":1.0}}},"df":0,"docs":{}}}}}},"p":{"df":0,"docs":{},"h":{"a":{"_":{"df":0,"docs":{},"v":{"df":2,"docs":{"721":{"tf":1.4142135623730951},"722":{"tf":2.0}}},"w":{"df":1,"docs":{"722":{"tf":1.0}}},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"u":{"df":2,"docs":{"721":{"tf":1.0},"723":{"tf":1.0}}},"v":{"df":3,"docs":{"721":{"tf":1.7320508075688772},"722":{"tf":1.4142135623730951},"723":{"tf":1.0}},"}":{",":{"\\":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"v":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":2,"docs":{"724":{"tf":1.0},"725":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"i":{"df":49,"docs":{"131":{"tf":1.0},"132":{"tf":1.0},"149":{"tf":1.4142135623730951},"155":{"tf":1.0},"156":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"210":{"tf":1.0},"234":{"tf":1.0},"252":{"tf":1.4142135623730951},"292":{"tf":1.0},"363":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"38":{"tf":1.0},"424":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"483":{"tf":1.0},"501":{"tf":1.4142135623730951},"503":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.4142135623730951},"61":{"tf":1.0},"615":{"tf":1.0},"650":{"tf":1.0},"659":{"tf":1.0},"680":{"tf":1.0},"697":{"tf":1.7320508075688772},"722":{"tf":1.0},"74":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"776":{"tf":1.0},"811":{"tf":1.0},"853":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"900":{"tf":1.0},"938":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":26,"docs":{"1011":{"tf":1.0},"124":{"tf":1.4142135623730951},"131":{"tf":1.0},"132":{"tf":1.0},"140":{"tf":1.0},"159":{"tf":1.0},"170":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.4142135623730951},"210":{"tf":1.0},"221":{"tf":1.0},"362":{"tf":1.0},"381":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"531":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"818":{"tf":1.0},"88":{"tf":1.0},"928":{"tf":1.0},"953":{"tf":1.0}},"n":{"df":25,"docs":{"1014":{"tf":1.0},"171":{"tf":1.0},"195":{"tf":1.0},"203":{"tf":1.0},"213":{"tf":1.0},"215":{"tf":1.0},"227":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"486":{"tf":1.0},"55":{"tf":1.7320508075688772},"630":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.7320508075688772},"761":{"tf":1.0},"810":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.0},"863":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0}}}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":14,"docs":{"326":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"51":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"778":{"tf":1.0},"792":{"tf":1.0},"81":{"tf":1.0},"874":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"740":{"tf":1.0}}}}}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":45,"docs":{"151":{"tf":1.0},"154":{"tf":1.0},"231":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.0},"281":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"341":{"tf":1.4142135623730951},"348":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.0},"481":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"532":{"tf":1.0},"550":{"tf":1.0},"563":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"67":{"tf":1.7320508075688772},"698":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"735":{"tf":2.8284271247461903},"744":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.0},"848":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}},"z":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"532":{"tf":1.0}}}}}}}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"21":{"tf":1.0},"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"270":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":2,"docs":{"325":{"tf":1.0},"735":{"tf":2.0}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"482":{"tf":1.0},"521":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":49,"docs":{"155":{"tf":1.0},"184":{"tf":1.4142135623730951},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"3":{"tf":1.4142135623730951},"308":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"466":{"tf":1.0},"469":{"tf":1.0},"471":{"tf":1.0},"472":{"tf":1.0},"522":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.4142135623730951},"577":{"tf":1.0},"58":{"tf":1.0},"602":{"tf":1.4142135623730951},"638":{"tf":1.0},"651":{"tf":1.0},"659":{"tf":1.0},"683":{"tf":1.0},"735":{"tf":1.7320508075688772},"763":{"tf":1.0},"765":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"807":{"tf":1.0},"814":{"tf":1.7320508075688772},"829":{"tf":1.7320508075688772},"83":{"tf":1.0},"831":{"tf":1.4142135623730951},"850":{"tf":1.0},"920":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":2.449489742783178},"932":{"tf":3.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"989":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"50":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0}}}}},"n":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"196":{"tf":1.0}}}}},"y":{"df":0,"docs":{},"s":{"df":1,"docs":{"571":{"tf":1.0}},"i":{"df":5,"docs":{"365":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.7320508075688772},"576":{"tf":1.0}}}},"z":{"df":2,"docs":{"3":{"tf":1.0},"724":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"500":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"45":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}}}},"d":{"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":10,"docs":{"114":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"382":{"tf":1.0},"412":{"tf":1.0},"420":{"tf":1.0},"441":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"697":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":1,"docs":{"627":{"tf":1.0}}}},"o":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"95":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"k":{"4":{"df":0,"docs":{},"n":{"df":1,"docs":{"878":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"c":{"df":4,"docs":{"209":{"tf":1.0},"500":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"843":{"tf":1.0}}},"df":0,"docs":{}}},"y":{"df":1,"docs":{"249":{"tf":1.4142135623730951}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"470":{"tf":1.0},"933":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":7,"docs":{"322":{"tf":1.0},"336":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.7320508075688772},"365":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"h":{"df":36,"docs":{"203":{"tf":1.0},"207":{"tf":1.0},"231":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":2.23606797749979},"300":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"363":{"tf":1.0},"364":{"tf":1.0},"374":{"tf":1.0},"428":{"tf":1.0},"450":{"tf":1.4142135623730951},"497":{"tf":1.0},"521":{"tf":1.0},"602":{"tf":1.4142135623730951},"61":{"tf":1.0},"666":{"tf":1.0},"673":{"tf":1.0},"694":{"tf":1.0},"715":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"77":{"tf":1.0},"778":{"tf":1.4142135623730951},"78":{"tf":1.0},"799":{"tf":1.4142135623730951},"81":{"tf":1.0},"84":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"942":{"tf":1.0},"975":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"553":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"38":{"tf":1.0}}}}},"df":2,"docs":{"270":{"tf":1.0},"912":{"tf":1.7320508075688772}}}},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":5,"docs":{"249":{"tf":1.0},"3":{"tf":1.0},"453":{"tf":1.0},"567":{"tf":1.0},"74":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":12,"docs":{"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.4142135623730951},"528":{"tf":1.0},"629":{"tf":1.0},"715":{"tf":1.7320508075688772},"811":{"tf":1.4142135623730951},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.7320508075688772},"817":{"tf":1.0},"848":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":14,"docs":{"151":{"tf":1.0},"152":{"tf":1.0},"199":{"tf":1.7320508075688772},"208":{"tf":1.0},"300":{"tf":1.0},"588":{"tf":1.0},"653":{"tf":1.0},"735":{"tf":2.449489742783178},"761":{"tf":1.0},"800":{"tf":1.0},"831":{"tf":1.0},"852":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"720":{"tf":1.0},"723":{"tf":1.0}}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":3,"docs":{"720":{"tf":1.0},"735":{"tf":1.0},"987":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"588":{"tf":1.0}}}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"205":{"tf":1.0},"843":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"#":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"n":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":37,"docs":{"17":{"tf":1.0},"19":{"tf":1.7320508075688772},"205":{"tf":1.0},"212":{"tf":1.0},"22":{"tf":1.7320508075688772},"234":{"tf":1.0},"279":{"tf":1.7320508075688772},"280":{"tf":1.0},"284":{"tf":1.4142135623730951},"33":{"tf":1.0},"34":{"tf":1.0},"362":{"tf":1.0},"372":{"tf":1.4142135623730951},"382":{"tf":1.0},"390":{"tf":1.0},"395":{"tf":1.0},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"455":{"tf":1.0},"461":{"tf":1.4142135623730951},"519":{"tf":1.0},"565":{"tf":1.0},"622":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.4142135623730951},"847":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0},"95":{"tf":1.0},"961":{"tf":1.0}}},"o":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"p":{"_":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":1,"docs":{"207":{"tf":1.0}}}}},"df":3,"docs":{"199":{"tf":1.0},"234":{"tf":1.0},"919":{"tf":1.0}}}},"df":4,"docs":{"185":{"tf":1.0},"191":{"tf":1.4142135623730951},"904":{"tf":1.0},"921":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"199":{"tf":1.0},"40":{"tf":1.0}}},"r":{"df":10,"docs":{"155":{"tf":1.0},"267":{"tf":1.0},"48":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"534":{"tf":1.0},"629":{"tf":1.0},"680":{"tf":1.0},"844":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"333":{"tf":1.0},"602":{"tf":2.8284271247461903}},"i":{"df":0,"docs":{},"x":{"df":4,"docs":{"430":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"l":{"df":1,"docs":{"95":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{},"’":{"df":1,"docs":{"95":{"tf":1.0}}}},"i":{"c":{"df":19,"docs":{"1004":{"tf":1.0},"125":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.0},"346":{"tf":1.0},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"417":{"tf":1.4142135623730951},"42":{"tf":1.0},"445":{"tf":1.0},"448":{"tf":1.0},"853":{"tf":1.0},"95":{"tf":1.7320508075688772},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"971":{"tf":1.0},"973":{"tf":1.4142135623730951}}},"df":26,"docs":{"1003":{"tf":1.0},"132":{"tf":1.4142135623730951},"140":{"tf":1.0},"148":{"tf":1.0},"151":{"tf":1.4142135623730951},"152":{"tf":1.0},"154":{"tf":1.0},"159":{"tf":1.0},"225":{"tf":1.0},"251":{"tf":1.0},"281":{"tf":1.0},"302":{"tf":1.0},"348":{"tf":1.0},"378":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"455":{"tf":1.0},"499":{"tf":1.0},"51":{"tf":1.0},"532":{"tf":1.0},"573":{"tf":2.23606797749979},"735":{"tf":1.0},"786":{"tf":1.0},"804":{"tf":1.0},"837":{"tf":1.0},"883":{"tf":1.0}}},"y":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"284":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"721":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"a":{"c":{"df":0,"docs":{},"h":{"df":34,"docs":{"1007":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"140":{"tf":1.0},"147":{"tf":1.0},"149":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"29":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.4142135623730951},"368":{"tf":1.0},"373":{"tf":1.0},"39":{"tf":1.0},"410":{"tf":1.0},"416":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.4142135623730951},"46":{"tf":1.0},"563":{"tf":1.0},"6":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"658":{"tf":1.0},"694":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.4142135623730951},"942":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":14,"docs":{"1014":{"tf":1.0},"169":{"tf":1.0},"204":{"tf":1.0},"239":{"tf":1.0},"246":{"tf":1.0},"253":{"tf":1.0},"274":{"tf":1.0},"457":{"tf":1.0},"564":{"tf":1.0},"721":{"tf":1.0},"727":{"tf":1.0},"786":{"tf":1.0},"817":{"tf":1.0},"846":{"tf":1.0}}}}},"v":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"715":{"tf":1.4142135623730951},"716":{"tf":1.0},"717":{"tf":1.0},"724":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"v":{"[":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"2":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"[":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"715":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":3,"docs":{"717":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"716":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"715":{"tf":1.7320508075688772}}}},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"715":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"716":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":1,"docs":{"716":{"tf":1.0}}}}},"df":34,"docs":{"112":{"tf":1.0},"126":{"tf":1.7320508075688772},"16":{"tf":1.0},"193":{"tf":1.0},"272":{"tf":1.0},"450":{"tf":1.7320508075688772},"709":{"tf":1.0},"710":{"tf":2.0},"711":{"tf":2.23606797749979},"714":{"tf":1.7320508075688772},"715":{"tf":2.8284271247461903},"716":{"tf":2.0},"717":{"tf":1.7320508075688772},"720":{"tf":3.3166247903554},"721":{"tf":5.0},"722":{"tf":3.872983346207417},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"725":{"tf":1.4142135623730951},"729":{"tf":1.4142135623730951},"811":{"tf":1.0},"815":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"876":{"tf":1.4142135623730951},"878":{"tf":1.7320508075688772},"879":{"tf":4.898979485566356},"880":{"tf":3.1622776601683795},"881":{"tf":2.6457513110645907},"885":{"tf":2.0},"890":{"tf":1.0},"984":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"872":{"tf":1.0},"875":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"_":{"a":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"\"":{"df":0,"docs":{},"{":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"272":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":7,"docs":{"184":{"tf":1.0},"235":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.4142135623730951},"721":{"tf":1.0},"725":{"tf":1.0},"996":{"tf":1.0}}}}}}}},"r":{"df":1,"docs":{"908":{"tf":1.0}}},"t":{"df":1,"docs":{"61":{"tf":1.0}}}},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":14,"docs":{"114":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"340":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"568":{"tf":1.0},"670":{"tf":1.0},"697":{"tf":1.4142135623730951},"777":{"tf":1.0},"95":{"tf":1.0}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"50":{"tf":1.0}}}}}}},"o":{"df":4,"docs":{"38":{"tf":1.0},"39":{"tf":1.0},"46":{"tf":1.0},"54":{"tf":1.0}}}},"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"470":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":5,"docs":{"147":{"tf":1.0},"366":{"tf":1.0},"373":{"tf":1.4142135623730951},"46":{"tf":1.0},"74":{"tf":1.0}}}}}},"df":0,"docs":{}}},"v":{"df":5,"docs":{"498":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":2.0},"502":{"tf":1.0},"512":{"tf":2.23606797749979}}}}}},"df":0,"docs":{},"e":{"a":{"df":2,"docs":{"1008":{"tf":1.0},"773":{"tf":1.0}}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":5,"docs":{"500":{"tf":1.0},"761":{"tf":1.4142135623730951},"832":{"tf":1.0},"850":{"tf":1.0},"874":{"tf":1.0}}}},"df":0,"docs":{}}},"g":{"df":2,"docs":{"831":{"tf":1.4142135623730951},"898":{"tf":1.0}},"u":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{}},"df":5,"docs":{"267":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"679":{"tf":1.0},"928":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"21":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"222":{"tf":1.0},"23":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":2.0},"416":{"tf":1.0},"429":{"tf":1.0},"749":{"tf":1.0},"773":{"tf":1.0},"879":{"tf":3.4641016151377544}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":6,"docs":{"264":{"tf":1.0},"267":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"742":{"tf":1.0},"779":{"tf":1.0}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":21,"docs":{"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"147":{"tf":1.0},"166":{"tf":1.0},"206":{"tf":1.0},"216":{"tf":1.0},"257":{"tf":1.0},"406":{"tf":1.0},"461":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"619":{"tf":1.0},"747":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"786":{"tf":1.0},"831":{"tf":1.0},"874":{"tf":1.0},"996":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"y":{"(":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"455":{"tf":1.0}}}}}},"df":5,"docs":{"170":{"tf":1.0},"332":{"tf":1.0},"432":{"tf":1.0},"455":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"223":{"tf":1.4142135623730951}}}},"u":{"d":{"a":{"df":1,"docs":{"782":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":119,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.4142135623730951},"105":{"tf":1.0},"106":{"tf":1.0},"120":{"tf":1.0},"122":{"tf":1.0},"133":{"tf":1.0},"136":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"150":{"tf":1.0},"161":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.0},"182":{"tf":1.0},"192":{"tf":1.0},"195":{"tf":1.0},"214":{"tf":1.0},"215":{"tf":1.0},"228":{"tf":1.0},"229":{"tf":1.0},"242":{"tf":1.0},"247":{"tf":1.0},"260":{"tf":1.0},"268":{"tf":1.0},"277":{"tf":1.0},"279":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.0},"308":{"tf":1.0},"311":{"tf":1.0},"319":{"tf":1.0},"322":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"366":{"tf":1.0},"383":{"tf":1.0},"386":{"tf":1.0},"397":{"tf":1.0},"400":{"tf":1.0},"409":{"tf":1.0},"430":{"tf":1.0},"447":{"tf":1.0},"451":{"tf":1.0},"462":{"tf":1.0},"465":{"tf":1.0},"479":{"tf":1.0},"481":{"tf":1.0},"492":{"tf":1.0},"495":{"tf":1.0},"510":{"tf":1.0},"513":{"tf":1.0},"532":{"tf":1.0},"535":{"tf":1.0},"546":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.0},"563":{"tf":1.0},"583":{"tf":1.0},"584":{"tf":1.0},"595":{"tf":1.0},"598":{"tf":1.0},"610":{"tf":1.0},"613":{"tf":1.0},"624":{"tf":1.0},"627":{"tf":1.0},"646":{"tf":1.0},"649":{"tf":1.0},"661":{"tf":1.0},"664":{"tf":1.0},"675":{"tf":1.0},"678":{"tf":1.0},"689":{"tf":1.0},"692":{"tf":1.0},"706":{"tf":1.0},"709":{"tf":1.0},"726":{"tf":1.0},"730":{"tf":1.0},"738":{"tf":1.0},"74":{"tf":1.0},"741":{"tf":1.0},"754":{"tf":1.0},"757":{"tf":1.0},"768":{"tf":1.0},"771":{"tf":1.0},"780":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.0},"795":{"tf":1.0},"805":{"tf":1.0},"808":{"tf":1.0},"824":{"tf":1.0},"827":{"tf":1.0},"838":{"tf":1.0},"857":{"tf":1.0},"869":{"tf":1.0},"871":{"tf":1.0},"888":{"tf":1.0},"891":{"tf":1.0},"90":{"tf":1.0},"905":{"tf":1.0},"908":{"tf":1.4142135623730951},"922":{"tf":1.0},"923":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.0},"940":{"tf":1.0},"954":{"tf":1.0},"957":{"tf":1.0},"971":{"tf":1.0},"974":{"tf":1.0},"985":{"tf":1.0},"988":{"tf":1.0},"999":{"tf":1.0}},"i":{"c":{"df":0,"docs":{},"l":{"df":3,"docs":{"214":{"tf":1.4142135623730951},"905":{"tf":1.0},"923":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"414":{"tf":1.7320508075688772},"423":{"tf":1.0}}}}}}},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}},"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"i":{"df":1,"docs":{"343":{"tf":1.0}}}}},"df":0,"docs":{},"k":{"df":7,"docs":{"254":{"tf":1.0},"497":{"tf":1.4142135623730951},"6":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"848":{"tf":1.0},"933":{"tf":1.0}}},"n":{".":{"1":{"df":1,"docs":{"331":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"1014":{"tf":1.0},"209":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.4142135623730951},"361":{"tf":1.0},"727":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"807":{"tf":1.0},"842":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"29":{"tf":1.0},"53":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"t":{"!":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"x":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"347":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}}}}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"347":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"!":{"(":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"x":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":1,"docs":{"435":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"df":5,"docs":{"350":{"tf":1.0},"418":{"tf":1.0},"576":{"tf":1.0},"582":{"tf":1.0},"781":{"tf":1.0}}}},"t":{"'":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}},"(":{"df":1,"docs":{"602":{"tf":1.0}}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"6":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"x":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"668":{"tf":1.0},"670":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"668":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":66,"docs":{"1":{"tf":1.7320508075688772},"114":{"tf":1.0},"14":{"tf":1.0},"18":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"3":{"tf":2.449489742783178},"35":{"tf":1.0},"373":{"tf":2.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.0},"410":{"tf":1.7320508075688772},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"415":{"tf":1.0},"417":{"tf":1.4142135623730951},"418":{"tf":2.0},"423":{"tf":1.0},"428":{"tf":1.0},"465":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"472":{"tf":1.0},"473":{"tf":1.4142135623730951},"5":{"tf":2.8284271247461903},"598":{"tf":1.4142135623730951},"599":{"tf":2.0},"6":{"tf":3.7416573867739413},"600":{"tf":3.4641016151377544},"602":{"tf":5.196152422706632},"603":{"tf":4.358898943540674},"605":{"tf":2.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"653":{"tf":2.8284271247461903},"654":{"tf":1.4142135623730951},"655":{"tf":1.0},"659":{"tf":1.4142135623730951},"663":{"tf":1.0},"666":{"tf":2.0},"668":{"tf":1.0},"670":{"tf":1.0},"692":{"tf":1.7320508075688772},"693":{"tf":1.0},"694":{"tf":1.7320508075688772},"696":{"tf":1.0},"697":{"tf":2.8284271247461903},"698":{"tf":1.0},"699":{"tf":1.7320508075688772},"7":{"tf":1.4142135623730951},"700":{"tf":1.4142135623730951},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"8":{"tf":1.0},"81":{"tf":1.0},"9":{"tf":1.0},"959":{"tf":1.0},"971":{"tf":1.0},"976":{"tf":1.0},"979":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"(":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":1,"docs":{"666":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"u":{"b":{"df":2,"docs":{"600":{"tf":1.0},"934":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"d":{"df":4,"docs":{"24":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"603":{"tf":1.0},"7":{"tf":1.4142135623730951}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"1":{"tf":1.0},"7":{"tf":1.0},"9":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":3,"docs":{"205":{"tf":1.0},"6":{"tf":1.7320508075688772},"7":{"tf":1.4142135623730951}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}},"`":{"df":1,"docs":{"602":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.4142135623730951},"223":{"tf":1.0}},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"208":{"tf":1.7320508075688772},"221":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":22,"docs":{"155":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"204":{"tf":2.449489742783178},"205":{"tf":3.1622776601683795},"208":{"tf":3.1622776601683795},"216":{"tf":1.4142135623730951},"221":{"tf":2.449489742783178},"3":{"tf":1.0},"323":{"tf":1.0},"430":{"tf":1.7320508075688772},"431":{"tf":1.0},"438":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.0},"636":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":2.6457513110645907},"735":{"tf":1.0}},"e":{"d":{"(":{"a":{"df":1,"docs":{"208":{"tf":2.0}}},"b":{"df":1,"docs":{"208":{"tf":2.449489742783178}}},"c":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"d":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"816":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"107":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"952":{"tf":1.0}}}}},"o":{"c":{"df":0,"docs":{},"i":{"df":26,"docs":{"138":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"209":{"tf":1.0},"24":{"tf":1.4142135623730951},"273":{"tf":1.0},"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"346":{"tf":1.7320508075688772},"348":{"tf":1.7320508075688772},"349":{"tf":2.23606797749979},"350":{"tf":1.0},"351":{"tf":1.7320508075688772},"571":{"tf":1.0},"761":{"tf":1.4142135623730951},"815":{"tf":1.0},"895":{"tf":1.0},"902":{"tf":1.0},"932":{"tf":1.0},"941":{"tf":1.0},"961":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"m":{"df":28,"docs":{"206":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"39":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"528":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"717":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"863":{"tf":1.0},"933":{"tf":1.0}},"p":{"df":0,"docs":{},"t":{"df":13,"docs":{"199":{"tf":1.0},"231":{"tf":1.4142135623730951},"267":{"tf":1.0},"402":{"tf":1.7320508075688772},"46":{"tf":1.0},"514":{"tf":1.0},"692":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":2.0},"710":{"tf":1.0},"721":{"tf":1.4142135623730951},"724":{"tf":1.0}}}}},"r":{"df":4,"docs":{"267":{"tf":1.0},"303":{"tf":1.0},"45":{"tf":1.0},"514":{"tf":1.0}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"990":{"tf":1.0}}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"602":{"tf":1.0}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"58":{"tf":1.0},"959":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"m":{".":{"0":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"l":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"[":{"df":0,"docs":{},"i":{"]":{".":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"440":{"tf":1.0},"600":{"tf":1.0}}}},"t":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"879":{"tf":1.0}}},"k":{"df":19,"docs":{"114":{"tf":1.0},"124":{"tf":1.4142135623730951},"127":{"tf":1.4142135623730951},"249":{"tf":1.0},"255":{"tf":1.4142135623730951},"356":{"tf":1.0},"453":{"tf":1.4142135623730951},"505":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":2.23606797749979},"573":{"tf":1.0},"577":{"tf":2.23606797749979},"58":{"tf":1.0},"619":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"230":{"tf":1.0}},"t":{"df":20,"docs":{"123":{"tf":1.0},"231":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":2.6457513110645907},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"437":{"tf":1.0},"450":{"tf":1.4142135623730951},"497":{"tf":1.0},"573":{"tf":1.0},"609":{"tf":1.0},"689":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"733":{"tf":1.0},"797":{"tf":1.0},"831":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0}},"s":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"342":{"tf":2.0},"346":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"53":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"231":{"tf":1.0},"40":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"565":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":4,"docs":{"373":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"669":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":13,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"133":{"tf":1.4142135623730951},"198":{"tf":2.0},"203":{"tf":1.0},"205":{"tf":1.0},"370":{"tf":1.0},"571":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"928":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":2,"docs":{"378":{"tf":1.0},"883":{"tf":1.0}}}}}}}}},"df":23,"docs":{"115":{"tf":1.0},"121":{"tf":1.4142135623730951},"128":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"282":{"tf":1.0},"304":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.4142135623730951},"354":{"tf":1.0},"39":{"tf":1.0},"45":{"tf":1.4142135623730951},"457":{"tf":1.0},"53":{"tf":1.0},"639":{"tf":1.0},"701":{"tf":1.0},"819":{"tf":1.0},"850":{"tf":1.0},"935":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.4142135623730951},"965":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"244":{"tf":1.0}}}}}}},"df":0,"docs":{},"g":{"df":3,"docs":{"182":{"tf":1.0},"311":{"tf":1.0},"79":{"tf":1.0}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"106":{"tf":1.0},"93":{"tf":1.0},"988":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":4,"docs":{"410":{"tf":1.0},"940":{"tf":1.0},"945":{"tf":1.0},"957":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"h":{"df":2,"docs":{"849":{"tf":1.7320508075688772},"850":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"175":{"tf":1.0},"177":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"848":{"tf":1.0},"95":{"tf":1.4142135623730951}}}}},"o":{"df":0,"docs":{},"r":{"df":106,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.4142135623730951},"169":{"tf":1.7320508075688772},"17":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.4142135623730951},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"284":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"3":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"323":{"tf":1.4142135623730951},"324":{"tf":1.0},"327":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":1.0},"345":{"tf":2.449489742783178},"346":{"tf":3.0},"347":{"tf":1.0},"348":{"tf":1.4142135623730951},"349":{"tf":3.1622776601683795},"350":{"tf":2.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"45":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.4142135623730951},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.7320508075688772},"549":{"tf":2.0},"550":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":2.0},"555":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"737":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"765":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"831":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":1.0},"85":{"tf":1.7320508075688772},"857":{"tf":1.0},"871":{"tf":1.0},"876":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"94":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"325":{"tf":1.0}},"h":{"df":0,"docs":{},"i":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}},"y":{"_":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"2":{"df":1,"docs":{"553":{"tf":1.0}}},"3":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":3,"docs":{"349":{"tf":1.7320508075688772},"350":{"tf":1.0},"351":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"350":{"tf":1.7320508075688772}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"349":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"o":{"df":1,"docs":{"208":{"tf":1.0}},"m":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"191":{"tf":2.0},"813":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0}}}},"df":5,"docs":{"427":{"tf":1.0},"442":{"tf":1.0},"516":{"tf":1.0},"847":{"tf":1.0},"959":{"tf":1.0}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"843":{"tf":1.0},"876":{"tf":1.0}}}}}}},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"776":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"v":{"a":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"63":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"65":{"tf":1.0}}}},"df":0,"docs":{}},"df":65,"docs":{"166":{"tf":1.0},"169":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":2.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.0},"264":{"tf":1.0},"282":{"tf":1.0},"346":{"tf":1.0},"372":{"tf":1.0},"38":{"tf":1.0},"417":{"tf":1.0},"430":{"tf":2.23606797749979},"431":{"tf":1.4142135623730951},"432":{"tf":1.7320508075688772},"435":{"tf":1.0},"436":{"tf":1.4142135623730951},"437":{"tf":1.4142135623730951},"439":{"tf":2.0},"440":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.4142135623730951},"449":{"tf":1.0},"450":{"tf":2.0},"46":{"tf":1.0},"47":{"tf":2.449489742783178},"497":{"tf":1.4142135623730951},"55":{"tf":1.0},"563":{"tf":1.0},"568":{"tf":1.0},"619":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.4142135623730951},"65":{"tf":1.0},"67":{"tf":1.0},"69":{"tf":1.4142135623730951},"709":{"tf":1.0},"710":{"tf":1.7320508075688772},"711":{"tf":1.4142135623730951},"712":{"tf":1.0},"714":{"tf":2.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.0},"718":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":2.8284271247461903},"723":{"tf":2.23606797749979},"724":{"tf":2.0},"725":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.4142135623730951},"74":{"tf":1.0},"75":{"tf":1.0},"776":{"tf":1.4142135623730951},"78":{"tf":1.0},"780":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":2.0},"831":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"996":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":1,"docs":{"78":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":12,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"479":{"tf":1.4142135623730951},"51":{"tf":1.0},"515":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"i":{"d":{"df":28,"docs":{"1008":{"tf":1.0},"121":{"tf":1.0},"128":{"tf":1.0},"141":{"tf":1.0},"144":{"tf":1.0},"196":{"tf":1.0},"200":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"252":{"tf":1.4142135623730951},"35":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"520":{"tf":1.0},"575":{"tf":1.0},"640":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"920":{"tf":1.0},"959":{"tf":1.0},"982":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"776":{"tf":1.0}}},"df":13,"docs":{"125":{"tf":1.0},"131":{"tf":1.0},"152":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"63":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0}}},"y":{"df":6,"docs":{"18":{"tf":1.0},"500":{"tf":1.0},"651":{"tf":1.0},"696":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"651":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":1.0}}}},"}":{"_":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":1,"docs":{"47":{"tf":2.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"·":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"b":{"\"":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"a":{"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":1,"docs":{"786":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"a":{"b":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"_":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"252":{"tf":1.0},"261":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"252":{"tf":1.0},"261":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"568":{"tf":2.0},"570":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":47,"docs":{"1004":{"tf":1.0},"126":{"tf":1.0},"184":{"tf":1.0},"203":{"tf":1.0},"221":{"tf":1.4142135623730951},"284":{"tf":1.0},"3":{"tf":1.0},"368":{"tf":1.4142135623730951},"436":{"tf":1.0},"437":{"tf":1.4142135623730951},"450":{"tf":2.0},"47":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.7320508075688772},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"603":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"634":{"tf":1.4142135623730951},"636":{"tf":1.4142135623730951},"637":{"tf":1.0},"64":{"tf":1.0},"642":{"tf":1.0},"709":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":2.8284271247461903},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"761":{"tf":1.4142135623730951},"831":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"933":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"29":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":16,"docs":{"437":{"tf":1.0},"56":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.4142135623730951},"63":{"tf":1.0},"633":{"tf":1.0},"636":{"tf":1.4142135623730951},"637":{"tf":1.0},"65":{"tf":1.7320508075688772},"67":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"720":{"tf":2.6457513110645907},"723":{"tf":1.0},"724":{"tf":2.0}},"s":{"/":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"449":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":8,"docs":{"217":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"501":{"tf":1.0},"891":{"tf":1.0},"894":{"tf":1.0},"908":{"tf":1.0},"911":{"tf":1.0}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"437":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":23,"docs":{"126":{"tf":1.0},"146":{"tf":1.0},"482":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"512":{"tf":1.0},"545":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"586":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"627":{"tf":1.0},"628":{"tf":1.0},"635":{"tf":1.0},"639":{"tf":1.0},"642":{"tf":1.0},"705":{"tf":1.0},"732":{"tf":1.0},"792":{"tf":1.0},"831":{"tf":1.0},"928":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"d":{"df":6,"docs":{"108":{"tf":1.4142135623730951},"124":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.0},"576":{"tf":1.0},"632":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":2,"docs":{"234":{"tf":1.4142135623730951},"370":{"tf":1.0}}},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"199":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"n":{"c":{"df":24,"docs":{"18":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"205":{"tf":2.23606797749979},"22":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"370":{"tf":1.0},"375":{"tf":3.0},"384":{"tf":1.0},"385":{"tf":1.0},"406":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"418":{"tf":1.4142135623730951},"427":{"tf":1.0},"429":{"tf":1.0},"48":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"759":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"945":{"tf":1.0}},"e":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"n":{"d":{"df":1,"docs":{"199":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":5,"docs":{"322":{"tf":1.0},"340":{"tf":1.7320508075688772},"341":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"359":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":13,"docs":{"257":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"507":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"849":{"tf":1.0}}},"r":{"df":0,"docs":{},"e":{"df":6,"docs":{"170":{"tf":1.4142135623730951},"322":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"588":{"tf":1.0},"7":{"tf":1.0}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":15,"docs":{"118":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.0},"58":{"tf":1.0},"602":{"tf":1.4142135623730951},"670":{"tf":1.0},"673":{"tf":1.7320508075688772},"701":{"tf":1.0},"705":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":2.23606797749979}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"199":{"tf":1.0}}}}}}}}}},"{":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":1,"docs":{"45":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"5":{"8":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":68,"docs":{"124":{"tf":1.0},"126":{"tf":1.0},"137":{"tf":1.4142135623730951},"140":{"tf":1.4142135623730951},"141":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"184":{"tf":1.4142135623730951},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"207":{"tf":1.0},"21":{"tf":1.0},"24":{"tf":1.7320508075688772},"240":{"tf":1.0},"3":{"tf":1.4142135623730951},"323":{"tf":1.0},"350":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"402":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.7320508075688772},"415":{"tf":1.0},"416":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.4142135623730951},"428":{"tf":1.0},"429":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"46":{"tf":1.7320508075688772},"465":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.0},"495":{"tf":1.4142135623730951},"50":{"tf":1.0},"515":{"tf":1.4142135623730951},"519":{"tf":1.0},"52":{"tf":1.0},"521":{"tf":1.7320508075688772},"576":{"tf":1.0},"586":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"634":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"747":{"tf":1.0},"754":{"tf":1.0},"797":{"tf":1.0},"808":{"tf":1.7320508075688772},"813":{"tf":1.4142135623730951},"814":{"tf":1.0},"878":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.0},"95":{"tf":1.0},"973":{"tf":1.0},"996":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"267":{"tf":1.0},"752":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}}},"i":{"c":{"df":14,"docs":{"1004":{"tf":1.0},"16":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.7320508075688772},"30":{"tf":1.0},"453":{"tf":1.0},"505":{"tf":1.0},"524":{"tf":1.0},"532":{"tf":1.0},"565":{"tf":1.0},"694":{"tf":1.0},"754":{"tf":1.0},"875":{"tf":1.0},"942":{"tf":1.0}}},"df":9,"docs":{"203":{"tf":1.0},"218":{"tf":1.0},"246":{"tf":1.0},"402":{"tf":1.0},"571":{"tf":1.4142135623730951},"66":{"tf":1.0},"670":{"tf":1.0},"778":{"tf":1.0},"932":{"tf":1.0}}},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"150":{"tf":1.0},"451":{"tf":1.0},"584":{"tf":1.0}}}},"df":0,"docs":{}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":10,"docs":{"313":{"tf":1.0},"315":{"tf":1.0},"449":{"tf":1.0},"517":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"890":{"tf":1.0}}}},"df":0,"docs":{}}},"df":14,"docs":{"208":{"tf":1.7320508075688772},"417":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"47":{"tf":3.3166247903554},"602":{"tf":1.0},"633":{"tf":1.7320508075688772},"696":{"tf":1.4142135623730951},"81":{"tf":2.0},"83":{"tf":2.23606797749979},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"835":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"58":{"tf":1.0},"721":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":34,"docs":{"1015":{"tf":1.0},"113":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.0},"198":{"tf":1.0},"205":{"tf":1.7320508075688772},"206":{"tf":1.0},"208":{"tf":1.0},"232":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"334":{"tf":1.0},"376":{"tf":1.0},"385":{"tf":1.0},"482":{"tf":1.0},"485":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"567":{"tf":1.0},"568":{"tf":1.0},"57":{"tf":1.0},"58":{"tf":1.7320508075688772},"63":{"tf":1.0},"656":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":1.0},"732":{"tf":1.0},"765":{"tf":1.0},"797":{"tf":1.0},"80":{"tf":1.0},"843":{"tf":1.4142135623730951},"987":{"tf":1.0}}}}},"df":70,"docs":{"108":{"tf":1.0},"113":{"tf":1.4142135623730951},"121":{"tf":1.0},"124":{"tf":1.0},"140":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.0},"220":{"tf":1.0},"222":{"tf":1.4142135623730951},"234":{"tf":1.0},"254":{"tf":1.0},"284":{"tf":1.0},"291":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"347":{"tf":1.0},"373":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.7320508075688772},"47":{"tf":1.0},"496":{"tf":1.0},"517":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.4142135623730951},"551":{"tf":1.0},"559":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"724":{"tf":1.7320508075688772},"736":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.7320508075688772},"761":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.0},"902":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.4142135623730951},"932":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"95":{"tf":1.0},"976":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":4,"docs":{"38":{"tf":1.0},"49":{"tf":1.4142135623730951},"500":{"tf":1.0},"714":{"tf":1.0}}},"y":{"df":0,"docs":{},"’":{"df":1,"docs":{"49":{"tf":1.0}}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":63,"docs":{"1014":{"tf":1.0},"121":{"tf":1.0},"126":{"tf":1.7320508075688772},"148":{"tf":1.0},"150":{"tf":1.0},"160":{"tf":1.0},"171":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"265":{"tf":1.0},"291":{"tf":1.4142135623730951},"303":{"tf":1.0},"338":{"tf":1.0},"344":{"tf":1.7320508075688772},"346":{"tf":1.0},"348":{"tf":1.0},"418":{"tf":1.0},"437":{"tf":1.7320508075688772},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"452":{"tf":1.0},"461":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"618":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"645":{"tf":1.0},"661":{"tf":1.0},"670":{"tf":1.0},"675":{"tf":1.0},"69":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"727":{"tf":1.0},"732":{"tf":1.0},"74":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.0},"811":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"837":{"tf":1.0},"879":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"961":{"tf":1.0},"985":{"tf":1.0}},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"670":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"g":{"df":1,"docs":{"267":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":20,"docs":{"126":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":2.23606797749979},"207":{"tf":1.0},"208":{"tf":5.5677643628300215},"221":{"tf":1.4142135623730951},"223":{"tf":1.0},"281":{"tf":1.0},"338":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"371":{"tf":1.0},"440":{"tf":1.4142135623730951},"450":{"tf":1.0},"521":{"tf":1.0},"670":{"tf":1.0},"721":{"tf":1.4142135623730951},"846":{"tf":1.0},"881":{"tf":1.0}},"{":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"h":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":4,"docs":{"602":{"tf":1.0},"848":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.0}}}},"v":{"df":3,"docs":{"563":{"tf":1.0},"666":{"tf":1.0},"761":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":17,"docs":{"1004":{"tf":1.0},"169":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"342":{"tf":1.0},"388":{"tf":1.0},"391":{"tf":1.0},"49":{"tf":1.0},"665":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.4142135623730951},"788":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"976":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":14,"docs":{"123":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"134":{"tf":1.4142135623730951},"72":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"81":{"tf":1.0},"832":{"tf":1.0},"913":{"tf":1.4142135623730951},"975":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"198":{"tf":1.0},"249":{"tf":1.0},"483":{"tf":1.0},"546":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"720":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":11,"docs":{"184":{"tf":1.4142135623730951},"251":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"394":{"tf":1.0},"51":{"tf":1.0},"720":{"tf":1.0},"797":{"tf":1.0},"800":{"tf":1.0},"874":{"tf":1.0},"934":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":5,"docs":{"106":{"tf":1.0},"113":{"tf":1.0},"342":{"tf":1.0},"439":{"tf":1.4142135623730951},"735":{"tf":1.0}}}},"w":{"df":22,"docs":{"185":{"tf":1.0},"204":{"tf":1.4142135623730951},"267":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"45":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"520":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"619":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"777":{"tf":1.0},"814":{"tf":1.0},"992":{"tf":1.0}}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":8,"docs":{"209":{"tf":1.0},"239":{"tf":1.0},"402":{"tf":1.4142135623730951},"406":{"tf":1.0},"669":{"tf":1.0},"732":{"tf":1.0},"739":{"tf":1.0},"980":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"205":{"tf":1.7320508075688772},"414":{"tf":1.0},"603":{"tf":1.0}}},"y":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":6,"docs":{"249":{"tf":1.0},"315":{"tf":1.4142135623730951},"71":{"tf":1.0},"773":{"tf":1.0},"818":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":24,"docs":{"145":{"tf":1.0},"18":{"tf":1.0},"267":{"tf":2.449489742783178},"272":{"tf":1.0},"302":{"tf":1.0},"328":{"tf":1.0},"38":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"632":{"tf":1.0},"663":{"tf":1.0},"720":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":1.7320508075688772},"778":{"tf":1.0},"799":{"tf":1.0},"95":{"tf":1.0},"991":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"s":{"df":0,"docs":{},"i":{"d":{"df":4,"docs":{"158":{"tf":1.0},"166":{"tf":1.0},"3":{"tf":1.0},"528":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":14,"docs":{"1004":{"tf":1.4142135623730951},"124":{"tf":1.0},"265":{"tf":1.0},"30":{"tf":1.0},"376":{"tf":1.0},"609":{"tf":1.0},"640":{"tf":1.0},"66":{"tf":1.0},"732":{"tf":1.0},"849":{"tf":1.0},"870":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}}},"t":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"w":{"df":1,"docs":{"722":{"tf":1.0}}},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.4142135623730951},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":2.0}}}},"df":0,"docs":{}},"v":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}},"w":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":1,"docs":{"49":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"249":{"tf":1.4142135623730951},"292":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"515":{"tf":1.0},"575":{"tf":1.0},"658":{"tf":1.0},"673":{"tf":1.0},"72":{"tf":1.0},"749":{"tf":1.0},"810":{"tf":1.0},"856":{"tf":1.0},"886":{"tf":1.0}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":40,"docs":{"126":{"tf":1.0},"172":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"207":{"tf":1.0},"213":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"323":{"tf":1.0},"325":{"tf":1.0},"342":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.0},"407":{"tf":1.0},"430":{"tf":1.0},"469":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.0},"512":{"tf":1.0},"54":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.4142135623730951},"735":{"tf":1.0},"759":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.0},"81":{"tf":1.4142135623730951},"833":{"tf":1.0},"879":{"tf":1.0}}}}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":5,"docs":{"121":{"tf":1.0},"199":{"tf":1.4142135623730951},"214":{"tf":1.0},"326":{"tf":1.4142135623730951},"723":{"tf":1.0}}},"df":0,"docs":{}}}}},"f":{"df":4,"docs":{"44":{"tf":2.449489742783178},"45":{"tf":3.7416573867739413},"46":{"tf":2.23606797749979},"47":{"tf":2.449489742783178}},"t":{"df":1,"docs":{"231":{"tf":1.0}}}},"i":{"a":{"df":2,"docs":{"710":{"tf":1.0},"721":{"tf":1.0}},"s":{"df":1,"docs":{"725":{"tf":1.0}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"198":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.23606797749979}}}}},"df":5,"docs":{"198":{"tf":1.4142135623730951},"776":{"tf":2.0},"777":{"tf":2.0},"848":{"tf":1.0},"855":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":9,"docs":{"155":{"tf":1.0},"182":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.7320508075688772},"186":{"tf":1.7320508075688772},"346":{"tf":1.0},"347":{"tf":1.0},"388":{"tf":1.0},"520":{"tf":1.4142135623730951}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"163":{"tf":1.0},"342":{"tf":1.0},"388":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}}}}},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":7,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"26":{"tf":1.0},"525":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"831":{"tf":1.0}}}}},"d":{"df":4,"docs":{"207":{"tf":1.0},"322":{"tf":1.4142135623730951},"338":{"tf":1.0},"348":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"95":{"tf":1.0}}}}}}},"t":{"df":22,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951},"208":{"tf":3.0},"25":{"tf":1.4142135623730951},"332":{"tf":2.0},"333":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.0},"522":{"tf":1.7320508075688772},"537":{"tf":1.7320508075688772},"539":{"tf":2.6457513110645907},"554":{"tf":1.0},"593":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.7320508075688772},"761":{"tf":1.0},"765":{"tf":1.0},"836":{"tf":1.0},"898":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":7,"docs":{"440":{"tf":1.0},"63":{"tf":1.4142135623730951},"634":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0}}},"df":0,"docs":{}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":2,"docs":{"204":{"tf":1.4142135623730951},"208":{"tf":1.0}}},"s":{"df":0,"docs":{},"k":{"df":1,"docs":{"544":{"tf":1.0}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"523":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"(":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"[":{"0":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"_":{"1":{"2":{"8":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"(":{"&":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"df":3,"docs":{"333":{"tf":1.0},"345":{"tf":1.4142135623730951},"52":{"tf":1.0}}},"df":1,"docs":{"634":{"tf":1.7320508075688772}}},"3":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"v":{"1":{"df":1,"docs":{"526":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"520":{"tf":1.0},"525":{"tf":1.0}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}}},"df":0,"docs":{}}},"o":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"418":{"tf":1.0},"420":{"tf":1.0},"422":{"tf":1.4142135623730951},"428":{"tf":1.0},"919":{"tf":1.0}}}},"b":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"78":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"62":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":4,"docs":{"39":{"tf":1.0},"520":{"tf":1.4142135623730951},"62":{"tf":1.0},"78":{"tf":1.4142135623730951}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"62":{"tf":1.0},"78":{"tf":1.0}}}}}}}}},"s":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"78":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"k":{"'":{"df":6,"docs":{"339":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"388":{"tf":1.0},"634":{"tf":1.0}}},"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":13,"docs":{"124":{"tf":1.0},"203":{"tf":1.0},"214":{"tf":1.0},"322":{"tf":1.0},"328":{"tf":1.4142135623730951},"418":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.0},"971":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":114,"docs":{"106":{"tf":1.0},"107":{"tf":1.4142135623730951},"108":{"tf":1.0},"112":{"tf":1.0},"126":{"tf":2.0},"132":{"tf":1.0},"151":{"tf":2.23606797749979},"152":{"tf":1.7320508075688772},"154":{"tf":2.8284271247461903},"155":{"tf":3.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":3.1622776601683795},"207":{"tf":2.23606797749979},"208":{"tf":3.1622776601683795},"221":{"tf":2.0},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"238":{"tf":1.0},"279":{"tf":1.0},"281":{"tf":1.7320508075688772},"282":{"tf":1.0},"284":{"tf":2.449489742783178},"286":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.7320508075688772},"295":{"tf":1.0},"297":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"303":{"tf":1.4142135623730951},"308":{"tf":1.0},"323":{"tf":1.0},"327":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":3.0},"344":{"tf":2.23606797749979},"345":{"tf":2.8284271247461903},"346":{"tf":1.7320508075688772},"347":{"tf":1.7320508075688772},"349":{"tf":2.449489742783178},"350":{"tf":1.4142135623730951},"352":{"tf":1.0},"369":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.4142135623730951},"400":{"tf":1.4142135623730951},"401":{"tf":1.0},"402":{"tf":2.0},"404":{"tf":2.0},"406":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"44":{"tf":2.23606797749979},"444":{"tf":1.0},"45":{"tf":2.6457513110645907},"450":{"tf":1.7320508075688772},"46":{"tf":3.4641016151377544},"47":{"tf":3.4641016151377544},"49":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":2.6457513110645907},"500":{"tf":5.291502622129181},"512":{"tf":1.7320508075688772},"52":{"tf":1.0},"532":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.7320508075688772},"569":{"tf":1.4142135623730951},"57":{"tf":1.4142135623730951},"571":{"tf":1.0},"60":{"tf":2.23606797749979},"615":{"tf":1.0},"627":{"tf":1.4142135623730951},"629":{"tf":1.4142135623730951},"63":{"tf":1.0},"630":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"636":{"tf":1.0},"640":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.7320508075688772},"712":{"tf":1.7320508075688772},"714":{"tf":1.0},"715":{"tf":1.0},"72":{"tf":2.0},"721":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.4142135623730951},"73":{"tf":1.0},"740":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"83":{"tf":1.0},"85":{"tf":1.0},"874":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":2.449489742783178}},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"292":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":4,"docs":{"204":{"tf":1.0},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"83":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"/":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"50":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}}},"p":{"a":{"c":{"df":6,"docs":{"214":{"tf":1.4142135623730951},"368":{"tf":1.4142135623730951},"374":{"tf":1.0},"414":{"tf":1.0},"71":{"tf":1.0},"743":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{">":{":":{":":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"284":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"’":{"df":1,"docs":{"46":{"tf":1.0}}}}},"df":0,"docs":{}}},"o":{"b":{"df":5,"docs":{"208":{"tf":3.0},"741":{"tf":1.0},"796":{"tf":1.4142135623730951},"799":{"tf":1.4142135623730951},"878":{"tf":1.0}}},"d":{"a":{"df":1,"docs":{"871":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":5,"docs":{"253":{"tf":1.4142135623730951},"376":{"tf":1.4142135623730951},"497":{"tf":1.0},"500":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"231":{"tf":1.4142135623730951},"234":{"tf":2.6457513110645907},"235":{"tf":1.0},"240":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":1,"docs":{"267":{"tf":1.0}}}},"o":{"df":0,"docs":{},"k":{"df":2,"docs":{"0":{"tf":1.0},"133":{"tf":1.0}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"l":{"df":5,"docs":{"24":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"698":{"tf":1.0},"761":{"tf":1.7320508075688772},"97":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":8,"docs":{"247":{"tf":1.7320508075688772},"249":{"tf":2.6457513110645907},"255":{"tf":2.23606797749979},"257":{"tf":1.4142135623730951},"496":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":1,"docs":{"913":{"tf":1.0}},"h":{"df":54,"docs":{"1004":{"tf":1.0},"149":{"tf":1.0},"166":{"tf":1.4142135623730951},"172":{"tf":1.0},"186":{"tf":1.0},"199":{"tf":1.0},"201":{"tf":1.0},"218":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"329":{"tf":1.0},"340":{"tf":1.0},"37":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"384":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.7320508075688772},"40":{"tf":1.0},"402":{"tf":1.0},"440":{"tf":1.0},"442":{"tf":1.0},"47":{"tf":2.23606797749979},"499":{"tf":1.0},"5":{"tf":1.4142135623730951},"515":{"tf":1.0},"516":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"551":{"tf":1.0},"559":{"tf":1.0},"576":{"tf":1.0},"600":{"tf":1.0},"603":{"tf":1.7320508075688772},"619":{"tf":2.0},"62":{"tf":1.0},"633":{"tf":1.0},"635":{"tf":1.0},"705":{"tf":1.0},"759":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"872":{"tf":1.0},"885":{"tf":1.7320508075688772},"886":{"tf":1.0},"95":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"486":{"tf":1.0}}}}}}}},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"138":{"tf":1.0},"848":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"619":{"tf":1.0},"912":{"tf":1.0}}}}},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"288":{"tf":1.0},"374":{"tf":1.0},"732":{"tf":1.0},"843":{"tf":1.0}}}}},"df":15,"docs":{"15":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"347":{"tf":1.4142135623730951},"349":{"tf":1.0},"47":{"tf":1.0},"5":{"tf":1.0},"51":{"tf":1.4142135623730951},"564":{"tf":1.0},"670":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"831":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951}},"e":{"d":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"t":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":2,"docs":{"880":{"tf":2.0},"881":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"370":{"tf":1.0},"848":{"tf":1.0}}}}}},"x":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{":":{":":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{":":{":":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"1015":{"tf":1.0}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"346":{"tf":1.0},"439":{"tf":1.4142135623730951},"761":{"tf":1.0},"933":{"tf":1.0}}}},"d":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":1,"docs":{"843":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"705":{"tf":1.0}}}},"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"450":{"tf":1.0}}}}}},"df":28,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"173":{"tf":1.0},"178":{"tf":1.0},"280":{"tf":1.0},"282":{"tf":1.4142135623730951},"34":{"tf":1.0},"374":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"512":{"tf":1.0},"545":{"tf":1.0},"586":{"tf":1.0},"593":{"tf":1.0},"609":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0},"648":{"tf":1.0},"723":{"tf":1.0},"813":{"tf":1.0},"823":{"tf":1.0},"837":{"tf":1.0},"854":{"tf":1.0},"953":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"311":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":4,"docs":{"108":{"tf":1.4142135623730951},"112":{"tf":2.0},"121":{"tf":1.4142135623730951},"832":{"tf":1.4142135623730951}}}},"d":{"df":0,"docs":{},"g":{"df":7,"docs":{"114":{"tf":1.0},"18":{"tf":1.0},"567":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"699":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"375":{"tf":1.0}}}},"n":{"df":0,"docs":{},"g":{"df":7,"docs":{"272":{"tf":1.0},"453":{"tf":1.0},"522":{"tf":1.0},"526":{"tf":1.0},"60":{"tf":1.0},"606":{"tf":1.0},"932":{"tf":1.0}}}}},"o":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"429":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"264":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"586":{"tf":1.0}},"n":{"df":2,"docs":{"845":{"tf":1.0},"852":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"216":{"tf":1.0},"219":{"tf":1.0}}}},"df":12,"docs":{"743":{"tf":1.0},"745":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.0},"914":{"tf":1.0},"917":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":2.23606797749979},"943":{"tf":1.4142135623730951},"945":{"tf":1.0},"961":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":3,"docs":{"437":{"tf":1.0},"518":{"tf":1.0},"63":{"tf":1.0}}}}}},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"95":{"tf":1.0}}}}}}},"y":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"106":{"tf":1.0},"17":{"tf":1.0},"294":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"5":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"5":{"tf":1.0}}}}}}}}},"u":{"d":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"155":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"344":{"tf":1.0}}},"df":4,"docs":{"345":{"tf":1.4142135623730951},"732":{"tf":2.449489742783178},"735":{"tf":5.5677643628300215},"739":{"tf":1.0}}}}}},"g":{"df":11,"docs":{"108":{"tf":1.0},"152":{"tf":1.0},"161":{"tf":1.0},"19":{"tf":1.0},"500":{"tf":1.0},"53":{"tf":1.0},"573":{"tf":1.4142135623730951},"832":{"tf":1.0},"962":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.4142135623730951}}},"i":{"df":0,"docs":{},"l":{"d":{"df":23,"docs":{"147":{"tf":1.0},"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"160":{"tf":1.0},"196":{"tf":1.4142135623730951},"214":{"tf":1.0},"234":{"tf":1.4142135623730951},"293":{"tf":1.0},"296":{"tf":1.0},"414":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"501":{"tf":1.4142135623730951},"513":{"tf":1.0},"525":{"tf":2.0},"528":{"tf":1.4142135623730951},"567":{"tf":1.0},"600":{"tf":1.0},"694":{"tf":1.0},"773":{"tf":1.4142135623730951},"780":{"tf":1.0},"848":{"tf":1.7320508075688772},"850":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"r":{"c":{"/":{"b":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"#":{"df":0,"docs":{},"l":{"1":{"5":{"3":{"df":1,"docs":{"793":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"#":{"df":0,"docs":{},"l":{"1":{"2":{"2":{"df":1,"docs":{"793":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":9,"docs":{"154":{"tf":1.0},"286":{"tf":1.0},"402":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"804":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"154":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":12,"docs":{"1004":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"49":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.0},"701":{"tf":1.0},"783":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.0},"853":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":7,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":2.0},"748":{"tf":1.7320508075688772},"749":{"tf":1.0},"750":{"tf":1.0},"752":{"tf":2.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":6,"docs":{"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{")":{"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"750":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"750":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":6,"docs":{"207":{"tf":3.1622776601683795},"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{}}},"df":21,"docs":{"203":{"tf":3.0},"204":{"tf":3.4641016151377544},"205":{"tf":2.0},"206":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":2.23606797749979},"58":{"tf":1.0},"72":{"tf":1.0},"741":{"tf":1.7320508075688772},"742":{"tf":1.0},"743":{"tf":1.0},"745":{"tf":1.0},"752":{"tf":1.0},"756":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"909":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":7,"docs":{"166":{"tf":1.0},"280":{"tf":1.0},"315":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"539":{"tf":1.0},"593":{"tf":1.4142135623730951}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"571":{"tf":1.0}}}},"d":{"df":0,"docs":{},"l":{"df":1,"docs":{"336":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":5,"docs":{"282":{"tf":1.0},"826":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"853":{"tf":1.0}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"296":{"tf":1.0}}}}}}},"g":{"df":2,"docs":{"244":{"tf":1.0},"709":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":7,"docs":{"263":{"tf":1.7320508075688772},"264":{"tf":1.4142135623730951},"267":{"tf":2.8284271247461903},"576":{"tf":1.0},"602":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"i":{"df":4,"docs":{"700":{"tf":1.0},"876":{"tf":1.0},"894":{"tf":1.0},"912":{"tf":1.0}}}},"y":{"df":7,"docs":{"199":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"694":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"267":{"tf":1.0},"776":{"tf":1.4142135623730951}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":9,"docs":{"602":{"tf":1.7320508075688772},"605":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.7320508075688772},"650":{"tf":1.4142135623730951},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"x":{"!":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"v":{"4":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"540":{"tf":1.0},"860":{"tf":1.0}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}}},"df":35,"docs":{"163":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":3.1622776601683795},"171":{"tf":1.4142135623730951},"208":{"tf":2.23606797749979},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":2.0},"388":{"tf":1.0},"435":{"tf":1.4142135623730951},"485":{"tf":1.7320508075688772},"5":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"526":{"tf":2.0},"537":{"tf":1.0},"539":{"tf":2.0},"553":{"tf":1.7320508075688772},"586":{"tf":1.0},"589":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":3.0},"648":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":4.47213595499958},"75":{"tf":1.0},"761":{"tf":2.449489742783178},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"891":{"tf":1.7320508075688772},"895":{"tf":1.0},"898":{"tf":1.4142135623730951},"907":{"tf":1.0},"996":{"tf":1.4142135623730951}},"s":{"(":{"\"":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"s":{"df":1,"docs":{"349":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"349":{"tf":1.0},"350":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":3,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":1.0},"349":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{".":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"347":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"/":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"892":{"tf":1.4142135623730951},"895":{"tf":2.449489742783178},"896":{"tf":1.4142135623730951},"898":{"tf":1.7320508075688772},"900":{"tf":1.0},"902":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"z":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"231":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"c":{"[":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}}}}}},"a":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"255":{"tf":1.0},"257":{"tf":1.0}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"885":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":16,"docs":{"372":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.4142135623730951},"415":{"tf":1.7320508075688772},"417":{"tf":1.0},"46":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"776":{"tf":1.0},"814":{"tf":1.0},"885":{"tf":1.7320508075688772},"95":{"tf":1.0}},"t":{"df":1,"docs":{"415":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"(":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"885":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"25":{"tf":1.0}}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"24":{"tf":1.0},"25":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"879":{"tf":3.4641016151377544},"885":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":2,"docs":{"24":{"tf":1.0},"25":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"814":{"tf":1.0}}}},"df":0,"docs":{}},"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"281":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":74,"docs":{"108":{"tf":1.0},"112":{"tf":2.23606797749979},"170":{"tf":2.0},"171":{"tf":1.4142135623730951},"18":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"22":{"tf":1.4142135623730951},"220":{"tf":1.0},"222":{"tf":1.0},"24":{"tf":2.449489742783178},"25":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.0},"26":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0},"296":{"tf":1.7320508075688772},"300":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"407":{"tf":1.0},"438":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"482":{"tf":1.0},"5":{"tf":1.4142135623730951},"50":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":1.4142135623730951},"51":{"tf":1.0},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.7320508075688772},"61":{"tf":1.0},"614":{"tf":1.7320508075688772},"615":{"tf":1.4142135623730951},"617":{"tf":1.7320508075688772},"619":{"tf":2.0},"633":{"tf":1.0},"64":{"tf":1.0},"699":{"tf":1.4142135623730951},"732":{"tf":1.7320508075688772},"735":{"tf":2.449489742783178},"739":{"tf":1.4142135623730951},"759":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"814":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"818":{"tf":1.0},"83":{"tf":2.0},"832":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"860":{"tf":1.7320508075688772},"870":{"tf":1.0},"879":{"tf":4.795831523312719},"880":{"tf":2.0},"881":{"tf":1.7320508075688772},"885":{"tf":1.4142135623730951},"890":{"tf":1.4142135623730951},"898":{"tf":1.0},"932":{"tf":1.0},"980":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"'":{"df":2,"docs":{"205":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951}}},"<":{"'":{"_":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":9,"docs":{"194":{"tf":1.0},"205":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"602":{"tf":1.4142135623730951},"615":{"tf":1.0},"813":{"tf":1.0},"879":{"tf":3.4641016151377544},"944":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":2,"docs":{"879":{"tf":2.449489742783178},"885":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"m":{"df":0,"docs":{},"e":{"df":1,"docs":{"205":{"tf":1.0}}}},"n":{"'":{"df":0,"docs":{},"t":{"df":8,"docs":{"3":{"tf":1.4142135623730951},"347":{"tf":1.0},"358":{"tf":1.0},"439":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"660":{"tf":1.0},"735":{"tf":1.0}}}},"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"128":{"tf":1.0},"376":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":8,"docs":{"554":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.4142135623730951},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":2.8284271247461903},"885":{"tf":1.0},"912":{"tf":1.0}}}}},"d":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"633":{"tf":1.0},"635":{"tf":1.0}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.4142135623730951}},"v":{"2":{"<":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"634":{"tf":1.0}}}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":4,"docs":{"441":{"tf":1.4142135623730951},"450":{"tf":1.0},"635":{"tf":1.0},"646":{"tf":1.0}}}}}}},"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"715":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":39,"docs":{"234":{"tf":2.6457513110645907},"237":{"tf":1.0},"239":{"tf":1.0},"240":{"tf":1.4142135623730951},"322":{"tf":1.4142135623730951},"336":{"tf":1.4142135623730951},"337":{"tf":1.4142135623730951},"338":{"tf":1.0},"346":{"tf":1.4142135623730951},"370":{"tf":1.0},"439":{"tf":1.7320508075688772},"441":{"tf":1.0},"450":{"tf":3.7416573867739413},"60":{"tf":1.0},"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.7320508075688772},"63":{"tf":1.7320508075688772},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":2.23606797749979},"635":{"tf":1.4142135623730951},"636":{"tf":1.7320508075688772},"637":{"tf":1.0},"64":{"tf":1.4142135623730951},"640":{"tf":1.0},"642":{"tf":1.7320508075688772},"643":{"tf":1.0},"644":{"tf":1.7320508075688772},"646":{"tf":1.0},"648":{"tf":1.0},"65":{"tf":1.0},"67":{"tf":1.4142135623730951},"715":{"tf":2.23606797749979},"716":{"tf":1.0},"721":{"tf":2.6457513110645907},"722":{"tf":1.0},"77":{"tf":1.0},"933":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"l":{"df":6,"docs":{"122":{"tf":1.7320508075688772},"123":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":2.0},"133":{"tf":1.0},"198":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"p":{"a":{"b":{"df":0,"docs":{},"l":{"df":22,"docs":{"169":{"tf":1.0},"199":{"tf":1.0},"340":{"tf":1.0},"38":{"tf":1.0},"495":{"tf":2.0},"496":{"tf":1.7320508075688772},"497":{"tf":1.0},"500":{"tf":3.0},"501":{"tf":2.0},"502":{"tf":2.449489742783178},"503":{"tf":1.4142135623730951},"505":{"tf":1.7320508075688772},"507":{"tf":1.7320508075688772},"512":{"tf":2.0},"537":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"705":{"tf":1.0},"943":{"tf":1.0},"959":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0}}}},"c":{"df":8,"docs":{"113":{"tf":1.0},"270":{"tf":1.0},"376":{"tf":1.0},"469":{"tf":1.0},"576":{"tf":2.0},"60":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":4,"docs":{"203":{"tf":1.0},"537":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":4,"docs":{"196":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"58":{"tf":1.0}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":5,"docs":{"196":{"tf":1.0},"200":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0}}}}}},"r":{"d":{"df":3,"docs":{"849":{"tf":1.0},"852":{"tf":1.0},"894":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":9,"docs":{"141":{"tf":1.0},"239":{"tf":1.0},"249":{"tf":1.0},"593":{"tf":1.0},"602":{"tf":1.0},"642":{"tf":1.0},"653":{"tf":1.0},"763":{"tf":1.0},"945":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"114":{"tf":1.0},"121":{"tf":1.0},"358":{"tf":1.0},"429":{"tf":1.4142135623730951}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"818":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":6,"docs":{"108":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"47":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":78,"docs":{"1006":{"tf":1.0},"112":{"tf":1.4142135623730951},"126":{"tf":1.0},"151":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.0},"237":{"tf":1.0},"246":{"tf":1.4142135623730951},"249":{"tf":1.0},"254":{"tf":1.4142135623730951},"267":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":2.0},"303":{"tf":1.0},"356":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.0},"376":{"tf":1.0},"387":{"tf":1.0},"418":{"tf":1.0},"420":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.4142135623730951},"485":{"tf":1.0},"486":{"tf":1.0},"503":{"tf":1.0},"522":{"tf":1.4142135623730951},"525":{"tf":1.0},"527":{"tf":1.0},"537":{"tf":1.0},"573":{"tf":1.7320508075688772},"577":{"tf":1.0},"6":{"tf":1.4142135623730951},"600":{"tf":1.0},"615":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"62":{"tf":1.0},"629":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"696":{"tf":2.0},"701":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"749":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"8":{"tf":1.0},"809":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"832":{"tf":1.4142135623730951},"833":{"tf":1.0},"835":{"tf":1.4142135623730951},"864":{"tf":1.0},"871":{"tf":1.4142135623730951},"876":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.7320508075688772},"895":{"tf":1.0},"934":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.4142135623730951},"971":{"tf":1.0},"973":{"tf":1.0},"983":{"tf":1.0}}},"t":{"df":1,"docs":{"124":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":3,"docs":{"598":{"tf":1.0},"613":{"tf":1.0},"692":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"881":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"615":{"tf":1.0},"709":{"tf":1.0},"714":{"tf":1.0},"759":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"s":{"df":11,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"293":{"tf":1.0},"418":{"tf":1.0},"573":{"tf":1.7320508075688772},"615":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"852":{"tf":1.0},"912":{"tf":2.0},"917":{"tf":1.0}}}}},"d":{"df":1,"docs":{"126":{"tf":2.6457513110645907}},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.4142135623730951}}}}},"df":10,"docs":{"112":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"735":{"tf":1.0},"738":{"tf":1.0},"831":{"tf":1.4142135623730951},"835":{"tf":1.0},"837":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"203":{"tf":1.0},"440":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":1,"docs":{"55":{"tf":1.0}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"285":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"231":{"tf":2.0},"232":{"tf":1.0},"234":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"234":{"tf":1.0}}}}}}}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"303":{"tf":1.4142135623730951},"327":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"46":{"tf":1.0},"565":{"tf":1.0},"843":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"565":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"c":{"df":3,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"214":{"tf":1.0}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"364":{"tf":1.0}}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":19,"docs":{"152":{"tf":1.0},"204":{"tf":1.0},"249":{"tf":1.4142135623730951},"255":{"tf":1.0},"324":{"tf":1.0},"342":{"tf":1.0},"495":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"505":{"tf":1.0},"553":{"tf":1.0},"567":{"tf":1.0},"666":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"890":{"tf":1.4142135623730951},"913":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"849":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"773":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"x":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}},"f":{"df":1,"docs":{"126":{"tf":2.449489742783178}},"g":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"717":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":6,"docs":{"3":{"tf":1.0},"368":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"422":{"tf":1.0},"84":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":1,"docs":{"855":{"tf":1.0}}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"153":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"856":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":250,"docs":{"107":{"tf":1.0},"12":{"tf":1.7320508075688772},"140":{"tf":1.0},"147":{"tf":1.0},"151":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"169":{"tf":1.0},"18":{"tf":2.23606797749979},"19":{"tf":2.0},"191":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":2.0},"2":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":4.47213595499958},"204":{"tf":2.6457513110645907},"205":{"tf":2.449489742783178},"207":{"tf":2.0},"208":{"tf":1.4142135623730951},"212":{"tf":1.7320508075688772},"214":{"tf":1.0},"216":{"tf":1.7320508075688772},"217":{"tf":1.7320508075688772},"218":{"tf":2.23606797749979},"219":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"220":{"tf":1.4142135623730951},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"226":{"tf":1.0},"229":{"tf":1.0},"230":{"tf":1.7320508075688772},"231":{"tf":3.0},"232":{"tf":1.0},"234":{"tf":1.0},"235":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"24":{"tf":1.7320508075688772},"246":{"tf":1.4142135623730951},"247":{"tf":1.7320508075688772},"249":{"tf":3.1622776601683795},"251":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.4142135623730951},"255":{"tf":1.0},"26":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":2.8284271247461903},"30":{"tf":1.4142135623730951},"312":{"tf":1.4142135623730951},"313":{"tf":1.7320508075688772},"314":{"tf":1.4142135623730951},"315":{"tf":1.7320508075688772},"316":{"tf":1.0},"322":{"tf":1.7320508075688772},"329":{"tf":1.4142135623730951},"33":{"tf":1.0},"337":{"tf":1.0},"344":{"tf":1.4142135623730951},"345":{"tf":1.0},"346":{"tf":2.449489742783178},"347":{"tf":2.6457513110645907},"348":{"tf":1.4142135623730951},"349":{"tf":2.0},"35":{"tf":1.0},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"362":{"tf":2.449489742783178},"366":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":2.0},"369":{"tf":1.0},"37":{"tf":1.4142135623730951},"370":{"tf":1.4142135623730951},"371":{"tf":2.0},"372":{"tf":2.0},"373":{"tf":2.8284271247461903},"374":{"tf":2.449489742783178},"375":{"tf":3.1622776601683795},"376":{"tf":2.0},"377":{"tf":1.0},"378":{"tf":1.0},"380":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.4142135623730951},"384":{"tf":1.0},"385":{"tf":1.7320508075688772},"388":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"393":{"tf":1.0},"4":{"tf":1.0},"432":{"tf":1.4142135623730951},"433":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":2.0},"453":{"tf":2.0},"455":{"tf":1.0},"459":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":2.449489742783178},"48":{"tf":1.0},"49":{"tf":1.7320508075688772},"495":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"5":{"tf":1.0},"50":{"tf":1.0},"500":{"tf":3.0},"503":{"tf":1.7320508075688772},"512":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":3.0},"521":{"tf":2.449489742783178},"528":{"tf":1.7320508075688772},"530":{"tf":1.0},"531":{"tf":1.0},"534":{"tf":1.4142135623730951},"553":{"tf":1.0},"56":{"tf":1.7320508075688772},"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":2.0},"573":{"tf":1.7320508075688772},"58":{"tf":1.0},"586":{"tf":2.0},"588":{"tf":1.0},"59":{"tf":1.4142135623730951},"598":{"tf":1.0},"599":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"60":{"tf":2.23606797749979},"600":{"tf":2.23606797749979},"602":{"tf":3.7416573867739413},"603":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"614":{"tf":1.0},"615":{"tf":1.0},"627":{"tf":1.4142135623730951},"629":{"tf":1.7320508075688772},"63":{"tf":1.7320508075688772},"632":{"tf":1.0},"633":{"tf":2.23606797749979},"634":{"tf":1.4142135623730951},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"643":{"tf":1.0},"65":{"tf":1.4142135623730951},"66":{"tf":1.0},"68":{"tf":1.0},"693":{"tf":1.0},"694":{"tf":2.0},"695":{"tf":1.0},"696":{"tf":3.605551275463989},"697":{"tf":3.0},"698":{"tf":1.4142135623730951},"699":{"tf":1.4142135623730951},"700":{"tf":2.23606797749979},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":2.0},"710":{"tf":1.4142135623730951},"712":{"tf":1.0},"714":{"tf":1.7320508075688772},"715":{"tf":2.0},"716":{"tf":1.4142135623730951},"717":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":2.0},"74":{"tf":1.0},"743":{"tf":1.0},"75":{"tf":2.23606797749979},"752":{"tf":1.0},"759":{"tf":1.7320508075688772},"763":{"tf":1.0},"77":{"tf":1.7320508075688772},"776":{"tf":1.0},"78":{"tf":1.4142135623730951},"784":{"tf":1.0},"79":{"tf":1.0},"797":{"tf":1.0},"8":{"tf":1.0},"80":{"tf":2.0},"803":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":2.449489742783178},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"82":{"tf":1.0},"826":{"tf":1.0},"83":{"tf":2.23606797749979},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"84":{"tf":3.1622776601683795},"849":{"tf":1.0},"85":{"tf":3.1622776601683795},"852":{"tf":1.0},"855":{"tf":1.7320508075688772},"871":{"tf":1.0},"874":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":2.6457513110645907},"897":{"tf":1.0},"898":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":2.23606797749979},"917":{"tf":1.4142135623730951},"919":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0},"938":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.7320508075688772},"958":{"tf":1.0},"959":{"tf":2.0},"960":{"tf":1.7320508075688772},"961":{"tf":1.4142135623730951},"962":{"tf":1.4142135623730951},"970":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.4142135623730951}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":16,"docs":{"138":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"323":{"tf":1.0},"388":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"742":{"tf":1.0},"777":{"tf":1.0},"849":{"tf":1.0},"855":{"tf":1.0},"913":{"tf":1.0},"990":{"tf":1.0}}}}}}},"n":{"c":{"df":4,"docs":{"124":{"tf":1.0},"204":{"tf":1.0},"347":{"tf":1.0},"833":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":213,"docs":{"0":{"tf":1.0},"100":{"tf":1.0},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"125":{"tf":1.7320508075688772},"126":{"tf":1.0},"127":{"tf":1.7320508075688772},"130":{"tf":1.0},"131":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.4142135623730951},"139":{"tf":1.0},"142":{"tf":1.7320508075688772},"146":{"tf":1.0},"148":{"tf":2.0},"149":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":1.4142135623730951},"165":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":1.0},"172":{"tf":1.4142135623730951},"175":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.0},"183":{"tf":1.0},"186":{"tf":1.7320508075688772},"187":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.7320508075688772},"193":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"206":{"tf":1.0},"208":{"tf":1.0},"209":{"tf":1.0},"213":{"tf":1.4142135623730951},"218":{"tf":1.4142135623730951},"252":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"280":{"tf":1.0},"282":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"292":{"tf":1.0},"294":{"tf":1.0},"295":{"tf":1.0},"30":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"314":{"tf":1.0},"317":{"tf":1.4142135623730951},"318":{"tf":1.0},"322":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.0},"371":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"382":{"tf":1.0},"390":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.4142135623730951},"398":{"tf":1.0},"399":{"tf":1.0},"41":{"tf":1.0},"411":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.7320508075688772},"423":{"tf":1.0},"424":{"tf":1.0},"427":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.0},"455":{"tf":1.4142135623730951},"456":{"tf":1.0},"457":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.4142135623730951},"469":{"tf":1.0},"473":{"tf":1.0},"483":{"tf":1.0},"491":{"tf":1.0},"494":{"tf":1.0},"500":{"tf":1.4142135623730951},"501":{"tf":1.0},"505":{"tf":1.0},"511":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":1.7320508075688772},"539":{"tf":1.7320508075688772},"540":{"tf":1.4142135623730951},"542":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.0},"551":{"tf":1.4142135623730951},"559":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"585":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.4142135623730951},"591":{"tf":1.0},"593":{"tf":1.0},"600":{"tf":1.4142135623730951},"606":{"tf":1.0},"619":{"tf":1.0},"621":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"648":{"tf":1.0},"65":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"67":{"tf":1.0},"673":{"tf":1.0},"680":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"698":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"717":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"739":{"tf":1.4142135623730951},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.7320508075688772},"752":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"78":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.4142135623730951},"788":{"tf":1.0},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"8":{"tf":1.0},"800":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.7320508075688772},"813":{"tf":1.4142135623730951},"817":{"tf":1.0},"831":{"tf":2.0},"835":{"tf":1.0},"837":{"tf":1.7320508075688772},"844":{"tf":1.0},"846":{"tf":1.4142135623730951},"848":{"tf":1.7320508075688772},"849":{"tf":1.7320508075688772},"854":{"tf":1.0},"860":{"tf":1.0},"867":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":2.0},"875":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":2.23606797749979},"929":{"tf":1.7320508075688772},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"944":{"tf":1.0},"980":{"tf":1.0},"994":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"234":{"tf":1.0}}}},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"607":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"1006":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":4,"docs":{"219":{"tf":1.0},"221":{"tf":1.0},"843":{"tf":1.4142135623730951},"87":{"tf":1.0}}}}}},"o":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"d":{"a":{"df":0,"docs":{},"o":{"df":2,"docs":{"182":{"tf":1.0},"795":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"895":{"tf":1.0},"897":{"tf":1.4142135623730951},"898":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"522":{"tf":1.0}},"g":{"df":6,"docs":{"416":{"tf":1.0},"614":{"tf":1.0},"653":{"tf":1.4142135623730951},"75":{"tf":1.7320508075688772},"912":{"tf":1.4142135623730951},"979":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"208":{"tf":1.7320508075688772},"796":{"tf":1.7320508075688772},"799":{"tf":1.7320508075688772}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"272":{"tf":1.0},"273":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"206":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"58":{"tf":1.0},"75":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"435":{"tf":1.0}}}}},"t":{"df":2,"docs":{"723":{"tf":1.0},"725":{"tf":1.0}}}},"c":{"df":0,"docs":{},"k":{"df":45,"docs":{"154":{"tf":1.0},"156":{"tf":1.0},"177":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":1.0},"286":{"tf":1.0},"3":{"tf":1.0},"342":{"tf":1.0},"347":{"tf":1.4142135623730951},"436":{"tf":1.0},"439":{"tf":1.4142135623730951},"45":{"tf":1.0},"530":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.7320508075688772},"640":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.0},"711":{"tf":1.7320508075688772},"714":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":2.8284271247461903},"721":{"tf":2.0},"722":{"tf":2.449489742783178},"725":{"tf":1.0},"729":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.0},"77":{"tf":1.0},"811":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"817":{"tf":2.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.0},"900":{"tf":1.0},"982":{"tf":1.0}},"e":{"d":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"817":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":9,"docs":{"449":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.4142135623730951},"714":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.7320508075688772},"721":{"tf":2.0},"722":{"tf":2.8284271247461903},"723":{"tf":1.4142135623730951}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"586":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"249":{"tf":1.0},"567":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"n":{"df":3,"docs":{"106":{"tf":1.0},"17":{"tf":1.0},"294":{"tf":1.0}},"g":{"df":1,"docs":{"988":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"735":{"tf":2.449489742783178}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"761":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}}}}}},"df":2,"docs":{"697":{"tf":1.0},"761":{"tf":2.449489742783178}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"761":{"tf":2.449489742783178}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"761":{"tf":1.4142135623730951}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"761":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"i":{"c":{"df":11,"docs":{"126":{"tf":2.23606797749979},"170":{"tf":1.0},"221":{"tf":1.0},"356":{"tf":1.0},"428":{"tf":1.0},"473":{"tf":1.0},"500":{"tf":1.0},"569":{"tf":1.0},"640":{"tf":1.0},"700":{"tf":1.0},"723":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"s":{"df":11,"docs":{"38":{"tf":1.0},"471":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"700":{"tf":1.0},"718":{"tf":1.0},"77":{"tf":1.0},"831":{"tf":1.4142135623730951},"912":{"tf":1.0}}}},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"935":{"tf":1.0}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"e":{"df":1,"docs":{"570":{"tf":1.0}},"n":{"df":9,"docs":{"126":{"tf":1.0},"252":{"tf":1.0},"346":{"tf":1.0},"373":{"tf":1.0},"497":{"tf":1.4142135623730951},"631":{"tf":1.0},"633":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"'":{"df":1,"docs":{"439":{"tf":2.0}}},"(":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.0}}}}}}}}}}}}}},"df":0,"docs":{}},"df":29,"docs":{"155":{"tf":1.0},"430":{"tf":2.23606797749979},"431":{"tf":1.4142135623730951},"432":{"tf":1.7320508075688772},"435":{"tf":1.7320508075688772},"436":{"tf":2.23606797749979},"437":{"tf":2.6457513110645907},"438":{"tf":2.0},"439":{"tf":4.47213595499958},"440":{"tf":2.0},"449":{"tf":1.0},"514":{"tf":1.7320508075688772},"517":{"tf":2.23606797749979},"519":{"tf":1.4142135623730951},"522":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"576":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":2.0},"716":{"tf":1.0},"717":{"tf":1.7320508075688772},"720":{"tf":1.7320508075688772},"722":{"tf":3.0},"723":{"tf":2.449489742783178},"73":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"439":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.0}}}}}}}}}}}}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":4,"docs":{"432":{"tf":1.4142135623730951},"438":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"440":{"tf":1.0}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.7320508075688772}}}}}}}}}}}}},"i":{"df":2,"docs":{"314":{"tf":1.0},"639":{"tf":1.0}},"r":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"v":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{".":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"350":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":4,"docs":{"349":{"tf":1.7320508075688772},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"352":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":16,"docs":{"240":{"tf":1.0},"322":{"tf":1.7320508075688772},"323":{"tf":1.0},"339":{"tf":1.0},"343":{"tf":1.4142135623730951},"348":{"tf":1.4142135623730951},"349":{"tf":2.8284271247461903},"350":{"tf":1.0},"633":{"tf":2.0},"637":{"tf":1.7320508075688772},"666":{"tf":1.0},"668":{"tf":1.0},"717":{"tf":1.0},"815":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.0}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":2,"docs":{"633":{"tf":2.0},"640":{"tf":1.0}}}}}}}}}}}}}}},"m":{"df":0,"docs":{},"p":{"df":2,"docs":{"829":{"tf":1.0},"833":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"324":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"199":{"tf":1.0},"330":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"5":{"tf":1.0}}}},"w":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"409":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"y":{"df":1,"docs":{"841":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"df":4,"docs":{"705":{"tf":1.0},"768":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":2,"docs":{"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951}}}}}}}}},"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}},"r":{"df":25,"docs":{"180":{"tf":1.0},"210":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"30":{"tf":1.0},"356":{"tf":1.0},"48":{"tf":1.0},"600":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"698":{"tf":1.4142135623730951},"701":{"tf":1.4142135623730951},"705":{"tf":1.4142135623730951},"706":{"tf":1.0},"723":{"tf":1.0},"737":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"797":{"tf":1.0},"817":{"tf":1.0},"833":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"952":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"1008":{"tf":1.0},"16":{"tf":1.0},"267":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.7320508075688772},"693":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":34,"docs":{"19":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"262":{"tf":1.0},"358":{"tf":1.0},"381":{"tf":1.0},"403":{"tf":1.0},"440":{"tf":1.0},"498":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":1.4142135623730951},"758":{"tf":1.0},"759":{"tf":2.449489742783178},"763":{"tf":1.0},"765":{"tf":1.0},"81":{"tf":1.4142135623730951},"827":{"tf":1.7320508075688772},"828":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.4142135623730951},"830":{"tf":1.0},"831":{"tf":1.7320508075688772},"833":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.4142135623730951},"837":{"tf":1.7320508075688772},"84":{"tf":1.7320508075688772},"88":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"831":{"tf":1.4142135623730951}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":2,"docs":{"24":{"tf":1.0},"439":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":8,"docs":{"175":{"tf":1.0},"469":{"tf":1.0},"501":{"tf":1.0},"576":{"tf":1.0},"661":{"tf":1.0},"744":{"tf":1.0},"751":{"tf":1.4142135623730951},"773":{"tf":1.4142135623730951}},"r":{"df":2,"docs":{"207":{"tf":1.4142135623730951},"912":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"255":{"tf":1.7320508075688772},"505":{"tf":1.7320508075688772}}}}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"571":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"288":{"tf":1.0}}}}}}}},"o":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":2,"docs":{"24":{"tf":1.7320508075688772},"333":{"tf":1.7320508075688772}}},"df":68,"docs":{"111":{"tf":1.0},"121":{"tf":1.4142135623730951},"150":{"tf":1.7320508075688772},"151":{"tf":3.4641016151377544},"152":{"tf":1.0},"154":{"tf":3.4641016151377544},"155":{"tf":2.8284271247461903},"156":{"tf":1.0},"158":{"tf":1.4142135623730951},"163":{"tf":1.7320508075688772},"186":{"tf":1.0},"19":{"tf":1.0},"190":{"tf":1.0},"22":{"tf":1.0},"274":{"tf":1.0},"316":{"tf":1.0},"322":{"tf":1.4142135623730951},"333":{"tf":1.7320508075688772},"347":{"tf":1.0},"35":{"tf":1.4142135623730951},"362":{"tf":2.0},"430":{"tf":1.0},"435":{"tf":2.23606797749979},"436":{"tf":1.0},"437":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"483":{"tf":1.7320508075688772},"537":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":1.4142135623730951},"593":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":2.449489742783178},"632":{"tf":1.0},"634":{"tf":1.0},"64":{"tf":1.4142135623730951},"65":{"tf":1.4142135623730951},"67":{"tf":2.0},"71":{"tf":1.4142135623730951},"711":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"737":{"tf":1.0},"74":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"75":{"tf":1.4142135623730951},"750":{"tf":1.0},"762":{"tf":1.0},"77":{"tf":1.7320508075688772},"794":{"tf":1.0},"810":{"tf":1.7320508075688772},"811":{"tf":2.0},"813":{"tf":1.4142135623730951},"814":{"tf":2.449489742783178},"815":{"tf":2.449489742783178},"816":{"tf":1.0},"817":{"tf":2.23606797749979},"818":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"951":{"tf":1.0},"994":{"tf":1.0}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"444":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"371":{"tf":1.4142135623730951},"537":{"tf":1.0},"810":{"tf":1.0},"872":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"418":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"39":{"tf":1.0},"54":{"tf":1.0}}},"s":{"df":1,"docs":{"24":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"d":{"df":2,"docs":{"516":{"tf":1.0},"517":{"tf":1.0}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":35,"docs":{"203":{"tf":1.4142135623730951},"206":{"tf":1.4142135623730951},"229":{"tf":1.7320508075688772},"230":{"tf":1.4142135623730951},"231":{"tf":3.872983346207417},"232":{"tf":2.0},"234":{"tf":3.0},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.0},"240":{"tf":1.0},"243":{"tf":1.7320508075688772},"244":{"tf":1.0},"246":{"tf":1.0},"249":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.4142135623730951},"62":{"tf":2.449489742783178},"629":{"tf":1.4142135623730951},"632":{"tf":2.449489742783178},"633":{"tf":1.0},"634":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.7320508075688772},"644":{"tf":1.4142135623730951},"65":{"tf":1.4142135623730951},"66":{"tf":1.0},"67":{"tf":1.4142135623730951},"69":{"tf":1.0},"73":{"tf":1.4142135623730951},"78":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"634":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"634":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":49,"docs":{"106":{"tf":2.23606797749979},"107":{"tf":1.7320508075688772},"108":{"tf":1.0},"111":{"tf":2.8284271247461903},"112":{"tf":2.23606797749979},"113":{"tf":2.23606797749979},"120":{"tf":1.0},"121":{"tf":2.0},"125":{"tf":1.0},"2":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"267":{"tf":1.4142135623730951},"268":{"tf":2.0},"269":{"tf":2.449489742783178},"270":{"tf":2.449489742783178},"272":{"tf":2.0},"273":{"tf":2.6457513110645907},"274":{"tf":1.0},"276":{"tf":2.449489742783178},"3":{"tf":1.7320508075688772},"303":{"tf":1.4142135623730951},"338":{"tf":1.0},"346":{"tf":1.4142135623730951},"373":{"tf":1.7320508075688772},"375":{"tf":1.0},"376":{"tf":1.4142135623730951},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.4142135623730951},"418":{"tf":1.4142135623730951},"420":{"tf":1.0},"425":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"5":{"tf":1.0},"523":{"tf":1.7320508075688772},"6":{"tf":2.8284271247461903},"7":{"tf":2.0},"709":{"tf":1.0},"715":{"tf":1.4142135623730951},"8":{"tf":1.0},"801":{"tf":1.0},"876":{"tf":1.0},"9":{"tf":1.0},"913":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"272":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{}},"u":{"d":{"df":2,"docs":{"232":{"tf":1.0},"567":{"tf":1.0}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":2,"docs":{"435":{"tf":1.0},"633":{"tf":1.0}}}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":14,"docs":{"1004":{"tf":1.0},"111":{"tf":1.0},"296":{"tf":1.0},"429":{"tf":1.0},"51":{"tf":1.0},"525":{"tf":1.4142135623730951},"565":{"tf":1.0},"571":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"605":{"tf":1.0},"700":{"tf":1.0},"95":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":25,"docs":{"171":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"340":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.0},"645":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.4142135623730951},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0}}},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"602":{"tf":1.0},"694":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"440":{"tf":1.0},"776":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"470":{"tf":1.0}}}}},"t":{"df":4,"docs":{"0":{"tf":1.0},"264":{"tf":1.0},"437":{"tf":1.0},"447":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"1004":{"tf":1.0}}}},"t":{"df":11,"docs":{"203":{"tf":1.0},"272":{"tf":1.4142135623730951},"351":{"tf":1.0},"46":{"tf":1.4142135623730951},"467":{"tf":1.0},"49":{"tf":1.0},"627":{"tf":1.4142135623730951},"628":{"tf":1.4142135623730951},"633":{"tf":1.7320508075688772},"635":{"tf":1.0},"641":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"633":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"635":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"710":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"22":{"tf":1.0},"368":{"tf":1.4142135623730951},"51":{"tf":1.0},"696":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"874":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"55":{"tf":1.0}}}},"t":{"df":1,"docs":{"133":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"n":{"df":27,"docs":{"1":{"tf":1.0},"12":{"tf":1.0},"184":{"tf":1.0},"194":{"tf":1.0},"199":{"tf":1.0},"2":{"tf":1.0},"208":{"tf":1.0},"216":{"tf":1.4142135623730951},"218":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"3":{"tf":1.7320508075688772},"412":{"tf":1.0},"414":{"tf":1.0},"416":{"tf":1.0},"5":{"tf":2.0},"521":{"tf":1.0},"71":{"tf":1.0},"843":{"tf":1.7320508075688772},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"87":{"tf":1.0},"912":{"tf":1.4142135623730951},"943":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"'":{"df":2,"docs":{"267":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"1":{"df":3,"docs":{"482":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.4142135623730951}}},"df":0,"docs":{}},":":{":":{"<":{"df":0,"docs":{},"u":{"3":{"2":{">":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"(":{"*":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{")":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"786":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"<":{"df":0,"docs":{},"u":{"3":{"2":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":6,"docs":{"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"485":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":2.0},"523":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":1,"docs":{"992":{"tf":1.4142135623730951}}}}}}},"u":{"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"876":{"tf":1.0}}}},"r":{"df":13,"docs":{"147":{"tf":1.0},"204":{"tf":1.0},"314":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"779":{"tf":1.0},"813":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"759":{"tf":1.0}}}}}}},"t":{"df":193,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.0},"1002":{"tf":1.4142135623730951},"1009":{"tf":1.0},"101":{"tf":1.0},"1012":{"tf":1.4142135623730951},"104":{"tf":1.0},"106":{"tf":1.4142135623730951},"116":{"tf":1.0},"119":{"tf":1.4142135623730951},"122":{"tf":1.4142135623730951},"126":{"tf":1.0},"129":{"tf":1.0},"13":{"tf":1.4142135623730951},"132":{"tf":1.4142135623730951},"136":{"tf":1.4142135623730951},"143":{"tf":1.0},"146":{"tf":1.4142135623730951},"150":{"tf":1.4142135623730951},"157":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":1.4142135623730951},"17":{"tf":1.4142135623730951},"171":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.0},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.0},"191":{"tf":1.0},"195":{"tf":1.0},"210":{"tf":1.0},"215":{"tf":1.0},"224":{"tf":1.0},"229":{"tf":1.4142135623730951},"238":{"tf":1.0},"241":{"tf":1.4142135623730951},"247":{"tf":1.4142135623730951},"251":{"tf":1.7320508075688772},"256":{"tf":1.0},"259":{"tf":1.0},"26":{"tf":1.0},"268":{"tf":1.0},"276":{"tf":1.4142135623730951},"279":{"tf":1.4142135623730951},"287":{"tf":1.0},"290":{"tf":1.0},"294":{"tf":1.0},"307":{"tf":1.4142135623730951},"31":{"tf":1.0},"311":{"tf":1.0},"318":{"tf":1.0},"322":{"tf":1.4142135623730951},"34":{"tf":1.4142135623730951},"355":{"tf":1.0},"358":{"tf":1.0},"366":{"tf":1.4142135623730951},"379":{"tf":1.0},"38":{"tf":1.0},"382":{"tf":1.0},"386":{"tf":1.4142135623730951},"393":{"tf":1.4142135623730951},"396":{"tf":1.4142135623730951},"400":{"tf":1.4142135623730951},"405":{"tf":1.0},"408":{"tf":1.0},"410":{"tf":1.4142135623730951},"421":{"tf":1.0},"424":{"tf":1.4142135623730951},"430":{"tf":1.4142135623730951},"443":{"tf":1.0},"446":{"tf":1.0},"451":{"tf":1.4142135623730951},"458":{"tf":1.0},"461":{"tf":1.0},"465":{"tf":1.4142135623730951},"475":{"tf":1.0},"478":{"tf":1.0},"481":{"tf":1.4142135623730951},"482":{"tf":1.0},"486":{"tf":1.0},"488":{"tf":1.0},"491":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"506":{"tf":1.0},"509":{"tf":1.0},"512":{"tf":1.0},"513":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"52":{"tf":1.0},"529":{"tf":1.0},"531":{"tf":1.0},"535":{"tf":1.4142135623730951},"542":{"tf":1.0},"545":{"tf":1.0},"549":{"tf":1.4142135623730951},"553":{"tf":1.0},"556":{"tf":1.0},"559":{"tf":1.4142135623730951},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"579":{"tf":1.0},"582":{"tf":1.4142135623730951},"584":{"tf":1.4142135623730951},"586":{"tf":1.0},"591":{"tf":1.4142135623730951},"593":{"tf":1.0},"594":{"tf":1.4142135623730951},"598":{"tf":1.4142135623730951},"606":{"tf":1.0},"609":{"tf":1.7320508075688772},"613":{"tf":1.4142135623730951},"620":{"tf":1.0},"623":{"tf":1.4142135623730951},"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.0},"639":{"tf":1.0},"642":{"tf":1.4142135623730951},"649":{"tf":1.4142135623730951},"657":{"tf":1.0},"660":{"tf":1.0},"664":{"tf":1.4142135623730951},"671":{"tf":1.0},"674":{"tf":1.0},"678":{"tf":1.4142135623730951},"685":{"tf":1.0},"688":{"tf":1.0},"692":{"tf":1.4142135623730951},"70":{"tf":1.0},"701":{"tf":1.0},"702":{"tf":1.0},"705":{"tf":2.0},"709":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"757":{"tf":1.4142135623730951},"764":{"tf":1.0},"767":{"tf":1.0},"782":{"tf":1.4142135623730951},"789":{"tf":1.0},"79":{"tf":1.4142135623730951},"792":{"tf":1.4142135623730951},"795":{"tf":1.4142135623730951},"802":{"tf":1.0},"804":{"tf":1.0},"808":{"tf":1.4142135623730951},"811":{"tf":1.0},"820":{"tf":1.0},"823":{"tf":1.4142135623730951},"827":{"tf":1.4142135623730951},"831":{"tf":1.0},"834":{"tf":1.0},"837":{"tf":1.0},"841":{"tf":1.4142135623730951},"851":{"tf":1.0},"854":{"tf":1.4142135623730951},"857":{"tf":1.4142135623730951},"86":{"tf":1.0},"865":{"tf":1.0},"868":{"tf":1.4142135623730951},"871":{"tf":1.4142135623730951},"884":{"tf":1.0},"887":{"tf":1.4142135623730951},"89":{"tf":1.0},"891":{"tf":1.4142135623730951},"901":{"tf":1.0},"904":{"tf":1.0},"908":{"tf":1.4142135623730951},"918":{"tf":1.0},"921":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951},"940":{"tf":1.4142135623730951},"950":{"tf":1.0},"953":{"tf":1.4142135623730951},"957":{"tf":1.4142135623730951},"959":{"tf":1.0},"961":{"tf":1.0},"967":{"tf":1.0},"970":{"tf":1.7320508075688772},"971":{"tf":1.0},"974":{"tf":1.4142135623730951},"981":{"tf":1.0},"984":{"tf":1.0},"988":{"tf":1.4142135623730951},"995":{"tf":1.0},"998":{"tf":1.4142135623730951}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"545":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":3,"docs":{"121":{"tf":1.0},"212":{"tf":1.0},"849":{"tf":1.0}}}},"t":{"df":3,"docs":{"231":{"tf":1.4142135623730951},"240":{"tf":1.0},"801":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"38":{"tf":1.0},"40":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"912":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}}}},"i":{"df":0,"docs":{},"l":{"df":7,"docs":{"35":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"530":{"tf":1.0},"735":{"tf":2.0},"831":{"tf":1.7320508075688772}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"205":{"tf":1.0}}}}},"df":3,"docs":{"3":{"tf":1.0},"368":{"tf":1.0},"573":{"tf":1.0}}}}}},"t":{"df":16,"docs":{"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"402":{"tf":1.0},"437":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"515":{"tf":1.0},"525":{"tf":1.0},"615":{"tf":1.0},"817":{"tf":1.0},"833":{"tf":1.0},"835":{"tf":1.0},"848":{"tf":1.0},"889":{"tf":1.0}}},"x":{"df":28,"docs":{"140":{"tf":1.0},"141":{"tf":1.0},"145":{"tf":1.0},"375":{"tf":1.4142135623730951},"418":{"tf":1.0},"429":{"tf":1.4142135623730951},"438":{"tf":1.0},"576":{"tf":1.4142135623730951},"600":{"tf":1.0},"631":{"tf":1.0},"68":{"tf":1.0},"706":{"tf":1.0},"773":{"tf":1.4142135623730951},"777":{"tf":1.0},"799":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"874":{"tf":1.4142135623730951},"920":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"938":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"962":{"tf":1.4142135623730951},"972":{"tf":1.0}}}},"i":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"337":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":2,"docs":{"852":{"tf":1.4142135623730951},"894":{"tf":1.0}}}}},"c":{"df":11,"docs":{"375":{"tf":1.7320508075688772},"441":{"tf":1.0},"486":{"tf":1.0},"503":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"975":{"tf":1.0}}},"df":2,"docs":{"251":{"tf":1.0},"712":{"tf":1.0}}}},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"208":{"tf":1.0},"21":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"373":{"tf":1.4142135623730951},"576":{"tf":1.0},"933":{"tf":1.7320508075688772},"94":{"tf":1.0},"961":{"tf":1.0}}},"s":{"df":5,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"522":{"tf":1.7320508075688772},"602":{"tf":1.4142135623730951},"696":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"221":{"tf":1.0},"522":{"tf":2.23606797749979},"602":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"709":{"tf":1.0},"717":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"797":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":8,"docs":{"142":{"tf":1.0},"30":{"tf":1.0},"324":{"tf":1.0},"499":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0},"969":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"s":{"df":5,"docs":{"988":{"tf":1.7320508075688772},"989":{"tf":1.0},"992":{"tf":1.7320508075688772},"994":{"tf":1.0},"996":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"126":{"tf":1.0},"502":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":9,"docs":{"124":{"tf":1.0},"516":{"tf":1.4142135623730951},"564":{"tf":1.0},"697":{"tf":1.4142135623730951},"84":{"tf":1.4142135623730951},"85":{"tf":1.7320508075688772},"850":{"tf":1.0},"879":{"tf":1.4142135623730951},"934":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"725":{"tf":1.0}}}}}}},"df":32,"docs":{"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"26":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"33":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"35":{"tf":1.0},"368":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"633":{"tf":1.4142135623730951},"710":{"tf":1.0},"715":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.7320508075688772},"724":{"tf":1.0},"725":{"tf":1.0},"94":{"tf":1.0},"951":{"tf":1.0},"968":{"tf":1.0}}}}}},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"\"":{":":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{":":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"&":{"[":{"4":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":5,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":2.0},"350":{"tf":1.0},"485":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":4,"docs":{"205":{"tf":1.0},"333":{"tf":1.0},"435":{"tf":1.7320508075688772},"735":{"tf":1.0}}}}},"v":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":2,"docs":{"712":{"tf":1.0},"721":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"t":{"df":11,"docs":{"402":{"tf":1.0},"427":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.0},"653":{"tf":1.0},"827":{"tf":1.7320508075688772},"829":{"tf":1.4142135623730951},"83":{"tf":1.0},"843":{"tf":1.0},"847":{"tf":1.0},"931":{"tf":1.0}},"u":{"df":2,"docs":{"33":{"tf":1.0},"84":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"n":{"df":35,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"170":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"251":{"tf":1.0},"267":{"tf":1.0},"304":{"tf":1.0},"365":{"tf":1.0},"410":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.4142135623730951},"420":{"tf":1.4142135623730951},"427":{"tf":1.4142135623730951},"48":{"tf":1.0},"500":{"tf":1.0},"53":{"tf":1.0},"58":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"656":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.0},"8":{"tf":1.0},"819":{"tf":1.0},"850":{"tf":1.0},"917":{"tf":1.0},"936":{"tf":1.0},"949":{"tf":1.0},"966":{"tf":1.0}}},"t":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"340":{"tf":1.0}}}},"l":{"df":0,"docs":{},"u":{"d":{"df":1,"docs":{"721":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":8,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"207":{"tf":1.4142135623730951},"33":{"tf":1.0},"39":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"875":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":1,"docs":{"142":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":16,"docs":{"295":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.7320508075688772},"302":{"tf":1.0},"341":{"tf":1.4142135623730951},"376":{"tf":1.0},"412":{"tf":1.0},"427":{"tf":1.0},"467":{"tf":1.0},"500":{"tf":1.0},"568":{"tf":1.0},"62":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"754":{"tf":1.0},"95":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"526":{"tf":1.0}}}}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"142":{"tf":1.0},"211":{"tf":1.4142135623730951},"406":{"tf":1.0},"442":{"tf":1.0},"776":{"tf":1.0},"819":{"tf":1.0},"961":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"376":{"tf":1.0},"743":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"348":{"tf":1.0}}}}}}},"df":0,"docs":{},"g":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},">":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"24":{"tf":2.23606797749979},"814":{"tf":1.4142135623730951},"817":{"tf":1.0},"83":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":2.0}},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":48,"docs":{"108":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"140":{"tf":1.4142135623730951},"141":{"tf":1.4142135623730951},"145":{"tf":1.0},"146":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"208":{"tf":1.0},"222":{"tf":1.0},"26":{"tf":1.0},"270":{"tf":1.4142135623730951},"342":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.4142135623730951},"362":{"tf":1.0},"373":{"tf":1.0},"381":{"tf":1.0},"415":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"63":{"tf":1.4142135623730951},"664":{"tf":1.0},"697":{"tf":1.4142135623730951},"698":{"tf":1.0},"700":{"tf":1.4142135623730951},"705":{"tf":1.0},"741":{"tf":1.0},"752":{"tf":1.0},"811":{"tf":1.0},"818":{"tf":1.4142135623730951},"819":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":2.23606797749979},"848":{"tf":1.0},"850":{"tf":1.4142135623730951},"913":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"186":{"tf":1.7320508075688772},"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":18,"docs":{"122":{"tf":1.7320508075688772},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":2.8284271247461903},"127":{"tf":1.0},"182":{"tf":1.4142135623730951},"183":{"tf":1.0},"184":{"tf":2.23606797749979},"186":{"tf":1.0},"187":{"tf":1.4142135623730951},"188":{"tf":1.4142135623730951},"190":{"tf":1.0},"193":{"tf":1.0},"300":{"tf":1.0},"302":{"tf":1.0},"45":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"35":{"tf":1.0},"735":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":3,"docs":{"182":{"tf":1.0},"253":{"tf":1.0},"54":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"s":{"df":3,"docs":{"249":{"tf":1.0},"564":{"tf":1.0},"976":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"748":{"tf":1.0}}}}}}}},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"6":{"tf":1.0},"755":{"tf":1.0}}}},"df":0,"docs":{}}}},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":13,"docs":{"198":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"262":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.4142135623730951},"52":{"tf":1.0},"551":{"tf":1.0},"567":{"tf":1.0},"784":{"tf":1.0},"990":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":20,"docs":{"144":{"tf":1.0},"155":{"tf":1.0},"17":{"tf":1.7320508075688772},"18":{"tf":1.0},"19":{"tf":1.0},"3":{"tf":1.7320508075688772},"322":{"tf":1.7320508075688772},"323":{"tf":1.0},"327":{"tf":1.0},"356":{"tf":1.0},"388":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"5":{"tf":2.23606797749979},"567":{"tf":1.4142135623730951},"6":{"tf":1.0},"602":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"833":{"tf":1.0},"927":{"tf":1.0}}}},"t":{"df":1,"docs":{"303":{"tf":1.0}}}},"q":{"df":0,"docs":{},"u":{"df":9,"docs":{"108":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"429":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"928":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"v":{"df":2,"docs":{"239":{"tf":1.0},"752":{"tf":1.4142135623730951}}}}},"i":{"d":{"df":37,"docs":{"1003":{"tf":1.0},"126":{"tf":1.0},"193":{"tf":1.0},"267":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"325":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"412":{"tf":1.0},"426":{"tf":1.0},"435":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.4142135623730951},"450":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"500":{"tf":1.0},"564":{"tf":1.0},"6":{"tf":1.0},"630":{"tf":1.0},"635":{"tf":1.0},"7":{"tf":1.0},"724":{"tf":1.0},"736":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.4142135623730951},"778":{"tf":1.0},"809":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0},"889":{"tf":1.0},"928":{"tf":1.0},"962":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":18,"docs":{"210":{"tf":1.0},"224":{"tf":1.0},"346":{"tf":1.0},"357":{"tf":1.0},"38":{"tf":1.0},"422":{"tf":1.0},"51":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.0},"572":{"tf":1.0},"619":{"tf":1.4142135623730951},"694":{"tf":1.0},"754":{"tf":1.0},"763":{"tf":1.0},"788":{"tf":1.4142135623730951},"799":{"tf":1.0},"871":{"tf":1.0},"881":{"tf":1.0}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":17,"docs":{"1004":{"tf":1.0},"21":{"tf":1.0},"253":{"tf":1.4142135623730951},"267":{"tf":1.0},"292":{"tf":1.0},"313":{"tf":1.0},"330":{"tf":1.0},"374":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"501":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"835":{"tf":1.0},"992":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"565":{"tf":1.0}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"427":{"tf":1.0},"95":{"tf":1.0}}}}}}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":14,"docs":{"257":{"tf":1.0},"347":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.4142135623730951},"427":{"tf":1.0},"428":{"tf":1.4142135623730951},"507":{"tf":1.0},"516":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"736":{"tf":1.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"880":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"680":{"tf":1.0}}}}}}},"df":5,"docs":{"390":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"455":{"tf":1.0},"846":{"tf":1.4142135623730951}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"346":{"tf":1.0},"376":{"tf":1.0},"627":{"tf":1.0}},"t":{"df":6,"docs":{"337":{"tf":1.0},"347":{"tf":1.0},"377":{"tf":1.0},"402":{"tf":1.0},"514":{"tf":1.0},"748":{"tf":1.0}}}}}},"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":13,"docs":{"18":{"tf":1.0},"22":{"tf":1.0},"273":{"tf":1.0},"341":{"tf":1.4142135623730951},"345":{"tf":1.4142135623730951},"346":{"tf":1.7320508075688772},"349":{"tf":1.7320508075688772},"350":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"735":{"tf":1.0},"778":{"tf":1.0},"83":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"m":{"df":15,"docs":{"172":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"23":{"tf":1.0},"296":{"tf":1.4142135623730951},"314":{"tf":1.0},"402":{"tf":1.0},"435":{"tf":1.0},"444":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"786":{"tf":1.0},"912":{"tf":1.0}},"p":{"df":0,"docs":{},"t":{"df":2,"docs":{"773":{"tf":1.0},"828":{"tf":1.0}}}}}}},"t":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"111":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":40,"docs":{"0":{"tf":1.0},"151":{"tf":1.0},"16":{"tf":1.0},"223":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"351":{"tf":1.0},"367":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"399":{"tf":1.0},"44":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"523":{"tf":1.7320508075688772},"528":{"tf":1.0},"534":{"tf":1.0},"553":{"tf":1.0},"57":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"619":{"tf":1.0},"64":{"tf":1.0},"71":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"786":{"tf":1.0},"842":{"tf":1.0},"844":{"tf":1.0},"847":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":76,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1004":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"219":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"45":{"tf":1.4142135623730951},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.4142135623730951},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}}},"x":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"w":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"603":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":13,"docs":{"203":{"tf":1.0},"316":{"tf":1.0},"334":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.4142135623730951},"431":{"tf":1.0},"457":{"tf":1.0},"500":{"tf":1.0},"567":{"tf":1.0},"603":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"848":{"tf":1.0}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"o":{"df":1,"docs":{"743":{"tf":1.0}}}}},"u":{"df":14,"docs":{"155":{"tf":1.0},"194":{"tf":1.0},"236":{"tf":1.0},"314":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"63":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"760":{"tf":1.4142135623730951},"776":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0},"973":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":21,"docs":{"39":{"tf":1.4142135623730951},"44":{"tf":1.0},"46":{"tf":1.0},"697":{"tf":1.0},"78":{"tf":2.23606797749979},"874":{"tf":1.0},"9":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.7320508075688772},"958":{"tf":1.0},"959":{"tf":2.0},"961":{"tf":2.6457513110645907},"962":{"tf":1.7320508075688772},"964":{"tf":1.0},"965":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"971":{"tf":2.0},"972":{"tf":1.7320508075688772},"973":{"tf":2.0}}}},"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"773":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"267":{"tf":1.0},"576":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":13,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"329":{"tf":1.0},"340":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"470":{"tf":1.0},"565":{"tf":1.0},"81":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"'":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":4,"docs":{"208":{"tf":1.7320508075688772},"322":{"tf":1.0},"329":{"tf":1.0},"469":{"tf":1.0}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":31,"docs":{"111":{"tf":1.0},"114":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"255":{"tf":1.0},"313":{"tf":1.0},"427":{"tf":1.0},"505":{"tf":1.0},"526":{"tf":1.0},"602":{"tf":1.0},"694":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.4142135623730951},"744":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":2.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"81":{"tf":2.0},"831":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":2.23606797749979},"878":{"tf":1.0},"932":{"tf":1.4142135623730951},"934":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":3,"docs":{"251":{"tf":1.0},"697":{"tf":1.0},"740":{"tf":1.0}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":5,"docs":{"204":{"tf":1.0},"333":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.0},"683":{"tf":1.0}}},"t":{"df":4,"docs":{"333":{"tf":1.0},"455":{"tf":1.0},"564":{"tf":1.0},"7":{"tf":1.0}}}},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"551":{"tf":1.0}}},"s":{"df":8,"docs":{"184":{"tf":1.0},"30":{"tf":1.0},"349":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"609":{"tf":1.0},"807":{"tf":1.0}}},"t":{"df":6,"docs":{"146":{"tf":1.0},"19":{"tf":1.0},"40":{"tf":1.0},"519":{"tf":1.0},"522":{"tf":1.0},"83":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":6,"docs":{"370":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":2.449489742783178},"795":{"tf":1.7320508075688772},"796":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"799":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"733":{"tf":1.0}}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":9,"docs":{"139":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"438":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0},"94":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"201":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"i":{"df":2,"docs":{"735":{"tf":2.0},"739":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"'":{"df":2,"docs":{"203":{"tf":1.0},"208":{"tf":1.4142135623730951}}},":":{":":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"279":{"tf":1.0},"280":{"tf":1.0},"284":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":6,"docs":{"438":{"tf":2.0},"441":{"tf":1.4142135623730951},"450":{"tf":1.7320508075688772},"634":{"tf":1.4142135623730951},"636":{"tf":1.7320508075688772},"637":{"tf":1.0}}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":1,"docs":{"438":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}}},"df":78,"docs":{"16":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.4142135623730951},"200":{"tf":2.0},"203":{"tf":3.3166247903554},"204":{"tf":3.1622776601683795},"205":{"tf":4.123105625617661},"206":{"tf":1.7320508075688772},"207":{"tf":3.0},"208":{"tf":5.656854249492381},"213":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"218":{"tf":1.7320508075688772},"219":{"tf":1.0},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"23":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":1.4142135623730951},"270":{"tf":1.0},"279":{"tf":1.7320508075688772},"28":{"tf":1.0},"280":{"tf":1.4142135623730951},"322":{"tf":1.0},"325":{"tf":1.0},"328":{"tf":1.0},"335":{"tf":1.0},"361":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"374":{"tf":2.449489742783178},"377":{"tf":1.0},"409":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"438":{"tf":1.4142135623730951},"444":{"tf":1.0},"450":{"tf":2.6457513110645907},"46":{"tf":1.0},"47":{"tf":1.0},"52":{"tf":1.0},"615":{"tf":1.0},"627":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"63":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":3.3166247903554},"634":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.7320508075688772},"72":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"742":{"tf":2.0},"748":{"tf":2.0},"749":{"tf":2.23606797749979},"751":{"tf":2.23606797749979},"752":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":3.0},"777":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.7320508075688772},"911":{"tf":2.23606797749979},"912":{"tf":3.605551275463989},"913":{"tf":2.449489742783178},"916":{"tf":1.0},"917":{"tf":1.7320508075688772},"919":{"tf":1.7320508075688772},"938":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":7,"docs":{"205":{"tf":1.0},"208":{"tf":2.0},"221":{"tf":1.0},"438":{"tf":1.0},"627":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"644":{"tf":1.0}}}}},"df":0,"docs":{}}},"j":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"441":{"tf":1.0}}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":2,"docs":{"205":{"tf":1.0},"208":{"tf":2.6457513110645907}}}}},"df":0,"docs":{}},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{")":{"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"750":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":3,"docs":{"207":{"tf":2.449489742783178},"749":{"tf":1.0},"750":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"t":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":67,"docs":{"195":{"tf":2.23606797749979},"196":{"tf":1.0},"203":{"tf":6.244997998398398},"204":{"tf":4.58257569495584},"205":{"tf":4.0},"206":{"tf":3.3166247903554},"207":{"tf":3.1622776601683795},"208":{"tf":2.8284271247461903},"210":{"tf":1.4142135623730951},"212":{"tf":1.4142135623730951},"213":{"tf":2.6457513110645907},"215":{"tf":1.4142135623730951},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":1.7320508075688772},"221":{"tf":1.7320508075688772},"222":{"tf":1.0},"226":{"tf":1.0},"263":{"tf":1.7320508075688772},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"267":{"tf":3.4641016151377544},"368":{"tf":1.0},"370":{"tf":1.0},"374":{"tf":1.0},"381":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"48":{"tf":1.4142135623730951},"52":{"tf":1.7320508075688772},"58":{"tf":1.4142135623730951},"741":{"tf":1.7320508075688772},"742":{"tf":1.0},"743":{"tf":1.4142135623730951},"745":{"tf":1.0},"752":{"tf":1.0},"756":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":2.0},"776":{"tf":2.6457513110645907},"777":{"tf":1.7320508075688772},"778":{"tf":1.4142135623730951},"779":{"tf":1.7320508075688772},"811":{"tf":1.0},"909":{"tf":1.7320508075688772},"911":{"tf":2.23606797749979},"912":{"tf":3.0},"913":{"tf":1.7320508075688772},"914":{"tf":1.4142135623730951},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.7320508075688772},"938":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"945":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.7320508075688772},"958":{"tf":1.0},"959":{"tf":2.0},"960":{"tf":2.0},"961":{"tf":1.4142135623730951},"962":{"tf":1.4142135623730951},"970":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.4142135623730951}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"1006":{"tf":1.0},"833":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"876":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":24,"docs":{"142":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"343":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.0},"397":{"tf":1.0},"402":{"tf":1.0},"44":{"tf":1.0},"457":{"tf":1.0},"514":{"tf":1.0},"526":{"tf":1.0},"586":{"tf":1.0},"633":{"tf":1.0},"724":{"tf":1.0},"752":{"tf":1.0},"819":{"tf":1.0},"870":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.4142135623730951},"932":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"151":{"tf":1.0},"372":{"tf":1.0},"406":{"tf":1.0},"514":{"tf":1.0},"586":{"tf":1.0},"651":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"l":{"df":2,"docs":{"428":{"tf":1.0},"773":{"tf":1.0}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"413":{"tf":1.0}}},"df":0,"docs":{},"n":{"d":{"df":19,"docs":{"134":{"tf":1.0},"205":{"tf":1.4142135623730951},"231":{"tf":1.0},"24":{"tf":1.0},"252":{"tf":1.0},"257":{"tf":1.4142135623730951},"348":{"tf":1.0},"350":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"455":{"tf":1.0},"507":{"tf":1.4142135623730951},"524":{"tf":1.0},"637":{"tf":1.0},"837":{"tf":1.0},"894":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"198":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":1,"docs":{"532":{"tf":1.0}}}},"t":{"df":46,"docs":{"124":{"tf":1.0},"144":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"236":{"tf":1.0},"267":{"tf":1.4142135623730951},"29":{"tf":1.0},"39":{"tf":1.0},"42":{"tf":1.0},"428":{"tf":1.0},"471":{"tf":1.0},"486":{"tf":1.0},"51":{"tf":1.0},"54":{"tf":1.0},"554":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"577":{"tf":1.7320508075688772},"60":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"711":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"739":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"799":{"tf":1.4142135623730951},"810":{"tf":2.0},"811":{"tf":1.0},"814":{"tf":1.0},"826":{"tf":1.7320508075688772},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"863":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"951":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"577":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"722":{"tf":2.0}},"e":{"df":0,"docs":{},"r":{"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":0,"docs":{}},"df":6,"docs":{"208":{"tf":1.0},"63":{"tf":2.23606797749979},"64":{"tf":1.7320508075688772},"72":{"tf":1.0},"77":{"tf":1.0},"928":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":3,"docs":{"735":{"tf":3.3166247903554},"739":{"tf":1.4142135623730951},"776":{"tf":1.0}},"i":{"df":1,"docs":{"198":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"466":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"l":{"df":4,"docs":{"126":{"tf":1.0},"437":{"tf":1.0},"816":{"tf":1.7320508075688772},"874":{"tf":1.0}}}},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"571":{"tf":1.0},"712":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":16,"docs":{"204":{"tf":1.0},"237":{"tf":1.0},"30":{"tf":1.0},"402":{"tf":1.0},"519":{"tf":1.4142135623730951},"54":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"67":{"tf":1.0},"714":{"tf":1.4142135623730951},"720":{"tf":1.0},"721":{"tf":1.0},"810":{"tf":1.0},"817":{"tf":1.0},"843":{"tf":1.4142135623730951}}}}}},"p":{"df":1,"docs":{"126":{"tf":3.3166247903554}},"u":{"df":4,"docs":{"444":{"tf":1.4142135623730951},"711":{"tf":1.7320508075688772},"763":{"tf":1.0},"996":{"tf":1.0}}}},"q":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"151":{"tf":1.0},"912":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":2,"docs":{"315":{"tf":1.0},"786":{"tf":1.0}},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":1,"docs":{"315":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":46,"docs":{"113":{"tf":1.0},"121":{"tf":1.4142135623730951},"171":{"tf":1.7320508075688772},"180":{"tf":1.0},"193":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"249":{"tf":1.0},"300":{"tf":1.4142135623730951},"301":{"tf":1.0},"303":{"tf":1.0},"323":{"tf":1.0},"328":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"411":{"tf":1.0},"414":{"tf":1.0},"42":{"tf":1.0},"436":{"tf":1.0},"524":{"tf":1.0},"551":{"tf":1.0},"554":{"tf":1.0},"574":{"tf":1.0},"586":{"tf":1.0},"633":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"804":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"818":{"tf":1.0},"83":{"tf":1.4142135623730951},"849":{"tf":1.0},"85":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"895":{"tf":1.0},"898":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"948":{"tf":1.0},"959":{"tf":1.0},"976":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"!":{"(":{"\"":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"(":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"898":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}}}},"df":12,"docs":{"322":{"tf":1.0},"346":{"tf":1.4142135623730951},"410":{"tf":1.0},"412":{"tf":1.0},"549":{"tf":1.7320508075688772},"550":{"tf":1.0},"553":{"tf":1.0},"555":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"969":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.4142135623730951}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"848":{"tf":1.0}}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"234":{"tf":1.0}}}},"df":0,"docs":{},"t":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"203":{"tf":2.6457513110645907},"205":{"tf":1.7320508075688772},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":3,"docs":{"231":{"tf":1.0},"528":{"tf":1.0},"913":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"c":{"df":7,"docs":{"124":{"tf":1.0},"155":{"tf":1.0},"281":{"tf":1.0},"324":{"tf":1.0},"354":{"tf":1.0},"418":{"tf":1.0},"440":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":17,"docs":{"12":{"tf":1.0},"17":{"tf":1.0},"18":{"tf":1.4142135623730951},"19":{"tf":1.0},"4":{"tf":1.0},"49":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"608":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"8":{"tf":1.0},"81":{"tf":1.0},"82":{"tf":1.0},"874":{"tf":1.0}}}},"w":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":6,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":2.6457513110645907},"370":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"206":{"tf":1.4142135623730951},"267":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"361":{"tf":1.0},"418":{"tf":1.0},"514":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"40":{"tf":1.0}}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":1,"docs":{"418":{"tf":1.0}}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"h":{"df":6,"docs":{"322":{"tf":1.0},"340":{"tf":1.4142135623730951},"455":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"95":{"tf":1.0}},"i":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"113":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"342":{"tf":1.0},"723":{"tf":1.0}},"u":{"df":3,"docs":{"203":{"tf":1.0},"254":{"tf":1.0},"630":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"429":{"tf":1.7320508075688772}}},"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":1,"docs":{"568":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":117,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.4142135623730951},"140":{"tf":1.0},"148":{"tf":1.0},"171":{"tf":1.4142135623730951},"180":{"tf":1.0},"184":{"tf":1.4142135623730951},"193":{"tf":1.0},"194":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.449489742783178},"208":{"tf":2.0},"221":{"tf":1.0},"244":{"tf":1.0},"248":{"tf":1.0},"254":{"tf":1.0},"284":{"tf":1.0},"29":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.7320508075688772},"300":{"tf":1.4142135623730951},"303":{"tf":1.0},"314":{"tf":1.0},"344":{"tf":1.4142135623730951},"373":{"tf":1.0},"39":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"404":{"tf":1.4142135623730951},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"418":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"450":{"tf":1.0},"457":{"tf":1.0},"471":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.0},"50":{"tf":1.0},"500":{"tf":2.449489742783178},"512":{"tf":1.0},"515":{"tf":1.7320508075688772},"52":{"tf":1.0},"534":{"tf":1.4142135623730951},"537":{"tf":2.0},"539":{"tf":1.4142135623730951},"540":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.4142135623730951},"577":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":2.0},"606":{"tf":1.0},"614":{"tf":1.0},"619":{"tf":1.0},"637":{"tf":1.0},"65":{"tf":1.0},"653":{"tf":1.0},"694":{"tf":1.0},"701":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"732":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"770":{"tf":1.4142135623730951},"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951},"786":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.7320508075688772},"814":{"tf":1.0},"822":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"843":{"tf":1.0},"85":{"tf":1.0},"858":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.7320508075688772},"878":{"tf":1.0},"881":{"tf":1.4142135623730951},"895":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"931":{"tf":1.0},"937":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}}}},"s":{"df":1,"docs":{"777":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"749":{"tf":1.0}}}}}},"df":17,"docs":{"1002":{"tf":1.7320508075688772},"103":{"tf":1.0},"204":{"tf":1.0},"417":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"776":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"93":{"tf":1.7320508075688772},"94":{"tf":1.0},"95":{"tf":2.8284271247461903},"97":{"tf":1.0}},"e":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"(":{"7":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"577":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"663":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":11,"docs":{"169":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.7320508075688772},"21":{"tf":1.0},"26":{"tf":1.0},"30":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.0},"519":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"t":{"df":2,"docs":{"356":{"tf":1.0},"440":{"tf":1.0}}}},"y":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"936":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"38":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"49":{"tf":1.0},"55":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"d":{"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"df":4,"docs":{"39":{"tf":1.0},"42":{"tf":1.0},"47":{"tf":1.7320508075688772},"55":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":2.449489742783178}}},"y":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"571":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"m":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"108":{"tf":1.0},"267":{"tf":1.0},"697":{"tf":1.0},"852":{"tf":1.0}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"752":{"tf":1.0}}}}}},"n":{"c":{"df":1,"docs":{"293":{"tf":1.0}}},"df":4,"docs":{"467":{"tf":1.0},"469":{"tf":2.449489742783178},"470":{"tf":1.7320508075688772},"471":{"tf":1.0}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":3,"docs":{"1":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}}}},"o":{"df":3,"docs":{"188":{"tf":1.0},"784":{"tf":1.0},"876":{"tf":1.4142135623730951}}},"p":{"df":0,"docs":{},"p":{"df":13,"docs":{"18":{"tf":1.0},"33":{"tf":1.0},"4":{"tf":1.0},"414":{"tf":1.4142135623730951},"601":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"82":{"tf":1.0},"895":{"tf":1.4142135623730951},"977":{"tf":1.0}}}},"s":{"df":0,"docs":{},"h":{"b":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"804":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"a":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"512":{"tf":1.0}}}},"df":0,"docs":{}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":73,"docs":{"140":{"tf":1.0},"151":{"tf":1.4142135623730951},"152":{"tf":2.0},"155":{"tf":1.7320508075688772},"171":{"tf":1.0},"19":{"tf":1.7320508075688772},"191":{"tf":1.4142135623730951},"208":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.7320508075688772},"253":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":1.4142135623730951},"340":{"tf":1.0},"343":{"tf":1.4142135623730951},"346":{"tf":1.7320508075688772},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"375":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":1.0},"422":{"tf":1.0},"431":{"tf":1.0},"435":{"tf":2.0},"436":{"tf":2.0},"439":{"tf":1.7320508075688772},"44":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":2.0},"46":{"tf":1.4142135623730951},"47":{"tf":2.0},"49":{"tf":1.0},"497":{"tf":2.0},"5":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.4142135623730951},"520":{"tf":1.4142135623730951},"521":{"tf":2.6457513110645907},"522":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.7320508075688772},"526":{"tf":2.23606797749979},"532":{"tf":1.0},"537":{"tf":1.0},"553":{"tf":1.0},"571":{"tf":1.4142135623730951},"586":{"tf":1.0},"6":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"73":{"tf":1.0},"735":{"tf":4.795831523312719},"739":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.7320508075688772},"815":{"tf":1.4142135623730951},"818":{"tf":1.0},"826":{"tf":1.0},"84":{"tf":1.4142135623730951},"847":{"tf":1.0},"85":{"tf":1.0},"88":{"tf":1.0},"907":{"tf":1.0},"961":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.7320508075688772}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"204":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":69,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"376":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"418":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"515":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.4142135623730951},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"912":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}}},"v":{"df":0,"docs":{},"e":{"df":2,"docs":{"208":{"tf":1.7320508075688772},"878":{"tf":1.0}}},"i":{"d":{"df":1,"docs":{"322":{"tf":1.0}}},"df":0,"docs":{}}},"y":{"df":30,"docs":{"169":{"tf":1.0},"175":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":2.0},"186":{"tf":1.4142135623730951},"198":{"tf":1.0},"207":{"tf":1.7320508075688772},"39":{"tf":1.0},"470":{"tf":1.4142135623730951},"50":{"tf":1.0},"55":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":2.0},"565":{"tf":1.0},"567":{"tf":2.8284271247461903},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":2.23606797749979},"573":{"tf":3.0},"575":{"tf":1.7320508075688772},"576":{"tf":1.0},"577":{"tf":1.0},"776":{"tf":1.7320508075688772},"829":{"tf":1.0},"846":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.0}}}},"b":{"df":1,"docs":{"163":{"tf":1.0}}},"df":4,"docs":{"112":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"717":{"tf":1.4142135623730951},"749":{"tf":1.0}},"e":{"a":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"126":{"tf":1.4142135623730951},"208":{"tf":1.0},"281":{"tf":1.0},"735":{"tf":2.0}}}}}},"df":0,"docs":{},"l":{"df":3,"docs":{"377":{"tf":1.0},"651":{"tf":1.0},"852":{"tf":1.0}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"365":{"tf":1.0}}}}}}}},"b":{"a":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":2,"docs":{"121":{"tf":1.0},"29":{"tf":1.7320508075688772}},"g":{"df":1,"docs":{"29":{"tf":1.0}}}}}},"c":{"a":{"df":0,"docs":{},"y":{"df":3,"docs":{"1002":{"tf":1.0},"1003":{"tf":1.0},"749":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":17,"docs":{"111":{"tf":1.0},"138":{"tf":1.0},"147":{"tf":1.0},"303":{"tf":1.4142135623730951},"313":{"tf":1.0},"314":{"tf":1.0},"427":{"tf":1.0},"843":{"tf":1.0},"848":{"tf":1.4142135623730951},"849":{"tf":1.7320508075688772},"876":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"971":{"tf":1.0},"973":{"tf":1.4142135623730951}}}}}},"i":{"d":{"df":18,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"265":{"tf":1.0},"270":{"tf":1.0},"303":{"tf":1.4142135623730951},"402":{"tf":1.0},"438":{"tf":1.0},"512":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":1.0},"568":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"m":{"df":2,"docs":{"520":{"tf":1.7320508075688772},"534":{"tf":1.0}}},"s":{"df":21,"docs":{"1006":{"tf":1.0},"123":{"tf":1.0},"126":{"tf":4.0},"137":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"187":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"846":{"tf":1.4142135623730951},"857":{"tf":1.7320508075688772},"858":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.0},"861":{"tf":1.7320508075688772},"862":{"tf":1.7320508075688772},"863":{"tf":1.4142135623730951},"869":{"tf":1.0},"876":{"tf":1.4142135623730951},"878":{"tf":1.0},"913":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"126":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"a":{"df":0,"docs":{},"r":{"df":5,"docs":{"455":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.7320508075688772},"523":{"tf":1.0},"534":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"d":{"df":31,"docs":{"151":{"tf":2.0},"152":{"tf":1.0},"154":{"tf":1.0},"177":{"tf":1.0},"201":{"tf":1.0},"333":{"tf":1.0},"350":{"tf":1.4142135623730951},"435":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.0},"514":{"tf":1.4142135623730951},"516":{"tf":1.4142135623730951},"517":{"tf":1.0},"519":{"tf":1.7320508075688772},"521":{"tf":1.0},"522":{"tf":2.449489742783178},"523":{"tf":2.0},"586":{"tf":1.0},"588":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":2.449489742783178},"633":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.4142135623730951},"831":{"tf":1.0},"898":{"tf":1.0}},"e":{"<":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"d":{"a":{"df":0,"docs":{},"t":{"a":{">":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{">":{"(":{"df":0,"docs":{},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"3":{"2":{">":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{">":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"205":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"994":{"tf":1.0},"996":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":2,"docs":{"927":{"tf":1.0},"934":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":13,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":2.0},"213":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"444":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0},"732":{"tf":1.0},"749":{"tf":1.0},"846":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"63":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"i":{"c":{"df":10,"docs":{"203":{"tf":1.4142135623730951},"208":{"tf":1.0},"316":{"tf":1.0},"358":{"tf":1.0},"374":{"tf":1.4142135623730951},"467":{"tf":1.0},"482":{"tf":1.0},"651":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}},"df":0,"docs":{}}},"df":5,"docs":{"58":{"tf":1.0},"600":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"782":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"514":{"tf":1.0},"67":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"928":{"tf":1.0},"931":{"tf":1.0}}}}}},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":11,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"175":{"tf":1.0},"255":{"tf":1.0},"296":{"tf":1.0},"39":{"tf":1.0},"455":{"tf":1.0},"500":{"tf":1.0},"761":{"tf":2.23606797749979},"829":{"tf":1.0},"831":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"188":{"tf":1.0},"855":{"tf":1.0}}}},"r":{"df":2,"docs":{"563":{"tf":1.0},"573":{"tf":2.449489742783178}}}},"i":{"df":1,"docs":{"973":{"tf":1.0}},"n":{"df":38,"docs":{"111":{"tf":1.0},"126":{"tf":1.4142135623730951},"132":{"tf":1.0},"133":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":1.4142135623730951},"207":{"tf":1.7320508075688772},"222":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.4142135623730951},"255":{"tf":1.0},"284":{"tf":1.0},"331":{"tf":1.0},"34":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":2.0},"387":{"tf":1.0},"482":{"tf":1.0},"500":{"tf":1.0},"505":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.4142135623730951},"6":{"tf":1.0},"63":{"tf":1.0},"697":{"tf":1.4142135623730951},"723":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.7320508075688772},"831":{"tf":1.0},"961":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":15,"docs":{"1":{"tf":1.0},"140":{"tf":1.0},"164":{"tf":1.0},"165":{"tf":1.0},"171":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":1.4142135623730951},"341":{"tf":1.4142135623730951},"390":{"tf":1.0},"522":{"tf":1.0},"668":{"tf":1.0},"874":{"tf":1.0}}}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":3,"docs":{"152":{"tf":1.0},"290":{"tf":1.0},"968":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":1,"docs":{"929":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"y":{"df":8,"docs":{"138":{"tf":1.0},"257":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"507":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"799":{"tf":1.0}}},"_":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"799":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":11,"docs":{"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"795":{"tf":1.7320508075688772},"796":{"tf":3.1622776601683795},"797":{"tf":2.23606797749979},"799":{"tf":4.898979485566356},"800":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.7320508075688772},"807":{"tf":1.7320508075688772}}},"t":{"df":7,"docs":{"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"875":{"tf":1.4142135623730951},"879":{"tf":1.7320508075688772},"881":{"tf":2.449489742783178},"889":{"tf":1.0},"890":{"tf":1.0}},"e":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}}},"v":{"df":2,"docs":{"40":{"tf":1.0},"721":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"200":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.0}}}}}}},"t":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"723":{"tf":2.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"v":{"df":1,"docs":{"818":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":23,"docs":{"267":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"5":{"tf":1.0},"58":{"tf":1.0},"72":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":1.7320508075688772},"752":{"tf":1.0},"776":{"tf":1.7320508075688772},"779":{"tf":1.0},"808":{"tf":1.7320508075688772},"809":{"tf":1.7320508075688772},"810":{"tf":2.0},"812":{"tf":1.0},"813":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"815":{"tf":1.7320508075688772},"817":{"tf":1.4142135623730951},"826":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"938":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":2,"docs":{"207":{"tf":1.4142135623730951},"375":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"467":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"203":{"tf":1.4142135623730951},"221":{"tf":1.7320508075688772}}}}},"t":{"df":2,"docs":{"204":{"tf":1.0},"568":{"tf":1.4142135623730951}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"776":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":25,"docs":{"131":{"tf":1.0},"187":{"tf":1.0},"200":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"417":{"tf":1.0},"438":{"tf":1.0},"455":{"tf":1.0},"514":{"tf":1.0},"526":{"tf":1.0},"651":{"tf":1.0},"693":{"tf":1.0},"700":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"814":{"tf":1.0},"852":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":20,"docs":{"140":{"tf":1.0},"199":{"tf":1.7320508075688772},"200":{"tf":1.7320508075688772},"210":{"tf":1.0},"211":{"tf":1.0},"249":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.0},"358":{"tf":1.0},"363":{"tf":1.4142135623730951},"366":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"588":{"tf":1.0},"810":{"tf":1.4142135623730951},"928":{"tf":1.0},"959":{"tf":1.0},"960":{"tf":1.0},"961":{"tf":1.4142135623730951},"969":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":54,"docs":{"198":{"tf":1.4142135623730951},"300":{"tf":1.0},"375":{"tf":1.7320508075688772},"410":{"tf":2.0},"411":{"tf":1.4142135623730951},"412":{"tf":3.1622776601683795},"413":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"415":{"tf":2.449489742783178},"416":{"tf":1.7320508075688772},"417":{"tf":2.0},"418":{"tf":2.23606797749979},"420":{"tf":1.0},"422":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":2.23606797749979},"428":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"58":{"tf":1.4142135623730951},"60":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.0},"75":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":3.3166247903554},"815":{"tf":1.0},"817":{"tf":1.0},"857":{"tf":1.7320508075688772},"858":{"tf":1.4142135623730951},"859":{"tf":1.0},"860":{"tf":1.7320508075688772},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":2.0},"869":{"tf":1.0},"879":{"tf":3.7416573867739413},"880":{"tf":2.0},"881":{"tf":2.0},"889":{"tf":1.4142135623730951},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":2.0},"916":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.4142135623730951},"920":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"880":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}}}}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":11,"docs":{"169":{"tf":1.0},"440":{"tf":1.0},"650":{"tf":1.0},"660":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"739":{"tf":1.4142135623730951},"740":{"tf":1.0},"770":{"tf":1.4142135623730951},"984":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"206":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"402":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"300":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"818":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"v":{"df":22,"docs":{"123":{"tf":1.0},"124":{"tf":1.0},"24":{"tf":1.0},"3":{"tf":1.0},"341":{"tf":1.7320508075688772},"347":{"tf":1.0},"352":{"tf":1.0},"387":{"tf":1.7320508075688772},"388":{"tf":1.7320508075688772},"390":{"tf":1.0},"413":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0},"634":{"tf":1.4142135623730951},"782":{"tf":1.7320508075688772},"783":{"tf":1.4142135623730951},"784":{"tf":1.0},"786":{"tf":2.0},"799":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"874":{"tf":1.7320508075688772}},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"204":{"tf":1.0},"500":{"tf":1.4142135623730951},"706":{"tf":1.0},"761":{"tf":1.7320508075688772},"776":{"tf":1.0},"83":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":5,"docs":{"602":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.4142135623730951},"701":{"tf":1.0},"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"793":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"b":{"df":42,"docs":{"1008":{"tf":1.0},"1009":{"tf":1.0},"1015":{"tf":1.0},"123":{"tf":1.0},"191":{"tf":1.0},"203":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"251":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.7320508075688772},"267":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.0},"344":{"tf":1.0},"370":{"tf":1.0},"379":{"tf":1.0},"438":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"53":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"567":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"697":{"tf":1.0},"735":{"tf":1.0},"74":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":1.7320508075688772},"811":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"786":{"tf":2.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":71,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"184":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"333":{"tf":1.0},"346":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"748":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"786":{"tf":1.4142135623730951},"79":{"tf":1.0},"808":{"tf":1.0},"813":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":12,"docs":{"345":{"tf":1.7320508075688772},"627":{"tf":1.0},"632":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":2.0},"636":{"tf":1.7320508075688772},"637":{"tf":1.4142135623730951},"638":{"tf":1.0},"642":{"tf":1.7320508075688772},"644":{"tf":1.0},"648":{"tf":1.7320508075688772},"786":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"559":{"tf":1.7320508075688772}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":43,"docs":{"1006":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"124":{"tf":1.0},"138":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"303":{"tf":1.0},"323":{"tf":1.0},"349":{"tf":1.0},"35":{"tf":1.0},"356":{"tf":1.0},"38":{"tf":1.7320508075688772},"39":{"tf":1.0},"429":{"tf":1.0},"43":{"tf":1.0},"483":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"518":{"tf":1.0},"522":{"tf":1.0},"54":{"tf":1.0},"546":{"tf":1.0},"576":{"tf":1.0},"725":{"tf":1.0},"727":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"737":{"tf":1.0},"771":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"829":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}},"r":{"df":21,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"237":{"tf":1.0},"254":{"tf":1.0},"257":{"tf":1.0},"354":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"507":{"tf":1.0},"54":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"641":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"939":{"tf":1.0}}}},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"234":{"tf":1.0}}}}},"t":{"df":4,"docs":{"18":{"tf":1.0},"602":{"tf":3.872983346207417},"603":{"tf":1.7320508075688772},"696":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":11,"docs":{"222":{"tf":1.0},"599":{"tf":1.4142135623730951},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"666":{"tf":1.0},"692":{"tf":1.4142135623730951},"693":{"tf":1.0},"696":{"tf":1.0},"698":{"tf":1.0},"786":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":29,"docs":{"0":{"tf":1.0},"1006":{"tf":1.4142135623730951},"113":{"tf":1.0},"16":{"tf":1.0},"180":{"tf":1.0},"195":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.4142135623730951},"450":{"tf":1.0},"48":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"567":{"tf":1.0},"761":{"tf":1.0},"791":{"tf":1.0},"794":{"tf":1.0},"813":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":6,"docs":{"296":{"tf":1.0},"388":{"tf":1.0},"567":{"tf":1.7320508075688772},"635":{"tf":1.4142135623730951},"735":{"tf":1.0},"763":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"r":{"df":4,"docs":{"429":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":37,"docs":{"124":{"tf":1.4142135623730951},"126":{"tf":1.0},"127":{"tf":1.4142135623730951},"134":{"tf":1.0},"138":{"tf":1.0},"170":{"tf":1.0},"199":{"tf":1.0},"226":{"tf":1.0},"253":{"tf":1.4142135623730951},"303":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"364":{"tf":1.0},"415":{"tf":1.0},"51":{"tf":1.0},"524":{"tf":1.0},"550":{"tf":1.0},"553":{"tf":1.0},"568":{"tf":1.4142135623730951},"571":{"tf":1.4142135623730951},"588":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"648":{"tf":1.0},"721":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":2.0},"81":{"tf":1.0},"814":{"tf":1.0},"913":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"338":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"432":{"tf":1.0},"438":{"tf":1.4142135623730951},"516":{"tf":1.0},"525":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"c":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"874":{"tf":1.0}}}}}}}}}},"v":{"df":16,"docs":{"167":{"tf":1.4142135623730951},"170":{"tf":1.0},"175":{"tf":1.4142135623730951},"314":{"tf":1.0},"4":{"tf":1.0},"538":{"tf":1.4142135623730951},"587":{"tf":1.4142135623730951},"601":{"tf":1.7320508075688772},"615":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"82":{"tf":1.0},"977":{"tf":1.0}},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":74,"docs":{"1011":{"tf":1.0},"103":{"tf":1.0},"108":{"tf":1.0},"125":{"tf":1.7320508075688772},"131":{"tf":1.0},"141":{"tf":1.0},"145":{"tf":1.4142135623730951},"146":{"tf":1.0},"152":{"tf":1.0},"153":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.4142135623730951},"201":{"tf":1.0},"219":{"tf":1.4142135623730951},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"270":{"tf":1.0},"282":{"tf":1.0},"289":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"306":{"tf":1.0},"312":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.0},"322":{"tf":1.0},"328":{"tf":1.4142135623730951},"329":{"tf":1.0},"33":{"tf":1.7320508075688772},"367":{"tf":1.0},"369":{"tf":1.4142135623730951},"378":{"tf":1.0},"381":{"tf":1.7320508075688772},"382":{"tf":1.0},"407":{"tf":1.0},"414":{"tf":1.4142135623730951},"42":{"tf":1.0},"433":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.4142135623730951},"544":{"tf":1.0},"552":{"tf":1.0},"581":{"tf":1.0},"59":{"tf":1.0},"593":{"tf":1.0},"608":{"tf":1.0},"630":{"tf":1.7320508075688772},"687":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"774":{"tf":1.0},"785":{"tf":1.0},"830":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.4142135623730951},"856":{"tf":1.0},"877":{"tf":1.0},"886":{"tf":1.0},"902":{"tf":1.0},"914":{"tf":1.0},"943":{"tf":1.0},"952":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"969":{"tf":1.4142135623730951},"973":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"848":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"i":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"744":{"tf":1.0}}}},"c":{"df":5,"docs":{"514":{"tf":1.4142135623730951},"515":{"tf":2.449489742783178},"516":{"tf":1.4142135623730951},"517":{"tf":1.0},"95":{"tf":2.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"314":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"t":{"df":19,"docs":{"247":{"tf":2.0},"248":{"tf":1.4142135623730951},"249":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.7320508075688772},"255":{"tf":1.0},"257":{"tf":1.0},"495":{"tf":1.7320508075688772},"501":{"tf":1.4142135623730951},"502":{"tf":2.23606797749979},"503":{"tf":2.0},"505":{"tf":1.0},"507":{"tf":1.0},"549":{"tf":1.7320508075688772},"550":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":2.449489742783178},"554":{"tf":1.4142135623730951},"66":{"tf":1.0}}}},"i":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":3,"docs":{"126":{"tf":1.0},"46":{"tf":1.0},"878":{"tf":2.23606797749979}}}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"933":{"tf":1.0}},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"343":{"tf":1.0}}}}}}}}}}},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"553":{"tf":1.0},"761":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":62,"docs":{"142":{"tf":1.0},"151":{"tf":1.0},"163":{"tf":1.0},"169":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"21":{"tf":1.0},"218":{"tf":1.0},"22":{"tf":1.7320508075688772},"231":{"tf":1.0},"24":{"tf":1.7320508075688772},"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"288":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.4142135623730951},"33":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.4142135623730951},"407":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"52":{"tf":1.0},"522":{"tf":2.0},"567":{"tf":1.0},"586":{"tf":1.0},"598":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.0},"629":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"722":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"786":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"835":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.4142135623730951},"870":{"tf":1.0},"874":{"tf":1.0},"881":{"tf":1.0},"95":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":5,"docs":{"199":{"tf":1.0},"375":{"tf":1.0},"737":{"tf":1.4142135623730951},"832":{"tf":1.0},"990":{"tf":1.0}},"i":{"df":2,"docs":{"296":{"tf":1.0},"724":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":8,"docs":{"322":{"tf":1.0},"333":{"tf":1.0},"343":{"tf":2.449489742783178},"349":{"tf":2.0},"350":{"tf":1.4142135623730951},"513":{"tf":1.0},"516":{"tf":2.6457513110645907},"520":{"tf":2.23606797749979}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"343":{"tf":1.7320508075688772},"345":{"tf":1.0}}}}}}}}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}}},"m":{"a":{"df":1,"docs":{"430":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":105,"docs":{"1":{"tf":1.0},"1001":{"tf":1.0},"1002":{"tf":1.0},"1015":{"tf":1.0},"122":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.0},"182":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.0},"226":{"tf":1.0},"229":{"tf":1.0},"246":{"tf":1.0},"247":{"tf":1.0},"262":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"272":{"tf":1.0},"279":{"tf":1.0},"293":{"tf":1.0},"294":{"tf":1.0},"310":{"tf":1.0},"311":{"tf":1.0},"321":{"tf":1.0},"322":{"tf":1.0},"361":{"tf":1.0},"366":{"tf":1.0},"37":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"386":{"tf":1.0},"399":{"tf":1.0},"412":{"tf":1.0},"430":{"tf":1.0},"449":{"tf":1.0},"451":{"tf":1.0},"464":{"tf":1.0},"481":{"tf":1.0},"494":{"tf":1.0},"495":{"tf":1.0},"512":{"tf":1.0},"513":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.0},"584":{"tf":1.0},"597":{"tf":1.0},"598":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":1.0},"626":{"tf":1.0},"627":{"tf":1.0},"648":{"tf":1.0},"649":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":1.0},"708":{"tf":1.0},"709":{"tf":1.0},"728":{"tf":1.0},"757":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"799":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"826":{"tf":1.0},"827":{"tf":1.0},"840":{"tf":1.0},"871":{"tf":1.0},"890":{"tf":1.0},"891":{"tf":1.0},"907":{"tf":1.0},"908":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"926":{"tf":1.0},"939":{"tf":1.0},"940":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.0},"973":{"tf":1.0},"974":{"tf":1.0},"987":{"tf":1.0},"988":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":24,"docs":{"100":{"tf":1.0},"19":{"tf":1.0},"191":{"tf":1.4142135623730951},"314":{"tf":1.0},"365":{"tf":1.0},"375":{"tf":1.0},"40":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"633":{"tf":1.0},"663":{"tf":1.0},"696":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"959":{"tf":1.0},"979":{"tf":1.0}}}}}},"df":0,"docs":{}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":5,"docs":{"171":{"tf":1.0},"24":{"tf":1.0},"255":{"tf":1.0},"404":{"tf":1.0},"531":{"tf":1.0}}}},"d":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"453":{"tf":1.0},"777":{"tf":1.4142135623730951},"84":{"tf":1.4142135623730951},"895":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"799":{"tf":1.0}}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"829":{"tf":1.0}}}},"df":0,"docs":{}}}}},"c":{"a":{"df":0,"docs":{},"r":{"d":{"df":4,"docs":{"204":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"339":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"497":{"tf":1.0},"567":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"721":{"tf":1.0},"776":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"895":{"tf":2.0}}}},"df":0,"docs":{},"s":{"df":1,"docs":{"418":{"tf":1.0}}}}},"v":{"df":7,"docs":{"248":{"tf":1.0},"254":{"tf":1.0},"296":{"tf":1.0},"496":{"tf":1.0},"512":{"tf":1.0},"66":{"tf":1.0},"8":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"495":{"tf":1.0}},"i":{"df":12,"docs":{"18":{"tf":1.0},"22":{"tf":1.0},"248":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"496":{"tf":1.0},"549":{"tf":1.7320508075688772},"550":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.4142135623730951},"772":{"tf":1.4142135623730951},"773":{"tf":1.0},"777":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"516":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":51,"docs":{"1014":{"tf":1.0},"16":{"tf":1.0},"161":{"tf":1.0},"180":{"tf":1.0},"194":{"tf":1.4142135623730951},"201":{"tf":1.0},"207":{"tf":1.0},"219":{"tf":1.0},"229":{"tf":1.0},"243":{"tf":1.0},"265":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"35":{"tf":1.4142135623730951},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"409":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"417":{"tf":1.0},"441":{"tf":1.0},"518":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.0},"569":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"581":{"tf":1.0},"60":{"tf":1.0},"630":{"tf":1.0},"646":{"tf":1.4142135623730951},"712":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.4142135623730951},"724":{"tf":1.4142135623730951},"727":{"tf":1.0},"74":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"778":{"tf":1.0},"780":{"tf":1.0},"794":{"tf":1.0},"807":{"tf":1.0},"824":{"tf":1.0},"844":{"tf":1.4142135623730951},"846":{"tf":1.0},"869":{"tf":1.0},"878":{"tf":1.0},"954":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"863":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"927":{"tf":1.0}}}}}}},"k":{"df":7,"docs":{"255":{"tf":1.0},"62":{"tf":1.0},"69":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"78":{"tf":1.0}}},"p":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":12,"docs":{"205":{"tf":3.0},"24":{"tf":1.0},"25":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"372":{"tf":1.0},"409":{"tf":1.0},"614":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":2.0},"944":{"tf":1.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"814":{"tf":1.4142135623730951},"879":{"tf":3.4641016151377544}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"514":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":14,"docs":{"39":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.7320508075688772},"450":{"tf":2.6457513110645907},"628":{"tf":1.0},"629":{"tf":2.23606797749979},"641":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"67":{"tf":1.0},"69":{"tf":1.4142135623730951},"715":{"tf":1.0},"811":{"tf":1.0},"815":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"222":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":5,"docs":{"140":{"tf":1.0},"146":{"tf":1.0},"356":{"tf":1.0},"573":{"tf":1.0},"990":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"173":{"tf":1.0},"335":{"tf":1.0},"368":{"tf":1.0},"722":{"tf":1.0},"817":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"7":{"tf":1.0},"81":{"tf":1.0}}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":26,"docs":{"205":{"tf":1.0},"24":{"tf":1.0},"248":{"tf":1.0},"303":{"tf":1.0},"373":{"tf":1.0},"430":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.4142135623730951},"438":{"tf":1.0},"439":{"tf":1.0},"551":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"64":{"tf":1.0},"65":{"tf":1.4142135623730951},"714":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.4142135623730951},"724":{"tf":1.4142135623730951},"73":{"tf":1.0},"74":{"tf":1.0},"77":{"tf":1.0},"932":{"tf":2.0},"933":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"573":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"567":{"tf":1.0}},"r":{"df":0,"docs":{},"g":{"df":3,"docs":{"350":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}},"s":{"df":4,"docs":{"19":{"tf":1.0},"24":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0}}},"t":{"df":2,"docs":{"264":{"tf":1.0},"267":{"tf":1.0}}}}},"i":{"d":{"df":6,"docs":{"204":{"tf":1.0},"335":{"tf":1.0},"512":{"tf":1.0},"717":{"tf":1.0},"759":{"tf":1.0},"931":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"201":{"tf":1.0},"774":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"p":{"df":4,"docs":{"203":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"222":{"tf":1.0}}}},"o":{"b":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"780":{"tf":1.0}}}}}}}}},"c":{"df":2,"docs":{"456":{"tf":1.0},"7":{"tf":1.0}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"334":{"tf":1.0}}},"df":21,"docs":{"171":{"tf":1.0},"209":{"tf":1.4142135623730951},"210":{"tf":1.4142135623730951},"272":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"330":{"tf":1.0},"341":{"tf":1.4142135623730951},"391":{"tf":1.0},"564":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"772":{"tf":1.0},"81":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":1.4142135623730951},"904":{"tf":1.0},"92":{"tf":1.0},"921":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}}}}}},"df":21,"docs":{"154":{"tf":1.0},"19":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"296":{"tf":1.0},"452":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"600":{"tf":1.0},"629":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"697":{"tf":1.0},"725":{"tf":1.0},"732":{"tf":1.0},"885":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":41,"docs":{"112":{"tf":1.0},"115":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"32":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"35":{"tf":1.0},"351":{"tf":1.0},"442":{"tf":1.0},"453":{"tf":1.0},"459":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"511":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"534":{"tf":1.4142135623730951},"6":{"tf":1.0},"615":{"tf":1.0},"660":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":2.6457513110645907},"761":{"tf":2.0},"762":{"tf":1.0},"776":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"826":{"tf":1.0},"848":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"’":{"df":0,"docs":{},"t":{"df":1,"docs":{"751":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"249":{"tf":1.0},"388":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"n":{"'":{"df":0,"docs":{},"t":{"df":24,"docs":{"208":{"tf":1.0},"250":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"523":{"tf":1.0},"528":{"tf":1.0},"568":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"65":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"831":{"tf":1.0},"846":{"tf":1.4142135623730951},"855":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"881":{"tf":2.0},"885":{"tf":1.0},"932":{"tf":1.0}}}},"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":32,"docs":{"112":{"tf":1.0},"177":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"234":{"tf":1.0},"257":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.0},"371":{"tf":1.0},"459":{"tf":1.0},"472":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"507":{"tf":1.0},"520":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"591":{"tf":1.0},"619":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.4142135623730951},"710":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"932":{"tf":1.0},"95":{"tf":1.0}}}},"r":{"a":{"d":{"df":0,"docs":{},"o":{"df":3,"docs":{"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"/":{"df":0,"docs":{},"k":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":4,"docs":{"429":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"566":{"tf":1.0}}}}}},"df":36,"docs":{"185":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.7320508075688772},"221":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"265":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.7320508075688772},"316":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":2.449489742783178},"376":{"tf":1.0},"412":{"tf":2.0},"415":{"tf":2.0},"416":{"tf":2.23606797749979},"417":{"tf":1.0},"42":{"tf":1.0},"427":{"tf":1.0},"470":{"tf":1.0},"473":{"tf":1.0},"48":{"tf":1.0},"52":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"724":{"tf":1.0},"745":{"tf":1.0},"752":{"tf":1.4142135623730951},"77":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"861":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}},"u":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"184":{"tf":1.0},"207":{"tf":1.0},"752":{"tf":1.0}},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"<":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"617":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"749":{"tf":1.0}}}},"t":{"df":1,"docs":{"577":{"tf":1.0}}}},"df":0,"docs":{}},"w":{"df":0,"docs":{},"n":{"df":11,"docs":{"152":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"284":{"tf":1.0},"437":{"tf":1.0},"60":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.0},"776":{"tf":1.0},"845":{"tf":1.0},"852":{"tf":1.0}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":1,"docs":{"609":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":9,"docs":{"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.4142135623730951},"722":{"tf":1.7320508075688772},"724":{"tf":1.0},"895":{"tf":1.0},"990":{"tf":1.4142135623730951}},"e":{"d":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"715":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"658":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"172":{"tf":1.0}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":6,"docs":{"144":{"tf":1.0},"203":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"371":{"tf":1.0},"501":{"tf":1.0}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":2,"docs":{"749":{"tf":1.4142135623730951},"776":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"p":{"d":{"df":1,"docs":{"126":{"tf":2.8284271247461903}}},"df":1,"docs":{"126":{"tf":3.1622776601683795}}},"r":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":6,"docs":{"16":{"tf":1.4142135623730951},"724":{"tf":1.0},"83":{"tf":1.0},"878":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"564":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":125,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.7320508075688772},"106":{"tf":1.0},"114":{"tf":1.0},"122":{"tf":1.0},"127":{"tf":1.0},"136":{"tf":1.0},"141":{"tf":1.4142135623730951},"150":{"tf":1.0},"155":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"173":{"tf":1.0},"182":{"tf":1.0},"187":{"tf":1.4142135623730951},"195":{"tf":1.0},"213":{"tf":1.0},"215":{"tf":1.0},"227":{"tf":1.0},"229":{"tf":1.0},"236":{"tf":1.4142135623730951},"247":{"tf":1.0},"254":{"tf":1.0},"268":{"tf":1.0},"27":{"tf":1.0},"274":{"tf":1.0},"279":{"tf":1.0},"285":{"tf":1.7320508075688772},"294":{"tf":1.0},"303":{"tf":1.0},"311":{"tf":1.0},"316":{"tf":1.0},"322":{"tf":1.0},"353":{"tf":1.0},"366":{"tf":1.0},"377":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"391":{"tf":1.4142135623730951},"410":{"tf":1.0},"418":{"tf":1.4142135623730951},"430":{"tf":1.0},"441":{"tf":1.0},"451":{"tf":1.0},"456":{"tf":1.0},"465":{"tf":1.0},"473":{"tf":1.0},"481":{"tf":1.0},"486":{"tf":1.0},"495":{"tf":1.0},"504":{"tf":1.0},"513":{"tf":1.0},"527":{"tf":1.0},"535":{"tf":1.0},"540":{"tf":1.0},"549":{"tf":1.0},"55":{"tf":1.0},"554":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"577":{"tf":1.0},"584":{"tf":1.0},"589":{"tf":1.0},"598":{"tf":1.0},"604":{"tf":1.4142135623730951},"613":{"tf":1.0},"618":{"tf":1.4142135623730951},"627":{"tf":1.0},"638":{"tf":1.4142135623730951},"649":{"tf":1.0},"655":{"tf":1.0},"664":{"tf":1.0},"669":{"tf":1.0},"678":{"tf":1.0},"68":{"tf":1.4142135623730951},"683":{"tf":1.0},"692":{"tf":1.0},"700":{"tf":1.0},"709":{"tf":1.0},"724":{"tf":1.0},"730":{"tf":1.0},"737":{"tf":1.0},"741":{"tf":1.0},"753":{"tf":1.0},"757":{"tf":1.0},"762":{"tf":1.0},"771":{"tf":1.0},"779":{"tf":1.0},"782":{"tf":1.0},"787":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.4142135623730951},"800":{"tf":1.4142135623730951},"808":{"tf":1.0},"818":{"tf":1.0},"827":{"tf":1.0},"832":{"tf":1.0},"84":{"tf":1.0},"841":{"tf":1.0},"849":{"tf":1.4142135623730951},"852":{"tf":1.0},"857":{"tf":1.0},"863":{"tf":1.0},"871":{"tf":1.0},"882":{"tf":1.0},"891":{"tf":1.0},"899":{"tf":1.4142135623730951},"908":{"tf":1.0},"915":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"934":{"tf":1.7320508075688772},"936":{"tf":1.0},"940":{"tf":1.0},"945":{"tf":1.4142135623730951},"957":{"tf":1.0},"962":{"tf":1.4142135623730951},"974":{"tf":1.0},"979":{"tf":1.4142135623730951},"98":{"tf":1.0},"988":{"tf":1.0},"993":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":1,"docs":{"807":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"342":{"tf":1.0}},"n":{"df":1,"docs":{"772":{"tf":1.0}}},"r":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":9,"docs":{"347":{"tf":1.0},"376":{"tf":1.0},"385":{"tf":1.0},"439":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"720":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"e":{"df":20,"docs":{"108":{"tf":1.4142135623730951},"127":{"tf":1.0},"203":{"tf":1.0},"255":{"tf":1.0},"3":{"tf":1.0},"388":{"tf":1.0},"422":{"tf":1.0},"500":{"tf":1.0},"505":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"737":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.0},"832":{"tf":1.0},"895":{"tf":1.0},"968":{"tf":1.0}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"1015":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"19":{"tf":1.4142135623730951},"347":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.4142135623730951},"453":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"t":{"df":15,"docs":{"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"186":{"tf":1.0},"190":{"tf":1.0},"204":{"tf":1.0},"284":{"tf":1.0},"342":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.7320508075688772},"568":{"tf":1.0},"573":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"e":{"df":38,"docs":{"141":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":2.449489742783178},"206":{"tf":1.0},"207":{"tf":1.7320508075688772},"267":{"tf":1.0},"323":{"tf":1.0},"324":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.4142135623730951},"374":{"tf":1.0},"406":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.4142135623730951},"500":{"tf":1.0},"571":{"tf":1.0},"653":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"720":{"tf":1.0},"772":{"tf":1.4142135623730951},"776":{"tf":2.0},"777":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"831":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.4142135623730951}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":3,"docs":{"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.4142135623730951}}}}},"y":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":24,"docs":{"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"147":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.4142135623730951},"28":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.4142135623730951},"576":{"tf":1.4142135623730951},"711":{"tf":1.0},"741":{"tf":1.7320508075688772},"742":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":1.0},"754":{"tf":1.0},"756":{"tf":1.0},"777":{"tf":1.0},"912":{"tf":1.0},"959":{"tf":1.0}},"i":{"c":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}},"s":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{":":{":":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"i":{"d":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"$":{"'":{"df":1,"docs":{"721":{"tf":1.0}}},"df":0,"docs":{}},".":{"df":0,"docs":{},"g":{"df":24,"docs":{"154":{"tf":1.0},"203":{"tf":1.0},"234":{"tf":1.4142135623730951},"364":{"tf":1.0},"372":{"tf":1.4142135623730951},"381":{"tf":1.0},"45":{"tf":1.0},"453":{"tf":1.0},"47":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"576":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"68":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":2.23606797749979},"81":{"tf":2.449489742783178},"878":{"tf":1.0},"880":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":2.0}}}},"[":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}}}}}}},"x":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}},"^":{"df":0,"docs":{},"{":{"a":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"c":{"df":0,"docs":{},"h":{"df":74,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":2.6457513110645907},"221":{"tf":1.0},"231":{"tf":1.7320508075688772},"255":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"323":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"337":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":2.0},"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":2.23606797749979},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"426":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.7320508075688772},"45":{"tf":1.4142135623730951},"455":{"tf":1.4142135623730951},"46":{"tf":2.0},"467":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"482":{"tf":1.7320508075688772},"483":{"tf":1.0},"485":{"tf":1.0},"507":{"tf":1.0},"51":{"tf":1.0},"522":{"tf":2.23606797749979},"523":{"tf":1.0},"524":{"tf":1.4142135623730951},"528":{"tf":1.0},"534":{"tf":1.0},"553":{"tf":1.7320508075688772},"568":{"tf":1.0},"586":{"tf":1.4142135623730951},"589":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.4142135623730951},"673":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"715":{"tf":1.7320508075688772},"717":{"tf":1.4142135623730951},"72":{"tf":1.0},"721":{"tf":2.23606797749979},"722":{"tf":1.7320508075688772},"723":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"776":{"tf":1.7320508075688772},"797":{"tf":1.0},"814":{"tf":1.0},"831":{"tf":1.0},"836":{"tf":1.0},"85":{"tf":1.0},"872":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.449489742783178},"912":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"130":{"tf":1.0},"214":{"tf":1.0},"619":{"tf":1.0},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"124":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"568":{"tf":1.0},"576":{"tf":1.0},"577":{"tf":1.0},"715":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0},"817":{"tf":1.0}}}}}},"n":{"df":3,"docs":{"470":{"tf":1.4142135623730951},"720":{"tf":2.0},"724":{"tf":1.0}}}},"s":{"df":1,"docs":{"961":{"tf":1.0}},"i":{"df":10,"docs":{"296":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.4142135623730951},"460":{"tf":1.0},"75":{"tf":1.0},"786":{"tf":1.0},"846":{"tf":1.0},"849":{"tf":1.4142135623730951},"952":{"tf":1.0},"969":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"573":{"tf":1.0},"725":{"tf":1.0},"777":{"tf":1.0},"836":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951}}}},"l":{"df":0,"docs":{},"i":{"df":15,"docs":{"253":{"tf":1.0},"314":{"tf":1.0},"497":{"tf":1.0},"518":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":1.0},"763":{"tf":1.4142135623730951},"810":{"tf":1.0},"811":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"847":{"tf":1.0}}}}}}},"c":{"d":{"df":0,"docs":{},"s":{"a":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"505":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":15,"docs":{"195":{"tf":1.0},"207":{"tf":1.4142135623730951},"211":{"tf":1.0},"213":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.0},"243":{"tf":1.0},"265":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.4142135623730951},"779":{"tf":1.0},"916":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":35,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"201":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.0},"329":{"tf":1.4142135623730951},"362":{"tf":1.0},"364":{"tf":1.0},"376":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"49":{"tf":1.0},"514":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"518":{"tf":1.0},"52":{"tf":1.0},"521":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"539":{"tf":1.0},"54":{"tf":1.0},"600":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"784":{"tf":1.0},"785":{"tf":1.0},"804":{"tf":1.0},"844":{"tf":1.0},"874":{"tf":1.0},"912":{"tf":1.4142135623730951},"971":{"tf":1.0},"973":{"tf":1.4142135623730951},"984":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"699":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":1,"docs":{"340":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"g":{"df":8,"docs":{"207":{"tf":1.0},"30":{"tf":1.0},"40":{"tf":1.0},"871":{"tf":1.0},"881":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"779":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"c":{"df":1,"docs":{"270":{"tf":1.0}}},"df":0,"docs":{}}},"df":5,"docs":{"112":{"tf":1.4142135623730951},"346":{"tf":1.0},"45":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0}},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":31,"docs":{"1008":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":2.8284271247461903},"207":{"tf":1.0},"208":{"tf":1.0},"24":{"tf":1.0},"267":{"tf":1.4142135623730951},"304":{"tf":1.0},"354":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"52":{"tf":1.0},"54":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"600":{"tf":1.0},"650":{"tf":1.4142135623730951},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"773":{"tf":1.0},"810":{"tf":1.4142135623730951},"831":{"tf":1.0},"849":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":2.0},"900":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":2.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"i":{"c":{"df":1,"docs":{"720":{"tf":1.0}},"i":{"df":30,"docs":{"103":{"tf":1.0},"124":{"tf":1.0},"144":{"tf":1.0},"199":{"tf":1.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.0},"28":{"tf":1.0},"29":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"46":{"tf":1.0},"650":{"tf":1.0},"732":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":1.7320508075688772},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"874":{"tf":1.4142135623730951},"880":{"tf":1.0},"885":{"tf":1.4142135623730951},"94":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.0},"968":{"tf":1.0},"97":{"tf":1.0},"991":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":15,"docs":{"139":{"tf":1.0},"181":{"tf":1.0},"437":{"tf":1.0},"546":{"tf":1.0},"548":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"609":{"tf":1.0},"66":{"tf":1.0},"725":{"tf":1.0},"797":{"tf":1.0},"85":{"tf":1.0},"855":{"tf":1.0},"951":{"tf":1.0},"975":{"tf":1.0}}}}}}},"g":{"df":3,"docs":{"932":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"55":{"tf":1.0}}}},"df":0,"docs":{}}}}},"p":{"df":2,"docs":{"39":{"tf":1.0},"55":{"tf":1.0}}}},"l":{"a":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"931":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":2,"docs":{"148":{"tf":1.0},"204":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":6,"docs":{"441":{"tf":1.0},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"121":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"235":{"tf":1.0},"240":{"tf":1.0},"370":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"376":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":10,"docs":{"28":{"tf":1.0},"333":{"tf":2.0},"344":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"520":{"tf":1.0},"54":{"tf":1.0},"735":{"tf":1.0},"773":{"tf":1.0},"85":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"h":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"346":{"tf":1.0}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"144":{"tf":1.0},"325":{"tf":1.0},"356":{"tf":1.0},"39":{"tf":1.0},"55":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"84":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":5,"docs":{"103":{"tf":1.0},"93":{"tf":1.7320508075688772},"94":{"tf":1.0},"95":{"tf":2.23606797749979},"97":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"720":{"tf":1.0},"724":{"tf":1.0}}}}}}}},"v":{"df":3,"docs":{"45":{"tf":1.0},"53":{"tf":1.4142135623730951},"725":{"tf":1.0}}}},"m":{"b":{"df":1,"docs":{"438":{"tf":1.0}},"e":{"d":{"df":1,"docs":{"345":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":5,"docs":{"138":{"tf":1.0},"354":{"tf":1.0},"375":{"tf":1.0},"54":{"tf":1.0},"973":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"72":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.7320508075688772}}}},"p":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"935":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"r":{"df":6,"docs":{"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.4142135623730951},"576":{"tf":1.0},"777":{"tf":1.0}}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":4,"docs":{"351":{"tf":1.0},"723":{"tf":1.0},"876":{"tf":1.0},"968":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"799":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":8,"docs":{"208":{"tf":2.0},"522":{"tf":1.0},"525":{"tf":1.4142135623730951},"564":{"tf":1.0},"633":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"992":{"tf":1.0}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":52,"docs":{"1015":{"tf":1.0},"112":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":2.0},"128":{"tf":1.0},"137":{"tf":1.0},"139":{"tf":1.0},"154":{"tf":1.4142135623730951},"172":{"tf":1.0},"177":{"tf":1.0},"203":{"tf":1.0},"22":{"tf":1.0},"348":{"tf":1.0},"38":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":2.449489742783178},"446":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"50":{"tf":1.0},"500":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.7320508075688772},"696":{"tf":1.0},"697":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.7320508075688772},"783":{"tf":1.0},"786":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.4142135623730951},"83":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.4142135623730951},"958":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}},"c":{"df":0,"docs":{},"t":{"df":16,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"204":{"tf":1.0},"216":{"tf":1.0},"440":{"tf":1.4142135623730951},"461":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"73":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"21":{"tf":1.0},"33":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"v":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"o":{"d":{"df":36,"docs":{"164":{"tf":1.0},"165":{"tf":1.0},"166":{"tf":1.4142135623730951},"170":{"tf":3.1622776601683795},"171":{"tf":2.0},"22":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"333":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.7320508075688772},"455":{"tf":2.23606797749979},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":2.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.7320508075688772},"520":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"588":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":2.0},"786":{"tf":1.4142135623730951}},"e":{"(":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"s":{"df":1,"docs":{"349":{"tf":1.0}}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":8,"docs":{"311":{"tf":2.0},"312":{"tf":1.7320508075688772},"313":{"tf":1.7320508075688772},"314":{"tf":2.0},"315":{"tf":2.449489742783178},"316":{"tf":1.7320508075688772},"319":{"tf":1.0},"321":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"315":{"tf":1.0}}},".":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"321":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"347":{"tf":1.0},"778":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"250":{"tf":1.0},"323":{"tf":1.0},"895":{"tf":1.0},"898":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":9,"docs":{"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"761":{"tf":1.0},"895":{"tf":1.0}}}},"df":0,"docs":{}}}}},"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.7320508075688772}}}}}}},"df":35,"docs":{"1011":{"tf":1.0},"126":{"tf":2.449489742783178},"131":{"tf":1.0},"187":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":2.6457513110645907},"207":{"tf":2.449489742783178},"208":{"tf":4.898979485566356},"22":{"tf":1.0},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"40":{"tf":1.0},"435":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"525":{"tf":1.0},"544":{"tf":1.0},"551":{"tf":1.0},"57":{"tf":1.0},"633":{"tf":1.0},"653":{"tf":1.0},"670":{"tf":1.0},"72":{"tf":1.0},"750":{"tf":1.0},"776":{"tf":1.4142135623730951},"797":{"tf":1.0},"846":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"886":{"tf":1.0},"902":{"tf":1.0},"912":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}},"e":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"267":{"tf":1.0},"374":{"tf":1.0}}}}}}},"df":0,"docs":{}},"i":{"a":{"df":0,"docs":{},"n":{"df":4,"docs":{"252":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"735":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"848":{"tf":1.0}}}}},"s":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"35":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"577":{"tf":1.0}}}},"{":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"741":{"tf":1.0}}}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"c":{"df":11,"docs":{"100":{"tf":1.0},"284":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"481":{"tf":1.4142135623730951},"491":{"tf":1.0},"605":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.0},"828":{"tf":1.4142135623730951},"855":{"tf":1.0}}},"df":0,"docs":{}}}},"g":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":6,"docs":{"201":{"tf":1.0},"358":{"tf":1.0},"470":{"tf":1.4142135623730951},"479":{"tf":1.0},"774":{"tf":1.0},"934":{"tf":1.0}}}}},"h":{"a":{"c":{"df":1,"docs":{"551":{"tf":1.0}}},"df":0,"docs":{},"n":{"c":{"df":30,"docs":{"140":{"tf":1.0},"188":{"tf":1.0},"365":{"tf":1.0},"40":{"tf":1.0},"410":{"tf":1.4142135623730951},"414":{"tf":1.0},"416":{"tf":1.0},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"55":{"tf":1.0},"560":{"tf":1.0},"564":{"tf":1.0},"602":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"617":{"tf":1.0},"705":{"tf":1.0},"778":{"tf":1.0},"784":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"878":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":33,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"126":{"tf":1.0},"15":{"tf":1.0},"156":{"tf":1.0},"178":{"tf":1.0},"232":{"tf":1.0},"261":{"tf":1.0},"388":{"tf":1.0},"39":{"tf":1.0},"436":{"tf":1.0},"511":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.4142135623730951},"577":{"tf":1.4142135623730951},"619":{"tf":1.4142135623730951},"69":{"tf":1.0},"724":{"tf":1.0},"797":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0},"849":{"tf":1.0},"863":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"928":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"979":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"412":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"388":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":93,"docs":{"111":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.4142135623730951},"140":{"tf":1.0},"142":{"tf":1.4142135623730951},"154":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"175":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"206":{"tf":1.4142135623730951},"212":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"230":{"tf":1.0},"234":{"tf":1.7320508075688772},"237":{"tf":1.0},"239":{"tf":1.0},"24":{"tf":1.4142135623730951},"26":{"tf":1.0},"28":{"tf":1.0},"284":{"tf":1.4142135623730951},"290":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"304":{"tf":1.0},"323":{"tf":1.0},"324":{"tf":1.0},"325":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"346":{"tf":1.4142135623730951},"354":{"tf":1.0},"376":{"tf":1.0},"380":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"45":{"tf":1.4142135623730951},"452":{"tf":1.0},"453":{"tf":1.0},"457":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"47":{"tf":1.4142135623730951},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"591":{"tf":1.0},"593":{"tf":1.0},"633":{"tf":1.0},"639":{"tf":1.0},"644":{"tf":1.0},"67":{"tf":1.0},"694":{"tf":1.0},"711":{"tf":1.0},"742":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"772":{"tf":1.0},"776":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"816":{"tf":1.4142135623730951},"819":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":2.6457513110645907},"881":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.7320508075688772},"964":{"tf":1.0},"970":{"tf":1.0},"972":{"tf":1.0},"994":{"tf":1.0}},"e":{"!":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"1004":{"tf":1.0},"52":{"tf":1.0},"568":{"tf":1.0}}}},"i":{"df":0,"docs":{},"r":{"df":24,"docs":{"163":{"tf":1.0},"205":{"tf":2.0},"255":{"tf":1.0},"261":{"tf":1.0},"335":{"tf":1.0},"376":{"tf":1.4142135623730951},"432":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.0},"511":{"tf":1.0},"60":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.4142135623730951},"799":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.4142135623730951},"832":{"tf":1.0},"844":{"tf":1.0},"990":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"6":{"tf":1.0},"619":{"tf":1.0},"653":{"tf":1.4142135623730951}}}}}},"t":{"df":0,"docs":{},"i":{"df":9,"docs":{"185":{"tf":1.0},"3":{"tf":1.0},"5":{"tf":2.449489742783178},"515":{"tf":1.0},"565":{"tf":1.4142135623730951},"577":{"tf":1.0},"6":{"tf":1.0},"843":{"tf":1.0},"874":{"tf":1.7320508075688772}}},"l":{"df":2,"docs":{"848":{"tf":1.0},"907":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"416":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":24,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"208":{"tf":1.4142135623730951},"24":{"tf":1.7320508075688772},"25":{"tf":1.0},"255":{"tf":1.0},"284":{"tf":1.0},"343":{"tf":1.7320508075688772},"344":{"tf":2.449489742783178},"345":{"tf":2.0},"349":{"tf":2.0},"350":{"tf":1.4142135623730951},"410":{"tf":1.0},"411":{"tf":1.0},"416":{"tf":1.0},"505":{"tf":1.0},"519":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"778":{"tf":1.0},"992":{"tf":1.4142135623730951}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":3,"docs":{"350":{"tf":1.0},"46":{"tf":1.0},"51":{"tf":1.0}}}}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"976":{"tf":1.0}}}}}}}}}},"u":{"df":0,"docs":{},"m":{"df":20,"docs":{"208":{"tf":1.4142135623730951},"22":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.0},"280":{"tf":1.0},"284":{"tf":1.0},"288":{"tf":1.0},"439":{"tf":1.0},"517":{"tf":1.7320508075688772},"520":{"tf":1.7320508075688772},"522":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"602":{"tf":1.0},"61":{"tf":1.0},"633":{"tf":1.4142135623730951},"668":{"tf":2.0},"7":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.0},"879":{"tf":2.23606797749979}},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"522":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"522":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}}}}},"df":5,"docs":{"522":{"tf":2.23606797749979},"524":{"tf":1.0},"525":{"tf":1.0},"668":{"tf":1.0},"735":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":2,"docs":{"346":{"tf":1.7320508075688772},"885":{"tf":1.0}},"e":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":1,"docs":{"347":{"tf":1.0}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"142":{"tf":1.0},"26":{"tf":1.4142135623730951},"362":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}}}}},"s":{"df":4,"docs":{"203":{"tf":1.0},"216":{"tf":1.0},"48":{"tf":1.0},"54":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"843":{"tf":1.0}}}}}},"o":{"c":{"df":0,"docs":{},"h":{"'":{"df":7,"docs":{"323":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.7320508075688772},"349":{"tf":1.0}}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"348":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"342":{"tf":1.4142135623730951}}}}}}}}},"df":18,"docs":{"322":{"tf":1.0},"335":{"tf":1.7320508075688772},"336":{"tf":1.0},"338":{"tf":1.4142135623730951},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":2.23606797749979},"344":{"tf":3.0},"345":{"tf":3.1622776601683795},"346":{"tf":3.4641016151377544},"347":{"tf":2.0},"348":{"tf":1.7320508075688772},"349":{"tf":2.0},"350":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":2.0},"722":{"tf":1.0}}}},"df":0,"docs":{}}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":29,"docs":{"205":{"tf":3.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"221":{"tf":1.0},"252":{"tf":1.7320508075688772},"253":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.0},"439":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"569":{"tf":1.0},"575":{"tf":1.0},"636":{"tf":1.0},"735":{"tf":2.0},"739":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"777":{"tf":1.0},"829":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.7320508075688772},"895":{"tf":1.0}}},"t":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"723":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"776":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"205":{"tf":1.0},"485":{"tf":1.0},"5":{"tf":1.4142135623730951},"609":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.0}}}},"df":0,"docs":{},"o":{"c":{"df":2,"docs":{"372":{"tf":1.0},"721":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"r":{"a":{"df":8,"docs":{"375":{"tf":1.0},"517":{"tf":1.0},"568":{"tf":2.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.0},"571":{"tf":1.0},"931":{"tf":1.4142135623730951},"932":{"tf":2.6457513110645907}},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"931":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"s":{"df":1,"docs":{"833":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":7,"docs":{"430":{"tf":1.0},"435":{"tf":2.0},"436":{"tf":1.7320508075688772},"437":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"444":{"tf":1.0},"634":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"634":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"c":{"2":{"0":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":173,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.0},"1002":{"tf":1.4142135623730951},"1007":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1011":{"tf":1.0},"103":{"tf":1.0},"106":{"tf":1.4142135623730951},"116":{"tf":1.0},"118":{"tf":1.0},"12":{"tf":1.0},"122":{"tf":1.4142135623730951},"129":{"tf":1.0},"131":{"tf":1.0},"136":{"tf":1.4142135623730951},"143":{"tf":1.0},"145":{"tf":1.0},"150":{"tf":1.4142135623730951},"157":{"tf":1.0},"159":{"tf":1.0},"164":{"tf":1.4142135623730951},"17":{"tf":1.4142135623730951},"175":{"tf":1.0},"177":{"tf":1.0},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.0},"191":{"tf":1.0},"195":{"tf":1.0},"210":{"tf":1.0},"215":{"tf":1.0},"224":{"tf":1.0},"229":{"tf":1.4142135623730951},"238":{"tf":1.0},"240":{"tf":1.0},"247":{"tf":1.4142135623730951},"256":{"tf":1.0},"258":{"tf":1.0},"268":{"tf":1.0},"276":{"tf":1.0},"279":{"tf":1.4142135623730951},"287":{"tf":1.0},"289":{"tf":1.4142135623730951},"294":{"tf":1.0},"306":{"tf":1.0},"31":{"tf":1.0},"311":{"tf":1.0},"318":{"tf":1.0},"322":{"tf":1.4142135623730951},"33":{"tf":1.0},"355":{"tf":1.0},"357":{"tf":1.0},"366":{"tf":1.4142135623730951},"379":{"tf":1.0},"381":{"tf":1.4142135623730951},"386":{"tf":1.4142135623730951},"393":{"tf":1.0},"395":{"tf":1.0},"400":{"tf":1.4142135623730951},"405":{"tf":1.0},"407":{"tf":1.0},"410":{"tf":1.4142135623730951},"421":{"tf":1.0},"423":{"tf":1.0},"430":{"tf":1.4142135623730951},"443":{"tf":1.0},"445":{"tf":1.0},"451":{"tf":1.4142135623730951},"456":{"tf":1.0},"458":{"tf":1.0},"460":{"tf":1.0},"465":{"tf":1.4142135623730951},"475":{"tf":1.0},"477":{"tf":1.0},"481":{"tf":1.4142135623730951},"488":{"tf":1.0},"490":{"tf":1.0},"495":{"tf":1.4142135623730951},"506":{"tf":1.0},"508":{"tf":1.0},"513":{"tf":1.4142135623730951},"529":{"tf":1.0},"531":{"tf":1.0},"535":{"tf":1.4142135623730951},"542":{"tf":1.0},"544":{"tf":1.0},"549":{"tf":1.4142135623730951},"556":{"tf":1.0},"558":{"tf":1.0},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"579":{"tf":1.0},"581":{"tf":1.4142135623730951},"584":{"tf":1.4142135623730951},"591":{"tf":1.0},"593":{"tf":1.0},"598":{"tf":1.4142135623730951},"606":{"tf":1.0},"608":{"tf":1.0},"613":{"tf":1.4142135623730951},"620":{"tf":1.0},"622":{"tf":1.4142135623730951},"627":{"tf":1.0},"641":{"tf":1.0},"649":{"tf":1.4142135623730951},"657":{"tf":1.0},"659":{"tf":1.0},"663":{"tf":1.4142135623730951},"664":{"tf":1.4142135623730951},"671":{"tf":1.0},"673":{"tf":1.0},"678":{"tf":1.4142135623730951},"685":{"tf":1.0},"687":{"tf":1.4142135623730951},"692":{"tf":1.4142135623730951},"70":{"tf":1.0},"700":{"tf":1.0},"702":{"tf":1.0},"704":{"tf":1.4142135623730951},"709":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"757":{"tf":1.4142135623730951},"764":{"tf":1.0},"766":{"tf":1.0},"782":{"tf":1.4142135623730951},"789":{"tf":1.0},"79":{"tf":1.4142135623730951},"791":{"tf":1.4142135623730951},"795":{"tf":1.4142135623730951},"8":{"tf":1.0},"802":{"tf":1.0},"804":{"tf":1.0},"808":{"tf":1.4142135623730951},"820":{"tf":1.0},"822":{"tf":1.0},"827":{"tf":1.4142135623730951},"834":{"tf":1.0},"836":{"tf":1.0},"841":{"tf":1.4142135623730951},"851":{"tf":1.0},"853":{"tf":1.0},"857":{"tf":1.4142135623730951},"86":{"tf":1.0},"865":{"tf":1.0},"867":{"tf":1.0},"871":{"tf":1.4142135623730951},"88":{"tf":1.0},"884":{"tf":1.0},"886":{"tf":1.4142135623730951},"891":{"tf":1.4142135623730951},"901":{"tf":1.0},"903":{"tf":1.4142135623730951},"908":{"tf":1.4142135623730951},"918":{"tf":1.0},"920":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.4142135623730951},"93":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951},"940":{"tf":1.4142135623730951},"950":{"tf":1.0},"952":{"tf":1.0},"957":{"tf":1.4142135623730951},"967":{"tf":1.0},"969":{"tf":1.0},"974":{"tf":1.4142135623730951},"981":{"tf":1.0},"983":{"tf":1.4142135623730951},"988":{"tf":1.4142135623730951},"995":{"tf":1.0},"997":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":12,"docs":{"440":{"tf":1.0},"497":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":4.242640687119285},"833":{"tf":1.0},"879":{"tf":4.123105625617661},"881":{"tf":1.4142135623730951},"895":{"tf":1.0},"898":{"tf":1.4142135623730951},"941":{"tf":1.0},"944":{"tf":1.0},"952":{"tf":1.0}}}}}},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"723":{"tf":1.0},"777":{"tf":1.0},"810":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"56":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":11,"docs":{"124":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"372":{"tf":1.0},"507":{"tf":1.0},"577":{"tf":1.0},"60":{"tf":1.0},"72":{"tf":1.0},"749":{"tf":1.0},"803":{"tf":1.0},"880":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"567":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"201":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":6,"docs":{"24":{"tf":1.4142135623730951},"371":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"575":{"tf":1.0},"720":{"tf":1.0}}}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":10,"docs":{"28":{"tf":1.0},"722":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":1.0},"847":{"tf":1.4142135623730951},"912":{"tf":1.0},"961":{"tf":1.0}}}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"436":{"tf":1.0},"570":{"tf":1.0}}}}}},"t":{"a":{"_":{"3":{"df":2,"docs":{"46":{"tf":1.0},"51":{"tf":1.0}}},"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"u":{"df":1,"docs":{"723":{"tf":1.4142135623730951}}},"v":{"df":1,"docs":{"723":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"c":{"df":14,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"18":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"376":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"522":{"tf":1.0},"534":{"tf":1.4142135623730951},"761":{"tf":1.0},"804":{"tf":1.0},"855":{"tf":1.0}}},"df":0,"docs":{},"h":{"df":5,"docs":{"39":{"tf":1.4142135623730951},"48":{"tf":1.0},"50":{"tf":1.0},"52":{"tf":1.0},"699":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"46":{"tf":1.0}}},"df":10,"docs":{"364":{"tf":1.0},"38":{"tf":2.23606797749979},"39":{"tf":1.0},"49":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"55":{"tf":1.0},"583":{"tf":1.0},"697":{"tf":1.4142135623730951},"699":{"tf":1.4142135623730951}},"’":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}}}}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":2,"docs":{"1004":{"tf":1.0},"246":{"tf":1.0}}}},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"270":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"745":{"tf":1.0}}}}},"n":{"df":42,"docs":{"155":{"tf":1.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"385":{"tf":1.0},"437":{"tf":1.0},"500":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"565":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"659":{"tf":1.0},"693":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":2.6457513110645907},"761":{"tf":1.4142135623730951},"763":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":1.0},"81":{"tf":1.0},"818":{"tf":1.4142135623730951},"837":{"tf":1.4142135623730951},"874":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0},"990":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"430":{"tf":1.0},"432":{"tf":1.0}}}},"t":{"df":13,"docs":{"374":{"tf":1.0},"450":{"tf":1.0},"453":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":2.23606797749979},"72":{"tf":1.0},"799":{"tf":1.4142135623730951},"832":{"tf":1.4142135623730951},"912":{"tf":1.0},"928":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"952":{"tf":1.0}},"u":{"df":6,"docs":{"169":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.4142135623730951},"282":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"249":{"tf":1.0},"528":{"tf":1.0},"570":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":4,"docs":{"499":{"tf":1.0},"840":{"tf":1.0},"848":{"tf":1.0},"933":{"tf":1.0}}}}}}},"i":{"d":{"df":1,"docs":{"913":{"tf":1.0}}},"df":0,"docs":{}},"m":{"df":2,"docs":{"959":{"tf":1.0},"971":{"tf":1.0}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":1,"docs":{"373":{"tf":1.0}}}}}},"x":{"a":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"293":{"tf":1.0},"402":{"tf":1.0},"62":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"784":{"tf":1.0},"874":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.0},"207":{"tf":1.0},"303":{"tf":1.0},"732":{"tf":1.0},"878":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"147":{"tf":1.0},"33":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":71,"docs":{"1014":{"tf":1.0},"155":{"tf":1.4142135623730951},"169":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"303":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.4142135623730951},"375":{"tf":1.0},"376":{"tf":1.0},"384":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"517":{"tf":1.0},"521":{"tf":1.4142135623730951},"523":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.4142135623730951},"575":{"tf":1.0},"586":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":1.0},"633":{"tf":1.7320508075688772},"649":{"tf":1.0},"650":{"tf":1.0},"654":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.4142135623730951},"697":{"tf":1.0},"699":{"tf":1.0},"727":{"tf":1.0},"732":{"tf":1.4142135623730951},"741":{"tf":1.0},"752":{"tf":1.7320508075688772},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"847":{"tf":1.0},"876":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"933":{"tf":1.7320508075688772},"95":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0},"996":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"df":10,"docs":{"111":{"tf":1.0},"47":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"879":{"tf":2.6457513110645907}},"e":{"d":{"df":2,"docs":{"30":{"tf":1.0},"990":{"tf":1.0}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"t":{"df":11,"docs":{"205":{"tf":1.0},"331":{"tf":1.0},"45":{"tf":1.0},"499":{"tf":1.0},"711":{"tf":1.0},"718":{"tf":1.0},"725":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.7320508075688772},"8":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"429":{"tf":1.0}}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":5,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"565":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"l":{"df":0,"docs":{},"u":{"d":{"df":2,"docs":{"722":{"tf":1.4142135623730951},"735":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"84":{"tf":1.0},"917":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":45,"docs":{"138":{"tf":1.0},"148":{"tf":1.0},"151":{"tf":1.4142135623730951},"17":{"tf":1.0},"22":{"tf":1.4142135623730951},"23":{"tf":1.7320508075688772},"25":{"tf":1.0},"26":{"tf":2.23606797749979},"291":{"tf":1.0},"344":{"tf":2.23606797749979},"346":{"tf":1.0},"352":{"tf":1.0},"368":{"tf":1.4142135623730951},"402":{"tf":1.4142135623730951},"404":{"tf":1.0},"521":{"tf":1.4142135623730951},"564":{"tf":1.0},"6":{"tf":2.0},"600":{"tf":2.23606797749979},"602":{"tf":2.8284271247461903},"603":{"tf":2.23606797749979},"605":{"tf":1.4142135623730951},"615":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"634":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.4142135623730951},"653":{"tf":2.23606797749979},"654":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.7320508075688772},"665":{"tf":1.0},"694":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":3.7416573867739413},"876":{"tf":1.0},"878":{"tf":2.23606797749979},"879":{"tf":2.23606797749979},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"890":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.7320508075688772},"962":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":3,"docs":{"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"885":{"tf":1.0}}}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}},"y":{"(":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"17":{"tf":1.0},"23":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":2.449489742783178},"666":{"tf":1.0},"705":{"tf":1.0}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"773":{"tf":1.0}}}}},"h":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"1007":{"tf":1.0},"180":{"tf":1.0},"340":{"tf":1.0},"648":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":117,"docs":{"1012":{"tf":1.0},"113":{"tf":1.0},"118":{"tf":1.0},"119":{"tf":1.0},"132":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.4142135623730951},"148":{"tf":1.4142135623730951},"152":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"178":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":2.449489742783178},"208":{"tf":1.0},"216":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.7320508075688772},"241":{"tf":1.0},"246":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"268":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"273":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"317":{"tf":1.0},"319":{"tf":1.0},"32":{"tf":1.0},"34":{"tf":1.0},"367":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"393":{"tf":1.0},"40":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.0},"453":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.0},"483":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"518":{"tf":1.0},"55":{"tf":1.0},"559":{"tf":1.4142135623730951},"564":{"tf":1.0},"568":{"tf":1.0},"575":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":2.23606797749979},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"606":{"tf":1.0},"609":{"tf":1.4142135623730951},"618":{"tf":1.0},"631":{"tf":1.0},"64":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"659":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"714":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"74":{"tf":1.4142135623730951},"757":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"768":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.7320508075688772},"786":{"tf":1.0},"80":{"tf":1.0},"810":{"tf":1.0},"829":{"tf":1.0},"842":{"tf":1.0},"867":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"875":{"tf":2.23606797749979},"879":{"tf":4.47213595499958},"88":{"tf":1.0},"881":{"tf":1.4142135623730951},"887":{"tf":1.4142135623730951},"900":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.4142135623730951},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"936":{"tf":1.0},"938":{"tf":1.0},"944":{"tf":1.0},"949":{"tf":1.0},"953":{"tf":1.4142135623730951},"961":{"tf":1.4142135623730951},"966":{"tf":1.0},"970":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"975":{"tf":1.0},"980":{"tf":1.0},"984":{"tf":1.0},"994":{"tf":1.0}}}},"t":{"df":7,"docs":{"130":{"tf":1.0},"39":{"tf":1.4142135623730951},"40":{"tf":1.0},"42":{"tf":1.0},"52":{"tf":1.0},"55":{"tf":1.0},"577":{"tf":1.0}}}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"569":{"tf":1.0}}}}}},"p":{"a":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"40":{"tf":1.4142135623730951},"847":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":49,"docs":{"124":{"tf":1.0},"130":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.7320508075688772},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"232":{"tf":1.4142135623730951},"254":{"tf":1.4142135623730951},"255":{"tf":1.0},"273":{"tf":1.0},"276":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.4142135623730951},"375":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"485":{"tf":1.0},"515":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"563":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"656":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.4142135623730951},"725":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.4142135623730951},"776":{"tf":1.0},"81":{"tf":1.0},"835":{"tf":1.0},"852":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":1.0},"898":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"951":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"351":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"50":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"196":{"tf":1.0},"200":{"tf":1.0}}}}}}},"df":0,"docs":{},"s":{"df":7,"docs":{"108":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.0},"296":{"tf":1.0},"575":{"tf":1.0},"725":{"tf":1.0},"863":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":17,"docs":{"1007":{"tf":1.0},"118":{"tf":1.0},"17":{"tf":1.0},"29":{"tf":1.0},"290":{"tf":1.0},"306":{"tf":1.0},"33":{"tf":1.0},"371":{"tf":1.0},"40":{"tf":1.0},"423":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"700":{"tf":1.0},"784":{"tf":1.4142135623730951},"799":{"tf":1.0},"8":{"tf":1.0},"928":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"199":{"tf":1.0},"778":{"tf":1.0},"843":{"tf":1.0},"928":{"tf":1.0}}}}}}},"t":{"df":2,"docs":{"53":{"tf":1.4142135623730951},"939":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"r":{"df":5,"docs":{"203":{"tf":1.0},"205":{"tf":1.0},"302":{"tf":1.0},"944":{"tf":1.4142135623730951},"947":{"tf":1.0}},"e":{"_":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}}},"df":0,"docs":{}},"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"s":{"(":{"3":{"6":{"df":0,"docs":{},"h":{"df":1,"docs":{"551":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":3,"docs":{"198":{"tf":1.0},"880":{"tf":1.0},"890":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":7,"docs":{"204":{"tf":1.0},"417":{"tf":1.0},"455":{"tf":1.4142135623730951},"467":{"tf":1.0},"485":{"tf":1.0},"519":{"tf":1.0},"874":{"tf":1.0}}}},"n":{"df":126,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1006":{"tf":1.7320508075688772},"106":{"tf":1.0},"110":{"tf":1.0},"122":{"tf":1.0},"126":{"tf":1.0},"136":{"tf":1.0},"140":{"tf":1.0},"150":{"tf":1.0},"154":{"tf":1.0},"164":{"tf":1.0},"168":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"186":{"tf":1.0},"195":{"tf":1.0},"202":{"tf":1.0},"21":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"229":{"tf":1.0},"234":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"255":{"tf":1.0},"263":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"272":{"tf":1.0},"279":{"tf":1.0},"283":{"tf":1.0},"294":{"tf":1.0},"299":{"tf":1.0},"311":{"tf":1.0},"315":{"tf":1.0},"340":{"tf":1.4142135623730951},"366":{"tf":1.0},"370":{"tf":1.0},"386":{"tf":1.0},"390":{"tf":1.0},"400":{"tf":1.0},"404":{"tf":1.0},"410":{"tf":1.0},"415":{"tf":1.0},"430":{"tf":1.0},"434":{"tf":1.0},"451":{"tf":1.0},"455":{"tf":1.0},"465":{"tf":1.0},"469":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.0},"495":{"tf":1.0},"499":{"tf":1.0},"5":{"tf":1.0},"505":{"tf":1.0},"513":{"tf":1.0},"519":{"tf":1.0},"535":{"tf":1.0},"539":{"tf":1.4142135623730951},"549":{"tf":1.0},"553":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.0},"584":{"tf":1.0},"588":{"tf":1.0},"598":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"613":{"tf":1.0},"617":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.0},"649":{"tf":1.0},"653":{"tf":1.0},"664":{"tf":1.0},"668":{"tf":1.0},"678":{"tf":1.0},"682":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":1.0},"709":{"tf":1.0},"719":{"tf":1.0},"730":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":1.0},"741":{"tf":1.0},"746":{"tf":1.0},"757":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":1.0},"782":{"tf":1.0},"786":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"799":{"tf":1.0},"808":{"tf":1.0},"813":{"tf":1.0},"827":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"841":{"tf":1.0},"845":{"tf":1.0},"857":{"tf":1.0},"860":{"tf":1.0},"871":{"tf":1.0},"878":{"tf":1.0},"891":{"tf":1.0},"898":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"930":{"tf":1.0},"940":{"tf":1.0},"944":{"tf":1.0},"957":{"tf":1.0},"961":{"tf":1.0},"97":{"tf":1.0},"974":{"tf":1.0},"978":{"tf":1.0},"988":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"655":{"tf":1.0},"878":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"222":{"tf":1.0},"295":{"tf":1.0},"302":{"tf":1.0},"345":{"tf":1.0},"440":{"tf":1.0},"51":{"tf":1.0},"609":{"tf":1.0},"698":{"tf":1.0}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":4,"docs":{"127":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0}}}},"r":{"df":11,"docs":{"1015":{"tf":1.0},"152":{"tf":1.4142135623730951},"28":{"tf":1.0},"340":{"tf":1.0},"369":{"tf":1.0},"388":{"tf":1.0},"630":{"tf":1.0},"810":{"tf":1.0},"938":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0}}},"s":{"df":1,"docs":{"779":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"428":{"tf":1.0},"749":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"t":{"df":5,"docs":{"23":{"tf":1.0},"25":{"tf":1.0},"45":{"tf":1.4142135623730951},"455":{"tf":1.0},"725":{"tf":1.0}}}},"s":{"df":24,"docs":{"1009":{"tf":1.0},"1011":{"tf":1.0},"131":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"33":{"tf":1.0},"362":{"tf":1.7320508075688772},"379":{"tf":1.0},"395":{"tf":1.0},"404":{"tf":1.0},"514":{"tf":1.0},"606":{"tf":1.0},"634":{"tf":1.0},"736":{"tf":1.0},"773":{"tf":1.0},"814":{"tf":1.0},"902":{"tf":1.0},"917":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"573":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":11,"docs":{"269":{"tf":1.0},"270":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"414":{"tf":1.0},"522":{"tf":2.0},"568":{"tf":1.0},"576":{"tf":1.0},"735":{"tf":1.7320508075688772},"780":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"85":{"tf":1.0}}}}}}}}},"t":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":2,"docs":{"732":{"tf":1.4142135623730951},"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"_":{"*":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"d":{"2":{"5":{"5":{"1":{"9":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"p":{"2":{"5":{"6":{"df":0,"docs":{},"k":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"r":{"2":{"5":{"5":{"1":{"9":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"4":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"_":{"1":{"2":{"8":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"1":{"2":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"h":{"a":{"2":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"_":{"1":{"2":{"8":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"732":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"4":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"83":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"/":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"_":{"df":1,"docs":{"739":{"tf":1.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"a":{"d":{"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"w":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}}},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"739":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"p":{"2":{"5":{"6":{"df":0,"docs":{},"r":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"97":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":3,"docs":{"739":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"404":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":16,"docs":{"126":{"tf":1.0},"156":{"tf":1.0},"19":{"tf":1.0},"248":{"tf":1.0},"38":{"tf":1.0},"496":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"586":{"tf":1.4142135623730951},"631":{"tf":1.0},"778":{"tf":1.0},"942":{"tf":1.0},"966":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":34,"docs":{"124":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":2.449489742783178},"17":{"tf":1.0},"170":{"tf":3.0},"171":{"tf":3.4641016151377544},"177":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.4142135623730951},"24":{"tf":4.123105625617661},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"289":{"tf":1.0},"30":{"tf":1.0},"308":{"tf":1.0},"340":{"tf":1.0},"442":{"tf":1.0},"516":{"tf":1.0},"518":{"tf":1.0},"521":{"tf":2.8284271247461903},"537":{"tf":2.23606797749979},"563":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.7320508075688772},"584":{"tf":1.7320508075688772},"585":{"tf":1.0},"586":{"tf":2.8284271247461903},"588":{"tf":2.6457513110645907},"591":{"tf":1.0},"648":{"tf":1.0},"780":{"tf":1.0},"83":{"tf":1.0},"939":{"tf":1.0},"945":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{">":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{">":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"24":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"24":{"tf":1.0}}}}}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":2,"docs":{"170":{"tf":1.0},"171":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":2,"docs":{"22":{"tf":1.0},"24":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":2.6457513110645907}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"t":{"df":2,"docs":{"648":{"tf":1.0},"913":{"tf":1.0}}}},"r":{"df":0,"docs":{},"n":{"df":10,"docs":{"211":{"tf":1.0},"25":{"tf":1.4142135623730951},"267":{"tf":1.0},"315":{"tf":1.0},"429":{"tf":1.0},"438":{"tf":1.0},"49":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"956":{"tf":1.0},"973":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":4,"docs":{"333":{"tf":1.0},"350":{"tf":1.4142135623730951},"418":{"tf":1.0},"485":{"tf":1.0}}}},"df":25,"docs":{"152":{"tf":1.0},"166":{"tf":1.0},"249":{"tf":1.4142135623730951},"340":{"tf":1.0},"341":{"tf":2.6457513110645907},"346":{"tf":2.0},"347":{"tf":1.0},"516":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"634":{"tf":1.0},"651":{"tf":1.0},"700":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.4142135623730951},"803":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"751":{"tf":1.4142135623730951},"778":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":63,"docs":{"164":{"tf":2.0},"165":{"tf":1.0},"166":{"tf":2.0},"169":{"tf":1.4142135623730951},"170":{"tf":2.6457513110645907},"171":{"tf":1.0},"172":{"tf":2.23606797749979},"173":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.0},"179":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.4142135623730951},"181":{"tf":1.4142135623730951},"24":{"tf":1.0},"284":{"tf":1.4142135623730951},"346":{"tf":1.0},"362":{"tf":1.0},"387":{"tf":1.4142135623730951},"388":{"tf":3.4641016151377544},"390":{"tf":2.23606797749979},"402":{"tf":1.7320508075688772},"440":{"tf":1.0},"45":{"tf":2.449489742783178},"513":{"tf":1.7320508075688772},"516":{"tf":1.7320508075688772},"517":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"520":{"tf":1.0},"521":{"tf":3.4641016151377544},"522":{"tf":1.7320508075688772},"523":{"tf":2.449489742783178},"526":{"tf":2.449489742783178},"535":{"tf":2.0},"536":{"tf":1.0},"537":{"tf":3.0},"539":{"tf":2.6457513110645907},"540":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.4142135623730951},"585":{"tf":1.0},"586":{"tf":2.23606797749979},"588":{"tf":2.23606797749979},"594":{"tf":1.4142135623730951},"61":{"tf":1.0},"799":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.23606797749979},"895":{"tf":1.0},"898":{"tf":1.0}},"i":{"c":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"170":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"284":{"tf":2.23606797749979},"292":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":5,"docs":{"180":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.0},"523":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}},"f":{"+":{"1":{"df":3,"docs":{"436":{"tf":1.0},"717":{"tf":1.4142135623730951},"722":{"tf":2.0}}},"df":0,"docs":{}},"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"c":{"a":{"d":{"df":1,"docs":{"3":{"tf":1.0}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"782":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":4,"docs":{"231":{"tf":1.0},"569":{"tf":1.0},"723":{"tf":1.0},"913":{"tf":1.0}},"t":{"df":1,"docs":{"95":{"tf":1.0}}}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"78":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":18,"docs":{"137":{"tf":1.0},"19":{"tf":1.0},"200":{"tf":1.4142135623730951},"205":{"tf":1.0},"326":{"tf":1.0},"33":{"tf":1.0},"363":{"tf":1.0},"414":{"tf":1.0},"776":{"tf":1.0},"83":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"849":{"tf":1.4142135623730951},"855":{"tf":1.0},"87":{"tf":1.0},"872":{"tf":1.0},"959":{"tf":1.0},"969":{"tf":1.0}}}}}},"t":{"df":8,"docs":{"15":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0},"559":{"tf":1.0},"577":{"tf":1.0},"722":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0}},"o":{"df":3,"docs":{"600":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0}},"r":{"(":{"(":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"207":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"207":{"tf":1.0}}}},"df":17,"docs":{"207":{"tf":2.6457513110645907},"221":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"469":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.4142135623730951},"81":{"tf":1.0},"928":{"tf":1.0},"95":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":20,"docs":{"125":{"tf":1.0},"126":{"tf":2.449489742783178},"160":{"tf":1.0},"347":{"tf":1.0},"436":{"tf":1.0},"461":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"609":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"653":{"tf":1.0},"75":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"879":{"tf":2.0},"898":{"tf":1.7320508075688772},"913":{"tf":1.0},"934":{"tf":1.0},"947":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"126":{"tf":1.0},"615":{"tf":1.0},"735":{"tf":3.1622776601683795}}}}},"r":{"df":4,"docs":{"432":{"tf":1.0},"575":{"tf":1.0},"772":{"tf":1.4142135623730951},"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"431":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"514":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"348":{"tf":1.0},"349":{"tf":1.0},"436":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":4,"docs":{"207":{"tf":1.0},"437":{"tf":1.4142135623730951},"615":{"tf":1.0},"747":{"tf":1.0}}},"s":{"df":5,"docs":{"698":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"761":{"tf":2.0},"97":{"tf":1.0}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":5,"docs":{"261":{"tf":1.0},"456":{"tf":1.0},"511":{"tf":1.0},"53":{"tf":1.0},"569":{"tf":1.0}}}},"df":2,"docs":{"783":{"tf":1.0},"876":{"tf":1.0}}}}}},"r":{"df":11,"docs":{"170":{"tf":1.0},"180":{"tf":1.0},"199":{"tf":1.0},"267":{"tf":1.0},"285":{"tf":1.0},"374":{"tf":1.0},"58":{"tf":1.0},"711":{"tf":1.4142135623730951},"715":{"tf":1.0},"854":{"tf":1.0},"880":{"tf":1.4142135623730951}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"200":{"tf":1.0},"281":{"tf":1.0},"374":{"tf":1.0}}}}}},"t":{"df":2,"docs":{"370":{"tf":1.0},"39":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"551":{"tf":1.0},"574":{"tf":1.0},"711":{"tf":1.0},"739":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"880":{"tf":2.0},"912":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"564":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"213":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"264":{"tf":1.0},"428":{"tf":1.0},"668":{"tf":1.0},"680":{"tf":1.0},"723":{"tf":1.0},"770":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"432":{"tf":1.0},"660":{"tf":1.0}}}}}}},"df":3,"docs":{"112":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951}},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"234":{"tf":1.0}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"781":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"254":{"tf":1.0},"573":{"tf":1.0},"762":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":35,"docs":{"154":{"tf":1.0},"160":{"tf":1.4142135623730951},"166":{"tf":1.0},"18":{"tf":1.4142135623730951},"210":{"tf":1.0},"22":{"tf":1.0},"281":{"tf":1.0},"376":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":2.0},"446":{"tf":1.0},"515":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"56":{"tf":1.4142135623730951},"564":{"tf":1.0},"644":{"tf":2.0},"693":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"74":{"tf":1.0},"776":{"tf":1.0},"833":{"tf":1.0},"847":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0},"856":{"tf":1.4142135623730951},"941":{"tf":1.0},"944":{"tf":1.4142135623730951},"945":{"tf":1.0},"95":{"tf":1.0},"951":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"990":{"tf":1.0}}}}}},"b":{"df":1,"docs":{"891":{"tf":1.0}},"r":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"513":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0}}}}},"df":0,"docs":{}}}},"d":{"df":1,"docs":{"933":{"tf":1.0}}},"df":0,"docs":{},"e":{"d":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":10,"docs":{"206":{"tf":1.0},"229":{"tf":1.0},"244":{"tf":1.0},"272":{"tf":1.0},"797":{"tf":1.4142135623730951},"846":{"tf":1.0},"870":{"tf":1.0},"878":{"tf":1.0},"952":{"tf":1.0},"973":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":35,"docs":{"18":{"tf":1.4142135623730951},"267":{"tf":1.0},"48":{"tf":1.4142135623730951},"534":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"576":{"tf":2.449489742783178},"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.7320508075688772},"605":{"tf":1.0},"649":{"tf":1.7320508075688772},"650":{"tf":2.6457513110645907},"651":{"tf":3.3166247903554},"653":{"tf":3.4641016151377544},"656":{"tf":1.0},"658":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.0},"663":{"tf":1.0},"666":{"tf":1.0},"696":{"tf":1.0},"78":{"tf":1.0},"797":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"912":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0},"974":{"tf":1.4142135623730951},"975":{"tf":1.4142135623730951},"976":{"tf":1.7320508075688772},"978":{"tf":1.0},"987":{"tf":1.4142135623730951}},"l":{"df":5,"docs":{"390":{"tf":1.0},"397":{"tf":1.0},"720":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.4142135623730951}}},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"974":{"tf":1.0},"975":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}},"o":{"df":0,"docs":{},"w":{"df":6,"docs":{"113":{"tf":1.0},"219":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"582":{"tf":1.0},"935":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"c":{"df":1,"docs":{"0":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"9":{"df":1,"docs":{"388":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"4":{"df":1,"docs":{"840":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"m":{"df":5,"docs":{"661":{"tf":1.0},"665":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"985":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"(":{"df":1,"docs":{"270":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"849":{"tf":1.0}}}}}}}}}},"df":43,"docs":{"0":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"109":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.4142135623730951},"193":{"tf":1.0},"201":{"tf":1.0},"269":{"tf":1.4142135623730951},"270":{"tf":2.0},"271":{"tf":1.0},"272":{"tf":2.0},"273":{"tf":2.0},"277":{"tf":1.0},"3":{"tf":1.0},"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.4142135623730951},"316":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"389":{"tf":1.0},"465":{"tf":1.7320508075688772},"466":{"tf":1.0},"467":{"tf":1.4142135623730951},"468":{"tf":1.0},"471":{"tf":1.0},"479":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"727":{"tf":1.0},"774":{"tf":1.0},"798":{"tf":1.0},"801":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"850":{"tf":1.0},"932":{"tf":1.0},"985":{"tf":1.0}}}}}}}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":17,"docs":{"191":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":2.23606797749979},"64":{"tf":1.0},"65":{"tf":1.4142135623730951},"67":{"tf":1.7320508075688772},"69":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"w":{"df":12,"docs":{"257":{"tf":1.0},"331":{"tf":1.0},"418":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"517":{"tf":1.0},"565":{"tf":1.4142135623730951},"569":{"tf":1.0},"729":{"tf":1.0},"759":{"tf":1.0},"797":{"tf":1.0},"832":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"346":{"tf":1.0},"912":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"o":{"df":1,"docs":{"95":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":31,"docs":{"180":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.4142135623730951},"221":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.7320508075688772},"331":{"tf":1.0},"346":{"tf":1.0},"387":{"tf":1.4142135623730951},"439":{"tf":1.0},"501":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":3.1622776601683795},"553":{"tf":1.0},"555":{"tf":1.0},"559":{"tf":1.4142135623730951},"6":{"tf":1.0},"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.4142135623730951},"634":{"tf":2.449489742783178},"635":{"tf":1.4142135623730951},"636":{"tf":1.0},"644":{"tf":1.0},"648":{"tf":1.4142135623730951},"717":{"tf":1.0},"761":{"tf":2.0},"895":{"tf":2.6457513110645907},"9":{"tf":1.0}}},"df":0,"docs":{}}},"f":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"199":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"282":{"tf":1.0}}},"l":{"df":4,"docs":{"204":{"tf":1.0},"234":{"tf":1.4142135623730951},"346":{"tf":1.0},"632":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":7,"docs":{"24":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"697":{"tf":1.0},"698":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"890":{"tf":1.0}}}}}},"n":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"a":{"c":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"524":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":41,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.4142135623730951},"130":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":3.605551275463989},"211":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"45":{"tf":1.0},"500":{"tf":2.8284271247461903},"519":{"tf":1.0},"523":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"64":{"tf":1.0},"67":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":2.0},"716":{"tf":1.7320508075688772},"721":{"tf":1.4142135623730951},"725":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"209":{"tf":1.0}}}}},"n":{"c":{"df":3,"docs":{"316":{"tf":1.0},"876":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":4,"docs":{"412":{"tf":1.0},"429":{"tf":1.0},"810":{"tf":1.0},"876":{"tf":1.0}}}},"df":0,"docs":{}}},"d":{"df":17,"docs":{"199":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"435":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"516":{"tf":1.4142135623730951},"553":{"tf":1.7320508075688772},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"743":{"tf":1.0},"858":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":7,"docs":{"428":{"tf":1.0},"440":{"tf":1.0},"567":{"tf":1.0},"645":{"tf":1.0},"773":{"tf":1.0},"848":{"tf":1.0},"874":{"tf":1.4142135623730951}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":9,"docs":{"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"894":{"tf":1.4142135623730951},"895":{"tf":2.449489742783178},"896":{"tf":1.7320508075688772},"897":{"tf":1.4142135623730951},"898":{"tf":2.23606797749979},"900":{"tf":1.0},"902":{"tf":1.0}}}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":8,"docs":{"124":{"tf":1.0},"126":{"tf":1.0},"155":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"735":{"tf":1.0},"777":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"t":{"df":2,"docs":{"199":{"tf":1.0},"517":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":67,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.7320508075688772},"158":{"tf":1.0},"208":{"tf":2.23606797749979},"222":{"tf":1.0},"257":{"tf":1.0},"284":{"tf":1.0},"297":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"343":{"tf":1.4142135623730951},"344":{"tf":2.0},"345":{"tf":2.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"348":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"412":{"tf":1.0},"432":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.4142135623730951},"453":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.4142135623730951},"499":{"tf":1.0},"516":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"537":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"567":{"tf":1.4142135623730951},"571":{"tf":1.0},"576":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.7320508075688772},"63":{"tf":1.0},"632":{"tf":1.0},"64":{"tf":1.0},"643":{"tf":1.0},"668":{"tf":1.0},"67":{"tf":1.0},"697":{"tf":1.4142135623730951},"71":{"tf":1.0},"716":{"tf":1.0},"720":{"tf":1.4142135623730951},"735":{"tf":1.0},"75":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"879":{"tf":1.0},"912":{"tf":1.4142135623730951},"931":{"tf":1.0},"933":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"t":{"df":5,"docs":{"108":{"tf":1.0},"517":{"tf":1.0},"564":{"tf":1.0},"615":{"tf":1.0},"735":{"tf":2.449489742783178}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"235":{"tf":1.0}}}},"x":{"df":17,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"234":{"tf":2.0},"332":{"tf":1.4142135623730951},"438":{"tf":1.0},"500":{"tf":1.0},"522":{"tf":1.4142135623730951},"564":{"tf":1.0},"575":{"tf":1.0},"711":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":2.0}},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"l":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"709":{"tf":1.0},"729":{"tf":1.7320508075688772},"761":{"tf":1.0},"831":{"tf":1.4142135623730951}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"485":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"635":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"29":{"tf":1.0}}}},"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":20,"docs":{"137":{"tf":1.0},"138":{"tf":1.0},"141":{"tf":1.0},"147":{"tf":1.0},"207":{"tf":1.0},"373":{"tf":1.0},"427":{"tf":1.4142135623730951},"537":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"61":{"tf":1.0},"651":{"tf":1.0},"773":{"tf":1.0},"926":{"tf":1.4142135623730951},"932":{"tf":1.0},"939":{"tf":1.4142135623730951},"942":{"tf":1.0},"95":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0}}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"374":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"554":{"tf":1.0}}}}},"p":{"df":1,"docs":{"749":{"tf":1.0}}}},"o":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"346":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}},"w":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":5,"docs":{"17":{"tf":1.0},"26":{"tf":1.0},"267":{"tf":1.0},"618":{"tf":1.0},"983":{"tf":1.0}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"429":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"n":{"df":17,"docs":{"22":{"tf":1.4142135623730951},"221":{"tf":2.0},"222":{"tf":1.4142135623730951},"23":{"tf":1.0},"24":{"tf":2.449489742783178},"25":{"tf":1.4142135623730951},"284":{"tf":1.0},"341":{"tf":2.6457513110645907},"404":{"tf":1.0},"438":{"tf":1.0},"455":{"tf":1.4142135623730951},"524":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"879":{"tf":3.3166247903554},"885":{"tf":1.7320508075688772},"97":{"tf":1.0}}},"o":{"c":{"df":0,"docs":{},"u":{"df":4,"docs":{"363":{"tf":1.0},"40":{"tf":1.0},"469":{"tf":1.0},"725":{"tf":1.0}},"s":{"df":5,"docs":{"16":{"tf":1.0},"325":{"tf":1.0},"45":{"tf":1.0},"564":{"tf":1.0},"818":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":91,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"126":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.7320508075688772},"181":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":1.0},"267":{"tf":1.4142135623730951},"272":{"tf":1.0},"300":{"tf":1.4142135623730951},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"333":{"tf":1.0},"341":{"tf":1.4142135623730951},"345":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.7320508075688772},"352":{"tf":1.0},"356":{"tf":1.0},"370":{"tf":1.0},"375":{"tf":1.0},"404":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"428":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.4142135623730951},"450":{"tf":1.0},"47":{"tf":1.4142135623730951},"49":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"524":{"tf":1.0},"528":{"tf":1.4142135623730951},"537":{"tf":1.0},"539":{"tf":1.4142135623730951},"548":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"588":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":2.449489742783178},"605":{"tf":1.4142135623730951},"62":{"tf":1.4142135623730951},"63":{"tf":1.0},"632":{"tf":1.0},"636":{"tf":1.0},"668":{"tf":1.0},"694":{"tf":1.0},"705":{"tf":1.0},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"736":{"tf":1.4142135623730951},"739":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.4142135623730951},"786":{"tf":1.0},"799":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"831":{"tf":1.4142135623730951},"840":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"860":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.0},"885":{"tf":1.4142135623730951},"912":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"944":{"tf":1.0},"961":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"107":{"tf":1.0}}}}}}}},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}}},"t":{"df":1,"docs":{"874":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"412":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.4142135623730951}}}}}}}}},"r":{"c":{"df":13,"docs":{"199":{"tf":1.0},"267":{"tf":1.0},"388":{"tf":1.0},"485":{"tf":1.0},"573":{"tf":1.4142135623730951},"599":{"tf":1.0},"606":{"tf":1.0},"614":{"tf":1.0},"63":{"tf":1.0},"670":{"tf":1.0},"773":{"tf":2.449489742783178},"776":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":1,"docs":{"420":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"x":{"df":1,"docs":{"600":{"tf":1.0}}}}}}}},"df":3,"docs":{"3":{"tf":1.0},"6":{"tf":1.0},"603":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":1,"docs":{"800":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"47":{"tf":1.4142135623730951},"51":{"tf":1.0}}}}},"k":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"253":{"tf":1.4142135623730951},"254":{"tf":1.0}}},"df":0,"docs":{}}},"df":10,"docs":{"253":{"tf":1.0},"254":{"tf":1.0},"323":{"tf":1.0},"347":{"tf":1.0},"356":{"tf":1.7320508075688772},"39":{"tf":1.0},"450":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"724":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"515":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"209":{"tf":1.0},"844":{"tf":1.4142135623730951}}},"t":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"3":{"7":{"df":1,"docs":{"665":{"tf":1.0}}},"df":0,"docs":{}},"5":{"3":{"df":1,"docs":{"661":{"tf":1.0}}},"7":{"df":1,"docs":{"985":{"tf":1.0}}},"8":{"df":1,"docs":{"689":{"tf":1.0}}},"9":{"df":1,"docs":{"675":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":53,"docs":{"12":{"tf":1.4142135623730951},"164":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"3":{"tf":1.0},"333":{"tf":1.0},"369":{"tf":1.0},"37":{"tf":1.0},"39":{"tf":1.0},"455":{"tf":1.0},"482":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"491":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"516":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.4142135623730951},"526":{"tf":1.0},"535":{"tf":1.7320508075688772},"536":{"tf":1.0},"537":{"tf":1.7320508075688772},"539":{"tf":1.0},"540":{"tf":1.0},"545":{"tf":1.0},"553":{"tf":1.0},"585":{"tf":1.0},"586":{"tf":1.4142135623730951},"588":{"tf":2.0},"594":{"tf":1.4142135623730951},"634":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"646":{"tf":1.4142135623730951},"661":{"tf":1.0},"675":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"848":{"tf":1.0},"985":{"tf":1.0}}}},"df":19,"docs":{"12":{"tf":1.0},"206":{"tf":1.0},"221":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"45":{"tf":1.0},"565":{"tf":1.0},"629":{"tf":1.0},"697":{"tf":1.0},"717":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"759":{"tf":1.0},"786":{"tf":1.4142135623730951},"815":{"tf":1.0},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"291":{"tf":1.0},"842":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"'":{"df":1,"docs":{"934":{"tf":1.0}}},"df":4,"docs":{"207":{"tf":1.0},"346":{"tf":1.0},"415":{"tf":1.0},"934":{"tf":1.0}}},"df":1,"docs":{"939":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"417":{"tf":1.0}}},"u":{"df":0,"docs":{},"n":{"df":1,"docs":{"51":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"m":{"df":7,"docs":{"120":{"tf":1.4142135623730951},"243":{"tf":1.0},"277":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"646":{"tf":1.0},"756":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":14,"docs":{"126":{"tf":1.0},"483":{"tf":1.0},"570":{"tf":1.0},"602":{"tf":1.0},"61":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"780":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.4142135623730951},"850":{"tf":1.0},"931":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"411":{"tf":1.0},"973":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"211":{"tf":1.0},"324":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0}}}},"df":22,"docs":{"151":{"tf":1.0},"154":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"331":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.0},"343":{"tf":1.4142135623730951},"350":{"tf":1.0},"352":{"tf":1.0},"414":{"tf":1.0},"501":{"tf":1.0},"520":{"tf":2.0},"521":{"tf":1.4142135623730951},"537":{"tf":1.0},"553":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.0},"898":{"tf":1.0},"933":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":3,"docs":{"335":{"tf":1.0},"344":{"tf":1.0},"711":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"221":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"573":{"tf":1.0}}}}}},"{":{"\\":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":2,"docs":{"390":{"tf":1.0},"397":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":13,"docs":{"234":{"tf":1.0},"254":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.0},"515":{"tf":2.23606797749979},"519":{"tf":2.23606797749979},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":1.7320508075688772},"526":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":7,"docs":{"180":{"tf":1.0},"203":{"tf":1.4142135623730951},"514":{"tf":1.0},"771":{"tf":1.0},"773":{"tf":1.4142135623730951},"949":{"tf":1.0},"991":{"tf":1.0}}}}}}}},"n":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":3,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"974":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"u":{"d":{"df":3,"docs":{"388":{"tf":2.0},"39":{"tf":2.0},"55":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"605":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":11,"docs":{"198":{"tf":1.0},"205":{"tf":1.4142135623730951},"300":{"tf":1.0},"375":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.7320508075688772},"619":{"tf":2.0},"651":{"tf":1.0},"732":{"tf":1.7320508075688772},"807":{"tf":1.0},"835":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"52":{"tf":1.0},"942":{"tf":1.0}}}},"z":{"df":1,"docs":{"573":{"tf":1.0}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":3,"docs":{"356":{"tf":1.0},"797":{"tf":1.0},"814":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":10,"docs":{"267":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"427":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"58":{"tf":1.0},"63":{"tf":1.0},"724":{"tf":1.0},"814":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"352":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":2,"docs":{"204":{"tf":1.0},"352":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"724":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"19":{"tf":1.0},"423":{"tf":1.0},"942":{"tf":1.0}}}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"22":{"tf":1.0},"35":{"tf":1.0},"576":{"tf":1.0},"843":{"tf":1.0}}}},"z":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"780":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":6,"docs":{"288":{"tf":1.0},"303":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"939":{"tf":1.0}}}}},"l":{"df":26,"docs":{"136":{"tf":1.0},"144":{"tf":1.0},"205":{"tf":1.7320508075688772},"218":{"tf":1.0},"248":{"tf":1.7320508075688772},"249":{"tf":1.0},"252":{"tf":1.4142135623730951},"257":{"tf":2.23606797749979},"29":{"tf":1.0},"388":{"tf":1.7320508075688772},"46":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"47":{"tf":1.0},"48":{"tf":1.0},"507":{"tf":1.4142135623730951},"522":{"tf":1.0},"553":{"tf":1.4142135623730951},"64":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"759":{"tf":2.23606797749979},"77":{"tf":1.0},"776":{"tf":1.0},"931":{"tf":1.0}},"i":{"df":14,"docs":{"119":{"tf":1.0},"204":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"307":{"tf":1.0},"47":{"tf":1.7320508075688772},"51":{"tf":1.0},"515":{"tf":1.0},"60":{"tf":1.0},"642":{"tf":1.0},"72":{"tf":1.0},"75":{"tf":1.0},"878":{"tf":1.0},"984":{"tf":1.0}}}}},"n":{"c":{"df":2,"docs":{"735":{"tf":7.0},"736":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"428":{"tf":1.0}}},"df":127,"docs":{"100":{"tf":1.0},"1004":{"tf":1.0},"1009":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"111":{"tf":1.4142135623730951},"13":{"tf":1.0},"163":{"tf":1.4142135623730951},"169":{"tf":1.0},"171":{"tf":1.0},"173":{"tf":1.0},"195":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.0},"21":{"tf":1.4142135623730951},"217":{"tf":1.0},"22":{"tf":1.0},"221":{"tf":1.0},"23":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":2.0},"25":{"tf":1.7320508075688772},"252":{"tf":1.4142135623730951},"26":{"tf":2.0},"267":{"tf":1.0},"276":{"tf":1.0},"284":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"32":{"tf":1.0},"322":{"tf":1.0},"334":{"tf":1.4142135623730951},"35":{"tf":2.0},"362":{"tf":1.0},"366":{"tf":1.4142135623730951},"371":{"tf":1.0},"373":{"tf":2.23606797749979},"374":{"tf":1.7320508075688772},"375":{"tf":1.7320508075688772},"379":{"tf":1.0},"38":{"tf":1.4142135623730951},"400":{"tf":1.7320508075688772},"401":{"tf":1.0},"403":{"tf":1.4142135623730951},"404":{"tf":2.23606797749979},"406":{"tf":1.0},"407":{"tf":1.4142135623730951},"408":{"tf":1.0},"409":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.0},"424":{"tf":1.0},"426":{"tf":1.0},"428":{"tf":2.23606797749979},"430":{"tf":1.0},"438":{"tf":2.6457513110645907},"440":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"50":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"521":{"tf":1.4142135623730951},"525":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"553":{"tf":1.0},"606":{"tf":1.0},"639":{"tf":1.0},"699":{"tf":1.4142135623730951},"730":{"tf":1.0},"732":{"tf":2.0},"735":{"tf":7.280109889280518},"736":{"tf":2.23606797749979},"738":{"tf":1.0},"739":{"tf":1.7320508075688772},"740":{"tf":1.0},"741":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":2.0},"748":{"tf":1.4142135623730951},"749":{"tf":2.23606797749979},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"799":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"849":{"tf":1.0},"860":{"tf":1.4142135623730951},"867":{"tf":1.0},"871":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":3.3166247903554},"928":{"tf":1.0},"93":{"tf":1.7320508075688772},"932":{"tf":1.4142135623730951},"938":{"tf":1.0},"94":{"tf":1.7320508075688772},"942":{"tf":2.0},"944":{"tf":1.4142135623730951},"945":{"tf":1.4142135623730951},"947":{"tf":1.0},"949":{"tf":1.0},"95":{"tf":1.7320508075688772},"952":{"tf":1.0},"953":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"964":{"tf":1.0},"966":{"tf":1.0},"969":{"tf":1.0},"97":{"tf":1.7320508075688772},"970":{"tf":1.0},"975":{"tf":1.0},"994":{"tf":1.0}},"s":{"/":{"1":{"0":{"4":{"5":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"d":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"261":{"tf":1.0},"511":{"tf":1.0}}}}}}},"df":21,"docs":{"121":{"tf":1.0},"184":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"234":{"tf":1.0},"236":{"tf":1.0},"267":{"tf":1.4142135623730951},"273":{"tf":1.0},"316":{"tf":1.7320508075688772},"619":{"tf":1.0},"660":{"tf":1.0},"694":{"tf":1.0},"777":{"tf":1.0},"80":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"869":{"tf":1.0},"874":{"tf":1.4142135623730951},"876":{"tf":1.0},"976":{"tf":1.0}}},"df":2,"docs":{"603":{"tf":1.4142135623730951},"7":{"tf":1.0}},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":9,"docs":{"2":{"tf":1.4142135623730951},"203":{"tf":1.0},"3":{"tf":1.7320508075688772},"373":{"tf":1.4142135623730951},"376":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":2.23606797749979},"7":{"tf":1.0},"9":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"2":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":39,"docs":{"108":{"tf":1.0},"152":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"267":{"tf":1.0},"281":{"tf":1.0},"285":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"335":{"tf":1.0},"347":{"tf":1.0},"388":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.4142135623730951},"436":{"tf":1.0},"452":{"tf":1.0},"56":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"583":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"638":{"tf":1.0},"651":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"77":{"tf":1.4142135623730951},"771":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"906":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"938":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":8,"docs":{"128":{"tf":1.0},"154":{"tf":1.0},"200":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.4142135623730951},"505":{"tf":1.0},"602":{"tf":1.0},"732":{"tf":1.0}}}}}}}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":142,"docs":{"1":{"tf":1.0},"1001":{"tf":1.0},"1002":{"tf":1.0},"1015":{"tf":1.4142135623730951},"108":{"tf":1.0},"111":{"tf":1.0},"122":{"tf":1.0},"124":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"16":{"tf":1.4142135623730951},"163":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.4142135623730951},"182":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"226":{"tf":1.0},"229":{"tf":1.0},"246":{"tf":1.4142135623730951},"247":{"tf":1.0},"254":{"tf":1.0},"262":{"tf":1.4142135623730951},"279":{"tf":1.0},"281":{"tf":1.0},"289":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"310":{"tf":1.7320508075688772},"311":{"tf":1.0},"316":{"tf":1.0},"321":{"tf":1.0},"322":{"tf":1.0},"361":{"tf":1.4142135623730951},"363":{"tf":1.0},"364":{"tf":1.0},"366":{"tf":1.0},"37":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"386":{"tf":1.0},"399":{"tf":1.4142135623730951},"412":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"430":{"tf":1.0},"441":{"tf":1.0},"449":{"tf":1.4142135623730951},"451":{"tf":1.0},"464":{"tf":1.0},"473":{"tf":1.0},"481":{"tf":1.0},"494":{"tf":1.0},"495":{"tf":1.0},"500":{"tf":1.0},"512":{"tf":1.0},"513":{"tf":1.0},"520":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.0},"584":{"tf":1.0},"597":{"tf":1.0},"598":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":1.0},"626":{"tf":1.0},"627":{"tf":1.0},"634":{"tf":1.0},"648":{"tf":1.7320508075688772},"649":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":1.0},"708":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"728":{"tf":1.0},"730":{"tf":1.0},"740":{"tf":1.4142135623730951},"741":{"tf":1.0},"751":{"tf":1.0},"755":{"tf":1.0},"757":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"812":{"tf":1.0},"826":{"tf":1.0},"827":{"tf":1.0},"840":{"tf":1.0},"871":{"tf":1.0},"880":{"tf":1.0},"890":{"tf":1.0},"891":{"tf":1.0},"907":{"tf":1.0},"908":{"tf":1.0},"911":{"tf":1.0},"913":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.0},"940":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.0},"973":{"tf":1.0},"974":{"tf":1.0},"987":{"tf":1.0},"988":{"tf":1.0}}}}},"z":{"df":0,"docs":{},"z":{"df":1,"docs":{"211":{"tf":1.0}}}}}},"g":{"a":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"782":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":3,"docs":{"715":{"tf":1.0},"716":{"tf":1.0},"725":{"tf":1.0}}}}}},"df":7,"docs":{"29":{"tf":1.4142135623730951},"30":{"tf":1.0},"38":{"tf":1.0},"51":{"tf":2.23606797749979},"54":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"144":{"tf":1.0},"33":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.0},"577":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.0},"835":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"322":{"tf":1.0}}}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"e":{"df":5,"docs":{"124":{"tf":1.0},"230":{"tf":1.0},"63":{"tf":1.0},"710":{"tf":1.0},"777":{"tf":1.0}}},"m":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.0},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.7320508075688772},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"p":{"df":1,"docs":{"500":{"tf":1.4142135623730951}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"121":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"g":{"df":1,"docs":{"564":{"tf":1.0}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"195":{"tf":1.0},"215":{"tf":1.0},"366":{"tf":1.0},"465":{"tf":1.0},"807":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"722":{"tf":1.0}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"263":{"tf":1.0},"563":{"tf":1.0},"771":{"tf":1.0}}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"452":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":78,"docs":{"155":{"tf":1.0},"164":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.7320508075688772},"170":{"tf":1.4142135623730951},"171":{"tf":1.4142135623730951},"172":{"tf":1.0},"184":{"tf":1.4142135623730951},"199":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"217":{"tf":1.0},"24":{"tf":1.4142135623730951},"255":{"tf":1.0},"257":{"tf":1.4142135623730951},"264":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"276":{"tf":1.7320508075688772},"296":{"tf":1.0},"310":{"tf":1.0},"327":{"tf":1.0},"336":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.7320508075688772},"368":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.0},"451":{"tf":1.7320508075688772},"452":{"tf":1.0},"457":{"tf":1.0},"459":{"tf":1.0},"460":{"tf":1.0},"461":{"tf":1.0},"469":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"513":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"524":{"tf":1.4142135623730951},"526":{"tf":1.7320508075688772},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"534":{"tf":1.7320508075688772},"535":{"tf":1.4142135623730951},"536":{"tf":1.0},"537":{"tf":1.4142135623730951},"542":{"tf":1.0},"548":{"tf":1.0},"56":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"588":{"tf":1.7320508075688772},"634":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"665":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"71":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"78":{"tf":1.7320508075688772},"798":{"tf":1.0},"83":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":1.4142135623730951},"938":{"tf":1.0},"987":{"tf":1.0},"992":{"tf":1.0}}},"s":{"df":0,"docs":{},"i":{"df":16,"docs":{"249":{"tf":1.0},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"303":{"tf":1.7320508075688772},"345":{"tf":2.23606797749979},"348":{"tf":1.0},"362":{"tf":1.0},"371":{"tf":1.4142135623730951},"375":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":2.0},"502":{"tf":1.4142135623730951},"52":{"tf":1.0},"521":{"tf":1.0},"526":{"tf":1.0},"680":{"tf":1.0}},"s":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{">":{"/":{"df":0,"docs":{},"k":{"a":{"d":{"df":1,"docs":{"503":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"253":{"tf":1.0},"254":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"814":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"345":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":2,"docs":{"164":{"tf":1.0},"535":{"tf":1.0}}}}},"t":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":1,"docs":{"333":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"349":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}},"<":{"b":{"a":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"<":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"438":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":24,"docs":{"121":{"tf":1.0},"154":{"tf":1.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"441":{"tf":1.0},"450":{"tf":2.0},"455":{"tf":1.0},"514":{"tf":1.4142135623730951},"528":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"697":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"78":{"tf":1.0},"817":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.4142135623730951},"875":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.4142135623730951},"912":{"tf":1.0},"933":{"tf":1.0}}}},"g":{"df":0,"docs":{},"w":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"938":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"549":{"tf":1.0}}}}}}}},"i":{"b":{"df":4,"docs":{"735":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.4142135623730951},"990":{"tf":1.0}}},"df":0,"docs":{},"g":{"a":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":2,"docs":{"990":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":5,"docs":{"243":{"tf":1.4142135623730951},"249":{"tf":1.0},"272":{"tf":1.0},"826":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":18,"docs":{"178":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"208":{"tf":1.0},"347":{"tf":1.0},"376":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0},"784":{"tf":1.0}},"n":{"df":51,"docs":{"1007":{"tf":1.0},"124":{"tf":1.0},"173":{"tf":1.0},"205":{"tf":1.7320508075688772},"221":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"273":{"tf":1.4142135623730951},"274":{"tf":1.0},"30":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":2.23606797749979},"375":{"tf":1.0},"376":{"tf":1.0},"427":{"tf":1.0},"439":{"tf":1.0},"467":{"tf":1.0},"507":{"tf":1.0},"516":{"tf":1.4142135623730951},"522":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"602":{"tf":1.0},"633":{"tf":1.0},"635":{"tf":1.0},"64":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"735":{"tf":2.8284271247461903},"739":{"tf":1.4142135623730951},"744":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.0},"885":{"tf":1.4142135623730951},"928":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"o":{"b":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":1,"docs":{"786":{"tf":1.0}},"s":{"(":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"m":{"a":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}}}},"df":3,"docs":{"44":{"tf":1.0},"522":{"tf":1.0},"831":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"729":{"tf":1.0}},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"729":{"tf":1.0}}}}}}}}}},"n":{"df":0,"docs":{},"u":{"df":1,"docs":{"894":{"tf":1.0}}}},"o":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"111":{"tf":1.0},"208":{"tf":1.0},"295":{"tf":1.0},"346":{"tf":1.0},"467":{"tf":1.0},"49":{"tf":1.0},"54":{"tf":1.0},"565":{"tf":1.0},"829":{"tf":1.0},"934":{"tf":1.0}}}},"df":28,"docs":{"126":{"tf":1.0},"148":{"tf":1.0},"214":{"tf":1.0},"296":{"tf":1.0},"310":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.4142135623730951},"659":{"tf":1.0},"679":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"718":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"77":{"tf":1.4142135623730951},"807":{"tf":1.0},"831":{"tf":1.0},"849":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"928":{"tf":1.0},"954":{"tf":1.0}},"e":{"df":3,"docs":{"207":{"tf":1.4142135623730951},"532":{"tf":1.0},"933":{"tf":1.0}}},"o":{"d":{"df":21,"docs":{"126":{"tf":1.0},"133":{"tf":1.0},"156":{"tf":1.0},"187":{"tf":1.0},"231":{"tf":1.0},"250":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.0},"370":{"tf":1.0},"511":{"tf":1.0},"574":{"tf":1.0},"651":{"tf":1.0},"710":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":1.0},"732":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"849":{"tf":1.0},"894":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":2,"docs":{"482":{"tf":1.0},"500":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"v":{"1":{"df":1,"docs":{"371":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"742":{"tf":1.0}}},"r":{"df":0,"docs":{},"n":{"df":66,"docs":{"108":{"tf":1.7320508075688772},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"137":{"tf":1.4142135623730951},"138":{"tf":2.0},"139":{"tf":1.0},"140":{"tf":2.0},"141":{"tf":1.0},"142":{"tf":1.7320508075688772},"144":{"tf":1.0},"145":{"tf":1.4142135623730951},"146":{"tf":1.0},"147":{"tf":1.7320508075688772},"148":{"tf":1.0},"185":{"tf":1.0},"191":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"209":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.7320508075688772},"236":{"tf":1.0},"237":{"tf":1.0},"273":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"301":{"tf":1.4142135623730951},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":2.0},"375":{"tf":3.0},"376":{"tf":2.23606797749979},"384":{"tf":1.0},"385":{"tf":1.0},"410":{"tf":1.0},"420":{"tf":1.0},"427":{"tf":1.4142135623730951},"438":{"tf":1.0},"440":{"tf":1.4142135623730951},"446":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.7320508075688772},"720":{"tf":1.0},"729":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"797":{"tf":1.0},"804":{"tf":1.0},"811":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"853":{"tf":1.0},"876":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951},"932":{"tf":1.0},"934":{"tf":1.0}}}}}}},"p":{"df":1,"docs":{"45":{"tf":1.0}},"g":{"df":5,"docs":{"894":{"tf":1.0},"895":{"tf":1.0},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.4142135623730951}}}},"r":{"a":{"d":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"427":{"tf":1.0},"428":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"874":{"tf":1.4142135623730951}}}},"n":{"d":{"df":0,"docs":{},"p":{"a":{"df":2,"docs":{"45":{"tf":1.0},"500":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":6,"docs":{"440":{"tf":1.0},"776":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"85":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"h":{"df":2,"docs":{"213":{"tf":1.0},"571":{"tf":1.7320508075688772}}}},"y":{"df":2,"docs":{"39":{"tf":1.0},"44":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"928":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"114":{"tf":1.0},"517":{"tf":1.0},"807":{"tf":1.4142135623730951},"819":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":9,"docs":{"184":{"tf":1.0},"187":{"tf":1.0},"205":{"tf":1.0},"221":{"tf":1.0},"326":{"tf":1.0},"347":{"tf":1.0},"84":{"tf":1.0},"879":{"tf":2.23606797749979},"956":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"565":{"tf":1.0},"600":{"tf":1.0},"663":{"tf":1.0},"712":{"tf":1.0},"77":{"tf":1.0},"797":{"tf":1.0}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":2,"docs":{"577":{"tf":1.0},"628":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"466":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":2,"docs":{"326":{"tf":1.0},"361":{"tf":1.0}}}}}}},"df":0,"docs":{}},"p":{"df":16,"docs":{"211":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"240":{"tf":1.0},"269":{"tf":1.4142135623730951},"270":{"tf":1.4142135623730951},"272":{"tf":1.0},"368":{"tf":1.4142135623730951},"373":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"376":{"tf":1.0},"436":{"tf":1.0},"44":{"tf":1.0},"629":{"tf":1.0},"759":{"tf":1.0},"844":{"tf":1.0}}}},"w":{"df":1,"docs":{"744":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":7,"docs":{"416":{"tf":1.0},"418":{"tf":1.4142135623730951},"428":{"tf":1.0},"54":{"tf":1.0},"742":{"tf":1.0},"752":{"tf":1.0},"973":{"tf":1.0}}}}}}},"u":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":10,"docs":{"124":{"tf":1.0},"203":{"tf":1.0},"231":{"tf":1.0},"342":{"tf":1.0},"368":{"tf":1.4142135623730951},"45":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"609":{"tf":1.0},"78":{"tf":1.0}},"e":{"d":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"/":{"a":{"df":0,"docs":{},"u":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"46":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"d":{"df":1,"docs":{"894":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"615":{"tf":1.0}}}}}}}},"df":3,"docs":{"615":{"tf":1.0},"73":{"tf":1.0},"75":{"tf":1.0}}},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"28":{"tf":1.0},"30":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"h":{"(":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":2,"docs":{"45":{"tf":2.449489742783178},"47":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"r":{"df":1,"docs":{"46":{"tf":1.0}}}},"a":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":3,"docs":{"214":{"tf":1.0},"215":{"tf":1.0},"244":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"780":{"tf":1.0}}}}}}},"l":{"df":0,"docs":{},"f":{"df":4,"docs":{"208":{"tf":1.4142135623730951},"515":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0}}},"t":{"df":4,"docs":{"108":{"tf":1.0},"151":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0}}},"v":{"df":2,"docs":{"444":{"tf":1.0},"567":{"tf":1.0}}}},"n":{"d":{"df":5,"docs":{"316":{"tf":1.0},"440":{"tf":1.0},"471":{"tf":1.0},"515":{"tf":1.0},"936":{"tf":1.0}},"l":{"df":29,"docs":{"111":{"tf":1.0},"112":{"tf":1.7320508075688772},"114":{"tf":1.0},"141":{"tf":1.0},"148":{"tf":1.0},"237":{"tf":1.0},"241":{"tf":1.0},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"375":{"tf":1.4142135623730951},"517":{"tf":1.0},"52":{"tf":1.0},"537":{"tf":1.0},"56":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"600":{"tf":1.0},"602":{"tf":2.0},"62":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.7320508075688772},"651":{"tf":1.0},"729":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"887":{"tf":1.0},"912":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.4142135623730951},"975":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"602":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":30,"docs":{"126":{"tf":1.0},"127":{"tf":1.0},"142":{"tf":1.0},"152":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"450":{"tf":1.0},"459":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.0},"606":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.4142135623730951},"735":{"tf":1.0},"739":{"tf":1.0},"765":{"tf":1.0},"777":{"tf":1.0},"833":{"tf":1.0},"846":{"tf":1.0},"849":{"tf":1.0},"879":{"tf":1.4142135623730951},"927":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.7320508075688772}}}}}},"r":{"d":{"c":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"140":{"tf":1.0},"175":{"tf":1.0}}},"df":0,"docs":{}}},"df":8,"docs":{"537":{"tf":1.0},"573":{"tf":1.0},"615":{"tf":1.0},"669":{"tf":1.0},"724":{"tf":1.0},"850":{"tf":1.0},"874":{"tf":1.0},"928":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"56":{"tf":1.0},"77":{"tf":1.0}}},"r":{"df":2,"docs":{"1004":{"tf":1.0},"73":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"402":{"tf":1.0},"515":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"729":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"df":3,"docs":{"505":{"tf":1.0},"565":{"tf":1.0},"720":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"565":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"776":{"tf":1.0}},"i":{"df":1,"docs":{"771":{"tf":1.0}}}}}}},"s":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"879":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},">":{"/":{"df":0,"docs":{},"k":{"a":{"d":{"/":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"502":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"502":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":53,"docs":{"113":{"tf":1.0},"163":{"tf":1.0},"171":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"248":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"333":{"tf":1.0},"345":{"tf":1.4142135623730951},"349":{"tf":1.0},"39":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":2.23606797749979},"450":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"501":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":2.23606797749979},"52":{"tf":1.7320508075688772},"520":{"tf":3.1622776601683795},"521":{"tf":1.4142135623730951},"525":{"tf":2.449489742783178},"526":{"tf":3.605551275463989},"528":{"tf":2.23606797749979},"530":{"tf":1.0},"531":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.4142135623730951},"632":{"tf":1.7320508075688772},"634":{"tf":3.1622776601683795},"635":{"tf":1.0},"64":{"tf":1.4142135623730951},"680":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":2.23606797749979},"78":{"tf":2.449489742783178},"786":{"tf":2.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"879":{"tf":2.449489742783178},"880":{"tf":1.4142135623730951},"94":{"tf":1.0}},"e":{"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"786":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":1,"docs":{"171":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"p":{"<":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"i":{"d":{",":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"715":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"n":{"'":{"df":0,"docs":{},"t":{"df":2,"docs":{"112":{"tf":1.0},"3":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"df":38,"docs":{"152":{"tf":1.4142135623730951},"155":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"262":{"tf":1.0},"270":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.0},"495":{"tf":1.0},"515":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"545":{"tf":1.0},"571":{"tf":1.0},"58":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"632":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"762":{"tf":1.0},"77":{"tf":1.0},"777":{"tf":1.0},"799":{"tf":1.4142135623730951},"816":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":2.0}}}}},"df":5,"docs":{"44":{"tf":2.0},"45":{"tf":2.8284271247461903},"46":{"tf":1.0},"47":{"tf":2.0},"634":{"tf":1.0}},"e":{"a":{"d":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"814":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":12,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.0},"114":{"tf":1.0},"300":{"tf":1.0},"495":{"tf":1.0},"500":{"tf":2.23606797749979},"503":{"tf":1.7320508075688772},"512":{"tf":1.0},"715":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}}},"df":14,"docs":{"322":{"tf":1.0},"343":{"tf":1.4142135623730951},"349":{"tf":1.7320508075688772},"350":{"tf":2.23606797749979},"44":{"tf":2.0},"45":{"tf":2.6457513110645907},"46":{"tf":2.0},"47":{"tf":2.23606797749979},"49":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.7320508075688772},"500":{"tf":1.4142135623730951},"634":{"tf":1.0},"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{},"p":{"df":4,"docs":{"732":{"tf":1.4142135623730951},"827":{"tf":1.7320508075688772},"829":{"tf":1.4142135623730951},"832":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"g":{"df":5,"docs":{"828":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.7320508075688772},"832":{"tf":1.0},"833":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":1,"docs":{"881":{"tf":1.0}}},"v":{"df":0,"docs":{},"i":{"df":2,"docs":{"1006":{"tf":1.0},"530":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"553":{"tf":1.0},"738":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":4,"docs":{"46":{"tf":1.0},"500":{"tf":1.0},"83":{"tf":1.0},"996":{"tf":1.0}}}}}},"l":{"d":{"df":5,"docs":{"206":{"tf":1.0},"375":{"tf":1.4142135623730951},"39":{"tf":1.0},"414":{"tf":1.0},"879":{"tf":1.7320508075688772}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":1,"docs":{"847":{"tf":1.4142135623730951}}}},"p":{"df":22,"docs":{"106":{"tf":1.0},"121":{"tf":1.4142135623730951},"127":{"tf":1.0},"145":{"tf":1.0},"172":{"tf":1.0},"206":{"tf":1.0},"273":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"574":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"780":{"tf":1.0},"797":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0},"810":{"tf":1.0},"843":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"334":{"tf":1.0}}}}}},"n":{"c":{"df":4,"docs":{"199":{"tf":1.0},"71":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"'":{"df":2,"docs":{"450":{"tf":1.0},"848":{"tf":1.0}}},"df":50,"docs":{"16":{"tf":1.0},"186":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.7320508075688772},"290":{"tf":1.0},"293":{"tf":1.0},"348":{"tf":1.0},"388":{"tf":1.0},"415":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"435":{"tf":1.0},"44":{"tf":1.0},"444":{"tf":1.0},"450":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0},"520":{"tf":1.0},"54":{"tf":1.0},"553":{"tf":1.4142135623730951},"56":{"tf":1.4142135623730951},"560":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"634":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"74":{"tf":1.0},"748":{"tf":1.0},"761":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.0},"844":{"tf":1.0},"881":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"778":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"127":{"tf":1.0}}}}}}},"x":{"a":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"253":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"815":{"tf":1.4142135623730951}}}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"520":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"874":{"tf":1.0}},"i":{"df":3,"docs":{"483":{"tf":1.0},"485":{"tf":1.0},"783":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"h":{"df":21,"docs":{"1004":{"tf":1.0},"1008":{"tf":1.0},"199":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"38":{"tf":1.0},"412":{"tf":1.0},"456":{"tf":1.0},"467":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.4142135623730951},"916":{"tf":1.0},"929":{"tf":1.0},"939":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":20,"docs":{"184":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"25":{"tf":1.0},"267":{"tf":1.0},"417":{"tf":1.0},"42":{"tf":1.0},"429":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"747":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"818":{"tf":1.0},"874":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"234":{"tf":1.0},"711":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"198":{"tf":1.0},"231":{"tf":1.0},"40":{"tf":1.0},"54":{"tf":1.0},"697":{"tf":1.0},"779":{"tf":1.0},"813":{"tf":1.0},"826":{"tf":1.0},"846":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":4,"docs":{"418":{"tf":1.0},"804":{"tf":1.0},"933":{"tf":1.0},"971":{"tf":1.0}}}}}}}}},"m":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"281":{"tf":1.4142135623730951},"284":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"df":9,"docs":{"44":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.4142135623730951},"665":{"tf":1.0},"666":{"tf":1.0},"668":{"tf":1.7320508075688772},"669":{"tf":1.0},"670":{"tf":2.0},"673":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"138":{"tf":1.0},"290":{"tf":1.0},"512":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.7320508075688772},"913":{"tf":1.0}},"i":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":2,"docs":{"45":{"tf":1.4142135623730951},"46":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":7,"docs":{"49":{"tf":1.0},"500":{"tf":2.23606797749979},"501":{"tf":1.0},"502":{"tf":1.0},"512":{"tf":1.0},"571":{"tf":1.4142135623730951},"843":{"tf":1.0}}}}}}},"t":{"df":3,"docs":{"394":{"tf":1.0},"571":{"tf":1.0},"846":{"tf":1.0}}}},"o":{"c":{"df":2,"docs":{"12":{"tf":1.0},"364":{"tf":1.0}}},"df":0,"docs":{},"l":{"d":{"df":14,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"437":{"tf":1.0},"515":{"tf":2.0},"56":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":2.0},"605":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":2.0},"654":{"tf":1.4142135623730951},"66":{"tf":1.0},"67":{"tf":1.0},"976":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"(":{"df":1,"docs":{"844":{"tf":1.0}}},"df":26,"docs":{"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"193":{"tf":1.4142135623730951},"198":{"tf":1.0},"201":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.4142135623730951},"376":{"tf":1.0},"42":{"tf":1.0},"432":{"tf":1.0},"566":{"tf":1.0},"577":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"797":{"tf":1.4142135623730951},"798":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"858":{"tf":1.0},"876":{"tf":1.0},"877":{"tf":1.0},"897":{"tf":1.0},"914":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"332":{"tf":1.7320508075688772},"48":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"712":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0}},"i":{"df":2,"docs":{"710":{"tf":1.0},"722":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"9":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"k":{"df":3,"docs":{"281":{"tf":1.4142135623730951},"284":{"tf":1.0},"291":{"tf":1.4142135623730951}}}},"p":{"df":7,"docs":{"18":{"tf":1.0},"600":{"tf":1.7320508075688772},"602":{"tf":2.0},"606":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":2.449489742783178}},"e":{"df":4,"docs":{"121":{"tf":1.0},"16":{"tf":1.0},"58":{"tf":1.0},"928":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"723":{"tf":1.0},"807":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"179":{"tf":1.0},"181":{"tf":1.0},"537":{"tf":1.0},"548":{"tf":1.0}},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"t":{"_":{"c":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"24":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"26":{"tf":1.4142135623730951}},"l":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"25":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}}}}}},"df":38,"docs":{"100":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"199":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"362":{"tf":2.0},"38":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":1.7320508075688772},"401":{"tf":1.0},"403":{"tf":1.4142135623730951},"404":{"tf":1.7320508075688772},"406":{"tf":1.0},"407":{"tf":1.4142135623730951},"408":{"tf":1.0},"409":{"tf":1.0},"45":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"53":{"tf":1.0},"54":{"tf":1.4142135623730951},"730":{"tf":2.23606797749979},"731":{"tf":1.4142135623730951},"732":{"tf":3.0},"735":{"tf":4.898979485566356},"736":{"tf":2.23606797749979},"739":{"tf":1.4142135623730951},"740":{"tf":1.4142135623730951},"761":{"tf":1.0},"78":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"93":{"tf":1.7320508075688772},"94":{"tf":1.0},"95":{"tf":1.7320508075688772},"97":{"tf":1.7320508075688772}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"231":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"73":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":8,"docs":{"183":{"tf":1.4142135623730951},"184":{"tf":1.0},"186":{"tf":1.4142135623730951},"257":{"tf":1.0},"507":{"tf":1.0},"861":{"tf":1.4142135623730951},"862":{"tf":1.4142135623730951},"932":{"tf":1.0}}},"s":{"df":2,"docs":{"849":{"tf":1.0},"852":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":1,"docs":{"735":{"tf":1.7320508075688772}},"s":{":":{"/":{"/":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"df":0,"docs":{},"t":{"/":{"a":{"d":{"df":0,"docs":{},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"937":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":1,"docs":{"646":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"35":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"1":{"1":{"0":{"df":1,"docs":{"990":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"h":{"/":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"3":{"7":{"7":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"4":{"7":{"5":{"8":{"df":1,"docs":{"308":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"6":{"8":{"5":{"df":2,"docs":{"308":{"tf":1.0},"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"5":{"3":{"9":{"df":1,"docs":{"308":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":11,"docs":{"35":{"tf":1.4142135623730951},"440":{"tf":1.0},"500":{"tf":1.0},"551":{"tf":1.4142135623730951},"555":{"tf":1.0},"712":{"tf":1.4142135623730951},"74":{"tf":1.0},"793":{"tf":1.4142135623730951},"824":{"tf":1.0},"831":{"tf":1.0},"990":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":8,"docs":{"186":{"tf":1.4142135623730951},"388":{"tf":1.0},"661":{"tf":1.0},"665":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"840":{"tf":1.0},"985":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"w":{"3":{"df":0,"docs":{},"f":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"1":{"0":{"df":1,"docs":{"760":{"tf":1.0}}},"df":0,"docs":{}},"5":{"df":1,"docs":{"760":{"tf":1.0}}},"6":{"df":1,"docs":{"735":{"tf":1.0}}},"7":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"h":{"a":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"m":{"d":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"/":{"@":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"b":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"q":{"6":{"7":{"df":0,"docs":{},"j":{"b":{"df":0,"docs":{},"w":{"/":{"df":0,"docs":{},"s":{"1":{"df":0,"docs":{},"f":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"v":{"df":0,"docs":{},"x":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":3,"docs":{"712":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"w":{"df":0,"docs":{},"e":{"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"/":{"#":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"%":{"df":0,"docs":{},"e":{"2":{"%":{"9":{"1":{"%":{"a":{"0":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"d":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"92":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{".":{"b":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"6":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"3":{"df":0,"docs":{},"q":{"?":{"df":0,"docs":{},"t":{"=":{"5":{"2":{"6":{"df":1,"docs":{"807":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"u":{"b":{"df":18,"docs":{"234":{"tf":1.0},"373":{"tf":1.7320508075688772},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"410":{"tf":1.7320508075688772},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"415":{"tf":1.0},"418":{"tf":2.0},"423":{"tf":1.0},"428":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":2.449489742783178},"697":{"tf":3.1622776601683795},"699":{"tf":1.0},"700":{"tf":1.0},"959":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":3,"docs":{"289":{"tf":1.0},"567":{"tf":1.0},"779":{"tf":1.0}}}}},"}":{"_":{"df":0,"docs":{},"p":{"df":2,"docs":{"45":{"tf":1.0},"46":{"tf":1.0}}},"r":{"df":3,"docs":{"44":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"i":{"'":{"d":{"df":1,"docs":{"267":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"878":{"tf":1.0}}}},"m":{"df":4,"docs":{"261":{"tf":1.0},"511":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.4142135623730951}}},"v":{"df":1,"docs":{"878":{"tf":1.4142135623730951}}}},"+":{"1":{"df":1,"docs":{"45":{"tf":1.0}}},"df":0,"docs":{}},".":{"df":20,"docs":{"113":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.4142135623730951},"186":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.4142135623730951},"3":{"tf":1.7320508075688772},"568":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":1.0},"7":{"tf":1.0},"777":{"tf":1.4142135623730951},"847":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"763":{"tf":1.0}}}},"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{"df":2,"docs":{"522":{"tf":1.0},"735":{"tf":9.273618495495704}}},"df":0,"docs":{}},"6":{"4":{"df":3,"docs":{"522":{"tf":1.0},"735":{"tf":8.246211251235321},"736":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"522":{"tf":1.0}}},"=":{"b":{"+":{"1":{"df":1,"docs":{"47":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"df":30,"docs":{"126":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"343":{"tf":1.4142135623730951},"347":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":1.0},"456":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":1.4142135623730951},"48":{"tf":1.0},"524":{"tf":1.7320508075688772},"553":{"tf":1.4142135623730951},"555":{"tf":1.0},"6":{"tf":2.449489742783178},"603":{"tf":1.4142135623730951},"632":{"tf":1.0},"634":{"tf":1.0},"7":{"tf":1.0},"735":{"tf":1.4142135623730951},"761":{"tf":1.0},"81":{"tf":2.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"84":{"tf":1.0},"879":{"tf":2.449489742783178}},"e":{"a":{"df":16,"docs":{"108":{"tf":1.0},"429":{"tf":1.0},"514":{"tf":1.0},"518":{"tf":1.0},"588":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"732":{"tf":1.0},"780":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.7320508075688772},"845":{"tf":1.0},"849":{"tf":1.0},"856":{"tf":1.0}},"l":{"df":13,"docs":{"148":{"tf":1.0},"199":{"tf":1.0},"207":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"385":{"tf":1.0},"777":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"928":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":25,"docs":{"323":{"tf":1.0},"339":{"tf":1.0},"348":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.4142135623730951},"373":{"tf":1.4142135623730951},"375":{"tf":2.6457513110645907},"376":{"tf":1.0},"385":{"tf":1.0},"432":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.1622776601683795},"81":{"tf":1.0},"891":{"tf":1.7320508075688772},"894":{"tf":1.0},"895":{"tf":2.6457513110645907},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.7320508075688772},"907":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.7320508075688772},"917":{"tf":1.4142135623730951},"919":{"tf":1.0}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"95":{"tf":1.0}},"i":{"df":34,"docs":{"191":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.7320508075688772},"208":{"tf":1.0},"234":{"tf":1.0},"253":{"tf":1.0},"273":{"tf":1.0},"285":{"tf":1.0},"320":{"tf":1.0},"346":{"tf":1.4142135623730951},"351":{"tf":1.0},"521":{"tf":2.23606797749979},"522":{"tf":1.4142135623730951},"524":{"tf":2.23606797749979},"525":{"tf":1.0},"539":{"tf":1.0},"602":{"tf":1.0},"604":{"tf":1.0},"648":{"tf":1.0},"7":{"tf":1.0},"735":{"tf":2.23606797749979},"787":{"tf":1.0},"801":{"tf":1.0},"880":{"tf":1.0},"899":{"tf":1.0},"900":{"tf":1.4142135623730951},"903":{"tf":1.0},"917":{"tf":1.0},"948":{"tf":1.0},"965":{"tf":1.0},"993":{"tf":1.0},"998":{"tf":1.0}}}},"t":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"898":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":1,"docs":{"340":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":10,"docs":{"435":{"tf":1.0},"439":{"tf":1.0},"503":{"tf":1.0},"531":{"tf":1.0},"559":{"tf":1.0},"645":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"761":{"tf":1.0},"934":{"tf":1.0}}}}}},"i":{"df":3,"docs":{"469":{"tf":1.4142135623730951},"470":{"tf":1.0},"471":{"tf":1.0}},"i":{"df":3,"docs":{"469":{"tf":2.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":1,"docs":{"912":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"39":{"tf":1.0}},"t":{"df":0,"docs":{},"r":{"df":6,"docs":{"207":{"tf":1.0},"208":{"tf":1.0},"568":{"tf":1.0},"777":{"tf":1.0},"83":{"tf":1.0},"878":{"tf":1.0}}}}}}}},"m":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"516":{"tf":1.0},"852":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"60":{"tf":1.0},"846":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":14,"docs":{"126":{"tf":1.0},"170":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"417":{"tf":1.0},"564":{"tf":1.4142135623730951},"573":{"tf":1.0},"605":{"tf":1.0},"660":{"tf":1.4142135623730951},"751":{"tf":1.0},"77":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"206":{"tf":1.0},"209":{"tf":1.0}}}},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"126":{"tf":1.0}}}}},"o":{"df":1,"docs":{"399":{"tf":1.0}}},"p":{"a":{"c":{"df":0,"docs":{},"t":{"df":58,"docs":{"1003":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"11":{"tf":1.0},"117":{"tf":1.0},"130":{"tf":1.0},"152":{"tf":1.0},"158":{"tf":1.0},"174":{"tf":1.0},"176":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"303":{"tf":1.0},"305":{"tf":1.0},"310":{"tf":1.0},"379":{"tf":1.0},"392":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.4142135623730951},"422":{"tf":1.0},"424":{"tf":1.0},"517":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"537":{"tf":1.0},"541":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.0},"575":{"tf":1.4142135623730951},"577":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.4142135623730951},"582":{"tf":1.0},"590":{"tf":1.0},"592":{"tf":1.0},"606":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"703":{"tf":1.0},"711":{"tf":1.4142135623730951},"712":{"tf":1.0},"725":{"tf":1.0},"739":{"tf":1.4142135623730951},"77":{"tf":1.0},"778":{"tf":1.0},"8":{"tf":1.0},"819":{"tf":1.0},"821":{"tf":1.0},"866":{"tf":1.0},"87":{"tf":1.0},"916":{"tf":1.0},"929":{"tf":1.0},"936":{"tf":1.0},"968":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"515":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"720":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":2,"docs":{"24":{"tf":2.0},"933":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"819":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":166,"docs":{"0":{"tf":1.0},"1006":{"tf":1.0},"1008":{"tf":1.4142135623730951},"1012":{"tf":1.0},"115":{"tf":1.4142135623730951},"126":{"tf":1.0},"128":{"tf":1.4142135623730951},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.7320508075688772},"169":{"tf":1.0},"18":{"tf":1.4142135623730951},"19":{"tf":1.0},"191":{"tf":1.0},"193":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"209":{"tf":2.0},"211":{"tf":1.0},"212":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"226":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"240":{"tf":1.0},"241":{"tf":1.0},"249":{"tf":1.0},"251":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"281":{"tf":1.0},"282":{"tf":1.0},"284":{"tf":1.0},"291":{"tf":1.0},"30":{"tf":1.4142135623730951},"304":{"tf":1.4142135623730951},"32":{"tf":1.0},"324":{"tf":1.4142135623730951},"326":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.4142135623730951},"354":{"tf":1.4142135623730951},"359":{"tf":1.7320508075688772},"373":{"tf":1.0},"38":{"tf":1.0},"382":{"tf":1.0},"384":{"tf":1.0},"390":{"tf":1.4142135623730951},"402":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.0},"417":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.0},"429":{"tf":1.4142135623730951},"435":{"tf":1.0},"436":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"464":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"486":{"tf":1.0},"496":{"tf":1.4142135623730951},"50":{"tf":1.7320508075688772},"500":{"tf":2.23606797749979},"501":{"tf":2.449489742783178},"502":{"tf":1.7320508075688772},"503":{"tf":2.0},"505":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.7320508075688772},"53":{"tf":1.0},"54":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"555":{"tf":1.0},"56":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.4142135623730951},"574":{"tf":1.0},"576":{"tf":1.0},"59":{"tf":1.0},"594":{"tf":1.0},"609":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.0},"631":{"tf":1.0},"635":{"tf":1.4142135623730951},"639":{"tf":1.4142135623730951},"641":{"tf":1.0},"644":{"tf":1.4142135623730951},"648":{"tf":1.4142135623730951},"651":{"tf":2.23606797749979},"653":{"tf":1.4142135623730951},"658":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"69":{"tf":1.4142135623730951},"7":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"732":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"737":{"tf":1.0},"739":{"tf":1.0},"755":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"794":{"tf":1.0},"796":{"tf":1.0},"798":{"tf":1.0},"800":{"tf":1.0},"814":{"tf":1.0},"819":{"tf":1.0},"830":{"tf":1.0},"84":{"tf":1.0},"842":{"tf":1.4142135623730951},"843":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"856":{"tf":1.4142135623730951},"870":{"tf":1.0},"887":{"tf":1.0},"890":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.4142135623730951},"917":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":2.0},"934":{"tf":1.7320508075688772},"938":{"tf":1.4142135623730951},"940":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.7320508075688772},"956":{"tf":1.0},"957":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"980":{"tf":1.0},"983":{"tf":1.0},"990":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"322":{"tf":1.0},"325":{"tf":1.4142135623730951},"403":{"tf":1.0},"404":{"tf":1.0},"454":{"tf":1.4142135623730951},"518":{"tf":2.23606797749979}}}}}}}}},"i":{"c":{"df":4,"docs":{"171":{"tf":1.0},"418":{"tf":1.0},"564":{"tf":1.0},"765":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"171":{"tf":1.0}}}}},"df":8,"docs":{"130":{"tf":1.0},"198":{"tf":1.0},"3":{"tf":1.0},"570":{"tf":1.0},"8":{"tf":1.0},"84":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"60":{"tf":1.0},"813":{"tf":1.0}}}}}}},"df":30,"docs":{"1008":{"tf":1.0},"154":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"25":{"tf":1.0},"251":{"tf":1.0},"255":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"290":{"tf":1.0},"3":{"tf":1.0},"381":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"514":{"tf":1.0},"565":{"tf":1.0},"629":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"761":{"tf":1.4142135623730951},"804":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"919":{"tf":1.0},"95":{"tf":1.0}}}},"s":{"df":4,"docs":{"531":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"73":{"tf":1.0}},"s":{"df":6,"docs":{"199":{"tf":1.0},"3":{"tf":1.0},"437":{"tf":1.0},"483":{"tf":1.0},"600":{"tf":1.0},"762":{"tf":1.7320508075688772}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"826":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"b":{"df":0,"docs":{},"v":{"df":1,"docs":{"724":{"tf":1.0}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"141":{"tf":1.0}}}}}}},"v":{"df":37,"docs":{"107":{"tf":1.0},"118":{"tf":1.0},"120":{"tf":1.0},"147":{"tf":1.0},"238":{"tf":1.0},"294":{"tf":1.7320508075688772},"296":{"tf":1.0},"306":{"tf":1.0},"356":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":1.4142135623730951},"401":{"tf":1.0},"404":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"575":{"tf":1.0},"605":{"tf":1.0},"614":{"tf":1.0},"622":{"tf":1.0},"640":{"tf":1.0},"649":{"tf":1.4142135623730951},"663":{"tf":1.7320508075688772},"687":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.0},"757":{"tf":1.4142135623730951},"758":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.0},"919":{"tf":1.0},"927":{"tf":1.0},"94":{"tf":1.0},"973":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"991":{"tf":1.0}}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"108":{"tf":1.0},"3":{"tf":1.0},"567":{"tf":1.0},"599":{"tf":1.0}}}},"c":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"80":{"tf":1.0},"81":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"797":{"tf":1.0},"843":{"tf":1.0}}}},"d":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"142":{"tf":1.0},"777":{"tf":1.0}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"261":{"tf":1.0},"511":{"tf":1.0}}}}}}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.4142135623730951},"234":{"tf":1.0},"267":{"tf":1.0},"467":{"tf":1.0},"573":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"818":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":5,"docs":{"1003":{"tf":1.0},"124":{"tf":1.0},"206":{"tf":1.0},"776":{"tf":1.0},"881":{"tf":1.0}}}}}}},"i":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"108":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"u":{"d":{"df":99,"docs":{"1014":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.4142135623730951},"126":{"tf":1.0},"127":{"tf":1.0},"170":{"tf":1.0},"18":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.7320508075688772},"234":{"tf":1.4142135623730951},"24":{"tf":1.0},"244":{"tf":1.0},"254":{"tf":1.0},"270":{"tf":1.7320508075688772},"272":{"tf":1.4142135623730951},"28":{"tf":1.0},"282":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"302":{"tf":1.0},"312":{"tf":1.0},"315":{"tf":1.0},"345":{"tf":1.0},"35":{"tf":1.0},"364":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.7320508075688772},"374":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"40":{"tf":1.0},"402":{"tf":1.4142135623730951},"403":{"tf":1.4142135623730951},"408":{"tf":1.0},"409":{"tf":1.0},"422":{"tf":1.0},"450":{"tf":2.0},"46":{"tf":1.4142135623730951},"500":{"tf":1.7320508075688772},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"516":{"tf":1.4142135623730951},"521":{"tf":2.23606797749979},"526":{"tf":2.6457513110645907},"528":{"tf":1.0},"532":{"tf":1.0},"573":{"tf":1.0},"585":{"tf":1.0},"619":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"635":{"tf":1.4142135623730951},"64":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"704":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"77":{"tf":1.0},"796":{"tf":1.0},"84":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.7320508075688772},"849":{"tf":1.0},"85":{"tf":1.0},"853":{"tf":1.0},"870":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"912":{"tf":1.4142135623730951},"941":{"tf":1.0},"943":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"958":{"tf":1.0},"960":{"tf":1.0},"964":{"tf":1.0},"973":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"df":6,"docs":{"411":{"tf":1.0},"450":{"tf":1.0},"46":{"tf":1.0},"513":{"tf":1.0},"516":{"tf":1.0},"526":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"m":{"df":5,"docs":{"267":{"tf":1.7320508075688772},"466":{"tf":1.0},"69":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"763":{"tf":1.0}}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"842":{"tf":1.0},"850":{"tf":1.0}}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"267":{"tf":1.0},"325":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"344":{"tf":1.0},"365":{"tf":1.0},"427":{"tf":1.0},"536":{"tf":1.0},"75":{"tf":1.0},"933":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"152":{"tf":1.0},"514":{"tf":1.0},"567":{"tf":1.4142135623730951},"615":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"945":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"108":{"tf":1.0},"151":{"tf":1.0},"521":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":64,"docs":{"1004":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"190":{"tf":1.0},"193":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"213":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.7320508075688772},"234":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.7320508075688772},"40":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"42":{"tf":1.0},"420":{"tf":1.0},"422":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"437":{"tf":1.0},"469":{"tf":1.0},"507":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"61":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"729":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.7320508075688772},"749":{"tf":1.0},"751":{"tf":2.0},"752":{"tf":1.7320508075688772},"773":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"779":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"804":{"tf":1.0},"807":{"tf":1.4142135623730951},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"885":{"tf":1.0},"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"907":{"tf":1.0},"912":{"tf":1.4142135623730951},"945":{"tf":1.0},"962":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"373":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"208":{"tf":1.0},"322":{"tf":1.0},"334":{"tf":1.4142135623730951},"721":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"78":{"tf":1.4142135623730951}}}}}}}},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"1004":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":4,"docs":{"131":{"tf":1.0},"39":{"tf":1.0},"574":{"tf":1.0},"720":{"tf":1.0}}}}},"d":{"df":0,"docs":{},"e":{"df":5,"docs":{"128":{"tf":1.0},"450":{"tf":1.0},"479":{"tf":1.0},"78":{"tf":1.0},"84":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"199":{"tf":1.0},"206":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":7,"docs":{"204":{"tf":1.0},"417":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.4142135623730951},"934":{"tf":1.0}}},"df":0,"docs":{}}}},"x":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}},"df":28,"docs":{"132":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"18":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"221":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.7320508075688772},"438":{"tf":1.0},"439":{"tf":3.605551275463989},"450":{"tf":2.449489742783178},"520":{"tf":2.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.4142135623730951},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"633":{"tf":2.0},"634":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0},"804":{"tf":1.4142135623730951},"83":{"tf":2.0},"85":{"tf":1.0},"88":{"tf":1.0}}}},"i":{"c":{"df":19,"docs":{"221":{"tf":1.0},"222":{"tf":1.4142135623730951},"254":{"tf":1.0},"267":{"tf":1.0},"273":{"tf":1.7320508075688772},"341":{"tf":1.4142135623730951},"427":{"tf":1.0},"431":{"tf":1.0},"438":{"tf":1.4142135623730951},"439":{"tf":1.0},"483":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.4142135623730951},"615":{"tf":1.0},"735":{"tf":3.605551275463989},"761":{"tf":1.0},"8":{"tf":1.0},"847":{"tf":1.0},"913":{"tf":1.0}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"430":{"tf":1.0},"524":{"tf":1.0},"575":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"46":{"tf":1.0}}}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"u":{"df":21,"docs":{"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.0},"373":{"tf":1.0},"411":{"tf":1.0},"459":{"tf":1.0},"469":{"tf":1.0},"485":{"tf":1.0},"514":{"tf":1.0},"574":{"tf":1.0},"600":{"tf":1.4142135623730951},"700":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0},"797":{"tf":1.0},"844":{"tf":1.0},"876":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"467":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":3,"docs":{"141":{"tf":1.0},"732":{"tf":1.0},"779":{"tf":1.0}}}},"df":0,"docs":{}}}},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"346":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"761":{"tf":1.0}}}}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":14,"docs":{"234":{"tf":1.0},"267":{"tf":2.0},"926":{"tf":1.7320508075688772},"927":{"tf":1.7320508075688772},"928":{"tf":3.4641016151377544},"929":{"tf":1.0},"931":{"tf":2.0},"932":{"tf":3.872983346207417},"933":{"tf":2.0},"934":{"tf":1.4142135623730951},"935":{"tf":1.0},"936":{"tf":1.7320508075688772},"937":{"tf":1.4142135623730951},"939":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"231":{"tf":1.0},"933":{"tf":1.4142135623730951},"934":{"tf":1.0}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"933":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"w":{"/":{"3":{"3":{"0":{"1":{"df":1,"docs":{"937":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"267":{"tf":1.7320508075688772}}}},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":5,"docs":{"265":{"tf":1.0},"267":{"tf":1.0},"342":{"tf":1.4142135623730951},"459":{"tf":1.4142135623730951},"797":{"tf":1.0}}},"df":0,"docs":{}}},"x":{"df":1,"docs":{"414":{"tf":1.0}}}}},"o":{"df":8,"docs":{"121":{"tf":1.4142135623730951},"22":{"tf":1.0},"321":{"tf":1.0},"343":{"tf":1.0},"375":{"tf":1.0},"6":{"tf":1.0},"614":{"tf":1.0},"872":{"tf":1.0}},"r":{"df":0,"docs":{},"m":{"df":42,"docs":{"203":{"tf":2.449489742783178},"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"216":{"tf":1.0},"218":{"tf":1.0},"222":{"tf":1.7320508075688772},"272":{"tf":1.4142135623730951},"343":{"tf":1.7320508075688772},"348":{"tf":1.0},"349":{"tf":1.4142135623730951},"375":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"5":{"tf":1.4142135623730951},"513":{"tf":1.0},"516":{"tf":1.4142135623730951},"519":{"tf":3.3166247903554},"520":{"tf":1.7320508075688772},"521":{"tf":2.8284271247461903},"522":{"tf":3.605551275463989},"523":{"tf":2.23606797749979},"524":{"tf":1.0},"525":{"tf":1.0},"528":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"568":{"tf":1.0},"574":{"tf":1.0},"6":{"tf":1.7320508075688772},"628":{"tf":1.0},"631":{"tf":1.0},"634":{"tf":1.0},"64":{"tf":1.0},"710":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"8":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.0},"895":{"tf":1.0},"931":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":9,"docs":{"178":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"233":{"tf":1.0},"236":{"tf":1.0},"249":{"tf":1.4142135623730951},"565":{"tf":1.0},"571":{"tf":1.0},"853":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"77":{"tf":1.0}}}},"df":0,"docs":{}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"267":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":2.0},"285":{"tf":1.0},"291":{"tf":1.4142135623730951},"3":{"tf":1.0},"346":{"tf":1.0},"722":{"tf":1.0},"739":{"tf":1.0},"85":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"171":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"83":{"tf":1.0}}},"z":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"284":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":3,"docs":{"284":{"tf":1.4142135623730951},"286":{"tf":1.0},"288":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":8,"docs":{"598":{"tf":1.7320508075688772},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"692":{"tf":1.0},"698":{"tf":1.7320508075688772},"701":{"tf":1.0},"705":{"tf":1.7320508075688772},"706":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":1,"docs":{"693":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}}}}}}}}}}},"df":58,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"161":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"213":{"tf":1.4142135623730951},"214":{"tf":1.0},"250":{"tf":1.0},"257":{"tf":1.0},"270":{"tf":1.0},"277":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.0},"364":{"tf":1.4142135623730951},"412":{"tf":1.0},"428":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":2.0},"525":{"tf":1.7320508075688772},"537":{"tf":1.0},"564":{"tf":1.0},"583":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"609":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"642":{"tf":1.0},"696":{"tf":1.0},"709":{"tf":1.0},"718":{"tf":1.0},"72":{"tf":1.4142135623730951},"725":{"tf":1.0},"75":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":2.0},"815":{"tf":1.0},"83":{"tf":1.7320508075688772},"831":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":1.4142135623730951},"909":{"tf":1.0},"911":{"tf":1.0},"932":{"tf":1.0},"939":{"tf":1.0}}}}},"k":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":7,"docs":{"221":{"tf":1.4142135623730951},"523":{"tf":1.0},"614":{"tf":1.4142135623730951},"615":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.7320508075688772},"786":{"tf":1.0}}}},"o":{"df":0,"docs":{},"v":{"df":5,"docs":{"199":{"tf":2.0},"426":{"tf":1.0},"515":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":21,"docs":{"22":{"tf":2.449489742783178},"229":{"tf":1.0},"23":{"tf":1.4142135623730951},"244":{"tf":1.0},"30":{"tf":1.0},"333":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":3.1622776601683795},"346":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"45":{"tf":1.0},"516":{"tf":1.7320508075688772},"633":{"tf":1.0},"637":{"tf":1.0},"735":{"tf":2.449489742783178},"898":{"tf":1.0},"931":{"tf":1.0},"94":{"tf":1.0},"948":{"tf":1.0},"95":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"142":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":3,"docs":{"169":{"tf":1.0},"208":{"tf":1.0},"346":{"tf":1.0}}}}},"i":{"d":{"df":2,"docs":{"555":{"tf":1.0},"9":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"325":{"tf":1.0},"364":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"849":{"tf":1.0}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"932":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"r":{"df":2,"docs":{"560":{"tf":1.0},"738":{"tf":1.0}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"141":{"tf":1.0}}}},"df":0,"docs":{},"n":{"c":{"df":16,"docs":{"108":{"tf":1.0},"171":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.7320508075688772},"325":{"tf":1.0},"346":{"tf":1.0},"363":{"tf":1.0},"5":{"tf":1.4142135623730951},"6":{"tf":3.1622776601683795},"7":{"tf":1.0},"776":{"tf":1.4142135623730951},"831":{"tf":1.0},"9":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":15,"docs":{"195":{"tf":1.0},"203":{"tf":4.0},"204":{"tf":2.0},"205":{"tf":2.449489742783178},"206":{"tf":2.449489742783178},"207":{"tf":2.8284271247461903},"208":{"tf":2.0},"212":{"tf":1.4142135623730951},"213":{"tf":1.4142135623730951},"218":{"tf":1.7320508075688772},"221":{"tf":2.0},"222":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.7320508075688772},"909":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"221":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{},"i":{"df":2,"docs":{"48":{"tf":1.0},"534":{"tf":1.4142135623730951}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"568":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}}}}}},"df":1,"docs":{"208":{"tf":2.23606797749979}},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"y":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"i":{"df":0,"docs":{},"o":{"df":1,"docs":{"208":{"tf":2.449489742783178}}}}}}}},"t":{"df":1,"docs":{"269":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":33,"docs":{"124":{"tf":1.0},"127":{"tf":1.0},"180":{"tf":1.0},"203":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.0},"292":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"52":{"tf":1.0},"522":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.0},"614":{"tf":1.0},"617":{"tf":1.0},"62":{"tf":1.0},"634":{"tf":1.0},"666":{"tf":1.4142135623730951},"680":{"tf":1.0},"696":{"tf":1.7320508075688772},"706":{"tf":1.0},"72":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.3166247903554},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"814":{"tf":1.0},"84":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":53,"docs":{"1":{"tf":1.0},"16":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"218":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"269":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.4142135623730951},"372":{"tf":1.0},"5":{"tf":1.0},"51":{"tf":1.0},"598":{"tf":1.7320508075688772},"599":{"tf":1.4142135623730951},"6":{"tf":3.7416573867739413},"600":{"tf":2.23606797749979},"602":{"tf":5.0},"605":{"tf":1.7320508075688772},"606":{"tf":1.4142135623730951},"609":{"tf":1.4142135623730951},"614":{"tf":1.0},"615":{"tf":1.0},"617":{"tf":1.4142135623730951},"619":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.0},"653":{"tf":2.0},"654":{"tf":1.7320508075688772},"660":{"tf":1.7320508075688772},"665":{"tf":1.7320508075688772},"668":{"tf":2.0},"669":{"tf":1.0},"670":{"tf":1.4142135623730951},"673":{"tf":1.7320508075688772},"692":{"tf":1.0},"693":{"tf":1.0},"694":{"tf":1.7320508075688772},"696":{"tf":1.7320508075688772},"698":{"tf":1.7320508075688772},"7":{"tf":1.0},"701":{"tf":1.7320508075688772},"705":{"tf":2.23606797749979},"786":{"tf":1.7320508075688772},"8":{"tf":1.0},"83":{"tf":1.0},"9":{"tf":1.0},"974":{"tf":1.0},"975":{"tf":1.0},"978":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":2,"docs":{"267":{"tf":1.0},"537":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"t":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"994":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":4,"docs":{"332":{"tf":2.6457513110645907},"346":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.0}},"r":{"df":31,"docs":{"12":{"tf":1.0},"185":{"tf":1.0},"205":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"234":{"tf":1.0},"237":{"tf":1.0},"30":{"tf":1.0},"326":{"tf":1.0},"365":{"tf":1.0},"378":{"tf":1.0},"411":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"564":{"tf":1.0},"651":{"tf":1.0},"673":{"tf":1.0},"700":{"tf":1.0},"771":{"tf":1.0},"855":{"tf":1.0},"933":{"tf":1.0},"935":{"tf":1.0},"938":{"tf":1.4142135623730951},"942":{"tf":1.4142135623730951},"956":{"tf":1.0},"958":{"tf":1.0},"961":{"tf":1.7320508075688772},"964":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}}},"n":{"d":{"df":15,"docs":{"207":{"tf":1.4142135623730951},"310":{"tf":1.0},"324":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.0},"40":{"tf":1.0},"573":{"tf":1.0},"628":{"tf":1.0},"822":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"887":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"983":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":3,"docs":{"340":{"tf":1.0},"435":{"tf":1.0},"962":{"tf":1.0}}},"t":{"df":3,"docs":{"723":{"tf":1.0},"777":{"tf":1.0},"911":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"341":{"tf":1.4142135623730951},"418":{"tf":1.0}}}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":21,"docs":{"125":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"212":{"tf":1.0},"26":{"tf":1.0},"30":{"tf":1.0},"322":{"tf":1.0},"362":{"tf":1.0},"369":{"tf":1.0},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":1.4142135623730951},"694":{"tf":1.0},"771":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"894":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":18,"docs":{"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"273":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"498":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"71":{"tf":1.0},"724":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0},"971":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}}}}}},"f":{"a":{"c":{"df":46,"docs":{"1011":{"tf":1.0},"1012":{"tf":1.0},"119":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"203":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.7320508075688772},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":2.449489742783178},"220":{"tf":1.0},"226":{"tf":1.0},"289":{"tf":1.0},"307":{"tf":1.0},"322":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.4142135623730951},"362":{"tf":2.449489742783178},"366":{"tf":1.0},"370":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"452":{"tf":1.0},"460":{"tf":1.0},"48":{"tf":1.0},"515":{"tf":1.0},"609":{"tf":1.0},"659":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"736":{"tf":1.0},"804":{"tf":1.0},"88":{"tf":1.0},"902":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"961":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"198":{"tf":1.0},"284":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"205":{"tf":1.0},"697":{"tf":1.0},"786":{"tf":1.7320508075688772}}}}},"l":{"a":{"c":{"df":3,"docs":{"204":{"tf":2.0},"205":{"tf":1.0},"208":{"tf":2.23606797749979}},"e":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"d":{"df":2,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"204":{"tf":1.7320508075688772},"207":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":5,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"402":{"tf":1.0},"696":{"tf":1.4142135623730951},"956":{"tf":1.0}}}}},"df":1,"docs":{"150":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"n":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"634":{"tf":1.0}}}}}}}},"df":6,"docs":{"515":{"tf":1.0},"522":{"tf":1.0},"6":{"tf":1.0},"693":{"tf":1.0},"737":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"198":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"12":{"tf":1.0},"313":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"54":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":12,"docs":{"199":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"5":{"tf":1.0},"539":{"tf":1.0},"545":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.4142135623730951}}}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"928":{"tf":1.0}}}}}},"v":{"df":2,"docs":{"200":{"tf":1.0},"814":{"tf":1.0}}}}},"r":{"a":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{},"i":{"c":{"a":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"d":{"df":0,"docs":{},"u":{"c":{"df":90,"docs":{"1002":{"tf":1.0},"114":{"tf":1.0},"115":{"tf":1.0},"117":{"tf":1.0},"12":{"tf":1.0},"128":{"tf":1.0},"137":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"150":{"tf":1.4142135623730951},"152":{"tf":1.4142135623730951},"154":{"tf":1.7320508075688772},"163":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":1.0},"17":{"tf":1.7320508075688772},"171":{"tf":1.0},"178":{"tf":1.0},"18":{"tf":1.0},"181":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"217":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"225":{"tf":1.0},"267":{"tf":1.0},"280":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"305":{"tf":1.0},"334":{"tf":1.0},"354":{"tf":1.0},"358":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"390":{"tf":1.4142135623730951},"397":{"tf":1.7320508075688772},"400":{"tf":1.4142135623730951},"412":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"461":{"tf":1.0},"486":{"tf":1.4142135623730951},"496":{"tf":1.0},"519":{"tf":1.0},"53":{"tf":1.0},"537":{"tf":1.0},"548":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":1.7320508075688772},"586":{"tf":1.4142135623730951},"588":{"tf":1.0},"594":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"61":{"tf":1.4142135623730951},"62":{"tf":1.0},"627":{"tf":1.4142135623730951},"631":{"tf":1.0},"633":{"tf":1.0},"639":{"tf":1.0},"641":{"tf":1.0},"648":{"tf":1.0},"665":{"tf":1.4142135623730951},"72":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":2.0},"77":{"tf":1.0},"773":{"tf":2.0},"788":{"tf":1.4142135623730951},"790":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"819":{"tf":1.0},"821":{"tf":1.0},"829":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"93":{"tf":1.4142135623730951},"942":{"tf":1.0},"944":{"tf":1.0},"949":{"tf":1.0},"951":{"tf":1.0},"953":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"966":{"tf":1.0},"996":{"tf":1.0}},"t":{"df":15,"docs":{"0":{"tf":1.0},"169":{"tf":1.0},"269":{"tf":1.0},"322":{"tf":1.4142135623730951},"334":{"tf":1.0},"335":{"tf":1.0},"359":{"tf":1.0},"371":{"tf":1.0},"412":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"95":{"tf":1.0},"968":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"928":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"/":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"b":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"439":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":12,"docs":{"152":{"tf":1.4142135623730951},"293":{"tf":1.0},"296":{"tf":1.4142135623730951},"303":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"450":{"tf":1.0},"635":{"tf":1.0},"735":{"tf":2.23606797749979},"761":{"tf":1.4142135623730951},"944":{"tf":1.0},"948":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"944":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"r":{"c":{"df":0,"docs":{},"h":{"'":{"df":1,"docs":{"784":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":1,"docs":{"284":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"267":{"tf":1.0},"749":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"274":{"tf":1.0}},"i":{"df":0,"docs":{},"g":{"df":2,"docs":{"363":{"tf":1.0},"365":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"199":{"tf":1.0},"418":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}},"o":{"df":0,"docs":{},"k":{"df":4,"docs":{"108":{"tf":1.0},"24":{"tf":1.0},"284":{"tf":1.0},"30":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"v":{"df":16,"docs":{"108":{"tf":1.0},"112":{"tf":1.0},"375":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.4142135623730951},"698":{"tf":1.0},"705":{"tf":1.0},"739":{"tf":1.0},"745":{"tf":1.0},"771":{"tf":1.0},"786":{"tf":1.0},"8":{"tf":1.0},"809":{"tf":1.0},"951":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"231":{"tf":1.0},"234":{"tf":2.449489742783178},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.0},"239":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":12,"docs":{"258":{"tf":1.0},"259":{"tf":1.0},"487":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"492":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"766":{"tf":1.0}}}}}}}},"s":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"d":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":10,"docs":{"255":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"701":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"817":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":4,"docs":{"373":{"tf":1.0},"494":{"tf":1.0},"63":{"tf":1.0},"836":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"264":{"tf":1.0},"267":{"tf":1.0}}},"df":0,"docs":{}}},"df":54,"docs":{"127":{"tf":1.0},"13":{"tf":1.0},"152":{"tf":2.23606797749979},"155":{"tf":1.4142135623730951},"161":{"tf":1.0},"163":{"tf":1.0},"17":{"tf":1.4142135623730951},"193":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"267":{"tf":1.0},"28":{"tf":1.4142135623730951},"29":{"tf":1.4142135623730951},"291":{"tf":1.0},"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"375":{"tf":1.0},"409":{"tf":1.0},"427":{"tf":1.0},"440":{"tf":1.0},"447":{"tf":1.0},"450":{"tf":1.0},"51":{"tf":1.0},"53":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"568":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.4142135623730951},"630":{"tf":1.0},"639":{"tf":1.0},"67":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"799":{"tf":1.0},"80":{"tf":1.0},"826":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.4142135623730951},"859":{"tf":1.0},"864":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"88":{"tf":1.0},"912":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"998":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"234":{"tf":1.0}}}}}}},"t":{"'":{"df":26,"docs":{"126":{"tf":1.0},"267":{"tf":1.7320508075688772},"3":{"tf":1.0},"32":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"422":{"tf":1.0},"438":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"522":{"tf":1.0},"697":{"tf":1.0},"724":{"tf":1.0},"762":{"tf":1.4142135623730951},"773":{"tf":1.0},"786":{"tf":1.0},"813":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.7320508075688772},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"887":{"tf":1.0}},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}}}}}}},"df":15,"docs":{"205":{"tf":1.7320508075688772},"223":{"tf":1.0},"343":{"tf":1.4142135623730951},"347":{"tf":1.0},"402":{"tf":1.7320508075688772},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"417":{"tf":1.4142135623730951},"45":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.7320508075688772},"485":{"tf":1.4142135623730951},"758":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":2.0}}},"r":{"df":17,"docs":{"136":{"tf":1.4142135623730951},"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"141":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"147":{"tf":1.0},"149":{"tf":1.4142135623730951},"199":{"tf":1.0},"257":{"tf":1.0},"507":{"tf":1.0},"523":{"tf":1.0},"573":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"928":{"tf":1.0},"992":{"tf":1.0}}}},"h":{"df":1,"docs":{"717":{"tf":1.0}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":31,"docs":{"15":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"198":{"tf":1.0},"222":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"300":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.4142135623730951},"586":{"tf":1.0},"62":{"tf":1.0},"641":{"tf":1.0},"697":{"tf":1.0},"7":{"tf":1.4142135623730951},"700":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":1.4142135623730951},"777":{"tf":1.0},"788":{"tf":1.0},"855":{"tf":1.0},"875":{"tf":2.0},"879":{"tf":1.0}}}}}}},"v":{"df":3,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}},"x":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}}},"z":{"df":1,"docs":{"762":{"tf":1.0}}}},"j":{"a":{"df":0,"docs":{},"m":{"'":{"df":10,"docs":{"38":{"tf":1.4142135623730951},"40":{"tf":1.4142135623730951},"45":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.4142135623730951},"49":{"tf":1.4142135623730951},"51":{"tf":1.0},"52":{"tf":1.0},"54":{"tf":1.4142135623730951},"725":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"38":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":18,"docs":{"111":{"tf":1.0},"38":{"tf":2.6457513110645907},"39":{"tf":1.4142135623730951},"40":{"tf":2.23606797749979},"41":{"tf":1.4142135623730951},"42":{"tf":1.0},"43":{"tf":1.0},"44":{"tf":1.7320508075688772},"45":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"47":{"tf":2.0},"48":{"tf":1.0},"49":{"tf":1.4142135623730951},"50":{"tf":1.7320508075688772},"52":{"tf":1.4142135623730951},"53":{"tf":1.7320508075688772},"54":{"tf":1.7320508075688772},"928":{"tf":1.4142135623730951}}},"n":{"df":1,"docs":{"312":{"tf":1.0}},"u":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"418":{"tf":1.0},"841":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"45":{"tf":1.4142135623730951},"47":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"244":{"tf":1.0},"709":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"l":{"df":1,"docs":{"857":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"663":{"tf":1.0},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"983":{"tf":1.0},"987":{"tf":1.0}}},"y":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"17":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"b":{"df":2,"docs":{"467":{"tf":1.0},"515":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":5,"docs":{"229":{"tf":1.0},"268":{"tf":1.0},"366":{"tf":1.0},"410":{"tf":1.0},"465":{"tf":1.0}}},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"234":{"tf":1.0},"272":{"tf":1.0},"315":{"tf":1.0},"471":{"tf":1.0},"576":{"tf":1.0}},"t":{"df":1,"docs":{"876":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"n":{"a":{"df":3,"docs":{"263":{"tf":1.0},"563":{"tf":1.0},"771":{"tf":1.0}}},"df":0,"docs":{}}},"s":{"/":{"df":0,"docs":{},"t":{"df":1,"docs":{"19":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"50":{"tf":1.0},"512":{"tf":1.0},"522":{"tf":1.0}}}}},"u":{"d":{"df":0,"docs":{},"g":{"df":4,"docs":{"207":{"tf":1.4142135623730951},"45":{"tf":1.0},"761":{"tf":1.0},"895":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":17,"docs":{"1002":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"252":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"741":{"tf":1.0},"974":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"576":{"tf":1.0}}}},"n":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"195":{"tf":1.0}}},"k":{"df":1,"docs":{"863":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":1,"docs":{"410":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":2,"docs":{"1006":{"tf":1.0},"500":{"tf":1.4142135623730951}},"i":{"df":2,"docs":{"54":{"tf":1.0},"575":{"tf":1.0}}}}}}}}},"k":{"*":{"df":0,"docs":{},"n":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}}},"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"a":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"a":{"df":8,"docs":{"252":{"tf":1.7320508075688772},"255":{"tf":1.0},"257":{"tf":1.0},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"a":{"df":1,"docs":{"855":{"tf":1.0}}},"df":0,"docs":{}}}},"b":{"df":1,"docs":{"517":{"tf":1.0}}},"df":2,"docs":{"436":{"tf":1.0},"885":{"tf":2.8284271247461903}},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"2":{"5":{"6":{"df":3,"docs":{"50":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":18,"docs":{"121":{"tf":1.0},"208":{"tf":1.0},"315":{"tf":1.0},"407":{"tf":1.4142135623730951},"439":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.4142135623730951},"551":{"tf":1.0},"567":{"tf":1.0},"631":{"tf":1.0},"643":{"tf":1.0},"660":{"tf":1.0},"67":{"tf":1.0},"723":{"tf":1.4142135623730951},"761":{"tf":1.0},"881":{"tf":1.0},"932":{"tf":1.0},"944":{"tf":1.0}}}},"p":{"df":0,"docs":{},"t":{"df":5,"docs":{"255":{"tf":1.0},"349":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"505":{"tf":1.0}}}},"y":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"735":{"tf":3.605551275463989}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":54,"docs":{"108":{"tf":1.0},"150":{"tf":1.4142135623730951},"151":{"tf":1.4142135623730951},"154":{"tf":1.7320508075688772},"155":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"25":{"tf":1.0},"252":{"tf":2.449489742783178},"255":{"tf":2.0},"257":{"tf":1.4142135623730951},"296":{"tf":1.0},"341":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"38":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":2.8284271247461903},"453":{"tf":2.8284271247461903},"455":{"tf":2.0},"456":{"tf":1.0},"459":{"tf":2.0},"46":{"tf":1.7320508075688772},"461":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"5":{"tf":2.23606797749979},"501":{"tf":2.8284271247461903},"505":{"tf":2.0},"507":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"553":{"tf":1.0},"555":{"tf":1.0},"565":{"tf":1.0},"6":{"tf":2.8284271247461903},"629":{"tf":1.0},"735":{"tf":5.916079783099616},"759":{"tf":2.8284271247461903},"761":{"tf":4.47213595499958},"763":{"tf":1.4142135623730951},"81":{"tf":1.4142135623730951},"829":{"tf":1.7320508075688772},"876":{"tf":1.0},"894":{"tf":1.4142135623730951},"932":{"tf":2.0},"94":{"tf":1.0},"944":{"tf":1.0},"95":{"tf":2.0},"961":{"tf":1.0},"992":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"80":{"tf":1.4142135623730951},"81":{"tf":2.23606797749979},"83":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"6":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":1,"docs":{"6":{"tf":1.4142135623730951}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"&":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"735":{"tf":1.0},"95":{"tf":1.7320508075688772}}}}}}}},"i":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"244":{"tf":1.0},"926":{"tf":1.0}}}},"b":{"df":4,"docs":{"257":{"tf":1.0},"436":{"tf":1.4142135623730951},"507":{"tf":1.0},"515":{"tf":1.0}}},"df":0,"docs":{},"n":{"d":{"df":11,"docs":{"108":{"tf":1.0},"3":{"tf":1.0},"453":{"tf":1.7320508075688772},"521":{"tf":1.0},"527":{"tf":1.0},"531":{"tf":1.0},"534":{"tf":1.4142135623730951},"54":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"63":{"tf":1.0}}},"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"187":{"tf":1.0}}}},"df":0,"docs":{},"w":{"df":28,"docs":{"257":{"tf":1.0},"303":{"tf":1.0},"373":{"tf":1.0},"391":{"tf":1.0},"439":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"619":{"tf":1.0},"669":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"846":{"tf":1.0},"854":{"tf":1.0},"895":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"844":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"df":20,"docs":{"126":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"220":{"tf":1.0},"255":{"tf":1.0},"335":{"tf":1.0},"348":{"tf":1.0},"362":{"tf":1.7320508075688772},"368":{"tf":1.0},"373":{"tf":1.0},"439":{"tf":1.0},"514":{"tf":1.4142135623730951},"521":{"tf":1.0},"6":{"tf":1.0},"735":{"tf":2.0},"777":{"tf":1.0},"829":{"tf":1.4142135623730951},"842":{"tf":1.0},"874":{"tf":1.0}}}}}},"r":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"247":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0},"827":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"m":{"df":9,"docs":{"316":{"tf":1.0},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"843":{"tf":1.0},"844":{"tf":1.0},"849":{"tf":1.0},"862":{"tf":1.0},"914":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"400":{"tf":1.0}}}}}},"s":{"a":{"df":0,"docs":{},"m":{"a":{"'":{"df":9,"docs":{"375":{"tf":1.0},"376":{"tf":1.0},"843":{"tf":1.4142135623730951},"846":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"711":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":39,"docs":{"128":{"tf":1.0},"253":{"tf":1.0},"312":{"tf":1.0},"314":{"tf":1.0},"366":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":2.8284271247461903},"385":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"418":{"tf":1.7320508075688772},"423":{"tf":1.4142135623730951},"429":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"600":{"tf":1.4142135623730951},"697":{"tf":1.0},"759":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":2.449489742783178},"848":{"tf":1.4142135623730951},"849":{"tf":1.4142135623730951},"852":{"tf":1.7320508075688772},"853":{"tf":1.0},"857":{"tf":1.0},"859":{"tf":1.0},"862":{"tf":1.0},"869":{"tf":1.0},"909":{"tf":1.0},"911":{"tf":2.0},"912":{"tf":3.3166247903554},"913":{"tf":1.7320508075688772},"914":{"tf":1.7320508075688772},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.7320508075688772}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"'":{"df":1,"docs":{"841":{"tf":1.0}}},"df":2,"docs":{"841":{"tf":1.4142135623730951},"842":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"ö":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"150":{"tf":1.0},"451":{"tf":1.0},"584":{"tf":1.0}}}}}},"df":0,"docs":{}}},"l":{".":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":0,"docs":{},"s":{")":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":0,"docs":{},"s":{")":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"1":{"7":{"6":{"2":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"39":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"39":{"tf":1.0},"48":{"tf":1.0}}},"3":{"4":{"0":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"7":{"5":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"2":{"c":{"1":{"5":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"b":{"df":1,"docs":{"244":{"tf":1.0}},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"84":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"k":{"df":10,"docs":{"234":{"tf":1.0},"296":{"tf":1.0},"725":{"tf":1.0},"735":{"tf":1.0},"81":{"tf":1.0},"874":{"tf":1.0},"917":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"204":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"g":{"df":7,"docs":{"651":{"tf":1.0},"679":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"687":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.0}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"g":{"df":30,"docs":{"184":{"tf":1.0},"196":{"tf":1.0},"201":{"tf":1.0},"230":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"375":{"tf":1.0},"436":{"tf":1.0},"444":{"tf":1.0},"505":{"tf":1.4142135623730951},"515":{"tf":1.0},"522":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951},"571":{"tf":1.0},"577":{"tf":1.4142135623730951},"619":{"tf":1.0},"683":{"tf":1.0},"697":{"tf":1.0},"75":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"774":{"tf":1.0},"810":{"tf":1.0},"833":{"tf":1.0},"850":{"tf":1.0},"87":{"tf":1.0},"990":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":9,"docs":{"376":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"577":{"tf":1.0},"735":{"tf":1.4142135623730951},"779":{"tf":1.0},"797":{"tf":1.4142135623730951},"832":{"tf":1.0},"885":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"571":{"tf":1.4142135623730951},"843":{"tf":1.0},"850":{"tf":1.0},"992":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"292":{"tf":1.4142135623730951}}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"222":{"tf":1.4142135623730951}}}}}}}},"df":25,"docs":{"188":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"333":{"tf":1.4142135623730951},"343":{"tf":1.4142135623730951},"346":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"45":{"tf":2.449489742783178},"46":{"tf":1.0},"47":{"tf":1.0},"49":{"tf":1.7320508075688772},"503":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.4142135623730951},"721":{"tf":1.0},"761":{"tf":1.0},"815":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0},"932":{"tf":1.4142135623730951}},"i":{"c":{".":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"df":0,"docs":{},"z":{"df":1,"docs":{"911":{"tf":1.0}}}}}},"df":3,"docs":{"941":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"342":{"tf":1.0}},"n":{"c":{"df":4,"docs":{"138":{"tf":1.0},"207":{"tf":1.0},"218":{"tf":1.0},"640":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"r":{"df":19,"docs":{"154":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.0},"22":{"tf":1.0},"441":{"tf":1.0},"486":{"tf":1.0},"567":{"tf":1.4142135623730951},"570":{"tf":1.7320508075688772},"717":{"tf":1.0},"732":{"tf":1.0},"777":{"tf":1.0},"809":{"tf":1.0},"814":{"tf":1.0},"847":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"911":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"191":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"67":{"tf":1.0},"881":{"tf":1.0},"895":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"371":{"tf":1.0}}},"df":2,"docs":{"776":{"tf":1.0},"831":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":11,"docs":{"108":{"tf":1.0},"209":{"tf":1.0},"277":{"tf":1.0},"303":{"tf":1.0},"367":{"tf":1.0},"371":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.0},"644":{"tf":1.0},"797":{"tf":1.0}}}},"df":0,"docs":{}}},"w":{"df":1,"docs":{"912":{"tf":1.0}}},"y":{"df":2,"docs":{"326":{"tf":1.0},"361":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"1004":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"430":{"tf":1.0},"47":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"359":{"tf":1.0},"848":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"151":{"tf":1.7320508075688772},"163":{"tf":1.0},"523":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0}}}}}},"z":{"df":0,"docs":{},"i":{"df":2,"docs":{"69":{"tf":1.0},"724":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"880":{"tf":1.0}}}}}}},"df":1,"docs":{"749":{"tf":1.0}},"e":{"a":{"d":{"df":30,"docs":{"1004":{"tf":1.0},"113":{"tf":1.0},"126":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"170":{"tf":1.4142135623730951},"19":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"505":{"tf":1.0},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.4142135623730951},"574":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"779":{"tf":1.4142135623730951},"80":{"tf":1.0},"818":{"tf":1.0},"975":{"tf":1.0},"979":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"204":{"tf":1.0},"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"df":4,"docs":{"204":{"tf":1.7320508075688772},"207":{"tf":2.23606797749979},"213":{"tf":1.0},"773":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":1,"docs":{"78":{"tf":1.7320508075688772}}},"k":{"df":4,"docs":{"453":{"tf":1.0},"528":{"tf":1.4142135623730951},"723":{"tf":1.0},"934":{"tf":1.0}}},"s":{"df":18,"docs":{"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.7320508075688772},"205":{"tf":1.7320508075688772},"296":{"tf":2.0},"297":{"tf":1.0},"300":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"48":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":2.449489742783178},"911":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"/":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"203":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"v":{"df":9,"docs":{"203":{"tf":1.0},"231":{"tf":1.0},"255":{"tf":1.0},"525":{"tf":2.6457513110645907},"526":{"tf":1.0},"570":{"tf":1.0},"574":{"tf":1.0},"78":{"tf":1.0},"928":{"tf":1.0}}}},"b":{"1":{"2":{"8":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"1":{"df":1,"docs":{"485":{"tf":1.0}}},"2":{"df":1,"docs":{"485":{"tf":1.0}}},"3":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"df":2,"docs":{"161":{"tf":1.0},"54":{"tf":1.0}}},"df":1,"docs":{"722":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":1,"docs":{"182":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"t":{"(":{"1":{"df":1,"docs":{"749":{"tf":1.0}}},"\\":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"{":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.0}}},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"k":{"df":0,"docs":{},"k":{"df":1,"docs":{"879":{"tf":1.0}}}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":15,"docs":{"204":{"tf":1.0},"324":{"tf":1.0},"341":{"tf":1.4142135623730951},"358":{"tf":1.0},"525":{"tf":1.7320508075688772},"576":{"tf":1.0},"577":{"tf":1.0},"747":{"tf":1.7320508075688772},"748":{"tf":1.0},"749":{"tf":1.7320508075688772},"751":{"tf":1.4142135623730951},"776":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.4142135623730951},"976":{"tf":1.0}},"o":{"df":0,"docs":{},"v":{"df":5,"docs":{"375":{"tf":1.0},"653":{"tf":1.7320508075688772},"656":{"tf":1.0},"660":{"tf":1.0},"666":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"663":{"tf":1.0},"666":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"g":{"a":{"c":{"df":0,"docs":{},"i":{"df":4,"docs":{"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772}}}},"df":0,"docs":{},"l":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":2,"docs":{"602":{"tf":1.4142135623730951},"603":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":1,"docs":{"376":{"tf":1.0}}}},"t":{"df":1,"docs":{"349":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"a":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"514":{"tf":1.0}}}},"df":0,"docs":{}},"df":3,"docs":{"127":{"tf":1.4142135623730951},"567":{"tf":1.0},"858":{"tf":1.0}}}}}}},"n":{"d":{"df":1,"docs":{"372":{"tf":1.0}}},"df":2,"docs":{"455":{"tf":1.0},"522":{"tf":1.0}},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":1,"docs":{"333":{"tf":1.0}}},"df":21,"docs":{"170":{"tf":1.0},"204":{"tf":1.0},"25":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"26":{"tf":1.0},"332":{"tf":2.0},"347":{"tf":1.7320508075688772},"435":{"tf":1.0},"455":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.0},"632":{"tf":1.0},"743":{"tf":1.0},"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"895":{"tf":2.0},"896":{"tf":1.0},"898":{"tf":1.4142135623730951},"907":{"tf":1.0}},"i":{"df":3,"docs":{"296":{"tf":1.0},"55":{"tf":1.0},"942":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"73":{"tf":1.0}}}}}}},"q":{"df":1,"docs":{"749":{"tf":1.0}}},"s":{"df":0,"docs":{},"s":{"df":36,"docs":{"199":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":1.0},"223":{"tf":1.7320508075688772},"231":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.4142135623730951},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"375":{"tf":1.0},"470":{"tf":1.0},"513":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"631":{"tf":1.0},"66":{"tf":1.0},"683":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.7320508075688772},"724":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"895":{"tf":1.0},"916":{"tf":1.0},"919":{"tf":1.0},"932":{"tf":2.0},"976":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"777":{"tf":1.0}}}}}},"t":{"'":{"df":6,"docs":{"5":{"tf":1.4142135623730951},"568":{"tf":1.0},"60":{"tf":1.0},"749":{"tf":1.0},"878":{"tf":1.0},"931":{"tf":1.0}}},"df":5,"docs":{"267":{"tf":1.0},"280":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"749":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":25,"docs":{"163":{"tf":1.4142135623730951},"184":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"212":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"29":{"tf":1.4142135623730951},"35":{"tf":1.0},"375":{"tf":1.0},"418":{"tf":1.0},"456":{"tf":1.0},"465":{"tf":1.0},"469":{"tf":1.4142135623730951},"470":{"tf":1.4142135623730951},"471":{"tf":1.0},"472":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"712":{"tf":1.0},"830":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"g":{"df":12,"docs":{"147":{"tf":1.0},"171":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.0},"437":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"537":{"tf":1.0},"571":{"tf":1.0},"784":{"tf":1.0},"94":{"tf":1.0},"97":{"tf":1.0}}}},"df":1,"docs":{"751":{"tf":1.0}}}}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}}}},"p":{"2":{"df":0,"docs":{},"p":{"df":3,"docs":{"252":{"tf":1.0},"255":{"tf":1.0},"505":{"tf":1.0}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"741":{"tf":1.0}}}}}},"df":1,"docs":{"776":{"tf":1.0}},"e":{"df":1,"docs":{"723":{"tf":1.0}}},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"y":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"187":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"206":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"78":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":12,"docs":{"249":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"381":{"tf":1.0},"403":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"757":{"tf":1.4142135623730951},"758":{"tf":1.0},"759":{"tf":2.23606797749979},"765":{"tf":1.0},"815":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"71":{"tf":1.0}}}}}}},"k":{"df":0,"docs":{},"e":{"df":2,"docs":{"697":{"tf":1.0},"847":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{}}}}}},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"231":{"tf":1.0},"273":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":61,"docs":{"198":{"tf":1.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"215":{"tf":1.0},"22":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"223":{"tf":1.0},"23":{"tf":1.0},"239":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"255":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.4142135623730951},"30":{"tf":1.7320508075688772},"347":{"tf":1.0},"376":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.0},"46":{"tf":1.4142135623730951},"505":{"tf":1.0},"537":{"tf":1.0},"540":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"568":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"615":{"tf":1.0},"638":{"tf":1.0},"659":{"tf":1.0},"694":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.7320508075688772},"765":{"tf":1.0},"80":{"tf":1.0},"828":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":2.0},"832":{"tf":1.0},"85":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.0},"892":{"tf":1.4142135623730951},"895":{"tf":1.0},"896":{"tf":1.4142135623730951},"898":{"tf":1.4142135623730951},"902":{"tf":1.0},"911":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"752":{"tf":1.7320508075688772},"754":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"df":9,"docs":{"152":{"tf":1.0},"186":{"tf":1.0},"188":{"tf":1.0},"267":{"tf":1.0},"701":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.0}}},"k":{"df":7,"docs":{"252":{"tf":1.0},"410":{"tf":1.0},"429":{"tf":1.0},"501":{"tf":1.0},"553":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"565":{"tf":2.0},"575":{"tf":1.0},"577":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"df":33,"docs":{"137":{"tf":1.0},"180":{"tf":1.4142135623730951},"234":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.4142135623730951},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"273":{"tf":1.0},"345":{"tf":1.0},"370":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"505":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":2.0},"525":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"602":{"tf":1.0},"735":{"tf":2.23606797749979},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"929":{"tf":1.0},"940":{"tf":1.0},"941":{"tf":1.4142135623730951},"942":{"tf":1.0},"944":{"tf":3.3166247903554},"947":{"tf":1.0},"948":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"a":{"d":{"d":{"df":0,"docs":{},"r":{"df":1,"docs":{"253":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"721":{"tf":1.0},"848":{"tf":1.7320508075688772}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"c":{"df":0,"docs":{},"r":{"df":1,"docs":{"944":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}}}}},"t":{"df":1,"docs":{"126":{"tf":1.4142135623730951}},"t":{"df":0,"docs":{},"l":{"df":8,"docs":{"238":{"tf":1.0},"276":{"tf":1.0},"303":{"tf":1.0},"381":{"tf":1.0},"438":{"tf":1.0},"593":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.4142135623730951}}}}},"u":{"df":1,"docs":{"988":{"tf":1.0}}},"v":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"467":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":10,"docs":{"230":{"tf":1.0},"231":{"tf":1.0},"356":{"tf":1.0},"358":{"tf":1.0},"440":{"tf":1.0},"551":{"tf":1.0},"63":{"tf":1.0},"720":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0}}}}},"o":{"a":{"d":{"df":13,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.7320508075688772},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"163":{"tf":1.0},"26":{"tf":1.4142135623730951},"605":{"tf":1.0},"654":{"tf":1.4142135623730951},"66":{"tf":1.0},"71":{"tf":1.0},"828":{"tf":1.0},"831":{"tf":1.0},"87":{"tf":1.0}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":13,"docs":{"347":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.0},"555":{"tf":1.0},"599":{"tf":1.4142135623730951},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"694":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"78":{"tf":1.0}}},"t":{"df":21,"docs":{"151":{"tf":1.4142135623730951},"154":{"tf":1.0},"163":{"tf":1.0},"237":{"tf":1.0},"315":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":2.23606797749979},"668":{"tf":1.0},"697":{"tf":3.0},"698":{"tf":1.0},"701":{"tf":1.0},"735":{"tf":3.1622776601683795},"782":{"tf":1.7320508075688772},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":4.47213595499958},"83":{"tf":1.0},"976":{"tf":1.0},"980":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"6":{"tf":1.0}}},":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"2":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"k":{"df":18,"docs":{"120":{"tf":1.0},"198":{"tf":1.0},"284":{"tf":1.0},"294":{"tf":1.7320508075688772},"295":{"tf":2.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.4142135623730951},"300":{"tf":2.23606797749979},"301":{"tf":3.1622776601683795},"302":{"tf":1.4142135623730951},"303":{"tf":1.7320508075688772},"310":{"tf":1.0},"375":{"tf":2.0},"52":{"tf":1.0},"564":{"tf":2.23606797749979},"575":{"tf":2.8284271247461903},"908":{"tf":1.7320508075688772},"913":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"df":1,"docs":{"428":{"tf":1.0}}}}}}}},"df":7,"docs":{"29":{"tf":1.0},"322":{"tf":1.0},"343":{"tf":2.0},"349":{"tf":1.7320508075688772},"350":{"tf":1.4142135623730951},"440":{"tf":1.0},"996":{"tf":1.0}},"i":{"c":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"376":{"tf":1.0}}}}},"df":53,"docs":{"124":{"tf":1.0},"151":{"tf":1.0},"16":{"tf":1.0},"19":{"tf":1.4142135623730951},"219":{"tf":1.0},"234":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.0},"281":{"tf":1.0},"286":{"tf":1.0},"289":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.7320508075688772},"367":{"tf":1.4142135623730951},"368":{"tf":1.0},"369":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.7320508075688772},"455":{"tf":1.0},"459":{"tf":1.0},"461":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"553":{"tf":1.0},"575":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"605":{"tf":1.0},"608":{"tf":1.0},"632":{"tf":1.0},"643":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.4142135623730951},"709":{"tf":1.0},"713":{"tf":1.0},"714":{"tf":1.0},"735":{"tf":1.0},"799":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951},"928":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"935":{"tf":1.0},"959":{"tf":1.0},"966":{"tf":1.0}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"g":{"df":39,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"178":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"231":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"316":{"tf":1.0},"39":{"tf":1.7320508075688772},"410":{"tf":1.0},"417":{"tf":1.4142135623730951},"497":{"tf":1.0},"505":{"tf":1.0},"520":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"565":{"tf":1.4142135623730951},"567":{"tf":1.0},"575":{"tf":1.0},"69":{"tf":1.0},"696":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"763":{"tf":1.0},"767":{"tf":1.0},"770":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"797":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.4142135623730951},"898":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":31,"docs":{"1004":{"tf":1.0},"187":{"tf":1.0},"222":{"tf":1.0},"296":{"tf":1.0},"33":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"617":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"71":{"tf":1.0},"715":{"tf":1.0},"724":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"736":{"tf":1.4142135623730951},"75":{"tf":1.0},"763":{"tf":1.0},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"815":{"tf":1.0},"831":{"tf":1.4142135623730951},"895":{"tf":1.4142135623730951},"897":{"tf":1.4142135623730951},"898":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":1.0},"956":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"565":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"773":{"tf":1.4142135623730951}}}}}}}},"o":{"df":0,"docs":{},"k":{"df":12,"docs":{"1004":{"tf":1.0},"390":{"tf":1.0},"455":{"tf":1.0},"521":{"tf":1.0},"567":{"tf":1.0},"61":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"725":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"880":{"tf":2.0}}}}},"p":{"df":3,"docs":{"485":{"tf":1.0},"715":{"tf":1.0},"721":{"tf":2.23606797749979}}},"s":{"df":3,"docs":{"251":{"tf":1.0},"816":{"tf":1.0},"874":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":6,"docs":{"577":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.0},"799":{"tf":1.0},"913":{"tf":1.0}}},"s":{"df":3,"docs":{"124":{"tf":1.0},"570":{"tf":1.0},"721":{"tf":1.0}}},"t":{"df":3,"docs":{"199":{"tf":1.0},"60":{"tf":1.0},"694":{"tf":1.0}}}},"t":{"'":{"df":1,"docs":{"60":{"tf":1.0}}},"df":9,"docs":{"194":{"tf":1.0},"251":{"tf":1.0},"417":{"tf":1.0},"523":{"tf":1.0},"534":{"tf":1.0},"586":{"tf":1.0},"656":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"323":{"tf":1.0}}}}}}},"w":{"df":21,"docs":{"163":{"tf":1.4142135623730951},"184":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"29":{"tf":1.0},"346":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.4142135623730951},"428":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"507":{"tf":1.0},"63":{"tf":1.4142135623730951},"69":{"tf":1.0},"711":{"tf":1.4142135623730951},"77":{"tf":1.0},"830":{"tf":1.0},"929":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":29,"docs":{"118":{"tf":1.0},"231":{"tf":1.0},"25":{"tf":1.0},"267":{"tf":1.0},"410":{"tf":1.7320508075688772},"411":{"tf":1.4142135623730951},"412":{"tf":1.0},"416":{"tf":1.4142135623730951},"417":{"tf":1.4142135623730951},"418":{"tf":1.0},"42":{"tf":1.0},"422":{"tf":1.0},"471":{"tf":1.0},"540":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"640":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"725":{"tf":1.0},"747":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"810":{"tf":1.0},"829":{"tf":1.0},"881":{"tf":1.0},"992":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"776":{"tf":1.0}}}}}}},"r":{"a":{"df":4,"docs":{"567":{"tf":3.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"583":{"tf":1.0}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":1,"docs":{"957":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":2,"docs":{"940":{"tf":1.0},"945":{"tf":1.0}}}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":2,"docs":{"891":{"tf":1.0},"908":{"tf":1.0}}}}},"y":{"df":1,"docs":{"723":{"tf":1.0}}}},"m":{"a":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"198":{"tf":1.0},"368":{"tf":1.0},"402":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":3.4641016151377544}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"927":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"df":18,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"435":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"6":{"tf":1.0},"733":{"tf":1.0},"78":{"tf":1.0},"797":{"tf":1.0},"83":{"tf":1.0},"876":{"tf":1.0},"933":{"tf":1.0},"951":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":23,"docs":{"111":{"tf":1.0},"201":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"281":{"tf":1.0},"359":{"tf":1.0},"388":{"tf":1.0},"432":{"tf":1.0},"45":{"tf":1.0},"503":{"tf":2.0},"515":{"tf":1.0},"571":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"761":{"tf":2.23606797749979},"763":{"tf":1.0},"776":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":1.0},"945":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"152":{"tf":1.0},"316":{"tf":1.0},"519":{"tf":1.0},"928":{"tf":1.0}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":32,"docs":{"234":{"tf":1.0},"24":{"tf":1.0},"248":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"282":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"316":{"tf":1.0},"344":{"tf":1.0},"375":{"tf":1.0},"389":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"47":{"tf":1.0},"482":{"tf":1.0},"486":{"tf":1.0},"505":{"tf":1.0},"565":{"tf":1.0},"767":{"tf":1.0},"777":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"855":{"tf":1.4142135623730951},"882":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"970":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":7,"docs":{"249":{"tf":1.7320508075688772},"274":{"tf":1.0},"282":{"tf":1.0},"316":{"tf":1.0},"317":{"tf":1.0},"945":{"tf":1.0},"962":{"tf":1.0}}}}}}},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":11,"docs":{"148":{"tf":1.0},"154":{"tf":1.0},"237":{"tf":1.0},"276":{"tf":1.0},"571":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"778":{"tf":1.0},"850":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":114,"docs":{"1014":{"tf":1.0},"121":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"218":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.4142135623730951},"272":{"tf":1.0},"281":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"333":{"tf":1.4142135623730951},"346":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"40":{"tf":1.0},"402":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"423":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"456":{"tf":1.0},"460":{"tf":1.0},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.4142135623730951},"512":{"tf":1.4142135623730951},"514":{"tf":1.4142135623730951},"515":{"tf":1.0},"520":{"tf":1.0},"525":{"tf":1.0},"539":{"tf":1.4142135623730951},"564":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.4142135623730951},"576":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"605":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"665":{"tf":1.0},"673":{"tf":1.0},"683":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.4142135623730951},"701":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"727":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"75":{"tf":1.4142135623730951},"754":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.23606797749979},"763":{"tf":1.0},"77":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"788":{"tf":1.0},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"814":{"tf":1.4142135623730951},"826":{"tf":1.0},"832":{"tf":1.0},"836":{"tf":1.0},"843":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"849":{"tf":1.7320508075688772},"870":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":2.0},"881":{"tf":1.4142135623730951},"912":{"tf":1.0},"934":{"tf":1.4142135623730951},"942":{"tf":1.0},"979":{"tf":1.0},"990":{"tf":1.0},"992":{"tf":1.0}},"r":{"df":1,"docs":{"912":{"tf":1.0}}}},"o":{"df":0,"docs":{},"v":{"a":{"c":{"df":1,"docs":{"945":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"833":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":9,"docs":{"134":{"tf":1.0},"388":{"tf":1.0},"555":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.0},"721":{"tf":1.0},"763":{"tf":1.4142135623730951},"849":{"tf":1.0},"85":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"835":{"tf":1.0}}},"df":0,"docs":{}}}},"n":{"a":{"df":0,"docs":{},"g":{"df":43,"docs":{"113":{"tf":1.0},"121":{"tf":1.0},"137":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"199":{"tf":1.0},"219":{"tf":1.0},"234":{"tf":1.7320508075688772},"239":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"295":{"tf":1.4142135623730951},"296":{"tf":2.23606797749979},"297":{"tf":1.7320508075688772},"300":{"tf":2.23606797749979},"301":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.4142135623730951},"426":{"tf":1.0},"427":{"tf":1.0},"470":{"tf":1.0},"515":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"843":{"tf":1.7320508075688772},"848":{"tf":1.0},"849":{"tf":2.23606797749979},"850":{"tf":1.0},"855":{"tf":1.0},"874":{"tf":1.4142135623730951},"886":{"tf":1.0},"919":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.0},"968":{"tf":1.0}}}},"d":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"270":{"tf":1.0},"272":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":7,"docs":{"208":{"tf":1.0},"251":{"tf":1.0},"343":{"tf":2.23606797749979},"485":{"tf":1.0},"63":{"tf":1.0},"639":{"tf":1.0},"641":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":33,"docs":{"1004":{"tf":1.7320508075688772},"108":{"tf":1.7320508075688772},"218":{"tf":1.0},"231":{"tf":1.4142135623730951},"244":{"tf":1.0},"250":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"483":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.4142135623730951},"58":{"tf":1.0},"665":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.4142135623730951},"72":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.4142135623730951},"761":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"858":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0},"992":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":5,"docs":{"272":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"470":{"tf":1.0},"479":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":5,"docs":{"204":{"tf":2.0},"215":{"tf":1.0},"555":{"tf":1.0},"712":{"tf":1.0},"724":{"tf":1.4142135623730951}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"284":{"tf":1.0},"553":{"tf":1.0},"650":{"tf":1.0},"697":{"tf":1.0}}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"209":{"tf":1.0},"211":{"tf":1.0},"442":{"tf":1.0},"452":{"tf":1.0}}}},"df":0,"docs":{}}},"p":{"<":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}}},"df":14,"docs":{"208":{"tf":1.4142135623730951},"323":{"tf":1.0},"335":{"tf":1.0},"343":{"tf":1.0},"438":{"tf":1.4142135623730951},"439":{"tf":2.23606797749979},"440":{"tf":2.6457513110645907},"5":{"tf":1.4142135623730951},"522":{"tf":1.0},"6":{"tf":1.4142135623730951},"817":{"tf":1.0},"880":{"tf":1.4142135623730951},"944":{"tf":1.0},"951":{"tf":1.0}}},"r":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"122":{"tf":1.0},"535":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"776":{"tf":1.0}}}}},"k":{"df":5,"docs":{"356":{"tf":1.0},"633":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"t":{"'":{"df":2,"docs":{"199":{"tf":1.0},"418":{"tf":1.0}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"772":{"tf":1.0},"776":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":35,"docs":{"195":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"206":{"tf":1.7320508075688772},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"212":{"tf":1.4142135623730951},"214":{"tf":1.0},"217":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"40":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"771":{"tf":2.23606797749979},"772":{"tf":1.7320508075688772},"773":{"tf":3.1622776601683795},"776":{"tf":3.605551275463989},"777":{"tf":2.6457513110645907},"778":{"tf":1.7320508075688772},"912":{"tf":1.4142135623730951},"940":{"tf":1.7320508075688772},"941":{"tf":1.0},"942":{"tf":1.7320508075688772},"945":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0}},"p":{"df":0,"docs":{},"l":{"a":{"c":{"df":5,"docs":{"414":{"tf":1.0},"911":{"tf":1.0},"943":{"tf":1.0},"956":{"tf":1.4142135623730951},"960":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"k":{"df":3,"docs":{"204":{"tf":2.0},"205":{"tf":3.872983346207417},"208":{"tf":6.6332495807108}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":14,"docs":{"184":{"tf":1.0},"331":{"tf":1.0},"351":{"tf":1.0},"45":{"tf":1.7320508075688772},"469":{"tf":1.0},"49":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":2.6457513110645907},"636":{"tf":1.4142135623730951},"786":{"tf":1.7320508075688772},"861":{"tf":1.0},"862":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"!":{"(":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":99,"docs":{"1":{"tf":1.0},"1001":{"tf":1.0},"1002":{"tf":1.0},"1015":{"tf":1.0},"122":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.0},"182":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"206":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.0},"226":{"tf":1.0},"229":{"tf":1.0},"246":{"tf":1.0},"247":{"tf":1.0},"262":{"tf":1.0},"279":{"tf":1.0},"293":{"tf":1.0},"294":{"tf":1.0},"310":{"tf":1.0},"311":{"tf":1.0},"321":{"tf":1.0},"322":{"tf":1.0},"361":{"tf":1.0},"366":{"tf":1.0},"37":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"386":{"tf":1.0},"399":{"tf":1.0},"430":{"tf":1.0},"449":{"tf":1.0},"451":{"tf":1.0},"464":{"tf":1.0},"481":{"tf":1.0},"494":{"tf":1.0},"495":{"tf":1.0},"512":{"tf":1.0},"513":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.0},"584":{"tf":1.0},"597":{"tf":1.0},"598":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":1.0},"626":{"tf":1.0},"627":{"tf":1.0},"648":{"tf":1.0},"649":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":1.0},"708":{"tf":1.0},"709":{"tf":1.0},"728":{"tf":1.0},"757":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"826":{"tf":1.0},"827":{"tf":1.0},"840":{"tf":1.0},"871":{"tf":1.0},"890":{"tf":1.0},"891":{"tf":1.0},"907":{"tf":1.0},"908":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"926":{"tf":1.0},"939":{"tf":1.0},"940":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.0},"973":{"tf":1.0},"974":{"tf":1.0},"987":{"tf":1.0},"988":{"tf":1.0}}}}},"h":{"b":{"b":{"df":0,"docs":{},"{":{"df":0,"docs":{},"i":{"df":1,"docs":{"45":{"tf":1.0}}},"p":{"df":1,"docs":{"45":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"340":{"tf":1.0},"428":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"723":{"tf":1.0}}}},"m":{"df":0,"docs":{},"{":{"1":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"722":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"54":{"tf":1.0}}}}},"x":{"(":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"d":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":5,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":2.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":3,"docs":{"568":{"tf":2.0},"570":{"tf":1.0},"571":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}}},"df":5,"docs":{"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"879":{"tf":1.0},"881":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"402":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"749":{"tf":1.0},"777":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"368":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":38,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":1.0},"253":{"tf":1.0},"30":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"388":{"tf":1.0},"417":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.4142135623730951},"540":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"614":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"773":{"tf":1.0},"776":{"tf":2.0},"777":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"879":{"tf":2.0},"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"895":{"tf":2.0},"896":{"tf":1.0},"898":{"tf":1.4142135623730951},"907":{"tf":1.0}}}}}}},"y":{"b":{"df":6,"docs":{"257":{"tf":1.0},"304":{"tf":1.0},"507":{"tf":1.0},"521":{"tf":1.0},"714":{"tf":1.0},"880":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":3.0}}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"b":{"df":0,"docs":{},"m":{"df":2,"docs":{"279":{"tf":1.4142135623730951},"281":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"df":60,"docs":{"114":{"tf":1.0},"139":{"tf":1.0},"155":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"169":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.4142135623730951},"269":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":1.4142135623730951},"303":{"tf":1.0},"373":{"tf":1.4142135623730951},"376":{"tf":1.0},"438":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"525":{"tf":1.0},"526":{"tf":1.0},"530":{"tf":1.0},"534":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"586":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"668":{"tf":1.0},"69":{"tf":1.0},"694":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"735":{"tf":1.0},"75":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.4142135623730951},"880":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.7320508075688772},"990":{"tf":1.0},"992":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"124":{"tf":1.0},"134":{"tf":1.0},"574":{"tf":1.0}}}}},"t":{"df":4,"docs":{"252":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"501":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"567":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":11,"docs":{"267":{"tf":1.0},"530":{"tf":1.0},"650":{"tf":1.0},"739":{"tf":1.0},"777":{"tf":1.0},"931":{"tf":1.0},"945":{"tf":1.0},"955":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"972":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":82,"docs":{"103":{"tf":1.0},"107":{"tf":1.0},"111":{"tf":1.0},"120":{"tf":1.0},"122":{"tf":1.7320508075688772},"123":{"tf":1.0},"124":{"tf":1.7320508075688772},"125":{"tf":1.0},"126":{"tf":1.7320508075688772},"127":{"tf":1.4142135623730951},"132":{"tf":1.0},"133":{"tf":1.0},"140":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":2.0},"229":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"24":{"tf":1.0},"243":{"tf":1.0},"251":{"tf":1.4142135623730951},"255":{"tf":2.8284271247461903},"257":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.4142135623730951},"294":{"tf":1.7320508075688772},"295":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"35":{"tf":1.0},"365":{"tf":1.0},"404":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"467":{"tf":1.0},"495":{"tf":1.4142135623730951},"496":{"tf":1.4142135623730951},"505":{"tf":1.7320508075688772},"507":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":2.23606797749979},"565":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"632":{"tf":1.0},"649":{"tf":1.4142135623730951},"664":{"tf":1.0},"665":{"tf":1.0},"69":{"tf":1.0},"705":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"73":{"tf":1.0},"743":{"tf":1.4142135623730951},"768":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"797":{"tf":1.0},"804":{"tf":1.0},"818":{"tf":1.0},"920":{"tf":1.0},"94":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0},"97":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.0},"987":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"413":{"tf":1.0},"567":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"i":{"a":{"df":3,"docs":{"270":{"tf":1.0},"3":{"tf":1.0},"847":{"tf":1.0}},"n":{"df":6,"docs":{"710":{"tf":1.0},"717":{"tf":1.7320508075688772},"721":{"tf":2.0},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"184":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":6,"docs":{"1006":{"tf":1.0},"130":{"tf":1.0},"191":{"tf":1.0},"231":{"tf":1.0},"470":{"tf":1.0},"777":{"tf":1.0}}}},"g":{"a":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":5,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"832":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":16,"docs":{"111":{"tf":1.0},"113":{"tf":2.23606797749979},"121":{"tf":1.4142135623730951},"272":{"tf":2.449489742783178},"273":{"tf":1.4142135623730951},"466":{"tf":1.0},"467":{"tf":1.0},"468":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.4142135623730951},"573":{"tf":1.0},"81":{"tf":1.4142135623730951},"850":{"tf":1.0},"874":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"471":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":15,"docs":{"26":{"tf":1.4142135623730951},"28":{"tf":1.0},"450":{"tf":1.0},"483":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"730":{"tf":1.4142135623730951},"732":{"tf":1.7320508075688772},"735":{"tf":4.898979485566356},"763":{"tf":1.0},"828":{"tf":1.0},"829":{"tf":2.23606797749979},"831":{"tf":3.3166247903554},"832":{"tf":1.7320508075688772},"840":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":1,"docs":{"244":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"16":{"tf":1.0},"170":{"tf":1.0},"499":{"tf":1.0},"534":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":1.4142135623730951},"85":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":4,"docs":{"198":{"tf":1.0},"849":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}},"g":{"df":4,"docs":{"269":{"tf":1.0},"291":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"207":{"tf":1.0}}}},"k":{"df":0,"docs":{},"l":{"df":14,"docs":{"439":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"46":{"tf":1.0},"49":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"519":{"tf":1.0},"525":{"tf":2.0},"634":{"tf":1.0},"759":{"tf":1.4142135623730951},"762":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"78":{"tf":1.7320508075688772}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"525":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":3,"docs":{"513":{"tf":1.7320508075688772},"514":{"tf":1.0},"520":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":46,"docs":{"15":{"tf":1.0},"215":{"tf":1.4142135623730951},"218":{"tf":1.0},"220":{"tf":2.449489742783178},"221":{"tf":2.449489742783178},"222":{"tf":1.7320508075688772},"223":{"tf":1.4142135623730951},"253":{"tf":1.0},"38":{"tf":1.0},"450":{"tf":1.0},"54":{"tf":1.0},"553":{"tf":1.7320508075688772},"56":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.0},"61":{"tf":2.449489742783178},"619":{"tf":1.0},"62":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":3.3166247903554},"636":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"645":{"tf":1.7320508075688772},"651":{"tf":1.0},"670":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"709":{"tf":1.0},"716":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"73":{"tf":1.0},"74":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":2.6457513110645907},"77":{"tf":1.0},"786":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"988":{"tf":1.7320508075688772},"989":{"tf":1.0},"992":{"tf":1.4142135623730951}},"e":{"1":{"df":1,"docs":{"633":{"tf":1.0}}},"2":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"'":{"df":1,"docs":{"516":{"tf":1.0}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"519":{"tf":1.0},"520":{"tf":2.23606797749979},"526":{"tf":1.7320508075688772},"534":{"tf":1.0}}}}}}}},"df":32,"docs":{"1":{"tf":1.7320508075688772},"12":{"tf":1.0},"14":{"tf":1.0},"154":{"tf":1.0},"16":{"tf":1.7320508075688772},"173":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.7320508075688772},"2":{"tf":1.0},"22":{"tf":2.449489742783178},"24":{"tf":1.0},"3":{"tf":4.69041575982343},"411":{"tf":1.0},"412":{"tf":1.0},"5":{"tf":3.3166247903554},"513":{"tf":2.6457513110645907},"514":{"tf":3.3166247903554},"515":{"tf":3.3166247903554},"516":{"tf":2.23606797749979},"517":{"tf":1.7320508075688772},"519":{"tf":2.449489742783178},"520":{"tf":2.6457513110645907},"521":{"tf":1.7320508075688772},"523":{"tf":1.7320508075688772},"524":{"tf":1.7320508075688772},"526":{"tf":3.4641016151377544},"528":{"tf":2.6457513110645907},"530":{"tf":1.0},"531":{"tf":1.0},"534":{"tf":1.7320508075688772},"6":{"tf":4.242640687119285},"9":{"tf":1.0}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":2,"docs":{"15":{"tf":1.0},"5":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"15":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":1.0}}}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"6":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.7320508075688772}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"22":{"tf":1.4142135623730951},"735":{"tf":1.4142135623730951}}},"df":1,"docs":{"467":{"tf":1.0}},"h":{"df":0,"docs":{},"o":{"d":{"df":15,"docs":{"121":{"tf":1.0},"140":{"tf":1.0},"177":{"tf":1.0},"196":{"tf":1.4142135623730951},"22":{"tf":2.0},"23":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"322":{"tf":1.0},"338":{"tf":1.0},"349":{"tf":2.449489742783178},"350":{"tf":1.0},"351":{"tf":2.0},"650":{"tf":1.0},"735":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}}}}},"i":{"b":{"df":6,"docs":{"515":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":2.23606797749979},"829":{"tf":1.0},"831":{"tf":1.0},"996":{"tf":1.0}}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"95":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":38,"docs":{"1012":{"tf":1.0},"108":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":2.0},"155":{"tf":3.3166247903554},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"210":{"tf":1.0},"241":{"tf":1.0},"249":{"tf":1.4142135623730951},"269":{"tf":1.0},"279":{"tf":1.0},"281":{"tf":1.4142135623730951},"282":{"tf":1.0},"284":{"tf":2.0},"289":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.0},"3":{"tf":1.0},"302":{"tf":1.7320508075688772},"363":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":2.0},"374":{"tf":1.7320508075688772},"375":{"tf":2.8284271247461903},"376":{"tf":2.0},"512":{"tf":1.0},"575":{"tf":1.0},"609":{"tf":1.0},"73":{"tf":1.0},"813":{"tf":1.0},"872":{"tf":1.0},"887":{"tf":1.0},"953":{"tf":1.0},"970":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"567":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"931":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"(":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"568":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"568":{"tf":1.0},"569":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"194":{"tf":1.0},"846":{"tf":1.0}}}}}}}}}},"d":{"df":3,"docs":{"127":{"tf":1.0},"499":{"tf":1.0},"542":{"tf":1.0}},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":27,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0},"172":{"tf":1.0},"200":{"tf":1.0},"24":{"tf":1.0},"288":{"tf":1.0},"292":{"tf":1.0},"30":{"tf":1.0},"366":{"tf":1.4142135623730951},"41":{"tf":1.0},"438":{"tf":1.0},"53":{"tf":1.0},"537":{"tf":1.0},"544":{"tf":1.0},"605":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"648":{"tf":1.0},"720":{"tf":1.0},"835":{"tf":1.0},"87":{"tf":1.0},"902":{"tf":1.0},"919":{"tf":1.0},"942":{"tf":1.0},"951":{"tf":1.0},"965":{"tf":1.0},"968":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":4,"docs":{"366":{"tf":1.0},"368":{"tf":1.0},"374":{"tf":1.0},"83":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":14,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"410":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"979":{"tf":1.0}}}},"t":{"df":3,"docs":{"411":{"tf":1.0},"931":{"tf":1.7320508075688772},"932":{"tf":1.4142135623730951}}},"u":{"df":2,"docs":{"500":{"tf":1.0},"573":{"tf":1.0}},"t":{"df":5,"docs":{"183":{"tf":1.0},"184":{"tf":1.0},"207":{"tf":1.0},"551":{"tf":1.0},"846":{"tf":1.7320508075688772}}}}},"s":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"v":{"df":2,"docs":{"439":{"tf":1.0},"564":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"564":{"tf":1.0},"567":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"849":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}}},"m":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":11,"docs":{"121":{"tf":1.0},"208":{"tf":1.0},"238":{"tf":1.0},"437":{"tf":1.0},"60":{"tf":1.0},"721":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.4142135623730951},"761":{"tf":2.449489742783178},"78":{"tf":1.4142135623730951},"912":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"108":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":1,"docs":{"293":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":4,"docs":{"296":{"tf":1.0},"720":{"tf":1.4142135623730951},"81":{"tf":1.0},"84":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"81":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"s":{"df":3,"docs":{"141":{"tf":1.0},"81":{"tf":1.0},"919":{"tf":1.0}}}}},"t":{"df":1,"docs":{"741":{"tf":1.0}},"i":{"df":0,"docs":{},"g":{"df":11,"docs":{"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"144":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"441":{"tf":1.0},"567":{"tf":1.0},"583":{"tf":1.0},"63":{"tf":1.0},"77":{"tf":1.0},"965":{"tf":1.0}}}}},"x":{"df":3,"docs":{"365":{"tf":1.0},"598":{"tf":1.0},"603":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"365":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"426":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"u":{",":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}},"df":1,"docs":{"717":{"tf":1.0}}}},"o":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"95":{"tf":1.0}}}}},"d":{"df":2,"docs":{"814":{"tf":1.0},"83":{"tf":1.0}},"e":{"df":6,"docs":{"284":{"tf":1.0},"29":{"tf":1.0},"292":{"tf":1.0},"526":{"tf":2.0},"974":{"tf":1.4142135623730951},"978":{"tf":1.0}},"l":{"'":{"df":1,"docs":{"427":{"tf":1.0}}},"df":49,"docs":{"195":{"tf":1.0},"199":{"tf":1.4142135623730951},"214":{"tf":1.0},"216":{"tf":1.0},"243":{"tf":1.0},"246":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"402":{"tf":1.0},"410":{"tf":1.4142135623730951},"426":{"tf":1.4142135623730951},"427":{"tf":1.7320508075688772},"428":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.7320508075688772},"49":{"tf":1.0},"51":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":2.0},"55":{"tf":1.0},"564":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":2.0},"744":{"tf":1.0},"747":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":2.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.4142135623730951},"808":{"tf":1.7320508075688772},"809":{"tf":1.4142135623730951},"810":{"tf":2.6457513110645907},"811":{"tf":1.4142135623730951},"813":{"tf":1.7320508075688772},"814":{"tf":1.7320508075688772},"817":{"tf":1.0},"822":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"937":{"tf":1.0}}},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":1.7320508075688772}}}}},"i":{"df":0,"docs":{},"f":{"df":12,"docs":{"114":{"tf":1.0},"136":{"tf":1.0},"140":{"tf":1.4142135623730951},"142":{"tf":1.0},"182":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.7320508075688772},"6":{"tf":2.0},"786":{"tf":1.4142135623730951},"795":{"tf":1.7320508075688772},"796":{"tf":1.0},"814":{"tf":1.0}},"i":{"df":28,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"137":{"tf":1.4142135623730951},"138":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"237":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":2.0},"32":{"tf":1.0},"418":{"tf":1.0},"437":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"711":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"786":{"tf":1.0},"832":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0}}},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":2.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"28":{"tf":1.0},"33":{"tf":1.0}}}},"df":7,"docs":{"112":{"tf":1.0},"23":{"tf":1.0},"270":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.0},"291":{"tf":1.0},"872":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"126":{"tf":1.4142135623730951},"254":{"tf":1.0},"387":{"tf":1.0},"398":{"tf":1.0},"436":{"tf":1.0},"815":{"tf":1.4142135623730951}},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"209":{"tf":1.0},"402":{"tf":1.0},"422":{"tf":1.0},"724":{"tf":1.0},"919":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"h":{"df":9,"docs":{"124":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"374":{"tf":1.0},"778":{"tf":2.0},"843":{"tf":1.0},"911":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"466":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.4142135623730951}}}}}}},"o":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"105":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":142,"docs":{"103":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"139":{"tf":1.0},"155":{"tf":1.0},"16":{"tf":1.0},"160":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"194":{"tf":1.0},"199":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"216":{"tf":1.0},"217":{"tf":1.0},"223":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"244":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"289":{"tf":1.0},"292":{"tf":1.0},"310":{"tf":1.0},"313":{"tf":1.0},"321":{"tf":1.0},"33":{"tf":1.0},"334":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"368":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"375":{"tf":1.0},"376":{"tf":1.0},"378":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"439":{"tf":1.0},"444":{"tf":1.0},"453":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"486":{"tf":1.0},"496":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"534":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":2.23606797749979},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.4142135623730951},"574":{"tf":1.4142135623730951},"576":{"tf":1.0},"58":{"tf":2.23606797749979},"589":{"tf":1.0},"593":{"tf":1.0},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"61":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"668":{"tf":1.0},"711":{"tf":1.4142135623730951},"717":{"tf":1.0},"72":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"723":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.7320508075688772},"729":{"tf":1.4142135623730951},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"75":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.7320508075688772},"754":{"tf":1.0},"761":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":2.0},"831":{"tf":1.0},"832":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.4142135623730951},"890":{"tf":1.0},"912":{"tf":1.4142135623730951},"913":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"94":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.7320508075688772},"97":{"tf":1.0},"973":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.4142135623730951},"990":{"tf":1.0}},"o":{"df":0,"docs":{},"v":{"df":2,"docs":{"47":{"tf":1.0},"84":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"331":{"tf":1.0},"515":{"tf":1.0},"571":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":132,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1004":{"tf":1.4142135623730951},"106":{"tf":1.0},"108":{"tf":1.0},"122":{"tf":1.0},"124":{"tf":1.0},"136":{"tf":1.0},"138":{"tf":1.0},"150":{"tf":1.0},"152":{"tf":1.0},"164":{"tf":1.0},"166":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"195":{"tf":1.0},"197":{"tf":1.0},"215":{"tf":1.0},"217":{"tf":1.4142135623730951},"229":{"tf":1.0},"231":{"tf":1.0},"235":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"263":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"270":{"tf":1.0},"279":{"tf":1.0},"281":{"tf":1.4142135623730951},"284":{"tf":1.0},"294":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"311":{"tf":1.0},"313":{"tf":1.0},"322":{"tf":1.0},"324":{"tf":1.0},"366":{"tf":1.0},"368":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"388":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":1.0},"402":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"430":{"tf":1.0},"432":{"tf":1.0},"451":{"tf":1.0},"453":{"tf":1.0},"465":{"tf":1.0},"467":{"tf":1.4142135623730951},"481":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.0},"495":{"tf":1.0},"497":{"tf":1.0},"513":{"tf":1.0},"515":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.0},"546":{"tf":1.0},"549":{"tf":1.0},"551":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"565":{"tf":1.0},"58":{"tf":1.0},"584":{"tf":1.0},"586":{"tf":1.0},"598":{"tf":1.0},"600":{"tf":1.0},"613":{"tf":1.0},"615":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"649":{"tf":1.0},"651":{"tf":1.0},"664":{"tf":1.0},"666":{"tf":1.0},"678":{"tf":1.0},"680":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"730":{"tf":1.0},"732":{"tf":1.0},"741":{"tf":1.0},"743":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.0},"771":{"tf":1.0},"773":{"tf":1.0},"782":{"tf":1.0},"784":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"797":{"tf":1.0},"808":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"827":{"tf":1.0},"829":{"tf":1.0},"841":{"tf":1.0},"843":{"tf":1.4142135623730951},"857":{"tf":1.0},"859":{"tf":1.0},"871":{"tf":1.0},"873":{"tf":1.0},"891":{"tf":1.0},"893":{"tf":1.0},"908":{"tf":1.0},"910":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"957":{"tf":1.0},"959":{"tf":1.0},"974":{"tf":1.0},"976":{"tf":1.0},"988":{"tf":1.0},"990":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"e":{"df":36,"docs":{"150":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"163":{"tf":2.0},"175":{"tf":1.0},"214":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":1.0},"293":{"tf":1.4142135623730951},"311":{"tf":1.0},"315":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"383":{"tf":1.0},"384":{"tf":1.0},"417":{"tf":1.0},"439":{"tf":1.0},"54":{"tf":1.0},"570":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"68":{"tf":1.0},"732":{"tf":1.0},"778":{"tf":1.0},"827":{"tf":1.0},"835":{"tf":1.0},"848":{"tf":1.4142135623730951},"932":{"tf":1.0},"985":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"g":{"df":2,"docs":{"735":{"tf":2.449489742783178},"97":{"tf":1.0}}}},"u":{"c":{"df":0,"docs":{},"h":{"df":27,"docs":{"255":{"tf":1.0},"261":{"tf":1.0},"272":{"tf":1.0},"371":{"tf":1.0},"418":{"tf":1.0},"46":{"tf":1.0},"503":{"tf":1.0},"511":{"tf":1.0},"568":{"tf":1.4142135623730951},"573":{"tf":1.0},"614":{"tf":1.4142135623730951},"619":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"669":{"tf":1.0},"694":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"779":{"tf":1.0},"790":{"tf":1.0},"853":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.4142135623730951},"876":{"tf":1.0},"885":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":1,"docs":{"855":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"79":{"tf":1.0}}}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"d":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"253":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"198":{"tf":1.0}}}}},"df":14,"docs":{"155":{"tf":1.4142135623730951},"279":{"tf":1.0},"281":{"tf":1.0},"282":{"tf":1.0},"284":{"tf":1.0},"289":{"tf":1.0},"291":{"tf":1.0},"374":{"tf":1.0},"378":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":1.0},"95":{"tf":1.0}},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"786":{"tf":1.7320508075688772}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":37,"docs":{"142":{"tf":1.0},"155":{"tf":1.0},"161":{"tf":1.0},"204":{"tf":1.0},"222":{"tf":1.0},"249":{"tf":1.0},"28":{"tf":1.0},"281":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"402":{"tf":1.4142135623730951},"48":{"tf":1.4142135623730951},"483":{"tf":1.0},"522":{"tf":2.23606797749979},"524":{"tf":1.0},"534":{"tf":1.4142135623730951},"599":{"tf":1.0},"600":{"tf":2.449489742783178},"602":{"tf":1.7320508075688772},"603":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"615":{"tf":1.4142135623730951},"649":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.4142135623730951},"78":{"tf":1.0},"799":{"tf":1.4142135623730951},"876":{"tf":1.7320508075688772},"881":{"tf":1.0},"912":{"tf":1.0}},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"483":{"tf":1.0}}}},"i":{"df":4,"docs":{"1003":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"776":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"879":{"tf":3.605551275463989},"885":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":16,"docs":{"784":{"tf":1.4142135623730951},"81":{"tf":1.4142135623730951},"871":{"tf":1.7320508075688772},"872":{"tf":2.6457513110645907},"874":{"tf":3.872983346207417},"875":{"tf":3.4641016151377544},"876":{"tf":1.7320508075688772},"878":{"tf":2.6457513110645907},"879":{"tf":8.717797887081348},"880":{"tf":3.0},"881":{"tf":2.449489742783178},"885":{"tf":3.4641016151377544},"886":{"tf":1.4142135623730951},"887":{"tf":1.0},"888":{"tf":1.0},"890":{"tf":1.0}},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"171":{"tf":1.0}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":3.872983346207417}}},"df":0,"docs":{}}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"715":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"208":{"tf":1.4142135623730951},"375":{"tf":1.0},"537":{"tf":1.0}}}},"df":2,"docs":{"23":{"tf":1.0},"717":{"tf":2.0}},"e":{"df":1,"docs":{"514":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"880":{"tf":1.0}}}}}}}}},"y":{"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"l":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{")":{".":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"(":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"n":{"+":{"1":{"df":3,"docs":{"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"344":{"tf":1.0},"346":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"/":{"3":{"df":3,"docs":{"432":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0}}},"a":{"df":13,"docs":{"102":{"tf":1.0},"192":{"tf":1.0},"286":{"tf":1.4142135623730951},"474":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"647":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"98":{"tf":1.0}}},"df":0,"docs":{}},"=":{"3":{"df":0,"docs":{},"f":{"+":{"df":0,"docs":{},"k":{"df":1,"docs":{"436":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"2":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"3":{"df":2,"docs":{"435":{"tf":1.0},"438":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":2,"docs":{"432":{"tf":1.0},"438":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"a":{"df":2,"docs":{"578":{"tf":1.0},"579":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":3,"docs":{"432":{"tf":1.0},"450":{"tf":1.0},"732":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"df":29,"docs":{"171":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":3.0},"23":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"253":{"tf":1.7320508075688772},"272":{"tf":1.0},"273":{"tf":1.0},"292":{"tf":1.7320508075688772},"3":{"tf":1.0},"373":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"5":{"tf":1.0},"502":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"534":{"tf":1.0},"56":{"tf":1.4142135623730951},"735":{"tf":2.23606797749979},"736":{"tf":1.0},"74":{"tf":1.0},"748":{"tf":1.0},"761":{"tf":1.4142135623730951},"846":{"tf":1.0},"9":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"723":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":10,"docs":{"114":{"tf":1.0},"198":{"tf":1.0},"358":{"tf":1.0},"429":{"tf":1.0},"512":{"tf":1.0},"603":{"tf":2.0},"699":{"tf":1.0},"829":{"tf":2.23606797749979},"874":{"tf":1.0},"95":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"df":11,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"267":{"tf":1.4142135623730951},"429":{"tf":1.0},"48":{"tf":1.0},"514":{"tf":1.0},"551":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"776":{"tf":1.0}}}}},"y":{"df":2,"docs":{"188":{"tf":1.0},"75":{"tf":1.0}}}},"b":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{";":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"0":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":14,"docs":{"234":{"tf":1.4142135623730951},"332":{"tf":1.4142135623730951},"344":{"tf":2.23606797749979},"345":{"tf":1.0},"346":{"tf":2.6457513110645907},"436":{"tf":1.4142135623730951},"44":{"tf":1.4142135623730951},"45":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":2.23606797749979},"749":{"tf":2.0},"885":{"tf":2.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"203":{"tf":1.0}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":39,"docs":{"1010":{"tf":1.0},"1012":{"tf":1.0},"130":{"tf":1.0},"184":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"230":{"tf":1.0},"284":{"tf":1.0},"325":{"tf":1.0},"367":{"tf":1.0},"399":{"tf":1.0},"444":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.0},"516":{"tf":1.4142135623730951},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"54":{"tf":1.0},"573":{"tf":1.0},"609":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.4142135623730951},"698":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"843":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.4142135623730951},"849":{"tf":1.0},"856":{"tf":1.0},"942":{"tf":1.0},"953":{"tf":1.0},"965":{"tf":1.0},"970":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"204":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"855":{"tf":1.0}}}}}}},"df":3,"docs":{"314":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"418":{"tf":1.0},"46":{"tf":1.0},"48":{"tf":1.0},"776":{"tf":1.0},"962":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"d":{"df":146,"docs":{"104":{"tf":1.0},"111":{"tf":1.0},"114":{"tf":1.0},"12":{"tf":1.0},"136":{"tf":1.0},"138":{"tf":1.4142135623730951},"140":{"tf":1.4142135623730951},"142":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.4142135623730951},"159":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"186":{"tf":1.0},"19":{"tf":1.0},"196":{"tf":1.4142135623730951},"200":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"209":{"tf":1.0},"231":{"tf":1.7320508075688772},"240":{"tf":1.0},"249":{"tf":2.0},"254":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"272":{"tf":1.4142135623730951},"288":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.0},"368":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.4142135623730951},"374":{"tf":2.0},"375":{"tf":2.23606797749979},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.0},"408":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"432":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"441":{"tf":1.4142135623730951},"446":{"tf":1.0},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.7320508075688772},"456":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.4142135623730951},"467":{"tf":1.0},"470":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"519":{"tf":1.0},"52":{"tf":1.4142135623730951},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"57":{"tf":1.0},"573":{"tf":1.4142135623730951},"593":{"tf":1.0},"6":{"tf":1.0},"608":{"tf":1.0},"614":{"tf":1.0},"619":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.4142135623730951},"666":{"tf":1.0},"673":{"tf":1.4142135623730951},"68":{"tf":1.4142135623730951},"69":{"tf":1.0},"700":{"tf":1.0},"71":{"tf":1.0},"710":{"tf":1.0},"72":{"tf":1.4142135623730951},"73":{"tf":1.0},"732":{"tf":1.7320508075688772},"736":{"tf":1.0},"739":{"tf":1.0},"743":{"tf":1.4142135623730951},"751":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"773":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.4142135623730951},"781":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.7320508075688772},"849":{"tf":2.0},"850":{"tf":1.0},"853":{"tf":1.0},"858":{"tf":1.0},"864":{"tf":1.0},"874":{"tf":1.7320508075688772},"876":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":3.3166247903554},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.0},"932":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"942":{"tf":1.0},"947":{"tf":1.0},"955":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"60":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"f":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"206":{"tf":1.0}}}}},"df":0,"docs":{}},"g":{"df":6,"docs":{"1004":{"tf":1.0},"187":{"tf":1.4142135623730951},"30":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"593":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"574":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":13,"docs":{"257":{"tf":1.0},"288":{"tf":1.0},"507":{"tf":1.0},"554":{"tf":1.0},"60":{"tf":1.0},"640":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"739":{"tf":1.0},"835":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"796":{"tf":1.0},"799":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.4142135623730951},"931":{"tf":1.0}}}},"t":{"df":5,"docs":{"211":{"tf":1.0},"267":{"tf":1.0},"700":{"tf":1.0},"800":{"tf":1.0},"835":{"tf":1.0}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"'":{"df":4,"docs":{"274":{"tf":1.0},"371":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0}}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":79,"docs":{"0":{"tf":1.0},"1004":{"tf":1.0},"111":{"tf":1.0},"124":{"tf":1.0},"128":{"tf":1.0},"139":{"tf":1.0},"147":{"tf":1.0},"152":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"247":{"tf":1.0},"248":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"254":{"tf":2.0},"257":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":2.0},"273":{"tf":1.0},"314":{"tf":1.4142135623730951},"316":{"tf":1.4142135623730951},"356":{"tf":1.0},"358":{"tf":1.0},"365":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"376":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.7320508075688772},"430":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"512":{"tf":1.0},"515":{"tf":1.4142135623730951},"532":{"tf":1.0},"54":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"555":{"tf":1.0},"559":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0},"60":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"71":{"tf":1.4142135623730951},"720":{"tf":1.0},"743":{"tf":1.0},"757":{"tf":1.7320508075688772},"758":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":2.23606797749979},"763":{"tf":1.4142135623730951},"767":{"tf":1.0},"770":{"tf":1.0},"784":{"tf":1.0},"797":{"tf":2.6457513110645907},"799":{"tf":1.7320508075688772},"807":{"tf":1.0},"819":{"tf":1.0},"990":{"tf":1.4142135623730951},"996":{"tf":1.0}},"i":{"d":{":":{":":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":2,"docs":{"680":{"tf":1.0},"688":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":1,"docs":{"689":{"tf":1.0}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"688":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"688":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":3,"docs":{"678":{"tf":1.7320508075688772},"679":{"tf":1.0},"682":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"700":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"204":{"tf":1.0},"302":{"tf":1.4142135623730951},"308":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":2.0},"912":{"tf":1.0}}}}},"w":{"/":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"618":{"tf":1.0}}}}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"207":{"tf":1.7320508075688772},"750":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.449489742783178}}},"df":0,"docs":{}}}}}}}}},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"568":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":182,"docs":{"1":{"tf":1.0},"1004":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"118":{"tf":1.0},"125":{"tf":1.0},"13":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"151":{"tf":2.449489742783178},"154":{"tf":1.4142135623730951},"155":{"tf":1.7320508075688772},"158":{"tf":1.0},"160":{"tf":1.0},"166":{"tf":1.4142135623730951},"171":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"191":{"tf":1.0},"203":{"tf":1.4142135623730951},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"221":{"tf":1.0},"225":{"tf":1.0},"24":{"tf":1.4142135623730951},"247":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.4142135623730951},"255":{"tf":1.0},"261":{"tf":1.0},"268":{"tf":1.7320508075688772},"269":{"tf":2.23606797749979},"270":{"tf":1.7320508075688772},"274":{"tf":1.0},"276":{"tf":1.7320508075688772},"281":{"tf":1.0},"286":{"tf":1.0},"289":{"tf":1.0},"296":{"tf":1.4142135623730951},"3":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":1.0},"306":{"tf":1.0},"32":{"tf":1.0},"333":{"tf":1.4142135623730951},"34":{"tf":1.0},"343":{"tf":1.0},"371":{"tf":1.4142135623730951},"373":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"381":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.0},"40":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":2.23606797749979},"450":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"457":{"tf":1.0},"461":{"tf":1.4142135623730951},"482":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"5":{"tf":1.0},"511":{"tf":1.0},"53":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":2.23606797749979},"540":{"tf":1.0},"542":{"tf":1.0},"545":{"tf":1.0},"551":{"tf":2.23606797749979},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"559":{"tf":2.0},"56":{"tf":1.7320508075688772},"564":{"tf":2.0},"565":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.4142135623730951},"598":{"tf":1.7320508075688772},"599":{"tf":1.0},"6":{"tf":2.23606797749979},"600":{"tf":1.0},"602":{"tf":1.7320508075688772},"605":{"tf":1.0},"606":{"tf":1.0},"609":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"62":{"tf":1.4142135623730951},"63":{"tf":1.7320508075688772},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":2.23606797749979},"635":{"tf":1.0},"639":{"tf":1.0},"64":{"tf":1.7320508075688772},"641":{"tf":1.4142135623730951},"642":{"tf":1.4142135623730951},"643":{"tf":1.4142135623730951},"644":{"tf":2.0},"645":{"tf":1.0},"646":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.7320508075688772},"651":{"tf":1.0},"653":{"tf":1.7320508075688772},"654":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"668":{"tf":1.4142135623730951},"67":{"tf":1.4142135623730951},"673":{"tf":1.0},"69":{"tf":1.4142135623730951},"698":{"tf":1.0},"7":{"tf":1.0},"705":{"tf":2.23606797749979},"72":{"tf":1.0},"73":{"tf":2.0},"730":{"tf":1.0},"735":{"tf":3.4641016151377544},"736":{"tf":1.4142135623730951},"738":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"761":{"tf":1.7320508075688772},"772":{"tf":1.0},"8":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":1.7320508075688772},"813":{"tf":1.7320508075688772},"814":{"tf":2.0},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"819":{"tf":1.4142135623730951},"843":{"tf":1.0},"846":{"tf":1.0},"853":{"tf":1.0},"860":{"tf":1.4142135623730951},"874":{"tf":1.0},"879":{"tf":3.872983346207417},"882":{"tf":1.0},"9":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.7320508075688772},"931":{"tf":1.0},"932":{"tf":2.449489742783178},"933":{"tf":1.0},"935":{"tf":1.0},"936":{"tf":1.0},"94":{"tf":1.0},"944":{"tf":1.7320508075688772},"945":{"tf":1.0},"947":{"tf":1.0},"949":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"969":{"tf":1.0},"97":{"tf":1.0},"987":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"512":{"tf":1.0},"550":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"553":{"tf":1.4142135623730951},"637":{"tf":1.0},"640":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"843":{"tf":1.0}}},"df":0,"docs":{}}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"249":{"tf":1.0},"47":{"tf":1.0},"571":{"tf":1.4142135623730951},"735":{"tf":1.0},"928":{"tf":1.0}}}}},"x":{"df":0,"docs":{},"t":{"df":24,"docs":{"126":{"tf":1.0},"151":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"170":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"327":{"tf":1.0},"343":{"tf":1.4142135623730951},"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"347":{"tf":1.0},"350":{"tf":1.0},"385":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"483":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"735":{"tf":2.8284271247461903},"776":{"tf":1.4142135623730951},"848":{"tf":1.0},"879":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"345":{"tf":1.7320508075688772}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"f":{"df":0,"docs":{},"t":{"df":19,"docs":{"208":{"tf":1.0},"3":{"tf":3.3166247903554},"410":{"tf":1.4142135623730951},"411":{"tf":1.7320508075688772},"412":{"tf":2.0},"414":{"tf":2.0},"415":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"418":{"tf":1.0},"425":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"5":{"tf":1.4142135623730951},"6":{"tf":1.4142135623730951},"7":{"tf":1.0},"8":{"tf":1.0},"912":{"tf":1.0},"956":{"tf":1.0}},"s":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"416":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"i":{"b":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"761":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"e":{"df":3,"docs":{"281":{"tf":1.0},"721":{"tf":1.0},"78":{"tf":1.0}}}},"df":1,"docs":{"370":{"tf":1.0}},"l":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"93":{"tf":1.7320508075688772},"94":{"tf":1.0},"95":{"tf":1.0}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":1,"docs":{"38":{"tf":1.0}}}}}}},"o":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":76,"docs":{"152":{"tf":1.4142135623730951},"153":{"tf":1.4142135623730951},"154":{"tf":1.7320508075688772},"159":{"tf":1.0},"160":{"tf":2.0},"231":{"tf":1.0},"233":{"tf":1.0},"248":{"tf":1.7320508075688772},"249":{"tf":2.8284271247461903},"251":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":2.23606797749979},"257":{"tf":2.23606797749979},"290":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.4142135623730951},"404":{"tf":1.0},"406":{"tf":1.0},"409":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.7320508075688772},"452":{"tf":1.0},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.0},"495":{"tf":1.7320508075688772},"496":{"tf":1.0},"497":{"tf":3.4641016151377544},"500":{"tf":2.449489742783178},"501":{"tf":2.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.7320508075688772},"505":{"tf":1.7320508075688772},"507":{"tf":2.23606797749979},"512":{"tf":2.449489742783178},"525":{"tf":4.0},"532":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":2.23606797749979},"552":{"tf":1.0},"553":{"tf":2.8284271247461903},"554":{"tf":1.0},"555":{"tf":1.4142135623730951},"559":{"tf":1.0},"567":{"tf":1.7320508075688772},"59":{"tf":1.0},"61":{"tf":1.0},"630":{"tf":1.0},"635":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.7320508075688772},"68":{"tf":1.4142135623730951},"71":{"tf":1.4142135623730951},"711":{"tf":1.0},"720":{"tf":1.4142135623730951},"735":{"tf":1.0},"759":{"tf":2.6457513110645907},"761":{"tf":1.7320508075688772},"763":{"tf":1.4142135623730951},"990":{"tf":1.4142135623730951},"991":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}},"df":0,"docs":{}}},"s":{".":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"525":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"525":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"525":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"_":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"525":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"3":{":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"(":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"525":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"724":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":13,"docs":{"1002":{"tf":1.7320508075688772},"1003":{"tf":2.23606797749979},"1004":{"tf":2.8284271247461903},"1005":{"tf":1.0},"205":{"tf":1.0},"370":{"tf":1.0},"373":{"tf":1.0},"51":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":2.23606797749979},"577":{"tf":1.0},"724":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"c":{"df":3,"docs":{"521":{"tf":1.0},"54":{"tf":1.0},"880":{"tf":1.0}}},"df":32,"docs":{"1007":{"tf":1.0},"151":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.0},"231":{"tf":1.0},"249":{"tf":1.4142135623730951},"281":{"tf":1.0},"284":{"tf":1.0},"332":{"tf":1.0},"373":{"tf":1.4142135623730951},"38":{"tf":1.0},"39":{"tf":1.0},"416":{"tf":1.0},"51":{"tf":1.0},"54":{"tf":1.4142135623730951},"573":{"tf":1.0},"631":{"tf":1.0},"7":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":2.23606797749979},"776":{"tf":1.0},"81":{"tf":1.0},"842":{"tf":1.0},"85":{"tf":1.0},"9":{"tf":1.0},"938":{"tf":1.0},"947":{"tf":1.0}},"e":{"df":67,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"162":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"227":{"tf":1.0},"228":{"tf":1.0},"245":{"tf":1.0},"260":{"tf":1.0},"278":{"tf":1.0},"309":{"tf":1.0},"320":{"tf":1.0},"353":{"tf":1.0},"360":{"tf":1.0},"462":{"tf":1.0},"463":{"tf":1.0},"480":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"504":{"tf":1.0},"526":{"tf":1.0},"533":{"tf":1.0},"547":{"tf":1.0},"55":{"tf":1.0},"559":{"tf":1.0},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"602":{"tf":1.4142135623730951},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"662":{"tf":1.0},"672":{"tf":1.0},"674":{"tf":1.0},"676":{"tf":1.0},"677":{"tf":1.0},"684":{"tf":1.0},"686":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0},"707":{"tf":1.0},"726":{"tf":1.0},"735":{"tf":1.0},"753":{"tf":1.0},"761":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"825":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"880":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"976":{"tf":1.0},"986":{"tf":1.0},"993":{"tf":1.0},"997":{"tf":1.0},"999":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"16":{"tf":1.0},"254":{"tf":1.0}}}}}}}}}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"205":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"6":{"tf":2.23606797749979}}}}}}},"r":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"221":{"tf":1.0},"292":{"tf":1.0},"346":{"tf":1.0},"416":{"tf":1.0},"47":{"tf":1.0},"571":{"tf":1.0},"701":{"tf":1.0}}}},"df":1,"docs":{"427":{"tf":1.0}}}},"s":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"439":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"375":{"tf":1.0},"46":{"tf":1.0},"779":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"322":{"tf":1.0},"330":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"e":{"df":49,"docs":{"170":{"tf":1.0},"195":{"tf":1.7320508075688772},"204":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"22":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"3":{"tf":1.0},"301":{"tf":1.0},"315":{"tf":1.0},"341":{"tf":1.0},"348":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"420":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"523":{"tf":1.0},"564":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"602":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"761":{"tf":1.7320508075688772},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"817":{"tf":1.0},"826":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.7320508075688772},"938":{"tf":1.0}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.0}}}}}}}}},"h":{"df":4,"docs":{"170":{"tf":1.0},"522":{"tf":1.4142135623730951},"723":{"tf":1.0},"855":{"tf":1.0}}},"i":{"c":{"df":5,"docs":{"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"450":{"tf":1.4142135623730951},"63":{"tf":1.0},"8":{"tf":1.0}}},"df":0,"docs":{},"f":{"df":7,"docs":{"208":{"tf":1.0},"481":{"tf":1.7320508075688772},"482":{"tf":1.7320508075688772},"483":{"tf":1.4142135623730951},"485":{"tf":2.8284271247461903},"486":{"tf":1.4142135623730951},"491":{"tf":1.0}},"i":{"df":3,"docs":{"218":{"tf":1.4142135623730951},"222":{"tf":1.0},"60":{"tf":1.0}}},"y":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":2,"docs":{"221":{"tf":1.0},"222":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":2,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"222":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"234":{"tf":1.0},"3":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"v":{"a":{"df":3,"docs":{"191":{"tf":1.0},"804":{"tf":1.0},"853":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"323":{"tf":1.0}}},"m":{"b":{"df":5,"docs":{"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"808":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"df":29,"docs":{"140":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"46":{"tf":1.0},"485":{"tf":1.0},"537":{"tf":1.0},"573":{"tf":1.0},"605":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.7320508075688772},"651":{"tf":1.0},"653":{"tf":1.0},"697":{"tf":1.0},"701":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"75":{"tf":1.0},"767":{"tf":1.0},"776":{"tf":1.0},"831":{"tf":1.0},"885":{"tf":1.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"983":{"tf":1.0}}}},"p":{"df":0,"docs":{},"o":{"df":3,"docs":{"1004":{"tf":1.0},"374":{"tf":1.0},"571":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"234":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"207":{"tf":1.0}}}},"m":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"715":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":78,"docs":{"132":{"tf":1.0},"172":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":2.0},"205":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":2.0},"218":{"tf":1.4142135623730951},"221":{"tf":2.449489742783178},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"237":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.7320508075688772},"255":{"tf":1.0},"333":{"tf":1.0},"342":{"tf":2.23606797749979},"346":{"tf":2.6457513110645907},"347":{"tf":1.4142135623730951},"348":{"tf":1.7320508075688772},"349":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.4142135623730951},"428":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.0},"459":{"tf":1.0},"47":{"tf":2.23606797749979},"500":{"tf":1.0},"505":{"tf":1.0},"51":{"tf":1.4142135623730951},"520":{"tf":1.0},"525":{"tf":1.4142135623730951},"537":{"tf":1.0},"568":{"tf":1.7320508075688772},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"631":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"723":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.3166247903554},"742":{"tf":1.4142135623730951},"743":{"tf":1.4142135623730951},"744":{"tf":1.4142135623730951},"747":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.7320508075688772},"751":{"tf":1.4142135623730951},"758":{"tf":1.0},"761":{"tf":1.7320508075688772},"814":{"tf":1.0},"829":{"tf":1.0},"85":{"tf":1.0},"858":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":3.1622776601683795},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"221":{"tf":1.0},"427":{"tf":1.0},"55":{"tf":1.0}}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"668":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":2,"docs":{"435":{"tf":1.0},"553":{"tf":1.0}}}}}}}},"}":{"df":0,"docs":{},"{":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}},"}":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{")":{"^":{"d":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"o":{"[":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}},"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"537":{"tf":1.0}}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"231":{"tf":1.0},"255":{"tf":1.0},"3":{"tf":2.0},"333":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951},"352":{"tf":1.0},"390":{"tf":1.0},"411":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"776":{"tf":1.0}}}}},"s":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"833":{"tf":1.0},"874":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":6,"docs":{"450":{"tf":1.0},"555":{"tf":1.0},"571":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":10,"docs":{"193":{"tf":1.0},"254":{"tf":1.0},"567":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"739":{"tf":1.0},"759":{"tf":1.0},"84":{"tf":1.0},"88":{"tf":1.0}}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":3,"docs":{"234":{"tf":1.0},"571":{"tf":1.0},"732":{"tf":1.0}}}}}}},"c":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"450":{"tf":1.0}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"234":{"tf":1.0}},"i":{"df":7,"docs":{"441":{"tf":1.0},"450":{"tf":2.23606797749979},"60":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"724":{"tf":1.0},"77":{"tf":1.0}}}},"r":{"df":13,"docs":{"111":{"tf":1.0},"204":{"tf":1.0},"267":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"573":{"tf":1.0},"670":{"tf":1.0},"751":{"tf":1.0},"776":{"tf":1.4142135623730951},"804":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"95":{"tf":1.0}},"r":{"df":2,"docs":{"108":{"tf":1.0},"441":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"1":{"tf":1.0},"17":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"332":{"tf":1.7320508075688772},"333":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":6,"docs":{"332":{"tf":1.0},"333":{"tf":2.6457513110645907},"341":{"tf":3.0},"343":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"<":{"3":{"2":{"df":4,"docs":{"333":{"tf":1.0},"341":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.0}}},"df":0,"docs":{}},"4":{"df":1,"docs":{"343":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"o":{"b":{"df":6,"docs":{"164":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"782":{"tf":1.0},"795":{"tf":1.0}}},"df":0,"docs":{}}}},"df":2,"docs":{"112":{"tf":1.4142135623730951},"45":{"tf":1.0}},"e":{"c":{"d":{"df":4,"docs":{"466":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"479":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"f":{"3":{"df":0,"docs":{},"x":{"df":1,"docs":{"575":{"tf":1.0}}}},"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"459":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":1,"docs":{"779":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"372":{"tf":1.0},"375":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"376":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"d":{"df":1,"docs":{"573":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":25,"docs":{"121":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.0},"267":{"tf":1.0},"3":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.4142135623730951},"346":{"tf":1.0},"368":{"tf":1.7320508075688772},"412":{"tf":1.0},"429":{"tf":1.0},"521":{"tf":1.4142135623730951},"55":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"577":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"77":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"826":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":13,"docs":{"346":{"tf":1.4142135623730951},"514":{"tf":2.6457513110645907},"515":{"tf":3.0},"516":{"tf":1.0},"518":{"tf":1.7320508075688772},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"526":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"534":{"tf":1.4142135623730951}}}},"o":{"a":{"d":{"df":1,"docs":{"843":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"349":{"tf":1.0},"633":{"tf":2.0},"637":{"tf":1.0},"735":{"tf":2.8284271247461903}}}}}}},"l":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":2,"docs":{"122":{"tf":1.0},"136":{"tf":1.0}}}}},"d":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":4,"docs":{"207":{"tf":2.449489742783178},"749":{"tf":1.4142135623730951},"750":{"tf":1.7320508075688772},"752":{"tf":2.0}}},"df":0,"docs":{}}}}},"df":21,"docs":{"151":{"tf":1.0},"205":{"tf":1.7320508075688772},"221":{"tf":1.0},"3":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.7320508075688772},"559":{"tf":1.4142135623730951},"567":{"tf":1.0},"575":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"619":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.0},"67":{"tf":1.0},"705":{"tf":1.0},"73":{"tf":1.0},"983":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"440":{"tf":1.4142135623730951},"500":{"tf":1.0},"512":{"tf":1.4142135623730951},"553":{"tf":1.0},"559":{"tf":1.0},"609":{"tf":1.7320508075688772},"631":{"tf":1.0},"640":{"tf":1.0},"642":{"tf":1.0},"740":{"tf":1.0},"767":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"279":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"_":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"t":{"df":7,"docs":{"16":{"tf":1.0},"439":{"tf":1.0},"516":{"tf":1.0},"526":{"tf":1.0},"633":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":1,"docs":{"198":{"tf":1.0}}}}}}}}},"n":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"281":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"281":{"tf":1.0}}}}}}}},"b":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"r":{"d":{"df":5,"docs":{"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"301":{"tf":1.0},"414":{"tf":1.0},"928":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"c":{"df":34,"docs":{"1003":{"tf":1.0},"106":{"tf":1.0},"126":{"tf":2.0},"187":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.4142135623730951},"208":{"tf":1.0},"270":{"tf":1.0},"346":{"tf":1.0},"432":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"534":{"tf":1.0},"605":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"644":{"tf":1.4142135623730951},"67":{"tf":1.0},"71":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"739":{"tf":1.0},"759":{"tf":1.0},"77":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"816":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"936":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"303":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"61":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":131,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"177":{"tf":1.0},"188":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"214":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.0},"254":{"tf":1.7320508075688772},"257":{"tf":1.0},"267":{"tf":1.0},"276":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"314":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"351":{"tf":1.0},"356":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"388":{"tf":1.4142135623730951},"417":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"481":{"tf":1.7320508075688772},"483":{"tf":1.0},"485":{"tf":2.0},"486":{"tf":1.0},"491":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":2.0},"524":{"tf":1.7320508075688772},"525":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.0},"554":{"tf":1.0},"565":{"tf":1.0},"586":{"tf":1.0},"589":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.7320508075688772},"615":{"tf":1.0},"632":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.4142135623730951},"653":{"tf":1.0},"659":{"tf":1.4142135623730951},"665":{"tf":1.0},"67":{"tf":1.4142135623730951},"673":{"tf":1.4142135623730951},"69":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":1.7320508075688772},"718":{"tf":1.0},"720":{"tf":2.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.7320508075688772},"749":{"tf":1.0},"751":{"tf":1.0},"757":{"tf":1.0},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"770":{"tf":1.0},"778":{"tf":2.0},"779":{"tf":1.0},"78":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"80":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.4142135623730951},"815":{"tf":1.0},"822":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"832":{"tf":1.4142135623730951},"835":{"tf":1.0},"837":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.0},"855":{"tf":1.0},"879":{"tf":2.6457513110645907},"885":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"928":{"tf":1.4142135623730951},"933":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"976":{"tf":1.0}},"g":{"df":0,"docs":{},"o":{"df":7,"docs":{"124":{"tf":1.0},"126":{"tf":2.0},"132":{"tf":1.0},"148":{"tf":1.7320508075688772},"200":{"tf":1.0},"208":{"tf":1.0},"249":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"514":{"tf":1.7320508075688772}}}},"y":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"284":{"tf":1.7320508075688772},"286":{"tf":1.0},"292":{"tf":1.0}}}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":2.449489742783178}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"b":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"761":{"tf":2.23606797749979}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"o":{"df":7,"docs":{"199":{"tf":1.0},"217":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"522":{"tf":1.0},"588":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":3,"docs":{"222":{"tf":1.0},"602":{"tf":3.1622776601683795},"694":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":2,"docs":{"343":{"tf":1.0},"402":{"tf":1.0}},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.4142135623730951}}}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":8,"docs":{"205":{"tf":1.4142135623730951},"222":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"50":{"tf":1.0},"54":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":11,"docs":{"140":{"tf":1.0},"234":{"tf":1.0},"250":{"tf":1.0},"324":{"tf":1.0},"358":{"tf":1.0},"482":{"tf":1.0},"78":{"tf":1.0},"807":{"tf":1.0},"83":{"tf":1.0},"848":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951}},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":12,"docs":{"109":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"194":{"tf":1.0},"371":{"tf":1.0},"573":{"tf":1.0},"615":{"tf":1.0},"797":{"tf":1.0},"843":{"tf":1.0},"850":{"tf":1.0},"853":{"tf":1.0},"913":{"tf":1.0}}}}}},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"653":{"tf":1.0}}},"df":0,"docs":{}}},"df":58,"docs":{"107":{"tf":1.0},"138":{"tf":1.0},"146":{"tf":1.0},"153":{"tf":1.0},"18":{"tf":1.0},"205":{"tf":2.449489742783178},"207":{"tf":1.0},"22":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.4142135623730951},"232":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"29":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"325":{"tf":1.0},"33":{"tf":1.0},"335":{"tf":1.0},"363":{"tf":1.0},"368":{"tf":1.0},"38":{"tf":1.0},"41":{"tf":1.0},"418":{"tf":1.4142135623730951},"42":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"452":{"tf":1.7320508075688772},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":2.23606797749979},"48":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"554":{"tf":1.0},"573":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.4142135623730951},"72":{"tf":1.0},"720":{"tf":1.0},"725":{"tf":1.4142135623730951},"83":{"tf":1.0},"835":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"880":{"tf":2.449489742783178},"948":{"tf":1.0},"951":{"tf":1.0},"959":{"tf":1.0},"991":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":6,"docs":{"261":{"tf":1.0},"511":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"761":{"tf":1.0},"843":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":5,"docs":{"124":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"776":{"tf":1.0},"959":{"tf":1.0}}}}}},"s":{"df":2,"docs":{"175":{"tf":1.0},"933":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"735":{"tf":1.0},"932":{"tf":1.0}}}}}}},"t":{"df":7,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"385":{"tf":1.0},"705":{"tf":1.0},"776":{"tf":1.0},"813":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"df":32,"docs":{"1004":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"144":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"28":{"tf":1.4142135623730951},"373":{"tf":1.0},"377":{"tf":1.0},"380":{"tf":1.0},"429":{"tf":1.0},"460":{"tf":1.0},"483":{"tf":1.0},"50":{"tf":1.0},"522":{"tf":1.0},"527":{"tf":1.0},"58":{"tf":1.0},"608":{"tf":1.0},"640":{"tf":1.0},"761":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"951":{"tf":1.0},"968":{"tf":1.0},"972":{"tf":1.0},"996":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":5,"docs":{"436":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.4142135623730951},"449":{"tf":1.0}},"t":{"df":10,"docs":{"38":{"tf":2.23606797749979},"388":{"tf":1.0},"39":{"tf":2.23606797749979},"40":{"tf":2.0},"41":{"tf":1.0},"42":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.0},"49":{"tf":1.0},"54":{"tf":1.4142135623730951}}}}}},"o":{"df":0,"docs":{},"n":{"<":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"64":{"tf":1.0}}}}},"df":0,"docs":{}}},"[":{"df":0,"docs":{},"u":{"8":{";":{"2":{"0":{"df":1,"docs":{"898":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"526":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":3,"docs":{"602":{"tf":1.4142135623730951},"605":{"tf":1.0},"698":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"208":{"tf":1.0},"222":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"221":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"455":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"553":{"tf":1.0}}}}},"df":24,"docs":{"180":{"tf":1.0},"24":{"tf":1.4142135623730951},"253":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.4142135623730951},"290":{"tf":1.0},"356":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.4142135623730951},"530":{"tf":1.0},"553":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0},"693":{"tf":1.0},"715":{"tf":1.0},"761":{"tf":2.449489742783178},"778":{"tf":1.4142135623730951},"815":{"tf":1.0},"831":{"tf":1.7320508075688772},"84":{"tf":1.0},"848":{"tf":1.0},"872":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0}}}}}}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":60,"docs":{"107":{"tf":1.0},"111":{"tf":1.0},"171":{"tf":1.0},"172":{"tf":1.0},"173":{"tf":1.0},"188":{"tf":1.0},"203":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"216":{"tf":1.0},"231":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"293":{"tf":1.0},"302":{"tf":1.0},"313":{"tf":1.0},"331":{"tf":1.0},"335":{"tf":1.0},"343":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"375":{"tf":1.0},"390":{"tf":1.0},"436":{"tf":1.7320508075688772},"450":{"tf":1.0},"455":{"tf":1.4142135623730951},"467":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"540":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.4142135623730951},"600":{"tf":1.0},"63":{"tf":1.0},"665":{"tf":1.0},"697":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":2.8284271247461903},"758":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.4142135623730951},"816":{"tf":1.0},"829":{"tf":1.4142135623730951},"926":{"tf":1.4142135623730951},"931":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"936":{"tf":1.0},"938":{"tf":1.0}}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"n":{"df":7,"docs":{"134":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"317":{"tf":1.0},"362":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}},"z":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"876":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"777":{"tf":1.0}}}}}},"df":1,"docs":{"640":{"tf":1.0}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"701":{"tf":1.0}}},":":{":":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"/":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"3":{"2":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"617":{"tf":1.4142135623730951},"83":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":58,"docs":{"108":{"tf":1.7320508075688772},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"121":{"tf":1.0},"16":{"tf":1.4142135623730951},"169":{"tf":1.4142135623730951},"171":{"tf":1.4142135623730951},"177":{"tf":1.0},"205":{"tf":3.1622776601683795},"234":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"274":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.7320508075688772},"35":{"tf":1.4142135623730951},"375":{"tf":1.0},"410":{"tf":1.0},"427":{"tf":1.4142135623730951},"435":{"tf":1.4142135623730951},"436":{"tf":1.0},"483":{"tf":1.0},"537":{"tf":2.23606797749979},"546":{"tf":1.4142135623730951},"565":{"tf":1.0},"570":{"tf":1.0},"58":{"tf":1.0},"6":{"tf":2.449489742783178},"600":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"619":{"tf":1.0},"692":{"tf":2.8284271247461903},"693":{"tf":2.0},"694":{"tf":1.7320508075688772},"696":{"tf":2.6457513110645907},"697":{"tf":1.7320508075688772},"698":{"tf":2.0},"700":{"tf":1.4142135623730951},"701":{"tf":2.0},"704":{"tf":1.0},"705":{"tf":2.0},"706":{"tf":1.0},"722":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":2.23606797749979},"80":{"tf":1.0},"814":{"tf":1.0},"83":{"tf":1.7320508075688772},"85":{"tf":1.0},"879":{"tf":5.0990195135927845},"885":{"tf":2.0},"931":{"tf":1.0},"976":{"tf":1.0},"983":{"tf":1.0}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":3,"docs":{"814":{"tf":1.4142135623730951},"879":{"tf":3.4641016151377544},"885":{"tf":2.0}}}},"df":0,"docs":{}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{":":{":":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"83":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":1,"docs":{"617":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}},"p":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"348":{"tf":1.4142135623730951},"349":{"tf":1.0}}}},"df":0,"docs":{}}},"u":{"df":8,"docs":{"39":{"tf":1.0},"40":{"tf":1.0},"41":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.4142135623730951},"48":{"tf":1.4142135623730951},"55":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":12,"docs":{"253":{"tf":1.0},"276":{"tf":1.0},"371":{"tf":1.0},"453":{"tf":1.0},"469":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"78":{"tf":1.0},"80":{"tf":1.0}},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":20,"docs":{"124":{"tf":1.0},"160":{"tf":1.4142135623730951},"204":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"44":{"tf":1.0},"461":{"tf":1.0},"499":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"629":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"69":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"752":{"tf":1.0},"814":{"tf":1.0},"879":{"tf":2.0},"97":{"tf":1.0}}}}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":2,"docs":{"267":{"tf":1.0},"723":{"tf":1.0}}}}}}},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":4,"docs":{"124":{"tf":1.0},"125":{"tf":1.0},"829":{"tf":1.0},"933":{"tf":1.4142135623730951}}}}},"df":35,"docs":{"187":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"47":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"577":{"tf":1.0},"660":{"tf":1.0},"680":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":1.0},"722":{"tf":1.7320508075688772},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":8.12403840463596},"740":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.4142135623730951},"855":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"267":{"tf":1.0},"330":{"tf":1.0},"351":{"tf":1.0},"361":{"tf":1.0},"38":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":1,"docs":{"187":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":10,"docs":{"22":{"tf":1.7320508075688772},"340":{"tf":1.4142135623730951},"341":{"tf":1.7320508075688772},"346":{"tf":1.0},"435":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"633":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.1622776601683795}}}}},"r":{"df":0,"docs":{},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"711":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"d":{"df":18,"docs":{"155":{"tf":1.0},"16":{"tf":1.0},"190":{"tf":1.0},"194":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"272":{"tf":1.0},"290":{"tf":1.0},"343":{"tf":1.0},"348":{"tf":1.0},"514":{"tf":1.0},"567":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":3.4641016151377544},"776":{"tf":1.0},"849":{"tf":1.0}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"577":{"tf":1.0}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":17,"docs":{"144":{"tf":1.0},"198":{"tf":1.0},"21":{"tf":1.0},"267":{"tf":1.4142135623730951},"407":{"tf":1.0},"414":{"tf":1.0},"459":{"tf":1.0},"563":{"tf":1.0},"599":{"tf":1.0},"640":{"tf":1.0},"724":{"tf":1.0},"794":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0},"835":{"tf":1.0},"843":{"tf":1.0},"94":{"tf":1.0}}}},"b":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"777":{"tf":1.0}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"898":{"tf":1.0}}}}},"df":57,"docs":{"126":{"tf":1.7320508075688772},"19":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"21":{"tf":1.0},"214":{"tf":1.0},"237":{"tf":1.0},"281":{"tf":1.0},"33":{"tf":1.0},"373":{"tf":1.4142135623730951},"38":{"tf":1.0},"428":{"tf":1.0},"436":{"tf":1.0},"455":{"tf":1.0},"46":{"tf":1.0},"523":{"tf":1.0},"537":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":1.0},"69":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"701":{"tf":1.0},"722":{"tf":1.7320508075688772},"729":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"779":{"tf":1.0},"815":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":2.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"885":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"402":{"tf":1.0}}}}}}},"f":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"208":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":21,"docs":{"1010":{"tf":1.0},"131":{"tf":1.0},"144":{"tf":1.0},"257":{"tf":1.0},"288":{"tf":1.0},"296":{"tf":1.0},"437":{"tf":1.0},"507":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"615":{"tf":1.0},"725":{"tf":1.0},"777":{"tf":1.0},"790":{"tf":1.0},"853":{"tf":1.0},"902":{"tf":1.0},"945":{"tf":1.0},"951":{"tf":1.0},"962":{"tf":1.0},"968":{"tf":1.0},"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"p":{"df":5,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":1,"docs":{"826":{"tf":1.0}}},"o":{"a":{"d":{"df":1,"docs":{"218":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"111":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":7,"docs":{"195":{"tf":1.0},"203":{"tf":1.0},"38":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.0},"741":{"tf":1.0},"747":{"tf":1.0}}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"720":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"154":{"tf":1.0}}}}}}}}},"w":{"df":1,"docs":{"573":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"878":{"tf":1.0}}}},"n":{"df":3,"docs":{"203":{"tf":1.0},"3":{"tf":1.0},"553":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"203":{"tf":2.0},"204":{"tf":1.7320508075688772},"205":{"tf":2.8284271247461903},"208":{"tf":4.69041575982343},"3":{"tf":1.4142135623730951},"339":{"tf":1.0},"349":{"tf":1.0},"457":{"tf":1.0},"773":{"tf":1.0},"81":{"tf":1.0},"944":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":18,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.0},"208":{"tf":1.0},"322":{"tf":1.0},"339":{"tf":1.4142135623730951},"346":{"tf":1.0},"351":{"tf":1.0},"451":{"tf":1.7320508075688772},"452":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"460":{"tf":1.0},"461":{"tf":1.0},"602":{"tf":1.0},"79":{"tf":1.0},"84":{"tf":1.4142135623730951}}}}}}}}}}},"p":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.0}}}},"0":{"df":1,"docs":{"208":{"tf":1.0}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"5":{"6":{"df":2,"docs":{"93":{"tf":1.7320508075688772},"94":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":1,"docs":{"551":{"tf":1.0}}}},"4":{"9":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"n":{"df":2,"docs":{"44":{"tf":1.0},"45":{"tf":1.0}}},"{":{"\\":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.7320508075688772}}}}},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"749":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"n":{"+":{"1":{"df":2,"docs":{"44":{"tf":1.0},"45":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"44":{"tf":1.7320508075688772},"45":{"tf":1.0}}}}},"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":3,"docs":{"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"e":{"df":1,"docs":{"440":{"tf":1.0}}},"k":{"a":{"df":0,"docs":{},"g":{"df":8,"docs":{"44":{"tf":2.23606797749979},"45":{"tf":2.23606797749979},"46":{"tf":1.7320508075688772},"49":{"tf":1.0},"50":{"tf":1.4142135623730951},"51":{"tf":1.0},"52":{"tf":1.0},"553":{"tf":1.4142135623730951}}}},"df":1,"docs":{"25":{"tf":1.4142135623730951}}}},"d":{"df":1,"docs":{"435":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":3,"docs":{"827":{"tf":1.7320508075688772},"829":{"tf":2.0},"832":{"tf":1.0}}}},"i":{"d":{"df":21,"docs":{"111":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"267":{"tf":1.7320508075688772},"272":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"649":{"tf":1.0},"653":{"tf":1.0},"711":{"tf":1.0},"808":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.7320508075688772},"815":{"tf":1.7320508075688772},"816":{"tf":1.4142135623730951},"817":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":2,"docs":{"244":{"tf":1.0},"926":{"tf":1.0}}}}},"df":0,"docs":{}},"n":{"df":1,"docs":{"799":{"tf":1.4142135623730951}}},"r":{"df":5,"docs":{"47":{"tf":1.0},"5":{"tf":1.0},"697":{"tf":1.0},"722":{"tf":1.0},"95":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"234":{"tf":1.0}}},":":{":":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"(":{"3":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{":":{":":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":5,"docs":{"927":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.4142135623730951},"935":{"tf":1.0}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"937":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"a":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"a":{":":{":":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":3,"docs":{"931":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"935":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"931":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"931":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"931":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"701":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":68,"docs":{"121":{"tf":1.0},"125":{"tf":1.0},"133":{"tf":1.0},"149":{"tf":1.4142135623730951},"18":{"tf":1.4142135623730951},"21":{"tf":1.0},"216":{"tf":1.0},"219":{"tf":1.0},"220":{"tf":1.0},"234":{"tf":2.0},"24":{"tf":1.0},"261":{"tf":1.0},"269":{"tf":1.0},"273":{"tf":1.7320508075688772},"284":{"tf":1.7320508075688772},"300":{"tf":1.0},"315":{"tf":1.4142135623730951},"35":{"tf":2.0},"370":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":2.449489742783178},"382":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"511":{"tf":1.0},"519":{"tf":1.7320508075688772},"697":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"804":{"tf":1.0},"814":{"tf":1.7320508075688772},"816":{"tf":2.6457513110645907},"817":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0},"871":{"tf":1.7320508075688772},"872":{"tf":1.7320508075688772},"874":{"tf":1.4142135623730951},"878":{"tf":1.0},"882":{"tf":1.0},"885":{"tf":1.4142135623730951},"887":{"tf":1.0},"888":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.0},"914":{"tf":1.0},"917":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.7320508075688772},"936":{"tf":1.0},"938":{"tf":1.4142135623730951},"939":{"tf":1.4142135623730951},"941":{"tf":1.4142135623730951},"942":{"tf":2.8284271247461903},"943":{"tf":1.0},"945":{"tf":1.4142135623730951},"961":{"tf":1.7320508075688772},"972":{"tf":1.0},"980":{"tf":1.0}},"’":{"df":1,"docs":{"943":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"324":{"tf":1.4142135623730951},"325":{"tf":1.0},"359":{"tf":1.4142135623730951},"39":{"tf":1.0},"44":{"tf":1.0}}}}},"r":{"a":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"[":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"634":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"d":{"df":3,"docs":{"252":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"634":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"df":1,"docs":{"699":{"tf":1.0}}},"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"715":{"tf":1.0},"720":{"tf":1.0}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"300":{"tf":1.0}}},"(":{"1":{"0":{"0":{"0":{")":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"786":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"/":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"3":{"2":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"600":{"tf":1.0}}},"df":130,"docs":{"100":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"108":{"tf":2.0},"109":{"tf":1.4142135623730951},"111":{"tf":1.4142135623730951},"114":{"tf":1.0},"118":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":2.0},"155":{"tf":1.7320508075688772},"160":{"tf":1.4142135623730951},"18":{"tf":1.0},"198":{"tf":2.0},"199":{"tf":1.4142135623730951},"200":{"tf":1.0},"201":{"tf":1.4142135623730951},"203":{"tf":2.6457513110645907},"209":{"tf":1.0},"210":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.4142135623730951},"222":{"tf":1.0},"247":{"tf":1.7320508075688772},"248":{"tf":1.0},"249":{"tf":2.23606797749979},"251":{"tf":2.0},"252":{"tf":1.7320508075688772},"253":{"tf":2.449489742783178},"254":{"tf":2.23606797749979},"255":{"tf":2.6457513110645907},"257":{"tf":2.23606797749979},"262":{"tf":1.4142135623730951},"269":{"tf":1.4142135623730951},"270":{"tf":1.0},"276":{"tf":1.4142135623730951},"282":{"tf":1.0},"289":{"tf":1.0},"294":{"tf":1.7320508075688772},"295":{"tf":2.6457513110645907},"296":{"tf":4.58257569495584},"297":{"tf":2.6457513110645907},"298":{"tf":1.4142135623730951},"30":{"tf":1.0},"300":{"tf":4.123105625617661},"301":{"tf":3.3166247903554},"302":{"tf":2.449489742783178},"303":{"tf":3.7416573867739413},"306":{"tf":1.0},"308":{"tf":2.0},"310":{"tf":1.0},"367":{"tf":1.7320508075688772},"368":{"tf":1.7320508075688772},"369":{"tf":1.0},"374":{"tf":1.4142135623730951},"375":{"tf":3.872983346207417},"376":{"tf":2.23606797749979},"381":{"tf":1.4142135623730951},"39":{"tf":1.0},"400":{"tf":1.4142135623730951},"401":{"tf":1.0},"402":{"tf":1.4142135623730951},"403":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"438":{"tf":1.0},"440":{"tf":1.0},"444":{"tf":1.0},"450":{"tf":1.0},"496":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"515":{"tf":1.0},"56":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.4142135623730951},"571":{"tf":1.0},"58":{"tf":2.0},"59":{"tf":1.0},"60":{"tf":1.7320508075688772},"627":{"tf":1.4142135623730951},"629":{"tf":2.0},"63":{"tf":1.4142135623730951},"632":{"tf":1.4142135623730951},"633":{"tf":2.0},"636":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.7320508075688772},"65":{"tf":1.0},"67":{"tf":1.0},"697":{"tf":1.4142135623730951},"699":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.4142135623730951},"714":{"tf":1.0},"72":{"tf":1.4142135623730951},"722":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":2.449489742783178},"73":{"tf":1.7320508075688772},"745":{"tf":1.0},"77":{"tf":1.7320508075688772},"774":{"tf":1.0},"78":{"tf":1.4142135623730951},"808":{"tf":1.7320508075688772},"809":{"tf":1.0},"81":{"tf":2.8284271247461903},"810":{"tf":2.6457513110645907},"812":{"tf":1.0},"813":{"tf":2.0},"814":{"tf":2.8284271247461903},"815":{"tf":2.8284271247461903},"816":{"tf":1.0},"817":{"tf":1.7320508075688772},"818":{"tf":1.4142135623730951},"822":{"tf":1.7320508075688772},"826":{"tf":1.4142135623730951},"83":{"tf":3.3166247903554},"831":{"tf":1.0},"859":{"tf":1.0},"928":{"tf":1.4142135623730951},"934":{"tf":1.0},"938":{"tf":1.4142135623730951}},"x":{"df":1,"docs":{"600":{"tf":1.0}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"m":{"df":1,"docs":{"198":{"tf":1.0}}}}}},"df":22,"docs":{"106":{"tf":1.0},"107":{"tf":1.4142135623730951},"108":{"tf":1.7320508075688772},"111":{"tf":2.6457513110645907},"112":{"tf":3.4641016151377544},"113":{"tf":1.4142135623730951},"114":{"tf":1.4142135623730951},"118":{"tf":1.0},"121":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"243":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"329":{"tf":1.0},"440":{"tf":1.0},"633":{"tf":3.4641016151377544},"634":{"tf":1.4142135623730951},"808":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":2.0},"817":{"tf":1.7320508075688772}},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"h":{"df":1,"docs":{"346":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"d":{"df":10,"docs":{"204":{"tf":1.4142135623730951},"218":{"tf":1.0},"221":{"tf":1.0},"273":{"tf":1.0},"634":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":2.23606797749979},"817":{"tf":1.4142135623730951},"818":{"tf":1.0}}},"df":0,"docs":{}},"k":{"df":1,"docs":{"600":{"tf":1.0}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":2,"docs":{"375":{"tf":1.4142135623730951},"436":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"735":{"tf":11.269427669584644}},"e":{"df":0,"docs":{},"t":{"df":52,"docs":{"121":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"148":{"tf":1.0},"184":{"tf":1.0},"186":{"tf":1.0},"191":{"tf":1.4142135623730951},"194":{"tf":1.0},"204":{"tf":1.7320508075688772},"207":{"tf":2.0},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"322":{"tf":1.0},"342":{"tf":1.4142135623730951},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"364":{"tf":1.4142135623730951},"390":{"tf":1.0},"397":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.4142135623730951},"521":{"tf":1.0},"534":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.7320508075688772},"602":{"tf":1.7320508075688772},"605":{"tf":1.0},"613":{"tf":1.7320508075688772},"614":{"tf":1.0},"615":{"tf":1.7320508075688772},"617":{"tf":1.0},"668":{"tf":1.0},"693":{"tf":1.0},"698":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"741":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":1.0},"857":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"870":{"tf":1.0},"885":{"tf":1.0},"929":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"939":{"tf":1.0},"95":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":2,"docs":{"416":{"tf":1.0},"933":{"tf":1.0}}}}}},"df":7,"docs":{"196":{"tf":1.0},"438":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"213":{"tf":1.0}}}}}},"r":{"df":1,"docs":{"575":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"244":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"df":1,"docs":{"600":{"tf":1.0}}},"s":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"300":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":2,"docs":{"466":{"tf":1.0},"467":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":9,"docs":{"44":{"tf":1.0},"450":{"tf":1.0},"46":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"637":{"tf":1.4142135623730951},"640":{"tf":1.7320508075688772},"786":{"tf":2.23606797749979},"932":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":4,"docs":{"201":{"tf":1.4142135623730951},"513":{"tf":1.0},"774":{"tf":1.0},"843":{"tf":1.0}}},"y":{"'":{"df":3,"docs":{"436":{"tf":1.0},"450":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":3,"docs":{"517":{"tf":1.0},"544":{"tf":1.0},"762":{"tf":1.0}}},"t":{"df":41,"docs":{"126":{"tf":1.0},"181":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"230":{"tf":1.4142135623730951},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"270":{"tf":1.7320508075688772},"272":{"tf":1.0},"293":{"tf":1.0},"333":{"tf":1.0},"345":{"tf":1.0},"347":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.4142135623730951},"459":{"tf":1.0},"5":{"tf":1.0},"514":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"537":{"tf":1.0},"544":{"tf":1.0},"548":{"tf":1.0},"605":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.0},"634":{"tf":1.0},"67":{"tf":1.0},"701":{"tf":1.4142135623730951},"725":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"796":{"tf":1.0},"83":{"tf":1.7320508075688772},"863":{"tf":1.0},"878":{"tf":1.0},"931":{"tf":1.0}},"i":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"6":{"tf":1.0},"615":{"tf":1.0},"881":{"tf":1.0}}}},"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":29,"docs":{"1004":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.4142135623730951},"303":{"tf":2.0},"346":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"439":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.0},"500":{"tf":1.0},"502":{"tf":1.7320508075688772},"503":{"tf":2.0},"512":{"tf":1.0},"565":{"tf":1.4142135623730951},"570":{"tf":1.0},"629":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":1.4142135623730951},"797":{"tf":2.23606797749979},"799":{"tf":2.0},"807":{"tf":1.0},"929":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":27,"docs":{"171":{"tf":1.0},"177":{"tf":1.4142135623730951},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"231":{"tf":1.0},"267":{"tf":1.0},"352":{"tf":1.0},"371":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"418":{"tf":1.0},"432":{"tf":1.0},"46":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":1.0},"628":{"tf":1.0},"633":{"tf":1.0},"664":{"tf":1.0},"711":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"799":{"tf":1.7320508075688772},"832":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"832":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"142":{"tf":1.0},"381":{"tf":1.0},"414":{"tf":1.0},"439":{"tf":1.0},"711":{"tf":1.0},"810":{"tf":1.0},"876":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":8,"docs":{"170":{"tf":1.0},"514":{"tf":1.0},"528":{"tf":1.0},"56":{"tf":1.0},"66":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.4142135623730951},"912":{"tf":1.0}},"t":{"df":4,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.0},"335":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"5":{"7":{"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":3,"docs":{"128":{"tf":1.0},"142":{"tf":1.0},"680":{"tf":1.0}}}},"s":{"df":33,"docs":{"126":{"tf":2.6457513110645907},"205":{"tf":2.0},"207":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"211":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"272":{"tf":1.0},"274":{"tf":1.0},"288":{"tf":1.0},"388":{"tf":1.4142135623730951},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"456":{"tf":1.0},"457":{"tf":1.0},"461":{"tf":1.0},"531":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":1.0},"64":{"tf":1.0},"653":{"tf":1.0},"655":{"tf":1.0},"72":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"786":{"tf":1.0},"829":{"tf":1.0},"849":{"tf":1.0},"885":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":3,"docs":{"471":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":2,"docs":{"221":{"tf":1.0},"761":{"tf":1.0}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"996":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":20,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"138":{"tf":1.0},"264":{"tf":1.0},"270":{"tf":1.0},"430":{"tf":1.0},"440":{"tf":1.0},"446":{"tf":1.0},"522":{"tf":2.23606797749979},"602":{"tf":2.23606797749979},"603":{"tf":1.0},"705":{"tf":1.0},"73":{"tf":1.0},"786":{"tf":1.0},"831":{"tf":2.23606797749979},"832":{"tf":1.7320508075688772},"835":{"tf":1.7320508075688772},"837":{"tf":1.0},"840":{"tf":1.0},"970":{"tf":1.0}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"139":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"a":{"df":1,"docs":{"46":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":8,"docs":{"1011":{"tf":1.0},"147":{"tf":1.0},"21":{"tf":1.0},"267":{"tf":1.0},"407":{"tf":1.0},"605":{"tf":1.0},"696":{"tf":1.0},"786":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"573":{"tf":1.0}}}},"y":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":1,"docs":{"814":{"tf":1.0}}}}}}},"df":24,"docs":{"208":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"534":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":2.23606797749979},"600":{"tf":1.0},"603":{"tf":1.7320508075688772},"614":{"tf":1.0},"615":{"tf":1.0},"651":{"tf":1.0},"654":{"tf":1.0},"659":{"tf":1.0},"699":{"tf":2.0},"724":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.7320508075688772},"777":{"tf":2.23606797749979},"811":{"tf":1.0},"849":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0}},"e":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"f":{"df":0,"docs":{},"e":{"df":6,"docs":{"650":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"655":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.4142135623730951}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":10,"docs":{"170":{"tf":1.0},"171":{"tf":2.0},"175":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.0},"517":{"tf":1.0},"537":{"tf":1.0},"586":{"tf":1.4142135623730951},"78":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"208":{"tf":1.0},"473":{"tf":1.0},"537":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"653":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.7320508075688772},"813":{"tf":1.4142135623730951},"814":{"tf":2.0},"822":{"tf":1.0},"860":{"tf":1.0},"976":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":3,"docs":{"208":{"tf":1.0},"376":{"tf":1.0},"932":{"tf":1.0}}}}}}},"b":{"a":{"df":1,"docs":{"133":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"44":{"tf":1.0}},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"253":{"tf":1.0},"254":{"tf":1.0}}},"df":0,"docs":{}}},"df":11,"docs":{"248":{"tf":1.4142135623730951},"253":{"tf":1.0},"257":{"tf":1.0},"436":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"512":{"tf":2.0},"554":{"tf":1.0},"69":{"tf":1.0},"759":{"tf":1.4142135623730951}},"i":{"d":{"/":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"551":{"tf":1.0}}}}}}}}}},"df":6,"docs":{"249":{"tf":1.0},"254":{"tf":2.0},"255":{"tf":1.0},"505":{"tf":1.0},"551":{"tf":1.4142135623730951},"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"553":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"g":{"df":1,"docs":{"429":{"tf":1.0}}},"n":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"718":{"tf":1.0},"724":{"tf":1.0}}}},"d":{"df":3,"docs":{"450":{"tf":1.0},"573":{"tf":1.0},"879":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":6,"docs":{"150":{"tf":1.7320508075688772},"154":{"tf":2.23606797749979},"155":{"tf":1.0},"156":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}},"df":1,"docs":{"603":{"tf":2.8284271247461903}},"p":{"a":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":1,"docs":{"603":{"tf":2.6457513110645907}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{">":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{"]":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":9,"docs":{"233":{"tf":1.0},"250":{"tf":1.0},"373":{"tf":1.4142135623730951},"385":{"tf":1.0},"471":{"tf":1.0},"498":{"tf":1.0},"761":{"tf":1.0},"849":{"tf":1.4142135623730951},"852":{"tf":1.0}},"e":{"/":{"d":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"r":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{".":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"(":{"(":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{".":{"0":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{".":{"0":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"s":{"df":1,"docs":{"814":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"2":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"199":{"tf":1.0}}}},"n":{"df":0,"docs":{},"t":{"(":{"1":{"0":{"0":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"0":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"213":{"tf":1.0},"576":{"tf":1.0},"814":{"tf":1.0},"928":{"tf":1.0}}}},"df":2,"docs":{"221":{"tf":1.0},"846":{"tf":1.7320508075688772}}}},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"723":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}}}},"df":50,"docs":{"1003":{"tf":1.0},"1008":{"tf":1.0},"191":{"tf":1.0},"199":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"235":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"402":{"tf":1.0},"432":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"481":{"tf":1.4142135623730951},"485":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"50":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"586":{"tf":1.0},"606":{"tf":1.4142135623730951},"670":{"tf":1.0},"71":{"tf":1.0},"722":{"tf":1.0},"724":{"tf":1.0},"739":{"tf":1.0},"744":{"tf":1.4142135623730951},"75":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"835":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.4142135623730951}},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"199":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":211,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.0},"1002":{"tf":1.4142135623730951},"1004":{"tf":1.0},"1007":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1010":{"tf":1.0},"102":{"tf":1.0},"106":{"tf":1.4142135623730951},"108":{"tf":1.0},"11":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"116":{"tf":1.0},"117":{"tf":1.4142135623730951},"122":{"tf":1.4142135623730951},"129":{"tf":1.0},"130":{"tf":1.0},"136":{"tf":1.4142135623730951},"143":{"tf":1.0},"144":{"tf":1.4142135623730951},"150":{"tf":1.4142135623730951},"151":{"tf":1.0},"152":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.4142135623730951},"164":{"tf":1.4142135623730951},"17":{"tf":1.7320508075688772},"175":{"tf":1.0},"176":{"tf":1.4142135623730951},"18":{"tf":1.0},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.4142135623730951},"195":{"tf":1.0},"210":{"tf":1.0},"215":{"tf":1.0},"224":{"tf":1.0},"229":{"tf":1.4142135623730951},"238":{"tf":1.4142135623730951},"239":{"tf":1.0},"247":{"tf":1.4142135623730951},"25":{"tf":1.0},"256":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.0},"268":{"tf":1.0},"276":{"tf":1.4142135623730951},"279":{"tf":1.4142135623730951},"28":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.7320508075688772},"294":{"tf":1.0},"296":{"tf":2.0},"297":{"tf":1.0},"300":{"tf":1.0},"305":{"tf":1.4142135623730951},"31":{"tf":1.0},"311":{"tf":1.0},"318":{"tf":1.0},"32":{"tf":1.0},"322":{"tf":1.4142135623730951},"355":{"tf":1.0},"356":{"tf":1.0},"366":{"tf":1.4142135623730951},"379":{"tf":1.0},"380":{"tf":1.4142135623730951},"386":{"tf":1.4142135623730951},"393":{"tf":1.0},"394":{"tf":1.4142135623730951},"400":{"tf":1.4142135623730951},"405":{"tf":1.0},"406":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"421":{"tf":1.0},"422":{"tf":1.7320508075688772},"430":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.4142135623730951},"438":{"tf":1.0},"440":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.4142135623730951},"449":{"tf":1.0},"45":{"tf":1.0},"451":{"tf":1.4142135623730951},"458":{"tf":1.0},"459":{"tf":1.7320508075688772},"465":{"tf":1.4142135623730951},"47":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"481":{"tf":1.4142135623730951},"488":{"tf":1.0},"489":{"tf":1.0},"495":{"tf":1.4142135623730951},"506":{"tf":1.0},"507":{"tf":1.0},"513":{"tf":1.4142135623730951},"529":{"tf":1.0},"530":{"tf":1.7320508075688772},"535":{"tf":1.4142135623730951},"54":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.4142135623730951},"549":{"tf":1.4142135623730951},"556":{"tf":1.0},"557":{"tf":1.0},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"565":{"tf":1.0},"579":{"tf":1.0},"580":{"tf":1.4142135623730951},"584":{"tf":1.4142135623730951},"591":{"tf":1.0},"592":{"tf":1.4142135623730951},"598":{"tf":1.4142135623730951},"606":{"tf":1.0},"607":{"tf":1.4142135623730951},"613":{"tf":1.4142135623730951},"620":{"tf":1.0},"621":{"tf":1.4142135623730951},"627":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.4142135623730951},"649":{"tf":1.4142135623730951},"657":{"tf":1.0},"658":{"tf":1.7320508075688772},"664":{"tf":1.4142135623730951},"671":{"tf":1.0},"672":{"tf":1.0},"678":{"tf":1.4142135623730951},"685":{"tf":1.0},"686":{"tf":1.0},"692":{"tf":1.4142135623730951},"70":{"tf":1.0},"700":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"709":{"tf":1.0},"71":{"tf":1.4142135623730951},"72":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.4142135623730951},"725":{"tf":1.0},"739":{"tf":1.4142135623730951},"757":{"tf":1.4142135623730951},"759":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.4142135623730951},"782":{"tf":1.4142135623730951},"789":{"tf":1.0},"79":{"tf":1.4142135623730951},"790":{"tf":1.4142135623730951},"795":{"tf":1.4142135623730951},"8":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"808":{"tf":1.4142135623730951},"820":{"tf":1.0},"821":{"tf":1.4142135623730951},"827":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":2.0},"841":{"tf":1.4142135623730951},"851":{"tf":1.0},"852":{"tf":1.7320508075688772},"857":{"tf":1.4142135623730951},"86":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.4142135623730951},"87":{"tf":1.0},"871":{"tf":1.4142135623730951},"874":{"tf":1.4142135623730951},"884":{"tf":1.0},"885":{"tf":1.0},"891":{"tf":1.4142135623730951},"901":{"tf":1.0},"902":{"tf":1.0},"908":{"tf":1.7320508075688772},"916":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.7320508075688772},"926":{"tf":1.0},"93":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951},"94":{"tf":1.0},"940":{"tf":1.4142135623730951},"948":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"957":{"tf":1.4142135623730951},"962":{"tf":1.4142135623730951},"965":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.7320508075688772},"972":{"tf":1.0},"974":{"tf":1.4142135623730951},"981":{"tf":1.0},"982":{"tf":1.4142135623730951},"988":{"tf":1.4142135623730951},"992":{"tf":1.0},"995":{"tf":1.0},"996":{"tf":1.4142135623730951}}}}}},"h":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"376":{"tf":1.0},"720":{"tf":1.0},"849":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"d":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"u":{"3":{"2":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"d":{"df":57,"docs":{"1003":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":5.291502622129181},"127":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"148":{"tf":1.0},"172":{"tf":1.0},"182":{"tf":1.7320508075688772},"183":{"tf":1.0},"184":{"tf":2.23606797749979},"186":{"tf":1.0},"187":{"tf":1.7320508075688772},"188":{"tf":1.4142135623730951},"190":{"tf":1.0},"193":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.7320508075688772},"204":{"tf":4.242640687119285},"205":{"tf":2.6457513110645907},"206":{"tf":1.0},"207":{"tf":2.0},"213":{"tf":1.4142135623730951},"221":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.4142135623730951},"372":{"tf":1.0},"422":{"tf":1.0},"505":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":2.23606797749979},"567":{"tf":1.7320508075688772},"575":{"tf":1.7320508075688772},"577":{"tf":1.0},"63":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":2.23606797749979},"744":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":3.4641016151377544},"809":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"837":{"tf":1.0},"846":{"tf":1.4142135623730951},"861":{"tf":2.0},"862":{"tf":2.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"199":{"tf":1.0},"311":{"tf":1.0},"875":{"tf":1.0}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":12,"docs":{"111":{"tf":1.0},"199":{"tf":1.0},"237":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"371":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"124":{"tf":1.0},"199":{"tf":1.0}}}}}}}}}}},"t":{"df":3,"docs":{"111":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0}}}},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"431":{"tf":1.0},"438":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"337":{"tf":1.0},"347":{"tf":2.23606797749979},"634":{"tf":1.0},"69":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"373":{"tf":1.0}}},"df":0,"docs":{}}}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.0},"230":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"605":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0},"786":{"tf":2.449489742783178}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"402":{"tf":1.4142135623730951}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"244":{"tf":1.0}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":5,"docs":{"229":{"tf":1.0},"268":{"tf":1.0},"366":{"tf":1.0},"410":{"tf":1.0},"465":{"tf":1.0}}}}}}}}}},"g":{"df":0,"docs":{},"p":{"df":9,"docs":{"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"894":{"tf":1.7320508075688772},"895":{"tf":2.0},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":1.7320508075688772},"900":{"tf":1.0},"902":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"895":{"tf":2.449489742783178},"898":{"tf":1.0}}}}}}}}}}}}}}},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":14,"docs":{"209":{"tf":1.0},"335":{"tf":1.0},"339":{"tf":1.0},"450":{"tf":1.0},"680":{"tf":1.0},"720":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"841":{"tf":1.7320508075688772},"845":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"957":{"tf":1.0}},"i":{"df":0,"docs":{},"p":{"df":2,"docs":{"940":{"tf":1.0},"945":{"tf":1.0}}}}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"711":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"436":{"tf":1.0},"553":{"tf":1.4142135623730951},"640":{"tf":1.0}}}},"df":1,"docs":{"45":{"tf":1.0}},"e":{"c":{"df":5,"docs":{"214":{"tf":1.0},"497":{"tf":1.0},"514":{"tf":1.0},"522":{"tf":1.0},"724":{"tf":1.0}},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"747":{"tf":1.0}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":6,"docs":{"247":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0},"827":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"y":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"588":{"tf":1.0},"74":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"177":{"tf":1.0},"776":{"tf":1.0}}}}}}},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":2,"docs":{"164":{"tf":1.0},"535":{"tf":1.0}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"1008":{"tf":1.0},"900":{"tf":1.0},"917":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":2,"docs":{"205":{"tf":1.7320508075688772},"778":{"tf":1.0}}}}}},"l":{"a":{"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"860":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"860":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":28,"docs":{"1015":{"tf":1.0},"133":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"208":{"tf":1.7320508075688772},"212":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.4142135623730951},"239":{"tf":1.0},"267":{"tf":1.0},"303":{"tf":1.0},"314":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.0},"602":{"tf":1.0},"73":{"tf":1.0},"776":{"tf":1.4142135623730951},"816":{"tf":1.0},"84":{"tf":1.0},"844":{"tf":1.0},"857":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.0},"911":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"df":0,"docs":{},"n":{"df":10,"docs":{"121":{"tf":1.0},"196":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"371":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.4142135623730951},"61":{"tf":1.0},"680":{"tf":1.0},"700":{"tf":1.0}}},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"u":{"df":3,"docs":{"747":{"tf":1.4142135623730951},"749":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":9,"docs":{"199":{"tf":2.0},"39":{"tf":1.0},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"54":{"tf":1.0},"853":{"tf":1.0},"961":{"tf":1.0},"971":{"tf":1.4142135623730951},"973":{"tf":1.4142135623730951}}}}}}},"y":{"df":2,"docs":{"1004":{"tf":1.0},"522":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":5,"docs":{"292":{"tf":1.4142135623730951},"499":{"tf":1.0},"697":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":1,"docs":{"515":{"tf":1.0}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"571":{"tf":1.0}}}},"u":{"df":5,"docs":{"205":{"tf":1.0},"223":{"tf":1.0},"244":{"tf":1.0},"715":{"tf":1.0},"720":{"tf":1.0}},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"373":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"c":{"df":3,"docs":{"38":{"tf":1.0},"50":{"tf":1.7320508075688772},"537":{"tf":1.0}}},"df":1,"docs":{"934":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":27,"docs":{"111":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.4142135623730951},"132":{"tf":1.0},"173":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"25":{"tf":1.0},"284":{"tf":1.0},"372":{"tf":1.4142135623730951},"412":{"tf":1.0},"418":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":2.0},"648":{"tf":1.0},"653":{"tf":1.0},"722":{"tf":1.4142135623730951},"736":{"tf":1.0},"771":{"tf":1.0},"778":{"tf":1.0},"799":{"tf":1.7320508075688772},"846":{"tf":1.0},"874":{"tf":1.0},"932":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"25":{"tf":1.4142135623730951},"26":{"tf":1.0},"732":{"tf":1.7320508075688772},"735":{"tf":3.4641016151377544}}}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"30":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"878":{"tf":1.0}}}}},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"'":{"df":18,"docs":{"1004":{"tf":1.0},"138":{"tf":1.0},"147":{"tf":1.0},"231":{"tf":1.0},"267":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"39":{"tf":1.0},"435":{"tf":1.4142135623730951},"437":{"tf":1.0},"515":{"tf":1.0},"571":{"tf":1.0},"711":{"tf":1.4142135623730951},"720":{"tf":1.0},"724":{"tf":1.0},"961":{"tf":1.0}}},".":{"df":0,"docs":{},"j":{"df":4,"docs":{"895":{"tf":1.0},"898":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0}}}},"/":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"m":{"a":{"df":1,"docs":{"160":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":165,"docs":{"0":{"tf":1.4142135623730951},"1003":{"tf":1.0},"1004":{"tf":2.0},"1009":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":2.0},"109":{"tf":1.0},"111":{"tf":1.7320508075688772},"113":{"tf":1.4142135623730951},"120":{"tf":1.4142135623730951},"121":{"tf":1.0},"124":{"tf":1.0},"133":{"tf":1.0},"164":{"tf":1.0},"169":{"tf":1.0},"171":{"tf":1.4142135623730951},"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"188":{"tf":1.0},"190":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":2.0},"198":{"tf":2.0},"199":{"tf":2.6457513110645907},"200":{"tf":2.449489742783178},"201":{"tf":2.0},"203":{"tf":2.23606797749979},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"210":{"tf":1.7320508075688772},"214":{"tf":1.4142135623730951},"215":{"tf":1.0},"216":{"tf":1.0},"225":{"tf":1.0},"230":{"tf":1.0},"233":{"tf":1.0},"238":{"tf":1.0},"243":{"tf":1.0},"248":{"tf":1.4142135623730951},"251":{"tf":1.4142135623730951},"252":{"tf":1.7320508075688772},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.7320508075688772},"264":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.7320508075688772},"270":{"tf":2.23606797749979},"271":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"282":{"tf":1.4142135623730951},"291":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.4142135623730951},"326":{"tf":1.4142135623730951},"329":{"tf":1.4142135623730951},"362":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.7320508075688772},"371":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":2.0},"379":{"tf":1.0},"38":{"tf":1.4142135623730951},"385":{"tf":1.0},"39":{"tf":1.0},"41":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.7320508075688772},"415":{"tf":1.4142135623730951},"416":{"tf":1.4142135623730951},"417":{"tf":1.4142135623730951},"418":{"tf":2.0},"423":{"tf":1.4142135623730951},"429":{"tf":1.0},"436":{"tf":1.4142135623730951},"444":{"tf":1.0},"450":{"tf":1.4142135623730951},"454":{"tf":1.4142135623730951},"467":{"tf":1.4142135623730951},"468":{"tf":1.0},"469":{"tf":1.0},"479":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.4142135623730951},"507":{"tf":1.4142135623730951},"51":{"tf":1.4142135623730951},"514":{"tf":1.7320508075688772},"515":{"tf":3.0},"518":{"tf":1.0},"521":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"539":{"tf":1.0},"54":{"tf":1.7320508075688772},"542":{"tf":1.0},"552":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":2.0},"565":{"tf":1.7320508075688772},"567":{"tf":1.7320508075688772},"568":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.0},"600":{"tf":1.7320508075688772},"606":{"tf":1.0},"627":{"tf":1.0},"630":{"tf":1.0},"634":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.4142135623730951},"745":{"tf":1.4142135623730951},"756":{"tf":1.0},"759":{"tf":1.4142135623730951},"772":{"tf":1.0},"773":{"tf":1.4142135623730951},"774":{"tf":1.7320508075688772},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"798":{"tf":1.0},"801":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.7320508075688772},"812":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"857":{"tf":1.0},"861":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"877":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"888":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.7320508075688772},"897":{"tf":1.4142135623730951},"911":{"tf":1.0},"912":{"tf":1.4142135623730951},"927":{"tf":1.4142135623730951},"928":{"tf":1.7320508075688772},"931":{"tf":1.0},"933":{"tf":1.4142135623730951},"935":{"tf":1.0},"971":{"tf":1.0},"996":{"tf":1.0}},"’":{"df":3,"docs":{"147":{"tf":1.0},"959":{"tf":1.0},"971":{"tf":1.0}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"191":{"tf":1.0},"804":{"tf":1.0},"853":{"tf":1.0}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"50":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"m":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"25":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":10,"docs":{"21":{"tf":1.0},"22":{"tf":1.0},"23":{"tf":1.7320508075688772},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"28":{"tf":1.0},"29":{"tf":1.7320508075688772},"30":{"tf":1.0},"33":{"tf":1.0}}}}},"d":{"a":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"699":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"219":{"tf":1.0}}}}},"df":0,"docs":{}},"l":{"df":11,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":2.0},"125":{"tf":1.4142135623730951},"126":{"tf":4.358898943540674},"127":{"tf":1.4142135623730951},"132":{"tf":1.0},"134":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":1.7320508075688772},"847":{"tf":1.0}}}},"o":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}},"df":9,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":2.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":2.0},"218":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"370":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}}}}},"r":{"df":2,"docs":{"599":{"tf":1.0},"615":{"tf":1.0}}}},"p":{"(":{"df":1,"docs":{"333":{"tf":1.0}}},"df":1,"docs":{"797":{"tf":1.0}},"p":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":3,"docs":{"410":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"40":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":10,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.0},"517":{"tf":1.0},"563":{"tf":1.0},"568":{"tf":1.0},"762":{"tf":1.0},"815":{"tf":1.0},"932":{"tf":1.0},"992":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"e":{"df":10,"docs":{"124":{"tf":1.0},"138":{"tf":1.0},"365":{"tf":1.0},"418":{"tf":1.0},"432":{"tf":1.0},"51":{"tf":1.0},"575":{"tf":1.0},"777":{"tf":1.0},"911":{"tf":1.0},"938":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":16,"docs":{"184":{"tf":1.0},"187":{"tf":1.0},"231":{"tf":1.0},"30":{"tf":1.0},"343":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"700":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"783":{"tf":1.0},"797":{"tf":1.0},"8":{"tf":1.0},"800":{"tf":1.0},"835":{"tf":1.0},"939":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"439":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":85,"docs":{"1008":{"tf":1.0},"1015":{"tf":1.0},"112":{"tf":1.0},"114":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.0},"130":{"tf":1.0},"140":{"tf":1.4142135623730951},"155":{"tf":1.0},"184":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"249":{"tf":1.0},"262":{"tf":1.0},"281":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"3":{"tf":1.7320508075688772},"303":{"tf":1.7320508075688772},"315":{"tf":1.0},"316":{"tf":1.4142135623730951},"343":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"460":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.7320508075688772},"512":{"tf":1.7320508075688772},"515":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"521":{"tf":1.7320508075688772},"523":{"tf":1.4142135623730951},"540":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"586":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"653":{"tf":1.4142135623730951},"665":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"724":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":1.0},"740":{"tf":1.4142135623730951},"741":{"tf":1.0},"744":{"tf":1.0},"755":{"tf":1.0},"759":{"tf":3.1622776601683795},"761":{"tf":2.449489742783178},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"772":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"799":{"tf":1.0},"83":{"tf":1.0},"844":{"tf":1.0},"85":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.4142135623730951},"928":{"tf":1.0},"929":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"292":{"tf":1.0}}}}}}}},"df":13,"docs":{"277":{"tf":1.0},"292":{"tf":1.0},"756":{"tf":1.0},"776":{"tf":1.0},"832":{"tf":1.0},"841":{"tf":1.4142135623730951},"842":{"tf":1.7320508075688772},"843":{"tf":1.4142135623730951},"844":{"tf":1.0},"847":{"tf":2.6457513110645907},"848":{"tf":1.7320508075688772},"849":{"tf":2.0},"852":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"121":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"932":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":48,"docs":{"112":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.0},"19":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"365":{"tf":1.4142135623730951},"418":{"tf":1.4142135623730951},"422":{"tf":1.0},"429":{"tf":1.0},"453":{"tf":1.0},"563":{"tf":1.0},"565":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.4142135623730951},"576":{"tf":1.0},"58":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.4142135623730951},"582":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"697":{"tf":1.0},"722":{"tf":1.0},"752":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"807":{"tf":1.0},"818":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"903":{"tf":1.0},"911":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.0},"945":{"tf":1.4142135623730951},"955":{"tf":1.0},"962":{"tf":1.4142135623730951}}}}}}},"v":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":12,"docs":{"203":{"tf":1.0},"239":{"tf":1.4142135623730951},"376":{"tf":1.0},"409":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"444":{"tf":1.4142135623730951},"62":{"tf":1.4142135623730951},"628":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"78":{"tf":1.7320508075688772}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":1,"docs":{"184":{"tf":1.0}}}}}}}}}}},"df":12,"docs":{"111":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.0},"375":{"tf":1.0},"378":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"796":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":2.23606797749979},"850":{"tf":1.0},"912":{"tf":1.0}}}}}},"p":{"df":1,"docs":{"126":{"tf":2.449489742783178}},"p":{"df":1,"docs":{"735":{"tf":1.0}}}},"r":{"#":{"3":{"3":{"0":{"0":{"df":1,"docs":{"878":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"6":{"8":{"5":{"df":2,"docs":{"169":{"tf":1.0},"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"[":{"df":0,"docs":{},"x":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}},"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":22,"docs":{"198":{"tf":1.0},"261":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"41":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"511":{"tf":1.0},"539":{"tf":1.0},"567":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"615":{"tf":1.4142135623730951},"632":{"tf":1.0},"660":{"tf":1.0},"697":{"tf":1.4142135623730951},"723":{"tf":1.0},"735":{"tf":1.0},"928":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"375":{"tf":1.0},"467":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":10,"docs":{"312":{"tf":1.0},"315":{"tf":1.0},"359":{"tf":1.0},"447":{"tf":1.0},"546":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"878":{"tf":1.4142135623730951},"954":{"tf":1.0},"985":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"c":{"df":0,"docs":{},"e":{"d":{"df":4,"docs":{"203":{"tf":1.0},"735":{"tf":1.0},"843":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"201":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"251":{"tf":1.0},"38":{"tf":1.0}}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"105":{"tf":1.0}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"333":{"tf":1.0},"427":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":16,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.7320508075688772},"427":{"tf":1.0},"429":{"tf":1.0},"505":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"203":{"tf":1.0}}}}}}},"df":16,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.4142135623730951},"72":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"811":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.7320508075688772},"832":{"tf":1.0},"912":{"tf":1.7320508075688772},"933":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":14,"docs":{"1004":{"tf":1.0},"264":{"tf":1.0},"292":{"tf":1.0},"374":{"tf":1.0},"53":{"tf":1.0},"550":{"tf":1.0},"565":{"tf":1.0},"66":{"tf":1.0},"666":{"tf":1.0},"69":{"tf":1.0},"722":{"tf":1.4142135623730951},"761":{"tf":1.0},"81":{"tf":1.0},"831":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}}}}},"r":{"df":1,"docs":{"267":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"x":{"df":7,"docs":{"253":{"tf":1.0},"520":{"tf":1.4142135623730951},"735":{"tf":2.0},"759":{"tf":2.0},"786":{"tf":1.0},"933":{"tf":1.0},"992":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":9,"docs":{"47":{"tf":1.7320508075688772},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"85":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"437":{"tf":1.0},"444":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"773":{"tf":1.0}}},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"231":{"tf":1.0},"776":{"tf":1.4142135623730951}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":3,"docs":{"126":{"tf":1.7320508075688772},"279":{"tf":1.7320508075688772},"740":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"44":{"tf":1.0}}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"602":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":38,"docs":{"1004":{"tf":1.0},"155":{"tf":1.0},"169":{"tf":1.0},"175":{"tf":1.0},"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.4142135623730951},"201":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"227":{"tf":1.0},"264":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"430":{"tf":1.0},"436":{"tf":1.0},"480":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"564":{"tf":1.0},"644":{"tf":1.0},"711":{"tf":1.0},"725":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"774":{"tf":1.0},"777":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.0},"829":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"931":{"tf":1.0},"990":{"tf":1.0}}}},"r":{"df":0,"docs":{},"v":{"df":8,"docs":{"126":{"tf":1.0},"435":{"tf":1.0},"516":{"tf":1.0},"6":{"tf":1.0},"698":{"tf":1.4142135623730951},"700":{"tf":1.0},"71":{"tf":1.0},"772":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"698":{"tf":1.7320508075688772},"700":{"tf":1.0},"705":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":4,"docs":{"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"945":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"577":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"399":{"tf":1.0},"732":{"tf":1.0},"894":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":32,"docs":{"111":{"tf":1.0},"142":{"tf":1.0},"152":{"tf":1.0},"255":{"tf":1.0},"30":{"tf":1.0},"346":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"567":{"tf":1.0},"576":{"tf":1.0},"577":{"tf":1.0},"629":{"tf":1.4142135623730951},"69":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"799":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":1.0},"863":{"tf":1.0},"911":{"tf":1.0},"913":{"tf":1.0},"948":{"tf":1.0},"951":{"tf":1.0},"955":{"tf":1.0},"961":{"tf":1.0},"972":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":30,"docs":{"132":{"tf":1.0},"147":{"tf":1.0},"204":{"tf":2.449489742783178},"205":{"tf":1.0},"207":{"tf":2.0},"267":{"tf":1.0},"285":{"tf":1.0},"345":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.7320508075688772},"45":{"tf":1.7320508075688772},"46":{"tf":1.7320508075688772},"524":{"tf":1.0},"532":{"tf":1.0},"623":{"tf":1.0},"64":{"tf":1.0},"665":{"tf":1.0},"67":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.0},"937":{"tf":1.0},"953":{"tf":1.0},"985":{"tf":1.0}},"s":{"df":11,"docs":{"166":{"tf":1.0},"177":{"tf":1.0},"205":{"tf":1.0},"303":{"tf":1.0},"344":{"tf":1.0},"347":{"tf":1.0},"62":{"tf":1.0},"71":{"tf":1.0},"735":{"tf":1.0},"771":{"tf":1.0},"979":{"tf":1.0}}}}}}}},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"776":{"tf":1.4142135623730951}}}}}}}}}},"df":32,"docs":{"203":{"tf":2.23606797749979},"204":{"tf":3.605551275463989},"205":{"tf":3.605551275463989},"206":{"tf":1.4142135623730951},"207":{"tf":4.795831523312719},"213":{"tf":2.449489742783178},"267":{"tf":1.7320508075688772},"410":{"tf":1.0},"413":{"tf":1.0},"415":{"tf":1.0},"428":{"tf":2.23606797749979},"429":{"tf":1.4142135623730951},"741":{"tf":2.0},"742":{"tf":2.6457513110645907},"743":{"tf":2.23606797749979},"744":{"tf":2.6457513110645907},"747":{"tf":1.4142135623730951},"748":{"tf":1.4142135623730951},"749":{"tf":1.7320508075688772},"75":{"tf":1.0},"751":{"tf":3.1622776601683795},"752":{"tf":3.605551275463989},"754":{"tf":1.4142135623730951},"756":{"tf":1.0},"772":{"tf":2.23606797749979},"773":{"tf":3.7416573867739413},"776":{"tf":4.123105625617661},"777":{"tf":3.7416573867739413},"779":{"tf":1.4142135623730951},"912":{"tf":2.23606797749979},"944":{"tf":1.4142135623730951},"959":{"tf":1.0}}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":25,"docs":{"1004":{"tf":1.0},"1005":{"tf":1.0},"185":{"tf":1.0},"201":{"tf":1.0},"219":{"tf":1.0},"231":{"tf":1.0},"236":{"tf":1.0},"240":{"tf":1.0},"322":{"tf":1.0},"340":{"tf":1.0},"349":{"tf":2.0},"351":{"tf":1.4142135623730951},"368":{"tf":1.0},"380":{"tf":1.0},"414":{"tf":1.0},"422":{"tf":1.0},"469":{"tf":1.0},"745":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"81":{"tf":1.4142135623730951},"845":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"231":{"tf":1.0},"324":{"tf":1.0},"342":{"tf":1.0},"55":{"tf":1.0},"631":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"843":{"tf":1.0},"951":{"tf":1.0}}}}},"y":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"350":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":10,"docs":{"322":{"tf":1.0},"340":{"tf":1.7320508075688772},"375":{"tf":1.0},"522":{"tf":3.3166247903554},"524":{"tf":2.449489742783178},"627":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.4142135623730951},"643":{"tf":1.0}}}}},"n":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"255":{"tf":1.0},"67":{"tf":1.0},"720":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"722":{"tf":1.0},"894":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":131,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.4142135623730951},"105":{"tf":1.0},"106":{"tf":1.0},"120":{"tf":1.0},"122":{"tf":1.0},"133":{"tf":1.0},"136":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"150":{"tf":1.0},"161":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.0},"182":{"tf":1.0},"192":{"tf":1.0},"195":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.0},"211":{"tf":1.0},"214":{"tf":1.0},"215":{"tf":1.0},"221":{"tf":1.0},"228":{"tf":1.0},"229":{"tf":1.4142135623730951},"242":{"tf":1.0},"244":{"tf":1.0},"247":{"tf":1.0},"260":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"277":{"tf":1.0},"279":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.0},"308":{"tf":1.0},"311":{"tf":1.0},"319":{"tf":1.0},"322":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"383":{"tf":1.0},"386":{"tf":1.0},"397":{"tf":1.0},"400":{"tf":1.0},"409":{"tf":1.0},"430":{"tf":1.0},"447":{"tf":1.0},"451":{"tf":1.0},"46":{"tf":1.0},"462":{"tf":1.0},"465":{"tf":1.0},"479":{"tf":1.0},"481":{"tf":1.0},"492":{"tf":1.0},"495":{"tf":1.0},"510":{"tf":1.0},"513":{"tf":1.0},"532":{"tf":1.0},"535":{"tf":1.0},"546":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.0},"563":{"tf":1.0},"583":{"tf":1.0},"584":{"tf":1.0},"595":{"tf":1.0},"598":{"tf":1.0},"610":{"tf":1.0},"613":{"tf":1.0},"624":{"tf":1.0},"627":{"tf":1.0},"646":{"tf":1.0},"649":{"tf":1.0},"661":{"tf":1.0},"664":{"tf":1.0},"675":{"tf":1.0},"678":{"tf":1.0},"689":{"tf":1.0},"692":{"tf":1.0},"706":{"tf":1.0},"709":{"tf":1.0},"726":{"tf":1.0},"730":{"tf":1.0},"738":{"tf":1.0},"74":{"tf":1.0},"741":{"tf":1.0},"754":{"tf":1.0},"757":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"771":{"tf":1.0},"780":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.0},"795":{"tf":1.0},"805":{"tf":1.0},"808":{"tf":1.0},"824":{"tf":1.4142135623730951},"827":{"tf":1.0},"838":{"tf":1.0},"857":{"tf":1.0},"869":{"tf":1.0},"871":{"tf":1.0},"888":{"tf":1.0},"891":{"tf":1.0},"90":{"tf":1.0},"905":{"tf":1.4142135623730951},"908":{"tf":1.4142135623730951},"913":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.0},"940":{"tf":1.0},"954":{"tf":1.0},"957":{"tf":1.0},"971":{"tf":1.0},"974":{"tf":1.0},"985":{"tf":1.0},"988":{"tf":1.0},"999":{"tf":1.0}},"i":{"df":1,"docs":{"724":{"tf":1.0}},"t":{"df":3,"docs":{"375":{"tf":1.0},"58":{"tf":1.0},"779":{"tf":1.0}},"i":{"df":8,"docs":{"203":{"tf":1.0},"63":{"tf":1.4142135623730951},"69":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}}}}},"v":{"a":{"c":{"df":0,"docs":{},"i":{"df":123,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.4142135623730951},"106":{"tf":1.0},"115":{"tf":1.4142135623730951},"122":{"tf":1.0},"128":{"tf":1.4142135623730951},"136":{"tf":1.0},"142":{"tf":1.4142135623730951},"150":{"tf":1.0},"156":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.4142135623730951},"182":{"tf":1.0},"188":{"tf":1.0},"195":{"tf":1.0},"211":{"tf":1.4142135623730951},"215":{"tf":1.0},"225":{"tf":1.4142135623730951},"229":{"tf":1.0},"237":{"tf":1.0},"247":{"tf":1.0},"255":{"tf":1.0},"268":{"tf":1.0},"275":{"tf":1.0},"279":{"tf":1.0},"286":{"tf":1.4142135623730951},"294":{"tf":1.0},"30":{"tf":1.0},"304":{"tf":1.4142135623730951},"311":{"tf":1.0},"317":{"tf":1.0},"322":{"tf":1.0},"354":{"tf":1.0},"365":{"tf":1.0},"366":{"tf":1.0},"378":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"392":{"tf":1.4142135623730951},"410":{"tf":1.0},"419":{"tf":1.0},"430":{"tf":1.0},"442":{"tf":1.4142135623730951},"451":{"tf":1.0},"457":{"tf":1.0},"465":{"tf":1.0},"474":{"tf":1.0},"481":{"tf":1.0},"487":{"tf":1.0},"495":{"tf":1.0},"505":{"tf":1.0},"513":{"tf":1.0},"528":{"tf":1.4142135623730951},"53":{"tf":1.4142135623730951},"535":{"tf":1.0},"541":{"tf":1.4142135623730951},"549":{"tf":1.0},"555":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"578":{"tf":1.0},"584":{"tf":1.0},"590":{"tf":1.4142135623730951},"598":{"tf":1.0},"605":{"tf":1.0},"613":{"tf":1.0},"619":{"tf":1.0},"627":{"tf":1.0},"639":{"tf":1.4142135623730951},"649":{"tf":1.0},"656":{"tf":1.0},"664":{"tf":1.0},"670":{"tf":1.0},"678":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.4142135623730951},"692":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"709":{"tf":1.0},"724":{"tf":1.0},"757":{"tf":1.0},"763":{"tf":1.0},"782":{"tf":1.0},"788":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"801":{"tf":1.0},"808":{"tf":1.0},"819":{"tf":1.4142135623730951},"827":{"tf":1.0},"833":{"tf":1.0},"841":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"857":{"tf":1.0},"864":{"tf":1.4142135623730951},"871":{"tf":1.0},"883":{"tf":1.0},"891":{"tf":1.0},"894":{"tf":1.4142135623730951},"9":{"tf":1.0},"900":{"tf":1.4142135623730951},"908":{"tf":1.0},"917":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"935":{"tf":1.0},"940":{"tf":1.4142135623730951},"946":{"tf":1.0},"949":{"tf":1.4142135623730951},"957":{"tf":1.4142135623730951},"963":{"tf":1.0},"966":{"tf":1.4142135623730951},"974":{"tf":1.0},"980":{"tf":1.0},"988":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":8,"docs":{"206":{"tf":1.7320508075688772},"452":{"tf":1.4142135623730951},"453":{"tf":1.7320508075688772},"455":{"tf":1.0},"528":{"tf":1.0},"565":{"tf":1.0},"81":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"e":{"(":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":5,"docs":{"184":{"tf":1.0},"234":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.0},"349":{"tf":1.0}}}}}}}},"o":{"b":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":1.0},"347":{"tf":1.0}}}}}}},"l":{"df":8,"docs":{"127":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.7320508075688772},"534":{"tf":1.0},"740":{"tf":1.0},"849":{"tf":1.0},"936":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"388":{"tf":1.0},"723":{"tf":1.0}}}},"df":39,"docs":{"1004":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"161":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"252":{"tf":1.0},"257":{"tf":1.4142135623730951},"388":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.4142135623730951},"512":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"551":{"tf":1.4142135623730951},"629":{"tf":1.0},"63":{"tf":1.0},"694":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":1.0},"77":{"tf":1.4142135623730951},"818":{"tf":1.0},"832":{"tf":1.0},"871":{"tf":1.0},"874":{"tf":1.0},"891":{"tf":1.0},"895":{"tf":1.0},"908":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":6,"docs":{"333":{"tf":1.0},"344":{"tf":1.0},"349":{"tf":1.4142135623730951},"351":{"tf":1.0},"364":{"tf":1.0},"435":{"tf":1.0}}}}},"df":2,"docs":{"112":{"tf":1.0},"198":{"tf":1.0}},"s":{"df":0,"docs":{},"s":{"df":59,"docs":{"106":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.4142135623730951},"126":{"tf":1.0},"132":{"tf":1.0},"145":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.0},"207":{"tf":1.7320508075688772},"209":{"tf":1.0},"24":{"tf":1.0},"268":{"tf":1.7320508075688772},"284":{"tf":1.4142135623730951},"296":{"tf":1.4142135623730951},"3":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.0},"337":{"tf":1.0},"345":{"tf":1.0},"350":{"tf":1.0},"364":{"tf":1.0},"38":{"tf":1.0},"436":{"tf":1.0},"441":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.4142135623730951},"459":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.7320508075688772},"503":{"tf":1.0},"521":{"tf":1.0},"528":{"tf":1.0},"537":{"tf":1.0},"56":{"tf":1.0},"57":{"tf":1.4142135623730951},"64":{"tf":1.4142135623730951},"640":{"tf":1.4142135623730951},"644":{"tf":1.0},"65":{"tf":1.0},"694":{"tf":1.0},"715":{"tf":1.0},"735":{"tf":1.4142135623730951},"77":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"826":{"tf":1.0},"83":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":2.23606797749979},"942":{"tf":1.0},"95":{"tf":1.0},"989":{"tf":1.0},"990":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"u":{"c":{"df":20,"docs":{"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.0},"151":{"tf":1.0},"159":{"tf":1.0},"295":{"tf":1.0},"297":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"342":{"tf":1.4142135623730951},"345":{"tf":1.4142135623730951},"349":{"tf":1.0},"44":{"tf":1.0},"532":{"tf":1.0},"63":{"tf":1.0},"829":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"160":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"t":{"df":11,"docs":{"107":{"tf":1.0},"155":{"tf":1.0},"323":{"tf":1.0},"339":{"tf":1.0},"372":{"tf":1.0},"53":{"tf":1.0},"577":{"tf":1.0},"640":{"tf":1.0},"712":{"tf":1.4142135623730951},"714":{"tf":1.0},"778":{"tf":1.0}}}},"df":0,"docs":{}}},"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"211":{"tf":1.0},"849":{"tf":1.0}}}}}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"469":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":6,"docs":{"231":{"tf":1.0},"267":{"tf":1.0},"711":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"912":{"tf":1.4142135623730951}}}}},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"26":{"tf":1.0}}},"df":36,"docs":{"147":{"tf":1.0},"17":{"tf":1.4142135623730951},"21":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"23":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"25":{"tf":2.0},"26":{"tf":2.8284271247461903},"270":{"tf":1.0},"28":{"tf":2.23606797749979},"29":{"tf":1.0},"33":{"tf":1.0},"374":{"tf":1.0},"600":{"tf":2.23606797749979},"602":{"tf":2.8284271247461903},"606":{"tf":1.4142135623730951},"608":{"tf":1.0},"609":{"tf":1.7320508075688772},"615":{"tf":1.0},"619":{"tf":1.0},"623":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"673":{"tf":1.4142135623730951},"693":{"tf":1.0},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"701":{"tf":2.0},"704":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.0},"799":{"tf":1.0},"83":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0}},"m":{"df":2,"docs":{"959":{"tf":1.0},"966":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":7,"docs":{"105":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":1.0},"343":{"tf":1.0},"447":{"tf":1.0},"467":{"tf":1.0},"77":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"414":{"tf":1.0},"428":{"tf":1.0}}}}},"df":0,"docs":{}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"185":{"tf":1.0},"200":{"tf":1.0},"267":{"tf":1.4142135623730951},"388":{"tf":1.0},"390":{"tf":1.0},"465":{"tf":1.0},"471":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"991":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"565":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":4,"docs":{"303":{"tf":1.0},"44":{"tf":1.0},"81":{"tf":1.0},"852":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"t":{"df":5,"docs":{"272":{"tf":1.0},"326":{"tf":1.0},"467":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"df":1,"docs":{"962":{"tf":1.0}}}},"o":{"df":0,"docs":{},"f":{"df":47,"docs":{"1004":{"tf":1.0},"155":{"tf":1.4142135623730951},"336":{"tf":1.0},"337":{"tf":1.0},"38":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":2.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.0},"404":{"tf":2.23606797749979},"406":{"tf":1.4142135623730951},"407":{"tf":1.4142135623730951},"439":{"tf":2.6457513110645907},"44":{"tf":1.7320508075688772},"45":{"tf":1.7320508075688772},"451":{"tf":1.7320508075688772},"452":{"tf":1.4142135623730951},"455":{"tf":3.0},"457":{"tf":1.0},"459":{"tf":1.4142135623730951},"46":{"tf":1.7320508075688772},"460":{"tf":1.0},"461":{"tf":1.0},"49":{"tf":1.0},"500":{"tf":2.23606797749979},"51":{"tf":1.7320508075688772},"514":{"tf":1.0},"517":{"tf":1.4142135623730951},"520":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":1.0},"628":{"tf":1.0},"648":{"tf":1.0},"754":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":2.23606797749979},"762":{"tf":2.23606797749979},"763":{"tf":1.7320508075688772},"83":{"tf":1.0},"843":{"tf":1.0},"885":{"tf":1.0},"913":{"tf":1.0},"992":{"tf":1.7320508075688772}}}},"p":{"a":{"df":0,"docs":{},"g":{"df":3,"docs":{"343":{"tf":1.0},"551":{"tf":1.0},"71":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"175":{"tf":1.0},"205":{"tf":1.0},"30":{"tf":1.0},"483":{"tf":1.0},"54":{"tf":1.0},"819":{"tf":1.0},"932":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"203":{"tf":1.0},"207":{"tf":1.0},"212":{"tf":1.0},"216":{"tf":1.0},"265":{"tf":1.0},"522":{"tf":1.0},"551":{"tf":1.0},"78":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":10,"docs":{"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"402":{"tf":1.0},"438":{"tf":1.4142135623730951},"515":{"tf":1.0},"602":{"tf":1.0},"741":{"tf":1.0},"751":{"tf":1.0},"84":{"tf":1.0},"912":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":9,"docs":{"51":{"tf":1.4142135623730951},"576":{"tf":1.0},"714":{"tf":1.4142135623730951},"723":{"tf":1.0},"814":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":2.0},"917":{"tf":1.0},"919":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"563":{"tf":1.0},"564":{"tf":1.0},"722":{"tf":1.0}}}}}}},"s":{"a":{"df":0,"docs":{},"l":{"'":{"df":1,"docs":{"124":{"tf":1.0}}},"(":{"df":1,"docs":{"209":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}}},"df":232,"docs":{"0":{"tf":1.0},"1003":{"tf":1.4142135623730951},"1008":{"tf":1.4142135623730951},"1009":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1014":{"tf":1.0},"103":{"tf":1.0},"105":{"tf":1.0},"107":{"tf":1.0},"112":{"tf":2.0},"113":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.0},"13":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"135":{"tf":1.0},"138":{"tf":1.0},"142":{"tf":1.0},"144":{"tf":1.0},"147":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.7320508075688772},"151":{"tf":1.0},"154":{"tf":1.4142135623730951},"155":{"tf":1.0},"165":{"tf":1.0},"18":{"tf":1.0},"183":{"tf":1.0},"186":{"tf":1.4142135623730951},"196":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":2.8284271247461903},"209":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"212":{"tf":1.4142135623730951},"216":{"tf":1.4142135623730951},"221":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.4142135623730951},"230":{"tf":1.0},"231":{"tf":2.0},"234":{"tf":1.0},"238":{"tf":1.0},"248":{"tf":1.0},"269":{"tf":1.0},"272":{"tf":1.7320508075688772},"294":{"tf":1.0},"295":{"tf":1.0},"3":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"312":{"tf":1.0},"317":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"347":{"tf":1.0},"35":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"37":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"379":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"387":{"tf":1.0},"39":{"tf":1.0},"390":{"tf":1.4142135623730951},"397":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.0},"407":{"tf":1.0},"409":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.0},"418":{"tf":1.0},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"431":{"tf":1.0},"438":{"tf":1.0},"442":{"tf":1.0},"452":{"tf":1.7320508075688772},"465":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"525":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"536":{"tf":1.0},"539":{"tf":1.0},"542":{"tf":1.0},"546":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":1.4142135623730951},"567":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"583":{"tf":1.0},"585":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"614":{"tf":1.0},"615":{"tf":1.0},"617":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"642":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"660":{"tf":1.0},"663":{"tf":1.7320508075688772},"7":{"tf":1.0},"705":{"tf":1.0},"709":{"tf":1.0},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"752":{"tf":1.0},"754":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"763":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":2.449489742783178},"776":{"tf":1.4142135623730951},"779":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":2.0},"787":{"tf":1.0},"788":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"796":{"tf":1.4142135623730951},"799":{"tf":1.0},"80":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"829":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"842":{"tf":1.4142135623730951},"843":{"tf":1.4142135623730951},"846":{"tf":1.0},"847":{"tf":1.7320508075688772},"848":{"tf":1.7320508075688772},"85":{"tf":1.0},"858":{"tf":1.0},"860":{"tf":1.0},"870":{"tf":1.0},"872":{"tf":2.23606797749979},"875":{"tf":1.7320508075688772},"878":{"tf":2.449489742783178},"879":{"tf":6.324555320336759},"88":{"tf":1.0},"880":{"tf":2.449489742783178},"881":{"tf":3.1622776601683795},"885":{"tf":2.0},"890":{"tf":1.4142135623730951},"892":{"tf":1.0},"902":{"tf":1.0},"909":{"tf":1.4142135623730951},"919":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951},"928":{"tf":2.23606797749979},"929":{"tf":1.0},"931":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"934":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"94":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"949":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"966":{"tf":1.0},"97":{"tf":1.4142135623730951},"970":{"tf":1.0},"971":{"tf":1.0},"975":{"tf":1.0},"987":{"tf":1.0},"989":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":1,"docs":{"553":{"tf":1.0}}}},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"270":{"tf":1.0},"564":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"199":{"tf":1.0},"799":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"914":{"tf":1.0}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"108":{"tf":1.0},"763":{"tf":1.4142135623730951},"777":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"2":{"df":1,"docs":{"253":{"tf":1.0}}},"3":{"df":1,"docs":{"553":{"tf":1.0}}},"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":4,"docs":{"253":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"761":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"'":{"df":3,"docs":{"185":{"tf":1.0},"325":{"tf":1.0},"343":{"tf":1.0}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"342":{"tf":1.4142135623730951},"346":{"tf":1.0}}}}}}}}}},"df":86,"docs":{"100":{"tf":1.0},"124":{"tf":1.4142135623730951},"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"188":{"tf":1.0},"190":{"tf":1.0},"201":{"tf":1.0},"230":{"tf":1.0},"234":{"tf":1.4142135623730951},"247":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":2.449489742783178},"254":{"tf":1.0},"270":{"tf":1.7320508075688772},"322":{"tf":2.23606797749979},"323":{"tf":1.7320508075688772},"324":{"tf":1.0},"327":{"tf":1.0},"328":{"tf":1.0},"333":{"tf":1.0},"335":{"tf":1.4142135623730951},"337":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.7320508075688772},"343":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"356":{"tf":1.0},"361":{"tf":1.0},"363":{"tf":1.4142135623730951},"365":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.0},"382":{"tf":1.0},"39":{"tf":1.0},"430":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.7320508075688772},"440":{"tf":2.0},"441":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.7320508075688772},"473":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"486":{"tf":1.0},"49":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"512":{"tf":1.0},"53":{"tf":1.0},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"559":{"tf":2.23606797749979},"565":{"tf":1.4142135623730951},"600":{"tf":1.0},"62":{"tf":1.4142135623730951},"629":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"709":{"tf":1.0},"710":{"tf":1.0},"712":{"tf":1.4142135623730951},"72":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.4142135623730951},"729":{"tf":1.0},"73":{"tf":1.4142135623730951},"745":{"tf":1.0},"757":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":2.449489742783178},"763":{"tf":1.4142135623730951},"767":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"774":{"tf":1.0},"78":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.4142135623730951},"786":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":3,"docs":{"209":{"tf":1.0},"221":{"tf":2.0},"222":{"tf":1.4142135623730951}}}}}}},"v":{"df":0,"docs":{},"e":{"df":9,"docs":{"339":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"759":{"tf":1.4142135623730951},"83":{"tf":1.0},"847":{"tf":1.0},"95":{"tf":1.0}},"n":{"df":2,"docs":{"44":{"tf":1.0},"444":{"tf":1.0}}},"r":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}},"i":{"d":{"df":130,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.4142135623730951},"1013":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"121":{"tf":1.4142135623730951},"124":{"tf":1.0},"138":{"tf":1.0},"171":{"tf":1.0},"173":{"tf":1.0},"175":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"206":{"tf":1.7320508075688772},"207":{"tf":1.0},"210":{"tf":1.0},"22":{"tf":1.0},"222":{"tf":1.4142135623730951},"231":{"tf":1.0},"232":{"tf":1.0},"233":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.7320508075688772},"254":{"tf":1.0},"255":{"tf":2.0},"257":{"tf":1.7320508075688772},"272":{"tf":1.0},"276":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.7320508075688772},"30":{"tf":1.0},"303":{"tf":1.0},"315":{"tf":1.0},"325":{"tf":1.0},"35":{"tf":1.0},"364":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.7320508075688772},"375":{"tf":1.0},"376":{"tf":1.4142135623730951},"38":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"439":{"tf":1.0},"467":{"tf":1.4142135623730951},"47":{"tf":1.0},"470":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"500":{"tf":3.605551275463989},"501":{"tf":2.8284271247461903},"502":{"tf":1.4142135623730951},"503":{"tf":2.0},"505":{"tf":1.4142135623730951},"507":{"tf":1.7320508075688772},"51":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"534":{"tf":1.0},"55":{"tf":1.0},"574":{"tf":1.0},"577":{"tf":1.0},"599":{"tf":1.0},"602":{"tf":1.7320508075688772},"629":{"tf":1.7320508075688772},"632":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.0},"673":{"tf":1.0},"705":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"718":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":2.449489742783178},"723":{"tf":1.4142135623730951},"727":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.7320508075688772},"744":{"tf":1.7320508075688772},"75":{"tf":1.4142135623730951},"761":{"tf":2.0},"772":{"tf":1.0},"773":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"797":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"843":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"895":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0},"913":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"938":{"tf":1.0},"94":{"tf":1.0},"947":{"tf":1.0},"95":{"tf":1.0},"952":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"969":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"206":{"tf":1.0},"776":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951}}}}}}}},"x":{"df":0,"docs":{},"i":{"df":8,"docs":{"79":{"tf":1.7320508075688772},"80":{"tf":1.7320508075688772},"81":{"tf":3.0},"83":{"tf":3.1622776601683795},"84":{"tf":2.23606797749979},"85":{"tf":2.0},"874":{"tf":2.6457513110645907},"92":{"tf":1.4142135623730951}}},"y":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"83":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"|":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"524":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":16,"docs":{"500":{"tf":1.4142135623730951},"513":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":1.7320508075688772},"56":{"tf":1.0},"62":{"tf":1.0},"67":{"tf":2.0},"68":{"tf":1.0},"78":{"tf":1.0},"808":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.4142135623730951},"814":{"tf":1.0},"815":{"tf":2.449489742783178},"817":{"tf":1.0},"818":{"tf":1.0}}}}}},"s":{"df":1,"docs":{"126":{"tf":2.8284271247461903}},"e":{"df":0,"docs":{},"u":{"d":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"438":{"tf":1.0}}},"df":0,"docs":{}}},"df":8,"docs":{"322":{"tf":1.0},"333":{"tf":1.0},"336":{"tf":1.0},"347":{"tf":1.0},"600":{"tf":1.0},"741":{"tf":1.0},"750":{"tf":1.0},"849":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"b":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"817":{"tf":1.0}}}}}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"97":{"tf":1.0}}}}}},"df":22,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":2.0},"372":{"tf":1.0},"382":{"tf":1.0},"390":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"438":{"tf":1.0},"439":{"tf":3.3166247903554},"455":{"tf":1.7320508075688772},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"633":{"tf":1.7320508075688772},"634":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"879":{"tf":3.3166247903554},"880":{"tf":3.605551275463989},"885":{"tf":1.7320508075688772},"933":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"c":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"380":{"tf":1.0}}}}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"553":{"tf":1.0}}}}}},"df":18,"docs":{"124":{"tf":1.0},"198":{"tf":1.0},"272":{"tf":1.0},"296":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"350":{"tf":1.0},"452":{"tf":2.0},"453":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.0},"735":{"tf":2.0},"843":{"tf":1.0},"894":{"tf":1.4142135623730951},"94":{"tf":1.0},"95":{"tf":1.0}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":10,"docs":{"257":{"tf":1.0},"272":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"348":{"tf":1.0},"507":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"722":{"tf":1.0},"95":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":6,"docs":{"105":{"tf":1.4142135623730951},"135":{"tf":1.0},"149":{"tf":1.0},"249":{"tf":1.0},"35":{"tf":1.0},"409":{"tf":1.0}}}},"n":{"df":1,"docs":{"928":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":3,"docs":{"439":{"tf":1.0},"632":{"tf":1.0},"723":{"tf":1.4142135623730951}}}}}},"r":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":21,"docs":{"203":{"tf":2.0},"204":{"tf":3.605551275463989},"205":{"tf":3.3166247903554},"206":{"tf":2.8284271247461903},"207":{"tf":2.23606797749979},"210":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":2.0},"911":{"tf":1.4142135623730951},"912":{"tf":2.449489742783178},"913":{"tf":2.449489742783178},"914":{"tf":1.0},"916":{"tf":1.0},"919":{"tf":1.4142135623730951},"941":{"tf":1.4142135623730951},"942":{"tf":1.0},"944":{"tf":1.4142135623730951},"947":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"_":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}}},"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"1":{"df":2,"docs":{"81":{"tf":2.0},"83":{"tf":1.4142135623730951}}},"df":9,"docs":{"79":{"tf":1.7320508075688772},"80":{"tf":1.4142135623730951},"81":{"tf":3.0},"83":{"tf":3.4641016151377544},"84":{"tf":3.1622776601683795},"85":{"tf":2.23606797749979},"874":{"tf":2.449489742783178},"92":{"tf":1.4142135623730951},"933":{"tf":1.0}}},"g":{"df":1,"docs":{"711":{"tf":1.0}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":15,"docs":{"248":{"tf":1.0},"375":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"512":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":1.0},"7":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.4142135623730951},"786":{"tf":1.0},"81":{"tf":1.0},"846":{"tf":1.0},"863":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"h":{"(":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":1,"docs":{"333":{"tf":1.0}}},"df":7,"docs":{"126":{"tf":1.0},"349":{"tf":1.4142135623730951},"571":{"tf":1.0},"576":{"tf":1.0},"71":{"tf":1.0},"729":{"tf":1.0},"843":{"tf":1.0}}}},"t":{"df":15,"docs":{"163":{"tf":1.0},"199":{"tf":1.0},"249":{"tf":1.0},"284":{"tf":1.0},"375":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"633":{"tf":1.0},"653":{"tf":1.0},"780":{"tf":1.0},"858":{"tf":1.0},"976":{"tf":1.0},"979":{"tf":1.0}}}},"v":{"df":0,"docs":{},"f":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"113":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":16,"docs":{"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"56":{"tf":1.0},"58":{"tf":1.4142135623730951},"62":{"tf":1.0},"63":{"tf":1.4142135623730951},"65":{"tf":1.0},"66":{"tf":1.0},"67":{"tf":1.4142135623730951},"68":{"tf":1.0},"69":{"tf":2.449489742783178},"73":{"tf":1.7320508075688772},"77":{"tf":1.0},"78":{"tf":2.449489742783178},"817":{"tf":1.0}}},"m":{"df":2,"docs":{"51":{"tf":1.0},"53":{"tf":1.0}}}}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"1004":{"tf":1.7320508075688772},"58":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"204":{"tf":1.0},"776":{"tf":1.7320508075688772},"911":{"tf":1.0}}}},"z":{"df":1,"docs":{"204":{"tf":1.4142135623730951}}}}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"221":{"tf":1.0}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"846":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"h":{"a":{"df":1,"docs":{"93":{"tf":1.0}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"df":23,"docs":{"17":{"tf":1.7320508075688772},"18":{"tf":3.0},"19":{"tf":1.4142135623730951},"21":{"tf":2.449489742783178},"22":{"tf":2.6457513110645907},"23":{"tf":1.0},"24":{"tf":1.4142135623730951},"25":{"tf":1.0},"257":{"tf":1.4142135623730951},"26":{"tf":1.7320508075688772},"28":{"tf":1.7320508075688772},"3":{"tf":1.0},"30":{"tf":2.449489742783178},"450":{"tf":1.0},"5":{"tf":1.0},"507":{"tf":1.0},"553":{"tf":1.4142135623730951},"6":{"tf":3.3166247903554},"758":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":2.23606797749979},"762":{"tf":1.0},"763":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"759":{"tf":2.0},"761":{"tf":2.0}}}}},"y":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"6":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"6":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}}}}}}}}}}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":120,"docs":{"1":{"tf":1.0},"1000":{"tf":1.0},"1002":{"tf":1.0},"1014":{"tf":1.4142135623730951},"106":{"tf":1.0},"121":{"tf":1.0},"122":{"tf":1.0},"134":{"tf":1.0},"136":{"tf":1.0},"148":{"tf":1.0},"15":{"tf":1.0},"150":{"tf":1.0},"162":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"180":{"tf":1.0},"182":{"tf":1.0},"193":{"tf":1.0},"229":{"tf":1.0},"245":{"tf":1.0},"247":{"tf":1.0},"261":{"tf":1.0},"264":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"278":{"tf":1.0},"279":{"tf":1.0},"292":{"tf":1.0},"294":{"tf":1.0},"309":{"tf":1.0},"311":{"tf":1.0},"320":{"tf":1.0},"322":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"366":{"tf":1.0},"384":{"tf":1.4142135623730951},"386":{"tf":1.0},"398":{"tf":1.4142135623730951},"410":{"tf":1.0},"425":{"tf":1.4142135623730951},"430":{"tf":1.0},"448":{"tf":1.0},"451":{"tf":1.0},"463":{"tf":1.0},"465":{"tf":1.0},"480":{"tf":1.0},"481":{"tf":1.0},"493":{"tf":1.0},"495":{"tf":1.0},"511":{"tf":1.0},"513":{"tf":1.0},"533":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":1.0},"547":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"561":{"tf":1.0},"584":{"tf":1.0},"596":{"tf":1.0},"598":{"tf":1.0},"611":{"tf":1.0},"613":{"tf":1.0},"625":{"tf":1.0},"627":{"tf":1.0},"647":{"tf":1.0},"649":{"tf":1.0},"662":{"tf":1.0},"664":{"tf":1.0},"676":{"tf":1.0},"678":{"tf":1.0},"690":{"tf":1.0},"692":{"tf":1.0},"707":{"tf":1.0},"709":{"tf":1.0},"727":{"tf":1.4142135623730951},"730":{"tf":1.0},"732":{"tf":1.0},"739":{"tf":1.0},"75":{"tf":1.4142135623730951},"757":{"tf":1.0},"769":{"tf":1.0},"771":{"tf":1.0},"78":{"tf":1.4142135623730951},"781":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"794":{"tf":1.0},"795":{"tf":1.0},"806":{"tf":1.0},"808":{"tf":1.0},"825":{"tf":1.0},"827":{"tf":1.0},"833":{"tf":1.0},"839":{"tf":1.0},"841":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"856":{"tf":1.0},"857":{"tf":1.0},"870":{"tf":1.0},"871":{"tf":1.0},"889":{"tf":1.0},"891":{"tf":1.0},"906":{"tf":1.4142135623730951},"908":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"926":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.0},"940":{"tf":1.0},"955":{"tf":1.0},"957":{"tf":1.0},"972":{"tf":1.0},"974":{"tf":1.0},"986":{"tf":1.0},"988":{"tf":1.0}}}}}}},"u":{"df":2,"docs":{"207":{"tf":1.0},"564":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}},"df":19,"docs":{"148":{"tf":1.0},"207":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"564":{"tf":1.4142135623730951},"567":{"tf":1.0},"568":{"tf":1.7320508075688772},"570":{"tf":1.4142135623730951},"571":{"tf":2.0},"573":{"tf":2.6457513110645907},"574":{"tf":1.4142135623730951},"575":{"tf":1.0},"576":{"tf":2.449489742783178},"577":{"tf":1.0},"633":{"tf":2.449489742783178},"637":{"tf":1.7320508075688772},"640":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0},"863":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":8,"docs":{"170":{"tf":1.0},"293":{"tf":1.0},"438":{"tf":1.0},"752":{"tf":1.4142135623730951},"809":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"885":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"138":{"tf":1.0},"574":{"tf":1.0},"815":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"576":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"516":{"tf":1.0},"564":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"942":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"199":{"tf":1.0},"459":{"tf":1.0},"522":{"tf":1.0}}}},"o":{"df":2,"docs":{"294":{"tf":1.0},"300":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"e":{"df":2,"docs":{"240":{"tf":1.0},"500":{"tf":1.0}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":1,"docs":{"697":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":5,"docs":{"199":{"tf":1.0},"629":{"tf":1.0},"644":{"tf":1.0},"826":{"tf":1.0},"912":{"tf":1.0}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"843":{"tf":1.0}}}},"p":{"df":1,"docs":{"267":{"tf":1.0}}}},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":14,"docs":{"126":{"tf":1.0},"252":{"tf":2.23606797749979},"257":{"tf":1.0},"322":{"tf":1.4142135623730951},"336":{"tf":1.0},"344":{"tf":2.6457513110645907},"345":{"tf":2.449489742783178},"346":{"tf":1.7320508075688772},"349":{"tf":1.4142135623730951},"352":{"tf":1.7320508075688772},"436":{"tf":1.4142135623730951},"501":{"tf":2.6457513110645907},"507":{"tf":1.0},"69":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"255":{"tf":1.0},"436":{"tf":1.0},"497":{"tf":1.4142135623730951},"505":{"tf":1.0}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"[":{"0":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":2,"docs":{"349":{"tf":2.0},"352":{"tf":1.0}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":4,"docs":{"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"g":{"df":11,"docs":{"108":{"tf":1.0},"222":{"tf":1.4142135623730951},"346":{"tf":1.0},"47":{"tf":1.0},"519":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":3.7416573867739413},"747":{"tf":1.4142135623730951},"959":{"tf":1.0},"973":{"tf":1.0}}},"k":{"df":4,"docs":{"113":{"tf":1.0},"465":{"tf":1.0},"470":{"tf":1.0},"77":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":7,"docs":{"440":{"tf":1.0},"441":{"tf":1.0},"459":{"tf":1.0},"497":{"tf":1.0},"573":{"tf":1.4142135623730951},"721":{"tf":1.0},"779":{"tf":1.0}},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"554":{"tf":1.0}}}}}}},"t":{"a":{"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":16,"docs":{"199":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.449489742783178},"417":{"tf":2.0},"418":{"tf":1.0},"420":{"tf":1.0},"428":{"tf":1.0},"60":{"tf":1.0},"744":{"tf":1.4142135623730951},"777":{"tf":1.0},"928":{"tf":2.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0},"934":{"tf":1.4142135623730951}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"53":{"tf":1.0}},"i":{"df":1,"docs":{"269":{"tf":1.0}}}},"o":{"df":9,"docs":{"203":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"342":{"tf":1.0},"472":{"tf":1.0},"571":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"992":{"tf":1.0}},"n":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"1006":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{}}}}},"w":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"23":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":6,"docs":{"249":{"tf":1.4142135623730951},"5":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"634":{"tf":1.0},"907":{"tf":1.0}}}},"df":5,"docs":{"346":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.0},"735":{"tf":1.0},"94":{"tf":1.0}},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":6,"docs":{"63":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":1.4142135623730951},"744":{"tf":1.0},"776":{"tf":1.0},"832":{"tf":1.0}}},"t":{"df":2,"docs":{"188":{"tf":1.0},"752":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"939":{"tf":1.0}}}},"v":{"df":1,"docs":{"720":{"tf":1.0}}}}}},"d":{"df":23,"docs":{"133":{"tf":1.0},"152":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"16":{"tf":1.0},"19":{"tf":1.0},"26":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"47":{"tf":1.0},"499":{"tf":1.4142135623730951},"5":{"tf":1.4142135623730951},"503":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.0},"6":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"757":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"931":{"tf":1.0},"936":{"tf":1.0},"951":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"567":{"tf":1.0}}}},"i":{"df":1,"docs":{"272":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":9,"docs":{"137":{"tf":1.0},"138":{"tf":1.0},"199":{"tf":1.4142135623730951},"50":{"tf":1.0},"615":{"tf":1.0},"729":{"tf":1.0},"754":{"tf":1.0},"912":{"tf":1.0},"935":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.0}},"t":{"df":7,"docs":{"215":{"tf":1.0},"223":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.0},"376":{"tf":1.0},"505":{"tf":1.0},"762":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}},"z":{"df":4,"docs":{"250":{"tf":1.0},"567":{"tf":1.0},"749":{"tf":1.0},"843":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"615":{"tf":1.0},"723":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.4142135623730951}}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"701":{"tf":1.0}},"e":{"d":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"i":{"d":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":36,"docs":{"108":{"tf":1.4142135623730951},"124":{"tf":1.0},"148":{"tf":1.0},"170":{"tf":1.0},"232":{"tf":1.4142135623730951},"234":{"tf":1.0},"235":{"tf":1.0},"24":{"tf":1.0},"255":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"438":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"505":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"576":{"tf":1.0},"64":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"721":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"832":{"tf":1.0},"836":{"tf":1.0},"846":{"tf":1.0},"928":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"571":{"tf":1.0}}}}}}},"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"563":{"tf":1.0},"570":{"tf":2.23606797749979}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"528":{"tf":1.0}}},"df":0,"docs":{}}}}},"c":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"526":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":9,"docs":{"627":{"tf":1.4142135623730951},"632":{"tf":1.7320508075688772},"635":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.4142135623730951},"643":{"tf":1.0},"644":{"tf":1.7320508075688772},"646":{"tf":1.0},"648":{"tf":1.4142135623730951}}}},"v":{"df":29,"docs":{"1004":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"439":{"tf":2.0},"466":{"tf":1.0},"467":{"tf":1.0},"483":{"tf":1.0},"491":{"tf":1.0},"507":{"tf":1.4142135623730951},"553":{"tf":1.0},"554":{"tf":1.4142135623730951},"555":{"tf":1.0},"564":{"tf":1.0},"605":{"tf":1.0},"62":{"tf":1.7320508075688772},"633":{"tf":1.0},"65":{"tf":1.4142135623730951},"659":{"tf":1.0},"69":{"tf":1.0},"722":{"tf":1.4142135623730951},"762":{"tf":1.0},"773":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.7320508075688772},"912":{"tf":1.0},"932":{"tf":1.4142135623730951},"994":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"124":{"tf":1.0},"184":{"tf":1.0},"207":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.4142135623730951},"586":{"tf":1.0},"829":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.0},"859":{"tf":1.0},"869":{"tf":1.0},"996":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":6,"docs":{"401":{"tf":1.0},"404":{"tf":1.0},"409":{"tf":1.0},"627":{"tf":1.0},"632":{"tf":1.4142135623730951},"634":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"1007":{"tf":1.0},"381":{"tf":1.0},"470":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":13,"docs":{"272":{"tf":1.0},"290":{"tf":1.0},"346":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":1.0},"712":{"tf":1.0},"846":{"tf":1.7320508075688772},"850":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"567":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"435":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"437":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0}},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"723":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"r":{"d":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"551":{"tf":1.0}}}}},"df":26,"docs":{"126":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.7320508075688772},"257":{"tf":1.0},"348":{"tf":1.0},"350":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"507":{"tf":1.0},"549":{"tf":1.7320508075688772},"550":{"tf":1.7320508075688772},"551":{"tf":2.449489742783178},"553":{"tf":3.1622776601683795},"554":{"tf":1.4142135623730951},"559":{"tf":1.7320508075688772},"568":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"721":{"tf":1.0},"848":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"931":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"1004":{"tf":1.0}}}}},"v":{"df":4,"docs":{"120":{"tf":1.0},"431":{"tf":1.0},"436":{"tf":1.4142135623730951},"437":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":12,"docs":{"310":{"tf":1.0},"356":{"tf":1.0},"430":{"tf":1.4142135623730951},"432":{"tf":1.4142135623730951},"436":{"tf":1.0},"437":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"440":{"tf":1.7320508075688772},"441":{"tf":1.4142135623730951},"444":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":2.0}}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"80":{"tf":1.0},"84":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":4,"docs":{"323":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":1.4142135623730951}},"s":{"df":1,"docs":{"523":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"221":{"tf":1.0}}}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"75":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"424":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"285":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"709":{"tf":1.0},"714":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"u":{"c":{"df":47,"docs":{"1003":{"tf":1.4142135623730951},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"144":{"tf":1.0},"148":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"238":{"tf":1.0},"267":{"tf":1.0},"342":{"tf":1.0},"347":{"tf":1.0},"356":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"40":{"tf":1.0},"410":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"540":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.4142135623730951},"571":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.7320508075688772},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"629":{"tf":1.0},"687":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"723":{"tf":1.4142135623730951},"744":{"tf":1.0},"758":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.4142135623730951},"799":{"tf":1.0},"818":{"tf":1.0},"833":{"tf":1.0},"852":{"tf":1.0},"863":{"tf":1.4142135623730951},"919":{"tf":1.0},"94":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.0}},"t":{"df":5,"docs":{"406":{"tf":1.0},"417":{"tf":1.0},"655":{"tf":1.0},"818":{"tf":1.0},"996":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"f":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"342":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":7,"docs":{"169":{"tf":1.0},"257":{"tf":1.0},"346":{"tf":1.0},"507":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"811":{"tf":1.0}}},"df":0,"docs":{}}}},"df":17,"docs":{"208":{"tf":1.0},"436":{"tf":1.4142135623730951},"437":{"tf":1.0},"640":{"tf":1.0},"717":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"761":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":2.0},"832":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"df":1,"docs":{"444":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":140,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.4142135623730951},"105":{"tf":1.0},"106":{"tf":1.0},"120":{"tf":1.0},"121":{"tf":1.0},"122":{"tf":1.0},"133":{"tf":1.0},"136":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"150":{"tf":1.0},"161":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.0},"182":{"tf":1.0},"192":{"tf":1.0},"195":{"tf":1.0},"214":{"tf":1.0},"215":{"tf":1.0},"228":{"tf":1.0},"229":{"tf":1.0},"231":{"tf":1.0},"242":{"tf":1.0},"247":{"tf":1.0},"260":{"tf":1.0},"268":{"tf":1.0},"277":{"tf":1.0},"279":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.0},"308":{"tf":1.0},"311":{"tf":1.0},"319":{"tf":1.0},"322":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":2.0},"364":{"tf":1.0},"366":{"tf":1.0},"383":{"tf":1.0},"386":{"tf":1.0},"397":{"tf":1.0},"400":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.0},"430":{"tf":1.0},"447":{"tf":1.0},"450":{"tf":1.0},"451":{"tf":1.0},"46":{"tf":1.4142135623730951},"462":{"tf":1.0},"465":{"tf":1.0},"479":{"tf":1.0},"481":{"tf":1.0},"492":{"tf":1.0},"495":{"tf":1.0},"510":{"tf":1.0},"513":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"524":{"tf":2.0},"525":{"tf":1.4142135623730951},"532":{"tf":1.4142135623730951},"535":{"tf":1.0},"546":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.0},"563":{"tf":1.0},"583":{"tf":1.0},"584":{"tf":1.0},"595":{"tf":1.0},"598":{"tf":1.0},"610":{"tf":1.0},"613":{"tf":1.0},"624":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"646":{"tf":1.0},"649":{"tf":1.0},"661":{"tf":1.0},"664":{"tf":1.0},"675":{"tf":1.0},"678":{"tf":1.0},"689":{"tf":1.0},"692":{"tf":1.0},"706":{"tf":1.0},"709":{"tf":1.0},"726":{"tf":1.0},"74":{"tf":1.0},"741":{"tf":1.4142135623730951},"748":{"tf":1.0},"754":{"tf":1.0},"756":{"tf":1.0},"757":{"tf":1.0},"768":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"780":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.0},"795":{"tf":1.0},"805":{"tf":1.0},"808":{"tf":1.0},"824":{"tf":1.0},"827":{"tf":1.0},"838":{"tf":1.0},"841":{"tf":1.0},"855":{"tf":1.4142135623730951},"857":{"tf":1.0},"869":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"888":{"tf":1.0},"891":{"tf":1.0},"90":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.4142135623730951},"908":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.0},"940":{"tf":1.0},"954":{"tf":1.0},"957":{"tf":1.0},"971":{"tf":1.0},"974":{"tf":1.0},"985":{"tf":1.0},"988":{"tf":1.0},"999":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"523":{"tf":1.0}}},"d":{"a":{"'":{"df":1,"docs":{"149":{"tf":1.0}}},"df":26,"docs":{"122":{"tf":1.4142135623730951},"123":{"tf":1.0},"124":{"tf":1.7320508075688772},"125":{"tf":1.4142135623730951},"126":{"tf":1.4142135623730951},"132":{"tf":1.0},"136":{"tf":1.7320508075688772},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.4142135623730951},"146":{"tf":1.0},"148":{"tf":1.4142135623730951},"149":{"tf":1.0},"187":{"tf":1.4142135623730951},"272":{"tf":1.0},"370":{"tf":1.0},"797":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.4142135623730951},"848":{"tf":2.0},"849":{"tf":1.0},"852":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.4142135623730951},"863":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"185":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"126":{"tf":1.0}}}}}},"df":20,"docs":{"132":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.4142135623730951},"272":{"tf":1.7320508075688772},"274":{"tf":1.0},"315":{"tf":1.0},"440":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772},"847":{"tf":1.4142135623730951},"852":{"tf":1.0},"857":{"tf":2.23606797749979},"860":{"tf":2.0},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":1.0},"869":{"tf":1.4142135623730951},"911":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"38":{"tf":1.4142135623730951},"45":{"tf":2.0},"47":{"tf":1.4142135623730951},"51":{"tf":1.0},"771":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"45":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.0},"125":{"tf":1.0},"138":{"tf":1.0},"191":{"tf":1.7320508075688772},"199":{"tf":1.0},"206":{"tf":1.0},"455":{"tf":1.0},"777":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"777":{"tf":1.0}}}},"m":{"df":2,"docs":{"214":{"tf":1.0},"7":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"203":{"tf":1.4142135623730951},"777":{"tf":1.0}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"653":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"g":{"a":{"df":0,"docs":{},"r":{"d":{"df":14,"docs":{"184":{"tf":1.0},"194":{"tf":1.0},"231":{"tf":1.0},"425":{"tf":1.0},"539":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"555":{"tf":1.0},"57":{"tf":1.0},"575":{"tf":1.0},"6":{"tf":1.0},"8":{"tf":1.0},"843":{"tf":1.0},"938":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":5,"docs":{"221":{"tf":1.0},"440":{"tf":1.0},"614":{"tf":1.0},"698":{"tf":1.7320508075688772},"783":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"205":{"tf":3.0}}},"df":19,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":5.196152422706632},"205":{"tf":6.082762530298219},"207":{"tf":1.0},"208":{"tf":4.0},"743":{"tf":1.7320508075688772},"744":{"tf":1.7320508075688772},"747":{"tf":1.0},"748":{"tf":1.0},"940":{"tf":1.7320508075688772},"941":{"tf":1.0},"942":{"tf":1.7320508075688772},"943":{"tf":1.0},"944":{"tf":3.0},"945":{"tf":1.0},"947":{"tf":1.0},"948":{"tf":1.0},"949":{"tf":1.0},"959":{"tf":1.0}},"i":{"d":{"df":2,"docs":{"205":{"tf":2.449489742783178},"208":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"944":{"tf":1.0}}},"df":0,"docs":{}}}},"x":{"df":1,"docs":{"911":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"t":{"df":45,"docs":{"108":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.7320508075688772},"254":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.0},"3":{"tf":1.0},"372":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"495":{"tf":1.0},"501":{"tf":2.6457513110645907},"502":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"58":{"tf":1.4142135623730951},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"62":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":2.6457513110645907},"654":{"tf":1.4142135623730951},"658":{"tf":1.0},"660":{"tf":1.0},"73":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.4142135623730951},"813":{"tf":1.0},"814":{"tf":3.0},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"826":{"tf":1.0},"974":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.0},"978":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"r":{"df":8,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"121":{"tf":1.0},"814":{"tf":1.4142135623730951},"816":{"tf":1.0},"817":{"tf":1.0},"895":{"tf":1.0}}}},"df":20,"docs":{"121":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.0},"58":{"tf":1.0},"808":{"tf":2.0},"809":{"tf":1.0},"810":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":2.0},"818":{"tf":1.0},"822":{"tf":1.0},"826":{"tf":1.0},"859":{"tf":1.0},"912":{"tf":1.0}},"i":{"df":1,"docs":{"111":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":18,"docs":{"200":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":2.6457513110645907},"205":{"tf":2.23606797749979},"211":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.4142135623730951},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"61":{"tf":1.0},"645":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.0},"81":{"tf":1.4142135623730951},"814":{"tf":1.7320508075688772},"817":{"tf":1.0},"983":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"203":{"tf":1.0},"515":{"tf":1.0}}}}}},"df":2,"docs":{"428":{"tf":1.0},"842":{"tf":1.0}}}}},"h":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"375":{"tf":1.0},"376":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"231":{"tf":1.0},"232":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"19":{"tf":1.0}}}}}}}}}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":11,"docs":{"112":{"tf":1.0},"126":{"tf":2.0},"272":{"tf":1.0},"284":{"tf":1.0},"514":{"tf":1.0},"6":{"tf":1.4142135623730951},"629":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"879":{"tf":3.605551275463989},"880":{"tf":1.7320508075688772}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}}}}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"t":{"df":137,"docs":{"1":{"tf":1.0},"1001":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.0},"1015":{"tf":1.4142135623730951},"112":{"tf":1.0},"115":{"tf":1.0},"122":{"tf":1.0},"128":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":1.0},"140":{"tf":1.0},"144":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.0},"182":{"tf":1.0},"184":{"tf":1.0},"188":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":1.0},"226":{"tf":1.0},"229":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"246":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.0},"262":{"tf":1.0},"276":{"tf":1.0},"279":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.0},"294":{"tf":1.0},"3":{"tf":1.7320508075688772},"304":{"tf":1.0},"310":{"tf":1.0},"311":{"tf":1.0},"321":{"tf":1.0},"322":{"tf":1.0},"323":{"tf":1.0},"341":{"tf":1.4142135623730951},"343":{"tf":1.0},"35":{"tf":1.0},"361":{"tf":1.0},"366":{"tf":1.0},"37":{"tf":1.4142135623730951},"371":{"tf":1.0},"373":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"386":{"tf":1.0},"399":{"tf":1.0},"414":{"tf":1.0},"430":{"tf":1.0},"441":{"tf":1.0},"449":{"tf":1.0},"451":{"tf":1.0},"464":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"494":{"tf":1.0},"495":{"tf":1.0},"512":{"tf":1.4142135623730951},"513":{"tf":1.0},"53":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.0},"584":{"tf":1.0},"597":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"605":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":1.0},"626":{"tf":1.0},"627":{"tf":1.0},"648":{"tf":1.0},"649":{"tf":1.0},"663":{"tf":1.7320508075688772},"664":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":1.0},"708":{"tf":1.0},"709":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"728":{"tf":1.0},"757":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"815":{"tf":1.0},"826":{"tf":1.0},"827":{"tf":1.0},"840":{"tf":1.4142135623730951},"859":{"tf":1.4142135623730951},"867":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.0},"879":{"tf":1.0},"890":{"tf":1.0},"891":{"tf":1.0},"9":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"926":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"940":{"tf":1.0},"954":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.0},"973":{"tf":1.0},"974":{"tf":1.0},"987":{"tf":1.4142135623730951},"988":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":7,"docs":{"267":{"tf":1.0},"571":{"tf":1.0},"698":{"tf":1.4142135623730951},"711":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.7320508075688772},"83":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"x":{"df":1,"docs":{"832":{"tf":1.0}}},"y":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"634":{"tf":1.0}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"205":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":4,"docs":{"296":{"tf":1.4142135623730951},"300":{"tf":1.7320508075688772},"301":{"tf":1.4142135623730951},"62":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":77,"docs":{"113":{"tf":1.0},"121":{"tf":1.0},"153":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":3.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.4142135623730951},"207":{"tf":2.0},"208":{"tf":2.449489742783178},"212":{"tf":1.4142135623730951},"216":{"tf":1.4142135623730951},"217":{"tf":1.4142135623730951},"218":{"tf":1.0},"219":{"tf":1.0},"220":{"tf":1.4142135623730951},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"226":{"tf":1.0},"230":{"tf":1.0},"247":{"tf":1.7320508075688772},"249":{"tf":1.7320508075688772},"254":{"tf":1.0},"329":{"tf":1.0},"346":{"tf":1.7320508075688772},"365":{"tf":1.0},"366":{"tf":1.7320508075688772},"367":{"tf":1.0},"368":{"tf":2.0},"369":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":2.449489742783178},"376":{"tf":1.4142135623730951},"377":{"tf":1.0},"380":{"tf":1.0},"383":{"tf":1.4142135623730951},"384":{"tf":1.0},"385":{"tf":1.4142135623730951},"432":{"tf":1.4142135623730951},"433":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.4142135623730951},"499":{"tf":1.0},"500":{"tf":1.7320508075688772},"515":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.7320508075688772},"58":{"tf":1.0},"59":{"tf":1.4142135623730951},"60":{"tf":1.7320508075688772},"61":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"632":{"tf":1.4142135623730951},"633":{"tf":2.23606797749979},"634":{"tf":1.7320508075688772},"637":{"tf":1.4142135623730951},"640":{"tf":1.7320508075688772},"643":{"tf":1.0},"66":{"tf":1.0},"71":{"tf":2.0},"712":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.7320508075688772},"78":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"938":{"tf":1.0}}}},"df":16,"docs":{"205":{"tf":1.0},"257":{"tf":1.0},"269":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.7320508075688772},"418":{"tf":1.0},"438":{"tf":1.0},"469":{"tf":1.4142135623730951},"472":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.0},"554":{"tf":1.0},"564":{"tf":1.0},"711":{"tf":1.4142135623730951},"777":{"tf":1.0},"786":{"tf":3.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":11,"docs":{"209":{"tf":1.0},"315":{"tf":1.0},"371":{"tf":1.0},"440":{"tf":1.0},"701":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":1.7320508075688772},"879":{"tf":2.449489742783178},"880":{"tf":1.0},"895":{"tf":2.0},"917":{"tf":1.0}}}},"df":1,"docs":{"773":{"tf":1.0}},"v":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"697":{"tf":1.0}}}}}}},"df":13,"docs":{"1013":{"tf":1.0},"208":{"tf":1.0},"218":{"tf":1.0},"322":{"tf":1.0},"325":{"tf":1.0},"334":{"tf":1.0},"340":{"tf":1.0},"345":{"tf":1.0},"522":{"tf":1.0},"58":{"tf":1.0},"723":{"tf":1.0},"929":{"tf":1.0},"941":{"tf":1.0}}}},"i":{"a":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"230":{"tf":1.0},"512":{"tf":1.4142135623730951},"720":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"n":{"c":{"df":4,"docs":{"230":{"tf":1.0},"236":{"tf":1.0},"296":{"tf":1.0},"429":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"934":{"tf":1.0}}}}},"df":21,"docs":{"15":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"262":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"303":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"473":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"514":{"tf":1.4142135623730951},"55":{"tf":1.0},"553":{"tf":1.0},"629":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0}}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"797":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"204":{"tf":1.0}}},"df":30,"docs":{"193":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"267":{"tf":1.0},"323":{"tf":1.0},"348":{"tf":1.4142135623730951},"361":{"tf":1.0},"384":{"tf":1.0},"51":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"638":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.0},"735":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"792":{"tf":1.0},"817":{"tf":1.0},"84":{"tf":1.0},"889":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.4142135623730951},"992":{"tf":1.0},"994":{"tf":1.0}}}},"r":{"df":0,"docs":{},"k":{"(":{"df":1,"docs":{"848":{"tf":1.0}}},"df":5,"docs":{"272":{"tf":1.0},"273":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"850":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":15,"docs":{"375":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":3.0},"603":{"tf":1.4142135623730951},"605":{"tf":1.0},"614":{"tf":1.0},"694":{"tf":1.4142135623730951},"701":{"tf":1.7320508075688772},"704":{"tf":1.0},"758":{"tf":1.0},"761":{"tf":1.4142135623730951},"79":{"tf":1.0},"84":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":4,"docs":{"602":{"tf":2.6457513110645907},"603":{"tf":2.0},"605":{"tf":1.0},"698":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"2":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}}},"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"m":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":2.23606797749979},"603":{"tf":1.4142135623730951},"698":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.7320508075688772}},"v":{"2":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"v":{"df":65,"docs":{"169":{"tf":1.0},"172":{"tf":1.0},"178":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"249":{"tf":1.4142135623730951},"255":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.4142135623730951},"273":{"tf":2.23606797749979},"285":{"tf":1.0},"295":{"tf":1.0},"310":{"tf":1.0},"347":{"tf":1.0},"375":{"tf":1.4142135623730951},"380":{"tf":1.0},"386":{"tf":1.0},"440":{"tf":1.4142135623730951},"505":{"tf":1.0},"519":{"tf":1.0},"524":{"tf":1.4142135623730951},"573":{"tf":1.0},"613":{"tf":1.7320508075688772},"614":{"tf":1.0},"617":{"tf":1.0},"632":{"tf":1.0},"643":{"tf":1.0},"663":{"tf":1.0},"668":{"tf":1.0},"678":{"tf":1.7320508075688772},"679":{"tf":1.0},"682":{"tf":1.0},"714":{"tf":1.0},"730":{"tf":1.4142135623730951},"735":{"tf":1.4142135623730951},"740":{"tf":1.7320508075688772},"767":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.4142135623730951},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.7320508075688772},"818":{"tf":1.4142135623730951},"827":{"tf":1.7320508075688772},"829":{"tf":1.0},"835":{"tf":1.0},"879":{"tf":2.8284271247461903},"880":{"tf":2.23606797749979},"881":{"tf":1.4142135623730951},"885":{"tf":1.0},"889":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0},"974":{"tf":1.7320508075688772},"975":{"tf":1.0},"978":{"tf":1.4142135623730951},"983":{"tf":1.0},"984":{"tf":1.4142135623730951}},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"\"":{"df":0,"docs":{},"{":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"273":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.7320508075688772}}}}}}},"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"292":{"tf":1.4142135623730951},"634":{"tf":1.0}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"375":{"tf":1.0},"517":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"205":{"tf":1.0}}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"l":{"_":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"c":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":14,"docs":{"1003":{"tf":1.4142135623730951},"203":{"tf":2.8284271247461903},"204":{"tf":2.8284271247461903},"205":{"tf":4.123105625617661},"207":{"tf":1.7320508075688772},"213":{"tf":1.0},"296":{"tf":1.4142135623730951},"308":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":2.23606797749979},"776":{"tf":2.8284271247461903},"777":{"tf":1.4142135623730951},"909":{"tf":1.0},"913":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}}}}}}}}},"df":1,"docs":{"814":{"tf":1.7320508075688772}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}}}}}}}}},"df":0,"docs":{}}}}},"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":9,"docs":{"51":{"tf":1.0},"808":{"tf":2.0},"809":{"tf":1.0},"811":{"tf":1.7320508075688772},"813":{"tf":2.0},"814":{"tf":2.449489742783178},"815":{"tf":1.7320508075688772},"816":{"tf":1.7320508075688772},"817":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"565":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"253":{"tf":1.0},"483":{"tf":1.0},"553":{"tf":1.0},"711":{"tf":1.0},"761":{"tf":1.7320508075688772}},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"402":{"tf":1.0}}}}}},"l":{"a":{"c":{"df":24,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"151":{"tf":1.0},"234":{"tf":1.0},"255":{"tf":1.0},"281":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"363":{"tf":1.0},"370":{"tf":1.0},"386":{"tf":1.4142135623730951},"391":{"tf":1.0},"417":{"tf":1.0},"524":{"tf":1.4142135623730951},"64":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"69":{"tf":1.0},"705":{"tf":1.0},"721":{"tf":1.0},"739":{"tf":1.0},"761":{"tf":1.4142135623730951},"887":{"tf":1.0},"95":{"tf":1.0}},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":11,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"551":{"tf":1.0},"79":{"tf":1.7320508075688772},"80":{"tf":1.0},"81":{"tf":1.4142135623730951},"83":{"tf":2.6457513110645907},"84":{"tf":1.4142135623730951},"85":{"tf":1.0},"87":{"tf":1.4142135623730951},"933":{"tf":1.0}}},"df":4,"docs":{"759":{"tf":1.7320508075688772},"761":{"tf":1.4142135623730951},"763":{"tf":2.23606797749979},"847":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"761":{"tf":2.0},"763":{"tf":1.4142135623730951}}}}}},"o":{"df":7,"docs":{"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.4142135623730951},"319":{"tf":1.0},"985":{"tf":1.0}},"r":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"6":{"tf":1.0}}}}}}}}},"df":12,"docs":{"121":{"tf":1.0},"161":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"375":{"tf":1.7320508075688772},"45":{"tf":1.0},"450":{"tf":1.0},"6":{"tf":2.23606797749979},"710":{"tf":1.4142135623730951},"72":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":2,"docs":{"6":{"tf":2.0},"8":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":8,"docs":{"249":{"tf":1.0},"272":{"tf":1.0},"313":{"tf":1.0},"415":{"tf":1.0},"571":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"933":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":32,"docs":{"198":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.7320508075688772},"22":{"tf":1.0},"221":{"tf":1.4142135623730951},"255":{"tf":1.0},"270":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"385":{"tf":1.0},"404":{"tf":1.4142135623730951},"44":{"tf":1.0},"47":{"tf":1.0},"5":{"tf":1.4142135623730951},"505":{"tf":1.0},"514":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"524":{"tf":1.7320508075688772},"525":{"tf":1.0},"539":{"tf":1.4142135623730951},"588":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"7":{"tf":1.0},"735":{"tf":1.4142135623730951},"747":{"tf":1.4142135623730951},"761":{"tf":1.0},"774":{"tf":1.0},"786":{"tf":1.4142135623730951},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"19":{"tf":1.0},"3":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"532":{"tf":1.7320508075688772},"539":{"tf":1.0}}}}}}},"o":{"d":{"df":0,"docs":{},"u":{"c":{"df":4,"docs":{"528":{"tf":1.0},"571":{"tf":1.0},"81":{"tf":1.0},"85":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":3,"docs":{"1":{"tf":1.0},"631":{"tf":1.0},"7":{"tf":1.0}}}}}},"t":{"df":5,"docs":{"439":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.4142135623730951},"919":{"tf":1.4142135623730951}}}}},"q":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"/":{"1":{"df":1,"docs":{"440":{"tf":1.0}}},"2":{"df":1,"docs":{"440":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"439":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":4,"docs":{"62":{"tf":1.4142135623730951},"65":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0}}}}}}}}}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"735":{"tf":2.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"_":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"223":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}}},"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"62":{"tf":1.0}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":4,"docs":{"56":{"tf":1.4142135623730951},"61":{"tf":1.0},"62":{"tf":1.4142135623730951},"63":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"61":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"77":{"tf":1.0}}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":48,"docs":{"0":{"tf":1.0},"105":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.7320508075688772},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"25":{"tf":1.0},"253":{"tf":2.23606797749979},"254":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"291":{"tf":1.0},"35":{"tf":1.0},"409":{"tf":1.0},"436":{"tf":1.7320508075688772},"439":{"tf":3.7416573867739413},"450":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":1.0},"503":{"tf":1.0},"512":{"tf":1.4142135623730951},"554":{"tf":1.0},"564":{"tf":1.7320508075688772},"568":{"tf":1.0},"570":{"tf":1.0},"576":{"tf":1.0},"6":{"tf":2.6457513110645907},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"66":{"tf":1.4142135623730951},"69":{"tf":2.0},"711":{"tf":1.0},"735":{"tf":2.8284271247461903},"757":{"tf":1.7320508075688772},"761":{"tf":3.4641016151377544},"763":{"tf":1.4142135623730951},"765":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"770":{"tf":1.0},"78":{"tf":2.0},"83":{"tf":1.0},"992":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"r":{"df":165,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"108":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"115":{"tf":1.0},"121":{"tf":1.0},"125":{"tf":1.0},"128":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"141":{"tf":1.0},"146":{"tf":1.4142135623730951},"151":{"tf":1.0},"152":{"tf":1.4142135623730951},"158":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"166":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.4142135623730951},"209":{"tf":1.0},"215":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.0},"229":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.7320508075688772},"284":{"tf":1.0},"288":{"tf":1.0},"294":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"315":{"tf":1.0},"339":{"tf":1.0},"341":{"tf":1.0},"343":{"tf":1.4142135623730951},"345":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"372":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"378":{"tf":1.0},"38":{"tf":1.0},"382":{"tf":1.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.0},"41":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"411":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"414":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.7320508075688772},"422":{"tf":1.4142135623730951},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"436":{"tf":1.0},"44":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"456":{"tf":1.0},"457":{"tf":1.0},"467":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.0},"51":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"519":{"tf":1.7320508075688772},"52":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":2.23606797749979},"523":{"tf":1.7320508075688772},"526":{"tf":2.0},"528":{"tf":1.0},"53":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.4142135623730951},"588":{"tf":1.0},"593":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":2.6457513110645907},"605":{"tf":1.0},"644":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"696":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":1.4142135623730951},"72":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"744":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"779":{"tf":1.4142135623730951},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"797":{"tf":1.0},"801":{"tf":1.0},"803":{"tf":1.0},"808":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.4142135623730951},"813":{"tf":1.7320508075688772},"814":{"tf":2.23606797749979},"817":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.7320508075688772},"847":{"tf":1.4142135623730951},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"855":{"tf":1.4142135623730951},"860":{"tf":1.4142135623730951},"871":{"tf":1.0},"874":{"tf":1.0},"875":{"tf":1.4142135623730951},"876":{"tf":1.4142135623730951},"879":{"tf":1.0},"88":{"tf":1.0},"880":{"tf":1.7320508075688772},"883":{"tf":1.0},"891":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"902":{"tf":1.0},"904":{"tf":1.0},"908":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.7320508075688772},"919":{"tf":1.0},"921":{"tf":1.0},"929":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0},"994":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"_":{"a":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"613":{"tf":1.7320508075688772},"615":{"tf":2.0},"617":{"tf":1.7320508075688772},"619":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"575":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"374":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{"df":4,"docs":{"106":{"tf":1.0},"121":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":12,"docs":{"1013":{"tf":1.0},"201":{"tf":1.0},"211":{"tf":1.0},"324":{"tf":1.7320508075688772},"325":{"tf":1.0},"359":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"798":{"tf":1.0},"819":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":1,"docs":{"912":{"tf":2.0}}},"m":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"175":{"tf":1.0},"569":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"v":{"df":25,"docs":{"204":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"539":{"tf":1.7320508075688772},"599":{"tf":2.0},"6":{"tf":2.0},"600":{"tf":1.0},"602":{"tf":2.449489742783178},"603":{"tf":2.0},"634":{"tf":1.4142135623730951},"635":{"tf":1.0},"648":{"tf":1.4142135623730951},"653":{"tf":1.0},"735":{"tf":1.7320508075688772},"776":{"tf":1.0},"810":{"tf":1.0},"814":{"tf":2.0},"815":{"tf":1.0},"818":{"tf":1.0},"879":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.4142135623730951},"917":{"tf":1.4142135623730951},"919":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"232":{"tf":1.0}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":3,"docs":{"773":{"tf":1.0},"776":{"tf":3.1622776601683795},"777":{"tf":1.0}}},"df":0,"docs":{}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"d":{"1":{"df":1,"docs":{"634":{"tf":2.6457513110645907}}},"2":{"df":1,"docs":{"634":{"tf":2.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"198":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"628":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"249":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"628":{"tf":1.0},"776":{"tf":1.0}}}},"v":{"df":5,"docs":{"553":{"tf":1.0},"573":{"tf":1.0},"67":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.4142135623730951}}}},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"c":{"df":28,"docs":{"108":{"tf":1.0},"121":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"204":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"251":{"tf":1.0},"296":{"tf":1.0},"346":{"tf":1.0},"366":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"377":{"tf":1.0},"380":{"tf":1.0},"418":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"77":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"968":{"tf":1.0}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"284":{"tf":1.0},"370":{"tf":1.0},"450":{"tf":1.0},"516":{"tf":1.0},"576":{"tf":1.0},"747":{"tf":1.0},"751":{"tf":1.0},"803":{"tf":1.0},"931":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"n":{"d":{"df":7,"docs":{"253":{"tf":1.0},"439":{"tf":1.4142135623730951},"69":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"78":{"tf":1.4142135623730951}}},"df":0,"docs":{},"s":{"df":29,"docs":{"113":{"tf":1.0},"121":{"tf":1.0},"139":{"tf":1.0},"175":{"tf":1.0},"203":{"tf":1.4142135623730951},"216":{"tf":1.0},"253":{"tf":2.23606797749979},"254":{"tf":1.0},"255":{"tf":1.0},"328":{"tf":1.0},"418":{"tf":1.4142135623730951},"427":{"tf":1.7320508075688772},"439":{"tf":2.0},"450":{"tf":1.4142135623730951},"505":{"tf":1.0},"6":{"tf":2.0},"735":{"tf":1.4142135623730951},"761":{"tf":2.23606797749979},"762":{"tf":1.7320508075688772},"763":{"tf":1.4142135623730951},"777":{"tf":1.0},"78":{"tf":1.4142135623730951},"810":{"tf":1.0},"913":{"tf":1.0},"988":{"tf":1.7320508075688772},"989":{"tf":1.0},"992":{"tf":1.0},"994":{"tf":1.0},"996":{"tf":1.0}},"e":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"6":{"tf":1.0}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"6":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"257":{"tf":1.0}}}}},"df":12,"docs":{"485":{"tf":1.0},"602":{"tf":1.4142135623730951},"606":{"tf":1.0},"615":{"tf":1.0},"632":{"tf":1.0},"654":{"tf":1.4142135623730951},"660":{"tf":1.0},"696":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"872":{"tf":1.0},"933":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"107":{"tf":1.0},"573":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"199":{"tf":1.4142135623730951},"388":{"tf":1.0},"576":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"772":{"tf":1.0},"776":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"u":{"b":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"78":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"u":{"6":{"4":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"23":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"q":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}}},"df":60,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"137":{"tf":1.0},"152":{"tf":1.0},"171":{"tf":1.4142135623730951},"179":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"206":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.0},"25":{"tf":2.0},"26":{"tf":2.0},"296":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"350":{"tf":1.4142135623730951},"356":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"404":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"49":{"tf":1.0},"50":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.4142135623730951},"539":{"tf":1.0},"553":{"tf":1.0},"565":{"tf":1.0},"599":{"tf":1.4142135623730951},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"651":{"tf":1.0},"658":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":3.0},"736":{"tf":1.0},"776":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"858":{"tf":1.0},"916":{"tf":1.0},"983":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"40":{"tf":1.0}}},"n":{"df":4,"docs":{"207":{"tf":1.0},"467":{"tf":1.0},"693":{"tf":1.0},"815":{"tf":1.0}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"577":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":5,"docs":{"26":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":2.0},"449":{"tf":1.0},"450":{"tf":1.0}}}}},"o":{"a":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"401":{"tf":1.0},"402":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"302":{"tf":1.0},"564":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"25":{"tf":1.0},"26":{"tf":1.4142135623730951}}},"y":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"25":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"df":32,"docs":{"140":{"tf":1.0},"149":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"221":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"280":{"tf":1.0},"284":{"tf":2.0},"286":{"tf":1.0},"288":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":1.0},"333":{"tf":1.0},"341":{"tf":1.4142135623730951},"351":{"tf":1.0},"404":{"tf":1.7320508075688772},"439":{"tf":1.0},"452":{"tf":1.4142135623730951},"455":{"tf":1.4142135623730951},"461":{"tf":1.0},"565":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"660":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":7.280109889280518},"786":{"tf":1.0},"879":{"tf":2.23606797749979},"97":{"tf":1.0}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"847":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"276":{"tf":1.0}}}},"df":0,"docs":{}},"df":2,"docs":{"203":{"tf":1.0},"364":{"tf":1.0}}}},"v":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"721":{"tf":1.0},"722":{"tf":1.0},"777":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":15,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"206":{"tf":1.7320508075688772},"208":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":2.23606797749979},"263":{"tf":1.7320508075688772},"264":{"tf":2.0},"265":{"tf":1.0},"267":{"tf":2.6457513110645907},"576":{"tf":1.0},"777":{"tf":2.0}}}},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"773":{"tf":1.0}}},"t":{"df":1,"docs":{"913":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":6,"docs":{"211":{"tf":1.4142135623730951},"314":{"tf":1.0},"422":{"tf":1.0},"797":{"tf":1.4142135623730951},"885":{"tf":1.0},"935":{"tf":1.0}}}},"s":{"df":3,"docs":{"272":{"tf":1.0},"415":{"tf":1.0},"926":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"243":{"tf":1.0},"771":{"tf":1.4142135623730951},"831":{"tf":1.0}}}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":30,"docs":{"1002":{"tf":1.7320508075688772},"1003":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"303":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"632":{"tf":1.0},"709":{"tf":2.0},"710":{"tf":1.0},"711":{"tf":2.0},"712":{"tf":2.8284271247461903},"714":{"tf":2.8284271247461903},"717":{"tf":1.7320508075688772},"718":{"tf":1.0},"720":{"tf":2.23606797749979},"721":{"tf":1.7320508075688772},"722":{"tf":1.7320508075688772},"724":{"tf":2.0},"725":{"tf":2.23606797749979},"729":{"tf":1.4142135623730951},"813":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{"[":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"577":{"tf":1.0}}}}}}},"f":{"c":{"#":{"0":{"0":{"0":{"1":{"df":1,"docs":{"811":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"'":{"df":1,"docs":{"555":{"tf":1.0}}},"2":{"0":{"df":1,"docs":{"184":{"tf":1.0}}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"927":{"tf":1.0}}},"df":0,"docs":{}},"4":{"2":{"df":1,"docs":{"154":{"tf":1.0}}},"df":0,"docs":{}},"8":{"4":{"df":4,"docs":{"166":{"tf":1.0},"170":{"tf":1.0},"588":{"tf":1.0},"594":{"tf":1.0}}},"df":0,"docs":{}},"9":{"9":{"df":3,"docs":{"166":{"tf":1.0},"170":{"tf":1.0},"179":{"tf":1.0}}},"df":0,"docs":{}},"df":284,"docs":{"0":{"tf":1.0},"1":{"tf":1.4142135623730951},"1002":{"tf":1.4142135623730951},"1004":{"tf":1.0},"1006":{"tf":1.0},"1007":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.7320508075688772},"103":{"tf":1.0},"106":{"tf":1.4142135623730951},"107":{"tf":1.4142135623730951},"115":{"tf":1.0},"117":{"tf":1.0},"118":{"tf":1.0},"119":{"tf":1.0},"120":{"tf":1.0},"122":{"tf":1.4142135623730951},"128":{"tf":1.0},"13":{"tf":1.0},"136":{"tf":1.4142135623730951},"14":{"tf":1.0},"150":{"tf":1.4142135623730951},"151":{"tf":1.0},"152":{"tf":1.0},"154":{"tf":1.4142135623730951},"155":{"tf":1.0},"159":{"tf":1.0},"16":{"tf":1.4142135623730951},"161":{"tf":1.0},"164":{"tf":1.4142135623730951},"165":{"tf":1.0},"17":{"tf":1.4142135623730951},"182":{"tf":1.4142135623730951},"183":{"tf":1.0},"185":{"tf":1.0},"186":{"tf":1.4142135623730951},"191":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.4142135623730951},"2":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"212":{"tf":1.4142135623730951},"215":{"tf":1.4142135623730951},"216":{"tf":1.4142135623730951},"219":{"tf":1.0},"226":{"tf":1.4142135623730951},"229":{"tf":1.4142135623730951},"230":{"tf":1.0},"231":{"tf":1.7320508075688772},"234":{"tf":1.0},"240":{"tf":1.0},"241":{"tf":1.0},"247":{"tf":1.4142135623730951},"248":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"251":{"tf":2.23606797749979},"252":{"tf":1.4142135623730951},"255":{"tf":1.7320508075688772},"261":{"tf":1.0},"263":{"tf":1.4142135623730951},"264":{"tf":1.0},"267":{"tf":1.4142135623730951},"268":{"tf":1.4142135623730951},"269":{"tf":1.0},"279":{"tf":1.4142135623730951},"281":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.4142135623730951},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"3":{"tf":2.449489742783178},"301":{"tf":1.0},"302":{"tf":1.0},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"310":{"tf":1.4142135623730951},"311":{"tf":1.4142135623730951},"312":{"tf":1.0},"322":{"tf":1.4142135623730951},"324":{"tf":1.0},"325":{"tf":1.4142135623730951},"326":{"tf":1.0},"340":{"tf":1.0},"354":{"tf":1.0},"358":{"tf":1.0},"361":{"tf":1.4142135623730951},"363":{"tf":1.0},"364":{"tf":1.0},"365":{"tf":1.0},"366":{"tf":1.4142135623730951},"37":{"tf":1.0},"370":{"tf":1.4142135623730951},"373":{"tf":1.7320508075688772},"375":{"tf":1.0},"38":{"tf":1.4142135623730951},"386":{"tf":1.4142135623730951},"400":{"tf":1.4142135623730951},"401":{"tf":1.0},"404":{"tf":1.4142135623730951},"407":{"tf":1.0},"410":{"tf":1.4142135623730951},"411":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"430":{"tf":1.4142135623730951},"441":{"tf":1.0},"451":{"tf":1.4142135623730951},"452":{"tf":2.0},"453":{"tf":1.0},"464":{"tf":1.0},"465":{"tf":1.4142135623730951},"466":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"472":{"tf":1.0},"481":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"495":{"tf":1.4142135623730951},"496":{"tf":1.7320508075688772},"497":{"tf":1.0},"499":{"tf":1.4142135623730951},"5":{"tf":1.0},"500":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"513":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.0},"518":{"tf":1.0},"519":{"tf":1.4142135623730951},"522":{"tf":1.0},"523":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.4142135623730951},"535":{"tf":1.4142135623730951},"536":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.4142135623730951},"549":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"56":{"tf":1.4142135623730951},"563":{"tf":1.7320508075688772},"564":{"tf":1.0},"576":{"tf":1.0},"584":{"tf":1.4142135623730951},"585":{"tf":1.0},"598":{"tf":1.4142135623730951},"599":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"613":{"tf":1.4142135623730951},"614":{"tf":1.0},"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.0},"641":{"tf":1.0},"646":{"tf":1.0},"648":{"tf":1.0},"649":{"tf":1.4142135623730951},"650":{"tf":1.0},"654":{"tf":1.0},"658":{"tf":1.0},"660":{"tf":1.0},"661":{"tf":1.7320508075688772},"664":{"tf":1.4142135623730951},"665":{"tf":1.4142135623730951},"675":{"tf":1.7320508075688772},"678":{"tf":1.4142135623730951},"679":{"tf":1.0},"683":{"tf":1.0},"69":{"tf":1.4142135623730951},"692":{"tf":1.4142135623730951},"697":{"tf":1.0},"7":{"tf":1.4142135623730951},"700":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.4142135623730951},"709":{"tf":1.4142135623730951},"727":{"tf":1.0},"730":{"tf":1.4142135623730951},"736":{"tf":1.0},"737":{"tf":1.4142135623730951},"739":{"tf":1.4142135623730951},"740":{"tf":1.4142135623730951},"741":{"tf":1.4142135623730951},"742":{"tf":1.0},"743":{"tf":2.23606797749979},"745":{"tf":1.0},"748":{"tf":1.0},"75":{"tf":1.0},"754":{"tf":1.0},"755":{"tf":1.4142135623730951},"757":{"tf":1.4142135623730951},"765":{"tf":1.0},"768":{"tf":1.0},"771":{"tf":1.7320508075688772},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"780":{"tf":1.4142135623730951},"782":{"tf":1.4142135623730951},"783":{"tf":1.0},"79":{"tf":1.4142135623730951},"795":{"tf":1.4142135623730951},"796":{"tf":1.0},"798":{"tf":1.4142135623730951},"799":{"tf":1.0},"80":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.4142135623730951},"809":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.4142135623730951},"819":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.0},"823":{"tf":1.0},"826":{"tf":1.0},"827":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":1.7320508075688772},"832":{"tf":2.23606797749979},"833":{"tf":1.4142135623730951},"835":{"tf":1.0},"836":{"tf":1.0},"840":{"tf":1.0},"841":{"tf":1.4142135623730951},"842":{"tf":1.0},"843":{"tf":1.7320508075688772},"846":{"tf":1.0},"857":{"tf":1.4142135623730951},"871":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.4142135623730951},"887":{"tf":1.0},"891":{"tf":1.4142135623730951},"907":{"tf":1.0},"908":{"tf":1.4142135623730951},"926":{"tf":1.4142135623730951},"927":{"tf":1.0},"928":{"tf":2.23606797749979},"929":{"tf":1.0},"93":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"933":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"94":{"tf":1.0},"940":{"tf":1.4142135623730951},"941":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.0},"957":{"tf":1.4142135623730951},"958":{"tf":1.0},"961":{"tf":1.0},"97":{"tf":1.0},"974":{"tf":1.4142135623730951},"984":{"tf":1.0},"985":{"tf":1.7320508075688772},"988":{"tf":1.4142135623730951},"989":{"tf":1.0},"991":{"tf":1.0},"994":{"tf":1.0},"996":{"tf":1.0}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"196":{"tf":1.0}}}},"d":{"df":1,"docs":{"872":{"tf":1.0}},"e":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":19,"docs":{"124":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"485":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.4142135623730951},"61":{"tf":1.0},"651":{"tf":1.0},"700":{"tf":1.0},"747":{"tf":1.7320508075688772},"748":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":1.0},"84":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"324":{"tf":1.0},"354":{"tf":1.0},"962":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"347":{"tf":1.4142135623730951}}}}}}},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"341":{"tf":1.0},"346":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":2,"docs":{"341":{"tf":1.0},"347":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"df":5,"docs":{"340":{"tf":1.0},"341":{"tf":2.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"359":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}}},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"341":{"tf":2.0},"346":{"tf":1.0},"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}}},"p":{"df":1,"docs":{"105":{"tf":1.0}}},"s":{"df":0,"docs":{},"e":{"df":2,"docs":{"428":{"tf":1.0},"747":{"tf":1.0}}},"k":{"df":26,"docs":{"121":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"138":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"198":{"tf":1.0},"303":{"tf":1.7320508075688772},"316":{"tf":1.0},"365":{"tf":1.0},"374":{"tf":1.0},"429":{"tf":1.4142135623730951},"58":{"tf":1.0},"583":{"tf":1.0},"605":{"tf":1.0},"69":{"tf":1.0},"720":{"tf":1.0},"752":{"tf":1.0},"83":{"tf":1.0},"849":{"tf":1.4142135623730951},"85":{"tf":1.0},"911":{"tf":1.0},"919":{"tf":1.7320508075688772},"938":{"tf":1.0},"945":{"tf":1.0},"965":{"tf":1.0}}}}},"j":{"df":1,"docs":{"126":{"tf":2.8284271247461903}}},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"714":{"tf":1.0}}}}}},"o":{"a":{"d":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"243":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"b":{"'":{"df":1,"docs":{"724":{"tf":1.0}}},"df":1,"docs":{"244":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"214":{"tf":1.0},"215":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"374":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"376":{"tf":1.0},"628":{"tf":1.0},"720":{"tf":1.0},"773":{"tf":1.0},"956":{"tf":1.0},"961":{"tf":1.0},"964":{"tf":1.0}}}}}},"c":{"df":1,"docs":{"603":{"tf":3.4641016151377544}},"o":{"c":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}}}},"df":9,"docs":{"115":{"tf":1.0},"304":{"tf":1.0},"390":{"tf":1.4142135623730951},"603":{"tf":2.23606797749979},"678":{"tf":1.0},"679":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"819":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"_":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"i":{"d":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":1,"docs":{"93":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":5,"docs":{"1004":{"tf":1.0},"271":{"tf":1.0},"327":{"tf":1.0},"340":{"tf":1.0},"389":{"tf":1.0}}},"l":{"df":1,"docs":{"660":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"195":{"tf":1.0},"209":{"tf":1.4142135623730951}}}}},"u":{"df":0,"docs":{},"p":{"'":{"df":1,"docs":{"44":{"tf":1.0}}},"df":16,"docs":{"38":{"tf":3.3166247903554},"388":{"tf":1.0},"39":{"tf":2.23606797749979},"40":{"tf":2.6457513110645907},"41":{"tf":1.4142135623730951},"42":{"tf":1.4142135623730951},"44":{"tf":2.0},"46":{"tf":2.0},"47":{"tf":1.7320508075688772},"48":{"tf":1.4142135623730951},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":2.449489742783178},"54":{"tf":2.8284271247461903},"55":{"tf":1.7320508075688772}},"’":{"df":1,"docs":{"45":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"526":{"tf":1.0}}},"t":{"/":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"615":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}},"df":39,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0},"300":{"tf":1.7320508075688772},"375":{"tf":1.0},"387":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":1.0},"390":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.23606797749979},"45":{"tf":1.0},"46":{"tf":2.6457513110645907},"49":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":2.23606797749979},"520":{"tf":1.0},"525":{"tf":2.23606797749979},"530":{"tf":1.0},"531":{"tf":1.0},"634":{"tf":1.0},"697":{"tf":2.6457513110645907},"761":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951},"858":{"tf":1.4142135623730951},"859":{"tf":1.0},"860":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"257":{"tf":1.0},"439":{"tf":1.0},"456":{"tf":1.0},"507":{"tf":1.0},"724":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"721":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"204":{"tf":1.0},"335":{"tf":1.0},"435":{"tf":1.0},"438":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"723":{"tf":1.0}}}}}},"n":{"d":{"df":3,"docs":{"374":{"tf":1.0},"723":{"tf":1.0},"758":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":3,"docs":{"374":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"696":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"p":{"c":{"df":5,"docs":{"191":{"tf":1.0},"249":{"tf":1.7320508075688772},"461":{"tf":1.4142135623730951},"50":{"tf":1.0},"512":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":7,"docs":{"347":{"tf":1.0},"6":{"tf":1.7320508075688772},"693":{"tf":1.0},"697":{"tf":2.6457513110645907},"817":{"tf":1.0},"855":{"tf":1.4142135623730951},"876":{"tf":1.0}}}},"n":{"df":27,"docs":{"1004":{"tf":1.0},"160":{"tf":1.0},"171":{"tf":1.0},"203":{"tf":1.0},"233":{"tf":1.0},"234":{"tf":1.4142135623730951},"281":{"tf":1.4142135623730951},"296":{"tf":1.0},"297":{"tf":1.0},"308":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.0},"58":{"tf":1.0},"608":{"tf":1.0},"711":{"tf":1.4142135623730951},"715":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.4142135623730951},"848":{"tf":1.7320508075688772},"849":{"tf":1.4142135623730951},"912":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":160,"docs":{"103":{"tf":1.0},"108":{"tf":1.0},"125":{"tf":1.4142135623730951},"133":{"tf":1.0},"136":{"tf":1.4142135623730951},"137":{"tf":1.4142135623730951},"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"144":{"tf":1.4142135623730951},"145":{"tf":1.0},"147":{"tf":1.4142135623730951},"150":{"tf":1.7320508075688772},"151":{"tf":4.358898943540674},"152":{"tf":1.0},"154":{"tf":3.605551275463989},"155":{"tf":2.6457513110645907},"158":{"tf":1.4142135623730951},"159":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.4142135623730951},"167":{"tf":1.4142135623730951},"17":{"tf":1.0},"170":{"tf":1.4142135623730951},"172":{"tf":1.0},"175":{"tf":1.4142135623730951},"18":{"tf":1.0},"19":{"tf":2.0},"193":{"tf":1.0},"20":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.7320508075688772},"23":{"tf":1.0},"24":{"tf":1.0},"261":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"271":{"tf":1.0},"272":{"tf":1.4142135623730951},"279":{"tf":1.7320508075688772},"280":{"tf":1.0},"282":{"tf":1.4142135623730951},"284":{"tf":2.23606797749979},"289":{"tf":1.0},"293":{"tf":2.0},"311":{"tf":2.0},"313":{"tf":1.7320508075688772},"314":{"tf":1.4142135623730951},"315":{"tf":1.7320508075688772},"316":{"tf":1.4142135623730951},"319":{"tf":1.0},"35":{"tf":1.4142135623730951},"358":{"tf":1.0},"362":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.0},"4":{"tf":1.4142135623730951},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.7320508075688772},"403":{"tf":1.4142135623730951},"404":{"tf":1.4142135623730951},"407":{"tf":1.0},"438":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"454":{"tf":1.0},"455":{"tf":1.4142135623730951},"461":{"tf":1.7320508075688772},"482":{"tf":1.0},"483":{"tf":1.7320508075688772},"511":{"tf":1.0},"514":{"tf":2.0},"516":{"tf":1.0},"518":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"520":{"tf":1.0},"521":{"tf":2.0},"526":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.4142135623730951},"538":{"tf":1.4142135623730951},"56":{"tf":1.0},"57":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.4142135623730951},"587":{"tf":1.4142135623730951},"588":{"tf":1.0},"59":{"tf":1.0},"593":{"tf":1.4142135623730951},"594":{"tf":1.0},"60":{"tf":2.449489742783178},"601":{"tf":1.4142135623730951},"616":{"tf":1.4142135623730951},"627":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.4142135623730951},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"643":{"tf":1.7320508075688772},"652":{"tf":1.4142135623730951},"667":{"tf":1.0},"681":{"tf":1.0},"69":{"tf":1.0},"695":{"tf":1.4142135623730951},"697":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.4142135623730951},"73":{"tf":1.4142135623730951},"730":{"tf":1.7320508075688772},"731":{"tf":1.0},"732":{"tf":2.8284271247461903},"735":{"tf":4.47213595499958},"736":{"tf":1.7320508075688772},"739":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.4142135623730951},"751":{"tf":1.0},"762":{"tf":1.0},"783":{"tf":1.0},"786":{"tf":1.0},"799":{"tf":1.0},"817":{"tf":1.0},"82":{"tf":1.4142135623730951},"827":{"tf":1.0},"828":{"tf":1.0},"829":{"tf":3.0},"830":{"tf":1.0},"831":{"tf":2.6457513110645907},"832":{"tf":2.0},"835":{"tf":1.0},"836":{"tf":1.4142135623730951},"837":{"tf":1.7320508075688772},"840":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0},"880":{"tf":1.7320508075688772},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"933":{"tf":2.23606797749979},"934":{"tf":1.0},"935":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"977":{"tf":1.4142135623730951}},"e":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}},"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"292":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":4,"docs":{"386":{"tf":1.4142135623730951},"387":{"tf":1.4142135623730951},"390":{"tf":2.0},"520":{"tf":1.4142135623730951}}}}}}}}}}},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"147":{"tf":1.0},"19":{"tf":1.0},"24":{"tf":1.0},"333":{"tf":1.0},"50":{"tf":1.0},"668":{"tf":1.0},"831":{"tf":1.0}}}}},"·":{"df":1,"docs":{"346":{"tf":1.0}},"s":{")":{"/":{"(":{"a":{"df":0,"docs":{},"·":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"·":{"df":0,"docs":{},"n":{")":{"/":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"/":{"2":{"1":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"df":1,"docs":{"696":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":7,"docs":{"111":{"tf":1.0},"450":{"tf":1.0},"563":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"644":{"tf":1.0},"815":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"6":{"tf":1.0},"602":{"tf":1.0}}}}}},"k":{"a":{"c":{"df":1,"docs":{"808":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":1,"docs":{"207":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":7,"docs":{"272":{"tf":1.0},"274":{"tf":1.0},"465":{"tf":2.0},"469":{"tf":1.4142135623730951},"470":{"tf":2.449489742783178},"471":{"tf":1.0},"479":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"204":{"tf":1.0}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":28,"docs":{"195":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":4.58257569495584},"205":{"tf":3.0},"207":{"tf":3.3166247903554},"213":{"tf":1.7320508075688772},"222":{"tf":1.0},"263":{"tf":1.0},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"267":{"tf":2.6457513110645907},"741":{"tf":1.7320508075688772},"742":{"tf":1.7320508075688772},"743":{"tf":1.7320508075688772},"744":{"tf":1.4142135623730951},"751":{"tf":1.0},"756":{"tf":1.0},"776":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":2.23606797749979},"914":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.0},"940":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.4142135623730951}}}},"m":{"df":0,"docs":{},"e":{"df":67,"docs":{"169":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.449489742783178},"205":{"tf":2.449489742783178},"206":{"tf":1.0},"207":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"402":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"48":{"tf":1.0},"505":{"tf":1.0},"516":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.4142135623730951},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"55":{"tf":1.0},"598":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":2.0},"605":{"tf":1.0},"619":{"tf":1.0},"62":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"654":{"tf":1.0},"68":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":1.0},"699":{"tf":1.0},"701":{"tf":1.4142135623730951},"705":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"759":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":2.0},"784":{"tf":1.0},"786":{"tf":1.7320508075688772},"80":{"tf":1.0},"81":{"tf":1.7320508075688772},"811":{"tf":1.0},"817":{"tf":1.7320508075688772},"829":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"84":{"tf":1.0},"840":{"tf":1.0},"85":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"95":{"tf":1.4142135623730951},"992":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"46":{"tf":1.0},"51":{"tf":1.0},"571":{"tf":1.0}}}},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"780":{"tf":1.0}}}}}},"n":{"d":{"df":0,"docs":{},"u":{"df":1,"docs":{"627":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":13,"docs":{"322":{"tf":2.23606797749979},"323":{"tf":1.0},"324":{"tf":1.0},"326":{"tf":1.7320508075688772},"328":{"tf":1.0},"335":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.4142135623730951},"356":{"tf":1.0},"358":{"tf":1.0},"359":{"tf":2.0},"363":{"tf":1.0},"721":{"tf":1.0}}},"df":0,"docs":{}}}},"df":1,"docs":{"343":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":3,"docs":{"341":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"a":{"d":{"d":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"d":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{":":{":":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"n":{"df":1,"docs":{"784":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"e":{"df":2,"docs":{"732":{"tf":1.4142135623730951},"996":{"tf":1.0}}}},"w":{"df":1,"docs":{"721":{"tf":1.0}}}},"b":{"df":1,"docs":{"126":{"tf":2.449489742783178}}},"c":{"a":{"df":0,"docs":{},"l":{"a":{"b":{"df":0,"docs":{},"l":{"df":6,"docs":{"230":{"tf":1.0},"231":{"tf":1.0},"42":{"tf":1.0},"427":{"tf":1.4142135623730951},"437":{"tf":1.0},"58":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"1":{"df":1,"docs":{"485":{"tf":1.7320508075688772}}},"3":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"1":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":4,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.23606797749979}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"p":{"df":4,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":2.0}}}}},"df":39,"docs":{"170":{"tf":1.0},"22":{"tf":1.4142135623730951},"231":{"tf":1.4142135623730951},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"333":{"tf":1.4142135623730951},"343":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.7320508075688772},"368":{"tf":1.0},"435":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.0},"455":{"tf":2.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.4142135623730951},"5":{"tf":1.4142135623730951},"52":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"526":{"tf":1.0},"553":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":1.4142135623730951},"568":{"tf":1.0},"571":{"tf":1.0},"588":{"tf":1.0},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.4142135623730951},"711":{"tf":1.0},"735":{"tf":1.4142135623730951},"747":{"tf":1.0},"752":{"tf":1.0}}},"p":{"df":1,"docs":{"912":{"tf":2.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"270":{"tf":1.0}}},"n":{"df":1,"docs":{"191":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":18,"docs":{"138":{"tf":1.0},"142":{"tf":1.4142135623730951},"296":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"346":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.0},"564":{"tf":1.0},"618":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"732":{"tf":1.4142135623730951},"947":{"tf":1.0},"964":{"tf":1.0}}}}}},"df":0,"docs":{}}},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":17,"docs":{"138":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"208":{"tf":1.0},"218":{"tf":1.4142135623730951},"221":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"342":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.4142135623730951},"349":{"tf":1.0},"374":{"tf":1.7320508075688772},"911":{"tf":1.0}},"e":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":1,"docs":{"300":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"m":{"a":{"df":3,"docs":{"208":{"tf":1.0},"553":{"tf":1.0},"761":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":9,"docs":{"177":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":1.0},"570":{"tf":1.0},"575":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"714":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"891":{"tf":1.0},"908":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":16,"docs":{"194":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"24":{"tf":1.0},"326":{"tf":1.0},"340":{"tf":1.0},"40":{"tf":1.0},"523":{"tf":1.0},"740":{"tf":1.0},"743":{"tf":1.0},"776":{"tf":1.0},"840":{"tf":1.0},"849":{"tf":1.0},"855":{"tf":1.0},"928":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"336":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"191":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"k":{"#":{"1":{"7":{"8":{"1":{"df":1,"docs":{"291":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"/":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"/":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"793":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"7":{"9":{"6":{"df":1,"docs":{"824":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"1":{"1":{"df":1,"docs":{"712":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"1":{"6":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"7":{"3":{"3":{"df":1,"docs":{"500":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"6":{"7":{"3":{"df":1,"docs":{"551":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"df":1,"docs":{"990":{"tf":1.0}}},"5":{"1":{"2":{"2":{"df":1,"docs":{"712":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"7":{"1":{"df":1,"docs":{"74":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"2":{"1":{"7":{"7":{"df":1,"docs":{"440":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"7":{"8":{"6":{"df":2,"docs":{"551":{"tf":1.0},"555":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"7":{"2":{"2":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":11,"docs":{"108":{"tf":1.0},"210":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":2.23606797749979},"872":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"888":{"tf":1.0},"933":{"tf":1.0},"969":{"tf":1.0},"973":{"tf":1.0}},"’":{"df":1,"docs":{"515":{"tf":1.0}}}}},"df":4,"docs":{"333":{"tf":2.0},"346":{"tf":2.449489742783178},"735":{"tf":1.0},"94":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"350":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"349":{"tf":2.449489742783178},"350":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"df":3,"docs":{"343":{"tf":1.0},"349":{"tf":2.23606797749979},"350":{"tf":1.0}}},"m":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"439":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"363":{"tf":1.0},"956":{"tf":1.0}}}}}}}}},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"573":{"tf":1.0}}}},"df":0,"docs":{}}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"400":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":21,"docs":{"196":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"252":{"tf":1.0},"267":{"tf":1.0},"349":{"tf":1.7320508075688772},"351":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":2.23606797749979},"773":{"tf":1.0},"776":{"tf":1.4142135623730951},"778":{"tf":1.0},"799":{"tf":1.0},"940":{"tf":1.7320508075688772},"941":{"tf":1.0},"942":{"tf":1.7320508075688772},"943":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"960":{"tf":1.0}}}}},"df":10,"docs":{"284":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.0},"349":{"tf":1.0},"485":{"tf":1.0},"503":{"tf":1.0},"516":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"83":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"204":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"2":{"5":{"6":{"df":0,"docs":{},"k":{"1":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}},"r":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"93":{"tf":1.4142135623730951},"94":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":5,"docs":{"103":{"tf":1.0},"105":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.7320508075688772},"97":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"723":{"tf":1.0}}}},"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"346":{"tf":1.0}}}}}},"df":3,"docs":{"341":{"tf":2.0},"349":{"tf":1.0},"723":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"341":{"tf":2.0}}}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":28,"docs":{"185":{"tf":1.0},"204":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"30":{"tf":1.0},"330":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.0},"344":{"tf":1.0},"351":{"tf":1.0},"446":{"tf":1.0},"470":{"tf":1.0},"485":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.4142135623730951},"521":{"tf":1.0},"524":{"tf":1.0},"64":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"814":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951},"992":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":165,"docs":{"1":{"tf":1.0},"100":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1004":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.4142135623730951},"106":{"tf":1.0},"115":{"tf":1.0},"122":{"tf":1.0},"128":{"tf":1.0},"136":{"tf":1.0},"142":{"tf":1.4142135623730951},"150":{"tf":1.0},"156":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.4142135623730951},"182":{"tf":1.0},"188":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"211":{"tf":1.7320508075688772},"215":{"tf":1.0},"225":{"tf":1.4142135623730951},"229":{"tf":1.0},"231":{"tf":1.7320508075688772},"237":{"tf":1.0},"247":{"tf":1.0},"255":{"tf":1.4142135623730951},"268":{"tf":1.0},"275":{"tf":1.0},"279":{"tf":1.0},"286":{"tf":1.4142135623730951},"294":{"tf":1.0},"30":{"tf":1.7320508075688772},"303":{"tf":1.0},"304":{"tf":1.0},"311":{"tf":1.0},"317":{"tf":1.0},"322":{"tf":1.0},"346":{"tf":1.0},"354":{"tf":1.4142135623730951},"366":{"tf":1.0},"368":{"tf":1.4142135623730951},"378":{"tf":1.0},"38":{"tf":1.7320508075688772},"386":{"tf":1.0},"392":{"tf":1.4142135623730951},"40":{"tf":1.4142135623730951},"41":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"418":{"tf":1.0},"419":{"tf":1.0},"42":{"tf":1.0},"420":{"tf":1.4142135623730951},"430":{"tf":1.0},"44":{"tf":1.0},"442":{"tf":1.4142135623730951},"451":{"tf":1.0},"457":{"tf":1.0},"46":{"tf":1.0},"465":{"tf":1.0},"474":{"tf":1.0},"481":{"tf":1.0},"487":{"tf":1.0},"495":{"tf":1.0},"505":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":2.0},"52":{"tf":1.0},"528":{"tf":1.4142135623730951},"53":{"tf":1.4142135623730951},"535":{"tf":1.0},"541":{"tf":1.4142135623730951},"549":{"tf":1.0},"555":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.7320508075688772},"569":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"578":{"tf":1.0},"584":{"tf":1.0},"590":{"tf":1.4142135623730951},"598":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.7320508075688772},"613":{"tf":1.0},"619":{"tf":1.7320508075688772},"627":{"tf":1.0},"628":{"tf":1.0},"639":{"tf":1.7320508075688772},"649":{"tf":1.0},"656":{"tf":1.4142135623730951},"664":{"tf":1.0},"670":{"tf":1.0},"678":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.4142135623730951},"701":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.4142135623730951},"757":{"tf":1.0},"763":{"tf":1.4142135623730951},"772":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"782":{"tf":1.0},"788":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"801":{"tf":1.0},"808":{"tf":1.0},"819":{"tf":1.0},"827":{"tf":1.0},"83":{"tf":1.0},"833":{"tf":1.0},"841":{"tf":1.0},"85":{"tf":1.4142135623730951},"850":{"tf":1.4142135623730951},"857":{"tf":1.0},"864":{"tf":1.4142135623730951},"871":{"tf":1.0},"874":{"tf":1.0},"883":{"tf":1.0},"891":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.4142135623730951},"908":{"tf":1.0},"917":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.4142135623730951},"935":{"tf":1.0},"940":{"tf":1.4142135623730951},"942":{"tf":1.0},"945":{"tf":1.4142135623730951},"946":{"tf":1.0},"948":{"tf":1.4142135623730951},"95":{"tf":1.7320508075688772},"955":{"tf":1.0},"957":{"tf":1.4142135623730951},"961":{"tf":2.0},"962":{"tf":1.4142135623730951},"963":{"tf":1.0},"965":{"tf":1.7320508075688772},"972":{"tf":1.0},"974":{"tf":1.0},"980":{"tf":1.0},"988":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}}}}},"df":3,"docs":{"1008":{"tf":1.0},"210":{"tf":1.0},"724":{"tf":1.0}},"e":{"d":{"df":6,"docs":{"113":{"tf":1.4142135623730951},"126":{"tf":1.0},"272":{"tf":1.0},"455":{"tf":1.0},"735":{"tf":1.7320508075688772},"85":{"tf":1.4142135623730951}}},"df":37,"docs":{"184":{"tf":1.0},"185":{"tf":1.0},"186":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"277":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.0},"373":{"tf":1.0},"384":{"tf":1.0},"415":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.4142135623730951},"504":{"tf":1.0},"565":{"tf":1.0},"571":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"735":{"tf":1.4142135623730951},"77":{"tf":1.0},"800":{"tf":1.0},"831":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.7320508075688772}},"k":{"df":9,"docs":{"272":{"tf":1.0},"296":{"tf":1.0},"313":{"tf":1.0},"42":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"723":{"tf":1.0},"772":{"tf":1.0},"810":{"tf":1.0}}},"m":{"df":6,"docs":{"697":{"tf":1.0},"724":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":1.4142135623730951},"84":{"tf":1.0}}},"n":{"df":7,"docs":{"135":{"tf":1.0},"450":{"tf":1.0},"520":{"tf":1.0},"58":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"680":{"tf":1.0}}}},"g":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"335":{"tf":1.4142135623730951},"45":{"tf":1.7320508075688772},"776":{"tf":1.0}}}}}}},"l":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"1004":{"tf":1.0},"515":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":12,"docs":{"1003":{"tf":1.4142135623730951},"204":{"tf":1.0},"229":{"tf":1.7320508075688772},"231":{"tf":1.4142135623730951},"232":{"tf":1.4142135623730951},"234":{"tf":2.8284271247461903},"237":{"tf":1.0},"243":{"tf":1.4142135623730951},"246":{"tf":1.0},"565":{"tf":1.0},"633":{"tf":1.4142135623730951},"856":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}},"f":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"24":{"tf":3.3166247903554}}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":10,"docs":{"208":{"tf":1.4142135623730951},"23":{"tf":1.0},"272":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"375":{"tf":1.0},"399":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"722":{"tf":1.0}}},"l":{"df":4,"docs":{"196":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"743":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.7320508075688772}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":8,"docs":{"166":{"tf":1.0},"24":{"tf":1.0},"534":{"tf":1.4142135623730951},"61":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.0},"660":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":3,"docs":{"231":{"tf":1.0},"374":{"tf":1.0},"54":{"tf":1.0}}}},"n":{"d":{"df":31,"docs":{"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"257":{"tf":1.0},"439":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":2.0},"486":{"tf":1.0},"491":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"512":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"594":{"tf":1.0},"62":{"tf":1.0},"641":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":2.0},"763":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"980":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"455":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.0},"521":{"tf":1.0},"994":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"470":{"tf":1.0}}}}},"s":{"df":9,"docs":{"121":{"tf":1.0},"267":{"tf":1.0},"288":{"tf":1.0},"3":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"5":{"tf":1.0},"571":{"tf":1.0},"720":{"tf":1.0}},"i":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"175":{"tf":1.0},"376":{"tf":1.0},"569":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"564":{"tf":1.0},"571":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}},"t":{"df":16,"docs":{"222":{"tf":1.0},"253":{"tf":1.0},"47":{"tf":1.0},"485":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":2.0},"633":{"tf":1.4142135623730951},"701":{"tf":1.0},"715":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.4142135623730951}}}}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":16,"docs":{"163":{"tf":1.0},"203":{"tf":1.0},"254":{"tf":1.0},"28":{"tf":1.0},"314":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"60":{"tf":1.0},"645":{"tf":1.0},"68":{"tf":1.0},"74":{"tf":1.0},"772":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.4142135623730951},"945":{"tf":1.0},"95":{"tf":1.0}}}},"df":1,"docs":{"692":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":3,"docs":{"136":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0}}},"df":0,"docs":{}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":19,"docs":{"126":{"tf":1.0},"332":{"tf":2.449489742783178},"333":{"tf":2.449489742783178},"335":{"tf":1.4142135623730951},"342":{"tf":1.0},"343":{"tf":2.0},"344":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":2.0},"348":{"tf":1.4142135623730951},"349":{"tf":2.0},"350":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.4142135623730951},"522":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}}},"<":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"343":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"<":{"3":{"2":{"df":1,"docs":{"344":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"345":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"t":{",":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":2,"docs":{"332":{"tf":1.4142135623730951},"333":{"tf":1.7320508075688772}},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"347":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"8":{"df":1,"docs":{"332":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"335":{"tf":1.0},"436":{"tf":1.0},"992":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"j":{"df":1,"docs":{"808":{"tf":1.0}}}}},"i":{"a":{"df":0,"docs":{},"l":{"df":5,"docs":{"26":{"tf":1.7320508075688772},"331":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"759":{"tf":1.0}}}},"df":1,"docs":{"124":{"tf":1.0}}},"v":{"df":22,"docs":{"111":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"214":{"tf":1.0},"22":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"340":{"tf":1.0},"375":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":2.449489742783178},"503":{"tf":1.0},"512":{"tf":1.7320508075688772},"63":{"tf":1.4142135623730951},"66":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"765":{"tf":1.0}}}},"i":{"c":{"df":24,"docs":{"198":{"tf":1.0},"206":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.0},"276":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"38":{"tf":2.8284271247461903},"39":{"tf":1.4142135623730951},"40":{"tf":1.7320508075688772},"41":{"tf":1.4142135623730951},"43":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.4142135623730951},"48":{"tf":1.7320508075688772},"50":{"tf":1.4142135623730951},"51":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"54":{"tf":1.7320508075688772},"58":{"tf":1.0},"95":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"38":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":2,"docs":{"634":{"tf":1.4142135623730951},"636":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":21,"docs":{"234":{"tf":1.7320508075688772},"239":{"tf":1.0},"376":{"tf":1.0},"432":{"tf":1.4142135623730951},"452":{"tf":2.8284271247461903},"453":{"tf":2.6457513110645907},"455":{"tf":1.7320508075688772},"456":{"tf":1.0},"459":{"tf":2.0},"461":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"627":{"tf":1.0},"629":{"tf":1.7320508075688772},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.0},"641":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":5,"docs":{"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.4142135623730951},"634":{"tf":1.0},"644":{"tf":1.0}}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":3,"docs":{"451":{"tf":1.7320508075688772},"455":{"tf":2.0},"461":{"tf":1.0}},"s":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"452":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.0}},"s":{"(":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"455":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}}}},"t":{"_":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"300":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":3,"docs":{"665":{"tf":1.4142135623730951},"668":{"tf":1.0},"673":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":76,"docs":{"1004":{"tf":1.7320508075688772},"113":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":1.7320508075688772},"207":{"tf":2.0},"219":{"tf":1.0},"229":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":2.23606797749979},"232":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"235":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"29":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"323":{"tf":1.0},"333":{"tf":1.0},"336":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"368":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"459":{"tf":1.4142135623730951},"46":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.0},"517":{"tf":1.0},"525":{"tf":1.0},"567":{"tf":1.7320508075688772},"569":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"752":{"tf":1.7320508075688772},"774":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.4142135623730951},"842":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.4142135623730951},"895":{"tf":1.4142135623730951},"898":{"tf":1.0},"916":{"tf":1.0},"920":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":3,"docs":{"974":{"tf":1.0},"975":{"tf":1.0},"978":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"665":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"670":{"tf":1.0},"673":{"tf":1.0}},"s":{"(":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"668":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":2,"docs":{"895":{"tf":1.0},"898":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"729":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"776":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":2,"docs":{"773":{"tf":1.0},"776":{"tf":1.4142135623730951}}}}}}}}},"u":{"df":0,"docs":{},"p":{"df":3,"docs":{"113":{"tf":1.0},"26":{"tf":1.0},"364":{"tf":1.4142135623730951}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"199":{"tf":1.0}}},"r":{"df":15,"docs":{"198":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"209":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"35":{"tf":1.0},"361":{"tf":1.0},"367":{"tf":1.0},"426":{"tf":1.0},"483":{"tf":1.0},"724":{"tf":1.0},"81":{"tf":1.0},"962":{"tf":1.0},"990":{"tf":1.0}}}}}},"h":{"a":{"(":{"0":{"df":0,"docs":{},"x":{"a":{"1":{"0":{"df":0,"docs":{},"f":{"1":{"2":{"8":{"7":{"2":{"4":{"4":{"7":{"9":{"5":{"8":{"d":{"5":{"0":{"a":{"a":{"7":{"b":{"9":{"3":{"7":{"b":{"0":{"1":{"0":{"6":{"5":{"6":{"1":{"a":{"5":{"8":{"8":{"df":0,"docs":{},"e":{"0":{"df":0,"docs":{},"e":{"2":{"6":{"2":{"8":{"d":{"3":{"3":{"df":0,"docs":{},"f":{"8":{"1":{"b":{"5":{"3":{"6":{"1":{"b":{"1":{"3":{"d":{"b":{"c":{"df":0,"docs":{},"f":{"8":{"d":{"df":0,"docs":{},"f":{"7":{"0":{"8":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"2":{"5":{"6":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"\"":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"501":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"501":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"255":{"tf":1.0},"505":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"780":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"l":{"df":17,"docs":{"111":{"tf":1.0},"121":{"tf":1.0},"205":{"tf":3.0},"247":{"tf":1.0},"401":{"tf":1.0},"472":{"tf":1.0},"602":{"tf":3.0},"609":{"tf":1.0},"617":{"tf":1.4142135623730951},"693":{"tf":1.4142135623730951},"696":{"tf":1.0},"712":{"tf":1.4142135623730951},"722":{"tf":1.0},"743":{"tf":1.7320508075688772},"75":{"tf":1.0},"751":{"tf":1.0},"755":{"tf":1.0}}}},"p":{"df":0,"docs":{},"e":{"df":5,"docs":{"181":{"tf":1.0},"548":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":14,"docs":{"198":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.7320508075688772},"26":{"tf":1.4142135623730951},"336":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"569":{"tf":1.0},"716":{"tf":1.0},"78":{"tf":1.0},"876":{"tf":1.0},"992":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"846":{"tf":1.0}}}}}},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"1002":{"tf":1.0}},"t":{"a":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"206":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":2,"docs":{"712":{"tf":1.0},"778":{"tf":1.0}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"df":1,"docs":{"1":{"tf":1.0}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"874":{"tf":1.0}}}},"r":{"df":0,"docs":{},"t":{"df":12,"docs":{"206":{"tf":1.0},"208":{"tf":1.0},"310":{"tf":1.0},"356":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0},"729":{"tf":1.0},"762":{"tf":1.0},"778":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"111":{"tf":1.0},"203":{"tf":1.0},"42":{"tf":1.0},"894":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"895":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"934":{"tf":1.0}}}}}}}}},"t":{"df":1,"docs":{"600":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":7,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"679":{"tf":1.0},"7":{"tf":1.0},"850":{"tf":1.0},"853":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"w":{"df":9,"docs":{"152":{"tf":1.0},"444":{"tf":1.0},"526":{"tf":1.0},"564":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.7320508075688772},"729":{"tf":1.4142135623730951},"874":{"tf":1.0}},"n":{"df":3,"docs":{"406":{"tf":1.0},"471":{"tf":1.0},"992":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"744":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"432":{"tf":1.0}}}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"697":{"tf":1.0},"786":{"tf":1.4142135623730951}}}},"d":{"df":0,"docs":{},"e":{"df":36,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"19":{"tf":1.0},"217":{"tf":1.0},"253":{"tf":1.7320508075688772},"304":{"tf":1.0},"315":{"tf":1.0},"354":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.0},"485":{"tf":1.0},"521":{"tf":1.7320508075688772},"526":{"tf":1.0},"602":{"tf":1.4142135623730951},"61":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"701":{"tf":1.4142135623730951},"730":{"tf":1.7320508075688772},"731":{"tf":1.0},"732":{"tf":2.0},"747":{"tf":2.0},"748":{"tf":1.4142135623730951},"749":{"tf":2.449489742783178},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"828":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"831":{"tf":1.0},"835":{"tf":1.0},"837":{"tf":1.0},"983":{"tf":1.0},"994":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"g":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"97":{"tf":1.0}},"m":{"a":{"df":1,"docs":{"855":{"tf":1.0}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"417":{"tf":1.0},"428":{"tf":1.0}}},"df":0,"docs":{}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"516":{"tf":1.0},"517":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"l":{"df":12,"docs":{"322":{"tf":1.0},"343":{"tf":1.4142135623730951},"345":{"tf":1.4142135623730951},"60":{"tf":1.4142135623730951},"633":{"tf":1.0},"644":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.4142135623730951},"786":{"tf":1.0}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"879":{"tf":2.0},"885":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"r":{"df":35,"docs":{"103":{"tf":1.0},"164":{"tf":1.0},"171":{"tf":2.23606797749979},"175":{"tf":1.4142135623730951},"340":{"tf":1.0},"341":{"tf":3.7416573867739413},"343":{"tf":1.0},"346":{"tf":2.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":2.0},"352":{"tf":1.0},"404":{"tf":1.0},"455":{"tf":2.6457513110645907},"459":{"tf":1.0},"513":{"tf":1.0},"521":{"tf":1.0},"530":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"588":{"tf":1.4142135623730951},"629":{"tf":1.0},"632":{"tf":2.23606797749979},"634":{"tf":1.0},"640":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":2.449489742783178},"736":{"tf":1.0},"93":{"tf":1.7320508075688772},"94":{"tf":1.7320508075688772},"95":{"tf":1.0},"97":{"tf":1.7320508075688772}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}}}},"df":36,"docs":{"166":{"tf":1.0},"169":{"tf":1.4142135623730951},"170":{"tf":1.4142135623730951},"171":{"tf":2.449489742783178},"172":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.0},"205":{"tf":2.449489742783178},"340":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"455":{"tf":1.0},"49":{"tf":1.0},"514":{"tf":1.7320508075688772},"516":{"tf":1.7320508075688772},"521":{"tf":3.3166247903554},"526":{"tf":2.449489742783178},"531":{"tf":1.0},"532":{"tf":1.4142135623730951},"537":{"tf":2.0},"539":{"tf":1.0},"545":{"tf":1.0},"550":{"tf":1.0},"553":{"tf":1.0},"555":{"tf":1.0},"567":{"tf":1.4142135623730951},"586":{"tf":1.4142135623730951},"588":{"tf":1.7320508075688772},"589":{"tf":1.0},"63":{"tf":1.4142135623730951},"65":{"tf":1.0},"73":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.4142135623730951},"895":{"tf":1.0},"95":{"tf":2.23606797749979}},"e":{"d":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"696":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}}}}},"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"555":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"341":{"tf":1.0}}},"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}},"df":12,"docs":{"515":{"tf":1.0},"516":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"875":{"tf":1.7320508075688772},"878":{"tf":1.7320508075688772},"879":{"tf":6.4031242374328485},"880":{"tf":2.449489742783178},"881":{"tf":2.23606797749979},"885":{"tf":1.4142135623730951},"889":{"tf":1.0},"890":{"tf":1.0}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"564":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"486":{"tf":1.0},"563":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"928":{"tf":1.0},"973":{"tf":1.0}}}}}}},"df":19,"docs":{"108":{"tf":1.0},"11":{"tf":1.0},"141":{"tf":1.0},"308":{"tf":1.0},"356":{"tf":1.0},"412":{"tf":1.0},"51":{"tf":1.0},"522":{"tf":1.7320508075688772},"537":{"tf":1.0},"55":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"776":{"tf":1.0},"866":{"tf":1.0},"876":{"tf":1.0},"912":{"tf":1.0},"962":{"tf":1.0},"990":{"tf":1.0}}},"df":1,"docs":{"666":{"tf":1.0}}}}}}},"k":{"df":1,"docs":{"244":{"tf":1.0}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":34,"docs":{"111":{"tf":1.7320508075688772},"122":{"tf":1.0},"123":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"204":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"276":{"tf":1.0},"281":{"tf":1.0},"33":{"tf":1.0},"333":{"tf":1.0},"35":{"tf":1.0},"39":{"tf":1.0},"390":{"tf":1.0},"397":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.0},"520":{"tf":1.0},"526":{"tf":1.0},"54":{"tf":1.0},"583":{"tf":1.0},"659":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"831":{"tf":1.0},"855":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.7320508075688772},"913":{"tf":1.0},"932":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"25":{"tf":1.0},"371":{"tf":1.0},"415":{"tf":1.0},"502":{"tf":1.0},"663":{"tf":1.0},"736":{"tf":1.0},"761":{"tf":1.0}}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":16,"docs":{"121":{"tf":1.0},"190":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.4142135623730951},"269":{"tf":1.0},"291":{"tf":1.0},"358":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0},"494":{"tf":1.0},"576":{"tf":2.0},"617":{"tf":1.0},"648":{"tf":1.0},"721":{"tf":1.0},"754":{"tf":1.0},"788":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"22":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"659":{"tf":1.0},"673":{"tf":1.0},"74":{"tf":1.0},"878":{"tf":1.0},"934":{"tf":1.0}}}},"i":{"c":{"df":2,"docs":{"761":{"tf":1.0},"777":{"tf":1.0}}},"df":13,"docs":{"177":{"tf":1.0},"253":{"tf":1.0},"272":{"tf":1.0},"371":{"tf":1.0},"485":{"tf":1.0},"573":{"tf":1.0},"696":{"tf":1.0},"712":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"777":{"tf":1.0}},"f":{"df":2,"docs":{"658":{"tf":1.0},"829":{"tf":1.0}},"i":{"df":11,"docs":{"145":{"tf":1.0},"24":{"tf":1.0},"293":{"tf":1.0},"375":{"tf":1.0},"622":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.0},"83":{"tf":1.4142135623730951},"885":{"tf":1.0},"975":{"tf":1.0},"983":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"571":{"tf":1.4142135623730951},"935":{"tf":1.0}},"t":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"375":{"tf":1.0}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"386":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"l":{"df":40,"docs":{"180":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.4142135623730951},"272":{"tf":1.0},"346":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"48":{"tf":1.0},"517":{"tf":1.0},"519":{"tf":1.0},"522":{"tf":1.0},"571":{"tf":1.0},"599":{"tf":1.4142135623730951},"60":{"tf":1.0},"600":{"tf":2.0},"602":{"tf":2.23606797749979},"603":{"tf":1.0},"605":{"tf":1.7320508075688772},"606":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"668":{"tf":1.0},"673":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"762":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"796":{"tf":1.0},"799":{"tf":2.0},"843":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"7":{"tf":1.0}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":2,"docs":{"615":{"tf":1.0},"912":{"tf":1.0}}},"u":{"a":{"df":0,"docs":{},"t":{"df":16,"docs":{"207":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"348":{"tf":1.0},"375":{"tf":1.0},"497":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"747":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}},"x":{"df":3,"docs":{"198":{"tf":1.0},"199":{"tf":1.0},"778":{"tf":1.0}}},"z":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"469":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":39,"docs":{"204":{"tf":1.0},"207":{"tf":1.4142135623730951},"229":{"tf":1.0},"235":{"tf":1.0},"239":{"tf":1.0},"253":{"tf":1.0},"28":{"tf":1.4142135623730951},"30":{"tf":1.0},"388":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.23606797749979},"404":{"tf":1.7320508075688772},"407":{"tf":1.4142135623730951},"412":{"tf":1.0},"418":{"tf":1.0},"436":{"tf":1.0},"444":{"tf":1.0},"485":{"tf":1.0},"51":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.7320508075688772},"522":{"tf":1.4142135623730951},"564":{"tf":1.0},"60":{"tf":1.0},"710":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":4.898979485566356},"75":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.7320508075688772},"763":{"tf":2.0},"813":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"880":{"tf":1.4142135623730951},"885":{"tf":3.0},"990":{"tf":1.4142135623730951},"996":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":7,"docs":{"286":{"tf":1.0},"644":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":2.23606797749979},"724":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":1.0}},"e":{"df":1,"docs":{"723":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"761":{"tf":2.0}}}}},"df":0,"docs":{}}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"b":{"df":0,"docs":{},"l":{"df":10,"docs":{"567":{"tf":1.0},"569":{"tf":1.0},"863":{"tf":1.0},"908":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":1.4142135623730951},"916":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.4142135623730951},"920":{"tf":1.0}}}},"df":0,"docs":{}},"df":10,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"453":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"569":{"tf":1.0},"573":{"tf":4.358898943540674},"644":{"tf":1.0},"863":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"df":3,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"574":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"144":{"tf":1.0},"776":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"456":{"tf":1.0},"515":{"tf":1.0},"622":{"tf":1.0},"687":{"tf":1.0},"739":{"tf":1.0},"752":{"tf":1.0},"777":{"tf":1.0}}}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":2,"docs":{"749":{"tf":1.0},"751":{"tf":1.0}}}},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"348":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":26,"docs":{"198":{"tf":1.7320508075688772},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.7320508075688772},"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":2.0},"323":{"tf":1.7320508075688772},"335":{"tf":1.7320508075688772},"338":{"tf":1.4142135623730951},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":1.4142135623730951},"346":{"tf":2.0},"347":{"tf":1.4142135623730951},"348":{"tf":3.3166247903554},"349":{"tf":4.123105625617661},"350":{"tf":1.4142135623730951},"351":{"tf":1.7320508075688772},"928":{"tf":1.0}}},"w":{"df":4,"docs":{"274":{"tf":1.0},"711":{"tf":1.0},"729":{"tf":1.0},"744":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"739":{"tf":1.4142135623730951},"765":{"tf":1.0},"858":{"tf":1.0},"990":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"660":{"tf":1.0},"751":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":16,"docs":{"182":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.7320508075688772},"186":{"tf":1.7320508075688772},"199":{"tf":1.0},"201":{"tf":1.0},"253":{"tf":1.0},"436":{"tf":1.0},"486":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"554":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"208":{"tf":1.0},"46":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"817":{"tf":1.0},"885":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"t":{"df":19,"docs":{"39":{"tf":1.0},"44":{"tf":1.0},"697":{"tf":1.0},"78":{"tf":2.0},"874":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":1.7320508075688772},"958":{"tf":1.0},"959":{"tf":1.7320508075688772},"961":{"tf":2.6457513110645907},"962":{"tf":1.7320508075688772},"964":{"tf":1.0},"965":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"971":{"tf":1.7320508075688772},"972":{"tf":1.7320508075688772},"973":{"tf":2.0}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":3,"docs":{"363":{"tf":1.0},"644":{"tf":1.0},"73":{"tf":1.0}}}}}}},"n":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":5,"docs":{"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"k":{"df":4,"docs":{"322":{"tf":1.0},"340":{"tf":1.0},"347":{"tf":1.0},"364":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"1004":{"tf":1.0}}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"p":{"df":3,"docs":{"6":{"tf":1.0},"668":{"tf":1.4142135623730951},"814":{"tf":1.7320508075688772}},"e":{"df":3,"docs":{"127":{"tf":1.0},"184":{"tf":1.0},"187":{"tf":1.4142135623730951}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"333":{"tf":1.0},"933":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"w":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"g":{"df":2,"docs":{"697":{"tf":1.0},"699":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"o":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"201":{"tf":1.4142135623730951},"219":{"tf":1.0},"230":{"tf":1.0},"844":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"855":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"df":4,"docs":{"209":{"tf":1.4142135623730951},"210":{"tf":1.0},"514":{"tf":1.0},"895":{"tf":2.23606797749979}}}},"df":0,"docs":{}}}},"l":{"d":{"df":17,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"213":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":1.0},"748":{"tf":1.7320508075688772},"749":{"tf":1.7320508075688772},"751":{"tf":2.0},"776":{"tf":1.0},"778":{"tf":1.0},"912":{"tf":1.0},"944":{"tf":1.4142135623730951}}},"df":0,"docs":{},"e":{"df":3,"docs":{"221":{"tf":1.0},"46":{"tf":1.0},"564":{"tf":1.0}}},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"201":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.0}}}}},"d":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"871":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"444":{"tf":1.4142135623730951}}}}}},"u":{"df":0,"docs":{},"t":{"df":50,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"147":{"tf":1.0},"149":{"tf":1.0},"161":{"tf":1.0},"200":{"tf":2.6457513110645907},"207":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"254":{"tf":1.0},"310":{"tf":1.0},"402":{"tf":1.0},"515":{"tf":1.0},"518":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.4142135623730951},"54":{"tf":1.0},"573":{"tf":1.7320508075688772},"575":{"tf":1.0},"583":{"tf":1.4142135623730951},"68":{"tf":1.4142135623730951},"721":{"tf":1.0},"724":{"tf":1.0},"744":{"tf":2.23606797749979},"75":{"tf":1.0},"754":{"tf":1.0},"80":{"tf":1.0},"809":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":2.6457513110645907},"813":{"tf":1.4142135623730951},"826":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.4142135623730951},"843":{"tf":1.4142135623730951},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"85":{"tf":1.0},"874":{"tf":1.0},"88":{"tf":1.0},"891":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"902":{"tf":1.0},"908":{"tf":1.0},"913":{"tf":1.7320508075688772},"919":{"tf":1.0},"934":{"tf":1.4142135623730951},"956":{"tf":1.0}}}},"v":{"df":15,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"163":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"450":{"tf":1.4142135623730951},"452":{"tf":1.0},"497":{"tf":1.0},"512":{"tf":1.0},"528":{"tf":1.0},"573":{"tf":1.0},"629":{"tf":1.0},"757":{"tf":1.0},"762":{"tf":1.0},"77":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"x":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"526":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"df":1,"docs":{"208":{"tf":1.0}}},"4":{"9":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"208":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"121":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":8,"docs":{"273":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"469":{"tf":1.0},"619":{"tf":1.0},"701":{"tf":1.0},"858":{"tf":1.0},"881":{"tf":1.0},"894":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":11,"docs":{"151":{"tf":1.0},"184":{"tf":1.0},"193":{"tf":1.0},"390":{"tf":1.0},"441":{"tf":1.0},"512":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0},"870":{"tf":1.0}}},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}}}},"w":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.0}}}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"n":{"df":6,"docs":{"204":{"tf":1.0},"221":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"837":{"tf":1.0},"928":{"tf":1.0},"984":{"tf":1.0}}}},"p":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"46":{"tf":1.0},"959":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"t":{"df":7,"docs":{"234":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"524":{"tf":1.4142135623730951},"525":{"tf":2.0},"551":{"tf":1.0},"633":{"tf":1.0},"874":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"234":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"711":{"tf":1.0},"712":{"tf":1.0},"850":{"tf":1.0},"852":{"tf":1.0}}},"df":0,"docs":{}},"r":{"a":{"b":{"df":0,"docs":{},"h":{"df":1,"docs":{"38":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":82,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"24":{"tf":1.4142135623730951},"247":{"tf":1.0},"263":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"30":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"366":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":2.449489742783178},"697":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.7320508075688772},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"895":{"tf":1.4142135623730951},"908":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"932":{"tf":2.0},"938":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"3":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0}}}}}}}}}},"p":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"a":{"c":{"df":0,"docs":{},"e":{"df":8,"docs":{"196":{"tf":1.0},"515":{"tf":1.0},"627":{"tf":1.0},"632":{"tf":1.0},"638":{"tf":1.0},"648":{"tf":1.0},"71":{"tf":1.0},"831":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":5,"docs":{"411":{"tf":1.0},"420":{"tf":1.0},"429":{"tf":1.0},"863":{"tf":1.0},"913":{"tf":1.0}}},"n":{"df":6,"docs":{"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"843":{"tf":1.0}}},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"843":{"tf":1.0}}}},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"83":{"tf":1.0},"84":{"tf":2.0},"85":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"198":{"tf":1.0},"435":{"tf":1.0}}}},"c":{"_":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"390":{"tf":1.0},"520":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"390":{"tf":1.0},"520":{"tf":2.0}}}}}}},"df":9,"docs":{"436":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"711":{"tf":1.7320508075688772},"841":{"tf":1.0},"847":{"tf":1.4142135623730951},"848":{"tf":1.0},"983":{"tf":1.0}},"e":{"df":1,"docs":{"711":{"tf":1.0}}},"i":{"a":{"df":0,"docs":{},"l":{"df":8,"docs":{"154":{"tf":1.0},"249":{"tf":1.4142135623730951},"272":{"tf":1.0},"346":{"tf":1.0},"522":{"tf":1.4142135623730951},"780":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":3,"docs":{"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"216":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"df":73,"docs":{"1014":{"tf":1.0},"126":{"tf":1.0},"164":{"tf":1.0},"165":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"18":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.0},"221":{"tf":1.4142135623730951},"224":{"tf":1.0},"249":{"tf":2.449489742783178},"251":{"tf":1.0},"252":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"262":{"tf":1.0},"3":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"337":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.4142135623730951},"343":{"tf":1.0},"357":{"tf":1.0},"359":{"tf":1.0},"371":{"tf":1.0},"390":{"tf":1.0},"398":{"tf":1.0},"416":{"tf":1.0},"429":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.4142135623730951},"496":{"tf":1.0},"497":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"542":{"tf":1.0},"553":{"tf":1.4142135623730951},"568":{"tf":1.0},"576":{"tf":1.0},"586":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"627":{"tf":1.0},"651":{"tf":1.4142135623730951},"665":{"tf":1.0},"666":{"tf":1.0},"697":{"tf":1.4142135623730951},"727":{"tf":1.0},"759":{"tf":1.4142135623730951},"762":{"tf":1.4142135623730951},"818":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"85":{"tf":1.7320508075688772},"972":{"tf":1.0},"991":{"tf":1.0}},"i":{"df":32,"docs":{"170":{"tf":1.0},"171":{"tf":1.0},"180":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":2.6457513110645907},"212":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"345":{"tf":1.0},"350":{"tf":1.0},"470":{"tf":1.0},"5":{"tf":1.4142135623730951},"52":{"tf":1.0},"553":{"tf":1.0},"560":{"tf":1.0},"6":{"tf":1.7320508075688772},"602":{"tf":2.8284271247461903},"651":{"tf":1.0},"666":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.7320508075688772},"673":{"tf":1.0},"680":{"tf":1.0},"683":{"tf":1.0},"698":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951},"814":{"tf":1.0},"831":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"y":{"/":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"k":{"df":1,"docs":{"711":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"470":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"d":{"df":3,"docs":{"54":{"tf":1.0},"553":{"tf":1.0},"739":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"n":{"d":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"205":{"tf":1.0}}}},"df":0,"docs":{}},"df":6,"docs":{"184":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"273":{"tf":1.0},"375":{"tf":1.0},"720":{"tf":1.0},"81":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"184":{"tf":2.23606797749979}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"615":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":3,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"571":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":9,"docs":{"203":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.4142135623730951},"217":{"tf":1.0},"281":{"tf":1.0},"374":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":1,"docs":{"28":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"df":2,"docs":{"537":{"tf":1.0},"869":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"240":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"j":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"111":{"tf":1.0}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"777":{"tf":1.0}}}}}}},"r":{"df":3,"docs":{"244":{"tf":1.0},"347":{"tf":1.0},"364":{"tf":1.4142135623730951}}},"s":{"5":{"8":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}}},"df":1,"docs":{"520":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":7,"docs":{"267":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.0},"470":{"tf":1.4142135623730951},"473":{"tf":1.0},"564":{"tf":1.0},"687":{"tf":1.0}}}},"l":{"df":5,"docs":{"204":{"tf":1.0},"249":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"72":{"tf":1.0}},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"234":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"k":{"df":9,"docs":{"254":{"tf":1.7320508075688772},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"50":{"tf":1.0},"54":{"tf":1.0},"575":{"tf":1.0},"732":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":5,"docs":{"201":{"tf":1.0},"309":{"tf":1.0},"376":{"tf":1.0},"815":{"tf":1.7320508075688772},"906":{"tf":1.0}}}},"k":{"df":0,"docs":{},"e":{"df":37,"docs":{"1002":{"tf":1.0},"1003":{"tf":1.0},"1004":{"tf":1.0},"231":{"tf":2.23606797749979},"244":{"tf":1.0},"370":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.7320508075688772},"373":{"tf":2.23606797749979},"375":{"tf":4.0},"376":{"tf":1.4142135623730951},"377":{"tf":1.0},"383":{"tf":1.0},"384":{"tf":1.4142135623730951},"385":{"tf":1.0},"563":{"tf":1.7320508075688772},"564":{"tf":2.0},"565":{"tf":2.6457513110645907},"567":{"tf":2.23606797749979},"568":{"tf":2.0},"569":{"tf":1.7320508075688772},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"575":{"tf":1.7320508075688772},"576":{"tf":1.7320508075688772},"577":{"tf":1.7320508075688772},"797":{"tf":1.4142135623730951},"927":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":2.0},"932":{"tf":3.4641016151377544},"933":{"tf":1.7320508075688772},"934":{"tf":2.0},"936":{"tf":1.0}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":127,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1005":{"tf":1.4142135623730951},"106":{"tf":1.0},"109":{"tf":1.0},"122":{"tf":1.0},"125":{"tf":1.0},"136":{"tf":1.0},"139":{"tf":1.4142135623730951},"150":{"tf":1.0},"153":{"tf":1.0},"164":{"tf":1.0},"167":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"185":{"tf":1.4142135623730951},"195":{"tf":1.0},"20":{"tf":1.0},"201":{"tf":1.7320508075688772},"209":{"tf":1.0},"215":{"tf":1.0},"219":{"tf":1.4142135623730951},"229":{"tf":1.0},"233":{"tf":1.0},"247":{"tf":1.0},"250":{"tf":1.0},"263":{"tf":1.0},"266":{"tf":1.0},"268":{"tf":1.0},"271":{"tf":1.4142135623730951},"279":{"tf":1.0},"282":{"tf":1.0},"294":{"tf":1.0},"298":{"tf":1.0},"311":{"tf":1.0},"314":{"tf":1.0},"322":{"tf":1.0},"327":{"tf":1.0},"366":{"tf":1.0},"369":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"389":{"tf":1.0},"4":{"tf":1.0},"400":{"tf":1.0},"403":{"tf":1.0},"410":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.4142135623730951},"42":{"tf":1.0},"430":{"tf":1.0},"433":{"tf":1.0},"451":{"tf":1.0},"454":{"tf":1.0},"465":{"tf":1.0},"468":{"tf":1.0},"481":{"tf":1.0},"484":{"tf":1.0},"495":{"tf":1.0},"498":{"tf":1.0},"513":{"tf":1.0},"518":{"tf":1.0},"535":{"tf":1.0},"538":{"tf":1.0},"549":{"tf":1.0},"552":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"566":{"tf":1.0},"584":{"tf":1.0},"587":{"tf":1.0},"59":{"tf":1.0},"598":{"tf":1.0},"601":{"tf":1.0},"613":{"tf":1.0},"616":{"tf":1.0},"627":{"tf":1.0},"630":{"tf":1.0},"649":{"tf":1.0},"652":{"tf":1.0},"664":{"tf":1.0},"667":{"tf":1.0},"678":{"tf":1.0},"681":{"tf":1.0},"692":{"tf":1.0},"695":{"tf":1.0},"709":{"tf":1.0},"712":{"tf":1.0},"730":{"tf":1.0},"733":{"tf":1.4142135623730951},"741":{"tf":1.0},"745":{"tf":1.4142135623730951},"757":{"tf":1.0},"760":{"tf":1.0},"771":{"tf":1.0},"774":{"tf":1.4142135623730951},"782":{"tf":1.0},"785":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"798":{"tf":1.4142135623730951},"808":{"tf":1.0},"812":{"tf":1.0},"82":{"tf":1.0},"827":{"tf":1.0},"830":{"tf":1.0},"841":{"tf":1.0},"844":{"tf":1.0},"871":{"tf":1.0},"877":{"tf":1.0},"891":{"tf":1.0},"897":{"tf":1.0},"908":{"tf":1.0},"914":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.4142135623730951},"93":{"tf":1.0},"940":{"tf":1.0},"943":{"tf":1.4142135623730951},"957":{"tf":1.0},"96":{"tf":1.0},"960":{"tf":1.4142135623730951},"974":{"tf":1.0},"977":{"tf":1.0},"988":{"tf":1.0},"991":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"df":3,"docs":{"573":{"tf":2.0},"929":{"tf":1.0},"932":{"tf":1.4142135623730951}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"e":{"df":2,"docs":{"1002":{"tf":1.7320508075688772},"1003":{"tf":1.4142135623730951}}},"l":{"df":2,"docs":{"118":{"tf":1.0},"438":{"tf":1.0}}}},"n":{"d":{"a":{"df":0,"docs":{},"r":{"d":{"df":17,"docs":{"12":{"tf":1.0},"147":{"tf":1.0},"220":{"tf":1.0},"225":{"tf":1.0},"24":{"tf":1.0},"3":{"tf":1.4142135623730951},"331":{"tf":1.0},"333":{"tf":1.0},"378":{"tf":1.0},"415":{"tf":1.0},"418":{"tf":1.0},"532":{"tf":1.0},"639":{"tf":1.0},"651":{"tf":1.4142135623730951},"883":{"tf":1.0},"931":{"tf":1.0},"95":{"tf":2.0}}},"df":0,"docs":{}}},"df":3,"docs":{"414":{"tf":1.0},"931":{"tf":1.0},"939":{"tf":1.0}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"269":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":2,"docs":{"879":{"tf":1.4142135623730951},"885":{"tf":1.0}}}}}}}}},"df":102,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"126":{"tf":1.7320508075688772},"132":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.4142135623730951},"182":{"tf":1.0},"195":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"215":{"tf":1.0},"221":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"263":{"tf":1.0},"265":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"303":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"346":{"tf":1.4142135623730951},"349":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"430":{"tf":1.0},"440":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"495":{"tf":1.0},"500":{"tf":1.0},"513":{"tf":1.0},"52":{"tf":1.0},"520":{"tf":1.0},"523":{"tf":1.0},"535":{"tf":1.0},"54":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"567":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"605":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"63":{"tf":1.7320508075688772},"633":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"73":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":2.23606797749979},"741":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":1.4142135623730951},"857":{"tf":1.0},"863":{"tf":1.0},"871":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":1.7320508075688772},"889":{"tf":1.0},"891":{"tf":1.0},"902":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0},"992":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":3,"docs":{"345":{"tf":1.0},"553":{"tf":1.0},"809":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"565":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"108":{"tf":1.0}}}}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":4,"docs":{"391":{"tf":1.0},"393":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951}}}}}}},"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"126":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":79,"docs":{"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":2.8284271247461903},"151":{"tf":3.1622776601683795},"152":{"tf":1.7320508075688772},"154":{"tf":2.23606797749979},"155":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"30":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"362":{"tf":1.0},"368":{"tf":2.449489742783178},"371":{"tf":1.4142135623730951},"375":{"tf":2.0},"376":{"tf":1.0},"386":{"tf":1.0},"387":{"tf":1.4142135623730951},"388":{"tf":1.0},"39":{"tf":1.4142135623730951},"390":{"tf":2.23606797749979},"402":{"tf":1.4142135623730951},"418":{"tf":2.0},"420":{"tf":1.0},"422":{"tf":1.4142135623730951},"44":{"tf":2.449489742783178},"440":{"tf":1.0},"45":{"tf":1.7320508075688772},"46":{"tf":3.7416573867739413},"466":{"tf":1.0},"47":{"tf":1.0},"479":{"tf":1.0},"49":{"tf":2.0},"500":{"tf":1.0},"501":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.0},"54":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.0},"6":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":1.0},"770":{"tf":1.0},"773":{"tf":1.4142135623730951},"786":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0},"847":{"tf":1.0},"871":{"tf":1.7320508075688772},"872":{"tf":1.4142135623730951},"874":{"tf":1.0},"875":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"879":{"tf":1.7320508075688772},"881":{"tf":1.0},"885":{"tf":3.872983346207417},"886":{"tf":1.0},"919":{"tf":1.0},"935":{"tf":1.0},"988":{"tf":2.449489742783178},"989":{"tf":1.4142135623730951},"990":{"tf":2.23606797749979},"991":{"tf":1.0},"992":{"tf":1.0},"994":{"tf":1.0},"996":{"tf":1.7320508075688772}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"885":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"885":{"tf":2.6457513110645907}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"450":{"tf":1.0},"58":{"tf":1.0},"71":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"786":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"721":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"s":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"386":{"tf":1.4142135623730951},"390":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"v":{"0":{"df":1,"docs":{"388":{"tf":1.4142135623730951}}},"1":{"df":2,"docs":{"387":{"tf":1.0},"388":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"i":{"c":{"df":5,"docs":{"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"146":{"tf":1.0},"783":{"tf":1.0},"786":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"134":{"tf":1.0},"571":{"tf":1.0},"724":{"tf":1.0}}}}},"u":{"df":10,"docs":{"126":{"tf":1.4142135623730951},"127":{"tf":1.4142135623730951},"134":{"tf":1.0},"203":{"tf":1.0},"294":{"tf":1.0},"300":{"tf":1.0},"735":{"tf":1.0},"816":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0}}}},"y":{"df":3,"docs":{"204":{"tf":1.0},"375":{"tf":1.0},"748":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"267":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"841":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":5,"docs":{"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951},"751":{"tf":1.0}}}},"m":{"df":1,"docs":{"422":{"tf":1.0}}},"p":{"df":27,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0},"171":{"tf":1.7320508075688772},"26":{"tf":1.0},"274":{"tf":1.0},"339":{"tf":1.0},"347":{"tf":1.0},"385":{"tf":1.0},"417":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":2.449489742783178},"483":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.0},"519":{"tf":1.0},"524":{"tf":1.4142135623730951},"525":{"tf":1.0},"564":{"tf":1.0},"60":{"tf":1.0},"643":{"tf":1.0},"694":{"tf":1.0},"799":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.7320508075688772},"983":{"tf":1.0}}},"w":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"563":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"723":{"tf":1.7320508075688772}},"f":{"df":3,"docs":{"718":{"tf":1.4142135623730951},"723":{"tf":1.0},"724":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":50,"docs":{"112":{"tf":1.0},"126":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"178":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"290":{"tf":1.0},"296":{"tf":1.0},"315":{"tf":1.4142135623730951},"35":{"tf":1.0},"372":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":1.4142135623730951},"501":{"tf":1.0},"503":{"tf":1.0},"564":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"57":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"586":{"tf":1.0},"594":{"tf":1.0},"71":{"tf":1.0},"712":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0},"773":{"tf":1.7320508075688772},"778":{"tf":1.0},"78":{"tf":1.0},"794":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"863":{"tf":1.4142135623730951},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.7320508075688772},"885":{"tf":1.0},"932":{"tf":1.4142135623730951},"934":{"tf":1.0},"984":{"tf":1.0}}}},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"987":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":10,"docs":{"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.0},"160":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0},"602":{"tf":1.0},"735":{"tf":3.4641016151377544}}},"r":{"a":{"df":0,"docs":{},"g":{"df":62,"docs":{"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"141":{"tf":1.0},"144":{"tf":1.0},"146":{"tf":1.0},"150":{"tf":1.4142135623730951},"151":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"19":{"tf":1.0},"205":{"tf":1.7320508075688772},"249":{"tf":1.4142135623730951},"28":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"362":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.4142135623730951},"387":{"tf":1.4142135623730951},"390":{"tf":2.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.6457513110645907},"404":{"tf":1.4142135623730951},"412":{"tf":1.4142135623730951},"415":{"tf":1.0},"416":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"44":{"tf":1.4142135623730951},"46":{"tf":2.449489742783178},"47":{"tf":2.23606797749979},"48":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"51":{"tf":2.23606797749979},"519":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"54":{"tf":1.0},"56":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.4142135623730951},"75":{"tf":1.7320508075688772},"757":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":2.449489742783178},"761":{"tf":2.23606797749979},"762":{"tf":1.7320508075688772},"777":{"tf":1.0},"78":{"tf":1.7320508075688772},"803":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.4142135623730951},"826":{"tf":1.0},"829":{"tf":1.4142135623730951},"831":{"tf":1.0},"832":{"tf":1.0},"880":{"tf":1.4142135623730951},"936":{"tf":1.0},"944":{"tf":1.4142135623730951},"951":{"tf":1.0},"961":{"tf":1.4142135623730951},"992":{"tf":1.7320508075688772}},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"871":{"tf":1.0},"880":{"tf":1.0}}}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":2,"docs":{"400":{"tf":1.4142135623730951},"401":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"<":{"_":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":41,"docs":{"126":{"tf":1.0},"140":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"151":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"247":{"tf":1.4142135623730951},"249":{"tf":1.0},"255":{"tf":1.0},"39":{"tf":1.0},"412":{"tf":1.0},"439":{"tf":1.0},"47":{"tf":1.0},"497":{"tf":1.7320508075688772},"505":{"tf":1.0},"522":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"568":{"tf":1.7320508075688772},"570":{"tf":1.4142135623730951},"573":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.4142135623730951},"68":{"tf":1.0},"75":{"tf":1.4142135623730951},"759":{"tf":1.0},"78":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.7320508075688772},"815":{"tf":1.7320508075688772},"816":{"tf":1.0},"817":{"tf":1.7320508075688772},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"880":{"tf":1.7320508075688772},"881":{"tf":1.0},"885":{"tf":1.4142135623730951},"895":{"tf":1.0},"932":{"tf":1.0}}},"i":{"df":1,"docs":{"308":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":6,"docs":{"483":{"tf":1.0},"61":{"tf":1.0},"749":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":3,"docs":{"156":{"tf":1.0},"942":{"tf":1.0},"994":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"n":{"df":1,"docs":{"418":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":18,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"272":{"tf":1.0},"28":{"tf":1.0},"322":{"tf":1.0},"326":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.4142135623730951},"358":{"tf":1.0},"363":{"tf":1.4142135623730951},"422":{"tf":1.0},"44":{"tf":1.0},"609":{"tf":1.0},"68":{"tf":1.0},"709":{"tf":1.0},"718":{"tf":1.7320508075688772},"723":{"tf":1.4142135623730951},"777":{"tf":1.0}}}}}}},"df":2,"docs":{"23":{"tf":1.0},"522":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"762":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"145":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.0}}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"773":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"121":{"tf":1.0},"778":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"432":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"239":{"tf":1.0},"30":{"tf":1.0},"368":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"697":{"tf":1.0},"73":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":11,"docs":{"169":{"tf":1.0},"200":{"tf":1.0},"254":{"tf":1.4142135623730951},"276":{"tf":1.0},"528":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"831":{"tf":1.0},"835":{"tf":1.0}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":8,"docs":{"253":{"tf":1.0},"332":{"tf":1.4142135623730951},"333":{"tf":1.4142135623730951},"343":{"tf":1.0},"364":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.0}}}},"p":{"df":1,"docs":{"517":{"tf":1.4142135623730951}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"199":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"516":{"tf":1.0},"615":{"tf":1.0},"818":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"807":{"tf":1.0},"831":{"tf":1.0}}}}}}},"u":{"c":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"332":{"tf":1.0}}}}}}},"df":18,"docs":{"208":{"tf":2.23606797749979},"24":{"tf":1.4142135623730951},"253":{"tf":1.0},"439":{"tf":1.7320508075688772},"440":{"tf":1.0},"455":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":2.6457513110645907},"6":{"tf":1.0},"62":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.4142135623730951},"761":{"tf":1.0},"83":{"tf":1.0},"880":{"tf":1.4142135623730951},"898":{"tf":1.4142135623730951}},"u":{"df":0,"docs":{},"r":{"df":17,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"142":{"tf":1.0},"17":{"tf":1.0},"25":{"tf":1.4142135623730951},"28":{"tf":1.0},"313":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":1.7320508075688772},"343":{"tf":1.0},"364":{"tf":1.0},"5":{"tf":1.0},"522":{"tf":1.4142135623730951},"628":{"tf":1.0},"654":{"tf":1.0},"780":{"tf":1.0},"961":{"tf":1.0}}}}}},"df":0,"docs":{}}},"u":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"333":{"tf":1.0}}}}}},"u":{"b":{"0":{"df":1,"docs":{"807":{"tf":1.0}}},"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}}}},"df":6,"docs":{"203":{"tf":1.0},"372":{"tf":1.0},"382":{"tf":1.0},"416":{"tf":1.0},"483":{"tf":1.0},"522":{"tf":1.0}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"214":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"358":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"722":{"tf":1.0},"911":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":7,"docs":{"126":{"tf":1.4142135623730951},"322":{"tf":1.7320508075688772},"336":{"tf":1.0},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"365":{"tf":1.0},"39":{"tf":1.0}}}},"t":{"df":20,"docs":{"1013":{"tf":1.0},"112":{"tf":1.4142135623730951},"184":{"tf":1.0},"185":{"tf":1.0},"187":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"365":{"tf":1.0},"375":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.0},"453":{"tf":1.0},"51":{"tf":1.0},"573":{"tf":1.0},"60":{"tf":1.0},"721":{"tf":1.0},"776":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0}}}}},"s":{"c":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"633":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":9,"docs":{"345":{"tf":1.0},"365":{"tf":1.0},"407":{"tf":1.0},"45":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"984":{"tf":1.0}}}},"t":{"df":10,"docs":{"231":{"tf":1.7320508075688772},"232":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.0},"338":{"tf":1.0},"368":{"tf":1.0},"46":{"tf":1.0},"517":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951}}}},"i":{"d":{"df":1,"docs":{"416":{"tf":1.0}},"i":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":1,"docs":{"417":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"p":{"a":{"c":{"df":1,"docs":{"388":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"388":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"191":{"tf":1.0},"804":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":5,"docs":{"199":{"tf":1.0},"201":{"tf":1.0},"563":{"tf":1.0},"732":{"tf":1.0},"826":{"tf":1.0}}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":13,"docs":{"19":{"tf":1.0},"251":{"tf":2.0},"282":{"tf":1.0},"464":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"500":{"tf":1.7320508075688772},"721":{"tf":1.0},"737":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"991":{"tf":1.4142135623730951}},"e":{"#":{"1":{"4":{"2":{"7":{"5":{"df":1,"docs":{"291":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"198":{"tf":1.0}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"933":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"253":{"tf":1.0},"482":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":13,"docs":{"367":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.7320508075688772},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.4142135623730951},"377":{"tf":1.0},"381":{"tf":1.0},"450":{"tf":1.0},"711":{"tf":1.0},"815":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"230":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"l":{"df":1,"docs":{"720":{"tf":1.0}},"i":{"df":1,"docs":{"776":{"tf":1.0}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"c":{"df":0,"docs":{},"e":{"df":4,"docs":{"60":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"832":{"tf":1.0}},"e":{"d":{"df":2,"docs":{"63":{"tf":1.0},"64":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"df":14,"docs":{"205":{"tf":1.0},"223":{"tf":1.4142135623730951},"267":{"tf":1.0},"293":{"tf":1.0},"341":{"tf":1.4142135623730951},"350":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"575":{"tf":1.0},"609":{"tf":1.0},"735":{"tf":3.1622776601683795},"776":{"tf":1.0},"843":{"tf":1.0},"947":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"205":{"tf":1.0},"295":{"tf":1.0},"297":{"tf":1.0},"301":{"tf":1.4142135623730951},"45":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"817":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"h":{"df":68,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"124":{"tf":1.4142135623730951},"169":{"tf":1.0},"19":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"231":{"tf":1.4142135623730951},"249":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.4142135623730951},"267":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":1.7320508075688772},"303":{"tf":1.0},"348":{"tf":1.0},"356":{"tf":1.0},"373":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"449":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"5":{"tf":1.0},"518":{"tf":1.0},"537":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"573":{"tf":1.0},"609":{"tf":1.0},"696":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"765":{"tf":1.0},"778":{"tf":1.0},"784":{"tf":1.0},"804":{"tf":1.4142135623730951},"809":{"tf":1.0},"818":{"tf":1.0},"833":{"tf":1.0},"835":{"tf":1.0},"846":{"tf":1.4142135623730951},"872":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.4142135623730951},"934":{"tf":1.0},"939":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951},"968":{"tf":1.0},"973":{"tf":1.0},"976":{"tf":1.0},"990":{"tf":1.0}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":4,"docs":{"257":{"tf":1.0},"417":{"tf":1.0},"507":{"tf":1.0},"752":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":3,"docs":{"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"724":{"tf":1.0},"759":{"tf":1.0},"928":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":11,"docs":{"255":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"44":{"tf":1.0},"505":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0},"797":{"tf":1.0},"846":{"tf":1.0}}}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":20,"docs":{"113":{"tf":1.0},"124":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":2.23606797749979},"292":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"412":{"tf":1.0},"429":{"tf":1.0},"576":{"tf":1.0},"63":{"tf":1.0},"697":{"tf":1.7320508075688772},"700":{"tf":1.0},"743":{"tf":1.0},"748":{"tf":1.0},"772":{"tf":1.0},"810":{"tf":1.0},"831":{"tf":1.0},"902":{"tf":1.0},"928":{"tf":1.4142135623730951}}}}}}},"i":{"df":0,"docs":{},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"1006":{"tf":1.0},"313":{"tf":1.0},"49":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"30":{"tf":1.0}}}},"m":{"_":{"df":0,"docs":{},"u":{"df":2,"docs":{"722":{"tf":1.0},"723":{"tf":1.0}}},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":5,"docs":{"199":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"715":{"tf":1.4142135623730951},"717":{"tf":1.0}},"m":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"1012":{"tf":1.0},"609":{"tf":1.0}},"i":{"df":125,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1003":{"tf":1.0},"106":{"tf":1.0},"107":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"136":{"tf":1.0},"137":{"tf":1.0},"150":{"tf":1.0},"151":{"tf":1.0},"164":{"tf":1.4142135623730951},"165":{"tf":1.0},"17":{"tf":1.0},"172":{"tf":1.0},"18":{"tf":1.0},"182":{"tf":1.0},"183":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":1.0},"2":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"229":{"tf":1.0},"230":{"tf":1.0},"247":{"tf":1.0},"248":{"tf":1.0},"263":{"tf":1.0},"264":{"tf":1.0},"268":{"tf":1.0},"269":{"tf":1.0},"279":{"tf":1.0},"280":{"tf":1.0},"294":{"tf":1.0},"295":{"tf":1.0},"311":{"tf":1.0},"312":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"386":{"tf":1.0},"387":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"430":{"tf":1.0},"431":{"tf":1.0},"45":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":1.0},"465":{"tf":1.0},"466":{"tf":1.0},"47":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.0},"495":{"tf":1.0},"496":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.0},"535":{"tf":1.0},"536":{"tf":1.0},"549":{"tf":1.0},"550":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.0},"584":{"tf":1.0},"585":{"tf":1.0},"598":{"tf":1.0},"599":{"tf":1.0},"613":{"tf":1.0},"614":{"tf":1.0},"627":{"tf":1.0},"628":{"tf":1.0},"649":{"tf":1.0},"650":{"tf":1.0},"664":{"tf":1.0},"665":{"tf":1.0},"678":{"tf":1.0},"679":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"709":{"tf":1.0},"710":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.0},"757":{"tf":1.0},"758":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"782":{"tf":1.0},"783":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"796":{"tf":1.0},"80":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"827":{"tf":1.0},"828":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"857":{"tf":1.0},"858":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.0},"891":{"tf":1.0},"892":{"tf":1.0},"908":{"tf":1.0},"909":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"93":{"tf":1.0},"94":{"tf":1.0},"940":{"tf":1.0},"941":{"tf":1.0},"957":{"tf":1.0},"958":{"tf":1.0},"974":{"tf":1.0},"975":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"201":{"tf":1.0}}}}}},"p":{"_":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"e":{"d":{"df":2,"docs":{"735":{"tf":1.7320508075688772},"736":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"500":{"tf":1.0},"735":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"724":{"tf":1.0}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"3":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"500":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"878":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"743":{"tf":1.0},"747":{"tf":1.0},"776":{"tf":1.4142135623730951},"84":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":68,"docs":{"121":{"tf":1.4142135623730951},"160":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"178":{"tf":1.0},"18":{"tf":1.4142135623730951},"196":{"tf":1.0},"200":{"tf":1.0},"209":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.0},"37":{"tf":1.0},"375":{"tf":1.0},"440":{"tf":1.7320508075688772},"451":{"tf":1.0},"461":{"tf":1.4142135623730951},"467":{"tf":1.0},"48":{"tf":1.7320508075688772},"49":{"tf":1.4142135623730951},"516":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"537":{"tf":2.0},"54":{"tf":1.0},"542":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"635":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.4142135623730951},"700":{"tf":1.4142135623730951},"711":{"tf":1.0},"73":{"tf":1.0},"740":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"804":{"tf":1.0},"810":{"tf":1.0},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"849":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"88":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"900":{"tf":1.0},"902":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951},"972":{"tf":1.0},"984":{"tf":1.0}}}},"s":{"df":2,"docs":{"765":{"tf":1.0},"832":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":15,"docs":{"253":{"tf":1.0},"267":{"tf":1.0},"439":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"605":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"773":{"tf":1.0},"788":{"tf":1.0},"829":{"tf":1.0},"846":{"tf":1.0},"879":{"tf":2.0},"939":{"tf":1.0},"979":{"tf":1.0}}},"f":{"a":{"c":{"df":1,"docs":{"976":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"g":{"df":1,"docs":{"752":{"tf":1.0}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"735":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"267":{"tf":1.0},"534":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"937":{"tf":1.0}}}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"300":{"tf":1.4142135623730951}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"64":{"tf":1.0},"641":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"y":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"520":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"n":{"c":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"48":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":12,"docs":{"160":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.4142135623730951},"567":{"tf":1.7320508075688772},"770":{"tf":1.0},"988":{"tf":1.7320508075688772},"989":{"tf":1.0},"990":{"tf":1.4142135623730951},"991":{"tf":1.0},"992":{"tf":1.0},"994":{"tf":1.0},"996":{"tf":1.4142135623730951}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":7,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"47":{"tf":1.0},"740":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"959":{"tf":1.0}},"i":{"df":1,"docs":{"721":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"314":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"7":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"x":{"df":3,"docs":{"253":{"tf":1.0},"331":{"tf":1.0},"553":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"709":{"tf":1.0},"729":{"tf":2.23606797749979}}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"'":{"df":2,"docs":{"237":{"tf":1.0},"373":{"tf":1.0}}},".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"(":{"'":{"df":0,"docs":{},"{":{"\"":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":1,"docs":{"847":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":1,"docs":{"847":{"tf":1.0}}}}},"df":0,"docs":{}}}}},":":{":":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"284":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"281":{"tf":1.0},"284":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"0":{"df":1,"docs":{"416":{"tf":1.0}}},"1":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"393":{"tf":1.0}}}},"s":{"df":4,"docs":{"154":{"tf":1.4142135623730951},"387":{"tf":1.4142135623730951},"390":{"tf":1.0},"391":{"tf":1.0}}}}}}},"a":{"df":0,"docs":{},"t":{"df":10,"docs":{"430":{"tf":1.4142135623730951},"431":{"tf":1.0},"432":{"tf":1.7320508075688772},"435":{"tf":2.0},"437":{"tf":2.449489742783178},"439":{"tf":1.0},"440":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.0},"723":{"tf":1.4142135623730951}},"i":{"c":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"(":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"438":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"773":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":97,"docs":{"1003":{"tf":1.0},"1004":{"tf":1.7320508075688772},"126":{"tf":1.4142135623730951},"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"144":{"tf":1.0},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":2.6457513110645907},"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":1.0},"219":{"tf":1.0},"22":{"tf":1.4142135623730951},"229":{"tf":1.7320508075688772},"230":{"tf":1.0},"231":{"tf":2.6457513110645907},"232":{"tf":1.7320508075688772},"235":{"tf":1.0},"238":{"tf":1.0},"24":{"tf":1.0},"243":{"tf":1.0},"246":{"tf":1.0},"252":{"tf":1.0},"268":{"tf":1.7320508075688772},"270":{"tf":1.0},"271":{"tf":1.0},"3":{"tf":2.0},"30":{"tf":1.0},"310":{"tf":1.0},"312":{"tf":1.4142135623730951},"313":{"tf":2.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.7320508075688772},"316":{"tf":1.0},"317":{"tf":1.0},"327":{"tf":1.0},"335":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":2.0},"374":{"tf":1.4142135623730951},"375":{"tf":3.1622776601683795},"376":{"tf":1.4142135623730951},"380":{"tf":1.0},"386":{"tf":1.7320508075688772},"389":{"tf":1.0},"390":{"tf":2.0},"417":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"459":{"tf":1.0},"515":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.4142135623730951},"586":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"663":{"tf":1.0},"697":{"tf":1.0},"720":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"819":{"tf":1.0},"871":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":2.0},"931":{"tf":1.0},"932":{"tf":2.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.4142135623730951},"937":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"973":{"tf":1.0},"983":{"tf":1.0}}}}}}},"·":{"2":{"df":1,"docs":{"346":{"tf":1.0}}},"4":{"/":{"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"0":{"df":1,"docs":{"567":{"tf":1.7320508075688772}}},":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"879":{"tf":3.0},"880":{"tf":1.7320508075688772},"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"818":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"880":{"tf":1.0}}}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"x":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{")":{".":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"_":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"a":{"b":{"df":0,"docs":{},"l":{"df":66,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"248":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"633":{"tf":1.4142135623730951},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"885":{"tf":1.4142135623730951},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"1002":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"148":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":4,"docs":{"342":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"786":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"147":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":40,"docs":{"114":{"tf":1.0},"140":{"tf":1.0},"155":{"tf":1.0},"196":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.4142135623730951},"22":{"tf":1.0},"221":{"tf":1.0},"23":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"296":{"tf":1.0},"314":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"471":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"528":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.0},"571":{"tf":1.0},"593":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"631":{"tf":1.0},"634":{"tf":1.7320508075688772},"653":{"tf":1.4142135623730951},"668":{"tf":1.0},"670":{"tf":1.0},"717":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"763":{"tf":1.4142135623730951},"844":{"tf":1.0},"85":{"tf":1.0},"94":{"tf":1.0},"945":{"tf":1.0}},"n":{"df":8,"docs":{"1010":{"tf":1.0},"239":{"tf":1.0},"346":{"tf":1.0},"642":{"tf":1.0},"653":{"tf":1.0},"735":{"tf":1.0},"788":{"tf":1.0},"945":{"tf":1.0}}},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"231":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"279":{"tf":1.0}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"467":{"tf":1.0}}}}},"k":{"df":1,"docs":{"835":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"124":{"tf":1.0},"51":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.0},"725":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":3,"docs":{"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"349":{"tf":2.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":29,"docs":{"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"338":{"tf":1.4142135623730951},"339":{"tf":1.0},"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":2.449489742783178},"350":{"tf":1.0},"505":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"615":{"tf":1.0},"697":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":2.23606797749979},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0}},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"k":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"221":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":14,"docs":{"108":{"tf":1.0},"113":{"tf":1.0},"203":{"tf":2.8284271247461903},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"208":{"tf":4.58257569495584},"218":{"tf":1.4142135623730951},"221":{"tf":1.0},"296":{"tf":1.0},"450":{"tf":1.0},"565":{"tf":1.0},"711":{"tf":1.0},"776":{"tf":1.4142135623730951},"919":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"i":{"d":{"df":3,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.0}}},"df":0,"docs":{}},"s":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"714":{"tf":1.0}}}},"t":{"df":6,"docs":{"709":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.7320508075688772},"724":{"tf":1.0}}},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}}},"b":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"874":{"tf":1.0}}}}},"df":0,"docs":{}},"d":{"df":1,"docs":{"112":{"tf":1.0}}},"df":7,"docs":{"207":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":2.449489742783178},"346":{"tf":1.4142135623730951},"348":{"tf":2.6457513110645907},"539":{"tf":1.0},"749":{"tf":1.7320508075688772}},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"725":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"m":{"df":30,"docs":{"104":{"tf":1.0},"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.4142135623730951},"109":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"118":{"tf":1.0},"121":{"tf":1.4142135623730951},"196":{"tf":1.0},"199":{"tf":1.0},"201":{"tf":1.7320508075688772},"270":{"tf":1.0},"282":{"tf":1.0},"296":{"tf":1.0},"298":{"tf":1.0},"303":{"tf":1.4142135623730951},"306":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"403":{"tf":1.0},"408":{"tf":1.0},"532":{"tf":1.0},"571":{"tf":1.0},"59":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"810":{"tf":1.4142135623730951},"848":{"tf":1.0}}}},"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"c":{"df":29,"docs":{"0":{"tf":1.0},"113":{"tf":1.7320508075688772},"121":{"tf":1.0},"140":{"tf":1.0},"145":{"tf":1.0},"193":{"tf":1.0},"208":{"tf":1.0},"230":{"tf":1.0},"250":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"277":{"tf":1.0},"296":{"tf":1.0},"340":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"389":{"tf":1.0},"418":{"tf":1.0},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"582":{"tf":1.0},"777":{"tf":1.4142135623730951},"781":{"tf":1.0},"798":{"tf":1.4142135623730951},"801":{"tf":1.0},"842":{"tf":1.4142135623730951},"928":{"tf":1.0}}},"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"968":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":5,"docs":{"199":{"tf":1.0},"201":{"tf":1.0},"416":{"tf":1.0},"513":{"tf":1.0},"774":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":1,"docs":{"799":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":5,"docs":{"3":{"tf":1.0},"599":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"603":{"tf":1.7320508075688772}}}}}}},"l":{"df":3,"docs":{"177":{"tf":1.0},"551":{"tf":1.0},"717":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"296":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"152":{"tf":1.0},"932":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"n":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"772":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"912":{"tf":1.0}}}}},"df":1,"docs":{"58":{"tf":1.0}},"t":{"df":1,"docs":{"932":{"tf":1.0}},"h":{"df":1,"docs":{"221":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"1004":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"m":{"df":32,"docs":{"140":{"tf":1.0},"169":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"255":{"tf":1.0},"274":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.4142135623730951},"39":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.4142135623730951},"505":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.7320508075688772},"711":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.4142135623730951},"772":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.4142135623730951},"8":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":131,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1008":{"tf":1.4142135623730951},"106":{"tf":1.0},"115":{"tf":1.4142135623730951},"122":{"tf":1.0},"128":{"tf":1.4142135623730951},"136":{"tf":1.0},"142":{"tf":1.7320508075688772},"150":{"tf":1.0},"156":{"tf":1.7320508075688772},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.4142135623730951},"182":{"tf":1.0},"188":{"tf":1.0},"195":{"tf":1.0},"209":{"tf":1.4142135623730951},"211":{"tf":2.449489742783178},"215":{"tf":1.0},"225":{"tf":1.4142135623730951},"229":{"tf":1.0},"237":{"tf":1.7320508075688772},"239":{"tf":1.0},"247":{"tf":1.0},"255":{"tf":1.0},"268":{"tf":1.0},"275":{"tf":1.0},"279":{"tf":1.0},"282":{"tf":1.0},"286":{"tf":1.4142135623730951},"294":{"tf":1.0},"30":{"tf":2.449489742783178},"304":{"tf":1.4142135623730951},"311":{"tf":1.0},"315":{"tf":1.0},"317":{"tf":1.0},"322":{"tf":1.0},"354":{"tf":1.4142135623730951},"366":{"tf":1.0},"376":{"tf":1.0},"378":{"tf":1.4142135623730951},"38":{"tf":1.0},"386":{"tf":1.0},"392":{"tf":1.0},"410":{"tf":1.0},"419":{"tf":1.0},"430":{"tf":1.0},"442":{"tf":1.4142135623730951},"451":{"tf":1.0},"457":{"tf":1.7320508075688772},"465":{"tf":1.0},"474":{"tf":1.0},"481":{"tf":1.0},"487":{"tf":1.0},"495":{"tf":1.0},"50":{"tf":1.0},"505":{"tf":1.0},"513":{"tf":1.0},"528":{"tf":1.4142135623730951},"53":{"tf":1.0},"535":{"tf":1.0},"541":{"tf":1.4142135623730951},"549":{"tf":1.0},"555":{"tf":1.7320508075688772},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"578":{"tf":1.0},"584":{"tf":1.0},"590":{"tf":1.4142135623730951},"598":{"tf":1.0},"605":{"tf":1.0},"613":{"tf":1.0},"619":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.0},"639":{"tf":2.23606797749979},"648":{"tf":1.0},"649":{"tf":1.0},"656":{"tf":1.0},"664":{"tf":1.0},"670":{"tf":1.0},"678":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.0},"692":{"tf":1.0},"701":{"tf":1.0},"709":{"tf":1.0},"724":{"tf":1.0},"757":{"tf":1.0},"763":{"tf":1.0},"782":{"tf":1.0},"788":{"tf":1.7320508075688772},"79":{"tf":1.0},"795":{"tf":1.0},"801":{"tf":1.4142135623730951},"808":{"tf":1.0},"819":{"tf":1.4142135623730951},"827":{"tf":1.0},"833":{"tf":1.0},"841":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"857":{"tf":1.0},"864":{"tf":1.4142135623730951},"871":{"tf":1.0},"883":{"tf":1.0},"891":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.4142135623730951},"908":{"tf":1.0},"917":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"935":{"tf":1.0},"940":{"tf":1.4142135623730951},"944":{"tf":1.4142135623730951},"945":{"tf":1.0},"946":{"tf":1.0},"947":{"tf":1.7320508075688772},"957":{"tf":1.4142135623730951},"961":{"tf":1.0},"963":{"tf":1.0},"964":{"tf":2.0},"974":{"tf":1.0},"980":{"tf":1.0},"988":{"tf":1.0},"99":{"tf":1.0},"992":{"tf":1.0},"994":{"tf":1.4142135623730951}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":14,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"211":{"tf":1.0},"304":{"tf":1.0},"376":{"tf":1.0},"50":{"tf":1.0},"639":{"tf":1.0},"678":{"tf":1.7320508075688772},"679":{"tf":1.0},"680":{"tf":1.0},"683":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0}}}}}}},"x":{"df":0,"docs":{},"t":{"df":4,"docs":{"272":{"tf":1.0},"273":{"tf":1.0},"75":{"tf":1.0},"847":{"tf":1.4142135623730951}},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"721":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"532":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"{":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"749":{"tf":1.4142135623730951}}}}}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":5,"docs":{"571":{"tf":1.0},"710":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.0},"780":{"tf":1.0}}}},"t":{"'":{"df":4,"docs":{"483":{"tf":1.0},"673":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{}}},"df":2,"docs":{"333":{"tf":1.0},"439":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":14,"docs":{"1015":{"tf":1.0},"234":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.4142135623730951},"267":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":2.449489742783178},"502":{"tf":1.0},"503":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"849":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"230":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.4142135623730951},"992":{"tf":1.0}}}},"i":{"df":5,"docs":{"124":{"tf":1.0},"254":{"tf":1.0},"554":{"tf":1.0},"718":{"tf":1.0},"777":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"'":{"df":6,"docs":{"316":{"tf":1.0},"429":{"tf":1.0},"832":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"880":{"tf":1.0}}},"b":{"df":0,"docs":{},"i":{"df":6,"docs":{"264":{"tf":1.0},"267":{"tf":1.0},"412":{"tf":1.0},"576":{"tf":1.0},"725":{"tf":1.0},"776":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":29,"docs":{"108":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"169":{"tf":1.0},"19":{"tf":1.4142135623730951},"206":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"310":{"tf":1.0},"314":{"tf":1.0},"345":{"tf":1.0},"35":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.0},"402":{"tf":1.0},"432":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"537":{"tf":1.0},"60":{"tf":1.0},"697":{"tf":1.0},"799":{"tf":1.0},"818":{"tf":1.0},"945":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"852":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"418":{"tf":1.0}}}},"y":{"'":{"df":0,"docs":{},"r":{"df":3,"docs":{"16":{"tf":1.0},"500":{"tf":1.0},"885":{"tf":1.0}}},"v":{"df":1,"docs":{"853":{"tf":1.0}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":14,"docs":{"16":{"tf":1.0},"187":{"tf":1.0},"439":{"tf":1.0},"482":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"666":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"835":{"tf":1.0},"874":{"tf":1.0},"979":{"tf":1.0}}},"k":{"df":8,"docs":{"1004":{"tf":1.0},"234":{"tf":1.0},"250":{"tf":1.0},"60":{"tf":1.0},"64":{"tf":1.0},"78":{"tf":1.0},"852":{"tf":1.0},"855":{"tf":1.0}}}},"r":{"d":{"df":11,"docs":{"113":{"tf":1.0},"170":{"tf":1.0},"221":{"tf":1.0},"344":{"tf":1.4142135623730951},"345":{"tf":1.0},"469":{"tf":1.0},"528":{"tf":1.0},"571":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":2,"docs":{"354":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"935":{"tf":1.0}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":24,"docs":{"111":{"tf":1.0},"186":{"tf":1.0},"187":{"tf":1.4142135623730951},"216":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"368":{"tf":1.0},"414":{"tf":1.0},"426":{"tf":1.0},"467":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"650":{"tf":1.0},"701":{"tf":1.0},"714":{"tf":1.0},"73":{"tf":1.0},"799":{"tf":1.4142135623730951},"848":{"tf":1.0},"858":{"tf":1.0},"904":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"917":{"tf":1.0},"921":{"tf":1.0}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":17,"docs":{"144":{"tf":1.0},"16":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"570":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":2.0},"732":{"tf":1.0},"74":{"tf":1.0},"818":{"tf":1.4142135623730951},"842":{"tf":1.0},"858":{"tf":1.0},"885":{"tf":1.0},"979":{"tf":1.0}},"t":{"df":3,"docs":{"650":{"tf":1.0},"780":{"tf":1.0},"881":{"tf":1.0}}}}},"s":{"a":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"58":{"tf":1.4142135623730951},"63":{"tf":1.0},"832":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"565":{"tf":1.0},"965":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"54":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":11,"docs":{"1008":{"tf":1.0},"126":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.7320508075688772},"21":{"tf":1.0},"374":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"814":{"tf":1.0},"831":{"tf":1.0}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{",":{".":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":2,"docs":{"872":{"tf":1.0},"878":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":12,"docs":{"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"438":{"tf":1.4142135623730951},"564":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.7320508075688772},"875":{"tf":1.0},"879":{"tf":4.242640687119285},"880":{"tf":1.4142135623730951},"881":{"tf":2.23606797749979},"885":{"tf":1.7320508075688772},"913":{"tf":1.0}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"797":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":2,"docs":{"720":{"tf":1.0},"763":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":45,"docs":{"140":{"tf":1.0},"148":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"175":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"209":{"tf":1.4142135623730951},"21":{"tf":1.0},"211":{"tf":1.4142135623730951},"234":{"tf":1.0},"267":{"tf":1.0},"288":{"tf":1.0},"296":{"tf":1.0},"33":{"tf":1.0},"345":{"tf":1.0},"365":{"tf":1.0},"388":{"tf":1.0},"39":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.7320508075688772},"603":{"tf":1.0},"605":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"732":{"tf":1.0},"77":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"829":{"tf":1.0},"846":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":1.0},"952":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"330":{"tf":1.0},"776":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"374":{"tf":1.0},"38":{"tf":1.0},"629":{"tf":1.0},"640":{"tf":1.0},"711":{"tf":1.0}}}}}}}},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"500":{"tf":1.0}}}}}},"u":{"df":40,"docs":{"124":{"tf":1.4142135623730951},"132":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":2.0},"269":{"tf":1.0},"276":{"tf":1.0},"285":{"tf":1.0},"324":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"358":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"439":{"tf":1.0},"459":{"tf":1.0},"461":{"tf":1.0},"470":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":1.4142135623730951},"524":{"tf":1.0},"570":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.4142135623730951},"63":{"tf":1.7320508075688772},"634":{"tf":1.0},"7":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"723":{"tf":1.0},"759":{"tf":2.0},"763":{"tf":1.0},"78":{"tf":1.4142135623730951},"784":{"tf":1.0},"797":{"tf":1.0},"83":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"348":{"tf":1.4142135623730951}}},"_":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"347":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":2.0},"347":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":2,"docs":{"347":{"tf":1.4142135623730951},"351":{"tf":1.0}}}},"df":0,"docs":{}}},"df":18,"docs":{"322":{"tf":2.8284271247461903},"335":{"tf":1.0},"336":{"tf":1.7320508075688772},"337":{"tf":1.7320508075688772},"338":{"tf":1.7320508075688772},"339":{"tf":1.7320508075688772},"342":{"tf":2.449489742783178},"343":{"tf":1.4142135623730951},"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":5.0},"347":{"tf":3.605551275463989},"348":{"tf":3.0},"349":{"tf":2.23606797749979},"350":{"tf":1.0},"351":{"tf":2.0},"365":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}}}}}}},"i":{"d":{"df":4,"docs":{"346":{"tf":1.7320508075688772},"347":{"tf":2.0},"349":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":3,"docs":{"351":{"tf":1.0},"483":{"tf":1.0},"78":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"293":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"697":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"816":{"tf":1.4142135623730951},"874":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"e":{"df":112,"docs":{"1003":{"tf":1.0},"1004":{"tf":1.0},"108":{"tf":1.0},"124":{"tf":1.4142135623730951},"132":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"148":{"tf":1.0},"155":{"tf":1.0},"173":{"tf":1.0},"178":{"tf":1.0},"194":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"245":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"265":{"tf":1.0},"278":{"tf":1.0},"296":{"tf":1.4142135623730951},"301":{"tf":1.0},"308":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"402":{"tf":2.23606797749979},"427":{"tf":1.0},"435":{"tf":1.0},"444":{"tf":1.7320508075688772},"459":{"tf":1.0},"467":{"tf":1.7320508075688772},"469":{"tf":1.4142135623730951},"48":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"526":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"542":{"tf":1.0},"549":{"tf":1.7320508075688772},"550":{"tf":1.0},"553":{"tf":2.0},"555":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":2.23606797749979},"568":{"tf":1.0},"569":{"tf":2.6457513110645907},"570":{"tf":1.0},"571":{"tf":2.23606797749979},"573":{"tf":1.4142135623730951},"574":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":2.0},"577":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"631":{"tf":1.0},"673":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"73":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":2.8284271247461903},"759":{"tf":1.4142135623730951},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"763":{"tf":1.0},"767":{"tf":1.0},"770":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":1.4142135623730951},"797":{"tf":2.0},"799":{"tf":1.4142135623730951},"810":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"822":{"tf":1.0},"825":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0},"890":{"tf":1.0},"912":{"tf":2.0},"932":{"tf":1.0},"938":{"tf":1.4142135623730951},"956":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"185":{"tf":1.0},"335":{"tf":1.0},"564":{"tf":1.0},"942":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":4,"docs":{"204":{"tf":2.6457513110645907},"205":{"tf":2.0},"207":{"tf":1.0},"208":{"tf":3.872983346207417}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":3,"docs":{"553":{"tf":1.0},"932":{"tf":1.0},"938":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}},"p":{"df":1,"docs":{"521":{"tf":1.0}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"182":{"tf":1.7320508075688772},"183":{"tf":2.0},"184":{"tf":2.0},"186":{"tf":2.449489742783178}}}}}},"t":{"df":6,"docs":{"709":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.7320508075688772},"724":{"tf":1.0}}}},"o":{"d":{"a":{"df":0,"docs":{},"y":{"df":5,"docs":{"49":{"tf":1.0},"515":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":3,"docs":{"1002":{"tf":1.4142135623730951},"63":{"tf":1.0},"75":{"tf":1.0}}}},"df":1,"docs":{"849":{"tf":1.0}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":14,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"21":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"350":{"tf":1.0},"452":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"594":{"tf":1.0},"633":{"tf":1.0},"64":{"tf":1.0},"68":{"tf":1.0},"711":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"'":{"df":2,"docs":{"3":{"tf":1.0},"928":{"tf":1.0}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}}},"df":36,"docs":{"114":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"193":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":2.23606797749979},"3":{"tf":1.0},"520":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"564":{"tf":2.6457513110645907},"565":{"tf":1.7320508075688772},"566":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.7320508075688772},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"6":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"797":{"tf":1.0},"798":{"tf":1.0},"849":{"tf":1.7320508075688772},"850":{"tf":1.0},"9":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":2,"docs":{"125":{"tf":1.0},"314":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"231":{"tf":1.0},"303":{"tf":1.0},"346":{"tf":1.0},"831":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":1,"docs":{"741":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":27,"docs":{"125":{"tf":1.0},"145":{"tf":1.0},"154":{"tf":1.0},"173":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.0},"19":{"tf":1.0},"296":{"tf":1.0},"369":{"tf":1.0},"378":{"tf":1.0},"38":{"tf":1.0},"381":{"tf":1.0},"516":{"tf":1.0},"586":{"tf":1.0},"627":{"tf":1.0},"630":{"tf":1.0},"633":{"tf":1.0},"645":{"tf":1.4142135623730951},"841":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":3.1622776601683795},"849":{"tf":2.0},"850":{"tf":1.0},"856":{"tf":1.0},"928":{"tf":1.0},"969":{"tf":1.0},"973":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"842":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"i":{"df":4,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.0},"848":{"tf":1.0}}}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"879":{"tf":2.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"p":{"df":6,"docs":{"1004":{"tf":1.0},"234":{"tf":1.4142135623730951},"39":{"tf":1.0},"444":{"tf":1.0},"50":{"tf":1.0},"673":{"tf":1.0}},"i":{"c":{"df":4,"docs":{"251":{"tf":1.0},"361":{"tf":1.0},"712":{"tf":1.0},"824":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"l":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":3.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}},"y":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":23,"docs":{"208":{"tf":1.4142135623730951},"257":{"tf":1.0},"264":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"428":{"tf":1.0},"444":{"tf":1.0},"471":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.4142135623730951},"571":{"tf":1.4142135623730951},"576":{"tf":1.0},"714":{"tf":1.4142135623730951},"722":{"tf":1.0},"73":{"tf":1.0},"814":{"tf":1.0},"828":{"tf":1.0},"831":{"tf":1.0},"843":{"tf":1.4142135623730951},"849":{"tf":1.0},"855":{"tf":1.0},"879":{"tf":2.23606797749979},"885":{"tf":1.4142135623730951}},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":6,"docs":{"194":{"tf":1.0},"204":{"tf":1.0},"54":{"tf":1.0},"721":{"tf":1.0},"807":{"tf":1.0},"928":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"a":{"c":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"50":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"46":{"tf":1.0}}},"k":{"'":{"df":1,"docs":{"184":{"tf":1.0}}},"df":64,"docs":{"113":{"tf":1.4142135623730951},"121":{"tf":1.0},"136":{"tf":1.7320508075688772},"137":{"tf":1.7320508075688772},"138":{"tf":1.4142135623730951},"139":{"tf":1.0},"140":{"tf":2.6457513110645907},"141":{"tf":1.4142135623730951},"142":{"tf":1.4142135623730951},"144":{"tf":1.0},"145":{"tf":1.4142135623730951},"146":{"tf":1.4142135623730951},"147":{"tf":1.0},"148":{"tf":1.7320508075688772},"149":{"tf":1.4142135623730951},"182":{"tf":1.7320508075688772},"183":{"tf":1.0},"184":{"tf":2.8284271247461903},"185":{"tf":1.0},"186":{"tf":2.0},"187":{"tf":1.4142135623730951},"190":{"tf":1.0},"194":{"tf":1.4142135623730951},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"375":{"tf":1.0},"402":{"tf":1.0},"407":{"tf":1.4142135623730951},"439":{"tf":1.0},"447":{"tf":1.0},"568":{"tf":1.0},"710":{"tf":1.0},"715":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"831":{"tf":1.4142135623730951},"841":{"tf":2.23606797749979},"842":{"tf":2.0},"846":{"tf":2.449489742783178},"847":{"tf":1.7320508075688772},"848":{"tf":2.0},"849":{"tf":1.7320508075688772},"850":{"tf":1.7320508075688772},"852":{"tf":1.4142135623730951},"853":{"tf":1.4142135623730951},"857":{"tf":2.449489742783178},"858":{"tf":2.0},"859":{"tf":1.0},"860":{"tf":1.4142135623730951},"861":{"tf":1.4142135623730951},"862":{"tf":1.4142135623730951},"863":{"tf":2.0},"867":{"tf":1.0},"870":{"tf":1.4142135623730951},"929":{"tf":1.0},"932":{"tf":1.0},"944":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"191":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{":":{":":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"140":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":2,"docs":{"137":{"tf":1.0},"149":{"tf":1.4142135623730951}}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":15,"docs":{"1014":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"208":{"tf":1.0},"569":{"tf":1.0},"574":{"tf":1.0},"727":{"tf":1.0},"745":{"tf":1.0},"776":{"tf":1.7320508075688772},"779":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"949":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.0}},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"412":{"tf":1.0},"426":{"tf":1.0}}}}},"r":{"df":1,"docs":{"423":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"257":{"tf":1.4142135623730951},"365":{"tf":1.0},"507":{"tf":1.4142135623730951},"554":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"435":{"tf":1.0}}},"t":{"df":8,"docs":{"180":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"22":{"tf":1.0},"24":{"tf":2.0},"402":{"tf":1.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"931":{"tf":1.0}}}},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"619":{"tf":1.0}}},"df":65,"docs":{"12":{"tf":1.0},"164":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":2.0},"170":{"tf":1.7320508075688772},"171":{"tf":2.449489742783178},"177":{"tf":1.4142135623730951},"220":{"tf":1.0},"231":{"tf":2.449489742783178},"232":{"tf":1.0},"234":{"tf":1.0},"284":{"tf":1.4142135623730951},"286":{"tf":1.0},"291":{"tf":1.4142135623730951},"296":{"tf":1.0},"346":{"tf":1.4142135623730951},"362":{"tf":1.4142135623730951},"372":{"tf":1.0},"380":{"tf":1.0},"39":{"tf":1.4142135623730951},"44":{"tf":1.4142135623730951},"459":{"tf":1.0},"46":{"tf":1.4142135623730951},"481":{"tf":2.0},"482":{"tf":1.7320508075688772},"483":{"tf":2.6457513110645907},"485":{"tf":2.0},"486":{"tf":1.4142135623730951},"491":{"tf":1.0},"514":{"tf":3.3166247903554},"521":{"tf":1.0},"523":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.4142135623730951},"532":{"tf":1.7320508075688772},"535":{"tf":1.4142135623730951},"536":{"tf":1.4142135623730951},"537":{"tf":3.0},"540":{"tf":1.0},"542":{"tf":1.4142135623730951},"545":{"tf":1.4142135623730951},"548":{"tf":1.0},"574":{"tf":1.4142135623730951},"584":{"tf":1.7320508075688772},"585":{"tf":1.0},"586":{"tf":2.6457513110645907},"588":{"tf":2.449489742783178},"589":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"613":{"tf":1.7320508075688772},"614":{"tf":1.4142135623730951},"615":{"tf":2.23606797749979},"617":{"tf":1.7320508075688772},"619":{"tf":1.7320508075688772},"622":{"tf":1.0},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"697":{"tf":1.7320508075688772},"699":{"tf":2.0},"700":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.4142135623730951},"876":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"514":{"tf":1.0}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"171":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":4,"docs":{"171":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.0},"546":{"tf":1.0}}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"383":{"tf":1.0},"385":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":41,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"3":{"tf":2.0},"38":{"tf":1.0},"406":{"tf":1.0},"48":{"tf":1.4142135623730951},"520":{"tf":1.0},"598":{"tf":1.4142135623730951},"599":{"tf":2.449489742783178},"6":{"tf":1.0},"600":{"tf":3.872983346207417},"602":{"tf":5.385164807134504},"603":{"tf":3.0},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"692":{"tf":1.7320508075688772},"693":{"tf":1.0},"694":{"tf":2.23606797749979},"696":{"tf":1.7320508075688772},"700":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"715":{"tf":1.0},"722":{"tf":1.0},"759":{"tf":1.0},"776":{"tf":1.4142135623730951},"80":{"tf":1.0},"81":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"932":{"tf":1.7320508075688772},"945":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.0}},"r":{"df":2,"docs":{"221":{"tf":1.0},"776":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":5,"docs":{"19":{"tf":1.0},"38":{"tf":1.0},"519":{"tf":1.0},"532":{"tf":1.0},"786":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"t":{"df":12,"docs":{"148":{"tf":1.0},"172":{"tf":1.0},"203":{"tf":1.0},"363":{"tf":1.0},"368":{"tf":2.23606797749979},"46":{"tf":1.0},"575":{"tf":1.0},"759":{"tf":1.0},"778":{"tf":1.0},"837":{"tf":1.0},"871":{"tf":1.0},"879":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"567":{"tf":1.0}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"28":{"tf":1.4142135623730951}}}},"t":{"df":2,"docs":{"439":{"tf":1.0},"517":{"tf":1.0}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":4,"docs":{"602":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":4,"docs":{"627":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"651":{"tf":1.0}}}}}}}},"p":{"df":7,"docs":{"653":{"tf":1.0},"656":{"tf":1.0},"663":{"tf":1.0},"666":{"tf":1.4142135623730951},"668":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"78":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"184":{"tf":1.0}},"i":{"df":27,"docs":{"111":{"tf":1.0},"121":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"233":{"tf":1.0},"236":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":3.1622776601683795},"273":{"tf":1.0},"316":{"tf":1.4142135623730951},"370":{"tf":1.0},"375":{"tf":1.0},"468":{"tf":1.0},"81":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"852":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"937":{"tf":1.0}}},"y":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"t":{"df":8,"docs":{"127":{"tf":1.0},"208":{"tf":1.0},"24":{"tf":1.0},"308":{"tf":1.0},"312":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"729":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":11,"docs":{"439":{"tf":1.4142135623730951},"49":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"525":{"tf":3.1622776601683795},"528":{"tf":1.0},"634":{"tf":1.0},"78":{"tf":1.7320508075688772}}},"n":{"d":{"df":2,"docs":{"184":{"tf":1.4142135623730951},"194":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"497":{"tf":1.0}}}},"df":17,"docs":{"128":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"292":{"tf":1.0},"436":{"tf":1.4142135623730951},"453":{"tf":1.0},"497":{"tf":1.0},"553":{"tf":1.0},"599":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"761":{"tf":1.4142135623730951},"777":{"tf":1.0},"843":{"tf":1.0},"895":{"tf":1.0},"898":{"tf":1.4142135623730951},"935":{"tf":1.0}},"e":{"df":11,"docs":{"163":{"tf":1.0},"249":{"tf":1.0},"402":{"tf":2.0},"436":{"tf":1.0},"44":{"tf":1.4142135623730951},"46":{"tf":1.0},"49":{"tf":1.0},"54":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":3.872983346207417},"762":{"tf":1.0}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"427":{"tf":1.0},"450":{"tf":1.0},"571":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"208":{"tf":1.0}}},"p":{"df":1,"docs":{"758":{"tf":1.0}},"l":{"df":1,"docs":{"752":{"tf":1.0}}}},"v":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"207":{"tf":1.4142135623730951},"296":{"tf":1.0},"842":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":1,"docs":{"797":{"tf":1.0}}}},"u":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"249":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"450":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"e":{"df":8,"docs":{"439":{"tf":1.4142135623730951},"522":{"tf":1.0},"6":{"tf":1.0},"636":{"tf":1.0},"721":{"tf":1.0},"761":{"tf":2.0},"777":{"tf":1.0},"97":{"tf":1.0}}},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"761":{"tf":1.0},"763":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"t":{"df":28,"docs":{"121":{"tf":1.0},"198":{"tf":1.0},"231":{"tf":1.7320508075688772},"254":{"tf":1.0},"262":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"567":{"tf":1.7320508075688772},"6":{"tf":1.0},"603":{"tf":1.0},"629":{"tf":1.4142135623730951},"692":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.4142135623730951},"700":{"tf":1.0},"8":{"tf":1.0},"84":{"tf":2.0},"848":{"tf":1.0},"852":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"46":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"198":{"tf":1.0},"46":{"tf":1.0}}}}}}}}}},"t":{"df":0,"docs":{},"h":{"df":2,"docs":{"6":{"tf":1.0},"777":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"852":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"e":{"df":2,"docs":{"428":{"tf":1.0},"773":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":2,"docs":{"455":{"tf":1.0},"522":{"tf":2.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"r":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"244":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"n":{"df":7,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"40":{"tf":1.0},"49":{"tf":1.0},"722":{"tf":1.4142135623730951},"799":{"tf":1.0},"912":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":3,"docs":{"797":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0}}}}}}}},"w":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":4,"docs":{"342":{"tf":1.0},"735":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"e":{"df":4,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"71":{"tf":1.0},"732":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"842":{"tf":1.0}}}}}}},"o":{"df":64,"docs":{"112":{"tf":1.0},"113":{"tf":1.0},"149":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"22":{"tf":1.0},"220":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.4142135623730951},"264":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.0},"340":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.4142135623730951},"350":{"tf":1.0},"373":{"tf":1.0},"39":{"tf":1.0},"402":{"tf":1.0},"45":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"491":{"tf":1.0},"512":{"tf":1.0},"515":{"tf":1.0},"525":{"tf":1.4142135623730951},"564":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"650":{"tf":1.0},"66":{"tf":1.0},"694":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.4142135623730951},"711":{"tf":1.0},"716":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"739":{"tf":1.0},"747":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":1.0},"814":{"tf":1.4142135623730951},"829":{"tf":1.0},"84":{"tf":1.0},"894":{"tf":1.0},"927":{"tf":1.0},"931":{"tf":1.4142135623730951},"932":{"tf":1.0}},"x":{"6":{"4":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"y":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":1,"docs":{"524":{"tf":2.23606797749979}}}}}}},"df":3,"docs":{"22":{"tf":2.23606797749979},"522":{"tf":1.0},"524":{"tf":1.7320508075688772}},"p":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"524":{"tf":1.0}}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.7320508075688772}}}}},"df":80,"docs":{"1011":{"tf":1.0},"140":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.4142135623730951},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"208":{"tf":3.605551275463989},"215":{"tf":1.4142135623730951},"22":{"tf":2.8284271247461903},"220":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"24":{"tf":3.7416573867739413},"25":{"tf":1.4142135623730951},"26":{"tf":1.0},"272":{"tf":1.0},"30":{"tf":1.0},"322":{"tf":1.4142135623730951},"332":{"tf":1.0},"333":{"tf":1.0},"334":{"tf":1.4142135623730951},"341":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"362":{"tf":1.0},"372":{"tf":1.0},"455":{"tf":2.0},"483":{"tf":1.0},"5":{"tf":1.7320508075688772},"513":{"tf":1.4142135623730951},"519":{"tf":2.8284271247461903},"520":{"tf":2.0},"521":{"tf":3.3166247903554},"522":{"tf":7.3484692283495345},"523":{"tf":4.242640687119285},"524":{"tf":4.0},"525":{"tf":1.0},"528":{"tf":1.0},"534":{"tf":1.7320508075688772},"535":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":2.8284271247461903},"539":{"tf":2.23606797749979},"542":{"tf":1.4142135623730951},"544":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.0},"56":{"tf":1.0},"588":{"tf":1.0},"598":{"tf":1.4142135623730951},"599":{"tf":1.7320508075688772},"6":{"tf":1.4142135623730951},"600":{"tf":2.0},"602":{"tf":2.449489742783178},"603":{"tf":1.4142135623730951},"605":{"tf":1.4142135623730951},"609":{"tf":1.0},"61":{"tf":1.0},"649":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":1.0},"668":{"tf":1.4142135623730951},"705":{"tf":1.0},"73":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"793":{"tf":1.4142135623730951},"814":{"tf":2.23606797749979},"815":{"tf":1.0},"817":{"tf":1.0},"84":{"tf":1.0},"880":{"tf":1.4142135623730951},"912":{"tf":1.0},"933":{"tf":2.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":5,"docs":{"513":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":2.8284271247461903},"522":{"tf":2.23606797749979},"524":{"tf":2.449489742783178}}}}}},"i":{"c":{"df":10,"docs":{"218":{"tf":1.0},"249":{"tf":1.0},"253":{"tf":1.0},"407":{"tf":1.0},"44":{"tf":1.0},"470":{"tf":1.0},"522":{"tf":1.0},"735":{"tf":1.0},"762":{"tf":1.0},"81":{"tf":1.0}}},"df":0,"docs":{}}}},"}":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{")":{"^":{"df":0,"docs":{},"u":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"{":{"df":0,"docs":{},"l":{"df":1,"docs":{"749":{"tf":1.0}}}}},"·":{"a":{"df":0,"docs":{},"·":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{".":{"df":1,"docs":{"470":{"tf":1.0}}},"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"df":8,"docs":{"208":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"83":{"tf":1.0},"885":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":13,"docs":{"204":{"tf":1.0},"208":{"tf":2.0},"24":{"tf":1.7320508075688772},"25":{"tf":1.7320508075688772},"438":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.7320508075688772},"634":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"83":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"404":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":7,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.4142135623730951},"25":{"tf":2.23606797749979},"404":{"tf":1.0},"455":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"8":{";":{"2":{"0":{"df":1,"docs":{"898":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":13,"docs":{"208":{"tf":1.0},"23":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"455":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"526":{"tf":1.0},"588":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.7320508075688772},"885":{"tf":1.0},"97":{"tf":1.7320508075688772}}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":6,"docs":{"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"368":{"tf":1.0}}}}}}}},"c":{"'":{"df":1,"docs":{"772":{"tf":1.0}}},"df":11,"docs":{"198":{"tf":1.0},"200":{"tf":2.23606797749979},"203":{"tf":1.0},"204":{"tf":1.0},"210":{"tf":1.0},"264":{"tf":1.0},"742":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0}}},"df":3,"docs":{"721":{"tf":2.0},"722":{"tf":1.7320508075688772},"749":{"tf":1.0}},"i":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"518":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":13,"docs":{"125":{"tf":1.0},"152":{"tf":1.4142135623730951},"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"191":{"tf":1.0},"276":{"tf":1.0},"369":{"tf":1.0},"461":{"tf":1.0},"514":{"tf":1.0},"564":{"tf":1.0},"574":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0}}},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":13,"docs":{"126":{"tf":1.0},"187":{"tf":1.0},"270":{"tf":1.0},"517":{"tf":1.0},"568":{"tf":1.0},"650":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"849":{"tf":1.4142135623730951}}}}}},"m":{"df":0,"docs":{},"p":{"df":14,"docs":{"203":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.0},"56":{"tf":1.0},"61":{"tf":1.7320508075688772},"627":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.7320508075688772},"640":{"tf":1.0},"645":{"tf":1.4142135623730951},"72":{"tf":1.0},"73":{"tf":1.0},"77":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"633":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":2,"docs":{"61":{"tf":1.0},"633":{"tf":2.449489742783178}}}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"300":{"tf":1.4142135623730951},"303":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}},"df":0,"docs":{}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"735":{"tf":1.0}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"30":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.0}},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{}}}}}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"721":{"tf":1.0},"84":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":0,"docs":{}}},"b":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"336":{"tf":1.0},"346":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"n":{"d":{"df":13,"docs":{"563":{"tf":2.23606797749979},"564":{"tf":3.1622776601683795},"565":{"tf":2.23606797749979},"567":{"tf":2.449489742783178},"568":{"tf":3.1622776601683795},"569":{"tf":2.23606797749979},"570":{"tf":2.6457513110645907},"571":{"tf":4.123105625617661},"573":{"tf":3.1622776601683795},"574":{"tf":2.0},"575":{"tf":2.0},"576":{"tf":3.0},"577":{"tf":1.7320508075688772}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"568":{"tf":1.4142135623730951},"573":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":2,"docs":{"568":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"348":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":9,"docs":{"106":{"tf":2.0},"107":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":2.449489742783178},"112":{"tf":2.6457513110645907},"113":{"tf":1.7320508075688772},"118":{"tf":1.0},"120":{"tf":1.0},"121":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":7,"docs":{"203":{"tf":1.0},"221":{"tf":1.0},"564":{"tf":1.0},"633":{"tf":1.0},"792":{"tf":1.0},"817":{"tf":1.0},"867":{"tf":1.0}}}}},"df":0,"docs":{}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"776":{"tf":1.0}}}}},"df":1,"docs":{"714":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"1014":{"tf":1.0},"51":{"tf":1.0},"727":{"tf":1.0},"739":{"tf":1.4142135623730951},"765":{"tf":1.0},"835":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"721":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}}}}}}},"d":{"df":1,"docs":{"741":{"tf":1.0}},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"152":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"341":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"7":{"tf":1.7320508075688772}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"799":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":2,"docs":{"796":{"tf":1.0},"799":{"tf":1.7320508075688772}}}}},"r":{"c":{"a":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"776":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"568":{"tf":1.0}}}}},"df":24,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.7320508075688772},"207":{"tf":1.0},"221":{"tf":1.0},"235":{"tf":1.0},"267":{"tf":1.0},"387":{"tf":1.0},"437":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"501":{"tf":1.7320508075688772},"537":{"tf":1.4142135623730951},"568":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0},"754":{"tf":1.0},"799":{"tf":1.0},"811":{"tf":1.0},"817":{"tf":1.0},"878":{"tf":1.0},"954":{"tf":1.0}},"g":{"df":0,"docs":{},"o":{"df":4,"docs":{"337":{"tf":1.0},"354":{"tf":1.0},"53":{"tf":1.0},"778":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"124":{"tf":1.0},"152":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"651":{"tf":1.0}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"779":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"711":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"804":{"tf":1.0},"84":{"tf":1.0},"927":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"217":{"tf":1.0},"221":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"375":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":3,"docs":{"763":{"tf":1.0},"863":{"tf":1.0},"919":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"323":{"tf":1.0}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"983":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"df":2,"docs":{"418":{"tf":1.0},"920":{"tf":1.0}}}},"df":1,"docs":{"284":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}},"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"435":{"tf":1.0},"436":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"272":{"tf":1.0}}},"df":0,"docs":{}}}}}},"x":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"343":{"tf":1.0},"975":{"tf":1.0}}}},"df":0,"docs":{}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":8,"docs":{"1004":{"tf":1.0},"390":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.0},"600":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"832":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"573":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":5,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"293":{"tf":1.0},"576":{"tf":1.0},"784":{"tf":1.0}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":3,"docs":{"374":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"438":{"tf":1.0}}}}}}}},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"718":{"tf":1.0}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"450":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"111":{"tf":1.0},"429":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"44":{"tf":1.0}}}}}}}}}},"q":{"df":0,"docs":{},"u":{"df":14,"docs":{"147":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"338":{"tf":1.0},"414":{"tf":1.0},"429":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.7320508075688772},"524":{"tf":2.449489742783178},"525":{"tf":1.0},"810":{"tf":1.0},"880":{"tf":1.0}}}},"t":{"df":11,"docs":{"209":{"tf":1.0},"211":{"tf":1.0},"237":{"tf":1.0},"479":{"tf":1.0},"639":{"tf":1.0},"776":{"tf":1.0},"788":{"tf":1.0},"846":{"tf":1.0},"945":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"+":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"786":{"tf":1.4142135623730951}}}}}}}}}},"df":2,"docs":{"18":{"tf":1.0},"786":{"tf":1.0}}}}}},"x":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":9,"docs":{"195":{"tf":1.0},"213":{"tf":1.4142135623730951},"215":{"tf":1.0},"227":{"tf":1.0},"38":{"tf":1.0},"402":{"tf":1.0},"510":{"tf":1.0},"55":{"tf":1.0},"635":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"206":{"tf":1.0},"44":{"tf":1.0},"875":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"k":{"df":3,"docs":{"204":{"tf":1.0},"234":{"tf":1.0},"939":{"tf":1.0}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.0}}}}}},"o":{"c":{"df":0,"docs":{},"k":{"df":8,"docs":{"108":{"tf":1.0},"112":{"tf":2.0},"198":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.7320508075688772},"301":{"tf":2.0},"302":{"tf":1.0},"308":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":6,"docs":{"267":{"tf":1.0},"44":{"tf":1.0},"483":{"tf":1.0},"576":{"tf":1.0},"951":{"tf":1.0},"982":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"763":{"tf":1.0},"917":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"615":{"tf":1.0}},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"111":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"255":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"199":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"385":{"tf":1.0},"432":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"362":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"809":{"tf":1.0}}}}}},"l":{"df":3,"docs":{"513":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"705":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":1,"docs":{"852":{"tf":1.0}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":110,"docs":{"1":{"tf":1.0},"1000":{"tf":1.0},"1002":{"tf":1.0},"1014":{"tf":1.0},"106":{"tf":1.0},"121":{"tf":1.0},"122":{"tf":1.0},"134":{"tf":1.0},"136":{"tf":1.0},"148":{"tf":1.0},"15":{"tf":1.0},"150":{"tf":1.0},"162":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"180":{"tf":1.0},"182":{"tf":1.0},"193":{"tf":1.0},"229":{"tf":1.0},"245":{"tf":1.0},"247":{"tf":1.0},"261":{"tf":1.0},"268":{"tf":1.0},"278":{"tf":1.0},"279":{"tf":1.0},"292":{"tf":1.0},"294":{"tf":1.0},"309":{"tf":1.0},"311":{"tf":1.0},"320":{"tf":1.0},"322":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"366":{"tf":1.0},"384":{"tf":1.0},"386":{"tf":1.0},"398":{"tf":1.0},"410":{"tf":1.0},"425":{"tf":1.4142135623730951},"430":{"tf":1.0},"448":{"tf":1.0},"451":{"tf":1.0},"463":{"tf":1.0},"465":{"tf":1.0},"480":{"tf":1.0},"481":{"tf":1.0},"493":{"tf":1.0},"495":{"tf":1.0},"511":{"tf":1.0},"513":{"tf":1.0},"533":{"tf":1.0},"535":{"tf":1.0},"547":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"561":{"tf":1.0},"584":{"tf":1.0},"596":{"tf":1.0},"598":{"tf":1.0},"611":{"tf":1.0},"613":{"tf":1.0},"625":{"tf":1.0},"627":{"tf":1.0},"647":{"tf":1.0},"649":{"tf":1.0},"662":{"tf":1.0},"664":{"tf":1.0},"676":{"tf":1.0},"678":{"tf":1.0},"690":{"tf":1.0},"692":{"tf":1.0},"707":{"tf":1.0},"709":{"tf":1.0},"727":{"tf":1.0},"730":{"tf":1.0},"739":{"tf":1.0},"75":{"tf":1.0},"757":{"tf":1.0},"769":{"tf":1.0},"771":{"tf":1.0},"781":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"794":{"tf":1.0},"795":{"tf":1.0},"806":{"tf":1.0},"808":{"tf":1.0},"825":{"tf":1.0},"827":{"tf":1.0},"839":{"tf":1.0},"841":{"tf":1.0},"856":{"tf":1.0},"857":{"tf":1.0},"870":{"tf":1.0},"871":{"tf":1.0},"889":{"tf":1.0},"891":{"tf":1.0},"906":{"tf":1.0},"908":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"926":{"tf":1.0},"938":{"tf":1.0},"940":{"tf":1.0},"955":{"tf":1.0},"957":{"tf":1.0},"972":{"tf":1.0},"974":{"tf":1.0},"986":{"tf":1.0},"988":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"350":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}},"t":{"df":2,"docs":{"349":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":1,"docs":{"204":{"tf":1.0}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":9,"docs":{"166":{"tf":1.0},"177":{"tf":1.0},"332":{"tf":2.449489742783178},"333":{"tf":1.4142135623730951},"347":{"tf":1.0},"404":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.0},"545":{"tf":1.0}},"e":{"d":{"3":{"2":{"df":3,"docs":{"332":{"tf":1.0},"342":{"tf":1.0},"349":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":4,"docs":{"332":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.0}}},"<":{"1":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}},"3":{"2":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"573":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"d":{"df":3,"docs":{"776":{"tf":1.4142135623730951},"913":{"tf":1.0},"917":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"370":{"tf":1.0},"564":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"5":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":26,"docs":{"126":{"tf":1.0},"138":{"tf":1.0},"155":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":2.0},"255":{"tf":1.0},"301":{"tf":1.0},"323":{"tf":1.0},"436":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"573":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0},"648":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"253":{"tf":1.4142135623730951}}}}}}},"u":{"df":0,"docs":{},"s":{"df":9,"docs":{"206":{"tf":1.0},"254":{"tf":1.0},"346":{"tf":1.0},"401":{"tf":1.0},"517":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"638":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"115":{"tf":1.0},"123":{"tf":1.0},"128":{"tf":1.0},"134":{"tf":1.0},"304":{"tf":1.0},"788":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":5,"docs":{"208":{"tf":1.0},"60":{"tf":1.0},"743":{"tf":1.0},"776":{"tf":1.0},"914":{"tf":1.0}}}}},"d":{"a":{"df":0,"docs":{},"t":{"df":57,"docs":{"1003":{"tf":1.4142135623730951},"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0},"125":{"tf":1.0},"154":{"tf":1.0},"191":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"237":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"290":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"300":{"tf":1.0},"313":{"tf":1.0},"316":{"tf":1.0},"344":{"tf":1.0},"352":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"44":{"tf":1.0},"441":{"tf":1.0},"456":{"tf":1.0},"461":{"tf":1.7320508075688772},"465":{"tf":1.0},"472":{"tf":1.4142135623730951},"515":{"tf":1.0},"535":{"tf":1.0},"544":{"tf":1.0},"565":{"tf":1.0},"58":{"tf":1.0},"6":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0},"645":{"tf":1.0},"7":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.0},"78":{"tf":1.4142135623730951},"831":{"tf":1.0},"832":{"tf":1.0},"837":{"tf":1.7320508075688772},"848":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0},"928":{"tf":1.0},"937":{"tf":1.0},"965":{"tf":1.0},"973":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"237":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":55,"docs":{"124":{"tf":1.0},"140":{"tf":1.4142135623730951},"184":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"208":{"tf":1.0},"234":{"tf":1.4142135623730951},"249":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"315":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"375":{"tf":1.4142135623730951},"436":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"5":{"tf":1.0},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"515":{"tf":1.0},"518":{"tf":1.0},"521":{"tf":1.0},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0},"57":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.4142135623730951},"583":{"tf":1.0},"629":{"tf":1.0},"650":{"tf":1.0},"700":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"747":{"tf":1.0},"768":{"tf":1.0},"77":{"tf":1.0},"794":{"tf":1.0},"797":{"tf":1.4142135623730951},"829":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"858":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":56,"docs":{"1012":{"tf":1.0},"104":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.0},"132":{"tf":1.0},"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.7320508075688772},"140":{"tf":1.4142135623730951},"144":{"tf":1.4142135623730951},"147":{"tf":1.0},"150":{"tf":1.0},"151":{"tf":1.7320508075688772},"152":{"tf":1.0},"154":{"tf":1.4142135623730951},"159":{"tf":1.0},"160":{"tf":1.0},"193":{"tf":1.0},"209":{"tf":1.4142135623730951},"24":{"tf":1.0},"241":{"tf":1.0},"300":{"tf":1.0},"315":{"tf":1.0},"358":{"tf":1.0},"408":{"tf":1.0},"430":{"tf":1.0},"438":{"tf":1.0},"440":{"tf":3.0},"441":{"tf":1.0},"446":{"tf":1.4142135623730951},"515":{"tf":2.0},"56":{"tf":1.4142135623730951},"57":{"tf":1.7320508075688772},"58":{"tf":1.0},"60":{"tf":2.6457513110645907},"609":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.0},"642":{"tf":1.4142135623730951},"643":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.4142135623730951},"705":{"tf":1.0},"71":{"tf":2.449489742783178},"72":{"tf":2.0},"729":{"tf":1.0},"73":{"tf":2.23606797749979},"74":{"tf":1.0},"75":{"tf":1.7320508075688772},"751":{"tf":1.0},"77":{"tf":1.7320508075688772},"78":{"tf":1.0},"817":{"tf":1.0},"887":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"467":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":5,"docs":{"715":{"tf":1.0},"722":{"tf":1.0},"763":{"tf":1.0},"817":{"tf":1.0},"832":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"715":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":13,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"314":{"tf":1.0},"356":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.0},"773":{"tf":1.0},"810":{"tf":1.0},"928":{"tf":1.0}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":3,"docs":{"436":{"tf":1.0},"51":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}},"r":{"a":{"d":{"df":1,"docs":{"60":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"633":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"54":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":5,"docs":{"250":{"tf":1.0},"565":{"tf":1.0},"614":{"tf":1.0},"696":{"tf":1.0},"698":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":28,"docs":{"1011":{"tf":1.0},"154":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":2.23606797749979},"204":{"tf":1.0},"208":{"tf":1.0},"215":{"tf":1.4142135623730951},"218":{"tf":1.0},"22":{"tf":1.0},"223":{"tf":1.0},"24":{"tf":1.4142135623730951},"267":{"tf":1.0},"28":{"tf":1.0},"407":{"tf":1.0},"428":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"52":{"tf":1.0},"598":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"696":{"tf":1.0},"700":{"tf":1.0},"722":{"tf":1.0},"758":{"tf":1.0},"913":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}}}},"d":{"(":{"df":0,"docs":{},"x":{"df":2,"docs":{"410":{"tf":1.0},"429":{"tf":1.0}}}},"df":2,"docs":{"429":{"tf":1.4142135623730951},"470":{"tf":1.4142135623730951}},"t":{"df":3,"docs":{"470":{"tf":1.7320508075688772},"600":{"tf":1.0},"699":{"tf":1.0}}}},"df":236,"docs":{"100":{"tf":1.0},"103":{"tf":1.0},"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.4142135623730951},"126":{"tf":1.0},"140":{"tf":1.4142135623730951},"149":{"tf":1.0},"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"16":{"tf":1.4142135623730951},"160":{"tf":1.0},"163":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":2.0},"177":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"191":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":2.0},"226":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"248":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"251":{"tf":1.0},"252":{"tf":1.7320508075688772},"253":{"tf":1.4142135623730951},"254":{"tf":2.0},"255":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.4142135623730951},"261":{"tf":1.0},"281":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"3":{"tf":2.0},"30":{"tf":1.0},"303":{"tf":1.0},"331":{"tf":1.0},"333":{"tf":1.4142135623730951},"338":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.7320508075688772},"345":{"tf":1.7320508075688772},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"349":{"tf":2.23606797749979},"35":{"tf":1.0},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"352":{"tf":1.0},"368":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.4142135623730951},"378":{"tf":1.0},"38":{"tf":1.0},"384":{"tf":1.0},"387":{"tf":2.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.4142135623730951},"390":{"tf":2.449489742783178},"391":{"tf":1.0},"393":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"415":{"tf":1.0},"420":{"tf":1.0},"428":{"tf":1.0},"432":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.7320508075688772},"44":{"tf":1.0},"440":{"tf":1.4142135623730951},"441":{"tf":1.4142135623730951},"444":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"46":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"472":{"tf":1.0},"473":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"5":{"tf":1.4142135623730951},"50":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"51":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":2.0},"516":{"tf":1.0},"519":{"tf":1.0},"52":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":2.449489742783178},"522":{"tf":1.7320508075688772},"524":{"tf":1.7320508075688772},"525":{"tf":1.7320508075688772},"526":{"tf":1.7320508075688772},"528":{"tf":1.4142135623730951},"530":{"tf":1.4142135623730951},"531":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.7320508075688772},"559":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.4142135623730951},"571":{"tf":1.7320508075688772},"588":{"tf":1.4142135623730951},"594":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":3.0},"600":{"tf":2.0},"602":{"tf":3.4641016151377544},"603":{"tf":1.0},"605":{"tf":1.0},"609":{"tf":1.4142135623730951},"61":{"tf":1.0},"615":{"tf":2.23606797749979},"617":{"tf":1.0},"619":{"tf":1.0},"62":{"tf":1.4142135623730951},"629":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":2.6457513110645907},"634":{"tf":1.4142135623730951},"635":{"tf":1.4142135623730951},"637":{"tf":1.0},"64":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"648":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.7320508075688772},"653":{"tf":2.23606797749979},"654":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"67":{"tf":1.0},"680":{"tf":1.0},"688":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"697":{"tf":1.7320508075688772},"699":{"tf":1.4142135623730951},"7":{"tf":1.0},"701":{"tf":1.4142135623730951},"705":{"tf":1.7320508075688772},"710":{"tf":1.4142135623730951},"715":{"tf":2.23606797749979},"716":{"tf":2.0},"717":{"tf":1.4142135623730951},"721":{"tf":2.6457513110645907},"722":{"tf":2.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":2.23606797749979},"735":{"tf":2.449489742783178},"736":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"749":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.7320508075688772},"765":{"tf":1.0},"770":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"783":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"8":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"822":{"tf":1.0},"83":{"tf":1.4142135623730951},"831":{"tf":1.7320508075688772},"858":{"tf":1.7320508075688772},"859":{"tf":1.0},"870":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.0},"876":{"tf":1.7320508075688772},"880":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"894":{"tf":1.4142135623730951},"895":{"tf":2.8284271247461903},"897":{"tf":1.0},"898":{"tf":1.0},"902":{"tf":1.0},"909":{"tf":1.0},"911":{"tf":1.4142135623730951},"912":{"tf":1.7320508075688772},"913":{"tf":1.7320508075688772},"914":{"tf":1.0},"919":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.23606797749979},"933":{"tf":1.4142135623730951},"935":{"tf":1.0},"938":{"tf":1.4142135623730951},"95":{"tf":2.449489742783178},"952":{"tf":1.0},"961":{"tf":1.4142135623730951},"964":{"tf":1.0},"969":{"tf":1.0},"971":{"tf":1.4142135623730951},"973":{"tf":1.0},"983":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{}},"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":3,"docs":{"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":4,"docs":{"663":{"tf":1.0},"670":{"tf":1.0},"722":{"tf":1.0},"987":{"tf":1.0}}}}}},"r":{"'":{"df":3,"docs":{"170":{"tf":1.0},"375":{"tf":1.0},"568":{"tf":1.0}}},"df":99,"docs":{"1007":{"tf":1.0},"1011":{"tf":1.0},"108":{"tf":1.0},"109":{"tf":1.4142135623730951},"131":{"tf":1.0},"152":{"tf":1.0},"167":{"tf":1.0},"169":{"tf":1.0},"17":{"tf":1.0},"171":{"tf":1.4142135623730951},"173":{"tf":1.0},"19":{"tf":1.0},"201":{"tf":1.0},"231":{"tf":1.0},"238":{"tf":1.0},"284":{"tf":1.0},"29":{"tf":1.0},"290":{"tf":1.0},"298":{"tf":1.0},"3":{"tf":1.4142135623730951},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"38":{"tf":1.0},"381":{"tf":1.0},"4":{"tf":1.0},"40":{"tf":1.7320508075688772},"414":{"tf":1.0},"418":{"tf":1.0},"423":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"453":{"tf":1.0},"456":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":1.7320508075688772},"526":{"tf":1.0},"528":{"tf":1.4142135623730951},"537":{"tf":1.4142135623730951},"538":{"tf":1.0},"544":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"568":{"tf":2.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951},"571":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.7320508075688772},"575":{"tf":1.0},"576":{"tf":2.23606797749979},"577":{"tf":1.0},"581":{"tf":1.0},"587":{"tf":1.0},"601":{"tf":1.0},"608":{"tf":1.0},"614":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"659":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.4142135623730951},"700":{"tf":1.0},"72":{"tf":1.4142135623730951},"774":{"tf":1.0},"784":{"tf":1.4142135623730951},"799":{"tf":1.4142135623730951},"8":{"tf":1.0},"81":{"tf":1.7320508075688772},"814":{"tf":1.0},"82":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.7320508075688772},"874":{"tf":2.23606797749979},"878":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.7320508075688772},"886":{"tf":1.0},"895":{"tf":2.6457513110645907},"898":{"tf":1.0},"902":{"tf":1.0},"914":{"tf":1.0},"920":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":2.0},"943":{"tf":1.0},"944":{"tf":1.0},"95":{"tf":1.4142135623730951},"952":{"tf":1.0},"956":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0},"977":{"tf":1.0},"979":{"tf":1.4142135623730951},"983":{"tf":1.0},"991":{"tf":1.0}}}},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"455":{"tf":1.0}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"3":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"573":{"tf":1.4142135623730951},"6":{"tf":1.0},"749":{"tf":1.0},"859":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"c":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":26,"docs":{"1004":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.4142135623730951},"24":{"tf":1.0},"267":{"tf":1.4142135623730951},"289":{"tf":1.0},"3":{"tf":1.0},"335":{"tf":1.0},"35":{"tf":1.0},"400":{"tf":1.4142135623730951},"401":{"tf":1.0},"402":{"tf":1.0},"404":{"tf":1.0},"423":{"tf":1.0},"517":{"tf":1.0},"52":{"tf":1.0},"773":{"tf":1.0},"813":{"tf":1.0},"860":{"tf":1.0},"876":{"tf":1.0},"919":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"991":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"x":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":3,"docs":{"563":{"tf":1.0},"574":{"tf":1.0},"581":{"tf":1.0}}}}},"df":8,"docs":{"249":{"tf":1.0},"55":{"tf":1.4142135623730951},"564":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"599":{"tf":1.0},"602":{"tf":1.0},"615":{"tf":1.4142135623730951}}}},"v":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"717":{"tf":1.0}}}}}}},"0":{"df":1,"docs":{"390":{"tf":1.4142135623730951}}},"1":{".":{"1":{".":{"1":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"163":{"tf":1.0},"390":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"520":{"tf":1.0},"526":{"tf":1.4142135623730951}}},"2":{".":{"0":{"df":1,"docs":{"390":{"tf":1.0}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.0}}}}}}}},"/":{"3":{"7":{"3":{"8":{"df":1,"docs":{"646":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"126":{"tf":1.4142135623730951},"439":{"tf":1.0}}},"3":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"4":{"df":2,"docs":{"169":{"tf":1.0},"172":{"tf":1.0}}},"5":{"df":4,"docs":{"170":{"tf":1.7320508075688772},"171":{"tf":1.0},"172":{"tf":1.7320508075688772},"984":{"tf":1.0}}},"6":{"df":1,"docs":{"984":{"tf":1.0}}},"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"410":{"tf":1.0}},"i":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"62":{"tf":1.0}}}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"711":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"814":{"tf":1.0}},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"814":{"tf":1.0}},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"634":{"tf":1.0},"817":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"233":{"tf":1.0}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"438":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":4,"docs":{"432":{"tf":1.4142135623730951},"438":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"440":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":113,"docs":{"1003":{"tf":1.4142135623730951},"1004":{"tf":2.6457513110645907},"1005":{"tf":1.0},"142":{"tf":1.0},"155":{"tf":1.4142135623730951},"205":{"tf":1.0},"231":{"tf":2.0},"232":{"tf":1.0},"248":{"tf":1.0},"296":{"tf":1.0},"322":{"tf":1.4142135623730951},"336":{"tf":1.0},"337":{"tf":2.0},"338":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.7320508075688772},"347":{"tf":2.23606797749979},"350":{"tf":1.0},"356":{"tf":1.0},"368":{"tf":1.7320508075688772},"372":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"38":{"tf":1.7320508075688772},"39":{"tf":1.7320508075688772},"430":{"tf":1.7320508075688772},"431":{"tf":1.0},"432":{"tf":1.7320508075688772},"436":{"tf":1.7320508075688772},"437":{"tf":1.0},"438":{"tf":1.4142135623730951},"439":{"tf":2.8284271247461903},"44":{"tf":1.7320508075688772},"440":{"tf":2.6457513110645907},"441":{"tf":1.0},"446":{"tf":1.0},"45":{"tf":2.449489742783178},"450":{"tf":2.6457513110645907},"452":{"tf":1.7320508075688772},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":2.449489742783178},"47":{"tf":3.0},"49":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":3.1622776601683795},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"588":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.4142135623730951},"627":{"tf":1.7320508075688772},"628":{"tf":1.0},"629":{"tf":3.0},"63":{"tf":2.6457513110645907},"632":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"636":{"tf":1.4142135623730951},"64":{"tf":1.0},"642":{"tf":1.7320508075688772},"644":{"tf":2.0},"65":{"tf":1.4142135623730951},"66":{"tf":1.4142135623730951},"67":{"tf":1.7320508075688772},"69":{"tf":2.0},"709":{"tf":1.7320508075688772},"71":{"tf":1.4142135623730951},"710":{"tf":1.4142135623730951},"711":{"tf":2.449489742783178},"712":{"tf":1.7320508075688772},"714":{"tf":1.4142135623730951},"715":{"tf":2.449489742783178},"716":{"tf":2.0},"717":{"tf":2.0},"718":{"tf":1.4142135623730951},"720":{"tf":1.0},"721":{"tf":3.872983346207417},"722":{"tf":3.0},"723":{"tf":1.4142135623730951},"724":{"tf":2.449489742783178},"725":{"tf":1.0},"729":{"tf":1.7320508075688772},"73":{"tf":2.0},"75":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":2.0},"799":{"tf":1.0},"810":{"tf":1.7320508075688772},"811":{"tf":2.0},"813":{"tf":1.4142135623730951},"814":{"tf":2.23606797749979},"815":{"tf":2.449489742783178},"816":{"tf":1.0},"817":{"tf":2.0},"818":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"894":{"tf":1.0},"929":{"tf":1.0},"948":{"tf":1.0},"964":{"tf":1.0},"97":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"67":{"tf":1.0}}}}},"df":0,"docs":{}},"u":{"a":{"b":{"df":0,"docs":{},"l":{"df":7,"docs":{"12":{"tf":1.0},"3":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"51":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"777":{"tf":1.4142135623730951}}}},"df":75,"docs":{"154":{"tf":1.0},"163":{"tf":1.0},"196":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"207":{"tf":2.449489742783178},"208":{"tf":2.0},"221":{"tf":2.23606797749979},"222":{"tf":1.4142135623730951},"24":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.0},"254":{"tf":1.0},"257":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.4142135623730951},"270":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":2.0},"347":{"tf":1.4142135623730951},"376":{"tf":1.0},"393":{"tf":1.0},"404":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":2.0},"418":{"tf":1.0},"429":{"tf":2.23606797749979},"439":{"tf":1.4142135623730951},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"467":{"tf":1.0},"469":{"tf":1.0},"485":{"tf":1.0},"5":{"tf":2.0},"501":{"tf":1.4142135623730951},"507":{"tf":1.0},"526":{"tf":1.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.0},"6":{"tf":3.0},"615":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"634":{"tf":1.0},"640":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":5.196152422706632},"743":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":1.0},"759":{"tf":3.605551275463989},"761":{"tf":2.6457513110645907},"763":{"tf":1.0},"818":{"tf":1.4142135623730951},"819":{"tf":1.4142135623730951},"828":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":2.0},"832":{"tf":1.0},"833":{"tf":1.0},"880":{"tf":1.0},"891":{"tf":1.7320508075688772},"892":{"tf":1.0},"895":{"tf":1.4142135623730951},"896":{"tf":1.0},"898":{"tf":1.0},"9":{"tf":1.0},"907":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}},"e":{"<":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"735":{"tf":3.1622776601683795}}}}}},"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"6":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"6":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"721":{"tf":1.0}}}}}}}}}}},"r":{"df":0,"docs":{},"i":{"a":{"b":{"df":0,"docs":{},"l":{"df":12,"docs":{"253":{"tf":1.0},"267":{"tf":1.0},"332":{"tf":1.4142135623730951},"346":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"51":{"tf":1.0},"568":{"tf":1.4142135623730951},"576":{"tf":1.0},"751":{"tf":1.0},"831":{"tf":1.4142135623730951},"846":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":16,"docs":{"166":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.4142135623730951},"249":{"tf":1.0},"340":{"tf":1.4142135623730951},"388":{"tf":1.4142135623730951},"517":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":2.23606797749979},"524":{"tf":2.0},"525":{"tf":1.0},"6":{"tf":1.7320508075688772},"668":{"tf":1.4142135623730951},"7":{"tf":1.4142135623730951},"776":{"tf":1.0}}}},"t":{"df":1,"docs":{"571":{"tf":1.0}}}},"df":5,"docs":{"19":{"tf":1.0},"204":{"tf":1.0},"231":{"tf":1.0},"418":{"tf":1.0},"634":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":13,"docs":{"19":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.4142135623730951},"555":{"tf":1.0},"771":{"tf":1.0},"964":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"237":{"tf":1.0},"697":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"779":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"515":{"tf":1.0}}}}}},"df":11,"docs":{"346":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0},"539":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":2.23606797749979},"722":{"tf":1.7320508075688772},"723":{"tf":1.7320508075688772},"735":{"tf":1.0}},"e":{"c":{"!":{"[":{"(":{"a":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":2,"docs":{"524":{"tf":1.0},"717":{"tf":1.0}}}}}},"df":0,"docs":{}},"<":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"602":{"tf":1.0},"698":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"992":{"tf":1.4142135623730951}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"522":{"tf":1.0}}}}},"t":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"885":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"482":{"tf":1.0},"483":{"tf":1.7320508075688772},"485":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"3":{"2":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":5,"docs":{"22":{"tf":2.0},"439":{"tf":1.4142135623730951},"455":{"tf":2.0},"62":{"tf":1.0},"633":{"tf":1.0}}},"df":0,"docs":{}}},"[":{"0":{"df":0,"docs":{},"u":{"6":{"4":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":8,"docs":{"208":{"tf":3.0},"22":{"tf":1.7320508075688772},"482":{"tf":1.0},"485":{"tf":1.0},"603":{"tf":1.4142135623730951},"633":{"tf":1.0},"83":{"tf":1.0},"933":{"tf":1.0}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"114":{"tf":1.0},"124":{"tf":1.0},"332":{"tf":1.0},"522":{"tf":1.7320508075688772},"63":{"tf":1.0},"670":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"y":{"a":{"df":1,"docs":{"386":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":36,"docs":{"108":{"tf":1.0},"184":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"221":{"tf":1.0},"238":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"255":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.4142135623730951},"346":{"tf":1.0},"381":{"tf":1.0},"418":{"tf":1.0},"438":{"tf":1.0},"441":{"tf":1.0},"486":{"tf":1.0},"499":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"659":{"tf":1.0},"687":{"tf":1.0},"732":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.7320508075688772},"776":{"tf":1.0},"779":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"932":{"tf":1.0},"939":{"tf":1.0}},"f":{"df":18,"docs":{"103":{"tf":1.0},"111":{"tf":1.0},"322":{"tf":1.0},"341":{"tf":1.7320508075688772},"343":{"tf":1.0},"350":{"tf":1.7320508075688772},"351":{"tf":1.0},"388":{"tf":1.0},"453":{"tf":1.0},"457":{"tf":1.0},"459":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.4142135623730951},"97":{"tf":1.0}},"i":{"df":34,"docs":{"113":{"tf":1.0},"254":{"tf":1.0},"341":{"tf":1.0},"344":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.7320508075688772},"351":{"tf":1.0},"388":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"459":{"tf":1.0},"46":{"tf":1.4142135623730951},"49":{"tf":1.0},"514":{"tf":1.0},"531":{"tf":1.0},"537":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"811":{"tf":1.0},"817":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.4142135623730951},"93":{"tf":1.7320508075688772},"94":{"tf":1.0},"944":{"tf":1.0}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"s":{"a":{"df":1,"docs":{"559":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":2,"docs":{"555":{"tf":1.0},"639":{"tf":1.0}},"o":{"df":0,"docs":{},"n":{"df":70,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"154":{"tf":1.0},"16":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":2.23606797749979},"165":{"tf":1.4142135623730951},"166":{"tf":1.7320508075688772},"170":{"tf":2.8284271247461903},"171":{"tf":1.0},"172":{"tf":1.7320508075688772},"173":{"tf":1.0},"175":{"tf":1.4142135623730951},"178":{"tf":2.0},"180":{"tf":2.23606797749979},"181":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"280":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"386":{"tf":2.0},"387":{"tf":1.4142135623730951},"388":{"tf":1.0},"390":{"tf":3.3166247903554},"439":{"tf":2.0},"440":{"tf":2.449489742783178},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"461":{"tf":1.0},"486":{"tf":1.0},"516":{"tf":1.4142135623730951},"520":{"tf":1.4142135623730951},"521":{"tf":2.0},"526":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":2.23606797749979},"540":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"584":{"tf":1.7320508075688772},"585":{"tf":1.0},"586":{"tf":1.4142135623730951},"588":{"tf":2.449489742783178},"593":{"tf":1.7320508075688772},"594":{"tf":1.0},"609":{"tf":2.0},"619":{"tf":1.4142135623730951},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":2.0},"635":{"tf":2.8284271247461903},"636":{"tf":1.0},"637":{"tf":1.4142135623730951},"644":{"tf":1.0},"648":{"tf":1.7320508075688772},"653":{"tf":1.0},"705":{"tf":1.7320508075688772},"735":{"tf":5.916079783099616},"740":{"tf":1.0},"767":{"tf":1.0},"804":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"878":{"tf":1.0},"894":{"tf":1.0},"953":{"tf":1.0},"984":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"414":{"tf":1.0}}}}},"i":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"54":{"tf":1.0}}}},"l":{"df":4,"docs":{"810":{"tf":1.0},"831":{"tf":1.0},"913":{"tf":1.0},"942":{"tf":1.0}}}},"df":50,"docs":{"1":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"12":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"126":{"tf":1.0},"141":{"tf":1.0},"191":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.4142135623730951},"21":{"tf":1.0},"22":{"tf":1.0},"241":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"28":{"tf":1.0},"3":{"tf":2.0},"358":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.4142135623730951},"446":{"tf":1.0},"45":{"tf":1.0},"472":{"tf":1.0},"5":{"tf":1.0},"55":{"tf":1.0},"573":{"tf":1.4142135623730951},"6":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"66":{"tf":1.0},"680":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.0},"800":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.0},"879":{"tf":1.0},"887":{"tf":1.0},"932":{"tf":1.0},"959":{"tf":1.0}}},"b":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"412":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"411":{"tf":1.0}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"e":{"df":1,"docs":{"559":{"tf":1.0}}}},"df":3,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"w":{"df":4,"docs":{"201":{"tf":1.0},"21":{"tf":1.4142135623730951},"35":{"tf":1.7320508075688772},"6":{"tf":1.0}}}},"i":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}},"i":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}}}},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"410":{"tf":1.0}}}},"o":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"284":{"tf":1.0},"724":{"tf":1.0},"849":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"198":{"tf":1.0},"735":{"tf":3.4641016151377544}}}},"df":1,"docs":{"205":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"40":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"170":{"tf":1.0},"525":{"tf":1.4142135623730951},"742":{"tf":1.0},"756":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"324":{"tf":1.0},"422":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"218":{"tf":1.0}}}},"o":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"373":{"tf":1.0},"376":{"tf":1.0}}},"d":{"df":2,"docs":{"273":{"tf":1.0},"522":{"tf":2.449489742783178}}},"df":0,"docs":{}},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":2,"docs":{"267":{"tf":1.7320508075688772},"418":{"tf":1.0}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"418":{"tf":1.0},"912":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":32,"docs":{"1004":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":1.0},"188":{"tf":1.0},"234":{"tf":1.4142135623730951},"296":{"tf":1.0},"370":{"tf":1.0},"375":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":2.23606797749979},"563":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":2.23606797749979},"629":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":2.6457513110645907},"722":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.0},"727":{"tf":1.0},"729":{"tf":1.4142135623730951},"75":{"tf":1.0},"795":{"tf":1.7320508075688772},"796":{"tf":3.3166247903554},"797":{"tf":2.23606797749979},"799":{"tf":4.358898943540674},"973":{"tf":1.0}},"r":{"df":6,"docs":{"127":{"tf":1.0},"234":{"tf":1.0},"575":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":2,"docs":{"346":{"tf":1.0},"349":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"341":{"tf":1.0},"349":{"tf":1.4142135623730951}},"e":{"d":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"350":{"tf":1.0},"351":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":2,"docs":{"341":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}}}}}},"df":11,"docs":{"126":{"tf":1.0},"131":{"tf":1.0},"133":{"tf":1.0},"322":{"tf":1.4142135623730951},"340":{"tf":2.6457513110645907},"341":{"tf":3.605551275463989},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951},"359":{"tf":1.7320508075688772}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"341":{"tf":2.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"s":{"df":4,"docs":{"187":{"tf":1.0},"427":{"tf":1.0},"48":{"tf":1.0},"553":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"127":{"tf":1.0},"142":{"tf":1.0},"231":{"tf":1.0},"711":{"tf":1.0},"945":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0}}}}}}},"·":{"2":{"/":{"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"w":{"3":{"c":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}},"df":0,"docs":{},"f":{"df":3,"docs":{"359":{"tf":1.0},"843":{"tf":1.0},"931":{"tf":1.0}}}},"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":2,"docs":{"467":{"tf":1.0},"479":{"tf":1.0}}}},"h":{"df":1,"docs":{"603":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":13,"docs":{"207":{"tf":1.4142135623730951},"554":{"tf":1.0},"573":{"tf":1.4142135623730951},"576":{"tf":1.0},"63":{"tf":1.4142135623730951},"642":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"837":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"942":{"tf":1.0}}}},"l":{"df":0,"docs":{},"k":{"df":1,"docs":{"759":{"tf":1.0}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":28,"docs":{"167":{"tf":1.0},"18":{"tf":1.0},"191":{"tf":1.0},"33":{"tf":1.0},"4":{"tf":1.0},"514":{"tf":3.0},"515":{"tf":2.0},"518":{"tf":1.7320508075688772},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"526":{"tf":1.4142135623730951},"527":{"tf":1.0},"528":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"538":{"tf":1.0},"587":{"tf":1.0},"601":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"804":{"tf":1.4142135623730951},"82":{"tf":1.0},"853":{"tf":1.0},"977":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":1,"docs":{"30":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"t":{"df":34,"docs":{"121":{"tf":1.4142135623730951},"154":{"tf":1.0},"171":{"tf":1.0},"193":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.7320508075688772},"255":{"tf":1.0},"273":{"tf":1.0},"387":{"tf":1.0},"42":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"497":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"60":{"tf":1.0},"603":{"tf":1.0},"61":{"tf":1.0},"635":{"tf":1.0},"673":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"711":{"tf":1.0},"752":{"tf":1.0},"780":{"tf":1.0},"804":{"tf":1.0},"826":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.4142135623730951},"895":{"tf":1.0},"934":{"tf":1.0},"960":{"tf":1.0}}}},"r":{"df":0,"docs":{},"p":{"df":5,"docs":{"500":{"tf":1.4142135623730951},"503":{"tf":1.4142135623730951},"770":{"tf":1.0},"992":{"tf":1.0},"996":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"121":{"tf":1.0},"46":{"tf":1.0}}}}},"df":0,"docs":{}},"t":{"df":1,"docs":{"486":{"tf":1.0}}}},"s":{"df":0,"docs":{},"m":{"/":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":3,"docs":{"296":{"tf":1.7320508075688772},"297":{"tf":1.4142135623730951},"303":{"tf":1.0}}}}}}}}},"df":9,"docs":{"111":{"tf":1.0},"288":{"tf":1.0},"300":{"tf":1.0},"303":{"tf":1.0},"35":{"tf":1.0},"732":{"tf":1.0},"829":{"tf":2.23606797749979},"831":{"tf":2.0},"832":{"tf":1.4142135623730951}}},"t":{"df":10,"docs":{"124":{"tf":1.0},"346":{"tf":1.0},"374":{"tf":1.0},"60":{"tf":1.0},"71":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"77":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.0}}}},"y":{"df":75,"docs":{"1":{"tf":1.0},"112":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.4142135623730951},"134":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"154":{"tf":1.4142135623730951},"159":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"296":{"tf":1.0},"3":{"tf":2.23606797749979},"303":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"397":{"tf":1.0},"402":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"483":{"tf":1.0},"505":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":2.0},"518":{"tf":1.0},"522":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"551":{"tf":1.0},"555":{"tf":1.0},"573":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.4142135623730951},"602":{"tf":1.0},"628":{"tf":1.7320508075688772},"629":{"tf":1.0},"633":{"tf":1.4142135623730951},"648":{"tf":1.0},"651":{"tf":1.7320508075688772},"66":{"tf":1.4142135623730951},"693":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"78":{"tf":1.0},"807":{"tf":1.4142135623730951},"811":{"tf":1.0},"817":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.0},"847":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"874":{"tf":2.0},"912":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":2.23606797749979},"976":{"tf":1.0},"983":{"tf":1.0}}}},"df":5,"docs":{"45":{"tf":1.0},"47":{"tf":2.0},"51":{"tf":1.0},"722":{"tf":1.7320508075688772},"723":{"tf":2.23606797749979}},"e":{"'":{"d":{"df":1,"docs":{"779":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":5,"docs":{"603":{"tf":1.0},"711":{"tf":1.0},"725":{"tf":1.0},"846":{"tf":1.0},"874":{"tf":1.4142135623730951}}}},"r":{"df":7,"docs":{"711":{"tf":1.0},"831":{"tf":1.0},"835":{"tf":1.0},"852":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0}}},"v":{"df":5,"docs":{"573":{"tf":1.0},"615":{"tf":1.4142135623730951},"680":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0}}}},"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"410":{"tf":1.0},"427":{"tf":1.4142135623730951}}}},"b":{"2":{"df":1,"docs":{"895":{"tf":1.4142135623730951}}},"3":{"df":5,"docs":{"211":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"42":{"tf":1.0},"895":{"tf":1.7320508075688772}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"198":{"tf":1.0}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":2.0}}}}}}},"df":1,"docs":{"95":{"tf":2.23606797749979}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"k":{"df":6,"docs":{"140":{"tf":1.0},"204":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"777":{"tf":1.0},"843":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":2,"docs":{"617":{"tf":1.7320508075688772},"619":{"tf":1.4142135623730951}},"t":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"654":{"tf":1.0}}}}}}}},"df":24,"docs":{"1003":{"tf":1.0},"108":{"tf":1.0},"18":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"23":{"tf":1.0},"30":{"tf":1.4142135623730951},"388":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":2.23606797749979},"404":{"tf":1.0},"409":{"tf":1.0},"575":{"tf":1.7320508075688772},"602":{"tf":1.0},"614":{"tf":1.7320508075688772},"615":{"tf":1.7320508075688772},"617":{"tf":1.0},"619":{"tf":1.7320508075688772},"650":{"tf":1.0},"669":{"tf":1.0},"717":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"885":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"844":{"tf":1.0},"870":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"df":40,"docs":{"1008":{"tf":1.0},"1015":{"tf":1.0},"107":{"tf":1.0},"166":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.7320508075688772},"209":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"249":{"tf":1.0},"375":{"tf":1.0},"455":{"tf":1.0},"48":{"tf":1.0},"515":{"tf":1.0},"523":{"tf":1.0},"526":{"tf":1.4142135623730951},"532":{"tf":1.0},"602":{"tf":1.0},"68":{"tf":1.0},"712":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"742":{"tf":1.0},"75":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"78":{"tf":1.0},"804":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"941":{"tf":1.0},"947":{"tf":1.0},"961":{"tf":1.0}}}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"255":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}}}},"df":9,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"304":{"tf":1.0},"603":{"tf":1.7320508075688772},"639":{"tf":1.0},"678":{"tf":1.0},"679":{"tf":1.0},"682":{"tf":1.0}}},"df":0,"docs":{}}}}}},"h":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"724":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":6,"docs":{"71":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"199":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"315":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":2,"docs":{"203":{"tf":1.0},"205":{"tf":1.0}}},"b":{"df":0,"docs":{},"i":{"df":4,"docs":{"198":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":22,"docs":{"126":{"tf":1.0},"127":{"tf":1.0},"177":{"tf":1.0},"255":{"tf":1.0},"273":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"364":{"tf":1.0},"439":{"tf":1.0},"472":{"tf":1.0},"49":{"tf":1.0},"526":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"849":{"tf":1.0},"870":{"tf":1.0},"913":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"992":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"912":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"194":{"tf":1.0},"272":{"tf":1.0},"83":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"c":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"112":{"tf":1.0},"121":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"272":{"tf":1.0}}}}}}}}}}}}}}},"o":{"/":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"848":{"tf":1.0},"849":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"e":{"df":7,"docs":{"204":{"tf":1.0},"231":{"tf":1.0},"5":{"tf":1.0},"537":{"tf":1.0},"571":{"tf":1.0},"697":{"tf":1.0},"715":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"df":2,"docs":{"715":{"tf":1.0},"723":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":13,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.0},"469":{"tf":1.0},"500":{"tf":1.0},"502":{"tf":1.0},"505":{"tf":1.0},"567":{"tf":1.0},"715":{"tf":1.0},"761":{"tf":1.7320508075688772}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":4,"docs":{"519":{"tf":1.0},"874":{"tf":1.0},"895":{"tf":1.0},"95":{"tf":1.4142135623730951}},"r":{"df":2,"docs":{"199":{"tf":1.0},"973":{"tf":1.0}}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"848":{"tf":1.0}}}},"l":{"d":{"(":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}},"df":3,"docs":{"701":{"tf":1.0},"705":{"tf":1.0},"77":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"l":{"df":3,"docs":{"416":{"tf":1.0},"659":{"tf":1.0},"858":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"574":{"tf":1.0},"576":{"tf":1.0},"777":{"tf":1.0}}}}}}},"n":{"d":{"df":1,"docs":{"712":{"tf":1.0}},"o":{"df":0,"docs":{},"w":{"df":6,"docs":{"39":{"tf":1.4142135623730951},"40":{"tf":1.0},"42":{"tf":1.0},"47":{"tf":1.4142135623730951},"55":{"tf":1.4142135623730951},"563":{"tf":1.0}}}}},"df":2,"docs":{"346":{"tf":1.7320508075688772},"879":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"777":{"tf":1.0}}},"df":0,"docs":{}}}}},"p":{"df":1,"docs":{"932":{"tf":1.0}}},"r":{"df":0,"docs":{},"e":{"df":2,"docs":{"485":{"tf":1.0},"761":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":5,"docs":{"190":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"724":{"tf":1.0},"874":{"tf":1.0}}},"h":{"df":12,"docs":{"185":{"tf":1.0},"193":{"tf":1.0},"272":{"tf":1.0},"776":{"tf":1.0},"799":{"tf":1.0},"897":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"914":{"tf":1.0},"917":{"tf":1.0},"928":{"tf":1.0},"943":{"tf":1.0}}}},"t":{"df":4,"docs":{"46":{"tf":1.4142135623730951},"83":{"tf":2.23606797749979},"84":{"tf":1.4142135623730951},"88":{"tf":1.0}},"h":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"786":{"tf":1.4142135623730951},"793":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":2,"docs":{"602":{"tf":1.0},"979":{"tf":1.0}}}}}}},"df":8,"docs":{"516":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"983":{"tf":1.0},"987":{"tf":1.0}},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"n":{"df":43,"docs":{"126":{"tf":1.0},"196":{"tf":1.0},"207":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.0},"28":{"tf":1.0},"3":{"tf":1.7320508075688772},"30":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0},"340":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.7320508075688772},"352":{"tf":1.0},"373":{"tf":1.4142135623730951},"414":{"tf":1.0},"46":{"tf":1.4142135623730951},"485":{"tf":1.0},"511":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"539":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"699":{"tf":1.0},"735":{"tf":1.4142135623730951},"773":{"tf":2.0},"777":{"tf":1.0},"81":{"tf":1.0},"85":{"tf":1.0},"928":{"tf":1.0},"949":{"tf":1.0},"971":{"tf":1.0}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":58,"docs":{"1004":{"tf":1.0},"113":{"tf":1.0},"12":{"tf":1.0},"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"198":{"tf":1.0},"217":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"262":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.4142135623730951},"303":{"tf":1.4142135623730951},"308":{"tf":1.0},"349":{"tf":1.0},"387":{"tf":1.0},"418":{"tf":1.0},"435":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"551":{"tf":1.0},"555":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.0},"593":{"tf":1.0},"6":{"tf":1.0},"619":{"tf":1.4142135623730951},"628":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":1.0},"705":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"778":{"tf":1.0},"811":{"tf":1.0},"816":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"835":{"tf":1.0},"837":{"tf":1.4142135623730951},"881":{"tf":1.0},"929":{"tf":1.0},"939":{"tf":1.0},"953":{"tf":1.0},"992":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"84":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"o":{"df":1,"docs":{"555":{"tf":1.0}},"n":{"'":{"df":0,"docs":{},"t":{"df":3,"docs":{"399":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"d":{"df":5,"docs":{"195":{"tf":1.0},"215":{"tf":1.0},"366":{"tf":1.0},"465":{"tf":1.0},"807":{"tf":1.0}}},"df":0,"docs":{}},"r":{"d":{"df":9,"docs":{"345":{"tf":1.0},"438":{"tf":1.0},"485":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.0},"575":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.7320508075688772},"776":{"tf":1.0}}},"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"658":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":61,"docs":{"1015":{"tf":1.0},"147":{"tf":1.0},"179":{"tf":1.0},"181":{"tf":1.0},"200":{"tf":1.7320508075688772},"207":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"249":{"tf":1.7320508075688772},"255":{"tf":1.0},"314":{"tf":1.4142135623730951},"35":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"39":{"tf":1.0},"399":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.0},"440":{"tf":1.0},"45":{"tf":3.1622776601683795},"450":{"tf":1.0},"46":{"tf":1.7320508075688772},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"47":{"tf":1.4142135623730951},"49":{"tf":1.0},"50":{"tf":1.4142135623730951},"505":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.4142135623730951},"516":{"tf":1.0},"518":{"tf":1.0},"52":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"548":{"tf":1.0},"568":{"tf":1.0},"6":{"tf":1.0},"605":{"tf":1.0},"615":{"tf":1.0},"618":{"tf":1.0},"68":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.4142135623730951},"701":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0},"983":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"739":{"tf":1.0}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":7,"docs":{"19":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"208":{"tf":3.1622776601683795},"223":{"tf":1.0},"729":{"tf":1.4142135623730951},"911":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"205":{"tf":1.4142135623730951},"208":{"tf":2.449489742783178}}}},"df":0,"docs":{}}}},"l":{"d":{"df":5,"docs":{"199":{"tf":1.0},"362":{"tf":1.0},"50":{"tf":1.0},"847":{"tf":1.4142135623730951},"95":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"831":{"tf":1.0},"832":{"tf":1.0}}}},"s":{"df":2,"docs":{"564":{"tf":1.0},"711":{"tf":1.0}},"t":{"df":6,"docs":{"151":{"tf":1.0},"573":{"tf":1.4142135623730951},"732":{"tf":1.0},"765":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":6,"docs":{"204":{"tf":1.0},"267":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0}},"i":{"df":1,"docs":{"938":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"d":{"'":{"df":0,"docs":{},"v":{"df":1,"docs":{"724":{"tf":1.0}}}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":7,"docs":{"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"418":{"tf":1.0},"453":{"tf":1.0},"735":{"tf":2.0},"849":{"tf":1.0},"854":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":1,"docs":{"47":{"tf":1.4142135623730951}}}}},"p":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"555":{"tf":1.0}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"633":{"tf":1.0},"786":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":14,"docs":{"252":{"tf":1.0},"26":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"5":{"tf":1.0},"521":{"tf":1.0},"542":{"tf":1.0},"567":{"tf":1.0},"583":{"tf":1.0},"673":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":5.656854249492381},"936":{"tf":1.0},"951":{"tf":1.0}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":5,"docs":{"229":{"tf":1.0},"243":{"tf":1.0},"483":{"tf":1.0},"654":{"tf":1.0},"735":{"tf":2.6457513110645907}}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":4,"docs":{"343":{"tf":1.0},"615":{"tf":1.0},"701":{"tf":1.0},"724":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"214":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"x":{"'":{"df":3,"docs":{"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0}}},".":{"0":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"(":{")":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{")":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"2":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"d":{"df":1,"docs":{"749":{"tf":1.0}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"!":{"[":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},":":{":":{"<":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{">":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"a":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":75,"docs":{"1":{"tf":2.0},"12":{"tf":1.0},"14":{"tf":1.0},"15":{"tf":1.0},"18":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"220":{"tf":1.4142135623730951},"237":{"tf":1.0},"24":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":2.449489742783178},"30":{"tf":1.0},"367":{"tf":1.0},"369":{"tf":1.0},"37":{"tf":1.0},"372":{"tf":1.4142135623730951},"374":{"tf":1.0},"375":{"tf":1.0},"5":{"tf":2.449489742783178},"598":{"tf":2.0},"599":{"tf":1.4142135623730951},"6":{"tf":1.4142135623730951},"600":{"tf":2.6457513110645907},"602":{"tf":4.898979485566356},"603":{"tf":2.23606797749979},"605":{"tf":1.0},"606":{"tf":1.4142135623730951},"608":{"tf":1.0},"609":{"tf":1.7320508075688772},"61":{"tf":1.0},"613":{"tf":1.7320508075688772},"614":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.4142135623730951},"623":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":2.23606797749979},"640":{"tf":1.0},"645":{"tf":1.4142135623730951},"649":{"tf":1.4142135623730951},"650":{"tf":1.0},"651":{"tf":1.7320508075688772},"654":{"tf":1.0},"661":{"tf":1.4142135623730951},"664":{"tf":1.7320508075688772},"665":{"tf":1.0},"673":{"tf":1.0},"675":{"tf":1.4142135623730951},"678":{"tf":1.4142135623730951},"692":{"tf":1.7320508075688772},"693":{"tf":1.0},"694":{"tf":2.6457513110645907},"696":{"tf":1.7320508075688772},"697":{"tf":1.0},"698":{"tf":1.7320508075688772},"701":{"tf":1.7320508075688772},"704":{"tf":1.0},"705":{"tf":1.7320508075688772},"706":{"tf":1.0},"782":{"tf":1.7320508075688772},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.4142135623730951},"788":{"tf":1.4142135623730951},"83":{"tf":2.0},"87":{"tf":1.0},"959":{"tf":1.0},"974":{"tf":1.7320508075688772},"975":{"tf":1.0},"980":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0},"985":{"tf":1.4142135623730951}},"p":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"28":{"tf":1.0}}}}}}},"df":1,"docs":{"711":{"tf":1.0}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"83":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"v":{"5":{"df":2,"docs":{"609":{"tf":1.0},"701":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"q":{"(":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"17":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":12,"docs":{"17":{"tf":2.449489742783178},"18":{"tf":1.7320508075688772},"21":{"tf":1.7320508075688772},"22":{"tf":2.449489742783178},"23":{"tf":1.7320508075688772},"24":{"tf":2.6457513110645907},"25":{"tf":2.0},"26":{"tf":1.7320508075688772},"28":{"tf":1.4142135623730951},"30":{"tf":1.4142135623730951},"35":{"tf":1.4142135623730951},"37":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}}}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"23":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}}}}}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"df":0,"docs":{},"h":{"2":{"5":{"6":{"df":1,"docs":{"22":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"3":{"2":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"22":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"m":{"df":7,"docs":{"605":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.0},"651":{"tf":2.0},"653":{"tf":1.0},"665":{"tf":1.0},"976":{"tf":1.4142135623730951}}}}},"df":18,"docs":{"333":{"tf":2.449489742783178},"346":{"tf":1.0},"417":{"tf":1.7320508075688772},"45":{"tf":1.0},"50":{"tf":1.0},"568":{"tf":1.0},"697":{"tf":1.0},"749":{"tf":1.0},"841":{"tf":2.0},"842":{"tf":1.7320508075688772},"843":{"tf":1.7320508075688772},"844":{"tf":1.0},"847":{"tf":2.0},"848":{"tf":2.0},"849":{"tf":2.6457513110645907},"850":{"tf":1.0},"852":{"tf":1.0},"94":{"tf":1.0}},"l":{"c":{"df":1,"docs":{"79":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"'":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":1,"docs":{"205":{"tf":1.0}}}},"u":{"df":1,"docs":{"988":{"tf":1.0}}}},"y":{"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"d":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"z":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"279":{"tf":1.0}}}},"df":0,"docs":{}}},"df":5,"docs":{"112":{"tf":1.4142135623730951},"45":{"tf":1.0},"571":{"tf":1.0},"749":{"tf":1.4142135623730951},"94":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":8,"docs":{"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"470":{"tf":1.0},"471":{"tf":1.0},"778":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"471":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":3,"docs":{"720":{"tf":1.0},"776":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"874":{"tf":1.0}}}}}}}}}},"z":{"[":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"112":{"tf":1.0}}},"df":0,"docs":{}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"364":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":11,"docs":{"207":{"tf":1.4142135623730951},"222":{"tf":1.0},"435":{"tf":1.4142135623730951},"520":{"tf":1.0},"525":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.0},"648":{"tf":1.0},"735":{"tf":2.0},"879":{"tf":2.0}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"17":{"tf":1.0}}}}}},"k":{"df":5,"docs":{"322":{"tf":1.0},"340":{"tf":1.0},"364":{"tf":1.4142135623730951},"537":{"tf":1.0},"54":{"tf":1.0}}},"o":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"i":{"df":1,"docs":{"211":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"639":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"n":{"d":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"513":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"311":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"breadcrumbs":{"root":{"0":{".":{".":{"1":{"df":1,"docs":{"346":{"tf":1.0}}},"2":{"^":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"0":{"0":{"0":{"1":{"6":{"7":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"0":{"9":{"6":{"6":{"6":{"6":{"1":{"7":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":1,"docs":{"415":{"tf":1.0}}},"2":{"df":1,"docs":{"416":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"416":{"tf":1.0}}},"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"6":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"8":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"0":{"9":{"6":{"6":{"6":{"6":{"1":{"7":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"1":{"0":{"8":{"3":{"3":{"df":1,"docs":{"720":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"df":1,"docs":{"469":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.0}}},"2":{"0":{"0":{"6":{"4":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":0,"docs":{}},"7":{"6":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"8":{"1":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"2":{"9":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"df":1,"docs":{"469":{"tf":1.0}}},"8":{"7":{"df":2,"docs":{"567":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"412":{"tf":1.0},"415":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"752":{"tf":1.0}}},"6":{"df":1,"docs":{"406":{"tf":1.0}}},"8":{"df":1,"docs":{"715":{"tf":1.0}}},"9":{"5":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"0":{"0":{"df":44,"docs":{"56":{"tf":2.0},"57":{"tf":1.0},"58":{"tf":1.0},"59":{"tf":1.0},"60":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"66":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"69":{"tf":1.0},"70":{"tf":1.0},"709":{"tf":2.0},"71":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"713":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.0},"718":{"tf":1.0},"719":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"726":{"tf":1.0},"727":{"tf":1.0},"728":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.0},"76":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":1.0}}},"1":{"df":17,"docs":{"940":{"tf":2.0},"941":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.0},"946":{"tf":1.0},"947":{"tf":1.0},"948":{"tf":1.0},"949":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"954":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0}}},"2":{"df":17,"docs":{"957":{"tf":2.0},"958":{"tf":1.0},"959":{"tf":1.0},"960":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"963":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"970":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}},"4":{"df":11,"docs":{"730":{"tf":2.0},"731":{"tf":1.0},"732":{"tf":1.0},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"740":{"tf":1.0}}},"6":{"df":16,"docs":{"741":{"tf":2.0},"742":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.0},"745":{"tf":1.0},"746":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.0}}},"7":{"df":18,"docs":{"229":{"tf":2.0},"230":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"233":{"tf":1.0},"234":{"tf":1.0},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"240":{"tf":1.0},"241":{"tf":1.0},"242":{"tf":1.0},"243":{"tf":1.0},"244":{"tf":1.0},"245":{"tf":1.0},"246":{"tf":1.0}}},"8":{"df":16,"docs":{"247":{"tf":2.0},"248":{"tf":1.0},"249":{"tf":1.0},"250":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.0},"256":{"tf":1.0},"257":{"tf":1.0},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0}}},"9":{"df":14,"docs":{"757":{"tf":2.0},"758":{"tf":1.0},"759":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.0},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.0}}},"df":0,"docs":{}},"1":{"0":{"df":5,"docs":{"263":{"tf":2.0},"264":{"tf":1.0},"265":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.0}}},"2":{"df":11,"docs":{"268":{"tf":2.0},"269":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"277":{"tf":1.0},"278":{"tf":1.0}}},"3":{"df":15,"docs":{"279":{"tf":2.0},"280":{"tf":1.0},"281":{"tf":1.0},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0}}},"4":{"df":19,"docs":{"107":{"tf":1.0},"120":{"tf":1.0},"294":{"tf":2.0},"295":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.0},"298":{"tf":1.0},"299":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"308":{"tf":1.0},"309":{"tf":1.0},"310":{"tf":1.0}}},"5":{"df":11,"docs":{"771":{"tf":2.0},"772":{"tf":1.0},"773":{"tf":1.0},"774":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"780":{"tf":1.0},"781":{"tf":1.0}}},"df":0,"docs":{}},"2":{"2":{"df":11,"docs":{"311":{"tf":2.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"317":{"tf":1.0},"318":{"tf":1.0},"319":{"tf":1.0},"320":{"tf":1.0},"321":{"tf":1.0}}},"6":{"df":44,"docs":{"322":{"tf":2.0},"323":{"tf":1.0},"324":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"327":{"tf":1.0},"328":{"tf":1.0},"329":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"351":{"tf":1.0},"352":{"tf":1.0},"353":{"tf":1.0},"354":{"tf":1.0},"355":{"tf":1.0},"356":{"tf":1.0},"357":{"tf":1.0},"358":{"tf":1.0},"359":{"tf":1.0},"360":{"tf":1.0},"361":{"tf":1.0},"362":{"tf":1.0},"363":{"tf":1.0},"364":{"tf":1.0},"365":{"tf":1.0}}},"df":0,"docs":{}},"3":{"2":{"df":20,"docs":{"366":{"tf":2.0},"367":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"377":{"tf":1.0},"378":{"tf":1.0},"379":{"tf":1.0},"380":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.0},"384":{"tf":1.0},"385":{"tf":1.0}}},"5":{"df":13,"docs":{"795":{"tf":2.0},"796":{"tf":1.0},"797":{"tf":1.0},"798":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"801":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":1.0}}},"df":0,"docs":{}},"4":{"2":{"df":14,"docs":{"386":{"tf":2.0},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.0},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0}}},"3":{"df":10,"docs":{"400":{"tf":2.0},"401":{"tf":1.0},"402":{"tf":1.0},"403":{"tf":1.0},"404":{"tf":1.0},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0}}},"4":{"df":19,"docs":{"808":{"tf":2.0},"809":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"812":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.0},"823":{"tf":1.0},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.0}}},"5":{"df":20,"docs":{"410":{"tf":2.0},"411":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"419":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"423":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0}}},"7":{"df":21,"docs":{"430":{"tf":2.0},"431":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"445":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.0}}},"8":{"df":14,"docs":{"451":{"tf":2.0},"452":{"tf":1.0},"453":{"tf":1.0},"454":{"tf":1.0},"455":{"tf":1.0},"456":{"tf":1.0},"457":{"tf":1.0},"458":{"tf":1.0},"459":{"tf":1.0},"460":{"tf":1.0},"461":{"tf":1.0},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.0}}},"df":0,"docs":{}},"5":{"0":{"df":16,"docs":{"465":{"tf":2.0},"466":{"tf":1.0},"467":{"tf":1.0},"468":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"472":{"tf":1.0},"473":{"tf":1.0},"474":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"479":{"tf":1.0},"480":{"tf":1.0}}},"4":{"df":14,"docs":{"827":{"tf":2.0},"828":{"tf":1.0},"829":{"tf":1.0},"830":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"833":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"840":{"tf":1.0}}},"6":{"df":14,"docs":{"481":{"tf":2.0},"482":{"tf":1.0},"483":{"tf":1.0},"484":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.0},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0}}},"9":{"df":18,"docs":{"495":{"tf":2.0},"496":{"tf":1.0},"497":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":1.0},"506":{"tf":1.0},"507":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0}}},"df":0,"docs":{}},"7":{"0":{"df":16,"docs":{"841":{"tf":2.0},"842":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"851":{"tf":1.0},"852":{"tf":1.0},"853":{"tf":1.0},"854":{"tf":1.0},"855":{"tf":1.0},"856":{"tf":1.0}}},"3":{"df":14,"docs":{"857":{"tf":2.0},"858":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":1.0},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0}}},"4":{"df":20,"docs":{"871":{"tf":2.0},"872":{"tf":1.0},"873":{"tf":1.0},"874":{"tf":1.0},"875":{"tf":1.0},"876":{"tf":1.0},"877":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"882":{"tf":1.0},"883":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":1.0},"886":{"tf":1.0},"887":{"tf":1.0},"888":{"tf":1.0},"889":{"tf":1.0},"890":{"tf":1.0}}},"7":{"df":17,"docs":{"891":{"tf":2.0},"892":{"tf":1.0},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.0},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.0},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.0}}},"8":{"df":22,"docs":{"513":{"tf":2.0},"514":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"518":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.0},"526":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"529":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"533":{"tf":1.0},"534":{"tf":1.0}}},"df":0,"docs":{}},"8":{"4":{"df":14,"docs":{"535":{"tf":2.0},"536":{"tf":1.0},"537":{"tf":1.0},"538":{"tf":1.0},"539":{"tf":1.0},"540":{"tf":1.0},"541":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.0}}},"8":{"df":18,"docs":{"908":{"tf":2.0},"909":{"tf":1.0},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}}},"9":{"df":14,"docs":{"926":{"tf":2.0},"927":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"930":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"935":{"tf":1.0},"936":{"tf":1.0},"937":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0}}},"df":0,"docs":{}},"9":{"1":{"df":14,"docs":{"549":{"tf":2.0},"550":{"tf":1.0},"551":{"tf":1.0},"552":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"555":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0}}},"7":{"df":21,"docs":{"563":{"tf":2.0},"564":{"tf":1.0},"565":{"tf":1.0},"566":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"572":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"577":{"tf":1.0},"578":{"tf":1.0},"579":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"583":{"tf":1.0}}},"9":{"df":14,"docs":{"584":{"tf":2.0},"585":{"tf":1.0},"586":{"tf":1.0},"587":{"tf":1.0},"588":{"tf":1.0},"589":{"tf":1.0},"590":{"tf":1.0},"591":{"tf":1.0},"592":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"539":{"tf":1.0}}},"1":{"0":{"0":{"df":15,"docs":{"598":{"tf":2.0},"599":{"tf":1.0},"600":{"tf":1.0},"601":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"604":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"607":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0}}},"1":{"df":14,"docs":{"613":{"tf":2.0},"614":{"tf":1.0},"615":{"tf":1.0},"616":{"tf":1.0},"617":{"tf":1.0},"618":{"tf":1.0},"619":{"tf":1.0},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0}}},"3":{"df":22,"docs":{"627":{"tf":2.0},"628":{"tf":1.0},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.0}}},"5":{"df":15,"docs":{"649":{"tf":2.0},"650":{"tf":1.0},"651":{"tf":1.0},"652":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.0},"655":{"tf":1.0},"656":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.0},"661":{"tf":1.0},"662":{"tf":1.0},"663":{"tf":1.0}}},"6":{"df":14,"docs":{"974":{"tf":2.0},"975":{"tf":1.0},"976":{"tf":1.0},"977":{"tf":1.0},"978":{"tf":1.0},"979":{"tf":1.0},"980":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0},"985":{"tf":1.0},"986":{"tf":1.0},"987":{"tf":1.0}}},"7":{"df":14,"docs":{"664":{"tf":2.0},"665":{"tf":1.0},"666":{"tf":1.0},"667":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"670":{"tf":1.0},"671":{"tf":1.0},"672":{"tf":1.0},"673":{"tf":1.0},"674":{"tf":1.0},"675":{"tf":1.0},"676":{"tf":1.0},"677":{"tf":1.0}}},"8":{"df":14,"docs":{"678":{"tf":2.0},"679":{"tf":1.0},"680":{"tf":1.0},"681":{"tf":1.0},"682":{"tf":1.0},"683":{"tf":1.0},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0},"689":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0}}},"df":0,"docs":{}},"1":{"1":{"df":14,"docs":{"79":{"tf":2.0},"80":{"tf":1.0},"81":{"tf":1.0},"82":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"85":{"tf":1.0},"86":{"tf":1.0},"87":{"tf":1.0},"88":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"92":{"tf":1.0}}},"2":{"df":14,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"988":{"tf":2.0},"989":{"tf":1.0},"990":{"tf":1.0},"991":{"tf":1.0},"992":{"tf":1.0},"993":{"tf":1.0},"994":{"tf":1.0},"995":{"tf":1.0},"996":{"tf":1.0},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}}},"4":{"df":13,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"93":{"tf":2.0},"94":{"tf":1.0},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0}}},"7":{"df":16,"docs":{"106":{"tf":2.0},"107":{"tf":1.0},"108":{"tf":1.0},"109":{"tf":1.0},"110":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"115":{"tf":1.0},"116":{"tf":1.0},"117":{"tf":1.0},"118":{"tf":1.0},"119":{"tf":1.0},"120":{"tf":1.0},"121":{"tf":1.0}}},"df":0,"docs":{}},"2":{"0":{"df":14,"docs":{"122":{"tf":2.0},"123":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"133":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0}}},"1":{"df":14,"docs":{"136":{"tf":2.0},"137":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"143":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"147":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.0}}},"2":{"df":17,"docs":{"692":{"tf":2.0},"693":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"707":{"tf":1.0},"708":{"tf":1.0}}},"3":{"df":14,"docs":{"150":{"tf":2.0},"151":{"tf":1.0},"152":{"tf":1.0},"153":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.0}}},"4":{"df":18,"docs":{"164":{"tf":2.0},"165":{"tf":1.0},"166":{"tf":1.0},"167":{"tf":1.0},"168":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"172":{"tf":1.0},"173":{"tf":1.0},"174":{"tf":1.0},"175":{"tf":1.0},"176":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.0},"179":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.0}}},"5":{"df":16,"docs":{"1":{"tf":2.0},"10":{"tf":1.0},"11":{"tf":1.0},"12":{"tf":1.0},"13":{"tf":1.0},"14":{"tf":1.0},"15":{"tf":1.0},"16":{"tf":1.0},"2":{"tf":1.0},"3":{"tf":1.0},"4":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":1.0},"7":{"tf":1.0},"8":{"tf":1.0},"9":{"tf":1.0}}},"6":{"df":21,"docs":{"17":{"tf":2.0},"18":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"27":{"tf":1.0},"28":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"31":{"tf":1.0},"32":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"35":{"tf":1.0},"36":{"tf":1.0},"37":{"tf":1.0}}},"7":{"df":18,"docs":{"38":{"tf":2.0},"39":{"tf":1.0},"40":{"tf":1.0},"41":{"tf":1.0},"42":{"tf":1.0},"43":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"49":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"539":{"tf":1.0},"692":{"tf":1.0}}},"3":{"df":2,"docs":{"430":{"tf":1.0},"584":{"tf":1.0}}},"4":{"df":1,"docs":{"730":{"tf":1.0}}},"5":{".":{"0":{"8":{".":{"2":{"0":{"2":{"3":{"df":1,"docs":{"771":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"549":{"tf":1.0},"782":{"tf":1.0}}},"6":{"df":4,"docs":{"215":{"tf":1.0},"322":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}},"7":{"df":4,"docs":{"229":{"tf":1.0},"247":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0}}},"9":{":":{"1":{"3":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":3,"docs":{"741":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}},"b":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"1":{"df":1,"docs":{"170":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"0":{"_":{"0":{"1":{"0":{"1":{"df":1,"docs":{"170":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"1":{"1":{"_":{"1":{"1":{"1":{"1":{"_":{"0":{"0":{"0":{"0":{"_":{"0":{"0":{"0":{"0":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"1":{"1":{"1":{"_":{"1":{"1":{"1":{"1":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":3.3166247903554}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"t":{"0":{"0":{"0":{"_":{"0":{"1":{"0":{"0":{"df":1,"docs":{"539":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"t":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":1,"docs":{"539":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":0,"docs":{},"v":{"df":1,"docs":{"539":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":31,"docs":{"194":{"tf":1.0},"208":{"tf":3.872983346207417},"222":{"tf":1.0},"24":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.7320508075688772},"416":{"tf":1.0},"437":{"tf":1.0},"471":{"tf":1.7320508075688772},"525":{"tf":3.872983346207417},"526":{"tf":1.4142135623730951},"531":{"tf":1.0},"537":{"tf":1.0},"63":{"tf":1.4142135623730951},"633":{"tf":1.0},"635":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.0},"735":{"tf":4.58257569495584},"747":{"tf":1.0},"748":{"tf":2.23606797749979},"751":{"tf":1.7320508075688772},"752":{"tf":1.0},"761":{"tf":1.0},"786":{"tf":1.4142135623730951},"846":{"tf":1.0},"879":{"tf":1.0}},"u":{"1":{"6":{"df":1,"docs":{"208":{"tf":4.795831523312719}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"525":{"tf":1.0}}},"df":0,"docs":{}},"x":{"0":{"0":{"0":{"0":{"6":{"0":{"7":{"b":{"2":{"2":{"7":{"4":{"6":{"5":{"7":{"8":{"7":{"4":{"2":{"2":{"3":{"a":{"2":{"0":{"2":{"2":{"4":{"8":{"6":{"5":{"6":{"c":{"6":{"c":{"6":{"df":0,"docs":{},"f":{"2":{"0":{"5":{"7":{"6":{"df":0,"docs":{},"f":{"7":{"2":{"6":{"c":{"6":{"4":{"2":{"1":{"2":{"2":{"7":{"d":{"df":1,"docs":{"847":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"8":{"3":{"d":{"d":{"8":{"0":{"8":{"4":{"d":{"5":{"0":{"d":{"b":{"b":{"b":{"c":{"9":{"6":{"2":{"0":{"6":{"7":{"df":0,"docs":{},"f":{"2":{"1":{"6":{"c":{"3":{"7":{"b":{"6":{"2":{"7":{"8":{"3":{"1":{"d":{"9":{"3":{"3":{"9":{"df":0,"docs":{},"f":{"5":{"a":{"6":{"df":0,"docs":{},"e":{"4":{"2":{"6":{"a":{"3":{"2":{"df":0,"docs":{},"e":{"3":{"0":{"7":{"6":{"3":{"1":{"3":{"d":{"8":{"7":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"1":{"0":{"df":0,"docs":{},"f":{"df":1,"docs":{"253":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"1":{",":{"0":{"0":{"0":{"df":1,"docs":{"200":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"2":{",":{"3":{"df":1,"docs":{"436":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},".":{"0":{"df":2,"docs":{"53":{"tf":1.0},"762":{"tf":1.0}}},"1":{"df":2,"docs":{"322":{"tf":1.0},"325":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"326":{"tf":1.4142135623730951}}},"5":{"df":3,"docs":{"469":{"tf":1.0},"752":{"tf":1.4142135623730951},"762":{"tf":1.0}}},"df":0,"docs":{}},"/":{"1":{"0":{"0":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"375":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"df":1,"docs":{"569":{"tf":1.0}}},"3":{"df":4,"docs":{"346":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.0},"569":{"tf":1.0}}},"8":{"0":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"223":{"tf":1.0},"470":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":7,"docs":{"208":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"507":{"tf":1.0},"752":{"tf":2.0},"861":{"tf":1.0}}},"2":{"0":{"df":1,"docs":{"390":{"tf":1.0}}},"df":0,"docs":{}},"df":6,"docs":{"208":{"tf":3.872983346207417},"223":{"tf":1.0},"24":{"tf":1.0},"46":{"tf":1.0},"60":{"tf":1.0},"735":{"tf":1.0}},"m":{"df":1,"docs":{"933":{"tf":1.0}}}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":22,"docs":{"1002":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":1.0},"208":{"tf":2.23606797749979},"223":{"tf":1.0},"322":{"tf":1.0},"359":{"tf":1.4142135623730951},"412":{"tf":1.4142135623730951},"415":{"tf":1.4142135623730951},"416":{"tf":1.4142135623730951},"45":{"tf":1.0},"47":{"tf":1.0},"539":{"tf":1.0},"63":{"tf":1.4142135623730951},"714":{"tf":1.0},"776":{"tf":1.0},"795":{"tf":1.0},"846":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"554":{"tf":1.0}}}}},"x":{"df":1,"docs":{"63":{"tf":1.0}}}},"1":{",":{"6":{"df":1,"docs":{"761":{"tf":1.0}}},"7":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"0":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":2.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"4":{"df":13,"docs":{"182":{"tf":2.0},"183":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"186":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.0}}},"df":7,"docs":{"322":{"tf":1.0},"360":{"tf":1.4142135623730951},"471":{"tf":1.0},"481":{"tf":1.0},"539":{"tf":1.0},"598":{"tf":1.0},"827":{"tf":1.0}}},"2":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"362":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"363":{"tf":1.4142135623730951}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"364":{"tf":1.4142135623730951}}},"4":{"df":2,"docs":{"322":{"tf":1.0},"365":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"208":{"tf":1.0},"567":{"tf":1.0}}},"2":{"df":1,"docs":{"6":{"tf":1.0}}},"7":{"df":1,"docs":{"540":{"tf":1.0}}},"8":{"df":5,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"436":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":1.0}}},"9":{"df":1,"docs":{"416":{"tf":1.0}}},"df":10,"docs":{"183":{"tf":1.0},"186":{"tf":1.4142135623730951},"322":{"tf":1.0},"361":{"tf":1.4142135623730951},"495":{"tf":1.0},"535":{"tf":1.0},"613":{"tf":1.0},"79":{"tf":1.0},"857":{"tf":1.0},"861":{"tf":1.0}}},"3":{",":{"1":{"1":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"df":3,"docs":{"451":{"tf":1.0},"56":{"tf":1.0},"720":{"tf":1.0}}},"4":{".":{"1":{"0":{".":{"2":{"0":{"2":{"4":{"df":1,"docs":{"150":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"0":{"df":1,"docs":{"50":{"tf":1.0}}},"df":0,"docs":{}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":5,"docs":{"208":{"tf":1.0},"247":{"tf":1.0},"776":{"tf":1.0},"861":{"tf":1.0},"988":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"252":{"tf":1.0}}}}},"5":{",":{"1":{"7":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"0":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":2,"docs":{"208":{"tf":3.4641016151377544},"50":{"tf":1.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":3.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"df":1,"docs":{"208":{"tf":1.0}}},"df":8,"docs":{"208":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.0},"465":{"tf":1.0},"627":{"tf":1.0},"714":{"tf":1.0},"799":{"tf":1.0},"871":{"tf":1.0}},"k":{"b":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"39":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"6":{"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"898":{"tf":1.0}}},"4":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}},"9":{"df":1,"docs":{"996":{"tf":1.0}}},"df":5,"docs":{"208":{"tf":3.4641016151377544},"500":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"93":{"tf":1.0}},"k":{"df":0,"docs":{},"i":{"b":{"df":1,"docs":{"253":{"tf":1.0}}},"df":0,"docs":{}}}},"7":{"df":2,"docs":{"136":{"tf":1.0},"182":{"tf":1.0}}},"8":{",":{"3":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"4":{"6":{"7":{"4":{"4":{"0":{"7":{"3":{"7":{"0":{"9":{"5":{"5":{"1":{"6":{"1":{"5":{"df":1,"docs":{"404":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"164":{"tf":1.0},"495":{"tf":1.0}}},"9":{".":{"0":{"6":{".":{"2":{"0":{"2":{"4":{"df":2,"docs":{"563":{"tf":1.0},"567":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{".":{"2":{"0":{"2":{"3":{"df":1,"docs":{"263":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"df":1,"docs":{"418":{"tf":1.0}}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"757":{"tf":1.0}}},":":{"1":{"df":1,"docs":{"440":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":97,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"171":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.0},"186":{"tf":1.0},"195":{"tf":2.0},"196":{"tf":1.0},"197":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"201":{"tf":1.0},"202":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"216":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"322":{"tf":1.0},"324":{"tf":1.4142135623730951},"332":{"tf":1.0},"341":{"tf":1.4142135623730951},"344":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"370":{"tf":1.0},"390":{"tf":1.4142135623730951},"416":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.4142135623730951},"440":{"tf":1.7320508075688772},"45":{"tf":1.0},"455":{"tf":1.0},"469":{"tf":1.0},"47":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":2.23606797749979},"520":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":3.7416573867739413},"526":{"tf":1.4142135623730951},"537":{"tf":1.0},"553":{"tf":1.4142135623730951},"60":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":2.23606797749979},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":5.656854249492381},"742":{"tf":1.0},"743":{"tf":1.7320508075688772},"748":{"tf":1.7320508075688772},"749":{"tf":1.4142135623730951},"750":{"tf":1.4142135623730951},"752":{"tf":3.1622776601683795},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.23606797749979},"762":{"tf":1.4142135623730951},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"780":{"tf":1.0},"786":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":2.23606797749979},"862":{"tf":1.0},"878":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"v":{"df":1,"docs":{"799":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}},"2":{"(":{"df":0,"docs":{},"j":{"df":1,"docs":{"45":{"tf":1.0}}}},",":{"8":{"9":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},".":{"0":{"df":1,"docs":{"469":{"tf":1.0}}},"1":{"df":2,"docs":{"322":{"tf":1.0},"328":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"329":{"tf":1.4142135623730951}}},"5":{"df":1,"docs":{"469":{"tf":2.0}}},"6":{"7":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"3":{"df":5,"docs":{"567":{"tf":1.4142135623730951},"63":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":1.0},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":2,"docs":{"470":{"tf":2.0},"471":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"208":{"tf":1.7320508075688772},"24":{"tf":1.0}},"u":{"3":{"2":{"df":1,"docs":{"208":{"tf":2.6457513110645907}}},"df":0,"docs":{}},"df":0,"docs":{}}},"2":{"2":{"df":2,"docs":{"312":{"tf":1.0},"807":{"tf":1.0}}},"3":{"df":27,"docs":{"195":{"tf":1.0},"201":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"782":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0}}},"4":{"df":33,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"38":{"tf":1.0},"418":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"79":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}},"5":{"df":1,"docs":{"54":{"tf":1.0}}},"df":0,"docs":{}},"4":{"8":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}},"df":27,"docs":{"191":{"tf":1.0},"235":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":2.0},"366":{"tf":1.0},"505":{"tf":1.4142135623730951},"507":{"tf":1.7320508075688772},"549":{"tf":1.0},"714":{"tf":1.0},"891":{"tf":2.449489742783178},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":2.6457513110645907},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":2.0},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.0},"932":{"tf":1.0}}},"2":{",":{"5":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"6":{"6":{"5":{"3":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"1":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"390":{"tf":1.0},"513":{"tf":1.0},"860":{"tf":1.0}},"n":{"d":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}}},"3":{"df":4,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"974":{"tf":1.0}}},"4":{"0":{",":{"8":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":7,"docs":{"182":{"tf":1.0},"198":{"tf":1.0},"257":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"507":{"tf":1.0},"827":{"tf":1.0}}},"5":{"6":{"df":4,"docs":{"333":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"634":{"tf":1.7320508075688772}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":4,"docs":{"17":{"tf":1.0},"294":{"tf":1.0},"634":{"tf":1.0},"908":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"386":{"tf":1.0}}}}},"6":{"df":2,"docs":{"38":{"tf":1.0},"575":{"tf":1.0}}},"7":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"471":{"tf":1.0}}},"8":{"8":{"0":{"0":{"df":1,"docs":{"569":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":12,"docs":{"207":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":2.449489742783178},"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.7320508075688772},"573":{"tf":2.449489742783178},"575":{"tf":1.0},"577":{"tf":1.0},"846":{"tf":1.0}}},"9":{"6":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"841":{"tf":1.0}}},"df":51,"docs":{"171":{"tf":1.0},"184":{"tf":1.0},"190":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":1.7320508075688772},"249":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"327":{"tf":1.4142135623730951},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.0},"410":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"45":{"tf":1.0},"525":{"tf":3.605551275463989},"537":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.4142135623730951},"569":{"tf":1.4142135623730951},"573":{"tf":1.4142135623730951},"575":{"tf":1.0},"576":{"tf":1.0},"598":{"tf":1.0},"603":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":1.0},"637":{"tf":1.0},"735":{"tf":3.4641016151377544},"748":{"tf":1.7320508075688772},"752":{"tf":2.23606797749979},"761":{"tf":2.0},"779":{"tf":1.0},"841":{"tf":1.0},"847":{"tf":1.4142135623730951},"861":{"tf":1.0},"880":{"tf":1.0},"933":{"tf":1.4142135623730951}},"n":{"/":{"3":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"3":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"331":{"tf":1.4142135623730951}}},"2":{"5":{"df":1,"docs":{"720":{"tf":1.0}}},"df":3,"docs":{"322":{"tf":1.4142135623730951},"332":{"tf":1.4142135623730951},"333":{"tf":1.4142135623730951}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"334":{"tf":1.4142135623730951}}},"a":{"df":1,"docs":{"450":{"tf":1.0}}},"b":{"df":1,"docs":{"450":{"tf":1.0}}},"c":{"df":1,"docs":{"450":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":8,"docs":{"195":{"tf":1.0},"207":{"tf":1.0},"400":{"tf":1.0},"481":{"tf":1.0},"50":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":2.0},"776":{"tf":1.0}}},"2":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"831":{"tf":1.0}}}}},"df":17,"docs":{"163":{"tf":1.0},"208":{"tf":1.4142135623730951},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"332":{"tf":1.0},"388":{"tf":1.0},"455":{"tf":1.0},"520":{"tf":1.4142135623730951},"525":{"tf":1.0},"526":{"tf":1.4142135623730951},"634":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"885":{"tf":1.0},"897":{"tf":1.4142135623730951},"907":{"tf":1.0},"97":{"tf":1.0}}},"3":{".":{"3":{"3":{"3":{"3":{"3":{"3":{"df":1,"docs":{"862":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"996":{"tf":1.0}}},"4":{"0":{"df":1,"docs":{"869":{"tf":1.0}}},"df":13,"docs":{"782":{"tf":2.0},"783":{"tf":1.0},"784":{"tf":1.0},"785":{"tf":1.0},"786":{"tf":1.0},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0}}},"5":{"2":{",":{"5":{"8":{"3":{",":{"4":{"5":{"5":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"5":{"df":1,"docs":{"537":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"df":1,"docs":{"551":{"tf":1.4142135623730951}}}},"7":{"1":{"2":{"df":1,"docs":{"537":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"208":{"tf":1.0}}},"8":{"df":1,"docs":{"735":{"tf":1.0}}},"df":35,"docs":{"113":{"tf":1.0},"154":{"tf":1.4142135623730951},"171":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"216":{"tf":1.0},"221":{"tf":1.0},"226":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"330":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.0},"432":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.4142135623730951},"50":{"tf":1.4142135623730951},"525":{"tf":3.605551275463989},"598":{"tf":1.0},"603":{"tf":1.4142135623730951},"633":{"tf":2.0},"722":{"tf":1.0},"735":{"tf":2.449489742783178},"743":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":2.0},"841":{"tf":1.0},"845":{"tf":1.0},"848":{"tf":1.4142135623730951},"878":{"tf":1.0}},"x":{"df":1,"docs":{"575":{"tf":1.0}}}},"4":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"336":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"337":{"tf":1.4142135623730951}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"338":{"tf":1.4142135623730951}}},"4":{"df":2,"docs":{"322":{"tf":1.0},"339":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"0":{"3":{"2":{"0":{"0":{"df":1,"docs":{"569":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":8,"docs":{"208":{"tf":1.4142135623730951},"416":{"tf":1.0},"892":{"tf":1.0},"895":{"tf":1.4142135623730951},"896":{"tf":1.0},"898":{"tf":1.7320508075688772},"900":{"tf":1.0},"902":{"tf":1.0}}},"2":{"1":{"6":{"1":{"df":2,"docs":{"45":{"tf":1.0},"47":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"418":{"tf":1.0}}},"5":{"df":3,"docs":{"207":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":2.0}}},"6":{"df":1,"docs":{"532":{"tf":1.0}}},"8":{",":{"6":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"4":{"4":{"'":{"df":1,"docs":{"39":{"tf":1.0}}},"df":1,"docs":{"55":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{",":{"2":{"1":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":30,"docs":{"165":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.4142135623730951},"184":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"280":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"335":{"tf":1.4142135623730951},"344":{"tf":1.0},"485":{"tf":1.0},"521":{"tf":1.0},"525":{"tf":3.7416573867739413},"537":{"tf":1.0},"539":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":2.449489742783178},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"761":{"tf":1.7320508075688772},"799":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.4142135623730951},"846":{"tf":1.0},"928":{"tf":1.0}},"·":{"1":{"0":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"5":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"341":{"tf":1.4142135623730951}}},"4":{".":{"2":{"df":2,"docs":{"341":{"tf":1.0},"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":2,"docs":{"497":{"tf":1.4142135623730951},"515":{"tf":1.0}}},"df":6,"docs":{"208":{"tf":2.0},"257":{"tf":1.0},"436":{"tf":1.0},"507":{"tf":1.0},"717":{"tf":1.0},"846":{"tf":1.4142135623730951}}},"3":{",":{"3":{"3":{"3":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"3":{"1":{"0":{",":{"1":{"2":{"1":{"df":1,"docs":{"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{",":{"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"2":{"df":1,"docs":{"911":{"tf":1.0}}},"df":0,"docs":{}},"df":51,"docs":{"164":{"tf":2.6457513110645907},"165":{"tf":1.4142135623730951},"166":{"tf":1.0},"167":{"tf":1.0},"168":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.7320508075688772},"171":{"tf":1.0},"172":{"tf":1.7320508075688772},"173":{"tf":1.0},"174":{"tf":1.0},"175":{"tf":1.4142135623730951},"176":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.7320508075688772},"179":{"tf":1.0},"180":{"tf":1.4142135623730951},"181":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":2.0},"216":{"tf":1.0},"217":{"tf":1.0},"218":{"tf":1.0},"219":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"223":{"tf":1.0},"224":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.0},"227":{"tf":1.0},"228":{"tf":1.0},"280":{"tf":1.0},"300":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":1.0},"340":{"tf":1.4142135623730951},"370":{"tf":1.0},"471":{"tf":1.0},"525":{"tf":3.0},"539":{"tf":1.0},"588":{"tf":1.4142135623730951},"594":{"tf":1.0},"714":{"tf":1.4142135623730951},"735":{"tf":1.0},"761":{"tf":1.4142135623730951},"990":{"tf":1.0}}},"6":{".":{"1":{"0":{"df":3,"docs":{"322":{"tf":1.0},"344":{"tf":1.0},"352":{"tf":1.4142135623730951}}},"df":1,"docs":{"342":{"tf":1.0}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"343":{"tf":1.4142135623730951}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"344":{"tf":1.4142135623730951}}},"4":{".":{"1":{"df":1,"docs":{"345":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"345":{"tf":1.4142135623730951}}},"5":{".":{"1":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"342":{"tf":1.0},"346":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"346":{"tf":1.4142135623730951}}},"6":{"df":2,"docs":{"322":{"tf":1.0},"347":{"tf":1.4142135623730951}}},"7":{"df":2,"docs":{"322":{"tf":1.0},"348":{"tf":1.4142135623730951}}},"8":{".":{"1":{"df":1,"docs":{"349":{"tf":1.0}}},"2":{"df":3,"docs":{"348":{"tf":1.0},"349":{"tf":1.0},"351":{"tf":1.0}}},"3":{"df":1,"docs":{"349":{"tf":1.0}}},"4":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":3,"docs":{"322":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0}}},"9":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"351":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"351":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"350":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"0":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"3":{"df":1,"docs":{"540":{"tf":1.0}}},"4":{"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"735":{"tf":1.7320508075688772},"831":{"tf":1.4142135623730951}}}}},"df":4,"docs":{"332":{"tf":1.0},"404":{"tf":1.0},"634":{"tf":1.4142135623730951},"97":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"i":{"b":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}}}},"5":{",":{"3":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{",":{"6":{"6":{"7":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"df":1,"docs":{"846":{"tf":1.0}}},"df":10,"docs":{"205":{"tf":1.0},"322":{"tf":1.0},"342":{"tf":1.4142135623730951},"525":{"tf":1.0},"588":{"tf":1.0},"761":{"tf":1.4142135623730951},"779":{"tf":1.0},"808":{"tf":1.0},"862":{"tf":1.0},"926":{"tf":1.0}}},"7":{"0":{"df":2,"docs":{"714":{"tf":1.0},"932":{"tf":1.0}}},"2":{"1":{"2":{"df":1,"docs":{"105":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"df":1,"docs":{"714":{"tf":1.0}}},"7":{",":{"0":{"0":{"0":{"df":1,"docs":{"470":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":13,"docs":{"184":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"322":{"tf":1.0},"353":{"tf":1.4142135623730951},"39":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.4142135623730951},"568":{"tf":1.0},"632":{"tf":1.0},"720":{"tf":1.0},"776":{"tf":1.4142135623730951},"862":{"tf":1.0}}},"8":{"0":{",":{"0":{"0":{"0":{"df":3,"docs":{"208":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{",":{"0":{"0":{"0":{"df":1,"docs":{"471":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"0":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}},"df":5,"docs":{"204":{"tf":1.7320508075688772},"208":{"tf":2.23606797749979},"444":{"tf":1.0},"720":{"tf":1.7320508075688772},"721":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"1":{",":{"8":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"5":{"df":2,"docs":{"959":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{}},"df":15,"docs":{"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.7320508075688772},"221":{"tf":1.0},"322":{"tf":1.0},"332":{"tf":1.0},"354":{"tf":1.4142135623730951},"470":{"tf":1.0},"471":{"tf":1.0},"496":{"tf":1.4142135623730951},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"735":{"tf":1.0}}},"9":{".":{"1":{"df":2,"docs":{"322":{"tf":1.0},"356":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"322":{"tf":1.0},"357":{"tf":1.4142135623730951}}},"3":{"df":2,"docs":{"322":{"tf":1.0},"358":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"1":{"b":{"1":{"7":{"1":{"b":{"b":{"1":{"5":{"8":{"df":0,"docs":{},"e":{"2":{"d":{"3":{"8":{"4":{"8":{"df":0,"docs":{},"f":{"a":{"2":{"3":{"a":{"9":{"df":0,"docs":{},"f":{"1":{"c":{"2":{"5":{"1":{"8":{"2":{"df":0,"docs":{},"f":{"b":{"8":{"df":0,"docs":{},"e":{"2":{"0":{"3":{"1":{"3":{"b":{"2":{"c":{"1":{"df":0,"docs":{},"e":{"b":{"4":{"9":{"2":{"1":{"9":{"d":{"a":{"7":{"a":{"7":{"0":{"c":{"df":0,"docs":{},"e":{"9":{"0":{"c":{"3":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"253":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"8":{"1":{"df":1,"docs":{"340":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"9":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"322":{"tf":1.0},"355":{"tf":1.4142135623730951}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"418":{"tf":1.0}}}}},"_":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"_":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"736":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":1,"docs":{"880":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"a":{"(":{"1":{"df":1,"docs":{"749":{"tf":1.0}}},"df":0,"docs":{},"x":{"^":{"df":0,"docs":{},"u":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}}},".":{"df":0,"docs":{},"k":{".":{"a":{"df":2,"docs":{"111":{"tf":1.0},"368":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"[":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{}}}},"b":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"871":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":12,"docs":{"114":{"tf":1.0},"199":{"tf":1.7320508075688772},"203":{"tf":1.0},"3":{"tf":1.4142135623730951},"375":{"tf":1.0},"473":{"tf":1.0},"515":{"tf":1.0},"602":{"tf":1.0},"786":{"tf":1.0},"849":{"tf":1.0},"875":{"tf":2.23606797749979},"942":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"188":{"tf":1.0}}}},"v":{"df":33,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"170":{"tf":1.0},"203":{"tf":1.0},"207":{"tf":1.4142135623730951},"417":{"tf":1.0},"420":{"tf":1.0},"446":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"534":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"576":{"tf":1.0},"581":{"tf":1.0},"633":{"tf":1.0},"65":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.7320508075688772},"722":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"847":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"571":{"tf":1.0}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"829":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":17,"docs":{"284":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"782":{"tf":2.23606797749979},"783":{"tf":1.4142135623730951},"784":{"tf":1.4142135623730951},"785":{"tf":1.0},"786":{"tf":3.1622776601683795},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"933":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"796":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772}}}}},"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"18":{"tf":1.0},"322":{"tf":1.0},"323":{"tf":1.4142135623730951},"38":{"tf":1.0},"696":{"tf":1.0},"83":{"tf":1.0},"932":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"s":{"df":7,"docs":{"142":{"tf":1.0},"255":{"tf":1.4142135623730951},"420":{"tf":1.0},"505":{"tf":1.0},"912":{"tf":1.0},"917":{"tf":1.0},"955":{"tf":1.0}}}}},"c":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"723":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":22,"docs":{"1015":{"tf":1.0},"121":{"tf":1.0},"132":{"tf":1.0},"171":{"tf":1.0},"200":{"tf":1.4142135623730951},"207":{"tf":1.0},"222":{"tf":1.0},"254":{"tf":1.0},"270":{"tf":1.4142135623730951},"425":{"tf":1.0},"441":{"tf":1.0},"503":{"tf":1.0},"559":{"tf":1.0},"660":{"tf":1.0},"735":{"tf":3.0},"736":{"tf":1.0},"739":{"tf":1.0},"755":{"tf":1.0},"777":{"tf":1.0},"85":{"tf":1.0},"879":{"tf":1.0},"890":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"s":{"df":32,"docs":{"140":{"tf":1.0},"144":{"tf":1.0},"19":{"tf":1.0},"231":{"tf":1.0},"255":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":1.0},"340":{"tf":1.0},"372":{"tf":1.0},"402":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"423":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":2.0},"498":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":2.0},"697":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":1.0},"874":{"tf":1.0},"912":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"763":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":3,"docs":{"166":{"tf":1.0},"173":{"tf":1.0},"39":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":2,"docs":{"655":{"tf":1.0},"742":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"346":{"tf":1.0},"526":{"tf":1.0}}}}}}}},"r":{"d":{"df":14,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"22":{"tf":1.0},"234":{"tf":1.0},"273":{"tf":1.0},"29":{"tf":1.0},"333":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"436":{"tf":1.0},"537":{"tf":1.0},"6":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"1004":{"tf":1.0},"6":{"tf":1.4142135623730951},"7":{"tf":1.0},"700":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"881":{"tf":1.0}}},"df":0,"docs":{},"t":{"'":{"df":2,"docs":{"848":{"tf":1.0},"850":{"tf":1.0}}},"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"44":{"tf":1.0},"46":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"455":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":78,"docs":{"126":{"tf":1.0},"145":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.0},"205":{"tf":2.8284271247461903},"207":{"tf":1.4142135623730951},"21":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":1.0},"375":{"tf":1.0},"402":{"tf":1.7320508075688772},"417":{"tf":1.0},"452":{"tf":1.7320508075688772},"453":{"tf":1.4142135623730951},"456":{"tf":1.0},"461":{"tf":1.0},"515":{"tf":1.0},"537":{"tf":1.4142135623730951},"54":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":2.23606797749979},"602":{"tf":1.0},"603":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":2.0},"697":{"tf":1.0},"742":{"tf":1.0},"759":{"tf":1.4142135623730951},"782":{"tf":2.23606797749979},"783":{"tf":1.4142135623730951},"784":{"tf":1.4142135623730951},"785":{"tf":1.0},"786":{"tf":2.0},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"79":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"799":{"tf":2.0},"80":{"tf":1.4142135623730951},"81":{"tf":4.795831523312719},"814":{"tf":1.0},"83":{"tf":3.1622776601683795},"84":{"tf":3.1622776601683795},"841":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":1.7320508075688772},"848":{"tf":1.4142135623730951},"849":{"tf":2.23606797749979},"85":{"tf":2.0},"852":{"tf":1.0},"872":{"tf":2.0},"874":{"tf":3.3166247903554},"875":{"tf":2.6457513110645907},"876":{"tf":2.449489742783178},"878":{"tf":2.0},"879":{"tf":8.426149773176359},"880":{"tf":2.449489742783178},"881":{"tf":2.449489742783178},"885":{"tf":2.449489742783178},"886":{"tf":1.0},"889":{"tf":1.0},"890":{"tf":1.0},"897":{"tf":1.0},"913":{"tf":1.4142135623730951},"914":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.0},"932":{"tf":3.4641016151377544},"95":{"tf":1.4142135623730951},"979":{"tf":1.0}},"i":{"d":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"3":{"2":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"696":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":10,"docs":{"19":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"221":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"783":{"tf":1.0},"786":{"tf":1.0},"83":{"tf":1.0},"879":{"tf":2.0}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":2,"docs":{"265":{"tf":1.0},"267":{"tf":1.4142135623730951}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"51":{"tf":1.0}}},"df":0,"docs":{}}}},"df":10,"docs":{"222":{"tf":1.0},"267":{"tf":1.0},"322":{"tf":1.0},"344":{"tf":2.23606797749979},"345":{"tf":1.0},"352":{"tf":2.0},"38":{"tf":1.4142135623730951},"47":{"tf":2.23606797749979},"49":{"tf":1.4142135623730951},"51":{"tf":1.0}}}}},"r":{"df":4,"docs":{"218":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"938":{"tf":1.0}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":29,"docs":{"1004":{"tf":1.4142135623730951},"137":{"tf":1.0},"186":{"tf":1.0},"208":{"tf":1.0},"235":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"295":{"tf":1.0},"346":{"tf":1.0},"404":{"tf":1.0},"532":{"tf":1.0},"54":{"tf":1.0},"559":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"658":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.0},"721":{"tf":1.0},"752":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"829":{"tf":1.4142135623730951},"874":{"tf":1.4142135623730951},"880":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"934":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":4,"docs":{"231":{"tf":1.0},"349":{"tf":1.0},"473":{"tf":1.0},"629":{"tf":1.0}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"894":{"tf":1.0}}}}}}},"t":{"df":7,"docs":{"273":{"tf":1.0},"602":{"tf":1.0},"644":{"tf":1.0},"705":{"tf":1.0},"77":{"tf":1.0},"863":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":14,"docs":{"108":{"tf":1.0},"111":{"tf":2.0},"210":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"300":{"tf":1.0},"600":{"tf":1.0},"700":{"tf":1.0},"776":{"tf":1.0},"844":{"tf":1.0},"879":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0}}}},"v":{"df":16,"docs":{"1004":{"tf":1.7320508075688772},"205":{"tf":1.0},"267":{"tf":1.0},"323":{"tf":1.0},"422":{"tf":1.0},"52":{"tf":1.0},"567":{"tf":1.0},"65":{"tf":1.0},"777":{"tf":1.4142135623730951},"797":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":8,"docs":{"124":{"tf":2.23606797749979},"125":{"tf":1.0},"145":{"tf":1.0},"267":{"tf":1.7320508075688772},"373":{"tf":1.0},"696":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":43,"docs":{"166":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"39":{"tf":1.0},"412":{"tf":1.0},"428":{"tf":1.0},"455":{"tf":1.7320508075688772},"505":{"tf":1.0},"519":{"tf":1.4142135623730951},"521":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"528":{"tf":1.0},"60":{"tf":1.4142135623730951},"602":{"tf":1.0},"614":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"63":{"tf":1.0},"651":{"tf":1.0},"658":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.4142135623730951},"751":{"tf":1.0},"761":{"tf":1.0},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"911":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"935":{"tf":1.0}}}},"df":0,"docs":{}}}},"d":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"841":{"tf":1.0}}},"p":{"df":0,"docs":{},"t":{"df":17,"docs":{"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"151":{"tf":1.0},"159":{"tf":1.0},"177":{"tf":1.0},"282":{"tf":1.4142135623730951},"418":{"tf":1.0},"420":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"72":{"tf":1.0},"741":{"tf":1.0},"743":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":1.0},"84":{"tf":1.0}}}}},"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":3,"docs":{"874":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.0}}}}}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"300":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.7320508075688772}}}}}}},"df":101,"docs":{"105":{"tf":1.0},"172":{"tf":1.0},"180":{"tf":1.0},"187":{"tf":1.0},"221":{"tf":1.0},"251":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"386":{"tf":2.23606797749979},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.0},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"485":{"tf":1.0},"495":{"tf":2.0},"496":{"tf":1.0},"497":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":1.4142135623730951},"506":{"tf":1.0},"507":{"tf":1.4142135623730951},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.4142135623730951},"520":{"tf":1.0},"526":{"tf":1.7320508075688772},"549":{"tf":1.0},"576":{"tf":1.4142135623730951},"586":{"tf":1.0},"588":{"tf":1.4142135623730951},"589":{"tf":1.0},"593":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"664":{"tf":1.0},"673":{"tf":1.0},"68":{"tf":1.0},"689":{"tf":1.0},"714":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"773":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"831":{"tf":1.4142135623730951},"841":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"857":{"tf":1.0},"860":{"tf":1.0},"87":{"tf":1.0},"871":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0},"890":{"tf":1.0},"894":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.0},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"934":{"tf":1.0},"942":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":3,"docs":{"410":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"872":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"t":{"df":60,"docs":{"1010":{"tf":1.0},"113":{"tf":1.0},"12":{"tf":1.0},"121":{"tf":1.0},"127":{"tf":1.0},"131":{"tf":1.0},"16":{"tf":1.0},"170":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.0},"281":{"tf":1.0},"3":{"tf":1.0},"340":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"402":{"tf":1.0},"500":{"tf":1.0},"537":{"tf":1.4142135623730951},"563":{"tf":1.0},"568":{"tf":1.0},"570":{"tf":1.0},"572":{"tf":1.4142135623730951},"573":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"628":{"tf":1.0},"634":{"tf":1.0},"638":{"tf":1.0},"64":{"tf":1.4142135623730951},"642":{"tf":1.0},"648":{"tf":1.0},"651":{"tf":1.0},"736":{"tf":1.0},"751":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"864":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":1.0},"889":{"tf":1.0},"902":{"tf":1.0},"912":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.4142135623730951},"95":{"tf":1.0},"955":{"tf":1.0},"968":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"890":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"835":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":16,"docs":{"141":{"tf":1.0},"166":{"tf":1.0},"204":{"tf":1.4142135623730951},"33":{"tf":1.0},"440":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"628":{"tf":1.0},"770":{"tf":1.0},"780":{"tf":1.0},"807":{"tf":1.0},"860":{"tf":1.0},"909":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}}}}},"r":{"df":2,"docs":{"253":{"tf":2.0},"254":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"df":38,"docs":{"1006":{"tf":1.0},"1014":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"253":{"tf":1.0},"254":{"tf":2.0},"28":{"tf":1.0},"285":{"tf":1.0},"296":{"tf":1.0},"323":{"tf":1.0},"361":{"tf":1.0},"365":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"46":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":2.0},"588":{"tf":1.4142135623730951},"727":{"tf":1.0},"742":{"tf":1.0},"773":{"tf":1.0},"784":{"tf":1.0},"80":{"tf":1.4142135623730951},"81":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"928":{"tf":1.0},"942":{"tf":1.0},"965":{"tf":1.0}}}}}}},"df":61,"docs":{"107":{"tf":1.0},"12":{"tf":1.0},"130":{"tf":1.0},"137":{"tf":1.0},"170":{"tf":1.0},"205":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":2.23606797749979},"269":{"tf":1.4142135623730951},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"277":{"tf":1.0},"278":{"tf":1.0},"288":{"tf":1.0},"343":{"tf":1.0},"364":{"tf":1.0},"375":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.0},"440":{"tf":1.4142135623730951},"441":{"tf":1.0},"450":{"tf":1.0},"500":{"tf":1.0},"526":{"tf":1.7320508075688772},"553":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.0},"586":{"tf":1.4142135623730951},"619":{"tf":1.0},"629":{"tf":1.0},"648":{"tf":1.0},"650":{"tf":1.4142135623730951},"668":{"tf":1.4142135623730951},"673":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"729":{"tf":1.0},"78":{"tf":1.4142135623730951},"799":{"tf":1.0},"831":{"tf":1.0},"842":{"tf":1.0},"85":{"tf":1.0},"853":{"tf":1.0},"860":{"tf":1.0},"867":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"927":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.4142135623730951},"95":{"tf":1.0},"956":{"tf":1.0},"962":{"tf":1.0}},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":3,"docs":{"210":{"tf":1.0},"315":{"tf":1.0},"913":{"tf":1.4142135623730951}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"1008":{"tf":1.0},"427":{"tf":1.0},"69":{"tf":1.0},"773":{"tf":1.0},"847":{"tf":1.0},"900":{"tf":1.0}}}}},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":39,"docs":{"1004":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"142":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"182":{"tf":2.0},"183":{"tf":1.0},"184":{"tf":2.0},"185":{"tf":1.0},"186":{"tf":1.4142135623730951},"187":{"tf":1.0},"188":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.4142135623730951},"203":{"tf":1.0},"253":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"416":{"tf":1.4142135623730951},"417":{"tf":1.0},"418":{"tf":1.4142135623730951},"427":{"tf":2.0},"428":{"tf":1.0},"429":{"tf":1.0},"469":{"tf":1.0},"50":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"77":{"tf":1.0},"776":{"tf":2.23606797749979},"811":{"tf":1.0},"945":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":3,"docs":{"849":{"tf":1.0},"852":{"tf":1.0},"872":{"tf":1.0}}}}}}},"t":{"df":1,"docs":{"725":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":20,"docs":{"311":{"tf":2.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"317":{"tf":1.0},"318":{"tf":1.0},"319":{"tf":1.0},"320":{"tf":1.0},"321":{"tf":1.0},"330":{"tf":1.0},"356":{"tf":1.0},"358":{"tf":1.0},"40":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.4142135623730951},"515":{"tf":1.0},"718":{"tf":1.0},"95":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"598":{"tf":1.0},"613":{"tf":1.0},"692":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"a":{"df":0,"docs":{},"n":{"c":{"df":7,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"761":{"tf":1.0},"777":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"g":{"df":10,"docs":{"289":{"tf":1.0},"38":{"tf":1.0},"40":{"tf":1.0},"429":{"tf":1.0},"453":{"tf":1.0},"526":{"tf":1.0},"574":{"tf":1.0},"61":{"tf":1.0},"777":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"440":{"tf":1.0},"724":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":3,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"528":{"tf":1.0}}}}}}},"i":{"c":{"df":1,"docs":{"290":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":1,"docs":{"576":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":1,"docs":{"392":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":28,"docs":{"100":{"tf":1.0},"125":{"tf":1.0},"132":{"tf":1.0},"185":{"tf":1.4142135623730951},"190":{"tf":1.0},"240":{"tf":1.0},"255":{"tf":1.0},"276":{"tf":1.0},"358":{"tf":1.0},"369":{"tf":1.0},"41":{"tf":1.0},"418":{"tf":1.0},"442":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.4142135623730951},"72":{"tf":1.0},"773":{"tf":1.0},"804":{"tf":1.4142135623730951},"811":{"tf":1.0},"822":{"tf":1.0},"835":{"tf":1.0},"885":{"tf":1.0},"949":{"tf":1.0},"962":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"843":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"752":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"d":{"df":5,"docs":{"776":{"tf":1.0},"858":{"tf":1.0},"872":{"tf":1.0},"912":{"tf":1.0},"942":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"127":{"tf":1.0},"267":{"tf":1.0},"30":{"tf":1.0},"759":{"tf":1.0},"932":{"tf":1.0}}}}}}}}}},"g":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":11,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"522":{"tf":1.0},"540":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"722":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"815":{"tf":1.0}},"s":{"df":0,"docs":{},"t":{"df":15,"docs":{"108":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"528":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.0},"628":{"tf":1.0},"642":{"tf":1.0},"720":{"tf":1.0},"777":{"tf":1.0},"786":{"tf":1.4142135623730951},"913":{"tf":1.0},"931":{"tf":1.0}}}}}}},"df":1,"docs":{"513":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"849":{"tf":1.0}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":4,"docs":{"24":{"tf":1.0},"44":{"tf":1.0},"49":{"tf":1.0},"710":{"tf":1.4142135623730951}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"752":{"tf":1.4142135623730951}}}}}}},"i":{"df":0,"docs":{},"l":{"df":27,"docs":{"140":{"tf":1.0},"195":{"tf":2.23606797749979},"196":{"tf":1.0},"197":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"201":{"tf":1.0},"202":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.4142135623730951},"211":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"216":{"tf":1.0},"374":{"tf":1.0},"58":{"tf":1.0},"811":{"tf":1.0},"846":{"tf":1.0},"938":{"tf":1.0}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":5,"docs":{"273":{"tf":1.0},"420":{"tf":1.0},"469":{"tf":1.0},"799":{"tf":1.0},"848":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"729":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":3,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"974":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":2,"docs":{"402":{"tf":1.0},"497":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":1,"docs":{"603":{"tf":1.7320508075688772}}}},"i":{"df":0,"docs":{},"m":{"df":27,"docs":{"106":{"tf":1.0},"18":{"tf":1.0},"207":{"tf":1.0},"249":{"tf":1.0},"296":{"tf":1.0},"313":{"tf":1.0},"323":{"tf":1.0},"326":{"tf":1.0},"335":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"412":{"tf":1.4142135623730951},"42":{"tf":1.0},"423":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"564":{"tf":1.0},"58":{"tf":1.0},"632":{"tf":1.0},"679":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.4142135623730951},"80":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}},"r":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{}}},"k":{"a":{"df":1,"docs":{"204":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"l":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"549":{"tf":1.0}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"549":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"df":8,"docs":{"132":{"tf":1.0},"175":{"tf":1.0},"213":{"tf":1.4142135623730951},"435":{"tf":2.0},"455":{"tf":1.0},"560":{"tf":1.0},"571":{"tf":1.0},"721":{"tf":1.0}}}}}}}}},"i":{"a":{"df":19,"docs":{"322":{"tf":1.0},"332":{"tf":1.4142135623730951},"692":{"tf":2.0},"693":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":2.449489742783178},"698":{"tf":1.4142135623730951},"699":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"707":{"tf":1.0},"708":{"tf":1.0}},"s":{"df":8,"docs":{"6":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":2.8284271247461903},"698":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.7320508075688772}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0}}}}}}}}}},"c":{"df":7,"docs":{"208":{"tf":4.242640687119285},"741":{"tf":1.0},"796":{"tf":2.0},"799":{"tf":2.0},"81":{"tf":2.0},"83":{"tf":1.0},"878":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"267":{"tf":1.0},"428":{"tf":1.0},"575":{"tf":1.0}}}},"n":{"df":1,"docs":{"430":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":2,"docs":{"563":{"tf":1.0},"583":{"tf":1.0}}}}},"df":0,"docs":{}}},"v":{"df":1,"docs":{"303":{"tf":1.0}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"284":{"tf":1.0},"292":{"tf":1.0}}}}}}}}},"i":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}},"df":43,"docs":{"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"204":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.0},"212":{"tf":1.0},"214":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":2.449489742783178},"220":{"tf":1.4142135623730951},"226":{"tf":1.4142135623730951},"366":{"tf":1.0},"373":{"tf":1.4142135623730951},"374":{"tf":2.0},"380":{"tf":1.0},"539":{"tf":1.4142135623730951},"724":{"tf":1.0},"730":{"tf":2.23606797749979},"731":{"tf":1.4142135623730951},"732":{"tf":3.872983346207417},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":3.605551275463989},"736":{"tf":1.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"740":{"tf":1.4142135623730951},"772":{"tf":1.0},"773":{"tf":1.7320508075688772},"776":{"tf":1.7320508075688772},"777":{"tf":1.0},"779":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":2.23606797749979},"832":{"tf":1.4142135623730951},"840":{"tf":1.0},"876":{"tf":1.0},"931":{"tf":1.4142135623730951}}},"df":0,"docs":{},"w":{"(":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":124,"docs":{"1004":{"tf":1.0},"103":{"tf":1.0},"107":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0},"136":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":2.23606797749979},"22":{"tf":1.0},"221":{"tf":1.4142135623730951},"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"254":{"tf":1.0},"28":{"tf":1.0},"284":{"tf":1.4142135623730951},"289":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.0},"308":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"38":{"tf":1.0},"39":{"tf":1.0},"407":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"46":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"470":{"tf":1.7320508075688772},"485":{"tf":1.0},"49":{"tf":1.0},"542":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"6":{"tf":1.0},"600":{"tf":2.0},"602":{"tf":2.449489742783178},"605":{"tf":1.0},"606":{"tf":1.0},"614":{"tf":1.0},"618":{"tf":1.0},"619":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.4142135623730951},"640":{"tf":1.0},"643":{"tf":1.0},"649":{"tf":1.0},"653":{"tf":1.0},"659":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":2.6457513110645907},"700":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":2.23606797749979},"776":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"796":{"tf":1.7320508075688772},"799":{"tf":2.0},"811":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"83":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"870":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0},"881":{"tf":1.0},"890":{"tf":1.0},"895":{"tf":1.0},"913":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.7320508075688772},"95":{"tf":1.0},"959":{"tf":1.0},"975":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"281":{"tf":1.0},"284":{"tf":1.0}}}}}}}}}}}}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"44":{"tf":1.0},"599":{"tf":1.0},"711":{"tf":1.4142135623730951}},"g":{"df":9,"docs":{"165":{"tf":1.0},"412":{"tf":1.0},"53":{"tf":1.0},"544":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.0},"640":{"tf":1.0},"776":{"tf":1.0},"945":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"d":{"df":10,"docs":{"38":{"tf":1.0},"461":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.0},"600":{"tf":1.0},"653":{"tf":1.0},"722":{"tf":1.4142135623730951},"796":{"tf":1.0},"799":{"tf":1.0}}},"df":0,"docs":{}}}}}},"p":{"df":0,"docs":{},"h":{"a":{"_":{"df":0,"docs":{},"v":{"df":2,"docs":{"721":{"tf":1.4142135623730951},"722":{"tf":2.0}}},"w":{"df":1,"docs":{"722":{"tf":1.0}}},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"u":{"df":2,"docs":{"721":{"tf":1.0},"723":{"tf":1.0}}},"v":{"df":3,"docs":{"721":{"tf":1.7320508075688772},"722":{"tf":1.4142135623730951},"723":{"tf":1.0}},"}":{",":{"\\":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"v":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":2,"docs":{"724":{"tf":1.0},"725":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"i":{"df":49,"docs":{"131":{"tf":1.0},"132":{"tf":1.0},"149":{"tf":1.4142135623730951},"155":{"tf":1.0},"156":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"210":{"tf":1.0},"234":{"tf":1.0},"252":{"tf":1.4142135623730951},"292":{"tf":1.0},"363":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"38":{"tf":1.0},"424":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"483":{"tf":1.0},"501":{"tf":1.4142135623730951},"503":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.4142135623730951},"61":{"tf":1.0},"615":{"tf":1.0},"650":{"tf":1.0},"659":{"tf":1.0},"680":{"tf":1.0},"697":{"tf":1.7320508075688772},"722":{"tf":1.0},"74":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"776":{"tf":1.0},"811":{"tf":1.0},"853":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"900":{"tf":1.0},"938":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":26,"docs":{"1011":{"tf":1.0},"124":{"tf":1.4142135623730951},"131":{"tf":1.0},"132":{"tf":1.0},"140":{"tf":1.0},"159":{"tf":1.0},"170":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.4142135623730951},"210":{"tf":1.0},"221":{"tf":1.0},"362":{"tf":1.0},"381":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"531":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"818":{"tf":1.0},"88":{"tf":1.0},"928":{"tf":1.0},"953":{"tf":1.0}},"n":{"df":25,"docs":{"1014":{"tf":1.0},"171":{"tf":1.0},"195":{"tf":1.0},"203":{"tf":1.0},"213":{"tf":1.4142135623730951},"215":{"tf":1.0},"227":{"tf":1.4142135623730951},"38":{"tf":1.0},"39":{"tf":1.0},"486":{"tf":1.0},"55":{"tf":2.0},"630":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.7320508075688772},"761":{"tf":1.0},"810":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.0},"863":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0}}}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":14,"docs":{"326":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"51":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"778":{"tf":1.0},"792":{"tf":1.0},"81":{"tf":1.0},"874":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"740":{"tf":1.0}}}}}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":45,"docs":{"151":{"tf":1.0},"154":{"tf":1.0},"231":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.0},"281":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"341":{"tf":1.4142135623730951},"348":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.0},"481":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"532":{"tf":1.0},"550":{"tf":1.0},"563":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"67":{"tf":1.7320508075688772},"698":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"735":{"tf":2.8284271247461903},"744":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.0},"848":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}},"z":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"532":{"tf":1.0}}}}}}}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"21":{"tf":1.0},"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"270":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":2,"docs":{"325":{"tf":1.0},"735":{"tf":2.0}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"482":{"tf":1.0},"521":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":49,"docs":{"155":{"tf":1.0},"184":{"tf":1.4142135623730951},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"3":{"tf":1.4142135623730951},"308":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"466":{"tf":1.0},"469":{"tf":1.0},"471":{"tf":1.0},"472":{"tf":1.0},"522":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.4142135623730951},"577":{"tf":1.0},"58":{"tf":1.0},"602":{"tf":1.4142135623730951},"638":{"tf":1.0},"651":{"tf":1.0},"659":{"tf":1.0},"683":{"tf":1.0},"735":{"tf":1.7320508075688772},"763":{"tf":1.0},"765":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"807":{"tf":1.0},"814":{"tf":1.7320508075688772},"829":{"tf":1.7320508075688772},"83":{"tf":1.0},"831":{"tf":1.4142135623730951},"850":{"tf":1.0},"920":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":2.449489742783178},"932":{"tf":3.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"989":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"50":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0}}}}},"n":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"196":{"tf":1.0}}}}},"y":{"df":0,"docs":{},"s":{"df":1,"docs":{"571":{"tf":1.0}},"i":{"df":5,"docs":{"365":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":2.0},"576":{"tf":1.0}}}},"z":{"df":2,"docs":{"3":{"tf":1.0},"724":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"500":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"45":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}}}},"d":{"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":10,"docs":{"114":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"382":{"tf":1.0},"412":{"tf":1.0},"420":{"tf":1.0},"441":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"697":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":1,"docs":{"627":{"tf":1.0}}}},"o":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"95":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"k":{"4":{"df":0,"docs":{},"n":{"df":1,"docs":{"878":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"c":{"df":4,"docs":{"209":{"tf":1.0},"500":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"843":{"tf":1.0}}},"df":0,"docs":{}}},"y":{"df":1,"docs":{"249":{"tf":1.4142135623730951}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"470":{"tf":1.0},"933":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":7,"docs":{"322":{"tf":1.0},"336":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.7320508075688772},"365":{"tf":1.4142135623730951},"913":{"tf":1.0},"917":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"h":{"df":36,"docs":{"203":{"tf":1.0},"207":{"tf":1.0},"231":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":2.23606797749979},"300":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"363":{"tf":1.0},"364":{"tf":1.0},"374":{"tf":1.0},"428":{"tf":1.0},"450":{"tf":1.4142135623730951},"497":{"tf":1.0},"521":{"tf":1.0},"602":{"tf":1.4142135623730951},"61":{"tf":1.0},"666":{"tf":1.0},"673":{"tf":1.0},"694":{"tf":1.0},"715":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"77":{"tf":1.0},"778":{"tf":1.4142135623730951},"78":{"tf":1.0},"799":{"tf":1.4142135623730951},"81":{"tf":1.0},"84":{"tf":1.0},"85":{"tf":1.0},"860":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"942":{"tf":1.0},"975":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"553":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"38":{"tf":1.0}}}}},"df":2,"docs":{"270":{"tf":1.0},"912":{"tf":1.7320508075688772}}}},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":5,"docs":{"249":{"tf":1.0},"3":{"tf":1.0},"453":{"tf":1.0},"567":{"tf":1.0},"74":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":12,"docs":{"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.4142135623730951},"528":{"tf":1.0},"629":{"tf":1.0},"715":{"tf":1.7320508075688772},"811":{"tf":1.4142135623730951},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.7320508075688772},"817":{"tf":1.0},"848":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":14,"docs":{"151":{"tf":1.0},"152":{"tf":1.0},"199":{"tf":1.7320508075688772},"208":{"tf":1.0},"300":{"tf":1.0},"588":{"tf":1.0},"653":{"tf":1.0},"735":{"tf":2.449489742783178},"761":{"tf":1.0},"800":{"tf":1.0},"831":{"tf":1.0},"852":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"720":{"tf":1.0},"723":{"tf":1.0}}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":3,"docs":{"720":{"tf":1.0},"735":{"tf":1.0},"987":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"588":{"tf":1.0}}}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"205":{"tf":1.0},"843":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"#":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"n":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":49,"docs":{"17":{"tf":1.0},"19":{"tf":1.7320508075688772},"205":{"tf":1.0},"212":{"tf":1.0},"22":{"tf":2.0},"234":{"tf":1.0},"279":{"tf":2.23606797749979},"280":{"tf":1.4142135623730951},"281":{"tf":1.0},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.7320508075688772},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"362":{"tf":1.0},"372":{"tf":1.4142135623730951},"382":{"tf":1.0},"390":{"tf":1.0},"395":{"tf":1.0},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"455":{"tf":1.0},"461":{"tf":1.4142135623730951},"519":{"tf":1.0},"565":{"tf":1.0},"622":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.4142135623730951},"847":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0},"95":{"tf":1.0},"961":{"tf":1.0}}},"o":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"p":{"_":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":1,"docs":{"207":{"tf":1.0}}}}},"df":3,"docs":{"199":{"tf":1.0},"234":{"tf":1.0},"919":{"tf":1.0}}}},"df":4,"docs":{"185":{"tf":1.0},"191":{"tf":1.4142135623730951},"904":{"tf":1.0},"921":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"199":{"tf":1.0},"40":{"tf":1.0}}},"r":{"df":10,"docs":{"155":{"tf":1.0},"267":{"tf":1.0},"48":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"534":{"tf":1.0},"629":{"tf":1.0},"680":{"tf":1.0},"844":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"333":{"tf":1.0},"602":{"tf":2.8284271247461903}},"i":{"df":0,"docs":{},"x":{"df":4,"docs":{"430":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}},"l":{"df":1,"docs":{"95":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{},"’":{"df":1,"docs":{"95":{"tf":1.0}}}},"i":{"c":{"df":19,"docs":{"1004":{"tf":1.0},"125":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.0},"346":{"tf":1.0},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"417":{"tf":1.4142135623730951},"42":{"tf":1.0},"445":{"tf":1.0},"448":{"tf":1.0},"853":{"tf":1.0},"95":{"tf":1.7320508075688772},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"971":{"tf":1.0},"973":{"tf":1.4142135623730951}}},"df":26,"docs":{"1003":{"tf":1.0},"132":{"tf":1.4142135623730951},"140":{"tf":1.0},"148":{"tf":1.0},"151":{"tf":1.4142135623730951},"152":{"tf":1.0},"154":{"tf":1.0},"159":{"tf":1.0},"225":{"tf":1.0},"251":{"tf":1.0},"281":{"tf":1.0},"302":{"tf":1.0},"348":{"tf":1.0},"378":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"455":{"tf":1.0},"499":{"tf":1.0},"51":{"tf":1.0},"532":{"tf":1.0},"573":{"tf":2.23606797749979},"735":{"tf":1.0},"786":{"tf":1.0},"804":{"tf":1.0},"837":{"tf":1.0},"883":{"tf":1.0}}},"y":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"284":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"721":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"a":{"c":{"df":0,"docs":{},"h":{"df":34,"docs":{"1007":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"140":{"tf":1.0},"147":{"tf":1.0},"149":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"29":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.4142135623730951},"368":{"tf":1.0},"373":{"tf":1.0},"39":{"tf":1.0},"410":{"tf":1.0},"416":{"tf":1.4142135623730951},"427":{"tf":1.0},"429":{"tf":1.4142135623730951},"46":{"tf":1.0},"563":{"tf":1.0},"6":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"658":{"tf":1.0},"694":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.4142135623730951},"942":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":14,"docs":{"1014":{"tf":1.0},"169":{"tf":1.0},"204":{"tf":1.0},"239":{"tf":1.0},"246":{"tf":1.0},"253":{"tf":1.0},"274":{"tf":1.0},"457":{"tf":1.0},"564":{"tf":1.0},"721":{"tf":1.0},"727":{"tf":1.0},"786":{"tf":1.0},"817":{"tf":1.0},"846":{"tf":1.0}}}}},"v":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"715":{"tf":1.4142135623730951},"716":{"tf":1.0},"717":{"tf":1.0},"724":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"v":{"[":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"2":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"[":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"715":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":3,"docs":{"717":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"716":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"715":{"tf":1.7320508075688772}}}},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"715":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"716":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":1,"docs":{"716":{"tf":1.0}}}}},"df":34,"docs":{"112":{"tf":1.0},"126":{"tf":1.7320508075688772},"16":{"tf":1.0},"193":{"tf":1.0},"272":{"tf":1.0},"450":{"tf":1.7320508075688772},"709":{"tf":1.0},"710":{"tf":2.0},"711":{"tf":2.23606797749979},"714":{"tf":1.7320508075688772},"715":{"tf":2.8284271247461903},"716":{"tf":2.0},"717":{"tf":1.7320508075688772},"720":{"tf":3.3166247903554},"721":{"tf":5.0990195135927845},"722":{"tf":3.872983346207417},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"725":{"tf":1.4142135623730951},"729":{"tf":1.4142135623730951},"811":{"tf":1.0},"815":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"876":{"tf":1.4142135623730951},"878":{"tf":1.7320508075688772},"879":{"tf":4.898979485566356},"880":{"tf":3.1622776601683795},"881":{"tf":2.6457513110645907},"885":{"tf":2.0},"890":{"tf":1.0},"984":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"872":{"tf":1.0},"875":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"_":{"a":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"\"":{"df":0,"docs":{},"{":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"272":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":7,"docs":{"184":{"tf":1.0},"235":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.4142135623730951},"721":{"tf":1.0},"725":{"tf":1.0},"996":{"tf":1.0}}}}}}}},"r":{"df":1,"docs":{"908":{"tf":1.0}}},"t":{"df":1,"docs":{"61":{"tf":1.0}}}},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":14,"docs":{"114":{"tf":1.0},"208":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"340":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"568":{"tf":1.0},"670":{"tf":1.0},"697":{"tf":1.4142135623730951},"777":{"tf":1.0},"95":{"tf":1.0}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"50":{"tf":1.0}}}}}}},"o":{"df":4,"docs":{"38":{"tf":1.0},"39":{"tf":1.0},"46":{"tf":1.0},"54":{"tf":1.0}}}},"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"470":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":5,"docs":{"147":{"tf":1.0},"366":{"tf":1.0},"373":{"tf":1.7320508075688772},"46":{"tf":1.0},"74":{"tf":1.0}}}}}},"df":0,"docs":{}}},"v":{"df":5,"docs":{"498":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":2.0},"502":{"tf":1.0},"512":{"tf":2.23606797749979}}}}}},"df":0,"docs":{},"e":{"a":{"df":2,"docs":{"1008":{"tf":1.0},"773":{"tf":1.0}}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":5,"docs":{"500":{"tf":1.0},"761":{"tf":1.4142135623730951},"832":{"tf":1.0},"850":{"tf":1.0},"874":{"tf":1.0}}}},"df":0,"docs":{}}},"g":{"df":2,"docs":{"831":{"tf":1.4142135623730951},"898":{"tf":1.0}},"u":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{}},"df":5,"docs":{"267":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"679":{"tf":1.0},"928":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"21":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"222":{"tf":1.0},"23":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":2.0},"416":{"tf":1.0},"429":{"tf":1.0},"749":{"tf":1.0},"773":{"tf":1.0},"879":{"tf":3.4641016151377544}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":6,"docs":{"264":{"tf":1.0},"267":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"742":{"tf":1.0},"779":{"tf":1.0}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":21,"docs":{"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"147":{"tf":1.0},"166":{"tf":1.0},"206":{"tf":1.0},"216":{"tf":1.0},"257":{"tf":1.0},"406":{"tf":1.0},"461":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"619":{"tf":1.0},"747":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"786":{"tf":1.0},"831":{"tf":1.0},"874":{"tf":1.0},"996":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"y":{"(":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"455":{"tf":1.0}}}}}},"df":5,"docs":{"170":{"tf":1.0},"332":{"tf":1.0},"432":{"tf":1.0},"455":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"223":{"tf":1.4142135623730951}}}},"u":{"d":{"a":{"df":1,"docs":{"782":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":119,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.7320508075688772},"105":{"tf":1.4142135623730951},"106":{"tf":1.0},"120":{"tf":1.4142135623730951},"122":{"tf":1.0},"133":{"tf":1.4142135623730951},"136":{"tf":1.0},"14":{"tf":1.4142135623730951},"147":{"tf":1.4142135623730951},"150":{"tf":1.0},"161":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.4142135623730951},"182":{"tf":1.0},"192":{"tf":1.4142135623730951},"195":{"tf":1.0},"214":{"tf":1.4142135623730951},"215":{"tf":1.0},"228":{"tf":1.4142135623730951},"229":{"tf":1.0},"242":{"tf":1.4142135623730951},"247":{"tf":1.0},"260":{"tf":1.4142135623730951},"268":{"tf":1.0},"277":{"tf":1.4142135623730951},"279":{"tf":1.0},"291":{"tf":1.4142135623730951},"294":{"tf":1.0},"308":{"tf":1.4142135623730951},"311":{"tf":1.0},"319":{"tf":1.4142135623730951},"322":{"tf":1.0},"35":{"tf":1.4142135623730951},"359":{"tf":1.4142135623730951},"366":{"tf":1.0},"383":{"tf":1.4142135623730951},"386":{"tf":1.0},"397":{"tf":1.4142135623730951},"400":{"tf":1.0},"409":{"tf":1.4142135623730951},"430":{"tf":1.0},"447":{"tf":1.4142135623730951},"451":{"tf":1.0},"462":{"tf":1.4142135623730951},"465":{"tf":1.0},"479":{"tf":1.4142135623730951},"481":{"tf":1.0},"492":{"tf":1.4142135623730951},"495":{"tf":1.0},"510":{"tf":1.4142135623730951},"513":{"tf":1.0},"532":{"tf":1.4142135623730951},"535":{"tf":1.0},"546":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.4142135623730951},"563":{"tf":1.0},"583":{"tf":1.4142135623730951},"584":{"tf":1.0},"595":{"tf":1.4142135623730951},"598":{"tf":1.0},"610":{"tf":1.4142135623730951},"613":{"tf":1.0},"624":{"tf":1.4142135623730951},"627":{"tf":1.0},"646":{"tf":1.4142135623730951},"649":{"tf":1.0},"661":{"tf":1.4142135623730951},"664":{"tf":1.0},"675":{"tf":1.4142135623730951},"678":{"tf":1.0},"689":{"tf":1.4142135623730951},"692":{"tf":1.0},"706":{"tf":1.4142135623730951},"709":{"tf":1.0},"726":{"tf":1.4142135623730951},"730":{"tf":1.0},"738":{"tf":1.4142135623730951},"74":{"tf":1.4142135623730951},"741":{"tf":1.0},"754":{"tf":1.4142135623730951},"757":{"tf":1.0},"768":{"tf":1.4142135623730951},"771":{"tf":1.0},"780":{"tf":1.4142135623730951},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.4142135623730951},"795":{"tf":1.0},"805":{"tf":1.4142135623730951},"808":{"tf":1.0},"824":{"tf":1.4142135623730951},"827":{"tf":1.0},"838":{"tf":1.4142135623730951},"857":{"tf":1.0},"869":{"tf":1.4142135623730951},"871":{"tf":1.0},"888":{"tf":1.4142135623730951},"891":{"tf":1.0},"90":{"tf":1.4142135623730951},"905":{"tf":1.4142135623730951},"908":{"tf":1.4142135623730951},"922":{"tf":1.4142135623730951},"923":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.4142135623730951},"940":{"tf":1.0},"954":{"tf":1.4142135623730951},"957":{"tf":1.0},"971":{"tf":1.4142135623730951},"974":{"tf":1.0},"985":{"tf":1.4142135623730951},"988":{"tf":1.0},"999":{"tf":1.4142135623730951}},"i":{"c":{"df":0,"docs":{},"l":{"df":3,"docs":{"214":{"tf":1.4142135623730951},"905":{"tf":1.0},"923":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"414":{"tf":1.7320508075688772},"423":{"tf":1.0}}}}}}},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}},"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"i":{"df":1,"docs":{"343":{"tf":1.0}}}}},"df":0,"docs":{},"k":{"df":7,"docs":{"254":{"tf":1.0},"497":{"tf":1.4142135623730951},"6":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"848":{"tf":1.0},"933":{"tf":1.0}}},"n":{".":{"1":{"df":1,"docs":{"331":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"1014":{"tf":1.0},"209":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.4142135623730951},"361":{"tf":1.0},"727":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"807":{"tf":1.0},"842":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"29":{"tf":1.0},"53":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"t":{"!":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"x":{"df":1,"docs":{"221":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"347":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}}}}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"347":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"!":{"(":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"x":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":1,"docs":{"435":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"df":5,"docs":{"350":{"tf":1.0},"418":{"tf":1.0},"576":{"tf":1.0},"582":{"tf":1.0},"781":{"tf":1.0}}}},"t":{"'":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}},"(":{"df":1,"docs":{"602":{"tf":1.0}}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"6":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"x":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"668":{"tf":1.0},"670":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"668":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":90,"docs":{"1":{"tf":2.23606797749979},"10":{"tf":1.0},"11":{"tf":1.0},"114":{"tf":1.0},"12":{"tf":1.0},"13":{"tf":1.0},"14":{"tf":1.4142135623730951},"15":{"tf":1.0},"16":{"tf":1.0},"18":{"tf":1.4142135623730951},"2":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"3":{"tf":2.6457513110645907},"35":{"tf":1.0},"373":{"tf":2.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.0},"4":{"tf":1.0},"410":{"tf":2.23606797749979},"411":{"tf":1.4142135623730951},"412":{"tf":1.7320508075688772},"413":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.7320508075688772},"418":{"tf":2.23606797749979},"419":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"423":{"tf":1.4142135623730951},"424":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"465":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"472":{"tf":1.0},"473":{"tf":1.4142135623730951},"5":{"tf":3.0},"598":{"tf":1.4142135623730951},"599":{"tf":2.0},"6":{"tf":3.872983346207417},"600":{"tf":3.4641016151377544},"602":{"tf":5.196152422706632},"603":{"tf":4.47213595499958},"605":{"tf":2.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"653":{"tf":2.8284271247461903},"654":{"tf":1.4142135623730951},"655":{"tf":1.0},"659":{"tf":1.4142135623730951},"663":{"tf":1.0},"666":{"tf":2.0},"668":{"tf":1.0},"670":{"tf":1.0},"692":{"tf":2.23606797749979},"693":{"tf":1.4142135623730951},"694":{"tf":2.0},"695":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":3.0},"698":{"tf":1.4142135623730951},"699":{"tf":2.0},"7":{"tf":1.7320508075688772},"700":{"tf":1.7320508075688772},"701":{"tf":1.4142135623730951},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.4142135623730951},"705":{"tf":1.4142135623730951},"706":{"tf":1.4142135623730951},"707":{"tf":1.0},"708":{"tf":1.0},"8":{"tf":1.4142135623730951},"81":{"tf":1.0},"9":{"tf":1.4142135623730951},"959":{"tf":1.0},"971":{"tf":1.0},"976":{"tf":1.0},"979":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"(":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":1,"docs":{"666":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"u":{"b":{"df":2,"docs":{"600":{"tf":1.0},"934":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"d":{"df":4,"docs":{"24":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"603":{"tf":1.0},"7":{"tf":1.4142135623730951}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"1":{"tf":1.0},"7":{"tf":1.4142135623730951},"9":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":3,"docs":{"205":{"tf":1.0},"6":{"tf":1.7320508075688772},"7":{"tf":1.4142135623730951}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}},"`":{"df":1,"docs":{"602":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.4142135623730951},"223":{"tf":1.0}},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"208":{"tf":1.7320508075688772},"221":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":40,"docs":{"155":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"204":{"tf":2.449489742783178},"205":{"tf":3.1622776601683795},"208":{"tf":3.1622776601683795},"216":{"tf":1.4142135623730951},"221":{"tf":2.449489742783178},"3":{"tf":1.0},"323":{"tf":1.0},"430":{"tf":2.23606797749979},"431":{"tf":1.4142135623730951},"432":{"tf":1.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.7320508075688772},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"445":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.0},"636":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":2.6457513110645907},"735":{"tf":1.0}},"e":{"d":{"(":{"a":{"df":1,"docs":{"208":{"tf":2.0}}},"b":{"df":1,"docs":{"208":{"tf":2.449489742783178}}},"c":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"d":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"816":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"107":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"952":{"tf":1.0}}}}},"o":{"c":{"df":0,"docs":{},"i":{"df":26,"docs":{"138":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"209":{"tf":1.0},"24":{"tf":1.4142135623730951},"273":{"tf":1.0},"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"346":{"tf":1.7320508075688772},"348":{"tf":1.7320508075688772},"349":{"tf":2.23606797749979},"350":{"tf":1.0},"351":{"tf":1.7320508075688772},"571":{"tf":1.0},"761":{"tf":1.4142135623730951},"815":{"tf":1.0},"895":{"tf":1.0},"902":{"tf":1.0},"932":{"tf":1.0},"941":{"tf":1.0},"961":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"m":{"df":28,"docs":{"206":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"39":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"528":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"717":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"863":{"tf":1.0},"933":{"tf":1.0}},"p":{"df":0,"docs":{},"t":{"df":13,"docs":{"199":{"tf":1.0},"231":{"tf":1.4142135623730951},"267":{"tf":1.0},"402":{"tf":1.7320508075688772},"46":{"tf":1.0},"514":{"tf":1.0},"692":{"tf":1.0},"697":{"tf":1.4142135623730951},"700":{"tf":1.0},"701":{"tf":2.0},"710":{"tf":1.0},"721":{"tf":1.4142135623730951},"724":{"tf":1.0}}}}},"r":{"df":4,"docs":{"267":{"tf":1.0},"303":{"tf":1.0},"45":{"tf":1.0},"514":{"tf":1.0}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"990":{"tf":1.0}}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"602":{"tf":1.0}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"58":{"tf":1.0},"959":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"m":{".":{"0":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"l":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"[":{"df":0,"docs":{},"i":{"]":{".":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"440":{"tf":1.0},"600":{"tf":1.0}}}},"t":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"879":{"tf":1.0}}},"k":{"df":19,"docs":{"114":{"tf":1.0},"124":{"tf":1.4142135623730951},"127":{"tf":1.4142135623730951},"249":{"tf":1.0},"255":{"tf":1.4142135623730951},"356":{"tf":1.0},"453":{"tf":1.4142135623730951},"505":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":2.23606797749979},"573":{"tf":1.0},"577":{"tf":2.23606797749979},"58":{"tf":1.0},"619":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"230":{"tf":1.0}},"t":{"df":20,"docs":{"123":{"tf":1.0},"231":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":2.6457513110645907},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"437":{"tf":1.0},"450":{"tf":1.4142135623730951},"497":{"tf":1.0},"573":{"tf":1.0},"609":{"tf":1.0},"689":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"733":{"tf":1.0},"797":{"tf":1.0},"831":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0}},"s":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"342":{"tf":2.0},"346":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"53":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"231":{"tf":1.0},"40":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"565":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":4,"docs":{"373":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"669":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":13,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"133":{"tf":1.4142135623730951},"198":{"tf":2.0},"203":{"tf":1.0},"205":{"tf":1.0},"370":{"tf":1.0},"571":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"928":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":2,"docs":{"378":{"tf":1.0},"883":{"tf":1.0}}}}}}}}},"df":23,"docs":{"115":{"tf":1.0},"121":{"tf":1.4142135623730951},"128":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"282":{"tf":1.0},"304":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.4142135623730951},"354":{"tf":1.0},"39":{"tf":1.0},"45":{"tf":1.4142135623730951},"457":{"tf":1.0},"53":{"tf":1.0},"639":{"tf":1.0},"701":{"tf":1.0},"819":{"tf":1.0},"850":{"tf":1.0},"935":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.4142135623730951},"965":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"244":{"tf":1.0}}}}}}},"df":0,"docs":{},"g":{"df":3,"docs":{"182":{"tf":1.0},"311":{"tf":1.0},"79":{"tf":1.0}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"106":{"tf":1.0},"93":{"tf":1.0},"988":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":4,"docs":{"410":{"tf":1.0},"940":{"tf":1.0},"945":{"tf":1.0},"957":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"h":{"df":2,"docs":{"849":{"tf":1.7320508075688772},"850":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"175":{"tf":1.0},"177":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"848":{"tf":1.0},"95":{"tf":1.4142135623730951}}}}},"o":{"df":0,"docs":{},"r":{"df":115,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.4142135623730951},"169":{"tf":2.0},"17":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.4142135623730951},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"284":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"3":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"323":{"tf":1.4142135623730951},"324":{"tf":1.0},"327":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":1.0},"345":{"tf":2.449489742783178},"346":{"tf":3.0},"347":{"tf":1.0},"348":{"tf":1.4142135623730951},"349":{"tf":3.1622776601683795},"350":{"tf":2.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"45":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.4142135623730951},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.7320508075688772},"549":{"tf":2.449489742783178},"550":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"552":{"tf":1.0},"553":{"tf":2.23606797749979},"554":{"tf":1.0},"555":{"tf":1.4142135623730951},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"563":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"737":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"765":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"831":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":1.0},"85":{"tf":1.7320508075688772},"857":{"tf":1.0},"871":{"tf":1.0},"876":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"94":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"325":{"tf":1.0}},"h":{"df":0,"docs":{},"i":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}},"y":{"_":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"2":{"df":1,"docs":{"553":{"tf":1.0}}},"3":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":3,"docs":{"349":{"tf":1.7320508075688772},"350":{"tf":1.0},"351":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"350":{"tf":1.7320508075688772}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"349":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"o":{"df":1,"docs":{"208":{"tf":1.0}},"m":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"191":{"tf":2.0},"813":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0}}}},"df":5,"docs":{"427":{"tf":1.0},"442":{"tf":1.0},"516":{"tf":1.0},"847":{"tf":1.0},"959":{"tf":1.0}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"843":{"tf":1.0},"876":{"tf":1.0}}}}}}},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"776":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"v":{"a":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"63":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"65":{"tf":1.0}}}},"df":0,"docs":{}},"df":74,"docs":{"166":{"tf":1.0},"169":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":2.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.0},"264":{"tf":1.0},"282":{"tf":1.0},"346":{"tf":1.0},"372":{"tf":1.0},"38":{"tf":1.0},"417":{"tf":1.0},"430":{"tf":2.6457513110645907},"431":{"tf":1.7320508075688772},"432":{"tf":2.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":1.4142135623730951},"436":{"tf":2.0},"437":{"tf":2.0},"438":{"tf":1.0},"439":{"tf":2.23606797749979},"440":{"tf":1.4142135623730951},"441":{"tf":1.4142135623730951},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.7320508075688772},"445":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.4142135623730951},"450":{"tf":2.23606797749979},"46":{"tf":1.0},"47":{"tf":2.449489742783178},"497":{"tf":1.4142135623730951},"55":{"tf":1.0},"563":{"tf":1.0},"568":{"tf":1.0},"619":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.4142135623730951},"65":{"tf":1.0},"67":{"tf":1.0},"69":{"tf":1.4142135623730951},"709":{"tf":1.0},"710":{"tf":1.7320508075688772},"711":{"tf":1.4142135623730951},"712":{"tf":1.0},"714":{"tf":2.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.0},"718":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":3.0},"723":{"tf":2.23606797749979},"724":{"tf":2.0},"725":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.4142135623730951},"74":{"tf":1.0},"75":{"tf":1.0},"776":{"tf":1.4142135623730951},"78":{"tf":1.0},"780":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":2.0},"831":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"996":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":1,"docs":{"78":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":12,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"479":{"tf":1.4142135623730951},"51":{"tf":1.0},"515":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"i":{"d":{"df":28,"docs":{"1008":{"tf":1.0},"121":{"tf":1.0},"128":{"tf":1.0},"141":{"tf":1.0},"144":{"tf":1.0},"196":{"tf":1.0},"200":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"252":{"tf":1.4142135623730951},"35":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"520":{"tf":1.0},"575":{"tf":1.0},"640":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"920":{"tf":1.0},"959":{"tf":1.0},"982":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"776":{"tf":1.0}}},"df":13,"docs":{"125":{"tf":1.0},"131":{"tf":1.0},"152":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"63":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0}}},"y":{"df":6,"docs":{"18":{"tf":1.0},"500":{"tf":1.0},"651":{"tf":1.0},"696":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"651":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":1.0}}}},"}":{"_":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":1,"docs":{"47":{"tf":2.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"·":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"b":{"\"":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"a":{"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":1,"docs":{"786":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"a":{"b":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"_":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"252":{"tf":1.0},"261":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"252":{"tf":1.0},"261":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"568":{"tf":2.0},"570":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":47,"docs":{"1004":{"tf":1.0},"126":{"tf":1.0},"184":{"tf":1.0},"203":{"tf":1.0},"221":{"tf":1.4142135623730951},"284":{"tf":1.0},"3":{"tf":1.0},"368":{"tf":1.4142135623730951},"436":{"tf":1.0},"437":{"tf":1.4142135623730951},"450":{"tf":2.0},"47":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.7320508075688772},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"603":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"634":{"tf":1.4142135623730951},"636":{"tf":1.4142135623730951},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"642":{"tf":1.0},"709":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":3.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"761":{"tf":1.4142135623730951},"831":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"933":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"29":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":16,"docs":{"437":{"tf":1.0},"56":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.7320508075688772},"63":{"tf":1.0},"633":{"tf":1.0},"636":{"tf":1.4142135623730951},"637":{"tf":1.0},"65":{"tf":1.7320508075688772},"67":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"720":{"tf":2.6457513110645907},"723":{"tf":1.0},"724":{"tf":2.0}},"s":{"/":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"449":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":8,"docs":{"217":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.4142135623730951},"501":{"tf":1.0},"891":{"tf":1.0},"894":{"tf":1.4142135623730951},"908":{"tf":1.0},"911":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"437":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":23,"docs":{"126":{"tf":1.0},"146":{"tf":1.0},"482":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"512":{"tf":1.0},"545":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"586":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"627":{"tf":1.0},"628":{"tf":1.0},"635":{"tf":1.4142135623730951},"639":{"tf":1.0},"642":{"tf":1.0},"705":{"tf":1.0},"732":{"tf":1.0},"792":{"tf":1.0},"831":{"tf":1.0},"928":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"d":{"df":6,"docs":{"108":{"tf":1.4142135623730951},"124":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.0},"576":{"tf":1.0},"632":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":2,"docs":{"234":{"tf":1.4142135623730951},"370":{"tf":1.0}}},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"199":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"n":{"c":{"df":24,"docs":{"18":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"205":{"tf":2.23606797749979},"22":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"370":{"tf":1.0},"375":{"tf":3.0},"384":{"tf":1.0},"385":{"tf":1.0},"406":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"418":{"tf":1.4142135623730951},"427":{"tf":1.0},"429":{"tf":1.0},"48":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"759":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"945":{"tf":1.0}},"e":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"n":{"d":{"df":1,"docs":{"199":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":5,"docs":{"322":{"tf":1.0},"340":{"tf":2.0},"341":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"359":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":13,"docs":{"257":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"507":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"849":{"tf":1.0}}},"r":{"df":0,"docs":{},"e":{"df":6,"docs":{"170":{"tf":1.4142135623730951},"322":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.4142135623730951},"588":{"tf":1.0},"7":{"tf":1.0}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":15,"docs":{"118":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.4142135623730951},"58":{"tf":1.0},"602":{"tf":1.4142135623730951},"670":{"tf":1.0},"673":{"tf":1.7320508075688772},"701":{"tf":1.0},"705":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":2.23606797749979}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"199":{"tf":1.0}}}}}}}}}},"{":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":1,"docs":{"45":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"5":{"8":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":101,"docs":{"124":{"tf":1.0},"126":{"tf":1.0},"137":{"tf":1.4142135623730951},"140":{"tf":1.4142135623730951},"141":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"184":{"tf":1.4142135623730951},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"207":{"tf":1.0},"21":{"tf":1.0},"24":{"tf":1.7320508075688772},"240":{"tf":1.0},"3":{"tf":1.4142135623730951},"323":{"tf":1.0},"350":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"402":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.7320508075688772},"415":{"tf":1.0},"416":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.4142135623730951},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"46":{"tf":1.7320508075688772},"465":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.0},"495":{"tf":2.0},"496":{"tf":1.0},"497":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"50":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":1.0},"506":{"tf":1.0},"507":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"515":{"tf":1.4142135623730951},"519":{"tf":1.0},"52":{"tf":1.0},"521":{"tf":1.7320508075688772},"576":{"tf":1.0},"586":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"634":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"747":{"tf":1.0},"754":{"tf":1.0},"797":{"tf":1.0},"808":{"tf":2.23606797749979},"809":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"812":{"tf":1.0},"813":{"tf":1.7320508075688772},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.0},"823":{"tf":1.0},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.0},"878":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.0},"95":{"tf":1.0},"973":{"tf":1.0},"996":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"267":{"tf":1.0},"752":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}}},"i":{"c":{"df":14,"docs":{"1004":{"tf":1.0},"16":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.7320508075688772},"30":{"tf":1.0},"453":{"tf":1.0},"505":{"tf":1.0},"524":{"tf":1.0},"532":{"tf":1.0},"565":{"tf":1.0},"694":{"tf":1.0},"754":{"tf":1.0},"875":{"tf":1.0},"942":{"tf":1.0}}},"df":9,"docs":{"203":{"tf":1.0},"218":{"tf":1.0},"246":{"tf":1.0},"402":{"tf":1.0},"571":{"tf":1.4142135623730951},"66":{"tf":1.0},"670":{"tf":1.0},"778":{"tf":1.0},"932":{"tf":1.0}}},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"150":{"tf":1.0},"451":{"tf":1.0},"584":{"tf":1.0}}}},"df":0,"docs":{}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":10,"docs":{"313":{"tf":1.0},"315":{"tf":1.0},"449":{"tf":1.0},"517":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"890":{"tf":1.0}}}},"df":0,"docs":{}}},"df":14,"docs":{"208":{"tf":1.7320508075688772},"417":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"47":{"tf":3.3166247903554},"602":{"tf":1.0},"633":{"tf":1.7320508075688772},"696":{"tf":1.4142135623730951},"81":{"tf":2.0},"83":{"tf":2.23606797749979},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"835":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"58":{"tf":1.0},"721":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":34,"docs":{"1015":{"tf":1.0},"113":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.0},"198":{"tf":1.0},"205":{"tf":1.7320508075688772},"206":{"tf":1.0},"208":{"tf":1.0},"232":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"334":{"tf":1.0},"376":{"tf":1.0},"385":{"tf":1.0},"482":{"tf":1.0},"485":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"567":{"tf":1.0},"568":{"tf":1.0},"57":{"tf":1.0},"58":{"tf":1.7320508075688772},"63":{"tf":1.0},"656":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":1.0},"732":{"tf":1.0},"765":{"tf":1.0},"797":{"tf":1.0},"80":{"tf":1.0},"843":{"tf":1.4142135623730951},"987":{"tf":1.0}}}}},"df":70,"docs":{"108":{"tf":1.0},"113":{"tf":1.4142135623730951},"121":{"tf":1.0},"124":{"tf":1.0},"140":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.0},"220":{"tf":1.0},"222":{"tf":1.4142135623730951},"234":{"tf":1.0},"254":{"tf":1.0},"284":{"tf":1.0},"291":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"347":{"tf":1.0},"373":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.7320508075688772},"47":{"tf":1.0},"496":{"tf":1.0},"517":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.4142135623730951},"551":{"tf":1.0},"559":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"724":{"tf":1.7320508075688772},"736":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.7320508075688772},"761":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.0},"902":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.4142135623730951},"932":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"95":{"tf":1.0},"976":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":4,"docs":{"38":{"tf":1.0},"49":{"tf":1.7320508075688772},"500":{"tf":1.0},"714":{"tf":1.0}}},"y":{"df":0,"docs":{},"’":{"df":1,"docs":{"49":{"tf":1.0}}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":63,"docs":{"1014":{"tf":1.0},"121":{"tf":1.0},"126":{"tf":1.7320508075688772},"148":{"tf":1.0},"150":{"tf":1.0},"160":{"tf":1.0},"171":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"265":{"tf":1.0},"291":{"tf":1.4142135623730951},"303":{"tf":1.0},"338":{"tf":1.0},"344":{"tf":1.7320508075688772},"346":{"tf":1.0},"348":{"tf":1.0},"418":{"tf":1.0},"437":{"tf":1.7320508075688772},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"452":{"tf":1.0},"461":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"618":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"645":{"tf":1.0},"661":{"tf":1.0},"670":{"tf":1.0},"675":{"tf":1.0},"69":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"727":{"tf":1.0},"732":{"tf":1.0},"74":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.0},"811":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"837":{"tf":1.0},"879":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"961":{"tf":1.0},"985":{"tf":1.0}},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"670":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"g":{"df":1,"docs":{"267":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":20,"docs":{"126":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":2.23606797749979},"207":{"tf":1.0},"208":{"tf":5.5677643628300215},"221":{"tf":1.4142135623730951},"223":{"tf":1.0},"281":{"tf":1.0},"338":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"371":{"tf":1.0},"440":{"tf":1.4142135623730951},"450":{"tf":1.0},"521":{"tf":1.0},"670":{"tf":1.0},"721":{"tf":1.4142135623730951},"846":{"tf":1.0},"881":{"tf":1.0}},"{":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"h":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":4,"docs":{"602":{"tf":1.0},"848":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.0}}}},"v":{"df":3,"docs":{"563":{"tf":1.0},"666":{"tf":1.0},"761":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":17,"docs":{"1004":{"tf":1.0},"169":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"342":{"tf":1.0},"388":{"tf":1.0},"391":{"tf":1.0},"49":{"tf":1.0},"665":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.4142135623730951},"788":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"976":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":14,"docs":{"123":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"134":{"tf":1.4142135623730951},"72":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"81":{"tf":1.0},"832":{"tf":1.0},"913":{"tf":1.4142135623730951},"975":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"198":{"tf":1.0},"249":{"tf":1.0},"483":{"tf":1.0},"546":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"720":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":11,"docs":{"184":{"tf":1.4142135623730951},"251":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"394":{"tf":1.0},"51":{"tf":1.0},"720":{"tf":1.0},"797":{"tf":1.0},"800":{"tf":1.0},"874":{"tf":1.0},"934":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":5,"docs":{"106":{"tf":1.0},"113":{"tf":1.4142135623730951},"342":{"tf":1.0},"439":{"tf":1.4142135623730951},"735":{"tf":1.0}}}},"w":{"df":22,"docs":{"185":{"tf":1.0},"204":{"tf":1.4142135623730951},"267":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"45":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"520":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"619":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"777":{"tf":1.0},"814":{"tf":1.0},"992":{"tf":1.0}}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":8,"docs":{"209":{"tf":1.0},"239":{"tf":1.0},"402":{"tf":1.4142135623730951},"406":{"tf":1.0},"669":{"tf":1.0},"732":{"tf":1.0},"739":{"tf":1.0},"980":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"205":{"tf":1.7320508075688772},"414":{"tf":1.0},"603":{"tf":1.0}}},"y":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":6,"docs":{"249":{"tf":1.0},"315":{"tf":1.4142135623730951},"71":{"tf":1.0},"773":{"tf":1.0},"818":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":24,"docs":{"145":{"tf":1.0},"18":{"tf":1.0},"267":{"tf":2.449489742783178},"272":{"tf":1.0},"302":{"tf":1.0},"328":{"tf":1.0},"38":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"632":{"tf":1.0},"663":{"tf":1.0},"720":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"778":{"tf":1.0},"799":{"tf":1.0},"95":{"tf":1.0},"991":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"s":{"df":0,"docs":{},"i":{"d":{"df":4,"docs":{"158":{"tf":1.0},"166":{"tf":1.0},"3":{"tf":1.0},"528":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":14,"docs":{"1004":{"tf":1.4142135623730951},"124":{"tf":1.0},"265":{"tf":1.0},"30":{"tf":1.0},"376":{"tf":1.0},"609":{"tf":1.0},"640":{"tf":1.0},"66":{"tf":1.0},"732":{"tf":1.0},"849":{"tf":1.0},"870":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}}},"t":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"w":{"df":1,"docs":{"722":{"tf":1.0}}},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.4142135623730951},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":2.0}}}},"df":0,"docs":{}},"v":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}},"w":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":1,"docs":{"49":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"249":{"tf":1.4142135623730951},"292":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"515":{"tf":1.0},"575":{"tf":1.0},"658":{"tf":1.0},"673":{"tf":1.0},"72":{"tf":1.0},"749":{"tf":1.0},"810":{"tf":1.0},"856":{"tf":1.0},"886":{"tf":1.0}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":40,"docs":{"126":{"tf":1.0},"172":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"207":{"tf":1.0},"213":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"323":{"tf":1.0},"325":{"tf":1.0},"342":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.0},"407":{"tf":1.0},"430":{"tf":1.0},"469":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.0},"512":{"tf":1.0},"54":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.4142135623730951},"735":{"tf":1.0},"759":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.0},"81":{"tf":1.4142135623730951},"833":{"tf":1.0},"879":{"tf":1.0}}}}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":5,"docs":{"121":{"tf":1.0},"199":{"tf":1.4142135623730951},"214":{"tf":1.0},"326":{"tf":1.4142135623730951},"723":{"tf":1.0}}},"df":0,"docs":{}}}}},"f":{"df":4,"docs":{"44":{"tf":2.449489742783178},"45":{"tf":3.7416573867739413},"46":{"tf":2.23606797749979},"47":{"tf":2.449489742783178}},"t":{"df":1,"docs":{"231":{"tf":1.0}}}},"i":{"a":{"df":2,"docs":{"710":{"tf":1.0},"721":{"tf":1.0}},"s":{"df":1,"docs":{"725":{"tf":1.0}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"198":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.23606797749979}}}}},"df":5,"docs":{"198":{"tf":1.4142135623730951},"776":{"tf":2.0},"777":{"tf":2.0},"848":{"tf":1.0},"855":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":9,"docs":{"155":{"tf":1.0},"182":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.7320508075688772},"186":{"tf":1.7320508075688772},"346":{"tf":1.0},"347":{"tf":1.0},"388":{"tf":1.0},"520":{"tf":1.4142135623730951}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"163":{"tf":1.0},"342":{"tf":1.0},"388":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}}}}},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":7,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"26":{"tf":1.0},"525":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"831":{"tf":1.0}}}}},"d":{"df":4,"docs":{"207":{"tf":1.0},"322":{"tf":1.4142135623730951},"338":{"tf":1.4142135623730951},"348":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"95":{"tf":1.0}}}}}}},"t":{"df":22,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951},"208":{"tf":3.0},"25":{"tf":1.4142135623730951},"332":{"tf":2.0},"333":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.0},"522":{"tf":1.7320508075688772},"537":{"tf":1.7320508075688772},"539":{"tf":2.6457513110645907},"554":{"tf":1.0},"593":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.7320508075688772},"761":{"tf":1.0},"765":{"tf":1.0},"836":{"tf":1.0},"898":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":7,"docs":{"440":{"tf":1.0},"63":{"tf":1.4142135623730951},"634":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0}}},"df":0,"docs":{}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":2,"docs":{"204":{"tf":1.4142135623730951},"208":{"tf":1.0}}},"s":{"df":0,"docs":{},"k":{"df":1,"docs":{"544":{"tf":1.0}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"523":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"(":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"[":{"0":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"_":{"1":{"2":{"8":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"(":{"&":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"df":3,"docs":{"333":{"tf":1.0},"345":{"tf":1.4142135623730951},"52":{"tf":1.0}}},"df":1,"docs":{"634":{"tf":1.7320508075688772}}},"3":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"v":{"1":{"df":1,"docs":{"526":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"520":{"tf":1.0},"525":{"tf":1.0}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}}},"df":0,"docs":{}}},"o":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"418":{"tf":1.0},"420":{"tf":1.0},"422":{"tf":1.4142135623730951},"428":{"tf":1.0},"919":{"tf":1.0}}}},"b":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"78":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"62":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":4,"docs":{"39":{"tf":1.0},"520":{"tf":1.4142135623730951},"62":{"tf":1.0},"78":{"tf":1.4142135623730951}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"62":{"tf":1.0},"78":{"tf":1.0}}}}}}}}},"s":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"78":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"k":{"'":{"df":6,"docs":{"339":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"388":{"tf":1.0},"634":{"tf":1.0}}},"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":13,"docs":{"124":{"tf":1.0},"203":{"tf":1.0},"214":{"tf":1.0},"322":{"tf":1.0},"328":{"tf":1.7320508075688772},"418":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.0},"971":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":119,"docs":{"106":{"tf":1.0},"107":{"tf":1.4142135623730951},"108":{"tf":1.0},"112":{"tf":1.0},"126":{"tf":2.0},"132":{"tf":1.0},"151":{"tf":2.23606797749979},"152":{"tf":1.7320508075688772},"154":{"tf":2.8284271247461903},"155":{"tf":3.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":3.1622776601683795},"207":{"tf":2.23606797749979},"208":{"tf":3.1622776601683795},"221":{"tf":2.0},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"238":{"tf":1.0},"279":{"tf":1.0},"281":{"tf":1.7320508075688772},"282":{"tf":1.0},"284":{"tf":2.449489742783178},"286":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.7320508075688772},"295":{"tf":1.0},"297":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"303":{"tf":1.4142135623730951},"308":{"tf":1.0},"323":{"tf":1.0},"327":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":3.0},"344":{"tf":2.23606797749979},"345":{"tf":2.8284271247461903},"346":{"tf":1.7320508075688772},"347":{"tf":1.7320508075688772},"349":{"tf":2.449489742783178},"350":{"tf":1.4142135623730951},"352":{"tf":1.0},"369":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.4142135623730951},"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.23606797749979},"403":{"tf":1.0},"404":{"tf":2.23606797749979},"405":{"tf":1.0},"406":{"tf":1.4142135623730951},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"44":{"tf":2.23606797749979},"444":{"tf":1.0},"45":{"tf":2.6457513110645907},"450":{"tf":1.7320508075688772},"46":{"tf":3.4641016151377544},"47":{"tf":3.4641016151377544},"49":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":2.6457513110645907},"500":{"tf":5.291502622129181},"512":{"tf":1.7320508075688772},"52":{"tf":1.0},"532":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":1.7320508075688772},"569":{"tf":1.4142135623730951},"57":{"tf":1.4142135623730951},"571":{"tf":1.0},"60":{"tf":2.23606797749979},"615":{"tf":1.0},"627":{"tf":1.4142135623730951},"629":{"tf":1.4142135623730951},"63":{"tf":1.0},"630":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"636":{"tf":1.4142135623730951},"640":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.7320508075688772},"712":{"tf":1.7320508075688772},"714":{"tf":1.0},"715":{"tf":1.0},"72":{"tf":2.0},"721":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.4142135623730951},"73":{"tf":1.0},"740":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"83":{"tf":1.0},"85":{"tf":1.0},"874":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":2.449489742783178}},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"292":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":4,"docs":{"204":{"tf":1.0},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"83":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"/":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"50":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}}},"p":{"a":{"c":{"df":6,"docs":{"214":{"tf":1.4142135623730951},"368":{"tf":1.4142135623730951},"374":{"tf":1.0},"414":{"tf":1.0},"71":{"tf":1.0},"743":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{">":{":":{":":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"284":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"’":{"df":1,"docs":{"46":{"tf":1.0}}}}},"df":0,"docs":{}}},"o":{"b":{"df":5,"docs":{"208":{"tf":3.0},"741":{"tf":1.0},"796":{"tf":1.4142135623730951},"799":{"tf":1.4142135623730951},"878":{"tf":1.0}}},"d":{"a":{"df":1,"docs":{"871":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":5,"docs":{"253":{"tf":1.4142135623730951},"376":{"tf":1.4142135623730951},"497":{"tf":1.0},"500":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"231":{"tf":1.4142135623730951},"234":{"tf":2.6457513110645907},"235":{"tf":1.0},"240":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":1,"docs":{"267":{"tf":1.0}}}},"o":{"df":0,"docs":{},"k":{"df":2,"docs":{"0":{"tf":1.0},"133":{"tf":1.0}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"l":{"df":5,"docs":{"24":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"698":{"tf":1.0},"761":{"tf":1.7320508075688772},"97":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":20,"docs":{"247":{"tf":2.23606797749979},"248":{"tf":1.0},"249":{"tf":2.8284271247461903},"250":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":2.449489742783178},"256":{"tf":1.0},"257":{"tf":1.7320508075688772},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0},"496":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":1,"docs":{"913":{"tf":1.0}},"h":{"df":54,"docs":{"1004":{"tf":1.0},"149":{"tf":1.0},"166":{"tf":1.4142135623730951},"172":{"tf":1.0},"186":{"tf":1.0},"199":{"tf":1.0},"201":{"tf":1.0},"218":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"329":{"tf":1.0},"340":{"tf":1.0},"37":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"384":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.7320508075688772},"40":{"tf":1.0},"402":{"tf":1.0},"440":{"tf":1.0},"442":{"tf":1.0},"47":{"tf":2.23606797749979},"499":{"tf":1.0},"5":{"tf":1.4142135623730951},"515":{"tf":1.0},"516":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"551":{"tf":1.0},"559":{"tf":1.0},"576":{"tf":1.0},"600":{"tf":1.0},"603":{"tf":1.7320508075688772},"619":{"tf":2.0},"62":{"tf":1.0},"633":{"tf":1.0},"635":{"tf":1.0},"705":{"tf":1.0},"759":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"872":{"tf":1.0},"885":{"tf":1.7320508075688772},"886":{"tf":1.0},"95":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"486":{"tf":1.0}}}}}}}},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"138":{"tf":1.0},"848":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"619":{"tf":1.0},"912":{"tf":1.0}}}}},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"288":{"tf":1.0},"374":{"tf":1.0},"732":{"tf":1.0},"843":{"tf":1.0}}}}},"df":15,"docs":{"15":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"347":{"tf":1.4142135623730951},"349":{"tf":1.0},"47":{"tf":1.0},"5":{"tf":1.0},"51":{"tf":1.4142135623730951},"564":{"tf":1.0},"670":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"831":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951}},"e":{"d":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"t":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":2,"docs":{"880":{"tf":2.0},"881":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"370":{"tf":1.0},"848":{"tf":1.0}}}}}},"x":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{":":{":":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{":":{":":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"1015":{"tf":1.0}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":4,"docs":{"346":{"tf":1.0},"439":{"tf":1.4142135623730951},"761":{"tf":1.0},"933":{"tf":1.0}}}},"d":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":1,"docs":{"843":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"705":{"tf":1.0}}}},"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"450":{"tf":1.0}}}}}},"df":28,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"173":{"tf":1.0},"178":{"tf":1.0},"280":{"tf":1.0},"282":{"tf":1.4142135623730951},"34":{"tf":1.0},"374":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"512":{"tf":1.0},"545":{"tf":1.0},"586":{"tf":1.0},"593":{"tf":1.0},"609":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0},"648":{"tf":1.0},"723":{"tf":1.0},"813":{"tf":1.0},"823":{"tf":1.0},"837":{"tf":1.0},"854":{"tf":1.0},"953":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"311":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":4,"docs":{"108":{"tf":1.4142135623730951},"112":{"tf":2.0},"121":{"tf":1.4142135623730951},"832":{"tf":1.4142135623730951}}}},"d":{"df":0,"docs":{},"g":{"df":7,"docs":{"114":{"tf":1.0},"18":{"tf":1.0},"567":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"699":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"375":{"tf":1.0}}}},"n":{"df":0,"docs":{},"g":{"df":7,"docs":{"272":{"tf":1.0},"453":{"tf":1.0},"522":{"tf":1.0},"526":{"tf":1.0},"60":{"tf":1.0},"606":{"tf":1.0},"932":{"tf":1.0}}}}},"o":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"429":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"264":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"586":{"tf":1.0}},"n":{"df":2,"docs":{"845":{"tf":1.0},"852":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"216":{"tf":1.0},"219":{"tf":1.0}}}},"df":25,"docs":{"743":{"tf":1.0},"745":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.4142135623730951},"914":{"tf":1.4142135623730951},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"918":{"tf":1.0},"919":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":2.23606797749979},"943":{"tf":1.4142135623730951},"945":{"tf":1.0},"961":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":3,"docs":{"437":{"tf":1.0},"518":{"tf":1.0},"63":{"tf":1.0}}}}}},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"95":{"tf":1.0}}}}}}},"y":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"106":{"tf":1.0},"17":{"tf":1.0},"294":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"5":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"5":{"tf":1.0}}}}}}}}},"u":{"d":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"155":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"344":{"tf":1.0}}},"df":4,"docs":{"345":{"tf":1.4142135623730951},"732":{"tf":2.449489742783178},"735":{"tf":5.5677643628300215},"739":{"tf":1.0}}}}}},"g":{"df":11,"docs":{"108":{"tf":1.0},"152":{"tf":1.0},"161":{"tf":1.0},"19":{"tf":1.0},"500":{"tf":1.0},"53":{"tf":1.0},"573":{"tf":1.4142135623730951},"832":{"tf":1.0},"962":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.4142135623730951}}},"i":{"df":0,"docs":{},"l":{"d":{"df":23,"docs":{"147":{"tf":1.0},"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"160":{"tf":1.0},"196":{"tf":1.4142135623730951},"214":{"tf":1.0},"234":{"tf":1.4142135623730951},"293":{"tf":1.0},"296":{"tf":1.0},"414":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"501":{"tf":1.4142135623730951},"513":{"tf":1.0},"525":{"tf":2.23606797749979},"528":{"tf":1.4142135623730951},"567":{"tf":1.0},"600":{"tf":1.0},"694":{"tf":1.0},"773":{"tf":1.4142135623730951},"780":{"tf":1.0},"848":{"tf":1.7320508075688772},"850":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"r":{"c":{"/":{"b":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"#":{"df":0,"docs":{},"l":{"1":{"5":{"3":{"df":1,"docs":{"793":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"#":{"df":0,"docs":{},"l":{"1":{"2":{"2":{"df":1,"docs":{"793":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":9,"docs":{"154":{"tf":1.0},"286":{"tf":1.0},"402":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"804":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"154":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":12,"docs":{"1004":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"49":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.0},"701":{"tf":1.0},"783":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.0},"853":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":7,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":2.0},"748":{"tf":1.7320508075688772},"749":{"tf":1.0},"750":{"tf":1.0},"752":{"tf":2.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":6,"docs":{"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{")":{"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"750":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"750":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":6,"docs":{"207":{"tf":3.1622776601683795},"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{}}},"df":31,"docs":{"203":{"tf":3.0},"204":{"tf":3.4641016151377544},"205":{"tf":2.0},"206":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":2.23606797749979},"58":{"tf":1.0},"72":{"tf":1.0},"741":{"tf":2.23606797749979},"742":{"tf":1.4142135623730951},"743":{"tf":1.4142135623730951},"744":{"tf":1.0},"745":{"tf":1.4142135623730951},"746":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"753":{"tf":1.0},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.4142135623730951},"909":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":7,"docs":{"166":{"tf":1.0},"280":{"tf":1.0},"315":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"539":{"tf":1.0},"593":{"tf":1.4142135623730951}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"571":{"tf":1.0}}}},"d":{"df":0,"docs":{},"l":{"df":1,"docs":{"336":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":5,"docs":{"282":{"tf":1.0},"826":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"853":{"tf":1.0}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"296":{"tf":1.0}}}}}}},"g":{"df":2,"docs":{"244":{"tf":1.0},"709":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":9,"docs":{"263":{"tf":2.23606797749979},"264":{"tf":1.7320508075688772},"265":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":3.0},"576":{"tf":1.0},"602":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"i":{"df":4,"docs":{"700":{"tf":1.0},"876":{"tf":1.0},"894":{"tf":1.0},"912":{"tf":1.0}}}},"y":{"df":7,"docs":{"199":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"694":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"267":{"tf":1.0},"776":{"tf":1.4142135623730951}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":9,"docs":{"602":{"tf":1.7320508075688772},"605":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.7320508075688772},"650":{"tf":1.4142135623730951},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"x":{"!":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"v":{"4":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"540":{"tf":1.0},"860":{"tf":1.0}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"829":{"tf":1.0}}},"df":0,"docs":{}}},"df":48,"docs":{"163":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":3.1622776601683795},"171":{"tf":1.4142135623730951},"208":{"tf":2.23606797749979},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":2.0},"388":{"tf":1.0},"435":{"tf":1.4142135623730951},"485":{"tf":1.7320508075688772},"5":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"526":{"tf":2.0},"537":{"tf":1.0},"539":{"tf":2.0},"553":{"tf":1.7320508075688772},"586":{"tf":1.0},"589":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":3.0},"648":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":4.47213595499958},"75":{"tf":1.0},"761":{"tf":2.449489742783178},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"891":{"tf":2.23606797749979},"892":{"tf":1.0},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.4142135623730951},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.7320508075688772},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951},"996":{"tf":1.4142135623730951}},"s":{"(":{"\"":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"s":{"df":1,"docs":{"349":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"349":{"tf":1.0},"350":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":3,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":1.0},"349":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{".":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"347":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"/":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"892":{"tf":1.4142135623730951},"895":{"tf":2.449489742783178},"896":{"tf":1.4142135623730951},"898":{"tf":1.7320508075688772},"900":{"tf":1.0},"902":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"z":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"231":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"c":{"[":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}}}}}},"a":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"255":{"tf":1.0},"257":{"tf":1.0}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"885":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":16,"docs":{"372":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.4142135623730951},"415":{"tf":1.7320508075688772},"417":{"tf":1.0},"46":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"776":{"tf":1.0},"814":{"tf":1.0},"885":{"tf":1.7320508075688772},"95":{"tf":1.0}},"t":{"df":1,"docs":{"415":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"(":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"885":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"25":{"tf":1.0}}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"24":{"tf":1.0},"25":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"879":{"tf":3.4641016151377544},"885":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":2,"docs":{"24":{"tf":1.0},"25":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"814":{"tf":1.0}}}},"df":0,"docs":{}},"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"281":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":74,"docs":{"108":{"tf":1.0},"112":{"tf":2.23606797749979},"170":{"tf":2.0},"171":{"tf":1.4142135623730951},"18":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"22":{"tf":1.4142135623730951},"220":{"tf":1.0},"222":{"tf":1.0},"24":{"tf":2.449489742783178},"25":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.0},"26":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0},"296":{"tf":1.7320508075688772},"300":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"407":{"tf":1.0},"438":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"482":{"tf":1.0},"5":{"tf":1.4142135623730951},"50":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":1.4142135623730951},"51":{"tf":1.0},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.7320508075688772},"61":{"tf":1.0},"614":{"tf":1.7320508075688772},"615":{"tf":1.4142135623730951},"617":{"tf":1.7320508075688772},"619":{"tf":2.0},"633":{"tf":1.0},"64":{"tf":1.0},"699":{"tf":1.4142135623730951},"732":{"tf":1.7320508075688772},"735":{"tf":2.449489742783178},"739":{"tf":1.4142135623730951},"759":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"814":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"818":{"tf":1.0},"83":{"tf":2.0},"832":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"860":{"tf":1.7320508075688772},"870":{"tf":1.0},"879":{"tf":4.795831523312719},"880":{"tf":2.0},"881":{"tf":1.7320508075688772},"885":{"tf":1.4142135623730951},"890":{"tf":1.4142135623730951},"898":{"tf":1.0},"932":{"tf":1.0},"980":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"'":{"df":2,"docs":{"205":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951}}},"<":{"'":{"_":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":9,"docs":{"194":{"tf":1.0},"205":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"602":{"tf":1.4142135623730951},"615":{"tf":1.0},"813":{"tf":1.0},"879":{"tf":3.4641016151377544},"944":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":2,"docs":{"879":{"tf":2.449489742783178},"885":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"m":{"df":0,"docs":{},"e":{"df":1,"docs":{"205":{"tf":1.0}}}},"n":{"'":{"df":0,"docs":{},"t":{"df":8,"docs":{"3":{"tf":1.4142135623730951},"347":{"tf":1.0},"358":{"tf":1.0},"439":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"660":{"tf":1.0},"735":{"tf":1.0}}}},"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"128":{"tf":1.0},"376":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":8,"docs":{"554":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.4142135623730951},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":2.8284271247461903},"885":{"tf":1.0},"912":{"tf":1.0}}}}},"d":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"633":{"tf":1.0},"635":{"tf":1.0}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.4142135623730951}},"v":{"2":{"<":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"634":{"tf":1.0}}}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":4,"docs":{"441":{"tf":1.4142135623730951},"450":{"tf":1.0},"635":{"tf":1.0},"646":{"tf":1.0}}}}}}},"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"715":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"df":46,"docs":{"234":{"tf":2.6457513110645907},"237":{"tf":1.0},"239":{"tf":1.0},"240":{"tf":1.4142135623730951},"322":{"tf":1.4142135623730951},"336":{"tf":1.7320508075688772},"337":{"tf":1.7320508075688772},"338":{"tf":1.0},"346":{"tf":1.4142135623730951},"370":{"tf":1.0},"439":{"tf":1.7320508075688772},"441":{"tf":1.0},"450":{"tf":3.7416573867739413},"60":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.4142135623730951},"629":{"tf":2.0},"63":{"tf":1.7320508075688772},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.4142135623730951},"633":{"tf":1.7320508075688772},"634":{"tf":2.449489742783178},"635":{"tf":1.7320508075688772},"636":{"tf":2.0},"637":{"tf":1.4142135623730951},"638":{"tf":1.0},"639":{"tf":1.0},"64":{"tf":1.4142135623730951},"640":{"tf":1.4142135623730951},"641":{"tf":1.0},"642":{"tf":2.0},"643":{"tf":1.4142135623730951},"644":{"tf":2.0},"645":{"tf":1.0},"646":{"tf":1.4142135623730951},"647":{"tf":1.0},"648":{"tf":1.4142135623730951},"65":{"tf":1.0},"67":{"tf":1.4142135623730951},"715":{"tf":2.23606797749979},"716":{"tf":1.0},"721":{"tf":2.6457513110645907},"722":{"tf":1.0},"77":{"tf":1.0},"933":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"l":{"df":15,"docs":{"122":{"tf":2.23606797749979},"123":{"tf":1.4142135623730951},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":2.23606797749979},"127":{"tf":1.0},"128":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"133":{"tf":1.4142135623730951},"134":{"tf":1.0},"135":{"tf":1.0},"198":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"p":{"a":{"b":{"df":0,"docs":{},"l":{"df":30,"docs":{"169":{"tf":1.0},"199":{"tf":1.0},"340":{"tf":1.0},"38":{"tf":1.0},"495":{"tf":2.449489742783178},"496":{"tf":2.0},"497":{"tf":1.4142135623730951},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":3.3166247903554},"501":{"tf":2.23606797749979},"502":{"tf":2.6457513110645907},"503":{"tf":1.7320508075688772},"504":{"tf":1.0},"505":{"tf":2.0},"506":{"tf":1.0},"507":{"tf":2.0},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":2.23606797749979},"537":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"705":{"tf":1.0},"943":{"tf":1.0},"959":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0}}}},"c":{"df":8,"docs":{"113":{"tf":1.0},"270":{"tf":1.0},"376":{"tf":1.0},"469":{"tf":1.0},"576":{"tf":2.0},"60":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":4,"docs":{"203":{"tf":1.0},"537":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":4,"docs":{"196":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"58":{"tf":1.0}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":5,"docs":{"196":{"tf":1.0},"200":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0}}}}}},"r":{"d":{"df":3,"docs":{"849":{"tf":1.0},"852":{"tf":1.0},"894":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":9,"docs":{"141":{"tf":1.0},"239":{"tf":1.0},"249":{"tf":1.0},"593":{"tf":1.0},"602":{"tf":1.0},"642":{"tf":1.0},"653":{"tf":1.0},"763":{"tf":1.0},"945":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"114":{"tf":1.0},"121":{"tf":1.0},"358":{"tf":1.0},"429":{"tf":1.4142135623730951}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"818":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":6,"docs":{"108":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"47":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":78,"docs":{"1006":{"tf":1.0},"112":{"tf":1.4142135623730951},"126":{"tf":1.0},"151":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.0},"237":{"tf":1.0},"246":{"tf":1.4142135623730951},"249":{"tf":1.0},"254":{"tf":1.4142135623730951},"267":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":2.0},"303":{"tf":1.0},"356":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.0},"376":{"tf":1.0},"387":{"tf":1.0},"418":{"tf":1.0},"420":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.4142135623730951},"485":{"tf":1.0},"486":{"tf":1.0},"503":{"tf":1.0},"522":{"tf":1.4142135623730951},"525":{"tf":1.0},"527":{"tf":1.0},"537":{"tf":1.0},"573":{"tf":1.7320508075688772},"577":{"tf":1.0},"6":{"tf":1.4142135623730951},"600":{"tf":1.0},"615":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"62":{"tf":1.0},"629":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"696":{"tf":2.0},"701":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"749":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"8":{"tf":1.0},"809":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"832":{"tf":1.4142135623730951},"833":{"tf":1.0},"835":{"tf":1.4142135623730951},"864":{"tf":1.0},"871":{"tf":1.4142135623730951},"876":{"tf":1.4142135623730951},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":2.0},"895":{"tf":1.0},"934":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.4142135623730951},"971":{"tf":1.0},"973":{"tf":1.0},"983":{"tf":1.0}}},"t":{"df":1,"docs":{"124":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":3,"docs":{"598":{"tf":1.0},"613":{"tf":1.0},"692":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"881":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"615":{"tf":1.0},"709":{"tf":1.0},"714":{"tf":1.4142135623730951},"759":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"s":{"df":11,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"293":{"tf":1.0},"418":{"tf":1.0},"573":{"tf":1.7320508075688772},"615":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"852":{"tf":1.0},"912":{"tf":2.0},"917":{"tf":1.0}}}}},"d":{"df":1,"docs":{"126":{"tf":2.6457513110645907}},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.4142135623730951}}}}},"df":10,"docs":{"112":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"735":{"tf":1.0},"738":{"tf":1.0},"831":{"tf":1.4142135623730951},"835":{"tf":1.0},"837":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"203":{"tf":1.0},"440":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":1,"docs":{"55":{"tf":1.0}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"285":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"231":{"tf":2.0},"232":{"tf":1.0},"234":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"234":{"tf":1.0}}}}}}}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"303":{"tf":1.4142135623730951},"327":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"46":{"tf":1.0},"565":{"tf":1.0},"843":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"565":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"c":{"df":3,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"214":{"tf":1.0}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"364":{"tf":1.0}}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":19,"docs":{"152":{"tf":1.0},"204":{"tf":1.0},"249":{"tf":1.4142135623730951},"255":{"tf":1.0},"324":{"tf":1.0},"342":{"tf":1.0},"495":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"505":{"tf":1.0},"553":{"tf":1.0},"567":{"tf":1.0},"666":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"890":{"tf":1.4142135623730951},"913":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"849":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"773":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"x":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}},"f":{"df":1,"docs":{"126":{"tf":2.449489742783178}},"g":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"717":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":6,"docs":{"3":{"tf":1.0},"368":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"422":{"tf":1.0},"84":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":1,"docs":{"855":{"tf":1.0}}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"153":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"856":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":281,"docs":{"107":{"tf":1.0},"12":{"tf":1.7320508075688772},"140":{"tf":1.0},"147":{"tf":1.0},"151":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"169":{"tf":1.0},"18":{"tf":2.23606797749979},"19":{"tf":2.0},"191":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":2.0},"2":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":4.47213595499958},"204":{"tf":2.6457513110645907},"205":{"tf":2.6457513110645907},"207":{"tf":2.0},"208":{"tf":1.4142135623730951},"212":{"tf":1.7320508075688772},"214":{"tf":1.0},"216":{"tf":1.7320508075688772},"217":{"tf":1.7320508075688772},"218":{"tf":2.23606797749979},"219":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"220":{"tf":1.4142135623730951},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"226":{"tf":1.0},"229":{"tf":1.0},"230":{"tf":1.7320508075688772},"231":{"tf":3.0},"232":{"tf":1.0},"234":{"tf":1.0},"235":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"24":{"tf":1.7320508075688772},"246":{"tf":1.4142135623730951},"247":{"tf":2.23606797749979},"248":{"tf":1.0},"249":{"tf":3.3166247903554},"250":{"tf":1.0},"251":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"254":{"tf":1.7320508075688772},"255":{"tf":1.4142135623730951},"256":{"tf":1.0},"257":{"tf":1.0},"258":{"tf":1.0},"259":{"tf":1.0},"26":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":2.8284271247461903},"30":{"tf":1.4142135623730951},"312":{"tf":1.4142135623730951},"313":{"tf":1.7320508075688772},"314":{"tf":1.4142135623730951},"315":{"tf":1.7320508075688772},"316":{"tf":1.0},"322":{"tf":1.7320508075688772},"329":{"tf":1.4142135623730951},"33":{"tf":1.0},"337":{"tf":1.0},"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":2.449489742783178},"347":{"tf":2.8284271247461903},"348":{"tf":1.4142135623730951},"349":{"tf":2.0},"35":{"tf":1.0},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"362":{"tf":2.6457513110645907},"366":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":2.0},"369":{"tf":1.0},"37":{"tf":1.4142135623730951},"370":{"tf":1.4142135623730951},"371":{"tf":2.0},"372":{"tf":2.0},"373":{"tf":2.8284271247461903},"374":{"tf":2.449489742783178},"375":{"tf":3.1622776601683795},"376":{"tf":2.0},"377":{"tf":1.0},"378":{"tf":1.0},"380":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.4142135623730951},"384":{"tf":1.0},"385":{"tf":1.7320508075688772},"388":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"393":{"tf":1.0},"4":{"tf":1.0},"432":{"tf":1.4142135623730951},"433":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":2.0},"453":{"tf":2.0},"455":{"tf":1.0},"459":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":2.449489742783178},"48":{"tf":1.0},"49":{"tf":1.7320508075688772},"495":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"5":{"tf":1.0},"50":{"tf":1.0},"500":{"tf":3.0},"503":{"tf":2.0},"512":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":3.0},"521":{"tf":2.449489742783178},"528":{"tf":1.7320508075688772},"530":{"tf":1.0},"531":{"tf":1.0},"534":{"tf":1.4142135623730951},"553":{"tf":1.0},"56":{"tf":1.7320508075688772},"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":2.0},"573":{"tf":1.7320508075688772},"58":{"tf":1.0},"586":{"tf":2.0},"588":{"tf":1.0},"59":{"tf":1.4142135623730951},"598":{"tf":1.0},"599":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"60":{"tf":2.23606797749979},"600":{"tf":2.23606797749979},"602":{"tf":3.7416573867739413},"603":{"tf":1.4142135623730951},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"614":{"tf":1.0},"615":{"tf":1.0},"627":{"tf":1.4142135623730951},"629":{"tf":1.7320508075688772},"63":{"tf":1.7320508075688772},"632":{"tf":1.0},"633":{"tf":2.23606797749979},"634":{"tf":1.4142135623730951},"637":{"tf":1.7320508075688772},"64":{"tf":1.4142135623730951},"643":{"tf":1.4142135623730951},"65":{"tf":1.4142135623730951},"66":{"tf":1.0},"68":{"tf":1.0},"693":{"tf":1.0},"694":{"tf":2.0},"695":{"tf":1.0},"696":{"tf":3.605551275463989},"697":{"tf":3.0},"698":{"tf":1.4142135623730951},"699":{"tf":1.4142135623730951},"700":{"tf":2.23606797749979},"701":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":2.0},"710":{"tf":1.4142135623730951},"712":{"tf":1.0},"714":{"tf":1.7320508075688772},"715":{"tf":2.0},"716":{"tf":1.4142135623730951},"717":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":2.0},"74":{"tf":1.0},"743":{"tf":1.0},"75":{"tf":2.23606797749979},"752":{"tf":1.0},"759":{"tf":1.7320508075688772},"763":{"tf":1.0},"77":{"tf":1.7320508075688772},"776":{"tf":1.0},"78":{"tf":1.7320508075688772},"784":{"tf":1.0},"79":{"tf":1.0},"797":{"tf":1.0},"8":{"tf":1.0},"80":{"tf":2.0},"803":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":2.449489742783178},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"82":{"tf":1.0},"826":{"tf":1.0},"83":{"tf":2.23606797749979},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"84":{"tf":3.1622776601683795},"849":{"tf":1.0},"85":{"tf":3.1622776601683795},"852":{"tf":1.0},"855":{"tf":1.7320508075688772},"871":{"tf":1.0},"874":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":2.6457513110645907},"897":{"tf":1.0},"898":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":2.449489742783178},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.7320508075688772},"918":{"tf":1.0},"919":{"tf":1.4142135623730951},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0},"938":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":2.23606797749979},"958":{"tf":1.4142135623730951},"959":{"tf":2.23606797749979},"960":{"tf":2.0},"961":{"tf":1.7320508075688772},"962":{"tf":1.7320508075688772},"963":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"970":{"tf":1.4142135623730951},"971":{"tf":1.0},"972":{"tf":1.4142135623730951},"973":{"tf":1.7320508075688772}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":16,"docs":{"138":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"323":{"tf":1.0},"388":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"742":{"tf":1.0},"777":{"tf":1.0},"849":{"tf":1.0},"855":{"tf":1.0},"913":{"tf":1.0},"990":{"tf":1.0}}}}}}},"n":{"c":{"df":4,"docs":{"124":{"tf":1.0},"204":{"tf":1.0},"347":{"tf":1.0},"833":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":213,"docs":{"0":{"tf":1.0},"100":{"tf":1.0},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"125":{"tf":1.7320508075688772},"126":{"tf":1.0},"127":{"tf":1.7320508075688772},"130":{"tf":1.0},"131":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.4142135623730951},"139":{"tf":1.0},"142":{"tf":1.7320508075688772},"146":{"tf":1.0},"148":{"tf":2.0},"149":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":1.4142135623730951},"165":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":1.4142135623730951},"172":{"tf":1.7320508075688772},"175":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.0},"183":{"tf":1.0},"186":{"tf":1.7320508075688772},"187":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.7320508075688772},"193":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"206":{"tf":1.0},"208":{"tf":1.0},"209":{"tf":1.0},"213":{"tf":1.4142135623730951},"218":{"tf":1.4142135623730951},"252":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"280":{"tf":1.0},"282":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"292":{"tf":1.0},"294":{"tf":1.0},"295":{"tf":1.0},"30":{"tf":1.0},"301":{"tf":1.7320508075688772},"302":{"tf":1.0},"314":{"tf":1.0},"317":{"tf":1.4142135623730951},"318":{"tf":1.0},"322":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.4142135623730951},"371":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"382":{"tf":1.0},"390":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.4142135623730951},"398":{"tf":1.0},"399":{"tf":1.0},"41":{"tf":1.0},"411":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.7320508075688772},"423":{"tf":1.0},"424":{"tf":1.0},"427":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"446":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.0},"455":{"tf":1.4142135623730951},"456":{"tf":1.0},"457":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.4142135623730951},"469":{"tf":1.0},"473":{"tf":1.0},"483":{"tf":1.0},"491":{"tf":1.0},"494":{"tf":1.0},"500":{"tf":1.4142135623730951},"501":{"tf":1.0},"505":{"tf":1.0},"511":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":1.7320508075688772},"539":{"tf":1.7320508075688772},"540":{"tf":1.4142135623730951},"542":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.0},"551":{"tf":1.4142135623730951},"559":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"585":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.4142135623730951},"591":{"tf":1.0},"593":{"tf":1.0},"600":{"tf":1.4142135623730951},"606":{"tf":1.0},"619":{"tf":1.0},"621":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"636":{"tf":1.0},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"648":{"tf":1.0},"65":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"67":{"tf":1.0},"673":{"tf":1.0},"680":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"698":{"tf":1.4142135623730951},"700":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"717":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.7320508075688772},"739":{"tf":1.4142135623730951},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.7320508075688772},"752":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"78":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.4142135623730951},"788":{"tf":1.0},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"8":{"tf":1.0},"800":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.7320508075688772},"813":{"tf":1.4142135623730951},"817":{"tf":1.0},"831":{"tf":2.0},"835":{"tf":1.0},"837":{"tf":1.7320508075688772},"844":{"tf":1.0},"846":{"tf":1.4142135623730951},"848":{"tf":1.7320508075688772},"849":{"tf":1.7320508075688772},"854":{"tf":1.0},"860":{"tf":1.0},"867":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":2.0},"875":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":2.23606797749979},"929":{"tf":1.7320508075688772},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"944":{"tf":1.0},"980":{"tf":1.0},"994":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"234":{"tf":1.0}}}},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"607":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"1006":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":4,"docs":{"219":{"tf":1.0},"221":{"tf":1.0},"843":{"tf":1.4142135623730951},"87":{"tf":1.0}}}}}},"o":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"d":{"a":{"df":0,"docs":{},"o":{"df":2,"docs":{"182":{"tf":1.0},"795":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"895":{"tf":1.0},"897":{"tf":1.4142135623730951},"898":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"522":{"tf":1.0}},"g":{"df":6,"docs":{"416":{"tf":1.0},"614":{"tf":1.0},"653":{"tf":1.4142135623730951},"75":{"tf":1.7320508075688772},"912":{"tf":1.4142135623730951},"979":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"208":{"tf":1.7320508075688772},"796":{"tf":1.7320508075688772},"799":{"tf":1.7320508075688772}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"272":{"tf":1.0},"273":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"206":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"58":{"tf":1.0},"75":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"435":{"tf":1.0}}}}},"t":{"df":2,"docs":{"723":{"tf":1.0},"725":{"tf":1.0}}}},"c":{"df":0,"docs":{},"k":{"df":45,"docs":{"154":{"tf":1.0},"156":{"tf":1.0},"177":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":1.0},"286":{"tf":1.0},"3":{"tf":1.0},"342":{"tf":1.0},"347":{"tf":1.4142135623730951},"436":{"tf":1.0},"439":{"tf":1.4142135623730951},"45":{"tf":1.0},"530":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.7320508075688772},"640":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.0},"711":{"tf":1.7320508075688772},"714":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":2.8284271247461903},"721":{"tf":2.0},"722":{"tf":2.449489742783178},"725":{"tf":1.0},"729":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.0},"77":{"tf":1.0},"811":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"817":{"tf":2.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.0},"900":{"tf":1.0},"982":{"tf":1.0}},"e":{"d":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"817":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":9,"docs":{"449":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.4142135623730951},"714":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.7320508075688772},"721":{"tf":2.0},"722":{"tf":2.8284271247461903},"723":{"tf":1.4142135623730951}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"586":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"249":{"tf":1.0},"567":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"n":{"df":3,"docs":{"106":{"tf":1.0},"17":{"tf":1.0},"294":{"tf":1.0}},"g":{"df":1,"docs":{"988":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"735":{"tf":2.449489742783178}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"761":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}}}}}},"df":2,"docs":{"697":{"tf":1.0},"761":{"tf":2.449489742783178}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"761":{"tf":2.449489742783178}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"761":{"tf":1.4142135623730951}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"761":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"i":{"c":{"df":11,"docs":{"126":{"tf":2.23606797749979},"170":{"tf":1.0},"221":{"tf":1.0},"356":{"tf":1.0},"428":{"tf":1.0},"473":{"tf":1.0},"500":{"tf":1.0},"569":{"tf":1.0},"640":{"tf":1.0},"700":{"tf":1.0},"723":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"s":{"df":11,"docs":{"38":{"tf":1.0},"471":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"700":{"tf":1.0},"718":{"tf":1.0},"77":{"tf":1.0},"831":{"tf":1.4142135623730951},"912":{"tf":1.0}}}},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"935":{"tf":1.0}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"e":{"df":1,"docs":{"570":{"tf":1.0}},"n":{"df":9,"docs":{"126":{"tf":1.0},"252":{"tf":1.0},"346":{"tf":1.0},"373":{"tf":1.0},"497":{"tf":1.4142135623730951},"631":{"tf":1.0},"633":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"'":{"df":1,"docs":{"439":{"tf":2.0}}},"(":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.0}}}}}}}}}}}}}},"df":0,"docs":{}},"df":40,"docs":{"155":{"tf":1.0},"430":{"tf":2.6457513110645907},"431":{"tf":1.7320508075688772},"432":{"tf":2.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":2.0},"436":{"tf":2.449489742783178},"437":{"tf":3.0},"438":{"tf":2.449489742783178},"439":{"tf":4.58257569495584},"440":{"tf":2.23606797749979},"441":{"tf":1.0},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"445":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.4142135623730951},"450":{"tf":1.0},"514":{"tf":1.7320508075688772},"517":{"tf":2.23606797749979},"519":{"tf":1.4142135623730951},"522":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"576":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":2.0},"716":{"tf":1.0},"717":{"tf":1.7320508075688772},"720":{"tf":1.7320508075688772},"722":{"tf":3.0},"723":{"tf":2.449489742783178},"73":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"439":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.0}}}}}}}}}}}}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":4,"docs":{"432":{"tf":1.4142135623730951},"438":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"440":{"tf":1.0}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"439":{"tf":1.7320508075688772}}}}}}}}}}}}},"i":{"df":2,"docs":{"314":{"tf":1.0},"639":{"tf":1.0}},"r":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"v":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{".":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"350":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":4,"docs":{"349":{"tf":1.7320508075688772},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"352":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":16,"docs":{"240":{"tf":1.0},"322":{"tf":1.7320508075688772},"323":{"tf":1.0},"339":{"tf":1.4142135623730951},"343":{"tf":1.4142135623730951},"348":{"tf":1.4142135623730951},"349":{"tf":3.0},"350":{"tf":1.4142135623730951},"633":{"tf":2.0},"637":{"tf":1.7320508075688772},"666":{"tf":1.0},"668":{"tf":1.0},"717":{"tf":1.0},"815":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.0}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":2,"docs":{"633":{"tf":2.0},"640":{"tf":1.0}}}}}}}}}}}}}}},"m":{"df":0,"docs":{},"p":{"df":2,"docs":{"829":{"tf":1.0},"833":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"324":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"199":{"tf":1.0},"330":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"5":{"tf":1.0}}}},"w":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"409":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"y":{"df":1,"docs":{"841":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"df":4,"docs":{"705":{"tf":1.0},"768":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":2,"docs":{"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951}}}}}}}}},"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}},"r":{"df":25,"docs":{"180":{"tf":1.0},"210":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"30":{"tf":1.0},"356":{"tf":1.0},"48":{"tf":1.0},"600":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"698":{"tf":1.4142135623730951},"701":{"tf":1.4142135623730951},"705":{"tf":1.4142135623730951},"706":{"tf":1.0},"723":{"tf":1.0},"737":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"797":{"tf":1.0},"817":{"tf":1.0},"833":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"952":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"1008":{"tf":1.0},"16":{"tf":1.0},"267":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.7320508075688772},"693":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":48,"docs":{"19":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"262":{"tf":1.0},"358":{"tf":1.0},"381":{"tf":1.0},"403":{"tf":1.0},"440":{"tf":1.0},"498":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":2.0},"758":{"tf":1.4142135623730951},"759":{"tf":2.6457513110645907},"760":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.4142135623730951},"764":{"tf":1.0},"765":{"tf":1.4142135623730951},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.0},"81":{"tf":1.4142135623730951},"827":{"tf":2.23606797749979},"828":{"tf":1.4142135623730951},"829":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"830":{"tf":1.4142135623730951},"831":{"tf":2.0},"832":{"tf":1.0},"833":{"tf":1.4142135623730951},"834":{"tf":1.0},"835":{"tf":1.4142135623730951},"836":{"tf":1.7320508075688772},"837":{"tf":2.0},"838":{"tf":1.0},"839":{"tf":1.0},"84":{"tf":1.7320508075688772},"840":{"tf":1.0},"88":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"831":{"tf":1.4142135623730951}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":2,"docs":{"24":{"tf":1.0},"439":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":8,"docs":{"175":{"tf":1.0},"469":{"tf":1.0},"501":{"tf":1.0},"576":{"tf":1.0},"661":{"tf":1.0},"744":{"tf":1.0},"751":{"tf":1.4142135623730951},"773":{"tf":1.4142135623730951}},"r":{"df":2,"docs":{"207":{"tf":1.4142135623730951},"912":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"255":{"tf":1.7320508075688772},"505":{"tf":1.7320508075688772}}}}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"571":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"288":{"tf":1.0}}}}}}}},"o":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":2,"docs":{"24":{"tf":1.7320508075688772},"333":{"tf":1.7320508075688772}}},"df":74,"docs":{"111":{"tf":1.0},"121":{"tf":1.4142135623730951},"150":{"tf":2.23606797749979},"151":{"tf":3.605551275463989},"152":{"tf":1.4142135623730951},"153":{"tf":1.0},"154":{"tf":3.605551275463989},"155":{"tf":3.0},"156":{"tf":1.4142135623730951},"157":{"tf":1.0},"158":{"tf":1.7320508075688772},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":2.0},"186":{"tf":1.0},"19":{"tf":1.0},"190":{"tf":1.0},"22":{"tf":1.0},"274":{"tf":1.0},"316":{"tf":1.0},"322":{"tf":1.4142135623730951},"333":{"tf":2.0},"347":{"tf":1.0},"35":{"tf":1.4142135623730951},"362":{"tf":2.23606797749979},"430":{"tf":1.0},"435":{"tf":2.449489742783178},"436":{"tf":1.0},"437":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"483":{"tf":1.7320508075688772},"537":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":1.4142135623730951},"593":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":2.6457513110645907},"632":{"tf":1.0},"634":{"tf":1.0},"64":{"tf":1.7320508075688772},"65":{"tf":1.4142135623730951},"67":{"tf":2.0},"71":{"tf":1.4142135623730951},"711":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"737":{"tf":1.0},"74":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"75":{"tf":1.4142135623730951},"750":{"tf":1.4142135623730951},"762":{"tf":1.0},"77":{"tf":1.7320508075688772},"794":{"tf":1.0},"810":{"tf":1.7320508075688772},"811":{"tf":2.0},"813":{"tf":1.4142135623730951},"814":{"tf":2.449489742783178},"815":{"tf":2.449489742783178},"816":{"tf":1.0},"817":{"tf":2.23606797749979},"818":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"951":{"tf":1.0},"994":{"tf":1.0}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"444":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"371":{"tf":1.4142135623730951},"537":{"tf":1.0},"810":{"tf":1.0},"872":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"418":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"39":{"tf":1.0},"54":{"tf":1.0}}},"s":{"df":1,"docs":{"24":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"d":{"df":2,"docs":{"516":{"tf":1.0},"517":{"tf":1.0}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":41,"docs":{"203":{"tf":1.4142135623730951},"206":{"tf":1.4142135623730951},"229":{"tf":2.23606797749979},"230":{"tf":1.7320508075688772},"231":{"tf":4.0},"232":{"tf":2.23606797749979},"233":{"tf":1.0},"234":{"tf":3.1622776601683795},"235":{"tf":1.4142135623730951},"236":{"tf":1.4142135623730951},"237":{"tf":1.4142135623730951},"238":{"tf":1.0},"239":{"tf":1.0},"240":{"tf":1.4142135623730951},"241":{"tf":1.0},"242":{"tf":1.0},"243":{"tf":2.0},"244":{"tf":1.4142135623730951},"245":{"tf":1.0},"246":{"tf":1.4142135623730951},"249":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.4142135623730951},"62":{"tf":2.449489742783178},"629":{"tf":1.4142135623730951},"632":{"tf":2.449489742783178},"633":{"tf":1.0},"634":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.7320508075688772},"644":{"tf":1.4142135623730951},"65":{"tf":1.4142135623730951},"66":{"tf":1.0},"67":{"tf":1.4142135623730951},"69":{"tf":1.0},"73":{"tf":1.4142135623730951},"78":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"634":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"634":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":61,"docs":{"106":{"tf":2.6457513110645907},"107":{"tf":2.0},"108":{"tf":1.4142135623730951},"109":{"tf":1.0},"110":{"tf":1.0},"111":{"tf":3.1622776601683795},"112":{"tf":2.449489742783178},"113":{"tf":2.6457513110645907},"114":{"tf":1.0},"115":{"tf":1.0},"116":{"tf":1.0},"117":{"tf":1.0},"118":{"tf":1.0},"119":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":2.23606797749979},"125":{"tf":1.0},"2":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"267":{"tf":1.4142135623730951},"268":{"tf":2.449489742783178},"269":{"tf":2.6457513110645907},"270":{"tf":2.6457513110645907},"271":{"tf":1.0},"272":{"tf":2.23606797749979},"273":{"tf":3.0},"274":{"tf":1.4142135623730951},"275":{"tf":1.0},"276":{"tf":2.6457513110645907},"277":{"tf":1.0},"278":{"tf":1.0},"3":{"tf":1.7320508075688772},"303":{"tf":1.4142135623730951},"338":{"tf":1.0},"346":{"tf":1.4142135623730951},"373":{"tf":1.7320508075688772},"375":{"tf":1.0},"376":{"tf":1.4142135623730951},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.4142135623730951},"418":{"tf":1.4142135623730951},"420":{"tf":1.0},"425":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"5":{"tf":1.0},"523":{"tf":1.7320508075688772},"6":{"tf":2.8284271247461903},"7":{"tf":2.0},"709":{"tf":1.0},"715":{"tf":1.7320508075688772},"8":{"tf":1.0},"801":{"tf":1.0},"876":{"tf":1.0},"9":{"tf":1.0},"913":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"272":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{}},"u":{"d":{"df":2,"docs":{"232":{"tf":1.0},"567":{"tf":1.0}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":2,"docs":{"435":{"tf":1.0},"633":{"tf":1.0}}}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":14,"docs":{"1004":{"tf":1.0},"111":{"tf":1.0},"296":{"tf":1.0},"429":{"tf":1.0},"51":{"tf":1.0},"525":{"tf":1.4142135623730951},"565":{"tf":1.0},"571":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"605":{"tf":1.0},"700":{"tf":1.0},"95":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":25,"docs":{"171":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"340":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.0},"645":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.4142135623730951},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0}}},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"602":{"tf":1.0},"694":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"440":{"tf":1.0},"776":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"470":{"tf":1.0}}}}},"t":{"df":4,"docs":{"0":{"tf":1.0},"264":{"tf":1.0},"437":{"tf":1.0},"447":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"1004":{"tf":1.0}}}},"t":{"df":28,"docs":{"203":{"tf":1.0},"272":{"tf":1.4142135623730951},"351":{"tf":1.0},"46":{"tf":1.4142135623730951},"467":{"tf":1.0},"49":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.7320508075688772},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":2.0},"634":{"tf":1.0},"635":{"tf":1.4142135623730951},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.4142135623730951},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"633":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"635":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"710":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"22":{"tf":1.0},"368":{"tf":1.4142135623730951},"51":{"tf":1.0},"696":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"874":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"55":{"tf":1.0}}}},"t":{"df":1,"docs":{"133":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"n":{"df":27,"docs":{"1":{"tf":1.0},"12":{"tf":1.0},"184":{"tf":1.0},"194":{"tf":1.0},"199":{"tf":1.0},"2":{"tf":1.0},"208":{"tf":1.0},"216":{"tf":1.4142135623730951},"218":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"3":{"tf":1.7320508075688772},"412":{"tf":1.0},"414":{"tf":1.0},"416":{"tf":1.0},"5":{"tf":2.0},"521":{"tf":1.0},"71":{"tf":1.0},"843":{"tf":1.7320508075688772},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"87":{"tf":1.0},"912":{"tf":1.4142135623730951},"943":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"'":{"df":2,"docs":{"267":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"1":{"df":3,"docs":{"482":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.4142135623730951}}},"df":0,"docs":{}},":":{":":{"<":{"df":0,"docs":{},"u":{"3":{"2":{">":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"(":{"*":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{")":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"786":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"<":{"df":0,"docs":{},"u":{"3":{"2":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":6,"docs":{"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"485":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":2.0},"523":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":1,"docs":{"992":{"tf":1.4142135623730951}}}}}}},"u":{"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"876":{"tf":1.0}}}},"r":{"df":13,"docs":{"147":{"tf":1.0},"204":{"tf":1.0},"314":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"779":{"tf":1.0},"813":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"759":{"tf":1.0}}}}}}},"t":{"df":193,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.4142135623730951},"1002":{"tf":1.4142135623730951},"1009":{"tf":1.4142135623730951},"101":{"tf":1.4142135623730951},"1012":{"tf":1.7320508075688772},"104":{"tf":1.4142135623730951},"106":{"tf":1.4142135623730951},"116":{"tf":1.4142135623730951},"119":{"tf":1.7320508075688772},"122":{"tf":1.4142135623730951},"126":{"tf":1.0},"129":{"tf":1.4142135623730951},"13":{"tf":1.7320508075688772},"132":{"tf":1.7320508075688772},"136":{"tf":1.4142135623730951},"143":{"tf":1.4142135623730951},"146":{"tf":1.7320508075688772},"150":{"tf":1.4142135623730951},"157":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"164":{"tf":1.4142135623730951},"17":{"tf":1.4142135623730951},"171":{"tf":1.0},"175":{"tf":1.4142135623730951},"178":{"tf":1.4142135623730951},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.4142135623730951},"191":{"tf":1.4142135623730951},"195":{"tf":1.0},"210":{"tf":1.4142135623730951},"215":{"tf":1.0},"224":{"tf":1.4142135623730951},"229":{"tf":1.4142135623730951},"238":{"tf":1.4142135623730951},"241":{"tf":1.7320508075688772},"247":{"tf":1.4142135623730951},"251":{"tf":1.7320508075688772},"256":{"tf":1.4142135623730951},"259":{"tf":1.4142135623730951},"26":{"tf":1.0},"268":{"tf":1.0},"276":{"tf":1.7320508075688772},"279":{"tf":1.4142135623730951},"287":{"tf":1.4142135623730951},"290":{"tf":1.4142135623730951},"294":{"tf":1.0},"307":{"tf":1.7320508075688772},"31":{"tf":1.4142135623730951},"311":{"tf":1.0},"318":{"tf":1.4142135623730951},"322":{"tf":1.4142135623730951},"34":{"tf":1.7320508075688772},"355":{"tf":1.4142135623730951},"358":{"tf":1.4142135623730951},"366":{"tf":1.4142135623730951},"379":{"tf":1.4142135623730951},"38":{"tf":1.0},"382":{"tf":1.4142135623730951},"386":{"tf":1.4142135623730951},"393":{"tf":1.7320508075688772},"396":{"tf":1.7320508075688772},"400":{"tf":1.4142135623730951},"405":{"tf":1.4142135623730951},"408":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"421":{"tf":1.4142135623730951},"424":{"tf":1.7320508075688772},"430":{"tf":1.4142135623730951},"443":{"tf":1.4142135623730951},"446":{"tf":1.4142135623730951},"451":{"tf":1.4142135623730951},"458":{"tf":1.4142135623730951},"461":{"tf":1.4142135623730951},"465":{"tf":1.4142135623730951},"475":{"tf":1.4142135623730951},"478":{"tf":1.4142135623730951},"481":{"tf":1.4142135623730951},"482":{"tf":1.0},"486":{"tf":1.0},"488":{"tf":1.4142135623730951},"491":{"tf":1.7320508075688772},"495":{"tf":1.4142135623730951},"506":{"tf":1.4142135623730951},"509":{"tf":1.4142135623730951},"512":{"tf":1.0},"513":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"52":{"tf":1.4142135623730951},"529":{"tf":1.4142135623730951},"531":{"tf":1.4142135623730951},"535":{"tf":1.4142135623730951},"542":{"tf":1.4142135623730951},"545":{"tf":1.4142135623730951},"549":{"tf":1.4142135623730951},"553":{"tf":1.0},"556":{"tf":1.4142135623730951},"559":{"tf":1.7320508075688772},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"579":{"tf":1.4142135623730951},"582":{"tf":1.7320508075688772},"584":{"tf":1.4142135623730951},"586":{"tf":1.0},"591":{"tf":1.7320508075688772},"593":{"tf":1.0},"594":{"tf":1.7320508075688772},"598":{"tf":1.4142135623730951},"606":{"tf":1.4142135623730951},"609":{"tf":2.0},"613":{"tf":1.4142135623730951},"620":{"tf":1.4142135623730951},"623":{"tf":1.7320508075688772},"627":{"tf":1.4142135623730951},"628":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.4142135623730951},"639":{"tf":1.0},"642":{"tf":1.7320508075688772},"649":{"tf":1.4142135623730951},"657":{"tf":1.4142135623730951},"660":{"tf":1.4142135623730951},"664":{"tf":1.4142135623730951},"671":{"tf":1.4142135623730951},"674":{"tf":1.4142135623730951},"678":{"tf":1.4142135623730951},"685":{"tf":1.4142135623730951},"688":{"tf":1.4142135623730951},"692":{"tf":1.4142135623730951},"70":{"tf":1.4142135623730951},"701":{"tf":1.0},"702":{"tf":1.4142135623730951},"705":{"tf":2.23606797749979},"709":{"tf":1.0},"725":{"tf":1.4142135623730951},"73":{"tf":1.4142135623730951},"732":{"tf":1.0},"757":{"tf":1.4142135623730951},"764":{"tf":1.4142135623730951},"767":{"tf":1.4142135623730951},"782":{"tf":1.4142135623730951},"789":{"tf":1.4142135623730951},"79":{"tf":1.4142135623730951},"792":{"tf":1.7320508075688772},"795":{"tf":1.4142135623730951},"802":{"tf":1.4142135623730951},"804":{"tf":1.4142135623730951},"808":{"tf":1.4142135623730951},"811":{"tf":1.0},"820":{"tf":1.4142135623730951},"823":{"tf":1.7320508075688772},"827":{"tf":1.4142135623730951},"831":{"tf":1.0},"834":{"tf":1.4142135623730951},"837":{"tf":1.4142135623730951},"841":{"tf":1.4142135623730951},"851":{"tf":1.4142135623730951},"854":{"tf":1.7320508075688772},"857":{"tf":1.4142135623730951},"86":{"tf":1.4142135623730951},"865":{"tf":1.4142135623730951},"868":{"tf":1.7320508075688772},"871":{"tf":1.4142135623730951},"884":{"tf":1.4142135623730951},"887":{"tf":1.7320508075688772},"89":{"tf":1.4142135623730951},"891":{"tf":1.4142135623730951},"901":{"tf":1.4142135623730951},"904":{"tf":1.4142135623730951},"908":{"tf":1.4142135623730951},"918":{"tf":1.4142135623730951},"921":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.4142135623730951},"936":{"tf":1.7320508075688772},"940":{"tf":1.4142135623730951},"950":{"tf":1.4142135623730951},"953":{"tf":1.7320508075688772},"957":{"tf":1.4142135623730951},"959":{"tf":1.0},"961":{"tf":1.0},"967":{"tf":1.4142135623730951},"970":{"tf":2.0},"971":{"tf":1.0},"974":{"tf":1.4142135623730951},"981":{"tf":1.4142135623730951},"984":{"tf":1.4142135623730951},"988":{"tf":1.4142135623730951},"995":{"tf":1.4142135623730951},"998":{"tf":1.7320508075688772}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"545":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":3,"docs":{"121":{"tf":1.0},"212":{"tf":1.0},"849":{"tf":1.0}}}},"t":{"df":3,"docs":{"231":{"tf":1.4142135623730951},"240":{"tf":1.0},"801":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"38":{"tf":1.0},"40":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"912":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}}}},"i":{"df":0,"docs":{},"l":{"df":7,"docs":{"35":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"530":{"tf":1.0},"735":{"tf":2.0},"831":{"tf":1.7320508075688772}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"205":{"tf":1.0}}}}},"df":3,"docs":{"3":{"tf":1.0},"368":{"tf":1.0},"573":{"tf":1.0}}}}}},"t":{"df":16,"docs":{"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"402":{"tf":1.0},"437":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"515":{"tf":1.0},"525":{"tf":1.0},"615":{"tf":1.0},"817":{"tf":1.0},"833":{"tf":1.0},"835":{"tf":1.0},"848":{"tf":1.0},"889":{"tf":1.0}}},"x":{"df":28,"docs":{"140":{"tf":1.0},"141":{"tf":1.0},"145":{"tf":1.0},"375":{"tf":1.4142135623730951},"418":{"tf":1.0},"429":{"tf":1.4142135623730951},"438":{"tf":1.0},"576":{"tf":1.4142135623730951},"600":{"tf":1.0},"631":{"tf":1.0},"68":{"tf":1.0},"706":{"tf":1.0},"773":{"tf":1.4142135623730951},"777":{"tf":1.0},"799":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"874":{"tf":1.4142135623730951},"920":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"938":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"962":{"tf":1.4142135623730951},"972":{"tf":1.0}}}},"i":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"337":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":2,"docs":{"852":{"tf":1.4142135623730951},"894":{"tf":1.0}}}}},"c":{"df":11,"docs":{"375":{"tf":1.7320508075688772},"441":{"tf":1.0},"486":{"tf":1.0},"503":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"975":{"tf":1.0}}},"df":2,"docs":{"251":{"tf":1.0},"712":{"tf":1.0}}}},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"208":{"tf":1.0},"21":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"373":{"tf":1.4142135623730951},"576":{"tf":1.0},"933":{"tf":1.7320508075688772},"94":{"tf":1.0},"961":{"tf":1.0}}},"s":{"df":5,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"522":{"tf":1.7320508075688772},"602":{"tf":1.4142135623730951},"696":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"221":{"tf":1.0},"522":{"tf":2.23606797749979},"602":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"709":{"tf":1.0},"717":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"797":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":8,"docs":{"142":{"tf":1.0},"30":{"tf":1.0},"324":{"tf":1.0},"499":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0},"969":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"s":{"df":14,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"988":{"tf":2.23606797749979},"989":{"tf":1.4142135623730951},"990":{"tf":1.0},"991":{"tf":1.0},"992":{"tf":2.0},"993":{"tf":1.0},"994":{"tf":1.4142135623730951},"995":{"tf":1.0},"996":{"tf":1.7320508075688772},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"126":{"tf":1.0},"502":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":9,"docs":{"124":{"tf":1.0},"516":{"tf":1.4142135623730951},"564":{"tf":1.0},"697":{"tf":1.4142135623730951},"84":{"tf":1.4142135623730951},"85":{"tf":1.7320508075688772},"850":{"tf":1.0},"879":{"tf":1.4142135623730951},"934":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"725":{"tf":1.0}}}}}}},"df":32,"docs":{"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"26":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"33":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"35":{"tf":1.0},"368":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"633":{"tf":1.4142135623730951},"710":{"tf":1.0},"715":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.7320508075688772},"724":{"tf":1.0},"725":{"tf":1.0},"94":{"tf":1.0},"951":{"tf":1.0},"968":{"tf":1.0}}}}}},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"\"":{":":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{":":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"&":{"[":{"4":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":5,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":2.0},"350":{"tf":1.0},"485":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":4,"docs":{"205":{"tf":1.0},"333":{"tf":1.0},"435":{"tf":1.7320508075688772},"735":{"tf":1.0}}}}},"v":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":2,"docs":{"712":{"tf":1.0},"721":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"t":{"df":23,"docs":{"402":{"tf":1.0},"427":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.0},"653":{"tf":1.0},"827":{"tf":2.23606797749979},"828":{"tf":1.0},"829":{"tf":1.7320508075688772},"83":{"tf":1.0},"830":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"833":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"840":{"tf":1.0},"843":{"tf":1.0},"847":{"tf":1.0},"931":{"tf":1.0}},"u":{"df":2,"docs":{"33":{"tf":1.0},"84":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"n":{"df":35,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"170":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"251":{"tf":1.0},"267":{"tf":1.0},"304":{"tf":1.0},"365":{"tf":1.0},"410":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.4142135623730951},"420":{"tf":1.7320508075688772},"427":{"tf":1.4142135623730951},"48":{"tf":1.0},"500":{"tf":1.0},"53":{"tf":1.0},"58":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"656":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"763":{"tf":1.0},"8":{"tf":1.0},"819":{"tf":1.0},"850":{"tf":1.0},"917":{"tf":1.0},"936":{"tf":1.0},"949":{"tf":1.0},"966":{"tf":1.0}}},"t":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"340":{"tf":1.0}}}},"l":{"df":0,"docs":{},"u":{"d":{"df":1,"docs":{"721":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":8,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"207":{"tf":1.4142135623730951},"33":{"tf":1.0},"39":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"875":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":1,"docs":{"142":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":16,"docs":{"295":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.7320508075688772},"302":{"tf":1.0},"341":{"tf":1.4142135623730951},"376":{"tf":1.0},"412":{"tf":1.0},"427":{"tf":1.0},"467":{"tf":1.0},"500":{"tf":1.0},"568":{"tf":1.0},"62":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"754":{"tf":1.0},"95":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"526":{"tf":1.0}}}}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"142":{"tf":1.0},"211":{"tf":1.4142135623730951},"406":{"tf":1.0},"442":{"tf":1.0},"776":{"tf":1.0},"819":{"tf":1.0},"961":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"376":{"tf":1.0},"743":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"348":{"tf":1.0}}}}}}},"df":0,"docs":{},"g":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},">":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"24":{"tf":2.23606797749979},"814":{"tf":1.4142135623730951},"817":{"tf":1.0},"83":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":2.0}},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":48,"docs":{"108":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"140":{"tf":1.4142135623730951},"141":{"tf":1.4142135623730951},"145":{"tf":1.0},"146":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"208":{"tf":1.0},"222":{"tf":1.0},"26":{"tf":1.0},"270":{"tf":1.4142135623730951},"342":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.4142135623730951},"362":{"tf":1.0},"373":{"tf":1.0},"381":{"tf":1.0},"415":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"63":{"tf":1.4142135623730951},"664":{"tf":1.0},"697":{"tf":1.4142135623730951},"698":{"tf":1.0},"700":{"tf":1.4142135623730951},"705":{"tf":1.0},"741":{"tf":1.0},"752":{"tf":1.4142135623730951},"811":{"tf":1.0},"818":{"tf":1.4142135623730951},"819":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":2.449489742783178},"848":{"tf":1.0},"850":{"tf":1.4142135623730951},"913":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"186":{"tf":1.7320508075688772},"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":32,"docs":{"122":{"tf":2.23606797749979},"123":{"tf":1.0},"124":{"tf":1.7320508075688772},"125":{"tf":1.4142135623730951},"126":{"tf":3.0},"127":{"tf":1.4142135623730951},"128":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"133":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0},"182":{"tf":2.0},"183":{"tf":1.4142135623730951},"184":{"tf":2.449489742783178},"185":{"tf":1.0},"186":{"tf":1.4142135623730951},"187":{"tf":1.7320508075688772},"188":{"tf":1.7320508075688772},"189":{"tf":1.0},"190":{"tf":1.4142135623730951},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.4142135623730951},"194":{"tf":1.0},"300":{"tf":1.0},"302":{"tf":1.0},"45":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"35":{"tf":1.0},"735":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":3,"docs":{"182":{"tf":1.0},"253":{"tf":1.0},"54":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"s":{"df":3,"docs":{"249":{"tf":1.0},"564":{"tf":1.0},"976":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"748":{"tf":1.0}}}}}}}},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"6":{"tf":1.0},"755":{"tf":1.0}}}},"df":0,"docs":{}}}},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":13,"docs":{"198":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"262":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.4142135623730951},"52":{"tf":1.0},"551":{"tf":1.0},"567":{"tf":1.0},"784":{"tf":1.0},"990":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":78,"docs":{"144":{"tf":1.0},"155":{"tf":1.0},"17":{"tf":2.23606797749979},"18":{"tf":1.4142135623730951},"19":{"tf":1.4142135623730951},"20":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"27":{"tf":1.0},"28":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.7320508075688772},"30":{"tf":1.0},"31":{"tf":1.0},"32":{"tf":1.0},"322":{"tf":2.23606797749979},"323":{"tf":1.4142135623730951},"324":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"327":{"tf":1.4142135623730951},"328":{"tf":1.0},"329":{"tf":1.0},"33":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"35":{"tf":1.0},"350":{"tf":1.0},"351":{"tf":1.0},"352":{"tf":1.0},"353":{"tf":1.0},"354":{"tf":1.0},"355":{"tf":1.0},"356":{"tf":1.4142135623730951},"357":{"tf":1.0},"358":{"tf":1.0},"359":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"361":{"tf":1.0},"362":{"tf":1.0},"363":{"tf":1.0},"364":{"tf":1.0},"365":{"tf":1.0},"37":{"tf":1.0},"388":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"5":{"tf":2.23606797749979},"567":{"tf":1.4142135623730951},"6":{"tf":1.0},"602":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"833":{"tf":1.0},"927":{"tf":1.0}}}},"t":{"df":1,"docs":{"303":{"tf":1.0}}}},"q":{"df":0,"docs":{},"u":{"df":9,"docs":{"108":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"429":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"928":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"v":{"df":2,"docs":{"239":{"tf":1.0},"752":{"tf":1.4142135623730951}}}}},"i":{"d":{"df":37,"docs":{"1003":{"tf":1.0},"126":{"tf":1.0},"193":{"tf":1.0},"267":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"325":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"412":{"tf":1.0},"426":{"tf":1.0},"435":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.4142135623730951},"450":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"500":{"tf":1.0},"564":{"tf":1.0},"6":{"tf":1.0},"630":{"tf":1.0},"635":{"tf":1.0},"7":{"tf":1.0},"724":{"tf":1.0},"736":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.4142135623730951},"778":{"tf":1.0},"809":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0},"889":{"tf":1.0},"928":{"tf":1.0},"962":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":18,"docs":{"210":{"tf":1.0},"224":{"tf":1.0},"346":{"tf":1.0},"357":{"tf":1.0},"38":{"tf":1.0},"422":{"tf":1.0},"51":{"tf":1.4142135623730951},"563":{"tf":1.0},"567":{"tf":1.0},"572":{"tf":1.4142135623730951},"619":{"tf":1.4142135623730951},"694":{"tf":1.0},"754":{"tf":1.0},"763":{"tf":1.0},"788":{"tf":1.4142135623730951},"799":{"tf":1.0},"871":{"tf":1.0},"881":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":17,"docs":{"1004":{"tf":1.0},"21":{"tf":1.0},"253":{"tf":1.4142135623730951},"267":{"tf":1.0},"292":{"tf":1.0},"313":{"tf":1.0},"330":{"tf":1.0},"374":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"501":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"835":{"tf":1.0},"992":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"565":{"tf":1.0}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"427":{"tf":1.0},"95":{"tf":1.0}}}}}}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":14,"docs":{"257":{"tf":1.0},"347":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.4142135623730951},"427":{"tf":1.0},"428":{"tf":1.4142135623730951},"507":{"tf":1.0},"516":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"736":{"tf":1.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"880":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"680":{"tf":1.0}}}}}}},"df":5,"docs":{"390":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"455":{"tf":1.0},"846":{"tf":1.4142135623730951}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"346":{"tf":1.0},"376":{"tf":1.0},"627":{"tf":1.0}},"t":{"df":6,"docs":{"337":{"tf":1.0},"347":{"tf":1.0},"377":{"tf":1.0},"402":{"tf":1.0},"514":{"tf":1.0},"748":{"tf":1.0}}}}}},"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":13,"docs":{"18":{"tf":1.0},"22":{"tf":1.0},"273":{"tf":1.0},"341":{"tf":1.4142135623730951},"345":{"tf":1.4142135623730951},"346":{"tf":1.7320508075688772},"349":{"tf":1.7320508075688772},"350":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"735":{"tf":1.0},"778":{"tf":1.0},"83":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"m":{"df":15,"docs":{"172":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"23":{"tf":1.0},"296":{"tf":1.4142135623730951},"314":{"tf":1.0},"402":{"tf":1.0},"435":{"tf":1.0},"444":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"786":{"tf":1.0},"912":{"tf":1.0}},"p":{"df":0,"docs":{},"t":{"df":2,"docs":{"773":{"tf":1.0},"828":{"tf":1.0}}}}}}},"t":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"111":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":40,"docs":{"0":{"tf":1.0},"151":{"tf":1.0},"16":{"tf":1.0},"223":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"351":{"tf":1.0},"367":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"399":{"tf":1.0},"44":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"523":{"tf":1.7320508075688772},"528":{"tf":1.0},"534":{"tf":1.0},"553":{"tf":1.0},"57":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"619":{"tf":1.0},"64":{"tf":1.0},"71":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"786":{"tf":1.0},"842":{"tf":1.0},"844":{"tf":1.0},"847":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":76,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1004":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"219":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"45":{"tf":1.4142135623730951},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.4142135623730951},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}}},"x":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"w":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"603":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":13,"docs":{"203":{"tf":1.0},"316":{"tf":1.0},"334":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.4142135623730951},"431":{"tf":1.0},"457":{"tf":1.0},"500":{"tf":1.0},"567":{"tf":1.0},"603":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"848":{"tf":1.0}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"o":{"df":1,"docs":{"743":{"tf":1.0}}}}},"u":{"df":14,"docs":{"155":{"tf":1.0},"194":{"tf":1.0},"236":{"tf":1.0},"314":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"63":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"760":{"tf":1.4142135623730951},"776":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0},"973":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":26,"docs":{"39":{"tf":1.4142135623730951},"44":{"tf":1.0},"46":{"tf":1.0},"697":{"tf":1.0},"78":{"tf":2.23606797749979},"874":{"tf":1.0},"9":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":2.23606797749979},"958":{"tf":1.4142135623730951},"959":{"tf":2.23606797749979},"960":{"tf":1.0},"961":{"tf":2.8284271247461903},"962":{"tf":2.0},"963":{"tf":1.0},"964":{"tf":1.4142135623730951},"965":{"tf":1.4142135623730951},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.4142135623730951},"969":{"tf":1.4142135623730951},"970":{"tf":1.0},"971":{"tf":2.23606797749979},"972":{"tf":2.0},"973":{"tf":2.23606797749979}}}},"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"773":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"267":{"tf":1.0},"576":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":13,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"329":{"tf":1.0},"340":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"470":{"tf":1.0},"565":{"tf":1.0},"81":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"'":{"df":1,"docs":{"208":{"tf":1.0}}},"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":4,"docs":{"208":{"tf":1.7320508075688772},"322":{"tf":1.0},"329":{"tf":1.4142135623730951},"469":{"tf":1.0}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":31,"docs":{"111":{"tf":1.0},"114":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"255":{"tf":1.0},"313":{"tf":1.0},"427":{"tf":1.0},"505":{"tf":1.0},"526":{"tf":1.0},"602":{"tf":1.0},"694":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.4142135623730951},"744":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":2.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"81":{"tf":2.0},"831":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":2.23606797749979},"878":{"tf":1.0},"932":{"tf":1.4142135623730951},"934":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":3,"docs":{"251":{"tf":1.0},"697":{"tf":1.0},"740":{"tf":1.0}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":5,"docs":{"204":{"tf":1.0},"333":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.0},"683":{"tf":1.0}}},"t":{"df":4,"docs":{"333":{"tf":1.0},"455":{"tf":1.0},"564":{"tf":1.0},"7":{"tf":1.0}}}},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"551":{"tf":1.0}}},"s":{"df":8,"docs":{"184":{"tf":1.0},"30":{"tf":1.0},"349":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"609":{"tf":1.0},"807":{"tf":1.0}}},"t":{"df":6,"docs":{"146":{"tf":1.0},"19":{"tf":1.0},"40":{"tf":1.0},"519":{"tf":1.0},"522":{"tf":1.0},"83":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":17,"docs":{"370":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":2.6457513110645907},"795":{"tf":2.23606797749979},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"798":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"801":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"799":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"733":{"tf":1.0}}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":9,"docs":{"139":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"438":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0},"94":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"201":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"i":{"df":2,"docs":{"735":{"tf":2.0},"739":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"'":{"df":2,"docs":{"203":{"tf":1.0},"208":{"tf":1.4142135623730951}}},":":{":":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"279":{"tf":1.0},"280":{"tf":1.0},"284":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":6,"docs":{"438":{"tf":2.0},"441":{"tf":1.4142135623730951},"450":{"tf":1.7320508075688772},"634":{"tf":1.4142135623730951},"636":{"tf":1.7320508075688772},"637":{"tf":1.0}}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":1,"docs":{"438":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}}},"df":101,"docs":{"16":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.4142135623730951},"200":{"tf":2.0},"203":{"tf":3.3166247903554},"204":{"tf":3.1622776601683795},"205":{"tf":4.123105625617661},"206":{"tf":1.7320508075688772},"207":{"tf":3.0},"208":{"tf":5.656854249492381},"213":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"218":{"tf":1.7320508075688772},"219":{"tf":1.0},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"23":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":1.4142135623730951},"270":{"tf":1.0},"279":{"tf":2.23606797749979},"28":{"tf":1.0},"280":{"tf":1.7320508075688772},"281":{"tf":1.0},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0},"322":{"tf":1.0},"325":{"tf":1.0},"328":{"tf":1.4142135623730951},"335":{"tf":1.0},"361":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"374":{"tf":2.449489742783178},"377":{"tf":1.0},"409":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"438":{"tf":1.4142135623730951},"444":{"tf":1.0},"450":{"tf":2.6457513110645907},"46":{"tf":1.0},"47":{"tf":1.0},"52":{"tf":1.0},"615":{"tf":1.0},"627":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"63":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":3.3166247903554},"634":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0},"694":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.7320508075688772},"72":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"742":{"tf":2.0},"748":{"tf":2.0},"749":{"tf":2.23606797749979},"751":{"tf":2.23606797749979},"752":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":3.0},"777":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":2.0},"910":{"tf":1.0},"911":{"tf":2.449489742783178},"912":{"tf":3.7416573867739413},"913":{"tf":2.6457513110645907},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.4142135623730951},"917":{"tf":2.0},"918":{"tf":1.0},"919":{"tf":2.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"938":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":26,"docs":{"205":{"tf":1.0},"208":{"tf":2.0},"221":{"tf":1.0},"438":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.0},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.7320508075688772},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.4142135623730951},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.0}}}}},"df":0,"docs":{}}},"j":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"441":{"tf":1.0}}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":2,"docs":{"205":{"tf":1.0},"208":{"tf":2.6457513110645907}}}}},"df":0,"docs":{}},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{")":{"^":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"750":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":3,"docs":{"207":{"tf":2.449489742783178},"749":{"tf":1.0},"750":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"t":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":102,"docs":{"195":{"tf":2.6457513110645907},"196":{"tf":1.4142135623730951},"197":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"201":{"tf":1.0},"202":{"tf":1.0},"203":{"tf":6.324555320336759},"204":{"tf":4.69041575982343},"205":{"tf":4.242640687119285},"206":{"tf":3.605551275463989},"207":{"tf":3.3166247903554},"208":{"tf":3.0},"209":{"tf":1.0},"210":{"tf":1.7320508075688772},"211":{"tf":1.0},"212":{"tf":1.7320508075688772},"213":{"tf":2.8284271247461903},"214":{"tf":1.0},"215":{"tf":2.0},"216":{"tf":1.4142135623730951},"217":{"tf":1.7320508075688772},"218":{"tf":2.0},"219":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":2.0},"222":{"tf":1.4142135623730951},"223":{"tf":1.0},"224":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.4142135623730951},"227":{"tf":1.0},"228":{"tf":1.0},"263":{"tf":2.23606797749979},"264":{"tf":1.7320508075688772},"265":{"tf":1.4142135623730951},"266":{"tf":1.0},"267":{"tf":3.605551275463989},"368":{"tf":1.0},"370":{"tf":1.0},"374":{"tf":1.0},"381":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"48":{"tf":1.4142135623730951},"52":{"tf":1.7320508075688772},"58":{"tf":1.4142135623730951},"741":{"tf":2.23606797749979},"742":{"tf":1.4142135623730951},"743":{"tf":1.7320508075688772},"744":{"tf":1.0},"745":{"tf":1.4142135623730951},"746":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"753":{"tf":1.0},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":2.0},"776":{"tf":2.6457513110645907},"777":{"tf":1.7320508075688772},"778":{"tf":1.4142135623730951},"779":{"tf":1.7320508075688772},"811":{"tf":1.0},"909":{"tf":1.7320508075688772},"911":{"tf":2.23606797749979},"912":{"tf":3.0},"913":{"tf":1.7320508075688772},"914":{"tf":1.4142135623730951},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.7320508075688772},"938":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"945":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":2.23606797749979},"958":{"tf":1.4142135623730951},"959":{"tf":2.23606797749979},"960":{"tf":2.23606797749979},"961":{"tf":1.7320508075688772},"962":{"tf":1.7320508075688772},"963":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"970":{"tf":1.4142135623730951},"971":{"tf":1.0},"972":{"tf":1.4142135623730951},"973":{"tf":1.7320508075688772}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"1006":{"tf":1.0},"833":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"876":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":24,"docs":{"142":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"343":{"tf":1.0},"349":{"tf":1.0},"390":{"tf":1.0},"397":{"tf":1.0},"402":{"tf":1.0},"44":{"tf":1.0},"457":{"tf":1.0},"514":{"tf":1.0},"526":{"tf":1.0},"586":{"tf":1.0},"633":{"tf":1.0},"724":{"tf":1.0},"752":{"tf":1.0},"819":{"tf":1.0},"870":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.4142135623730951},"932":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"151":{"tf":1.0},"372":{"tf":1.0},"406":{"tf":1.0},"514":{"tf":1.0},"586":{"tf":1.0},"651":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"l":{"df":2,"docs":{"428":{"tf":1.0},"773":{"tf":1.0}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"413":{"tf":1.0}}},"df":0,"docs":{},"n":{"d":{"df":19,"docs":{"134":{"tf":1.0},"205":{"tf":1.4142135623730951},"231":{"tf":1.0},"24":{"tf":1.0},"252":{"tf":1.0},"257":{"tf":1.4142135623730951},"348":{"tf":1.0},"350":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"455":{"tf":1.0},"507":{"tf":1.4142135623730951},"524":{"tf":1.0},"637":{"tf":1.0},"837":{"tf":1.0},"894":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"198":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":1,"docs":{"532":{"tf":1.0}}}},"t":{"df":46,"docs":{"124":{"tf":1.0},"144":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"236":{"tf":1.0},"267":{"tf":1.4142135623730951},"29":{"tf":1.0},"39":{"tf":1.0},"42":{"tf":1.0},"428":{"tf":1.0},"471":{"tf":1.0},"486":{"tf":1.0},"51":{"tf":1.0},"54":{"tf":1.0},"554":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"577":{"tf":1.7320508075688772},"60":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"711":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"739":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"799":{"tf":1.4142135623730951},"810":{"tf":2.0},"811":{"tf":1.0},"814":{"tf":1.0},"826":{"tf":1.7320508075688772},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"863":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"951":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"577":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"722":{"tf":2.0}},"e":{"df":0,"docs":{},"r":{"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":0,"docs":{}},"df":6,"docs":{"208":{"tf":1.0},"63":{"tf":2.23606797749979},"64":{"tf":1.7320508075688772},"72":{"tf":1.0},"77":{"tf":1.0},"928":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":3,"docs":{"735":{"tf":3.3166247903554},"739":{"tf":1.4142135623730951},"776":{"tf":1.0}},"i":{"df":1,"docs":{"198":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"466":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"l":{"df":4,"docs":{"126":{"tf":1.0},"437":{"tf":1.0},"816":{"tf":1.7320508075688772},"874":{"tf":1.0}}}},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"571":{"tf":1.0},"712":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":16,"docs":{"204":{"tf":1.0},"237":{"tf":1.0},"30":{"tf":1.0},"402":{"tf":1.0},"519":{"tf":1.4142135623730951},"54":{"tf":1.0},"6":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"67":{"tf":1.0},"714":{"tf":1.4142135623730951},"720":{"tf":1.0},"721":{"tf":1.0},"810":{"tf":1.0},"817":{"tf":1.0},"843":{"tf":1.4142135623730951}}}}}},"p":{"df":1,"docs":{"126":{"tf":3.3166247903554}},"u":{"df":4,"docs":{"444":{"tf":1.4142135623730951},"711":{"tf":1.7320508075688772},"763":{"tf":1.0},"996":{"tf":1.0}}}},"q":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"633":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"151":{"tf":1.0},"912":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":2,"docs":{"315":{"tf":1.0},"786":{"tf":1.0}},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":1,"docs":{"315":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":46,"docs":{"113":{"tf":1.0},"121":{"tf":1.4142135623730951},"171":{"tf":1.7320508075688772},"180":{"tf":1.0},"193":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"249":{"tf":1.0},"300":{"tf":1.4142135623730951},"301":{"tf":1.0},"303":{"tf":1.0},"323":{"tf":1.0},"328":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"411":{"tf":1.0},"414":{"tf":1.0},"42":{"tf":1.0},"436":{"tf":1.0},"524":{"tf":1.0},"551":{"tf":1.0},"554":{"tf":1.0},"574":{"tf":1.0},"586":{"tf":1.0},"633":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"804":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"818":{"tf":1.0},"83":{"tf":1.4142135623730951},"849":{"tf":1.0},"85":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"895":{"tf":1.0},"898":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"948":{"tf":1.0},"959":{"tf":1.0},"976":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"!":{"(":{"\"":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"(":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"898":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}}}},"df":22,"docs":{"322":{"tf":1.0},"346":{"tf":1.7320508075688772},"410":{"tf":1.0},"412":{"tf":1.0},"549":{"tf":2.23606797749979},"550":{"tf":1.4142135623730951},"551":{"tf":1.0},"552":{"tf":1.0},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"555":{"tf":1.4142135623730951},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"969":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.4142135623730951}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"848":{"tf":1.0}}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"234":{"tf":1.0}}}},"df":0,"docs":{},"t":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"203":{"tf":2.6457513110645907},"205":{"tf":1.7320508075688772},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":3,"docs":{"231":{"tf":1.0},"528":{"tf":1.0},"913":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"c":{"df":7,"docs":{"124":{"tf":1.0},"155":{"tf":1.0},"281":{"tf":1.0},"324":{"tf":1.0},"354":{"tf":1.0},"418":{"tf":1.0},"440":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":17,"docs":{"12":{"tf":1.0},"17":{"tf":1.0},"18":{"tf":1.4142135623730951},"19":{"tf":1.0},"4":{"tf":1.0},"49":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"608":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"8":{"tf":1.0},"81":{"tf":1.0},"82":{"tf":1.0},"874":{"tf":1.0}}}},"w":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":6,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":2.6457513110645907},"370":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"206":{"tf":1.4142135623730951},"267":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"361":{"tf":1.0},"418":{"tf":1.0},"514":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"40":{"tf":1.0}}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":1,"docs":{"418":{"tf":1.0}}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"h":{"df":6,"docs":{"322":{"tf":1.0},"340":{"tf":1.7320508075688772},"455":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"95":{"tf":1.0}},"i":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"113":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"342":{"tf":1.0},"723":{"tf":1.0}},"u":{"df":3,"docs":{"203":{"tf":1.0},"254":{"tf":1.0},"630":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"429":{"tf":1.7320508075688772}}},"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":1,"docs":{"568":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":117,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.4142135623730951},"140":{"tf":1.0},"148":{"tf":1.0},"171":{"tf":1.4142135623730951},"180":{"tf":1.0},"184":{"tf":1.4142135623730951},"193":{"tf":1.0},"194":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":2.449489742783178},"208":{"tf":2.0},"221":{"tf":1.0},"244":{"tf":1.0},"248":{"tf":1.0},"254":{"tf":1.0},"284":{"tf":1.0},"29":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.7320508075688772},"300":{"tf":1.4142135623730951},"303":{"tf":1.0},"314":{"tf":1.0},"344":{"tf":1.4142135623730951},"373":{"tf":1.0},"39":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"404":{"tf":1.4142135623730951},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"418":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"450":{"tf":1.0},"457":{"tf":1.0},"471":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.0},"50":{"tf":1.0},"500":{"tf":2.449489742783178},"512":{"tf":1.0},"515":{"tf":1.7320508075688772},"52":{"tf":1.0},"534":{"tf":1.4142135623730951},"537":{"tf":2.0},"539":{"tf":1.4142135623730951},"540":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.4142135623730951},"577":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":2.0},"606":{"tf":1.0},"614":{"tf":1.0},"619":{"tf":1.0},"637":{"tf":1.0},"65":{"tf":1.0},"653":{"tf":1.0},"694":{"tf":1.0},"701":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"732":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"770":{"tf":1.4142135623730951},"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951},"786":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.7320508075688772},"814":{"tf":1.0},"822":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0},"843":{"tf":1.0},"85":{"tf":1.0},"858":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.7320508075688772},"878":{"tf":1.0},"881":{"tf":1.4142135623730951},"895":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"931":{"tf":1.0},"937":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}}}},"s":{"df":1,"docs":{"777":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"749":{"tf":1.0}}}}}},"df":38,"docs":{"100":{"tf":1.0},"1002":{"tf":2.23606797749979},"1003":{"tf":1.0},"1004":{"tf":1.0},"1005":{"tf":1.0},"1006":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.0},"105":{"tf":1.0},"204":{"tf":1.0},"417":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"95":{"tf":3.0},"96":{"tf":1.0},"97":{"tf":1.4142135623730951},"98":{"tf":1.0},"99":{"tf":1.0}},"e":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"(":{"7":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"577":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"663":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":11,"docs":{"169":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.7320508075688772},"21":{"tf":1.0},"26":{"tf":1.0},"30":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.0},"519":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"t":{"df":2,"docs":{"356":{"tf":1.0},"440":{"tf":1.0}}}},"y":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"936":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"38":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"49":{"tf":1.0},"55":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"d":{"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"df":4,"docs":{"39":{"tf":1.0},"42":{"tf":1.0},"47":{"tf":1.7320508075688772},"55":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":2.449489742783178}}},"y":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"571":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"m":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"108":{"tf":1.0},"267":{"tf":1.0},"697":{"tf":1.0},"852":{"tf":1.0}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"752":{"tf":1.0}}}}}},"n":{"c":{"df":1,"docs":{"293":{"tf":1.0}}},"df":4,"docs":{"467":{"tf":1.0},"469":{"tf":2.449489742783178},"470":{"tf":1.7320508075688772},"471":{"tf":1.0}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":3,"docs":{"1":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}}}},"o":{"df":3,"docs":{"188":{"tf":1.0},"784":{"tf":1.0},"876":{"tf":1.4142135623730951}}},"p":{"df":0,"docs":{},"p":{"df":13,"docs":{"18":{"tf":1.0},"33":{"tf":1.0},"4":{"tf":1.0},"414":{"tf":1.4142135623730951},"601":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"82":{"tf":1.0},"895":{"tf":1.4142135623730951},"977":{"tf":1.0}}}},"s":{"df":0,"docs":{},"h":{"b":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"804":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"a":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"512":{"tf":1.0}}}},"df":0,"docs":{}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":73,"docs":{"140":{"tf":1.0},"151":{"tf":1.4142135623730951},"152":{"tf":2.0},"155":{"tf":1.7320508075688772},"171":{"tf":1.0},"19":{"tf":1.7320508075688772},"191":{"tf":1.4142135623730951},"208":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.7320508075688772},"253":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":1.7320508075688772},"340":{"tf":1.0},"343":{"tf":1.4142135623730951},"346":{"tf":1.7320508075688772},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"375":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":1.0},"422":{"tf":1.0},"431":{"tf":1.0},"435":{"tf":2.0},"436":{"tf":2.0},"439":{"tf":1.7320508075688772},"44":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":2.0},"46":{"tf":1.4142135623730951},"47":{"tf":2.0},"49":{"tf":1.0},"497":{"tf":2.0},"5":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.4142135623730951},"520":{"tf":1.4142135623730951},"521":{"tf":2.6457513110645907},"522":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.7320508075688772},"526":{"tf":2.23606797749979},"532":{"tf":1.0},"537":{"tf":1.0},"553":{"tf":1.0},"571":{"tf":1.4142135623730951},"586":{"tf":1.0},"6":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"73":{"tf":1.0},"735":{"tf":4.795831523312719},"739":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.7320508075688772},"815":{"tf":1.4142135623730951},"818":{"tf":1.0},"826":{"tf":1.0},"84":{"tf":1.4142135623730951},"847":{"tf":1.0},"85":{"tf":1.0},"88":{"tf":1.0},"907":{"tf":1.0},"961":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.7320508075688772}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"204":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":69,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"376":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"418":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"515":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.4142135623730951},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"912":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}}},"v":{"df":0,"docs":{},"e":{"df":2,"docs":{"208":{"tf":1.7320508075688772},"878":{"tf":1.0}}},"i":{"d":{"df":1,"docs":{"322":{"tf":1.0}}},"df":0,"docs":{}}},"y":{"df":30,"docs":{"169":{"tf":1.0},"175":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":2.0},"186":{"tf":1.4142135623730951},"198":{"tf":1.0},"207":{"tf":1.7320508075688772},"39":{"tf":1.0},"470":{"tf":1.4142135623730951},"50":{"tf":1.0},"55":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":2.0},"565":{"tf":1.0},"567":{"tf":2.8284271247461903},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":2.23606797749979},"573":{"tf":3.0},"575":{"tf":1.7320508075688772},"576":{"tf":1.0},"577":{"tf":1.0},"776":{"tf":1.7320508075688772},"829":{"tf":1.0},"846":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.0}}}},"b":{"df":1,"docs":{"163":{"tf":1.0}}},"df":4,"docs":{"112":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"717":{"tf":1.4142135623730951},"749":{"tf":1.0}},"e":{"a":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"126":{"tf":1.4142135623730951},"208":{"tf":1.0},"281":{"tf":1.0},"735":{"tf":2.0}}}}}},"df":0,"docs":{},"l":{"df":3,"docs":{"377":{"tf":1.0},"651":{"tf":1.0},"852":{"tf":1.0}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"365":{"tf":1.0}}}}}}}},"b":{"a":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":2,"docs":{"121":{"tf":1.0},"29":{"tf":1.7320508075688772}},"g":{"df":1,"docs":{"29":{"tf":1.0}}}}}},"c":{"a":{"df":0,"docs":{},"y":{"df":3,"docs":{"1002":{"tf":1.0},"1003":{"tf":1.0},"749":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":17,"docs":{"111":{"tf":1.0},"138":{"tf":1.0},"147":{"tf":1.0},"303":{"tf":1.4142135623730951},"313":{"tf":1.0},"314":{"tf":1.0},"427":{"tf":1.0},"843":{"tf":1.0},"848":{"tf":1.4142135623730951},"849":{"tf":1.7320508075688772},"876":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"971":{"tf":1.0},"973":{"tf":1.4142135623730951}}}}}},"i":{"d":{"df":18,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"265":{"tf":1.0},"270":{"tf":1.0},"303":{"tf":1.4142135623730951},"402":{"tf":1.0},"438":{"tf":1.0},"512":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.4142135623730951},"553":{"tf":1.0},"568":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"m":{"df":2,"docs":{"520":{"tf":1.7320508075688772},"534":{"tf":1.0}}},"s":{"df":27,"docs":{"1006":{"tf":1.0},"123":{"tf":1.0},"126":{"tf":4.0},"137":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"187":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"846":{"tf":1.4142135623730951},"857":{"tf":2.23606797749979},"858":{"tf":1.4142135623730951},"859":{"tf":1.4142135623730951},"860":{"tf":1.4142135623730951},"861":{"tf":2.0},"862":{"tf":2.0},"863":{"tf":1.7320508075688772},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.4142135623730951},"870":{"tf":1.0},"876":{"tf":1.4142135623730951},"878":{"tf":1.0},"913":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"126":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"a":{"df":0,"docs":{},"r":{"df":5,"docs":{"455":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.7320508075688772},"523":{"tf":1.0},"534":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"d":{"df":31,"docs":{"151":{"tf":2.0},"152":{"tf":1.0},"154":{"tf":1.0},"177":{"tf":1.0},"201":{"tf":1.0},"333":{"tf":1.0},"350":{"tf":1.4142135623730951},"435":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.0},"514":{"tf":1.4142135623730951},"516":{"tf":1.4142135623730951},"517":{"tf":1.0},"519":{"tf":1.7320508075688772},"521":{"tf":1.0},"522":{"tf":2.449489742783178},"523":{"tf":2.0},"586":{"tf":1.0},"588":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":2.449489742783178},"633":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.4142135623730951},"831":{"tf":1.0},"898":{"tf":1.0}},"e":{"<":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"d":{"a":{"df":0,"docs":{},"t":{"a":{">":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{">":{"(":{"df":0,"docs":{},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"3":{"2":{">":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{">":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"205":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"994":{"tf":1.0},"996":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":2,"docs":{"927":{"tf":1.0},"934":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":13,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":2.0},"213":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"444":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0},"732":{"tf":1.0},"749":{"tf":1.0},"846":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"63":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"i":{"c":{"df":10,"docs":{"203":{"tf":1.4142135623730951},"208":{"tf":1.0},"316":{"tf":1.0},"358":{"tf":1.0},"374":{"tf":1.4142135623730951},"467":{"tf":1.0},"482":{"tf":1.0},"651":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}},"df":0,"docs":{}}},"df":5,"docs":{"58":{"tf":1.0},"600":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"782":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"514":{"tf":1.0},"67":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"928":{"tf":1.0},"931":{"tf":1.0}}}}}},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":11,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"175":{"tf":1.0},"255":{"tf":1.0},"296":{"tf":1.0},"39":{"tf":1.0},"455":{"tf":1.0},"500":{"tf":1.0},"761":{"tf":2.23606797749979},"829":{"tf":1.0},"831":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":2,"docs":{"188":{"tf":1.0},"855":{"tf":1.0}}}},"r":{"df":2,"docs":{"563":{"tf":1.0},"573":{"tf":2.6457513110645907}}}},"i":{"df":1,"docs":{"973":{"tf":1.0}},"n":{"df":38,"docs":{"111":{"tf":1.0},"126":{"tf":1.4142135623730951},"132":{"tf":1.0},"133":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":1.4142135623730951},"207":{"tf":1.7320508075688772},"222":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.4142135623730951},"255":{"tf":1.0},"284":{"tf":1.0},"331":{"tf":1.0},"34":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":2.0},"387":{"tf":1.0},"482":{"tf":1.0},"500":{"tf":1.0},"505":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.4142135623730951},"6":{"tf":1.0},"63":{"tf":1.0},"697":{"tf":1.4142135623730951},"723":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.7320508075688772},"831":{"tf":1.0},"961":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":15,"docs":{"1":{"tf":1.0},"140":{"tf":1.0},"164":{"tf":1.0},"165":{"tf":1.0},"171":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":1.7320508075688772},"341":{"tf":1.4142135623730951},"390":{"tf":1.0},"522":{"tf":1.0},"668":{"tf":1.0},"874":{"tf":1.0}}}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":3,"docs":{"152":{"tf":1.0},"290":{"tf":1.0},"968":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":1,"docs":{"929":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"y":{"df":8,"docs":{"138":{"tf":1.0},"257":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"427":{"tf":1.0},"507":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"799":{"tf":1.0}}},"_":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"799":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":16,"docs":{"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"795":{"tf":2.23606797749979},"796":{"tf":3.3166247903554},"797":{"tf":2.449489742783178},"798":{"tf":1.0},"799":{"tf":5.0},"800":{"tf":1.4142135623730951},"801":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.4142135623730951},"804":{"tf":2.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":2.0}}},"t":{"df":7,"docs":{"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"875":{"tf":1.4142135623730951},"879":{"tf":1.7320508075688772},"881":{"tf":2.449489742783178},"889":{"tf":1.0},"890":{"tf":1.0}},"e":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}}},"v":{"df":2,"docs":{"40":{"tf":1.0},"721":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":4,"docs":{"200":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.0}}}}}}},"t":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"723":{"tf":2.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"v":{"df":1,"docs":{"818":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":23,"docs":{"267":{"tf":1.0},"40":{"tf":1.0},"42":{"tf":1.0},"5":{"tf":1.0},"58":{"tf":1.0},"72":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":1.7320508075688772},"752":{"tf":1.0},"776":{"tf":1.7320508075688772},"779":{"tf":1.0},"808":{"tf":1.7320508075688772},"809":{"tf":1.7320508075688772},"810":{"tf":2.0},"812":{"tf":1.0},"813":{"tf":1.4142135623730951},"814":{"tf":1.7320508075688772},"815":{"tf":2.0},"817":{"tf":1.7320508075688772},"826":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"938":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":2,"docs":{"207":{"tf":1.4142135623730951},"375":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"467":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"203":{"tf":1.4142135623730951},"221":{"tf":1.7320508075688772}}}}},"t":{"df":2,"docs":{"204":{"tf":1.0},"568":{"tf":1.4142135623730951}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"776":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":25,"docs":{"131":{"tf":1.0},"187":{"tf":1.0},"200":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"417":{"tf":1.0},"438":{"tf":1.0},"455":{"tf":1.0},"514":{"tf":1.0},"526":{"tf":1.0},"651":{"tf":1.0},"693":{"tf":1.0},"700":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"814":{"tf":1.0},"852":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":20,"docs":{"140":{"tf":1.0},"199":{"tf":1.7320508075688772},"200":{"tf":1.7320508075688772},"210":{"tf":1.0},"211":{"tf":1.0},"249":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.0},"358":{"tf":1.0},"363":{"tf":1.7320508075688772},"366":{"tf":1.0},"375":{"tf":1.4142135623730951},"417":{"tf":1.0},"588":{"tf":1.0},"810":{"tf":1.4142135623730951},"928":{"tf":1.0},"959":{"tf":1.0},"960":{"tf":1.0},"961":{"tf":1.4142135623730951},"969":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":75,"docs":{"198":{"tf":1.4142135623730951},"300":{"tf":1.0},"375":{"tf":1.7320508075688772},"410":{"tf":2.449489742783178},"411":{"tf":1.7320508075688772},"412":{"tf":3.3166247903554},"413":{"tf":1.7320508075688772},"414":{"tf":1.7320508075688772},"415":{"tf":2.6457513110645907},"416":{"tf":2.0},"417":{"tf":2.23606797749979},"418":{"tf":2.449489742783178},"419":{"tf":1.0},"420":{"tf":1.4142135623730951},"421":{"tf":1.0},"422":{"tf":1.4142135623730951},"423":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.4142135623730951},"426":{"tf":1.4142135623730951},"427":{"tf":2.449489742783178},"428":{"tf":1.7320508075688772},"429":{"tf":2.0},"58":{"tf":1.4142135623730951},"60":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.0},"75":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":3.3166247903554},"815":{"tf":1.0},"817":{"tf":1.0},"857":{"tf":2.23606797749979},"858":{"tf":1.7320508075688772},"859":{"tf":1.4142135623730951},"860":{"tf":2.0},"861":{"tf":1.4142135623730951},"862":{"tf":1.4142135623730951},"863":{"tf":2.23606797749979},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.4142135623730951},"870":{"tf":1.0},"879":{"tf":3.7416573867739413},"880":{"tf":2.0},"881":{"tf":2.0},"889":{"tf":1.4142135623730951},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":2.23606797749979},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.4142135623730951},"917":{"tf":1.4142135623730951},"918":{"tf":1.0},"919":{"tf":1.7320508075688772},"920":{"tf":1.4142135623730951},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"880":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}}}}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":11,"docs":{"169":{"tf":1.0},"440":{"tf":1.0},"650":{"tf":1.0},"660":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"739":{"tf":1.4142135623730951},"740":{"tf":1.0},"770":{"tf":1.4142135623730951},"984":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"206":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"402":{"tf":1.4142135623730951}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"300":{"tf":1.4142135623730951},"815":{"tf":1.4142135623730951},"818":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"v":{"df":31,"docs":{"123":{"tf":1.0},"124":{"tf":1.0},"24":{"tf":1.0},"3":{"tf":1.0},"341":{"tf":1.7320508075688772},"347":{"tf":1.0},"352":{"tf":1.0},"387":{"tf":1.7320508075688772},"388":{"tf":1.7320508075688772},"390":{"tf":1.0},"413":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0},"634":{"tf":1.4142135623730951},"782":{"tf":2.23606797749979},"783":{"tf":1.7320508075688772},"784":{"tf":1.4142135623730951},"785":{"tf":1.0},"786":{"tf":2.23606797749979},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"799":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"874":{"tf":1.7320508075688772}},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":1,"docs":{"439":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":6,"docs":{"204":{"tf":1.0},"500":{"tf":1.4142135623730951},"706":{"tf":1.0},"761":{"tf":1.7320508075688772},"776":{"tf":1.0},"83":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":5,"docs":{"602":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.4142135623730951},"701":{"tf":1.0},"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"793":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"b":{"df":42,"docs":{"1008":{"tf":1.0},"1009":{"tf":1.0},"1015":{"tf":1.0},"123":{"tf":1.0},"191":{"tf":1.0},"203":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"251":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.7320508075688772},"267":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.0},"344":{"tf":1.0},"370":{"tf":1.0},"379":{"tf":1.0},"438":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"53":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"567":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"697":{"tf":1.0},"735":{"tf":1.0},"74":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":1.7320508075688772},"811":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"786":{"tf":2.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":71,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"184":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"333":{"tf":1.0},"346":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"748":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"786":{"tf":1.4142135623730951},"79":{"tf":1.0},"808":{"tf":1.0},"813":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":12,"docs":{"345":{"tf":1.7320508075688772},"627":{"tf":1.0},"632":{"tf":1.7320508075688772},"634":{"tf":1.0},"635":{"tf":2.0},"636":{"tf":1.7320508075688772},"637":{"tf":1.4142135623730951},"638":{"tf":1.0},"642":{"tf":1.7320508075688772},"644":{"tf":1.0},"648":{"tf":1.7320508075688772},"786":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"559":{"tf":1.7320508075688772}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":51,"docs":{"1006":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"124":{"tf":1.0},"138":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"303":{"tf":1.0},"323":{"tf":1.0},"349":{"tf":1.0},"35":{"tf":1.0},"356":{"tf":1.0},"38":{"tf":1.7320508075688772},"39":{"tf":1.0},"429":{"tf":1.0},"43":{"tf":1.4142135623730951},"483":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"518":{"tf":1.0},"522":{"tf":1.0},"54":{"tf":1.0},"546":{"tf":1.0},"576":{"tf":1.0},"725":{"tf":1.0},"727":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"737":{"tf":1.0},"771":{"tf":2.0},"772":{"tf":1.0},"773":{"tf":1.4142135623730951},"774":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"780":{"tf":1.0},"781":{"tf":1.0},"829":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}},"r":{"df":21,"docs":{"204":{"tf":1.0},"208":{"tf":1.0},"237":{"tf":1.0},"254":{"tf":1.0},"257":{"tf":1.0},"354":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"507":{"tf":1.0},"54":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"641":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"939":{"tf":1.0}}}},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"234":{"tf":1.0}}}}},"t":{"df":4,"docs":{"18":{"tf":1.0},"602":{"tf":3.872983346207417},"603":{"tf":1.7320508075688772},"696":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":24,"docs":{"222":{"tf":1.0},"599":{"tf":1.4142135623730951},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"666":{"tf":1.0},"692":{"tf":2.0},"693":{"tf":1.4142135623730951},"694":{"tf":1.0},"695":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":1.0},"698":{"tf":1.4142135623730951},"699":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"707":{"tf":1.0},"708":{"tf":1.0},"786":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":29,"docs":{"0":{"tf":1.0},"1006":{"tf":1.4142135623730951},"113":{"tf":1.0},"16":{"tf":1.0},"180":{"tf":1.0},"195":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.4142135623730951},"450":{"tf":1.0},"48":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"567":{"tf":1.0},"761":{"tf":1.0},"791":{"tf":1.0},"794":{"tf":1.0},"813":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":6,"docs":{"296":{"tf":1.0},"388":{"tf":1.0},"567":{"tf":1.7320508075688772},"635":{"tf":1.4142135623730951},"735":{"tf":1.0},"763":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"r":{"df":4,"docs":{"429":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":37,"docs":{"124":{"tf":1.4142135623730951},"126":{"tf":1.0},"127":{"tf":1.4142135623730951},"134":{"tf":1.0},"138":{"tf":1.0},"170":{"tf":1.0},"199":{"tf":1.0},"226":{"tf":1.0},"253":{"tf":1.4142135623730951},"303":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"364":{"tf":1.0},"415":{"tf":1.0},"51":{"tf":1.0},"524":{"tf":1.0},"550":{"tf":1.0},"553":{"tf":1.0},"568":{"tf":1.4142135623730951},"571":{"tf":1.4142135623730951},"588":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"648":{"tf":1.0},"721":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":2.0},"81":{"tf":1.0},"814":{"tf":1.0},"913":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"338":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"432":{"tf":1.0},"438":{"tf":1.4142135623730951},"516":{"tf":1.0},"525":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"c":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"874":{"tf":1.0}}}}}}}}}},"v":{"df":16,"docs":{"167":{"tf":1.4142135623730951},"170":{"tf":1.0},"175":{"tf":1.4142135623730951},"314":{"tf":1.0},"4":{"tf":1.0},"538":{"tf":1.4142135623730951},"587":{"tf":1.4142135623730951},"601":{"tf":1.7320508075688772},"615":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"82":{"tf":1.0},"977":{"tf":1.0}},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":74,"docs":{"1011":{"tf":1.0},"103":{"tf":1.0},"108":{"tf":1.0},"125":{"tf":1.7320508075688772},"131":{"tf":1.0},"141":{"tf":1.0},"145":{"tf":1.4142135623730951},"146":{"tf":1.0},"152":{"tf":1.0},"153":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.4142135623730951},"201":{"tf":1.0},"219":{"tf":1.4142135623730951},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"270":{"tf":1.0},"282":{"tf":1.0},"289":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"306":{"tf":1.0},"312":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.0},"322":{"tf":1.0},"328":{"tf":1.7320508075688772},"329":{"tf":1.0},"33":{"tf":1.7320508075688772},"367":{"tf":1.0},"369":{"tf":1.4142135623730951},"378":{"tf":1.0},"381":{"tf":1.7320508075688772},"382":{"tf":1.0},"407":{"tf":1.0},"414":{"tf":1.4142135623730951},"42":{"tf":1.0},"433":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.4142135623730951},"544":{"tf":1.0},"552":{"tf":1.0},"581":{"tf":1.0},"59":{"tf":1.0},"593":{"tf":1.0},"608":{"tf":1.0},"630":{"tf":1.7320508075688772},"687":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"774":{"tf":1.0},"785":{"tf":1.0},"830":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.4142135623730951},"856":{"tf":1.0},"877":{"tf":1.0},"886":{"tf":1.0},"902":{"tf":1.0},"914":{"tf":1.0},"943":{"tf":1.0},"952":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.4142135623730951},"960":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"969":{"tf":1.4142135623730951},"973":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"848":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"i":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"744":{"tf":1.0}}}},"c":{"df":5,"docs":{"514":{"tf":1.4142135623730951},"515":{"tf":2.449489742783178},"516":{"tf":1.4142135623730951},"517":{"tf":1.0},"95":{"tf":2.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"314":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"t":{"df":37,"docs":{"247":{"tf":2.449489742783178},"248":{"tf":1.7320508075688772},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"251":{"tf":1.4142135623730951},"252":{"tf":2.23606797749979},"253":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"256":{"tf":1.0},"257":{"tf":1.4142135623730951},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0},"495":{"tf":1.7320508075688772},"501":{"tf":1.7320508075688772},"502":{"tf":2.449489742783178},"503":{"tf":2.0},"505":{"tf":1.0},"507":{"tf":1.0},"549":{"tf":2.23606797749979},"550":{"tf":1.4142135623730951},"551":{"tf":1.7320508075688772},"552":{"tf":1.0},"553":{"tf":2.6457513110645907},"554":{"tf":1.7320508075688772},"555":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"66":{"tf":1.0}}}},"i":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":3,"docs":{"126":{"tf":1.0},"46":{"tf":1.0},"878":{"tf":2.23606797749979}}}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":1,"docs":{"483":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"933":{"tf":1.0}},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"343":{"tf":1.0}}}}}}}}}}},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"553":{"tf":1.0},"761":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":62,"docs":{"142":{"tf":1.0},"151":{"tf":1.0},"163":{"tf":1.0},"169":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"21":{"tf":1.0},"218":{"tf":1.0},"22":{"tf":1.7320508075688772},"231":{"tf":1.0},"24":{"tf":1.7320508075688772},"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"288":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.4142135623730951},"33":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.4142135623730951},"407":{"tf":1.0},"432":{"tf":1.0},"436":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"52":{"tf":1.0},"522":{"tf":2.0},"567":{"tf":1.0},"586":{"tf":1.0},"598":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"629":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"722":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"786":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"835":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.4142135623730951},"870":{"tf":1.0},"874":{"tf":1.0},"881":{"tf":1.0},"95":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":5,"docs":{"199":{"tf":1.0},"375":{"tf":1.0},"737":{"tf":1.4142135623730951},"832":{"tf":1.0},"990":{"tf":1.0}},"i":{"df":2,"docs":{"296":{"tf":1.0},"724":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":8,"docs":{"322":{"tf":1.0},"333":{"tf":1.0},"343":{"tf":2.6457513110645907},"349":{"tf":2.0},"350":{"tf":1.4142135623730951},"513":{"tf":1.0},"516":{"tf":2.6457513110645907},"520":{"tf":2.449489742783178}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"343":{"tf":1.7320508075688772},"345":{"tf":1.0}}}}}}}}}},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}}},"m":{"a":{"df":1,"docs":{"430":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":105,"docs":{"1":{"tf":1.0},"1001":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1015":{"tf":1.4142135623730951},"122":{"tf":1.0},"135":{"tf":1.4142135623730951},"136":{"tf":1.0},"149":{"tf":1.4142135623730951},"150":{"tf":1.0},"16":{"tf":1.4142135623730951},"163":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.4142135623730951},"182":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.4142135623730951},"195":{"tf":1.0},"212":{"tf":1.4142135623730951},"215":{"tf":1.0},"226":{"tf":1.4142135623730951},"229":{"tf":1.0},"246":{"tf":1.4142135623730951},"247":{"tf":1.0},"262":{"tf":1.4142135623730951},"267":{"tf":1.0},"270":{"tf":1.0},"272":{"tf":1.0},"279":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"310":{"tf":1.4142135623730951},"311":{"tf":1.0},"321":{"tf":1.4142135623730951},"322":{"tf":1.0},"361":{"tf":1.4142135623730951},"366":{"tf":1.0},"37":{"tf":1.4142135623730951},"38":{"tf":1.0},"385":{"tf":1.4142135623730951},"386":{"tf":1.0},"399":{"tf":1.4142135623730951},"412":{"tf":1.0},"430":{"tf":1.0},"449":{"tf":1.4142135623730951},"451":{"tf":1.0},"464":{"tf":1.4142135623730951},"481":{"tf":1.0},"494":{"tf":1.4142135623730951},"495":{"tf":1.0},"512":{"tf":1.4142135623730951},"513":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"54":{"tf":1.4142135623730951},"548":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.4142135623730951},"584":{"tf":1.0},"597":{"tf":1.4142135623730951},"598":{"tf":1.0},"612":{"tf":1.4142135623730951},"613":{"tf":1.0},"626":{"tf":1.4142135623730951},"627":{"tf":1.0},"648":{"tf":1.4142135623730951},"649":{"tf":1.0},"663":{"tf":1.4142135623730951},"664":{"tf":1.0},"677":{"tf":1.4142135623730951},"678":{"tf":1.0},"691":{"tf":1.4142135623730951},"692":{"tf":1.0},"708":{"tf":1.4142135623730951},"709":{"tf":1.0},"728":{"tf":1.4142135623730951},"757":{"tf":1.0},"76":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"799":{"tf":1.0},"807":{"tf":1.4142135623730951},"808":{"tf":1.0},"826":{"tf":1.4142135623730951},"827":{"tf":1.0},"840":{"tf":1.4142135623730951},"871":{"tf":1.0},"890":{"tf":1.4142135623730951},"891":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":1.0},"92":{"tf":1.4142135623730951},"925":{"tf":1.4142135623730951},"926":{"tf":1.0},"939":{"tf":1.4142135623730951},"940":{"tf":1.0},"956":{"tf":1.4142135623730951},"957":{"tf":1.0},"973":{"tf":1.4142135623730951},"974":{"tf":1.0},"987":{"tf":1.4142135623730951},"988":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":24,"docs":{"100":{"tf":1.0},"19":{"tf":1.0},"191":{"tf":1.4142135623730951},"314":{"tf":1.0},"365":{"tf":1.0},"375":{"tf":1.0},"40":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"633":{"tf":1.0},"663":{"tf":1.0},"696":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"959":{"tf":1.0},"979":{"tf":1.0}}}}}},"df":0,"docs":{}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":5,"docs":{"171":{"tf":1.0},"24":{"tf":1.0},"255":{"tf":1.0},"404":{"tf":1.0},"531":{"tf":1.0}}}},"d":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"453":{"tf":1.0},"777":{"tf":1.4142135623730951},"84":{"tf":1.4142135623730951},"895":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"799":{"tf":1.0}}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"829":{"tf":1.0}}}},"df":0,"docs":{}}}}},"c":{"a":{"df":0,"docs":{},"r":{"d":{"df":4,"docs":{"204":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"339":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"497":{"tf":1.0},"567":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"721":{"tf":1.0},"776":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"895":{"tf":2.0}}}},"df":0,"docs":{},"s":{"df":1,"docs":{"418":{"tf":1.0}}}}},"v":{"df":7,"docs":{"248":{"tf":1.0},"254":{"tf":1.0},"296":{"tf":1.0},"496":{"tf":1.0},"512":{"tf":1.0},"66":{"tf":1.0},"8":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"495":{"tf":1.0}},"i":{"df":38,"docs":{"18":{"tf":1.0},"22":{"tf":1.0},"248":{"tf":1.4142135623730951},"495":{"tf":2.0},"496":{"tf":1.4142135623730951},"497":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":1.0},"506":{"tf":1.0},"507":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"549":{"tf":2.23606797749979},"550":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"552":{"tf":1.0},"553":{"tf":1.7320508075688772},"554":{"tf":1.0},"555":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":1.0},"777":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"516":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":51,"docs":{"1014":{"tf":1.0},"16":{"tf":1.0},"161":{"tf":1.0},"180":{"tf":1.0},"194":{"tf":1.4142135623730951},"201":{"tf":1.0},"207":{"tf":1.0},"219":{"tf":1.0},"229":{"tf":1.0},"243":{"tf":1.4142135623730951},"265":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"35":{"tf":1.4142135623730951},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"409":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"417":{"tf":1.0},"441":{"tf":1.0},"518":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.0},"569":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.0},"581":{"tf":1.0},"60":{"tf":1.0},"630":{"tf":1.0},"646":{"tf":1.4142135623730951},"712":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.4142135623730951},"724":{"tf":1.4142135623730951},"727":{"tf":1.0},"74":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"778":{"tf":1.4142135623730951},"780":{"tf":1.0},"794":{"tf":1.0},"807":{"tf":1.0},"824":{"tf":1.0},"844":{"tf":1.4142135623730951},"846":{"tf":1.0},"869":{"tf":1.0},"878":{"tf":1.0},"954":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"863":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"927":{"tf":1.0}}}}}}},"k":{"df":7,"docs":{"255":{"tf":1.0},"62":{"tf":1.0},"69":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"78":{"tf":1.0}}},"p":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":12,"docs":{"205":{"tf":3.0},"24":{"tf":1.0},"25":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"372":{"tf":1.0},"409":{"tf":1.0},"614":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":2.0},"944":{"tf":1.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"814":{"tf":1.4142135623730951},"879":{"tf":3.4641016151377544}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"514":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":14,"docs":{"39":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.7320508075688772},"450":{"tf":2.6457513110645907},"628":{"tf":1.0},"629":{"tf":2.23606797749979},"641":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"67":{"tf":1.0},"69":{"tf":1.4142135623730951},"715":{"tf":1.0},"811":{"tf":1.0},"815":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"222":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":5,"docs":{"140":{"tf":1.0},"146":{"tf":1.0},"356":{"tf":1.0},"573":{"tf":1.0},"990":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"173":{"tf":1.0},"335":{"tf":1.0},"368":{"tf":1.0},"722":{"tf":1.0},"817":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"7":{"tf":1.0},"81":{"tf":1.0}}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":26,"docs":{"205":{"tf":1.0},"24":{"tf":1.0},"248":{"tf":1.0},"303":{"tf":1.0},"373":{"tf":1.0},"430":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.4142135623730951},"438":{"tf":1.0},"439":{"tf":1.0},"551":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"64":{"tf":1.0},"65":{"tf":1.4142135623730951},"714":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.4142135623730951},"724":{"tf":1.4142135623730951},"73":{"tf":1.0},"74":{"tf":1.0},"77":{"tf":1.0},"932":{"tf":2.0},"933":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"573":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"567":{"tf":1.0}},"r":{"df":0,"docs":{},"g":{"df":3,"docs":{"350":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}},"s":{"df":4,"docs":{"19":{"tf":1.0},"24":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0}}},"t":{"df":2,"docs":{"264":{"tf":1.0},"267":{"tf":1.0}}}}},"i":{"d":{"df":6,"docs":{"204":{"tf":1.0},"335":{"tf":1.0},"512":{"tf":1.0},"717":{"tf":1.0},"759":{"tf":1.0},"931":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"201":{"tf":1.0},"774":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"p":{"df":4,"docs":{"203":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"222":{"tf":1.4142135623730951}}}},"o":{"b":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"780":{"tf":1.0}}}}}}}}},"c":{"df":2,"docs":{"456":{"tf":1.0},"7":{"tf":1.0}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"334":{"tf":1.0}}},"df":21,"docs":{"171":{"tf":1.0},"209":{"tf":1.4142135623730951},"210":{"tf":1.4142135623730951},"272":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"330":{"tf":1.0},"341":{"tf":1.4142135623730951},"391":{"tf":1.0},"564":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"772":{"tf":1.0},"81":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":1.7320508075688772},"904":{"tf":1.0},"92":{"tf":1.0},"921":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}}}}}},"df":21,"docs":{"154":{"tf":1.0},"19":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"296":{"tf":1.0},"452":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"600":{"tf":1.0},"629":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"697":{"tf":1.0},"725":{"tf":1.0},"732":{"tf":1.0},"885":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":41,"docs":{"112":{"tf":1.0},"115":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"32":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"35":{"tf":1.0},"351":{"tf":1.0},"442":{"tf":1.0},"453":{"tf":1.0},"459":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"511":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"534":{"tf":1.4142135623730951},"6":{"tf":1.0},"615":{"tf":1.0},"660":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":2.6457513110645907},"761":{"tf":2.0},"762":{"tf":1.0},"776":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"826":{"tf":1.0},"848":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"’":{"df":0,"docs":{},"t":{"df":1,"docs":{"751":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"249":{"tf":1.0},"388":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"n":{"'":{"df":0,"docs":{},"t":{"df":24,"docs":{"208":{"tf":1.0},"250":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"523":{"tf":1.0},"528":{"tf":1.0},"568":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"65":{"tf":1.0},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"831":{"tf":1.0},"846":{"tf":1.4142135623730951},"855":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"881":{"tf":2.0},"885":{"tf":1.0},"932":{"tf":1.0}}}},"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":32,"docs":{"112":{"tf":1.0},"177":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"234":{"tf":1.0},"257":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.0},"371":{"tf":1.0},"459":{"tf":1.0},"472":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"507":{"tf":1.0},"520":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"591":{"tf":1.0},"619":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.4142135623730951},"710":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"786":{"tf":1.0},"788":{"tf":1.0},"932":{"tf":1.0},"95":{"tf":1.0}}}},"r":{"a":{"d":{"df":0,"docs":{},"o":{"df":3,"docs":{"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"/":{"df":0,"docs":{},"k":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":4,"docs":{"429":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"566":{"tf":1.0}}}}}},"df":36,"docs":{"185":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.7320508075688772},"221":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"265":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.7320508075688772},"316":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":2.449489742783178},"376":{"tf":1.0},"412":{"tf":2.0},"415":{"tf":2.0},"416":{"tf":2.23606797749979},"417":{"tf":1.0},"42":{"tf":1.0},"427":{"tf":1.0},"470":{"tf":1.0},"473":{"tf":1.0},"48":{"tf":1.0},"52":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"724":{"tf":1.0},"745":{"tf":1.0},"752":{"tf":1.4142135623730951},"77":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"861":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}},"u":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"184":{"tf":1.0},"207":{"tf":1.0},"752":{"tf":1.0}},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"<":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"617":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"749":{"tf":1.0}}}},"t":{"df":1,"docs":{"577":{"tf":1.0}}}},"df":0,"docs":{}},"w":{"df":0,"docs":{},"n":{"df":11,"docs":{"152":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"284":{"tf":1.0},"437":{"tf":1.0},"60":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.0},"776":{"tf":1.0},"845":{"tf":1.0},"852":{"tf":1.0}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":1,"docs":{"609":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":9,"docs":{"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.4142135623730951},"722":{"tf":1.7320508075688772},"724":{"tf":1.0},"895":{"tf":1.0},"990":{"tf":1.4142135623730951}},"e":{"d":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"715":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"658":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"172":{"tf":1.0}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":6,"docs":{"144":{"tf":1.0},"203":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"371":{"tf":1.0},"501":{"tf":1.0}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":2,"docs":{"749":{"tf":1.4142135623730951},"776":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"p":{"d":{"df":1,"docs":{"126":{"tf":2.8284271247461903}}},"df":1,"docs":{"126":{"tf":3.1622776601683795}}},"r":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":6,"docs":{"16":{"tf":1.4142135623730951},"724":{"tf":1.0},"83":{"tf":1.0},"878":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"564":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":125,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":2.0},"106":{"tf":1.0},"114":{"tf":1.4142135623730951},"122":{"tf":1.0},"127":{"tf":1.4142135623730951},"136":{"tf":1.0},"141":{"tf":1.7320508075688772},"150":{"tf":1.0},"155":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"173":{"tf":1.4142135623730951},"182":{"tf":1.0},"187":{"tf":1.7320508075688772},"195":{"tf":1.0},"213":{"tf":1.4142135623730951},"215":{"tf":1.0},"227":{"tf":1.4142135623730951},"229":{"tf":1.0},"236":{"tf":1.7320508075688772},"247":{"tf":1.0},"254":{"tf":1.4142135623730951},"268":{"tf":1.0},"27":{"tf":1.4142135623730951},"274":{"tf":1.4142135623730951},"279":{"tf":1.0},"285":{"tf":2.0},"294":{"tf":1.0},"303":{"tf":1.4142135623730951},"311":{"tf":1.0},"316":{"tf":1.4142135623730951},"322":{"tf":1.0},"353":{"tf":1.4142135623730951},"366":{"tf":1.0},"377":{"tf":1.4142135623730951},"38":{"tf":1.0},"386":{"tf":1.0},"391":{"tf":1.7320508075688772},"410":{"tf":1.0},"418":{"tf":1.7320508075688772},"430":{"tf":1.0},"441":{"tf":1.4142135623730951},"451":{"tf":1.0},"456":{"tf":1.4142135623730951},"465":{"tf":1.0},"473":{"tf":1.4142135623730951},"481":{"tf":1.0},"486":{"tf":1.4142135623730951},"495":{"tf":1.0},"504":{"tf":1.4142135623730951},"513":{"tf":1.0},"527":{"tf":1.4142135623730951},"535":{"tf":1.0},"540":{"tf":1.4142135623730951},"549":{"tf":1.0},"55":{"tf":1.4142135623730951},"554":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"577":{"tf":1.4142135623730951},"584":{"tf":1.0},"589":{"tf":1.4142135623730951},"598":{"tf":1.0},"604":{"tf":1.7320508075688772},"613":{"tf":1.0},"618":{"tf":1.7320508075688772},"627":{"tf":1.0},"638":{"tf":1.7320508075688772},"649":{"tf":1.0},"655":{"tf":1.4142135623730951},"664":{"tf":1.0},"669":{"tf":1.4142135623730951},"678":{"tf":1.0},"68":{"tf":1.7320508075688772},"683":{"tf":1.4142135623730951},"692":{"tf":1.0},"700":{"tf":1.4142135623730951},"709":{"tf":1.0},"724":{"tf":1.4142135623730951},"730":{"tf":1.0},"737":{"tf":1.4142135623730951},"741":{"tf":1.0},"753":{"tf":1.4142135623730951},"757":{"tf":1.0},"762":{"tf":1.4142135623730951},"771":{"tf":1.0},"779":{"tf":1.4142135623730951},"782":{"tf":1.0},"787":{"tf":1.7320508075688772},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.7320508075688772},"800":{"tf":1.7320508075688772},"808":{"tf":1.0},"818":{"tf":1.4142135623730951},"827":{"tf":1.0},"832":{"tf":1.4142135623730951},"84":{"tf":1.4142135623730951},"841":{"tf":1.0},"849":{"tf":1.7320508075688772},"852":{"tf":1.0},"857":{"tf":1.0},"863":{"tf":1.4142135623730951},"871":{"tf":1.0},"882":{"tf":1.4142135623730951},"891":{"tf":1.0},"899":{"tf":1.7320508075688772},"908":{"tf":1.0},"915":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"934":{"tf":2.0},"936":{"tf":1.0},"940":{"tf":1.0},"945":{"tf":1.7320508075688772},"957":{"tf":1.0},"962":{"tf":1.7320508075688772},"974":{"tf":1.0},"979":{"tf":1.7320508075688772},"98":{"tf":1.4142135623730951},"988":{"tf":1.0},"993":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":1,"docs":{"807":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"342":{"tf":1.0}},"n":{"df":1,"docs":{"772":{"tf":1.0}}},"r":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":9,"docs":{"347":{"tf":1.0},"376":{"tf":1.0},"385":{"tf":1.0},"439":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"720":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"e":{"df":20,"docs":{"108":{"tf":1.4142135623730951},"127":{"tf":1.0},"203":{"tf":1.0},"255":{"tf":1.0},"3":{"tf":1.0},"388":{"tf":1.0},"422":{"tf":1.0},"500":{"tf":1.0},"505":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"737":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.0},"832":{"tf":1.0},"895":{"tf":1.0},"968":{"tf":1.0}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"1015":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"19":{"tf":1.4142135623730951},"347":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.4142135623730951},"453":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"t":{"df":15,"docs":{"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"186":{"tf":1.0},"190":{"tf":1.0},"204":{"tf":1.0},"284":{"tf":1.0},"342":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.7320508075688772},"568":{"tf":1.0},"573":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"e":{"df":38,"docs":{"141":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":2.449489742783178},"206":{"tf":1.0},"207":{"tf":1.7320508075688772},"267":{"tf":1.0},"323":{"tf":1.0},"324":{"tf":1.0},"339":{"tf":1.0},"342":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.4142135623730951},"374":{"tf":1.0},"406":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.4142135623730951},"500":{"tf":1.0},"571":{"tf":1.0},"653":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"720":{"tf":1.0},"772":{"tf":1.4142135623730951},"776":{"tf":2.0},"777":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0},"831":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.4142135623730951}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":3,"docs":{"772":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.4142135623730951}}}}},"y":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":33,"docs":{"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"147":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.4142135623730951},"28":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.4142135623730951},"576":{"tf":1.4142135623730951},"711":{"tf":1.0},"741":{"tf":2.23606797749979},"742":{"tf":1.4142135623730951},"743":{"tf":1.4142135623730951},"744":{"tf":1.4142135623730951},"745":{"tf":1.0},"746":{"tf":1.0},"747":{"tf":1.4142135623730951},"748":{"tf":1.0},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.4142135623730951},"755":{"tf":1.0},"756":{"tf":1.4142135623730951},"777":{"tf":1.0},"912":{"tf":1.0},"959":{"tf":1.0}},"i":{"c":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}},"s":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{":":{":":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"i":{"d":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"$":{"'":{"df":1,"docs":{"721":{"tf":1.0}}},"df":0,"docs":{}},".":{"df":0,"docs":{},"g":{"df":24,"docs":{"154":{"tf":1.0},"203":{"tf":1.0},"234":{"tf":1.4142135623730951},"364":{"tf":1.0},"372":{"tf":1.4142135623730951},"381":{"tf":1.0},"45":{"tf":1.0},"453":{"tf":1.0},"47":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"576":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"68":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":2.23606797749979},"81":{"tf":2.449489742783178},"878":{"tf":1.0},"880":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":2.0}}}},"[":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}}}}}}},"x":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}},"^":{"df":0,"docs":{},"{":{"a":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"c":{"df":0,"docs":{},"h":{"df":74,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":2.6457513110645907},"221":{"tf":1.0},"231":{"tf":1.7320508075688772},"255":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"323":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"337":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":2.0},"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":2.23606797749979},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"426":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.7320508075688772},"45":{"tf":1.4142135623730951},"455":{"tf":1.4142135623730951},"46":{"tf":2.0},"467":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"482":{"tf":1.7320508075688772},"483":{"tf":1.0},"485":{"tf":1.0},"507":{"tf":1.0},"51":{"tf":1.0},"522":{"tf":2.23606797749979},"523":{"tf":1.0},"524":{"tf":1.4142135623730951},"528":{"tf":1.0},"534":{"tf":1.0},"553":{"tf":1.7320508075688772},"568":{"tf":1.0},"586":{"tf":1.4142135623730951},"589":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.4142135623730951},"673":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"715":{"tf":1.7320508075688772},"717":{"tf":1.4142135623730951},"72":{"tf":1.0},"721":{"tf":2.23606797749979},"722":{"tf":1.7320508075688772},"723":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"776":{"tf":1.7320508075688772},"797":{"tf":1.0},"814":{"tf":1.0},"831":{"tf":1.0},"836":{"tf":1.0},"85":{"tf":1.0},"872":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.449489742783178},"912":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"130":{"tf":1.0},"214":{"tf":1.0},"619":{"tf":1.0},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"124":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"568":{"tf":1.0},"576":{"tf":1.0},"577":{"tf":1.0},"715":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0},"817":{"tf":1.0}}}}}},"n":{"df":3,"docs":{"470":{"tf":1.4142135623730951},"720":{"tf":2.0},"724":{"tf":1.0}}}},"s":{"df":1,"docs":{"961":{"tf":1.0}},"i":{"df":10,"docs":{"296":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.4142135623730951},"460":{"tf":1.0},"75":{"tf":1.0},"786":{"tf":1.0},"846":{"tf":1.0},"849":{"tf":1.4142135623730951},"952":{"tf":1.0},"969":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"573":{"tf":1.0},"725":{"tf":1.0},"777":{"tf":1.0},"836":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951}}}},"l":{"df":0,"docs":{},"i":{"df":15,"docs":{"253":{"tf":1.0},"314":{"tf":1.0},"497":{"tf":1.0},"518":{"tf":1.0},"528":{"tf":1.0},"531":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":1.0},"763":{"tf":1.4142135623730951},"810":{"tf":1.0},"811":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"847":{"tf":1.0}}}}}}},"c":{"d":{"df":0,"docs":{},"s":{"a":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"505":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":15,"docs":{"195":{"tf":1.0},"207":{"tf":1.7320508075688772},"211":{"tf":1.0},"213":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.0},"243":{"tf":1.0},"265":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.4142135623730951},"779":{"tf":1.0},"916":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":35,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"201":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.0},"329":{"tf":1.7320508075688772},"362":{"tf":1.0},"364":{"tf":1.0},"376":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"49":{"tf":1.0},"514":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"518":{"tf":1.0},"52":{"tf":1.0},"521":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"539":{"tf":1.0},"54":{"tf":1.0},"600":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"784":{"tf":1.0},"785":{"tf":1.0},"804":{"tf":1.0},"844":{"tf":1.0},"874":{"tf":1.0},"912":{"tf":1.4142135623730951},"971":{"tf":1.0},"973":{"tf":1.4142135623730951},"984":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"699":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":1,"docs":{"340":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"g":{"df":8,"docs":{"207":{"tf":1.0},"30":{"tf":1.0},"40":{"tf":1.0},"871":{"tf":1.0},"881":{"tf":1.4142135623730951},"944":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"779":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"c":{"df":1,"docs":{"270":{"tf":1.0}}},"df":0,"docs":{}}},"df":5,"docs":{"112":{"tf":1.4142135623730951},"346":{"tf":1.0},"45":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0}},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":31,"docs":{"1008":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":2.8284271247461903},"207":{"tf":1.0},"208":{"tf":1.0},"24":{"tf":1.0},"267":{"tf":1.4142135623730951},"304":{"tf":1.0},"354":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"52":{"tf":1.0},"54":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"600":{"tf":1.0},"650":{"tf":1.4142135623730951},"693":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"773":{"tf":1.0},"810":{"tf":1.4142135623730951},"831":{"tf":1.0},"849":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":2.0},"900":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":2.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"i":{"c":{"df":1,"docs":{"720":{"tf":1.0}},"i":{"df":30,"docs":{"103":{"tf":1.0},"124":{"tf":1.0},"144":{"tf":1.0},"199":{"tf":1.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.0},"28":{"tf":1.0},"29":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"46":{"tf":1.0},"650":{"tf":1.0},"732":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":1.7320508075688772},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"874":{"tf":1.4142135623730951},"880":{"tf":1.0},"885":{"tf":1.4142135623730951},"94":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.0},"968":{"tf":1.0},"97":{"tf":1.0},"991":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":15,"docs":{"139":{"tf":1.0},"181":{"tf":1.0},"437":{"tf":1.0},"546":{"tf":1.0},"548":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"609":{"tf":1.0},"66":{"tf":1.0},"725":{"tf":1.0},"797":{"tf":1.0},"85":{"tf":1.0},"855":{"tf":1.0},"951":{"tf":1.0},"975":{"tf":1.0}}}}}}},"g":{"df":3,"docs":{"932":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"55":{"tf":1.0}}}},"df":0,"docs":{}}}}},"p":{"df":2,"docs":{"39":{"tf":1.0},"55":{"tf":1.0}}}},"l":{"a":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"931":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":2,"docs":{"148":{"tf":1.0},"204":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":6,"docs":{"441":{"tf":1.0},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"121":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"235":{"tf":1.0},"240":{"tf":1.0},"370":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"376":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":10,"docs":{"28":{"tf":1.0},"333":{"tf":2.0},"344":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"520":{"tf":1.0},"54":{"tf":1.0},"735":{"tf":1.0},"773":{"tf":1.0},"85":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"h":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"346":{"tf":1.0}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"144":{"tf":1.0},"325":{"tf":1.0},"356":{"tf":1.0},"39":{"tf":1.0},"55":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"84":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":13,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.0},"105":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"95":{"tf":2.449489742783178},"96":{"tf":1.0},"97":{"tf":1.4142135623730951},"98":{"tf":1.0},"99":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"720":{"tf":1.0},"724":{"tf":1.0}}}}}}}},"v":{"df":3,"docs":{"45":{"tf":1.0},"53":{"tf":1.4142135623730951},"725":{"tf":1.0}}}},"m":{"b":{"df":1,"docs":{"438":{"tf":1.0}},"e":{"d":{"df":1,"docs":{"345":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":5,"docs":{"138":{"tf":1.0},"354":{"tf":1.0},"375":{"tf":1.0},"54":{"tf":1.0},"973":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"72":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.7320508075688772}}}},"p":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"935":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"r":{"df":6,"docs":{"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.7320508075688772},"576":{"tf":1.0},"777":{"tf":1.0}}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":4,"docs":{"351":{"tf":1.0},"723":{"tf":1.0},"876":{"tf":1.0},"968":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"799":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":8,"docs":{"208":{"tf":2.0},"522":{"tf":1.0},"525":{"tf":1.4142135623730951},"564":{"tf":1.0},"633":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"992":{"tf":1.0}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":52,"docs":{"1015":{"tf":1.0},"112":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":2.0},"128":{"tf":1.0},"137":{"tf":1.0},"139":{"tf":1.0},"154":{"tf":1.4142135623730951},"172":{"tf":1.0},"177":{"tf":1.0},"203":{"tf":1.0},"22":{"tf":1.0},"348":{"tf":1.0},"38":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":2.449489742783178},"446":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"50":{"tf":1.0},"500":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.7320508075688772},"696":{"tf":1.0},"697":{"tf":1.0},"723":{"tf":1.0},"729":{"tf":1.7320508075688772},"783":{"tf":1.0},"786":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.4142135623730951},"83":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.4142135623730951},"958":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}},"c":{"df":0,"docs":{},"t":{"df":16,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"204":{"tf":1.0},"216":{"tf":1.0},"440":{"tf":1.4142135623730951},"461":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"73":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"21":{"tf":1.0},"33":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"v":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"o":{"d":{"df":36,"docs":{"164":{"tf":1.0},"165":{"tf":1.0},"166":{"tf":1.4142135623730951},"170":{"tf":3.3166247903554},"171":{"tf":2.0},"22":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"333":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.7320508075688772},"455":{"tf":2.23606797749979},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":2.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.7320508075688772},"520":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"588":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":2.0},"786":{"tf":1.4142135623730951}},"e":{"(":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"349":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"s":{"df":1,"docs":{"349":{"tf":1.0}}},"x":{"df":1,"docs":{"333":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":11,"docs":{"311":{"tf":2.449489742783178},"312":{"tf":2.0},"313":{"tf":2.0},"314":{"tf":2.23606797749979},"315":{"tf":2.6457513110645907},"316":{"tf":2.0},"317":{"tf":1.0},"318":{"tf":1.0},"319":{"tf":1.4142135623730951},"320":{"tf":1.0},"321":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"315":{"tf":1.0}}},".":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"321":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"347":{"tf":1.0},"778":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"250":{"tf":1.0},"323":{"tf":1.0},"895":{"tf":1.0},"898":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"g":{"df":9,"docs":{"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"761":{"tf":1.0},"895":{"tf":1.0}}}},"df":0,"docs":{}}}}},"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.7320508075688772}}}}}}},"df":35,"docs":{"1011":{"tf":1.0},"126":{"tf":2.449489742783178},"131":{"tf":1.0},"187":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":2.6457513110645907},"207":{"tf":2.449489742783178},"208":{"tf":4.898979485566356},"22":{"tf":1.0},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"40":{"tf":1.0},"435":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"525":{"tf":1.0},"544":{"tf":1.0},"551":{"tf":1.0},"57":{"tf":1.0},"633":{"tf":1.0},"653":{"tf":1.0},"670":{"tf":1.0},"72":{"tf":1.0},"750":{"tf":1.0},"776":{"tf":1.4142135623730951},"797":{"tf":1.0},"846":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"886":{"tf":1.0},"902":{"tf":1.0},"912":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}},"e":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"267":{"tf":1.0},"374":{"tf":1.0}}}}}}},"df":0,"docs":{}},"i":{"a":{"df":0,"docs":{},"n":{"df":4,"docs":{"252":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"735":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"848":{"tf":1.0}}}}},"s":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"35":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"577":{"tf":1.0}}}},"{":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"741":{"tf":1.0}}}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"c":{"df":23,"docs":{"100":{"tf":1.0},"284":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"481":{"tf":2.0},"482":{"tf":1.0},"483":{"tf":1.0},"484":{"tf":1.0},"485":{"tf":1.0},"486":{"tf":1.0},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.4142135623730951},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"605":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.0},"828":{"tf":1.4142135623730951},"855":{"tf":1.0}}},"df":0,"docs":{}}}},"g":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":6,"docs":{"201":{"tf":1.0},"358":{"tf":1.0},"470":{"tf":1.4142135623730951},"479":{"tf":1.0},"774":{"tf":1.0},"934":{"tf":1.0}}}}},"h":{"a":{"c":{"df":1,"docs":{"551":{"tf":1.0}}},"df":0,"docs":{},"n":{"c":{"df":30,"docs":{"140":{"tf":1.0},"188":{"tf":1.0},"365":{"tf":1.0},"40":{"tf":1.0},"410":{"tf":1.4142135623730951},"414":{"tf":1.0},"416":{"tf":1.4142135623730951},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.4142135623730951},"55":{"tf":1.0},"560":{"tf":1.0},"564":{"tf":1.0},"602":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"617":{"tf":1.0},"705":{"tf":1.0},"778":{"tf":1.0},"784":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"878":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":33,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"126":{"tf":1.0},"15":{"tf":1.0},"156":{"tf":1.0},"178":{"tf":1.0},"232":{"tf":1.0},"261":{"tf":1.0},"388":{"tf":1.0},"39":{"tf":1.0},"436":{"tf":1.0},"511":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.4142135623730951},"577":{"tf":1.4142135623730951},"619":{"tf":1.4142135623730951},"69":{"tf":1.0},"724":{"tf":1.0},"797":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0},"849":{"tf":1.0},"863":{"tf":1.0},"872":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"928":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"979":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"412":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"388":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":93,"docs":{"111":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.4142135623730951},"140":{"tf":1.0},"142":{"tf":1.4142135623730951},"154":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"175":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"206":{"tf":1.4142135623730951},"212":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"230":{"tf":1.0},"234":{"tf":1.7320508075688772},"237":{"tf":1.0},"239":{"tf":1.0},"24":{"tf":1.4142135623730951},"26":{"tf":1.0},"28":{"tf":1.0},"284":{"tf":1.4142135623730951},"290":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"304":{"tf":1.0},"323":{"tf":1.0},"324":{"tf":1.0},"325":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"346":{"tf":1.4142135623730951},"354":{"tf":1.0},"376":{"tf":1.0},"380":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"45":{"tf":1.4142135623730951},"452":{"tf":1.0},"453":{"tf":1.0},"457":{"tf":1.0},"46":{"tf":1.0},"467":{"tf":1.0},"47":{"tf":1.4142135623730951},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"591":{"tf":1.0},"593":{"tf":1.0},"633":{"tf":1.0},"639":{"tf":1.0},"644":{"tf":1.0},"67":{"tf":1.0},"694":{"tf":1.0},"711":{"tf":1.0},"742":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"772":{"tf":1.0},"776":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"816":{"tf":1.7320508075688772},"819":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":2.6457513110645907},"881":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.7320508075688772},"964":{"tf":1.0},"970":{"tf":1.0},"972":{"tf":1.0},"994":{"tf":1.0}},"e":{"!":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"1004":{"tf":1.0},"52":{"tf":1.0},"568":{"tf":1.0}}}},"i":{"df":0,"docs":{},"r":{"df":24,"docs":{"163":{"tf":1.0},"205":{"tf":2.0},"255":{"tf":1.0},"261":{"tf":1.0},"335":{"tf":1.0},"376":{"tf":1.4142135623730951},"432":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.0},"511":{"tf":1.0},"60":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.4142135623730951},"799":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.4142135623730951},"832":{"tf":1.0},"844":{"tf":1.0},"990":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"6":{"tf":1.0},"619":{"tf":1.0},"653":{"tf":1.4142135623730951}}}}}},"t":{"df":0,"docs":{},"i":{"df":9,"docs":{"185":{"tf":1.0},"3":{"tf":1.0},"5":{"tf":2.449489742783178},"515":{"tf":1.0},"565":{"tf":1.4142135623730951},"577":{"tf":1.0},"6":{"tf":1.0},"843":{"tf":1.0},"874":{"tf":1.7320508075688772}}},"l":{"df":2,"docs":{"848":{"tf":1.0},"907":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"416":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":24,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"208":{"tf":1.4142135623730951},"24":{"tf":1.7320508075688772},"25":{"tf":1.0},"255":{"tf":1.0},"284":{"tf":1.0},"343":{"tf":1.7320508075688772},"344":{"tf":2.449489742783178},"345":{"tf":2.0},"349":{"tf":2.0},"350":{"tf":1.4142135623730951},"410":{"tf":1.0},"411":{"tf":1.0},"416":{"tf":1.4142135623730951},"505":{"tf":1.0},"519":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"778":{"tf":1.0},"992":{"tf":1.4142135623730951}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":3,"docs":{"350":{"tf":1.0},"46":{"tf":1.0},"51":{"tf":1.0}}}}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"976":{"tf":1.0}}}}}}}}}},"u":{"df":0,"docs":{},"m":{"df":20,"docs":{"208":{"tf":1.4142135623730951},"22":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.0},"280":{"tf":1.0},"284":{"tf":1.0},"288":{"tf":1.0},"439":{"tf":1.0},"517":{"tf":1.7320508075688772},"520":{"tf":1.7320508075688772},"522":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"602":{"tf":1.0},"61":{"tf":1.0},"633":{"tf":1.4142135623730951},"668":{"tf":2.0},"7":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.0},"879":{"tf":2.23606797749979}},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"522":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"522":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}}}}},"df":5,"docs":{"522":{"tf":2.23606797749979},"524":{"tf":1.0},"525":{"tf":1.0},"668":{"tf":1.0},"735":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":2,"docs":{"346":{"tf":1.7320508075688772},"885":{"tf":1.0}},"e":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":1,"docs":{"347":{"tf":1.0}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"142":{"tf":1.0},"26":{"tf":1.4142135623730951},"362":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}}}}},"s":{"df":4,"docs":{"203":{"tf":1.0},"216":{"tf":1.0},"48":{"tf":1.0},"54":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"843":{"tf":1.0}}}}}},"o":{"c":{"df":0,"docs":{},"h":{"'":{"df":7,"docs":{"323":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.7320508075688772},"349":{"tf":1.0}}},"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"348":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"342":{"tf":1.4142135623730951}}}}}}}}},"df":18,"docs":{"322":{"tf":1.0},"335":{"tf":1.7320508075688772},"336":{"tf":1.0},"338":{"tf":1.4142135623730951},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":2.23606797749979},"344":{"tf":3.0},"345":{"tf":3.3166247903554},"346":{"tf":3.4641016151377544},"347":{"tf":2.0},"348":{"tf":1.7320508075688772},"349":{"tf":2.0},"350":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":2.0},"722":{"tf":1.0}}}},"df":0,"docs":{}}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":29,"docs":{"205":{"tf":3.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"221":{"tf":1.0},"252":{"tf":1.7320508075688772},"253":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.0},"439":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"569":{"tf":1.0},"575":{"tf":1.0},"636":{"tf":1.0},"735":{"tf":2.0},"739":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"777":{"tf":1.0},"829":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.7320508075688772},"895":{"tf":1.0}}},"t":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"723":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"776":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"205":{"tf":1.0},"485":{"tf":1.0},"5":{"tf":1.4142135623730951},"609":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.0}}}},"df":0,"docs":{},"o":{"c":{"df":2,"docs":{"372":{"tf":1.0},"721":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"r":{"a":{"df":8,"docs":{"375":{"tf":1.0},"517":{"tf":1.0},"568":{"tf":2.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.0},"571":{"tf":1.0},"931":{"tf":1.4142135623730951},"932":{"tf":2.6457513110645907}},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"931":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"s":{"df":1,"docs":{"833":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":7,"docs":{"430":{"tf":1.0},"435":{"tf":2.23606797749979},"436":{"tf":1.7320508075688772},"437":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"444":{"tf":1.0},"634":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"634":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"c":{"2":{"0":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":173,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.4142135623730951},"1002":{"tf":1.4142135623730951},"1007":{"tf":1.0},"1009":{"tf":1.4142135623730951},"101":{"tf":1.4142135623730951},"1011":{"tf":1.4142135623730951},"103":{"tf":1.4142135623730951},"106":{"tf":1.4142135623730951},"116":{"tf":1.4142135623730951},"118":{"tf":1.4142135623730951},"12":{"tf":1.4142135623730951},"122":{"tf":1.4142135623730951},"129":{"tf":1.4142135623730951},"131":{"tf":1.4142135623730951},"136":{"tf":1.4142135623730951},"143":{"tf":1.4142135623730951},"145":{"tf":1.4142135623730951},"150":{"tf":1.4142135623730951},"157":{"tf":1.4142135623730951},"159":{"tf":1.4142135623730951},"164":{"tf":1.4142135623730951},"17":{"tf":1.4142135623730951},"175":{"tf":1.4142135623730951},"177":{"tf":1.4142135623730951},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.4142135623730951},"191":{"tf":1.4142135623730951},"195":{"tf":1.0},"210":{"tf":1.4142135623730951},"215":{"tf":1.0},"224":{"tf":1.4142135623730951},"229":{"tf":1.4142135623730951},"238":{"tf":1.4142135623730951},"240":{"tf":1.4142135623730951},"247":{"tf":1.4142135623730951},"256":{"tf":1.4142135623730951},"258":{"tf":1.4142135623730951},"268":{"tf":1.0},"276":{"tf":1.4142135623730951},"279":{"tf":1.4142135623730951},"287":{"tf":1.4142135623730951},"289":{"tf":1.7320508075688772},"294":{"tf":1.0},"306":{"tf":1.4142135623730951},"31":{"tf":1.4142135623730951},"311":{"tf":1.0},"318":{"tf":1.4142135623730951},"322":{"tf":1.4142135623730951},"33":{"tf":1.4142135623730951},"355":{"tf":1.4142135623730951},"357":{"tf":1.4142135623730951},"366":{"tf":1.4142135623730951},"379":{"tf":1.4142135623730951},"381":{"tf":1.7320508075688772},"386":{"tf":1.4142135623730951},"393":{"tf":1.4142135623730951},"395":{"tf":1.4142135623730951},"400":{"tf":1.4142135623730951},"405":{"tf":1.4142135623730951},"407":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"421":{"tf":1.4142135623730951},"423":{"tf":1.4142135623730951},"430":{"tf":1.4142135623730951},"443":{"tf":1.4142135623730951},"445":{"tf":1.4142135623730951},"451":{"tf":1.4142135623730951},"456":{"tf":1.0},"458":{"tf":1.4142135623730951},"460":{"tf":1.4142135623730951},"465":{"tf":1.4142135623730951},"475":{"tf":1.4142135623730951},"477":{"tf":1.4142135623730951},"481":{"tf":1.4142135623730951},"488":{"tf":1.4142135623730951},"490":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"506":{"tf":1.4142135623730951},"508":{"tf":1.4142135623730951},"513":{"tf":1.4142135623730951},"529":{"tf":1.4142135623730951},"531":{"tf":1.4142135623730951},"535":{"tf":1.4142135623730951},"542":{"tf":1.4142135623730951},"544":{"tf":1.4142135623730951},"549":{"tf":1.4142135623730951},"556":{"tf":1.4142135623730951},"558":{"tf":1.4142135623730951},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"579":{"tf":1.4142135623730951},"581":{"tf":1.7320508075688772},"584":{"tf":1.4142135623730951},"591":{"tf":1.4142135623730951},"593":{"tf":1.4142135623730951},"598":{"tf":1.4142135623730951},"606":{"tf":1.4142135623730951},"608":{"tf":1.4142135623730951},"613":{"tf":1.4142135623730951},"620":{"tf":1.4142135623730951},"622":{"tf":1.7320508075688772},"627":{"tf":1.0},"641":{"tf":1.4142135623730951},"649":{"tf":1.4142135623730951},"657":{"tf":1.4142135623730951},"659":{"tf":1.4142135623730951},"663":{"tf":1.4142135623730951},"664":{"tf":1.4142135623730951},"671":{"tf":1.4142135623730951},"673":{"tf":1.4142135623730951},"678":{"tf":1.4142135623730951},"685":{"tf":1.4142135623730951},"687":{"tf":1.7320508075688772},"692":{"tf":1.4142135623730951},"70":{"tf":1.4142135623730951},"700":{"tf":1.0},"702":{"tf":1.4142135623730951},"704":{"tf":1.7320508075688772},"709":{"tf":1.0},"72":{"tf":1.4142135623730951},"725":{"tf":1.4142135623730951},"757":{"tf":1.4142135623730951},"764":{"tf":1.4142135623730951},"766":{"tf":1.4142135623730951},"782":{"tf":1.4142135623730951},"789":{"tf":1.4142135623730951},"79":{"tf":1.4142135623730951},"791":{"tf":1.7320508075688772},"795":{"tf":1.4142135623730951},"8":{"tf":1.0},"802":{"tf":1.4142135623730951},"804":{"tf":1.4142135623730951},"808":{"tf":1.4142135623730951},"820":{"tf":1.4142135623730951},"822":{"tf":1.4142135623730951},"827":{"tf":1.4142135623730951},"834":{"tf":1.4142135623730951},"836":{"tf":1.4142135623730951},"841":{"tf":1.4142135623730951},"851":{"tf":1.4142135623730951},"853":{"tf":1.4142135623730951},"857":{"tf":1.4142135623730951},"86":{"tf":1.4142135623730951},"865":{"tf":1.4142135623730951},"867":{"tf":1.4142135623730951},"871":{"tf":1.4142135623730951},"88":{"tf":1.4142135623730951},"884":{"tf":1.4142135623730951},"886":{"tf":1.7320508075688772},"891":{"tf":1.4142135623730951},"901":{"tf":1.4142135623730951},"903":{"tf":1.7320508075688772},"908":{"tf":1.4142135623730951},"918":{"tf":1.4142135623730951},"920":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.4142135623730951},"93":{"tf":1.4142135623730951},"936":{"tf":1.7320508075688772},"940":{"tf":1.4142135623730951},"950":{"tf":1.4142135623730951},"952":{"tf":1.4142135623730951},"957":{"tf":1.4142135623730951},"967":{"tf":1.4142135623730951},"969":{"tf":1.4142135623730951},"974":{"tf":1.4142135623730951},"981":{"tf":1.4142135623730951},"983":{"tf":1.7320508075688772},"988":{"tf":1.4142135623730951},"995":{"tf":1.4142135623730951},"997":{"tf":1.4142135623730951}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":12,"docs":{"440":{"tf":1.0},"497":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":4.242640687119285},"833":{"tf":1.0},"879":{"tf":4.123105625617661},"881":{"tf":1.4142135623730951},"895":{"tf":1.0},"898":{"tf":1.4142135623730951},"941":{"tf":1.0},"944":{"tf":1.0},"952":{"tf":1.0}}}}}},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"723":{"tf":1.0},"777":{"tf":1.0},"810":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"56":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":11,"docs":{"124":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"372":{"tf":1.0},"507":{"tf":1.0},"577":{"tf":1.0},"60":{"tf":1.0},"72":{"tf":1.0},"749":{"tf":1.0},"803":{"tf":1.0},"880":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"567":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"201":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":6,"docs":{"24":{"tf":1.4142135623730951},"371":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0},"575":{"tf":1.0},"720":{"tf":1.0}}}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":10,"docs":{"28":{"tf":1.0},"722":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":1.0},"847":{"tf":1.7320508075688772},"912":{"tf":1.0},"961":{"tf":1.0}}}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"436":{"tf":1.0},"570":{"tf":1.0}}}}}},"t":{"a":{"_":{"3":{"df":2,"docs":{"46":{"tf":1.0},"51":{"tf":1.0}}},"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"u":{"df":1,"docs":{"723":{"tf":1.4142135623730951}}},"v":{"df":1,"docs":{"723":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"c":{"df":14,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"18":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"376":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"522":{"tf":1.0},"534":{"tf":1.4142135623730951},"761":{"tf":1.0},"804":{"tf":1.0},"855":{"tf":1.0}}},"df":0,"docs":{},"h":{"df":5,"docs":{"39":{"tf":1.4142135623730951},"48":{"tf":1.0},"50":{"tf":1.0},"52":{"tf":1.0},"699":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"46":{"tf":1.0}}},"df":22,"docs":{"364":{"tf":1.0},"38":{"tf":2.6457513110645907},"39":{"tf":1.4142135623730951},"40":{"tf":1.0},"41":{"tf":1.0},"42":{"tf":1.0},"43":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.4142135623730951},"53":{"tf":1.4142135623730951},"54":{"tf":1.0},"55":{"tf":1.4142135623730951},"583":{"tf":1.0},"697":{"tf":1.4142135623730951},"699":{"tf":1.4142135623730951}},"’":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}}}}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":2,"docs":{"1004":{"tf":1.0},"246":{"tf":1.0}}}},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"270":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"745":{"tf":1.0}}}}},"n":{"df":42,"docs":{"155":{"tf":1.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"385":{"tf":1.0},"437":{"tf":1.0},"500":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"565":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"659":{"tf":1.0},"693":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":2.6457513110645907},"761":{"tf":1.4142135623730951},"763":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":1.0},"81":{"tf":1.0},"818":{"tf":1.4142135623730951},"837":{"tf":1.4142135623730951},"874":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0},"990":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"430":{"tf":1.0},"432":{"tf":1.0}}}},"t":{"df":13,"docs":{"374":{"tf":1.0},"450":{"tf":1.0},"453":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":2.23606797749979},"72":{"tf":1.0},"799":{"tf":1.4142135623730951},"832":{"tf":1.4142135623730951},"912":{"tf":1.0},"928":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.0},"952":{"tf":1.0}},"u":{"df":6,"docs":{"169":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.4142135623730951},"282":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"249":{"tf":1.0},"528":{"tf":1.0},"570":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":4,"docs":{"499":{"tf":1.0},"840":{"tf":1.0},"848":{"tf":1.0},"933":{"tf":1.0}}}}}}},"i":{"d":{"df":1,"docs":{"913":{"tf":1.0}}},"df":0,"docs":{}},"m":{"df":2,"docs":{"959":{"tf":1.0},"971":{"tf":1.0}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":1,"docs":{"373":{"tf":1.0}}}}}},"x":{"a":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"293":{"tf":1.0},"402":{"tf":1.0},"62":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"784":{"tf":1.0},"874":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.0},"207":{"tf":1.0},"303":{"tf":1.0},"732":{"tf":1.0},"878":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"147":{"tf":1.0},"33":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":71,"docs":{"1014":{"tf":1.0},"155":{"tf":1.4142135623730951},"169":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"303":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.4142135623730951},"375":{"tf":1.0},"376":{"tf":1.0},"384":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"517":{"tf":1.0},"521":{"tf":1.4142135623730951},"523":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.4142135623730951},"575":{"tf":1.0},"586":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":1.4142135623730951},"633":{"tf":1.7320508075688772},"649":{"tf":1.0},"650":{"tf":1.0},"654":{"tf":1.4142135623730951},"692":{"tf":1.0},"694":{"tf":1.4142135623730951},"697":{"tf":1.0},"699":{"tf":1.4142135623730951},"727":{"tf":1.0},"732":{"tf":1.4142135623730951},"741":{"tf":1.0},"752":{"tf":2.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"847":{"tf":1.0},"876":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"933":{"tf":1.7320508075688772},"95":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0},"996":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"df":10,"docs":{"111":{"tf":1.0},"47":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"879":{"tf":2.6457513110645907}},"e":{"d":{"df":2,"docs":{"30":{"tf":1.0},"990":{"tf":1.0}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"t":{"df":11,"docs":{"205":{"tf":1.0},"331":{"tf":1.0},"45":{"tf":1.0},"499":{"tf":1.0},"711":{"tf":1.0},"718":{"tf":1.0},"725":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0},"759":{"tf":1.7320508075688772},"8":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"429":{"tf":1.0}}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":5,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"565":{"tf":1.0}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"l":{"df":0,"docs":{},"u":{"d":{"df":2,"docs":{"722":{"tf":1.4142135623730951},"735":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"84":{"tf":1.0},"917":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":57,"docs":{"138":{"tf":1.0},"148":{"tf":1.0},"151":{"tf":1.4142135623730951},"17":{"tf":1.0},"22":{"tf":1.4142135623730951},"23":{"tf":1.7320508075688772},"25":{"tf":1.0},"26":{"tf":2.449489742783178},"291":{"tf":1.0},"344":{"tf":2.23606797749979},"346":{"tf":1.0},"352":{"tf":1.0},"368":{"tf":1.4142135623730951},"402":{"tf":1.4142135623730951},"404":{"tf":1.0},"521":{"tf":1.4142135623730951},"564":{"tf":1.0},"6":{"tf":2.0},"600":{"tf":2.23606797749979},"602":{"tf":2.8284271247461903},"603":{"tf":2.23606797749979},"605":{"tf":1.4142135623730951},"615":{"tf":1.4142135623730951},"619":{"tf":1.7320508075688772},"634":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.4142135623730951},"653":{"tf":2.23606797749979},"654":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":2.23606797749979},"665":{"tf":1.4142135623730951},"666":{"tf":1.0},"667":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"670":{"tf":1.0},"671":{"tf":1.0},"672":{"tf":1.0},"673":{"tf":1.0},"674":{"tf":1.0},"675":{"tf":1.0},"676":{"tf":1.0},"677":{"tf":1.0},"694":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":3.7416573867739413},"876":{"tf":1.0},"878":{"tf":2.23606797749979},"879":{"tf":2.23606797749979},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"890":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.7320508075688772},"962":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":3,"docs":{"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"885":{"tf":1.0}}}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}},"y":{"(":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"17":{"tf":1.0},"23":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":2.449489742783178},"666":{"tf":1.0},"705":{"tf":1.0}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"773":{"tf":1.0}}}}},"h":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"1007":{"tf":1.0},"180":{"tf":1.0},"340":{"tf":1.0},"648":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":117,"docs":{"1012":{"tf":1.0},"113":{"tf":1.0},"118":{"tf":1.0},"119":{"tf":1.0},"132":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.4142135623730951},"148":{"tf":1.4142135623730951},"152":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"178":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":2.449489742783178},"208":{"tf":1.0},"216":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.7320508075688772},"241":{"tf":1.0},"246":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"268":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"273":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"317":{"tf":1.0},"319":{"tf":1.0},"32":{"tf":1.0},"34":{"tf":1.0},"367":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"393":{"tf":1.0},"40":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.0},"453":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.0},"483":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"518":{"tf":1.0},"55":{"tf":1.0},"559":{"tf":1.4142135623730951},"564":{"tf":1.0},"568":{"tf":1.0},"575":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":2.23606797749979},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"606":{"tf":1.0},"609":{"tf":1.4142135623730951},"618":{"tf":1.0},"631":{"tf":1.0},"64":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"659":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"714":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"74":{"tf":1.4142135623730951},"757":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"768":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.7320508075688772},"786":{"tf":1.0},"80":{"tf":1.0},"810":{"tf":1.0},"829":{"tf":1.0},"842":{"tf":1.0},"867":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"875":{"tf":2.23606797749979},"879":{"tf":4.47213595499958},"88":{"tf":1.0},"881":{"tf":1.4142135623730951},"887":{"tf":1.4142135623730951},"900":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.7320508075688772},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"936":{"tf":1.0},"938":{"tf":1.0},"944":{"tf":1.0},"949":{"tf":1.0},"953":{"tf":1.4142135623730951},"961":{"tf":1.4142135623730951},"966":{"tf":1.0},"970":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"975":{"tf":1.0},"980":{"tf":1.0},"984":{"tf":1.0},"994":{"tf":1.0}}}},"t":{"df":7,"docs":{"130":{"tf":1.0},"39":{"tf":1.4142135623730951},"40":{"tf":1.0},"42":{"tf":1.0},"52":{"tf":1.0},"55":{"tf":1.0},"577":{"tf":1.0}}}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"569":{"tf":1.0}}}}}},"p":{"a":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"40":{"tf":1.4142135623730951},"847":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":49,"docs":{"124":{"tf":1.0},"130":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.7320508075688772},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"232":{"tf":1.4142135623730951},"254":{"tf":1.4142135623730951},"255":{"tf":1.0},"273":{"tf":1.0},"276":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.4142135623730951},"375":{"tf":1.0},"435":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"485":{"tf":1.0},"515":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"563":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"656":{"tf":1.0},"717":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.4142135623730951},"725":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.4142135623730951},"776":{"tf":1.0},"81":{"tf":1.0},"835":{"tf":1.0},"852":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":1.0},"898":{"tf":1.0},"932":{"tf":1.0},"942":{"tf":1.0},"951":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"351":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"50":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"196":{"tf":1.0},"200":{"tf":1.0}}}}}}},"df":0,"docs":{},"s":{"df":7,"docs":{"108":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.0},"296":{"tf":1.0},"575":{"tf":1.0},"725":{"tf":1.0},"863":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":17,"docs":{"1007":{"tf":1.0},"118":{"tf":1.0},"17":{"tf":1.0},"29":{"tf":1.4142135623730951},"290":{"tf":1.0},"306":{"tf":1.0},"33":{"tf":1.0},"371":{"tf":1.0},"40":{"tf":1.0},"423":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"700":{"tf":1.0},"784":{"tf":1.4142135623730951},"799":{"tf":1.0},"8":{"tf":1.0},"928":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"199":{"tf":1.0},"778":{"tf":1.0},"843":{"tf":1.0},"928":{"tf":1.0}}}}}}},"t":{"df":2,"docs":{"53":{"tf":1.4142135623730951},"939":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"r":{"df":5,"docs":{"203":{"tf":1.0},"205":{"tf":1.0},"302":{"tf":1.0},"944":{"tf":1.4142135623730951},"947":{"tf":1.0}},"e":{"_":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}}},"df":0,"docs":{}},"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"s":{"(":{"3":{"6":{"df":0,"docs":{},"h":{"df":1,"docs":{"551":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":3,"docs":{"198":{"tf":1.0},"880":{"tf":1.0},"890":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":7,"docs":{"204":{"tf":1.0},"417":{"tf":1.0},"455":{"tf":1.4142135623730951},"467":{"tf":1.0},"485":{"tf":1.0},"519":{"tf":1.0},"874":{"tf":1.0}}}},"n":{"df":126,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1006":{"tf":2.0},"106":{"tf":1.0},"110":{"tf":1.4142135623730951},"122":{"tf":1.0},"126":{"tf":1.4142135623730951},"136":{"tf":1.0},"140":{"tf":1.4142135623730951},"150":{"tf":1.0},"154":{"tf":1.4142135623730951},"164":{"tf":1.0},"168":{"tf":1.4142135623730951},"17":{"tf":1.0},"182":{"tf":1.0},"186":{"tf":1.4142135623730951},"195":{"tf":1.0},"202":{"tf":1.4142135623730951},"21":{"tf":1.4142135623730951},"215":{"tf":1.0},"220":{"tf":1.4142135623730951},"229":{"tf":1.0},"234":{"tf":1.4142135623730951},"247":{"tf":1.0},"251":{"tf":1.4142135623730951},"255":{"tf":1.0},"263":{"tf":1.0},"267":{"tf":1.4142135623730951},"268":{"tf":1.0},"272":{"tf":1.4142135623730951},"279":{"tf":1.0},"283":{"tf":1.4142135623730951},"294":{"tf":1.0},"299":{"tf":1.4142135623730951},"311":{"tf":1.0},"315":{"tf":1.4142135623730951},"340":{"tf":1.4142135623730951},"366":{"tf":1.0},"370":{"tf":1.4142135623730951},"386":{"tf":1.0},"390":{"tf":1.4142135623730951},"400":{"tf":1.0},"404":{"tf":1.4142135623730951},"410":{"tf":1.0},"415":{"tf":1.4142135623730951},"430":{"tf":1.0},"434":{"tf":1.4142135623730951},"451":{"tf":1.0},"455":{"tf":1.4142135623730951},"465":{"tf":1.0},"469":{"tf":1.4142135623730951},"481":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"495":{"tf":1.0},"499":{"tf":1.4142135623730951},"5":{"tf":1.4142135623730951},"505":{"tf":1.0},"513":{"tf":1.0},"519":{"tf":1.4142135623730951},"535":{"tf":1.0},"539":{"tf":1.7320508075688772},"549":{"tf":1.0},"553":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.4142135623730951},"584":{"tf":1.0},"588":{"tf":1.4142135623730951},"598":{"tf":1.0},"60":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"613":{"tf":1.0},"617":{"tf":1.4142135623730951},"627":{"tf":1.0},"631":{"tf":1.4142135623730951},"649":{"tf":1.0},"653":{"tf":1.4142135623730951},"664":{"tf":1.0},"668":{"tf":1.4142135623730951},"678":{"tf":1.0},"682":{"tf":1.4142135623730951},"692":{"tf":1.0},"696":{"tf":1.4142135623730951},"709":{"tf":1.0},"719":{"tf":1.4142135623730951},"730":{"tf":1.0},"734":{"tf":1.4142135623730951},"735":{"tf":1.0},"741":{"tf":1.0},"746":{"tf":1.4142135623730951},"757":{"tf":1.0},"761":{"tf":1.4142135623730951},"771":{"tf":1.0},"775":{"tf":1.4142135623730951},"776":{"tf":1.0},"782":{"tf":1.0},"786":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"799":{"tf":1.4142135623730951},"808":{"tf":1.0},"813":{"tf":1.4142135623730951},"827":{"tf":1.0},"83":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"841":{"tf":1.0},"845":{"tf":1.4142135623730951},"857":{"tf":1.0},"860":{"tf":1.4142135623730951},"871":{"tf":1.0},"878":{"tf":1.4142135623730951},"891":{"tf":1.0},"898":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"930":{"tf":1.4142135623730951},"940":{"tf":1.0},"944":{"tf":1.4142135623730951},"957":{"tf":1.0},"961":{"tf":1.4142135623730951},"97":{"tf":1.4142135623730951},"974":{"tf":1.0},"978":{"tf":1.4142135623730951},"988":{"tf":1.0},"992":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"655":{"tf":1.0},"878":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"222":{"tf":1.0},"295":{"tf":1.0},"302":{"tf":1.0},"345":{"tf":1.0},"440":{"tf":1.0},"51":{"tf":1.0},"609":{"tf":1.0},"698":{"tf":1.0}}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":4,"docs":{"127":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0}}}},"r":{"df":11,"docs":{"1015":{"tf":1.0},"152":{"tf":1.4142135623730951},"28":{"tf":1.0},"340":{"tf":1.0},"369":{"tf":1.0},"388":{"tf":1.0},"630":{"tf":1.0},"810":{"tf":1.0},"938":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0}}},"s":{"df":1,"docs":{"779":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"428":{"tf":1.0},"749":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"t":{"df":5,"docs":{"23":{"tf":1.0},"25":{"tf":1.0},"45":{"tf":1.4142135623730951},"455":{"tf":1.0},"725":{"tf":1.0}}}},"s":{"df":24,"docs":{"1009":{"tf":1.0},"1011":{"tf":1.0},"131":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"33":{"tf":1.0},"362":{"tf":1.7320508075688772},"379":{"tf":1.0},"395":{"tf":1.0},"404":{"tf":1.0},"514":{"tf":1.0},"606":{"tf":1.0},"634":{"tf":1.0},"736":{"tf":1.0},"773":{"tf":1.0},"814":{"tf":1.0},"902":{"tf":1.0},"917":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"573":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":11,"docs":{"269":{"tf":1.0},"270":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"414":{"tf":1.0},"522":{"tf":2.0},"568":{"tf":1.0},"576":{"tf":1.0},"735":{"tf":1.7320508075688772},"780":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"85":{"tf":1.0}}}}}}}}},"t":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":2,"docs":{"732":{"tf":1.4142135623730951},"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"_":{"*":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"d":{"2":{"5":{"5":{"1":{"9":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"p":{"2":{"5":{"6":{"df":0,"docs":{},"k":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"r":{"2":{"5":{"5":{"1":{"9":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"4":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"_":{"1":{"2":{"8":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"1":{"2":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"h":{"a":{"2":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"_":{"1":{"2":{"8":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"5":{"6":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"732":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"4":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"83":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"/":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"_":{"df":1,"docs":{"739":{"tf":1.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"a":{"d":{"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"w":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}}},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"739":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}},"s":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"p":{"2":{"5":{"6":{"df":0,"docs":{},"r":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"97":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"736":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":3,"docs":{"739":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"1":{"df":1,"docs":{"404":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"2":{"df":1,"docs":{"735":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":1,"docs":{"739":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"2":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"_":{"2":{"5":{"6":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"3":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":16,"docs":{"126":{"tf":1.0},"156":{"tf":1.0},"19":{"tf":1.0},"248":{"tf":1.0},"38":{"tf":1.0},"496":{"tf":1.0},"521":{"tf":1.0},"537":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"586":{"tf":1.4142135623730951},"631":{"tf":1.0},"778":{"tf":1.0},"942":{"tf":1.0},"966":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":43,"docs":{"124":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":2.449489742783178},"17":{"tf":1.0},"170":{"tf":3.0},"171":{"tf":3.4641016151377544},"177":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.4142135623730951},"24":{"tf":4.242640687119285},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"289":{"tf":1.0},"30":{"tf":1.0},"308":{"tf":1.0},"340":{"tf":1.0},"442":{"tf":1.0},"516":{"tf":1.0},"518":{"tf":1.0},"521":{"tf":2.8284271247461903},"537":{"tf":2.23606797749979},"563":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":2.0},"584":{"tf":2.23606797749979},"585":{"tf":1.4142135623730951},"586":{"tf":3.0},"587":{"tf":1.0},"588":{"tf":2.8284271247461903},"589":{"tf":1.0},"590":{"tf":1.0},"591":{"tf":1.4142135623730951},"592":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"648":{"tf":1.0},"780":{"tf":1.0},"83":{"tf":1.0},"939":{"tf":1.0},"945":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{">":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{">":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"24":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"24":{"tf":1.0}}}}}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":2,"docs":{"170":{"tf":1.0},"171":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":2,"docs":{"22":{"tf":1.0},"24":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":2.6457513110645907}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"t":{"df":2,"docs":{"648":{"tf":1.0},"913":{"tf":1.0}}}},"r":{"df":0,"docs":{},"n":{"df":10,"docs":{"211":{"tf":1.0},"25":{"tf":1.4142135623730951},"267":{"tf":1.0},"315":{"tf":1.0},"429":{"tf":1.0},"438":{"tf":1.0},"49":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"956":{"tf":1.0},"973":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":4,"docs":{"333":{"tf":1.0},"350":{"tf":1.4142135623730951},"418":{"tf":1.0},"485":{"tf":1.0}}}},"df":25,"docs":{"152":{"tf":1.0},"166":{"tf":1.0},"249":{"tf":1.4142135623730951},"340":{"tf":1.0},"341":{"tf":2.6457513110645907},"346":{"tf":2.0},"347":{"tf":1.0},"516":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"634":{"tf":1.0},"651":{"tf":1.0},"700":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.4142135623730951},"803":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":2,"docs":{"751":{"tf":1.4142135623730951},"778":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":74,"docs":{"164":{"tf":2.449489742783178},"165":{"tf":1.4142135623730951},"166":{"tf":2.23606797749979},"167":{"tf":1.0},"168":{"tf":1.0},"169":{"tf":2.0},"170":{"tf":2.8284271247461903},"171":{"tf":1.4142135623730951},"172":{"tf":2.449489742783178},"173":{"tf":1.4142135623730951},"174":{"tf":1.0},"175":{"tf":1.4142135623730951},"176":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.4142135623730951},"179":{"tf":1.4142135623730951},"18":{"tf":1.0},"180":{"tf":1.7320508075688772},"181":{"tf":1.7320508075688772},"24":{"tf":1.0},"284":{"tf":1.4142135623730951},"346":{"tf":1.0},"362":{"tf":1.0},"387":{"tf":1.4142135623730951},"388":{"tf":3.4641016151377544},"390":{"tf":2.23606797749979},"402":{"tf":1.7320508075688772},"440":{"tf":1.0},"45":{"tf":2.449489742783178},"513":{"tf":1.7320508075688772},"516":{"tf":1.7320508075688772},"517":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"520":{"tf":1.0},"521":{"tf":3.605551275463989},"522":{"tf":1.7320508075688772},"523":{"tf":2.449489742783178},"526":{"tf":2.6457513110645907},"535":{"tf":2.449489742783178},"536":{"tf":1.4142135623730951},"537":{"tf":3.1622776601683795},"538":{"tf":1.0},"539":{"tf":2.8284271247461903},"540":{"tf":1.4142135623730951},"541":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.4142135623730951},"545":{"tf":1.4142135623730951},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.4142135623730951},"570":{"tf":1.0},"573":{"tf":1.4142135623730951},"585":{"tf":1.0},"586":{"tf":2.23606797749979},"588":{"tf":2.23606797749979},"594":{"tf":1.4142135623730951},"61":{"tf":1.0},"799":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.23606797749979},"895":{"tf":1.0},"898":{"tf":1.0}},"i":{"c":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"170":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"284":{"tf":2.23606797749979},"292":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":5,"docs":{"180":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.0},"523":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}},"f":{"+":{"1":{"df":3,"docs":{"436":{"tf":1.0},"717":{"tf":1.4142135623730951},"722":{"tf":2.0}}},"df":0,"docs":{}},"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"a":{"c":{"a":{"d":{"df":1,"docs":{"3":{"tf":1.0}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"782":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":4,"docs":{"231":{"tf":1.0},"569":{"tf":1.0},"723":{"tf":1.0},"913":{"tf":1.0}},"t":{"df":1,"docs":{"95":{"tf":1.0}}}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"78":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":18,"docs":{"137":{"tf":1.0},"19":{"tf":1.0},"200":{"tf":1.4142135623730951},"205":{"tf":1.0},"326":{"tf":1.0},"33":{"tf":1.0},"363":{"tf":1.0},"414":{"tf":1.0},"776":{"tf":1.0},"83":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"849":{"tf":1.4142135623730951},"855":{"tf":1.0},"87":{"tf":1.0},"872":{"tf":1.0},"959":{"tf":1.0},"969":{"tf":1.0}}}}}},"t":{"df":8,"docs":{"15":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0},"559":{"tf":1.0},"577":{"tf":1.0},"722":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0}},"o":{"df":3,"docs":{"600":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0}},"r":{"(":{"(":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"207":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"207":{"tf":1.0}}}},"df":17,"docs":{"207":{"tf":2.6457513110645907},"221":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"469":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.4142135623730951},"81":{"tf":1.0},"928":{"tf":1.0},"95":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":20,"docs":{"125":{"tf":1.0},"126":{"tf":2.449489742783178},"160":{"tf":1.0},"347":{"tf":1.0},"436":{"tf":1.0},"461":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"609":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"653":{"tf":1.0},"75":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"879":{"tf":2.0},"898":{"tf":1.7320508075688772},"913":{"tf":1.0},"934":{"tf":1.0},"947":{"tf":1.0}},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"126":{"tf":1.0},"615":{"tf":1.0},"735":{"tf":3.1622776601683795}}}}},"r":{"df":4,"docs":{"432":{"tf":1.0},"575":{"tf":1.0},"772":{"tf":1.4142135623730951},"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"431":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":1,"docs":{"514":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"348":{"tf":1.0},"349":{"tf":1.0},"436":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":4,"docs":{"207":{"tf":1.0},"437":{"tf":1.4142135623730951},"615":{"tf":1.0},"747":{"tf":1.0}}},"s":{"df":5,"docs":{"698":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"761":{"tf":2.0},"97":{"tf":1.0}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":5,"docs":{"261":{"tf":1.0},"456":{"tf":1.0},"511":{"tf":1.0},"53":{"tf":1.0},"569":{"tf":1.0}}}},"df":2,"docs":{"783":{"tf":1.0},"876":{"tf":1.0}}}}}},"r":{"df":11,"docs":{"170":{"tf":1.0},"180":{"tf":1.0},"199":{"tf":1.0},"267":{"tf":1.0},"285":{"tf":1.0},"374":{"tf":1.0},"58":{"tf":1.0},"711":{"tf":1.4142135623730951},"715":{"tf":1.0},"854":{"tf":1.0},"880":{"tf":1.4142135623730951}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"200":{"tf":1.0},"281":{"tf":1.0},"374":{"tf":1.0}}}}}},"t":{"df":2,"docs":{"370":{"tf":1.0},"39":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"551":{"tf":1.0},"574":{"tf":1.0},"711":{"tf":1.0},"739":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"880":{"tf":2.0},"912":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"564":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"213":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"264":{"tf":1.0},"428":{"tf":1.0},"668":{"tf":1.0},"680":{"tf":1.0},"723":{"tf":1.0},"770":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"432":{"tf":1.0},"660":{"tf":1.0}}}}}}},"df":3,"docs":{"112":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951}},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"234":{"tf":1.0}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"781":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"254":{"tf":1.0},"573":{"tf":1.0},"762":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":56,"docs":{"154":{"tf":1.0},"160":{"tf":1.4142135623730951},"166":{"tf":1.0},"18":{"tf":1.4142135623730951},"210":{"tf":1.0},"22":{"tf":1.0},"281":{"tf":1.0},"376":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":2.0},"446":{"tf":1.0},"515":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"56":{"tf":2.0},"564":{"tf":1.0},"57":{"tf":1.0},"58":{"tf":1.0},"59":{"tf":1.0},"60":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"644":{"tf":2.0},"65":{"tf":1.0},"66":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"70":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0},"74":{"tf":1.4142135623730951},"75":{"tf":1.0},"76":{"tf":1.0},"77":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"833":{"tf":1.0},"847":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0},"856":{"tf":1.4142135623730951},"941":{"tf":1.0},"944":{"tf":1.4142135623730951},"945":{"tf":1.0},"95":{"tf":1.0},"951":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"990":{"tf":1.0}}}}}},"b":{"df":1,"docs":{"891":{"tf":1.0}},"r":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"513":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0}}}}},"df":0,"docs":{}}}},"d":{"df":1,"docs":{"933":{"tf":1.0}}},"df":0,"docs":{},"e":{"d":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":10,"docs":{"206":{"tf":1.0},"229":{"tf":1.0},"244":{"tf":1.4142135623730951},"272":{"tf":1.0},"797":{"tf":1.4142135623730951},"846":{"tf":1.0},"870":{"tf":1.0},"878":{"tf":1.0},"952":{"tf":1.0},"973":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":50,"docs":{"18":{"tf":1.4142135623730951},"267":{"tf":1.0},"48":{"tf":1.4142135623730951},"534":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"576":{"tf":2.449489742783178},"6":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.7320508075688772},"605":{"tf":1.0},"649":{"tf":2.23606797749979},"650":{"tf":2.8284271247461903},"651":{"tf":3.4641016151377544},"652":{"tf":1.0},"653":{"tf":3.605551275463989},"654":{"tf":1.0},"655":{"tf":1.0},"656":{"tf":1.4142135623730951},"657":{"tf":1.0},"658":{"tf":1.4142135623730951},"659":{"tf":1.4142135623730951},"660":{"tf":1.4142135623730951},"661":{"tf":1.0},"662":{"tf":1.0},"663":{"tf":1.4142135623730951},"666":{"tf":1.0},"696":{"tf":1.0},"78":{"tf":1.0},"797":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"912":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0},"974":{"tf":2.0},"975":{"tf":1.7320508075688772},"976":{"tf":2.0},"977":{"tf":1.0},"978":{"tf":1.4142135623730951},"979":{"tf":1.0},"980":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0},"985":{"tf":1.0},"986":{"tf":1.0},"987":{"tf":1.7320508075688772}},"l":{"df":5,"docs":{"390":{"tf":1.0},"397":{"tf":1.0},"720":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.4142135623730951}}},"s":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"974":{"tf":1.0},"975":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}},"o":{"df":0,"docs":{},"w":{"df":6,"docs":{"113":{"tf":1.0},"219":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"582":{"tf":1.0},"935":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"c":{"df":1,"docs":{"0":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"9":{"df":1,"docs":{"388":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"4":{"df":1,"docs":{"840":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"m":{"df":5,"docs":{"661":{"tf":1.0},"665":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"985":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"(":{"df":1,"docs":{"270":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"849":{"tf":1.0}}}}}}}}}},"df":53,"docs":{"0":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"109":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.4142135623730951},"193":{"tf":1.0},"201":{"tf":1.0},"269":{"tf":1.4142135623730951},"270":{"tf":2.0},"271":{"tf":1.0},"272":{"tf":2.0},"273":{"tf":2.0},"277":{"tf":1.0},"3":{"tf":1.0},"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.4142135623730951},"316":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"389":{"tf":1.0},"465":{"tf":2.23606797749979},"466":{"tf":1.4142135623730951},"467":{"tf":1.7320508075688772},"468":{"tf":1.4142135623730951},"469":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.4142135623730951},"472":{"tf":1.0},"473":{"tf":1.0},"474":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"479":{"tf":1.4142135623730951},"480":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"727":{"tf":1.0},"774":{"tf":1.0},"798":{"tf":1.0},"801":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"850":{"tf":1.0},"932":{"tf":1.0},"985":{"tf":1.0}}}}}}}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":17,"docs":{"191":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"47":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":2.23606797749979},"64":{"tf":1.0},"65":{"tf":1.4142135623730951},"67":{"tf":1.7320508075688772},"69":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"w":{"df":12,"docs":{"257":{"tf":1.0},"331":{"tf":1.0},"418":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"517":{"tf":1.0},"565":{"tf":1.4142135623730951},"569":{"tf":1.0},"729":{"tf":1.0},"759":{"tf":1.0},"797":{"tf":1.0},"832":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"346":{"tf":1.0},"912":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"o":{"df":1,"docs":{"95":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":44,"docs":{"180":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.4142135623730951},"221":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.7320508075688772},"331":{"tf":1.0},"346":{"tf":1.0},"387":{"tf":1.4142135623730951},"439":{"tf":1.0},"501":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":3.1622776601683795},"553":{"tf":1.0},"555":{"tf":1.0},"559":{"tf":1.4142135623730951},"6":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.7320508075688772},"633":{"tf":1.0},"634":{"tf":2.6457513110645907},"635":{"tf":1.7320508075688772},"636":{"tf":1.4142135623730951},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.4142135623730951},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.7320508075688772},"717":{"tf":1.0},"761":{"tf":2.0},"895":{"tf":2.6457513110645907},"9":{"tf":1.0}}},"df":0,"docs":{}}},"f":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"221":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"199":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"282":{"tf":1.0}}},"l":{"df":4,"docs":{"204":{"tf":1.0},"234":{"tf":1.4142135623730951},"346":{"tf":1.0},"632":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":7,"docs":{"24":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"697":{"tf":1.0},"698":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"890":{"tf":1.0}}}}}},"n":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"a":{"c":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"524":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":41,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.4142135623730951},"130":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":3.605551275463989},"211":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"45":{"tf":1.0},"500":{"tf":2.8284271247461903},"519":{"tf":1.0},"523":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"64":{"tf":1.0},"67":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":2.0},"716":{"tf":1.7320508075688772},"721":{"tf":1.4142135623730951},"725":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"209":{"tf":1.0}}}}},"n":{"c":{"df":3,"docs":{"316":{"tf":1.0},"876":{"tf":1.0},"973":{"tf":1.0}},"i":{"df":4,"docs":{"412":{"tf":1.0},"429":{"tf":1.0},"810":{"tf":1.0},"876":{"tf":1.0}}}},"df":0,"docs":{}}},"d":{"df":17,"docs":{"199":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"435":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"516":{"tf":1.4142135623730951},"553":{"tf":1.7320508075688772},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"743":{"tf":1.0},"858":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":7,"docs":{"428":{"tf":1.0},"440":{"tf":1.0},"567":{"tf":1.0},"645":{"tf":1.0},"773":{"tf":1.0},"848":{"tf":1.0},"874":{"tf":1.4142135623730951}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":17,"docs":{"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.7320508075688772},"895":{"tf":2.6457513110645907},"896":{"tf":2.0},"897":{"tf":1.7320508075688772},"898":{"tf":2.449489742783178},"899":{"tf":1.0},"900":{"tf":1.4142135623730951},"901":{"tf":1.0},"902":{"tf":1.4142135623730951},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.0}}}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":8,"docs":{"124":{"tf":1.0},"126":{"tf":1.0},"155":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"735":{"tf":1.0},"777":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"t":{"df":2,"docs":{"199":{"tf":1.0},"517":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":67,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.7320508075688772},"158":{"tf":1.0},"208":{"tf":2.23606797749979},"222":{"tf":1.0},"257":{"tf":1.0},"284":{"tf":1.0},"297":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"343":{"tf":1.4142135623730951},"344":{"tf":2.0},"345":{"tf":2.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"348":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"412":{"tf":1.0},"432":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.4142135623730951},"453":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.4142135623730951},"499":{"tf":1.0},"516":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"537":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"567":{"tf":1.4142135623730951},"571":{"tf":1.0},"576":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.7320508075688772},"63":{"tf":1.0},"632":{"tf":1.0},"64":{"tf":1.0},"643":{"tf":1.0},"668":{"tf":1.0},"67":{"tf":1.0},"697":{"tf":1.4142135623730951},"71":{"tf":1.0},"716":{"tf":1.0},"720":{"tf":1.4142135623730951},"735":{"tf":1.0},"75":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"879":{"tf":1.0},"912":{"tf":1.4142135623730951},"931":{"tf":1.0},"933":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"t":{"df":5,"docs":{"108":{"tf":1.0},"517":{"tf":1.0},"564":{"tf":1.0},"615":{"tf":1.0},"735":{"tf":2.449489742783178}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"235":{"tf":1.0}}}},"x":{"df":17,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"234":{"tf":2.0},"332":{"tf":1.4142135623730951},"438":{"tf":1.0},"500":{"tf":1.0},"522":{"tf":1.4142135623730951},"564":{"tf":1.0},"575":{"tf":1.0},"711":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":2.0}},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"l":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"709":{"tf":1.0},"729":{"tf":2.0},"761":{"tf":1.0},"831":{"tf":1.4142135623730951}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"485":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"635":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"29":{"tf":1.0}}}},"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":31,"docs":{"137":{"tf":1.0},"138":{"tf":1.0},"141":{"tf":1.0},"147":{"tf":1.0},"207":{"tf":1.0},"373":{"tf":1.0},"427":{"tf":1.4142135623730951},"537":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"61":{"tf":1.0},"651":{"tf":1.0},"773":{"tf":1.0},"926":{"tf":2.0},"927":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"930":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.0},"934":{"tf":1.0},"935":{"tf":1.0},"936":{"tf":1.0},"937":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.7320508075688772},"942":{"tf":1.0},"95":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0}}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"374":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"554":{"tf":1.0}}}}},"p":{"df":1,"docs":{"749":{"tf":1.0}}}},"o":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"346":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}}},"w":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":5,"docs":{"17":{"tf":1.0},"26":{"tf":1.4142135623730951},"267":{"tf":1.0},"618":{"tf":1.0},"983":{"tf":1.0}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"429":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"n":{"df":17,"docs":{"22":{"tf":1.4142135623730951},"221":{"tf":2.0},"222":{"tf":1.4142135623730951},"23":{"tf":1.0},"24":{"tf":2.449489742783178},"25":{"tf":1.4142135623730951},"284":{"tf":1.0},"341":{"tf":2.6457513110645907},"404":{"tf":1.0},"438":{"tf":1.0},"455":{"tf":1.4142135623730951},"524":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"879":{"tf":3.3166247903554},"885":{"tf":1.7320508075688772},"97":{"tf":1.0}}},"o":{"c":{"df":0,"docs":{},"u":{"df":4,"docs":{"363":{"tf":1.0},"40":{"tf":1.0},"469":{"tf":1.0},"725":{"tf":1.0}},"s":{"df":5,"docs":{"16":{"tf":1.0},"325":{"tf":1.0},"45":{"tf":1.0},"564":{"tf":1.0},"818":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":91,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"126":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.7320508075688772},"181":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"25":{"tf":1.0},"26":{"tf":1.0},"267":{"tf":1.4142135623730951},"272":{"tf":1.0},"300":{"tf":1.4142135623730951},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"333":{"tf":1.0},"341":{"tf":1.4142135623730951},"345":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.7320508075688772},"352":{"tf":1.0},"356":{"tf":1.0},"370":{"tf":1.0},"375":{"tf":1.0},"404":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"428":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.4142135623730951},"450":{"tf":1.0},"47":{"tf":1.4142135623730951},"49":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"524":{"tf":1.0},"528":{"tf":1.4142135623730951},"537":{"tf":1.0},"539":{"tf":1.4142135623730951},"548":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"588":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":2.449489742783178},"605":{"tf":1.4142135623730951},"62":{"tf":1.4142135623730951},"63":{"tf":1.0},"632":{"tf":1.0},"636":{"tf":1.0},"668":{"tf":1.0},"694":{"tf":1.0},"705":{"tf":1.0},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"736":{"tf":1.4142135623730951},"739":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.4142135623730951},"786":{"tf":1.0},"799":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"831":{"tf":1.4142135623730951},"840":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"860":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.0},"885":{"tf":1.4142135623730951},"912":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"944":{"tf":1.0},"961":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"107":{"tf":1.0}}}}}}}},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}}},"t":{"df":1,"docs":{"874":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"412":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.4142135623730951}}}}}}}}},"r":{"c":{"df":13,"docs":{"199":{"tf":1.0},"267":{"tf":1.0},"388":{"tf":1.0},"485":{"tf":1.0},"573":{"tf":1.4142135623730951},"599":{"tf":1.0},"606":{"tf":1.0},"614":{"tf":1.0},"63":{"tf":1.0},"670":{"tf":1.0},"773":{"tf":2.449489742783178},"776":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":1,"docs":{"420":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"x":{"df":1,"docs":{"600":{"tf":1.0}}}}}}}},"df":3,"docs":{"3":{"tf":1.0},"6":{"tf":1.0},"603":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":1,"docs":{"800":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"47":{"tf":1.4142135623730951},"51":{"tf":1.0}}}}},"k":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"253":{"tf":1.4142135623730951},"254":{"tf":1.0}}},"df":0,"docs":{}}},"df":10,"docs":{"253":{"tf":1.0},"254":{"tf":1.0},"323":{"tf":1.0},"347":{"tf":1.0},"356":{"tf":1.7320508075688772},"39":{"tf":1.0},"450":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"721":{"tf":1.7320508075688772},"724":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"515":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"209":{"tf":1.0},"844":{"tf":1.4142135623730951}}},"t":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"3":{"7":{"df":1,"docs":{"665":{"tf":1.0}}},"df":0,"docs":{}},"5":{"3":{"df":1,"docs":{"661":{"tf":1.0}}},"7":{"df":1,"docs":{"985":{"tf":1.0}}},"8":{"df":1,"docs":{"689":{"tf":1.0}}},"9":{"df":1,"docs":{"675":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":61,"docs":{"12":{"tf":1.4142135623730951},"164":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.4142135623730951},"172":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"3":{"tf":1.0},"333":{"tf":1.0},"369":{"tf":1.0},"37":{"tf":1.0},"39":{"tf":1.0},"455":{"tf":1.0},"482":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"491":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"516":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.4142135623730951},"526":{"tf":1.0},"535":{"tf":2.23606797749979},"536":{"tf":1.4142135623730951},"537":{"tf":2.0},"538":{"tf":1.0},"539":{"tf":1.4142135623730951},"540":{"tf":1.4142135623730951},"541":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.4142135623730951},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.0},"553":{"tf":1.0},"585":{"tf":1.0},"586":{"tf":1.4142135623730951},"588":{"tf":2.0},"594":{"tf":1.4142135623730951},"634":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"646":{"tf":1.4142135623730951},"661":{"tf":1.0},"675":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"848":{"tf":1.0},"985":{"tf":1.0}}}},"df":19,"docs":{"12":{"tf":1.0},"206":{"tf":1.0},"221":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"45":{"tf":1.0},"565":{"tf":1.0},"629":{"tf":1.0},"697":{"tf":1.0},"717":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"759":{"tf":1.0},"786":{"tf":1.4142135623730951},"815":{"tf":1.0},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"291":{"tf":1.0},"842":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"'":{"df":1,"docs":{"934":{"tf":1.0}}},"df":4,"docs":{"207":{"tf":1.0},"346":{"tf":1.0},"415":{"tf":1.0},"934":{"tf":1.0}}},"df":1,"docs":{"939":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"417":{"tf":1.0}}},"u":{"df":0,"docs":{},"n":{"df":1,"docs":{"51":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"m":{"df":7,"docs":{"120":{"tf":1.4142135623730951},"243":{"tf":1.0},"277":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"646":{"tf":1.0},"756":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":14,"docs":{"126":{"tf":1.0},"483":{"tf":1.0},"570":{"tf":1.0},"602":{"tf":1.0},"61":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"780":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.4142135623730951},"850":{"tf":1.0},"931":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"411":{"tf":1.0},"973":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"211":{"tf":1.0},"324":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0}}}},"df":22,"docs":{"151":{"tf":1.0},"154":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"331":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.0},"343":{"tf":1.4142135623730951},"350":{"tf":1.0},"352":{"tf":1.0},"414":{"tf":1.0},"501":{"tf":1.0},"520":{"tf":2.0},"521":{"tf":1.4142135623730951},"537":{"tf":1.0},"553":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.0},"898":{"tf":1.0},"933":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":3,"docs":{"335":{"tf":1.0},"344":{"tf":1.0},"711":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"221":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"573":{"tf":1.0}}}}}},"{":{"\\":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":2,"docs":{"390":{"tf":1.0},"397":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":13,"docs":{"234":{"tf":1.0},"254":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.0},"515":{"tf":2.23606797749979},"519":{"tf":2.23606797749979},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":1.7320508075688772},"526":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":7,"docs":{"180":{"tf":1.0},"203":{"tf":1.4142135623730951},"514":{"tf":1.0},"771":{"tf":1.0},"773":{"tf":1.4142135623730951},"949":{"tf":1.0},"991":{"tf":1.0}}}}}}}},"n":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":3,"docs":{"649":{"tf":1.0},"664":{"tf":1.0},"974":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"u":{"d":{"df":3,"docs":{"388":{"tf":2.0},"39":{"tf":2.0},"55":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"605":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":11,"docs":{"198":{"tf":1.0},"205":{"tf":1.4142135623730951},"300":{"tf":1.0},"375":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.7320508075688772},"619":{"tf":2.0},"651":{"tf":1.0},"732":{"tf":1.7320508075688772},"807":{"tf":1.0},"835":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"52":{"tf":1.0},"942":{"tf":1.0}}}},"z":{"df":1,"docs":{"573":{"tf":1.0}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":3,"docs":{"356":{"tf":1.0},"797":{"tf":1.0},"814":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":10,"docs":{"267":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"427":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"58":{"tf":1.0},"63":{"tf":1.0},"724":{"tf":1.0},"814":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"352":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":2,"docs":{"204":{"tf":1.0},"352":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"724":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"19":{"tf":1.0},"423":{"tf":1.0},"942":{"tf":1.0}}}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":4,"docs":{"22":{"tf":1.0},"35":{"tf":1.0},"576":{"tf":1.0},"843":{"tf":1.0}}}},"z":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"780":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":6,"docs":{"288":{"tf":1.0},"303":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"939":{"tf":1.0}}}}},"l":{"df":26,"docs":{"136":{"tf":1.0},"144":{"tf":1.0},"205":{"tf":1.7320508075688772},"218":{"tf":1.0},"248":{"tf":1.7320508075688772},"249":{"tf":1.0},"252":{"tf":1.4142135623730951},"257":{"tf":2.23606797749979},"29":{"tf":1.0},"388":{"tf":1.7320508075688772},"46":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"47":{"tf":1.0},"48":{"tf":1.0},"507":{"tf":1.4142135623730951},"522":{"tf":1.0},"553":{"tf":1.4142135623730951},"64":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"759":{"tf":2.23606797749979},"77":{"tf":1.0},"776":{"tf":1.0},"931":{"tf":1.0}},"i":{"df":14,"docs":{"119":{"tf":1.0},"204":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"307":{"tf":1.0},"47":{"tf":1.7320508075688772},"51":{"tf":1.0},"515":{"tf":1.0},"60":{"tf":1.0},"642":{"tf":1.0},"72":{"tf":1.0},"75":{"tf":1.0},"878":{"tf":1.0},"984":{"tf":1.0}}}}},"n":{"c":{"df":2,"docs":{"735":{"tf":7.0},"736":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"428":{"tf":1.0}}},"df":134,"docs":{"100":{"tf":1.4142135623730951},"1004":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.4142135623730951},"105":{"tf":1.4142135623730951},"111":{"tf":1.4142135623730951},"13":{"tf":1.0},"163":{"tf":1.4142135623730951},"169":{"tf":1.0},"171":{"tf":1.0},"173":{"tf":1.0},"195":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":2.0},"207":{"tf":1.0},"21":{"tf":1.4142135623730951},"217":{"tf":1.0},"22":{"tf":1.0},"221":{"tf":1.0},"23":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":2.0},"25":{"tf":1.7320508075688772},"252":{"tf":1.4142135623730951},"26":{"tf":2.0},"267":{"tf":1.0},"276":{"tf":1.0},"284":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.0},"32":{"tf":1.0},"322":{"tf":1.0},"334":{"tf":1.7320508075688772},"35":{"tf":2.0},"362":{"tf":1.0},"366":{"tf":1.4142135623730951},"371":{"tf":1.0},"373":{"tf":2.449489742783178},"374":{"tf":1.7320508075688772},"375":{"tf":1.7320508075688772},"379":{"tf":1.0},"38":{"tf":1.4142135623730951},"400":{"tf":2.23606797749979},"401":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.7320508075688772},"404":{"tf":2.449489742783178},"405":{"tf":1.0},"406":{"tf":1.4142135623730951},"407":{"tf":1.7320508075688772},"408":{"tf":1.4142135623730951},"409":{"tf":1.4142135623730951},"410":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.0},"424":{"tf":1.0},"426":{"tf":1.0},"428":{"tf":2.449489742783178},"430":{"tf":1.0},"438":{"tf":2.8284271247461903},"440":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"50":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"521":{"tf":1.4142135623730951},"525":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"553":{"tf":1.0},"606":{"tf":1.0},"639":{"tf":1.0},"699":{"tf":1.4142135623730951},"730":{"tf":1.0},"732":{"tf":2.0},"735":{"tf":7.3484692283495345},"736":{"tf":2.23606797749979},"738":{"tf":1.0},"739":{"tf":1.7320508075688772},"740":{"tf":1.0},"741":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":2.0},"748":{"tf":1.4142135623730951},"749":{"tf":2.449489742783178},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"799":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"849":{"tf":1.0},"860":{"tf":1.4142135623730951},"867":{"tf":1.0},"871":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":3.4641016151377544},"928":{"tf":1.0},"93":{"tf":2.23606797749979},"932":{"tf":1.4142135623730951},"938":{"tf":1.0},"94":{"tf":2.0},"942":{"tf":2.0},"944":{"tf":1.4142135623730951},"945":{"tf":1.4142135623730951},"947":{"tf":1.0},"949":{"tf":1.0},"95":{"tf":2.0},"952":{"tf":1.0},"953":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"96":{"tf":1.0},"964":{"tf":1.0},"966":{"tf":1.0},"969":{"tf":1.0},"97":{"tf":2.0},"970":{"tf":1.0},"975":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}},"s":{"/":{"1":{"0":{"4":{"5":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"d":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"261":{"tf":1.0},"511":{"tf":1.0}}}}}}},"df":21,"docs":{"121":{"tf":1.0},"184":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"234":{"tf":1.0},"236":{"tf":1.0},"267":{"tf":1.4142135623730951},"273":{"tf":1.0},"316":{"tf":1.7320508075688772},"619":{"tf":1.0},"660":{"tf":1.0},"694":{"tf":1.0},"777":{"tf":1.0},"80":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"869":{"tf":1.0},"874":{"tf":1.4142135623730951},"876":{"tf":1.0},"976":{"tf":1.0}}},"df":2,"docs":{"603":{"tf":1.4142135623730951},"7":{"tf":1.0}},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":9,"docs":{"2":{"tf":1.4142135623730951},"203":{"tf":1.0},"3":{"tf":1.7320508075688772},"373":{"tf":1.4142135623730951},"376":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":2.23606797749979},"7":{"tf":1.0},"9":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"2":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":39,"docs":{"108":{"tf":1.0},"152":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"267":{"tf":1.0},"281":{"tf":1.0},"285":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"335":{"tf":1.0},"347":{"tf":1.0},"388":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"416":{"tf":1.7320508075688772},"436":{"tf":1.0},"452":{"tf":1.0},"56":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"583":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"638":{"tf":1.0},"651":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"77":{"tf":1.7320508075688772},"771":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.4142135623730951},"906":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"938":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":8,"docs":{"128":{"tf":1.0},"154":{"tf":1.0},"200":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.4142135623730951},"505":{"tf":1.0},"602":{"tf":1.0},"732":{"tf":1.0}}}}}}}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":142,"docs":{"1":{"tf":1.0},"1001":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1015":{"tf":1.7320508075688772},"108":{"tf":1.0},"111":{"tf":1.0},"122":{"tf":1.0},"124":{"tf":1.0},"135":{"tf":1.4142135623730951},"136":{"tf":1.0},"149":{"tf":1.4142135623730951},"150":{"tf":1.0},"16":{"tf":1.7320508075688772},"163":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.7320508075688772},"182":{"tf":1.0},"194":{"tf":1.4142135623730951},"195":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.4142135623730951},"215":{"tf":1.0},"220":{"tf":1.0},"226":{"tf":1.4142135623730951},"229":{"tf":1.0},"246":{"tf":1.7320508075688772},"247":{"tf":1.0},"254":{"tf":1.0},"262":{"tf":1.7320508075688772},"279":{"tf":1.0},"281":{"tf":1.0},"289":{"tf":1.0},"293":{"tf":1.7320508075688772},"294":{"tf":1.0},"310":{"tf":2.0},"311":{"tf":1.0},"316":{"tf":1.0},"321":{"tf":1.4142135623730951},"322":{"tf":1.0},"361":{"tf":1.7320508075688772},"363":{"tf":1.0},"364":{"tf":1.0},"366":{"tf":1.0},"37":{"tf":1.4142135623730951},"372":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.4142135623730951},"386":{"tf":1.0},"399":{"tf":1.7320508075688772},"412":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"430":{"tf":1.0},"441":{"tf":1.0},"449":{"tf":1.7320508075688772},"451":{"tf":1.0},"464":{"tf":1.4142135623730951},"473":{"tf":1.0},"481":{"tf":1.0},"494":{"tf":1.4142135623730951},"495":{"tf":1.0},"500":{"tf":1.0},"512":{"tf":1.4142135623730951},"513":{"tf":1.0},"520":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.4142135623730951},"545":{"tf":1.0},"548":{"tf":1.7320508075688772},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.4142135623730951},"584":{"tf":1.0},"597":{"tf":1.4142135623730951},"598":{"tf":1.0},"612":{"tf":1.4142135623730951},"613":{"tf":1.0},"626":{"tf":1.4142135623730951},"627":{"tf":1.0},"634":{"tf":1.0},"648":{"tf":2.0},"649":{"tf":1.0},"663":{"tf":1.4142135623730951},"664":{"tf":1.0},"677":{"tf":1.4142135623730951},"678":{"tf":1.0},"691":{"tf":1.4142135623730951},"692":{"tf":1.0},"708":{"tf":1.4142135623730951},"709":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"728":{"tf":1.4142135623730951},"730":{"tf":1.0},"740":{"tf":1.7320508075688772},"741":{"tf":1.0},"751":{"tf":1.0},"755":{"tf":1.4142135623730951},"757":{"tf":1.0},"76":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"774":{"tf":1.0},"776":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.4142135623730951},"808":{"tf":1.0},"812":{"tf":1.0},"826":{"tf":1.4142135623730951},"827":{"tf":1.0},"840":{"tf":1.4142135623730951},"871":{"tf":1.0},"880":{"tf":1.0},"890":{"tf":1.4142135623730951},"891":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":1.0},"911":{"tf":1.0},"913":{"tf":1.0},"92":{"tf":1.4142135623730951},"925":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.4142135623730951},"940":{"tf":1.0},"956":{"tf":1.4142135623730951},"957":{"tf":1.0},"973":{"tf":1.4142135623730951},"974":{"tf":1.0},"987":{"tf":1.4142135623730951},"988":{"tf":1.0}}}}},"z":{"df":0,"docs":{},"z":{"df":1,"docs":{"211":{"tf":1.0}}}}}},"g":{"a":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"782":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":3,"docs":{"715":{"tf":1.0},"716":{"tf":1.0},"725":{"tf":1.0}}}}}},"df":7,"docs":{"29":{"tf":1.4142135623730951},"30":{"tf":1.0},"38":{"tf":1.0},"51":{"tf":2.449489742783178},"54":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":8,"docs":{"144":{"tf":1.0},"33":{"tf":1.0},"416":{"tf":1.0},"417":{"tf":1.0},"577":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.0},"835":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"322":{"tf":1.0}}}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"e":{"df":5,"docs":{"124":{"tf":1.0},"230":{"tf":1.0},"63":{"tf":1.0},"710":{"tf":1.0},"777":{"tf":1.0}}},"m":{"a":{"\\":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.0},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"_":{"df":0,"docs":{},"{":{"df":0,"docs":{},"u":{",":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"w":{",":{"df":0,"docs":{},"v":{"df":2,"docs":{"722":{"tf":1.7320508075688772},"723":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"p":{"df":1,"docs":{"500":{"tf":1.4142135623730951}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"121":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"g":{"df":1,"docs":{"564":{"tf":1.0}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"195":{"tf":1.0},"215":{"tf":1.0},"366":{"tf":1.0},"465":{"tf":1.0},"807":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"722":{"tf":1.0}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"263":{"tf":1.0},"563":{"tf":1.0},"771":{"tf":1.0}}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"452":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":95,"docs":{"155":{"tf":1.0},"164":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.7320508075688772},"170":{"tf":1.4142135623730951},"171":{"tf":1.7320508075688772},"172":{"tf":1.0},"184":{"tf":1.4142135623730951},"199":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"217":{"tf":1.0},"24":{"tf":1.4142135623730951},"255":{"tf":1.0},"257":{"tf":1.4142135623730951},"264":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"276":{"tf":1.7320508075688772},"296":{"tf":1.0},"310":{"tf":1.0},"327":{"tf":1.0},"336":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.7320508075688772},"368":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.0},"451":{"tf":2.23606797749979},"452":{"tf":1.4142135623730951},"453":{"tf":1.0},"454":{"tf":1.0},"455":{"tf":1.0},"456":{"tf":1.0},"457":{"tf":1.4142135623730951},"458":{"tf":1.0},"459":{"tf":1.4142135623730951},"460":{"tf":1.4142135623730951},"461":{"tf":1.4142135623730951},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.0},"469":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"513":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"524":{"tf":1.7320508075688772},"526":{"tf":1.7320508075688772},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"534":{"tf":1.7320508075688772},"535":{"tf":2.0},"536":{"tf":1.4142135623730951},"537":{"tf":1.7320508075688772},"538":{"tf":1.0},"539":{"tf":1.0},"540":{"tf":1.0},"541":{"tf":1.0},"542":{"tf":1.4142135623730951},"543":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.4142135623730951},"56":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.0},"588":{"tf":1.7320508075688772},"634":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"665":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"71":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"78":{"tf":2.0},"798":{"tf":1.0},"83":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":1.4142135623730951},"938":{"tf":1.0},"987":{"tf":1.0},"992":{"tf":1.0}}},"s":{"df":0,"docs":{},"i":{"df":16,"docs":{"249":{"tf":1.0},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"303":{"tf":1.7320508075688772},"345":{"tf":2.23606797749979},"348":{"tf":1.0},"362":{"tf":1.0},"371":{"tf":1.4142135623730951},"375":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":2.0},"502":{"tf":1.4142135623730951},"52":{"tf":1.0},"521":{"tf":1.0},"526":{"tf":1.0},"680":{"tf":1.0}},"s":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{">":{"/":{"df":0,"docs":{},"k":{"a":{"d":{"df":1,"docs":{"503":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"253":{"tf":1.0},"254":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"814":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"345":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":2,"docs":{"164":{"tf":1.0},"535":{"tf":1.0}}}}},"t":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"350":{"tf":1.0}}}}}}}},"df":1,"docs":{"333":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"349":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}},"<":{"b":{"a":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"<":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"438":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":24,"docs":{"121":{"tf":1.0},"154":{"tf":1.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"441":{"tf":1.0},"450":{"tf":2.0},"455":{"tf":1.0},"514":{"tf":1.4142135623730951},"528":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"697":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"78":{"tf":1.0},"817":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.4142135623730951},"875":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.4142135623730951},"912":{"tf":1.0},"933":{"tf":1.0}}}},"g":{"df":0,"docs":{},"w":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"938":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"549":{"tf":1.0}}}}}}}},"i":{"b":{"df":4,"docs":{"735":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.4142135623730951},"990":{"tf":1.0}}},"df":0,"docs":{},"g":{"a":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":2,"docs":{"990":{"tf":1.0},"996":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":5,"docs":{"243":{"tf":1.4142135623730951},"249":{"tf":1.0},"272":{"tf":1.0},"826":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":18,"docs":{"178":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"208":{"tf":1.0},"347":{"tf":1.0},"376":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"567":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0},"784":{"tf":1.0}},"n":{"df":51,"docs":{"1007":{"tf":1.0},"124":{"tf":1.0},"173":{"tf":1.0},"205":{"tf":1.7320508075688772},"221":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"253":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"273":{"tf":1.4142135623730951},"274":{"tf":1.0},"30":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":2.23606797749979},"375":{"tf":1.0},"376":{"tf":1.0},"427":{"tf":1.0},"439":{"tf":1.0},"467":{"tf":1.0},"507":{"tf":1.0},"516":{"tf":1.4142135623730951},"522":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"602":{"tf":1.0},"633":{"tf":1.0},"635":{"tf":1.0},"64":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.0},"735":{"tf":2.8284271247461903},"739":{"tf":1.4142135623730951},"744":{"tf":1.0},"761":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.0},"885":{"tf":1.4142135623730951},"928":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"o":{"b":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":1,"docs":{"786":{"tf":1.0}},"s":{"(":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"m":{"a":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}}}},"df":3,"docs":{"44":{"tf":1.0},"522":{"tf":1.0},"831":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"729":{"tf":1.0}},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"729":{"tf":1.0}}}}}}}}}},"n":{"df":0,"docs":{},"u":{"df":1,"docs":{"894":{"tf":1.0}}}},"o":{"a":{"df":0,"docs":{},"l":{"df":10,"docs":{"111":{"tf":1.0},"208":{"tf":1.0},"295":{"tf":1.0},"346":{"tf":1.0},"467":{"tf":1.0},"49":{"tf":1.0},"54":{"tf":1.0},"565":{"tf":1.0},"829":{"tf":1.0},"934":{"tf":1.0}}}},"df":28,"docs":{"126":{"tf":1.0},"148":{"tf":1.0},"214":{"tf":1.0},"296":{"tf":1.0},"310":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.0},"455":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.4142135623730951},"659":{"tf":1.0},"679":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"718":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"77":{"tf":1.4142135623730951},"807":{"tf":1.0},"831":{"tf":1.0},"849":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"928":{"tf":1.0},"954":{"tf":1.0}},"e":{"df":3,"docs":{"207":{"tf":1.4142135623730951},"532":{"tf":1.0},"933":{"tf":1.0}}},"o":{"d":{"df":21,"docs":{"126":{"tf":1.0},"133":{"tf":1.0},"156":{"tf":1.0},"187":{"tf":1.0},"231":{"tf":1.0},"250":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.0},"370":{"tf":1.0},"511":{"tf":1.0},"574":{"tf":1.0},"651":{"tf":1.0},"710":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":1.0},"732":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"849":{"tf":1.0},"894":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":2,"docs":{"482":{"tf":1.0},"500":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"v":{"1":{"df":1,"docs":{"371":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"742":{"tf":1.0}}},"r":{"df":0,"docs":{},"n":{"df":66,"docs":{"108":{"tf":1.7320508075688772},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"137":{"tf":1.4142135623730951},"138":{"tf":2.0},"139":{"tf":1.0},"140":{"tf":2.0},"141":{"tf":1.0},"142":{"tf":1.7320508075688772},"144":{"tf":1.0},"145":{"tf":1.4142135623730951},"146":{"tf":1.0},"147":{"tf":1.7320508075688772},"148":{"tf":1.0},"185":{"tf":1.0},"191":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"209":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.7320508075688772},"236":{"tf":1.0},"237":{"tf":1.0},"273":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"301":{"tf":1.4142135623730951},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":2.0},"375":{"tf":3.0},"376":{"tf":2.23606797749979},"384":{"tf":1.0},"385":{"tf":1.0},"410":{"tf":1.0},"420":{"tf":1.0},"427":{"tf":1.7320508075688772},"438":{"tf":1.0},"440":{"tf":1.4142135623730951},"446":{"tf":1.0},"564":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.7320508075688772},"720":{"tf":1.0},"729":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"744":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"797":{"tf":1.0},"804":{"tf":1.0},"811":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"853":{"tf":1.0},"876":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951},"932":{"tf":1.0},"934":{"tf":1.0}}}}}}},"p":{"df":1,"docs":{"45":{"tf":1.0}},"g":{"df":5,"docs":{"894":{"tf":1.0},"895":{"tf":1.0},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.4142135623730951}}}},"r":{"a":{"d":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"427":{"tf":1.0},"428":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"874":{"tf":1.4142135623730951}}}},"n":{"d":{"df":0,"docs":{},"p":{"a":{"df":2,"docs":{"45":{"tf":1.0},"500":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":6,"docs":{"440":{"tf":1.0},"776":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"85":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"h":{"df":2,"docs":{"213":{"tf":1.0},"571":{"tf":1.7320508075688772}}}},"y":{"df":2,"docs":{"39":{"tf":1.0},"44":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"928":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"114":{"tf":1.0},"517":{"tf":1.0},"807":{"tf":1.4142135623730951},"819":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":9,"docs":{"184":{"tf":1.0},"187":{"tf":1.0},"205":{"tf":1.0},"221":{"tf":1.0},"326":{"tf":1.0},"347":{"tf":1.0},"84":{"tf":1.0},"879":{"tf":2.23606797749979},"956":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"565":{"tf":1.0},"600":{"tf":1.0},"663":{"tf":1.0},"712":{"tf":1.0},"77":{"tf":1.0},"797":{"tf":1.0}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":2,"docs":{"577":{"tf":1.0},"628":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"466":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":2,"docs":{"326":{"tf":1.0},"361":{"tf":1.0}}}}}}},"df":0,"docs":{}},"p":{"df":16,"docs":{"211":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"240":{"tf":1.0},"269":{"tf":1.4142135623730951},"270":{"tf":1.4142135623730951},"272":{"tf":1.0},"368":{"tf":1.4142135623730951},"373":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"376":{"tf":1.0},"436":{"tf":1.0},"44":{"tf":1.0},"629":{"tf":1.0},"759":{"tf":1.0},"844":{"tf":1.0}}}},"w":{"df":1,"docs":{"744":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":7,"docs":{"416":{"tf":1.0},"418":{"tf":1.4142135623730951},"428":{"tf":1.0},"54":{"tf":1.0},"742":{"tf":1.0},"752":{"tf":1.0},"973":{"tf":1.0}}}}}}},"u":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":10,"docs":{"124":{"tf":1.0},"203":{"tf":1.0},"231":{"tf":1.0},"342":{"tf":1.0},"368":{"tf":1.4142135623730951},"45":{"tf":1.0},"576":{"tf":1.0},"602":{"tf":1.0},"609":{"tf":1.0},"78":{"tf":1.0}},"e":{"d":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"/":{"a":{"df":0,"docs":{},"u":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"46":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"d":{"df":1,"docs":{"894":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"615":{"tf":1.0}}}}}}}},"df":3,"docs":{"615":{"tf":1.0},"73":{"tf":1.0},"75":{"tf":1.0}}},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"28":{"tf":1.0},"30":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"h":{"(":{"df":0,"docs":{},"{":{"\\":{"b":{"df":0,"docs":{},"f":{"df":2,"docs":{"45":{"tf":2.449489742783178},"47":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"r":{"df":1,"docs":{"46":{"tf":1.0}}}},"a":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":3,"docs":{"214":{"tf":1.0},"215":{"tf":1.0},"244":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"780":{"tf":1.0}}}}}}},"l":{"df":0,"docs":{},"f":{"df":4,"docs":{"208":{"tf":1.4142135623730951},"515":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0}}},"t":{"df":4,"docs":{"108":{"tf":1.0},"151":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0}}},"v":{"df":2,"docs":{"444":{"tf":1.0},"567":{"tf":1.0}}}},"n":{"d":{"df":5,"docs":{"316":{"tf":1.0},"440":{"tf":1.0},"471":{"tf":1.0},"515":{"tf":1.0},"936":{"tf":1.0}},"l":{"df":29,"docs":{"111":{"tf":1.0},"112":{"tf":1.7320508075688772},"114":{"tf":1.0},"141":{"tf":1.0},"148":{"tf":1.0},"237":{"tf":1.0},"241":{"tf":1.0},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"375":{"tf":1.4142135623730951},"517":{"tf":1.0},"52":{"tf":1.0},"537":{"tf":1.0},"56":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"600":{"tf":1.0},"602":{"tf":2.0},"62":{"tf":1.4142135623730951},"65":{"tf":1.4142135623730951},"650":{"tf":1.7320508075688772},"651":{"tf":1.0},"729":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"887":{"tf":1.0},"912":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.4142135623730951},"975":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"602":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":30,"docs":{"126":{"tf":1.0},"127":{"tf":1.0},"142":{"tf":1.0},"152":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"450":{"tf":1.0},"459":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.0},"606":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.4142135623730951},"735":{"tf":1.0},"739":{"tf":1.0},"765":{"tf":1.0},"777":{"tf":1.0},"833":{"tf":1.0},"846":{"tf":1.0},"849":{"tf":1.0},"879":{"tf":1.4142135623730951},"927":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.7320508075688772}}}}}},"r":{"d":{"c":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"140":{"tf":1.0},"175":{"tf":1.0}}},"df":0,"docs":{}}},"df":8,"docs":{"537":{"tf":1.0},"573":{"tf":1.0},"615":{"tf":1.0},"669":{"tf":1.0},"724":{"tf":1.0},"850":{"tf":1.0},"874":{"tf":1.0},"928":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"56":{"tf":1.0},"77":{"tf":1.4142135623730951}}},"r":{"df":2,"docs":{"1004":{"tf":1.0},"73":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"402":{"tf":1.0},"515":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"729":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"df":3,"docs":{"505":{"tf":1.0},"565":{"tf":1.0},"720":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"565":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"776":{"tf":1.0}},"i":{"df":1,"docs":{"771":{"tf":1.0}}}}}}},"s":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"879":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},">":{"/":{"df":0,"docs":{},"k":{"a":{"d":{"/":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"502":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"502":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":53,"docs":{"113":{"tf":1.0},"163":{"tf":1.0},"171":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"248":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"333":{"tf":1.0},"345":{"tf":1.4142135623730951},"349":{"tf":1.0},"39":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":2.23606797749979},"450":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"501":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":2.23606797749979},"52":{"tf":1.7320508075688772},"520":{"tf":3.1622776601683795},"521":{"tf":1.4142135623730951},"525":{"tf":2.449489742783178},"526":{"tf":3.605551275463989},"528":{"tf":2.23606797749979},"530":{"tf":1.0},"531":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.4142135623730951},"632":{"tf":1.7320508075688772},"634":{"tf":3.1622776601683795},"635":{"tf":1.0},"64":{"tf":1.4142135623730951},"680":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"75":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":2.23606797749979},"78":{"tf":2.449489742783178},"786":{"tf":2.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"879":{"tf":2.449489742783178},"880":{"tf":1.4142135623730951},"94":{"tf":1.0}},"e":{"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"786":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":1,"docs":{"171":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"p":{"<":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"i":{"d":{",":{"df":0,"docs":{},"u":{"1":{"6":{"df":1,"docs":{"715":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"n":{"'":{"df":0,"docs":{},"t":{"df":2,"docs":{"112":{"tf":1.0},"3":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"df":38,"docs":{"152":{"tf":1.4142135623730951},"155":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"262":{"tf":1.0},"270":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.0},"346":{"tf":1.0},"35":{"tf":1.0},"439":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.0},"495":{"tf":1.0},"515":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"545":{"tf":1.0},"571":{"tf":1.0},"58":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"632":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"701":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"762":{"tf":1.0},"77":{"tf":1.0},"777":{"tf":1.0},"799":{"tf":1.4142135623730951},"816":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":2.0}}}}},"df":5,"docs":{"44":{"tf":2.0},"45":{"tf":2.8284271247461903},"46":{"tf":1.0},"47":{"tf":2.0},"634":{"tf":1.0}},"e":{"a":{"d":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"814":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":12,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.0},"114":{"tf":1.0},"300":{"tf":1.0},"495":{"tf":1.0},"500":{"tf":2.23606797749979},"503":{"tf":2.0},"512":{"tf":1.0},"715":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}}},"df":14,"docs":{"322":{"tf":1.0},"343":{"tf":1.7320508075688772},"349":{"tf":1.7320508075688772},"350":{"tf":2.23606797749979},"44":{"tf":2.0},"45":{"tf":2.6457513110645907},"46":{"tf":2.0},"47":{"tf":2.23606797749979},"49":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.7320508075688772},"500":{"tf":1.4142135623730951},"634":{"tf":1.0},"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{},"p":{"df":15,"docs":{"732":{"tf":1.4142135623730951},"827":{"tf":2.23606797749979},"828":{"tf":1.0},"829":{"tf":1.7320508075688772},"830":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"833":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"840":{"tf":1.0}},"p":{"a":{"df":0,"docs":{},"g":{"df":5,"docs":{"828":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.7320508075688772},"832":{"tf":1.0},"833":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":1,"docs":{"881":{"tf":1.0}}},"v":{"df":0,"docs":{},"i":{"df":2,"docs":{"1006":{"tf":1.0},"530":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"553":{"tf":1.0},"738":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":4,"docs":{"46":{"tf":1.0},"500":{"tf":1.0},"83":{"tf":1.0},"996":{"tf":1.0}}}}}},"l":{"d":{"df":5,"docs":{"206":{"tf":1.0},"375":{"tf":1.4142135623730951},"39":{"tf":1.0},"414":{"tf":1.0},"879":{"tf":1.7320508075688772}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":1,"docs":{"847":{"tf":1.4142135623730951}}}},"p":{"df":22,"docs":{"106":{"tf":1.0},"121":{"tf":1.4142135623730951},"127":{"tf":1.0},"145":{"tf":1.0},"172":{"tf":1.0},"206":{"tf":1.0},"273":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"303":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"574":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"780":{"tf":1.0},"797":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0},"810":{"tf":1.0},"843":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"334":{"tf":1.0}}}}}},"n":{"c":{"df":4,"docs":{"199":{"tf":1.0},"71":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"'":{"df":2,"docs":{"450":{"tf":1.0},"848":{"tf":1.0}}},"df":68,"docs":{"16":{"tf":1.0},"186":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.7320508075688772},"290":{"tf":1.0},"293":{"tf":1.0},"348":{"tf":1.0},"388":{"tf":1.0},"415":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"435":{"tf":1.0},"44":{"tf":1.0},"444":{"tf":1.0},"450":{"tf":1.0},"501":{"tf":1.0},"511":{"tf":1.0},"520":{"tf":1.0},"54":{"tf":1.0},"553":{"tf":1.4142135623730951},"56":{"tf":2.0},"560":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"57":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.4142135623730951},"59":{"tf":1.0},"60":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"634":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"66":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"69":{"tf":1.4142135623730951},"70":{"tf":1.0},"71":{"tf":1.0},"712":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0},"74":{"tf":1.4142135623730951},"748":{"tf":1.0},"75":{"tf":1.0},"76":{"tf":1.0},"761":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0},"78":{"tf":1.4142135623730951},"786":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.0},"844":{"tf":1.0},"881":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"778":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"127":{"tf":1.0}}}}}}},"x":{"a":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"253":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"815":{"tf":1.4142135623730951}}}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"520":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"874":{"tf":1.0}},"i":{"df":3,"docs":{"483":{"tf":1.0},"485":{"tf":1.0},"783":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"h":{"df":21,"docs":{"1004":{"tf":1.0},"1008":{"tf":1.0},"199":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"38":{"tf":1.0},"412":{"tf":1.0},"456":{"tf":1.0},"467":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.4142135623730951},"916":{"tf":1.0},"929":{"tf":1.0},"939":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":20,"docs":{"184":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"25":{"tf":1.0},"267":{"tf":1.0},"417":{"tf":1.0},"42":{"tf":1.0},"429":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"747":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"818":{"tf":1.0},"874":{"tf":1.0},"881":{"tf":1.0},"912":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"234":{"tf":1.0},"711":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"198":{"tf":1.0},"231":{"tf":1.0},"40":{"tf":1.0},"54":{"tf":1.0},"697":{"tf":1.0},"779":{"tf":1.0},"813":{"tf":1.0},"826":{"tf":1.0},"846":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":4,"docs":{"418":{"tf":1.0},"804":{"tf":1.0},"933":{"tf":1.0},"971":{"tf":1.0}}}}}}}}},"m":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"281":{"tf":1.4142135623730951},"284":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"df":16,"docs":{"44":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":2.0},"665":{"tf":1.4142135623730951},"666":{"tf":1.4142135623730951},"667":{"tf":1.0},"668":{"tf":2.0},"669":{"tf":1.4142135623730951},"670":{"tf":2.23606797749979},"671":{"tf":1.0},"672":{"tf":1.0},"673":{"tf":1.7320508075688772},"674":{"tf":1.0},"675":{"tf":1.0},"676":{"tf":1.0},"677":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"138":{"tf":1.0},"290":{"tf":1.0},"512":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.7320508075688772},"913":{"tf":1.0}},"i":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":2,"docs":{"45":{"tf":1.4142135623730951},"46":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":7,"docs":{"49":{"tf":1.0},"500":{"tf":2.23606797749979},"501":{"tf":1.0},"502":{"tf":1.0},"512":{"tf":1.0},"571":{"tf":1.4142135623730951},"843":{"tf":1.0}}}}}}},"t":{"df":3,"docs":{"394":{"tf":1.0},"571":{"tf":1.0},"846":{"tf":1.0}}}},"o":{"c":{"df":2,"docs":{"12":{"tf":1.0},"364":{"tf":1.0}}},"df":0,"docs":{},"l":{"d":{"df":14,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"437":{"tf":1.0},"515":{"tf":2.0},"56":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":2.0},"605":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":2.0},"654":{"tf":1.4142135623730951},"66":{"tf":1.4142135623730951},"67":{"tf":1.0},"976":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"(":{"df":1,"docs":{"844":{"tf":1.0}}},"df":26,"docs":{"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"193":{"tf":1.4142135623730951},"198":{"tf":1.0},"201":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.4142135623730951},"376":{"tf":1.0},"42":{"tf":1.0},"432":{"tf":1.0},"566":{"tf":1.0},"577":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"797":{"tf":1.4142135623730951},"798":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"858":{"tf":1.0},"876":{"tf":1.0},"877":{"tf":1.0},"897":{"tf":1.0},"914":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"332":{"tf":1.7320508075688772},"48":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"712":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0}},"i":{"df":2,"docs":{"710":{"tf":1.0},"722":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"9":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"k":{"df":3,"docs":{"281":{"tf":1.4142135623730951},"284":{"tf":1.0},"291":{"tf":1.4142135623730951}}}},"p":{"df":7,"docs":{"18":{"tf":1.0},"600":{"tf":1.7320508075688772},"602":{"tf":2.0},"606":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":2.449489742783178}},"e":{"df":4,"docs":{"121":{"tf":1.0},"16":{"tf":1.0},"58":{"tf":1.0},"928":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"723":{"tf":1.0},"807":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"179":{"tf":1.0},"181":{"tf":1.0},"537":{"tf":1.0},"548":{"tf":1.0}},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"t":{"_":{"c":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"24":{"tf":1.4142135623730951},"25":{"tf":1.4142135623730951},"26":{"tf":1.4142135623730951}},"l":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"25":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}}}}}},"df":49,"docs":{"100":{"tf":1.4142135623730951},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.4142135623730951},"105":{"tf":1.4142135623730951},"199":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"362":{"tf":2.0},"38":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":2.23606797749979},"401":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.7320508075688772},"404":{"tf":2.0},"405":{"tf":1.0},"406":{"tf":1.4142135623730951},"407":{"tf":1.7320508075688772},"408":{"tf":1.4142135623730951},"409":{"tf":1.4142135623730951},"45":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"53":{"tf":1.0},"54":{"tf":1.4142135623730951},"730":{"tf":2.6457513110645907},"731":{"tf":1.7320508075688772},"732":{"tf":3.1622776601683795},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":5.0990195135927845},"736":{"tf":2.449489742783178},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.7320508075688772},"740":{"tf":1.7320508075688772},"761":{"tf":1.0},"78":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"95":{"tf":2.0},"96":{"tf":1.0},"97":{"tf":2.0},"98":{"tf":1.0},"99":{"tf":1.0}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"231":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"73":{"tf":1.0}}},"u":{"df":0,"docs":{},"r":{"df":8,"docs":{"183":{"tf":1.4142135623730951},"184":{"tf":1.0},"186":{"tf":1.4142135623730951},"257":{"tf":1.0},"507":{"tf":1.0},"861":{"tf":1.4142135623730951},"862":{"tf":1.4142135623730951},"932":{"tf":1.0}}},"s":{"df":2,"docs":{"849":{"tf":1.0},"852":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":1,"docs":{"735":{"tf":1.7320508075688772}},"s":{":":{"/":{"/":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"df":0,"docs":{},"t":{"/":{"a":{"d":{"df":0,"docs":{},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"937":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":1,"docs":{"646":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"35":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"1":{"1":{"0":{"df":1,"docs":{"990":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"h":{"/":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"3":{"7":{"7":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"4":{"7":{"5":{"8":{"df":1,"docs":{"308":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"6":{"6":{"8":{"5":{"df":2,"docs":{"308":{"tf":1.0},"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"7":{"5":{"3":{"9":{"df":1,"docs":{"308":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":11,"docs":{"35":{"tf":1.4142135623730951},"440":{"tf":1.0},"500":{"tf":1.0},"551":{"tf":1.4142135623730951},"555":{"tf":1.0},"712":{"tf":1.4142135623730951},"74":{"tf":1.0},"793":{"tf":1.4142135623730951},"824":{"tf":1.0},"831":{"tf":1.0},"990":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":8,"docs":{"186":{"tf":1.4142135623730951},"388":{"tf":1.0},"661":{"tf":1.0},"665":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"840":{"tf":1.0},"985":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"w":{"3":{"df":0,"docs":{},"f":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"1":{"0":{"df":1,"docs":{"760":{"tf":1.0}}},"df":0,"docs":{}},"5":{"df":1,"docs":{"760":{"tf":1.0}}},"6":{"df":1,"docs":{"735":{"tf":1.0}}},"7":{"df":1,"docs":{"735":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"h":{"a":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"m":{"d":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"/":{"@":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"b":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"q":{"6":{"7":{"df":0,"docs":{},"j":{"b":{"df":0,"docs":{},"w":{"/":{"df":0,"docs":{},"s":{"1":{"df":0,"docs":{},"f":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"v":{"df":0,"docs":{},"x":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":3,"docs":{"712":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"w":{"df":0,"docs":{},"e":{"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"/":{"#":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"%":{"df":0,"docs":{},"e":{"2":{"%":{"9":{"1":{"%":{"a":{"0":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"/":{"d":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"92":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{".":{"b":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"6":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"3":{"df":0,"docs":{},"q":{"?":{"df":0,"docs":{},"t":{"=":{"5":{"2":{"6":{"df":1,"docs":{"807":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"u":{"b":{"df":31,"docs":{"234":{"tf":1.0},"373":{"tf":1.7320508075688772},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"410":{"tf":2.23606797749979},"411":{"tf":1.4142135623730951},"412":{"tf":1.7320508075688772},"413":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":2.23606797749979},"419":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"423":{"tf":1.4142135623730951},"424":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"600":{"tf":1.4142135623730951},"603":{"tf":2.449489742783178},"697":{"tf":3.1622776601683795},"699":{"tf":1.0},"700":{"tf":1.0},"959":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":3,"docs":{"289":{"tf":1.0},"567":{"tf":1.0},"779":{"tf":1.0}}}}},"}":{"_":{"df":0,"docs":{},"p":{"df":2,"docs":{"45":{"tf":1.0},"46":{"tf":1.0}}},"r":{"df":3,"docs":{"44":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"i":{"'":{"d":{"df":1,"docs":{"267":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"878":{"tf":1.0}}}},"m":{"df":4,"docs":{"261":{"tf":1.0},"511":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.4142135623730951}}},"v":{"df":1,"docs":{"878":{"tf":1.4142135623730951}}}},"+":{"1":{"df":1,"docs":{"45":{"tf":1.0}}},"df":0,"docs":{}},".":{"df":20,"docs":{"113":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.4142135623730951},"186":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.4142135623730951},"3":{"tf":1.7320508075688772},"568":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":1.0},"7":{"tf":1.0},"777":{"tf":1.4142135623730951},"847":{"tf":1.0}}},"/":{"df":0,"docs":{},"o":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"763":{"tf":1.0}}}},"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{"df":2,"docs":{"522":{"tf":1.0},"735":{"tf":9.273618495495704}}},"df":0,"docs":{}},"6":{"4":{"df":3,"docs":{"522":{"tf":1.0},"735":{"tf":8.246211251235321},"736":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"522":{"tf":1.0}}},"=":{"b":{"+":{"1":{"df":1,"docs":{"47":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"df":30,"docs":{"126":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"343":{"tf":1.4142135623730951},"347":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":1.0},"456":{"tf":1.0},"461":{"tf":1.0},"47":{"tf":1.4142135623730951},"48":{"tf":1.0},"524":{"tf":1.7320508075688772},"553":{"tf":1.4142135623730951},"555":{"tf":1.0},"6":{"tf":2.449489742783178},"603":{"tf":1.4142135623730951},"632":{"tf":1.0},"634":{"tf":1.0},"7":{"tf":1.0},"735":{"tf":1.4142135623730951},"761":{"tf":1.0},"81":{"tf":2.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"84":{"tf":1.0},"879":{"tf":2.449489742783178}},"e":{"a":{"df":16,"docs":{"108":{"tf":1.0},"429":{"tf":1.0},"514":{"tf":1.0},"518":{"tf":1.0},"588":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"732":{"tf":1.0},"780":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.7320508075688772},"845":{"tf":1.0},"849":{"tf":1.0},"856":{"tf":1.0}},"l":{"df":13,"docs":{"148":{"tf":1.0},"199":{"tf":1.0},"207":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"385":{"tf":1.0},"777":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"928":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":48,"docs":{"323":{"tf":1.0},"339":{"tf":1.0},"348":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.4142135623730951},"373":{"tf":1.4142135623730951},"375":{"tf":2.6457513110645907},"376":{"tf":1.0},"385":{"tf":1.0},"432":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.1622776601683795},"81":{"tf":1.0},"891":{"tf":2.23606797749979},"892":{"tf":1.0},"893":{"tf":1.0},"894":{"tf":1.4142135623730951},"895":{"tf":2.8284271247461903},"896":{"tf":1.4142135623730951},"897":{"tf":1.4142135623730951},"898":{"tf":2.0},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":2.0},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.7320508075688772},"918":{"tf":1.0},"919":{"tf":1.4142135623730951},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"95":{"tf":1.0}},"i":{"df":34,"docs":{"191":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.7320508075688772},"208":{"tf":1.0},"234":{"tf":1.0},"253":{"tf":1.0},"273":{"tf":1.0},"285":{"tf":1.0},"320":{"tf":1.0},"346":{"tf":1.4142135623730951},"351":{"tf":1.0},"521":{"tf":2.23606797749979},"522":{"tf":1.4142135623730951},"524":{"tf":2.23606797749979},"525":{"tf":1.0},"539":{"tf":1.0},"602":{"tf":1.0},"604":{"tf":1.0},"648":{"tf":1.0},"7":{"tf":1.0},"735":{"tf":2.23606797749979},"787":{"tf":1.0},"801":{"tf":1.0},"880":{"tf":1.0},"899":{"tf":1.0},"900":{"tf":1.4142135623730951},"903":{"tf":1.0},"917":{"tf":1.0},"948":{"tf":1.0},"965":{"tf":1.0},"993":{"tf":1.0},"998":{"tf":1.0}}}},"t":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"898":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":1,"docs":{"340":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":10,"docs":{"435":{"tf":1.0},"439":{"tf":1.0},"503":{"tf":1.0},"531":{"tf":1.0},"559":{"tf":1.0},"645":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"761":{"tf":1.0},"934":{"tf":1.0}}}}}},"i":{"df":3,"docs":{"469":{"tf":1.4142135623730951},"470":{"tf":1.0},"471":{"tf":1.0}},"i":{"df":3,"docs":{"469":{"tf":2.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":1,"docs":{"912":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"39":{"tf":1.0}},"t":{"df":0,"docs":{},"r":{"df":6,"docs":{"207":{"tf":1.0},"208":{"tf":1.0},"568":{"tf":1.0},"777":{"tf":1.0},"83":{"tf":1.0},"878":{"tf":1.0}}}}}}}},"m":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"516":{"tf":1.0},"852":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"60":{"tf":1.0},"846":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":14,"docs":{"126":{"tf":1.0},"170":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"417":{"tf":1.0},"564":{"tf":1.4142135623730951},"573":{"tf":1.0},"605":{"tf":1.0},"660":{"tf":1.4142135623730951},"751":{"tf":1.0},"77":{"tf":1.0},"831":{"tf":1.0},"837":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"206":{"tf":1.0},"209":{"tf":1.0}}}},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"126":{"tf":1.0}}}}},"o":{"df":1,"docs":{"399":{"tf":1.0}}},"p":{"a":{"c":{"df":0,"docs":{},"t":{"df":58,"docs":{"1003":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"11":{"tf":1.0},"117":{"tf":1.0},"130":{"tf":1.0},"152":{"tf":1.0},"158":{"tf":1.0},"174":{"tf":1.0},"176":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"303":{"tf":1.0},"305":{"tf":1.0},"310":{"tf":1.0},"379":{"tf":1.0},"392":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.4142135623730951},"422":{"tf":1.0},"424":{"tf":1.0},"517":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"537":{"tf":1.0},"541":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.0},"575":{"tf":1.4142135623730951},"577":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.4142135623730951},"582":{"tf":1.0},"590":{"tf":1.0},"592":{"tf":1.0},"606":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"703":{"tf":1.0},"711":{"tf":1.4142135623730951},"712":{"tf":1.0},"725":{"tf":1.0},"739":{"tf":1.4142135623730951},"77":{"tf":1.0},"778":{"tf":1.0},"8":{"tf":1.0},"819":{"tf":1.0},"821":{"tf":1.0},"866":{"tf":1.0},"87":{"tf":1.0},"916":{"tf":1.0},"929":{"tf":1.0},"936":{"tf":1.0},"968":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"515":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"720":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"390":{"tf":1.0}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":2,"docs":{"24":{"tf":2.0},"933":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"819":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":166,"docs":{"0":{"tf":1.0},"1006":{"tf":1.0},"1008":{"tf":1.4142135623730951},"1012":{"tf":1.0},"115":{"tf":1.4142135623730951},"126":{"tf":1.0},"128":{"tf":1.4142135623730951},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.7320508075688772},"169":{"tf":1.0},"18":{"tf":1.4142135623730951},"19":{"tf":1.0},"191":{"tf":1.0},"193":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"209":{"tf":2.0},"211":{"tf":1.0},"212":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"226":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"240":{"tf":1.0},"241":{"tf":1.0},"249":{"tf":1.0},"251":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"281":{"tf":1.0},"282":{"tf":1.0},"284":{"tf":1.0},"291":{"tf":1.0},"30":{"tf":1.4142135623730951},"304":{"tf":1.4142135623730951},"32":{"tf":1.0},"324":{"tf":1.4142135623730951},"326":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.4142135623730951},"354":{"tf":1.4142135623730951},"359":{"tf":1.7320508075688772},"373":{"tf":1.0},"38":{"tf":1.0},"382":{"tf":1.0},"384":{"tf":1.0},"390":{"tf":1.4142135623730951},"402":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.0},"417":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.0},"429":{"tf":1.4142135623730951},"435":{"tf":1.0},"436":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"464":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"486":{"tf":1.0},"496":{"tf":1.4142135623730951},"50":{"tf":2.0},"500":{"tf":2.23606797749979},"501":{"tf":2.449489742783178},"502":{"tf":1.7320508075688772},"503":{"tf":2.0},"505":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.7320508075688772},"53":{"tf":1.0},"54":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"555":{"tf":1.0},"56":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.4142135623730951},"574":{"tf":1.0},"576":{"tf":1.0},"59":{"tf":1.0},"594":{"tf":1.0},"609":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.0},"631":{"tf":1.0},"635":{"tf":1.4142135623730951},"639":{"tf":1.4142135623730951},"641":{"tf":1.0},"644":{"tf":1.4142135623730951},"648":{"tf":1.4142135623730951},"651":{"tf":2.23606797749979},"653":{"tf":1.4142135623730951},"658":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"69":{"tf":1.4142135623730951},"7":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"732":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"737":{"tf":1.0},"739":{"tf":1.0},"755":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"794":{"tf":1.0},"796":{"tf":1.0},"798":{"tf":1.0},"800":{"tf":1.0},"814":{"tf":1.0},"819":{"tf":1.0},"830":{"tf":1.0},"84":{"tf":1.0},"842":{"tf":1.4142135623730951},"843":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"856":{"tf":1.4142135623730951},"870":{"tf":1.0},"887":{"tf":1.0},"890":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.4142135623730951},"917":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":2.23606797749979},"934":{"tf":1.7320508075688772},"938":{"tf":1.4142135623730951},"940":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.7320508075688772},"956":{"tf":1.0},"957":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"980":{"tf":1.0},"983":{"tf":1.0},"990":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"322":{"tf":1.0},"325":{"tf":1.7320508075688772},"403":{"tf":1.0},"404":{"tf":1.0},"454":{"tf":1.4142135623730951},"518":{"tf":2.23606797749979}}}}}}}}},"i":{"c":{"df":4,"docs":{"171":{"tf":1.0},"418":{"tf":1.0},"564":{"tf":1.0},"765":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"171":{"tf":1.0}}}}},"df":8,"docs":{"130":{"tf":1.0},"198":{"tf":1.0},"3":{"tf":1.0},"570":{"tf":1.0},"8":{"tf":1.0},"84":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"60":{"tf":1.0},"813":{"tf":1.0}}}}}}},"df":30,"docs":{"1008":{"tf":1.0},"154":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"25":{"tf":1.0},"251":{"tf":1.0},"255":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"290":{"tf":1.0},"3":{"tf":1.0},"381":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"514":{"tf":1.0},"565":{"tf":1.0},"629":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"761":{"tf":1.4142135623730951},"804":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"919":{"tf":1.0},"95":{"tf":1.0}}}},"s":{"df":4,"docs":{"531":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"73":{"tf":1.0}},"s":{"df":6,"docs":{"199":{"tf":1.0},"3":{"tf":1.0},"437":{"tf":1.0},"483":{"tf":1.0},"600":{"tf":1.0},"762":{"tf":1.7320508075688772}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"826":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"b":{"df":0,"docs":{},"v":{"df":1,"docs":{"724":{"tf":1.0}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"141":{"tf":1.0}}}}}}},"v":{"df":83,"docs":{"107":{"tf":1.0},"118":{"tf":1.0},"120":{"tf":1.0},"147":{"tf":1.0},"238":{"tf":1.0},"294":{"tf":2.23606797749979},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0},"298":{"tf":1.0},"299":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.4142135623730951},"307":{"tf":1.0},"308":{"tf":1.0},"309":{"tf":1.0},"310":{"tf":1.0},"356":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.0},"404":{"tf":1.4142135623730951},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"575":{"tf":1.0},"605":{"tf":1.0},"614":{"tf":1.0},"622":{"tf":1.0},"640":{"tf":1.0},"649":{"tf":2.0},"650":{"tf":1.0},"651":{"tf":1.0},"652":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.0},"655":{"tf":1.0},"656":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.0},"661":{"tf":1.0},"662":{"tf":1.0},"663":{"tf":2.0},"687":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.0},"757":{"tf":2.0},"758":{"tf":1.4142135623730951},"759":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.0},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.0},"919":{"tf":1.0},"927":{"tf":1.0},"94":{"tf":1.0},"973":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"991":{"tf":1.0}}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"108":{"tf":1.0},"3":{"tf":1.0},"567":{"tf":1.0},"599":{"tf":1.0}}}},"c":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"80":{"tf":1.0},"81":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"797":{"tf":1.0},"843":{"tf":1.0}}}},"d":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"142":{"tf":1.0},"777":{"tf":1.0}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"261":{"tf":1.0},"511":{"tf":1.0}}}}}}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.4142135623730951},"234":{"tf":1.0},"267":{"tf":1.0},"467":{"tf":1.0},"573":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"818":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":5,"docs":{"1003":{"tf":1.0},"124":{"tf":1.0},"206":{"tf":1.0},"776":{"tf":1.0},"881":{"tf":1.0}}}}}}},"i":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"108":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"u":{"d":{"df":99,"docs":{"1014":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.4142135623730951},"126":{"tf":1.0},"127":{"tf":1.0},"170":{"tf":1.0},"18":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.7320508075688772},"234":{"tf":1.4142135623730951},"24":{"tf":1.0},"244":{"tf":1.0},"254":{"tf":1.0},"270":{"tf":1.7320508075688772},"272":{"tf":1.4142135623730951},"28":{"tf":1.0},"282":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"302":{"tf":1.0},"312":{"tf":1.0},"315":{"tf":1.0},"345":{"tf":1.0},"35":{"tf":1.0},"364":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.7320508075688772},"374":{"tf":1.0},"375":{"tf":1.0},"388":{"tf":1.0},"40":{"tf":1.0},"402":{"tf":1.4142135623730951},"403":{"tf":1.4142135623730951},"408":{"tf":1.0},"409":{"tf":1.0},"422":{"tf":1.0},"450":{"tf":2.0},"46":{"tf":1.4142135623730951},"500":{"tf":1.7320508075688772},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"516":{"tf":1.4142135623730951},"521":{"tf":2.23606797749979},"526":{"tf":2.6457513110645907},"528":{"tf":1.0},"532":{"tf":1.0},"573":{"tf":1.0},"585":{"tf":1.0},"619":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"632":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"635":{"tf":1.4142135623730951},"64":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"704":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"77":{"tf":1.0},"796":{"tf":1.0},"84":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.7320508075688772},"849":{"tf":1.0},"85":{"tf":1.0},"853":{"tf":1.0},"870":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"912":{"tf":1.4142135623730951},"941":{"tf":1.0},"943":{"tf":1.0},"944":{"tf":1.0},"947":{"tf":1.0},"958":{"tf":1.0},"960":{"tf":1.0},"964":{"tf":1.0},"973":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"df":6,"docs":{"411":{"tf":1.0},"450":{"tf":1.0},"46":{"tf":1.0},"513":{"tf":1.0},"516":{"tf":1.0},"526":{"tf":1.4142135623730951}}}}},"o":{"df":0,"docs":{},"m":{"df":5,"docs":{"267":{"tf":1.7320508075688772},"466":{"tf":1.0},"69":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"763":{"tf":1.0}}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"842":{"tf":1.0},"850":{"tf":1.0}}}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"267":{"tf":1.0},"325":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"344":{"tf":1.0},"365":{"tf":1.0},"427":{"tf":1.0},"536":{"tf":1.0},"75":{"tf":1.0},"933":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":7,"docs":{"152":{"tf":1.0},"514":{"tf":1.0},"567":{"tf":1.4142135623730951},"615":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"945":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"108":{"tf":1.0},"151":{"tf":1.0},"521":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":76,"docs":{"1004":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"190":{"tf":1.0},"193":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"213":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.7320508075688772},"234":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.7320508075688772},"40":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.0},"42":{"tf":1.0},"420":{"tf":1.0},"422":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"437":{"tf":1.0},"469":{"tf":1.0},"507":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"61":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"729":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.7320508075688772},"749":{"tf":1.0},"751":{"tf":2.0},"752":{"tf":1.7320508075688772},"773":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"779":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"804":{"tf":1.0},"807":{"tf":1.4142135623730951},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"885":{"tf":1.0},"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.0},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":1.4142135623730951},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951},"912":{"tf":1.4142135623730951},"945":{"tf":1.0},"962":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"373":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"208":{"tf":1.0},"322":{"tf":1.0},"334":{"tf":1.7320508075688772},"721":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"78":{"tf":1.4142135623730951}}}}}}}},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"1004":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":4,"docs":{"131":{"tf":1.0},"39":{"tf":1.0},"574":{"tf":1.0},"720":{"tf":1.0}}}}},"d":{"df":0,"docs":{},"e":{"df":5,"docs":{"128":{"tf":1.0},"450":{"tf":1.0},"479":{"tf":1.0},"78":{"tf":1.0},"84":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"199":{"tf":1.0},"206":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":7,"docs":{"204":{"tf":1.0},"417":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.4142135623730951},"934":{"tf":1.0}}},"df":0,"docs":{}}}},"x":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}},"df":28,"docs":{"132":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"18":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"221":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.7320508075688772},"438":{"tf":1.0},"439":{"tf":3.605551275463989},"450":{"tf":2.449489742783178},"520":{"tf":2.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.4142135623730951},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"633":{"tf":2.0},"634":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0},"804":{"tf":1.4142135623730951},"83":{"tf":2.0},"85":{"tf":1.0},"88":{"tf":1.0}}}},"i":{"c":{"df":19,"docs":{"221":{"tf":1.0},"222":{"tf":1.4142135623730951},"254":{"tf":1.0},"267":{"tf":1.0},"273":{"tf":1.7320508075688772},"341":{"tf":1.4142135623730951},"427":{"tf":1.0},"431":{"tf":1.0},"438":{"tf":1.4142135623730951},"439":{"tf":1.0},"483":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.4142135623730951},"615":{"tf":1.0},"735":{"tf":3.605551275463989},"761":{"tf":1.0},"8":{"tf":1.0},"847":{"tf":1.0},"913":{"tf":1.0}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"430":{"tf":1.0},"524":{"tf":1.0},"575":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"46":{"tf":1.0}}}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"u":{"df":21,"docs":{"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"272":{"tf":1.0},"373":{"tf":1.0},"411":{"tf":1.0},"459":{"tf":1.0},"469":{"tf":1.0},"485":{"tf":1.0},"514":{"tf":1.0},"574":{"tf":1.0},"600":{"tf":1.4142135623730951},"700":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0},"797":{"tf":1.0},"844":{"tf":1.0},"876":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"467":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":3,"docs":{"141":{"tf":1.0},"732":{"tf":1.0},"779":{"tf":1.0}}}},"df":0,"docs":{}}}},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"346":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"761":{"tf":1.0}}}}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":16,"docs":{"234":{"tf":1.0},"267":{"tf":2.0},"926":{"tf":2.23606797749979},"927":{"tf":2.0},"928":{"tf":3.605551275463989},"929":{"tf":1.4142135623730951},"930":{"tf":1.0},"931":{"tf":2.23606797749979},"932":{"tf":4.0},"933":{"tf":2.23606797749979},"934":{"tf":1.7320508075688772},"935":{"tf":1.4142135623730951},"936":{"tf":2.0},"937":{"tf":1.7320508075688772},"938":{"tf":1.0},"939":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":3,"docs":{"231":{"tf":1.0},"933":{"tf":1.4142135623730951},"934":{"tf":1.0}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"933":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"w":{"/":{"3":{"3":{"0":{"1":{"df":1,"docs":{"937":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"267":{"tf":1.7320508075688772}}}},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":5,"docs":{"265":{"tf":1.0},"267":{"tf":1.0},"342":{"tf":1.4142135623730951},"459":{"tf":1.4142135623730951},"797":{"tf":1.0}}},"df":0,"docs":{}}},"x":{"df":1,"docs":{"414":{"tf":1.0}}}}},"o":{"df":8,"docs":{"121":{"tf":1.4142135623730951},"22":{"tf":1.0},"321":{"tf":1.0},"343":{"tf":1.0},"375":{"tf":1.0},"6":{"tf":1.0},"614":{"tf":1.0},"872":{"tf":1.0}},"r":{"df":0,"docs":{},"m":{"df":42,"docs":{"203":{"tf":2.449489742783178},"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"216":{"tf":1.0},"218":{"tf":1.0},"222":{"tf":1.7320508075688772},"272":{"tf":1.4142135623730951},"343":{"tf":1.7320508075688772},"348":{"tf":1.0},"349":{"tf":1.4142135623730951},"375":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"5":{"tf":1.4142135623730951},"513":{"tf":1.0},"516":{"tf":1.4142135623730951},"519":{"tf":3.3166247903554},"520":{"tf":1.7320508075688772},"521":{"tf":2.8284271247461903},"522":{"tf":3.7416573867739413},"523":{"tf":2.23606797749979},"524":{"tf":1.0},"525":{"tf":1.0},"528":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"553":{"tf":1.4142135623730951},"568":{"tf":1.0},"574":{"tf":1.0},"6":{"tf":1.7320508075688772},"628":{"tf":1.0},"631":{"tf":1.0},"634":{"tf":1.0},"64":{"tf":1.0},"710":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"8":{"tf":1.0},"816":{"tf":1.0},"84":{"tf":1.0},"895":{"tf":1.0},"931":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":9,"docs":{"178":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"233":{"tf":1.0},"236":{"tf":1.0},"249":{"tf":1.4142135623730951},"565":{"tf":1.0},"571":{"tf":1.0},"853":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"77":{"tf":1.0}}}},"df":0,"docs":{}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"267":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":2.0},"285":{"tf":1.0},"291":{"tf":1.4142135623730951},"3":{"tf":1.0},"346":{"tf":1.0},"722":{"tf":1.0},"739":{"tf":1.0},"85":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"171":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"83":{"tf":1.0}}},"z":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"(":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"284":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":3,"docs":{"284":{"tf":1.4142135623730951},"286":{"tf":1.0},"288":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":20,"docs":{"598":{"tf":2.23606797749979},"599":{"tf":1.0},"600":{"tf":1.0},"601":{"tf":1.0},"602":{"tf":2.23606797749979},"603":{"tf":1.7320508075688772},"604":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"607":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"692":{"tf":1.0},"698":{"tf":2.0},"701":{"tf":1.0},"705":{"tf":1.7320508075688772},"706":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":1,"docs":{"693":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"701":{"tf":1.0},"705":{"tf":1.4142135623730951}}}}}}}}}}}}},"df":58,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"161":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"213":{"tf":1.4142135623730951},"214":{"tf":1.0},"250":{"tf":1.0},"257":{"tf":1.0},"270":{"tf":1.0},"277":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.0},"364":{"tf":1.4142135623730951},"412":{"tf":1.0},"428":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":2.0},"525":{"tf":1.7320508075688772},"537":{"tf":1.0},"564":{"tf":1.0},"583":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.4142135623730951},"609":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"642":{"tf":1.0},"696":{"tf":1.0},"709":{"tf":1.0},"718":{"tf":1.0},"72":{"tf":1.4142135623730951},"725":{"tf":1.0},"75":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":2.0},"815":{"tf":1.0},"83":{"tf":1.7320508075688772},"831":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":1.4142135623730951},"909":{"tf":1.0},"911":{"tf":1.0},"932":{"tf":1.0},"939":{"tf":1.0}}}}},"k":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":7,"docs":{"221":{"tf":1.4142135623730951},"523":{"tf":1.0},"614":{"tf":1.4142135623730951},"615":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.7320508075688772},"786":{"tf":1.0}}}},"o":{"df":0,"docs":{},"v":{"df":5,"docs":{"199":{"tf":2.0},"426":{"tf":1.0},"515":{"tf":1.0},"959":{"tf":1.0},"973":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":21,"docs":{"22":{"tf":2.449489742783178},"229":{"tf":1.0},"23":{"tf":1.4142135623730951},"244":{"tf":1.4142135623730951},"30":{"tf":1.0},"333":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":3.1622776601683795},"346":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.4142135623730951},"45":{"tf":1.0},"516":{"tf":1.7320508075688772},"633":{"tf":1.0},"637":{"tf":1.0},"735":{"tf":2.449489742783178},"898":{"tf":1.0},"931":{"tf":1.0},"94":{"tf":1.0},"948":{"tf":1.0},"95":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"142":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":3,"docs":{"169":{"tf":1.0},"208":{"tf":1.0},"346":{"tf":1.0}}}}},"i":{"d":{"df":2,"docs":{"555":{"tf":1.0},"9":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"325":{"tf":1.0},"364":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"849":{"tf":1.0}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"932":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"r":{"df":2,"docs":{"560":{"tf":1.0},"738":{"tf":1.0}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"141":{"tf":1.0}}}},"df":0,"docs":{},"n":{"c":{"df":16,"docs":{"108":{"tf":1.0},"171":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.7320508075688772},"325":{"tf":1.0},"346":{"tf":1.0},"363":{"tf":1.0},"5":{"tf":1.4142135623730951},"6":{"tf":3.1622776601683795},"7":{"tf":1.0},"776":{"tf":1.4142135623730951},"831":{"tf":1.0},"9":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}},"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":15,"docs":{"195":{"tf":1.0},"203":{"tf":4.0},"204":{"tf":2.0},"205":{"tf":2.449489742783178},"206":{"tf":2.6457513110645907},"207":{"tf":2.8284271247461903},"208":{"tf":2.0},"212":{"tf":1.4142135623730951},"213":{"tf":1.4142135623730951},"218":{"tf":1.7320508075688772},"221":{"tf":2.0},"222":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.7320508075688772},"909":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"221":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{},"i":{"df":2,"docs":{"48":{"tf":1.0},"534":{"tf":1.4142135623730951}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"568":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}}}}}},"df":1,"docs":{"208":{"tf":2.23606797749979}},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}},"y":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"i":{"df":0,"docs":{},"o":{"df":1,"docs":{"208":{"tf":2.449489742783178}}}}}}}},"t":{"df":1,"docs":{"269":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":33,"docs":{"124":{"tf":1.0},"127":{"tf":1.0},"180":{"tf":1.0},"203":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.0},"292":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"52":{"tf":1.0},"522":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.0},"614":{"tf":1.0},"617":{"tf":1.0},"62":{"tf":1.0},"634":{"tf":1.0},"666":{"tf":1.4142135623730951},"680":{"tf":1.0},"696":{"tf":1.7320508075688772},"706":{"tf":1.0},"72":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.3166247903554},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"814":{"tf":1.0},"84":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":61,"docs":{"1":{"tf":1.0},"16":{"tf":1.4142135623730951},"2":{"tf":1.0},"203":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"218":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"269":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.4142135623730951},"372":{"tf":1.0},"5":{"tf":1.0},"51":{"tf":1.0},"598":{"tf":2.23606797749979},"599":{"tf":1.7320508075688772},"6":{"tf":3.872983346207417},"600":{"tf":2.449489742783178},"601":{"tf":1.0},"602":{"tf":5.0990195135927845},"603":{"tf":1.0},"604":{"tf":1.0},"605":{"tf":2.0},"606":{"tf":1.7320508075688772},"607":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.7320508075688772},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"614":{"tf":1.0},"615":{"tf":1.0},"617":{"tf":1.4142135623730951},"619":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.0},"653":{"tf":2.0},"654":{"tf":1.7320508075688772},"660":{"tf":1.7320508075688772},"665":{"tf":1.7320508075688772},"668":{"tf":2.0},"669":{"tf":1.0},"670":{"tf":1.4142135623730951},"673":{"tf":1.7320508075688772},"692":{"tf":1.0},"693":{"tf":1.0},"694":{"tf":1.7320508075688772},"696":{"tf":1.7320508075688772},"698":{"tf":2.0},"7":{"tf":1.0},"701":{"tf":1.7320508075688772},"705":{"tf":2.23606797749979},"786":{"tf":1.7320508075688772},"8":{"tf":1.0},"83":{"tf":1.0},"9":{"tf":1.0},"974":{"tf":1.0},"975":{"tf":1.0},"978":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":2,"docs":{"267":{"tf":1.0},"537":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"t":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"994":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":4,"docs":{"332":{"tf":2.6457513110645907},"346":{"tf":1.0},"347":{"tf":1.0},"404":{"tf":1.0}},"r":{"df":31,"docs":{"12":{"tf":1.0},"185":{"tf":1.0},"205":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"234":{"tf":1.0},"237":{"tf":1.0},"30":{"tf":1.0},"326":{"tf":1.0},"365":{"tf":1.0},"378":{"tf":1.0},"411":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.0},"564":{"tf":1.0},"651":{"tf":1.0},"673":{"tf":1.0},"700":{"tf":1.0},"771":{"tf":1.0},"855":{"tf":1.0},"933":{"tf":1.0},"935":{"tf":1.0},"938":{"tf":1.4142135623730951},"942":{"tf":1.4142135623730951},"956":{"tf":1.0},"958":{"tf":1.0},"961":{"tf":1.7320508075688772},"964":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}}},"n":{"d":{"df":15,"docs":{"207":{"tf":1.4142135623730951},"310":{"tf":1.0},"324":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.0},"40":{"tf":1.0},"573":{"tf":1.0},"628":{"tf":1.0},"822":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"887":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"983":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":3,"docs":{"340":{"tf":1.0},"435":{"tf":1.0},"962":{"tf":1.0}}},"t":{"df":3,"docs":{"723":{"tf":1.0},"777":{"tf":1.0},"911":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"341":{"tf":1.4142135623730951},"418":{"tf":1.0}}}}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":21,"docs":{"125":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"212":{"tf":1.0},"26":{"tf":1.0},"30":{"tf":1.0},"322":{"tf":1.0},"362":{"tf":1.4142135623730951},"369":{"tf":1.0},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":1.4142135623730951},"694":{"tf":1.0},"771":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"894":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":18,"docs":{"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"273":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"498":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"71":{"tf":1.0},"724":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0},"971":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}}}}}},"f":{"a":{"c":{"df":54,"docs":{"1011":{"tf":1.0},"1012":{"tf":1.0},"119":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"203":{"tf":1.0},"212":{"tf":1.0},"215":{"tf":2.23606797749979},"216":{"tf":1.4142135623730951},"217":{"tf":1.7320508075688772},"218":{"tf":2.6457513110645907},"219":{"tf":1.0},"220":{"tf":1.4142135623730951},"221":{"tf":1.0},"222":{"tf":1.0},"223":{"tf":1.0},"224":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.4142135623730951},"227":{"tf":1.0},"228":{"tf":1.0},"289":{"tf":1.0},"307":{"tf":1.0},"322":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.7320508075688772},"362":{"tf":2.449489742783178},"366":{"tf":1.0},"370":{"tf":1.0},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"375":{"tf":1.0},"452":{"tf":1.0},"460":{"tf":1.0},"48":{"tf":1.0},"515":{"tf":1.0},"609":{"tf":1.0},"659":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"736":{"tf":1.0},"804":{"tf":1.0},"88":{"tf":1.0},"902":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"961":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"198":{"tf":1.0},"284":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"205":{"tf":1.0},"697":{"tf":1.0},"786":{"tf":1.7320508075688772}}}}},"l":{"a":{"c":{"df":3,"docs":{"204":{"tf":2.0},"205":{"tf":1.0},"208":{"tf":2.23606797749979}},"e":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"d":{"df":2,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"204":{"tf":1.7320508075688772},"207":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":5,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"402":{"tf":1.0},"696":{"tf":1.4142135623730951},"956":{"tf":1.0}}}}},"df":14,"docs":{"150":{"tf":2.0},"151":{"tf":1.0},"152":{"tf":1.0},"153":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"634":{"tf":1.0}}}}}}}},"df":6,"docs":{"515":{"tf":1.0},"522":{"tf":1.0},"6":{"tf":1.0},"693":{"tf":1.0},"737":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"198":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"12":{"tf":1.0},"313":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"325":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"54":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":12,"docs":{"199":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"5":{"tf":1.0},"539":{"tf":1.0},"545":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.4142135623730951}}}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"231":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"928":{"tf":1.0}}}}}},"v":{"df":2,"docs":{"200":{"tf":1.0},"814":{"tf":1.0}}}}},"r":{"a":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{},"i":{"c":{"a":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"o":{"d":{"df":0,"docs":{},"u":{"c":{"df":165,"docs":{"100":{"tf":1.0},"1002":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"114":{"tf":1.0},"115":{"tf":1.0},"117":{"tf":1.0},"12":{"tf":1.0},"128":{"tf":1.0},"137":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"150":{"tf":2.0},"151":{"tf":1.0},"152":{"tf":1.7320508075688772},"153":{"tf":1.0},"154":{"tf":2.0},"155":{"tf":1.0},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.4142135623730951},"166":{"tf":1.4142135623730951},"169":{"tf":1.0},"17":{"tf":2.23606797749979},"171":{"tf":1.0},"178":{"tf":1.0},"18":{"tf":1.4142135623730951},"181":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.0},"21":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"217":{"tf":1.0},"22":{"tf":1.4142135623730951},"220":{"tf":1.0},"225":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"267":{"tf":1.0},"27":{"tf":1.0},"28":{"tf":1.0},"280":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"304":{"tf":1.0},"305":{"tf":1.0},"31":{"tf":1.0},"32":{"tf":1.0},"33":{"tf":1.0},"334":{"tf":1.0},"34":{"tf":1.0},"35":{"tf":1.0},"354":{"tf":1.0},"358":{"tf":1.0},"36":{"tf":1.0},"37":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"390":{"tf":1.4142135623730951},"397":{"tf":1.7320508075688772},"400":{"tf":2.0},"401":{"tf":1.0},"402":{"tf":1.0},"403":{"tf":1.0},"404":{"tf":1.0},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0},"412":{"tf":1.0},"427":{"tf":1.0},"429":{"tf":1.0},"461":{"tf":1.0},"486":{"tf":1.4142135623730951},"496":{"tf":1.0},"519":{"tf":1.0},"53":{"tf":1.0},"537":{"tf":1.0},"548":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":2.23606797749979},"585":{"tf":1.0},"586":{"tf":1.7320508075688772},"587":{"tf":1.0},"588":{"tf":1.4142135623730951},"589":{"tf":1.0},"590":{"tf":1.0},"591":{"tf":1.0},"592":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.4142135623730951},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"61":{"tf":1.7320508075688772},"62":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.0},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.4142135623730951},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.4142135623730951},"665":{"tf":1.4142135623730951},"72":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":2.0},"77":{"tf":1.0},"773":{"tf":2.0},"788":{"tf":1.4142135623730951},"790":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"819":{"tf":1.0},"821":{"tf":1.0},"829":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"93":{"tf":2.0},"94":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.0},"949":{"tf":1.0},"95":{"tf":1.0},"951":{"tf":1.0},"953":{"tf":1.0},"96":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"966":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0},"996":{"tf":1.0}},"t":{"df":15,"docs":{"0":{"tf":1.7320508075688772},"169":{"tf":1.0},"269":{"tf":1.0},"322":{"tf":1.4142135623730951},"334":{"tf":1.4142135623730951},"335":{"tf":1.4142135623730951},"359":{"tf":1.0},"371":{"tf":1.0},"412":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"95":{"tf":1.0},"968":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"928":{"tf":1.0},"952":{"tf":1.0},"969":{"tf":1.0}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"/":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"b":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"439":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":12,"docs":{"152":{"tf":1.4142135623730951},"293":{"tf":1.0},"296":{"tf":1.4142135623730951},"303":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"450":{"tf":1.0},"635":{"tf":1.0},"735":{"tf":2.23606797749979},"761":{"tf":1.4142135623730951},"944":{"tf":1.0},"948":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"944":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"r":{"c":{"df":0,"docs":{},"h":{"'":{"df":1,"docs":{"784":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":1,"docs":{"284":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"267":{"tf":1.0},"749":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"274":{"tf":1.0}},"i":{"df":0,"docs":{},"g":{"df":2,"docs":{"363":{"tf":1.0},"365":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"199":{"tf":1.0},"418":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}},"o":{"df":0,"docs":{},"k":{"df":4,"docs":{"108":{"tf":1.0},"24":{"tf":1.0},"284":{"tf":1.0},"30":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"v":{"df":16,"docs":{"108":{"tf":1.0},"112":{"tf":1.0},"375":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.4142135623730951},"698":{"tf":1.0},"705":{"tf":1.0},"739":{"tf":1.0},"745":{"tf":1.0},"771":{"tf":1.0},"786":{"tf":1.0},"8":{"tf":1.0},"809":{"tf":1.0},"951":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"231":{"tf":1.0},"234":{"tf":2.449489742783178},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.0},"239":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":12,"docs":{"258":{"tf":1.0},"259":{"tf":1.0},"487":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"492":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"766":{"tf":1.0}}}}}}}},"s":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"d":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":10,"docs":{"255":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"512":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"701":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"817":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":4,"docs":{"373":{"tf":1.0},"494":{"tf":1.0},"63":{"tf":1.0},"836":{"tf":1.4142135623730951}}}},"s":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"264":{"tf":1.0},"267":{"tf":1.0}}},"df":0,"docs":{}}},"df":54,"docs":{"127":{"tf":1.0},"13":{"tf":1.0},"152":{"tf":2.23606797749979},"155":{"tf":1.4142135623730951},"161":{"tf":1.0},"163":{"tf":1.0},"17":{"tf":1.4142135623730951},"193":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"267":{"tf":1.0},"28":{"tf":1.7320508075688772},"29":{"tf":1.7320508075688772},"291":{"tf":1.0},"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"375":{"tf":1.0},"409":{"tf":1.0},"427":{"tf":1.0},"440":{"tf":1.0},"447":{"tf":1.0},"450":{"tf":1.0},"51":{"tf":1.0},"53":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"568":{"tf":1.0},"576":{"tf":1.0},"58":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.4142135623730951},"630":{"tf":1.0},"639":{"tf":1.0},"67":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"799":{"tf":1.0},"80":{"tf":1.0},"826":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.4142135623730951},"859":{"tf":1.0},"864":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"88":{"tf":1.0},"912":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"998":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"234":{"tf":1.0}}}}}}},"t":{"'":{"df":26,"docs":{"126":{"tf":1.0},"267":{"tf":1.7320508075688772},"3":{"tf":1.0},"32":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.0},"422":{"tf":1.0},"438":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"522":{"tf":1.0},"697":{"tf":1.0},"724":{"tf":1.0},"762":{"tf":1.4142135623730951},"773":{"tf":1.0},"786":{"tf":1.0},"813":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.7320508075688772},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"887":{"tf":1.0}},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"112":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}}}}}}},"df":15,"docs":{"205":{"tf":1.7320508075688772},"223":{"tf":1.0},"343":{"tf":1.4142135623730951},"347":{"tf":1.0},"402":{"tf":1.7320508075688772},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"417":{"tf":1.4142135623730951},"45":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.7320508075688772},"485":{"tf":1.4142135623730951},"758":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":2.0}}},"r":{"df":23,"docs":{"136":{"tf":2.0},"137":{"tf":1.4142135623730951},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.7320508075688772},"141":{"tf":1.4142135623730951},"142":{"tf":1.0},"143":{"tf":1.0},"144":{"tf":1.4142135623730951},"145":{"tf":1.4142135623730951},"146":{"tf":1.0},"147":{"tf":1.4142135623730951},"148":{"tf":1.0},"149":{"tf":1.7320508075688772},"199":{"tf":1.0},"257":{"tf":1.0},"507":{"tf":1.0},"523":{"tf":1.0},"573":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"928":{"tf":1.0},"992":{"tf":1.0}}}},"h":{"df":1,"docs":{"717":{"tf":1.0}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":31,"docs":{"15":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"198":{"tf":1.0},"222":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"300":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.4142135623730951},"586":{"tf":1.0},"62":{"tf":1.0},"641":{"tf":1.0},"697":{"tf":1.0},"7":{"tf":1.4142135623730951},"700":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":1.4142135623730951},"777":{"tf":1.0},"788":{"tf":1.0},"855":{"tf":1.0},"875":{"tf":2.0},"879":{"tf":1.0}}}}}}},"v":{"df":3,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0}}},"x":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}}},"z":{"df":1,"docs":{"762":{"tf":1.0}}}},"j":{"a":{"df":0,"docs":{},"m":{"'":{"df":10,"docs":{"38":{"tf":1.4142135623730951},"40":{"tf":1.4142135623730951},"45":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.4142135623730951},"49":{"tf":1.4142135623730951},"51":{"tf":1.0},"52":{"tf":1.0},"54":{"tf":1.4142135623730951},"725":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"38":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":20,"docs":{"111":{"tf":1.0},"38":{"tf":3.0},"39":{"tf":1.7320508075688772},"40":{"tf":2.449489742783178},"41":{"tf":1.7320508075688772},"42":{"tf":1.4142135623730951},"43":{"tf":1.7320508075688772},"44":{"tf":2.0},"45":{"tf":1.7320508075688772},"46":{"tf":1.7320508075688772},"47":{"tf":2.23606797749979},"48":{"tf":1.4142135623730951},"49":{"tf":1.7320508075688772},"50":{"tf":2.0},"51":{"tf":1.0},"52":{"tf":1.7320508075688772},"53":{"tf":2.0},"54":{"tf":2.0},"55":{"tf":1.0},"928":{"tf":1.4142135623730951}}},"n":{"df":1,"docs":{"312":{"tf":1.0}},"u":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"418":{"tf":1.0},"841":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"45":{"tf":1.4142135623730951},"47":{"tf":1.0}},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"244":{"tf":1.0},"709":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"l":{"df":1,"docs":{"857":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"663":{"tf":1.0},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"983":{"tf":1.0},"987":{"tf":1.0}}},"y":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"17":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"b":{"df":2,"docs":{"467":{"tf":1.0},"515":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":5,"docs":{"229":{"tf":1.0},"268":{"tf":1.0},"366":{"tf":1.0},"410":{"tf":1.0},"465":{"tf":1.0}}},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"234":{"tf":1.0},"272":{"tf":1.0},"315":{"tf":1.0},"471":{"tf":1.0},"576":{"tf":1.0}},"t":{"df":1,"docs":{"876":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.0}}}}}}},"n":{"a":{"df":3,"docs":{"263":{"tf":1.0},"563":{"tf":1.0},"771":{"tf":1.0}}},"df":0,"docs":{}}},"s":{"/":{"df":0,"docs":{},"t":{"df":1,"docs":{"19":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"50":{"tf":1.0},"512":{"tf":1.0},"522":{"tf":1.0}}}}},"u":{"d":{"df":0,"docs":{},"g":{"df":4,"docs":{"207":{"tf":1.4142135623730951},"45":{"tf":1.0},"761":{"tf":1.0},"895":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":17,"docs":{"1002":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"252":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"56":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"741":{"tf":1.0},"974":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"576":{"tf":1.0}}}},"n":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"195":{"tf":1.0}}},"k":{"df":1,"docs":{"863":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":0,"docs":{},"u":{"df":1,"docs":{"410":{"tf":1.0}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":2,"docs":{"1006":{"tf":1.0},"500":{"tf":1.4142135623730951}},"i":{"df":2,"docs":{"54":{"tf":1.0},"575":{"tf":1.0}}}}}}}}},"k":{"*":{"df":0,"docs":{},"n":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}}},"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"a":{"df":1,"docs":{"553":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"a":{"df":8,"docs":{"252":{"tf":1.7320508075688772},"255":{"tf":1.0},"257":{"tf":1.0},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"a":{"df":1,"docs":{"855":{"tf":1.0}}},"df":0,"docs":{}}}},"b":{"df":1,"docs":{"517":{"tf":1.0}}},"df":2,"docs":{"436":{"tf":1.0},"885":{"tf":2.8284271247461903}},"e":{"c":{"c":{"a":{"df":0,"docs":{},"k":{"2":{"5":{"6":{"df":3,"docs":{"50":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":18,"docs":{"121":{"tf":1.0},"208":{"tf":1.0},"315":{"tf":1.0},"407":{"tf":1.4142135623730951},"439":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.4142135623730951},"551":{"tf":1.0},"567":{"tf":1.0},"631":{"tf":1.0},"643":{"tf":1.0},"660":{"tf":1.0},"67":{"tf":1.0},"723":{"tf":1.4142135623730951},"761":{"tf":1.0},"881":{"tf":1.0},"932":{"tf":1.0},"944":{"tf":1.0}}}},"p":{"df":0,"docs":{},"t":{"df":5,"docs":{"255":{"tf":1.0},"349":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"505":{"tf":1.0}}}},"y":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"735":{"tf":3.605551275463989}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":64,"docs":{"108":{"tf":1.0},"150":{"tf":2.0},"151":{"tf":1.7320508075688772},"152":{"tf":1.0},"153":{"tf":1.0},"154":{"tf":2.0},"155":{"tf":1.4142135623730951},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.7320508075688772},"25":{"tf":1.0},"252":{"tf":2.449489742783178},"255":{"tf":2.0},"257":{"tf":1.4142135623730951},"296":{"tf":1.0},"341":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"38":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"45":{"tf":1.0},"452":{"tf":2.8284271247461903},"453":{"tf":2.8284271247461903},"455":{"tf":2.0},"456":{"tf":1.0},"459":{"tf":2.0},"46":{"tf":2.0},"461":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"5":{"tf":2.23606797749979},"501":{"tf":2.8284271247461903},"505":{"tf":2.0},"507":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"553":{"tf":1.0},"555":{"tf":1.0},"565":{"tf":1.0},"6":{"tf":2.8284271247461903},"629":{"tf":1.0},"735":{"tf":5.916079783099616},"759":{"tf":2.8284271247461903},"761":{"tf":4.47213595499958},"763":{"tf":1.4142135623730951},"81":{"tf":1.4142135623730951},"829":{"tf":1.7320508075688772},"876":{"tf":1.0},"894":{"tf":1.4142135623730951},"932":{"tf":2.0},"94":{"tf":1.0},"944":{"tf":1.0},"95":{"tf":2.0},"961":{"tf":1.0},"992":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"80":{"tf":1.4142135623730951},"81":{"tf":2.23606797749979},"83":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"6":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":1,"docs":{"6":{"tf":1.4142135623730951}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"&":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"735":{"tf":1.0},"95":{"tf":1.7320508075688772}}}}}}}},"i":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"244":{"tf":1.0},"926":{"tf":1.0}}}},"b":{"df":4,"docs":{"257":{"tf":1.0},"436":{"tf":1.4142135623730951},"507":{"tf":1.0},"515":{"tf":1.0}}},"df":0,"docs":{},"n":{"d":{"df":11,"docs":{"108":{"tf":1.0},"3":{"tf":1.0},"453":{"tf":1.7320508075688772},"521":{"tf":1.0},"527":{"tf":1.0},"531":{"tf":1.0},"534":{"tf":1.4142135623730951},"54":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"63":{"tf":1.0}}},"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"187":{"tf":1.0}}}},"df":0,"docs":{},"w":{"df":28,"docs":{"257":{"tf":1.0},"303":{"tf":1.0},"373":{"tf":1.0},"391":{"tf":1.0},"439":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"619":{"tf":1.0},"669":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"846":{"tf":1.0},"854":{"tf":1.0},"895":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"844":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"df":20,"docs":{"126":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"220":{"tf":1.0},"255":{"tf":1.0},"335":{"tf":1.0},"348":{"tf":1.0},"362":{"tf":1.7320508075688772},"368":{"tf":1.0},"373":{"tf":1.0},"439":{"tf":1.0},"514":{"tf":1.4142135623730951},"521":{"tf":1.0},"6":{"tf":1.0},"735":{"tf":2.0},"777":{"tf":1.0},"829":{"tf":1.4142135623730951},"842":{"tf":1.0},"874":{"tf":1.0}}}}}},"r":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"40":{"tf":1.0},"54":{"tf":1.0}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"247":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0},"827":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"m":{"df":9,"docs":{"316":{"tf":1.0},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"843":{"tf":1.0},"844":{"tf":1.0},"849":{"tf":1.0},"862":{"tf":1.0},"914":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"400":{"tf":1.0}}}}}},"s":{"a":{"df":0,"docs":{},"m":{"a":{"'":{"df":9,"docs":{"375":{"tf":1.0},"376":{"tf":1.0},"843":{"tf":1.4142135623730951},"846":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"852":{"tf":1.4142135623730951},"855":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"711":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":39,"docs":{"128":{"tf":1.0},"253":{"tf":1.0},"312":{"tf":1.0},"314":{"tf":1.0},"366":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":3.0},"385":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"418":{"tf":1.7320508075688772},"423":{"tf":1.4142135623730951},"429":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"600":{"tf":1.4142135623730951},"697":{"tf":1.0},"759":{"tf":1.0},"842":{"tf":1.0},"843":{"tf":2.449489742783178},"848":{"tf":1.4142135623730951},"849":{"tf":1.4142135623730951},"852":{"tf":1.7320508075688772},"853":{"tf":1.0},"857":{"tf":1.0},"859":{"tf":1.0},"862":{"tf":1.4142135623730951},"869":{"tf":1.0},"909":{"tf":1.0},"911":{"tf":2.0},"912":{"tf":3.3166247903554},"913":{"tf":1.7320508075688772},"914":{"tf":1.7320508075688772},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.7320508075688772}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"'":{"df":1,"docs":{"841":{"tf":1.0}}},"df":16,"docs":{"841":{"tf":2.0},"842":{"tf":1.4142135623730951},"843":{"tf":1.0},"844":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"851":{"tf":1.0},"852":{"tf":1.0},"853":{"tf":1.0},"854":{"tf":1.0},"855":{"tf":1.0},"856":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"ö":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"150":{"tf":1.0},"451":{"tf":1.0},"584":{"tf":1.0}}}}}},"df":0,"docs":{}}},"l":{".":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":0,"docs":{},"s":{")":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":0,"docs":{},"s":{")":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"1":{"7":{"6":{"2":{"df":1,"docs":{"831":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"39":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"39":{"tf":1.0},"48":{"tf":1.0}}},"3":{"4":{"0":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"7":{"5":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"2":{"c":{"1":{"5":{"df":1,"docs":{"310":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"b":{"df":1,"docs":{"244":{"tf":1.0}},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"84":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"k":{"df":10,"docs":{"234":{"tf":1.0},"296":{"tf":1.0},"725":{"tf":1.0},"735":{"tf":1.0},"81":{"tf":1.0},"874":{"tf":1.0},"917":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"204":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"g":{"df":7,"docs":{"651":{"tf":1.0},"679":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"687":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.0}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"g":{"df":30,"docs":{"184":{"tf":1.0},"196":{"tf":1.0},"201":{"tf":1.0},"230":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"375":{"tf":1.0},"436":{"tf":1.0},"444":{"tf":1.0},"505":{"tf":1.4142135623730951},"515":{"tf":1.0},"522":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951},"571":{"tf":1.0},"577":{"tf":1.4142135623730951},"619":{"tf":1.0},"683":{"tf":1.0},"697":{"tf":1.0},"75":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"774":{"tf":1.0},"810":{"tf":1.0},"833":{"tf":1.0},"850":{"tf":1.0},"87":{"tf":1.0},"990":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":9,"docs":{"376":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"577":{"tf":1.0},"735":{"tf":1.4142135623730951},"779":{"tf":1.0},"797":{"tf":1.4142135623730951},"832":{"tf":1.0},"885":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"571":{"tf":1.4142135623730951},"843":{"tf":1.0},"850":{"tf":1.0},"992":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"292":{"tf":1.4142135623730951}}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"222":{"tf":1.4142135623730951}}}}}}}},"df":25,"docs":{"188":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"333":{"tf":1.4142135623730951},"343":{"tf":1.4142135623730951},"346":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"45":{"tf":2.449489742783178},"46":{"tf":1.0},"47":{"tf":1.0},"49":{"tf":1.7320508075688772},"503":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.4142135623730951},"721":{"tf":1.0},"761":{"tf":1.0},"815":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0},"932":{"tf":1.4142135623730951}},"i":{"c":{".":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"df":0,"docs":{},"z":{"df":1,"docs":{"911":{"tf":1.0}}}}}},"df":3,"docs":{"941":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"342":{"tf":1.0}},"n":{"c":{"df":4,"docs":{"138":{"tf":1.0},"207":{"tf":1.0},"218":{"tf":1.0},"640":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"r":{"df":19,"docs":{"154":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.0},"22":{"tf":1.0},"441":{"tf":1.0},"486":{"tf":1.0},"567":{"tf":1.4142135623730951},"570":{"tf":1.7320508075688772},"717":{"tf":1.0},"732":{"tf":1.0},"777":{"tf":1.0},"809":{"tf":1.0},"814":{"tf":1.0},"847":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.0},"911":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"191":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"67":{"tf":1.0},"881":{"tf":1.0},"895":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"371":{"tf":1.0}}},"df":2,"docs":{"776":{"tf":1.0},"831":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":11,"docs":{"108":{"tf":1.0},"209":{"tf":1.0},"277":{"tf":1.0},"303":{"tf":1.0},"367":{"tf":1.0},"371":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.0},"644":{"tf":1.0},"797":{"tf":1.0}}}},"df":0,"docs":{}}},"w":{"df":1,"docs":{"912":{"tf":1.0}}},"y":{"df":2,"docs":{"326":{"tf":1.0},"361":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"1004":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"430":{"tf":1.0},"47":{"tf":1.0}}}},"m":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"359":{"tf":1.0},"848":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"151":{"tf":1.7320508075688772},"163":{"tf":1.0},"523":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0}}}}}},"z":{"df":0,"docs":{},"i":{"df":2,"docs":{"69":{"tf":1.0},"724":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"880":{"tf":1.0}}}}}}},"df":1,"docs":{"749":{"tf":1.0}},"e":{"a":{"d":{"df":30,"docs":{"1004":{"tf":1.0},"113":{"tf":1.0},"126":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"170":{"tf":1.4142135623730951},"19":{"tf":1.0},"205":{"tf":1.0},"249":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"505":{"tf":1.0},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.4142135623730951},"574":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"779":{"tf":1.4142135623730951},"80":{"tf":1.0},"818":{"tf":1.0},"975":{"tf":1.0},"979":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"204":{"tf":1.0},"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}},"df":4,"docs":{"204":{"tf":1.7320508075688772},"207":{"tf":2.23606797749979},"213":{"tf":1.0},"773":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":1,"docs":{"78":{"tf":1.7320508075688772}}},"k":{"df":4,"docs":{"453":{"tf":1.0},"528":{"tf":1.4142135623730951},"723":{"tf":1.0},"934":{"tf":1.0}}},"s":{"df":18,"docs":{"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.7320508075688772},"205":{"tf":1.7320508075688772},"296":{"tf":2.0},"297":{"tf":1.0},"300":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"48":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":2.449489742783178},"911":{"tf":1.0},"912":{"tf":1.0},"919":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"/":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"203":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"t":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"v":{"df":9,"docs":{"203":{"tf":1.0},"231":{"tf":1.0},"255":{"tf":1.0},"525":{"tf":2.6457513110645907},"526":{"tf":1.0},"570":{"tf":1.0},"574":{"tf":1.0},"78":{"tf":1.0},"928":{"tf":1.0}}}},"b":{"1":{"2":{"8":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"1":{"df":1,"docs":{"485":{"tf":1.0}}},"2":{"df":1,"docs":{"485":{"tf":1.0}}},"3":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"d":{"df":2,"docs":{"161":{"tf":1.0},"54":{"tf":1.0}}},"df":1,"docs":{"722":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":1,"docs":{"182":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"t":{"(":{"1":{"df":1,"docs":{"749":{"tf":1.0}}},"\\":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"{":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.0}}},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"k":{"df":0,"docs":{},"k":{"df":1,"docs":{"879":{"tf":1.0}}}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":15,"docs":{"204":{"tf":1.0},"324":{"tf":1.0},"341":{"tf":1.4142135623730951},"358":{"tf":1.0},"525":{"tf":1.7320508075688772},"576":{"tf":1.0},"577":{"tf":1.0},"747":{"tf":1.7320508075688772},"748":{"tf":1.0},"749":{"tf":1.7320508075688772},"751":{"tf":1.4142135623730951},"776":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.4142135623730951},"976":{"tf":1.0}},"o":{"df":0,"docs":{},"v":{"df":5,"docs":{"375":{"tf":1.0},"653":{"tf":1.7320508075688772},"656":{"tf":1.0},"660":{"tf":1.0},"666":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"663":{"tf":1.0},"666":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"g":{"a":{"c":{"df":0,"docs":{},"i":{"df":4,"docs":{"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772}}}},"df":0,"docs":{},"l":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":2,"docs":{"602":{"tf":1.4142135623730951},"603":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":1,"docs":{"376":{"tf":1.0}}}},"t":{"df":1,"docs":{"349":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"a":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"514":{"tf":1.0}}}},"df":0,"docs":{}},"df":3,"docs":{"127":{"tf":1.4142135623730951},"567":{"tf":1.0},"858":{"tf":1.0}}}}}}},"n":{"d":{"df":1,"docs":{"372":{"tf":1.0}}},"df":2,"docs":{"455":{"tf":1.0},"522":{"tf":1.0}},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"349":{"tf":1.0}}}}}}}},"df":1,"docs":{"333":{"tf":1.0}}},"df":32,"docs":{"170":{"tf":1.0},"204":{"tf":1.0},"25":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"26":{"tf":1.0},"332":{"tf":2.0},"347":{"tf":1.7320508075688772},"435":{"tf":1.0},"455":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":1.0},"522":{"tf":1.0},"565":{"tf":1.0},"632":{"tf":1.0},"743":{"tf":1.0},"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":2.23606797749979},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":1.7320508075688772},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951}},"i":{"df":3,"docs":{"296":{"tf":1.0},"55":{"tf":1.0},"942":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"73":{"tf":1.0}}}}}}},"q":{"df":1,"docs":{"749":{"tf":1.0}}},"s":{"df":0,"docs":{},"s":{"df":36,"docs":{"199":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":1.0},"223":{"tf":1.7320508075688772},"231":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.4142135623730951},"342":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"375":{"tf":1.0},"470":{"tf":1.0},"513":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"631":{"tf":1.0},"66":{"tf":1.0},"683":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.7320508075688772},"724":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"895":{"tf":1.0},"916":{"tf":1.0},"919":{"tf":1.0},"932":{"tf":2.0},"976":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"777":{"tf":1.0}}}}}},"t":{"'":{"df":6,"docs":{"5":{"tf":1.4142135623730951},"568":{"tf":1.0},"60":{"tf":1.0},"749":{"tf":1.0},"878":{"tf":1.0},"931":{"tf":1.0}}},"df":5,"docs":{"267":{"tf":1.0},"280":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"749":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":25,"docs":{"163":{"tf":1.4142135623730951},"184":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"212":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"29":{"tf":1.4142135623730951},"35":{"tf":1.0},"375":{"tf":1.0},"418":{"tf":1.0},"456":{"tf":1.0},"465":{"tf":1.0},"469":{"tf":1.4142135623730951},"470":{"tf":1.4142135623730951},"471":{"tf":1.0},"472":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"712":{"tf":1.0},"830":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"g":{"df":12,"docs":{"147":{"tf":1.0},"171":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.0},"437":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"537":{"tf":1.0},"571":{"tf":1.0},"784":{"tf":1.0},"94":{"tf":1.0},"97":{"tf":1.0}}}},"df":1,"docs":{"751":{"tf":1.0}}}}}},"i":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}}}},"p":{"2":{"df":0,"docs":{},"p":{"df":3,"docs":{"252":{"tf":1.0},"255":{"tf":1.0},"505":{"tf":1.0}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"741":{"tf":1.0}}}}}},"df":1,"docs":{"776":{"tf":1.0}},"e":{"df":1,"docs":{"723":{"tf":1.0}}},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"y":{"c":{"df":0,"docs":{},"l":{"df":1,"docs":{"187":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"206":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"78":{"tf":1.0}}}}}}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":22,"docs":{"249":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"381":{"tf":1.0},"403":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.0},"757":{"tf":2.0},"758":{"tf":1.4142135623730951},"759":{"tf":2.449489742783178},"760":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.4142135623730951},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.0},"815":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"71":{"tf":1.0}}}}}}},"k":{"df":0,"docs":{},"e":{"df":2,"docs":{"697":{"tf":1.0},"847":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{}}}}}},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"231":{"tf":1.0},"273":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":61,"docs":{"198":{"tf":1.0},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"215":{"tf":1.0},"22":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"23":{"tf":1.0},"239":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"255":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.4142135623730951},"30":{"tf":1.7320508075688772},"347":{"tf":1.0},"376":{"tf":1.0},"402":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.0},"46":{"tf":1.4142135623730951},"505":{"tf":1.0},"537":{"tf":1.0},"540":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"568":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"615":{"tf":1.0},"638":{"tf":1.0},"659":{"tf":1.0},"694":{"tf":1.0},"73":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.0},"747":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.7320508075688772},"765":{"tf":1.0},"80":{"tf":1.0},"828":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":2.0},"832":{"tf":1.0},"85":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.0},"892":{"tf":1.4142135623730951},"895":{"tf":1.0},"896":{"tf":1.4142135623730951},"898":{"tf":1.4142135623730951},"902":{"tf":1.0},"911":{"tf":1.0},"942":{"tf":1.0},"959":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"752":{"tf":1.7320508075688772},"754":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"776":{"tf":1.0}}}}}},"df":9,"docs":{"152":{"tf":1.0},"186":{"tf":1.0},"188":{"tf":1.0},"267":{"tf":1.0},"701":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.0}}},"k":{"df":7,"docs":{"252":{"tf":1.0},"410":{"tf":1.0},"429":{"tf":1.4142135623730951},"501":{"tf":1.0},"553":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"565":{"tf":2.0},"575":{"tf":1.0},"577":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"t":{"df":33,"docs":{"137":{"tf":1.0},"180":{"tf":1.4142135623730951},"234":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.4142135623730951},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"273":{"tf":1.0},"345":{"tf":1.0},"370":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"505":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":2.0},"525":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"602":{"tf":1.0},"735":{"tf":2.23606797749979},"759":{"tf":1.4142135623730951},"763":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"929":{"tf":1.0},"940":{"tf":1.0},"941":{"tf":1.4142135623730951},"942":{"tf":1.0},"944":{"tf":3.3166247903554},"947":{"tf":1.0},"948":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"a":{"d":{"d":{"df":0,"docs":{},"r":{"df":1,"docs":{"253":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"721":{"tf":1.0},"848":{"tf":1.7320508075688772}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"c":{"df":0,"docs":{},"r":{"df":1,"docs":{"944":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}}}}},"t":{"df":1,"docs":{"126":{"tf":1.4142135623730951}},"t":{"df":0,"docs":{},"l":{"df":8,"docs":{"238":{"tf":1.0},"276":{"tf":1.0},"303":{"tf":1.0},"381":{"tf":1.0},"438":{"tf":1.0},"593":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.4142135623730951}}}}},"u":{"df":1,"docs":{"988":{"tf":1.0}}},"v":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"467":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":10,"docs":{"230":{"tf":1.0},"231":{"tf":1.0},"356":{"tf":1.0},"358":{"tf":1.0},"440":{"tf":1.0},"551":{"tf":1.0},"63":{"tf":1.0},"720":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0}}}}},"o":{"a":{"d":{"df":13,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.7320508075688772},"155":{"tf":1.4142135623730951},"158":{"tf":1.0},"163":{"tf":1.0},"26":{"tf":1.4142135623730951},"605":{"tf":1.0},"654":{"tf":1.4142135623730951},"66":{"tf":1.0},"71":{"tf":1.0},"828":{"tf":1.0},"831":{"tf":1.0},"87":{"tf":1.0}}},"df":0,"docs":{}},"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":13,"docs":{"347":{"tf":1.0},"522":{"tf":1.0},"528":{"tf":1.0},"555":{"tf":1.0},"599":{"tf":1.4142135623730951},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"694":{"tf":1.0},"701":{"tf":1.0},"704":{"tf":1.0},"735":{"tf":1.4142135623730951},"759":{"tf":1.0},"78":{"tf":1.0}}},"t":{"df":30,"docs":{"151":{"tf":1.4142135623730951},"154":{"tf":1.0},"163":{"tf":1.0},"237":{"tf":1.0},"315":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":2.23606797749979},"668":{"tf":1.0},"697":{"tf":3.0},"698":{"tf":1.0},"701":{"tf":1.0},"735":{"tf":3.1622776601683795},"782":{"tf":2.23606797749979},"783":{"tf":1.4142135623730951},"784":{"tf":1.4142135623730951},"785":{"tf":1.0},"786":{"tf":4.58257569495584},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"83":{"tf":1.0},"976":{"tf":1.0},"980":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"6":{"tf":1.0}}},":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"2":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"k":{"df":42,"docs":{"120":{"tf":1.0},"198":{"tf":1.0},"284":{"tf":1.0},"294":{"tf":2.23606797749979},"295":{"tf":2.23606797749979},"296":{"tf":1.7320508075688772},"297":{"tf":1.7320508075688772},"298":{"tf":1.0},"299":{"tf":1.0},"300":{"tf":2.449489742783178},"301":{"tf":3.3166247903554},"302":{"tf":1.7320508075688772},"303":{"tf":2.0},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"308":{"tf":1.0},"309":{"tf":1.0},"310":{"tf":1.4142135623730951},"375":{"tf":2.0},"52":{"tf":1.0},"564":{"tf":2.23606797749979},"575":{"tf":2.8284271247461903},"908":{"tf":2.23606797749979},"909":{"tf":1.0},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.4142135623730951},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"m":{"df":1,"docs":{"428":{"tf":1.0}}}}}}}},"df":7,"docs":{"29":{"tf":1.0},"322":{"tf":1.0},"343":{"tf":2.23606797749979},"349":{"tf":1.7320508075688772},"350":{"tf":1.4142135623730951},"440":{"tf":1.0},"996":{"tf":1.0}},"i":{"c":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"376":{"tf":1.0}}}}},"df":53,"docs":{"124":{"tf":1.0},"151":{"tf":1.0},"16":{"tf":1.0},"19":{"tf":1.4142135623730951},"219":{"tf":1.0},"234":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.0},"281":{"tf":1.0},"286":{"tf":1.0},"289":{"tf":1.0},"293":{"tf":1.0},"3":{"tf":1.7320508075688772},"367":{"tf":1.4142135623730951},"368":{"tf":1.0},"369":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.7320508075688772},"455":{"tf":1.0},"459":{"tf":1.0},"461":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"553":{"tf":1.0},"575":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"605":{"tf":1.0},"608":{"tf":1.0},"632":{"tf":1.0},"643":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.4142135623730951},"709":{"tf":1.0},"713":{"tf":1.4142135623730951},"714":{"tf":1.0},"735":{"tf":1.0},"799":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951},"928":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"935":{"tf":1.0},"959":{"tf":1.0},"966":{"tf":1.0}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"g":{"df":39,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"178":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"231":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"316":{"tf":1.0},"39":{"tf":1.7320508075688772},"410":{"tf":1.0},"417":{"tf":1.7320508075688772},"497":{"tf":1.0},"505":{"tf":1.0},"520":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"565":{"tf":1.4142135623730951},"567":{"tf":1.0},"575":{"tf":1.0},"69":{"tf":1.0},"696":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"763":{"tf":1.0},"767":{"tf":1.0},"770":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"797":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.4142135623730951},"898":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":31,"docs":{"1004":{"tf":1.0},"187":{"tf":1.0},"222":{"tf":1.0},"296":{"tf":1.0},"33":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"617":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"71":{"tf":1.0},"715":{"tf":1.0},"724":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"736":{"tf":1.4142135623730951},"75":{"tf":1.0},"763":{"tf":1.0},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"815":{"tf":1.0},"831":{"tf":1.4142135623730951},"895":{"tf":1.4142135623730951},"897":{"tf":1.4142135623730951},"898":{"tf":1.0},"912":{"tf":1.0},"928":{"tf":1.0},"956":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"565":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"773":{"tf":1.4142135623730951}}}}}}}},"o":{"df":0,"docs":{},"k":{"df":12,"docs":{"1004":{"tf":1.0},"390":{"tf":1.0},"455":{"tf":1.0},"521":{"tf":1.0},"567":{"tf":1.0},"61":{"tf":1.0},"619":{"tf":1.0},"629":{"tf":1.0},"634":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"725":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"880":{"tf":2.0}}}}},"p":{"df":3,"docs":{"485":{"tf":1.0},"715":{"tf":1.0},"721":{"tf":2.23606797749979}}},"s":{"df":3,"docs":{"251":{"tf":1.0},"816":{"tf":1.0},"874":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":6,"docs":{"577":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.0},"799":{"tf":1.0},"913":{"tf":1.0}}},"s":{"df":3,"docs":{"124":{"tf":1.0},"570":{"tf":1.0},"721":{"tf":1.0}}},"t":{"df":3,"docs":{"199":{"tf":1.0},"60":{"tf":1.0},"694":{"tf":1.0}}}},"t":{"'":{"df":1,"docs":{"60":{"tf":1.0}}},"df":9,"docs":{"194":{"tf":1.0},"251":{"tf":1.0},"417":{"tf":1.0},"523":{"tf":1.0},"534":{"tf":1.0},"586":{"tf":1.0},"656":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"323":{"tf":1.0}}}}}}},"w":{"df":21,"docs":{"163":{"tf":1.4142135623730951},"184":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"267":{"tf":1.0},"29":{"tf":1.0},"346":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.4142135623730951},"428":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"507":{"tf":1.0},"63":{"tf":1.4142135623730951},"69":{"tf":1.0},"711":{"tf":1.4142135623730951},"77":{"tf":1.0},"830":{"tf":1.0},"929":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":42,"docs":{"118":{"tf":1.0},"231":{"tf":1.0},"25":{"tf":1.0},"267":{"tf":1.0},"410":{"tf":2.23606797749979},"411":{"tf":1.7320508075688772},"412":{"tf":1.4142135623730951},"413":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":2.0},"417":{"tf":1.7320508075688772},"418":{"tf":1.4142135623730951},"419":{"tf":1.0},"42":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.4142135623730951},"423":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"471":{"tf":1.0},"540":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"640":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"725":{"tf":1.0},"747":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"810":{"tf":1.0},"829":{"tf":1.0},"881":{"tf":1.0},"992":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"776":{"tf":1.0}}}}}}},"r":{"a":{"df":4,"docs":{"567":{"tf":3.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"583":{"tf":1.0}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":1,"docs":{"957":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":2,"docs":{"940":{"tf":1.0},"945":{"tf":1.0}}}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":2,"docs":{"891":{"tf":1.0},"908":{"tf":1.0}}}}},"y":{"df":1,"docs":{"723":{"tf":1.0}}}},"m":{"a":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"198":{"tf":1.0},"368":{"tf":1.0},"402":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":3.4641016151377544}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"927":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"df":18,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"435":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"6":{"tf":1.0},"733":{"tf":1.0},"78":{"tf":1.0},"797":{"tf":1.0},"83":{"tf":1.0},"876":{"tf":1.0},"933":{"tf":1.0},"951":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":23,"docs":{"111":{"tf":1.0},"201":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"281":{"tf":1.0},"359":{"tf":1.0},"388":{"tf":1.0},"432":{"tf":1.0},"45":{"tf":1.0},"503":{"tf":2.0},"515":{"tf":1.0},"571":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"761":{"tf":2.23606797749979},"763":{"tf":1.0},"776":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"885":{"tf":1.0},"945":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"152":{"tf":1.0},"316":{"tf":1.0},"519":{"tf":1.0},"928":{"tf":1.0}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":32,"docs":{"234":{"tf":1.0},"24":{"tf":1.0},"248":{"tf":1.0},"249":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"282":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"316":{"tf":1.0},"344":{"tf":1.0},"375":{"tf":1.0},"389":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0},"47":{"tf":1.0},"482":{"tf":1.0},"486":{"tf":1.0},"505":{"tf":1.0},"565":{"tf":1.0},"767":{"tf":1.0},"777":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"855":{"tf":1.4142135623730951},"882":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"970":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":7,"docs":{"249":{"tf":1.7320508075688772},"274":{"tf":1.0},"282":{"tf":1.0},"316":{"tf":1.0},"317":{"tf":1.0},"945":{"tf":1.0},"962":{"tf":1.0}}}}}}},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":11,"docs":{"148":{"tf":1.0},"154":{"tf":1.0},"237":{"tf":1.0},"276":{"tf":1.0},"571":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"778":{"tf":1.0},"850":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":114,"docs":{"1014":{"tf":1.0},"121":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"218":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.4142135623730951},"272":{"tf":1.0},"281":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"333":{"tf":1.4142135623730951},"346":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"40":{"tf":1.0},"402":{"tf":1.4142135623730951},"414":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"423":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"456":{"tf":1.0},"460":{"tf":1.0},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"485":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.4142135623730951},"512":{"tf":1.4142135623730951},"514":{"tf":1.4142135623730951},"515":{"tf":1.0},"520":{"tf":1.0},"525":{"tf":1.0},"539":{"tf":1.4142135623730951},"564":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.4142135623730951},"576":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.0},"605":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"665":{"tf":1.0},"673":{"tf":1.0},"683":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.4142135623730951},"701":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"727":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.0},"75":{"tf":1.4142135623730951},"754":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":2.23606797749979},"763":{"tf":1.0},"77":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"788":{"tf":1.0},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"814":{"tf":1.4142135623730951},"826":{"tf":1.0},"832":{"tf":1.0},"836":{"tf":1.0},"843":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"849":{"tf":1.7320508075688772},"870":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":2.0},"881":{"tf":1.4142135623730951},"912":{"tf":1.0},"934":{"tf":1.4142135623730951},"942":{"tf":1.0},"979":{"tf":1.0},"990":{"tf":1.0},"992":{"tf":1.0}},"r":{"df":1,"docs":{"912":{"tf":1.0}}}},"o":{"df":0,"docs":{},"v":{"a":{"c":{"df":1,"docs":{"945":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"833":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":9,"docs":{"134":{"tf":1.0},"388":{"tf":1.0},"555":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.0},"721":{"tf":1.0},"763":{"tf":1.4142135623730951},"849":{"tf":1.0},"85":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"835":{"tf":1.0}}},"df":0,"docs":{}}}},"n":{"a":{"df":0,"docs":{},"g":{"df":43,"docs":{"113":{"tf":1.0},"121":{"tf":1.0},"137":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"199":{"tf":1.0},"219":{"tf":1.0},"234":{"tf":1.7320508075688772},"239":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"295":{"tf":1.4142135623730951},"296":{"tf":2.23606797749979},"297":{"tf":1.7320508075688772},"300":{"tf":2.23606797749979},"301":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.4142135623730951},"426":{"tf":1.0},"427":{"tf":1.0},"470":{"tf":1.0},"515":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"843":{"tf":1.7320508075688772},"848":{"tf":1.0},"849":{"tf":2.23606797749979},"850":{"tf":1.0},"855":{"tf":1.0},"874":{"tf":1.4142135623730951},"886":{"tf":1.0},"919":{"tf":1.0},"95":{"tf":1.4142135623730951},"961":{"tf":1.0},"968":{"tf":1.0}}}},"d":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"270":{"tf":1.0},"272":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":7,"docs":{"208":{"tf":1.0},"251":{"tf":1.0},"343":{"tf":2.23606797749979},"485":{"tf":1.0},"63":{"tf":1.0},"639":{"tf":1.0},"641":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":33,"docs":{"1004":{"tf":1.7320508075688772},"108":{"tf":1.7320508075688772},"218":{"tf":1.0},"231":{"tf":1.4142135623730951},"244":{"tf":1.0},"250":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"368":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"483":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.4142135623730951},"58":{"tf":1.0},"665":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.4142135623730951},"72":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.4142135623730951},"761":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"858":{"tf":1.0},"931":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0},"992":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":5,"docs":{"272":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"470":{"tf":1.0},"479":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":5,"docs":{"204":{"tf":2.0},"215":{"tf":1.0},"555":{"tf":1.0},"712":{"tf":1.0},"724":{"tf":1.4142135623730951}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"284":{"tf":1.0},"553":{"tf":1.0},"650":{"tf":1.0},"697":{"tf":1.0}}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"209":{"tf":1.0},"211":{"tf":1.0},"442":{"tf":1.0},"452":{"tf":1.0}}}},"df":0,"docs":{}}},"p":{"<":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}}},"df":14,"docs":{"208":{"tf":1.4142135623730951},"323":{"tf":1.0},"335":{"tf":1.0},"343":{"tf":1.0},"438":{"tf":1.4142135623730951},"439":{"tf":2.23606797749979},"440":{"tf":2.6457513110645907},"5":{"tf":1.4142135623730951},"522":{"tf":1.0},"6":{"tf":1.4142135623730951},"817":{"tf":1.0},"880":{"tf":1.4142135623730951},"944":{"tf":1.0},"951":{"tf":1.0}}},"r":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"122":{"tf":1.0},"535":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"776":{"tf":1.0}}}}},"k":{"df":5,"docs":{"356":{"tf":1.0},"633":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"721":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"t":{"'":{"df":2,"docs":{"199":{"tf":1.0},"418":{"tf":1.0}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"772":{"tf":1.0},"776":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":52,"docs":{"195":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"206":{"tf":2.0},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"212":{"tf":1.4142135623730951},"214":{"tf":1.0},"217":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"40":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"771":{"tf":2.6457513110645907},"772":{"tf":2.0},"773":{"tf":3.3166247903554},"774":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":3.872983346207417},"777":{"tf":2.8284271247461903},"778":{"tf":2.0},"779":{"tf":1.0},"780":{"tf":1.0},"781":{"tf":1.0},"912":{"tf":1.4142135623730951},"940":{"tf":2.23606797749979},"941":{"tf":1.4142135623730951},"942":{"tf":2.0},"943":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.4142135623730951},"946":{"tf":1.0},"947":{"tf":1.0},"948":{"tf":1.0},"949":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"954":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.4142135623730951},"958":{"tf":1.0}},"p":{"df":0,"docs":{},"l":{"a":{"c":{"df":5,"docs":{"414":{"tf":1.0},"911":{"tf":1.0},"943":{"tf":1.0},"956":{"tf":1.4142135623730951},"960":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"k":{"df":3,"docs":{"204":{"tf":2.0},"205":{"tf":3.872983346207417},"208":{"tf":6.6332495807108}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":14,"docs":{"184":{"tf":1.0},"331":{"tf":1.0},"351":{"tf":1.0},"45":{"tf":1.7320508075688772},"469":{"tf":1.0},"49":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":2.6457513110645907},"636":{"tf":1.4142135623730951},"786":{"tf":1.7320508075688772},"861":{"tf":1.0},"862":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"!":{"(":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":99,"docs":{"1":{"tf":1.0},"1001":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1015":{"tf":1.4142135623730951},"122":{"tf":1.0},"135":{"tf":1.4142135623730951},"136":{"tf":1.0},"149":{"tf":1.4142135623730951},"150":{"tf":1.0},"16":{"tf":1.4142135623730951},"163":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.4142135623730951},"182":{"tf":1.0},"194":{"tf":1.4142135623730951},"195":{"tf":1.0},"206":{"tf":1.0},"212":{"tf":1.4142135623730951},"215":{"tf":1.0},"226":{"tf":1.4142135623730951},"229":{"tf":1.0},"246":{"tf":1.4142135623730951},"247":{"tf":1.0},"262":{"tf":1.4142135623730951},"279":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"310":{"tf":1.4142135623730951},"311":{"tf":1.0},"321":{"tf":1.4142135623730951},"322":{"tf":1.0},"361":{"tf":1.4142135623730951},"366":{"tf":1.0},"37":{"tf":1.4142135623730951},"38":{"tf":1.0},"385":{"tf":1.4142135623730951},"386":{"tf":1.0},"399":{"tf":1.4142135623730951},"430":{"tf":1.0},"449":{"tf":1.4142135623730951},"451":{"tf":1.0},"464":{"tf":1.4142135623730951},"481":{"tf":1.0},"494":{"tf":1.4142135623730951},"495":{"tf":1.0},"512":{"tf":1.4142135623730951},"513":{"tf":1.0},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"54":{"tf":1.4142135623730951},"548":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.4142135623730951},"584":{"tf":1.0},"597":{"tf":1.4142135623730951},"598":{"tf":1.0},"612":{"tf":1.4142135623730951},"613":{"tf":1.0},"626":{"tf":1.4142135623730951},"627":{"tf":1.0},"648":{"tf":1.4142135623730951},"649":{"tf":1.0},"663":{"tf":1.4142135623730951},"664":{"tf":1.0},"677":{"tf":1.4142135623730951},"678":{"tf":1.0},"691":{"tf":1.4142135623730951},"692":{"tf":1.0},"708":{"tf":1.4142135623730951},"709":{"tf":1.0},"728":{"tf":1.4142135623730951},"757":{"tf":1.0},"76":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.4142135623730951},"808":{"tf":1.0},"826":{"tf":1.4142135623730951},"827":{"tf":1.0},"840":{"tf":1.4142135623730951},"871":{"tf":1.0},"890":{"tf":1.4142135623730951},"891":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":1.0},"92":{"tf":1.4142135623730951},"925":{"tf":1.4142135623730951},"926":{"tf":1.0},"939":{"tf":1.4142135623730951},"940":{"tf":1.0},"956":{"tf":1.4142135623730951},"957":{"tf":1.0},"973":{"tf":1.4142135623730951},"974":{"tf":1.0},"987":{"tf":1.4142135623730951},"988":{"tf":1.0}}}}},"h":{"b":{"b":{"df":0,"docs":{},"{":{"df":0,"docs":{},"i":{"df":1,"docs":{"45":{"tf":1.0}}},"p":{"df":1,"docs":{"45":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"340":{"tf":1.0},"428":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"723":{"tf":1.0}}}},"m":{"df":0,"docs":{},"{":{"1":{"df":1,"docs":{"417":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"722":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"54":{"tf":1.0}}}}},"x":{"(":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"d":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"_":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":5,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":2.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":3,"docs":{"568":{"tf":2.0},"570":{"tf":1.0},"571":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}}},"df":5,"docs":{"751":{"tf":1.0},"752":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"879":{"tf":1.0},"881":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"402":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"749":{"tf":1.0},"777":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"368":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":49,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":1.0},"253":{"tf":1.0},"30":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"388":{"tf":1.0},"417":{"tf":1.0},"47":{"tf":1.0},"471":{"tf":1.4142135623730951},"540":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"575":{"tf":1.0},"614":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"773":{"tf":1.0},"776":{"tf":2.0},"777":{"tf":1.4142135623730951},"829":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"879":{"tf":2.0},"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":2.23606797749979},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":1.7320508075688772},"899":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951}}}}}}},"y":{"b":{"df":6,"docs":{"257":{"tf":1.0},"304":{"tf":1.0},"507":{"tf":1.0},"521":{"tf":1.0},"714":{"tf":1.0},"880":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":3.0}}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"b":{"df":0,"docs":{},"m":{"df":15,"docs":{"279":{"tf":2.0},"280":{"tf":1.0},"281":{"tf":1.7320508075688772},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"df":60,"docs":{"114":{"tf":1.0},"139":{"tf":1.0},"155":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"169":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.4142135623730951},"269":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":1.4142135623730951},"303":{"tf":1.0},"373":{"tf":1.4142135623730951},"376":{"tf":1.0},"438":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"525":{"tf":1.0},"526":{"tf":1.0},"530":{"tf":1.0},"534":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"586":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"668":{"tf":1.0},"69":{"tf":1.0},"694":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"735":{"tf":1.0},"75":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"81":{"tf":1.0},"815":{"tf":1.4142135623730951},"880":{"tf":1.0},"929":{"tf":1.0},"932":{"tf":1.7320508075688772},"990":{"tf":1.0},"992":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"124":{"tf":1.0},"134":{"tf":1.0},"574":{"tf":1.0}}}}},"t":{"df":4,"docs":{"252":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"501":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"567":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":11,"docs":{"267":{"tf":1.0},"530":{"tf":1.0},"650":{"tf":1.0},"739":{"tf":1.0},"777":{"tf":1.0},"931":{"tf":1.0},"945":{"tf":1.0},"955":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"972":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":129,"docs":{"103":{"tf":1.0},"107":{"tf":1.0},"111":{"tf":1.0},"120":{"tf":1.0},"122":{"tf":2.23606797749979},"123":{"tf":1.4142135623730951},"124":{"tf":2.0},"125":{"tf":1.4142135623730951},"126":{"tf":2.0},"127":{"tf":1.7320508075688772},"128":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.4142135623730951},"133":{"tf":1.4142135623730951},"134":{"tf":1.0},"135":{"tf":1.0},"140":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":2.0},"229":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"24":{"tf":1.0},"243":{"tf":1.0},"251":{"tf":1.4142135623730951},"255":{"tf":2.8284271247461903},"257":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.4142135623730951},"294":{"tf":2.23606797749979},"295":{"tf":1.4142135623730951},"296":{"tf":1.0},"297":{"tf":1.0},"298":{"tf":1.0},"299":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.4142135623730951},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.0},"307":{"tf":1.0},"308":{"tf":1.0},"309":{"tf":1.0},"310":{"tf":1.4142135623730951},"35":{"tf":1.0},"365":{"tf":1.0},"404":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.0},"467":{"tf":1.0},"495":{"tf":2.0},"496":{"tf":1.7320508075688772},"497":{"tf":1.0},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":2.0},"506":{"tf":1.0},"507":{"tf":1.4142135623730951},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":2.23606797749979},"565":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.4142135623730951},"576":{"tf":1.0},"602":{"tf":1.0},"632":{"tf":1.0},"649":{"tf":2.0},"650":{"tf":1.0},"651":{"tf":1.0},"652":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.0},"655":{"tf":1.0},"656":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.0},"661":{"tf":1.0},"662":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":1.0},"665":{"tf":1.0},"69":{"tf":1.0},"705":{"tf":1.0},"72":{"tf":1.0},"722":{"tf":1.0},"73":{"tf":1.0},"743":{"tf":1.4142135623730951},"768":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.7320508075688772},"797":{"tf":1.0},"804":{"tf":1.0},"818":{"tf":1.0},"920":{"tf":1.0},"94":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"968":{"tf":1.0},"97":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.0},"987":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"413":{"tf":1.0},"567":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"i":{"a":{"df":3,"docs":{"270":{"tf":1.0},"3":{"tf":1.0},"847":{"tf":1.0}},"n":{"df":6,"docs":{"710":{"tf":1.0},"717":{"tf":1.7320508075688772},"721":{"tf":2.0},"722":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"184":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":6,"docs":{"1006":{"tf":1.0},"130":{"tf":1.0},"191":{"tf":1.0},"231":{"tf":1.0},"470":{"tf":1.0},"777":{"tf":1.0}}}},"g":{"a":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":5,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"832":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":16,"docs":{"111":{"tf":1.0},"113":{"tf":2.23606797749979},"121":{"tf":1.4142135623730951},"272":{"tf":2.449489742783178},"273":{"tf":1.4142135623730951},"466":{"tf":1.0},"467":{"tf":1.0},"468":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.4142135623730951},"573":{"tf":1.0},"81":{"tf":1.4142135623730951},"850":{"tf":1.0},"874":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"471":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":23,"docs":{"26":{"tf":1.4142135623730951},"28":{"tf":1.0},"450":{"tf":1.0},"483":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"730":{"tf":2.0},"731":{"tf":1.0},"732":{"tf":2.0},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":5.0},"736":{"tf":1.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"740":{"tf":1.0},"763":{"tf":1.0},"828":{"tf":1.0},"829":{"tf":2.23606797749979},"831":{"tf":3.3166247903554},"832":{"tf":1.7320508075688772},"840":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"k":{"df":1,"docs":{"244":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":9,"docs":{"16":{"tf":1.0},"170":{"tf":1.0},"499":{"tf":1.0},"534":{"tf":1.0},"752":{"tf":1.0},"761":{"tf":1.4142135623730951},"85":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":4,"docs":{"198":{"tf":1.0},"849":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}}},"g":{"df":4,"docs":{"269":{"tf":1.0},"291":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"207":{"tf":1.0}}}},"k":{"df":0,"docs":{},"l":{"df":14,"docs":{"439":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"46":{"tf":1.0},"49":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"519":{"tf":1.0},"525":{"tf":2.23606797749979},"634":{"tf":1.0},"759":{"tf":1.4142135623730951},"762":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"78":{"tf":1.7320508075688772}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"525":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":22,"docs":{"513":{"tf":2.23606797749979},"514":{"tf":1.4142135623730951},"515":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"518":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.0},"526":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"529":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"533":{"tf":1.0},"534":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":57,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"15":{"tf":1.0},"215":{"tf":1.4142135623730951},"218":{"tf":1.0},"220":{"tf":2.449489742783178},"221":{"tf":2.6457513110645907},"222":{"tf":2.0},"223":{"tf":1.4142135623730951},"253":{"tf":1.0},"38":{"tf":1.0},"450":{"tf":1.0},"54":{"tf":1.0},"553":{"tf":1.7320508075688772},"56":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"603":{"tf":1.0},"61":{"tf":2.6457513110645907},"619":{"tf":1.0},"62":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":3.3166247903554},"636":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"645":{"tf":1.7320508075688772},"651":{"tf":1.0},"670":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"709":{"tf":1.0},"716":{"tf":1.4142135623730951},"72":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"73":{"tf":1.0},"74":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":2.6457513110645907},"77":{"tf":1.0},"786":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"988":{"tf":2.23606797749979},"989":{"tf":1.4142135623730951},"990":{"tf":1.0},"991":{"tf":1.0},"992":{"tf":1.7320508075688772},"993":{"tf":1.0},"994":{"tf":1.0},"995":{"tf":1.0},"996":{"tf":1.0},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}},"e":{"1":{"df":1,"docs":{"633":{"tf":1.0}}},"2":{"df":1,"docs":{"633":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"'":{"df":1,"docs":{"516":{"tf":1.0}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"519":{"tf":1.0},"520":{"tf":2.23606797749979},"526":{"tf":1.7320508075688772},"534":{"tf":1.0}}}}}}}},"df":46,"docs":{"1":{"tf":2.23606797749979},"10":{"tf":1.0},"11":{"tf":1.0},"12":{"tf":1.4142135623730951},"13":{"tf":1.0},"14":{"tf":1.4142135623730951},"15":{"tf":1.0},"154":{"tf":1.0},"16":{"tf":2.0},"173":{"tf":1.0},"178":{"tf":1.0},"180":{"tf":1.7320508075688772},"2":{"tf":1.4142135623730951},"22":{"tf":2.449489742783178},"24":{"tf":1.0},"3":{"tf":4.795831523312719},"4":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"5":{"tf":3.4641016151377544},"513":{"tf":3.0},"514":{"tf":3.4641016151377544},"515":{"tf":3.4641016151377544},"516":{"tf":2.449489742783178},"517":{"tf":2.23606797749979},"518":{"tf":1.0},"519":{"tf":2.6457513110645907},"520":{"tf":3.0},"521":{"tf":2.23606797749979},"522":{"tf":1.0},"523":{"tf":2.0},"524":{"tf":2.0},"525":{"tf":1.0},"526":{"tf":3.605551275463989},"527":{"tf":1.0},"528":{"tf":2.8284271247461903},"529":{"tf":1.0},"530":{"tf":1.4142135623730951},"531":{"tf":1.4142135623730951},"532":{"tf":1.0},"533":{"tf":1.0},"534":{"tf":2.0},"6":{"tf":4.358898943540674},"7":{"tf":1.0},"8":{"tf":1.0},"9":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":2,"docs":{"15":{"tf":1.0},"5":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"15":{"tf":1.0},"5":{"tf":1.0},"6":{"tf":1.0}}}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"y":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"6":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.7320508075688772}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":2,"docs":{"22":{"tf":1.4142135623730951},"735":{"tf":1.4142135623730951}}},"df":1,"docs":{"467":{"tf":1.0}},"h":{"df":0,"docs":{},"o":{"d":{"df":15,"docs":{"121":{"tf":1.0},"140":{"tf":1.0},"177":{"tf":1.0},"196":{"tf":1.4142135623730951},"22":{"tf":2.0},"23":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"322":{"tf":1.0},"338":{"tf":1.0},"349":{"tf":2.449489742783178},"350":{"tf":1.0},"351":{"tf":2.23606797749979},"650":{"tf":1.0},"735":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"571":{"tf":1.0}}},"df":0,"docs":{}}}}},"i":{"b":{"df":6,"docs":{"515":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":2.23606797749979},"829":{"tf":1.0},"831":{"tf":1.0},"996":{"tf":1.0}}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"95":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":38,"docs":{"1012":{"tf":1.0},"108":{"tf":1.0},"146":{"tf":1.0},"151":{"tf":2.0},"155":{"tf":3.3166247903554},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"210":{"tf":1.0},"241":{"tf":1.0},"249":{"tf":1.4142135623730951},"269":{"tf":1.0},"279":{"tf":1.0},"281":{"tf":1.4142135623730951},"282":{"tf":1.0},"284":{"tf":2.0},"289":{"tf":1.0},"291":{"tf":1.0},"294":{"tf":1.0},"3":{"tf":1.0},"302":{"tf":2.0},"363":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":2.23606797749979},"374":{"tf":1.7320508075688772},"375":{"tf":2.8284271247461903},"376":{"tf":2.0},"512":{"tf":1.0},"575":{"tf":1.0},"609":{"tf":1.0},"73":{"tf":1.0},"813":{"tf":1.0},"872":{"tf":1.0},"887":{"tf":1.0},"953":{"tf":1.0},"970":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"567":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"931":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"n":{"(":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"568":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"d":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"568":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"750":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"568":{"tf":1.0},"569":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"194":{"tf":1.0},"846":{"tf":1.0}}}}}}}}}},"d":{"df":3,"docs":{"127":{"tf":1.0},"499":{"tf":1.0},"542":{"tf":1.0}},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":46,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0},"172":{"tf":1.0},"200":{"tf":1.0},"24":{"tf":1.0},"288":{"tf":1.0},"292":{"tf":1.0},"30":{"tf":1.0},"366":{"tf":2.0},"367":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"377":{"tf":1.0},"378":{"tf":1.0},"379":{"tf":1.0},"380":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.0},"384":{"tf":1.0},"385":{"tf":1.0},"41":{"tf":1.0},"438":{"tf":1.0},"53":{"tf":1.0},"537":{"tf":1.0},"544":{"tf":1.0},"605":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.0},"648":{"tf":1.0},"720":{"tf":1.0},"835":{"tf":1.0},"87":{"tf":1.0},"902":{"tf":1.0},"919":{"tf":1.0},"942":{"tf":1.0},"951":{"tf":1.0},"965":{"tf":1.0},"968":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":4,"docs":{"366":{"tf":1.0},"368":{"tf":1.0},"374":{"tf":1.0},"83":{"tf":1.0}}}},"u":{"df":0,"docs":{},"m":{"df":14,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"410":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"979":{"tf":1.0}}}},"t":{"df":3,"docs":{"411":{"tf":1.0},"931":{"tf":1.7320508075688772},"932":{"tf":1.4142135623730951}}},"u":{"df":2,"docs":{"500":{"tf":1.0},"573":{"tf":1.0}},"t":{"df":5,"docs":{"183":{"tf":1.0},"184":{"tf":1.0},"207":{"tf":1.0},"551":{"tf":1.0},"846":{"tf":1.7320508075688772}}}}},"s":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"v":{"df":2,"docs":{"439":{"tf":1.0},"564":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"564":{"tf":1.0},"567":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"849":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"l":{"df":1,"docs":{"567":{"tf":1.0}}},"m":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"777":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":11,"docs":{"121":{"tf":1.0},"208":{"tf":1.0},"238":{"tf":1.0},"437":{"tf":1.0},"60":{"tf":1.0},"721":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.4142135623730951},"761":{"tf":2.449489742783178},"78":{"tf":1.4142135623730951},"912":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"108":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":1,"docs":{"293":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":4,"docs":{"296":{"tf":1.0},"720":{"tf":1.4142135623730951},"81":{"tf":1.0},"84":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"81":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"s":{"df":3,"docs":{"141":{"tf":1.0},"81":{"tf":1.0},"919":{"tf":1.0}}}}},"t":{"df":1,"docs":{"741":{"tf":1.0}},"i":{"df":0,"docs":{},"g":{"df":11,"docs":{"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"144":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"441":{"tf":1.0},"567":{"tf":1.0},"583":{"tf":1.0},"63":{"tf":1.0},"77":{"tf":1.0},"965":{"tf":1.0}}}}},"x":{"df":3,"docs":{"365":{"tf":1.0},"598":{"tf":1.0},"603":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"365":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"426":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"u":{",":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"m":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}},"df":1,"docs":{"717":{"tf":1.0}}}},"o":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"95":{"tf":1.0}}}}},"d":{"df":2,"docs":{"814":{"tf":1.0},"83":{"tf":1.0}},"e":{"df":18,"docs":{"284":{"tf":1.0},"29":{"tf":1.0},"292":{"tf":1.0},"526":{"tf":2.0},"974":{"tf":2.0},"975":{"tf":1.0},"976":{"tf":1.0},"977":{"tf":1.0},"978":{"tf":1.4142135623730951},"979":{"tf":1.0},"980":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0},"985":{"tf":1.0},"986":{"tf":1.0},"987":{"tf":1.0}},"l":{"'":{"df":1,"docs":{"427":{"tf":1.0}}},"df":60,"docs":{"195":{"tf":1.0},"199":{"tf":1.4142135623730951},"214":{"tf":1.0},"216":{"tf":1.0},"243":{"tf":1.0},"246":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"402":{"tf":1.0},"410":{"tf":1.4142135623730951},"426":{"tf":1.4142135623730951},"427":{"tf":2.0},"428":{"tf":1.4142135623730951},"47":{"tf":1.0},"48":{"tf":1.7320508075688772},"49":{"tf":1.0},"51":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":2.0},"55":{"tf":1.0},"564":{"tf":1.0},"6":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":2.0},"744":{"tf":1.0},"747":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":2.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.4142135623730951},"808":{"tf":2.23606797749979},"809":{"tf":1.7320508075688772},"810":{"tf":2.8284271247461903},"811":{"tf":1.7320508075688772},"812":{"tf":1.0},"813":{"tf":2.0},"814":{"tf":2.0},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"819":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.4142135623730951},"823":{"tf":1.0},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"937":{"tf":1.0}}},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":1.7320508075688772}}}}},"i":{"df":0,"docs":{},"f":{"df":23,"docs":{"114":{"tf":1.0},"136":{"tf":1.0},"140":{"tf":1.4142135623730951},"142":{"tf":1.0},"182":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.7320508075688772},"6":{"tf":2.0},"786":{"tf":1.4142135623730951},"795":{"tf":2.23606797749979},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"798":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"801":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":1.0},"814":{"tf":1.0}},"i":{"df":28,"docs":{"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"137":{"tf":1.4142135623730951},"138":{"tf":1.0},"140":{"tf":1.0},"141":{"tf":1.0},"237":{"tf":1.0},"249":{"tf":1.0},"3":{"tf":2.0},"32":{"tf":1.0},"418":{"tf":1.0},"437":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"711":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"786":{"tf":1.0},"832":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0}}},"y":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":2.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"28":{"tf":1.0},"33":{"tf":1.0}}}},"df":7,"docs":{"112":{"tf":1.0},"23":{"tf":1.0},"270":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.0},"291":{"tf":1.0},"872":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"126":{"tf":1.4142135623730951},"254":{"tf":1.0},"387":{"tf":1.0},"398":{"tf":1.0},"436":{"tf":1.0},"815":{"tf":1.4142135623730951}},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":7,"docs":{"209":{"tf":1.0},"402":{"tf":1.0},"422":{"tf":1.0},"724":{"tf":1.0},"919":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"h":{"df":9,"docs":{"124":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":2.0},"374":{"tf":1.0},"778":{"tf":2.0},"843":{"tf":1.0},"911":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"466":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.4142135623730951}}}}}}},"o":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"105":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":142,"docs":{"103":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"139":{"tf":1.0},"155":{"tf":1.0},"16":{"tf":1.0},"160":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"194":{"tf":1.0},"199":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"216":{"tf":1.0},"217":{"tf":1.0},"223":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.0},"244":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"289":{"tf":1.0},"292":{"tf":1.0},"310":{"tf":1.0},"313":{"tf":1.0},"321":{"tf":1.0},"33":{"tf":1.0},"334":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"368":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"375":{"tf":1.0},"376":{"tf":1.0},"378":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":1.4142135623730951},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"439":{"tf":1.0},"444":{"tf":1.0},"453":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"483":{"tf":1.0},"486":{"tf":1.0},"496":{"tf":1.0},"500":{"tf":1.0},"503":{"tf":1.0},"507":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"534":{"tf":1.0},"535":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":2.23606797749979},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.4142135623730951},"574":{"tf":1.4142135623730951},"576":{"tf":1.0},"58":{"tf":2.23606797749979},"589":{"tf":1.0},"593":{"tf":1.0},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"61":{"tf":1.0},"628":{"tf":1.0},"63":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"668":{"tf":1.0},"711":{"tf":1.4142135623730951},"717":{"tf":1.0},"72":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"723":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.7320508075688772},"729":{"tf":1.4142135623730951},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"75":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.7320508075688772},"754":{"tf":1.0},"761":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"797":{"tf":1.0},"799":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":2.0},"831":{"tf":1.0},"832":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"885":{"tf":1.4142135623730951},"890":{"tf":1.0},"912":{"tf":1.4142135623730951},"913":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"94":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.7320508075688772},"97":{"tf":1.0},"973":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.4142135623730951},"990":{"tf":1.0}},"o":{"df":0,"docs":{},"v":{"df":2,"docs":{"47":{"tf":1.0},"84":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":3,"docs":{"331":{"tf":1.0},"515":{"tf":1.0},"571":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":132,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1004":{"tf":1.7320508075688772},"106":{"tf":1.0},"108":{"tf":1.4142135623730951},"122":{"tf":1.0},"124":{"tf":1.4142135623730951},"136":{"tf":1.0},"138":{"tf":1.4142135623730951},"150":{"tf":1.0},"152":{"tf":1.4142135623730951},"164":{"tf":1.0},"166":{"tf":1.4142135623730951},"17":{"tf":1.0},"182":{"tf":1.0},"184":{"tf":1.4142135623730951},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"197":{"tf":1.4142135623730951},"215":{"tf":1.0},"217":{"tf":1.7320508075688772},"229":{"tf":1.0},"231":{"tf":1.4142135623730951},"235":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.4142135623730951},"263":{"tf":1.0},"265":{"tf":1.4142135623730951},"267":{"tf":1.0},"268":{"tf":1.0},"270":{"tf":1.4142135623730951},"279":{"tf":1.0},"281":{"tf":1.7320508075688772},"284":{"tf":1.0},"294":{"tf":1.0},"296":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"30":{"tf":1.0},"311":{"tf":1.0},"313":{"tf":1.4142135623730951},"322":{"tf":1.0},"324":{"tf":1.4142135623730951},"366":{"tf":1.0},"368":{"tf":1.4142135623730951},"38":{"tf":1.0},"386":{"tf":1.0},"388":{"tf":1.4142135623730951},"40":{"tf":1.4142135623730951},"400":{"tf":1.0},"402":{"tf":1.4142135623730951},"410":{"tf":1.0},"412":{"tf":1.4142135623730951},"430":{"tf":1.0},"432":{"tf":1.4142135623730951},"451":{"tf":1.0},"453":{"tf":1.4142135623730951},"465":{"tf":1.0},"467":{"tf":1.7320508075688772},"481":{"tf":1.0},"483":{"tf":1.7320508075688772},"485":{"tf":1.0},"495":{"tf":1.0},"497":{"tf":1.4142135623730951},"513":{"tf":1.0},"515":{"tf":1.4142135623730951},"535":{"tf":1.0},"537":{"tf":1.4142135623730951},"546":{"tf":1.0},"549":{"tf":1.0},"551":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"565":{"tf":1.4142135623730951},"58":{"tf":1.4142135623730951},"584":{"tf":1.0},"586":{"tf":1.4142135623730951},"598":{"tf":1.0},"600":{"tf":1.4142135623730951},"613":{"tf":1.0},"615":{"tf":1.4142135623730951},"627":{"tf":1.0},"629":{"tf":1.4142135623730951},"649":{"tf":1.0},"651":{"tf":1.4142135623730951},"664":{"tf":1.0},"666":{"tf":1.4142135623730951},"678":{"tf":1.0},"680":{"tf":1.4142135623730951},"692":{"tf":1.0},"694":{"tf":1.4142135623730951},"709":{"tf":1.0},"711":{"tf":1.4142135623730951},"730":{"tf":1.0},"732":{"tf":1.4142135623730951},"741":{"tf":1.0},"743":{"tf":1.4142135623730951},"757":{"tf":1.0},"759":{"tf":1.4142135623730951},"771":{"tf":1.0},"773":{"tf":1.4142135623730951},"782":{"tf":1.0},"784":{"tf":1.7320508075688772},"79":{"tf":1.0},"795":{"tf":1.0},"797":{"tf":1.4142135623730951},"808":{"tf":1.0},"81":{"tf":1.4142135623730951},"810":{"tf":1.4142135623730951},"827":{"tf":1.0},"829":{"tf":1.4142135623730951},"841":{"tf":1.0},"843":{"tf":1.7320508075688772},"857":{"tf":1.0},"859":{"tf":1.4142135623730951},"871":{"tf":1.0},"873":{"tf":1.4142135623730951},"891":{"tf":1.0},"893":{"tf":1.4142135623730951},"908":{"tf":1.0},"910":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.4142135623730951},"93":{"tf":1.0},"940":{"tf":1.0},"942":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951},"957":{"tf":1.0},"959":{"tf":1.4142135623730951},"974":{"tf":1.0},"976":{"tf":1.4142135623730951},"988":{"tf":1.0},"990":{"tf":1.4142135623730951}}}}},"v":{"df":0,"docs":{},"e":{"df":36,"docs":{"150":{"tf":1.0},"151":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"156":{"tf":1.0},"163":{"tf":2.0},"175":{"tf":1.0},"214":{"tf":1.0},"230":{"tf":1.0},"24":{"tf":1.0},"293":{"tf":1.4142135623730951},"311":{"tf":1.0},"315":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.4142135623730951},"383":{"tf":1.0},"384":{"tf":1.0},"417":{"tf":1.0},"439":{"tf":1.0},"54":{"tf":1.0},"570":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"68":{"tf":1.0},"732":{"tf":1.0},"778":{"tf":1.0},"827":{"tf":1.0},"835":{"tf":1.0},"848":{"tf":1.4142135623730951},"932":{"tf":1.0},"985":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"g":{"df":2,"docs":{"735":{"tf":2.449489742783178},"97":{"tf":1.0}}}},"u":{"c":{"df":0,"docs":{},"h":{"df":27,"docs":{"255":{"tf":1.0},"261":{"tf":1.0},"272":{"tf":1.0},"371":{"tf":1.0},"418":{"tf":1.0},"46":{"tf":1.0},"503":{"tf":1.0},"511":{"tf":1.0},"568":{"tf":1.4142135623730951},"573":{"tf":1.0},"614":{"tf":1.4142135623730951},"619":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"669":{"tf":1.0},"694":{"tf":1.0},"735":{"tf":1.0},"751":{"tf":1.0},"779":{"tf":1.0},"790":{"tf":1.0},"853":{"tf":1.0},"863":{"tf":1.0},"874":{"tf":1.4142135623730951},"876":{"tf":1.0},"885":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"df":1,"docs":{"855":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"79":{"tf":1.0}}}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"d":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"253":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"198":{"tf":1.0}}}}},"df":14,"docs":{"155":{"tf":1.4142135623730951},"279":{"tf":1.0},"281":{"tf":1.0},"282":{"tf":1.0},"284":{"tf":1.0},"289":{"tf":1.0},"291":{"tf":1.0},"374":{"tf":1.0},"378":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":1.0},"95":{"tf":1.0}},"l":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"786":{"tf":1.7320508075688772}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":37,"docs":{"142":{"tf":1.0},"155":{"tf":1.0},"161":{"tf":1.0},"204":{"tf":1.0},"222":{"tf":1.0},"249":{"tf":1.0},"28":{"tf":1.0},"281":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"402":{"tf":1.4142135623730951},"48":{"tf":1.4142135623730951},"483":{"tf":1.0},"522":{"tf":2.23606797749979},"524":{"tf":1.0},"534":{"tf":1.4142135623730951},"599":{"tf":1.0},"600":{"tf":2.449489742783178},"602":{"tf":1.7320508075688772},"603":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"615":{"tf":1.4142135623730951},"649":{"tf":1.0},"693":{"tf":1.0},"696":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.4142135623730951},"78":{"tf":1.0},"799":{"tf":1.4142135623730951},"876":{"tf":1.7320508075688772},"881":{"tf":1.0},"912":{"tf":1.0}},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"483":{"tf":1.0}}}},"i":{"df":4,"docs":{"1003":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"776":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"879":{"tf":3.605551275463989},"885":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":22,"docs":{"784":{"tf":1.4142135623730951},"81":{"tf":1.4142135623730951},"871":{"tf":2.23606797749979},"872":{"tf":2.8284271247461903},"873":{"tf":1.0},"874":{"tf":4.0},"875":{"tf":3.605551275463989},"876":{"tf":2.0},"877":{"tf":1.0},"878":{"tf":2.8284271247461903},"879":{"tf":8.774964387392123},"880":{"tf":3.1622776601683795},"881":{"tf":2.6457513110645907},"882":{"tf":1.0},"883":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":3.605551275463989},"886":{"tf":1.7320508075688772},"887":{"tf":1.4142135623730951},"888":{"tf":1.4142135623730951},"889":{"tf":1.0},"890":{"tf":1.4142135623730951}},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"171":{"tf":1.0}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":3.872983346207417}}},"df":0,"docs":{}}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"715":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"208":{"tf":1.4142135623730951},"375":{"tf":1.0},"537":{"tf":1.0}}}},"df":2,"docs":{"23":{"tf":1.0},"717":{"tf":2.0}},"e":{"df":1,"docs":{"514":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"880":{"tf":1.0}}}}}}}}},"y":{"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{")":{".":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"(":{"df":0,"docs":{},"|":{"df":0,"docs":{},"l":{"df":1,"docs":{"717":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{")":{".":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"(":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"n":{"+":{"1":{"df":3,"docs":{"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951}}},"2":{"df":2,"docs":{"344":{"tf":1.0},"346":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"/":{"3":{"df":3,"docs":{"432":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0}}},"a":{"df":13,"docs":{"102":{"tf":1.0},"192":{"tf":1.0},"286":{"tf":1.4142135623730951},"474":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"647":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"98":{"tf":1.0}}},"df":0,"docs":{}},"=":{"3":{"df":0,"docs":{},"f":{"+":{"df":0,"docs":{},"k":{"df":1,"docs":{"436":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"2":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"/":{"3":{"df":2,"docs":{"435":{"tf":1.0},"438":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":2,"docs":{"432":{"tf":1.0},"438":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"a":{"df":2,"docs":{"578":{"tf":1.0},"579":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":3,"docs":{"432":{"tf":1.0},"450":{"tf":1.0},"732":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"df":50,"docs":{"171":{"tf":1.0},"207":{"tf":1.0},"22":{"tf":3.0},"23":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"253":{"tf":1.7320508075688772},"272":{"tf":1.0},"273":{"tf":1.0},"292":{"tf":1.7320508075688772},"3":{"tf":1.0},"373":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":1.0},"5":{"tf":1.0},"502":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"534":{"tf":1.0},"56":{"tf":2.0},"57":{"tf":1.0},"58":{"tf":1.0},"59":{"tf":1.0},"60":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"66":{"tf":1.0},"67":{"tf":1.0},"68":{"tf":1.0},"69":{"tf":1.0},"70":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0},"735":{"tf":2.23606797749979},"736":{"tf":1.0},"74":{"tf":1.4142135623730951},"748":{"tf":1.0},"75":{"tf":1.0},"76":{"tf":1.0},"761":{"tf":1.4142135623730951},"77":{"tf":1.0},"78":{"tf":1.0},"846":{"tf":1.0},"9":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"723":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":10,"docs":{"114":{"tf":1.0},"198":{"tf":1.0},"358":{"tf":1.0},"429":{"tf":1.0},"512":{"tf":1.0},"603":{"tf":2.0},"699":{"tf":1.0},"829":{"tf":2.23606797749979},"874":{"tf":1.0},"95":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"df":11,"docs":{"108":{"tf":1.0},"124":{"tf":1.0},"267":{"tf":1.4142135623730951},"429":{"tf":1.0},"48":{"tf":1.0},"514":{"tf":1.0},"551":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"776":{"tf":1.0}}}}},"y":{"df":2,"docs":{"188":{"tf":1.0},"75":{"tf":1.0}}}},"b":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{";":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"0":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":14,"docs":{"234":{"tf":1.4142135623730951},"332":{"tf":1.4142135623730951},"344":{"tf":2.23606797749979},"345":{"tf":1.0},"346":{"tf":2.6457513110645907},"436":{"tf":1.4142135623730951},"44":{"tf":1.4142135623730951},"45":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"721":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":2.23606797749979},"749":{"tf":2.0},"885":{"tf":2.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"203":{"tf":1.0}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":39,"docs":{"1010":{"tf":1.0},"1012":{"tf":1.0},"130":{"tf":1.0},"184":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"230":{"tf":1.0},"284":{"tf":1.0},"325":{"tf":1.0},"367":{"tf":1.0},"399":{"tf":1.0},"444":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.0},"516":{"tf":1.4142135623730951},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"54":{"tf":1.0},"573":{"tf":1.0},"609":{"tf":1.0},"651":{"tf":1.0},"653":{"tf":1.4142135623730951},"698":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"843":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.4142135623730951},"849":{"tf":1.0},"856":{"tf":1.0},"942":{"tf":1.0},"953":{"tf":1.0},"965":{"tf":1.0},"970":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"204":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"855":{"tf":1.0}}}}}}},"df":3,"docs":{"314":{"tf":1.0},"751":{"tf":1.0},"759":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":5,"docs":{"418":{"tf":1.0},"46":{"tf":1.0},"48":{"tf":1.0},"776":{"tf":1.0},"962":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"d":{"df":146,"docs":{"104":{"tf":1.0},"111":{"tf":1.0},"114":{"tf":1.0},"12":{"tf":1.0},"136":{"tf":1.0},"138":{"tf":1.4142135623730951},"140":{"tf":1.4142135623730951},"142":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.4142135623730951},"159":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"186":{"tf":1.0},"19":{"tf":1.0},"196":{"tf":1.4142135623730951},"200":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"209":{"tf":1.0},"231":{"tf":1.7320508075688772},"240":{"tf":1.0},"249":{"tf":2.0},"254":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"272":{"tf":1.4142135623730951},"288":{"tf":1.0},"33":{"tf":1.0},"35":{"tf":1.0},"368":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.4142135623730951},"374":{"tf":2.0},"375":{"tf":2.23606797749979},"381":{"tf":1.4142135623730951},"382":{"tf":1.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.0},"404":{"tf":1.0},"406":{"tf":1.0},"408":{"tf":1.0},"418":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"432":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"441":{"tf":1.4142135623730951},"446":{"tf":1.0},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.7320508075688772},"456":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.4142135623730951},"467":{"tf":1.0},"470":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"5":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":1.4142135623730951},"519":{"tf":1.0},"52":{"tf":1.4142135623730951},"521":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"526":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"57":{"tf":1.0},"573":{"tf":1.4142135623730951},"593":{"tf":1.0},"6":{"tf":1.0},"608":{"tf":1.0},"614":{"tf":1.0},"619":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"655":{"tf":1.0},"660":{"tf":1.4142135623730951},"666":{"tf":1.0},"673":{"tf":1.4142135623730951},"68":{"tf":1.4142135623730951},"69":{"tf":1.0},"700":{"tf":1.0},"71":{"tf":1.0},"710":{"tf":1.0},"72":{"tf":1.4142135623730951},"73":{"tf":1.0},"732":{"tf":1.7320508075688772},"736":{"tf":1.0},"739":{"tf":1.0},"743":{"tf":1.4142135623730951},"751":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"773":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.4142135623730951},"781":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.7320508075688772},"849":{"tf":2.0},"850":{"tf":1.0},"853":{"tf":1.0},"858":{"tf":1.0},"864":{"tf":1.0},"874":{"tf":1.7320508075688772},"876":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":3.3166247903554},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":2.0},"932":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"942":{"tf":1.0},"947":{"tf":1.0},"955":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"60":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"f":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"206":{"tf":1.0}}}}},"df":0,"docs":{}},"g":{"df":6,"docs":{"1004":{"tf":1.0},"187":{"tf":1.4142135623730951},"30":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"422":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"593":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"574":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":13,"docs":{"257":{"tf":1.0},"288":{"tf":1.0},"507":{"tf":1.0},"554":{"tf":1.0},"60":{"tf":1.0},"640":{"tf":1.0},"712":{"tf":1.0},"720":{"tf":1.0},"739":{"tf":1.0},"835":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"796":{"tf":1.0},"799":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.4142135623730951},"931":{"tf":1.0}}}},"t":{"df":5,"docs":{"211":{"tf":1.0},"267":{"tf":1.0},"700":{"tf":1.0},"800":{"tf":1.0},"835":{"tf":1.0}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"'":{"df":4,"docs":{"274":{"tf":1.0},"371":{"tf":1.0},"418":{"tf":1.0},"426":{"tf":1.0}}},"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"786":{"tf":1.0}}},"df":0,"docs":{}}},"df":86,"docs":{"0":{"tf":1.0},"1004":{"tf":1.0},"111":{"tf":1.0},"124":{"tf":1.0},"128":{"tf":1.0},"139":{"tf":1.0},"147":{"tf":1.0},"152":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"247":{"tf":1.0},"248":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":2.0},"254":{"tf":2.0},"257":{"tf":1.0},"267":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":2.0},"273":{"tf":1.0},"314":{"tf":1.4142135623730951},"316":{"tf":1.4142135623730951},"356":{"tf":1.0},"358":{"tf":1.0},"365":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"376":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.7320508075688772},"430":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"439":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"512":{"tf":1.0},"515":{"tf":1.4142135623730951},"532":{"tf":1.0},"54":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"555":{"tf":1.0},"559":{"tf":1.0},"565":{"tf":1.0},"577":{"tf":1.0},"60":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"71":{"tf":1.4142135623730951},"720":{"tf":1.0},"743":{"tf":1.0},"757":{"tf":2.23606797749979},"758":{"tf":1.4142135623730951},"759":{"tf":2.23606797749979},"760":{"tf":1.0},"761":{"tf":2.449489742783178},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"764":{"tf":1.0},"765":{"tf":1.0},"766":{"tf":1.0},"767":{"tf":1.4142135623730951},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.4142135623730951},"784":{"tf":1.0},"797":{"tf":2.6457513110645907},"799":{"tf":1.7320508075688772},"807":{"tf":1.0},"819":{"tf":1.0},"990":{"tf":1.4142135623730951},"996":{"tf":1.0}},"i":{"d":{":":{":":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":2,"docs":{"680":{"tf":1.0},"688":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":1,"docs":{"689":{"tf":1.0}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"df":1,"docs":{"688":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"688":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":14,"docs":{"678":{"tf":2.23606797749979},"679":{"tf":1.4142135623730951},"680":{"tf":1.0},"681":{"tf":1.0},"682":{"tf":1.4142135623730951},"683":{"tf":1.0},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0},"689":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"700":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"204":{"tf":1.0},"302":{"tf":1.4142135623730951},"308":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":2.0},"912":{"tf":1.0}}}}},"w":{"/":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"618":{"tf":1.0}}}}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"207":{"tf":1.7320508075688772},"750":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.449489742783178}}},"df":0,"docs":{}}}}}}}}},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"568":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":196,"docs":{"1":{"tf":1.0},"1004":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"118":{"tf":1.0},"125":{"tf":1.0},"13":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"151":{"tf":2.449489742783178},"154":{"tf":1.4142135623730951},"155":{"tf":1.7320508075688772},"158":{"tf":1.0},"160":{"tf":1.0},"166":{"tf":1.4142135623730951},"171":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"191":{"tf":1.0},"203":{"tf":1.4142135623730951},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"209":{"tf":1.0},"211":{"tf":1.0},"221":{"tf":1.0},"225":{"tf":1.0},"24":{"tf":1.4142135623730951},"247":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.7320508075688772},"255":{"tf":1.0},"261":{"tf":1.0},"268":{"tf":2.23606797749979},"269":{"tf":2.449489742783178},"270":{"tf":2.0},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.4142135623730951},"275":{"tf":1.0},"276":{"tf":2.0},"277":{"tf":1.0},"278":{"tf":1.0},"281":{"tf":1.0},"286":{"tf":1.0},"289":{"tf":1.0},"296":{"tf":1.4142135623730951},"3":{"tf":1.0},"301":{"tf":1.0},"303":{"tf":1.0},"306":{"tf":1.0},"32":{"tf":1.0},"333":{"tf":1.4142135623730951},"34":{"tf":1.0},"343":{"tf":1.0},"371":{"tf":1.4142135623730951},"373":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"381":{"tf":1.0},"387":{"tf":1.0},"390":{"tf":1.0},"40":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":2.23606797749979},"450":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"457":{"tf":1.0},"461":{"tf":1.4142135623730951},"482":{"tf":1.0},"486":{"tf":1.0},"491":{"tf":1.0},"5":{"tf":1.0},"511":{"tf":1.0},"53":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":2.23606797749979},"540":{"tf":1.0},"542":{"tf":1.0},"545":{"tf":1.0},"551":{"tf":2.23606797749979},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"559":{"tf":2.0},"56":{"tf":1.7320508075688772},"564":{"tf":2.0},"565":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.4142135623730951},"598":{"tf":2.23606797749979},"599":{"tf":1.4142135623730951},"6":{"tf":2.449489742783178},"600":{"tf":1.4142135623730951},"601":{"tf":1.0},"602":{"tf":2.0},"603":{"tf":1.0},"604":{"tf":1.0},"605":{"tf":1.4142135623730951},"606":{"tf":1.4142135623730951},"607":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.7320508075688772},"61":{"tf":1.7320508075688772},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"619":{"tf":1.7320508075688772},"62":{"tf":1.4142135623730951},"63":{"tf":2.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":2.23606797749979},"635":{"tf":1.0},"639":{"tf":1.0},"64":{"tf":1.7320508075688772},"641":{"tf":1.4142135623730951},"642":{"tf":1.4142135623730951},"643":{"tf":1.4142135623730951},"644":{"tf":2.0},"645":{"tf":1.0},"646":{"tf":1.0},"65":{"tf":1.4142135623730951},"650":{"tf":1.7320508075688772},"651":{"tf":1.0},"653":{"tf":1.7320508075688772},"654":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"668":{"tf":1.4142135623730951},"67":{"tf":1.4142135623730951},"673":{"tf":1.0},"69":{"tf":1.4142135623730951},"698":{"tf":1.0},"7":{"tf":1.0},"705":{"tf":2.23606797749979},"72":{"tf":1.0},"73":{"tf":2.0},"730":{"tf":1.0},"735":{"tf":3.605551275463989},"736":{"tf":1.4142135623730951},"738":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"761":{"tf":1.7320508075688772},"772":{"tf":1.0},"8":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":1.7320508075688772},"813":{"tf":1.7320508075688772},"814":{"tf":2.0},"815":{"tf":1.4142135623730951},"817":{"tf":1.4142135623730951},"819":{"tf":1.4142135623730951},"843":{"tf":1.0},"846":{"tf":1.0},"853":{"tf":1.0},"860":{"tf":1.4142135623730951},"874":{"tf":1.0},"879":{"tf":3.872983346207417},"882":{"tf":1.0},"9":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.7320508075688772},"931":{"tf":1.0},"932":{"tf":2.6457513110645907},"933":{"tf":1.0},"935":{"tf":1.0},"936":{"tf":1.0},"94":{"tf":1.0},"944":{"tf":1.7320508075688772},"945":{"tf":1.0},"947":{"tf":1.0},"949":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"969":{"tf":1.0},"97":{"tf":1.0},"987":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"512":{"tf":1.0},"550":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"553":{"tf":1.4142135623730951},"637":{"tf":1.0},"640":{"tf":1.0}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"843":{"tf":1.0}}},"df":0,"docs":{}}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"249":{"tf":1.0},"47":{"tf":1.0},"571":{"tf":1.4142135623730951},"735":{"tf":1.0},"928":{"tf":1.0}}}}},"x":{"df":0,"docs":{},"t":{"df":24,"docs":{"126":{"tf":1.0},"151":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"170":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"327":{"tf":1.0},"343":{"tf":1.4142135623730951},"344":{"tf":1.0},"345":{"tf":1.4142135623730951},"347":{"tf":1.0},"350":{"tf":1.0},"385":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"483":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"735":{"tf":2.8284271247461903},"776":{"tf":1.4142135623730951},"848":{"tf":1.0},"879":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"345":{"tf":1.7320508075688772}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"f":{"df":0,"docs":{},"t":{"df":28,"docs":{"208":{"tf":1.0},"3":{"tf":3.3166247903554},"410":{"tf":2.0},"411":{"tf":2.0},"412":{"tf":2.23606797749979},"413":{"tf":1.0},"414":{"tf":2.23606797749979},"415":{"tf":1.4142135623730951},"416":{"tf":1.4142135623730951},"417":{"tf":1.7320508075688772},"418":{"tf":1.4142135623730951},"419":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"423":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.4142135623730951},"426":{"tf":1.0},"427":{"tf":1.4142135623730951},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"5":{"tf":1.4142135623730951},"6":{"tf":1.4142135623730951},"7":{"tf":1.0},"8":{"tf":1.0},"912":{"tf":1.0},"956":{"tf":1.0}},"s":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"416":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"415":{"tf":1.0},"416":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"b":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"i":{"b":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"761":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"e":{"df":3,"docs":{"281":{"tf":1.0},"721":{"tf":1.0},"78":{"tf":1.0}}}},"df":1,"docs":{"370":{"tf":1.0}},"l":{"df":1,"docs":{"885":{"tf":1.7320508075688772}}},"s":{"df":0,"docs":{},"t":{"df":13,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951},"96":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0}}}},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":1,"docs":{"38":{"tf":1.0}}}}}}},"o":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":84,"docs":{"152":{"tf":1.4142135623730951},"153":{"tf":1.4142135623730951},"154":{"tf":1.7320508075688772},"159":{"tf":1.0},"160":{"tf":2.0},"231":{"tf":1.0},"233":{"tf":1.0},"248":{"tf":1.7320508075688772},"249":{"tf":2.8284271247461903},"251":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":2.23606797749979},"257":{"tf":2.23606797749979},"290":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.4142135623730951},"404":{"tf":1.0},"406":{"tf":1.0},"409":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.7320508075688772},"452":{"tf":1.0},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":1.0},"461":{"tf":1.0},"495":{"tf":2.23606797749979},"496":{"tf":1.4142135623730951},"497":{"tf":3.605551275463989},"498":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":2.6457513110645907},"501":{"tf":2.23606797749979},"502":{"tf":1.7320508075688772},"503":{"tf":2.0},"504":{"tf":1.0},"505":{"tf":2.0},"506":{"tf":1.0},"507":{"tf":2.449489742783178},"508":{"tf":1.0},"509":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":2.6457513110645907},"525":{"tf":4.0},"532":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":2.23606797749979},"552":{"tf":1.0},"553":{"tf":2.8284271247461903},"554":{"tf":1.0},"555":{"tf":1.4142135623730951},"559":{"tf":1.0},"567":{"tf":1.7320508075688772},"59":{"tf":1.0},"61":{"tf":1.0},"630":{"tf":1.0},"635":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.7320508075688772},"68":{"tf":1.4142135623730951},"71":{"tf":1.4142135623730951},"711":{"tf":1.0},"720":{"tf":1.4142135623730951},"735":{"tf":1.0},"759":{"tf":2.6457513110645907},"761":{"tf":1.7320508075688772},"763":{"tf":1.4142135623730951},"990":{"tf":1.4142135623730951},"991":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"440":{"tf":1.0}}}}}},"df":0,"docs":{}}},"s":{".":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"525":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"525":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"525":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"_":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"525":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"b":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"3":{":":{":":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"(":{"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"(":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"525":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"724":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":23,"docs":{"1002":{"tf":2.23606797749979},"1003":{"tf":2.449489742783178},"1004":{"tf":3.0},"1005":{"tf":1.4142135623730951},"1006":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.0},"205":{"tf":1.0},"370":{"tf":1.0},"373":{"tf":1.0},"51":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":2.23606797749979},"577":{"tf":1.0},"724":{"tf":1.0}}}},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"c":{"df":3,"docs":{"521":{"tf":1.0},"54":{"tf":1.0},"880":{"tf":1.0}}},"df":32,"docs":{"1007":{"tf":1.0},"151":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"2":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.0},"231":{"tf":1.0},"249":{"tf":1.4142135623730951},"281":{"tf":1.0},"284":{"tf":1.0},"332":{"tf":1.0},"373":{"tf":1.4142135623730951},"38":{"tf":1.0},"39":{"tf":1.0},"416":{"tf":1.0},"51":{"tf":1.0},"54":{"tf":1.4142135623730951},"573":{"tf":1.0},"631":{"tf":1.0},"7":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":2.23606797749979},"776":{"tf":1.0},"81":{"tf":1.0},"842":{"tf":1.0},"85":{"tf":1.0},"9":{"tf":1.0},"938":{"tf":1.0},"947":{"tf":1.0}},"e":{"df":67,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"162":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"227":{"tf":1.0},"228":{"tf":1.0},"245":{"tf":1.0},"260":{"tf":1.0},"278":{"tf":1.0},"309":{"tf":1.0},"320":{"tf":1.0},"353":{"tf":1.0},"360":{"tf":1.0},"462":{"tf":1.0},"463":{"tf":1.0},"480":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"504":{"tf":1.0},"526":{"tf":1.0},"533":{"tf":1.0},"547":{"tf":1.0},"55":{"tf":1.0},"559":{"tf":1.0},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"602":{"tf":1.4142135623730951},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"662":{"tf":1.0},"672":{"tf":1.0},"674":{"tf":1.0},"676":{"tf":1.0},"677":{"tf":1.0},"684":{"tf":1.0},"686":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0},"707":{"tf":1.0},"726":{"tf":1.0},"735":{"tf":1.0},"753":{"tf":1.0},"761":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"825":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"880":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"976":{"tf":1.0},"986":{"tf":1.0},"993":{"tf":1.0},"997":{"tf":1.0},"999":{"tf":1.0}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"16":{"tf":1.0},"254":{"tf":1.0}}}}}}}}}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"205":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"6":{"tf":2.23606797749979}}}}}}},"r":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"221":{"tf":1.0},"292":{"tf":1.0},"346":{"tf":1.0},"416":{"tf":1.0},"47":{"tf":1.0},"571":{"tf":1.0},"701":{"tf":1.0}}}},"df":1,"docs":{"427":{"tf":1.0}}}},"s":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"439":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"375":{"tf":1.0},"46":{"tf":1.0},"779":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"322":{"tf":1.0},"330":{"tf":1.7320508075688772}}}},"df":0,"docs":{},"e":{"df":49,"docs":{"170":{"tf":1.0},"195":{"tf":1.7320508075688772},"204":{"tf":1.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"22":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"3":{"tf":1.0},"301":{"tf":1.0},"315":{"tf":1.0},"341":{"tf":1.0},"348":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"420":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"471":{"tf":1.0},"523":{"tf":1.0},"564":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"602":{"tf":1.4142135623730951},"697":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"761":{"tf":1.7320508075688772},"763":{"tf":1.0},"776":{"tf":1.4142135623730951},"817":{"tf":1.0},"826":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.7320508075688772},"938":{"tf":1.0}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":1,"docs":{"315":{"tf":1.0}}}}}}}}},"h":{"df":4,"docs":{"170":{"tf":1.0},"522":{"tf":1.4142135623730951},"723":{"tf":1.0},"855":{"tf":1.0}}},"i":{"c":{"df":5,"docs":{"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"450":{"tf":1.4142135623730951},"63":{"tf":1.0},"8":{"tf":1.0}}},"df":0,"docs":{},"f":{"df":15,"docs":{"208":{"tf":1.0},"481":{"tf":2.23606797749979},"482":{"tf":2.0},"483":{"tf":1.7320508075688772},"484":{"tf":1.0},"485":{"tf":3.0},"486":{"tf":1.7320508075688772},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.4142135623730951},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0}},"i":{"df":3,"docs":{"218":{"tf":1.4142135623730951},"222":{"tf":1.0},"60":{"tf":1.0}}},"y":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":2,"docs":{"221":{"tf":1.0},"222":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":2,"docs":{"221":{"tf":1.4142135623730951},"222":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"222":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"234":{"tf":1.0},"3":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"v":{"a":{"df":3,"docs":{"191":{"tf":1.0},"804":{"tf":1.0},"853":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"323":{"tf":1.0}}},"m":{"b":{"df":5,"docs":{"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"808":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"df":29,"docs":{"140":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"29":{"tf":1.0},"3":{"tf":1.0},"46":{"tf":1.0},"485":{"tf":1.0},"537":{"tf":1.0},"573":{"tf":1.0},"605":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.7320508075688772},"651":{"tf":1.0},"653":{"tf":1.0},"697":{"tf":1.0},"701":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"75":{"tf":1.0},"767":{"tf":1.0},"776":{"tf":1.0},"831":{"tf":1.0},"885":{"tf":1.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0},"983":{"tf":1.0}}}},"p":{"df":0,"docs":{},"o":{"df":3,"docs":{"1004":{"tf":1.0},"374":{"tf":1.0},"571":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"234":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":1,"docs":{"207":{"tf":1.0}}}},"m":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"715":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":78,"docs":{"132":{"tf":1.0},"172":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":2.0},"205":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":2.0},"218":{"tf":1.4142135623730951},"221":{"tf":2.449489742783178},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"237":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.7320508075688772},"255":{"tf":1.0},"333":{"tf":1.0},"342":{"tf":2.23606797749979},"346":{"tf":2.6457513110645907},"347":{"tf":1.4142135623730951},"348":{"tf":1.7320508075688772},"349":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.4142135623730951},"428":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.0},"459":{"tf":1.0},"47":{"tf":2.23606797749979},"500":{"tf":1.0},"505":{"tf":1.0},"51":{"tf":1.4142135623730951},"520":{"tf":1.0},"525":{"tf":1.4142135623730951},"537":{"tf":1.0},"568":{"tf":1.7320508075688772},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"631":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"723":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.3166247903554},"742":{"tf":1.4142135623730951},"743":{"tf":1.4142135623730951},"744":{"tf":1.4142135623730951},"747":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.7320508075688772},"751":{"tf":1.4142135623730951},"758":{"tf":1.0},"761":{"tf":1.7320508075688772},"814":{"tf":1.0},"829":{"tf":1.0},"85":{"tf":1.0},"858":{"tf":1.0},"87":{"tf":1.0},"879":{"tf":3.1622776601683795},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"221":{"tf":1.0},"427":{"tf":1.0},"55":{"tf":1.0}}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"668":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":2,"docs":{"435":{"tf":1.0},"553":{"tf":1.0}}}}}}}},"}":{"df":0,"docs":{},"{":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}},"}":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{")":{"^":{"d":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"749":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"o":{"[":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}}}},"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"537":{"tf":1.0}}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"231":{"tf":1.0},"255":{"tf":1.0},"3":{"tf":2.0},"333":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951},"352":{"tf":1.0},"390":{"tf":1.0},"411":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"776":{"tf":1.0}}}}},"s":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"833":{"tf":1.0},"874":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":6,"docs":{"450":{"tf":1.0},"555":{"tf":1.0},"571":{"tf":1.0},"724":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":10,"docs":{"193":{"tf":1.0},"254":{"tf":1.0},"567":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"739":{"tf":1.0},"759":{"tf":1.0},"84":{"tf":1.0},"88":{"tf":1.0}}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":3,"docs":{"234":{"tf":1.0},"571":{"tf":1.0},"732":{"tf":1.0}}}}}}},"c":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"450":{"tf":1.0}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"234":{"tf":1.0}},"i":{"df":7,"docs":{"441":{"tf":1.0},"450":{"tf":2.23606797749979},"60":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"724":{"tf":1.0},"77":{"tf":1.0}}}},"r":{"df":13,"docs":{"111":{"tf":1.0},"204":{"tf":1.0},"267":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"573":{"tf":1.0},"670":{"tf":1.0},"751":{"tf":1.0},"776":{"tf":1.4142135623730951},"804":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"95":{"tf":1.0}},"r":{"df":2,"docs":{"108":{"tf":1.0},"441":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"1":{"tf":1.0},"17":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"332":{"tf":1.7320508075688772},"333":{"tf":1.4142135623730951}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":6,"docs":{"332":{"tf":1.0},"333":{"tf":2.6457513110645907},"341":{"tf":3.0},"343":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"<":{"3":{"2":{"df":4,"docs":{"333":{"tf":1.0},"341":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.0}}},"df":0,"docs":{}},"4":{"df":1,"docs":{"343":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"o":{"b":{"df":6,"docs":{"164":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"782":{"tf":1.0},"795":{"tf":1.0}}},"df":0,"docs":{}}}},"df":2,"docs":{"112":{"tf":1.4142135623730951},"45":{"tf":1.0}},"e":{"c":{"d":{"df":4,"docs":{"466":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.0},"479":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"f":{"3":{"df":0,"docs":{},"x":{"df":1,"docs":{"575":{"tf":1.0}}}},"df":0,"docs":{},"f":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"459":{"tf":1.0},"735":{"tf":1.0},"739":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":1,"docs":{"779":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"372":{"tf":1.0},"375":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"376":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"d":{"df":1,"docs":{"573":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":25,"docs":{"121":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.0},"267":{"tf":1.0},"3":{"tf":1.0},"328":{"tf":1.0},"340":{"tf":1.4142135623730951},"346":{"tf":1.0},"368":{"tf":1.7320508075688772},"412":{"tf":1.0},"429":{"tf":1.0},"521":{"tf":1.4142135623730951},"55":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"577":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"77":{"tf":1.0},"772":{"tf":1.0},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"826":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"912":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":13,"docs":{"346":{"tf":1.4142135623730951},"514":{"tf":2.6457513110645907},"515":{"tf":3.0},"516":{"tf":1.0},"518":{"tf":1.7320508075688772},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"526":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.0},"534":{"tf":1.4142135623730951}}}},"o":{"a":{"d":{"df":1,"docs":{"843":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"349":{"tf":1.0},"633":{"tf":2.0},"637":{"tf":1.0},"735":{"tf":2.8284271247461903}}}}}}},"l":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":2,"docs":{"122":{"tf":1.0},"136":{"tf":1.0}}}}},"d":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":4,"docs":{"207":{"tf":2.449489742783178},"749":{"tf":1.4142135623730951},"750":{"tf":1.7320508075688772},"752":{"tf":2.0}}},"df":0,"docs":{}}}}},"df":21,"docs":{"151":{"tf":1.0},"205":{"tf":1.7320508075688772},"221":{"tf":1.0},"3":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.7320508075688772},"559":{"tf":1.4142135623730951},"567":{"tf":1.0},"575":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"619":{"tf":1.0},"632":{"tf":1.0},"635":{"tf":1.0},"67":{"tf":1.0},"705":{"tf":1.0},"73":{"tf":1.0},"983":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"440":{"tf":1.4142135623730951},"500":{"tf":1.0},"512":{"tf":1.4142135623730951},"553":{"tf":1.0},"559":{"tf":1.0},"609":{"tf":1.7320508075688772},"631":{"tf":1.0},"640":{"tf":1.0},"642":{"tf":1.0},"740":{"tf":1.0},"767":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"279":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"_":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"t":{"df":7,"docs":{"16":{"tf":1.0},"439":{"tf":1.0},"516":{"tf":1.0},"526":{"tf":1.0},"633":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":1,"docs":{"198":{"tf":1.0}}}}}}}}},"n":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"281":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"281":{"tf":1.0}}}}}}}},"b":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"r":{"d":{"df":5,"docs":{"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"301":{"tf":1.0},"414":{"tf":1.0},"928":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"c":{"df":34,"docs":{"1003":{"tf":1.0},"106":{"tf":1.0},"126":{"tf":2.0},"187":{"tf":1.0},"204":{"tf":1.0},"206":{"tf":1.4142135623730951},"208":{"tf":1.0},"270":{"tf":1.0},"346":{"tf":1.0},"432":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"534":{"tf":1.0},"605":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"644":{"tf":1.4142135623730951},"67":{"tf":1.0},"71":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":1.7320508075688772},"739":{"tf":1.0},"759":{"tf":1.0},"77":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"816":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"936":{"tf":1.0}},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"303":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"61":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":140,"docs":{"1004":{"tf":1.0},"124":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"177":{"tf":1.0},"188":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"214":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"234":{"tf":1.0},"254":{"tf":1.7320508075688772},"257":{"tf":1.0},"267":{"tf":1.0},"276":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"302":{"tf":1.0},"303":{"tf":1.0},"314":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"351":{"tf":1.0},"356":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"388":{"tf":1.4142135623730951},"417":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"481":{"tf":2.23606797749979},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"484":{"tf":1.0},"485":{"tf":2.23606797749979},"486":{"tf":1.4142135623730951},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.4142135623730951},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":2.0},"524":{"tf":1.7320508075688772},"525":{"tf":1.0},"526":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.0},"554":{"tf":1.0},"565":{"tf":1.0},"586":{"tf":1.0},"589":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.0},"600":{"tf":1.7320508075688772},"615":{"tf":1.0},"632":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.4142135623730951},"653":{"tf":1.0},"659":{"tf":1.4142135623730951},"665":{"tf":1.0},"67":{"tf":1.4142135623730951},"673":{"tf":1.4142135623730951},"69":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.0},"705":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":1.7320508075688772},"718":{"tf":1.0},"720":{"tf":2.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.7320508075688772},"749":{"tf":1.0},"751":{"tf":1.0},"757":{"tf":1.0},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"770":{"tf":1.0},"778":{"tf":2.0},"779":{"tf":1.0},"78":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":1.0},"80":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.4142135623730951},"815":{"tf":1.0},"822":{"tf":1.0},"829":{"tf":1.0},"83":{"tf":1.0},"832":{"tf":1.4142135623730951},"835":{"tf":1.0},"837":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.0},"855":{"tf":1.0},"879":{"tf":2.6457513110645907},"885":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"928":{"tf":1.4142135623730951},"933":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"976":{"tf":1.0}},"g":{"df":0,"docs":{},"o":{"df":7,"docs":{"124":{"tf":1.0},"126":{"tf":2.0},"132":{"tf":1.0},"148":{"tf":1.7320508075688772},"200":{"tf":1.0},"208":{"tf":1.0},"249":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"514":{"tf":1.7320508075688772}}}},"y":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"284":{"tf":1.7320508075688772},"286":{"tf":1.0},"292":{"tf":1.0}}}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":2.449489742783178}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"b":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"761":{"tf":2.23606797749979}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"o":{"df":7,"docs":{"199":{"tf":1.0},"217":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"522":{"tf":1.0},"588":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":3,"docs":{"222":{"tf":1.0},"602":{"tf":3.1622776601683795},"694":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"p":{"a":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":2,"docs":{"343":{"tf":1.0},"402":{"tf":1.0}},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.4142135623730951}}}}}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":8,"docs":{"205":{"tf":1.4142135623730951},"222":{"tf":1.0},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"50":{"tf":1.0},"54":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":11,"docs":{"140":{"tf":1.0},"234":{"tf":1.0},"250":{"tf":1.0},"324":{"tf":1.0},"358":{"tf":1.0},"482":{"tf":1.0},"78":{"tf":1.0},"807":{"tf":1.0},"83":{"tf":1.0},"848":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951}},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":12,"docs":{"109":{"tf":1.0},"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"194":{"tf":1.0},"371":{"tf":1.0},"573":{"tf":1.0},"615":{"tf":1.0},"797":{"tf":1.0},"843":{"tf":1.0},"850":{"tf":1.0},"853":{"tf":1.0},"913":{"tf":1.0}}}}}},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"653":{"tf":1.0}}},"df":0,"docs":{}}},"df":58,"docs":{"107":{"tf":1.0},"138":{"tf":1.0},"146":{"tf":1.0},"153":{"tf":1.0},"18":{"tf":1.0},"205":{"tf":2.449489742783178},"207":{"tf":1.0},"22":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.4142135623730951},"232":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"29":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.4142135623730951},"303":{"tf":1.0},"325":{"tf":1.0},"33":{"tf":1.0},"335":{"tf":1.0},"363":{"tf":1.0},"368":{"tf":1.0},"38":{"tf":1.0},"41":{"tf":1.0},"418":{"tf":1.4142135623730951},"42":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.7320508075688772},"452":{"tf":1.7320508075688772},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":2.23606797749979},"48":{"tf":1.0},"50":{"tf":1.0},"51":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"554":{"tf":1.0},"573":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"704":{"tf":1.0},"711":{"tf":1.4142135623730951},"72":{"tf":1.0},"720":{"tf":1.0},"725":{"tf":1.4142135623730951},"83":{"tf":1.0},"835":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"880":{"tf":2.449489742783178},"948":{"tf":1.0},"951":{"tf":1.0},"959":{"tf":1.0},"991":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":6,"docs":{"261":{"tf":1.0},"511":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"761":{"tf":1.0},"843":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":5,"docs":{"124":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"776":{"tf":1.0},"959":{"tf":1.0}}}}}},"s":{"df":2,"docs":{"175":{"tf":1.0},"933":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"735":{"tf":1.0},"932":{"tf":1.0}}}}}}},"t":{"df":7,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"385":{"tf":1.0},"705":{"tf":1.0},"776":{"tf":1.0},"813":{"tf":1.0}},"i":{"df":0,"docs":{},"m":{"df":32,"docs":{"1004":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"144":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.0},"221":{"tf":1.0},"249":{"tf":1.0},"28":{"tf":1.4142135623730951},"373":{"tf":1.0},"377":{"tf":1.0},"380":{"tf":1.0},"429":{"tf":1.0},"460":{"tf":1.0},"483":{"tf":1.0},"50":{"tf":1.0},"522":{"tf":1.0},"527":{"tf":1.0},"58":{"tf":1.0},"608":{"tf":1.0},"640":{"tf":1.0},"761":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"880":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"951":{"tf":1.0},"968":{"tf":1.0},"972":{"tf":1.0},"996":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":5,"docs":{"436":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.4142135623730951},"449":{"tf":1.0}},"t":{"df":19,"docs":{"38":{"tf":2.6457513110645907},"388":{"tf":1.0},"39":{"tf":2.449489742783178},"40":{"tf":2.23606797749979},"41":{"tf":1.4142135623730951},"42":{"tf":1.4142135623730951},"43":{"tf":1.0},"44":{"tf":1.4142135623730951},"45":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.0},"48":{"tf":1.0},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"54":{"tf":1.7320508075688772},"55":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"<":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"64":{"tf":1.0}}}}},"df":0,"docs":{}}},"[":{"df":0,"docs":{},"u":{"8":{";":{"2":{"0":{"df":1,"docs":{"898":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"526":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":3,"docs":{"602":{"tf":1.4142135623730951},"605":{"tf":1.0},"698":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"b":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"208":{"tf":1.0},"222":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":1,"docs":{"221":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"455":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"553":{"tf":1.0}}}}},"df":24,"docs":{"180":{"tf":1.0},"24":{"tf":1.4142135623730951},"253":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.4142135623730951},"290":{"tf":1.0},"356":{"tf":1.0},"417":{"tf":1.0},"436":{"tf":1.4142135623730951},"530":{"tf":1.0},"553":{"tf":1.0},"633":{"tf":1.0},"641":{"tf":1.0},"693":{"tf":1.0},"715":{"tf":1.0},"761":{"tf":2.449489742783178},"778":{"tf":1.4142135623730951},"815":{"tf":1.0},"831":{"tf":1.7320508075688772},"84":{"tf":1.0},"848":{"tf":1.0},"872":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0}}}}}}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":60,"docs":{"107":{"tf":1.0},"111":{"tf":1.0},"171":{"tf":1.0},"172":{"tf":1.0},"173":{"tf":1.0},"188":{"tf":1.0},"203":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"216":{"tf":1.0},"231":{"tf":1.0},"235":{"tf":1.0},"249":{"tf":1.4142135623730951},"252":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"293":{"tf":1.0},"302":{"tf":1.0},"313":{"tf":1.0},"331":{"tf":1.0},"335":{"tf":1.0},"343":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"375":{"tf":1.0},"390":{"tf":1.0},"436":{"tf":1.7320508075688772},"450":{"tf":1.0},"455":{"tf":1.4142135623730951},"467":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"540":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.4142135623730951},"600":{"tf":1.0},"63":{"tf":1.0},"665":{"tf":1.0},"697":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":2.8284271247461903},"758":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.4142135623730951},"816":{"tf":1.0},"829":{"tf":1.4142135623730951},"926":{"tf":1.4142135623730951},"931":{"tf":1.7320508075688772},"932":{"tf":1.7320508075688772},"936":{"tf":1.0},"938":{"tf":1.0}}}}},"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"n":{"df":7,"docs":{"134":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"317":{"tf":1.0},"362":{"tf":1.0},"874":{"tf":1.0},"876":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.4142135623730951}}},"z":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"876":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"777":{"tf":1.0}}}}}},"df":1,"docs":{"640":{"tf":1.0}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"701":{"tf":1.0}}},":":{":":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"/":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"3":{"2":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"617":{"tf":1.4142135623730951},"83":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":64,"docs":{"108":{"tf":1.7320508075688772},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"121":{"tf":1.0},"16":{"tf":1.4142135623730951},"169":{"tf":1.4142135623730951},"171":{"tf":1.4142135623730951},"177":{"tf":1.0},"205":{"tf":3.1622776601683795},"234":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"274":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.7320508075688772},"35":{"tf":1.4142135623730951},"375":{"tf":1.0},"410":{"tf":1.0},"427":{"tf":1.7320508075688772},"435":{"tf":1.4142135623730951},"436":{"tf":1.0},"483":{"tf":1.0},"537":{"tf":2.23606797749979},"546":{"tf":1.4142135623730951},"565":{"tf":1.0},"570":{"tf":1.0},"58":{"tf":1.0},"6":{"tf":2.449489742783178},"600":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"619":{"tf":1.0},"692":{"tf":3.7416573867739413},"693":{"tf":2.6457513110645907},"694":{"tf":2.449489742783178},"695":{"tf":1.7320508075688772},"696":{"tf":3.1622776601683795},"697":{"tf":2.449489742783178},"698":{"tf":2.6457513110645907},"699":{"tf":1.7320508075688772},"700":{"tf":2.23606797749979},"701":{"tf":2.6457513110645907},"702":{"tf":1.7320508075688772},"703":{"tf":1.7320508075688772},"704":{"tf":2.0},"705":{"tf":2.6457513110645907},"706":{"tf":2.0},"707":{"tf":1.7320508075688772},"708":{"tf":1.7320508075688772},"722":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"779":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":2.23606797749979},"80":{"tf":1.0},"814":{"tf":1.0},"83":{"tf":1.7320508075688772},"85":{"tf":1.0},"879":{"tf":5.0990195135927845},"885":{"tf":2.0},"931":{"tf":1.0},"976":{"tf":1.0},"983":{"tf":1.0}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":3,"docs":{"814":{"tf":1.4142135623730951},"879":{"tf":3.4641016151377544},"885":{"tf":2.0}}}},"df":0,"docs":{}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{":":{":":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"83":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":1,"docs":{"617":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}}}},"p":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"348":{"tf":1.4142135623730951},"349":{"tf":1.0}}}},"df":0,"docs":{}}},"u":{"df":8,"docs":{"39":{"tf":1.0},"40":{"tf":1.0},"41":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"47":{"tf":1.4142135623730951},"48":{"tf":1.4142135623730951},"55":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"885":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":12,"docs":{"253":{"tf":1.0},"276":{"tf":1.0},"371":{"tf":1.0},"453":{"tf":1.0},"469":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"78":{"tf":1.0},"80":{"tf":1.0}},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":20,"docs":{"124":{"tf":1.0},"160":{"tf":1.4142135623730951},"204":{"tf":1.0},"284":{"tf":1.0},"296":{"tf":1.0},"44":{"tf":1.0},"461":{"tf":1.0},"499":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"629":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"69":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"752":{"tf":1.0},"814":{"tf":1.0},"879":{"tf":2.0},"97":{"tf":1.0}}}}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":2,"docs":{"267":{"tf":1.0},"723":{"tf":1.0}}}}}}},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":4,"docs":{"124":{"tf":1.0},"125":{"tf":1.0},"829":{"tf":1.0},"933":{"tf":1.4142135623730951}}}}},"df":35,"docs":{"187":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"47":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"577":{"tf":1.0},"660":{"tf":1.0},"680":{"tf":1.0},"711":{"tf":1.0},"715":{"tf":1.0},"722":{"tf":1.7320508075688772},"723":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":8.12403840463596},"740":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.4142135623730951},"855":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"267":{"tf":1.0},"330":{"tf":1.0},"351":{"tf":1.0},"361":{"tf":1.0},"38":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":1,"docs":{"187":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":10,"docs":{"22":{"tf":1.7320508075688772},"340":{"tf":1.4142135623730951},"341":{"tf":1.7320508075688772},"346":{"tf":1.0},"435":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"633":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":3.1622776601683795}}}}},"r":{"df":0,"docs":{},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"711":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"i":{"d":{"df":18,"docs":{"155":{"tf":1.0},"16":{"tf":1.0},"190":{"tf":1.0},"194":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"272":{"tf":1.0},"290":{"tf":1.0},"343":{"tf":1.0},"348":{"tf":1.0},"514":{"tf":1.0},"567":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":3.4641016151377544},"776":{"tf":1.0},"849":{"tf":1.0}}},"df":0,"docs":{}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"577":{"tf":1.0}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"l":{"df":17,"docs":{"144":{"tf":1.0},"198":{"tf":1.0},"21":{"tf":1.0},"267":{"tf":1.4142135623730951},"407":{"tf":1.0},"414":{"tf":1.0},"459":{"tf":1.0},"563":{"tf":1.0},"599":{"tf":1.0},"640":{"tf":1.0},"724":{"tf":1.0},"794":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0},"835":{"tf":1.0},"843":{"tf":1.0},"94":{"tf":1.0}}}},"b":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"777":{"tf":1.0}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"898":{"tf":1.0}}}}},"df":57,"docs":{"126":{"tf":1.7320508075688772},"19":{"tf":1.0},"194":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"21":{"tf":1.0},"214":{"tf":1.0},"237":{"tf":1.0},"281":{"tf":1.0},"33":{"tf":1.0},"373":{"tf":1.4142135623730951},"38":{"tf":1.0},"428":{"tf":1.0},"436":{"tf":1.0},"455":{"tf":1.0},"46":{"tf":1.0},"523":{"tf":1.0},"537":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"571":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":1.0},"69":{"tf":1.0},"692":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.0},"701":{"tf":1.0},"722":{"tf":1.7320508075688772},"729":{"tf":1.0},"73":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.0},"749":{"tf":1.0},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"779":{"tf":1.0},"815":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":2.0},"879":{"tf":1.4142135623730951},"880":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"885":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0},"934":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"402":{"tf":1.0}}}}}}},"f":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"208":{"tf":1.0}}}}}},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":21,"docs":{"1010":{"tf":1.0},"131":{"tf":1.0},"144":{"tf":1.0},"257":{"tf":1.0},"288":{"tf":1.0},"296":{"tf":1.0},"437":{"tf":1.0},"507":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"615":{"tf":1.0},"725":{"tf":1.0},"777":{"tf":1.0},"790":{"tf":1.0},"853":{"tf":1.0},"902":{"tf":1.0},"945":{"tf":1.0},"951":{"tf":1.0},"962":{"tf":1.0},"968":{"tf":1.0},"996":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"p":{"df":5,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":1,"docs":{"826":{"tf":1.0}}},"o":{"a":{"d":{"df":1,"docs":{"218":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"111":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":7,"docs":{"195":{"tf":1.0},"203":{"tf":1.4142135623730951},"38":{"tf":1.0},"44":{"tf":1.4142135623730951},"46":{"tf":1.0},"741":{"tf":1.0},"747":{"tf":1.4142135623730951}}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"720":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"154":{"tf":1.0}}}}}}}}},"w":{"df":1,"docs":{"573":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"878":{"tf":1.0}}}},"n":{"df":3,"docs":{"203":{"tf":1.0},"3":{"tf":1.0},"553":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"203":{"tf":2.0},"204":{"tf":1.7320508075688772},"205":{"tf":2.8284271247461903},"208":{"tf":4.69041575982343},"3":{"tf":1.4142135623730951},"339":{"tf":1.0},"349":{"tf":1.0},"457":{"tf":1.0},"773":{"tf":1.0},"81":{"tf":1.0},"944":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":26,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.0},"208":{"tf":1.0},"322":{"tf":1.0},"339":{"tf":1.7320508075688772},"346":{"tf":1.0},"351":{"tf":1.0},"451":{"tf":2.23606797749979},"452":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"454":{"tf":1.0},"455":{"tf":1.4142135623730951},"456":{"tf":1.0},"457":{"tf":1.0},"458":{"tf":1.0},"459":{"tf":1.0},"460":{"tf":1.4142135623730951},"461":{"tf":1.4142135623730951},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.0},"602":{"tf":1.0},"79":{"tf":1.0},"84":{"tf":1.4142135623730951}}}}}}}}}}},"p":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.0}}}},"0":{"df":1,"docs":{"208":{"tf":1.0}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"5":{"6":{"df":13,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":1,"docs":{"551":{"tf":1.0}}}},"4":{"9":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"n":{"df":2,"docs":{"44":{"tf":1.0},"45":{"tf":1.0}}},"{":{"\\":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"749":{"tf":1.7320508075688772}}}}},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"749":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{},"n":{"+":{"1":{"df":2,"docs":{"44":{"tf":1.0},"45":{"tf":1.0}}},"df":0,"docs":{}},"df":2,"docs":{"44":{"tf":1.7320508075688772},"45":{"tf":1.0}}}}},"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":3,"docs":{"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"e":{"df":1,"docs":{"440":{"tf":1.0}}},"k":{"a":{"df":0,"docs":{},"g":{"df":8,"docs":{"44":{"tf":2.23606797749979},"45":{"tf":2.23606797749979},"46":{"tf":1.7320508075688772},"49":{"tf":1.0},"50":{"tf":1.4142135623730951},"51":{"tf":1.0},"52":{"tf":1.0},"553":{"tf":1.4142135623730951}}}},"df":1,"docs":{"25":{"tf":1.4142135623730951}}}},"d":{"df":1,"docs":{"435":{"tf":1.0}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":14,"docs":{"827":{"tf":2.23606797749979},"828":{"tf":1.0},"829":{"tf":2.23606797749979},"830":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.4142135623730951},"833":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.0},"836":{"tf":1.0},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"840":{"tf":1.0}}}},"i":{"d":{"df":21,"docs":{"111":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"267":{"tf":1.7320508075688772},"272":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"649":{"tf":1.0},"653":{"tf":1.0},"711":{"tf":1.0},"808":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.7320508075688772},"815":{"tf":1.7320508075688772},"816":{"tf":1.7320508075688772},"817":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":2,"docs":{"244":{"tf":1.0},"926":{"tf":1.0}}}}},"df":0,"docs":{}},"n":{"df":1,"docs":{"799":{"tf":1.4142135623730951}}},"r":{"df":5,"docs":{"47":{"tf":1.0},"5":{"tf":1.0},"697":{"tf":1.0},"722":{"tf":1.0},"95":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"234":{"tf":1.0}}},":":{":":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"(":{"3":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{":":{":":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":5,"docs":{"927":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.4142135623730951},"935":{"tf":1.0}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"932":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"937":{"tf":1.0}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"a":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"a":{":":{":":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"846":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":3,"docs":{"931":{"tf":1.4142135623730951},"932":{"tf":1.4142135623730951},"935":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"y":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"931":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"931":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"931":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"701":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":93,"docs":{"121":{"tf":1.0},"125":{"tf":1.0},"133":{"tf":1.0},"149":{"tf":1.4142135623730951},"18":{"tf":1.4142135623730951},"21":{"tf":1.0},"216":{"tf":1.0},"219":{"tf":1.0},"220":{"tf":1.0},"234":{"tf":2.0},"24":{"tf":1.0},"261":{"tf":1.0},"269":{"tf":1.0},"273":{"tf":1.7320508075688772},"284":{"tf":1.7320508075688772},"300":{"tf":1.0},"315":{"tf":1.4142135623730951},"35":{"tf":2.0},"370":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.4142135623730951},"375":{"tf":2.449489742783178},"382":{"tf":1.0},"415":{"tf":1.0},"417":{"tf":1.0},"470":{"tf":1.0},"511":{"tf":1.0},"519":{"tf":1.7320508075688772},"697":{"tf":1.0},"796":{"tf":1.0},"799":{"tf":1.0},"804":{"tf":1.0},"814":{"tf":1.7320508075688772},"816":{"tf":2.6457513110645907},"817":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0},"871":{"tf":2.23606797749979},"872":{"tf":2.0},"873":{"tf":1.0},"874":{"tf":1.7320508075688772},"875":{"tf":1.0},"876":{"tf":1.0},"877":{"tf":1.0},"878":{"tf":1.4142135623730951},"879":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"882":{"tf":1.4142135623730951},"883":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":1.7320508075688772},"886":{"tf":1.0},"887":{"tf":1.4142135623730951},"888":{"tf":1.4142135623730951},"889":{"tf":1.0},"890":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.4142135623730951},"914":{"tf":1.4142135623730951},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"918":{"tf":1.0},"919":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.7320508075688772},"936":{"tf":1.0},"938":{"tf":1.4142135623730951},"939":{"tf":1.4142135623730951},"941":{"tf":1.4142135623730951},"942":{"tf":2.8284271247461903},"943":{"tf":1.0},"945":{"tf":1.4142135623730951},"961":{"tf":1.7320508075688772},"972":{"tf":1.0},"980":{"tf":1.0}},"’":{"df":1,"docs":{"943":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"324":{"tf":1.4142135623730951},"325":{"tf":1.0},"359":{"tf":1.4142135623730951},"39":{"tf":1.0},"44":{"tf":1.0}}}}},"r":{"a":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"[":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"634":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"d":{"df":3,"docs":{"252":{"tf":1.4142135623730951},"253":{"tf":1.7320508075688772},"634":{"tf":1.0}}},"df":0,"docs":{}}},"a":{"df":1,"docs":{"699":{"tf":1.0}}},"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"715":{"tf":1.0},"720":{"tf":1.0}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"300":{"tf":1.0}}},"(":{"1":{"0":{"0":{"0":{")":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"786":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"/":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"3":{"2":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"1":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"600":{"tf":1.0}}},"df":143,"docs":{"100":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"108":{"tf":2.0},"109":{"tf":1.4142135623730951},"111":{"tf":1.4142135623730951},"114":{"tf":1.0},"118":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":2.0},"155":{"tf":1.7320508075688772},"160":{"tf":1.4142135623730951},"18":{"tf":1.0},"198":{"tf":2.0},"199":{"tf":1.4142135623730951},"200":{"tf":1.0},"201":{"tf":1.4142135623730951},"203":{"tf":2.6457513110645907},"209":{"tf":1.0},"210":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.4142135623730951},"222":{"tf":1.0},"247":{"tf":2.23606797749979},"248":{"tf":1.4142135623730951},"249":{"tf":2.449489742783178},"250":{"tf":1.0},"251":{"tf":2.23606797749979},"252":{"tf":2.0},"253":{"tf":2.6457513110645907},"254":{"tf":2.449489742783178},"255":{"tf":2.8284271247461903},"256":{"tf":1.0},"257":{"tf":2.449489742783178},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.7320508075688772},"269":{"tf":1.4142135623730951},"270":{"tf":1.0},"276":{"tf":1.4142135623730951},"282":{"tf":1.0},"289":{"tf":1.0},"294":{"tf":2.23606797749979},"295":{"tf":2.8284271247461903},"296":{"tf":4.69041575982343},"297":{"tf":2.8284271247461903},"298":{"tf":1.7320508075688772},"299":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":4.242640687119285},"301":{"tf":3.4641016151377544},"302":{"tf":2.6457513110645907},"303":{"tf":3.872983346207417},"304":{"tf":1.0},"305":{"tf":1.0},"306":{"tf":1.4142135623730951},"307":{"tf":1.0},"308":{"tf":2.23606797749979},"309":{"tf":1.0},"310":{"tf":1.4142135623730951},"367":{"tf":1.7320508075688772},"368":{"tf":1.7320508075688772},"369":{"tf":1.0},"374":{"tf":1.4142135623730951},"375":{"tf":3.872983346207417},"376":{"tf":2.23606797749979},"381":{"tf":1.4142135623730951},"39":{"tf":1.0},"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.7320508075688772},"403":{"tf":1.4142135623730951},"404":{"tf":1.4142135623730951},"405":{"tf":1.0},"406":{"tf":1.4142135623730951},"407":{"tf":1.4142135623730951},"408":{"tf":1.4142135623730951},"409":{"tf":1.0},"438":{"tf":1.0},"440":{"tf":1.0},"444":{"tf":1.0},"450":{"tf":1.0},"496":{"tf":1.0},"499":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"515":{"tf":1.0},"56":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.4142135623730951},"571":{"tf":1.0},"58":{"tf":2.0},"59":{"tf":1.0},"60":{"tf":1.7320508075688772},"627":{"tf":1.4142135623730951},"629":{"tf":2.0},"63":{"tf":1.4142135623730951},"632":{"tf":1.4142135623730951},"633":{"tf":2.0},"636":{"tf":1.4142135623730951},"64":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.7320508075688772},"65":{"tf":1.0},"67":{"tf":1.0},"697":{"tf":1.4142135623730951},"699":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.4142135623730951},"714":{"tf":1.0},"72":{"tf":1.4142135623730951},"722":{"tf":1.0},"725":{"tf":1.0},"729":{"tf":2.6457513110645907},"73":{"tf":1.7320508075688772},"745":{"tf":1.0},"77":{"tf":1.7320508075688772},"774":{"tf":1.0},"78":{"tf":1.4142135623730951},"808":{"tf":1.7320508075688772},"809":{"tf":1.0},"81":{"tf":2.8284271247461903},"810":{"tf":2.6457513110645907},"812":{"tf":1.0},"813":{"tf":2.0},"814":{"tf":3.0},"815":{"tf":3.0},"816":{"tf":1.0},"817":{"tf":1.7320508075688772},"818":{"tf":1.4142135623730951},"822":{"tf":1.7320508075688772},"826":{"tf":1.4142135623730951},"83":{"tf":3.3166247903554},"831":{"tf":1.0},"859":{"tf":1.0},"928":{"tf":1.4142135623730951},"934":{"tf":1.0},"938":{"tf":1.4142135623730951}},"x":{"df":1,"docs":{"600":{"tf":1.0}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"m":{"df":1,"docs":{"198":{"tf":1.0}}}}}},"df":22,"docs":{"106":{"tf":1.0},"107":{"tf":1.4142135623730951},"108":{"tf":1.7320508075688772},"111":{"tf":2.6457513110645907},"112":{"tf":3.4641016151377544},"113":{"tf":1.4142135623730951},"114":{"tf":1.4142135623730951},"118":{"tf":1.0},"121":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"243":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"329":{"tf":1.0},"440":{"tf":1.0},"633":{"tf":3.4641016151377544},"634":{"tf":1.4142135623730951},"808":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":2.0},"817":{"tf":2.0}},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"h":{"df":1,"docs":{"346":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"d":{"df":10,"docs":{"204":{"tf":1.4142135623730951},"218":{"tf":1.0},"221":{"tf":1.0},"273":{"tf":1.0},"634":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":2.23606797749979},"817":{"tf":1.4142135623730951},"818":{"tf":1.0}}},"df":0,"docs":{}},"k":{"df":1,"docs":{"600":{"tf":1.0}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":2,"docs":{"375":{"tf":1.4142135623730951},"436":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"735":{"tf":11.269427669584644}},"e":{"df":0,"docs":{},"t":{"df":62,"docs":{"121":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"148":{"tf":1.0},"184":{"tf":1.0},"186":{"tf":1.0},"191":{"tf":1.4142135623730951},"194":{"tf":1.0},"204":{"tf":1.7320508075688772},"207":{"tf":2.0},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"322":{"tf":1.0},"342":{"tf":1.4142135623730951},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"364":{"tf":1.7320508075688772},"390":{"tf":1.0},"397":{"tf":1.0},"455":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.4142135623730951},"521":{"tf":1.0},"534":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.4142135623730951},"571":{"tf":1.7320508075688772},"602":{"tf":1.7320508075688772},"605":{"tf":1.0},"613":{"tf":2.23606797749979},"614":{"tf":1.4142135623730951},"615":{"tf":2.0},"616":{"tf":1.0},"617":{"tf":1.4142135623730951},"618":{"tf":1.0},"619":{"tf":1.0},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"668":{"tf":1.0},"693":{"tf":1.0},"698":{"tf":1.4142135623730951},"735":{"tf":3.1622776601683795},"741":{"tf":1.0},"748":{"tf":1.4142135623730951},"752":{"tf":1.0},"857":{"tf":1.4142135623730951},"861":{"tf":1.4142135623730951},"862":{"tf":1.4142135623730951},"870":{"tf":1.0},"885":{"tf":1.0},"929":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"939":{"tf":1.0},"95":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":2,"docs":{"416":{"tf":1.0},"933":{"tf":1.0}}}}}},"df":7,"docs":{"196":{"tf":1.0},"438":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"213":{"tf":1.0}}}}}},"r":{"df":1,"docs":{"575":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"244":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"df":1,"docs":{"600":{"tf":1.0}}},"s":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"300":{"tf":1.0}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":2,"docs":{"466":{"tf":1.0},"467":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":9,"docs":{"44":{"tf":1.0},"450":{"tf":1.0},"46":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"637":{"tf":1.4142135623730951},"640":{"tf":1.7320508075688772},"786":{"tf":2.23606797749979},"932":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":4,"docs":{"201":{"tf":1.4142135623730951},"513":{"tf":1.0},"774":{"tf":1.0},"843":{"tf":1.0}}},"y":{"'":{"df":3,"docs":{"436":{"tf":1.0},"450":{"tf":1.0},"571":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":3,"docs":{"517":{"tf":1.0},"544":{"tf":1.0},"762":{"tf":1.0}}},"t":{"df":41,"docs":{"126":{"tf":1.0},"181":{"tf":1.0},"203":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"230":{"tf":1.4142135623730951},"234":{"tf":1.0},"24":{"tf":1.4142135623730951},"270":{"tf":1.7320508075688772},"272":{"tf":1.0},"293":{"tf":1.0},"333":{"tf":1.0},"345":{"tf":1.0},"347":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.4142135623730951},"459":{"tf":1.0},"5":{"tf":1.0},"514":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"537":{"tf":1.0},"544":{"tf":1.0},"548":{"tf":1.0},"605":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.0},"634":{"tf":1.0},"67":{"tf":1.0},"701":{"tf":1.4142135623730951},"725":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.0},"796":{"tf":1.0},"83":{"tf":1.7320508075688772},"863":{"tf":1.0},"878":{"tf":1.0},"931":{"tf":1.0}},"i":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"6":{"tf":1.0},"615":{"tf":1.0},"881":{"tf":1.0}}}},"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":29,"docs":{"1004":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"234":{"tf":1.0},"267":{"tf":1.4142135623730951},"303":{"tf":2.0},"346":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"439":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.0},"500":{"tf":1.0},"502":{"tf":1.7320508075688772},"503":{"tf":2.0},"512":{"tf":1.0},"565":{"tf":1.4142135623730951},"570":{"tf":1.0},"629":{"tf":1.0},"69":{"tf":1.0},"712":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":1.4142135623730951},"797":{"tf":2.23606797749979},"799":{"tf":2.0},"807":{"tf":1.0},"929":{"tf":1.0}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":27,"docs":{"171":{"tf":1.0},"177":{"tf":1.4142135623730951},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"231":{"tf":1.0},"267":{"tf":1.0},"352":{"tf":1.0},"371":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"418":{"tf":1.0},"432":{"tf":1.0},"46":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":1.0},"628":{"tf":1.0},"633":{"tf":1.0},"664":{"tf":1.0},"711":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.0},"799":{"tf":1.7320508075688772},"832":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.0}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"832":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"142":{"tf":1.0},"381":{"tf":1.0},"414":{"tf":1.0},"439":{"tf":1.0},"711":{"tf":1.0},"810":{"tf":1.0},"876":{"tf":1.0},"990":{"tf":1.0},"996":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":8,"docs":{"170":{"tf":1.0},"514":{"tf":1.0},"528":{"tf":1.0},"56":{"tf":1.0},"66":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"852":{"tf":1.4142135623730951},"912":{"tf":1.0}},"t":{"df":4,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.0},"335":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"5":{"7":{"6":{"0":{"0":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":3,"docs":{"128":{"tf":1.0},"142":{"tf":1.0},"680":{"tf":1.0}}}},"s":{"df":33,"docs":{"126":{"tf":2.6457513110645907},"205":{"tf":2.0},"207":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"211":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"272":{"tf":1.0},"274":{"tf":1.0},"288":{"tf":1.0},"388":{"tf":1.4142135623730951},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"456":{"tf":1.0},"457":{"tf":1.0},"461":{"tf":1.0},"531":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":1.0},"64":{"tf":1.0},"653":{"tf":1.0},"655":{"tf":1.0},"72":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"786":{"tf":1.0},"829":{"tf":1.0},"849":{"tf":1.0},"885":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}},"i":{"df":0,"docs":{},"v":{"df":3,"docs":{"471":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}}}},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"df":2,"docs":{"221":{"tf":1.0},"761":{"tf":1.0}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"996":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":20,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"138":{"tf":1.0},"264":{"tf":1.0},"270":{"tf":1.0},"430":{"tf":1.0},"440":{"tf":1.4142135623730951},"446":{"tf":1.0},"522":{"tf":2.23606797749979},"602":{"tf":2.23606797749979},"603":{"tf":1.0},"705":{"tf":1.0},"73":{"tf":1.0},"786":{"tf":1.0},"831":{"tf":2.23606797749979},"832":{"tf":1.7320508075688772},"835":{"tf":1.7320508075688772},"837":{"tf":1.0},"840":{"tf":1.0},"970":{"tf":1.0}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"139":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"a":{"df":1,"docs":{"46":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":8,"docs":{"1011":{"tf":1.0},"147":{"tf":1.0},"21":{"tf":1.0},"267":{"tf":1.0},"407":{"tf":1.0},"605":{"tf":1.0},"696":{"tf":1.0},"786":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"573":{"tf":1.0}}}},"y":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":1,"docs":{"814":{"tf":1.0}}}}}}},"df":24,"docs":{"208":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"534":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":2.23606797749979},"600":{"tf":1.0},"603":{"tf":1.7320508075688772},"614":{"tf":1.0},"615":{"tf":1.0},"651":{"tf":1.0},"654":{"tf":1.0},"659":{"tf":1.0},"699":{"tf":2.0},"724":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.7320508075688772},"777":{"tf":2.23606797749979},"811":{"tf":1.0},"849":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0}},"e":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}},"f":{"df":0,"docs":{},"e":{"df":6,"docs":{"650":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"655":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.4142135623730951}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":10,"docs":{"170":{"tf":1.0},"171":{"tf":2.0},"175":{"tf":1.0},"439":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.0},"517":{"tf":1.0},"537":{"tf":1.0},"586":{"tf":1.4142135623730951},"78":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"208":{"tf":1.0},"473":{"tf":1.0},"537":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"653":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.7320508075688772},"813":{"tf":1.4142135623730951},"814":{"tf":2.0},"822":{"tf":1.0},"860":{"tf":1.0},"976":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":3,"docs":{"208":{"tf":1.0},"376":{"tf":1.0},"932":{"tf":1.0}}}}}}},"b":{"a":{"df":1,"docs":{"133":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"44":{"tf":1.0}},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"253":{"tf":1.0},"254":{"tf":1.0}}},"df":0,"docs":{}}},"df":11,"docs":{"248":{"tf":1.4142135623730951},"253":{"tf":1.0},"257":{"tf":1.0},"436":{"tf":1.0},"482":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"512":{"tf":2.0},"554":{"tf":1.0},"69":{"tf":1.0},"759":{"tf":1.4142135623730951}},"i":{"d":{"/":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"551":{"tf":1.0}}}}}}}}}},"df":6,"docs":{"249":{"tf":1.0},"254":{"tf":2.0},"255":{"tf":1.0},"505":{"tf":1.0},"551":{"tf":1.4142135623730951},"735":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"553":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"g":{"df":1,"docs":{"429":{"tf":1.0}}},"n":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"718":{"tf":1.0},"724":{"tf":1.0}}}},"d":{"df":3,"docs":{"450":{"tf":1.0},"573":{"tf":1.0},"879":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":14,"docs":{"150":{"tf":2.23606797749979},"151":{"tf":1.0},"152":{"tf":1.0},"153":{"tf":1.0},"154":{"tf":2.449489742783178},"155":{"tf":1.4142135623730951},"156":{"tf":1.4142135623730951},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.4142135623730951},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}},"df":1,"docs":{"603":{"tf":2.8284271247461903}},"p":{"a":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":1,"docs":{"603":{"tf":2.6457513110645907}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{">":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{"]":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"_":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":9,"docs":{"233":{"tf":1.0},"250":{"tf":1.0},"373":{"tf":1.4142135623730951},"385":{"tf":1.0},"471":{"tf":1.0},"498":{"tf":1.0},"761":{"tf":1.0},"849":{"tf":1.4142135623730951},"852":{"tf":1.0}},"e":{"/":{"d":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"r":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{".":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"(":{"(":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{".":{"0":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{".":{"0":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"s":{"df":1,"docs":{"814":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"2":{"df":1,"docs":{"207":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"199":{"tf":1.0}}}},"n":{"df":0,"docs":{},"t":{"(":{"1":{"0":{"0":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"5":{"0":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"213":{"tf":1.0},"576":{"tf":1.0},"814":{"tf":1.0},"928":{"tf":1.0}}}},"df":2,"docs":{"221":{"tf":1.0},"846":{"tf":1.7320508075688772}}}},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"723":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}}}},"df":60,"docs":{"1003":{"tf":1.0},"1008":{"tf":1.0},"191":{"tf":1.0},"199":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"235":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"402":{"tf":1.0},"432":{"tf":1.0},"438":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"470":{"tf":1.0},"481":{"tf":2.0},"482":{"tf":1.0},"483":{"tf":1.0},"484":{"tf":1.0},"485":{"tf":1.4142135623730951},"486":{"tf":1.4142135623730951},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.4142135623730951},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"50":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.0},"586":{"tf":1.0},"606":{"tf":1.4142135623730951},"670":{"tf":1.0},"71":{"tf":1.0},"722":{"tf":1.0},"724":{"tf":1.0},"739":{"tf":1.0},"744":{"tf":1.4142135623730951},"75":{"tf":1.0},"761":{"tf":1.0},"776":{"tf":1.0},"814":{"tf":1.0},"826":{"tf":1.4142135623730951},"835":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.0},"932":{"tf":1.0},"936":{"tf":1.4142135623730951}},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"199":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":211,"docs":{"1":{"tf":1.4142135623730951},"10":{"tf":1.4142135623730951},"1002":{"tf":1.4142135623730951},"1004":{"tf":1.0},"1007":{"tf":1.0},"1009":{"tf":1.4142135623730951},"101":{"tf":1.4142135623730951},"1010":{"tf":1.4142135623730951},"102":{"tf":1.4142135623730951},"106":{"tf":1.4142135623730951},"108":{"tf":1.0},"11":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"116":{"tf":1.4142135623730951},"117":{"tf":1.7320508075688772},"122":{"tf":1.4142135623730951},"129":{"tf":1.4142135623730951},"130":{"tf":1.4142135623730951},"136":{"tf":1.4142135623730951},"143":{"tf":1.4142135623730951},"144":{"tf":1.7320508075688772},"150":{"tf":1.4142135623730951},"151":{"tf":1.0},"152":{"tf":1.0},"157":{"tf":1.4142135623730951},"158":{"tf":1.7320508075688772},"164":{"tf":1.4142135623730951},"17":{"tf":1.7320508075688772},"175":{"tf":1.4142135623730951},"176":{"tf":1.7320508075688772},"18":{"tf":1.0},"182":{"tf":1.4142135623730951},"185":{"tf":1.0},"189":{"tf":1.4142135623730951},"190":{"tf":1.7320508075688772},"195":{"tf":1.0},"210":{"tf":1.4142135623730951},"215":{"tf":1.0},"224":{"tf":1.4142135623730951},"229":{"tf":1.4142135623730951},"238":{"tf":1.7320508075688772},"239":{"tf":1.4142135623730951},"247":{"tf":1.4142135623730951},"25":{"tf":1.0},"256":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"26":{"tf":1.0},"268":{"tf":1.0},"276":{"tf":1.7320508075688772},"279":{"tf":1.4142135623730951},"28":{"tf":1.4142135623730951},"287":{"tf":1.4142135623730951},"288":{"tf":2.0},"294":{"tf":1.0},"296":{"tf":2.0},"297":{"tf":1.0},"300":{"tf":1.0},"305":{"tf":1.7320508075688772},"31":{"tf":1.4142135623730951},"311":{"tf":1.0},"318":{"tf":1.4142135623730951},"32":{"tf":1.4142135623730951},"322":{"tf":1.4142135623730951},"355":{"tf":1.4142135623730951},"356":{"tf":1.4142135623730951},"366":{"tf":1.4142135623730951},"379":{"tf":1.4142135623730951},"380":{"tf":1.7320508075688772},"386":{"tf":1.4142135623730951},"393":{"tf":1.4142135623730951},"394":{"tf":1.7320508075688772},"400":{"tf":1.4142135623730951},"405":{"tf":1.4142135623730951},"406":{"tf":1.7320508075688772},"410":{"tf":1.4142135623730951},"421":{"tf":1.4142135623730951},"422":{"tf":2.0},"430":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.4142135623730951},"438":{"tf":1.0},"440":{"tf":1.0},"443":{"tf":1.4142135623730951},"444":{"tf":1.7320508075688772},"449":{"tf":1.0},"45":{"tf":1.0},"451":{"tf":1.4142135623730951},"458":{"tf":1.4142135623730951},"459":{"tf":2.0},"465":{"tf":1.4142135623730951},"47":{"tf":1.0},"475":{"tf":1.4142135623730951},"476":{"tf":1.4142135623730951},"481":{"tf":1.4142135623730951},"488":{"tf":1.4142135623730951},"489":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"506":{"tf":1.4142135623730951},"507":{"tf":1.4142135623730951},"513":{"tf":1.4142135623730951},"529":{"tf":1.4142135623730951},"530":{"tf":2.0},"535":{"tf":1.4142135623730951},"54":{"tf":1.0},"542":{"tf":1.4142135623730951},"543":{"tf":1.7320508075688772},"549":{"tf":1.4142135623730951},"556":{"tf":1.4142135623730951},"557":{"tf":1.4142135623730951},"56":{"tf":1.4142135623730951},"563":{"tf":1.4142135623730951},"565":{"tf":1.0},"579":{"tf":1.4142135623730951},"580":{"tf":1.7320508075688772},"584":{"tf":1.4142135623730951},"591":{"tf":1.4142135623730951},"592":{"tf":1.7320508075688772},"598":{"tf":1.4142135623730951},"606":{"tf":1.4142135623730951},"607":{"tf":1.7320508075688772},"613":{"tf":1.4142135623730951},"620":{"tf":1.4142135623730951},"621":{"tf":1.7320508075688772},"627":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.7320508075688772},"649":{"tf":1.4142135623730951},"657":{"tf":1.4142135623730951},"658":{"tf":2.0},"664":{"tf":1.4142135623730951},"671":{"tf":1.4142135623730951},"672":{"tf":1.4142135623730951},"678":{"tf":1.4142135623730951},"685":{"tf":1.4142135623730951},"686":{"tf":1.4142135623730951},"692":{"tf":1.4142135623730951},"70":{"tf":1.4142135623730951},"700":{"tf":1.0},"702":{"tf":1.4142135623730951},"703":{"tf":1.4142135623730951},"709":{"tf":1.0},"71":{"tf":1.7320508075688772},"72":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.4142135623730951},"725":{"tf":1.4142135623730951},"739":{"tf":1.4142135623730951},"757":{"tf":1.4142135623730951},"759":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.4142135623730951},"765":{"tf":1.7320508075688772},"782":{"tf":1.4142135623730951},"789":{"tf":1.4142135623730951},"79":{"tf":1.4142135623730951},"790":{"tf":1.7320508075688772},"795":{"tf":1.4142135623730951},"8":{"tf":1.0},"802":{"tf":1.4142135623730951},"803":{"tf":1.4142135623730951},"808":{"tf":1.4142135623730951},"820":{"tf":1.4142135623730951},"821":{"tf":1.7320508075688772},"827":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"832":{"tf":1.0},"834":{"tf":1.4142135623730951},"835":{"tf":2.23606797749979},"841":{"tf":1.4142135623730951},"851":{"tf":1.4142135623730951},"852":{"tf":2.0},"857":{"tf":1.4142135623730951},"86":{"tf":1.4142135623730951},"865":{"tf":1.4142135623730951},"866":{"tf":1.7320508075688772},"87":{"tf":1.4142135623730951},"871":{"tf":1.4142135623730951},"874":{"tf":1.4142135623730951},"884":{"tf":1.4142135623730951},"885":{"tf":1.4142135623730951},"891":{"tf":1.4142135623730951},"901":{"tf":1.4142135623730951},"902":{"tf":1.4142135623730951},"908":{"tf":1.7320508075688772},"916":{"tf":1.4142135623730951},"918":{"tf":1.4142135623730951},"919":{"tf":2.0},"926":{"tf":1.0},"93":{"tf":1.4142135623730951},"936":{"tf":1.7320508075688772},"94":{"tf":1.0},"940":{"tf":1.4142135623730951},"948":{"tf":1.0},"950":{"tf":1.4142135623730951},"951":{"tf":1.4142135623730951},"957":{"tf":1.4142135623730951},"962":{"tf":1.4142135623730951},"965":{"tf":1.0},"967":{"tf":1.4142135623730951},"968":{"tf":2.0},"972":{"tf":1.0},"974":{"tf":1.4142135623730951},"981":{"tf":1.4142135623730951},"982":{"tf":1.7320508075688772},"988":{"tf":1.4142135623730951},"992":{"tf":1.0},"995":{"tf":1.4142135623730951},"996":{"tf":1.7320508075688772}}}}}},"h":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"376":{"tf":1.0},"720":{"tf":1.0},"849":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"d":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"u":{"3":{"2":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"o":{"d":{"df":62,"docs":{"1003":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":5.291502622129181},"127":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"148":{"tf":1.0},"172":{"tf":1.0},"182":{"tf":2.23606797749979},"183":{"tf":1.4142135623730951},"184":{"tf":2.449489742783178},"185":{"tf":1.0},"186":{"tf":1.4142135623730951},"187":{"tf":2.0},"188":{"tf":1.7320508075688772},"189":{"tf":1.0},"190":{"tf":1.4142135623730951},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.4142135623730951},"194":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.7320508075688772},"204":{"tf":4.242640687119285},"205":{"tf":2.6457513110645907},"206":{"tf":1.0},"207":{"tf":2.0},"213":{"tf":1.4142135623730951},"221":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.4142135623730951},"372":{"tf":1.0},"422":{"tf":1.0},"505":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":2.23606797749979},"567":{"tf":1.7320508075688772},"575":{"tf":1.7320508075688772},"577":{"tf":1.0},"63":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":2.23606797749979},"744":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":3.4641016151377544},"809":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"837":{"tf":1.0},"846":{"tf":1.4142135623730951},"861":{"tf":2.0},"862":{"tf":2.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"n":{"df":3,"docs":{"199":{"tf":1.0},"311":{"tf":1.0},"875":{"tf":1.0}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":12,"docs":{"111":{"tf":1.0},"199":{"tf":1.0},"237":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"371":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"124":{"tf":1.0},"199":{"tf":1.0}}}}}}}}}}},"t":{"df":3,"docs":{"111":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0}}}},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"431":{"tf":1.0},"438":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"337":{"tf":1.0},"347":{"tf":2.23606797749979},"634":{"tf":1.0},"69":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"373":{"tf":1.0}}},"df":0,"docs":{}}}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.0},"230":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"605":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0},"786":{"tf":2.449489742783178}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":2,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"402":{"tf":1.4142135623730951}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"244":{"tf":1.0}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":5,"docs":{"229":{"tf":1.0},"268":{"tf":1.0},"366":{"tf":1.0},"410":{"tf":1.0},"465":{"tf":1.0}}}}}}}}}},"g":{"df":0,"docs":{},"p":{"df":17,"docs":{"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":2.0},"895":{"tf":2.23606797749979},"896":{"tf":1.7320508075688772},"897":{"tf":1.4142135623730951},"898":{"tf":2.0},"899":{"tf":1.0},"900":{"tf":1.4142135623730951},"901":{"tf":1.0},"902":{"tf":1.4142135623730951},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.0}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"895":{"tf":2.449489742783178},"898":{"tf":1.0}}}}}}}}}}}}}}},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":14,"docs":{"209":{"tf":1.0},"335":{"tf":1.0},"339":{"tf":1.0},"450":{"tf":1.0},"680":{"tf":1.0},"720":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"841":{"tf":1.7320508075688772},"845":{"tf":1.0},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"957":{"tf":1.0}},"i":{"df":0,"docs":{},"p":{"df":2,"docs":{"940":{"tf":1.0},"945":{"tf":1.0}}}}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"711":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":3,"docs":{"436":{"tf":1.0},"553":{"tf":1.4142135623730951},"640":{"tf":1.0}}}},"df":1,"docs":{"45":{"tf":1.0}},"e":{"c":{"df":5,"docs":{"214":{"tf":1.0},"497":{"tf":1.0},"514":{"tf":1.0},"522":{"tf":1.0},"724":{"tf":1.0}},"e":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"747":{"tf":1.0}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":6,"docs":{"247":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"730":{"tf":1.0},"757":{"tf":1.0},"827":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"y":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"588":{"tf":1.0},"74":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"177":{"tf":1.0},"776":{"tf":1.0}}}}}}},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":2,"docs":{"164":{"tf":1.0},"535":{"tf":1.0}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"f":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"1008":{"tf":1.0},"900":{"tf":1.0},"917":{"tf":1.0}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":2,"docs":{"205":{"tf":1.7320508075688772},"778":{"tf":1.0}}}}}},"l":{"a":{"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"860":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"860":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":28,"docs":{"1015":{"tf":1.0},"133":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"208":{"tf":1.7320508075688772},"212":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.4142135623730951},"239":{"tf":1.0},"267":{"tf":1.0},"303":{"tf":1.0},"314":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.0},"602":{"tf":1.0},"73":{"tf":1.0},"776":{"tf":1.4142135623730951},"816":{"tf":1.0},"84":{"tf":1.0},"844":{"tf":1.0},"857":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.0},"911":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"df":0,"docs":{},"n":{"df":10,"docs":{"121":{"tf":1.0},"196":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"371":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.7320508075688772},"61":{"tf":1.0},"680":{"tf":1.0},"700":{"tf":1.0}}},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"u":{"df":3,"docs":{"747":{"tf":1.4142135623730951},"749":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":9,"docs":{"199":{"tf":2.0},"39":{"tf":1.0},"414":{"tf":1.4142135623730951},"418":{"tf":1.0},"54":{"tf":1.0},"853":{"tf":1.0},"961":{"tf":1.0},"971":{"tf":1.4142135623730951},"973":{"tf":1.4142135623730951}}}}}}},"y":{"df":2,"docs":{"1004":{"tf":1.0},"522":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":5,"docs":{"292":{"tf":1.4142135623730951},"499":{"tf":1.0},"697":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":1,"docs":{"515":{"tf":1.0}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"571":{"tf":1.0}}}},"u":{"df":5,"docs":{"205":{"tf":1.0},"223":{"tf":1.0},"244":{"tf":1.0},"715":{"tf":1.0},"720":{"tf":1.0}},"r":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"373":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"c":{"df":3,"docs":{"38":{"tf":1.0},"50":{"tf":2.0},"537":{"tf":1.0}}},"df":1,"docs":{"934":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":27,"docs":{"111":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.4142135623730951},"132":{"tf":1.0},"173":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"25":{"tf":1.0},"284":{"tf":1.0},"372":{"tf":1.4142135623730951},"412":{"tf":1.0},"418":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":2.0},"648":{"tf":1.0},"653":{"tf":1.0},"722":{"tf":1.4142135623730951},"736":{"tf":1.0},"771":{"tf":1.0},"778":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772},"846":{"tf":1.0},"874":{"tf":1.0},"932":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"25":{"tf":1.4142135623730951},"26":{"tf":1.0},"732":{"tf":1.7320508075688772},"735":{"tf":3.4641016151377544}}}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"30":{"tf":1.0}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"878":{"tf":1.0}}}}},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"'":{"df":18,"docs":{"1004":{"tf":1.0},"138":{"tf":1.0},"147":{"tf":1.0},"231":{"tf":1.0},"267":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"39":{"tf":1.0},"435":{"tf":1.4142135623730951},"437":{"tf":1.0},"515":{"tf":1.0},"571":{"tf":1.0},"711":{"tf":1.4142135623730951},"720":{"tf":1.0},"724":{"tf":1.0},"961":{"tf":1.0}}},".":{"df":0,"docs":{},"j":{"df":4,"docs":{"895":{"tf":1.0},"898":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0}}}},"/":{"df":0,"docs":{},"k":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"m":{"a":{"df":1,"docs":{"160":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":165,"docs":{"0":{"tf":1.4142135623730951},"1003":{"tf":1.0},"1004":{"tf":2.0},"1009":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":2.0},"109":{"tf":1.0},"111":{"tf":1.7320508075688772},"113":{"tf":1.4142135623730951},"120":{"tf":1.4142135623730951},"121":{"tf":1.0},"124":{"tf":1.0},"133":{"tf":1.0},"164":{"tf":1.0},"169":{"tf":1.0},"171":{"tf":1.7320508075688772},"183":{"tf":1.0},"184":{"tf":1.4142135623730951},"188":{"tf":1.0},"190":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"196":{"tf":2.0},"198":{"tf":2.0},"199":{"tf":2.6457513110645907},"200":{"tf":2.449489742783178},"201":{"tf":2.0},"203":{"tf":2.23606797749979},"204":{"tf":1.4142135623730951},"207":{"tf":1.0},"210":{"tf":1.7320508075688772},"214":{"tf":1.4142135623730951},"215":{"tf":1.0},"216":{"tf":1.0},"225":{"tf":1.0},"230":{"tf":1.0},"233":{"tf":1.0},"238":{"tf":1.0},"243":{"tf":1.0},"248":{"tf":1.4142135623730951},"251":{"tf":1.4142135623730951},"252":{"tf":1.7320508075688772},"253":{"tf":1.0},"255":{"tf":1.4142135623730951},"257":{"tf":1.7320508075688772},"264":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.7320508075688772},"270":{"tf":2.23606797749979},"271":{"tf":1.0},"272":{"tf":1.4142135623730951},"273":{"tf":1.0},"282":{"tf":1.4142135623730951},"291":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.4142135623730951},"326":{"tf":1.7320508075688772},"329":{"tf":1.7320508075688772},"362":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.7320508075688772},"371":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":2.0},"379":{"tf":1.0},"38":{"tf":1.4142135623730951},"385":{"tf":1.0},"39":{"tf":1.0},"41":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.4142135623730951},"414":{"tf":1.7320508075688772},"415":{"tf":1.4142135623730951},"416":{"tf":1.4142135623730951},"417":{"tf":1.4142135623730951},"418":{"tf":2.0},"423":{"tf":1.4142135623730951},"429":{"tf":1.0},"436":{"tf":1.4142135623730951},"444":{"tf":1.0},"450":{"tf":1.4142135623730951},"454":{"tf":1.4142135623730951},"467":{"tf":1.4142135623730951},"468":{"tf":1.0},"469":{"tf":1.0},"479":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.4142135623730951},"507":{"tf":1.4142135623730951},"51":{"tf":1.4142135623730951},"514":{"tf":1.7320508075688772},"515":{"tf":3.0},"518":{"tf":1.0},"521":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"539":{"tf":1.0},"54":{"tf":1.7320508075688772},"542":{"tf":1.0},"552":{"tf":1.0},"553":{"tf":1.0},"564":{"tf":2.0},"565":{"tf":1.7320508075688772},"567":{"tf":1.7320508075688772},"568":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.0},"600":{"tf":1.7320508075688772},"606":{"tf":1.0},"627":{"tf":1.0},"630":{"tf":1.0},"634":{"tf":1.4142135623730951},"697":{"tf":1.0},"699":{"tf":1.0},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"723":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.4142135623730951},"745":{"tf":1.4142135623730951},"756":{"tf":1.0},"759":{"tf":1.4142135623730951},"772":{"tf":1.0},"773":{"tf":1.4142135623730951},"774":{"tf":1.7320508075688772},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"798":{"tf":1.0},"801":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.7320508075688772},"812":{"tf":1.0},"826":{"tf":1.0},"829":{"tf":1.0},"857":{"tf":1.0},"861":{"tf":1.4142135623730951},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"877":{"tf":1.4142135623730951},"878":{"tf":1.4142135623730951},"888":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.7320508075688772},"897":{"tf":1.4142135623730951},"911":{"tf":1.0},"912":{"tf":1.4142135623730951},"927":{"tf":1.4142135623730951},"928":{"tf":1.7320508075688772},"931":{"tf":1.0},"933":{"tf":1.4142135623730951},"935":{"tf":1.0},"971":{"tf":1.0},"996":{"tf":1.0}},"’":{"df":3,"docs":{"147":{"tf":1.0},"959":{"tf":1.0},"971":{"tf":1.0}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"191":{"tf":1.0},"804":{"tf":1.0},"853":{"tf":1.0}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"50":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"m":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"25":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":10,"docs":{"21":{"tf":1.0},"22":{"tf":1.0},"23":{"tf":1.7320508075688772},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"28":{"tf":1.0},"29":{"tf":1.7320508075688772},"30":{"tf":1.0},"33":{"tf":1.0}}}}},"d":{"a":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"699":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"219":{"tf":1.0}}}}},"df":0,"docs":{}},"l":{"df":11,"docs":{"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":2.0},"125":{"tf":1.4142135623730951},"126":{"tf":4.358898943540674},"127":{"tf":1.4142135623730951},"132":{"tf":1.0},"134":{"tf":1.0},"281":{"tf":1.0},"284":{"tf":1.7320508075688772},"847":{"tf":1.0}}}},"o":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}},"df":9,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":2.0},"206":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":2.0},"218":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"370":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"208":{"tf":2.8284271247461903}}}}}},"r":{"df":2,"docs":{"599":{"tf":1.0},"615":{"tf":1.0}}}},"p":{"(":{"df":1,"docs":{"333":{"tf":1.0}}},"df":1,"docs":{"797":{"tf":1.0}},"p":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":3,"docs":{"410":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"40":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":10,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.0},"517":{"tf":1.0},"563":{"tf":1.0},"568":{"tf":1.0},"762":{"tf":1.0},"815":{"tf":1.0},"932":{"tf":1.0},"992":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"e":{"df":10,"docs":{"124":{"tf":1.0},"138":{"tf":1.0},"365":{"tf":1.0},"418":{"tf":1.0},"432":{"tf":1.0},"51":{"tf":1.0},"575":{"tf":1.0},"777":{"tf":1.0},"911":{"tf":1.0},"938":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":16,"docs":{"184":{"tf":1.0},"187":{"tf":1.0},"231":{"tf":1.0},"30":{"tf":1.0},"343":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.0},"700":{"tf":1.0},"729":{"tf":1.0},"735":{"tf":1.0},"783":{"tf":1.0},"797":{"tf":1.0},"8":{"tf":1.0},"800":{"tf":1.0},"835":{"tf":1.0},"939":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"439":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":85,"docs":{"1008":{"tf":1.0},"1015":{"tf":1.0},"112":{"tf":1.0},"114":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.0},"130":{"tf":1.0},"140":{"tf":1.4142135623730951},"155":{"tf":1.0},"184":{"tf":1.0},"196":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"249":{"tf":1.0},"262":{"tf":1.0},"281":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"3":{"tf":1.7320508075688772},"303":{"tf":1.7320508075688772},"315":{"tf":1.0},"316":{"tf":1.4142135623730951},"343":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0},"450":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"460":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.7320508075688772},"512":{"tf":1.7320508075688772},"515":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"521":{"tf":1.7320508075688772},"523":{"tf":1.4142135623730951},"540":{"tf":1.0},"567":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"586":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"653":{"tf":1.4142135623730951},"665":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.0},"706":{"tf":1.0},"724":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":1.0},"740":{"tf":1.7320508075688772},"741":{"tf":1.0},"744":{"tf":1.0},"755":{"tf":1.4142135623730951},"759":{"tf":3.1622776601683795},"761":{"tf":2.449489742783178},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"772":{"tf":1.0},"777":{"tf":1.0},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"799":{"tf":1.0},"83":{"tf":1.0},"844":{"tf":1.0},"85":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.4142135623730951},"928":{"tf":1.0},"929":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.0},"934":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"292":{"tf":1.0}}}}}}}},"df":13,"docs":{"277":{"tf":1.0},"292":{"tf":1.0},"756":{"tf":1.0},"776":{"tf":1.0},"832":{"tf":1.0},"841":{"tf":1.4142135623730951},"842":{"tf":1.7320508075688772},"843":{"tf":1.4142135623730951},"844":{"tf":1.0},"847":{"tf":2.8284271247461903},"848":{"tf":1.7320508075688772},"849":{"tf":2.0},"852":{"tf":1.4142135623730951}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"121":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"697":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"932":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":48,"docs":{"112":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.0},"19":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"210":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"365":{"tf":1.4142135623730951},"418":{"tf":1.4142135623730951},"422":{"tf":1.0},"429":{"tf":1.0},"453":{"tf":1.0},"563":{"tf":1.0},"565":{"tf":1.0},"568":{"tf":1.0},"573":{"tf":1.4142135623730951},"576":{"tf":1.4142135623730951},"58":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.4142135623730951},"582":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":1.0},"697":{"tf":1.0},"722":{"tf":1.0},"752":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"807":{"tf":1.0},"818":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"903":{"tf":1.0},"911":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.0},"945":{"tf":1.4142135623730951},"955":{"tf":1.0},"962":{"tf":1.4142135623730951}}}}}}},"v":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"450":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":12,"docs":{"203":{"tf":1.0},"239":{"tf":1.4142135623730951},"376":{"tf":1.0},"409":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"444":{"tf":1.4142135623730951},"62":{"tf":1.4142135623730951},"628":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"78":{"tf":1.7320508075688772}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":1,"docs":{"184":{"tf":1.0}}}}}}}}}}},"df":12,"docs":{"111":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.0},"375":{"tf":1.0},"378":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.4142135623730951},"796":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":2.23606797749979},"850":{"tf":1.0},"912":{"tf":1.0}}}}}},"p":{"df":1,"docs":{"126":{"tf":2.449489742783178}},"p":{"df":1,"docs":{"735":{"tf":1.0}}}},"r":{"#":{"3":{"3":{"0":{"0":{"df":1,"docs":{"878":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"6":{"8":{"5":{"df":2,"docs":{"169":{"tf":1.0},"171":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"[":{"df":0,"docs":{},"x":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}},"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":22,"docs":{"198":{"tf":1.0},"261":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"41":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"511":{"tf":1.0},"539":{"tf":1.0},"567":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"615":{"tf":1.4142135623730951},"632":{"tf":1.0},"660":{"tf":1.0},"697":{"tf":1.4142135623730951},"723":{"tf":1.0},"735":{"tf":1.0},"928":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"375":{"tf":1.0},"467":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":10,"docs":{"312":{"tf":1.0},"315":{"tf":1.0},"359":{"tf":1.0},"447":{"tf":1.0},"546":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"878":{"tf":1.4142135623730951},"954":{"tf":1.0},"985":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"c":{"df":0,"docs":{},"e":{"d":{"df":4,"docs":{"203":{"tf":1.0},"735":{"tf":1.0},"843":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"201":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"s":{"df":2,"docs":{"251":{"tf":1.0},"38":{"tf":1.0}}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"105":{"tf":1.0}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"333":{"tf":1.0},"427":{"tf":1.0}}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":16,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.7320508075688772},"427":{"tf":1.0},"429":{"tf":1.0},"505":{"tf":1.0},"576":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"979":{"tf":1.0},"983":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"203":{"tf":1.0}}}}}}},"df":16,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"516":{"tf":1.0},"537":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.4142135623730951},"72":{"tf":1.0},"74":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"811":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.7320508075688772},"832":{"tf":1.0},"912":{"tf":1.7320508075688772},"933":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":14,"docs":{"1004":{"tf":1.0},"264":{"tf":1.0},"292":{"tf":1.0},"374":{"tf":1.0},"53":{"tf":1.0},"550":{"tf":1.0},"565":{"tf":1.0},"66":{"tf":1.0},"666":{"tf":1.0},"69":{"tf":1.0},"722":{"tf":1.4142135623730951},"761":{"tf":1.0},"81":{"tf":1.0},"831":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}}}}},"r":{"df":1,"docs":{"267":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"x":{"df":7,"docs":{"253":{"tf":1.0},"520":{"tf":1.4142135623730951},"735":{"tf":2.0},"759":{"tf":2.0},"786":{"tf":1.0},"933":{"tf":1.0},"992":{"tf":1.0}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":9,"docs":{"47":{"tf":1.7320508075688772},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"85":{"tf":1.7320508075688772},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"437":{"tf":1.0},"444":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"773":{"tf":1.0}}},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"231":{"tf":1.0},"776":{"tf":1.4142135623730951}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":17,"docs":{"126":{"tf":1.7320508075688772},"279":{"tf":2.23606797749979},"280":{"tf":1.0},"281":{"tf":1.0},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":1.0},"740":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"846":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"44":{"tf":1.0}}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"602":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":38,"docs":{"1004":{"tf":1.0},"155":{"tf":1.0},"169":{"tf":1.0},"175":{"tf":1.0},"195":{"tf":1.0},"198":{"tf":1.7320508075688772},"199":{"tf":1.4142135623730951},"201":{"tf":1.4142135623730951},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"227":{"tf":1.0},"264":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"430":{"tf":1.0},"436":{"tf":1.4142135623730951},"480":{"tf":1.0},"503":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":1.0},"564":{"tf":1.0},"644":{"tf":1.0},"711":{"tf":1.0},"725":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.0},"771":{"tf":1.0},"774":{"tf":1.0},"777":{"tf":1.0},"801":{"tf":1.0},"807":{"tf":1.0},"829":{"tf":1.0},"84":{"tf":1.0},"843":{"tf":1.0},"931":{"tf":1.0},"990":{"tf":1.0}}}},"r":{"df":0,"docs":{},"v":{"df":8,"docs":{"126":{"tf":1.0},"435":{"tf":1.0},"516":{"tf":1.0},"6":{"tf":1.0},"698":{"tf":1.4142135623730951},"700":{"tf":1.0},"71":{"tf":1.0},"772":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"698":{"tf":1.7320508075688772},"700":{"tf":1.0},"705":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":4,"docs":{"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"945":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"577":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"399":{"tf":1.0},"732":{"tf":1.0},"894":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":32,"docs":{"111":{"tf":1.0},"142":{"tf":1.0},"152":{"tf":1.0},"255":{"tf":1.0},"30":{"tf":1.0},"346":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"411":{"tf":1.0},"418":{"tf":1.0},"428":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"567":{"tf":1.0},"576":{"tf":1.0},"577":{"tf":1.0},"629":{"tf":1.4142135623730951},"69":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"799":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":1.0},"863":{"tf":1.0},"911":{"tf":1.0},"913":{"tf":1.0},"948":{"tf":1.0},"951":{"tf":1.0},"955":{"tf":1.0},"961":{"tf":1.0},"972":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":30,"docs":{"132":{"tf":1.0},"147":{"tf":1.0},"204":{"tf":2.449489742783178},"205":{"tf":1.0},"207":{"tf":2.0},"267":{"tf":1.0},"285":{"tf":1.0},"345":{"tf":1.0},"414":{"tf":1.0},"418":{"tf":1.7320508075688772},"45":{"tf":1.7320508075688772},"46":{"tf":1.7320508075688772},"524":{"tf":1.0},"532":{"tf":1.0},"623":{"tf":1.0},"64":{"tf":1.0},"665":{"tf":1.0},"67":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"761":{"tf":1.0},"937":{"tf":1.0},"953":{"tf":1.0},"985":{"tf":1.0}},"s":{"df":11,"docs":{"166":{"tf":1.0},"177":{"tf":1.0},"205":{"tf":1.0},"303":{"tf":1.0},"344":{"tf":1.0},"347":{"tf":1.0},"62":{"tf":1.0},"71":{"tf":1.0},"735":{"tf":1.0},"771":{"tf":1.0},"979":{"tf":1.0}}}}}}}},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"776":{"tf":1.4142135623730951}}}}}}}}}},"df":37,"docs":{"203":{"tf":2.23606797749979},"204":{"tf":3.605551275463989},"205":{"tf":3.605551275463989},"206":{"tf":1.4142135623730951},"207":{"tf":4.795831523312719},"213":{"tf":2.449489742783178},"267":{"tf":1.7320508075688772},"410":{"tf":1.0},"413":{"tf":1.0},"415":{"tf":1.0},"428":{"tf":2.449489742783178},"429":{"tf":1.4142135623730951},"741":{"tf":2.449489742783178},"742":{"tf":2.8284271247461903},"743":{"tf":2.449489742783178},"744":{"tf":2.8284271247461903},"745":{"tf":1.0},"746":{"tf":1.0},"747":{"tf":1.7320508075688772},"748":{"tf":1.7320508075688772},"749":{"tf":2.0},"75":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":3.3166247903554},"752":{"tf":3.7416573867739413},"753":{"tf":1.0},"754":{"tf":1.7320508075688772},"755":{"tf":1.0},"756":{"tf":1.4142135623730951},"772":{"tf":2.23606797749979},"773":{"tf":3.7416573867739413},"776":{"tf":4.123105625617661},"777":{"tf":3.7416573867739413},"779":{"tf":1.4142135623730951},"912":{"tf":2.23606797749979},"944":{"tf":1.4142135623730951},"959":{"tf":1.0}}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":25,"docs":{"1004":{"tf":1.0},"1005":{"tf":1.0},"185":{"tf":1.0},"201":{"tf":1.0},"219":{"tf":1.0},"231":{"tf":1.0},"236":{"tf":1.0},"240":{"tf":1.0},"322":{"tf":1.0},"340":{"tf":1.0},"349":{"tf":2.0},"351":{"tf":1.7320508075688772},"368":{"tf":1.0},"380":{"tf":1.0},"414":{"tf":1.0},"422":{"tf":1.0},"469":{"tf":1.0},"745":{"tf":1.0},"774":{"tf":1.0},"776":{"tf":1.0},"798":{"tf":1.0},"81":{"tf":1.4142135623730951},"845":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"231":{"tf":1.0},"324":{"tf":1.0},"342":{"tf":1.0},"55":{"tf":1.0},"631":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"843":{"tf":1.0},"951":{"tf":1.0}}}}},"y":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"350":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":10,"docs":{"322":{"tf":1.0},"340":{"tf":2.0},"375":{"tf":1.0},"522":{"tf":3.3166247903554},"524":{"tf":2.449489742783178},"627":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.7320508075688772},"643":{"tf":1.0}}}}},"n":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"255":{"tf":1.0},"67":{"tf":1.0},"720":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":2,"docs":{"722":{"tf":1.0},"894":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":131,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.7320508075688772},"105":{"tf":1.4142135623730951},"106":{"tf":1.0},"120":{"tf":1.4142135623730951},"122":{"tf":1.0},"133":{"tf":1.4142135623730951},"136":{"tf":1.0},"14":{"tf":1.4142135623730951},"147":{"tf":1.4142135623730951},"150":{"tf":1.0},"161":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.4142135623730951},"182":{"tf":1.0},"192":{"tf":1.4142135623730951},"195":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.0},"211":{"tf":1.0},"214":{"tf":1.4142135623730951},"215":{"tf":1.0},"221":{"tf":1.0},"228":{"tf":1.4142135623730951},"229":{"tf":1.4142135623730951},"242":{"tf":1.4142135623730951},"244":{"tf":1.4142135623730951},"247":{"tf":1.0},"260":{"tf":1.4142135623730951},"267":{"tf":1.0},"268":{"tf":1.0},"277":{"tf":1.4142135623730951},"279":{"tf":1.0},"291":{"tf":1.4142135623730951},"294":{"tf":1.0},"308":{"tf":1.4142135623730951},"311":{"tf":1.0},"319":{"tf":1.4142135623730951},"322":{"tf":1.0},"35":{"tf":1.4142135623730951},"359":{"tf":1.4142135623730951},"366":{"tf":1.0},"367":{"tf":1.0},"383":{"tf":1.4142135623730951},"386":{"tf":1.0},"397":{"tf":1.4142135623730951},"400":{"tf":1.0},"409":{"tf":1.4142135623730951},"430":{"tf":1.0},"447":{"tf":1.4142135623730951},"451":{"tf":1.0},"46":{"tf":1.0},"462":{"tf":1.4142135623730951},"465":{"tf":1.0},"479":{"tf":1.4142135623730951},"481":{"tf":1.0},"492":{"tf":1.4142135623730951},"495":{"tf":1.0},"510":{"tf":1.4142135623730951},"513":{"tf":1.0},"532":{"tf":1.4142135623730951},"535":{"tf":1.0},"546":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.4142135623730951},"563":{"tf":1.0},"583":{"tf":1.4142135623730951},"584":{"tf":1.0},"595":{"tf":1.4142135623730951},"598":{"tf":1.0},"610":{"tf":1.4142135623730951},"613":{"tf":1.0},"624":{"tf":1.4142135623730951},"627":{"tf":1.0},"646":{"tf":1.4142135623730951},"649":{"tf":1.0},"661":{"tf":1.4142135623730951},"664":{"tf":1.0},"675":{"tf":1.4142135623730951},"678":{"tf":1.0},"689":{"tf":1.4142135623730951},"692":{"tf":1.0},"706":{"tf":1.4142135623730951},"709":{"tf":1.0},"726":{"tf":1.4142135623730951},"730":{"tf":1.0},"738":{"tf":1.4142135623730951},"74":{"tf":1.4142135623730951},"741":{"tf":1.0},"754":{"tf":1.4142135623730951},"757":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.4142135623730951},"771":{"tf":1.0},"780":{"tf":1.4142135623730951},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.4142135623730951},"795":{"tf":1.0},"805":{"tf":1.4142135623730951},"808":{"tf":1.0},"824":{"tf":1.7320508075688772},"827":{"tf":1.0},"838":{"tf":1.4142135623730951},"857":{"tf":1.0},"869":{"tf":1.4142135623730951},"871":{"tf":1.0},"888":{"tf":1.4142135623730951},"891":{"tf":1.0},"90":{"tf":1.4142135623730951},"905":{"tf":1.7320508075688772},"908":{"tf":1.4142135623730951},"913":{"tf":1.0},"922":{"tf":1.4142135623730951},"923":{"tf":1.7320508075688772},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.4142135623730951},"940":{"tf":1.0},"954":{"tf":1.4142135623730951},"957":{"tf":1.0},"971":{"tf":1.4142135623730951},"974":{"tf":1.0},"985":{"tf":1.4142135623730951},"988":{"tf":1.0},"999":{"tf":1.4142135623730951}},"i":{"df":1,"docs":{"724":{"tf":1.0}},"t":{"df":3,"docs":{"375":{"tf":1.0},"58":{"tf":1.0},"779":{"tf":1.0}},"i":{"df":8,"docs":{"203":{"tf":1.0},"63":{"tf":1.4142135623730951},"69":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0}}}}}}},"v":{"a":{"c":{"df":0,"docs":{},"i":{"df":123,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.7320508075688772},"106":{"tf":1.0},"115":{"tf":1.7320508075688772},"122":{"tf":1.0},"128":{"tf":1.7320508075688772},"136":{"tf":1.0},"142":{"tf":1.7320508075688772},"150":{"tf":1.0},"156":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.7320508075688772},"182":{"tf":1.0},"188":{"tf":1.4142135623730951},"195":{"tf":1.0},"211":{"tf":1.7320508075688772},"215":{"tf":1.0},"225":{"tf":1.7320508075688772},"229":{"tf":1.0},"237":{"tf":1.4142135623730951},"247":{"tf":1.0},"255":{"tf":1.4142135623730951},"268":{"tf":1.0},"275":{"tf":1.4142135623730951},"279":{"tf":1.0},"286":{"tf":1.7320508075688772},"294":{"tf":1.0},"30":{"tf":1.4142135623730951},"304":{"tf":1.7320508075688772},"311":{"tf":1.0},"317":{"tf":1.4142135623730951},"322":{"tf":1.0},"354":{"tf":1.4142135623730951},"365":{"tf":1.0},"366":{"tf":1.0},"378":{"tf":1.4142135623730951},"38":{"tf":1.0},"386":{"tf":1.0},"392":{"tf":1.7320508075688772},"410":{"tf":1.0},"419":{"tf":1.4142135623730951},"430":{"tf":1.0},"442":{"tf":1.7320508075688772},"451":{"tf":1.0},"457":{"tf":1.4142135623730951},"465":{"tf":1.0},"474":{"tf":1.4142135623730951},"481":{"tf":1.0},"487":{"tf":1.4142135623730951},"495":{"tf":1.0},"505":{"tf":1.4142135623730951},"513":{"tf":1.0},"528":{"tf":1.7320508075688772},"53":{"tf":1.7320508075688772},"535":{"tf":1.0},"541":{"tf":1.7320508075688772},"549":{"tf":1.0},"555":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"578":{"tf":1.4142135623730951},"584":{"tf":1.0},"590":{"tf":1.7320508075688772},"598":{"tf":1.0},"605":{"tf":1.4142135623730951},"613":{"tf":1.0},"619":{"tf":1.4142135623730951},"627":{"tf":1.0},"639":{"tf":1.7320508075688772},"649":{"tf":1.0},"656":{"tf":1.4142135623730951},"664":{"tf":1.0},"670":{"tf":1.4142135623730951},"678":{"tf":1.0},"684":{"tf":1.4142135623730951},"69":{"tf":1.7320508075688772},"692":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":1.4142135623730951},"709":{"tf":1.0},"724":{"tf":1.4142135623730951},"757":{"tf":1.0},"763":{"tf":1.4142135623730951},"782":{"tf":1.0},"788":{"tf":1.7320508075688772},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"801":{"tf":1.4142135623730951},"808":{"tf":1.0},"819":{"tf":1.7320508075688772},"827":{"tf":1.0},"833":{"tf":1.4142135623730951},"841":{"tf":1.0},"85":{"tf":1.4142135623730951},"850":{"tf":1.4142135623730951},"857":{"tf":1.0},"864":{"tf":1.7320508075688772},"871":{"tf":1.0},"883":{"tf":1.4142135623730951},"891":{"tf":1.0},"894":{"tf":1.4142135623730951},"9":{"tf":1.4142135623730951},"900":{"tf":1.7320508075688772},"908":{"tf":1.0},"917":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"935":{"tf":1.4142135623730951},"940":{"tf":1.4142135623730951},"946":{"tf":1.4142135623730951},"949":{"tf":1.7320508075688772},"957":{"tf":1.4142135623730951},"963":{"tf":1.4142135623730951},"966":{"tf":1.7320508075688772},"974":{"tf":1.0},"980":{"tf":1.4142135623730951},"988":{"tf":1.0},"99":{"tf":1.4142135623730951},"994":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"t":{"df":8,"docs":{"206":{"tf":1.7320508075688772},"452":{"tf":1.4142135623730951},"453":{"tf":1.7320508075688772},"455":{"tf":1.0},"528":{"tf":1.0},"565":{"tf":1.0},"81":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"e":{"(":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":5,"docs":{"184":{"tf":1.0},"234":{"tf":1.0},"3":{"tf":1.0},"300":{"tf":1.0},"349":{"tf":1.0}}}}}}}},"o":{"b":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":1.0},"347":{"tf":1.0}}}}}}},"l":{"df":8,"docs":{"127":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.7320508075688772},"534":{"tf":1.0},"740":{"tf":1.0},"849":{"tf":1.0},"936":{"tf":1.0},"984":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"388":{"tf":1.0},"723":{"tf":1.0}}}},"df":39,"docs":{"1004":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"161":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.7320508075688772},"231":{"tf":1.0},"234":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"252":{"tf":1.0},"257":{"tf":1.4142135623730951},"388":{"tf":1.0},"441":{"tf":1.0},"450":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.4142135623730951},"512":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"551":{"tf":1.4142135623730951},"629":{"tf":1.0},"63":{"tf":1.0},"694":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"757":{"tf":1.0},"77":{"tf":1.4142135623730951},"818":{"tf":1.0},"832":{"tf":1.0},"871":{"tf":1.0},"874":{"tf":1.4142135623730951},"891":{"tf":1.0},"895":{"tf":1.4142135623730951},"908":{"tf":1.0},"912":{"tf":1.4142135623730951},"928":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":6,"docs":{"333":{"tf":1.0},"344":{"tf":1.0},"349":{"tf":1.4142135623730951},"351":{"tf":1.0},"364":{"tf":1.0},"435":{"tf":1.0}}}}},"df":2,"docs":{"112":{"tf":1.0},"198":{"tf":1.0}},"s":{"df":0,"docs":{},"s":{"df":69,"docs":{"106":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.7320508075688772},"126":{"tf":1.0},"132":{"tf":1.0},"145":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.0},"207":{"tf":1.7320508075688772},"209":{"tf":1.0},"24":{"tf":1.0},"268":{"tf":2.23606797749979},"269":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"277":{"tf":1.0},"278":{"tf":1.0},"284":{"tf":1.4142135623730951},"296":{"tf":1.4142135623730951},"3":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.0},"337":{"tf":1.0},"345":{"tf":1.0},"350":{"tf":1.0},"364":{"tf":1.0},"38":{"tf":1.0},"436":{"tf":1.0},"441":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.4142135623730951},"459":{"tf":1.0},"46":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"503":{"tf":1.0},"521":{"tf":1.0},"528":{"tf":1.0},"537":{"tf":1.0},"56":{"tf":1.0},"57":{"tf":1.4142135623730951},"64":{"tf":1.7320508075688772},"640":{"tf":1.4142135623730951},"644":{"tf":1.0},"65":{"tf":1.0},"694":{"tf":1.0},"715":{"tf":1.0},"735":{"tf":1.4142135623730951},"77":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"826":{"tf":1.0},"83":{"tf":1.0},"876":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":2.23606797749979},"942":{"tf":1.0},"95":{"tf":1.0},"989":{"tf":1.0},"990":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"u":{"c":{"df":20,"docs":{"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.0},"151":{"tf":1.0},"159":{"tf":1.0},"295":{"tf":1.0},"297":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"342":{"tf":1.4142135623730951},"345":{"tf":1.4142135623730951},"349":{"tf":1.0},"44":{"tf":1.0},"532":{"tf":1.0},"63":{"tf":1.0},"829":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"160":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"t":{"df":11,"docs":{"107":{"tf":1.0},"155":{"tf":1.0},"323":{"tf":1.0},"339":{"tf":1.0},"372":{"tf":1.0},"53":{"tf":1.0},"577":{"tf":1.0},"640":{"tf":1.0},"712":{"tf":1.4142135623730951},"714":{"tf":1.0},"778":{"tf":1.0}}}},"df":0,"docs":{}}},"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"211":{"tf":1.0},"849":{"tf":1.0}}}}}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"469":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":6,"docs":{"231":{"tf":1.0},"267":{"tf":1.0},"711":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"912":{"tf":1.4142135623730951}}}}},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"26":{"tf":1.0}}},"df":36,"docs":{"147":{"tf":1.0},"17":{"tf":1.4142135623730951},"21":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"23":{"tf":1.7320508075688772},"24":{"tf":1.4142135623730951},"25":{"tf":2.23606797749979},"26":{"tf":3.0},"270":{"tf":1.0},"28":{"tf":2.23606797749979},"29":{"tf":1.0},"33":{"tf":1.0},"374":{"tf":1.0},"600":{"tf":2.23606797749979},"602":{"tf":2.8284271247461903},"606":{"tf":1.4142135623730951},"608":{"tf":1.0},"609":{"tf":1.7320508075688772},"615":{"tf":1.0},"619":{"tf":1.0},"623":{"tf":1.0},"653":{"tf":1.4142135623730951},"654":{"tf":1.0},"673":{"tf":1.4142135623730951},"693":{"tf":1.0},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"701":{"tf":2.0},"704":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0},"738":{"tf":1.0},"799":{"tf":1.0},"83":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.0}},"m":{"df":2,"docs":{"959":{"tf":1.0},"966":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":7,"docs":{"105":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":1.0},"343":{"tf":1.0},"447":{"tf":1.0},"467":{"tf":1.0},"77":{"tf":1.0}}}}}}},"h":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"414":{"tf":1.0},"428":{"tf":1.0}}}}},"df":0,"docs":{}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":10,"docs":{"185":{"tf":1.0},"200":{"tf":1.0},"267":{"tf":1.4142135623730951},"388":{"tf":1.0},"390":{"tf":1.0},"465":{"tf":1.0},"471":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"778":{"tf":1.0},"991":{"tf":1.0}}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"565":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":4,"docs":{"303":{"tf":1.0},"44":{"tf":1.0},"81":{"tf":1.0},"852":{"tf":1.4142135623730951}}}},"o":{"df":0,"docs":{},"t":{"df":5,"docs":{"272":{"tf":1.0},"326":{"tf":1.0},"467":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"e":{"df":1,"docs":{"962":{"tf":1.0}}}},"o":{"df":0,"docs":{},"f":{"df":54,"docs":{"1004":{"tf":1.0},"155":{"tf":1.4142135623730951},"336":{"tf":1.0},"337":{"tf":1.0},"38":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":2.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.0},"404":{"tf":2.23606797749979},"406":{"tf":1.4142135623730951},"407":{"tf":1.4142135623730951},"439":{"tf":2.6457513110645907},"44":{"tf":1.7320508075688772},"45":{"tf":1.7320508075688772},"451":{"tf":2.23606797749979},"452":{"tf":1.7320508075688772},"453":{"tf":1.0},"454":{"tf":1.0},"455":{"tf":3.1622776601683795},"456":{"tf":1.0},"457":{"tf":1.4142135623730951},"458":{"tf":1.0},"459":{"tf":1.7320508075688772},"46":{"tf":2.0},"460":{"tf":1.4142135623730951},"461":{"tf":1.4142135623730951},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.0},"49":{"tf":1.0},"500":{"tf":2.23606797749979},"51":{"tf":1.7320508075688772},"514":{"tf":1.0},"517":{"tf":1.4142135623730951},"520":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"55":{"tf":1.4142135623730951},"565":{"tf":1.0},"567":{"tf":1.0},"628":{"tf":1.0},"648":{"tf":1.0},"754":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":2.23606797749979},"762":{"tf":2.23606797749979},"763":{"tf":1.7320508075688772},"83":{"tf":1.0},"843":{"tf":1.0},"885":{"tf":1.0},"913":{"tf":1.0},"992":{"tf":1.7320508075688772}}}},"p":{"a":{"df":0,"docs":{},"g":{"df":3,"docs":{"343":{"tf":1.0},"551":{"tf":1.0},"71":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":8,"docs":{"175":{"tf":1.0},"205":{"tf":1.0},"30":{"tf":1.0},"483":{"tf":1.0},"54":{"tf":1.0},"819":{"tf":1.0},"932":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"203":{"tf":1.0},"207":{"tf":1.0},"212":{"tf":1.0},"216":{"tf":1.0},"265":{"tf":1.0},"522":{"tf":1.0},"551":{"tf":1.0},"78":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":10,"docs":{"203":{"tf":1.0},"205":{"tf":1.4142135623730951},"402":{"tf":1.0},"438":{"tf":1.4142135623730951},"515":{"tf":1.0},"602":{"tf":1.0},"741":{"tf":1.0},"751":{"tf":1.4142135623730951},"84":{"tf":1.0},"912":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":9,"docs":{"51":{"tf":1.4142135623730951},"576":{"tf":1.0},"714":{"tf":1.4142135623730951},"723":{"tf":1.0},"814":{"tf":1.7320508075688772},"909":{"tf":1.0},"913":{"tf":2.0},"917":{"tf":1.0},"919":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":3,"docs":{"563":{"tf":1.0},"564":{"tf":1.0},"722":{"tf":1.0}}}}}}},"s":{"a":{"df":0,"docs":{},"l":{"'":{"df":1,"docs":{"124":{"tf":1.0}}},"(":{"df":1,"docs":{"209":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}}}}}}}},"df":232,"docs":{"0":{"tf":1.0},"1003":{"tf":1.4142135623730951},"1008":{"tf":1.4142135623730951},"1009":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1014":{"tf":1.0},"103":{"tf":1.0},"105":{"tf":1.0},"107":{"tf":1.0},"112":{"tf":2.0},"113":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"126":{"tf":1.0},"13":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"135":{"tf":1.0},"138":{"tf":1.0},"142":{"tf":1.0},"144":{"tf":1.0},"147":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.7320508075688772},"151":{"tf":1.0},"154":{"tf":1.4142135623730951},"155":{"tf":1.0},"165":{"tf":1.0},"18":{"tf":1.0},"183":{"tf":1.0},"186":{"tf":1.4142135623730951},"196":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":2.8284271247461903},"209":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"212":{"tf":1.4142135623730951},"216":{"tf":1.4142135623730951},"221":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.4142135623730951},"230":{"tf":1.0},"231":{"tf":2.0},"234":{"tf":1.0},"238":{"tf":1.0},"248":{"tf":1.0},"269":{"tf":1.0},"272":{"tf":1.7320508075688772},"294":{"tf":1.0},"295":{"tf":1.0},"3":{"tf":1.0},"301":{"tf":1.7320508075688772},"302":{"tf":1.0},"312":{"tf":1.0},"317":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"347":{"tf":1.0},"35":{"tf":1.0},"366":{"tf":1.0},"367":{"tf":1.0},"37":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"379":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"387":{"tf":1.0},"39":{"tf":1.0},"390":{"tf":1.4142135623730951},"397":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.0},"407":{"tf":1.0},"409":{"tf":1.0},"410":{"tf":1.0},"411":{"tf":1.0},"412":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.0},"418":{"tf":1.0},"423":{"tf":1.0},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"431":{"tf":1.0},"438":{"tf":1.0},"442":{"tf":1.0},"452":{"tf":1.7320508075688772},"465":{"tf":1.0},"466":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"482":{"tf":1.0},"485":{"tf":1.0},"496":{"tf":1.0},"5":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"519":{"tf":1.0},"525":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"536":{"tf":1.0},"539":{"tf":1.0},"542":{"tf":1.0},"546":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":1.4142135623730951},"567":{"tf":1.0},"569":{"tf":1.4142135623730951},"571":{"tf":1.0},"583":{"tf":1.0},"585":{"tf":1.0},"599":{"tf":1.0},"600":{"tf":1.0},"602":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"614":{"tf":1.0},"615":{"tf":1.0},"617":{"tf":1.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.0},"631":{"tf":1.4142135623730951},"632":{"tf":1.0},"642":{"tf":1.0},"650":{"tf":1.0},"658":{"tf":1.0},"660":{"tf":1.0},"663":{"tf":1.7320508075688772},"7":{"tf":1.0},"705":{"tf":1.0},"709":{"tf":1.0},"71":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"727":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"752":{"tf":1.0},"754":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.0},"763":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":2.449489742783178},"776":{"tf":1.4142135623730951},"779":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.0},"786":{"tf":2.0},"787":{"tf":1.0},"788":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"796":{"tf":1.4142135623730951},"799":{"tf":1.0},"80":{"tf":1.0},"809":{"tf":1.4142135623730951},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"829":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"842":{"tf":1.4142135623730951},"843":{"tf":1.4142135623730951},"846":{"tf":1.0},"847":{"tf":1.7320508075688772},"848":{"tf":1.7320508075688772},"85":{"tf":1.0},"858":{"tf":1.0},"860":{"tf":1.0},"870":{"tf":1.0},"872":{"tf":2.23606797749979},"875":{"tf":1.7320508075688772},"878":{"tf":2.449489742783178},"879":{"tf":6.324555320336759},"88":{"tf":1.0},"880":{"tf":2.449489742783178},"881":{"tf":3.1622776601683795},"885":{"tf":2.0},"890":{"tf":1.4142135623730951},"892":{"tf":1.0},"902":{"tf":1.0},"909":{"tf":1.4142135623730951},"919":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.4142135623730951},"928":{"tf":2.23606797749979},"929":{"tf":1.0},"931":{"tf":1.4142135623730951},"933":{"tf":1.7320508075688772},"934":{"tf":1.0},"936":{"tf":1.0},"938":{"tf":1.0},"94":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.0},"945":{"tf":1.0},"949":{"tf":1.0},"953":{"tf":1.0},"956":{"tf":1.0},"958":{"tf":1.0},"959":{"tf":1.0},"966":{"tf":1.0},"97":{"tf":1.4142135623730951},"970":{"tf":1.0},"971":{"tf":1.0},"975":{"tf":1.0},"987":{"tf":1.0},"989":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":1,"docs":{"553":{"tf":1.0}}}},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"270":{"tf":1.0},"564":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"199":{"tf":1.0},"799":{"tf":1.0},"909":{"tf":1.0},"912":{"tf":1.0},"914":{"tf":1.0}}}},"df":0,"docs":{}}}},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"108":{"tf":1.0},"763":{"tf":1.4142135623730951},"777":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"2":{"df":1,"docs":{"253":{"tf":1.0}}},"3":{"df":1,"docs":{"553":{"tf":1.0}}},"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":4,"docs":{"253":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"761":{"tf":1.0}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"'":{"df":3,"docs":{"185":{"tf":1.0},"325":{"tf":1.0},"343":{"tf":1.0}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"342":{"tf":1.4142135623730951},"346":{"tf":1.0}}}}}}}}}},"df":120,"docs":{"100":{"tf":1.0},"124":{"tf":1.4142135623730951},"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"188":{"tf":1.0},"190":{"tf":1.0},"201":{"tf":1.0},"230":{"tf":1.0},"234":{"tf":1.4142135623730951},"247":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":2.6457513110645907},"254":{"tf":1.0},"270":{"tf":1.7320508075688772},"322":{"tf":2.6457513110645907},"323":{"tf":2.0},"324":{"tf":1.4142135623730951},"325":{"tf":1.0},"326":{"tf":1.0},"327":{"tf":1.4142135623730951},"328":{"tf":1.4142135623730951},"329":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":1.4142135623730951},"334":{"tf":1.0},"335":{"tf":2.0},"336":{"tf":1.0},"337":{"tf":1.4142135623730951},"338":{"tf":1.0},"339":{"tf":1.0},"340":{"tf":1.4142135623730951},"341":{"tf":1.0},"342":{"tf":2.23606797749979},"343":{"tf":1.7320508075688772},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"348":{"tf":1.0},"349":{"tf":1.7320508075688772},"350":{"tf":1.0},"351":{"tf":1.0},"352":{"tf":1.0},"353":{"tf":1.0},"354":{"tf":1.0},"355":{"tf":1.0},"356":{"tf":1.4142135623730951},"357":{"tf":1.0},"358":{"tf":1.0},"359":{"tf":1.0},"360":{"tf":1.0},"361":{"tf":1.4142135623730951},"362":{"tf":1.0},"363":{"tf":1.7320508075688772},"364":{"tf":1.0},"365":{"tf":1.4142135623730951},"368":{"tf":1.0},"369":{"tf":1.0},"372":{"tf":1.0},"374":{"tf":1.0},"382":{"tf":1.0},"39":{"tf":1.0},"430":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":2.0},"440":{"tf":2.0},"441":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.7320508075688772},"473":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"486":{"tf":1.0},"49":{"tf":1.0},"502":{"tf":1.4142135623730951},"503":{"tf":1.0},"512":{"tf":1.0},"53":{"tf":1.0},"553":{"tf":1.4142135623730951},"554":{"tf":1.0},"559":{"tf":2.23606797749979},"565":{"tf":1.4142135623730951},"600":{"tf":1.0},"62":{"tf":1.4142135623730951},"629":{"tf":1.0},"635":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"709":{"tf":1.0},"710":{"tf":1.0},"712":{"tf":1.4142135623730951},"72":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.4142135623730951},"729":{"tf":1.0},"73":{"tf":1.4142135623730951},"745":{"tf":1.0},"757":{"tf":2.0},"758":{"tf":1.0},"759":{"tf":1.4142135623730951},"760":{"tf":1.0},"761":{"tf":2.6457513110645907},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"764":{"tf":1.0},"765":{"tf":1.0},"766":{"tf":1.0},"767":{"tf":1.7320508075688772},"768":{"tf":1.0},"769":{"tf":1.0},"770":{"tf":1.7320508075688772},"774":{"tf":1.0},"78":{"tf":1.0},"783":{"tf":1.0},"784":{"tf":1.4142135623730951},"786":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":3,"docs":{"209":{"tf":1.0},"221":{"tf":2.0},"222":{"tf":1.4142135623730951}}}}}}},"v":{"df":0,"docs":{},"e":{"df":9,"docs":{"339":{"tf":1.0},"46":{"tf":1.4142135623730951},"516":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"759":{"tf":1.4142135623730951},"83":{"tf":1.0},"847":{"tf":1.0},"95":{"tf":1.0}},"n":{"df":2,"docs":{"44":{"tf":1.0},"444":{"tf":1.0}}},"r":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}},"i":{"d":{"df":130,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.4142135623730951},"1013":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"111":{"tf":1.0},"121":{"tf":1.4142135623730951},"124":{"tf":1.0},"138":{"tf":1.0},"171":{"tf":1.0},"173":{"tf":1.0},"175":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"196":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":2.23606797749979},"206":{"tf":1.7320508075688772},"207":{"tf":1.0},"210":{"tf":1.0},"22":{"tf":1.0},"222":{"tf":1.4142135623730951},"231":{"tf":1.0},"232":{"tf":1.0},"233":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":2.0},"254":{"tf":1.0},"255":{"tf":2.0},"257":{"tf":1.7320508075688772},"272":{"tf":1.0},"276":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.7320508075688772},"30":{"tf":1.0},"303":{"tf":1.0},"315":{"tf":1.0},"325":{"tf":1.0},"35":{"tf":1.0},"364":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.7320508075688772},"375":{"tf":1.0},"376":{"tf":1.4142135623730951},"38":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"418":{"tf":1.0},"439":{"tf":1.0},"467":{"tf":1.4142135623730951},"47":{"tf":1.0},"470":{"tf":1.4142135623730951},"495":{"tf":1.4142135623730951},"500":{"tf":3.605551275463989},"501":{"tf":3.0},"502":{"tf":1.4142135623730951},"503":{"tf":2.23606797749979},"505":{"tf":1.4142135623730951},"507":{"tf":1.7320508075688772},"51":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"524":{"tf":1.0},"534":{"tf":1.0},"55":{"tf":1.0},"574":{"tf":1.0},"577":{"tf":1.0},"599":{"tf":1.0},"602":{"tf":1.7320508075688772},"629":{"tf":1.7320508075688772},"632":{"tf":1.4142135623730951},"640":{"tf":1.0},"641":{"tf":1.0},"673":{"tf":1.0},"705":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.4142135623730951},"718":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":2.449489742783178},"723":{"tf":1.4142135623730951},"727":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"743":{"tf":1.7320508075688772},"744":{"tf":1.7320508075688772},"75":{"tf":1.4142135623730951},"761":{"tf":2.0},"772":{"tf":1.0},"773":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"797":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"83":{"tf":1.7320508075688772},"84":{"tf":1.0},"843":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"895":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0},"913":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.4142135623730951},"938":{"tf":1.0},"94":{"tf":1.0},"947":{"tf":1.0},"95":{"tf":1.0},"952":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.0},"969":{"tf":1.0},"970":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":2,"docs":{"206":{"tf":1.0},"776":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"204":{"tf":2.0},"205":{"tf":1.4142135623730951}}}}}}}},"x":{"df":0,"docs":{},"i":{"df":15,"docs":{"79":{"tf":2.23606797749979},"80":{"tf":2.0},"81":{"tf":3.1622776601683795},"82":{"tf":1.0},"83":{"tf":3.3166247903554},"84":{"tf":2.449489742783178},"85":{"tf":2.23606797749979},"86":{"tf":1.0},"87":{"tf":1.0},"874":{"tf":2.6457513110645907},"88":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"92":{"tf":1.7320508075688772}}},"y":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"83":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{":":{":":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"83":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"83":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"|":{"(":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"524":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":16,"docs":{"500":{"tf":1.4142135623730951},"513":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":2.0},"56":{"tf":1.0},"62":{"tf":1.0},"67":{"tf":2.23606797749979},"68":{"tf":1.0},"78":{"tf":1.0},"808":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.4142135623730951},"814":{"tf":1.0},"815":{"tf":2.6457513110645907},"817":{"tf":1.0},"818":{"tf":1.0}}}}}},"s":{"df":1,"docs":{"126":{"tf":2.8284271247461903}},"e":{"df":0,"docs":{},"u":{"d":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"438":{"tf":1.0}}},"df":0,"docs":{}}},"df":8,"docs":{"322":{"tf":1.0},"333":{"tf":1.4142135623730951},"336":{"tf":1.0},"347":{"tf":1.0},"600":{"tf":1.0},"741":{"tf":1.0},"750":{"tf":1.4142135623730951},"849":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"b":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"817":{"tf":1.0}}}}}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"97":{"tf":1.0}}}}}},"df":22,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":2.0},"372":{"tf":1.0},"382":{"tf":1.0},"390":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.23606797749979},"438":{"tf":1.0},"439":{"tf":3.3166247903554},"455":{"tf":1.7320508075688772},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"633":{"tf":1.7320508075688772},"634":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"879":{"tf":3.3166247903554},"880":{"tf":3.605551275463989},"885":{"tf":1.7320508075688772},"933":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"c":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"380":{"tf":1.0}}}}},"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"553":{"tf":1.0}}}}}},"df":18,"docs":{"124":{"tf":1.0},"198":{"tf":1.0},"272":{"tf":1.0},"296":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"350":{"tf":1.0},"452":{"tf":2.0},"453":{"tf":1.4142135623730951},"46":{"tf":1.0},"461":{"tf":1.0},"735":{"tf":2.0},"843":{"tf":1.0},"894":{"tf":1.4142135623730951},"94":{"tf":1.0},"95":{"tf":1.0}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":10,"docs":{"257":{"tf":1.0},"272":{"tf":1.0},"315":{"tf":1.0},"342":{"tf":1.0},"348":{"tf":1.0},"507":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"722":{"tf":1.0},"95":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":6,"docs":{"105":{"tf":1.4142135623730951},"135":{"tf":1.0},"149":{"tf":1.0},"249":{"tf":1.0},"35":{"tf":1.0},"409":{"tf":1.0}}}},"n":{"df":1,"docs":{"928":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":3,"docs":{"439":{"tf":1.0},"632":{"tf":1.0},"723":{"tf":1.4142135623730951}}}}}},"r":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":31,"docs":{"203":{"tf":2.0},"204":{"tf":3.605551275463989},"205":{"tf":3.3166247903554},"206":{"tf":2.8284271247461903},"207":{"tf":2.23606797749979},"210":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":2.23606797749979},"910":{"tf":1.0},"911":{"tf":1.7320508075688772},"912":{"tf":2.6457513110645907},"913":{"tf":2.6457513110645907},"914":{"tf":1.4142135623730951},"915":{"tf":1.0},"916":{"tf":1.4142135623730951},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.7320508075688772},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"941":{"tf":1.4142135623730951},"942":{"tf":1.0},"944":{"tf":1.4142135623730951},"947":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":1,"docs":{"204":{"tf":1.0}}}}}}}},"_":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}}},"d":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"1":{"df":2,"docs":{"81":{"tf":2.0},"83":{"tf":1.4142135623730951}}},"df":16,"docs":{"79":{"tf":2.23606797749979},"80":{"tf":1.7320508075688772},"81":{"tf":3.1622776601683795},"82":{"tf":1.0},"83":{"tf":3.605551275463989},"84":{"tf":3.3166247903554},"85":{"tf":2.449489742783178},"86":{"tf":1.0},"87":{"tf":1.0},"874":{"tf":2.449489742783178},"88":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"92":{"tf":1.7320508075688772},"933":{"tf":1.0}}},"g":{"df":1,"docs":{"711":{"tf":1.0}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":15,"docs":{"248":{"tf":1.0},"375":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"512":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.0},"633":{"tf":1.0},"7":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.4142135623730951},"786":{"tf":1.0},"81":{"tf":1.0},"846":{"tf":1.0},"863":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"h":{"(":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{".":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":1,"docs":{"333":{"tf":1.0}}},"df":7,"docs":{"126":{"tf":1.0},"349":{"tf":1.4142135623730951},"571":{"tf":1.0},"576":{"tf":1.0},"71":{"tf":1.0},"729":{"tf":1.0},"843":{"tf":1.0}}}},"t":{"df":15,"docs":{"163":{"tf":1.0},"199":{"tf":1.0},"249":{"tf":1.0},"284":{"tf":1.0},"375":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"537":{"tf":1.0},"633":{"tf":1.0},"653":{"tf":1.0},"780":{"tf":1.0},"858":{"tf":1.0},"976":{"tf":1.0},"979":{"tf":1.0}}}},"v":{"df":0,"docs":{},"f":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"113":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":16,"docs":{"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"56":{"tf":1.0},"58":{"tf":1.4142135623730951},"62":{"tf":1.0},"63":{"tf":1.4142135623730951},"65":{"tf":1.0},"66":{"tf":1.4142135623730951},"67":{"tf":1.4142135623730951},"68":{"tf":1.0},"69":{"tf":2.449489742783178},"73":{"tf":1.7320508075688772},"77":{"tf":1.0},"78":{"tf":2.449489742783178},"817":{"tf":1.0}}},"m":{"df":2,"docs":{"51":{"tf":1.0},"53":{"tf":1.0}}}}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"1004":{"tf":1.7320508075688772},"58":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"204":{"tf":1.0},"776":{"tf":1.7320508075688772},"911":{"tf":1.0}}}},"z":{"df":1,"docs":{"204":{"tf":1.4142135623730951}}}}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"221":{"tf":1.0}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"846":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"h":{"a":{"df":1,"docs":{"93":{"tf":1.0}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"df":33,"docs":{"17":{"tf":2.23606797749979},"18":{"tf":3.1622776601683795},"19":{"tf":1.7320508075688772},"20":{"tf":1.0},"21":{"tf":2.6457513110645907},"22":{"tf":2.8284271247461903},"23":{"tf":1.4142135623730951},"24":{"tf":1.7320508075688772},"25":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"26":{"tf":2.0},"27":{"tf":1.0},"28":{"tf":2.0},"29":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":2.6457513110645907},"31":{"tf":1.0},"32":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"35":{"tf":1.0},"36":{"tf":1.0},"37":{"tf":1.0},"450":{"tf":1.0},"5":{"tf":1.0},"507":{"tf":1.0},"553":{"tf":1.4142135623730951},"6":{"tf":3.3166247903554},"758":{"tf":1.0},"759":{"tf":2.0},"761":{"tf":2.23606797749979},"762":{"tf":1.0},"763":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"759":{"tf":2.0},"761":{"tf":2.0}}}}},"y":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"6":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"6":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"6":{"tf":1.7320508075688772}},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"6":{"tf":1.4142135623730951}}}}}}}}}}}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":120,"docs":{"1":{"tf":1.0},"1000":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1014":{"tf":1.7320508075688772},"106":{"tf":1.0},"121":{"tf":1.4142135623730951},"122":{"tf":1.0},"134":{"tf":1.4142135623730951},"136":{"tf":1.0},"148":{"tf":1.4142135623730951},"15":{"tf":1.4142135623730951},"150":{"tf":1.0},"162":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"180":{"tf":1.4142135623730951},"182":{"tf":1.0},"193":{"tf":1.4142135623730951},"229":{"tf":1.0},"245":{"tf":1.4142135623730951},"247":{"tf":1.0},"261":{"tf":1.4142135623730951},"264":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"278":{"tf":1.4142135623730951},"279":{"tf":1.0},"292":{"tf":1.4142135623730951},"294":{"tf":1.0},"309":{"tf":1.4142135623730951},"311":{"tf":1.0},"320":{"tf":1.4142135623730951},"322":{"tf":1.0},"36":{"tf":1.4142135623730951},"360":{"tf":1.4142135623730951},"366":{"tf":1.0},"384":{"tf":1.7320508075688772},"386":{"tf":1.0},"398":{"tf":1.7320508075688772},"410":{"tf":1.0},"425":{"tf":1.7320508075688772},"430":{"tf":1.0},"448":{"tf":1.4142135623730951},"451":{"tf":1.0},"463":{"tf":1.4142135623730951},"465":{"tf":1.0},"480":{"tf":1.4142135623730951},"481":{"tf":1.0},"493":{"tf":1.4142135623730951},"495":{"tf":1.0},"511":{"tf":1.4142135623730951},"513":{"tf":1.0},"533":{"tf":1.4142135623730951},"534":{"tf":1.0},"535":{"tf":1.0},"547":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"561":{"tf":1.4142135623730951},"584":{"tf":1.0},"596":{"tf":1.4142135623730951},"598":{"tf":1.0},"611":{"tf":1.4142135623730951},"613":{"tf":1.0},"625":{"tf":1.4142135623730951},"627":{"tf":1.0},"647":{"tf":1.4142135623730951},"649":{"tf":1.0},"662":{"tf":1.4142135623730951},"664":{"tf":1.0},"676":{"tf":1.4142135623730951},"678":{"tf":1.0},"690":{"tf":1.4142135623730951},"692":{"tf":1.0},"707":{"tf":1.4142135623730951},"709":{"tf":1.0},"727":{"tf":1.7320508075688772},"730":{"tf":1.0},"732":{"tf":1.0},"739":{"tf":1.4142135623730951},"75":{"tf":1.7320508075688772},"757":{"tf":1.0},"769":{"tf":1.4142135623730951},"771":{"tf":1.0},"78":{"tf":1.4142135623730951},"781":{"tf":1.4142135623730951},"782":{"tf":1.0},"79":{"tf":1.0},"794":{"tf":1.4142135623730951},"795":{"tf":1.0},"806":{"tf":1.4142135623730951},"808":{"tf":1.0},"825":{"tf":1.4142135623730951},"827":{"tf":1.0},"833":{"tf":1.0},"839":{"tf":1.4142135623730951},"841":{"tf":1.0},"849":{"tf":1.0},"852":{"tf":1.0},"856":{"tf":1.4142135623730951},"857":{"tf":1.0},"870":{"tf":1.4142135623730951},"871":{"tf":1.0},"889":{"tf":1.4142135623730951},"891":{"tf":1.0},"906":{"tf":1.7320508075688772},"908":{"tf":1.0},"91":{"tf":1.4142135623730951},"924":{"tf":1.4142135623730951},"926":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.4142135623730951},"940":{"tf":1.0},"955":{"tf":1.4142135623730951},"957":{"tf":1.0},"972":{"tf":1.4142135623730951},"974":{"tf":1.0},"986":{"tf":1.4142135623730951},"988":{"tf":1.0}}}}}}},"u":{"df":2,"docs":{"207":{"tf":1.0},"564":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}}}}},"df":29,"docs":{"148":{"tf":1.0},"207":{"tf":1.4142135623730951},"563":{"tf":2.0},"564":{"tf":1.7320508075688772},"565":{"tf":1.0},"566":{"tf":1.0},"567":{"tf":1.4142135623730951},"568":{"tf":2.0},"569":{"tf":1.0},"570":{"tf":1.7320508075688772},"571":{"tf":2.23606797749979},"572":{"tf":1.0},"573":{"tf":2.8284271247461903},"574":{"tf":1.7320508075688772},"575":{"tf":1.4142135623730951},"576":{"tf":2.6457513110645907},"577":{"tf":1.4142135623730951},"578":{"tf":1.0},"579":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"583":{"tf":1.0},"633":{"tf":2.449489742783178},"637":{"tf":1.7320508075688772},"640":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.0},"863":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":8,"docs":{"170":{"tf":1.0},"293":{"tf":1.0},"438":{"tf":1.0},"752":{"tf":1.4142135623730951},"809":{"tf":1.0},"814":{"tf":1.0},"817":{"tf":1.0},"885":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"138":{"tf":1.0},"574":{"tf":1.0},"815":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"576":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"516":{"tf":1.0},"564":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"723":{"tf":1.4142135623730951},"724":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"942":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"199":{"tf":1.0},"459":{"tf":1.0},"522":{"tf":1.0}}}},"o":{"df":2,"docs":{"294":{"tf":1.0},"300":{"tf":1.4142135623730951}}}}},"r":{"a":{"c":{"df":0,"docs":{},"e":{"df":2,"docs":{"240":{"tf":1.0},"500":{"tf":1.0}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"u":{"df":1,"docs":{"697":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":5,"docs":{"199":{"tf":1.0},"629":{"tf":1.0},"644":{"tf":1.0},"826":{"tf":1.0},"912":{"tf":1.0}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"843":{"tf":1.0}}}},"p":{"df":1,"docs":{"267":{"tf":1.0}}}},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":14,"docs":{"126":{"tf":1.0},"252":{"tf":2.23606797749979},"257":{"tf":1.0},"322":{"tf":1.4142135623730951},"336":{"tf":1.0},"344":{"tf":2.8284271247461903},"345":{"tf":2.449489742783178},"346":{"tf":1.7320508075688772},"349":{"tf":1.4142135623730951},"352":{"tf":2.0},"436":{"tf":1.4142135623730951},"501":{"tf":2.6457513110645907},"507":{"tf":1.0},"69":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"255":{"tf":1.0},"436":{"tf":1.0},"497":{"tf":1.4142135623730951},"505":{"tf":1.0}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"[":{"0":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":2,"docs":{"349":{"tf":2.0},"352":{"tf":1.0}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":4,"docs":{"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"g":{"df":11,"docs":{"108":{"tf":1.0},"222":{"tf":1.4142135623730951},"346":{"tf":1.0},"47":{"tf":1.0},"519":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":3.7416573867739413},"747":{"tf":1.4142135623730951},"959":{"tf":1.0},"973":{"tf":1.0}}},"k":{"df":4,"docs":{"113":{"tf":1.0},"465":{"tf":1.0},"470":{"tf":1.0},"77":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":7,"docs":{"440":{"tf":1.0},"441":{"tf":1.0},"459":{"tf":1.0},"497":{"tf":1.0},"573":{"tf":1.4142135623730951},"721":{"tf":1.0},"779":{"tf":1.0}},"r":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"554":{"tf":1.0}}}}}}},"t":{"a":{"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":16,"docs":{"199":{"tf":1.0},"415":{"tf":1.4142135623730951},"416":{"tf":2.449489742783178},"417":{"tf":2.0},"418":{"tf":1.0},"420":{"tf":1.0},"428":{"tf":1.0},"60":{"tf":1.0},"744":{"tf":1.4142135623730951},"777":{"tf":1.0},"928":{"tf":2.0},"929":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.0},"934":{"tf":1.4142135623730951}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"53":{"tf":1.0}},"i":{"df":1,"docs":{"269":{"tf":1.0}}}},"o":{"df":9,"docs":{"203":{"tf":1.0},"218":{"tf":1.0},"221":{"tf":1.4142135623730951},"342":{"tf":1.0},"472":{"tf":1.0},"571":{"tf":1.0},"933":{"tf":1.0},"934":{"tf":1.0},"992":{"tf":1.0}},"n":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"1006":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{}}}}},"w":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"23":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":6,"docs":{"249":{"tf":1.4142135623730951},"5":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"634":{"tf":1.0},"907":{"tf":1.0}}}},"df":5,"docs":{"346":{"tf":1.4142135623730951},"44":{"tf":1.0},"45":{"tf":1.0},"735":{"tf":1.0},"94":{"tf":1.0}},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":6,"docs":{"63":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":1.4142135623730951},"744":{"tf":1.0},"776":{"tf":1.0},"832":{"tf":1.0}}},"t":{"df":2,"docs":{"188":{"tf":1.0},"752":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"939":{"tf":1.0}}}},"v":{"df":1,"docs":{"720":{"tf":1.0}}}}}},"d":{"df":23,"docs":{"133":{"tf":1.0},"152":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"16":{"tf":1.0},"19":{"tf":1.0},"26":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"47":{"tf":1.0},"499":{"tf":1.4142135623730951},"5":{"tf":1.4142135623730951},"503":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":1.0},"6":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.7320508075688772},"757":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.7320508075688772},"931":{"tf":1.0},"936":{"tf":1.0},"951":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"567":{"tf":1.0}}}},"i":{"df":1,"docs":{"272":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":9,"docs":{"137":{"tf":1.0},"138":{"tf":1.0},"199":{"tf":1.4142135623730951},"50":{"tf":1.0},"615":{"tf":1.0},"729":{"tf":1.0},"754":{"tf":1.0},"912":{"tf":1.0},"935":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.0}},"t":{"df":7,"docs":{"215":{"tf":1.0},"223":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"376":{"tf":1.0},"505":{"tf":1.0},"762":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"573":{"tf":1.0}}}},"z":{"df":4,"docs":{"250":{"tf":1.0},"567":{"tf":1.0},"749":{"tf":1.0},"843":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"615":{"tf":1.0},"723":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0},"879":{"tf":1.4142135623730951}}}}},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"701":{"tf":1.0}},"e":{"d":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"i":{"d":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":36,"docs":{"108":{"tf":1.4142135623730951},"124":{"tf":1.0},"148":{"tf":1.0},"170":{"tf":1.0},"232":{"tf":1.4142135623730951},"234":{"tf":1.0},"235":{"tf":1.0},"24":{"tf":1.0},"255":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"273":{"tf":1.0},"284":{"tf":1.0},"438":{"tf":1.0},"467":{"tf":1.0},"469":{"tf":1.0},"505":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"576":{"tf":1.0},"64":{"tf":1.0},"701":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"721":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"832":{"tf":1.0},"836":{"tf":1.0},"846":{"tf":1.0},"928":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.0}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"571":{"tf":1.0}}}}}}},"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"563":{"tf":1.0},"570":{"tf":2.449489742783178}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"528":{"tf":1.0}}},"df":0,"docs":{}}}}},"c":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"526":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":22,"docs":{"627":{"tf":2.0},"628":{"tf":1.0},"629":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":2.0},"633":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.7320508075688772},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.4142135623730951},"641":{"tf":1.7320508075688772},"642":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":2.0},"645":{"tf":1.0},"646":{"tf":1.4142135623730951},"647":{"tf":1.0},"648":{"tf":1.7320508075688772}}}},"v":{"df":29,"docs":{"1004":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"257":{"tf":1.4142135623730951},"439":{"tf":2.0},"466":{"tf":1.0},"467":{"tf":1.0},"483":{"tf":1.0},"491":{"tf":1.0},"507":{"tf":1.4142135623730951},"553":{"tf":1.0},"554":{"tf":1.4142135623730951},"555":{"tf":1.0},"564":{"tf":1.0},"605":{"tf":1.0},"62":{"tf":1.7320508075688772},"633":{"tf":1.0},"65":{"tf":1.4142135623730951},"659":{"tf":1.0},"69":{"tf":1.0},"722":{"tf":1.4142135623730951},"762":{"tf":1.0},"773":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.7320508075688772},"912":{"tf":1.0},"932":{"tf":1.4142135623730951},"994":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"n":{"df":0,"docs":{},"t":{"df":13,"docs":{"124":{"tf":1.0},"184":{"tf":1.0},"207":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.4142135623730951},"586":{"tf":1.0},"829":{"tf":1.0},"843":{"tf":1.0},"844":{"tf":1.0},"859":{"tf":1.0},"869":{"tf":1.0},"996":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"722":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":6,"docs":{"401":{"tf":1.0},"404":{"tf":1.0},"409":{"tf":1.0},"627":{"tf":1.0},"632":{"tf":1.7320508075688772},"634":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"1007":{"tf":1.0},"381":{"tf":1.0},"470":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"375":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":13,"docs":{"272":{"tf":1.0},"290":{"tf":1.0},"346":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.0},"564":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"602":{"tf":1.0},"712":{"tf":1.0},"846":{"tf":1.7320508075688772},"850":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"567":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"435":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"437":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0}},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"723":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"r":{"d":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"551":{"tf":1.0}}}}},"df":34,"docs":{"126":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":2.23606797749979},"208":{"tf":1.7320508075688772},"257":{"tf":1.0},"348":{"tf":1.0},"350":{"tf":1.0},"401":{"tf":1.0},"404":{"tf":1.4142135623730951},"406":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"507":{"tf":1.0},"549":{"tf":2.23606797749979},"550":{"tf":2.0},"551":{"tf":2.6457513110645907},"552":{"tf":1.0},"553":{"tf":3.3166247903554},"554":{"tf":1.7320508075688772},"555":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":2.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"568":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"721":{"tf":1.0},"848":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"931":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"1004":{"tf":1.0}}}}},"v":{"df":4,"docs":{"120":{"tf":1.0},"431":{"tf":1.0},"436":{"tf":1.4142135623730951},"437":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":12,"docs":{"310":{"tf":1.0},"356":{"tf":1.0},"430":{"tf":1.4142135623730951},"432":{"tf":1.4142135623730951},"436":{"tf":1.4142135623730951},"437":{"tf":1.7320508075688772},"439":{"tf":1.7320508075688772},"440":{"tf":1.7320508075688772},"441":{"tf":1.4142135623730951},"444":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":2.0}}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"80":{"tf":1.0},"84":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":4,"docs":{"323":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":1.4142135623730951}},"s":{"df":1,"docs":{"523":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"221":{"tf":1.0}}}},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"75":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"424":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"285":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"709":{"tf":1.0},"714":{"tf":1.0},"718":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}}}},"u":{"c":{"df":47,"docs":{"1003":{"tf":1.4142135623730951},"138":{"tf":1.0},"139":{"tf":1.0},"140":{"tf":1.0},"144":{"tf":1.0},"148":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"238":{"tf":1.0},"267":{"tf":1.0},"342":{"tf":1.0},"347":{"tf":1.0},"356":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"40":{"tf":1.0},"410":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951},"540":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.4142135623730951},"571":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.7320508075688772},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"629":{"tf":1.0},"687":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"723":{"tf":1.4142135623730951},"744":{"tf":1.0},"758":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.4142135623730951},"799":{"tf":1.0},"818":{"tf":1.0},"833":{"tf":1.0},"852":{"tf":1.0},"863":{"tf":1.4142135623730951},"919":{"tf":1.0},"94":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.0}},"t":{"df":5,"docs":{"406":{"tf":1.0},"417":{"tf":1.0},"655":{"tf":1.0},"818":{"tf":1.0},"996":{"tf":1.0}}}},"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"f":{"a":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"342":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":7,"docs":{"169":{"tf":1.0},"257":{"tf":1.0},"346":{"tf":1.0},"507":{"tf":1.0},"553":{"tf":1.0},"554":{"tf":1.0},"811":{"tf":1.0}}},"df":0,"docs":{}}}},"df":17,"docs":{"208":{"tf":1.0},"436":{"tf":1.4142135623730951},"437":{"tf":1.0},"640":{"tf":1.0},"717":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"761":{"tf":1.0},"807":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"811":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":2.23606797749979},"832":{"tf":1.0},"990":{"tf":1.0}},"e":{"d":{"df":1,"docs":{"444":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":140,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1013":{"tf":1.7320508075688772},"105":{"tf":1.4142135623730951},"106":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":1.0},"122":{"tf":1.0},"133":{"tf":1.4142135623730951},"136":{"tf":1.0},"14":{"tf":1.4142135623730951},"147":{"tf":1.4142135623730951},"150":{"tf":1.0},"161":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"179":{"tf":1.4142135623730951},"182":{"tf":1.0},"192":{"tf":1.4142135623730951},"195":{"tf":1.0},"214":{"tf":1.4142135623730951},"215":{"tf":1.0},"228":{"tf":1.4142135623730951},"229":{"tf":1.0},"231":{"tf":1.0},"242":{"tf":1.4142135623730951},"247":{"tf":1.0},"260":{"tf":1.4142135623730951},"268":{"tf":1.0},"277":{"tf":1.4142135623730951},"279":{"tf":1.0},"291":{"tf":1.4142135623730951},"294":{"tf":1.0},"308":{"tf":1.4142135623730951},"311":{"tf":1.0},"319":{"tf":1.4142135623730951},"322":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.4142135623730951},"359":{"tf":2.23606797749979},"364":{"tf":1.0},"366":{"tf":1.0},"383":{"tf":1.4142135623730951},"386":{"tf":1.0},"397":{"tf":1.4142135623730951},"400":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.4142135623730951},"430":{"tf":1.0},"447":{"tf":1.4142135623730951},"450":{"tf":1.0},"451":{"tf":1.0},"46":{"tf":1.4142135623730951},"462":{"tf":1.4142135623730951},"465":{"tf":1.0},"479":{"tf":1.4142135623730951},"481":{"tf":1.0},"492":{"tf":1.4142135623730951},"495":{"tf":1.0},"510":{"tf":1.4142135623730951},"513":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"524":{"tf":2.0},"525":{"tf":1.4142135623730951},"532":{"tf":1.7320508075688772},"535":{"tf":1.0},"546":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"560":{"tf":1.4142135623730951},"563":{"tf":1.0},"583":{"tf":1.4142135623730951},"584":{"tf":1.0},"595":{"tf":1.4142135623730951},"598":{"tf":1.0},"610":{"tf":1.4142135623730951},"613":{"tf":1.0},"624":{"tf":1.4142135623730951},"627":{"tf":1.0},"629":{"tf":1.0},"646":{"tf":1.4142135623730951},"649":{"tf":1.0},"661":{"tf":1.4142135623730951},"664":{"tf":1.0},"675":{"tf":1.4142135623730951},"678":{"tf":1.0},"689":{"tf":1.4142135623730951},"692":{"tf":1.0},"706":{"tf":1.4142135623730951},"709":{"tf":1.0},"726":{"tf":1.4142135623730951},"74":{"tf":1.4142135623730951},"741":{"tf":1.4142135623730951},"748":{"tf":1.0},"754":{"tf":1.4142135623730951},"756":{"tf":1.4142135623730951},"757":{"tf":1.0},"768":{"tf":1.4142135623730951},"771":{"tf":1.0},"776":{"tf":1.0},"78":{"tf":1.0},"780":{"tf":1.4142135623730951},"782":{"tf":1.0},"79":{"tf":1.0},"793":{"tf":1.4142135623730951},"795":{"tf":1.0},"805":{"tf":1.4142135623730951},"808":{"tf":1.0},"824":{"tf":1.4142135623730951},"827":{"tf":1.0},"838":{"tf":1.4142135623730951},"841":{"tf":1.0},"855":{"tf":1.7320508075688772},"857":{"tf":1.0},"869":{"tf":1.4142135623730951},"871":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"888":{"tf":1.4142135623730951},"891":{"tf":1.0},"90":{"tf":1.4142135623730951},"904":{"tf":1.0},"905":{"tf":1.7320508075688772},"908":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"937":{"tf":1.4142135623730951},"940":{"tf":1.0},"954":{"tf":1.4142135623730951},"957":{"tf":1.0},"971":{"tf":1.4142135623730951},"974":{"tf":1.0},"985":{"tf":1.4142135623730951},"988":{"tf":1.0},"999":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"523":{"tf":1.0}}},"d":{"a":{"'":{"df":1,"docs":{"149":{"tf":1.0}}},"df":41,"docs":{"122":{"tf":2.0},"123":{"tf":1.4142135623730951},"124":{"tf":2.0},"125":{"tf":1.7320508075688772},"126":{"tf":1.7320508075688772},"127":{"tf":1.0},"128":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.4142135623730951},"133":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":2.23606797749979},"137":{"tf":1.4142135623730951},"138":{"tf":1.4142135623730951},"139":{"tf":1.0},"140":{"tf":1.7320508075688772},"141":{"tf":1.0},"142":{"tf":1.0},"143":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.4142135623730951},"147":{"tf":1.0},"148":{"tf":1.7320508075688772},"149":{"tf":1.4142135623730951},"187":{"tf":1.4142135623730951},"272":{"tf":1.0},"370":{"tf":1.0},"797":{"tf":1.0},"841":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.7320508075688772},"848":{"tf":2.0},"849":{"tf":1.0},"852":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":1.4142135623730951},"863":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"'":{"df":1,"docs":{"185":{"tf":1.0}}},"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"126":{"tf":1.0}}}}}},"df":28,"docs":{"132":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"187":{"tf":1.0},"188":{"tf":1.4142135623730951},"272":{"tf":1.7320508075688772},"274":{"tf":1.0},"315":{"tf":1.0},"440":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.7320508075688772},"847":{"tf":1.4142135623730951},"852":{"tf":1.0},"857":{"tf":2.6457513110645907},"858":{"tf":1.0},"859":{"tf":1.0},"860":{"tf":2.23606797749979},"861":{"tf":1.7320508075688772},"862":{"tf":1.7320508075688772},"863":{"tf":1.4142135623730951},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.7320508075688772},"870":{"tf":1.0},"911":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"38":{"tf":1.4142135623730951},"45":{"tf":2.23606797749979},"47":{"tf":1.4142135623730951},"51":{"tf":1.0},"771":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"45":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"124":{"tf":1.0},"125":{"tf":1.0},"138":{"tf":1.0},"191":{"tf":1.7320508075688772},"199":{"tf":1.0},"206":{"tf":1.0},"455":{"tf":1.0},"777":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"777":{"tf":1.0}}}},"m":{"df":2,"docs":{"214":{"tf":1.0},"7":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"203":{"tf":1.4142135623730951},"777":{"tf":1.0}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"653":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"g":{"a":{"df":0,"docs":{},"r":{"d":{"df":14,"docs":{"184":{"tf":1.0},"194":{"tf":1.0},"231":{"tf":1.0},"425":{"tf":1.0},"539":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"555":{"tf":1.0},"57":{"tf":1.0},"575":{"tf":1.0},"6":{"tf":1.0},"8":{"tf":1.0},"843":{"tf":1.0},"938":{"tf":1.0}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":5,"docs":{"221":{"tf":1.0},"440":{"tf":1.0},"614":{"tf":1.0},"698":{"tf":1.7320508075688772},"783":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"205":{"tf":3.0}}},"df":27,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":5.196152422706632},"205":{"tf":6.082762530298219},"207":{"tf":1.0},"208":{"tf":4.0},"743":{"tf":1.7320508075688772},"744":{"tf":1.7320508075688772},"747":{"tf":1.0},"748":{"tf":1.0},"940":{"tf":2.23606797749979},"941":{"tf":1.4142135623730951},"942":{"tf":2.0},"943":{"tf":1.4142135623730951},"944":{"tf":3.1622776601683795},"945":{"tf":1.4142135623730951},"946":{"tf":1.0},"947":{"tf":1.4142135623730951},"948":{"tf":1.4142135623730951},"949":{"tf":1.4142135623730951},"950":{"tf":1.0},"951":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"954":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.0}},"i":{"d":{"df":2,"docs":{"205":{"tf":2.449489742783178},"208":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"944":{"tf":1.0}}},"df":0,"docs":{}}}},"x":{"df":1,"docs":{"911":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"t":{"df":45,"docs":{"108":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"252":{"tf":1.7320508075688772},"254":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.0},"3":{"tf":1.0},"372":{"tf":1.0},"452":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"495":{"tf":1.0},"501":{"tf":2.6457513110645907},"502":{"tf":1.0},"503":{"tf":1.0},"505":{"tf":1.0},"507":{"tf":1.0},"58":{"tf":1.4142135623730951},"602":{"tf":2.0},"603":{"tf":1.4142135623730951},"62":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":2.6457513110645907},"654":{"tf":1.4142135623730951},"658":{"tf":1.0},"660":{"tf":1.0},"73":{"tf":1.0},"808":{"tf":1.0},"809":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.4142135623730951},"813":{"tf":1.0},"814":{"tf":3.1622776601683795},"815":{"tf":1.0},"817":{"tf":1.4142135623730951},"826":{"tf":1.0},"974":{"tf":1.0},"975":{"tf":1.0},"976":{"tf":1.0},"978":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"r":{"df":8,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"121":{"tf":1.0},"814":{"tf":1.4142135623730951},"816":{"tf":1.0},"817":{"tf":1.0},"895":{"tf":1.0}}}},"df":30,"docs":{"121":{"tf":1.0},"247":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.4142135623730951},"451":{"tf":1.0},"452":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.4142135623730951},"58":{"tf":1.0},"808":{"tf":2.449489742783178},"809":{"tf":1.4142135623730951},"810":{"tf":1.7320508075688772},"811":{"tf":1.0},"812":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.7320508075688772},"815":{"tf":1.4142135623730951},"816":{"tf":1.0},"817":{"tf":2.449489742783178},"818":{"tf":1.4142135623730951},"819":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.4142135623730951},"823":{"tf":1.0},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.4142135623730951},"859":{"tf":1.0},"912":{"tf":1.0}},"i":{"df":1,"docs":{"111":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":18,"docs":{"200":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":2.6457513110645907},"205":{"tf":2.23606797749979},"211":{"tf":1.4142135623730951},"435":{"tf":1.0},"437":{"tf":1.4142135623730951},"439":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.0},"61":{"tf":1.0},"645":{"tf":1.0},"741":{"tf":1.0},"742":{"tf":1.0},"81":{"tf":1.4142135623730951},"814":{"tf":1.7320508075688772},"817":{"tf":1.0},"983":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"203":{"tf":1.0},"515":{"tf":1.0}}}}}},"df":2,"docs":{"428":{"tf":1.0},"842":{"tf":1.0}}}}},"h":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"375":{"tf":1.0},"376":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"231":{"tf":1.0},"232":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"19":{"tf":1.0}}}}}}}}}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":11,"docs":{"112":{"tf":1.0},"126":{"tf":2.0},"272":{"tf":1.0},"284":{"tf":1.0},"514":{"tf":1.0},"6":{"tf":1.4142135623730951},"629":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.0},"879":{"tf":3.605551275463989},"880":{"tf":1.7320508075688772}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}}}}},"df":0,"docs":{}}},"l":{"a":{"df":0,"docs":{},"t":{"df":137,"docs":{"1":{"tf":1.0},"1001":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1007":{"tf":1.0},"1015":{"tf":1.7320508075688772},"112":{"tf":1.0},"115":{"tf":1.0},"122":{"tf":1.0},"128":{"tf":1.0},"135":{"tf":1.4142135623730951},"136":{"tf":1.0},"140":{"tf":1.0},"144":{"tf":1.0},"149":{"tf":1.4142135623730951},"150":{"tf":1.0},"16":{"tf":1.4142135623730951},"163":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"181":{"tf":1.4142135623730951},"182":{"tf":1.0},"184":{"tf":1.0},"188":{"tf":1.0},"194":{"tf":1.4142135623730951},"195":{"tf":1.0},"212":{"tf":1.4142135623730951},"215":{"tf":1.0},"226":{"tf":1.4142135623730951},"229":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.0},"246":{"tf":1.4142135623730951},"247":{"tf":1.0},"252":{"tf":1.0},"262":{"tf":1.4142135623730951},"276":{"tf":1.0},"279":{"tf":1.0},"291":{"tf":1.0},"293":{"tf":1.4142135623730951},"294":{"tf":1.0},"3":{"tf":1.7320508075688772},"304":{"tf":1.0},"310":{"tf":1.4142135623730951},"311":{"tf":1.0},"321":{"tf":1.4142135623730951},"322":{"tf":1.0},"323":{"tf":1.0},"341":{"tf":1.4142135623730951},"343":{"tf":1.0},"35":{"tf":1.0},"361":{"tf":1.4142135623730951},"366":{"tf":1.0},"37":{"tf":1.7320508075688772},"371":{"tf":1.0},"373":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.4142135623730951},"386":{"tf":1.0},"399":{"tf":1.4142135623730951},"414":{"tf":1.0},"430":{"tf":1.0},"441":{"tf":1.0},"449":{"tf":1.4142135623730951},"451":{"tf":1.0},"464":{"tf":1.4142135623730951},"481":{"tf":1.0},"483":{"tf":1.0},"494":{"tf":1.4142135623730951},"495":{"tf":1.0},"512":{"tf":1.7320508075688772},"513":{"tf":1.0},"53":{"tf":1.0},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"54":{"tf":1.4142135623730951},"548":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"562":{"tf":1.4142135623730951},"584":{"tf":1.0},"597":{"tf":1.4142135623730951},"598":{"tf":1.0},"6":{"tf":1.0},"605":{"tf":1.0},"612":{"tf":1.4142135623730951},"613":{"tf":1.0},"626":{"tf":1.4142135623730951},"627":{"tf":1.0},"648":{"tf":1.4142135623730951},"649":{"tf":1.0},"663":{"tf":2.0},"664":{"tf":1.0},"677":{"tf":1.4142135623730951},"678":{"tf":1.0},"691":{"tf":1.4142135623730951},"692":{"tf":1.0},"708":{"tf":1.4142135623730951},"709":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.0},"728":{"tf":1.4142135623730951},"757":{"tf":1.0},"76":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"807":{"tf":1.4142135623730951},"808":{"tf":1.0},"815":{"tf":1.0},"826":{"tf":1.4142135623730951},"827":{"tf":1.0},"840":{"tf":1.7320508075688772},"859":{"tf":1.4142135623730951},"867":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.0},"879":{"tf":1.0},"890":{"tf":1.4142135623730951},"891":{"tf":1.0},"9":{"tf":1.0},"907":{"tf":1.7320508075688772},"908":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0},"92":{"tf":1.4142135623730951},"925":{"tf":1.4142135623730951},"926":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.4142135623730951},"940":{"tf":1.0},"954":{"tf":1.0},"956":{"tf":1.4142135623730951},"957":{"tf":1.0},"973":{"tf":1.4142135623730951},"974":{"tf":1.0},"987":{"tf":1.7320508075688772},"988":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":7,"docs":{"267":{"tf":1.0},"571":{"tf":1.0},"698":{"tf":1.4142135623730951},"711":{"tf":1.0},"80":{"tf":1.0},"81":{"tf":1.7320508075688772},"83":{"tf":1.0}}}}}}}},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"x":{"df":1,"docs":{"832":{"tf":1.0}}},"y":{"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"634":{"tf":1.0}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"205":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":4,"docs":{"296":{"tf":1.4142135623730951},"300":{"tf":1.7320508075688772},"301":{"tf":1.4142135623730951},"62":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":94,"docs":{"113":{"tf":1.0},"121":{"tf":1.0},"153":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"203":{"tf":3.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.4142135623730951},"207":{"tf":2.0},"208":{"tf":2.449489742783178},"212":{"tf":1.4142135623730951},"216":{"tf":1.4142135623730951},"217":{"tf":1.4142135623730951},"218":{"tf":1.0},"219":{"tf":1.0},"220":{"tf":1.4142135623730951},"221":{"tf":2.8284271247461903},"222":{"tf":1.4142135623730951},"223":{"tf":1.4142135623730951},"226":{"tf":1.0},"230":{"tf":1.0},"247":{"tf":2.23606797749979},"248":{"tf":1.0},"249":{"tf":2.0},"250":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.4142135623730951},"255":{"tf":1.0},"256":{"tf":1.0},"257":{"tf":1.0},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0},"329":{"tf":1.0},"346":{"tf":1.7320508075688772},"365":{"tf":1.0},"366":{"tf":2.23606797749979},"367":{"tf":1.4142135623730951},"368":{"tf":2.23606797749979},"369":{"tf":1.4142135623730951},"370":{"tf":1.4142135623730951},"371":{"tf":1.4142135623730951},"372":{"tf":1.7320508075688772},"373":{"tf":1.4142135623730951},"374":{"tf":1.4142135623730951},"375":{"tf":2.6457513110645907},"376":{"tf":1.7320508075688772},"377":{"tf":1.4142135623730951},"378":{"tf":1.0},"379":{"tf":1.0},"380":{"tf":1.4142135623730951},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.7320508075688772},"384":{"tf":1.4142135623730951},"385":{"tf":1.7320508075688772},"432":{"tf":1.4142135623730951},"433":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.4142135623730951},"499":{"tf":1.0},"500":{"tf":1.7320508075688772},"515":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.7320508075688772},"58":{"tf":1.0},"59":{"tf":1.4142135623730951},"60":{"tf":1.7320508075688772},"61":{"tf":1.0},"627":{"tf":1.0},"629":{"tf":1.0},"632":{"tf":1.4142135623730951},"633":{"tf":2.23606797749979},"634":{"tf":1.7320508075688772},"637":{"tf":1.4142135623730951},"640":{"tf":1.7320508075688772},"643":{"tf":1.4142135623730951},"66":{"tf":1.0},"71":{"tf":2.0},"712":{"tf":1.0},"714":{"tf":1.4142135623730951},"715":{"tf":1.0},"721":{"tf":1.0},"77":{"tf":1.7320508075688772},"78":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"938":{"tf":1.0}}}},"df":16,"docs":{"205":{"tf":1.0},"257":{"tf":1.0},"269":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.7320508075688772},"418":{"tf":1.0},"438":{"tf":1.0},"469":{"tf":1.4142135623730951},"472":{"tf":1.0},"497":{"tf":1.0},"507":{"tf":1.0},"554":{"tf":1.0},"564":{"tf":1.0},"711":{"tf":1.4142135623730951},"777":{"tf":1.0},"786":{"tf":3.0}},"e":{"a":{"df":0,"docs":{},"s":{"df":11,"docs":{"209":{"tf":1.0},"315":{"tf":1.0},"371":{"tf":1.0},"440":{"tf":1.0},"701":{"tf":1.0},"841":{"tf":1.0},"848":{"tf":2.0},"879":{"tf":2.449489742783178},"880":{"tf":1.0},"895":{"tf":2.0},"917":{"tf":1.0}}}},"df":1,"docs":{"773":{"tf":1.0}},"v":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"697":{"tf":1.0}}}}}}},"df":13,"docs":{"1013":{"tf":1.0},"208":{"tf":1.0},"218":{"tf":1.0},"322":{"tf":1.0},"325":{"tf":1.4142135623730951},"334":{"tf":1.0},"340":{"tf":1.0},"345":{"tf":1.0},"522":{"tf":1.0},"58":{"tf":1.0},"723":{"tf":1.0},"929":{"tf":1.0},"941":{"tf":1.0}}}},"i":{"a":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"230":{"tf":1.0},"512":{"tf":1.4142135623730951},"720":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{},"n":{"c":{"df":4,"docs":{"230":{"tf":1.0},"236":{"tf":1.0},"296":{"tf":1.0},"429":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"934":{"tf":1.0}}}}},"df":21,"docs":{"15":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"262":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"303":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"473":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.0},"514":{"tf":1.4142135623730951},"55":{"tf":1.0},"553":{"tf":1.0},"629":{"tf":1.0},"852":{"tf":1.0},"874":{"tf":1.0},"934":{"tf":1.0},"95":{"tf":1.0}}},"u":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"797":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"204":{"tf":1.0}}},"df":30,"docs":{"193":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"267":{"tf":1.0},"323":{"tf":1.0},"348":{"tf":1.4142135623730951},"361":{"tf":1.0},"384":{"tf":1.0},"51":{"tf":1.0},"564":{"tf":1.0},"576":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"638":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.0},"735":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"792":{"tf":1.0},"817":{"tf":1.0},"84":{"tf":1.0},"889":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.4142135623730951},"992":{"tf":1.0},"994":{"tf":1.0}}}},"r":{"df":0,"docs":{},"k":{"(":{"df":1,"docs":{"848":{"tf":1.0}}},"df":5,"docs":{"272":{"tf":1.0},"273":{"tf":1.4142135623730951},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"850":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":15,"docs":{"375":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":3.0},"603":{"tf":1.4142135623730951},"605":{"tf":1.0},"614":{"tf":1.0},"694":{"tf":1.4142135623730951},"701":{"tf":1.7320508075688772},"704":{"tf":1.0},"758":{"tf":1.0},"761":{"tf":1.4142135623730951},"79":{"tf":1.0},"84":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":4,"docs":{"602":{"tf":2.6457513110645907},"603":{"tf":2.0},"605":{"tf":1.0},"698":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"a":{"d":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"v":{"2":{"df":1,"docs":{"761":{"tf":1.0}}},"df":0,"docs":{}}},"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"m":{"df":4,"docs":{"600":{"tf":1.0},"602":{"tf":2.23606797749979},"603":{"tf":1.4142135623730951},"698":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"d":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.7320508075688772}},"v":{"2":{"df":1,"docs":{"761":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"761":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"v":{"df":115,"docs":{"169":{"tf":1.0},"172":{"tf":1.0},"178":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":2.0},"208":{"tf":1.4142135623730951},"231":{"tf":1.0},"234":{"tf":1.0},"249":{"tf":1.4142135623730951},"255":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.4142135623730951},"273":{"tf":2.449489742783178},"285":{"tf":1.0},"295":{"tf":1.0},"310":{"tf":1.0},"347":{"tf":1.0},"375":{"tf":1.4142135623730951},"380":{"tf":1.0},"386":{"tf":1.0},"440":{"tf":1.4142135623730951},"505":{"tf":1.0},"519":{"tf":1.0},"524":{"tf":1.4142135623730951},"573":{"tf":1.0},"613":{"tf":2.23606797749979},"614":{"tf":1.4142135623730951},"615":{"tf":1.0},"616":{"tf":1.0},"617":{"tf":1.4142135623730951},"618":{"tf":1.0},"619":{"tf":1.0},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"632":{"tf":1.0},"643":{"tf":1.0},"663":{"tf":1.0},"668":{"tf":1.0},"678":{"tf":2.23606797749979},"679":{"tf":1.4142135623730951},"680":{"tf":1.0},"681":{"tf":1.0},"682":{"tf":1.4142135623730951},"683":{"tf":1.0},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0},"689":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0},"714":{"tf":1.0},"730":{"tf":2.0},"731":{"tf":1.0},"732":{"tf":1.0},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":1.7320508075688772},"736":{"tf":1.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"740":{"tf":2.0},"767":{"tf":1.0},"773":{"tf":1.0},"799":{"tf":1.4142135623730951},"811":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.7320508075688772},"818":{"tf":1.4142135623730951},"827":{"tf":2.23606797749979},"828":{"tf":1.0},"829":{"tf":1.4142135623730951},"830":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"833":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.4142135623730951},"836":{"tf":1.0},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"840":{"tf":1.0},"879":{"tf":2.8284271247461903},"880":{"tf":2.23606797749979},"881":{"tf":1.4142135623730951},"885":{"tf":1.0},"889":{"tf":1.0},"941":{"tf":1.0},"944":{"tf":1.7320508075688772},"947":{"tf":1.0},"948":{"tf":1.0},"974":{"tf":2.23606797749979},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"977":{"tf":1.0},"978":{"tf":1.7320508075688772},"979":{"tf":1.0},"980":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.4142135623730951},"984":{"tf":1.7320508075688772},"985":{"tf":1.0},"986":{"tf":1.0},"987":{"tf":1.0}},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"\"":{"df":0,"docs":{},"{":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"273":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.7320508075688772}}}}}}},"d":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"735":{"tf":2.23606797749979}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"292":{"tf":1.4142135623730951},"634":{"tf":1.0}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"375":{"tf":1.0},"517":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"205":{"tf":1.0}}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"l":{"_":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"776":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"772":{"tf":1.4142135623730951},"776":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"_":{"c":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":14,"docs":{"1003":{"tf":1.4142135623730951},"203":{"tf":2.8284271247461903},"204":{"tf":2.8284271247461903},"205":{"tf":4.123105625617661},"207":{"tf":1.7320508075688772},"213":{"tf":1.0},"296":{"tf":1.4142135623730951},"308":{"tf":1.0},"772":{"tf":1.4142135623730951},"773":{"tf":2.23606797749979},"776":{"tf":2.8284271247461903},"777":{"tf":1.4142135623730951},"909":{"tf":1.0},"913":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}}}}}}}}},"df":1,"docs":{"814":{"tf":1.7320508075688772}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}}}}}}}}},"df":0,"docs":{}}}}},"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":20,"docs":{"51":{"tf":1.0},"808":{"tf":2.449489742783178},"809":{"tf":1.4142135623730951},"810":{"tf":1.0},"811":{"tf":2.0},"812":{"tf":1.0},"813":{"tf":2.23606797749979},"814":{"tf":2.6457513110645907},"815":{"tf":2.0},"816":{"tf":2.23606797749979},"817":{"tf":1.4142135623730951},"818":{"tf":1.0},"819":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"822":{"tf":1.0},"823":{"tf":1.0},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"565":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"253":{"tf":1.0},"483":{"tf":1.0},"553":{"tf":1.0},"711":{"tf":1.0},"761":{"tf":1.7320508075688772}},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"735":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"402":{"tf":1.0}}}}}},"l":{"a":{"c":{"df":36,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"151":{"tf":1.0},"234":{"tf":1.0},"255":{"tf":1.0},"281":{"tf":1.0},"303":{"tf":1.0},"310":{"tf":1.0},"363":{"tf":1.0},"370":{"tf":1.0},"386":{"tf":2.0},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.0},"391":{"tf":1.4142135623730951},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"417":{"tf":1.0},"524":{"tf":1.4142135623730951},"64":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"69":{"tf":1.0},"705":{"tf":1.0},"721":{"tf":1.0},"739":{"tf":1.0},"761":{"tf":1.4142135623730951},"887":{"tf":1.0},"95":{"tf":1.0}},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":18,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"551":{"tf":1.0},"79":{"tf":2.23606797749979},"80":{"tf":1.4142135623730951},"81":{"tf":1.7320508075688772},"82":{"tf":1.0},"83":{"tf":2.8284271247461903},"84":{"tf":1.7320508075688772},"85":{"tf":1.4142135623730951},"86":{"tf":1.0},"87":{"tf":1.7320508075688772},"88":{"tf":1.0},"89":{"tf":1.0},"90":{"tf":1.0},"91":{"tf":1.0},"92":{"tf":1.0},"933":{"tf":1.0}}},"df":4,"docs":{"759":{"tf":1.7320508075688772},"761":{"tf":1.4142135623730951},"763":{"tf":2.23606797749979},"847":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"761":{"tf":2.0},"763":{"tf":1.4142135623730951}}}}}},"o":{"df":7,"docs":{"311":{"tf":1.0},"312":{"tf":1.0},"313":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.4142135623730951},"319":{"tf":1.0},"985":{"tf":1.0}},"r":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"6":{"tf":1.0}}}}}}}}},"df":12,"docs":{"121":{"tf":1.0},"161":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"375":{"tf":1.7320508075688772},"45":{"tf":1.0},"450":{"tf":1.0},"6":{"tf":2.23606797749979},"710":{"tf":1.4142135623730951},"72":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":2,"docs":{"6":{"tf":2.0},"8":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":8,"docs":{"249":{"tf":1.0},"272":{"tf":1.0},"313":{"tf":1.0},"415":{"tf":1.0},"571":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"933":{"tf":1.0}}}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":32,"docs":{"198":{"tf":1.0},"201":{"tf":1.0},"204":{"tf":1.7320508075688772},"22":{"tf":1.0},"221":{"tf":1.4142135623730951},"255":{"tf":1.0},"270":{"tf":1.0},"3":{"tf":1.0},"346":{"tf":1.0},"385":{"tf":1.0},"404":{"tf":1.4142135623730951},"44":{"tf":1.0},"47":{"tf":1.0},"5":{"tf":1.4142135623730951},"505":{"tf":1.0},"514":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"524":{"tf":1.7320508075688772},"525":{"tf":1.0},"539":{"tf":1.4142135623730951},"588":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.4142135623730951},"7":{"tf":1.0},"735":{"tf":1.4142135623730951},"747":{"tf":1.4142135623730951},"761":{"tf":1.0},"774":{"tf":1.0},"786":{"tf":1.4142135623730951},"829":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"19":{"tf":1.0},"3":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"532":{"tf":1.7320508075688772},"539":{"tf":1.0}}}}}}},"o":{"d":{"df":0,"docs":{},"u":{"c":{"df":4,"docs":{"528":{"tf":1.0},"571":{"tf":1.0},"81":{"tf":1.0},"85":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":3,"docs":{"1":{"tf":1.0},"631":{"tf":1.0},"7":{"tf":1.4142135623730951}}}}}},"t":{"df":19,"docs":{"439":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.7320508075688772},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.7320508075688772},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}}}}},"q":{"_":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"/":{"1":{"df":1,"docs":{"440":{"tf":1.0}}},"2":{"df":1,"docs":{"440":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"439":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":4,"docs":{"62":{"tf":1.4142135623730951},"65":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0}}}}}}}}}},"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"735":{"tf":2.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"_":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"223":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}}},"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"df":1,"docs":{"62":{"tf":1.0}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":4,"docs":{"56":{"tf":1.4142135623730951},"61":{"tf":1.4142135623730951},"62":{"tf":1.7320508075688772},"63":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"61":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"77":{"tf":1.0}}}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":57,"docs":{"0":{"tf":1.0},"105":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.7320508075688772},"222":{"tf":1.0},"223":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"25":{"tf":1.0},"253":{"tf":2.23606797749979},"254":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":1.0},"291":{"tf":1.0},"35":{"tf":1.0},"409":{"tf":1.0},"436":{"tf":1.7320508075688772},"439":{"tf":3.7416573867739413},"450":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":1.0},"503":{"tf":1.0},"512":{"tf":1.4142135623730951},"554":{"tf":1.0},"564":{"tf":1.7320508075688772},"568":{"tf":1.0},"570":{"tf":1.0},"576":{"tf":1.0},"6":{"tf":2.6457513110645907},"62":{"tf":1.0},"63":{"tf":1.7320508075688772},"66":{"tf":1.4142135623730951},"69":{"tf":2.0},"711":{"tf":1.0},"735":{"tf":2.8284271247461903},"757":{"tf":2.23606797749979},"758":{"tf":1.0},"759":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":3.605551275463989},"762":{"tf":1.0},"763":{"tf":1.7320508075688772},"764":{"tf":1.0},"765":{"tf":1.7320508075688772},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.0},"769":{"tf":1.0},"77":{"tf":1.4142135623730951},"770":{"tf":1.4142135623730951},"78":{"tf":2.0},"83":{"tf":1.0},"992":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"r":{"df":165,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"108":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"115":{"tf":1.0},"121":{"tf":1.0},"125":{"tf":1.0},"128":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"141":{"tf":1.0},"146":{"tf":1.4142135623730951},"151":{"tf":1.0},"152":{"tf":1.4142135623730951},"158":{"tf":1.0},"160":{"tf":1.0},"163":{"tf":1.0},"166":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.0},"200":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"209":{"tf":1.0},"215":{"tf":1.0},"218":{"tf":1.4142135623730951},"221":{"tf":1.0},"229":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.4142135623730951},"235":{"tf":1.0},"249":{"tf":1.7320508075688772},"284":{"tf":1.0},"288":{"tf":1.0},"294":{"tf":1.0},"296":{"tf":1.7320508075688772},"297":{"tf":1.4142135623730951},"303":{"tf":1.0},"304":{"tf":1.0},"315":{"tf":1.0},"339":{"tf":1.0},"341":{"tf":1.0},"343":{"tf":1.4142135623730951},"345":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"372":{"tf":1.0},"374":{"tf":1.0},"377":{"tf":1.0},"378":{"tf":1.0},"38":{"tf":1.0},"382":{"tf":1.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.0},"41":{"tf":1.7320508075688772},"410":{"tf":1.4142135623730951},"411":{"tf":1.0},"412":{"tf":1.0},"413":{"tf":1.4142135623730951},"414":{"tf":1.0},"417":{"tf":1.0},"418":{"tf":1.7320508075688772},"422":{"tf":1.4142135623730951},"426":{"tf":1.0},"427":{"tf":1.0},"428":{"tf":1.0},"436":{"tf":1.0},"44":{"tf":1.0},"440":{"tf":1.7320508075688772},"441":{"tf":1.0},"456":{"tf":1.0},"457":{"tf":1.0},"467":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.0},"51":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"52":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":2.23606797749979},"523":{"tf":1.7320508075688772},"526":{"tf":2.0},"528":{"tf":1.0},"53":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.0},"58":{"tf":1.4142135623730951},"588":{"tf":1.0},"593":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":2.6457513110645907},"605":{"tf":1.0},"644":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"696":{"tf":1.0},"698":{"tf":1.0},"705":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":1.4142135623730951},"72":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"744":{"tf":1.4142135623730951},"754":{"tf":1.0},"761":{"tf":2.0},"762":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"779":{"tf":1.4142135623730951},"78":{"tf":1.0},"786":{"tf":1.4142135623730951},"797":{"tf":1.0},"801":{"tf":1.0},"803":{"tf":1.0},"808":{"tf":1.0},"810":{"tf":1.0},"811":{"tf":1.7320508075688772},"813":{"tf":1.7320508075688772},"814":{"tf":2.23606797749979},"817":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.7320508075688772},"847":{"tf":1.4142135623730951},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"855":{"tf":1.4142135623730951},"860":{"tf":1.4142135623730951},"871":{"tf":1.0},"874":{"tf":1.0},"875":{"tf":1.7320508075688772},"876":{"tf":1.4142135623730951},"879":{"tf":1.0},"88":{"tf":1.0},"880":{"tf":1.7320508075688772},"883":{"tf":1.0},"891":{"tf":1.0},"896":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0},"904":{"tf":1.0},"908":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":2.0},"919":{"tf":1.0},"921":{"tf":1.0},"929":{"tf":1.4142135623730951},"956":{"tf":1.0},"959":{"tf":1.0},"990":{"tf":1.0},"994":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"_":{"a":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":14,"docs":{"613":{"tf":2.23606797749979},"614":{"tf":1.0},"615":{"tf":2.23606797749979},"616":{"tf":1.0},"617":{"tf":2.0},"618":{"tf":1.0},"619":{"tf":1.4142135623730951},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"575":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"374":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{"df":4,"docs":{"106":{"tf":1.0},"121":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":12,"docs":{"1013":{"tf":1.0},"201":{"tf":1.0},"211":{"tf":1.0},"324":{"tf":1.7320508075688772},"325":{"tf":1.0},"359":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"798":{"tf":1.0},"819":{"tf":1.0},"928":{"tf":1.0},"939":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"l":{"df":1,"docs":{"912":{"tf":2.0}}},"m":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"175":{"tf":1.0},"569":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"v":{"df":38,"docs":{"204":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"539":{"tf":1.7320508075688772},"599":{"tf":2.0},"6":{"tf":2.0},"600":{"tf":1.0},"602":{"tf":2.449489742783178},"603":{"tf":2.0},"634":{"tf":1.4142135623730951},"635":{"tf":1.0},"648":{"tf":1.4142135623730951},"653":{"tf":1.0},"735":{"tf":1.7320508075688772},"776":{"tf":1.0},"810":{"tf":1.0},"814":{"tf":2.0},"815":{"tf":1.0},"818":{"tf":1.0},"879":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.7320508075688772},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.7320508075688772},"918":{"tf":1.0},"919":{"tf":1.4142135623730951},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"232":{"tf":1.0}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":3,"docs":{"773":{"tf":1.0},"776":{"tf":3.1622776601683795},"777":{"tf":1.0}}},"df":0,"docs":{}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"d":{"1":{"df":1,"docs":{"634":{"tf":2.6457513110645907}}},"2":{"df":1,"docs":{"634":{"tf":2.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"w":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"198":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"628":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"249":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"912":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"628":{"tf":1.0},"776":{"tf":1.0}}}},"v":{"df":5,"docs":{"553":{"tf":1.0},"573":{"tf":1.0},"67":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.4142135623730951}}}},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"c":{"df":28,"docs":{"108":{"tf":1.0},"121":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"204":{"tf":1.0},"213":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"251":{"tf":1.0},"296":{"tf":1.0},"346":{"tf":1.0},"366":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.4142135623730951},"374":{"tf":1.7320508075688772},"377":{"tf":1.0},"380":{"tf":1.0},"418":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"77":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"968":{"tf":1.0}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"284":{"tf":1.0},"370":{"tf":1.0},"450":{"tf":1.0},"516":{"tf":1.0},"576":{"tf":1.0},"747":{"tf":1.0},"751":{"tf":1.0},"803":{"tf":1.0},"931":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"n":{"d":{"df":7,"docs":{"253":{"tf":1.0},"439":{"tf":1.4142135623730951},"69":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"765":{"tf":1.0},"78":{"tf":1.4142135623730951}}},"df":0,"docs":{},"s":{"df":38,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"113":{"tf":1.0},"121":{"tf":1.0},"139":{"tf":1.0},"175":{"tf":1.0},"203":{"tf":1.4142135623730951},"216":{"tf":1.0},"253":{"tf":2.23606797749979},"254":{"tf":1.0},"255":{"tf":1.0},"328":{"tf":1.0},"418":{"tf":1.4142135623730951},"427":{"tf":1.7320508075688772},"439":{"tf":2.0},"450":{"tf":1.4142135623730951},"505":{"tf":1.0},"6":{"tf":2.0},"735":{"tf":1.4142135623730951},"761":{"tf":2.23606797749979},"762":{"tf":1.7320508075688772},"763":{"tf":1.4142135623730951},"777":{"tf":1.0},"78":{"tf":1.4142135623730951},"810":{"tf":1.0},"913":{"tf":1.0},"988":{"tf":2.23606797749979},"989":{"tf":1.4142135623730951},"990":{"tf":1.0},"991":{"tf":1.0},"992":{"tf":1.4142135623730951},"993":{"tf":1.0},"994":{"tf":1.4142135623730951},"995":{"tf":1.0},"996":{"tf":1.4142135623730951},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}},"e":{":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"6":{"tf":1.0}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"6":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"t":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"257":{"tf":1.0}}}}},"df":12,"docs":{"485":{"tf":1.0},"602":{"tf":1.4142135623730951},"606":{"tf":1.0},"615":{"tf":1.0},"632":{"tf":1.0},"654":{"tf":1.4142135623730951},"660":{"tf":1.0},"696":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"872":{"tf":1.0},"933":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"107":{"tf":1.0},"573":{"tf":1.0}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":8,"docs":{"199":{"tf":1.4142135623730951},"388":{"tf":1.0},"576":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"772":{"tf":1.0},"776":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"u":{"b":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"78":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"<":{"df":0,"docs":{},"u":{"6":{"4":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"u":{"8":{"df":1,"docs":{"23":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"x":{"c":{"df":0,"docs":{},"q":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}}},"df":60,"docs":{"108":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.0},"127":{"tf":1.0},"137":{"tf":1.0},"152":{"tf":1.0},"171":{"tf":1.4142135623730951},"179":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"206":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.0},"25":{"tf":2.0},"26":{"tf":2.0},"296":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"350":{"tf":1.4142135623730951},"356":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"404":{"tf":1.0},"415":{"tf":1.0},"416":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"49":{"tf":1.0},"50":{"tf":1.0},"515":{"tf":1.0},"516":{"tf":1.4142135623730951},"523":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.4142135623730951},"539":{"tf":1.0},"553":{"tf":1.0},"565":{"tf":1.0},"599":{"tf":1.4142135623730951},"60":{"tf":1.4142135623730951},"600":{"tf":1.0},"651":{"tf":1.0},"658":{"tf":1.0},"710":{"tf":1.0},"722":{"tf":1.0},"735":{"tf":3.0},"736":{"tf":1.0},"776":{"tf":1.0},"797":{"tf":1.4142135623730951},"799":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0},"858":{"tf":1.0},"916":{"tf":1.0},"983":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"40":{"tf":1.0}}},"n":{"df":4,"docs":{"207":{"tf":1.0},"467":{"tf":1.0},"693":{"tf":1.0},"815":{"tf":1.0}}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"577":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":5,"docs":{"26":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":2.0},"449":{"tf":1.0},"450":{"tf":1.0}}}}},"o":{"a":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"401":{"tf":1.0},"402":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"302":{"tf":1.0},"564":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"25":{"tf":1.0},"26":{"tf":1.4142135623730951}}},"y":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"25":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"df":32,"docs":{"140":{"tf":1.0},"149":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.4142135623730951},"22":{"tf":1.4142135623730951},"221":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.4142135623730951},"280":{"tf":1.0},"284":{"tf":2.0},"286":{"tf":1.0},"288":{"tf":1.0},"30":{"tf":1.0},"300":{"tf":1.0},"333":{"tf":1.0},"341":{"tf":1.4142135623730951},"351":{"tf":1.0},"404":{"tf":1.7320508075688772},"439":{"tf":1.0},"452":{"tf":1.4142135623730951},"455":{"tf":1.4142135623730951},"461":{"tf":1.0},"565":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"660":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":7.280109889280518},"786":{"tf":1.0},"879":{"tf":2.23606797749979},"97":{"tf":1.0}}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"847":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"276":{"tf":1.0}}}},"df":0,"docs":{}},"df":2,"docs":{"203":{"tf":1.0},"364":{"tf":1.0}}}},"v":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"721":{"tf":1.0},"722":{"tf":1.0},"777":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":16,"docs":{"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"206":{"tf":1.7320508075688772},"208":{"tf":1.0},"212":{"tf":1.0},"213":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":2.23606797749979},"263":{"tf":2.23606797749979},"264":{"tf":2.23606797749979},"265":{"tf":1.4142135623730951},"266":{"tf":1.0},"267":{"tf":2.8284271247461903},"576":{"tf":1.0},"777":{"tf":2.0}}}},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"773":{"tf":1.0}}},"t":{"df":1,"docs":{"913":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":6,"docs":{"211":{"tf":1.4142135623730951},"314":{"tf":1.0},"422":{"tf":1.0},"797":{"tf":1.4142135623730951},"885":{"tf":1.0},"935":{"tf":1.0}}}},"s":{"df":3,"docs":{"272":{"tf":1.0},"415":{"tf":1.0},"926":{"tf":1.0}},"i":{"df":0,"docs":{},"t":{"df":13,"docs":{"243":{"tf":1.0},"771":{"tf":2.0},"772":{"tf":1.0},"773":{"tf":1.0},"774":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"780":{"tf":1.0},"781":{"tf":1.0},"831":{"tf":1.0}}}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":50,"docs":{"1002":{"tf":2.23606797749979},"1003":{"tf":1.4142135623730951},"1004":{"tf":1.0},"1005":{"tf":1.0},"1006":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.0},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"303":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"564":{"tf":1.0},"577":{"tf":1.0},"632":{"tf":1.0},"709":{"tf":2.449489742783178},"710":{"tf":1.4142135623730951},"711":{"tf":2.23606797749979},"712":{"tf":3.0},"713":{"tf":1.0},"714":{"tf":3.0},"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":2.23606797749979},"718":{"tf":1.4142135623730951},"719":{"tf":1.0},"720":{"tf":2.449489742783178},"721":{"tf":2.0},"722":{"tf":2.0},"723":{"tf":1.0},"724":{"tf":2.23606797749979},"725":{"tf":2.449489742783178},"726":{"tf":1.0},"727":{"tf":1.0},"728":{"tf":1.0},"729":{"tf":1.7320508075688772},"813":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"717":{"tf":1.4142135623730951}},"s":{"[":{"df":0,"docs":{},"i":{"df":1,"docs":{"717":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"577":{"tf":1.0}}}}}}},"f":{"c":{"#":{"0":{"0":{"0":{"1":{"df":1,"docs":{"811":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"'":{"df":1,"docs":{"555":{"tf":1.0}}},"2":{"0":{"df":1,"docs":{"184":{"tf":1.0}}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"927":{"tf":1.0}}},"df":0,"docs":{}},"4":{"2":{"df":1,"docs":{"154":{"tf":1.0}}},"df":0,"docs":{}},"8":{"4":{"df":4,"docs":{"166":{"tf":1.0},"170":{"tf":1.0},"588":{"tf":1.0},"594":{"tf":1.0}}},"df":0,"docs":{}},"9":{"9":{"df":3,"docs":{"166":{"tf":1.0},"170":{"tf":1.0},"179":{"tf":1.0}}},"df":0,"docs":{}},"df":1016,"docs":{"0":{"tf":1.0},"1":{"tf":2.0},"10":{"tf":1.0},"100":{"tf":1.0},"1000":{"tf":1.0},"1001":{"tf":1.0},"1002":{"tf":2.0},"1003":{"tf":1.0},"1004":{"tf":1.4142135623730951},"1005":{"tf":1.0},"1006":{"tf":1.4142135623730951},"1007":{"tf":1.4142135623730951},"1008":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.4142135623730951},"1015":{"tf":2.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.0},"105":{"tf":1.0},"106":{"tf":2.0},"107":{"tf":1.7320508075688772},"108":{"tf":1.0},"109":{"tf":1.0},"11":{"tf":1.0},"110":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"115":{"tf":1.4142135623730951},"116":{"tf":1.0},"117":{"tf":1.4142135623730951},"118":{"tf":1.4142135623730951},"119":{"tf":1.4142135623730951},"12":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":1.0},"122":{"tf":2.0},"123":{"tf":1.0},"124":{"tf":1.0},"125":{"tf":1.0},"126":{"tf":1.0},"127":{"tf":1.0},"128":{"tf":1.4142135623730951},"129":{"tf":1.0},"13":{"tf":1.4142135623730951},"130":{"tf":1.0},"131":{"tf":1.0},"132":{"tf":1.0},"133":{"tf":1.0},"134":{"tf":1.0},"135":{"tf":1.0},"136":{"tf":2.0},"137":{"tf":1.0},"138":{"tf":1.0},"139":{"tf":1.0},"14":{"tf":1.4142135623730951},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"143":{"tf":1.0},"144":{"tf":1.0},"145":{"tf":1.0},"146":{"tf":1.0},"147":{"tf":1.0},"148":{"tf":1.0},"149":{"tf":1.0},"15":{"tf":1.0},"150":{"tf":2.0},"151":{"tf":1.4142135623730951},"152":{"tf":1.4142135623730951},"153":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.4142135623730951},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.4142135623730951},"16":{"tf":1.7320508075688772},"160":{"tf":1.0},"161":{"tf":1.4142135623730951},"162":{"tf":1.0},"163":{"tf":1.0},"164":{"tf":2.0},"165":{"tf":1.4142135623730951},"166":{"tf":1.0},"167":{"tf":1.0},"168":{"tf":1.0},"169":{"tf":1.0},"17":{"tf":2.0},"170":{"tf":1.0},"171":{"tf":1.0},"172":{"tf":1.0},"173":{"tf":1.0},"174":{"tf":1.0},"175":{"tf":1.0},"176":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.0},"179":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"181":{"tf":1.0},"182":{"tf":2.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.0},"185":{"tf":1.4142135623730951},"186":{"tf":1.7320508075688772},"187":{"tf":1.0},"188":{"tf":1.0},"189":{"tf":1.0},"19":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.4142135623730951},"192":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.4142135623730951},"195":{"tf":2.0},"196":{"tf":1.0},"197":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.0},"2":{"tf":1.4142135623730951},"20":{"tf":1.0},"200":{"tf":1.4142135623730951},"201":{"tf":1.0},"202":{"tf":1.0},"203":{"tf":1.7320508075688772},"204":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"206":{"tf":1.0},"207":{"tf":1.7320508075688772},"208":{"tf":1.0},"209":{"tf":1.0},"21":{"tf":1.0},"210":{"tf":1.0},"211":{"tf":1.0},"212":{"tf":1.7320508075688772},"213":{"tf":1.0},"214":{"tf":1.0},"215":{"tf":2.0},"216":{"tf":1.7320508075688772},"217":{"tf":1.0},"218":{"tf":1.0},"219":{"tf":1.4142135623730951},"22":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"223":{"tf":1.0},"224":{"tf":1.0},"225":{"tf":1.0},"226":{"tf":1.7320508075688772},"227":{"tf":1.0},"228":{"tf":1.0},"229":{"tf":2.0},"23":{"tf":1.0},"230":{"tf":1.4142135623730951},"231":{"tf":2.0},"232":{"tf":1.0},"233":{"tf":1.0},"234":{"tf":1.4142135623730951},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"24":{"tf":1.0},"240":{"tf":1.4142135623730951},"241":{"tf":1.4142135623730951},"242":{"tf":1.0},"243":{"tf":1.0},"244":{"tf":1.0},"245":{"tf":1.0},"246":{"tf":1.0},"247":{"tf":2.0},"248":{"tf":1.4142135623730951},"249":{"tf":1.7320508075688772},"25":{"tf":1.0},"250":{"tf":1.4142135623730951},"251":{"tf":2.449489742783178},"252":{"tf":1.7320508075688772},"253":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":2.0},"256":{"tf":1.0},"257":{"tf":1.0},"258":{"tf":1.0},"259":{"tf":1.0},"26":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.4142135623730951},"262":{"tf":1.0},"263":{"tf":2.0},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":1.7320508075688772},"268":{"tf":2.0},"269":{"tf":1.4142135623730951},"27":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"277":{"tf":1.0},"278":{"tf":1.0},"279":{"tf":2.0},"28":{"tf":1.0},"280":{"tf":1.0},"281":{"tf":1.4142135623730951},"282":{"tf":1.0},"283":{"tf":1.0},"284":{"tf":1.0},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.0},"29":{"tf":1.0},"290":{"tf":1.4142135623730951},"291":{"tf":1.4142135623730951},"292":{"tf":1.0},"293":{"tf":1.0},"294":{"tf":2.0},"295":{"tf":1.4142135623730951},"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"298":{"tf":1.0},"299":{"tf":1.0},"3":{"tf":2.6457513110645907},"30":{"tf":1.0},"300":{"tf":1.0},"301":{"tf":1.4142135623730951},"302":{"tf":1.4142135623730951},"303":{"tf":1.0},"304":{"tf":1.4142135623730951},"305":{"tf":1.4142135623730951},"306":{"tf":1.4142135623730951},"307":{"tf":1.4142135623730951},"308":{"tf":1.0},"309":{"tf":1.0},"31":{"tf":1.0},"310":{"tf":1.7320508075688772},"311":{"tf":2.0},"312":{"tf":1.4142135623730951},"313":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"316":{"tf":1.0},"317":{"tf":1.0},"318":{"tf":1.0},"319":{"tf":1.0},"32":{"tf":1.0},"320":{"tf":1.0},"321":{"tf":1.0},"322":{"tf":2.0},"323":{"tf":1.0},"324":{"tf":1.4142135623730951},"325":{"tf":1.7320508075688772},"326":{"tf":1.4142135623730951},"327":{"tf":1.0},"328":{"tf":1.0},"329":{"tf":1.0},"33":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"34":{"tf":1.0},"340":{"tf":1.4142135623730951},"341":{"tf":1.0},"342":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"35":{"tf":1.0},"350":{"tf":1.0},"351":{"tf":1.0},"352":{"tf":1.0},"353":{"tf":1.0},"354":{"tf":1.4142135623730951},"355":{"tf":1.0},"356":{"tf":1.0},"357":{"tf":1.0},"358":{"tf":1.4142135623730951},"359":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"361":{"tf":1.7320508075688772},"362":{"tf":1.0},"363":{"tf":1.4142135623730951},"364":{"tf":1.4142135623730951},"365":{"tf":1.4142135623730951},"366":{"tf":2.0},"367":{"tf":1.0},"368":{"tf":1.0},"369":{"tf":1.0},"37":{"tf":1.4142135623730951},"370":{"tf":1.7320508075688772},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":2.0},"374":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"377":{"tf":1.0},"378":{"tf":1.0},"379":{"tf":1.0},"38":{"tf":2.0},"380":{"tf":1.0},"381":{"tf":1.0},"382":{"tf":1.0},"383":{"tf":1.0},"384":{"tf":1.0},"385":{"tf":1.0},"386":{"tf":2.0},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.0},"39":{"tf":1.0},"390":{"tf":1.0},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"4":{"tf":1.0},"40":{"tf":1.0},"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.0},"404":{"tf":1.7320508075688772},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.4142135623730951},"408":{"tf":1.0},"409":{"tf":1.0},"41":{"tf":1.0},"410":{"tf":2.0},"411":{"tf":1.4142135623730951},"412":{"tf":1.0},"413":{"tf":1.0},"414":{"tf":1.0},"415":{"tf":1.7320508075688772},"416":{"tf":1.4142135623730951},"417":{"tf":1.0},"418":{"tf":1.0},"419":{"tf":1.0},"42":{"tf":1.0},"420":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"423":{"tf":1.0},"424":{"tf":1.0},"425":{"tf":1.4142135623730951},"426":{"tf":1.4142135623730951},"427":{"tf":1.0},"428":{"tf":1.0},"429":{"tf":1.0},"43":{"tf":1.0},"430":{"tf":2.0},"431":{"tf":1.0},"432":{"tf":1.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"44":{"tf":1.0},"440":{"tf":1.0},"441":{"tf":1.4142135623730951},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"445":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.0},"451":{"tf":2.0},"452":{"tf":2.23606797749979},"453":{"tf":1.4142135623730951},"454":{"tf":1.0},"455":{"tf":1.0},"456":{"tf":1.0},"457":{"tf":1.0},"458":{"tf":1.0},"459":{"tf":1.0},"46":{"tf":1.0},"460":{"tf":1.0},"461":{"tf":1.0},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.4142135623730951},"465":{"tf":2.0},"466":{"tf":1.4142135623730951},"467":{"tf":1.4142135623730951},"468":{"tf":1.0},"469":{"tf":1.4142135623730951},"47":{"tf":1.0},"470":{"tf":1.7320508075688772},"471":{"tf":1.0},"472":{"tf":1.4142135623730951},"473":{"tf":1.0},"474":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"479":{"tf":1.0},"48":{"tf":1.0},"480":{"tf":1.0},"481":{"tf":2.0},"482":{"tf":1.4142135623730951},"483":{"tf":1.0},"484":{"tf":1.0},"485":{"tf":1.4142135623730951},"486":{"tf":1.4142135623730951},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"49":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.0},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"495":{"tf":2.0},"496":{"tf":2.0},"497":{"tf":1.4142135623730951},"498":{"tf":1.0},"499":{"tf":1.7320508075688772},"5":{"tf":1.4142135623730951},"50":{"tf":1.0},"500":{"tf":1.7320508075688772},"501":{"tf":1.7320508075688772},"502":{"tf":1.0},"503":{"tf":1.0},"504":{"tf":1.0},"505":{"tf":1.4142135623730951},"506":{"tf":1.0},"507":{"tf":1.0},"508":{"tf":1.0},"509":{"tf":1.0},"51":{"tf":1.0},"510":{"tf":1.0},"511":{"tf":1.4142135623730951},"512":{"tf":1.4142135623730951},"513":{"tf":2.0},"514":{"tf":1.4142135623730951},"515":{"tf":1.4142135623730951},"516":{"tf":1.0},"517":{"tf":1.0},"518":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"52":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"523":{"tf":1.4142135623730951},"524":{"tf":1.0},"525":{"tf":1.0},"526":{"tf":1.0},"527":{"tf":1.0},"528":{"tf":1.4142135623730951},"529":{"tf":1.0},"53":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.7320508075688772},"533":{"tf":1.0},"534":{"tf":1.0},"535":{"tf":2.0},"536":{"tf":1.4142135623730951},"537":{"tf":1.4142135623730951},"538":{"tf":1.0},"539":{"tf":1.7320508075688772},"54":{"tf":1.0},"540":{"tf":1.0},"541":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.0},"549":{"tf":2.0},"55":{"tf":1.0},"550":{"tf":1.0},"551":{"tf":1.7320508075688772},"552":{"tf":1.0},"553":{"tf":1.7320508075688772},"554":{"tf":1.0},"555":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":2.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"563":{"tf":2.23606797749979},"564":{"tf":1.4142135623730951},"565":{"tf":1.0},"566":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.0},"569":{"tf":1.0},"57":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"572":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":1.4142135623730951},"577":{"tf":1.0},"578":{"tf":1.0},"579":{"tf":1.0},"58":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"583":{"tf":1.0},"584":{"tf":2.0},"585":{"tf":1.4142135623730951},"586":{"tf":1.0},"587":{"tf":1.0},"588":{"tf":1.0},"589":{"tf":1.0},"59":{"tf":1.0},"590":{"tf":1.0},"591":{"tf":1.0},"592":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.0},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"598":{"tf":2.0},"599":{"tf":1.4142135623730951},"6":{"tf":1.4142135623730951},"60":{"tf":1.0},"600":{"tf":1.4142135623730951},"601":{"tf":1.0},"602":{"tf":1.4142135623730951},"603":{"tf":1.0},"604":{"tf":1.0},"605":{"tf":1.0},"606":{"tf":1.0},"607":{"tf":1.0},"608":{"tf":1.0},"609":{"tf":1.0},"61":{"tf":1.0},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":2.0},"614":{"tf":1.4142135623730951},"615":{"tf":1.0},"616":{"tf":1.0},"617":{"tf":1.0},"618":{"tf":1.0},"619":{"tf":1.0},"62":{"tf":1.0},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"627":{"tf":2.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.4142135623730951},"63":{"tf":1.0},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"64":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.4142135623730951},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"646":{"tf":1.4142135623730951},"647":{"tf":1.0},"648":{"tf":1.4142135623730951},"649":{"tf":2.0},"65":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.0},"652":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.4142135623730951},"655":{"tf":1.0},"656":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.4142135623730951},"659":{"tf":1.0},"66":{"tf":1.0},"660":{"tf":1.4142135623730951},"661":{"tf":2.0},"662":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":2.0},"665":{"tf":1.7320508075688772},"666":{"tf":1.0},"667":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"67":{"tf":1.0},"670":{"tf":1.0},"671":{"tf":1.0},"672":{"tf":1.0},"673":{"tf":1.0},"674":{"tf":1.0},"675":{"tf":2.0},"676":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":2.0},"679":{"tf":1.4142135623730951},"68":{"tf":1.0},"680":{"tf":1.0},"681":{"tf":1.0},"682":{"tf":1.0},"683":{"tf":1.4142135623730951},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0},"689":{"tf":1.0},"69":{"tf":1.7320508075688772},"690":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":2.0},"693":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.4142135623730951},"698":{"tf":1.0},"699":{"tf":1.0},"7":{"tf":1.7320508075688772},"70":{"tf":1.0},"700":{"tf":1.4142135623730951},"701":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.0},"705":{"tf":1.4142135623730951},"706":{"tf":1.7320508075688772},"707":{"tf":1.0},"708":{"tf":1.0},"709":{"tf":2.0},"71":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"713":{"tf":1.0},"714":{"tf":1.0},"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.0},"718":{"tf":1.0},"719":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"724":{"tf":1.0},"725":{"tf":1.0},"726":{"tf":1.0},"727":{"tf":1.4142135623730951},"728":{"tf":1.0},"729":{"tf":1.0},"73":{"tf":1.0},"730":{"tf":2.0},"731":{"tf":1.0},"732":{"tf":1.0},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.4142135623730951},"737":{"tf":1.7320508075688772},"738":{"tf":1.0},"739":{"tf":1.7320508075688772},"74":{"tf":1.0},"740":{"tf":1.7320508075688772},"741":{"tf":2.0},"742":{"tf":1.4142135623730951},"743":{"tf":2.449489742783178},"744":{"tf":1.0},"745":{"tf":1.4142135623730951},"746":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"75":{"tf":1.4142135623730951},"750":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.4142135623730951},"755":{"tf":1.7320508075688772},"756":{"tf":1.0},"757":{"tf":2.0},"758":{"tf":1.0},"759":{"tf":1.0},"76":{"tf":1.0},"760":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.4142135623730951},"766":{"tf":1.0},"767":{"tf":1.0},"768":{"tf":1.4142135623730951},"769":{"tf":1.0},"77":{"tf":1.0},"770":{"tf":1.0},"771":{"tf":2.23606797749979},"772":{"tf":1.0},"773":{"tf":1.7320508075688772},"774":{"tf":1.0},"775":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"778":{"tf":1.0},"779":{"tf":1.0},"78":{"tf":1.0},"780":{"tf":1.7320508075688772},"781":{"tf":1.0},"782":{"tf":2.0},"783":{"tf":1.4142135623730951},"784":{"tf":1.0},"785":{"tf":1.0},"786":{"tf":1.0},"787":{"tf":1.0},"788":{"tf":1.0},"789":{"tf":1.0},"79":{"tf":2.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"795":{"tf":2.0},"796":{"tf":1.4142135623730951},"797":{"tf":1.0},"798":{"tf":1.7320508075688772},"799":{"tf":1.4142135623730951},"8":{"tf":1.0},"80":{"tf":1.4142135623730951},"800":{"tf":1.0},"801":{"tf":1.4142135623730951},"802":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":1.4142135623730951},"808":{"tf":2.0},"809":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":1.4142135623730951},"811":{"tf":1.0},"812":{"tf":1.0},"813":{"tf":1.4142135623730951},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"816":{"tf":1.0},"817":{"tf":1.0},"818":{"tf":1.7320508075688772},"819":{"tf":1.4142135623730951},"82":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.4142135623730951},"822":{"tf":1.4142135623730951},"823":{"tf":1.4142135623730951},"824":{"tf":1.0},"825":{"tf":1.0},"826":{"tf":1.4142135623730951},"827":{"tf":2.0},"828":{"tf":1.0},"829":{"tf":1.4142135623730951},"83":{"tf":1.0},"830":{"tf":1.0},"831":{"tf":2.0},"832":{"tf":2.449489742783178},"833":{"tf":1.7320508075688772},"834":{"tf":1.0},"835":{"tf":1.4142135623730951},"836":{"tf":1.4142135623730951},"837":{"tf":1.0},"838":{"tf":1.0},"839":{"tf":1.0},"84":{"tf":1.0},"840":{"tf":1.4142135623730951},"841":{"tf":2.0},"842":{"tf":1.4142135623730951},"843":{"tf":2.0},"844":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":1.4142135623730951},"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"851":{"tf":1.0},"852":{"tf":1.0},"853":{"tf":1.0},"854":{"tf":1.0},"855":{"tf":1.0},"856":{"tf":1.0},"857":{"tf":2.0},"858":{"tf":1.0},"859":{"tf":1.0},"86":{"tf":1.0},"860":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":1.0},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.0},"868":{"tf":1.0},"869":{"tf":1.0},"87":{"tf":1.0},"870":{"tf":1.0},"871":{"tf":2.0},"872":{"tf":1.4142135623730951},"873":{"tf":1.0},"874":{"tf":1.4142135623730951},"875":{"tf":1.0},"876":{"tf":1.0},"877":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":1.0},"88":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"882":{"tf":1.0},"883":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":1.0},"886":{"tf":1.0},"887":{"tf":1.4142135623730951},"888":{"tf":1.0},"889":{"tf":1.0},"89":{"tf":1.0},"890":{"tf":1.0},"891":{"tf":2.0},"892":{"tf":1.0},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.0},"896":{"tf":1.0},"897":{"tf":1.0},"898":{"tf":1.0},"899":{"tf":1.0},"9":{"tf":1.0},"90":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951},"908":{"tf":2.0},"909":{"tf":1.0},"91":{"tf":1.0},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.0},"92":{"tf":1.0},"920":{"tf":1.0},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0},"926":{"tf":2.0},"927":{"tf":1.4142135623730951},"928":{"tf":2.449489742783178},"929":{"tf":1.4142135623730951},"93":{"tf":2.0},"930":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.7320508075688772},"933":{"tf":1.4142135623730951},"934":{"tf":1.0},"935":{"tf":1.0},"936":{"tf":1.4142135623730951},"937":{"tf":1.0},"938":{"tf":1.4142135623730951},"939":{"tf":1.0},"94":{"tf":1.4142135623730951},"940":{"tf":2.0},"941":{"tf":1.4142135623730951},"942":{"tf":1.4142135623730951},"943":{"tf":1.0},"944":{"tf":1.4142135623730951},"945":{"tf":1.0},"946":{"tf":1.0},"947":{"tf":1.0},"948":{"tf":1.0},"949":{"tf":1.0},"95":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"954":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":2.0},"958":{"tf":1.4142135623730951},"959":{"tf":1.0},"96":{"tf":1.0},"960":{"tf":1.0},"961":{"tf":1.4142135623730951},"962":{"tf":1.0},"963":{"tf":1.0},"964":{"tf":1.0},"965":{"tf":1.0},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.0},"969":{"tf":1.0},"97":{"tf":1.4142135623730951},"970":{"tf":1.0},"971":{"tf":1.0},"972":{"tf":1.0},"973":{"tf":1.0},"974":{"tf":2.0},"975":{"tf":1.0},"976":{"tf":1.0},"977":{"tf":1.0},"978":{"tf":1.0},"979":{"tf":1.0},"98":{"tf":1.0},"980":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.0},"984":{"tf":1.4142135623730951},"985":{"tf":2.0},"986":{"tf":1.0},"987":{"tf":1.0},"988":{"tf":2.0},"989":{"tf":1.4142135623730951},"99":{"tf":1.0},"990":{"tf":1.0},"991":{"tf":1.4142135623730951},"992":{"tf":1.0},"993":{"tf":1.0},"994":{"tf":1.4142135623730951},"995":{"tf":1.0},"996":{"tf":1.4142135623730951},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"196":{"tf":1.0}}}},"d":{"df":1,"docs":{"872":{"tf":1.0}},"e":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"v":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":19,"docs":{"124":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"485":{"tf":1.0},"524":{"tf":1.0},"525":{"tf":1.4142135623730951},"61":{"tf":1.0},"651":{"tf":1.0},"700":{"tf":1.0},"747":{"tf":1.7320508075688772},"748":{"tf":1.0},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":1.0},"84":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"324":{"tf":1.0},"354":{"tf":1.0},"962":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"347":{"tf":1.4142135623730951}}}}}}},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"341":{"tf":1.0},"346":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":2,"docs":{"341":{"tf":1.0},"347":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}},"df":5,"docs":{"340":{"tf":1.0},"341":{"tf":2.0},"346":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"359":{"tf":1.0}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}}},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"341":{"tf":2.0},"346":{"tf":1.0},"347":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}}},"p":{"df":1,"docs":{"105":{"tf":1.0}}},"s":{"df":0,"docs":{},"e":{"df":2,"docs":{"428":{"tf":1.0},"747":{"tf":1.0}}},"k":{"df":26,"docs":{"121":{"tf":1.0},"123":{"tf":1.0},"124":{"tf":1.4142135623730951},"138":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"198":{"tf":1.0},"303":{"tf":1.7320508075688772},"316":{"tf":1.0},"365":{"tf":1.0},"374":{"tf":1.0},"429":{"tf":1.4142135623730951},"58":{"tf":1.0},"583":{"tf":1.0},"605":{"tf":1.0},"69":{"tf":1.0},"720":{"tf":1.0},"752":{"tf":1.0},"83":{"tf":1.0},"849":{"tf":1.4142135623730951},"85":{"tf":1.0},"911":{"tf":1.0},"919":{"tf":1.7320508075688772},"938":{"tf":1.0},"945":{"tf":1.0},"965":{"tf":1.0}}}}},"j":{"df":1,"docs":{"126":{"tf":2.8284271247461903}}},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"714":{"tf":1.0}}}}}},"o":{"a":{"d":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"243":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"b":{"'":{"df":1,"docs":{"724":{"tf":1.0}}},"df":1,"docs":{"244":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":2,"docs":{"214":{"tf":1.0},"215":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"374":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"376":{"tf":1.0},"628":{"tf":1.0},"720":{"tf":1.0},"773":{"tf":1.0},"956":{"tf":1.0},"961":{"tf":1.0},"964":{"tf":1.0}}}}}},"c":{"df":1,"docs":{"603":{"tf":3.4641016151377544}},"o":{"c":{"df":0,"docs":{},"o":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}}}},"df":9,"docs":{"115":{"tf":1.0},"304":{"tf":1.0},"390":{"tf":1.4142135623730951},"603":{"tf":2.23606797749979},"678":{"tf":1.0},"679":{"tf":1.0},"680":{"tf":1.0},"682":{"tf":1.0},"819":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"_":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"i":{"d":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}},"e":{"(":{")":{".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"(":{"&":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"l":{"_":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":1,"docs":{"93":{"tf":1.0}}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":5,"docs":{"1004":{"tf":1.0},"271":{"tf":1.0},"327":{"tf":1.0},"340":{"tf":1.0},"389":{"tf":1.0}}},"l":{"df":1,"docs":{"660":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"195":{"tf":1.0},"209":{"tf":1.7320508075688772}}}}},"u":{"df":0,"docs":{},"p":{"'":{"df":1,"docs":{"44":{"tf":1.0}}},"df":19,"docs":{"38":{"tf":3.605551275463989},"388":{"tf":1.0},"39":{"tf":2.449489742783178},"40":{"tf":2.8284271247461903},"41":{"tf":1.7320508075688772},"42":{"tf":1.7320508075688772},"43":{"tf":1.0},"44":{"tf":2.23606797749979},"45":{"tf":1.0},"46":{"tf":2.23606797749979},"47":{"tf":2.0},"48":{"tf":1.7320508075688772},"49":{"tf":1.7320508075688772},"50":{"tf":1.4142135623730951},"51":{"tf":1.4142135623730951},"52":{"tf":2.6457513110645907},"53":{"tf":1.0},"54":{"tf":3.0},"55":{"tf":2.0}},"’":{"df":1,"docs":{"45":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"526":{"tf":1.0}}},"t":{"/":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"_":{"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"615":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}},"df":39,"docs":{"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0},"300":{"tf":1.7320508075688772},"375":{"tf":1.0},"387":{"tf":1.0},"388":{"tf":2.0},"39":{"tf":1.0},"390":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.23606797749979},"45":{"tf":1.0},"46":{"tf":2.6457513110645907},"49":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":2.23606797749979},"520":{"tf":1.0},"525":{"tf":2.449489742783178},"530":{"tf":1.0},"531":{"tf":1.0},"634":{"tf":1.0},"697":{"tf":2.6457513110645907},"761":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951},"858":{"tf":1.4142135623730951},"859":{"tf":1.0},"860":{"tf":1.4142135623730951},"861":{"tf":1.0},"862":{"tf":1.0},"863":{"tf":1.4142135623730951}}}},"t":{"a":{"df":0,"docs":{},"t":{"df":5,"docs":{"257":{"tf":1.0},"439":{"tf":1.0},"456":{"tf":1.0},"507":{"tf":1.0},"724":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":1,"docs":{"721":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":8,"docs":{"204":{"tf":1.0},"335":{"tf":1.0},"435":{"tf":1.0},"438":{"tf":1.0},"712":{"tf":1.0},"714":{"tf":1.4142135623730951},"720":{"tf":1.4142135623730951},"723":{"tf":1.0}}}}}},"n":{"d":{"df":3,"docs":{"374":{"tf":1.0},"723":{"tf":1.0},"758":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":3,"docs":{"374":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"696":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"p":{"c":{"df":5,"docs":{"191":{"tf":1.0},"249":{"tf":1.7320508075688772},"461":{"tf":1.4142135623730951},"50":{"tf":1.0},"512":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":7,"docs":{"347":{"tf":1.0},"6":{"tf":1.7320508075688772},"693":{"tf":1.0},"697":{"tf":2.6457513110645907},"817":{"tf":1.0},"855":{"tf":1.4142135623730951},"876":{"tf":1.0}}}},"n":{"df":27,"docs":{"1004":{"tf":1.0},"160":{"tf":1.0},"171":{"tf":1.0},"203":{"tf":1.0},"233":{"tf":1.0},"234":{"tf":1.4142135623730951},"281":{"tf":1.4142135623730951},"296":{"tf":1.0},"297":{"tf":1.0},"308":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"537":{"tf":1.0},"567":{"tf":1.0},"58":{"tf":1.0},"608":{"tf":1.0},"711":{"tf":1.4142135623730951},"715":{"tf":1.0},"721":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.4142135623730951},"848":{"tf":1.7320508075688772},"849":{"tf":1.4142135623730951},"912":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":184,"docs":{"103":{"tf":1.0},"108":{"tf":1.0},"125":{"tf":1.4142135623730951},"133":{"tf":1.0},"136":{"tf":1.4142135623730951},"137":{"tf":1.4142135623730951},"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"141":{"tf":1.0},"142":{"tf":1.0},"144":{"tf":1.4142135623730951},"145":{"tf":1.0},"147":{"tf":1.4142135623730951},"150":{"tf":2.23606797749979},"151":{"tf":4.47213595499958},"152":{"tf":1.4142135623730951},"153":{"tf":1.0},"154":{"tf":3.7416573867739413},"155":{"tf":2.8284271247461903},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.7320508075688772},"159":{"tf":1.4142135623730951},"160":{"tf":1.4142135623730951},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.7320508075688772},"167":{"tf":1.4142135623730951},"17":{"tf":1.0},"170":{"tf":1.4142135623730951},"172":{"tf":1.0},"175":{"tf":1.4142135623730951},"18":{"tf":1.0},"19":{"tf":2.0},"193":{"tf":1.0},"20":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":2.0},"23":{"tf":1.0},"24":{"tf":1.0},"261":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"271":{"tf":1.0},"272":{"tf":1.4142135623730951},"279":{"tf":2.23606797749979},"280":{"tf":1.4142135623730951},"281":{"tf":1.0},"282":{"tf":1.7320508075688772},"283":{"tf":1.0},"284":{"tf":2.449489742783178},"285":{"tf":1.0},"286":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"289":{"tf":1.4142135623730951},"290":{"tf":1.0},"291":{"tf":1.0},"292":{"tf":1.0},"293":{"tf":2.23606797749979},"311":{"tf":2.449489742783178},"312":{"tf":1.0},"313":{"tf":2.0},"314":{"tf":1.7320508075688772},"315":{"tf":2.0},"316":{"tf":1.7320508075688772},"317":{"tf":1.0},"318":{"tf":1.0},"319":{"tf":1.4142135623730951},"320":{"tf":1.0},"321":{"tf":1.0},"35":{"tf":1.4142135623730951},"358":{"tf":1.0},"362":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"381":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.0},"4":{"tf":1.4142135623730951},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.7320508075688772},"403":{"tf":1.4142135623730951},"404":{"tf":1.4142135623730951},"407":{"tf":1.0},"438":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"454":{"tf":1.0},"455":{"tf":1.4142135623730951},"461":{"tf":1.7320508075688772},"482":{"tf":1.0},"483":{"tf":1.7320508075688772},"511":{"tf":1.0},"514":{"tf":2.0},"516":{"tf":1.0},"518":{"tf":1.4142135623730951},"519":{"tf":1.7320508075688772},"520":{"tf":1.0},"521":{"tf":2.0},"526":{"tf":1.4142135623730951},"528":{"tf":1.0},"530":{"tf":1.4142135623730951},"538":{"tf":1.4142135623730951},"56":{"tf":1.0},"57":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.4142135623730951},"587":{"tf":1.4142135623730951},"588":{"tf":1.0},"59":{"tf":1.0},"593":{"tf":1.4142135623730951},"594":{"tf":1.0},"60":{"tf":2.449489742783178},"601":{"tf":1.4142135623730951},"616":{"tf":1.4142135623730951},"627":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.4142135623730951},"637":{"tf":1.4142135623730951},"64":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"643":{"tf":2.0},"652":{"tf":1.4142135623730951},"667":{"tf":1.0},"681":{"tf":1.0},"69":{"tf":1.0},"695":{"tf":1.4142135623730951},"697":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.4142135623730951},"73":{"tf":1.4142135623730951},"730":{"tf":2.23606797749979},"731":{"tf":1.4142135623730951},"732":{"tf":3.0},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":4.58257569495584},"736":{"tf":2.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.4142135623730951},"74":{"tf":1.0},"740":{"tf":1.0},"75":{"tf":1.4142135623730951},"751":{"tf":1.0},"762":{"tf":1.0},"783":{"tf":1.0},"786":{"tf":1.0},"799":{"tf":1.0},"817":{"tf":1.0},"82":{"tf":1.4142135623730951},"827":{"tf":1.0},"828":{"tf":1.0},"829":{"tf":3.0},"830":{"tf":1.0},"831":{"tf":2.6457513110645907},"832":{"tf":2.0},"835":{"tf":1.0},"836":{"tf":1.4142135623730951},"837":{"tf":1.7320508075688772},"840":{"tf":1.0},"842":{"tf":1.0},"846":{"tf":1.0},"848":{"tf":1.0},"860":{"tf":1.0},"864":{"tf":1.0},"880":{"tf":1.7320508075688772},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"933":{"tf":2.23606797749979},"934":{"tf":1.0},"935":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"977":{"tf":1.4142135623730951}},"e":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"_":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"24":{"tf":1.0}}}}},"c":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"879":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"292":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":15,"docs":{"386":{"tf":2.0},"387":{"tf":1.7320508075688772},"388":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":2.23606797749979},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"520":{"tf":1.4142135623730951}}}}}}}}}}},"s":{"df":0,"docs":{},"t":{"df":7,"docs":{"147":{"tf":1.0},"19":{"tf":1.0},"24":{"tf":1.0},"333":{"tf":1.0},"50":{"tf":1.0},"668":{"tf":1.0},"831":{"tf":1.0}}}}},"·":{"df":1,"docs":{"346":{"tf":1.0}},"s":{")":{"/":{"(":{"a":{"df":0,"docs":{},"·":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"·":{"df":0,"docs":{},"n":{")":{"/":{"df":0,"docs":{},"v":{"df":1,"docs":{"346":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"/":{"2":{"1":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"df":1,"docs":{"696":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":7,"docs":{"111":{"tf":1.0},"450":{"tf":1.0},"563":{"tf":1.0},"602":{"tf":1.0},"629":{"tf":1.0},"644":{"tf":1.0},"815":{"tf":1.0}},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"6":{"tf":1.0},"602":{"tf":1.0}}}}}},"k":{"a":{"c":{"df":1,"docs":{"808":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":1,"docs":{"207":{"tf":1.0}}}},"l":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":18,"docs":{"272":{"tf":1.0},"274":{"tf":1.0},"465":{"tf":2.449489742783178},"466":{"tf":1.0},"467":{"tf":1.0},"468":{"tf":1.0},"469":{"tf":1.7320508075688772},"470":{"tf":2.8284271247461903},"471":{"tf":1.4142135623730951},"472":{"tf":1.0},"473":{"tf":1.0},"474":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"477":{"tf":1.0},"478":{"tf":1.0},"479":{"tf":1.4142135623730951},"480":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"204":{"tf":1.0}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":38,"docs":{"195":{"tf":1.0},"196":{"tf":1.0},"203":{"tf":2.449489742783178},"204":{"tf":4.58257569495584},"205":{"tf":3.0},"207":{"tf":3.3166247903554},"213":{"tf":1.7320508075688772},"222":{"tf":1.0},"263":{"tf":1.0},"264":{"tf":1.4142135623730951},"265":{"tf":1.0},"267":{"tf":2.6457513110645907},"741":{"tf":2.23606797749979},"742":{"tf":2.0},"743":{"tf":2.0},"744":{"tf":1.7320508075688772},"745":{"tf":1.0},"746":{"tf":1.0},"747":{"tf":1.0},"748":{"tf":1.0},"749":{"tf":1.0},"750":{"tf":1.0},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"753":{"tf":1.0},"754":{"tf":1.0},"755":{"tf":1.0},"756":{"tf":1.4142135623730951},"776":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":2.23606797749979},"914":{"tf":1.0},"916":{"tf":1.0},"917":{"tf":1.4142135623730951},"919":{"tf":1.0},"940":{"tf":1.0},"942":{"tf":1.0},"944":{"tf":1.4142135623730951}}}},"m":{"df":0,"docs":{},"e":{"df":67,"docs":{"169":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.449489742783178},"205":{"tf":2.449489742783178},"206":{"tf":1.0},"207":{"tf":1.0},"251":{"tf":1.0},"253":{"tf":1.0},"284":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"402":{"tf":1.0},"439":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"48":{"tf":1.0},"505":{"tf":1.0},"516":{"tf":1.0},"522":{"tf":1.0},"524":{"tf":1.4142135623730951},"528":{"tf":1.4142135623730951},"532":{"tf":1.0},"55":{"tf":1.0},"598":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":2.0},"605":{"tf":1.0},"619":{"tf":1.0},"62":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"654":{"tf":1.0},"68":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":1.0},"699":{"tf":1.0},"701":{"tf":1.4142135623730951},"705":{"tf":1.7320508075688772},"735":{"tf":1.4142135623730951},"759":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":2.0},"784":{"tf":1.0},"786":{"tf":1.7320508075688772},"80":{"tf":1.0},"81":{"tf":1.7320508075688772},"811":{"tf":1.0},"817":{"tf":1.7320508075688772},"829":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"831":{"tf":1.4142135623730951},"84":{"tf":1.0},"840":{"tf":1.0},"85":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"95":{"tf":1.4142135623730951},"992":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":3,"docs":{"46":{"tf":1.0},"51":{"tf":1.0},"571":{"tf":1.0}}}},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"780":{"tf":1.0}}}}}},"n":{"d":{"df":0,"docs":{},"u":{"df":1,"docs":{"627":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":45,"docs":{"322":{"tf":2.6457513110645907},"323":{"tf":1.4142135623730951},"324":{"tf":1.4142135623730951},"325":{"tf":1.0},"326":{"tf":2.23606797749979},"327":{"tf":1.0},"328":{"tf":1.4142135623730951},"329":{"tf":1.0},"330":{"tf":1.0},"331":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.4142135623730951},"336":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.0},"342":{"tf":1.7320508075688772},"343":{"tf":1.7320508075688772},"344":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"351":{"tf":1.0},"352":{"tf":1.0},"353":{"tf":1.0},"354":{"tf":1.0},"355":{"tf":1.0},"356":{"tf":1.4142135623730951},"357":{"tf":1.0},"358":{"tf":1.4142135623730951},"359":{"tf":2.23606797749979},"360":{"tf":1.0},"361":{"tf":1.0},"362":{"tf":1.0},"363":{"tf":1.4142135623730951},"364":{"tf":1.0},"365":{"tf":1.0},"721":{"tf":1.0}}},"df":0,"docs":{}}}},"df":1,"docs":{"343":{"tf":1.0}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":3,"docs":{"341":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"a":{"d":{"d":{"(":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"d":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{":":{":":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"n":{"df":1,"docs":{"784":{"tf":1.0}}}}}},"v":{"df":0,"docs":{},"e":{"df":2,"docs":{"732":{"tf":1.4142135623730951},"996":{"tf":1.0}}}},"w":{"df":1,"docs":{"721":{"tf":1.0}}}},"b":{"df":1,"docs":{"126":{"tf":2.449489742783178}}},"c":{"a":{"df":0,"docs":{},"l":{"a":{"b":{"df":0,"docs":{},"l":{"df":6,"docs":{"230":{"tf":1.0},"231":{"tf":1.0},"42":{"tf":1.0},"427":{"tf":1.4142135623730951},"437":{"tf":1.0},"58":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"1":{"df":1,"docs":{"485":{"tf":1.7320508075688772}}},"3":{"df":1,"docs":{"485":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"1":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"2":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"3":{"df":1,"docs":{"485":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":4,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951},"751":{"tf":1.0},"752":{"tf":2.23606797749979}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"485":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"p":{"df":4,"docs":{"748":{"tf":1.4142135623730951},"749":{"tf":1.0},"751":{"tf":1.0},"752":{"tf":2.0}}}}},"df":39,"docs":{"170":{"tf":1.0},"22":{"tf":1.4142135623730951},"231":{"tf":1.4142135623730951},"24":{"tf":1.0},"25":{"tf":1.4142135623730951},"252":{"tf":1.0},"253":{"tf":1.4142135623730951},"333":{"tf":1.4142135623730951},"343":{"tf":1.0},"345":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.7320508075688772},"368":{"tf":1.0},"435":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.0},"455":{"tf":2.0},"482":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.4142135623730951},"5":{"tf":1.4142135623730951},"52":{"tf":1.0},"520":{"tf":1.4142135623730951},"522":{"tf":1.7320508075688772},"526":{"tf":1.0},"553":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":1.4142135623730951},"568":{"tf":1.0},"571":{"tf":1.0},"588":{"tf":1.0},"61":{"tf":1.4142135623730951},"628":{"tf":1.0},"629":{"tf":1.0},"633":{"tf":1.4142135623730951},"711":{"tf":1.0},"735":{"tf":1.4142135623730951},"747":{"tf":1.0},"752":{"tf":1.0}}},"p":{"df":1,"docs":{"912":{"tf":2.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"913":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"270":{"tf":1.0}}},"n":{"df":1,"docs":{"191":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":18,"docs":{"138":{"tf":1.0},"142":{"tf":1.4142135623730951},"296":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"303":{"tf":1.0},"346":{"tf":1.0},"440":{"tf":1.0},"450":{"tf":1.0},"564":{"tf":1.0},"618":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.4142135623730951},"732":{"tf":1.4142135623730951},"947":{"tf":1.0},"964":{"tf":1.0}}}}}},"df":0,"docs":{}}},"h":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":17,"docs":{"138":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"205":{"tf":1.7320508075688772},"208":{"tf":1.0},"218":{"tf":1.4142135623730951},"221":{"tf":1.0},"273":{"tf":1.0},"300":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"342":{"tf":1.0},"345":{"tf":1.0},"346":{"tf":1.4142135623730951},"349":{"tf":1.0},"374":{"tf":1.7320508075688772},"911":{"tf":1.0}},"e":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":1,"docs":{"300":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"m":{"a":{"df":3,"docs":{"208":{"tf":1.0},"553":{"tf":1.0},"761":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":9,"docs":{"177":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":1.0},"570":{"tf":1.0},"575":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"714":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"891":{"tf":1.0},"908":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":16,"docs":{"194":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.0},"24":{"tf":1.0},"326":{"tf":1.0},"340":{"tf":1.0},"40":{"tf":1.0},"523":{"tf":1.0},"740":{"tf":1.0},"743":{"tf":1.0},"776":{"tf":1.0},"840":{"tf":1.0},"849":{"tf":1.0},"855":{"tf":1.0},"928":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"336":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"191":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":1,"docs":{"913":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"k":{"#":{"1":{"7":{"8":{"1":{"df":1,"docs":{"291":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"b":{"/":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"/":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"793":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"/":{"1":{"7":{"9":{"6":{"df":1,"docs":{"824":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"8":{"1":{"1":{"df":1,"docs":{"712":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"2":{"1":{"6":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"7":{"3":{"3":{"df":1,"docs":{"500":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"6":{"7":{"3":{"df":1,"docs":{"551":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"df":1,"docs":{"990":{"tf":1.0}}},"5":{"1":{"2":{"2":{"df":1,"docs":{"712":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"9":{"7":{"1":{"df":1,"docs":{"74":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"/":{"2":{"1":{"7":{"7":{"df":1,"docs":{"440":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"7":{"8":{"6":{"df":2,"docs":{"551":{"tf":1.0},"555":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"4":{"7":{"2":{"2":{"df":1,"docs":{"35":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":11,"docs":{"108":{"tf":1.0},"210":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":2.23606797749979},"872":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"888":{"tf":1.0},"933":{"tf":1.0},"969":{"tf":1.0},"973":{"tf":1.0}},"’":{"df":1,"docs":{"515":{"tf":1.0}}}}},"df":4,"docs":{"333":{"tf":2.0},"346":{"tf":2.449489742783178},"735":{"tf":1.0},"94":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"350":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"349":{"tf":2.449489742783178},"350":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"df":3,"docs":{"343":{"tf":1.0},"349":{"tf":2.23606797749979},"350":{"tf":1.0}}},"m":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"439":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"363":{"tf":1.0},"956":{"tf":1.0}}}}}}}}},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"573":{"tf":1.0}}}},"df":0,"docs":{}}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"400":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":33,"docs":{"196":{"tf":1.0},"214":{"tf":1.0},"217":{"tf":1.0},"252":{"tf":1.0},"267":{"tf":1.0},"349":{"tf":1.7320508075688772},"351":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":2.449489742783178},"773":{"tf":1.0},"776":{"tf":1.4142135623730951},"778":{"tf":1.0},"799":{"tf":1.0},"940":{"tf":2.23606797749979},"941":{"tf":1.4142135623730951},"942":{"tf":2.0},"943":{"tf":1.4142135623730951},"944":{"tf":1.0},"945":{"tf":1.0},"946":{"tf":1.0},"947":{"tf":1.0},"948":{"tf":1.0},"949":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"952":{"tf":1.0},"953":{"tf":1.0},"954":{"tf":1.0},"955":{"tf":1.0},"956":{"tf":1.4142135623730951},"958":{"tf":1.0},"960":{"tf":1.0}}}}},"df":10,"docs":{"284":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.0},"349":{"tf":1.0},"485":{"tf":1.0},"503":{"tf":1.0},"516":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"83":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"204":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"2":{"5":{"6":{"df":0,"docs":{},"k":{"1":{"df":1,"docs":{"95":{"tf":1.0}}},"df":0,"docs":{}},"r":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":13,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"93":{"tf":2.0},"94":{"tf":1.4142135623730951},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":5,"docs":{"103":{"tf":1.0},"105":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.7320508075688772},"97":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":1,"docs":{"723":{"tf":1.0}}}},"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"346":{"tf":1.0}}}}}},"df":3,"docs":{"341":{"tf":2.0},"349":{"tf":1.0},"723":{"tf":1.4142135623730951}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"341":{"tf":2.0}}}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":28,"docs":{"185":{"tf":1.0},"204":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"252":{"tf":1.0},"255":{"tf":1.0},"30":{"tf":1.0},"330":{"tf":1.0},"340":{"tf":1.0},"342":{"tf":1.0},"344":{"tf":1.0},"351":{"tf":1.0},"446":{"tf":1.0},"470":{"tf":1.0},"485":{"tf":1.0},"501":{"tf":1.0},"505":{"tf":1.4142135623730951},"521":{"tf":1.0},"524":{"tf":1.0},"64":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"814":{"tf":1.0},"874":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.4142135623730951},"936":{"tf":1.4142135623730951},"992":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"r":{"df":165,"docs":{"1":{"tf":1.0},"100":{"tf":1.7320508075688772},"1002":{"tf":1.0},"1004":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.7320508075688772},"106":{"tf":1.0},"115":{"tf":1.4142135623730951},"122":{"tf":1.0},"128":{"tf":1.4142135623730951},"136":{"tf":1.0},"142":{"tf":1.7320508075688772},"150":{"tf":1.0},"156":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.7320508075688772},"182":{"tf":1.0},"188":{"tf":1.7320508075688772},"195":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"211":{"tf":2.0},"215":{"tf":1.0},"225":{"tf":1.7320508075688772},"229":{"tf":1.0},"231":{"tf":1.7320508075688772},"237":{"tf":1.4142135623730951},"247":{"tf":1.0},"255":{"tf":1.7320508075688772},"268":{"tf":1.0},"275":{"tf":1.4142135623730951},"279":{"tf":1.0},"286":{"tf":1.7320508075688772},"294":{"tf":1.0},"30":{"tf":2.0},"303":{"tf":1.0},"304":{"tf":1.4142135623730951},"311":{"tf":1.0},"317":{"tf":1.4142135623730951},"322":{"tf":1.0},"346":{"tf":1.0},"354":{"tf":1.7320508075688772},"366":{"tf":1.0},"368":{"tf":1.4142135623730951},"378":{"tf":1.4142135623730951},"38":{"tf":1.7320508075688772},"386":{"tf":1.0},"392":{"tf":1.7320508075688772},"40":{"tf":1.4142135623730951},"41":{"tf":1.4142135623730951},"410":{"tf":1.4142135623730951},"418":{"tf":1.0},"419":{"tf":1.4142135623730951},"42":{"tf":1.0},"420":{"tf":1.7320508075688772},"430":{"tf":1.0},"44":{"tf":1.0},"442":{"tf":1.7320508075688772},"451":{"tf":1.0},"457":{"tf":1.4142135623730951},"46":{"tf":1.0},"465":{"tf":1.0},"474":{"tf":1.4142135623730951},"481":{"tf":1.0},"487":{"tf":1.4142135623730951},"495":{"tf":1.0},"505":{"tf":1.7320508075688772},"513":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":2.0},"52":{"tf":1.0},"528":{"tf":1.7320508075688772},"53":{"tf":1.7320508075688772},"535":{"tf":1.0},"541":{"tf":1.7320508075688772},"549":{"tf":1.0},"555":{"tf":1.7320508075688772},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.7320508075688772},"569":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"578":{"tf":1.4142135623730951},"584":{"tf":1.0},"590":{"tf":1.7320508075688772},"598":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"605":{"tf":2.0},"613":{"tf":1.0},"619":{"tf":2.0},"627":{"tf":1.0},"628":{"tf":1.0},"639":{"tf":2.0},"649":{"tf":1.0},"656":{"tf":1.7320508075688772},"664":{"tf":1.0},"670":{"tf":1.4142135623730951},"678":{"tf":1.0},"684":{"tf":1.4142135623730951},"69":{"tf":1.4142135623730951},"692":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.4142135623730951},"701":{"tf":1.4142135623730951},"709":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":1.7320508075688772},"757":{"tf":1.0},"763":{"tf":1.7320508075688772},"772":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.4142135623730951},"782":{"tf":1.0},"788":{"tf":1.7320508075688772},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"801":{"tf":1.4142135623730951},"808":{"tf":1.0},"819":{"tf":1.4142135623730951},"827":{"tf":1.0},"83":{"tf":1.0},"833":{"tf":1.4142135623730951},"841":{"tf":1.0},"85":{"tf":1.7320508075688772},"850":{"tf":1.7320508075688772},"857":{"tf":1.0},"864":{"tf":1.7320508075688772},"871":{"tf":1.0},"874":{"tf":1.0},"883":{"tf":1.4142135623730951},"891":{"tf":1.0},"9":{"tf":1.4142135623730951},"900":{"tf":1.7320508075688772},"908":{"tf":1.0},"917":{"tf":1.7320508075688772},"926":{"tf":1.0},"93":{"tf":1.4142135623730951},"935":{"tf":1.4142135623730951},"940":{"tf":1.4142135623730951},"942":{"tf":1.0},"945":{"tf":1.4142135623730951},"946":{"tf":1.4142135623730951},"948":{"tf":1.7320508075688772},"95":{"tf":1.7320508075688772},"955":{"tf":1.0},"957":{"tf":1.4142135623730951},"961":{"tf":2.0},"962":{"tf":1.4142135623730951},"963":{"tf":1.4142135623730951},"965":{"tf":2.0},"972":{"tf":1.0},"974":{"tf":1.0},"980":{"tf":1.4142135623730951},"988":{"tf":1.0},"99":{"tf":1.4142135623730951},"994":{"tf":1.4142135623730951}}}}},"df":3,"docs":{"1008":{"tf":1.0},"210":{"tf":1.0},"724":{"tf":1.0}},"e":{"d":{"df":6,"docs":{"113":{"tf":1.4142135623730951},"126":{"tf":1.0},"272":{"tf":1.0},"455":{"tf":1.0},"735":{"tf":1.7320508075688772},"85":{"tf":1.4142135623730951}}},"df":37,"docs":{"184":{"tf":1.0},"185":{"tf":1.0},"186":{"tf":1.0},"198":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"277":{"tf":1.0},"314":{"tf":1.0},"316":{"tf":1.0},"373":{"tf":1.0},"384":{"tf":1.0},"415":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"441":{"tf":1.0},"444":{"tf":1.0},"446":{"tf":1.0},"447":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.4142135623730951},"504":{"tf":1.0},"565":{"tf":1.0},"571":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"64":{"tf":1.0},"65":{"tf":1.0},"735":{"tf":1.4142135623730951},"77":{"tf":1.0},"800":{"tf":1.0},"831":{"tf":1.0},"932":{"tf":1.0},"933":{"tf":1.7320508075688772}},"k":{"df":9,"docs":{"272":{"tf":1.0},"296":{"tf":1.0},"313":{"tf":1.0},"42":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"723":{"tf":1.0},"772":{"tf":1.0},"810":{"tf":1.0}}},"m":{"df":6,"docs":{"697":{"tf":1.0},"724":{"tf":1.0},"77":{"tf":1.0},"773":{"tf":1.0},"778":{"tf":1.4142135623730951},"84":{"tf":1.0}}},"n":{"df":7,"docs":{"135":{"tf":1.0},"450":{"tf":1.0},"520":{"tf":1.0},"58":{"tf":1.0},"615":{"tf":1.0},"619":{"tf":1.0},"680":{"tf":1.0}}}},"g":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"203":{"tf":1.0},"204":{"tf":1.0},"335":{"tf":1.4142135623730951},"45":{"tf":1.7320508075688772},"776":{"tf":1.0}}}}}}},"l":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"1004":{"tf":1.0},"515":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":23,"docs":{"1003":{"tf":1.4142135623730951},"204":{"tf":1.0},"229":{"tf":2.23606797749979},"230":{"tf":1.0},"231":{"tf":1.7320508075688772},"232":{"tf":1.7320508075688772},"233":{"tf":1.0},"234":{"tf":3.0},"235":{"tf":1.0},"236":{"tf":1.0},"237":{"tf":1.4142135623730951},"238":{"tf":1.0},"239":{"tf":1.0},"240":{"tf":1.0},"241":{"tf":1.0},"242":{"tf":1.0},"243":{"tf":1.7320508075688772},"244":{"tf":1.0},"245":{"tf":1.0},"246":{"tf":1.4142135623730951},"565":{"tf":1.0},"633":{"tf":1.4142135623730951},"856":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"633":{"tf":1.0}}}}}},"df":0,"docs":{}},"f":{":":{":":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"24":{"tf":3.3166247903554}}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"24":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":10,"docs":{"208":{"tf":1.4142135623730951},"23":{"tf":1.0},"272":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"375":{"tf":1.0},"399":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"722":{"tf":1.0}}},"l":{"df":4,"docs":{"196":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.4142135623730951},"743":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.7320508075688772}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"207":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":8,"docs":{"166":{"tf":1.0},"24":{"tf":1.0},"534":{"tf":1.4142135623730951},"61":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.0},"660":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":3,"docs":{"231":{"tf":1.0},"374":{"tf":1.0},"54":{"tf":1.0}}}},"n":{"d":{"df":31,"docs":{"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"257":{"tf":1.0},"439":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":2.0},"486":{"tf":1.0},"491":{"tf":1.0},"500":{"tf":1.0},"501":{"tf":1.0},"507":{"tf":1.0},"512":{"tf":1.0},"528":{"tf":1.0},"553":{"tf":1.0},"594":{"tf":1.0},"62":{"tf":1.0},"641":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"711":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":2.0},"763":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"980":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"455":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.0},"521":{"tf":1.0},"994":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"470":{"tf":1.0}}}}},"s":{"df":9,"docs":{"121":{"tf":1.0},"267":{"tf":1.0},"288":{"tf":1.0},"3":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"5":{"tf":1.0},"571":{"tf":1.0},"720":{"tf":1.0}},"i":{"b":{"df":0,"docs":{},"l":{"df":4,"docs":{"175":{"tf":1.0},"376":{"tf":1.0},"569":{"tf":1.0},"751":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":3,"docs":{"564":{"tf":1.0},"571":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}},"t":{"df":16,"docs":{"222":{"tf":1.0},"253":{"tf":1.0},"47":{"tf":1.0},"485":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.4142135623730951},"519":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":2.0},"633":{"tf":1.4142135623730951},"701":{"tf":1.0},"715":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.4142135623730951}}}}}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":16,"docs":{"163":{"tf":1.0},"203":{"tf":1.0},"254":{"tf":1.0},"28":{"tf":1.0},"314":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"60":{"tf":1.0},"645":{"tf":1.0},"68":{"tf":1.0},"74":{"tf":1.0},"772":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":1.4142135623730951},"945":{"tf":1.0},"95":{"tf":1.0}}}},"df":1,"docs":{"692":{"tf":1.0}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":3,"docs":{"136":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0}}},"df":0,"docs":{}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":19,"docs":{"126":{"tf":1.0},"332":{"tf":2.449489742783178},"333":{"tf":2.449489742783178},"335":{"tf":1.4142135623730951},"342":{"tf":1.0},"343":{"tf":2.0},"344":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":2.0},"348":{"tf":1.4142135623730951},"349":{"tf":2.0},"350":{"tf":1.0},"39":{"tf":1.0},"44":{"tf":1.0},"46":{"tf":1.4142135623730951},"522":{"tf":1.0},"878":{"tf":1.0},"932":{"tf":1.0}},"e":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}}},"<":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"343":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"<":{"3":{"2":{"df":1,"docs":{"344":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"345":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"t":{",":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":2,"docs":{"332":{"tf":1.4142135623730951},"333":{"tf":1.7320508075688772}},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"347":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"8":{"df":1,"docs":{"332":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":3,"docs":{"335":{"tf":1.0},"436":{"tf":1.0},"992":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"j":{"df":1,"docs":{"808":{"tf":1.0}}}}},"i":{"a":{"df":0,"docs":{},"l":{"df":5,"docs":{"26":{"tf":1.7320508075688772},"331":{"tf":1.0},"553":{"tf":1.0},"559":{"tf":1.0},"759":{"tf":1.0}}}},"df":1,"docs":{"124":{"tf":1.0}}},"v":{"df":22,"docs":{"111":{"tf":1.0},"18":{"tf":1.0},"19":{"tf":1.0},"214":{"tf":1.0},"22":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"267":{"tf":1.0},"270":{"tf":1.0},"340":{"tf":1.0},"375":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":2.449489742783178},"503":{"tf":1.0},"512":{"tf":1.7320508075688772},"63":{"tf":1.4142135623730951},"66":{"tf":1.0},"776":{"tf":1.0},"786":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"761":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"765":{"tf":1.0}}}},"i":{"c":{"df":28,"docs":{"198":{"tf":1.0},"206":{"tf":1.0},"221":{"tf":1.0},"231":{"tf":1.0},"276":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"38":{"tf":3.1622776601683795},"39":{"tf":1.7320508075688772},"40":{"tf":2.0},"41":{"tf":1.7320508075688772},"42":{"tf":1.0},"43":{"tf":1.7320508075688772},"44":{"tf":1.4142135623730951},"45":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"47":{"tf":1.7320508075688772},"48":{"tf":2.0},"49":{"tf":1.0},"50":{"tf":2.0},"51":{"tf":1.4142135623730951},"52":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.4142135623730951},"54":{"tf":2.0},"55":{"tf":1.0},"58":{"tf":1.0},"95":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"38":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":2,"docs":{"634":{"tf":1.4142135623730951},"636":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":21,"docs":{"234":{"tf":1.7320508075688772},"239":{"tf":1.0},"376":{"tf":1.0},"432":{"tf":1.4142135623730951},"452":{"tf":2.8284271247461903},"453":{"tf":2.6457513110645907},"455":{"tf":1.7320508075688772},"456":{"tf":1.0},"459":{"tf":2.0},"461":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"627":{"tf":1.0},"629":{"tf":1.7320508075688772},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"636":{"tf":1.0},"64":{"tf":1.0},"641":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":22,"docs":{"627":{"tf":2.0},"628":{"tf":1.4142135623730951},"629":{"tf":1.7320508075688772},"630":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.4142135623730951},"635":{"tf":1.0},"636":{"tf":1.0},"637":{"tf":1.0},"638":{"tf":1.0},"639":{"tf":1.0},"640":{"tf":1.0},"641":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.4142135623730951},"645":{"tf":1.0},"646":{"tf":1.0},"647":{"tf":1.0},"648":{"tf":1.0}}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":14,"docs":{"451":{"tf":2.23606797749979},"452":{"tf":1.0},"453":{"tf":1.0},"454":{"tf":1.0},"455":{"tf":2.23606797749979},"456":{"tf":1.0},"457":{"tf":1.0},"458":{"tf":1.0},"459":{"tf":1.0},"460":{"tf":1.0},"461":{"tf":1.4142135623730951},"462":{"tf":1.0},"463":{"tf":1.0},"464":{"tf":1.0}},"s":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"452":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.0}},"s":{"(":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"455":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"455":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}}}},"t":{"_":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"300":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":3,"docs":{"665":{"tf":1.4142135623730951},"668":{"tf":1.0},"673":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":76,"docs":{"1004":{"tf":1.7320508075688772},"113":{"tf":1.0},"154":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":2.23606797749979},"205":{"tf":1.7320508075688772},"207":{"tf":2.0},"219":{"tf":1.0},"229":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":2.23606797749979},"232":{"tf":1.4142135623730951},"234":{"tf":1.4142135623730951},"235":{"tf":1.4142135623730951},"24":{"tf":1.0},"253":{"tf":1.0},"29":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.0},"323":{"tf":1.0},"333":{"tf":1.0},"336":{"tf":1.0},"343":{"tf":1.0},"345":{"tf":1.7320508075688772},"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"368":{"tf":1.4142135623730951},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"412":{"tf":1.0},"418":{"tf":1.0},"452":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"459":{"tf":1.4142135623730951},"46":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"5":{"tf":1.0},"517":{"tf":1.0},"525":{"tf":1.0},"567":{"tf":1.7320508075688772},"569":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.0},"588":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"669":{"tf":1.0},"69":{"tf":1.0},"697":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"752":{"tf":1.7320508075688772},"774":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"818":{"tf":1.0},"819":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.4142135623730951},"842":{"tf":1.0},"876":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.4142135623730951},"895":{"tf":1.4142135623730951},"898":{"tf":1.0},"916":{"tf":1.0},"920":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"d":{"df":3,"docs":{"974":{"tf":1.0},"975":{"tf":1.0},"978":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"665":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"670":{"tf":1.0},"673":{"tf":1.0}},"s":{"(":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"668":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":2,"docs":{"895":{"tf":1.0},"898":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"729":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"776":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":2,"docs":{"773":{"tf":1.0},"776":{"tf":1.4142135623730951}}}}}}}}},"u":{"df":0,"docs":{},"p":{"df":3,"docs":{"113":{"tf":1.0},"26":{"tf":1.0},"364":{"tf":1.4142135623730951}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"199":{"tf":1.0}}},"r":{"df":15,"docs":{"198":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.4142135623730951},"209":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"35":{"tf":1.0},"361":{"tf":1.0},"367":{"tf":1.0},"426":{"tf":1.0},"483":{"tf":1.0},"724":{"tf":1.0},"81":{"tf":1.0},"962":{"tf":1.0},"990":{"tf":1.0}}}}}},"h":{"a":{"(":{"0":{"df":0,"docs":{},"x":{"a":{"1":{"0":{"df":0,"docs":{},"f":{"1":{"2":{"8":{"7":{"2":{"4":{"4":{"7":{"9":{"5":{"8":{"d":{"5":{"0":{"a":{"a":{"7":{"b":{"9":{"3":{"7":{"b":{"0":{"1":{"0":{"6":{"5":{"6":{"1":{"a":{"5":{"8":{"8":{"df":0,"docs":{},"e":{"0":{"df":0,"docs":{},"e":{"2":{"6":{"2":{"8":{"d":{"3":{"3":{"df":0,"docs":{},"f":{"8":{"1":{"b":{"5":{"3":{"6":{"1":{"b":{"1":{"3":{"d":{"b":{"c":{"df":0,"docs":{},"f":{"8":{"d":{"df":0,"docs":{},"f":{"7":{"0":{"8":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"2":{"5":{"6":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"(":{"\"":{"a":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"501":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"501":{"tf":1.0}}}}}}}}}},"df":0,"docs":{},"s":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"a":{"c":{"df":0,"docs":{},"t":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"255":{"tf":1.0},"505":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"780":{"tf":1.0}}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"l":{"df":17,"docs":{"111":{"tf":1.0},"121":{"tf":1.0},"205":{"tf":3.0},"247":{"tf":1.0},"401":{"tf":1.0},"472":{"tf":1.0},"602":{"tf":3.0},"609":{"tf":1.0},"617":{"tf":1.4142135623730951},"693":{"tf":1.4142135623730951},"696":{"tf":1.0},"712":{"tf":1.4142135623730951},"722":{"tf":1.0},"743":{"tf":1.7320508075688772},"75":{"tf":1.0},"751":{"tf":1.0},"755":{"tf":1.0}}}},"p":{"df":0,"docs":{},"e":{"df":5,"docs":{"181":{"tf":1.0},"548":{"tf":1.0},"747":{"tf":1.0},"749":{"tf":1.0},"776":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":14,"docs":{"198":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.7320508075688772},"26":{"tf":1.4142135623730951},"336":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.0},"569":{"tf":1.0},"716":{"tf":1.0},"78":{"tf":1.0},"876":{"tf":1.0},"992":{"tf":1.0}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"846":{"tf":1.0}}}}}},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"1002":{"tf":1.0}},"t":{"a":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"206":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":2,"docs":{"712":{"tf":1.0},"778":{"tf":1.0}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"df":1,"docs":{"1":{"tf":1.0}}},"df":0,"docs":{}}}}}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"874":{"tf":1.0}}}},"r":{"df":0,"docs":{},"t":{"df":12,"docs":{"206":{"tf":1.0},"208":{"tf":1.0},"310":{"tf":1.0},"356":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.4142135623730951},"567":{"tf":1.0},"569":{"tf":1.0},"729":{"tf":1.0},"762":{"tf":1.0},"778":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"111":{"tf":1.0},"203":{"tf":1.0},"42":{"tf":1.0},"894":{"tf":1.0}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"895":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"934":{"tf":1.0}}}}}}}}},"t":{"df":1,"docs":{"600":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":7,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"679":{"tf":1.0},"7":{"tf":1.0},"850":{"tf":1.0},"853":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"w":{"df":9,"docs":{"152":{"tf":1.0},"444":{"tf":1.0},"526":{"tf":1.0},"564":{"tf":1.0},"7":{"tf":1.0},"711":{"tf":1.0},"721":{"tf":1.7320508075688772},"729":{"tf":1.4142135623730951},"874":{"tf":1.0}},"n":{"df":3,"docs":{"406":{"tf":1.0},"471":{"tf":1.0},"992":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"744":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"432":{"tf":1.0}}}}}}},"i":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"697":{"tf":1.0},"786":{"tf":1.4142135623730951}}}},"d":{"df":0,"docs":{},"e":{"df":44,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"19":{"tf":1.0},"217":{"tf":1.0},"253":{"tf":1.7320508075688772},"304":{"tf":1.0},"315":{"tf":1.0},"354":{"tf":1.0},"402":{"tf":1.0},"409":{"tf":1.0},"485":{"tf":1.0},"521":{"tf":1.7320508075688772},"526":{"tf":1.0},"602":{"tf":1.4142135623730951},"61":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"701":{"tf":1.4142135623730951},"730":{"tf":2.23606797749979},"731":{"tf":1.4142135623730951},"732":{"tf":2.23606797749979},"733":{"tf":1.0},"734":{"tf":1.0},"735":{"tf":1.0},"736":{"tf":1.0},"737":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"740":{"tf":1.0},"747":{"tf":2.0},"748":{"tf":1.4142135623730951},"749":{"tf":2.449489742783178},"751":{"tf":1.4142135623730951},"752":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"777":{"tf":1.0},"828":{"tf":1.4142135623730951},"83":{"tf":1.4142135623730951},"831":{"tf":1.0},"835":{"tf":1.0},"837":{"tf":1.0},"983":{"tf":1.0},"994":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"g":{"df":2,"docs":{"735":{"tf":1.4142135623730951},"97":{"tf":1.0}},"m":{"a":{"df":1,"docs":{"855":{"tf":1.0}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"417":{"tf":1.0},"428":{"tf":1.0}}},"df":0,"docs":{}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"516":{"tf":1.0},"517":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"l":{"df":12,"docs":{"322":{"tf":1.0},"343":{"tf":1.4142135623730951},"345":{"tf":1.7320508075688772},"60":{"tf":1.4142135623730951},"633":{"tf":1.0},"644":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"73":{"tf":1.0},"75":{"tf":1.0},"77":{"tf":1.4142135623730951},"786":{"tf":1.0}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"879":{"tf":2.0},"885":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"u":{"df":0,"docs":{},"r":{"df":43,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.4142135623730951},"104":{"tf":1.0},"105":{"tf":1.0},"164":{"tf":1.0},"171":{"tf":2.449489742783178},"175":{"tf":1.4142135623730951},"340":{"tf":1.0},"341":{"tf":3.7416573867739413},"343":{"tf":1.0},"346":{"tf":2.0},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":2.0},"352":{"tf":1.0},"404":{"tf":1.0},"455":{"tf":2.6457513110645907},"459":{"tf":1.0},"513":{"tf":1.0},"521":{"tf":1.0},"530":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"588":{"tf":1.4142135623730951},"629":{"tf":1.0},"632":{"tf":2.23606797749979},"634":{"tf":1.0},"640":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.4142135623730951},"644":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":2.449489742783178},"736":{"tf":1.0},"93":{"tf":2.23606797749979},"94":{"tf":2.0},"95":{"tf":1.4142135623730951},"96":{"tf":1.0},"97":{"tf":2.0},"98":{"tf":1.0},"99":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}}}},"df":36,"docs":{"166":{"tf":1.0},"169":{"tf":1.4142135623730951},"170":{"tf":1.4142135623730951},"171":{"tf":2.449489742783178},"172":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.0},"205":{"tf":2.449489742783178},"340":{"tf":1.0},"346":{"tf":1.0},"349":{"tf":1.0},"455":{"tf":1.0},"49":{"tf":1.0},"514":{"tf":1.7320508075688772},"516":{"tf":1.7320508075688772},"521":{"tf":3.3166247903554},"526":{"tf":2.449489742783178},"531":{"tf":1.0},"532":{"tf":1.4142135623730951},"537":{"tf":2.0},"539":{"tf":1.0},"545":{"tf":1.0},"550":{"tf":1.0},"553":{"tf":1.0},"555":{"tf":1.0},"567":{"tf":1.4142135623730951},"586":{"tf":1.4142135623730951},"588":{"tf":1.7320508075688772},"589":{"tf":1.0},"63":{"tf":1.4142135623730951},"65":{"tf":1.0},"73":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.4142135623730951},"895":{"tf":1.0},"95":{"tf":2.23606797749979}},"e":{"d":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"696":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}}}}},"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"555":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"341":{"tf":1.0}}},"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}},"df":12,"docs":{"515":{"tf":1.0},"516":{"tf":1.0},"872":{"tf":1.7320508075688772},"874":{"tf":1.0},"875":{"tf":1.7320508075688772},"878":{"tf":1.7320508075688772},"879":{"tf":6.4031242374328485},"880":{"tf":2.449489742783178},"881":{"tf":2.23606797749979},"885":{"tf":1.4142135623730951},"889":{"tf":1.0},"890":{"tf":1.0}},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"879":{"tf":1.0}}},"df":0,"docs":{}}}}}}}},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"564":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":6,"docs":{"486":{"tf":1.0},"563":{"tf":1.0},"773":{"tf":1.0},"777":{"tf":1.0},"928":{"tf":1.0},"973":{"tf":1.0}}}}}}},"df":19,"docs":{"108":{"tf":1.0},"11":{"tf":1.0},"141":{"tf":1.0},"308":{"tf":1.0},"356":{"tf":1.0},"412":{"tf":1.0},"51":{"tf":1.0},"522":{"tf":1.7320508075688772},"537":{"tf":1.0},"55":{"tf":1.0},"565":{"tf":1.0},"573":{"tf":1.0},"575":{"tf":1.0},"776":{"tf":1.0},"866":{"tf":1.0},"876":{"tf":1.0},"912":{"tf":1.0},"962":{"tf":1.0},"990":{"tf":1.0}}},"df":1,"docs":{"666":{"tf":1.0}}}}}}},"k":{"df":1,"docs":{"244":{"tf":1.0}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"761":{"tf":1.0}}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":34,"docs":{"111":{"tf":1.7320508075688772},"122":{"tf":1.0},"123":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"204":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"272":{"tf":1.0},"276":{"tf":1.0},"281":{"tf":1.0},"33":{"tf":1.0},"333":{"tf":1.0},"35":{"tf":1.0},"39":{"tf":1.0},"390":{"tf":1.0},"397":{"tf":1.0},"499":{"tf":1.0},"515":{"tf":1.0},"520":{"tf":1.0},"526":{"tf":1.0},"54":{"tf":1.0},"583":{"tf":1.0},"659":{"tf":1.0},"697":{"tf":1.0},"735":{"tf":1.0},"831":{"tf":1.0},"855":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.7320508075688772},"913":{"tf":1.0},"932":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"25":{"tf":1.0},"371":{"tf":1.0},"415":{"tf":1.0},"502":{"tf":1.0},"663":{"tf":1.0},"736":{"tf":1.0},"761":{"tf":1.0}}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":16,"docs":{"121":{"tf":1.0},"190":{"tf":1.0},"207":{"tf":2.0},"208":{"tf":1.4142135623730951},"269":{"tf":1.0},"291":{"tf":1.0},"358":{"tf":1.0},"375":{"tf":1.0},"438":{"tf":1.0},"494":{"tf":1.0},"576":{"tf":2.0},"617":{"tf":1.0},"648":{"tf":1.0},"721":{"tf":1.0},"754":{"tf":1.0},"788":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"22":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"650":{"tf":1.0},"653":{"tf":1.0},"659":{"tf":1.0},"673":{"tf":1.0},"74":{"tf":1.0},"878":{"tf":1.0},"934":{"tf":1.0}}}},"i":{"c":{"df":2,"docs":{"761":{"tf":1.0},"777":{"tf":1.0}}},"df":13,"docs":{"177":{"tf":1.0},"253":{"tf":1.0},"272":{"tf":1.0},"371":{"tf":1.0},"485":{"tf":1.0},"573":{"tf":1.0},"696":{"tf":1.0},"712":{"tf":1.0},"729":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.4142135623730951},"763":{"tf":1.4142135623730951},"777":{"tf":1.0}},"f":{"df":2,"docs":{"658":{"tf":1.0},"829":{"tf":1.0}},"i":{"df":11,"docs":{"145":{"tf":1.0},"24":{"tf":1.0},"293":{"tf":1.0},"375":{"tf":1.0},"622":{"tf":1.0},"720":{"tf":1.0},"722":{"tf":1.0},"83":{"tf":1.4142135623730951},"885":{"tf":1.0},"975":{"tf":1.0},"983":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"571":{"tf":1.4142135623730951},"935":{"tf":1.0}},"t":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"375":{"tf":1.0}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"386":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"l":{"df":40,"docs":{"180":{"tf":1.0},"198":{"tf":1.4142135623730951},"203":{"tf":1.4142135623730951},"204":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"218":{"tf":1.0},"222":{"tf":1.0},"231":{"tf":1.0},"24":{"tf":1.4142135623730951},"272":{"tf":1.0},"346":{"tf":1.0},"368":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.4142135623730951},"469":{"tf":1.4142135623730951},"48":{"tf":1.0},"517":{"tf":1.0},"519":{"tf":1.0},"522":{"tf":1.0},"571":{"tf":1.0},"599":{"tf":1.4142135623730951},"60":{"tf":1.0},"600":{"tf":2.0},"602":{"tf":2.23606797749979},"603":{"tf":1.0},"605":{"tf":1.7320508075688772},"606":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"668":{"tf":1.0},"673":{"tf":1.0},"692":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"762":{"tf":1.4142135623730951},"777":{"tf":1.4142135623730951},"796":{"tf":1.0},"799":{"tf":2.0},"843":{"tf":1.0}},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"7":{"tf":1.0}}}}}}}}},"t":{"df":0,"docs":{},"e":{"df":2,"docs":{"615":{"tf":1.0},"912":{"tf":1.0}}},"u":{"a":{"df":0,"docs":{},"t":{"df":16,"docs":{"207":{"tf":1.0},"249":{"tf":1.0},"267":{"tf":1.0},"348":{"tf":1.0},"375":{"tf":1.0},"497":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"747":{"tf":1.4142135623730951},"761":{"tf":1.0},"762":{"tf":1.0},"763":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"832":{"tf":1.7320508075688772}}}},"df":0,"docs":{}}},"x":{"df":3,"docs":{"198":{"tf":1.0},"199":{"tf":1.0},"778":{"tf":1.0}}},"z":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"469":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":39,"docs":{"204":{"tf":1.0},"207":{"tf":1.4142135623730951},"229":{"tf":1.0},"235":{"tf":1.4142135623730951},"239":{"tf":1.0},"253":{"tf":1.0},"28":{"tf":1.4142135623730951},"30":{"tf":1.0},"388":{"tf":1.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.23606797749979},"404":{"tf":1.7320508075688772},"407":{"tf":1.4142135623730951},"412":{"tf":1.0},"418":{"tf":1.0},"436":{"tf":1.0},"444":{"tf":1.0},"485":{"tf":1.0},"51":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":2.0},"522":{"tf":1.4142135623730951},"564":{"tf":1.0},"60":{"tf":1.0},"710":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":4.898979485566356},"75":{"tf":1.0},"761":{"tf":1.4142135623730951},"762":{"tf":1.7320508075688772},"763":{"tf":2.0},"813":{"tf":1.0},"858":{"tf":1.0},"863":{"tf":1.0},"880":{"tf":1.4142135623730951},"885":{"tf":3.0},"990":{"tf":1.4142135623730951},"996":{"tf":1.0}}}}},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":7,"docs":{"286":{"tf":1.0},"644":{"tf":1.0},"711":{"tf":1.0},"723":{"tf":2.23606797749979},"724":{"tf":1.4142135623730951},"815":{"tf":1.0},"817":{"tf":1.0}},"e":{"df":1,"docs":{"723":{"tf":1.0}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"761":{"tf":2.0}}}}},"df":0,"docs":{}}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"b":{"df":0,"docs":{},"l":{"df":21,"docs":{"567":{"tf":1.0},"569":{"tf":1.0},"863":{"tf":1.0},"908":{"tf":2.23606797749979},"909":{"tf":1.4142135623730951},"910":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.7320508075688772},"914":{"tf":1.0},"915":{"tf":1.0},"916":{"tf":1.4142135623730951},"917":{"tf":1.4142135623730951},"918":{"tf":1.0},"919":{"tf":1.7320508075688772},"920":{"tf":1.4142135623730951},"921":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"924":{"tf":1.0},"925":{"tf":1.0}}}},"df":0,"docs":{}},"df":10,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"453":{"tf":1.0},"563":{"tf":1.4142135623730951},"564":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"569":{"tf":1.0},"573":{"tf":4.47213595499958},"644":{"tf":1.0},"863":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"e":{"df":3,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"574":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":2,"docs":{"144":{"tf":1.0},"776":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":7,"docs":{"456":{"tf":1.0},"515":{"tf":1.0},"622":{"tf":1.0},"687":{"tf":1.0},"739":{"tf":1.0},"752":{"tf":1.0},"777":{"tf":1.0}}}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":2,"docs":{"749":{"tf":1.0},"751":{"tf":1.0}}}},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"348":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"349":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":26,"docs":{"198":{"tf":1.7320508075688772},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"214":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.7320508075688772},"296":{"tf":1.4142135623730951},"300":{"tf":1.0},"303":{"tf":1.0},"308":{"tf":1.0},"310":{"tf":1.0},"322":{"tf":2.0},"323":{"tf":1.7320508075688772},"335":{"tf":1.7320508075688772},"338":{"tf":1.7320508075688772},"339":{"tf":1.0},"342":{"tf":1.4142135623730951},"343":{"tf":1.4142135623730951},"346":{"tf":2.0},"347":{"tf":1.4142135623730951},"348":{"tf":3.4641016151377544},"349":{"tf":4.242640687119285},"350":{"tf":1.7320508075688772},"351":{"tf":1.7320508075688772},"928":{"tf":1.0}}},"w":{"df":4,"docs":{"274":{"tf":1.0},"711":{"tf":1.0},"729":{"tf":1.0},"744":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"739":{"tf":1.4142135623730951},"765":{"tf":1.0},"858":{"tf":1.0},"990":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"660":{"tf":1.0},"751":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":16,"docs":{"182":{"tf":1.0},"183":{"tf":1.4142135623730951},"184":{"tf":1.7320508075688772},"186":{"tf":1.7320508075688772},"199":{"tf":1.0},"201":{"tf":1.0},"253":{"tf":1.0},"436":{"tf":1.0},"486":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"554":{"tf":1.0},"571":{"tf":1.0},"710":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":6,"docs":{"208":{"tf":1.0},"46":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"817":{"tf":1.0},"885":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"t":{"df":24,"docs":{"39":{"tf":1.0},"44":{"tf":1.0},"697":{"tf":1.0},"78":{"tf":2.0},"874":{"tf":1.0},"942":{"tf":1.0},"956":{"tf":1.0},"957":{"tf":2.23606797749979},"958":{"tf":1.4142135623730951},"959":{"tf":2.0},"960":{"tf":1.0},"961":{"tf":2.8284271247461903},"962":{"tf":2.0},"963":{"tf":1.0},"964":{"tf":1.4142135623730951},"965":{"tf":1.4142135623730951},"966":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.4142135623730951},"969":{"tf":1.4142135623730951},"970":{"tf":1.0},"971":{"tf":2.0},"972":{"tf":2.0},"973":{"tf":2.23606797749979}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":3,"docs":{"363":{"tf":1.0},"644":{"tf":1.0},"73":{"tf":1.0}}}}}}},"n":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":5,"docs":{"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"k":{"df":4,"docs":{"322":{"tf":1.0},"340":{"tf":1.0},"347":{"tf":1.0},"364":{"tf":1.7320508075688772}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"1004":{"tf":1.0}}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"p":{"df":3,"docs":{"6":{"tf":1.0},"668":{"tf":1.4142135623730951},"814":{"tf":1.7320508075688772}},"e":{"df":3,"docs":{"127":{"tf":1.0},"184":{"tf":1.0},"187":{"tf":1.4142135623730951}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"333":{"tf":1.0},"933":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"w":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"d":{"df":0,"docs":{},"g":{"df":2,"docs":{"697":{"tf":1.0},"699":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"o":{"c":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"201":{"tf":1.4142135623730951},"219":{"tf":1.0},"230":{"tf":1.0},"844":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"855":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"df":4,"docs":{"209":{"tf":1.4142135623730951},"210":{"tf":1.0},"514":{"tf":1.0},"895":{"tf":2.23606797749979}}}},"df":0,"docs":{}}}},"l":{"d":{"df":17,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":2.23606797749979},"205":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"213":{"tf":1.0},"742":{"tf":1.4142135623730951},"743":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":1.0},"748":{"tf":1.7320508075688772},"749":{"tf":1.7320508075688772},"751":{"tf":2.0},"776":{"tf":1.0},"778":{"tf":1.0},"912":{"tf":1.0},"944":{"tf":1.4142135623730951}}},"df":0,"docs":{},"e":{"df":3,"docs":{"221":{"tf":1.0},"46":{"tf":1.0},"564":{"tf":1.0}}},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"201":{"tf":1.0},"47":{"tf":1.0},"51":{"tf":1.0}}}}},"d":{"df":2,"docs":{"961":{"tf":1.0},"971":{"tf":1.0}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"871":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"444":{"tf":1.4142135623730951}}}}}},"u":{"df":0,"docs":{},"t":{"df":50,"docs":{"1004":{"tf":1.0},"1006":{"tf":1.0},"147":{"tf":1.0},"149":{"tf":1.0},"161":{"tf":1.0},"200":{"tf":2.6457513110645907},"207":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"254":{"tf":1.0},"310":{"tf":1.0},"402":{"tf":1.0},"515":{"tf":1.0},"518":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.4142135623730951},"54":{"tf":1.0},"573":{"tf":1.7320508075688772},"575":{"tf":1.0},"583":{"tf":1.4142135623730951},"68":{"tf":1.4142135623730951},"721":{"tf":1.0},"724":{"tf":1.0},"744":{"tf":2.23606797749979},"75":{"tf":1.0},"754":{"tf":1.0},"80":{"tf":1.0},"809":{"tf":1.0},"81":{"tf":1.0},"811":{"tf":2.6457513110645907},"813":{"tf":1.4142135623730951},"826":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"84":{"tf":1.4142135623730951},"843":{"tf":1.4142135623730951},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"85":{"tf":1.0},"874":{"tf":1.0},"88":{"tf":1.0},"891":{"tf":1.0},"896":{"tf":1.4142135623730951},"898":{"tf":1.0},"902":{"tf":1.0},"908":{"tf":1.0},"913":{"tf":2.0},"919":{"tf":1.0},"934":{"tf":1.4142135623730951},"956":{"tf":1.0}}}},"v":{"df":15,"docs":{"152":{"tf":1.0},"155":{"tf":1.0},"163":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"450":{"tf":1.4142135623730951},"452":{"tf":1.0},"497":{"tf":1.0},"512":{"tf":1.0},"528":{"tf":1.0},"573":{"tf":1.0},"629":{"tf":1.0},"757":{"tf":1.0},"762":{"tf":1.0},"77":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"x":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"526":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"0":{"df":1,"docs":{"208":{"tf":1.0}}},"1":{"df":1,"docs":{"208":{"tf":1.0}}},"2":{"df":1,"docs":{"208":{"tf":1.0}}},"4":{"9":{"df":1,"docs":{"208":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"208":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"121":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":8,"docs":{"273":{"tf":1.4142135623730951},"453":{"tf":1.4142135623730951},"469":{"tf":1.0},"619":{"tf":1.0},"701":{"tf":1.0},"858":{"tf":1.0},"881":{"tf":1.0},"894":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":11,"docs":{"151":{"tf":1.0},"184":{"tf":1.0},"193":{"tf":1.0},"390":{"tf":1.0},"441":{"tf":1.0},"512":{"tf":1.0},"567":{"tf":1.0},"697":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0},"870":{"tf":1.0}}},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"208":{"tf":1.7320508075688772}}}}},"w":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.0}}}},"df":0,"docs":{}}}}},"o":{"df":0,"docs":{},"n":{"df":6,"docs":{"204":{"tf":1.0},"221":{"tf":1.4142135623730951},"721":{"tf":1.4142135623730951},"837":{"tf":1.0},"928":{"tf":1.0},"984":{"tf":1.0}}}},"p":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"46":{"tf":1.0},"959":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"t":{"df":7,"docs":{"234":{"tf":1.4142135623730951},"347":{"tf":1.4142135623730951},"524":{"tf":1.4142135623730951},"525":{"tf":2.0},"551":{"tf":1.0},"633":{"tf":1.0},"874":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"234":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"711":{"tf":1.0},"712":{"tf":1.0},"850":{"tf":1.0},"852":{"tf":1.0}}},"df":0,"docs":{}},"r":{"a":{"b":{"df":0,"docs":{},"h":{"df":1,"docs":{"38":{"tf":1.0}}}},"df":0,"docs":{}},"c":{"df":82,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"24":{"tf":1.4142135623730951},"247":{"tf":1.0},"263":{"tf":1.0},"267":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"30":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"366":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.4142135623730951},"602":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"696":{"tf":2.449489742783178},"697":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"740":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"8":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"83":{"tf":1.4142135623730951},"84":{"tf":1.7320508075688772},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"895":{"tf":1.4142135623730951},"908":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0},"93":{"tf":1.0},"932":{"tf":2.0},"938":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":3,"docs":{"3":{"tf":1.0},"602":{"tf":1.0},"697":{"tf":1.0}}}}}}}}}},"p":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"a":{"c":{"df":0,"docs":{},"e":{"df":8,"docs":{"196":{"tf":1.0},"515":{"tf":1.0},"627":{"tf":1.0},"632":{"tf":1.4142135623730951},"638":{"tf":1.0},"648":{"tf":1.0},"71":{"tf":1.0},"831":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":5,"docs":{"411":{"tf":1.0},"420":{"tf":1.0},"429":{"tf":1.0},"863":{"tf":1.0},"913":{"tf":1.0}}},"n":{"df":6,"docs":{"200":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":2.23606797749979},"205":{"tf":2.23606797749979},"208":{"tf":1.0},"843":{"tf":1.0}}},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"843":{"tf":1.0}}}},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"83":{"tf":1.0},"84":{"tf":2.0},"85":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"198":{"tf":1.0},"435":{"tf":1.0}}}},"c":{"_":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"390":{"tf":1.0},"520":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":2,"docs":{"390":{"tf":1.0},"520":{"tf":2.0}}}}}}},"df":9,"docs":{"436":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"606":{"tf":1.0},"711":{"tf":1.7320508075688772},"841":{"tf":1.0},"847":{"tf":1.7320508075688772},"848":{"tf":1.0},"983":{"tf":1.0}},"e":{"df":1,"docs":{"711":{"tf":1.0}}},"i":{"a":{"df":0,"docs":{},"l":{"df":8,"docs":{"154":{"tf":1.0},"249":{"tf":1.4142135623730951},"272":{"tf":1.0},"346":{"tf":1.0},"522":{"tf":1.4142135623730951},"780":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":3,"docs":{"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"216":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"df":73,"docs":{"1014":{"tf":1.0},"126":{"tf":1.0},"164":{"tf":1.0},"165":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"18":{"tf":1.0},"195":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.0},"209":{"tf":1.0},"210":{"tf":1.0},"221":{"tf":1.4142135623730951},"224":{"tf":1.0},"249":{"tf":2.449489742783178},"251":{"tf":1.0},"252":{"tf":1.4142135623730951},"254":{"tf":1.0},"255":{"tf":1.0},"257":{"tf":1.0},"262":{"tf":1.0},"3":{"tf":1.0},"315":{"tf":1.0},"322":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"337":{"tf":1.0},"340":{"tf":1.0},"341":{"tf":1.4142135623730951},"343":{"tf":1.0},"357":{"tf":1.0},"359":{"tf":1.0},"371":{"tf":1.0},"390":{"tf":1.0},"398":{"tf":1.0},"416":{"tf":1.0},"429":{"tf":1.0},"46":{"tf":1.0},"483":{"tf":1.4142135623730951},"496":{"tf":1.0},"497":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"505":{"tf":1.0},"507":{"tf":1.0},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"542":{"tf":1.0},"553":{"tf":1.4142135623730951},"568":{"tf":1.0},"576":{"tf":1.0},"586":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"614":{"tf":1.0},"627":{"tf":1.0},"651":{"tf":1.4142135623730951},"665":{"tf":1.0},"666":{"tf":1.0},"697":{"tf":1.4142135623730951},"727":{"tf":1.0},"759":{"tf":1.4142135623730951},"762":{"tf":1.4142135623730951},"818":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0},"85":{"tf":1.7320508075688772},"972":{"tf":1.0},"991":{"tf":1.0}},"i":{"df":32,"docs":{"170":{"tf":1.0},"171":{"tf":1.0},"180":{"tf":1.4142135623730951},"204":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":2.6457513110645907},"212":{"tf":1.0},"24":{"tf":1.0},"251":{"tf":1.0},"345":{"tf":1.0},"350":{"tf":1.0},"470":{"tf":1.0},"5":{"tf":1.4142135623730951},"52":{"tf":1.0},"553":{"tf":1.0},"560":{"tf":1.0},"6":{"tf":1.7320508075688772},"602":{"tf":2.8284271247461903},"651":{"tf":1.0},"666":{"tf":1.0},"668":{"tf":1.0},"670":{"tf":1.7320508075688772},"673":{"tf":1.0},"680":{"tf":1.0},"683":{"tf":1.0},"698":{"tf":1.4142135623730951},"761":{"tf":1.4142135623730951},"78":{"tf":1.4142135623730951},"814":{"tf":1.0},"831":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}}},"y":{"/":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"207":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"k":{"df":1,"docs":{"711":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"470":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"d":{"df":3,"docs":{"54":{"tf":1.0},"553":{"tf":1.0},"739":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"n":{"d":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"205":{"tf":1.0}}}},"df":0,"docs":{}},"df":6,"docs":{"184":{"tf":1.4142135623730951},"267":{"tf":1.4142135623730951},"273":{"tf":1.0},"375":{"tf":1.0},"720":{"tf":1.0},"81":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"184":{"tf":2.23606797749979}}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"615":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":3,"docs":{"257":{"tf":1.0},"507":{"tf":1.0},"571":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":9,"docs":{"203":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.4142135623730951},"217":{"tf":1.0},"281":{"tf":1.0},"374":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"932":{"tf":1.0}},"e":{"df":1,"docs":{"28":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"537":{"tf":1.0}}},"df":2,"docs":{"537":{"tf":1.0},"869":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"240":{"tf":1.0}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"j":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"121":{"tf":1.0}}}},"df":0,"docs":{}}},"df":1,"docs":{"111":{"tf":1.0}}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"777":{"tf":1.0}}}}}}},"r":{"df":3,"docs":{"244":{"tf":1.0},"347":{"tf":1.0},"364":{"tf":1.4142135623730951}}},"s":{"5":{"8":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":1,"docs":{"520":{"tf":1.0}}}}}}}}},"df":1,"docs":{"520":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"t":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":7,"docs":{"267":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.0},"470":{"tf":1.4142135623730951},"473":{"tf":1.0},"564":{"tf":1.0},"687":{"tf":1.0}}}},"l":{"df":5,"docs":{"204":{"tf":1.0},"249":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"72":{"tf":1.0}},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"234":{"tf":1.0},"417":{"tf":1.0},"426":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"k":{"df":9,"docs":{"254":{"tf":1.7320508075688772},"38":{"tf":1.0},"39":{"tf":1.0},"40":{"tf":1.0},"46":{"tf":1.0},"50":{"tf":1.0},"54":{"tf":1.0},"575":{"tf":1.0},"732":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":5,"docs":{"201":{"tf":1.0},"309":{"tf":1.0},"376":{"tf":1.0},"815":{"tf":1.7320508075688772},"906":{"tf":1.0}}}},"k":{"df":0,"docs":{},"e":{"df":37,"docs":{"1002":{"tf":1.0},"1003":{"tf":1.0},"1004":{"tf":1.0},"231":{"tf":2.23606797749979},"244":{"tf":1.0},"370":{"tf":1.4142135623730951},"371":{"tf":1.0},"372":{"tf":1.7320508075688772},"373":{"tf":2.23606797749979},"375":{"tf":4.0},"376":{"tf":1.4142135623730951},"377":{"tf":1.0},"383":{"tf":1.0},"384":{"tf":1.4142135623730951},"385":{"tf":1.0},"563":{"tf":1.7320508075688772},"564":{"tf":2.0},"565":{"tf":2.6457513110645907},"567":{"tf":2.23606797749979},"568":{"tf":2.0},"569":{"tf":1.7320508075688772},"570":{"tf":1.0},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"574":{"tf":1.4142135623730951},"575":{"tf":1.7320508075688772},"576":{"tf":1.7320508075688772},"577":{"tf":1.7320508075688772},"797":{"tf":1.4142135623730951},"927":{"tf":1.4142135623730951},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":2.0},"932":{"tf":3.4641016151377544},"933":{"tf":1.7320508075688772},"934":{"tf":2.0},"936":{"tf":1.0}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":127,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1005":{"tf":1.7320508075688772},"106":{"tf":1.0},"109":{"tf":1.4142135623730951},"122":{"tf":1.0},"125":{"tf":1.4142135623730951},"136":{"tf":1.0},"139":{"tf":1.7320508075688772},"150":{"tf":1.0},"153":{"tf":1.4142135623730951},"164":{"tf":1.0},"167":{"tf":1.4142135623730951},"17":{"tf":1.0},"182":{"tf":1.0},"185":{"tf":1.7320508075688772},"195":{"tf":1.0},"20":{"tf":1.4142135623730951},"201":{"tf":2.0},"209":{"tf":1.0},"215":{"tf":1.0},"219":{"tf":1.7320508075688772},"229":{"tf":1.0},"233":{"tf":1.4142135623730951},"247":{"tf":1.0},"250":{"tf":1.4142135623730951},"263":{"tf":1.0},"266":{"tf":1.4142135623730951},"268":{"tf":1.0},"271":{"tf":1.7320508075688772},"279":{"tf":1.0},"282":{"tf":1.4142135623730951},"294":{"tf":1.0},"298":{"tf":1.4142135623730951},"311":{"tf":1.0},"314":{"tf":1.4142135623730951},"322":{"tf":1.0},"327":{"tf":1.4142135623730951},"366":{"tf":1.0},"369":{"tf":1.4142135623730951},"38":{"tf":1.0},"386":{"tf":1.0},"389":{"tf":1.4142135623730951},"4":{"tf":1.4142135623730951},"400":{"tf":1.0},"403":{"tf":1.4142135623730951},"410":{"tf":1.0},"414":{"tf":1.4142135623730951},"418":{"tf":1.4142135623730951},"42":{"tf":1.4142135623730951},"430":{"tf":1.0},"433":{"tf":1.4142135623730951},"451":{"tf":1.0},"454":{"tf":1.4142135623730951},"465":{"tf":1.0},"468":{"tf":1.4142135623730951},"481":{"tf":1.0},"484":{"tf":1.4142135623730951},"495":{"tf":1.0},"498":{"tf":1.4142135623730951},"513":{"tf":1.0},"518":{"tf":1.4142135623730951},"535":{"tf":1.0},"538":{"tf":1.4142135623730951},"549":{"tf":1.0},"552":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"566":{"tf":1.4142135623730951},"584":{"tf":1.0},"587":{"tf":1.4142135623730951},"59":{"tf":1.4142135623730951},"598":{"tf":1.0},"601":{"tf":1.4142135623730951},"613":{"tf":1.0},"616":{"tf":1.4142135623730951},"627":{"tf":1.0},"630":{"tf":1.4142135623730951},"649":{"tf":1.0},"652":{"tf":1.4142135623730951},"664":{"tf":1.0},"667":{"tf":1.4142135623730951},"678":{"tf":1.0},"681":{"tf":1.4142135623730951},"692":{"tf":1.0},"695":{"tf":1.4142135623730951},"709":{"tf":1.0},"712":{"tf":1.4142135623730951},"730":{"tf":1.0},"733":{"tf":1.7320508075688772},"741":{"tf":1.0},"745":{"tf":1.7320508075688772},"757":{"tf":1.0},"760":{"tf":1.4142135623730951},"771":{"tf":1.0},"774":{"tf":1.7320508075688772},"782":{"tf":1.0},"785":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"798":{"tf":1.7320508075688772},"808":{"tf":1.0},"812":{"tf":1.4142135623730951},"82":{"tf":1.4142135623730951},"827":{"tf":1.0},"830":{"tf":1.4142135623730951},"841":{"tf":1.0},"844":{"tf":1.4142135623730951},"871":{"tf":1.0},"877":{"tf":1.4142135623730951},"891":{"tf":1.0},"897":{"tf":1.4142135623730951},"908":{"tf":1.0},"914":{"tf":1.4142135623730951},"926":{"tf":1.0},"928":{"tf":1.0},"929":{"tf":1.7320508075688772},"93":{"tf":1.0},"940":{"tf":1.0},"943":{"tf":1.7320508075688772},"957":{"tf":1.0},"96":{"tf":1.4142135623730951},"960":{"tf":1.7320508075688772},"974":{"tf":1.0},"977":{"tf":1.4142135623730951},"988":{"tf":1.0},"991":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}},"r":{"df":3,"docs":{"573":{"tf":2.0},"929":{"tf":1.0},"932":{"tf":1.4142135623730951}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"e":{"df":14,"docs":{"1002":{"tf":2.23606797749979},"1003":{"tf":1.7320508075688772},"1004":{"tf":1.0},"1005":{"tf":1.0},"1006":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.0}}},"l":{"df":2,"docs":{"118":{"tf":1.0},"438":{"tf":1.0}}}},"n":{"d":{"a":{"df":0,"docs":{},"r":{"d":{"df":17,"docs":{"12":{"tf":1.0},"147":{"tf":1.0},"220":{"tf":1.0},"225":{"tf":1.0},"24":{"tf":1.0},"3":{"tf":1.4142135623730951},"331":{"tf":1.0},"333":{"tf":1.0},"378":{"tf":1.0},"415":{"tf":1.0},"418":{"tf":1.0},"532":{"tf":1.0},"639":{"tf":1.0},"651":{"tf":1.4142135623730951},"883":{"tf":1.0},"931":{"tf":1.0},"95":{"tf":2.0}}},"df":0,"docs":{}}},"df":3,"docs":{"414":{"tf":1.0},"931":{"tf":1.0},"939":{"tf":1.0}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"269":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":2,"docs":{"879":{"tf":1.4142135623730951},"885":{"tf":1.0}}}}}}}}},"df":102,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"126":{"tf":1.7320508075688772},"132":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.4142135623730951},"182":{"tf":1.0},"195":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"215":{"tf":1.0},"221":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"249":{"tf":1.0},"263":{"tf":1.0},"265":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"303":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"346":{"tf":1.4142135623730951},"349":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.0},"430":{"tf":1.0},"440":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":1.4142135623730951},"451":{"tf":1.0},"465":{"tf":1.0},"47":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"495":{"tf":1.0},"500":{"tf":1.0},"513":{"tf":1.0},"52":{"tf":1.0},"520":{"tf":1.0},"523":{"tf":1.0},"535":{"tf":1.0},"54":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"567":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"605":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"63":{"tf":1.7320508075688772},"633":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"73":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":2.23606797749979},"741":{"tf":1.0},"757":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":1.4142135623730951},"857":{"tf":1.0},"863":{"tf":1.0},"871":{"tf":1.0},"875":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":1.7320508075688772},"889":{"tf":1.0},"891":{"tf":1.0},"902":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0},"992":{"tf":1.0}},"u":{"df":0,"docs":{},"p":{"df":3,"docs":{"345":{"tf":1.0},"553":{"tf":1.0},"809":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"565":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"m":{"df":1,"docs":{"108":{"tf":1.0}}}}},"df":0,"docs":{}}},"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":4,"docs":{"391":{"tf":1.0},"393":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.4142135623730951}}}}}}},"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"126":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":97,"docs":{"1000":{"tf":1.4142135623730951},"1001":{"tf":1.4142135623730951},"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"112":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":2.8284271247461903},"151":{"tf":3.1622776601683795},"152":{"tf":1.7320508075688772},"154":{"tf":2.23606797749979},"155":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"194":{"tf":1.0},"30":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0},"362":{"tf":1.0},"368":{"tf":2.449489742783178},"371":{"tf":1.4142135623730951},"375":{"tf":2.0},"376":{"tf":1.0},"386":{"tf":1.0},"387":{"tf":1.4142135623730951},"388":{"tf":1.0},"39":{"tf":1.4142135623730951},"390":{"tf":2.23606797749979},"402":{"tf":1.4142135623730951},"418":{"tf":2.0},"420":{"tf":1.0},"422":{"tf":1.4142135623730951},"44":{"tf":2.449489742783178},"440":{"tf":1.0},"45":{"tf":1.7320508075688772},"46":{"tf":3.7416573867739413},"466":{"tf":1.0},"47":{"tf":1.0},"479":{"tf":1.0},"49":{"tf":2.0},"500":{"tf":1.0},"501":{"tf":1.0},"51":{"tf":1.0},"514":{"tf":1.0},"54":{"tf":1.0},"567":{"tf":1.0},"57":{"tf":1.0},"6":{"tf":1.0},"633":{"tf":1.0},"634":{"tf":1.0},"735":{"tf":1.0},"770":{"tf":1.0},"773":{"tf":1.4142135623730951},"786":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0},"818":{"tf":1.0},"847":{"tf":1.0},"871":{"tf":2.23606797749979},"872":{"tf":1.7320508075688772},"873":{"tf":1.0},"874":{"tf":1.4142135623730951},"875":{"tf":1.7320508075688772},"876":{"tf":1.0},"877":{"tf":1.0},"878":{"tf":1.7320508075688772},"879":{"tf":2.23606797749979},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"882":{"tf":1.0},"883":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":4.0},"886":{"tf":1.4142135623730951},"887":{"tf":1.0},"888":{"tf":1.0},"889":{"tf":1.0},"890":{"tf":1.0},"919":{"tf":1.0},"935":{"tf":1.0},"988":{"tf":3.1622776601683795},"989":{"tf":2.0},"990":{"tf":2.6457513110645907},"991":{"tf":1.7320508075688772},"992":{"tf":1.7320508075688772},"993":{"tf":1.4142135623730951},"994":{"tf":1.7320508075688772},"995":{"tf":1.4142135623730951},"996":{"tf":2.23606797749979},"997":{"tf":1.4142135623730951},"998":{"tf":1.4142135623730951},"999":{"tf":1.4142135623730951}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"885":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"885":{"tf":2.6457513110645907}}}}}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":7,"docs":{"450":{"tf":1.0},"58":{"tf":1.0},"71":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":1.0},"786":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"721":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"s":{"df":1,"docs":{"885":{"tf":1.4142135623730951}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":14,"docs":{"386":{"tf":2.0},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.0},"390":{"tf":1.4142135623730951},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"v":{"0":{"df":1,"docs":{"388":{"tf":1.4142135623730951}}},"1":{"df":2,"docs":{"387":{"tf":1.0},"388":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"i":{"c":{"df":5,"docs":{"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"146":{"tf":1.0},"783":{"tf":1.0},"786":{"tf":1.0}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":3,"docs":{"134":{"tf":1.0},"571":{"tf":1.0},"724":{"tf":1.0}}}}},"u":{"df":10,"docs":{"126":{"tf":1.4142135623730951},"127":{"tf":1.4142135623730951},"134":{"tf":1.0},"203":{"tf":1.0},"294":{"tf":1.0},"300":{"tf":1.4142135623730951},"735":{"tf":1.0},"816":{"tf":1.0},"909":{"tf":1.0},"913":{"tf":1.0}}}},"y":{"df":3,"docs":{"204":{"tf":1.0},"375":{"tf":1.0},"748":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"267":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"841":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":5,"docs":{"742":{"tf":1.0},"744":{"tf":1.0},"748":{"tf":1.4142135623730951},"749":{"tf":1.4142135623730951},"751":{"tf":1.0}}}},"m":{"df":1,"docs":{"422":{"tf":1.0}}},"p":{"df":27,"docs":{"1010":{"tf":1.0},"130":{"tf":1.0},"171":{"tf":1.7320508075688772},"26":{"tf":1.0},"274":{"tf":1.0},"339":{"tf":1.0},"347":{"tf":1.0},"385":{"tf":1.0},"417":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":2.449489742783178},"483":{"tf":1.0},"485":{"tf":1.0},"491":{"tf":1.0},"519":{"tf":1.0},"524":{"tf":1.4142135623730951},"525":{"tf":1.0},"564":{"tf":1.0},"60":{"tf":1.0},"643":{"tf":1.0},"694":{"tf":1.0},"799":{"tf":1.0},"848":{"tf":1.0},"878":{"tf":1.0},"928":{"tf":1.0},"932":{"tf":1.7320508075688772},"983":{"tf":1.0}}},"w":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"563":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"723":{"tf":1.7320508075688772}},"f":{"df":3,"docs":{"718":{"tf":1.4142135623730951},"723":{"tf":1.0},"724":{"tf":1.0}}}},"l":{"df":0,"docs":{},"l":{"df":50,"docs":{"112":{"tf":1.0},"126":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"155":{"tf":1.0},"170":{"tf":1.0},"178":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"290":{"tf":1.0},"296":{"tf":1.0},"315":{"tf":1.4142135623730951},"35":{"tf":1.0},"372":{"tf":1.0},"437":{"tf":1.0},"440":{"tf":1.4142135623730951},"501":{"tf":1.0},"503":{"tf":1.0},"564":{"tf":1.7320508075688772},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"57":{"tf":1.0},"570":{"tf":1.0},"573":{"tf":1.0},"577":{"tf":1.4142135623730951},"586":{"tf":1.0},"594":{"tf":1.0},"71":{"tf":1.0},"712":{"tf":1.0},"724":{"tf":1.0},"73":{"tf":1.0},"773":{"tf":1.7320508075688772},"778":{"tf":1.0},"78":{"tf":1.0},"794":{"tf":1.0},"811":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":1.0},"843":{"tf":1.0},"849":{"tf":1.0},"863":{"tf":1.4142135623730951},"872":{"tf":1.0},"875":{"tf":1.0},"879":{"tf":1.4142135623730951},"881":{"tf":1.7320508075688772},"885":{"tf":1.0},"932":{"tf":1.4142135623730951},"934":{"tf":1.0},"984":{"tf":1.0}}}},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":1,"docs":{"987":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":10,"docs":{"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.0},"112":{"tf":1.0},"160":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.0},"375":{"tf":1.0},"602":{"tf":1.0},"735":{"tf":3.4641016151377544}}},"r":{"a":{"df":0,"docs":{},"g":{"df":73,"docs":{"137":{"tf":1.0},"140":{"tf":1.4142135623730951},"141":{"tf":1.0},"144":{"tf":1.0},"146":{"tf":1.0},"150":{"tf":2.0},"151":{"tf":1.7320508075688772},"152":{"tf":1.0},"153":{"tf":1.0},"154":{"tf":1.7320508075688772},"155":{"tf":1.0},"156":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"159":{"tf":1.0},"160":{"tf":1.0},"161":{"tf":1.0},"162":{"tf":1.0},"163":{"tf":1.0},"19":{"tf":1.0},"205":{"tf":1.7320508075688772},"249":{"tf":1.4142135623730951},"28":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"362":{"tf":1.0},"375":{"tf":1.0},"38":{"tf":1.4142135623730951},"387":{"tf":1.4142135623730951},"390":{"tf":2.0},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"402":{"tf":2.6457513110645907},"404":{"tf":1.4142135623730951},"412":{"tf":1.4142135623730951},"415":{"tf":1.0},"416":{"tf":1.0},"422":{"tf":1.0},"427":{"tf":1.0},"44":{"tf":1.4142135623730951},"46":{"tf":2.6457513110645907},"47":{"tf":2.23606797749979},"48":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.4142135623730951},"51":{"tf":2.449489742783178},"519":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"54":{"tf":1.0},"56":{"tf":1.0},"58":{"tf":1.0},"735":{"tf":1.4142135623730951},"75":{"tf":1.7320508075688772},"757":{"tf":1.0},"758":{"tf":1.0},"759":{"tf":2.449489742783178},"761":{"tf":2.23606797749979},"762":{"tf":1.7320508075688772},"777":{"tf":1.0},"78":{"tf":2.0},"803":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.4142135623730951},"826":{"tf":1.0},"829":{"tf":1.4142135623730951},"831":{"tf":1.0},"832":{"tf":1.0},"880":{"tf":1.4142135623730951},"936":{"tf":1.0},"944":{"tf":1.4142135623730951},"951":{"tf":1.0},"961":{"tf":1.4142135623730951},"992":{"tf":1.7320508075688772}},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"871":{"tf":1.0},"880":{"tf":1.4142135623730951}}}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":10,"docs":{"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.0},"403":{"tf":1.0},"404":{"tf":1.0},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"p":{"<":{"_":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"df":54,"docs":{"126":{"tf":1.0},"140":{"tf":1.0},"149":{"tf":1.0},"150":{"tf":1.0},"151":{"tf":1.4142135623730951},"154":{"tf":1.4142135623730951},"247":{"tf":2.0},"248":{"tf":1.0},"249":{"tf":1.4142135623730951},"250":{"tf":1.0},"251":{"tf":1.0},"252":{"tf":1.0},"253":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"256":{"tf":1.0},"257":{"tf":1.0},"258":{"tf":1.0},"259":{"tf":1.0},"260":{"tf":1.0},"261":{"tf":1.0},"262":{"tf":1.0},"39":{"tf":1.0},"412":{"tf":1.0},"439":{"tf":1.0},"47":{"tf":1.0},"497":{"tf":1.7320508075688772},"505":{"tf":1.0},"522":{"tf":1.4142135623730951},"551":{"tf":1.4142135623730951},"568":{"tf":1.7320508075688772},"570":{"tf":1.4142135623730951},"573":{"tf":1.0},"633":{"tf":1.0},"637":{"tf":1.4142135623730951},"68":{"tf":1.0},"75":{"tf":1.4142135623730951},"759":{"tf":1.0},"78":{"tf":1.4142135623730951},"81":{"tf":1.0},"810":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.7320508075688772},"815":{"tf":1.7320508075688772},"816":{"tf":1.0},"817":{"tf":1.7320508075688772},"872":{"tf":1.0},"874":{"tf":1.4142135623730951},"879":{"tf":1.4142135623730951},"880":{"tf":1.7320508075688772},"881":{"tf":1.0},"885":{"tf":1.4142135623730951},"895":{"tf":1.0},"932":{"tf":1.0}}},"i":{"df":1,"docs":{"308":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":6,"docs":{"483":{"tf":1.0},"61":{"tf":1.0},"749":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"850":{"tf":1.0}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":3,"docs":{"156":{"tf":1.0},"942":{"tf":1.0},"994":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"n":{"df":1,"docs":{"418":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":18,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"272":{"tf":1.0},"28":{"tf":1.0},"322":{"tf":1.0},"326":{"tf":1.0},"346":{"tf":1.0},"348":{"tf":1.4142135623730951},"358":{"tf":1.0},"363":{"tf":1.7320508075688772},"422":{"tf":1.0},"44":{"tf":1.0},"609":{"tf":1.0},"68":{"tf":1.0},"709":{"tf":1.0},"718":{"tf":2.0},"723":{"tf":1.4142135623730951},"777":{"tf":1.0}}}}}}},"df":2,"docs":{"23":{"tf":1.0},"522":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"762":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"145":{"tf":1.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.0}}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"773":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":2,"docs":{"121":{"tf":1.0},"778":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"432":{"tf":1.0}}}}},"i":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"239":{"tf":1.0},"30":{"tf":1.0},"368":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"697":{"tf":1.0},"73":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":11,"docs":{"169":{"tf":1.0},"200":{"tf":1.0},"254":{"tf":1.4142135623730951},"276":{"tf":1.0},"528":{"tf":1.0},"711":{"tf":1.0},"735":{"tf":1.0},"761":{"tf":1.0},"763":{"tf":1.0},"831":{"tf":1.0},"835":{"tf":1.0}}}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":8,"docs":{"253":{"tf":1.0},"332":{"tf":1.4142135623730951},"333":{"tf":1.4142135623730951},"343":{"tf":1.0},"364":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.0}}}},"p":{"df":1,"docs":{"517":{"tf":1.4142135623730951}}},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"199":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"516":{"tf":1.0},"615":{"tf":1.0},"818":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"807":{"tf":1.0},"831":{"tf":1.0}}}}}}},"u":{"c":{"df":0,"docs":{},"t":{"/":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"332":{"tf":1.0}}}}}}},"df":18,"docs":{"208":{"tf":2.23606797749979},"24":{"tf":1.4142135623730951},"253":{"tf":1.0},"439":{"tf":1.7320508075688772},"440":{"tf":1.0},"455":{"tf":1.0},"521":{"tf":1.4142135623730951},"522":{"tf":2.6457513110645907},"6":{"tf":1.0},"62":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"634":{"tf":1.0},"715":{"tf":1.4142135623730951},"716":{"tf":1.4142135623730951},"761":{"tf":1.0},"83":{"tf":1.0},"880":{"tf":1.4142135623730951},"898":{"tf":1.4142135623730951}},"u":{"df":0,"docs":{},"r":{"df":17,"docs":{"137":{"tf":1.0},"140":{"tf":1.0},"142":{"tf":1.0},"17":{"tf":1.0},"25":{"tf":1.7320508075688772},"28":{"tf":1.0},"313":{"tf":1.0},"322":{"tf":1.0},"331":{"tf":2.0},"343":{"tf":1.0},"364":{"tf":1.0},"5":{"tf":1.0},"522":{"tf":1.4142135623730951},"628":{"tf":1.0},"654":{"tf":1.0},"780":{"tf":1.0},"961":{"tf":1.0}}}}}},"df":0,"docs":{}}},"u":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"878":{"tf":1.0}}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"333":{"tf":1.0}}}}}},"u":{"b":{"0":{"df":1,"docs":{"807":{"tf":1.0}}},"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}}}},"df":6,"docs":{"203":{"tf":1.0},"372":{"tf":1.0},"382":{"tf":1.0},"416":{"tf":1.0},"483":{"tf":1.0},"522":{"tf":1.0}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":9,"docs":{"214":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"358":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"722":{"tf":1.0},"911":{"tf":1.0},"932":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":7,"docs":{"126":{"tf":1.4142135623730951},"322":{"tf":1.7320508075688772},"336":{"tf":1.4142135623730951},"346":{"tf":2.0},"347":{"tf":1.0},"365":{"tf":1.4142135623730951},"39":{"tf":1.0}}}},"t":{"df":20,"docs":{"1013":{"tf":1.0},"112":{"tf":1.4142135623730951},"184":{"tf":1.0},"185":{"tf":1.0},"187":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.4142135623730951},"365":{"tf":1.0},"375":{"tf":1.0},"44":{"tf":1.0},"45":{"tf":1.0},"453":{"tf":1.0},"51":{"tf":1.0},"573":{"tf":1.0},"60":{"tf":1.0},"721":{"tf":1.0},"776":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0}}}}},"s":{"c":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"633":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":9,"docs":{"345":{"tf":1.0},"365":{"tf":1.0},"407":{"tf":1.0},"45":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"984":{"tf":1.0}}}},"t":{"df":10,"docs":{"231":{"tf":1.7320508075688772},"232":{"tf":1.0},"276":{"tf":1.0},"3":{"tf":1.0},"338":{"tf":1.0},"368":{"tf":1.0},"46":{"tf":1.0},"517":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951}}}},"i":{"d":{"df":1,"docs":{"416":{"tf":1.0}},"i":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":1,"docs":{"417":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"p":{"a":{"c":{"df":1,"docs":{"388":{"tf":1.0}},"e":{"'":{"df":1,"docs":{"388":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"191":{"tf":1.0},"804":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":5,"docs":{"199":{"tf":1.0},"201":{"tf":1.0},"563":{"tf":1.0},"732":{"tf":1.0},"826":{"tf":1.0}}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":13,"docs":{"19":{"tf":1.0},"251":{"tf":2.0},"282":{"tf":1.0},"464":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"500":{"tf":1.7320508075688772},"721":{"tf":1.0},"737":{"tf":1.0},"829":{"tf":1.0},"928":{"tf":1.0},"991":{"tf":1.4142135623730951}},"e":{"#":{"1":{"4":{"2":{"7":{"5":{"df":1,"docs":{"291":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"/":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"/":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":1,"docs":{"198":{"tf":1.0}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"/":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"df":1,"docs":{"933":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"933":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"253":{"tf":1.0},"482":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":13,"docs":{"367":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.7320508075688772},"372":{"tf":1.4142135623730951},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.4142135623730951},"377":{"tf":1.0},"381":{"tf":1.0},"450":{"tf":1.0},"711":{"tf":1.0},"815":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"230":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"l":{"df":1,"docs":{"720":{"tf":1.0}},"i":{"df":1,"docs":{"776":{"tf":1.0}}}},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"c":{"df":0,"docs":{},"e":{"df":4,"docs":{"60":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"832":{"tf":1.0}},"e":{"d":{"df":2,"docs":{"63":{"tf":1.0},"64":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"s":{"df":14,"docs":{"205":{"tf":1.0},"223":{"tf":1.4142135623730951},"267":{"tf":1.0},"293":{"tf":1.0},"341":{"tf":1.4142135623730951},"350":{"tf":1.0},"376":{"tf":1.0},"417":{"tf":1.0},"575":{"tf":1.0},"609":{"tf":1.0},"735":{"tf":3.1622776601683795},"776":{"tf":1.0},"843":{"tf":1.0},"947":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"724":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":9,"docs":{"205":{"tf":1.0},"295":{"tf":1.0},"297":{"tf":1.0},"301":{"tf":1.4142135623730951},"45":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"817":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"h":{"df":68,"docs":{"108":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"124":{"tf":1.4142135623730951},"169":{"tf":1.0},"19":{"tf":1.0},"199":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"231":{"tf":1.4142135623730951},"249":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.4142135623730951},"267":{"tf":1.0},"273":{"tf":1.0},"3":{"tf":1.7320508075688772},"303":{"tf":1.0},"348":{"tf":1.0},"356":{"tf":1.0},"373":{"tf":1.0},"38":{"tf":1.0},"385":{"tf":1.0},"416":{"tf":1.0},"418":{"tf":1.0},"429":{"tf":1.0},"439":{"tf":1.0},"449":{"tf":1.0},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"496":{"tf":1.0},"497":{"tf":1.0},"5":{"tf":1.0},"518":{"tf":1.0},"537":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":1.4142135623730951},"573":{"tf":1.0},"609":{"tf":1.0},"696":{"tf":1.4142135623730951},"763":{"tf":1.7320508075688772},"765":{"tf":1.0},"778":{"tf":1.0},"784":{"tf":1.0},"804":{"tf":1.4142135623730951},"809":{"tf":1.0},"818":{"tf":1.0},"833":{"tf":1.0},"835":{"tf":1.0},"846":{"tf":1.4142135623730951},"872":{"tf":1.0},"912":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.4142135623730951},"934":{"tf":1.0},"939":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951},"968":{"tf":1.0},"973":{"tf":1.0},"976":{"tf":1.0},"990":{"tf":1.0}}}},"d":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":4,"docs":{"257":{"tf":1.0},"417":{"tf":1.0},"507":{"tf":1.0},"752":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":3,"docs":{"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"199":{"tf":1.0},"203":{"tf":1.0},"724":{"tf":1.0},"759":{"tf":1.0},"928":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"i":{"df":11,"docs":{"255":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"44":{"tf":1.0},"505":{"tf":1.0},"565":{"tf":1.0},"569":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0},"797":{"tf":1.0},"846":{"tf":1.0}}}},"df":0,"docs":{}}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":20,"docs":{"113":{"tf":1.0},"124":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":2.23606797749979},"292":{"tf":1.0},"346":{"tf":1.0},"39":{"tf":1.0},"412":{"tf":1.0},"429":{"tf":1.0},"576":{"tf":1.0},"63":{"tf":1.0},"697":{"tf":1.7320508075688772},"700":{"tf":1.0},"743":{"tf":1.0},"748":{"tf":1.0},"772":{"tf":1.0},"810":{"tf":1.0},"831":{"tf":1.0},"902":{"tf":1.0},"928":{"tf":1.4142135623730951}}}}}}},"i":{"df":0,"docs":{},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"1006":{"tf":1.0},"313":{"tf":1.0},"49":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"30":{"tf":1.0}}}},"m":{"_":{"df":0,"docs":{},"u":{"df":2,"docs":{"722":{"tf":1.0},"723":{"tf":1.0}}},"v":{"df":1,"docs":{"722":{"tf":1.4142135623730951}}}},"df":5,"docs":{"199":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"715":{"tf":1.4142135623730951},"717":{"tf":1.0}},"m":{"a":{"df":0,"docs":{},"r":{"df":2,"docs":{"1012":{"tf":1.0},"609":{"tf":1.0}},"i":{"df":125,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1003":{"tf":1.4142135623730951},"106":{"tf":1.0},"107":{"tf":1.4142135623730951},"122":{"tf":1.0},"123":{"tf":1.4142135623730951},"136":{"tf":1.0},"137":{"tf":1.4142135623730951},"150":{"tf":1.0},"151":{"tf":1.4142135623730951},"164":{"tf":1.4142135623730951},"165":{"tf":1.4142135623730951},"17":{"tf":1.0},"172":{"tf":1.4142135623730951},"18":{"tf":1.4142135623730951},"182":{"tf":1.0},"183":{"tf":1.4142135623730951},"195":{"tf":1.0},"196":{"tf":1.4142135623730951},"2":{"tf":1.4142135623730951},"215":{"tf":1.0},"216":{"tf":1.4142135623730951},"229":{"tf":1.0},"230":{"tf":1.4142135623730951},"247":{"tf":1.0},"248":{"tf":1.4142135623730951},"263":{"tf":1.0},"264":{"tf":1.4142135623730951},"268":{"tf":1.0},"269":{"tf":1.4142135623730951},"279":{"tf":1.0},"280":{"tf":1.4142135623730951},"294":{"tf":1.0},"295":{"tf":1.4142135623730951},"311":{"tf":1.0},"312":{"tf":1.4142135623730951},"366":{"tf":1.0},"367":{"tf":1.4142135623730951},"386":{"tf":1.0},"387":{"tf":1.4142135623730951},"400":{"tf":1.0},"401":{"tf":1.4142135623730951},"410":{"tf":1.0},"411":{"tf":1.4142135623730951},"430":{"tf":1.0},"431":{"tf":1.4142135623730951},"45":{"tf":1.0},"451":{"tf":1.0},"452":{"tf":1.4142135623730951},"465":{"tf":1.0},"466":{"tf":1.4142135623730951},"47":{"tf":1.0},"481":{"tf":1.0},"482":{"tf":1.4142135623730951},"495":{"tf":1.0},"496":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"535":{"tf":1.0},"536":{"tf":1.4142135623730951},"549":{"tf":1.0},"550":{"tf":1.4142135623730951},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.4142135623730951},"57":{"tf":1.4142135623730951},"584":{"tf":1.0},"585":{"tf":1.4142135623730951},"598":{"tf":1.0},"599":{"tf":1.4142135623730951},"613":{"tf":1.0},"614":{"tf":1.4142135623730951},"627":{"tf":1.0},"628":{"tf":1.4142135623730951},"649":{"tf":1.0},"650":{"tf":1.4142135623730951},"664":{"tf":1.0},"665":{"tf":1.4142135623730951},"678":{"tf":1.0},"679":{"tf":1.4142135623730951},"692":{"tf":1.0},"693":{"tf":1.4142135623730951},"709":{"tf":1.0},"710":{"tf":1.4142135623730951},"730":{"tf":1.0},"731":{"tf":1.4142135623730951},"741":{"tf":1.0},"742":{"tf":1.4142135623730951},"757":{"tf":1.0},"758":{"tf":1.4142135623730951},"771":{"tf":1.0},"772":{"tf":1.4142135623730951},"782":{"tf":1.0},"783":{"tf":1.4142135623730951},"79":{"tf":1.0},"795":{"tf":1.0},"796":{"tf":1.4142135623730951},"80":{"tf":1.4142135623730951},"808":{"tf":1.0},"809":{"tf":1.4142135623730951},"827":{"tf":1.0},"828":{"tf":1.4142135623730951},"841":{"tf":1.0},"842":{"tf":1.4142135623730951},"857":{"tf":1.0},"858":{"tf":1.4142135623730951},"871":{"tf":1.0},"872":{"tf":1.4142135623730951},"891":{"tf":1.0},"892":{"tf":1.4142135623730951},"908":{"tf":1.0},"909":{"tf":1.4142135623730951},"926":{"tf":1.0},"927":{"tf":1.4142135623730951},"93":{"tf":1.0},"94":{"tf":1.4142135623730951},"940":{"tf":1.0},"941":{"tf":1.4142135623730951},"957":{"tf":1.0},"958":{"tf":1.4142135623730951},"974":{"tf":1.0},"975":{"tf":1.4142135623730951},"988":{"tf":1.0},"989":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"201":{"tf":1.0}}}}}},"p":{"_":{"df":0,"docs":{},"x":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"e":{"d":{"df":2,"docs":{"735":{"tf":1.7320508075688772},"736":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"500":{"tf":1.0},"735":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"j":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"724":{"tf":1.0}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"3":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"500":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"878":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":4,"docs":{"743":{"tf":1.0},"747":{"tf":1.0},"776":{"tf":1.4142135623730951},"84":{"tf":1.0}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":68,"docs":{"121":{"tf":1.4142135623730951},"160":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"178":{"tf":1.0},"18":{"tf":1.4142135623730951},"196":{"tf":1.0},"200":{"tf":1.0},"209":{"tf":1.0},"22":{"tf":1.0},"24":{"tf":1.0},"26":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.4142135623730951},"322":{"tf":1.0},"326":{"tf":1.4142135623730951},"33":{"tf":1.0},"35":{"tf":1.0},"37":{"tf":1.0},"375":{"tf":1.0},"440":{"tf":1.7320508075688772},"451":{"tf":1.0},"461":{"tf":1.4142135623730951},"467":{"tf":1.0},"48":{"tf":1.7320508075688772},"49":{"tf":1.4142135623730951},"516":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"535":{"tf":1.0},"537":{"tf":2.0},"54":{"tf":1.0},"542":{"tf":1.0},"586":{"tf":1.0},"588":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.0},"635":{"tf":1.0},"643":{"tf":1.0},"644":{"tf":1.0},"645":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.4142135623730951},"700":{"tf":1.4142135623730951},"711":{"tf":1.0},"73":{"tf":1.0},"740":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.0},"804":{"tf":1.0},"810":{"tf":1.0},"846":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"849":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"88":{"tf":1.0},"896":{"tf":1.0},"898":{"tf":1.0},"900":{"tf":1.0},"902":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"961":{"tf":1.4142135623730951},"972":{"tf":1.0},"984":{"tf":1.0}}}},"s":{"df":2,"docs":{"765":{"tf":1.0},"832":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"df":15,"docs":{"253":{"tf":1.0},"267":{"tf":1.0},"439":{"tf":1.0},"564":{"tf":1.0},"568":{"tf":1.0},"605":{"tf":1.0},"63":{"tf":1.0},"653":{"tf":1.0},"773":{"tf":1.0},"788":{"tf":1.0},"829":{"tf":1.0},"846":{"tf":1.0},"879":{"tf":2.0},"939":{"tf":1.0},"979":{"tf":1.0}}},"f":{"a":{"c":{"df":1,"docs":{"976":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"g":{"df":1,"docs":{"752":{"tf":1.0}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"735":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":5,"docs":{"267":{"tf":1.0},"534":{"tf":1.0},"809":{"tf":1.0},"810":{"tf":1.0},"937":{"tf":1.0}}}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"p":{"df":3,"docs":{"296":{"tf":1.7320508075688772},"297":{"tf":1.0},"300":{"tf":1.4142135623730951}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"83":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}},"t":{"c":{"df":0,"docs":{},"h":{"df":2,"docs":{"64":{"tf":1.0},"641":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"311":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}}},"y":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"520":{"tf":1.0}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"722":{"tf":1.0}}}}}}},"n":{"c":{"/":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"48":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":19,"docs":{"1000":{"tf":1.0},"1001":{"tf":1.0},"160":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.4142135623730951},"567":{"tf":1.7320508075688772},"770":{"tf":1.0},"988":{"tf":2.23606797749979},"989":{"tf":1.4142135623730951},"990":{"tf":1.7320508075688772},"991":{"tf":1.4142135623730951},"992":{"tf":1.4142135623730951},"993":{"tf":1.0},"994":{"tf":1.4142135623730951},"995":{"tf":1.0},"996":{"tf":1.7320508075688772},"997":{"tf":1.0},"998":{"tf":1.0},"999":{"tf":1.0}},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":7,"docs":{"373":{"tf":1.0},"374":{"tf":1.0},"47":{"tf":1.0},"740":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"959":{"tf":1.0}},"i":{"df":1,"docs":{"721":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"g":{"df":1,"docs":{"314":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"7":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"x":{"df":3,"docs":{"253":{"tf":1.0},"331":{"tf":1.0},"553":{"tf":1.0}}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"709":{"tf":1.0},"729":{"tf":2.449489742783178}}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"'":{"df":2,"docs":{"237":{"tf":1.0},"373":{"tf":1.0}}},".":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"(":{"'":{"df":0,"docs":{},"{":{"\"":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":1,"docs":{"847":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":1,"docs":{"847":{"tf":1.0}}}}},"df":0,"docs":{}}}}},":":{":":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"284":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"281":{"tf":1.0},"284":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"(":{"0":{"df":1,"docs":{"416":{"tf":1.0}}},"1":{"df":2,"docs":{"415":{"tf":1.4142135623730951},"416":{"tf":2.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"393":{"tf":1.0}}}},"s":{"df":4,"docs":{"154":{"tf":1.4142135623730951},"387":{"tf":1.4142135623730951},"390":{"tf":1.0},"391":{"tf":1.0}}}}}}},"a":{"df":0,"docs":{},"t":{"df":10,"docs":{"430":{"tf":1.4142135623730951},"431":{"tf":1.0},"432":{"tf":1.7320508075688772},"435":{"tf":2.23606797749979},"437":{"tf":2.6457513110645907},"439":{"tf":1.0},"440":{"tf":1.0},"449":{"tf":1.0},"450":{"tf":1.0},"723":{"tf":1.4142135623730951}},"i":{"c":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"(":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"438":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"773":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":126,"docs":{"1003":{"tf":1.0},"1004":{"tf":1.7320508075688772},"126":{"tf":1.4142135623730951},"138":{"tf":1.4142135623730951},"140":{"tf":1.0},"144":{"tf":1.0},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"198":{"tf":1.7320508075688772},"199":{"tf":1.0},"203":{"tf":2.6457513110645907},"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.0},"21":{"tf":1.0},"216":{"tf":1.0},"217":{"tf":1.4142135623730951},"218":{"tf":1.0},"219":{"tf":1.0},"22":{"tf":1.4142135623730951},"229":{"tf":2.23606797749979},"230":{"tf":1.4142135623730951},"231":{"tf":2.8284271247461903},"232":{"tf":2.0},"233":{"tf":1.0},"234":{"tf":1.0},"235":{"tf":1.4142135623730951},"236":{"tf":1.0},"237":{"tf":1.0},"238":{"tf":1.4142135623730951},"239":{"tf":1.0},"24":{"tf":1.0},"240":{"tf":1.0},"241":{"tf":1.0},"242":{"tf":1.0},"243":{"tf":1.4142135623730951},"244":{"tf":1.0},"245":{"tf":1.0},"246":{"tf":1.4142135623730951},"252":{"tf":1.0},"268":{"tf":2.23606797749979},"269":{"tf":1.0},"270":{"tf":1.4142135623730951},"271":{"tf":1.4142135623730951},"272":{"tf":1.0},"273":{"tf":1.0},"274":{"tf":1.0},"275":{"tf":1.0},"276":{"tf":1.0},"277":{"tf":1.0},"278":{"tf":1.0},"3":{"tf":2.0},"30":{"tf":1.0},"310":{"tf":1.0},"312":{"tf":1.4142135623730951},"313":{"tf":2.0},"314":{"tf":1.4142135623730951},"315":{"tf":1.7320508075688772},"316":{"tf":1.0},"317":{"tf":1.0},"327":{"tf":1.0},"335":{"tf":1.0},"367":{"tf":1.0},"368":{"tf":1.0},"370":{"tf":1.0},"371":{"tf":1.0},"372":{"tf":1.0},"373":{"tf":2.0},"374":{"tf":1.4142135623730951},"375":{"tf":3.1622776601683795},"376":{"tf":1.4142135623730951},"380":{"tf":1.0},"386":{"tf":2.23606797749979},"387":{"tf":1.0},"388":{"tf":1.0},"389":{"tf":1.4142135623730951},"390":{"tf":2.23606797749979},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"417":{"tf":1.0},"427":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"459":{"tf":1.0},"515":{"tf":1.0},"564":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.4142135623730951},"586":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"663":{"tf":1.0},"697":{"tf":1.0},"720":{"tf":1.4142135623730951},"722":{"tf":1.4142135623730951},"724":{"tf":1.0},"771":{"tf":1.0},"772":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.7320508075688772},"786":{"tf":1.0},"81":{"tf":1.0},"813":{"tf":1.0},"814":{"tf":1.0},"819":{"tf":1.0},"871":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":2.0},"931":{"tf":1.0},"932":{"tf":2.0},"933":{"tf":1.0},"934":{"tf":1.0},"936":{"tf":1.4142135623730951},"937":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"973":{"tf":1.0},"983":{"tf":1.0}}}}}}},"·":{"2":{"df":1,"docs":{"346":{"tf":1.0}}},"4":{"/":{"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"0":{"df":1,"docs":{"567":{"tf":1.7320508075688772}}},":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"879":{"tf":3.0},"880":{"tf":1.7320508075688772},"885":{"tf":1.7320508075688772}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"b":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"83":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}}}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"t":{"df":1,"docs":{"818":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"880":{"tf":1.0}}}}},"df":0,"docs":{}},"m":{"a":{"df":0,"docs":{},"x":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"879":{"tf":1.0},"880":{"tf":1.7320508075688772}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{")":{".":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"_":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"(":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}}}}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"814":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"a":{"b":{"df":0,"docs":{},"l":{"df":66,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"248":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"633":{"tf":1.4142135623730951},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"885":{"tf":1.4142135623730951},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"i":{"df":1,"docs":{"1002":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"148":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":4,"docs":{"342":{"tf":1.0},"343":{"tf":1.0},"347":{"tf":1.0},"786":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"147":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":40,"docs":{"114":{"tf":1.0},"140":{"tf":1.0},"155":{"tf":1.0},"196":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.7320508075688772},"207":{"tf":1.4142135623730951},"22":{"tf":1.0},"221":{"tf":1.0},"23":{"tf":1.0},"249":{"tf":1.0},"257":{"tf":1.0},"296":{"tf":1.0},"314":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"471":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"507":{"tf":1.0},"528":{"tf":1.0},"537":{"tf":1.0},"554":{"tf":1.0},"571":{"tf":1.0},"593":{"tf":1.0},"602":{"tf":1.0},"63":{"tf":1.0},"631":{"tf":1.0},"634":{"tf":1.7320508075688772},"653":{"tf":1.4142135623730951},"668":{"tf":1.0},"670":{"tf":1.0},"717":{"tf":1.0},"735":{"tf":1.0},"742":{"tf":1.0},"763":{"tf":1.4142135623730951},"844":{"tf":1.0},"85":{"tf":1.0},"94":{"tf":1.0},"945":{"tf":1.0}},"n":{"df":8,"docs":{"1010":{"tf":1.0},"239":{"tf":1.0},"346":{"tf":1.0},"642":{"tf":1.0},"653":{"tf":1.0},"735":{"tf":1.0},"788":{"tf":1.0},"945":{"tf":1.0}}},"o":{"df":0,"docs":{},"v":{"df":1,"docs":{"231":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"y":{"df":1,"docs":{"885":{"tf":1.0}}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"279":{"tf":1.0}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"467":{"tf":1.0}}}}},"k":{"df":1,"docs":{"835":{"tf":1.0}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"124":{"tf":1.0},"51":{"tf":1.0},"721":{"tf":1.7320508075688772},"722":{"tf":1.0},"725":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"_":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":3,"docs":{"346":{"tf":1.4142135623730951},"347":{"tf":1.0},"349":{"tf":2.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"df":29,"docs":{"205":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"208":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"335":{"tf":1.0},"336":{"tf":1.0},"338":{"tf":1.4142135623730951},"339":{"tf":1.0},"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":2.449489742783178},"350":{"tf":1.0},"505":{"tf":1.0},"6":{"tf":1.0},"600":{"tf":1.0},"615":{"tf":1.0},"697":{"tf":1.0},"742":{"tf":1.0},"744":{"tf":1.4142135623730951},"747":{"tf":2.23606797749979},"748":{"tf":1.0},"749":{"tf":1.0},"751":{"tf":1.0},"81":{"tf":1.0},"83":{"tf":1.0}},"s":{".":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"k":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"221":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":14,"docs":{"108":{"tf":1.0},"113":{"tf":1.0},"203":{"tf":2.8284271247461903},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"208":{"tf":4.58257569495584},"218":{"tf":1.4142135623730951},"221":{"tf":1.0},"296":{"tf":1.0},"450":{"tf":1.0},"565":{"tf":1.0},"711":{"tf":1.0},"776":{"tf":1.4142135623730951},"919":{"tf":1.0}},"e":{"d":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"204":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"i":{"d":{"df":3,"docs":{"204":{"tf":1.4142135623730951},"205":{"tf":1.0},"208":{"tf":1.0}}},"df":0,"docs":{}},"s":{"/":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"204":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"714":{"tf":1.0}}}},"t":{"df":6,"docs":{"709":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":2.0},"724":{"tf":1.0}}},"y":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"912":{"tf":1.0}}}}}}},"b":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"874":{"tf":1.0}}}}},"df":0,"docs":{}},"d":{"df":1,"docs":{"112":{"tf":1.0}}},"df":7,"docs":{"207":{"tf":1.0},"332":{"tf":1.0},"333":{"tf":2.449489742783178},"346":{"tf":1.4142135623730951},"348":{"tf":2.6457513110645907},"539":{"tf":1.0},"749":{"tf":1.7320508075688772}},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"725":{"tf":1.4142135623730951}}}},"df":0,"docs":{},"m":{"df":30,"docs":{"104":{"tf":1.0},"106":{"tf":1.0},"107":{"tf":1.0},"108":{"tf":1.4142135623730951},"109":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.4142135623730951},"113":{"tf":1.0},"118":{"tf":1.0},"121":{"tf":1.4142135623730951},"196":{"tf":1.0},"199":{"tf":1.0},"201":{"tf":1.7320508075688772},"270":{"tf":1.0},"282":{"tf":1.0},"296":{"tf":1.0},"298":{"tf":1.0},"303":{"tf":1.4142135623730951},"306":{"tf":1.0},"315":{"tf":1.0},"324":{"tf":1.0},"403":{"tf":1.0},"408":{"tf":1.0},"532":{"tf":1.0},"571":{"tf":1.0},"59":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"810":{"tf":1.4142135623730951},"848":{"tf":1.0}}}},"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"c":{"df":29,"docs":{"0":{"tf":1.0},"113":{"tf":1.7320508075688772},"121":{"tf":1.0},"140":{"tf":1.0},"145":{"tf":1.0},"193":{"tf":1.0},"208":{"tf":1.0},"230":{"tf":1.0},"250":{"tf":1.0},"269":{"tf":1.0},"270":{"tf":1.0},"271":{"tf":1.0},"272":{"tf":1.0},"277":{"tf":1.0},"296":{"tf":1.0},"340":{"tf":1.0},"375":{"tf":1.4142135623730951},"376":{"tf":1.0},"389":{"tf":1.0},"418":{"tf":1.0},"467":{"tf":1.4142135623730951},"483":{"tf":1.0},"582":{"tf":1.0},"777":{"tf":1.4142135623730951},"781":{"tf":1.0},"798":{"tf":1.4142135623730951},"801":{"tf":1.0},"842":{"tf":1.4142135623730951},"928":{"tf":1.0}}},"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":1,"docs":{"968":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":5,"docs":{"199":{"tf":1.0},"201":{"tf":1.0},"416":{"tf":1.0},"513":{"tf":1.0},"774":{"tf":1.0}}}}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":1,"docs":{"799":{"tf":1.0}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}},"df":5,"docs":{"3":{"tf":1.0},"599":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"603":{"tf":1.7320508075688772}}}}}}},"l":{"df":3,"docs":{"177":{"tf":1.0},"551":{"tf":1.0},"717":{"tf":1.0}}}},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"296":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"152":{"tf":1.0},"932":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"n":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":5,"docs":{"772":{"tf":1.4142135623730951},"773":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":2.0},"912":{"tf":1.0}}}}},"df":1,"docs":{"58":{"tf":1.0}},"t":{"df":1,"docs":{"932":{"tf":1.0}},"h":{"df":1,"docs":{"221":{"tf":1.0}}}},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"1004":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"m":{"df":32,"docs":{"140":{"tf":1.0},"169":{"tf":1.0},"196":{"tf":1.4142135623730951},"198":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"207":{"tf":1.4142135623730951},"255":{"tf":1.0},"274":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.4142135623730951},"39":{"tf":1.0},"410":{"tf":1.0},"417":{"tf":1.7320508075688772},"505":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"575":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.7320508075688772},"711":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.4142135623730951},"772":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.4142135623730951},"8":{"tf":1.0},"849":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.0},"885":{"tf":1.0},"932":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":131,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"1008":{"tf":1.7320508075688772},"106":{"tf":1.0},"115":{"tf":1.7320508075688772},"122":{"tf":1.0},"128":{"tf":1.7320508075688772},"136":{"tf":1.0},"142":{"tf":2.0},"150":{"tf":1.0},"156":{"tf":2.0},"164":{"tf":1.0},"17":{"tf":1.0},"174":{"tf":1.7320508075688772},"182":{"tf":1.0},"188":{"tf":1.4142135623730951},"195":{"tf":1.0},"209":{"tf":1.4142135623730951},"211":{"tf":2.6457513110645907},"215":{"tf":1.0},"225":{"tf":1.7320508075688772},"229":{"tf":1.0},"237":{"tf":2.0},"239":{"tf":1.0},"247":{"tf":1.0},"255":{"tf":1.4142135623730951},"268":{"tf":1.0},"275":{"tf":1.4142135623730951},"279":{"tf":1.0},"282":{"tf":1.0},"286":{"tf":1.7320508075688772},"294":{"tf":1.0},"30":{"tf":2.6457513110645907},"304":{"tf":1.7320508075688772},"311":{"tf":1.0},"315":{"tf":1.0},"317":{"tf":1.4142135623730951},"322":{"tf":1.0},"354":{"tf":1.7320508075688772},"366":{"tf":1.0},"376":{"tf":1.0},"378":{"tf":1.7320508075688772},"38":{"tf":1.0},"386":{"tf":1.0},"392":{"tf":1.4142135623730951},"410":{"tf":1.0},"419":{"tf":1.4142135623730951},"430":{"tf":1.0},"442":{"tf":1.7320508075688772},"451":{"tf":1.0},"457":{"tf":2.0},"465":{"tf":1.0},"474":{"tf":1.4142135623730951},"481":{"tf":1.0},"487":{"tf":1.4142135623730951},"495":{"tf":1.0},"50":{"tf":1.0},"505":{"tf":1.4142135623730951},"513":{"tf":1.0},"528":{"tf":1.7320508075688772},"53":{"tf":1.4142135623730951},"535":{"tf":1.0},"541":{"tf":1.7320508075688772},"549":{"tf":1.0},"555":{"tf":2.0},"56":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"578":{"tf":1.4142135623730951},"584":{"tf":1.0},"590":{"tf":1.7320508075688772},"598":{"tf":1.0},"605":{"tf":1.4142135623730951},"613":{"tf":1.0},"619":{"tf":1.4142135623730951},"627":{"tf":1.0},"631":{"tf":1.0},"639":{"tf":2.449489742783178},"648":{"tf":1.0},"649":{"tf":1.0},"656":{"tf":1.4142135623730951},"664":{"tf":1.0},"670":{"tf":1.4142135623730951},"678":{"tf":1.0},"684":{"tf":1.4142135623730951},"69":{"tf":1.4142135623730951},"692":{"tf":1.0},"701":{"tf":1.4142135623730951},"709":{"tf":1.0},"724":{"tf":1.4142135623730951},"757":{"tf":1.0},"763":{"tf":1.4142135623730951},"782":{"tf":1.0},"788":{"tf":2.0},"79":{"tf":1.0},"795":{"tf":1.0},"801":{"tf":1.7320508075688772},"808":{"tf":1.0},"819":{"tf":1.7320508075688772},"827":{"tf":1.0},"833":{"tf":1.4142135623730951},"841":{"tf":1.0},"85":{"tf":1.4142135623730951},"850":{"tf":1.4142135623730951},"857":{"tf":1.0},"864":{"tf":1.7320508075688772},"871":{"tf":1.0},"883":{"tf":1.4142135623730951},"891":{"tf":1.0},"9":{"tf":1.4142135623730951},"900":{"tf":1.7320508075688772},"908":{"tf":1.0},"917":{"tf":1.4142135623730951},"926":{"tf":1.0},"93":{"tf":1.0},"935":{"tf":1.4142135623730951},"940":{"tf":1.4142135623730951},"944":{"tf":1.4142135623730951},"945":{"tf":1.0},"946":{"tf":1.4142135623730951},"947":{"tf":2.0},"957":{"tf":1.4142135623730951},"961":{"tf":1.0},"963":{"tf":1.4142135623730951},"964":{"tf":2.23606797749979},"974":{"tf":1.0},"980":{"tf":1.4142135623730951},"988":{"tf":1.0},"99":{"tf":1.4142135623730951},"992":{"tf":1.0},"994":{"tf":1.7320508075688772}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":22,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"211":{"tf":1.0},"304":{"tf":1.0},"376":{"tf":1.0},"50":{"tf":1.0},"639":{"tf":1.0},"678":{"tf":2.23606797749979},"679":{"tf":1.4142135623730951},"680":{"tf":1.4142135623730951},"681":{"tf":1.0},"682":{"tf":1.0},"683":{"tf":1.4142135623730951},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.4142135623730951},"688":{"tf":1.4142135623730951},"689":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0}}}}}}},"x":{"df":0,"docs":{},"t":{"df":4,"docs":{"272":{"tf":1.0},"273":{"tf":1.0},"75":{"tf":1.0},"847":{"tf":1.4142135623730951}},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"{":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"721":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"532":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"{":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"749":{"tf":1.4142135623730951}}}}}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":5,"docs":{"571":{"tf":1.0},"710":{"tf":1.0},"759":{"tf":1.0},"763":{"tf":1.0},"780":{"tf":1.0}}}},"t":{"'":{"df":4,"docs":{"483":{"tf":1.0},"673":{"tf":1.0},"846":{"tf":1.0},"850":{"tf":1.0}}},"df":0,"docs":{}}},"df":2,"docs":{"333":{"tf":1.0},"439":{"tf":1.0}},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":14,"docs":{"1015":{"tf":1.0},"234":{"tf":1.0},"247":{"tf":1.0},"252":{"tf":1.4142135623730951},"267":{"tf":1.0},"495":{"tf":1.0},"501":{"tf":2.449489742783178},"502":{"tf":1.0},"503":{"tf":1.0},"720":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.4142135623730951},"848":{"tf":1.4142135623730951},"849":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"230":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.4142135623730951},"992":{"tf":1.0}}}},"i":{"df":5,"docs":{"124":{"tf":1.0},"254":{"tf":1.0},"554":{"tf":1.0},"718":{"tf":1.0},"777":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"'":{"df":6,"docs":{"316":{"tf":1.0},"429":{"tf":1.0},"832":{"tf":1.0},"849":{"tf":1.0},"850":{"tf":1.0},"880":{"tf":1.0}}},"b":{"df":0,"docs":{},"i":{"df":6,"docs":{"264":{"tf":1.0},"267":{"tf":1.0},"412":{"tf":1.0},"576":{"tf":1.0},"725":{"tf":1.0},"776":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":29,"docs":{"108":{"tf":1.0},"113":{"tf":1.0},"114":{"tf":1.0},"169":{"tf":1.0},"19":{"tf":1.4142135623730951},"206":{"tf":1.0},"267":{"tf":1.0},"3":{"tf":1.0},"310":{"tf":1.0},"314":{"tf":1.0},"345":{"tf":1.0},"35":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":2.0},"376":{"tf":1.0},"402":{"tf":1.0},"432":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"519":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"537":{"tf":1.0},"60":{"tf":1.0},"697":{"tf":1.0},"799":{"tf":1.0},"818":{"tf":1.0},"945":{"tf":1.4142135623730951}}}}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"852":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"418":{"tf":1.0}}}},"y":{"'":{"df":0,"docs":{},"r":{"df":3,"docs":{"16":{"tf":1.0},"500":{"tf":1.0},"885":{"tf":1.0}}},"v":{"df":1,"docs":{"853":{"tf":1.0}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":14,"docs":{"16":{"tf":1.0},"187":{"tf":1.0},"439":{"tf":1.0},"482":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.0},"666":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.4142135623730951},"77":{"tf":1.4142135623730951},"78":{"tf":1.0},"835":{"tf":1.0},"874":{"tf":1.0},"979":{"tf":1.0}}},"k":{"df":8,"docs":{"1004":{"tf":1.0},"234":{"tf":1.0},"250":{"tf":1.0},"60":{"tf":1.0},"64":{"tf":1.0},"78":{"tf":1.0},"852":{"tf":1.0},"855":{"tf":1.0}}}},"r":{"d":{"df":11,"docs":{"113":{"tf":1.0},"170":{"tf":1.0},"221":{"tf":1.0},"344":{"tf":1.4142135623730951},"345":{"tf":1.0},"469":{"tf":1.0},"528":{"tf":1.0},"571":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":2,"docs":{"354":{"tf":1.0},"961":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"935":{"tf":1.0}}}}}}}}},"s":{"df":0,"docs":{},"e":{"df":24,"docs":{"111":{"tf":1.0},"186":{"tf":1.0},"187":{"tf":1.4142135623730951},"216":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"368":{"tf":1.0},"414":{"tf":1.0},"426":{"tf":1.0},"467":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.0},"650":{"tf":1.0},"701":{"tf":1.0},"714":{"tf":1.0},"73":{"tf":1.0},"799":{"tf":1.4142135623730951},"848":{"tf":1.0},"858":{"tf":1.0},"904":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"917":{"tf":1.0},"921":{"tf":1.0}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":17,"docs":{"144":{"tf":1.0},"16":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"570":{"tf":1.0},"603":{"tf":1.0},"615":{"tf":1.0},"711":{"tf":1.0},"720":{"tf":1.0},"724":{"tf":2.0},"732":{"tf":1.0},"74":{"tf":1.0},"818":{"tf":1.4142135623730951},"842":{"tf":1.0},"858":{"tf":1.0},"885":{"tf":1.0},"979":{"tf":1.0}},"t":{"df":3,"docs":{"650":{"tf":1.0},"780":{"tf":1.0},"881":{"tf":1.0}}}}},"s":{"a":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"58":{"tf":1.4142135623730951},"63":{"tf":1.0},"832":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"565":{"tf":1.0},"965":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"54":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":11,"docs":{"1008":{"tf":1.0},"126":{"tf":1.0},"200":{"tf":1.0},"205":{"tf":1.0},"207":{"tf":1.7320508075688772},"21":{"tf":1.0},"374":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"814":{"tf":1.0},"831":{"tf":1.0}}},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{",":{".":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"c":{"df":2,"docs":{"872":{"tf":1.0},"878":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":12,"docs":{"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"438":{"tf":1.4142135623730951},"564":{"tf":1.0},"872":{"tf":1.0},"874":{"tf":1.7320508075688772},"875":{"tf":1.0},"879":{"tf":4.242640687119285},"880":{"tf":1.4142135623730951},"881":{"tf":2.23606797749979},"885":{"tf":1.7320508075688772},"913":{"tf":1.0}}},"df":0,"docs":{}}}}}},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":1,"docs":{"797":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"l":{"df":2,"docs":{"720":{"tf":1.0},"763":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":45,"docs":{"140":{"tf":1.0},"148":{"tf":1.0},"166":{"tf":1.0},"169":{"tf":1.0},"175":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.0},"205":{"tf":1.4142135623730951},"207":{"tf":1.0},"209":{"tf":1.4142135623730951},"21":{"tf":1.0},"211":{"tf":1.4142135623730951},"234":{"tf":1.0},"267":{"tf":1.0},"288":{"tf":1.0},"296":{"tf":1.0},"33":{"tf":1.0},"345":{"tf":1.0},"365":{"tf":1.0},"388":{"tf":1.0},"39":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"497":{"tf":1.0},"500":{"tf":1.0},"573":{"tf":1.0},"58":{"tf":1.0},"600":{"tf":1.4142135623730951},"602":{"tf":1.7320508075688772},"603":{"tf":1.0},"605":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"732":{"tf":1.0},"77":{"tf":1.0},"772":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"829":{"tf":1.0},"846":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.0},"931":{"tf":1.0},"952":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"330":{"tf":1.0},"776":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":5,"docs":{"374":{"tf":1.0},"38":{"tf":1.0},"629":{"tf":1.0},"640":{"tf":1.0},"711":{"tf":1.0}}}}}}}},"w":{"df":0,"docs":{},"n":{"df":1,"docs":{"500":{"tf":1.0}}}}}},"u":{"df":40,"docs":{"124":{"tf":1.4142135623730951},"132":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":2.0},"269":{"tf":1.0},"276":{"tf":1.0},"285":{"tf":1.0},"324":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"358":{"tf":1.0},"374":{"tf":1.0},"418":{"tf":1.0},"439":{"tf":1.0},"459":{"tf":1.0},"461":{"tf":1.0},"470":{"tf":1.0},"515":{"tf":1.0},"517":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":1.4142135623730951},"524":{"tf":1.0},"570":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.4142135623730951},"63":{"tf":1.7320508075688772},"634":{"tf":1.0},"7":{"tf":1.0},"705":{"tf":1.4142135623730951},"71":{"tf":1.0},"723":{"tf":1.0},"759":{"tf":2.0},"763":{"tf":1.0},"78":{"tf":1.4142135623730951},"784":{"tf":1.0},"797":{"tf":1.0},"83":{"tf":1.0}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"348":{"tf":1.4142135623730951}}},"_":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"346":{"tf":1.0},"347":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"347":{"tf":1.0}}},"df":0,"docs":{}}}}}}}}},"v":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"346":{"tf":2.0},"347":{"tf":1.4142135623730951}}}}}}}},"df":0,"docs":{}}}}},"b":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"i":{"df":2,"docs":{"347":{"tf":1.4142135623730951},"351":{"tf":1.0}}}},"df":0,"docs":{}}},"df":18,"docs":{"322":{"tf":2.8284271247461903},"335":{"tf":1.0},"336":{"tf":2.0},"337":{"tf":2.0},"338":{"tf":2.0},"339":{"tf":2.0},"342":{"tf":2.449489742783178},"343":{"tf":1.4142135623730951},"344":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":5.0990195135927845},"347":{"tf":3.7416573867739413},"348":{"tf":3.1622776601683795},"349":{"tf":2.23606797749979},"350":{"tf":1.0},"351":{"tf":2.0},"365":{"tf":1.7320508075688772},"912":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"346":{"tf":1.4142135623730951}}}}}}}}},"i":{"d":{"df":4,"docs":{"346":{"tf":1.7320508075688772},"347":{"tf":2.0},"349":{"tf":1.0},"351":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":3,"docs":{"351":{"tf":1.0},"483":{"tf":1.0},"78":{"tf":1.0}},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"293":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"697":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"816":{"tf":1.4142135623730951},"874":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"e":{"df":122,"docs":{"1003":{"tf":1.0},"1004":{"tf":1.0},"108":{"tf":1.0},"124":{"tf":1.4142135623730951},"132":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"148":{"tf":1.0},"155":{"tf":1.0},"173":{"tf":1.0},"178":{"tf":1.0},"194":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.7320508075688772},"205":{"tf":1.0},"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0},"245":{"tf":1.0},"252":{"tf":1.0},"254":{"tf":1.0},"265":{"tf":1.0},"278":{"tf":1.0},"296":{"tf":1.4142135623730951},"301":{"tf":1.0},"308":{"tf":1.0},"314":{"tf":1.0},"315":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"402":{"tf":2.23606797749979},"427":{"tf":1.0},"435":{"tf":1.0},"444":{"tf":1.7320508075688772},"459":{"tf":1.0},"467":{"tf":1.7320508075688772},"469":{"tf":1.4142135623730951},"48":{"tf":1.0},"481":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.4142135623730951},"500":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.4142135623730951},"526":{"tf":1.0},"528":{"tf":1.0},"530":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.0},"539":{"tf":1.0},"542":{"tf":1.0},"549":{"tf":2.23606797749979},"550":{"tf":1.4142135623730951},"551":{"tf":1.0},"552":{"tf":1.0},"553":{"tf":2.23606797749979},"554":{"tf":1.0},"555":{"tf":1.4142135623730951},"556":{"tf":1.0},"557":{"tf":1.0},"558":{"tf":1.0},"559":{"tf":1.0},"560":{"tf":1.0},"561":{"tf":1.0},"562":{"tf":1.0},"563":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":2.23606797749979},"568":{"tf":1.0},"569":{"tf":2.6457513110645907},"570":{"tf":1.0},"571":{"tf":2.23606797749979},"573":{"tf":1.4142135623730951},"574":{"tf":1.0},"575":{"tf":1.0},"576":{"tf":2.0},"577":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"631":{"tf":1.0},"673":{"tf":1.0},"71":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.0},"72":{"tf":1.0},"721":{"tf":1.0},"73":{"tf":1.4142135623730951},"732":{"tf":1.0},"735":{"tf":2.8284271247461903},"759":{"tf":1.4142135623730951},"761":{"tf":1.7320508075688772},"762":{"tf":1.0},"763":{"tf":1.0},"767":{"tf":1.0},"770":{"tf":1.0},"776":{"tf":1.7320508075688772},"777":{"tf":1.4142135623730951},"797":{"tf":2.0},"799":{"tf":1.4142135623730951},"810":{"tf":1.0},"813":{"tf":1.0},"817":{"tf":1.0},"822":{"tf":1.0},"825":{"tf":1.0},"858":{"tf":1.0},"859":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0},"890":{"tf":1.0},"912":{"tf":2.0},"932":{"tf":1.0},"938":{"tf":1.4142135623730951},"956":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":4,"docs":{"185":{"tf":1.0},"335":{"tf":1.0},"564":{"tf":1.0},"942":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"<":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"<":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"c":{"df":4,"docs":{"204":{"tf":2.6457513110645907},"205":{"tf":2.0},"207":{"tf":1.0},"208":{"tf":3.872983346207417}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":3,"docs":{"553":{"tf":1.0},"932":{"tf":1.0},"938":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}}}}}}},"df":0,"docs":{}}}}},"p":{"df":1,"docs":{"521":{"tf":1.0}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":13,"docs":{"182":{"tf":2.23606797749979},"183":{"tf":2.23606797749979},"184":{"tf":2.23606797749979},"185":{"tf":1.0},"186":{"tf":2.6457513110645907},"187":{"tf":1.0},"188":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.0},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.0}}}}}},"t":{"df":6,"docs":{"709":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":2.0},"724":{"tf":1.0}}}},"o":{"d":{"a":{"df":0,"docs":{},"y":{"df":5,"docs":{"49":{"tf":1.0},"515":{"tf":1.0},"694":{"tf":1.0},"697":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":16,"docs":{"1002":{"tf":2.0},"1003":{"tf":1.0},"1004":{"tf":1.0},"1005":{"tf":1.0},"1006":{"tf":1.0},"1007":{"tf":1.0},"1008":{"tf":1.0},"1009":{"tf":1.0},"1010":{"tf":1.0},"1011":{"tf":1.0},"1012":{"tf":1.0},"1013":{"tf":1.0},"1014":{"tf":1.0},"1015":{"tf":1.0},"63":{"tf":1.0},"75":{"tf":1.0}}}},"df":1,"docs":{"849":{"tf":1.0}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":14,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"21":{"tf":1.0},"340":{"tf":1.0},"346":{"tf":1.0},"350":{"tf":1.0},"452":{"tf":1.0},"517":{"tf":1.0},"522":{"tf":1.0},"594":{"tf":1.0},"633":{"tf":1.0},"64":{"tf":1.0},"68":{"tf":1.0},"711":{"tf":1.0}}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"'":{"df":2,"docs":{"3":{"tf":1.0},"928":{"tf":1.0}}},"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}}},"df":36,"docs":{"114":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"193":{"tf":1.4142135623730951},"198":{"tf":1.0},"199":{"tf":1.0},"2":{"tf":1.0},"201":{"tf":1.0},"203":{"tf":1.0},"266":{"tf":1.0},"267":{"tf":2.23606797749979},"3":{"tf":1.0},"520":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"564":{"tf":2.6457513110645907},"565":{"tf":1.7320508075688772},"566":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.7320508075688772},"571":{"tf":1.4142135623730951},"573":{"tf":1.0},"575":{"tf":1.0},"577":{"tf":1.0},"6":{"tf":1.4142135623730951},"745":{"tf":1.0},"774":{"tf":1.0},"797":{"tf":1.0},"798":{"tf":1.0},"849":{"tf":1.7320508075688772},"850":{"tf":1.0},"9":{"tf":1.0},"928":{"tf":1.4142135623730951},"929":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":1.4142135623730951}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":2,"docs":{"125":{"tf":1.0},"314":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":4,"docs":{"231":{"tf":1.0},"303":{"tf":1.0},"346":{"tf":1.0},"831":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":1,"docs":{"741":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"df":27,"docs":{"125":{"tf":1.0},"145":{"tf":1.0},"154":{"tf":1.0},"173":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":1.0},"19":{"tf":1.0},"296":{"tf":1.0},"369":{"tf":1.0},"378":{"tf":1.0},"38":{"tf":1.0},"381":{"tf":1.0},"516":{"tf":1.0},"586":{"tf":1.0},"627":{"tf":1.0},"630":{"tf":1.0},"633":{"tf":1.0},"645":{"tf":1.7320508075688772},"841":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":3.3166247903554},"849":{"tf":2.0},"850":{"tf":1.0},"856":{"tf":1.0},"928":{"tf":1.0},"969":{"tf":1.0},"973":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"842":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"i":{"df":4,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.0},"848":{"tf":1.0}}}}},"df":0,"docs":{}}},"m":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"879":{"tf":2.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"p":{"df":6,"docs":{"1004":{"tf":1.0},"234":{"tf":1.4142135623730951},"39":{"tf":1.0},"444":{"tf":1.0},"50":{"tf":1.0},"673":{"tf":1.0}},"i":{"c":{"df":4,"docs":{"251":{"tf":1.0},"361":{"tf":1.0},"712":{"tf":1.0},"824":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"l":{"_":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":3.0}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}},"y":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"24":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":23,"docs":{"208":{"tf":1.4142135623730951},"257":{"tf":1.0},"264":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"428":{"tf":1.0},"444":{"tf":1.0},"471":{"tf":1.0},"507":{"tf":1.0},"567":{"tf":1.4142135623730951},"571":{"tf":1.4142135623730951},"576":{"tf":1.0},"714":{"tf":1.4142135623730951},"722":{"tf":1.0},"73":{"tf":1.0},"814":{"tf":1.0},"828":{"tf":1.0},"831":{"tf":1.0},"843":{"tf":1.4142135623730951},"849":{"tf":1.0},"855":{"tf":1.0},"879":{"tf":2.23606797749979},"885":{"tf":1.4142135623730951}},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":6,"docs":{"194":{"tf":1.0},"204":{"tf":1.0},"54":{"tf":1.0},"721":{"tf":1.0},"807":{"tf":1.0},"928":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"a":{"c":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"50":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"46":{"tf":1.0}}},"k":{"'":{"df":1,"docs":{"184":{"tf":1.0}}},"df":82,"docs":{"113":{"tf":1.4142135623730951},"121":{"tf":1.0},"136":{"tf":2.23606797749979},"137":{"tf":2.0},"138":{"tf":1.7320508075688772},"139":{"tf":1.4142135623730951},"140":{"tf":2.8284271247461903},"141":{"tf":1.7320508075688772},"142":{"tf":1.7320508075688772},"143":{"tf":1.0},"144":{"tf":1.4142135623730951},"145":{"tf":1.7320508075688772},"146":{"tf":1.7320508075688772},"147":{"tf":1.4142135623730951},"148":{"tf":2.0},"149":{"tf":1.7320508075688772},"182":{"tf":2.23606797749979},"183":{"tf":1.4142135623730951},"184":{"tf":3.0},"185":{"tf":1.4142135623730951},"186":{"tf":2.23606797749979},"187":{"tf":1.7320508075688772},"188":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.4142135623730951},"191":{"tf":1.0},"192":{"tf":1.0},"193":{"tf":1.0},"194":{"tf":1.7320508075688772},"203":{"tf":1.0},"208":{"tf":1.4142135623730951},"295":{"tf":1.0},"296":{"tf":1.4142135623730951},"297":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"375":{"tf":1.0},"402":{"tf":1.0},"407":{"tf":1.4142135623730951},"439":{"tf":1.0},"447":{"tf":1.0},"568":{"tf":1.0},"710":{"tf":1.0},"715":{"tf":1.0},"776":{"tf":1.0},"796":{"tf":1.0},"797":{"tf":1.0},"799":{"tf":1.7320508075688772},"831":{"tf":1.4142135623730951},"841":{"tf":2.6457513110645907},"842":{"tf":2.23606797749979},"843":{"tf":1.0},"844":{"tf":1.0},"845":{"tf":1.0},"846":{"tf":2.8284271247461903},"847":{"tf":2.23606797749979},"848":{"tf":2.23606797749979},"849":{"tf":2.0},"850":{"tf":2.0},"851":{"tf":1.0},"852":{"tf":1.7320508075688772},"853":{"tf":1.7320508075688772},"854":{"tf":1.0},"855":{"tf":1.0},"856":{"tf":1.0},"857":{"tf":2.8284271247461903},"858":{"tf":2.23606797749979},"859":{"tf":1.4142135623730951},"860":{"tf":1.7320508075688772},"861":{"tf":2.0},"862":{"tf":2.0},"863":{"tf":2.23606797749979},"864":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"867":{"tf":1.4142135623730951},"868":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.7320508075688772},"929":{"tf":1.0},"932":{"tf":1.0},"944":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":1,"docs":{"191":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{":":{":":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"140":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":2,"docs":{"137":{"tf":1.0},"149":{"tf":1.4142135623730951}}}}}}}}},"d":{"df":0,"docs":{},"e":{"df":15,"docs":{"1014":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.4142135623730951},"208":{"tf":1.0},"569":{"tf":1.0},"574":{"tf":1.0},"727":{"tf":1.0},"745":{"tf":1.0},"776":{"tf":1.7320508075688772},"779":{"tf":1.0},"942":{"tf":1.0},"943":{"tf":1.0},"949":{"tf":1.0},"956":{"tf":1.0},"959":{"tf":1.0}},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":2,"docs":{"412":{"tf":1.0},"426":{"tf":1.0}}}}},"r":{"df":1,"docs":{"423":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"c":{"df":5,"docs":{"257":{"tf":1.4142135623730951},"365":{"tf":1.0},"507":{"tf":1.4142135623730951},"554":{"tf":1.0},"912":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"435":{"tf":1.0}}},"t":{"df":8,"docs":{"180":{"tf":1.4142135623730951},"205":{"tf":1.4142135623730951},"22":{"tf":1.0},"24":{"tf":2.0},"402":{"tf":1.0},"814":{"tf":1.4142135623730951},"83":{"tf":1.0},"931":{"tf":1.0}}}},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"'":{"df":1,"docs":{"619":{"tf":1.0}}},"df":95,"docs":{"12":{"tf":1.0},"164":{"tf":1.0},"166":{"tf":1.4142135623730951},"169":{"tf":2.0},"170":{"tf":1.7320508075688772},"171":{"tf":2.6457513110645907},"177":{"tf":1.4142135623730951},"220":{"tf":1.0},"231":{"tf":2.449489742783178},"232":{"tf":1.0},"234":{"tf":1.0},"284":{"tf":1.4142135623730951},"286":{"tf":1.0},"291":{"tf":1.4142135623730951},"296":{"tf":1.0},"346":{"tf":1.4142135623730951},"362":{"tf":1.4142135623730951},"372":{"tf":1.0},"380":{"tf":1.0},"39":{"tf":1.4142135623730951},"44":{"tf":1.4142135623730951},"459":{"tf":1.0},"46":{"tf":1.4142135623730951},"481":{"tf":2.449489742783178},"482":{"tf":2.0},"483":{"tf":2.8284271247461903},"484":{"tf":1.0},"485":{"tf":2.23606797749979},"486":{"tf":1.7320508075688772},"487":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"490":{"tf":1.0},"491":{"tf":1.4142135623730951},"492":{"tf":1.0},"493":{"tf":1.0},"494":{"tf":1.0},"514":{"tf":3.3166247903554},"521":{"tf":1.0},"523":{"tf":1.0},"530":{"tf":1.0},"531":{"tf":1.4142135623730951},"532":{"tf":1.7320508075688772},"535":{"tf":2.0},"536":{"tf":1.7320508075688772},"537":{"tf":3.1622776601683795},"538":{"tf":1.0},"539":{"tf":1.0},"540":{"tf":1.4142135623730951},"541":{"tf":1.0},"542":{"tf":1.7320508075688772},"543":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.7320508075688772},"546":{"tf":1.0},"547":{"tf":1.0},"548":{"tf":1.4142135623730951},"574":{"tf":1.4142135623730951},"584":{"tf":2.23606797749979},"585":{"tf":1.4142135623730951},"586":{"tf":2.8284271247461903},"587":{"tf":1.0},"588":{"tf":2.6457513110645907},"589":{"tf":1.4142135623730951},"590":{"tf":1.0},"591":{"tf":1.4142135623730951},"592":{"tf":1.0},"593":{"tf":1.0},"594":{"tf":1.4142135623730951},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"613":{"tf":2.23606797749979},"614":{"tf":1.7320508075688772},"615":{"tf":2.449489742783178},"616":{"tf":1.0},"617":{"tf":2.0},"618":{"tf":1.0},"619":{"tf":2.0},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.4142135623730951},"623":{"tf":1.0},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"697":{"tf":1.7320508075688772},"699":{"tf":2.0},"700":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.4142135623730951},"876":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"'":{"df":1,"docs":{"514":{"tf":1.0}}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"171":{"tf":1.0}},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{")":{".":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"171":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"390":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":4,"docs":{"171":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.0},"546":{"tf":1.0}}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"383":{"tf":1.0},"385":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"(":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"205":{"tf":1.0}}}}}}}}},"df":49,"docs":{"203":{"tf":1.7320508075688772},"204":{"tf":1.0},"205":{"tf":1.4142135623730951},"208":{"tf":1.0},"3":{"tf":2.0},"38":{"tf":1.0},"406":{"tf":1.0},"48":{"tf":1.7320508075688772},"520":{"tf":1.0},"598":{"tf":1.4142135623730951},"599":{"tf":2.449489742783178},"6":{"tf":1.0},"600":{"tf":3.872983346207417},"602":{"tf":5.385164807134504},"603":{"tf":3.1622776601683795},"605":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":1.0},"692":{"tf":2.23606797749979},"693":{"tf":1.4142135623730951},"694":{"tf":2.449489742783178},"695":{"tf":1.0},"696":{"tf":2.0},"697":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.0},"700":{"tf":1.4142135623730951},"701":{"tf":1.4142135623730951},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.4142135623730951},"705":{"tf":1.4142135623730951},"706":{"tf":1.4142135623730951},"707":{"tf":1.0},"708":{"tf":1.0},"715":{"tf":1.0},"722":{"tf":1.0},"759":{"tf":1.0},"776":{"tf":1.4142135623730951},"80":{"tf":1.0},"81":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"932":{"tf":1.7320508075688772},"945":{"tf":1.0},"988":{"tf":1.0},"989":{"tf":1.0},"996":{"tf":1.0}},"r":{"df":2,"docs":{"221":{"tf":1.0},"776":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":5,"docs":{"19":{"tf":1.0},"38":{"tf":1.0},"519":{"tf":1.0},"532":{"tf":1.0},"786":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"t":{"df":12,"docs":{"148":{"tf":1.0},"172":{"tf":1.0},"203":{"tf":1.0},"363":{"tf":1.0},"368":{"tf":2.23606797749979},"46":{"tf":1.0},"575":{"tf":1.0},"759":{"tf":1.0},"778":{"tf":1.0},"837":{"tf":1.0},"871":{"tf":1.0},"879":{"tf":1.4142135623730951}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"567":{"tf":1.0}}}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"28":{"tf":1.4142135623730951}}}},"t":{"df":2,"docs":{"439":{"tf":1.0},"517":{"tf":1.0}}}}},"p":{"a":{"df":0,"docs":{},"r":{"df":4,"docs":{"602":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":4,"docs":{"627":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":1.4142135623730951},"651":{"tf":1.0}}}}}}}},"p":{"df":7,"docs":{"653":{"tf":1.0},"656":{"tf":1.0},"663":{"tf":1.0},"666":{"tf":1.4142135623730951},"668":{"tf":1.0},"670":{"tf":1.0},"735":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"78":{"tf":1.0}}}}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"184":{"tf":1.0}},"i":{"df":27,"docs":{"111":{"tf":1.0},"121":{"tf":1.0},"184":{"tf":1.0},"185":{"tf":1.0},"188":{"tf":1.0},"231":{"tf":1.0},"232":{"tf":1.0},"233":{"tf":1.0},"236":{"tf":1.0},"264":{"tf":1.0},"267":{"tf":3.1622776601683795},"273":{"tf":1.0},"316":{"tf":1.4142135623730951},"370":{"tf":1.0},"375":{"tf":1.0},"468":{"tf":1.0},"81":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.4142135623730951},"852":{"tf":1.0},"881":{"tf":1.0},"889":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.4142135623730951},"933":{"tf":1.4142135623730951},"937":{"tf":1.0}}},"y":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"933":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"t":{"df":8,"docs":{"127":{"tf":1.0},"208":{"tf":1.0},"24":{"tf":1.0},"308":{"tf":1.0},"312":{"tf":1.0},"63":{"tf":1.0},"69":{"tf":1.0},"729":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":11,"docs":{"439":{"tf":1.4142135623730951},"49":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.4142135623730951},"519":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0},"525":{"tf":3.3166247903554},"528":{"tf":1.0},"634":{"tf":1.0},"78":{"tf":1.7320508075688772}}},"n":{"d":{"df":2,"docs":{"184":{"tf":1.4142135623730951},"194":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"497":{"tf":1.0}}}},"df":17,"docs":{"128":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"292":{"tf":1.0},"436":{"tf":1.4142135623730951},"453":{"tf":1.0},"497":{"tf":1.0},"553":{"tf":1.0},"599":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"761":{"tf":1.4142135623730951},"777":{"tf":1.0},"843":{"tf":1.0},"895":{"tf":1.0},"898":{"tf":1.4142135623730951},"935":{"tf":1.0}},"e":{"df":11,"docs":{"163":{"tf":1.0},"249":{"tf":1.0},"402":{"tf":2.0},"436":{"tf":1.0},"44":{"tf":1.4142135623730951},"46":{"tf":1.0},"49":{"tf":1.0},"54":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":3.872983346207417},"762":{"tf":1.0}}},"g":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"427":{"tf":1.0},"450":{"tf":1.0},"571":{"tf":1.0}}}}}},"m":{"df":1,"docs":{"208":{"tf":1.0}}},"p":{"df":1,"docs":{"758":{"tf":1.0}},"l":{"df":1,"docs":{"752":{"tf":1.0}}}},"v":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":3,"docs":{"207":{"tf":1.4142135623730951},"296":{"tf":1.0},"842":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":1,"docs":{"797":{"tf":1.0}}}},"u":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"249":{"tf":1.0}},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"450":{"tf":1.0}}}}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"e":{"df":8,"docs":{"439":{"tf":1.4142135623730951},"522":{"tf":1.0},"6":{"tf":1.0},"636":{"tf":1.0},"721":{"tf":1.0},"761":{"tf":2.0},"777":{"tf":1.0},"97":{"tf":1.0}}},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"761":{"tf":1.0},"763":{"tf":1.7320508075688772}}}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"t":{"df":28,"docs":{"121":{"tf":1.0},"198":{"tf":1.0},"231":{"tf":1.7320508075688772},"254":{"tf":1.0},"262":{"tf":1.0},"45":{"tf":1.0},"46":{"tf":1.0},"513":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"528":{"tf":1.0},"532":{"tf":1.0},"567":{"tf":1.7320508075688772},"6":{"tf":1.0},"603":{"tf":1.0},"629":{"tf":1.4142135623730951},"692":{"tf":1.0},"693":{"tf":1.0},"697":{"tf":1.4142135623730951},"698":{"tf":1.4142135623730951},"700":{"tf":1.0},"8":{"tf":1.0},"84":{"tf":2.0},"848":{"tf":1.0},"852":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.4142135623730951},"95":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"46":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"198":{"tf":1.0},"46":{"tf":1.0}}}}}}}}}},"t":{"df":0,"docs":{},"h":{"df":2,"docs":{"6":{"tf":1.0},"777":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"852":{"tf":1.0}}}},"df":0,"docs":{}},"n":{"df":0,"docs":{},"e":{"df":2,"docs":{"428":{"tf":1.0},"773":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"df":2,"docs":{"455":{"tf":1.0},"522":{"tf":2.0}},"e":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"<":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"r":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"244":{"tf":1.0}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"n":{"df":7,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"40":{"tf":1.0},"49":{"tf":1.0},"722":{"tf":1.4142135623730951},"799":{"tf":1.0},"912":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":3,"docs":{"797":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0}}}}}}}},"w":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":4,"docs":{"342":{"tf":1.0},"735":{"tf":1.0},"926":{"tf":1.0},"928":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"c":{"df":0,"docs":{},"e":{"df":4,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"71":{"tf":1.0},"732":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"842":{"tf":1.0}}}}}}},"o":{"df":64,"docs":{"112":{"tf":1.0},"113":{"tf":1.0},"149":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"203":{"tf":1.0},"204":{"tf":1.4142135623730951},"205":{"tf":2.0},"22":{"tf":1.0},"220":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.4142135623730951},"264":{"tf":1.0},"284":{"tf":1.0},"3":{"tf":1.0},"340":{"tf":1.0},"348":{"tf":1.0},"35":{"tf":1.4142135623730951},"350":{"tf":1.0},"373":{"tf":1.0},"39":{"tf":1.0},"402":{"tf":1.0},"45":{"tf":1.0},"482":{"tf":1.0},"483":{"tf":1.0},"485":{"tf":1.4142135623730951},"491":{"tf":1.0},"512":{"tf":1.0},"515":{"tf":1.0},"525":{"tf":1.4142135623730951},"564":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"63":{"tf":1.0},"635":{"tf":1.0},"650":{"tf":1.0},"66":{"tf":1.0},"694":{"tf":1.0},"698":{"tf":1.0},"699":{"tf":1.4142135623730951},"711":{"tf":1.0},"716":{"tf":1.0},"724":{"tf":1.0},"735":{"tf":1.4142135623730951},"736":{"tf":1.0},"739":{"tf":1.0},"747":{"tf":1.0},"759":{"tf":1.7320508075688772},"761":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0},"786":{"tf":1.0},"814":{"tf":1.4142135623730951},"829":{"tf":1.0},"84":{"tf":1.0},"894":{"tf":1.0},"927":{"tf":1.0},"931":{"tf":1.4142135623730951},"932":{"tf":1.0}},"x":{"6":{"4":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"c":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"817":{"tf":1.0},"880":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"y":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"u":{"b":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":1,"docs":{"524":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"b":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{".":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"df":1,"docs":{"524":{"tf":2.23606797749979}}}}}}},"df":3,"docs":{"22":{"tf":2.23606797749979},"522":{"tf":1.0},"524":{"tf":1.7320508075688772}},"p":{"df":0,"docs":{},"e":{"'":{"df":1,"docs":{"524":{"tf":1.0}}},"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}}}},"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"520":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"522":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"522":{"tf":1.7320508075688772}}}}},"df":80,"docs":{"1011":{"tf":1.0},"140":{"tf":1.0},"166":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":1.4142135623730951},"19":{"tf":1.4142135623730951},"195":{"tf":1.0},"203":{"tf":1.4142135623730951},"204":{"tf":1.0},"208":{"tf":3.7416573867739413},"215":{"tf":1.4142135623730951},"22":{"tf":2.8284271247461903},"220":{"tf":1.4142135623730951},"221":{"tf":1.7320508075688772},"222":{"tf":1.4142135623730951},"24":{"tf":3.7416573867739413},"25":{"tf":1.4142135623730951},"26":{"tf":1.0},"272":{"tf":1.0},"30":{"tf":1.0},"322":{"tf":1.4142135623730951},"332":{"tf":1.4142135623730951},"333":{"tf":1.0},"334":{"tf":1.7320508075688772},"341":{"tf":1.0},"342":{"tf":1.0},"346":{"tf":1.0},"362":{"tf":1.0},"372":{"tf":1.0},"455":{"tf":2.0},"483":{"tf":1.0},"5":{"tf":1.7320508075688772},"513":{"tf":1.4142135623730951},"519":{"tf":2.8284271247461903},"520":{"tf":2.0},"521":{"tf":3.3166247903554},"522":{"tf":7.416198487095663},"523":{"tf":4.358898943540674},"524":{"tf":4.0},"525":{"tf":1.0},"528":{"tf":1.0},"534":{"tf":1.7320508075688772},"535":{"tf":1.0},"536":{"tf":1.0},"537":{"tf":2.8284271247461903},"539":{"tf":2.23606797749979},"542":{"tf":1.4142135623730951},"544":{"tf":1.0},"545":{"tf":1.0},"548":{"tf":1.0},"56":{"tf":1.0},"588":{"tf":1.0},"598":{"tf":1.4142135623730951},"599":{"tf":1.7320508075688772},"6":{"tf":1.4142135623730951},"600":{"tf":2.0},"602":{"tf":2.449489742783178},"603":{"tf":1.7320508075688772},"605":{"tf":1.4142135623730951},"609":{"tf":1.0},"61":{"tf":1.4142135623730951},"649":{"tf":1.0},"650":{"tf":1.0},"651":{"tf":1.4142135623730951},"653":{"tf":1.0},"668":{"tf":1.4142135623730951},"705":{"tf":1.0},"73":{"tf":1.0},"761":{"tf":1.0},"777":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"793":{"tf":1.4142135623730951},"814":{"tf":2.23606797749979},"815":{"tf":1.0},"817":{"tf":1.0},"84":{"tf":1.0},"880":{"tf":1.4142135623730951},"912":{"tf":1.0},"933":{"tf":2.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"524":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"_":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"(":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"524":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{}},"df":5,"docs":{"513":{"tf":1.0},"519":{"tf":1.0},"521":{"tf":2.8284271247461903},"522":{"tf":2.23606797749979},"524":{"tf":2.6457513110645907}}}}}},"i":{"c":{"df":10,"docs":{"218":{"tf":1.0},"249":{"tf":1.0},"253":{"tf":1.0},"407":{"tf":1.0},"44":{"tf":1.0},"470":{"tf":1.0},"522":{"tf":1.0},"735":{"tf":1.0},"762":{"tf":1.0},"81":{"tf":1.0}}},"df":0,"docs":{}}}},"}":{"\\":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{")":{"^":{"df":0,"docs":{},"u":{"df":1,"docs":{"749":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"{":{"df":0,"docs":{},"l":{"df":1,"docs":{"749":{"tf":1.0}}}}},"·":{"a":{"df":0,"docs":{},"·":{"df":0,"docs":{},"n":{"df":1,"docs":{"346":{"tf":1.0}}}}},"df":0,"docs":{}}},"u":{".":{"df":1,"docs":{"470":{"tf":1.0}}},"1":{"2":{"8":{"df":1,"docs":{"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"df":8,"docs":{"208":{"tf":1.4142135623730951},"221":{"tf":1.4142135623730951},"222":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"83":{"tf":1.0},"885":{"tf":1.0}}},"df":0,"docs":{}},"2":{"5":{"6":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"3":{"2":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"814":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":13,"docs":{"204":{"tf":1.0},"208":{"tf":2.0},"24":{"tf":1.7320508075688772},"25":{"tf":1.7320508075688772},"438":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":1.7320508075688772},"634":{"tf":1.0},"715":{"tf":1.7320508075688772},"716":{"tf":1.4142135623730951},"83":{"tf":1.0},"879":{"tf":2.0},"880":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"404":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":7,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.4142135623730951},"25":{"tf":2.23606797749979},"404":{"tf":1.0},"455":{"tf":1.4142135623730951},"522":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"8":{";":{"2":{"0":{"df":1,"docs":{"898":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":13,"docs":{"208":{"tf":1.0},"23":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"455":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.7320508075688772},"526":{"tf":1.0},"588":{"tf":1.0},"633":{"tf":1.4142135623730951},"634":{"tf":1.7320508075688772},"885":{"tf":1.0},"97":{"tf":1.7320508075688772}}},"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":6,"docs":{"195":{"tf":1.0},"198":{"tf":1.4142135623730951},"199":{"tf":1.0},"215":{"tf":1.0},"216":{"tf":1.0},"368":{"tf":1.0}}}}}}}},"c":{"'":{"df":1,"docs":{"772":{"tf":1.0}}},"df":11,"docs":{"198":{"tf":1.0},"200":{"tf":2.23606797749979},"203":{"tf":1.0},"204":{"tf":1.0},"210":{"tf":1.0},"264":{"tf":1.0},"742":{"tf":1.0},"773":{"tf":1.4142135623730951},"776":{"tf":1.0},"777":{"tf":1.0},"778":{"tf":1.0}}},"df":3,"docs":{"721":{"tf":2.0},"722":{"tf":1.7320508075688772},"749":{"tf":1.0}},"i":{"/":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"518":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":13,"docs":{"125":{"tf":1.0},"152":{"tf":1.4142135623730951},"18":{"tf":1.0},"19":{"tf":1.4142135623730951},"191":{"tf":1.0},"276":{"tf":1.0},"369":{"tf":1.0},"461":{"tf":1.0},"514":{"tf":1.0},"564":{"tf":1.0},"574":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0}}},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":13,"docs":{"126":{"tf":1.0},"187":{"tf":1.0},"270":{"tf":1.0},"517":{"tf":1.0},"568":{"tf":1.0},"650":{"tf":1.0},"694":{"tf":1.0},"696":{"tf":1.0},"697":{"tf":1.0},"700":{"tf":1.0},"773":{"tf":1.0},"797":{"tf":1.0},"849":{"tf":1.4142135623730951}}}}}},"m":{"df":0,"docs":{},"p":{"df":14,"docs":{"203":{"tf":1.0},"215":{"tf":1.0},"220":{"tf":1.0},"221":{"tf":1.4142135623730951},"56":{"tf":1.0},"61":{"tf":2.0},"627":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":2.0},"640":{"tf":1.0},"645":{"tf":1.4142135623730951},"72":{"tf":1.0},"73":{"tf":1.0},"77":{"tf":1.0}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"l":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"633":{"tf":1.0},"636":{"tf":1.0},"641":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":2,"docs":{"61":{"tf":1.0},"633":{"tf":2.449489742783178}}}}}}}},"n":{"a":{"b":{"df":0,"docs":{},"l":{"df":3,"docs":{"300":{"tf":1.4142135623730951},"303":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"570":{"tf":1.0}}}},"df":0,"docs":{}}}},"m":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":1,"docs":{"735":{"tf":1.0}}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":3,"docs":{"30":{"tf":1.0},"944":{"tf":1.0},"945":{"tf":1.0}},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"879":{"tf":2.23606797749979}}}}}}},"df":0,"docs":{}}}}}}}}},"v":{"df":0,"docs":{},"o":{"df":0,"docs":{},"i":{"d":{"df":2,"docs":{"721":{"tf":1.0},"84":{"tf":1.0}}},"df":0,"docs":{}}}},"w":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":0,"docs":{}}},"b":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"s":{"df":2,"docs":{"336":{"tf":1.0},"346":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"n":{"d":{"df":21,"docs":{"563":{"tf":2.6457513110645907},"564":{"tf":3.3166247903554},"565":{"tf":2.449489742783178},"566":{"tf":1.0},"567":{"tf":2.6457513110645907},"568":{"tf":3.3166247903554},"569":{"tf":2.449489742783178},"570":{"tf":2.8284271247461903},"571":{"tf":4.242640687119285},"572":{"tf":1.0},"573":{"tf":3.3166247903554},"574":{"tf":2.23606797749979},"575":{"tf":2.23606797749979},"576":{"tf":3.1622776601683795},"577":{"tf":2.0},"578":{"tf":1.0},"579":{"tf":1.0},"580":{"tf":1.0},"581":{"tf":1.0},"582":{"tf":1.0},"583":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"_":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"b":{"df":2,"docs":{"568":{"tf":1.4142135623730951},"573":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"a":{"df":2,"docs":{"568":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"348":{"tf":1.0},"879":{"tf":1.0},"881":{"tf":1.0}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":16,"docs":{"106":{"tf":2.449489742783178},"107":{"tf":1.4142135623730951},"108":{"tf":1.4142135623730951},"109":{"tf":1.0},"110":{"tf":1.0},"111":{"tf":2.6457513110645907},"112":{"tf":3.0},"113":{"tf":2.0},"114":{"tf":1.0},"115":{"tf":1.0},"116":{"tf":1.0},"117":{"tf":1.0},"118":{"tf":1.4142135623730951},"119":{"tf":1.0},"120":{"tf":1.4142135623730951},"121":{"tf":2.0}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":2,"docs":{"257":{"tf":1.0},"507":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"h":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":7,"docs":{"203":{"tf":1.0},"221":{"tf":1.0},"564":{"tf":1.0},"633":{"tf":1.0},"792":{"tf":1.0},"817":{"tf":1.0},"867":{"tf":1.0}}}}},"df":0,"docs":{}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"776":{"tf":1.0}}}}},"df":1,"docs":{"714":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":6,"docs":{"1014":{"tf":1.0},"51":{"tf":1.0},"727":{"tf":1.0},"739":{"tf":1.4142135623730951},"765":{"tf":1.0},"835":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"721":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}}}}}}},"d":{"df":1,"docs":{"741":{"tf":1.0}},"e":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"152":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":3,"docs":{"341":{"tf":1.4142135623730951},"6":{"tf":1.7320508075688772},"7":{"tf":1.7320508075688772}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"_":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"799":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":2,"docs":{"796":{"tf":1.0},"799":{"tf":1.7320508075688772}}}}},"r":{"c":{"a":{"df":0,"docs":{},"p":{"a":{"c":{"df":1,"docs":{"776":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"568":{"tf":1.0}}}}},"df":24,"docs":{"151":{"tf":1.7320508075688772},"154":{"tf":1.7320508075688772},"207":{"tf":1.0},"221":{"tf":1.0},"235":{"tf":1.0},"267":{"tf":1.0},"387":{"tf":1.0},"437":{"tf":1.0},"47":{"tf":1.0},"48":{"tf":1.0},"501":{"tf":1.7320508075688772},"537":{"tf":1.4142135623730951},"568":{"tf":1.0},"575":{"tf":1.0},"602":{"tf":1.0},"710":{"tf":1.0},"721":{"tf":1.0},"724":{"tf":1.0},"754":{"tf":1.0},"799":{"tf":1.0},"811":{"tf":1.0},"817":{"tf":1.0},"878":{"tf":1.0},"954":{"tf":1.0}},"g":{"df":0,"docs":{},"o":{"df":4,"docs":{"337":{"tf":1.0},"354":{"tf":1.0},"53":{"tf":1.0},"778":{"tf":1.0}}}},"l":{"df":0,"docs":{},"i":{"df":5,"docs":{"124":{"tf":1.0},"152":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"651":{"tf":1.0}}}},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"779":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"267":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"711":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"804":{"tf":1.0},"84":{"tf":1.0},"927":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"217":{"tf":1.0},"221":{"tf":1.0}}},"df":0,"docs":{}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"375":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"267":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":3,"docs":{"763":{"tf":1.0},"863":{"tf":1.0},"919":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"323":{"tf":1.0}}}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"u":{"b":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"983":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"df":2,"docs":{"418":{"tf":1.0},"920":{"tf":1.0}}}},"df":1,"docs":{"284":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"722":{"tf":1.0}}}}},"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":2,"docs":{"435":{"tf":1.0},"436":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"o":{"c":{"df":1,"docs":{"272":{"tf":1.0}}},"df":0,"docs":{}}}}}},"x":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"343":{"tf":1.0},"975":{"tf":1.0}}}},"df":0,"docs":{}}}}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":8,"docs":{"1004":{"tf":1.0},"390":{"tf":1.0},"483":{"tf":1.0},"500":{"tf":1.0},"600":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"832":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"z":{"df":1,"docs":{"573":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":5,"docs":{"18":{"tf":1.0},"19":{"tf":1.0},"293":{"tf":1.0},"576":{"tf":1.0},"784":{"tf":1.0}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":3,"docs":{"374":{"tf":1.0},"776":{"tf":1.0},"777":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"438":{"tf":1.0}}}}}}}},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":1,"docs":{"718":{"tf":1.0}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"450":{"tf":1.0}}}}}}},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"111":{"tf":1.0},"429":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"44":{"tf":1.0}}}}}}}}}},"q":{"df":0,"docs":{},"u":{"df":14,"docs":{"147":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.4142135623730951},"218":{"tf":1.0},"338":{"tf":1.0},"414":{"tf":1.0},"429":{"tf":1.0},"515":{"tf":1.0},"521":{"tf":1.7320508075688772},"522":{"tf":1.7320508075688772},"524":{"tf":2.449489742783178},"525":{"tf":1.0},"810":{"tf":1.0},"880":{"tf":1.0}}}},"t":{"df":11,"docs":{"209":{"tf":1.0},"211":{"tf":1.0},"237":{"tf":1.0},"479":{"tf":1.0},"639":{"tf":1.0},"776":{"tf":1.0},"788":{"tf":1.0},"846":{"tf":1.0},"945":{"tf":1.0},"947":{"tf":1.0},"964":{"tf":1.0}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"+":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":1,"docs":{"786":{"tf":1.4142135623730951}}}}}}}}}},"df":2,"docs":{"18":{"tf":1.0},"786":{"tf":1.0}}}}}},"x":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"553":{"tf":1.4142135623730951}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":9,"docs":{"195":{"tf":1.0},"213":{"tf":1.7320508075688772},"215":{"tf":1.0},"227":{"tf":1.4142135623730951},"38":{"tf":1.0},"402":{"tf":1.0},"510":{"tf":1.0},"55":{"tf":1.4142135623730951},"635":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"944":{"tf":1.0}}}}}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"206":{"tf":1.0},"44":{"tf":1.0},"875":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"k":{"df":3,"docs":{"204":{"tf":1.0},"234":{"tf":1.0},"939":{"tf":1.0}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.0}}}}}},"o":{"c":{"df":0,"docs":{},"k":{"df":8,"docs":{"108":{"tf":1.0},"112":{"tf":2.0},"198":{"tf":1.0},"296":{"tf":1.0},"300":{"tf":1.7320508075688772},"301":{"tf":2.0},"302":{"tf":1.0},"308":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":6,"docs":{"267":{"tf":1.0},"44":{"tf":1.0},"483":{"tf":1.0},"576":{"tf":1.0},"951":{"tf":1.0},"982":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":2,"docs":{"763":{"tf":1.0},"917":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{},"e":{"d":{"df":1,"docs":{"874":{"tf":1.0}}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"615":{"tf":1.0}},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"267":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"111":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"255":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"199":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":4,"docs":{"199":{"tf":1.0},"200":{"tf":1.0},"385":{"tf":1.0},"432":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"362":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"809":{"tf":1.0}}}}}},"l":{"df":3,"docs":{"513":{"tf":1.0},"519":{"tf":1.0},"523":{"tf":1.4142135623730951}},"e":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"705":{"tf":1.0}}}},"df":0,"docs":{}},"i":{"df":1,"docs":{"852":{"tf":1.0}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":110,"docs":{"1":{"tf":1.0},"1000":{"tf":1.4142135623730951},"1002":{"tf":1.0},"1014":{"tf":1.4142135623730951},"106":{"tf":1.0},"121":{"tf":1.4142135623730951},"122":{"tf":1.0},"134":{"tf":1.4142135623730951},"136":{"tf":1.0},"148":{"tf":1.4142135623730951},"15":{"tf":1.4142135623730951},"150":{"tf":1.0},"162":{"tf":1.4142135623730951},"164":{"tf":1.0},"17":{"tf":1.0},"180":{"tf":1.4142135623730951},"182":{"tf":1.0},"193":{"tf":1.4142135623730951},"229":{"tf":1.0},"245":{"tf":1.4142135623730951},"247":{"tf":1.0},"261":{"tf":1.4142135623730951},"268":{"tf":1.0},"278":{"tf":1.4142135623730951},"279":{"tf":1.0},"292":{"tf":1.4142135623730951},"294":{"tf":1.0},"309":{"tf":1.4142135623730951},"311":{"tf":1.0},"320":{"tf":1.4142135623730951},"322":{"tf":1.0},"36":{"tf":1.4142135623730951},"360":{"tf":1.4142135623730951},"366":{"tf":1.0},"384":{"tf":1.4142135623730951},"386":{"tf":1.0},"398":{"tf":1.4142135623730951},"410":{"tf":1.0},"425":{"tf":1.7320508075688772},"430":{"tf":1.0},"448":{"tf":1.4142135623730951},"451":{"tf":1.0},"463":{"tf":1.4142135623730951},"465":{"tf":1.0},"480":{"tf":1.4142135623730951},"481":{"tf":1.0},"493":{"tf":1.4142135623730951},"495":{"tf":1.0},"511":{"tf":1.4142135623730951},"513":{"tf":1.0},"533":{"tf":1.4142135623730951},"535":{"tf":1.0},"547":{"tf":1.4142135623730951},"549":{"tf":1.0},"56":{"tf":1.0},"561":{"tf":1.4142135623730951},"584":{"tf":1.0},"596":{"tf":1.4142135623730951},"598":{"tf":1.0},"611":{"tf":1.4142135623730951},"613":{"tf":1.0},"625":{"tf":1.4142135623730951},"627":{"tf":1.0},"647":{"tf":1.4142135623730951},"649":{"tf":1.0},"662":{"tf":1.4142135623730951},"664":{"tf":1.0},"676":{"tf":1.4142135623730951},"678":{"tf":1.0},"690":{"tf":1.4142135623730951},"692":{"tf":1.0},"707":{"tf":1.4142135623730951},"709":{"tf":1.0},"727":{"tf":1.4142135623730951},"730":{"tf":1.0},"739":{"tf":1.4142135623730951},"75":{"tf":1.4142135623730951},"757":{"tf":1.0},"769":{"tf":1.4142135623730951},"771":{"tf":1.0},"781":{"tf":1.4142135623730951},"782":{"tf":1.0},"79":{"tf":1.0},"794":{"tf":1.4142135623730951},"795":{"tf":1.0},"806":{"tf":1.4142135623730951},"808":{"tf":1.0},"825":{"tf":1.4142135623730951},"827":{"tf":1.0},"839":{"tf":1.4142135623730951},"841":{"tf":1.0},"856":{"tf":1.4142135623730951},"857":{"tf":1.0},"870":{"tf":1.4142135623730951},"871":{"tf":1.0},"889":{"tf":1.4142135623730951},"891":{"tf":1.0},"906":{"tf":1.4142135623730951},"908":{"tf":1.0},"91":{"tf":1.4142135623730951},"924":{"tf":1.4142135623730951},"926":{"tf":1.0},"938":{"tf":1.4142135623730951},"940":{"tf":1.0},"955":{"tf":1.4142135623730951},"957":{"tf":1.0},"972":{"tf":1.4142135623730951},"974":{"tf":1.0},"986":{"tf":1.4142135623730951},"988":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"350":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"a":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"y":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"349":{"tf":1.0}}}},"t":{"df":2,"docs":{"349":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{},"g":{"df":1,"docs":{"204":{"tf":1.0}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":9,"docs":{"166":{"tf":1.0},"177":{"tf":1.0},"332":{"tf":2.449489742783178},"333":{"tf":1.4142135623730951},"347":{"tf":1.0},"404":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.0},"545":{"tf":1.0}},"e":{"d":{"3":{"2":{"df":3,"docs":{"332":{"tf":1.0},"342":{"tf":1.0},"349":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":4,"docs":{"332":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":1.0},"347":{"tf":1.0}}},"<":{"1":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}},"3":{"2":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":1,"docs":{"332":{"tf":1.0}}},"df":0,"docs":{},"n":{"df":1,"docs":{"332":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"573":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"d":{"df":3,"docs":{"776":{"tf":1.4142135623730951},"913":{"tf":1.0},"917":{"tf":1.0}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"205":{"tf":1.4142135623730951}}}}}},"t":{"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"370":{"tf":1.0},"564":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"5":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":26,"docs":{"126":{"tf":1.0},"138":{"tf":1.0},"155":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":2.0},"255":{"tf":1.0},"301":{"tf":1.0},"323":{"tf":1.0},"436":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.0},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"551":{"tf":1.0},"553":{"tf":1.0},"573":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0},"648":{"tf":1.0},"72":{"tf":1.0},"735":{"tf":1.0},"829":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0}}}},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"253":{"tf":1.4142135623730951}}}}}}},"u":{"df":0,"docs":{},"s":{"df":9,"docs":{"206":{"tf":1.0},"254":{"tf":1.0},"346":{"tf":1.0},"401":{"tf":1.0},"517":{"tf":1.0},"627":{"tf":1.0},"631":{"tf":1.0},"632":{"tf":1.4142135623730951},"638":{"tf":1.0}}}},"w":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":6,"docs":{"115":{"tf":1.0},"123":{"tf":1.0},"128":{"tf":1.0},"134":{"tf":1.0},"304":{"tf":1.0},"788":{"tf":1.0}}}}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}}},"p":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":5,"docs":{"208":{"tf":1.0},"60":{"tf":1.0},"743":{"tf":1.0},"776":{"tf":1.0},"914":{"tf":1.0}}}}},"d":{"a":{"df":0,"docs":{},"t":{"df":57,"docs":{"1003":{"tf":1.4142135623730951},"108":{"tf":1.0},"111":{"tf":1.4142135623730951},"121":{"tf":1.0},"125":{"tf":1.0},"154":{"tf":1.0},"191":{"tf":1.4142135623730951},"208":{"tf":1.7320508075688772},"237":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.4142135623730951},"290":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.4142135623730951},"3":{"tf":1.4142135623730951},"300":{"tf":1.0},"313":{"tf":1.0},"316":{"tf":1.0},"344":{"tf":1.0},"352":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"39":{"tf":1.0},"391":{"tf":1.0},"44":{"tf":1.0},"441":{"tf":1.0},"456":{"tf":1.0},"461":{"tf":1.7320508075688772},"465":{"tf":1.0},"472":{"tf":1.7320508075688772},"515":{"tf":1.0},"535":{"tf":1.0},"544":{"tf":1.0},"565":{"tf":1.0},"58":{"tf":1.0},"6":{"tf":1.4142135623730951},"60":{"tf":1.0},"63":{"tf":1.0},"645":{"tf":1.0},"7":{"tf":1.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":1.0},"742":{"tf":1.0},"78":{"tf":1.4142135623730951},"831":{"tf":1.0},"832":{"tf":1.0},"837":{"tf":1.7320508075688772},"848":{"tf":1.0},"878":{"tf":1.0},"879":{"tf":1.0},"904":{"tf":1.0},"921":{"tf":1.0},"928":{"tf":1.0},"937":{"tf":1.0},"965":{"tf":1.0},"973":{"tf":1.0}},"e":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"237":{"tf":1.0}}}}}}}}}}},"df":0,"docs":{}},"df":55,"docs":{"124":{"tf":1.0},"140":{"tf":1.4142135623730951},"184":{"tf":1.0},"198":{"tf":1.0},"200":{"tf":1.0},"208":{"tf":1.0},"234":{"tf":1.4142135623730951},"249":{"tf":1.0},"255":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.0},"315":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"368":{"tf":1.0},"375":{"tf":1.4142135623730951},"436":{"tf":1.0},"444":{"tf":1.0},"45":{"tf":1.0},"5":{"tf":1.0},"500":{"tf":1.4142135623730951},"505":{"tf":1.0},"515":{"tf":1.0},"518":{"tf":1.0},"521":{"tf":1.0},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.4142135623730951},"564":{"tf":1.0},"567":{"tf":1.0},"569":{"tf":1.0},"57":{"tf":1.0},"571":{"tf":1.0},"574":{"tf":1.4142135623730951},"583":{"tf":1.0},"629":{"tf":1.0},"650":{"tf":1.0},"700":{"tf":1.0},"712":{"tf":1.0},"723":{"tf":1.0},"73":{"tf":1.0},"747":{"tf":1.0},"768":{"tf":1.0},"77":{"tf":1.0},"794":{"tf":1.0},"797":{"tf":1.4142135623730951},"829":{"tf":1.0},"842":{"tf":1.0},"848":{"tf":1.0},"850":{"tf":1.0},"858":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0},"912":{"tf":1.0},"932":{"tf":1.0}},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":56,"docs":{"1012":{"tf":1.0},"104":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.0},"132":{"tf":1.0},"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.7320508075688772},"140":{"tf":1.4142135623730951},"144":{"tf":1.4142135623730951},"147":{"tf":1.0},"150":{"tf":1.0},"151":{"tf":1.7320508075688772},"152":{"tf":1.0},"154":{"tf":1.4142135623730951},"159":{"tf":1.0},"160":{"tf":1.0},"193":{"tf":1.0},"209":{"tf":1.4142135623730951},"24":{"tf":1.0},"241":{"tf":1.0},"300":{"tf":1.0},"315":{"tf":1.0},"358":{"tf":1.0},"408":{"tf":1.0},"430":{"tf":1.0},"438":{"tf":1.0},"440":{"tf":3.1622776601683795},"441":{"tf":1.0},"446":{"tf":1.4142135623730951},"515":{"tf":2.0},"56":{"tf":1.4142135623730951},"57":{"tf":1.7320508075688772},"58":{"tf":1.0},"60":{"tf":2.6457513110645907},"609":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.4142135623730951},"64":{"tf":1.4142135623730951},"642":{"tf":1.4142135623730951},"643":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"69":{"tf":1.4142135623730951},"705":{"tf":1.0},"71":{"tf":2.449489742783178},"72":{"tf":2.0},"729":{"tf":1.0},"73":{"tf":2.23606797749979},"74":{"tf":1.0},"75":{"tf":1.7320508075688772},"751":{"tf":1.0},"77":{"tf":1.7320508075688772},"78":{"tf":1.0},"817":{"tf":1.0},"887":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"467":{"tf":1.0}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":5,"docs":{"715":{"tf":1.0},"722":{"tf":1.0},"763":{"tf":1.0},"817":{"tf":1.0},"832":{"tf":1.0}},"e":{"d":{"_":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"715":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"n":{"df":13,"docs":{"198":{"tf":1.0},"203":{"tf":1.0},"314":{"tf":1.0},"356":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0},"721":{"tf":1.0},"722":{"tf":1.0},"725":{"tf":1.0},"773":{"tf":1.0},"810":{"tf":1.0},"928":{"tf":1.0}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"_":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":4,"docs":{"568":{"tf":2.0},"569":{"tf":1.0},"571":{"tf":1.0},"577":{"tf":1.0}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":3,"docs":{"436":{"tf":1.0},"51":{"tf":1.4142135623730951},"776":{"tf":1.0}}}}},"r":{"a":{"d":{"df":1,"docs":{"60":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"633":{"tf":1.0}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"54":{"tf":1.0}}},"df":0,"docs":{}}}},"i":{"df":1,"docs":{"735":{"tf":1.4142135623730951}}}},"s":{"a":{"b":{"df":0,"docs":{},"l":{"df":5,"docs":{"250":{"tf":1.0},"565":{"tf":1.0},"614":{"tf":1.0},"696":{"tf":1.0},"698":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":28,"docs":{"1011":{"tf":1.0},"154":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":2.23606797749979},"204":{"tf":1.0},"208":{"tf":1.0},"215":{"tf":1.4142135623730951},"218":{"tf":1.0},"22":{"tf":1.0},"223":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"267":{"tf":1.0},"28":{"tf":1.0},"407":{"tf":1.0},"428":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"52":{"tf":1.0},"598":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"696":{"tf":1.0},"700":{"tf":1.0},"722":{"tf":1.0},"758":{"tf":1.0},"913":{"tf":1.0},"938":{"tf":1.0},"996":{"tf":1.0}}}},"d":{"(":{"df":0,"docs":{},"x":{"df":2,"docs":{"410":{"tf":1.0},"429":{"tf":1.4142135623730951}}}},"df":2,"docs":{"429":{"tf":1.4142135623730951},"470":{"tf":1.4142135623730951}},"t":{"df":3,"docs":{"470":{"tf":1.7320508075688772},"600":{"tf":1.0},"699":{"tf":1.0}}}},"df":236,"docs":{"100":{"tf":1.0},"103":{"tf":1.0},"108":{"tf":1.4142135623730951},"111":{"tf":1.0},"121":{"tf":1.0},"124":{"tf":1.4142135623730951},"126":{"tf":1.0},"140":{"tf":1.4142135623730951},"149":{"tf":1.0},"151":{"tf":1.7320508075688772},"154":{"tf":1.0},"16":{"tf":1.4142135623730951},"160":{"tf":1.0},"163":{"tf":1.0},"170":{"tf":1.0},"171":{"tf":2.0},"177":{"tf":1.0},"18":{"tf":1.0},"180":{"tf":1.0},"19":{"tf":1.0},"191":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":2.0},"226":{"tf":1.0},"230":{"tf":1.0},"231":{"tf":1.4142135623730951},"24":{"tf":1.4142135623730951},"248":{"tf":1.4142135623730951},"249":{"tf":1.4142135623730951},"251":{"tf":1.0},"252":{"tf":1.7320508075688772},"253":{"tf":1.4142135623730951},"254":{"tf":2.0},"255":{"tf":1.0},"257":{"tf":1.0},"26":{"tf":1.4142135623730951},"261":{"tf":1.0},"281":{"tf":1.4142135623730951},"284":{"tf":1.4142135623730951},"3":{"tf":2.0},"30":{"tf":1.0},"303":{"tf":1.0},"331":{"tf":1.0},"333":{"tf":1.4142135623730951},"338":{"tf":1.0},"343":{"tf":1.0},"344":{"tf":1.7320508075688772},"345":{"tf":1.7320508075688772},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"349":{"tf":2.23606797749979},"35":{"tf":1.0},"350":{"tf":1.4142135623730951},"351":{"tf":1.0},"352":{"tf":1.0},"368":{"tf":1.0},"371":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.4142135623730951},"378":{"tf":1.0},"38":{"tf":1.0},"384":{"tf":1.0},"387":{"tf":2.0},"388":{"tf":1.4142135623730951},"39":{"tf":1.4142135623730951},"390":{"tf":2.449489742783178},"391":{"tf":1.0},"393":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":1.0},"415":{"tf":1.0},"420":{"tf":1.0},"428":{"tf":1.0},"432":{"tf":1.0},"435":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.7320508075688772},"44":{"tf":1.0},"440":{"tf":1.4142135623730951},"441":{"tf":1.4142135623730951},"444":{"tf":1.0},"45":{"tf":1.7320508075688772},"450":{"tf":1.0},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"46":{"tf":1.0},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"472":{"tf":1.0},"473":{"tf":1.0},"485":{"tf":1.0},"49":{"tf":1.0},"5":{"tf":1.4142135623730951},"50":{"tf":1.4142135623730951},"501":{"tf":1.4142135623730951},"51":{"tf":1.0},"511":{"tf":1.0},"512":{"tf":1.0},"514":{"tf":2.0},"516":{"tf":1.0},"519":{"tf":1.0},"52":{"tf":1.0},"520":{"tf":1.4142135623730951},"521":{"tf":2.449489742783178},"522":{"tf":1.7320508075688772},"524":{"tf":1.7320508075688772},"525":{"tf":1.7320508075688772},"526":{"tf":1.7320508075688772},"528":{"tf":1.4142135623730951},"530":{"tf":1.4142135623730951},"531":{"tf":1.0},"534":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":1.4142135623730951},"551":{"tf":1.0},"553":{"tf":1.7320508075688772},"559":{"tf":1.0},"567":{"tf":1.0},"568":{"tf":1.4142135623730951},"571":{"tf":1.7320508075688772},"588":{"tf":1.4142135623730951},"594":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":3.0},"600":{"tf":2.0},"602":{"tf":3.4641016151377544},"603":{"tf":1.0},"605":{"tf":1.0},"609":{"tf":1.4142135623730951},"61":{"tf":1.0},"615":{"tf":2.23606797749979},"617":{"tf":1.0},"619":{"tf":1.0},"62":{"tf":1.4142135623730951},"629":{"tf":1.0},"632":{"tf":1.0},"633":{"tf":2.6457513110645907},"634":{"tf":1.4142135623730951},"635":{"tf":1.4142135623730951},"637":{"tf":1.0},"64":{"tf":1.0},"642":{"tf":1.0},"643":{"tf":1.0},"648":{"tf":1.0},"65":{"tf":1.0},"650":{"tf":1.4142135623730951},"651":{"tf":1.7320508075688772},"653":{"tf":2.23606797749979},"654":{"tf":1.0},"660":{"tf":1.0},"665":{"tf":1.0},"666":{"tf":1.0},"67":{"tf":1.0},"680":{"tf":1.0},"688":{"tf":1.0},"69":{"tf":1.0},"693":{"tf":1.4142135623730951},"694":{"tf":1.4142135623730951},"696":{"tf":1.7320508075688772},"697":{"tf":1.7320508075688772},"699":{"tf":1.4142135623730951},"7":{"tf":1.0},"701":{"tf":1.4142135623730951},"705":{"tf":1.7320508075688772},"710":{"tf":1.4142135623730951},"715":{"tf":2.23606797749979},"716":{"tf":2.0},"717":{"tf":1.4142135623730951},"721":{"tf":2.6457513110645907},"722":{"tf":2.0},"730":{"tf":1.0},"731":{"tf":1.0},"732":{"tf":2.23606797749979},"735":{"tf":2.449489742783178},"736":{"tf":1.0},"738":{"tf":1.0},"739":{"tf":1.0},"749":{"tf":1.4142135623730951},"752":{"tf":1.0},"754":{"tf":1.0},"761":{"tf":1.7320508075688772},"765":{"tf":1.0},"770":{"tf":1.0},"773":{"tf":1.0},"776":{"tf":1.0},"778":{"tf":1.0},"78":{"tf":1.4142135623730951},"783":{"tf":1.4142135623730951},"786":{"tf":1.0},"788":{"tf":1.0},"8":{"tf":1.0},"81":{"tf":1.0},"814":{"tf":1.4142135623730951},"815":{"tf":1.0},"822":{"tf":1.0},"83":{"tf":1.4142135623730951},"831":{"tf":1.7320508075688772},"858":{"tf":1.7320508075688772},"859":{"tf":1.0},"870":{"tf":1.0},"871":{"tf":1.0},"872":{"tf":1.0},"876":{"tf":2.0},"880":{"tf":1.4142135623730951},"881":{"tf":1.4142135623730951},"894":{"tf":1.4142135623730951},"895":{"tf":2.8284271247461903},"897":{"tf":1.0},"898":{"tf":1.0},"902":{"tf":1.0},"909":{"tf":1.0},"911":{"tf":1.4142135623730951},"912":{"tf":1.7320508075688772},"913":{"tf":1.7320508075688772},"914":{"tf":1.0},"919":{"tf":1.0},"928":{"tf":1.4142135623730951},"931":{"tf":1.0},"932":{"tf":2.23606797749979},"933":{"tf":1.4142135623730951},"935":{"tf":1.0},"938":{"tf":1.4142135623730951},"95":{"tf":2.449489742783178},"952":{"tf":1.0},"961":{"tf":1.4142135623730951},"964":{"tf":1.0},"969":{"tf":1.0},"971":{"tf":1.4142135623730951},"973":{"tf":1.0},"983":{"tf":1.0}},"e":{"c":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"697":{"tf":1.0}}}},"df":0,"docs":{}},"d":{"_":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":3,"docs":{"715":{"tf":1.0},"716":{"tf":1.0},"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":1,"docs":{"715":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":4,"docs":{"663":{"tf":1.0},"670":{"tf":1.0},"722":{"tf":1.0},"987":{"tf":1.0}}}}}},"r":{"'":{"df":3,"docs":{"170":{"tf":1.0},"375":{"tf":1.0},"568":{"tf":1.0}}},"df":99,"docs":{"1007":{"tf":1.0},"1011":{"tf":1.0},"108":{"tf":1.0},"109":{"tf":1.4142135623730951},"131":{"tf":1.0},"152":{"tf":1.0},"167":{"tf":1.0},"169":{"tf":1.0},"17":{"tf":1.0},"171":{"tf":1.4142135623730951},"173":{"tf":1.0},"19":{"tf":1.0},"201":{"tf":1.0},"231":{"tf":1.0},"238":{"tf":1.0},"284":{"tf":1.0},"29":{"tf":1.4142135623730951},"290":{"tf":1.0},"298":{"tf":1.0},"3":{"tf":1.4142135623730951},"346":{"tf":1.0},"375":{"tf":1.4142135623730951},"38":{"tf":1.0},"381":{"tf":1.0},"4":{"tf":1.0},"40":{"tf":1.7320508075688772},"414":{"tf":1.0},"418":{"tf":1.0},"423":{"tf":1.4142135623730951},"429":{"tf":1.4142135623730951},"453":{"tf":1.0},"456":{"tf":1.0},"514":{"tf":1.7320508075688772},"515":{"tf":1.7320508075688772},"526":{"tf":1.0},"528":{"tf":1.4142135623730951},"537":{"tf":1.4142135623730951},"538":{"tf":1.0},"544":{"tf":1.0},"564":{"tf":1.4142135623730951},"565":{"tf":1.4142135623730951},"567":{"tf":1.4142135623730951},"568":{"tf":2.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.4142135623730951},"571":{"tf":1.0},"573":{"tf":1.0},"574":{"tf":1.7320508075688772},"575":{"tf":1.0},"576":{"tf":2.23606797749979},"577":{"tf":1.0},"581":{"tf":1.0},"587":{"tf":1.0},"601":{"tf":1.0},"608":{"tf":1.0},"614":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"659":{"tf":1.0},"666":{"tf":1.0},"694":{"tf":1.0},"695":{"tf":1.0},"697":{"tf":1.0},"699":{"tf":1.4142135623730951},"700":{"tf":1.0},"72":{"tf":1.4142135623730951},"774":{"tf":1.0},"784":{"tf":1.4142135623730951},"799":{"tf":1.4142135623730951},"8":{"tf":1.0},"81":{"tf":1.7320508075688772},"814":{"tf":1.0},"82":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.4142135623730951},"852":{"tf":1.7320508075688772},"874":{"tf":2.23606797749979},"878":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.7320508075688772},"886":{"tf":1.0},"895":{"tf":2.6457513110645907},"898":{"tf":1.0},"902":{"tf":1.0},"914":{"tf":1.0},"920":{"tf":1.0},"941":{"tf":1.0},"942":{"tf":2.0},"943":{"tf":1.0},"944":{"tf":1.0},"95":{"tf":1.4142135623730951},"952":{"tf":1.0},"956":{"tf":1.0},"960":{"tf":1.0},"973":{"tf":1.0},"977":{"tf":1.0},"979":{"tf":1.4142135623730951},"983":{"tf":1.0},"991":{"tf":1.0}}}},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"455":{"tf":1.0}}}},"u":{"a":{"df":0,"docs":{},"l":{"df":7,"docs":{"3":{"tf":1.0},"515":{"tf":1.0},"522":{"tf":1.0},"573":{"tf":1.4142135623730951},"6":{"tf":1.0},"749":{"tf":1.0},"859":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"c":{"df":1,"docs":{"252":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":32,"docs":{"1004":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"206":{"tf":1.4142135623730951},"24":{"tf":1.0},"267":{"tf":1.4142135623730951},"289":{"tf":1.0},"3":{"tf":1.0},"335":{"tf":1.0},"35":{"tf":1.0},"400":{"tf":2.0},"401":{"tf":1.4142135623730951},"402":{"tf":1.4142135623730951},"403":{"tf":1.0},"404":{"tf":1.4142135623730951},"405":{"tf":1.0},"406":{"tf":1.0},"407":{"tf":1.0},"408":{"tf":1.0},"409":{"tf":1.0},"423":{"tf":1.0},"517":{"tf":1.0},"52":{"tf":1.0},"773":{"tf":1.0},"813":{"tf":1.0},"860":{"tf":1.0},"876":{"tf":1.0},"919":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"991":{"tf":1.0}},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"x":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":3,"docs":{"563":{"tf":1.0},"574":{"tf":1.4142135623730951},"581":{"tf":1.0}}}}},"df":8,"docs":{"249":{"tf":1.0},"55":{"tf":1.4142135623730951},"564":{"tf":1.0},"574":{"tf":1.0},"576":{"tf":1.0},"599":{"tf":1.0},"602":{"tf":1.0},"615":{"tf":1.4142135623730951}}}},"v":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"717":{"tf":1.0}}}}}}},"0":{"df":1,"docs":{"390":{"tf":1.4142135623730951}}},"1":{".":{"1":{".":{"1":{"df":1,"docs":{"415":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":6,"docs":{"163":{"tf":1.0},"390":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"440":{"tf":1.4142135623730951},"520":{"tf":1.0},"526":{"tf":1.4142135623730951}}},"2":{".":{"0":{"df":1,"docs":{"390":{"tf":1.0}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.0}}}}}}}},"/":{"3":{"7":{"3":{"8":{"df":1,"docs":{"646":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"126":{"tf":1.4142135623730951},"439":{"tf":1.0}}},"3":{".":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"553":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"4":{"df":2,"docs":{"169":{"tf":1.0},"172":{"tf":1.0}}},"5":{"df":4,"docs":{"170":{"tf":1.7320508075688772},"171":{"tf":1.0},"172":{"tf":1.7320508075688772},"984":{"tf":1.0}}},"6":{"df":1,"docs":{"984":{"tf":1.0}}},"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"410":{"tf":1.0}},"i":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"62":{"tf":1.0}}}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"711":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"814":{"tf":1.0}},"e":{"_":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"634":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"814":{"tf":1.0}},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":2,"docs":{"634":{"tf":1.0},"817":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"r":{"/":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"233":{"tf":1.0}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"438":{"tf":1.7320508075688772}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":4,"docs":{"432":{"tf":1.4142135623730951},"438":{"tf":1.4142135623730951},"439":{"tf":1.7320508075688772},"440":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}},"df":139,"docs":{"1003":{"tf":1.4142135623730951},"1004":{"tf":2.6457513110645907},"1005":{"tf":1.0},"142":{"tf":1.0},"155":{"tf":1.4142135623730951},"205":{"tf":1.0},"231":{"tf":2.0},"232":{"tf":1.0},"248":{"tf":1.0},"296":{"tf":1.0},"322":{"tf":1.4142135623730951},"336":{"tf":1.0},"337":{"tf":2.23606797749979},"338":{"tf":1.0},"341":{"tf":1.4142135623730951},"342":{"tf":1.7320508075688772},"345":{"tf":1.0},"346":{"tf":1.7320508075688772},"347":{"tf":2.449489742783178},"350":{"tf":1.0},"356":{"tf":1.0},"368":{"tf":1.7320508075688772},"372":{"tf":1.0},"375":{"tf":1.7320508075688772},"376":{"tf":1.0},"38":{"tf":2.23606797749979},"39":{"tf":2.0},"40":{"tf":1.0},"41":{"tf":1.0},"42":{"tf":1.0},"43":{"tf":1.0},"430":{"tf":2.23606797749979},"431":{"tf":1.4142135623730951},"432":{"tf":2.0},"433":{"tf":1.0},"434":{"tf":1.0},"435":{"tf":1.0},"436":{"tf":2.0},"437":{"tf":1.4142135623730951},"438":{"tf":1.7320508075688772},"439":{"tf":3.0},"44":{"tf":2.0},"440":{"tf":2.8284271247461903},"441":{"tf":1.4142135623730951},"442":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"445":{"tf":1.0},"446":{"tf":1.4142135623730951},"447":{"tf":1.0},"448":{"tf":1.0},"449":{"tf":1.0},"45":{"tf":2.6457513110645907},"450":{"tf":2.8284271247461903},"452":{"tf":1.7320508075688772},"454":{"tf":1.0},"456":{"tf":1.0},"46":{"tf":2.8284271247461903},"47":{"tf":3.1622776601683795},"48":{"tf":1.0},"49":{"tf":1.4142135623730951},"50":{"tf":1.0},"51":{"tf":1.0},"52":{"tf":1.0},"53":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"54":{"tf":1.0},"55":{"tf":1.0},"559":{"tf":1.0},"56":{"tf":1.4142135623730951},"563":{"tf":1.0},"564":{"tf":1.0},"565":{"tf":1.0},"567":{"tf":3.1622776601683795},"568":{"tf":1.4142135623730951},"569":{"tf":1.0},"571":{"tf":1.0},"573":{"tf":1.0},"588":{"tf":1.0},"61":{"tf":1.0},"62":{"tf":1.4142135623730951},"627":{"tf":1.7320508075688772},"628":{"tf":1.0},"629":{"tf":3.0},"63":{"tf":2.8284271247461903},"632":{"tf":1.4142135623730951},"633":{"tf":1.4142135623730951},"634":{"tf":1.4142135623730951},"636":{"tf":1.7320508075688772},"64":{"tf":1.0},"642":{"tf":1.7320508075688772},"644":{"tf":2.23606797749979},"65":{"tf":1.7320508075688772},"66":{"tf":1.4142135623730951},"67":{"tf":1.7320508075688772},"69":{"tf":2.0},"709":{"tf":2.23606797749979},"71":{"tf":1.4142135623730951},"710":{"tf":1.7320508075688772},"711":{"tf":2.6457513110645907},"712":{"tf":2.0},"713":{"tf":1.0},"714":{"tf":1.7320508075688772},"715":{"tf":2.6457513110645907},"716":{"tf":2.23606797749979},"717":{"tf":2.23606797749979},"718":{"tf":1.7320508075688772},"719":{"tf":1.0},"720":{"tf":1.4142135623730951},"721":{"tf":4.0},"722":{"tf":3.1622776601683795},"723":{"tf":1.7320508075688772},"724":{"tf":2.6457513110645907},"725":{"tf":1.4142135623730951},"726":{"tf":1.0},"727":{"tf":1.0},"728":{"tf":1.0},"729":{"tf":2.0},"73":{"tf":2.0},"75":{"tf":1.0},"77":{"tf":1.0},"78":{"tf":2.0},"799":{"tf":1.0},"810":{"tf":1.7320508075688772},"811":{"tf":2.0},"813":{"tf":1.4142135623730951},"814":{"tf":2.23606797749979},"815":{"tf":2.449489742783178},"816":{"tf":1.0},"817":{"tf":2.0},"818":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.4142135623730951},"894":{"tf":1.0},"929":{"tf":1.0},"948":{"tf":1.0},"964":{"tf":1.0},"97":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"67":{"tf":1.0}}}}},"df":0,"docs":{}},"u":{"a":{"b":{"df":0,"docs":{},"l":{"df":7,"docs":{"12":{"tf":1.0},"3":{"tf":1.0},"373":{"tf":1.0},"374":{"tf":1.0},"51":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0}}}},"df":0,"docs":{},"t":{"df":1,"docs":{"777":{"tf":1.4142135623730951}}}},"df":86,"docs":{"154":{"tf":1.0},"163":{"tf":1.0},"196":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"207":{"tf":2.449489742783178},"208":{"tf":2.0},"221":{"tf":2.23606797749979},"222":{"tf":1.4142135623730951},"24":{"tf":1.0},"252":{"tf":1.4142135623730951},"253":{"tf":1.0},"254":{"tf":1.0},"257":{"tf":1.0},"265":{"tf":1.0},"267":{"tf":1.4142135623730951},"270":{"tf":1.0},"3":{"tf":1.0},"30":{"tf":1.0},"342":{"tf":1.4142135623730951},"346":{"tf":2.0},"347":{"tf":1.4142135623730951},"376":{"tf":1.0},"393":{"tf":1.0},"404":{"tf":1.0},"410":{"tf":1.0},"412":{"tf":1.4142135623730951},"416":{"tf":1.0},"417":{"tf":2.0},"418":{"tf":1.0},"429":{"tf":2.449489742783178},"439":{"tf":1.4142135623730951},"452":{"tf":1.0},"455":{"tf":1.4142135623730951},"46":{"tf":1.4142135623730951},"467":{"tf":1.0},"469":{"tf":1.0},"485":{"tf":1.0},"5":{"tf":2.0},"501":{"tf":1.4142135623730951},"507":{"tf":1.0},"526":{"tf":1.0},"569":{"tf":1.4142135623730951},"570":{"tf":1.0},"6":{"tf":3.0},"615":{"tf":1.4142135623730951},"63":{"tf":1.4142135623730951},"634":{"tf":1.0},"640":{"tf":1.0},"723":{"tf":1.0},"735":{"tf":5.196152422706632},"743":{"tf":1.0},"748":{"tf":1.0},"752":{"tf":1.0},"759":{"tf":3.605551275463989},"761":{"tf":2.6457513110645907},"763":{"tf":1.0},"818":{"tf":1.4142135623730951},"819":{"tf":1.4142135623730951},"828":{"tf":1.0},"829":{"tf":1.0},"831":{"tf":2.0},"832":{"tf":1.0},"833":{"tf":1.0},"880":{"tf":1.0},"891":{"tf":2.23606797749979},"892":{"tf":1.4142135623730951},"893":{"tf":1.0},"894":{"tf":1.0},"895":{"tf":1.7320508075688772},"896":{"tf":1.4142135623730951},"897":{"tf":1.0},"898":{"tf":1.4142135623730951},"899":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"903":{"tf":1.0},"904":{"tf":1.0},"905":{"tf":1.0},"906":{"tf":1.0},"907":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}},"e":{"<":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"k":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"208":{"tf":1.0}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"735":{"tf":3.1622776601683795}}}}}},"df":0,"docs":{},"s":{"(":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"6":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"p":{"df":1,"docs":{"6":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"721":{"tf":1.0}}}}}}}}}}},"r":{"df":0,"docs":{},"i":{"a":{"b":{"df":0,"docs":{},"l":{"df":12,"docs":{"253":{"tf":1.0},"267":{"tf":1.0},"332":{"tf":1.4142135623730951},"346":{"tf":1.0},"412":{"tf":1.0},"417":{"tf":1.0},"51":{"tf":1.0},"568":{"tf":1.4142135623730951},"576":{"tf":1.0},"751":{"tf":1.0},"831":{"tf":1.4142135623730951},"846":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":16,"docs":{"166":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.4142135623730951},"249":{"tf":1.0},"340":{"tf":1.4142135623730951},"388":{"tf":1.4142135623730951},"517":{"tf":1.0},"520":{"tf":1.0},"522":{"tf":2.23606797749979},"524":{"tf":2.0},"525":{"tf":1.0},"6":{"tf":1.7320508075688772},"668":{"tf":1.4142135623730951},"7":{"tf":1.4142135623730951},"776":{"tf":1.0}}}},"t":{"df":1,"docs":{"571":{"tf":1.0}}}},"df":5,"docs":{"19":{"tf":1.0},"204":{"tf":1.0},"231":{"tf":1.0},"418":{"tf":1.0},"634":{"tf":1.0}},"o":{"df":0,"docs":{},"u":{"df":13,"docs":{"19":{"tf":1.0},"200":{"tf":1.4142135623730951},"203":{"tf":1.0},"204":{"tf":1.0},"209":{"tf":1.0},"221":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"296":{"tf":1.0},"30":{"tf":1.4142135623730951},"555":{"tf":1.0},"771":{"tf":1.0},"964":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"237":{"tf":1.0},"697":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"779":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"515":{"tf":1.0}}}}}},"df":11,"docs":{"346":{"tf":1.4142135623730951},"439":{"tf":1.4142135623730951},"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.0},"539":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":2.23606797749979},"722":{"tf":1.7320508075688772},"723":{"tf":1.7320508075688772},"735":{"tf":1.0}},"e":{"c":{"!":{"[":{"(":{"a":{"df":1,"docs":{"208":{"tf":1.4142135623730951}}},"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"208":{"tf":1.0}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}},"p":{"a":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}},":":{":":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":2,"docs":{"524":{"tf":1.0},"717":{"tf":1.0}}}}}},"df":0,"docs":{}},"<":{"(":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":1,"docs":{"221":{"tf":1.0}}}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":2,"docs":{"602":{"tf":1.0},"698":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"522":{"tf":1.0}}},"df":0,"docs":{}}}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":0,"docs":{},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"992":{"tf":1.4142135623730951}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}},"p":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"<":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"933":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"521":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"r":{"df":1,"docs":{"522":{"tf":1.0}}}}},"t":{":":{":":{"a":{"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"d":{"df":1,"docs":{"885":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"482":{"tf":1.0},"483":{"tf":1.7320508075688772},"485":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"u":{"3":{"2":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"8":{"df":5,"docs":{"22":{"tf":2.0},"439":{"tf":1.4142135623730951},"455":{"tf":2.0},"62":{"tf":1.0},"633":{"tf":1.0}}},"df":0,"docs":{}}},"[":{"0":{"df":0,"docs":{},"u":{"6":{"4":{"df":1,"docs":{"717":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":8,"docs":{"208":{"tf":3.0},"22":{"tf":1.7320508075688772},"482":{"tf":1.0},"485":{"tf":1.0},"603":{"tf":1.4142135623730951},"633":{"tf":1.0},"83":{"tf":1.0},"933":{"tf":1.0}},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":6,"docs":{"114":{"tf":1.0},"124":{"tf":1.0},"332":{"tf":1.0},"522":{"tf":1.7320508075688772},"63":{"tf":1.0},"670":{"tf":1.0}}}}}},"d":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"v":{"df":0,"docs":{},"y":{"a":{"df":1,"docs":{"386":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":36,"docs":{"108":{"tf":1.0},"184":{"tf":1.0},"199":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"207":{"tf":1.0},"221":{"tf":1.0},"238":{"tf":1.0},"251":{"tf":1.4142135623730951},"253":{"tf":1.4142135623730951},"255":{"tf":1.0},"267":{"tf":1.0},"296":{"tf":1.4142135623730951},"346":{"tf":1.0},"381":{"tf":1.0},"418":{"tf":1.0},"438":{"tf":1.0},"441":{"tf":1.0},"486":{"tf":1.0},"499":{"tf":1.0},"514":{"tf":1.0},"515":{"tf":1.0},"567":{"tf":1.0},"60":{"tf":1.0},"63":{"tf":1.0},"659":{"tf":1.0},"687":{"tf":1.0},"732":{"tf":1.4142135623730951},"761":{"tf":1.0},"763":{"tf":1.7320508075688772},"776":{"tf":1.0},"779":{"tf":1.0},"832":{"tf":1.0},"842":{"tf":1.0},"932":{"tf":1.0},"939":{"tf":1.0}},"f":{"df":18,"docs":{"103":{"tf":1.0},"111":{"tf":1.0},"322":{"tf":1.0},"341":{"tf":1.7320508075688772},"343":{"tf":1.0},"350":{"tf":2.0},"351":{"tf":1.0},"388":{"tf":1.0},"453":{"tf":1.0},"457":{"tf":1.0},"459":{"tf":1.4142135623730951},"513":{"tf":1.0},"514":{"tf":1.0},"521":{"tf":1.0},"531":{"tf":1.0},"94":{"tf":1.0},"95":{"tf":1.4142135623730951},"97":{"tf":1.0}},"i":{"df":45,"docs":{"100":{"tf":1.0},"101":{"tf":1.0},"102":{"tf":1.0},"103":{"tf":1.0},"104":{"tf":1.0},"105":{"tf":1.0},"113":{"tf":1.0},"254":{"tf":1.0},"341":{"tf":1.0},"344":{"tf":1.0},"347":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.7320508075688772},"351":{"tf":1.0},"388":{"tf":1.0},"437":{"tf":1.0},"439":{"tf":1.0},"453":{"tf":1.0},"455":{"tf":1.0},"459":{"tf":1.0},"46":{"tf":1.4142135623730951},"49":{"tf":1.0},"514":{"tf":1.0},"531":{"tf":1.0},"537":{"tf":1.0},"642":{"tf":1.0},"644":{"tf":1.0},"705":{"tf":1.0},"735":{"tf":1.0},"759":{"tf":1.0},"762":{"tf":1.0},"811":{"tf":1.0},"817":{"tf":1.0},"83":{"tf":1.0},"84":{"tf":1.0},"848":{"tf":1.0},"895":{"tf":1.4142135623730951},"93":{"tf":2.23606797749979},"94":{"tf":1.4142135623730951},"944":{"tf":1.0},"95":{"tf":1.0},"96":{"tf":1.0},"97":{"tf":1.0},"98":{"tf":1.0},"99":{"tf":1.0}}},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"169":{"tf":1.0},"171":{"tf":1.0},"175":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}},"s":{"a":{"df":1,"docs":{"559":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":2,"docs":{"555":{"tf":1.0},"639":{"tf":1.0}},"o":{"df":0,"docs":{},"n":{"df":95,"docs":{"1012":{"tf":1.0},"132":{"tf":1.0},"154":{"tf":1.0},"16":{"tf":1.0},"160":{"tf":1.0},"164":{"tf":2.6457513110645907},"165":{"tf":1.7320508075688772},"166":{"tf":2.0},"167":{"tf":1.0},"168":{"tf":1.0},"169":{"tf":1.0},"170":{"tf":3.1622776601683795},"171":{"tf":1.4142135623730951},"172":{"tf":2.23606797749979},"173":{"tf":1.4142135623730951},"174":{"tf":1.0},"175":{"tf":1.7320508075688772},"176":{"tf":1.0},"177":{"tf":1.0},"178":{"tf":2.23606797749979},"179":{"tf":1.0},"180":{"tf":2.449489742783178},"181":{"tf":1.4142135623730951},"24":{"tf":1.0},"249":{"tf":1.0},"280":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"386":{"tf":2.449489742783178},"387":{"tf":1.7320508075688772},"388":{"tf":1.4142135623730951},"389":{"tf":1.0},"390":{"tf":3.4641016151377544},"391":{"tf":1.0},"392":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"395":{"tf":1.0},"396":{"tf":1.0},"397":{"tf":1.0},"398":{"tf":1.0},"399":{"tf":1.0},"439":{"tf":2.0},"440":{"tf":2.449489742783178},"441":{"tf":1.0},"446":{"tf":1.0},"450":{"tf":1.0},"455":{"tf":1.0},"461":{"tf":1.0},"486":{"tf":1.0},"516":{"tf":1.4142135623730951},"520":{"tf":1.4142135623730951},"521":{"tf":2.0},"526":{"tf":1.0},"537":{"tf":1.4142135623730951},"539":{"tf":2.23606797749979},"540":{"tf":1.0},"544":{"tf":1.0},"545":{"tf":1.0},"584":{"tf":2.23606797749979},"585":{"tf":1.4142135623730951},"586":{"tf":1.7320508075688772},"587":{"tf":1.0},"588":{"tf":2.6457513110645907},"589":{"tf":1.0},"590":{"tf":1.0},"591":{"tf":1.0},"592":{"tf":1.0},"593":{"tf":2.0},"594":{"tf":1.4142135623730951},"595":{"tf":1.0},"596":{"tf":1.0},"597":{"tf":1.0},"609":{"tf":2.0},"619":{"tf":1.4142135623730951},"631":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":2.0},"635":{"tf":2.8284271247461903},"636":{"tf":1.0},"637":{"tf":1.4142135623730951},"644":{"tf":1.0},"648":{"tf":1.7320508075688772},"653":{"tf":1.0},"705":{"tf":1.7320508075688772},"735":{"tf":5.916079783099616},"740":{"tf":1.0},"767":{"tf":1.0},"804":{"tf":1.0},"83":{"tf":1.4142135623730951},"85":{"tf":1.0},"878":{"tf":1.0},"894":{"tf":1.0},"953":{"tf":1.0},"984":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"414":{"tf":1.0}}}}},"i":{"a":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"54":{"tf":1.0}}}},"l":{"df":4,"docs":{"810":{"tf":1.0},"831":{"tf":1.0},"913":{"tf":1.0},"942":{"tf":1.0}}}},"df":50,"docs":{"1":{"tf":1.0},"111":{"tf":1.0},"112":{"tf":1.0},"12":{"tf":1.0},"122":{"tf":1.0},"123":{"tf":1.0},"126":{"tf":1.0},"141":{"tf":1.0},"191":{"tf":1.0},"198":{"tf":1.0},"203":{"tf":1.4142135623730951},"21":{"tf":1.0},"22":{"tf":1.0},"241":{"tf":1.0},"272":{"tf":1.0},"273":{"tf":1.0},"28":{"tf":1.0},"3":{"tf":2.0},"358":{"tf":1.0},"372":{"tf":1.0},"375":{"tf":1.0},"417":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"440":{"tf":1.4142135623730951},"446":{"tf":1.0},"45":{"tf":1.0},"472":{"tf":1.0},"5":{"tf":1.0},"55":{"tf":1.0},"573":{"tf":1.4142135623730951},"6":{"tf":1.0},"62":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"66":{"tf":1.0},"680":{"tf":1.0},"71":{"tf":1.0},"72":{"tf":1.0},"747":{"tf":1.0},"75":{"tf":1.0},"78":{"tf":1.0},"800":{"tf":1.0},"842":{"tf":1.0},"847":{"tf":1.0},"849":{"tf":1.0},"879":{"tf":1.0},"887":{"tf":1.0},"932":{"tf":1.0},"959":{"tf":1.0}}},"b":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"412":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":1,"docs":{"411":{"tf":1.0}}}}},"df":0,"docs":{}}},"c":{"df":0,"docs":{},"e":{"df":1,"docs":{"559":{"tf":1.0}}}},"df":3,"docs":{"469":{"tf":1.0},"470":{"tf":1.4142135623730951},"471":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"w":{"df":4,"docs":{"201":{"tf":1.0},"21":{"tf":1.4142135623730951},"35":{"tf":1.7320508075688772},"6":{"tf":1.0}}}},"i":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}},"i":{"df":2,"docs":{"469":{"tf":1.0},"470":{"tf":1.0}}}},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"410":{"tf":1.0}}}},"o":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":4,"docs":{"284":{"tf":1.0},"724":{"tf":1.0},"849":{"tf":1.0},"912":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"198":{"tf":1.0},"735":{"tf":3.4641016151377544}}}},"df":1,"docs":{"205":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"40":{"tf":1.0}}}},"df":0,"docs":{}},"u":{"a":{"df":0,"docs":{},"l":{"df":4,"docs":{"170":{"tf":1.0},"525":{"tf":1.4142135623730951},"742":{"tf":1.0},"756":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"324":{"tf":1.0},"422":{"tf":1.0}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"218":{"tf":1.0}}}},"o":{"df":0,"docs":{},"i":{"c":{"df":2,"docs":{"373":{"tf":1.0},"376":{"tf":1.0}}},"d":{"df":2,"docs":{"273":{"tf":1.0},"522":{"tf":2.449489742783178}}},"df":0,"docs":{}},"l":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":2,"docs":{"267":{"tf":1.7320508075688772},"418":{"tf":1.0}}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":2,"docs":{"418":{"tf":1.0},"912":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":41,"docs":{"1004":{"tf":1.0},"1014":{"tf":1.0},"108":{"tf":1.0},"124":{"tf":1.4142135623730951},"125":{"tf":1.0},"126":{"tf":1.0},"188":{"tf":1.0},"234":{"tf":1.4142135623730951},"296":{"tf":1.0},"370":{"tf":1.0},"375":{"tf":1.0},"45":{"tf":1.0},"450":{"tf":2.23606797749979},"563":{"tf":1.0},"564":{"tf":1.0},"575":{"tf":2.449489742783178},"629":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"717":{"tf":1.0},"721":{"tf":2.6457513110645907},"722":{"tf":1.0},"724":{"tf":1.4142135623730951},"725":{"tf":1.0},"727":{"tf":1.0},"729":{"tf":1.4142135623730951},"75":{"tf":1.0},"795":{"tf":2.23606797749979},"796":{"tf":3.4641016151377544},"797":{"tf":2.449489742783178},"798":{"tf":1.0},"799":{"tf":4.47213595499958},"800":{"tf":1.0},"801":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"804":{"tf":1.0},"805":{"tf":1.0},"806":{"tf":1.0},"807":{"tf":1.0},"973":{"tf":1.0}},"r":{"df":6,"docs":{"127":{"tf":1.0},"234":{"tf":1.0},"575":{"tf":1.0},"799":{"tf":1.0},"800":{"tf":1.0},"807":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":2,"docs":{"346":{"tf":1.0},"349":{"tf":1.0}}}}}},"df":0,"docs":{}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}}}}}}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}},"df":2,"docs":{"341":{"tf":1.0},"349":{"tf":1.4142135623730951}},"e":{"d":{"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"(":{"c":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{".":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"350":{"tf":1.0},"351":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"341":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}}}}}},"df":1,"docs":{"341":{"tf":1.0}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":2,"docs":{"341":{"tf":1.0},"350":{"tf":1.4142135623730951}}}}}}}}},"df":11,"docs":{"126":{"tf":1.0},"131":{"tf":1.0},"133":{"tf":1.0},"322":{"tf":1.4142135623730951},"340":{"tf":2.8284271247461903},"341":{"tf":3.7416573867739413},"346":{"tf":1.7320508075688772},"347":{"tf":1.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.4142135623730951},"359":{"tf":1.7320508075688772}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":3,"docs":{"341":{"tf":2.0},"349":{"tf":1.4142135623730951},"350":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}},"s":{"df":4,"docs":{"187":{"tf":1.0},"427":{"tf":1.0},"48":{"tf":1.0},"553":{"tf":1.0}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":10,"docs":{"127":{"tf":1.0},"142":{"tf":1.0},"231":{"tf":1.0},"711":{"tf":1.0},"945":{"tf":1.0},"948":{"tf":1.0},"961":{"tf":1.0},"962":{"tf":1.0},"965":{"tf":1.0},"972":{"tf":1.0}}}}}}},"·":{"2":{"/":{"3":{"df":1,"docs":{"346":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"w":{"3":{"c":{"df":1,"docs":{"95":{"tf":1.4142135623730951}}},"df":0,"docs":{},"f":{"df":3,"docs":{"359":{"tf":1.0},"843":{"tf":1.0},"931":{"tf":1.0}}}},"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":2,"docs":{"467":{"tf":1.0},"479":{"tf":1.0}}}},"h":{"df":1,"docs":{"603":{"tf":1.0}}},"i":{"df":0,"docs":{},"t":{"df":13,"docs":{"207":{"tf":1.4142135623730951},"554":{"tf":1.0},"573":{"tf":1.4142135623730951},"576":{"tf":1.0},"63":{"tf":1.4142135623730951},"642":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"815":{"tf":1.0},"837":{"tf":1.0},"913":{"tf":1.0},"917":{"tf":1.0},"942":{"tf":1.0}}}},"l":{"df":0,"docs":{},"k":{"df":1,"docs":{"759":{"tf":1.0}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":28,"docs":{"167":{"tf":1.0},"18":{"tf":1.0},"191":{"tf":1.0},"33":{"tf":1.0},"4":{"tf":1.0},"514":{"tf":3.0},"515":{"tf":2.0},"518":{"tf":1.7320508075688772},"519":{"tf":1.4142135623730951},"521":{"tf":1.0},"522":{"tf":1.4142135623730951},"523":{"tf":1.0},"526":{"tf":1.4142135623730951},"527":{"tf":1.0},"528":{"tf":1.4142135623730951},"534":{"tf":1.4142135623730951},"538":{"tf":1.0},"587":{"tf":1.0},"601":{"tf":1.0},"616":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"804":{"tf":1.4142135623730951},"82":{"tf":1.0},"853":{"tf":1.0},"977":{"tf":1.0}},"s":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":1,"docs":{"30":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"n":{"df":0,"docs":{},"t":{"df":34,"docs":{"121":{"tf":1.4142135623730951},"154":{"tf":1.0},"171":{"tf":1.0},"193":{"tf":1.0},"231":{"tf":1.0},"234":{"tf":1.7320508075688772},"255":{"tf":1.0},"273":{"tf":1.0},"387":{"tf":1.0},"42":{"tf":1.0},"438":{"tf":1.0},"439":{"tf":1.0},"497":{"tf":1.0},"565":{"tf":1.0},"570":{"tf":1.0},"571":{"tf":1.0},"576":{"tf":1.0},"60":{"tf":1.0},"603":{"tf":1.0},"61":{"tf":1.0},"635":{"tf":1.0},"673":{"tf":1.0},"694":{"tf":1.0},"700":{"tf":1.0},"711":{"tf":1.0},"752":{"tf":1.0},"780":{"tf":1.0},"804":{"tf":1.0},"826":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.4142135623730951},"895":{"tf":1.0},"934":{"tf":1.0},"960":{"tf":1.0}}}},"r":{"df":0,"docs":{},"p":{"df":5,"docs":{"500":{"tf":1.4142135623730951},"503":{"tf":1.4142135623730951},"770":{"tf":1.0},"992":{"tf":1.0},"996":{"tf":1.0}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"121":{"tf":1.0},"46":{"tf":1.0}}}}},"df":0,"docs":{}},"t":{"df":1,"docs":{"486":{"tf":1.0}}}},"s":{"df":0,"docs":{},"m":{"/":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":3,"docs":{"296":{"tf":1.7320508075688772},"297":{"tf":1.4142135623730951},"303":{"tf":1.0}}}}}}}}},"df":9,"docs":{"111":{"tf":1.0},"288":{"tf":1.0},"300":{"tf":1.0},"303":{"tf":1.0},"35":{"tf":1.0},"732":{"tf":1.0},"829":{"tf":2.23606797749979},"831":{"tf":2.0},"832":{"tf":1.4142135623730951}}},"t":{"df":10,"docs":{"124":{"tf":1.0},"346":{"tf":1.0},"374":{"tf":1.0},"60":{"tf":1.0},"71":{"tf":1.0},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"77":{"tf":1.0},"917":{"tf":1.0},"919":{"tf":1.0}}}},"y":{"df":75,"docs":{"1":{"tf":1.0},"112":{"tf":1.0},"12":{"tf":1.0},"124":{"tf":1.4142135623730951},"134":{"tf":1.0},"151":{"tf":1.0},"152":{"tf":1.0},"154":{"tf":1.4142135623730951},"159":{"tf":1.0},"173":{"tf":1.0},"180":{"tf":1.0},"203":{"tf":1.0},"204":{"tf":1.0},"208":{"tf":1.0},"251":{"tf":1.0},"254":{"tf":1.0},"255":{"tf":1.4142135623730951},"296":{"tf":1.0},"3":{"tf":2.23606797749979},"303":{"tf":1.0},"373":{"tf":1.0},"375":{"tf":1.0},"397":{"tf":1.0},"402":{"tf":1.0},"431":{"tf":1.0},"432":{"tf":1.0},"437":{"tf":1.0},"450":{"tf":1.0},"483":{"tf":1.0},"505":{"tf":1.4142135623730951},"514":{"tf":1.0},"515":{"tf":2.0},"518":{"tf":1.0},"522":{"tf":1.0},"531":{"tf":1.0},"532":{"tf":1.0},"537":{"tf":1.0},"551":{"tf":1.0},"555":{"tf":1.0},"573":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"599":{"tf":1.0},"6":{"tf":1.0},"60":{"tf":1.4142135623730951},"602":{"tf":1.0},"628":{"tf":1.7320508075688772},"629":{"tf":1.0},"633":{"tf":1.4142135623730951},"648":{"tf":1.0},"651":{"tf":1.7320508075688772},"66":{"tf":1.4142135623730951},"693":{"tf":1.0},"732":{"tf":1.0},"735":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"762":{"tf":1.4142135623730951},"78":{"tf":1.0},"807":{"tf":1.4142135623730951},"811":{"tf":1.0},"817":{"tf":1.0},"829":{"tf":1.0},"832":{"tf":1.0},"847":{"tf":1.0},"869":{"tf":1.0},"870":{"tf":1.0},"874":{"tf":2.0},"912":{"tf":1.0},"926":{"tf":1.0},"927":{"tf":1.0},"928":{"tf":2.23606797749979},"976":{"tf":1.0},"983":{"tf":1.0}}}},"df":5,"docs":{"45":{"tf":1.0},"47":{"tf":2.0},"51":{"tf":1.0},"722":{"tf":1.7320508075688772},"723":{"tf":2.23606797749979}},"e":{"'":{"d":{"df":1,"docs":{"779":{"tf":1.0}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":5,"docs":{"603":{"tf":1.0},"711":{"tf":1.0},"725":{"tf":1.0},"846":{"tf":1.0},"874":{"tf":1.4142135623730951}}}},"r":{"df":7,"docs":{"711":{"tf":1.0},"831":{"tf":1.0},"835":{"tf":1.0},"852":{"tf":1.0},"880":{"tf":1.0},"881":{"tf":1.0},"885":{"tf":1.0}}},"v":{"df":5,"docs":{"573":{"tf":1.0},"615":{"tf":1.4142135623730951},"680":{"tf":1.0},"711":{"tf":1.0},"712":{"tf":1.0}}}},"a":{"df":0,"docs":{},"k":{"df":2,"docs":{"410":{"tf":1.0},"427":{"tf":1.7320508075688772}}}},"b":{"2":{"df":1,"docs":{"895":{"tf":1.4142135623730951}}},"3":{"df":5,"docs":{"211":{"tf":1.0},"324":{"tf":1.0},"346":{"tf":1.0},"42":{"tf":1.0},"895":{"tf":1.7320508075688772}}},"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"198":{"tf":1.0}}}},"df":0,"docs":{}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"n":{"df":1,"docs":{"95":{"tf":2.0}}}}}}},"df":1,"docs":{"95":{"tf":2.23606797749979}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"912":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"k":{"df":6,"docs":{"140":{"tf":1.0},"204":{"tf":1.0},"743":{"tf":1.0},"752":{"tf":1.4142135623730951},"777":{"tf":1.0},"843":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"932":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":2,"docs":{"617":{"tf":1.7320508075688772},"619":{"tf":1.4142135623730951}},"t":{":":{":":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":3,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"654":{"tf":1.0}}}}}}}},"df":24,"docs":{"1003":{"tf":1.0},"108":{"tf":1.0},"18":{"tf":1.4142135623730951},"208":{"tf":1.4142135623730951},"22":{"tf":1.7320508075688772},"23":{"tf":1.0},"30":{"tf":1.4142135623730951},"388":{"tf":1.0},"401":{"tf":1.0},"402":{"tf":2.23606797749979},"404":{"tf":1.0},"409":{"tf":1.0},"575":{"tf":1.7320508075688772},"602":{"tf":1.0},"614":{"tf":1.7320508075688772},"615":{"tf":1.7320508075688772},"617":{"tf":1.0},"619":{"tf":1.7320508075688772},"650":{"tf":1.0},"669":{"tf":1.0},"717":{"tf":1.0},"722":{"tf":1.0},"723":{"tf":1.0},"885":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"602":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}},"l":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"844":{"tf":1.0},"870":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"df":40,"docs":{"1008":{"tf":1.0},"1015":{"tf":1.0},"107":{"tf":1.0},"166":{"tf":1.0},"200":{"tf":1.0},"204":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"208":{"tf":1.7320508075688772},"209":{"tf":1.0},"217":{"tf":1.0},"220":{"tf":1.0},"249":{"tf":1.0},"375":{"tf":1.0},"455":{"tf":1.0},"48":{"tf":1.0},"515":{"tf":1.0},"523":{"tf":1.0},"526":{"tf":1.4142135623730951},"532":{"tf":1.0},"602":{"tf":1.0},"68":{"tf":1.0},"712":{"tf":1.0},"72":{"tf":1.0},"720":{"tf":1.0},"723":{"tf":1.0},"742":{"tf":1.0},"75":{"tf":1.0},"776":{"tf":1.4142135623730951},"777":{"tf":1.0},"78":{"tf":1.0},"804":{"tf":1.0},"815":{"tf":1.0},"829":{"tf":1.0},"874":{"tf":1.0},"879":{"tf":1.0},"880":{"tf":1.4142135623730951},"941":{"tf":1.0},"947":{"tf":1.0},"961":{"tf":1.0}}}},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"255":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"u":{"b":{"df":1,"docs":{"603":{"tf":2.23606797749979}}},"df":0,"docs":{}}}}}}}},"df":9,"docs":{"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"304":{"tf":1.0},"603":{"tf":1.7320508075688772},"639":{"tf":1.0},"678":{"tf":1.0},"679":{"tf":1.0},"682":{"tf":1.0}}},"df":0,"docs":{}}}}}},"h":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"724":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":6,"docs":{"71":{"tf":1.0},"718":{"tf":1.0},"721":{"tf":1.4142135623730951},"847":{"tf":1.4142135623730951},"932":{"tf":1.0},"933":{"tf":1.0}}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"199":{"tf":1.0}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":1,"docs":{"315":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":2,"docs":{"203":{"tf":1.0},"205":{"tf":1.0}}},"b":{"df":0,"docs":{},"i":{"df":4,"docs":{"198":{"tf":1.0},"206":{"tf":1.0},"231":{"tf":1.0},"933":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":22,"docs":{"126":{"tf":1.0},"127":{"tf":1.0},"177":{"tf":1.0},"255":{"tf":1.0},"273":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0},"364":{"tf":1.0},"439":{"tf":1.0},"472":{"tf":1.0},"49":{"tf":1.0},"526":{"tf":1.0},"573":{"tf":1.0},"576":{"tf":1.4142135623730951},"759":{"tf":1.4142135623730951},"761":{"tf":1.0},"849":{"tf":1.0},"870":{"tf":1.0},"913":{"tf":1.0},"934":{"tf":1.0},"938":{"tf":1.0},"992":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"184":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"912":{"tf":1.4142135623730951}},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":5,"docs":{"111":{"tf":1.0},"112":{"tf":1.0},"194":{"tf":1.0},"272":{"tf":1.0},"83":{"tf":1.0}},"e":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"b":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"c":{"a":{"df":0,"docs":{},"l":{"df":2,"docs":{"112":{"tf":1.0},"121":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"272":{"tf":1.0}}}}}}}}}}}}}}},"o":{"/":{"df":0,"docs":{},"w":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"843":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"848":{"tf":1.0},"849":{"tf":1.0}}}}}},"l":{"df":0,"docs":{},"e":{"df":7,"docs":{"204":{"tf":1.0},"231":{"tf":1.0},"5":{"tf":1.0},"537":{"tf":1.0},"571":{"tf":1.0},"697":{"tf":1.0},"715":{"tf":1.0}}}},"m":{"df":0,"docs":{},"e":{"df":2,"docs":{"715":{"tf":1.0},"723":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":13,"docs":{"204":{"tf":1.0},"205":{"tf":1.0},"208":{"tf":1.4142135623730951},"221":{"tf":1.0},"253":{"tf":1.0},"255":{"tf":1.0},"469":{"tf":1.0},"500":{"tf":1.0},"502":{"tf":1.0},"505":{"tf":1.0},"567":{"tf":1.0},"715":{"tf":1.0},"761":{"tf":1.7320508075688772}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":4,"docs":{"519":{"tf":1.0},"874":{"tf":1.0},"895":{"tf":1.0},"95":{"tf":1.4142135623730951}},"r":{"df":2,"docs":{"199":{"tf":1.0},"973":{"tf":1.0}}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"i":{"df":1,"docs":{"848":{"tf":1.0}}}},"l":{"d":{"(":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"603":{"tf":1.0}}}},"df":0,"docs":{}},"df":3,"docs":{"701":{"tf":1.0},"705":{"tf":1.0},"77":{"tf":1.0}},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{":":{":":{"df":0,"docs":{},"f":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{},"l":{"df":3,"docs":{"416":{"tf":1.0},"659":{"tf":1.0},"858":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":3,"docs":{"574":{"tf":1.0},"576":{"tf":1.0},"777":{"tf":1.0}}}}}}},"n":{"d":{"df":1,"docs":{"712":{"tf":1.0}},"o":{"df":0,"docs":{},"w":{"df":6,"docs":{"39":{"tf":1.4142135623730951},"40":{"tf":1.0},"42":{"tf":1.0},"47":{"tf":1.4142135623730951},"55":{"tf":1.4142135623730951},"563":{"tf":1.0}}}}},"df":2,"docs":{"346":{"tf":1.7320508075688772},"879":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"'":{"df":1,"docs":{"777":{"tf":1.0}}},"df":0,"docs":{}}}}},"p":{"df":1,"docs":{"932":{"tf":1.0}}},"r":{"df":0,"docs":{},"e":{"df":2,"docs":{"485":{"tf":1.0},"761":{"tf":1.0}}}},"s":{"df":0,"docs":{},"e":{"df":5,"docs":{"190":{"tf":1.0},"435":{"tf":1.0},"440":{"tf":1.0},"724":{"tf":1.0},"874":{"tf":1.0}}},"h":{"df":12,"docs":{"185":{"tf":1.0},"193":{"tf":1.0},"272":{"tf":1.0},"776":{"tf":1.0},"799":{"tf":1.0},"897":{"tf":1.0},"911":{"tf":1.0},"912":{"tf":1.0},"914":{"tf":1.0},"917":{"tf":1.0},"928":{"tf":1.0},"943":{"tf":1.0}}}},"t":{"df":4,"docs":{"46":{"tf":1.4142135623730951},"83":{"tf":2.23606797749979},"84":{"tf":1.4142135623730951},"88":{"tf":1.0}},"h":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"786":{"tf":1.4142135623730951},"793":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"d":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"w":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"(":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{".":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"(":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":2,"docs":{"602":{"tf":1.0},"979":{"tf":1.0}}}}}}},"df":8,"docs":{"516":{"tf":1.0},"573":{"tf":1.0},"602":{"tf":1.0},"603":{"tf":1.4142135623730951},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"983":{"tf":1.0},"987":{"tf":1.0}},"n":{"df":1,"docs":{"603":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"879":{"tf":2.0}}},"df":0,"docs":{}}}},"i":{"df":0,"docs":{},"n":{"df":43,"docs":{"126":{"tf":1.0},"196":{"tf":1.0},"207":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"261":{"tf":1.0},"267":{"tf":1.0},"28":{"tf":1.0},"3":{"tf":1.7320508075688772},"30":{"tf":1.0},"326":{"tf":1.0},"331":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0},"340":{"tf":1.0},"343":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.7320508075688772},"352":{"tf":1.0},"373":{"tf":1.4142135623730951},"414":{"tf":1.0},"46":{"tf":1.4142135623730951},"485":{"tf":1.0},"511":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"539":{"tf":1.0},"563":{"tf":1.0},"567":{"tf":1.4142135623730951},"600":{"tf":1.0},"602":{"tf":1.4142135623730951},"699":{"tf":1.0},"735":{"tf":1.4142135623730951},"773":{"tf":2.0},"777":{"tf":1.0},"81":{"tf":1.0},"85":{"tf":1.0},"928":{"tf":1.0},"949":{"tf":1.0},"971":{"tf":1.0}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":58,"docs":{"1004":{"tf":1.0},"113":{"tf":1.0},"12":{"tf":1.0},"136":{"tf":1.0},"137":{"tf":1.0},"138":{"tf":1.0},"140":{"tf":1.0},"146":{"tf":1.0},"198":{"tf":1.0},"217":{"tf":1.0},"234":{"tf":1.0},"24":{"tf":1.0},"249":{"tf":1.0},"262":{"tf":1.0},"295":{"tf":1.0},"296":{"tf":1.0},"297":{"tf":1.4142135623730951},"303":{"tf":1.4142135623730951},"308":{"tf":1.0},"349":{"tf":1.0},"387":{"tf":1.0},"418":{"tf":1.0},"435":{"tf":1.0},"483":{"tf":1.4142135623730951},"485":{"tf":1.0},"49":{"tf":1.0},"497":{"tf":1.0},"514":{"tf":1.0},"516":{"tf":1.0},"517":{"tf":1.0},"551":{"tf":1.0},"555":{"tf":1.0},"564":{"tf":1.0},"567":{"tf":1.0},"577":{"tf":1.0},"593":{"tf":1.0},"6":{"tf":1.0},"619":{"tf":1.4142135623730951},"628":{"tf":1.0},"696":{"tf":1.4142135623730951},"697":{"tf":1.0},"705":{"tf":1.0},"724":{"tf":1.0},"729":{"tf":1.0},"759":{"tf":1.0},"761":{"tf":1.0},"778":{"tf":1.0},"811":{"tf":1.0},"816":{"tf":1.0},"831":{"tf":1.0},"832":{"tf":1.0},"835":{"tf":1.0},"837":{"tf":1.4142135623730951},"881":{"tf":1.0},"929":{"tf":1.0},"939":{"tf":1.0},"953":{"tf":1.0},"992":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"/":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"84":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}}}}},"o":{"df":1,"docs":{"555":{"tf":1.0}},"n":{"'":{"df":0,"docs":{},"t":{"df":3,"docs":{"399":{"tf":1.0},"813":{"tf":1.0},"815":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"d":{"df":5,"docs":{"195":{"tf":1.0},"215":{"tf":1.0},"366":{"tf":1.0},"465":{"tf":1.0},"807":{"tf":1.0}}},"df":0,"docs":{}},"r":{"d":{"df":9,"docs":{"345":{"tf":1.0},"438":{"tf":1.0},"485":{"tf":1.0},"500":{"tf":1.4142135623730951},"503":{"tf":1.0},"575":{"tf":1.0},"720":{"tf":1.0},"761":{"tf":1.7320508075688772},"776":{"tf":1.0}}},"df":0,"docs":{},"k":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"658":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":61,"docs":{"1015":{"tf":1.0},"147":{"tf":1.0},"179":{"tf":1.0},"181":{"tf":1.0},"200":{"tf":1.7320508075688772},"207":{"tf":1.0},"208":{"tf":1.0},"212":{"tf":1.0},"22":{"tf":1.0},"220":{"tf":1.0},"249":{"tf":1.7320508075688772},"255":{"tf":1.0},"314":{"tf":1.4142135623730951},"35":{"tf":1.0},"371":{"tf":1.0},"375":{"tf":1.0},"376":{"tf":1.0},"39":{"tf":1.0},"399":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"44":{"tf":2.0},"440":{"tf":1.0},"45":{"tf":3.1622776601683795},"450":{"tf":1.0},"46":{"tf":1.7320508075688772},"467":{"tf":1.4142135623730951},"469":{"tf":1.0},"47":{"tf":1.4142135623730951},"49":{"tf":1.0},"50":{"tf":1.4142135623730951},"505":{"tf":1.0},"51":{"tf":1.0},"515":{"tf":1.4142135623730951},"516":{"tf":1.0},"518":{"tf":1.0},"52":{"tf":1.0},"532":{"tf":1.0},"534":{"tf":1.0},"548":{"tf":1.0},"568":{"tf":1.0},"6":{"tf":1.0},"605":{"tf":1.0},"615":{"tf":1.0},"618":{"tf":1.0},"68":{"tf":1.0},"697":{"tf":1.0},"698":{"tf":1.4142135623730951},"701":{"tf":1.0},"710":{"tf":1.0},"711":{"tf":1.0},"714":{"tf":1.0},"720":{"tf":1.0},"759":{"tf":1.0},"777":{"tf":1.0},"933":{"tf":1.0},"938":{"tf":1.0},"939":{"tf":1.0},"943":{"tf":1.0},"960":{"tf":1.0},"983":{"tf":1.4142135623730951}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"739":{"tf":1.0}}}},"l":{"df":0,"docs":{},"o":{"a":{"d":{"df":7,"docs":{"19":{"tf":1.0},"204":{"tf":2.0},"205":{"tf":1.7320508075688772},"208":{"tf":3.1622776601683795},"223":{"tf":1.0},"729":{"tf":1.4142135623730951},"911":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"n":{"df":2,"docs":{"205":{"tf":1.4142135623730951},"208":{"tf":2.449489742783178}}}},"df":0,"docs":{}}}},"l":{"d":{"df":5,"docs":{"199":{"tf":1.0},"362":{"tf":1.0},"50":{"tf":1.0},"847":{"tf":1.4142135623730951},"95":{"tf":1.0}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"831":{"tf":1.0},"832":{"tf":1.0}}}},"s":{"df":2,"docs":{"564":{"tf":1.0},"711":{"tf":1.0}},"t":{"df":6,"docs":{"151":{"tf":1.0},"573":{"tf":1.4142135623730951},"732":{"tf":1.0},"765":{"tf":1.0},"773":{"tf":1.0},"779":{"tf":1.0}}}},"t":{"df":0,"docs":{},"h":{"df":6,"docs":{"204":{"tf":1.0},"267":{"tf":1.0},"761":{"tf":1.0},"78":{"tf":1.0},"849":{"tf":1.0},"85":{"tf":1.0}},"i":{"df":1,"docs":{"938":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"d":{"'":{"df":0,"docs":{},"v":{"df":1,"docs":{"724":{"tf":1.0}}}},"df":0,"docs":{},"n":{"'":{"df":0,"docs":{},"t":{"df":7,"docs":{"249":{"tf":1.4142135623730951},"254":{"tf":1.0},"418":{"tf":1.0},"453":{"tf":1.0},"735":{"tf":2.0},"849":{"tf":1.0},"854":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"l":{"df":1,"docs":{"47":{"tf":1.4142135623730951}}}}},"p":{"df":2,"docs":{"522":{"tf":1.4142135623730951},"555":{"tf":1.0}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"633":{"tf":1.0},"786":{"tf":1.0}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":14,"docs":{"252":{"tf":1.0},"26":{"tf":1.0},"47":{"tf":1.0},"483":{"tf":1.0},"5":{"tf":1.0},"521":{"tf":1.0},"542":{"tf":1.0},"567":{"tf":1.0},"583":{"tf":1.0},"673":{"tf":1.0},"732":{"tf":1.4142135623730951},"735":{"tf":5.656854249492381},"936":{"tf":1.0},"951":{"tf":1.0}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":5,"docs":{"229":{"tf":1.0},"243":{"tf":1.4142135623730951},"483":{"tf":1.0},"654":{"tf":1.0},"735":{"tf":2.6457513110645907}}}}}}},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":4,"docs":{"343":{"tf":1.0},"615":{"tf":1.0},"701":{"tf":1.0},"724":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"214":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"h":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"786":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}},"x":{"'":{"df":3,"docs":{"847":{"tf":1.0},"848":{"tf":1.0},"849":{"tf":1.0}}},".":{"0":{")":{".":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"_":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"(":{")":{".":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"221":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{")":{".":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"221":{"tf":1.0}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"2":{"(":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"(":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"696":{"tf":1.0}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"^":{"d":{"df":1,"docs":{"749":{"tf":1.0}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"846":{"tf":1.0}}}}}}},"c":{"df":0,"docs":{},"m":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"!":{"[":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.0}}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},":":{":":{"<":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"c":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{">":{"(":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"603":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"83":{"tf":1.4142135623730951}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"_":{"a":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}},"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"603":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"df":154,"docs":{"1":{"tf":2.449489742783178},"10":{"tf":1.0},"11":{"tf":1.0},"12":{"tf":1.4142135623730951},"13":{"tf":1.0},"14":{"tf":1.4142135623730951},"15":{"tf":1.4142135623730951},"16":{"tf":1.0},"18":{"tf":1.4142135623730951},"2":{"tf":1.4142135623730951},"203":{"tf":1.0},"205":{"tf":1.0},"220":{"tf":1.4142135623730951},"237":{"tf":1.0},"24":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":2.6457513110645907},"30":{"tf":1.0},"367":{"tf":1.0},"369":{"tf":1.0},"37":{"tf":1.0},"372":{"tf":1.4142135623730951},"374":{"tf":1.0},"375":{"tf":1.0},"4":{"tf":1.0},"5":{"tf":2.6457513110645907},"598":{"tf":2.449489742783178},"599":{"tf":1.7320508075688772},"6":{"tf":1.7320508075688772},"600":{"tf":2.8284271247461903},"601":{"tf":1.0},"602":{"tf":5.0},"603":{"tf":2.449489742783178},"604":{"tf":1.0},"605":{"tf":1.4142135623730951},"606":{"tf":1.7320508075688772},"607":{"tf":1.0},"608":{"tf":1.4142135623730951},"609":{"tf":2.0},"61":{"tf":1.0},"610":{"tf":1.0},"611":{"tf":1.0},"612":{"tf":1.0},"613":{"tf":2.23606797749979},"614":{"tf":1.4142135623730951},"615":{"tf":1.4142135623730951},"616":{"tf":1.0},"617":{"tf":1.0},"618":{"tf":1.0},"619":{"tf":1.7320508075688772},"620":{"tf":1.0},"621":{"tf":1.0},"622":{"tf":1.0},"623":{"tf":1.4142135623730951},"624":{"tf":1.0},"625":{"tf":1.0},"626":{"tf":1.0},"631":{"tf":1.0},"633":{"tf":2.23606797749979},"640":{"tf":1.0},"645":{"tf":1.4142135623730951},"649":{"tf":2.0},"650":{"tf":1.4142135623730951},"651":{"tf":2.0},"652":{"tf":1.0},"653":{"tf":1.0},"654":{"tf":1.4142135623730951},"655":{"tf":1.0},"656":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.0},"659":{"tf":1.0},"660":{"tf":1.0},"661":{"tf":1.7320508075688772},"662":{"tf":1.0},"663":{"tf":1.0},"664":{"tf":2.23606797749979},"665":{"tf":1.4142135623730951},"666":{"tf":1.0},"667":{"tf":1.0},"668":{"tf":1.0},"669":{"tf":1.0},"670":{"tf":1.0},"671":{"tf":1.0},"672":{"tf":1.0},"673":{"tf":1.4142135623730951},"674":{"tf":1.0},"675":{"tf":1.7320508075688772},"676":{"tf":1.0},"677":{"tf":1.0},"678":{"tf":2.0},"679":{"tf":1.0},"680":{"tf":1.0},"681":{"tf":1.0},"682":{"tf":1.0},"683":{"tf":1.0},"684":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"687":{"tf":1.0},"688":{"tf":1.0},"689":{"tf":1.0},"690":{"tf":1.0},"691":{"tf":1.0},"692":{"tf":2.23606797749979},"693":{"tf":1.4142135623730951},"694":{"tf":2.8284271247461903},"695":{"tf":1.0},"696":{"tf":2.0},"697":{"tf":1.4142135623730951},"698":{"tf":2.23606797749979},"699":{"tf":1.0},"7":{"tf":1.0},"700":{"tf":1.0},"701":{"tf":2.0},"702":{"tf":1.0},"703":{"tf":1.0},"704":{"tf":1.4142135623730951},"705":{"tf":2.0},"706":{"tf":1.4142135623730951},"707":{"tf":1.0},"708":{"tf":1.0},"782":{"tf":2.23606797749979},"783":{"tf":1.4142135623730951},"784":{"tf":1.4142135623730951},"785":{"tf":1.0},"786":{"tf":1.7320508075688772},"787":{"tf":1.0},"788":{"tf":1.7320508075688772},"789":{"tf":1.0},"790":{"tf":1.0},"791":{"tf":1.0},"792":{"tf":1.0},"793":{"tf":1.0},"794":{"tf":1.0},"8":{"tf":1.0},"83":{"tf":2.0},"87":{"tf":1.0},"9":{"tf":1.0},"959":{"tf":1.0},"974":{"tf":2.23606797749979},"975":{"tf":1.4142135623730951},"976":{"tf":1.0},"977":{"tf":1.0},"978":{"tf":1.0},"979":{"tf":1.0},"980":{"tf":1.4142135623730951},"981":{"tf":1.0},"982":{"tf":1.0},"983":{"tf":1.4142135623730951},"984":{"tf":1.4142135623730951},"985":{"tf":1.7320508075688772},"986":{"tf":1.0},"987":{"tf":1.0}},"p":{"/":{"df":0,"docs":{},"h":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"28":{"tf":1.0}}}}}}},"df":1,"docs":{"711":{"tf":1.0}}},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{":":{":":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"(":{"df":0,"docs":{},"x":{"c":{"df":0,"docs":{},"m":{"df":1,"docs":{"83":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}},"v":{"5":{"df":2,"docs":{"609":{"tf":1.0},"701":{"tf":1.4142135623730951}}},"df":0,"docs":{}}},"q":{"(":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":21,"docs":{"17":{"tf":2.0},"18":{"tf":1.0},"19":{"tf":1.0},"20":{"tf":1.0},"21":{"tf":1.0},"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0},"27":{"tf":1.0},"28":{"tf":1.0},"29":{"tf":1.0},"30":{"tf":1.0},"31":{"tf":1.0},"32":{"tf":1.0},"33":{"tf":1.0},"34":{"tf":1.0},"35":{"tf":1.0},"36":{"tf":1.0},"37":{"tf":1.0}}}}}}},"df":0,"docs":{}},"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{":":{":":{"d":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"l":{"_":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"24":{"tf":1.0}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}},"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":1,"docs":{"22":{"tf":1.0}}}}},"df":12,"docs":{"17":{"tf":2.449489742783178},"18":{"tf":1.7320508075688772},"21":{"tf":1.7320508075688772},"22":{"tf":2.6457513110645907},"23":{"tf":2.0},"24":{"tf":2.8284271247461903},"25":{"tf":2.23606797749979},"26":{"tf":2.0},"28":{"tf":1.4142135623730951},"30":{"tf":1.4142135623730951},"35":{"tf":1.4142135623730951},"37":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}}}}},"x":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"23":{"tf":1.0}}}}}}}}}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}}}}}}},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"(":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{":":{":":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":1,"docs":{"22":{"tf":1.0}}}}}},"df":0,"docs":{},"h":{"2":{"5":{"6":{"df":1,"docs":{"22":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"3":{"2":{"df":1,"docs":{"22":{"tf":1.4142135623730951}}},"df":0,"docs":{}},"6":{"4":{"df":1,"docs":{"22":{"tf":1.7320508075688772}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}}}}}}}}},"df":0,"docs":{}}}}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"v":{"df":0,"docs":{},"m":{"df":7,"docs":{"605":{"tf":1.0},"617":{"tf":1.0},"619":{"tf":1.0},"651":{"tf":2.0},"653":{"tf":1.0},"665":{"tf":1.0},"976":{"tf":1.4142135623730951}}}}},"df":25,"docs":{"333":{"tf":2.449489742783178},"346":{"tf":1.0},"417":{"tf":1.7320508075688772},"45":{"tf":1.0},"50":{"tf":1.0},"568":{"tf":1.0},"697":{"tf":1.0},"749":{"tf":1.0},"841":{"tf":2.449489742783178},"842":{"tf":2.0},"843":{"tf":2.0},"844":{"tf":1.4142135623730951},"845":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":2.449489742783178},"848":{"tf":2.23606797749979},"849":{"tf":2.8284271247461903},"850":{"tf":1.4142135623730951},"851":{"tf":1.0},"852":{"tf":1.4142135623730951},"853":{"tf":1.0},"854":{"tf":1.0},"855":{"tf":1.0},"856":{"tf":1.0},"94":{"tf":1.0}},"l":{"c":{"df":1,"docs":{"79":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"'":{"df":2,"docs":{"252":{"tf":1.0},"501":{"tf":1.0}}},"df":1,"docs":{"205":{"tf":1.0}}}},"u":{"df":1,"docs":{"988":{"tf":1.0}}}},"y":{"[":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"d":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"112":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"a":{"df":0,"docs":{},"z":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"279":{"tf":1.0}}}},"df":0,"docs":{}}},"df":5,"docs":{"112":{"tf":1.4142135623730951},"45":{"tf":1.0},"571":{"tf":1.0},"749":{"tf":1.4142135623730951},"94":{"tf":1.0}},"e":{"a":{"df":0,"docs":{},"r":{"df":8,"docs":{"198":{"tf":1.0},"199":{"tf":1.7320508075688772},"470":{"tf":1.0},"471":{"tf":1.0},"778":{"tf":1.0},"928":{"tf":1.0},"931":{"tf":1.0},"932":{"tf":1.0}},"l":{"df":0,"docs":{},"i":{"df":1,"docs":{"471":{"tf":1.4142135623730951}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":3,"docs":{"720":{"tf":1.0},"776":{"tf":1.0},"992":{"tf":1.0}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"f":{"df":1,"docs":{"874":{"tf":1.0}}}}}}}}}},"z":{"[":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"112":{"tf":1.0}}},"df":0,"docs":{}}}},"c":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"364":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":11,"docs":{"207":{"tf":1.4142135623730951},"222":{"tf":1.0},"435":{"tf":1.4142135623730951},"520":{"tf":1.0},"525":{"tf":1.0},"632":{"tf":1.0},"634":{"tf":1.0},"635":{"tf":1.0},"648":{"tf":1.0},"735":{"tf":2.0},"879":{"tf":2.0}}}}},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"17":{"tf":1.0}}}}}},"k":{"df":5,"docs":{"322":{"tf":1.0},"340":{"tf":1.0},"364":{"tf":1.7320508075688772},"537":{"tf":1.0},"54":{"tf":1.0}}},"o":{"df":0,"docs":{},"m":{"b":{"df":0,"docs":{},"i":{"df":1,"docs":{"211":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"639":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"n":{"d":{"a":{"df":0,"docs":{},"x":{"df":1,"docs":{"513":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"311":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"title":{"root":{"0":{"0":{"0":{"0":{"df":2,"docs":{"56":{"tf":1.0},"709":{"tf":1.0}}},"1":{"df":1,"docs":{"940":{"tf":1.0}}},"2":{"df":1,"docs":{"957":{"tf":1.0}}},"4":{"df":1,"docs":{"730":{"tf":1.0}}},"6":{"df":1,"docs":{"741":{"tf":1.0}}},"7":{"df":1,"docs":{"229":{"tf":1.0}}},"8":{"df":1,"docs":{"247":{"tf":1.0}}},"9":{"df":1,"docs":{"757":{"tf":1.0}}},"df":0,"docs":{}},"1":{"0":{"df":1,"docs":{"263":{"tf":1.0}}},"2":{"df":1,"docs":{"268":{"tf":1.0}}},"3":{"df":1,"docs":{"279":{"tf":1.0}}},"4":{"df":1,"docs":{"294":{"tf":1.0}}},"5":{"df":1,"docs":{"771":{"tf":1.0}}},"df":0,"docs":{}},"2":{"2":{"df":1,"docs":{"311":{"tf":1.0}}},"6":{"df":1,"docs":{"322":{"tf":1.0}}},"df":0,"docs":{}},"3":{"2":{"df":1,"docs":{"366":{"tf":1.0}}},"5":{"df":1,"docs":{"795":{"tf":1.0}}},"df":0,"docs":{}},"4":{"2":{"df":1,"docs":{"386":{"tf":1.0}}},"3":{"df":1,"docs":{"400":{"tf":1.0}}},"4":{"df":1,"docs":{"808":{"tf":1.0}}},"5":{"df":1,"docs":{"410":{"tf":1.0}}},"7":{"df":1,"docs":{"430":{"tf":1.0}}},"8":{"df":1,"docs":{"451":{"tf":1.0}}},"df":0,"docs":{}},"5":{"0":{"df":1,"docs":{"465":{"tf":1.0}}},"4":{"df":1,"docs":{"827":{"tf":1.0}}},"6":{"df":1,"docs":{"481":{"tf":1.0}}},"9":{"df":1,"docs":{"495":{"tf":1.0}}},"df":0,"docs":{}},"7":{"0":{"df":1,"docs":{"841":{"tf":1.0}}},"3":{"df":1,"docs":{"857":{"tf":1.0}}},"4":{"df":1,"docs":{"871":{"tf":1.0}}},"7":{"df":1,"docs":{"891":{"tf":1.0}}},"8":{"df":1,"docs":{"513":{"tf":1.0}}},"df":0,"docs":{}},"8":{"4":{"df":1,"docs":{"535":{"tf":1.0}}},"8":{"df":1,"docs":{"908":{"tf":1.0}}},"9":{"df":1,"docs":{"926":{"tf":1.0}}},"df":0,"docs":{}},"9":{"1":{"df":1,"docs":{"549":{"tf":1.0}}},"7":{"df":1,"docs":{"563":{"tf":1.0}}},"9":{"df":1,"docs":{"584":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{"0":{"0":{"df":1,"docs":{"598":{"tf":1.0}}},"1":{"df":1,"docs":{"613":{"tf":1.0}}},"3":{"df":1,"docs":{"627":{"tf":1.0}}},"5":{"df":1,"docs":{"649":{"tf":1.0}}},"6":{"df":1,"docs":{"974":{"tf":1.0}}},"7":{"df":1,"docs":{"664":{"tf":1.0}}},"8":{"df":1,"docs":{"678":{"tf":1.0}}},"df":0,"docs":{}},"1":{"1":{"df":1,"docs":{"79":{"tf":1.0}}},"2":{"df":1,"docs":{"988":{"tf":1.0}}},"4":{"df":1,"docs":{"93":{"tf":1.0}}},"7":{"df":1,"docs":{"106":{"tf":1.0}}},"df":0,"docs":{}},"2":{"0":{"df":1,"docs":{"122":{"tf":1.0}}},"1":{"df":1,"docs":{"136":{"tf":1.0}}},"2":{"df":1,"docs":{"692":{"tf":1.0}}},"3":{"df":1,"docs":{"150":{"tf":1.0}}},"4":{"df":1,"docs":{"164":{"tf":1.0}}},"5":{"df":1,"docs":{"1":{"tf":1.0}}},"6":{"df":1,"docs":{"17":{"tf":1.0}}},"7":{"df":1,"docs":{"38":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"1":{".":{"1":{"df":1,"docs":{"325":{"tf":1.0}}},"2":{"df":1,"docs":{"326":{"tf":1.0}}},"df":0,"docs":{}},"0":{"df":1,"docs":{"359":{"tf":1.0}}},"1":{"4":{"df":1,"docs":{"182":{"tf":1.0}}},"df":1,"docs":{"360":{"tf":1.0}}},"2":{".":{"1":{"df":1,"docs":{"362":{"tf":1.0}}},"2":{"df":1,"docs":{"363":{"tf":1.0}}},"3":{"df":1,"docs":{"364":{"tf":1.0}}},"4":{"df":1,"docs":{"365":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"361":{"tf":1.0}}},"df":3,"docs":{"195":{"tf":1.0},"324":{"tf":1.0},"846":{"tf":1.0}}},"2":{".":{"1":{"df":1,"docs":{"328":{"tf":1.0}}},"2":{"df":1,"docs":{"329":{"tf":1.0}}},"df":0,"docs":{}},"0":{"df":1,"docs":{"891":{"tf":1.0}}},"df":3,"docs":{"327":{"tf":1.0},"603":{"tf":1.0},"847":{"tf":1.0}}},"3":{".":{"1":{"df":1,"docs":{"331":{"tf":1.0}}},"2":{"df":2,"docs":{"332":{"tf":1.0},"333":{"tf":1.0}}},"3":{"df":1,"docs":{"334":{"tf":1.0}}},"df":0,"docs":{}},"4":{"df":1,"docs":{"782":{"tf":1.0}}},"df":3,"docs":{"330":{"tf":1.0},"603":{"tf":1.0},"848":{"tf":1.0}}},"4":{".":{"1":{"df":1,"docs":{"336":{"tf":1.0}}},"2":{"df":1,"docs":{"337":{"tf":1.0}}},"3":{"df":1,"docs":{"338":{"tf":1.0}}},"4":{"df":1,"docs":{"339":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"335":{"tf":1.0}}},"5":{".":{"1":{"df":1,"docs":{"341":{"tf":1.0}}},"df":0,"docs":{}},"df":5,"docs":{"164":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"215":{"tf":1.0},"340":{"tf":1.0}}},"6":{".":{"1":{"0":{"df":1,"docs":{"352":{"tf":1.0}}},"df":0,"docs":{}},"2":{"df":1,"docs":{"343":{"tf":1.0}}},"3":{"df":1,"docs":{"344":{"tf":1.0}}},"4":{"df":1,"docs":{"345":{"tf":1.0}}},"5":{"df":1,"docs":{"346":{"tf":1.0}}},"6":{"df":1,"docs":{"347":{"tf":1.0}}},"7":{"df":1,"docs":{"348":{"tf":1.0}}},"8":{"df":1,"docs":{"349":{"tf":1.0}}},"9":{".":{"1":{"df":1,"docs":{"351":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"350":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"342":{"tf":1.0}}},"7":{"df":1,"docs":{"353":{"tf":1.0}}},"8":{"df":1,"docs":{"354":{"tf":1.0}}},"9":{".":{"1":{"df":1,"docs":{"356":{"tf":1.0}}},"2":{"df":1,"docs":{"357":{"tf":1.0}}},"3":{"df":1,"docs":{"358":{"tf":1.0}}},"df":0,"docs":{}},"df":1,"docs":{"355":{"tf":1.0}}},"a":{"b":{"df":0,"docs":{},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"782":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"323":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"c":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"782":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"l":{"df":2,"docs":{"352":{"tf":1.0},"47":{"tf":1.0}}}}}}},"df":0,"docs":{}},"d":{"d":{"df":3,"docs":{"386":{"tf":1.0},"495":{"tf":1.0},"908":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"426":{"tf":1.0}}}}},"df":0,"docs":{}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"572":{"tf":1.0}}}}},"df":1,"docs":{"268":{"tf":1.0}},"j":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"182":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"311":{"tf":1.0}}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"195":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"i":{"a":{"df":2,"docs":{"332":{"tf":1.0},"692":{"tf":1.0}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"o":{"c":{"df":2,"docs":{"374":{"tf":1.0},"730":{"tf":1.0}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":3,"docs":{"213":{"tf":1.0},"227":{"tf":1.0},"55":{"tf":1.0}}}}}}},"n":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":1,"docs":{"571":{"tf":1.0}}}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"y":{"df":0,"docs":{},"m":{"df":1,"docs":{"365":{"tf":1.0}}}}}}},"p":{"df":0,"docs":{},"i":{"df":2,"docs":{"22":{"tf":1.0},"279":{"tf":1.0}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"x":{"df":1,"docs":{"450":{"tf":1.0}}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"o":{"a":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"416":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"v":{"df":1,"docs":{"721":{"tf":1.0}}}}}}},"r":{"c":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"373":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{},"t":{"df":60,"docs":{"1013":{"tf":1.0},"105":{"tf":1.0},"120":{"tf":1.0},"133":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"161":{"tf":1.0},"179":{"tf":1.0},"192":{"tf":1.0},"214":{"tf":1.0},"228":{"tf":1.0},"242":{"tf":1.0},"260":{"tf":1.0},"277":{"tf":1.0},"291":{"tf":1.0},"308":{"tf":1.0},"319":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"383":{"tf":1.0},"397":{"tf":1.0},"409":{"tf":1.0},"447":{"tf":1.0},"462":{"tf":1.0},"479":{"tf":1.0},"492":{"tf":1.0},"510":{"tf":1.0},"532":{"tf":1.0},"546":{"tf":1.0},"560":{"tf":1.0},"583":{"tf":1.0},"595":{"tf":1.0},"610":{"tf":1.0},"624":{"tf":1.0},"646":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"706":{"tf":1.0},"726":{"tf":1.0},"738":{"tf":1.0},"74":{"tf":1.0},"754":{"tf":1.0},"768":{"tf":1.0},"780":{"tf":1.0},"793":{"tf":1.0},"805":{"tf":1.0},"824":{"tf":1.0},"838":{"tf":1.0},"869":{"tf":1.0},"888":{"tf":1.0},"90":{"tf":1.0},"905":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"937":{"tf":1.0},"954":{"tf":1.0},"971":{"tf":1.0},"985":{"tf":1.0},"999":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":5,"docs":{"1":{"tf":1.0},"410":{"tf":1.0},"470":{"tf":1.0},"603":{"tf":1.0},"692":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"7":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":2,"docs":{"430":{"tf":1.0},"438":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":2,"docs":{"169":{"tf":1.0},"549":{"tf":1.0}}}}}}},"v":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":4,"docs":{"430":{"tf":1.0},"436":{"tf":1.0},"437":{"tf":1.0},"722":{"tf":1.0}}}}},"df":0,"docs":{}}},"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"637":{"tf":1.0},"720":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"62":{"tf":1.0}}}},"g":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"39":{"tf":1.0},"894":{"tf":1.0},"911":{"tf":1.0}}},"df":0,"docs":{}}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"635":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"340":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"341":{"tf":1.0}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"416":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"e":{"df":3,"docs":{"428":{"tf":1.0},"495":{"tf":1.0},"808":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":1,"docs":{"49":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"113":{"tf":1.0}}}}}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"777":{"tf":1.0}}}}}}}},"i":{"df":0,"docs":{},"n":{"d":{"df":2,"docs":{"338":{"tf":1.0},"348":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"328":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":2,"docs":{"400":{"tf":1.0},"636":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"247":{"tf":1.0}}},"df":0,"docs":{}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"908":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"525":{"tf":1.0}}},"df":0,"docs":{}}},"l":{"df":0,"docs":{},"k":{"df":2,"docs":{"741":{"tf":1.0},"776":{"tf":1.0}}}},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"263":{"tf":1.0}}}}},"y":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":1,"docs":{"891":{"tf":1.0}}}}}},"c":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"336":{"tf":1.0},"337":{"tf":1.0},"627":{"tf":1.0}}},"df":0,"docs":{}},"l":{"df":1,"docs":{"122":{"tf":1.0}}}},"df":0,"docs":{}},"p":{"a":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"495":{"tf":1.0},"500":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":2,"docs":{"876":{"tf":1.0},"881":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"714":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":13,"docs":{"205":{"tf":1.0},"247":{"tf":1.0},"344":{"tf":1.0},"347":{"tf":1.0},"362":{"tf":1.0},"503":{"tf":1.0},"603":{"tf":1.0},"637":{"tf":1.0},"64":{"tf":1.0},"643":{"tf":1.0},"78":{"tf":1.0},"908":{"tf":1.0},"957":{"tf":1.0}}}},"n":{"df":0,"docs":{},"g":{"df":7,"docs":{"169":{"tf":1.0},"172":{"tf":1.0},"301":{"tf":1.0},"345":{"tf":1.0},"634":{"tf":1.0},"698":{"tf":1.0},"736":{"tf":1.0}}}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"k":{"df":3,"docs":{"430":{"tf":1.0},"437":{"tf":1.0},"438":{"tf":1.0}}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":3,"docs":{"339":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"757":{"tf":1.0},"827":{"tf":1.0}}}}}}},"o":{"d":{"df":0,"docs":{},"e":{"df":7,"docs":{"150":{"tf":1.0},"333":{"tf":1.0},"362":{"tf":1.0},"435":{"tf":1.0},"63":{"tf":1.0},"64":{"tf":1.0},"750":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"229":{"tf":1.0}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":6,"docs":{"106":{"tf":1.0},"111":{"tf":1.0},"113":{"tf":1.0},"268":{"tf":1.0},"273":{"tf":1.0},"715":{"tf":1.0}}}},"df":0,"docs":{}}}},"m":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"627":{"tf":1.0}}}}},"p":{"a":{"df":0,"docs":{},"t":{"df":110,"docs":{"10":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1012":{"tf":1.0},"104":{"tf":1.0},"116":{"tf":1.0},"119":{"tf":1.0},"129":{"tf":1.0},"13":{"tf":1.0},"132":{"tf":1.0},"143":{"tf":1.0},"146":{"tf":1.0},"157":{"tf":1.0},"160":{"tf":1.0},"175":{"tf":1.0},"178":{"tf":1.0},"189":{"tf":1.0},"191":{"tf":1.0},"210":{"tf":1.0},"224":{"tf":1.0},"238":{"tf":1.0},"241":{"tf":1.0},"256":{"tf":1.0},"259":{"tf":1.0},"276":{"tf":1.0},"287":{"tf":1.0},"290":{"tf":1.0},"307":{"tf":1.0},"31":{"tf":1.0},"318":{"tf":1.0},"34":{"tf":1.0},"355":{"tf":1.0},"358":{"tf":1.0},"379":{"tf":1.0},"382":{"tf":1.0},"393":{"tf":1.0},"396":{"tf":1.0},"405":{"tf":1.0},"408":{"tf":1.0},"421":{"tf":1.0},"424":{"tf":1.0},"443":{"tf":1.0},"446":{"tf":1.0},"458":{"tf":1.0},"461":{"tf":1.0},"475":{"tf":1.0},"478":{"tf":1.0},"488":{"tf":1.0},"491":{"tf":1.0},"506":{"tf":1.0},"509":{"tf":1.0},"52":{"tf":1.0},"529":{"tf":1.0},"531":{"tf":1.0},"542":{"tf":1.0},"545":{"tf":1.0},"556":{"tf":1.0},"559":{"tf":1.0},"579":{"tf":1.0},"582":{"tf":1.0},"591":{"tf":1.0},"594":{"tf":1.0},"606":{"tf":1.0},"609":{"tf":1.0},"620":{"tf":1.0},"623":{"tf":1.0},"635":{"tf":1.0},"642":{"tf":1.0},"657":{"tf":1.0},"660":{"tf":1.0},"671":{"tf":1.0},"674":{"tf":1.0},"685":{"tf":1.0},"688":{"tf":1.0},"70":{"tf":1.0},"702":{"tf":1.0},"705":{"tf":1.0},"725":{"tf":1.0},"73":{"tf":1.0},"764":{"tf":1.0},"767":{"tf":1.0},"789":{"tf":1.0},"792":{"tf":1.0},"802":{"tf":1.0},"804":{"tf":1.0},"820":{"tf":1.0},"823":{"tf":1.0},"834":{"tf":1.0},"837":{"tf":1.0},"851":{"tf":1.0},"854":{"tf":1.0},"86":{"tf":1.0},"865":{"tf":1.0},"868":{"tf":1.0},"884":{"tf":1.0},"887":{"tf":1.0},"89":{"tf":1.0},"901":{"tf":1.0},"904":{"tf":1.0},"918":{"tf":1.0},"921":{"tf":1.0},"936":{"tf":1.0},"950":{"tf":1.0},"953":{"tf":1.0},"967":{"tf":1.0},"970":{"tf":1.0},"981":{"tf":1.0},"984":{"tf":1.0},"995":{"tf":1.0},"998":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"717":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"988":{"tf":1.0}}}}}}}},"n":{"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"827":{"tf":1.0}}}},"r":{"df":0,"docs":{},"n":{"df":2,"docs":{"420":{"tf":1.0},"724":{"tf":1.0}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"752":{"tf":1.0},"846":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"m":{"df":2,"docs":{"122":{"tf":1.0},"182":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":2,"docs":{"17":{"tf":1.0},"322":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"51":{"tf":1.0},"572":{"tf":1.0},"881":{"tf":1.0}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"957":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"329":{"tf":1.0}}}}}}},"df":0,"docs":{}}}},"v":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"t":{"df":2,"docs":{"575":{"tf":1.0},"795":{"tf":1.0}}}},"df":0,"docs":{}}}},"r":{"df":0,"docs":{},"e":{":":{":":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":0,"docs":{},"e":{"_":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"284":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}},"df":3,"docs":{"279":{"tf":1.0},"328":{"tf":1.0},"908":{"tf":1.0}},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"627":{"tf":1.0}}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":7,"docs":{"195":{"tf":1.0},"205":{"tf":1.0},"206":{"tf":1.0},"215":{"tf":1.0},"263":{"tf":1.0},"741":{"tf":1.0},"957":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":2,"docs":{"346":{"tf":1.0},"549":{"tf":1.0}}}}}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"p":{"df":0,"docs":{},"h":{"df":1,"docs":{"340":{"tf":1.0}}}}},"df":0,"docs":{}}}}}}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":3,"docs":{"1002":{"tf":1.0},"751":{"tf":1.0},"93":{"tf":1.0}}}}}},"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":1,"docs":{"331":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":1,"docs":{"857":{"tf":1.0}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"573":{"tf":1.0}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"331":{"tf":1.0}}}}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":1,"docs":{"795":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"n":{"d":{"df":3,"docs":{"814":{"tf":1.0},"815":{"tf":1.0},"817":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"y":{"df":2,"docs":{"363":{"tf":1.0},"375":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":4,"docs":{"410":{"tf":1.0},"429":{"tf":1.0},"857":{"tf":1.0},"908":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":1,"docs":{"782":{"tf":1.0}}}}},"s":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"632":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"df":2,"docs":{"43":{"tf":1.0},"771":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"692":{"tf":1.0}}}}}},"t":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"204":{"tf":1.0}}}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"p":{"df":1,"docs":{"328":{"tf":1.0}}}}}}}},"h":{"df":0,"docs":{},"t":{"df":5,"docs":{"247":{"tf":1.0},"252":{"tf":1.0},"501":{"tf":1.0},"502":{"tf":1.0},"549":{"tf":1.0}}}},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"603":{"tf":1.0}}}}}},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":2,"docs":{"343":{"tf":1.0},"520":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":49,"docs":{"1001":{"tf":1.0},"1015":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"181":{"tf":1.0},"194":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"246":{"tf":1.0},"262":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"321":{"tf":1.0},"361":{"tf":1.0},"37":{"tf":1.0},"385":{"tf":1.0},"399":{"tf":1.0},"449":{"tf":1.0},"464":{"tf":1.0},"494":{"tf":1.0},"512":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"562":{"tf":1.0},"597":{"tf":1.0},"612":{"tf":1.0},"626":{"tf":1.0},"648":{"tf":1.0},"663":{"tf":1.0},"677":{"tf":1.0},"691":{"tf":1.0},"708":{"tf":1.0},"728":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"807":{"tf":1.0},"826":{"tf":1.0},"840":{"tf":1.0},"890":{"tf":1.0},"907":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"939":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}}}},"df":0,"docs":{}}},"s":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"495":{"tf":1.0},"549":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":2,"docs":{"243":{"tf":1.0},"778":{"tf":1.0}}}}}},"df":0,"docs":{}}},"m":{"df":0,"docs":{},"p":{"df":1,"docs":{"222":{"tf":1.0}}}},"o":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"848":{"tf":1.0}}}}}}}},"df":0,"docs":{}},"r":{"a":{"df":0,"docs":{},"w":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":61,"docs":{"1007":{"tf":1.0},"114":{"tf":1.0},"127":{"tf":1.0},"141":{"tf":1.0},"155":{"tf":1.0},"173":{"tf":1.0},"187":{"tf":1.0},"213":{"tf":1.0},"227":{"tf":1.0},"236":{"tf":1.0},"254":{"tf":1.0},"27":{"tf":1.0},"274":{"tf":1.0},"285":{"tf":1.0},"303":{"tf":1.0},"316":{"tf":1.0},"353":{"tf":1.0},"377":{"tf":1.0},"391":{"tf":1.0},"418":{"tf":1.0},"441":{"tf":1.0},"456":{"tf":1.0},"473":{"tf":1.0},"486":{"tf":1.0},"504":{"tf":1.0},"527":{"tf":1.0},"540":{"tf":1.0},"55":{"tf":1.0},"554":{"tf":1.0},"577":{"tf":1.0},"589":{"tf":1.0},"604":{"tf":1.0},"618":{"tf":1.0},"638":{"tf":1.0},"655":{"tf":1.0},"669":{"tf":1.0},"68":{"tf":1.0},"683":{"tf":1.0},"700":{"tf":1.0},"724":{"tf":1.0},"737":{"tf":1.0},"753":{"tf":1.0},"762":{"tf":1.0},"779":{"tf":1.0},"787":{"tf":1.0},"8":{"tf":1.0},"800":{"tf":1.0},"818":{"tf":1.0},"832":{"tf":1.0},"84":{"tf":1.0},"849":{"tf":1.0},"863":{"tf":1.0},"882":{"tf":1.0},"899":{"tf":1.0},"915":{"tf":1.0},"934":{"tf":1.0},"945":{"tf":1.0},"962":{"tf":1.0},"979":{"tf":1.0},"98":{"tf":1.0},"993":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"y":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"m":{"df":1,"docs":{"741":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":1,"docs":{"207":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"y":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":1,"docs":{"329":{"tf":1.0}}}}}}}}}},"d":{"df":0,"docs":{},"g":{"df":1,"docs":{"881":{"tf":1.0}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"93":{"tf":1.0}}}}}}},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"i":{"df":0,"docs":{},"r":{"df":1,"docs":{"571":{"tf":1.0}}}}}},"n":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"170":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"311":{"tf":1.0}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"481":{"tf":1.0}}},"df":0,"docs":{}}}},"h":{"a":{"df":0,"docs":{},"n":{"c":{"df":2,"docs":{"416":{"tf":1.0},"427":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"816":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"416":{"tf":1.0}}}}}},"p":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"h":{"df":1,"docs":{"345":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"435":{"tf":1.0}}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":108,"docs":{"10":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1011":{"tf":1.0},"103":{"tf":1.0},"116":{"tf":1.0},"118":{"tf":1.0},"12":{"tf":1.0},"129":{"tf":1.0},"131":{"tf":1.0},"143":{"tf":1.0},"145":{"tf":1.0},"157":{"tf":1.0},"159":{"tf":1.0},"175":{"tf":1.0},"177":{"tf":1.0},"189":{"tf":1.0},"191":{"tf":1.0},"210":{"tf":1.0},"224":{"tf":1.0},"238":{"tf":1.0},"240":{"tf":1.0},"256":{"tf":1.0},"258":{"tf":1.0},"276":{"tf":1.0},"287":{"tf":1.0},"289":{"tf":1.0},"306":{"tf":1.0},"31":{"tf":1.0},"318":{"tf":1.0},"33":{"tf":1.0},"355":{"tf":1.0},"357":{"tf":1.0},"379":{"tf":1.0},"381":{"tf":1.0},"393":{"tf":1.0},"395":{"tf":1.0},"405":{"tf":1.0},"407":{"tf":1.0},"421":{"tf":1.0},"423":{"tf":1.0},"443":{"tf":1.0},"445":{"tf":1.0},"458":{"tf":1.0},"460":{"tf":1.0},"475":{"tf":1.0},"477":{"tf":1.0},"488":{"tf":1.0},"490":{"tf":1.0},"506":{"tf":1.0},"508":{"tf":1.0},"529":{"tf":1.0},"531":{"tf":1.0},"542":{"tf":1.0},"544":{"tf":1.0},"556":{"tf":1.0},"558":{"tf":1.0},"579":{"tf":1.0},"581":{"tf":1.0},"591":{"tf":1.0},"593":{"tf":1.0},"606":{"tf":1.0},"608":{"tf":1.0},"620":{"tf":1.0},"622":{"tf":1.0},"641":{"tf":1.0},"657":{"tf":1.0},"659":{"tf":1.0},"671":{"tf":1.0},"673":{"tf":1.0},"685":{"tf":1.0},"687":{"tf":1.0},"70":{"tf":1.0},"702":{"tf":1.0},"704":{"tf":1.0},"72":{"tf":1.0},"725":{"tf":1.0},"764":{"tf":1.0},"766":{"tf":1.0},"789":{"tf":1.0},"791":{"tf":1.0},"802":{"tf":1.0},"804":{"tf":1.0},"820":{"tf":1.0},"822":{"tf":1.0},"834":{"tf":1.0},"836":{"tf":1.0},"851":{"tf":1.0},"853":{"tf":1.0},"86":{"tf":1.0},"865":{"tf":1.0},"867":{"tf":1.0},"88":{"tf":1.0},"884":{"tf":1.0},"886":{"tf":1.0},"901":{"tf":1.0},"903":{"tf":1.0},"918":{"tf":1.0},"920":{"tf":1.0},"936":{"tf":1.0},"950":{"tf":1.0},"952":{"tf":1.0},"967":{"tf":1.0},"969":{"tf":1.0},"981":{"tf":1.0},"983":{"tf":1.0},"995":{"tf":1.0},"997":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"t":{"a":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"847":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"38":{"tf":1.0}}}}}}}}},"x":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":4,"docs":{"603":{"tf":1.0},"654":{"tf":1.0},"699":{"tf":1.0},"752":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"26":{"tf":1.0},"664":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"23":{"tf":1.0}}}}}}},"df":0,"docs":{}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"931":{"tf":1.0}}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"29":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"n":{"df":60,"docs":{"1006":{"tf":1.0},"110":{"tf":1.0},"126":{"tf":1.0},"140":{"tf":1.0},"154":{"tf":1.0},"168":{"tf":1.0},"186":{"tf":1.0},"202":{"tf":1.0},"21":{"tf":1.0},"220":{"tf":1.0},"234":{"tf":1.0},"251":{"tf":1.0},"267":{"tf":1.0},"272":{"tf":1.0},"283":{"tf":1.0},"299":{"tf":1.0},"315":{"tf":1.0},"370":{"tf":1.0},"390":{"tf":1.0},"404":{"tf":1.0},"415":{"tf":1.0},"434":{"tf":1.0},"455":{"tf":1.0},"469":{"tf":1.0},"485":{"tf":1.0},"499":{"tf":1.0},"5":{"tf":1.0},"519":{"tf":1.0},"539":{"tf":1.0},"553":{"tf":1.0},"567":{"tf":1.0},"588":{"tf":1.0},"60":{"tf":1.0},"602":{"tf":1.0},"617":{"tf":1.0},"631":{"tf":1.0},"653":{"tf":1.0},"668":{"tf":1.0},"682":{"tf":1.0},"696":{"tf":1.0},"719":{"tf":1.0},"734":{"tf":1.0},"746":{"tf":1.0},"761":{"tf":1.0},"775":{"tf":1.0},"786":{"tf":1.0},"799":{"tf":1.0},"813":{"tf":1.0},"83":{"tf":1.0},"831":{"tf":1.0},"845":{"tf":1.0},"860":{"tf":1.0},"878":{"tf":1.0},"898":{"tf":1.0},"930":{"tf":1.0},"944":{"tf":1.0},"961":{"tf":1.0},"97":{"tf":1.0},"978":{"tf":1.0},"992":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":3,"docs":{"24":{"tf":1.0},"576":{"tf":1.0},"584":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":5,"docs":{"164":{"tf":1.0},"169":{"tf":1.0},"521":{"tf":1.0},"526":{"tf":1.0},"535":{"tf":1.0}}}}}}}}},"f":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":1,"docs":{"56":{"tf":1.0}}}}}},"df":0,"docs":{},"e":{"d":{"b":{"a":{"c":{"df":0,"docs":{},"k":{"df":1,"docs":{"244":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"df":2,"docs":{"649":{"tf":1.0},"974":{"tf":1.0}}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":1,"docs":{"465":{"tf":1.0}}}}}}}}}}},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"627":{"tf":1.0}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"891":{"tf":1.0}}}}}}}}}}}},"l":{"a":{"df":0,"docs":{},"g":{"df":1,"docs":{"729":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"926":{"tf":1.0}}}},"df":0,"docs":{}}}},"o":{"df":0,"docs":{},"w":{"df":1,"docs":{"26":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"170":{"tf":1.0},"535":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"n":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":10,"docs":{"205":{"tf":1.0},"334":{"tf":1.0},"373":{"tf":1.0},"400":{"tf":1.0},"428":{"tf":1.0},"438":{"tf":1.0},"735":{"tf":1.0},"749":{"tf":1.0},"879":{"tf":1.0},"93":{"tf":1.0}}}}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"416":{"tf":1.0},"77":{"tf":1.0},"778":{"tf":1.0}}}}}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":51,"docs":{"1001":{"tf":1.0},"1015":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"181":{"tf":1.0},"194":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"246":{"tf":1.0},"262":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"321":{"tf":1.0},"361":{"tf":1.0},"37":{"tf":1.0},"385":{"tf":1.0},"399":{"tf":1.0},"449":{"tf":1.0},"464":{"tf":1.0},"494":{"tf":1.0},"512":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"562":{"tf":1.0},"597":{"tf":1.0},"612":{"tf":1.0},"626":{"tf":1.0},"648":{"tf":1.0},"663":{"tf":1.0},"677":{"tf":1.0},"691":{"tf":1.0},"708":{"tf":1.0},"728":{"tf":1.0},"740":{"tf":1.0},"755":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"807":{"tf":1.0},"826":{"tf":1.0},"840":{"tf":1.0},"890":{"tf":1.0},"907":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"939":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}}}}}}},"g":{"a":{"df":1,"docs":{"51":{"tf":1.0}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":5,"docs":{"171":{"tf":1.0},"451":{"tf":1.0},"524":{"tf":1.0},"535":{"tf":1.0},"78":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"n":{"df":1,"docs":{"427":{"tf":1.0}}}}}}}},"h":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"l":{"df":2,"docs":{"62":{"tf":1.0},"65":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"77":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"d":{"df":1,"docs":{"503":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"343":{"tf":1.0}}}}},"df":0,"docs":{},"p":{"df":1,"docs":{"827":{"tf":1.0}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":1,"docs":{"56":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"664":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"l":{"d":{"df":1,"docs":{"66":{"tf":1.0}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"t":{"df":4,"docs":{"400":{"tf":1.0},"730":{"tf":1.0},"735":{"tf":1.0},"93":{"tf":1.0}}}}},"u":{"b":{"df":1,"docs":{"410":{"tf":1.0}}},"df":0,"docs":{}}},"i":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"891":{"tf":1.0},"908":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"50":{"tf":1.0},"933":{"tf":1.0}},"o":{"df":0,"docs":{},"r":{"df":1,"docs":{"325":{"tf":1.0}}}}}}}}}},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":4,"docs":{"294":{"tf":1.0},"400":{"tf":1.0},"649":{"tf":1.0},"757":{"tf":1.0}}}}}}},"n":{"c":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"526":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"891":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"334":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"f":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"926":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"522":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":0,"docs":{},"f":{"df":2,"docs":{"598":{"tf":1.0},"698":{"tf":1.0}}}}}},"df":0,"docs":{}}}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"244":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"206":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"r":{"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":3,"docs":{"598":{"tf":1.0},"6":{"tf":1.0},"698":{"tf":1.0}}}},"df":0,"docs":{}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"a":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"362":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"f":{"a":{"c":{"df":3,"docs":{"215":{"tf":1.0},"341":{"tf":1.0},"372":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"m":{"df":0,"docs":{},"e":{"d":{"df":0,"docs":{},"i":{"df":1,"docs":{"150":{"tf":1.0}}}},"df":0,"docs":{}}}}},"r":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"u":{"c":{"df":7,"docs":{"150":{"tf":1.0},"17":{"tf":1.0},"400":{"tf":1.0},"584":{"tf":1.0},"61":{"tf":1.0},"627":{"tf":1.0},"93":{"tf":1.0}},"t":{"df":3,"docs":{"0":{"tf":1.0},"334":{"tf":1.0},"335":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"u":{"df":2,"docs":{"28":{"tf":1.0},"29":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"136":{"tf":1.0}}}}}},"j":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"38":{"tf":1.0},"43":{"tf":1.0}}}},"df":0,"docs":{}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":2,"docs":{"150":{"tf":1.0},"46":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"m":{"a":{"df":2,"docs":{"376":{"tf":1.0},"862":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"841":{"tf":1.0}}}}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}}}},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"891":{"tf":1.0}}}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"df":1,"docs":{"757":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"223":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"k":{"df":1,"docs":{"429":{"tf":1.0}}}}},"o":{"c":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"782":{"tf":1.0}}}},"df":0,"docs":{},"k":{"df":2,"docs":{"294":{"tf":1.0},"908":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":1,"docs":{"343":{"tf":1.0}},"i":{"c":{"df":1,"docs":{"713":{"tf":1.0}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"g":{"df":1,"docs":{"417":{"tf":1.0}}}},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"410":{"tf":1.0},"416":{"tf":1.0}}}}}}},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":4,"docs":{"206":{"tf":1.0},"771":{"tf":1.0},"776":{"tf":1.0},"940":{"tf":1.0}}}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":49,"docs":{"1001":{"tf":1.0},"1015":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"181":{"tf":1.0},"194":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"246":{"tf":1.0},"262":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"321":{"tf":1.0},"361":{"tf":1.0},"37":{"tf":1.0},"385":{"tf":1.0},"399":{"tf":1.0},"449":{"tf":1.0},"464":{"tf":1.0},"494":{"tf":1.0},"512":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"562":{"tf":1.0},"597":{"tf":1.0},"612":{"tf":1.0},"626":{"tf":1.0},"648":{"tf":1.0},"663":{"tf":1.0},"677":{"tf":1.0},"691":{"tf":1.0},"708":{"tf":1.0},"728":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"807":{"tf":1.0},"826":{"tf":1.0},"840":{"tf":1.0},"890":{"tf":1.0},"907":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"939":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}}}}}},"x":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":1,"docs":{"891":{"tf":1.0}}}}}}}},"b":{"df":0,"docs":{},"m":{"df":1,"docs":{"279":{"tf":1.0}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"n":{"df":6,"docs":{"122":{"tf":1.0},"294":{"tf":1.0},"495":{"tf":1.0},"568":{"tf":1.0},"649":{"tf":1.0},"78":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"730":{"tf":1.0}}}}}},"r":{"df":0,"docs":{},"k":{"df":0,"docs":{},"l":{"df":1,"docs":{"525":{"tf":1.0}},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"z":{"df":1,"docs":{"513":{"tf":1.0}}}}}}}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"g":{"df":5,"docs":{"221":{"tf":1.0},"222":{"tf":1.0},"61":{"tf":1.0},"716":{"tf":1.0},"988":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"a":{"d":{"a":{"df":0,"docs":{},"t":{"a":{"df":5,"docs":{"1":{"tf":1.0},"513":{"tf":1.0},"517":{"tf":1.0},"520":{"tf":1.0},"521":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"351":{"tf":1.0}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"302":{"tf":1.0},"371":{"tf":1.0}}}},"df":0,"docs":{}}},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"366":{"tf":1.0}}}}}},"o":{"d":{"df":0,"docs":{},"e":{"df":1,"docs":{"974":{"tf":1.0}},"l":{"df":3,"docs":{"427":{"tf":1.0},"428":{"tf":1.0},"808":{"tf":1.0}}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"795":{"tf":1.0}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"v":{"df":63,"docs":{"1004":{"tf":1.0},"108":{"tf":1.0},"124":{"tf":1.0},"138":{"tf":1.0},"152":{"tf":1.0},"166":{"tf":1.0},"184":{"tf":1.0},"19":{"tf":1.0},"197":{"tf":1.0},"217":{"tf":1.0},"231":{"tf":1.0},"249":{"tf":1.0},"265":{"tf":1.0},"270":{"tf":1.0},"281":{"tf":1.0},"296":{"tf":1.0},"3":{"tf":1.0},"313":{"tf":1.0},"324":{"tf":1.0},"368":{"tf":1.0},"388":{"tf":1.0},"40":{"tf":1.0},"402":{"tf":1.0},"412":{"tf":1.0},"432":{"tf":1.0},"453":{"tf":1.0},"467":{"tf":1.0},"483":{"tf":1.0},"497":{"tf":1.0},"515":{"tf":1.0},"537":{"tf":1.0},"551":{"tf":1.0},"565":{"tf":1.0},"58":{"tf":1.0},"586":{"tf":1.0},"600":{"tf":1.0},"615":{"tf":1.0},"629":{"tf":1.0},"651":{"tf":1.0},"666":{"tf":1.0},"680":{"tf":1.0},"694":{"tf":1.0},"711":{"tf":1.0},"732":{"tf":1.0},"743":{"tf":1.0},"759":{"tf":1.0},"773":{"tf":1.0},"784":{"tf":1.0},"797":{"tf":1.0},"81":{"tf":1.0},"810":{"tf":1.0},"829":{"tf":1.0},"843":{"tf":1.0},"859":{"tf":1.0},"873":{"tf":1.0},"893":{"tf":1.0},"910":{"tf":1.0},"928":{"tf":1.0},"942":{"tf":1.0},"95":{"tf":1.0},"959":{"tf":1.0},"976":{"tf":1.0},"990":{"tf":1.0}}}}}},"u":{"df":0,"docs":{},"l":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":1,"docs":{"871":{"tf":1.0}}}}}}}}}},"n":{"a":{"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":1,"docs":{"56":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":0,"docs":{},"w":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":3,"docs":{"253":{"tf":1.0},"439":{"tf":1.0},"757":{"tf":1.0}},"i":{"d":{"df":1,"docs":{"678":{"tf":1.0}}},"df":0,"docs":{}}}}}}},"w":{"df":9,"docs":{"253":{"tf":1.0},"268":{"tf":1.0},"598":{"tf":1.0},"6":{"tf":1.0},"61":{"tf":1.0},"63":{"tf":1.0},"65":{"tf":1.0},"735":{"tf":1.0},"932":{"tf":1.0}}}},"f":{"df":0,"docs":{},"t":{"df":1,"docs":{"410":{"tf":1.0}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"93":{"tf":1.0}}}}},"o":{"d":{"df":0,"docs":{},"e":{"df":1,"docs":{"495":{"tf":1.0}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"1002":{"tf":1.0}}}}},"t":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"330":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":3,"docs":{"206":{"tf":1.0},"207":{"tf":1.0},"208":{"tf":1.0}}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"481":{"tf":1.0}}}}}}},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"481":{"tf":1.0}}},"p":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"38":{"tf":1.0}}}}}}}}},"r":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":2,"docs":{"931":{"tf":1.0},"932":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":2,"docs":{"427":{"tf":1.0},"692":{"tf":1.7320508075688772}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"df":0,"docs":{},"e":{"df":0,"docs":{},"w":{"df":3,"docs":{"203":{"tf":1.0},"44":{"tf":1.0},"747":{"tf":1.0}}}}}}}}},"w":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":2,"docs":{"339":{"tf":1.0},"451":{"tf":1.0}}}}}}}}}}},"p":{"2":{"5":{"6":{"df":1,"docs":{"93":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}},"a":{"df":0,"docs":{},"g":{"df":0,"docs":{},"e":{"df":1,"docs":{"827":{"tf":1.0}}}},"i":{"d":{"df":1,"docs":{"816":{"tf":1.0}}},"df":0,"docs":{}},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":2,"docs":{"871":{"tf":1.0},"908":{"tf":1.0}}}}}},"r":{"a":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":7,"docs":{"247":{"tf":1.0},"294":{"tf":1.0},"400":{"tf":1.0},"636":{"tf":1.0},"729":{"tf":1.0},"814":{"tf":1.0},"815":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":1,"docs":{"817":{"tf":1.0}},"m":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":6,"docs":{"364":{"tf":1.0},"569":{"tf":1.0},"613":{"tf":1.0},"748":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"66":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"h":{"df":1,"docs":{"440":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"g":{"_":{"c":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"150":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}},"df":0,"docs":{}},"r":{"df":1,"docs":{"481":{"tf":1.0}},"f":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":110,"docs":{"10":{"tf":1.0},"1009":{"tf":1.0},"101":{"tf":1.0},"1010":{"tf":1.0},"102":{"tf":1.0},"11":{"tf":1.0},"116":{"tf":1.0},"117":{"tf":1.0},"129":{"tf":1.0},"130":{"tf":1.0},"143":{"tf":1.0},"144":{"tf":1.0},"157":{"tf":1.0},"158":{"tf":1.0},"175":{"tf":1.0},"176":{"tf":1.0},"189":{"tf":1.0},"190":{"tf":1.0},"210":{"tf":1.0},"224":{"tf":1.0},"238":{"tf":1.0},"239":{"tf":1.0},"256":{"tf":1.0},"257":{"tf":1.0},"276":{"tf":1.0},"28":{"tf":1.0},"287":{"tf":1.0},"288":{"tf":1.0},"305":{"tf":1.0},"31":{"tf":1.0},"318":{"tf":1.0},"32":{"tf":1.0},"355":{"tf":1.0},"356":{"tf":1.0},"379":{"tf":1.0},"380":{"tf":1.0},"393":{"tf":1.0},"394":{"tf":1.0},"405":{"tf":1.0},"406":{"tf":1.0},"421":{"tf":1.0},"422":{"tf":1.0},"443":{"tf":1.0},"444":{"tf":1.0},"458":{"tf":1.0},"459":{"tf":1.0},"475":{"tf":1.0},"476":{"tf":1.0},"488":{"tf":1.0},"489":{"tf":1.0},"506":{"tf":1.0},"507":{"tf":1.0},"529":{"tf":1.0},"530":{"tf":1.0},"542":{"tf":1.0},"543":{"tf":1.0},"556":{"tf":1.0},"557":{"tf":1.0},"579":{"tf":1.0},"580":{"tf":1.0},"591":{"tf":1.0},"592":{"tf":1.0},"606":{"tf":1.0},"607":{"tf":1.0},"620":{"tf":1.0},"621":{"tf":1.0},"640":{"tf":1.0},"657":{"tf":1.0},"658":{"tf":1.0},"671":{"tf":1.0},"672":{"tf":1.0},"685":{"tf":1.0},"686":{"tf":1.0},"70":{"tf":1.0},"702":{"tf":1.0},"703":{"tf":1.0},"71":{"tf":1.0},"725":{"tf":1.0},"764":{"tf":1.0},"765":{"tf":1.0},"789":{"tf":1.0},"790":{"tf":1.0},"802":{"tf":1.0},"803":{"tf":1.0},"820":{"tf":1.0},"821":{"tf":1.0},"834":{"tf":1.0},"835":{"tf":1.0},"851":{"tf":1.0},"852":{"tf":1.0},"86":{"tf":1.0},"865":{"tf":1.0},"866":{"tf":1.0},"87":{"tf":1.0},"884":{"tf":1.0},"885":{"tf":1.0},"901":{"tf":1.0},"902":{"tf":1.0},"916":{"tf":1.0},"918":{"tf":1.0},"919":{"tf":1.0},"936":{"tf":1.0},"950":{"tf":1.0},"951":{"tf":1.0},"967":{"tf":1.0},"968":{"tf":1.0},"981":{"tf":1.0},"982":{"tf":1.0},"995":{"tf":1.0},"996":{"tf":1.0}}}}}},"i":{"df":0,"docs":{},"o":{"d":{"df":1,"docs":{"182":{"tf":1.0}}},"df":0,"docs":{}}}}},"g":{"df":0,"docs":{},"p":{"df":1,"docs":{"891":{"tf":1.0}}}},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"e":{"df":3,"docs":{"846":{"tf":1.0},"847":{"tf":1.0},"848":{"tf":1.0}}}}},"df":0,"docs":{}},"l":{"a":{"df":0,"docs":{},"n":{"df":1,"docs":{"417":{"tf":1.0}}}},"df":0,"docs":{}},"o":{"c":{"df":1,"docs":{"50":{"tf":1.0}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":1,"docs":{"778":{"tf":1.0}}}}},"l":{"df":0,"docs":{},"k":{"a":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":5,"docs":{"171":{"tf":1.0},"326":{"tf":1.0},"329":{"tf":1.0},"634":{"tf":1.0},"861":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"l":{"df":2,"docs":{"740":{"tf":1.0},"755":{"tf":1.0}}}},"df":0,"docs":{}}},"t":{"df":1,"docs":{"847":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"576":{"tf":1.0}}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"p":{"a":{"df":0,"docs":{},"r":{"df":1,"docs":{"279":{"tf":1.0}}}},"df":0,"docs":{}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"198":{"tf":1.0},"436":{"tf":1.0}}}}}}},"i":{"c":{"df":0,"docs":{},"e":{"df":2,"docs":{"428":{"tf":1.0},"741":{"tf":1.0}}}},"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"351":{"tf":1.0}}}}},"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":2,"docs":{"340":{"tf":1.0},"634":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"r":{"df":61,"docs":{"1013":{"tf":1.0},"105":{"tf":1.0},"120":{"tf":1.0},"133":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"161":{"tf":1.0},"179":{"tf":1.0},"192":{"tf":1.0},"214":{"tf":1.0},"228":{"tf":1.0},"242":{"tf":1.0},"244":{"tf":1.0},"260":{"tf":1.0},"277":{"tf":1.0},"291":{"tf":1.0},"308":{"tf":1.0},"319":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"383":{"tf":1.0},"397":{"tf":1.0},"409":{"tf":1.0},"447":{"tf":1.0},"462":{"tf":1.0},"479":{"tf":1.0},"492":{"tf":1.0},"510":{"tf":1.0},"532":{"tf":1.0},"546":{"tf":1.0},"560":{"tf":1.0},"583":{"tf":1.0},"595":{"tf":1.0},"610":{"tf":1.0},"624":{"tf":1.0},"646":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"706":{"tf":1.0},"726":{"tf":1.0},"738":{"tf":1.0},"74":{"tf":1.0},"754":{"tf":1.0},"768":{"tf":1.0},"780":{"tf":1.0},"793":{"tf":1.0},"805":{"tf":1.0},"824":{"tf":1.0},"838":{"tf":1.0},"869":{"tf":1.0},"888":{"tf":1.0},"90":{"tf":1.0},"905":{"tf":1.0},"922":{"tf":1.0},"923":{"tf":1.0},"937":{"tf":1.0},"954":{"tf":1.0},"971":{"tf":1.0},"985":{"tf":1.0},"999":{"tf":1.0}}}},"v":{"a":{"c":{"df":0,"docs":{},"i":{"df":60,"docs":{"1008":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"156":{"tf":1.0},"174":{"tf":1.0},"188":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"237":{"tf":1.0},"255":{"tf":1.0},"275":{"tf":1.0},"286":{"tf":1.0},"30":{"tf":1.0},"304":{"tf":1.0},"317":{"tf":1.0},"354":{"tf":1.0},"378":{"tf":1.0},"392":{"tf":1.0},"419":{"tf":1.0},"442":{"tf":1.0},"457":{"tf":1.0},"474":{"tf":1.0},"487":{"tf":1.0},"505":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"541":{"tf":1.0},"555":{"tf":1.0},"578":{"tf":1.0},"590":{"tf":1.0},"605":{"tf":1.0},"619":{"tf":1.0},"639":{"tf":1.0},"656":{"tf":1.0},"670":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.0},"701":{"tf":1.0},"724":{"tf":1.0},"763":{"tf":1.0},"788":{"tf":1.0},"801":{"tf":1.0},"819":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"864":{"tf":1.0},"883":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.0},"917":{"tf":1.0},"935":{"tf":1.0},"946":{"tf":1.0},"949":{"tf":1.0},"963":{"tf":1.0},"966":{"tf":1.0},"980":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"o":{"b":{"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"df":4,"docs":{"199":{"tf":1.0},"874":{"tf":1.0},"895":{"tf":1.0},"912":{"tf":1.0}}}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":4,"docs":{"112":{"tf":1.0},"268":{"tf":1.0},"46":{"tf":1.0},"64":{"tf":1.0}}}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"m":{"df":2,"docs":{"25":{"tf":1.0},"26":{"tf":1.0}}}},"df":0,"docs":{}}},"j":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"471":{"tf":1.0}}}},"df":0,"docs":{}}},"o":{"df":0,"docs":{},"f":{"df":2,"docs":{"451":{"tf":1.0},"46":{"tf":1.0}}}},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":1,"docs":{"751":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"s":{"df":3,"docs":{"301":{"tf":1.0},"569":{"tf":1.0},"933":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"o":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":6,"docs":{"253":{"tf":1.0},"322":{"tf":1.0},"335":{"tf":1.0},"342":{"tf":1.0},"439":{"tf":1.0},"757":{"tf":1.0}}}}},"df":0,"docs":{}}},"v":{"df":0,"docs":{},"i":{"d":{"df":3,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"503":{"tf":1.0}}},"df":0,"docs":{}}},"x":{"df":0,"docs":{},"i":{"df":1,"docs":{"79":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"e":{"df":3,"docs":{"523":{"tf":1.0},"67":{"tf":1.0},"815":{"tf":1.0}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"d":{"df":0,"docs":{},"o":{"df":2,"docs":{"333":{"tf":1.0},"750":{"tf":1.0}}}},"df":0,"docs":{}}}},"u":{"df":0,"docs":{},"r":{"c":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"908":{"tf":1.0}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"df":1,"docs":{"79":{"tf":1.0}}}}},"v":{"df":0,"docs":{},"f":{"df":1,"docs":{"66":{"tf":1.0}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":1,"docs":{"17":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":55,"docs":{"1000":{"tf":1.0},"1014":{"tf":1.0},"121":{"tf":1.0},"134":{"tf":1.0},"148":{"tf":1.0},"15":{"tf":1.0},"162":{"tf":1.0},"180":{"tf":1.0},"193":{"tf":1.0},"245":{"tf":1.0},"261":{"tf":1.0},"278":{"tf":1.0},"292":{"tf":1.0},"309":{"tf":1.0},"320":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"384":{"tf":1.0},"398":{"tf":1.0},"425":{"tf":1.0},"448":{"tf":1.0},"463":{"tf":1.0},"480":{"tf":1.0},"493":{"tf":1.0},"511":{"tf":1.0},"533":{"tf":1.0},"547":{"tf":1.0},"561":{"tf":1.0},"596":{"tf":1.0},"611":{"tf":1.0},"625":{"tf":1.0},"647":{"tf":1.0},"662":{"tf":1.0},"676":{"tf":1.0},"690":{"tf":1.0},"707":{"tf":1.0},"727":{"tf":1.0},"739":{"tf":1.0},"75":{"tf":1.0},"769":{"tf":1.0},"781":{"tf":1.0},"794":{"tf":1.0},"806":{"tf":1.0},"825":{"tf":1.0},"839":{"tf":1.0},"856":{"tf":1.0},"870":{"tf":1.0},"889":{"tf":1.0},"906":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"938":{"tf":1.0},"955":{"tf":1.0},"972":{"tf":1.0},"986":{"tf":1.0}}}}}}},"u":{"df":0,"docs":{},"e":{"df":1,"docs":{"563":{"tf":1.0}}}}},"o":{"df":1,"docs":{"300":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"o":{"df":0,"docs":{},"m":{"df":2,"docs":{"344":{"tf":1.0},"352":{"tf":1.0}}}}},"df":0,"docs":{}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"223":{"tf":1.0}}}}}}},"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"570":{"tf":1.0}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"p":{"df":0,"docs":{},"t":{"df":1,"docs":{"627":{"tf":1.0}}}}}},"l":{"a":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":1,"docs":{"632":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"r":{"d":{"df":1,"docs":{"549":{"tf":1.0}}},"df":0,"docs":{}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"436":{"tf":1.0},"437":{"tf":1.0}}}}}}}},"d":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"b":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"722":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"u":{"c":{"df":1,"docs":{"517":{"tf":1.0}}},"df":0,"docs":{}}},"df":1,"docs":{"817":{"tf":1.0}},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":60,"docs":{"1013":{"tf":1.0},"105":{"tf":1.0},"120":{"tf":1.0},"133":{"tf":1.0},"14":{"tf":1.0},"147":{"tf":1.0},"161":{"tf":1.0},"179":{"tf":1.0},"192":{"tf":1.0},"214":{"tf":1.0},"228":{"tf":1.0},"242":{"tf":1.0},"260":{"tf":1.0},"277":{"tf":1.0},"291":{"tf":1.0},"308":{"tf":1.0},"319":{"tf":1.0},"35":{"tf":1.0},"359":{"tf":1.0},"383":{"tf":1.0},"397":{"tf":1.0},"409":{"tf":1.0},"447":{"tf":1.0},"462":{"tf":1.0},"479":{"tf":1.0},"492":{"tf":1.0},"510":{"tf":1.0},"532":{"tf":1.0},"546":{"tf":1.0},"560":{"tf":1.0},"583":{"tf":1.0},"595":{"tf":1.0},"610":{"tf":1.0},"624":{"tf":1.0},"646":{"tf":1.0},"661":{"tf":1.0},"675":{"tf":1.0},"689":{"tf":1.0},"706":{"tf":1.0},"726":{"tf":1.0},"74":{"tf":1.0},"754":{"tf":1.0},"756":{"tf":1.0},"768":{"tf":1.0},"780":{"tf":1.0},"793":{"tf":1.0},"805":{"tf":1.0},"824":{"tf":1.0},"838":{"tf":1.0},"855":{"tf":1.0},"869":{"tf":1.0},"888":{"tf":1.0},"90":{"tf":1.0},"905":{"tf":1.0},"922":{"tf":1.0},"937":{"tf":1.0},"954":{"tf":1.0},"971":{"tf":1.0},"985":{"tf":1.0},"999":{"tf":1.0}},"e":{"df":0,"docs":{},"n":{"d":{"a":{"df":3,"docs":{"122":{"tf":1.0},"136":{"tf":1.0},"847":{"tf":1.0}}},"df":0,"docs":{},"u":{"df":0,"docs":{},"m":{"df":3,"docs":{"857":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}}},"df":0,"docs":{}}}}},"i":{"df":0,"docs":{},"n":{"df":1,"docs":{"45":{"tf":1.0}}}}},"g":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":1,"docs":{"940":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"814":{"tf":1.0}},"r":{"df":4,"docs":{"252":{"tf":1.0},"501":{"tf":1.0},"808":{"tf":1.0},"817":{"tf":1.0}}}}}}},"l":{"a":{"df":0,"docs":{},"t":{"df":49,"docs":{"1001":{"tf":1.0},"1015":{"tf":1.0},"135":{"tf":1.0},"149":{"tf":1.0},"16":{"tf":1.0},"163":{"tf":1.0},"181":{"tf":1.0},"194":{"tf":1.0},"212":{"tf":1.0},"226":{"tf":1.0},"246":{"tf":1.0},"262":{"tf":1.0},"293":{"tf":1.0},"310":{"tf":1.0},"321":{"tf":1.0},"361":{"tf":1.0},"37":{"tf":1.0},"385":{"tf":1.0},"399":{"tf":1.0},"449":{"tf":1.0},"464":{"tf":1.0},"494":{"tf":1.0},"512":{"tf":1.0},"534":{"tf":1.0},"54":{"tf":1.0},"548":{"tf":1.0},"562":{"tf":1.0},"597":{"tf":1.0},"612":{"tf":1.0},"626":{"tf":1.0},"648":{"tf":1.0},"663":{"tf":1.0},"677":{"tf":1.0},"691":{"tf":1.0},"708":{"tf":1.0},"728":{"tf":1.0},"76":{"tf":1.0},"770":{"tf":1.0},"807":{"tf":1.0},"826":{"tf":1.0},"840":{"tf":1.0},"890":{"tf":1.0},"907":{"tf":1.0},"92":{"tf":1.0},"925":{"tf":1.0},"939":{"tf":1.0},"956":{"tf":1.0},"973":{"tf":1.0},"987":{"tf":1.0}}},"y":{"df":3,"docs":{"247":{"tf":1.0},"366":{"tf":1.0},"643":{"tf":1.0}}}},"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"s":{"df":1,"docs":{"848":{"tf":1.0}}}},"df":0,"docs":{},"v":{"df":1,"docs":{"325":{"tf":1.0}}}}},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"v":{"df":6,"docs":{"273":{"tf":1.0},"613":{"tf":1.0},"678":{"tf":1.0},"730":{"tf":1.0},"827":{"tf":1.0},"974":{"tf":1.0}}}}},"n":{"df":0,"docs":{},"t":{"df":2,"docs":{"808":{"tf":1.0},"816":{"tf":1.0}}}},"p":{"df":0,"docs":{},"l":{"a":{"c":{"df":1,"docs":{"386":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{},"i":{"c":{"df":1,"docs":{"79":{"tf":1.0}}},"df":0,"docs":{}}},"u":{"df":0,"docs":{},"r":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":1,"docs":{"7":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"908":{"tf":1.0}}}}},"q":{"df":0,"docs":{},"u":{"df":0,"docs":{},"e":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"c":{"df":0,"docs":{},"o":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"u":{"df":0,"docs":{},"p":{"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":2,"docs":{"61":{"tf":1.0},"62":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}},"df":1,"docs":{"757":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"r":{"df":12,"docs":{"200":{"tf":1.0},"218":{"tf":1.0},"232":{"tf":1.0},"297":{"tf":1.0},"41":{"tf":1.0},"413":{"tf":1.0},"516":{"tf":1.0},"744":{"tf":1.0},"811":{"tf":1.0},"875":{"tf":1.0},"896":{"tf":1.0},"913":{"tf":1.0}},"e":{"_":{"df":0,"docs":{},"w":{"df":0,"docs":{},"e":{"df":0,"docs":{},"i":{"df":0,"docs":{},"g":{"df":0,"docs":{},"h":{"df":0,"docs":{},"t":{"_":{"a":{"df":0,"docs":{},"t":{"_":{"df":0,"docs":{},"m":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"613":{"tf":1.0}}}}}}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}}}}}},"s":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"v":{"df":1,"docs":{"908":{"tf":1.0}}}}},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"c":{"df":1,"docs":{"374":{"tf":1.0}}},"df":0,"docs":{}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"df":1,"docs":{"988":{"tf":1.0}}}}}}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":0,"docs":{},"u":{"df":1,"docs":{"263":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"771":{"tf":1.0}}}}}}},"w":{"a":{"df":0,"docs":{},"r":{"d":{"df":3,"docs":{"1002":{"tf":1.0},"709":{"tf":1.0},"717":{"tf":1.0}}},"df":0,"docs":{}}},"df":0,"docs":{}}},"f":{"c":{"df":63,"docs":{"1":{"tf":1.0},"1002":{"tf":1.0},"106":{"tf":1.0},"122":{"tf":1.0},"136":{"tf":1.0},"150":{"tf":1.0},"164":{"tf":1.0},"17":{"tf":1.0},"182":{"tf":1.0},"195":{"tf":1.0},"215":{"tf":1.0},"229":{"tf":1.0},"247":{"tf":1.0},"263":{"tf":1.0},"268":{"tf":1.0},"279":{"tf":1.0},"294":{"tf":1.0},"311":{"tf":1.0},"322":{"tf":1.0},"366":{"tf":1.0},"38":{"tf":1.0},"386":{"tf":1.0},"400":{"tf":1.0},"410":{"tf":1.0},"430":{"tf":1.0},"451":{"tf":1.0},"465":{"tf":1.0},"481":{"tf":1.0},"495":{"tf":1.0},"513":{"tf":1.0},"535":{"tf":1.0},"549":{"tf":1.0},"56":{"tf":1.0},"563":{"tf":1.0},"584":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"627":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"709":{"tf":1.0},"730":{"tf":1.0},"741":{"tf":1.0},"757":{"tf":1.0},"771":{"tf":1.0},"782":{"tf":1.0},"79":{"tf":1.0},"795":{"tf":1.0},"808":{"tf":1.0},"827":{"tf":1.0},"841":{"tf":1.0},"857":{"tf":1.0},"871":{"tf":1.0},"891":{"tf":1.0},"908":{"tf":1.0},"926":{"tf":1.0},"93":{"tf":1.0},"940":{"tf":1.0},"957":{"tf":1.0},"974":{"tf":1.0},"988":{"tf":1.0}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"l":{"df":0,"docs":{},"o":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":1,"docs":{"209":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"p":{"df":1,"docs":{"38":{"tf":1.0}}}}}},"o":{"df":0,"docs":{},"t":{"df":1,"docs":{"525":{"tf":1.0}}}}},"u":{"df":0,"docs":{},"n":{"df":0,"docs":{},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"m":{"df":6,"docs":{"150":{"tf":1.0},"22":{"tf":1.0},"279":{"tf":1.0},"311":{"tf":1.0},"643":{"tf":1.0},"730":{"tf":1.0}},"e":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"386":{"tf":1.0}}}}}}}}}}}}},"s":{"a":{"df":0,"docs":{},"l":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"465":{"tf":1.0},"470":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"741":{"tf":1.0}}}},"s":{"df":0,"docs":{},"s":{"a":{"df":0,"docs":{},"f":{"df":0,"docs":{},"r":{"a":{"df":3,"docs":{"322":{"tf":1.0},"326":{"tf":1.0},"342":{"tf":1.0}}},"df":0,"docs":{}}}},"df":0,"docs":{}}}},"c":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":1,"docs":{"699":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":2,"docs":{"502":{"tf":1.0},"940":{"tf":1.0}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"p":{"2":{"5":{"6":{"df":0,"docs":{},"r":{"1":{"_":{"df":0,"docs":{},"e":{"c":{"d":{"df":0,"docs":{},"s":{"a":{"_":{"df":0,"docs":{},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":0,"docs":{},"y":{"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"df":1,"docs":{"93":{"tf":1.0}}}}},"df":0,"docs":{}}}}}},"df":0,"docs":{}}}}}}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}}},"df":0,"docs":{}},"df":0,"docs":{}},"df":0,"docs":{}},"u":{"df":0,"docs":{},"r":{"df":62,"docs":{"100":{"tf":1.0},"1008":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"156":{"tf":1.0},"174":{"tf":1.0},"188":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"237":{"tf":1.0},"255":{"tf":1.0},"275":{"tf":1.0},"286":{"tf":1.0},"30":{"tf":1.0},"304":{"tf":1.0},"317":{"tf":1.0},"354":{"tf":1.0},"378":{"tf":1.0},"392":{"tf":1.0},"419":{"tf":1.0},"420":{"tf":1.0},"442":{"tf":1.0},"457":{"tf":1.0},"474":{"tf":1.0},"487":{"tf":1.0},"505":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"541":{"tf":1.0},"555":{"tf":1.0},"578":{"tf":1.0},"590":{"tf":1.0},"605":{"tf":1.0},"619":{"tf":1.0},"639":{"tf":1.0},"656":{"tf":1.0},"670":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.0},"701":{"tf":1.0},"724":{"tf":1.0},"763":{"tf":1.0},"788":{"tf":1.0},"801":{"tf":1.0},"819":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"864":{"tf":1.0},"883":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.0},"917":{"tf":1.0},"935":{"tf":1.0},"946":{"tf":1.0},"948":{"tf":1.0},"963":{"tf":1.0},"965":{"tf":1.0},"980":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}}}}},"df":0,"docs":{},"l":{"df":0,"docs":{},"e":{"c":{"df":0,"docs":{},"t":{"df":1,"docs":{"229":{"tf":1.0}}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"v":{"df":0,"docs":{},"i":{"c":{"df":3,"docs":{"38":{"tf":1.0},"43":{"tf":1.0},"50":{"tf":1.0}}},"df":0,"docs":{}}}},"s":{"df":0,"docs":{},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":0,"docs":{},"i":{"df":0,"docs":{},"n":{"d":{"df":0,"docs":{},"e":{"df":0,"docs":{},"x":{"df":1,"docs":{"627":{"tf":1.0}}}}},"df":0,"docs":{}}},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"y":{"df":1,"docs":{"451":{"tf":1.0}}}}}}}}}},"t":{"df":1,"docs":{"235":{"tf":1.0}}}},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"417":{"tf":1.0}}}}}},"i":{"d":{"df":0,"docs":{},"e":{"df":1,"docs":{"730":{"tf":1.0}}}},"df":0,"docs":{},"g":{"df":0,"docs":{},"n":{"a":{"df":0,"docs":{},"l":{"df":1,"docs":{"345":{"tf":1.0}}},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"171":{"tf":1.0},"93":{"tf":1.0}}}}}},"df":0,"docs":{}}},"z":{"df":0,"docs":{},"e":{"df":2,"docs":{"235":{"tf":1.0},"517":{"tf":1.0}}}}},"l":{"a":{"df":0,"docs":{},"s":{"df":0,"docs":{},"h":{"a":{"b":{"df":0,"docs":{},"l":{"df":1,"docs":{"908":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"573":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"t":{"df":4,"docs":{"338":{"tf":1.0},"348":{"tf":1.0},"349":{"tf":1.0},"350":{"tf":1.0}}}}},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"957":{"tf":1.0}}}}},"df":0,"docs":{}},"n":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"k":{"df":1,"docs":{"364":{"tf":1.0}}}}},"df":0,"docs":{}},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"u":{"df":0,"docs":{},"t":{"df":2,"docs":{"896":{"tf":1.0},"913":{"tf":1.0}}}}}},"p":{"a":{"c":{"df":0,"docs":{},"e":{"df":1,"docs":{"632":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"e":{"c":{"df":1,"docs":{"847":{"tf":1.0}},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"205":{"tf":1.0}}}}},"df":0,"docs":{}}},"t":{"a":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"h":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"d":{"df":62,"docs":{"1005":{"tf":1.0},"109":{"tf":1.0},"125":{"tf":1.0},"139":{"tf":1.0},"153":{"tf":1.0},"167":{"tf":1.0},"185":{"tf":1.0},"20":{"tf":1.0},"201":{"tf":1.0},"219":{"tf":1.0},"233":{"tf":1.0},"250":{"tf":1.0},"266":{"tf":1.0},"271":{"tf":1.0},"282":{"tf":1.0},"298":{"tf":1.0},"314":{"tf":1.0},"327":{"tf":1.0},"369":{"tf":1.0},"389":{"tf":1.0},"4":{"tf":1.0},"403":{"tf":1.0},"414":{"tf":1.0},"42":{"tf":1.0},"433":{"tf":1.0},"454":{"tf":1.0},"468":{"tf":1.0},"484":{"tf":1.0},"498":{"tf":1.0},"518":{"tf":1.0},"538":{"tf":1.0},"552":{"tf":1.0},"566":{"tf":1.0},"587":{"tf":1.0},"59":{"tf":1.0},"601":{"tf":1.0},"616":{"tf":1.0},"630":{"tf":1.0},"652":{"tf":1.0},"667":{"tf":1.0},"681":{"tf":1.0},"695":{"tf":1.0},"712":{"tf":1.0},"733":{"tf":1.0},"745":{"tf":1.0},"760":{"tf":1.0},"774":{"tf":1.0},"785":{"tf":1.0},"798":{"tf":1.0},"812":{"tf":1.0},"82":{"tf":1.0},"830":{"tf":1.0},"844":{"tf":1.0},"877":{"tf":1.0},"897":{"tf":1.0},"914":{"tf":1.0},"929":{"tf":1.0},"943":{"tf":1.0},"96":{"tf":1.0},"960":{"tf":1.0},"977":{"tf":1.0},"991":{"tf":1.0}}},"df":0,"docs":{}}}}}},"l":{"df":0,"docs":{},"e":{"df":1,"docs":{"1002":{"tf":1.0}}}},"t":{"df":0,"docs":{},"e":{"df":3,"docs":{"871":{"tf":1.0},"879":{"tf":1.0},"988":{"tf":1.4142135623730951}},"v":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"s":{"df":1,"docs":{"386":{"tf":1.0}}}}}}},"u":{"df":1,"docs":{"300":{"tf":1.0}}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"a":{"df":0,"docs":{},"g":{"df":4,"docs":{"150":{"tf":1.0},"46":{"tf":1.0},"51":{"tf":1.0},"78":{"tf":1.0}},"e":{"/":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"880":{"tf":1.0}}}}},"_":{"df":0,"docs":{},"p":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"o":{"df":0,"docs":{},"f":{"_":{"df":0,"docs":{},"s":{"df":1,"docs":{"400":{"tf":1.0}}}},"df":0,"docs":{}}}}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"e":{"df":1,"docs":{"247":{"tf":1.0}}}}},"r":{"a":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"g":{"df":0,"docs":{},"i":{"df":2,"docs":{"363":{"tf":1.0},"718":{"tf":1.0}}}}}}},"df":0,"docs":{},"u":{"c":{"df":0,"docs":{},"t":{"df":0,"docs":{},"u":{"df":0,"docs":{},"r":{"df":2,"docs":{"25":{"tf":1.0},"331":{"tf":1.0}}}}}},"df":0,"docs":{}}}},"u":{"b":{"df":0,"docs":{},"m":{"df":0,"docs":{},"i":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":3,"docs":{"336":{"tf":1.0},"346":{"tf":1.0},"365":{"tf":1.0}}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":62,"docs":{"1003":{"tf":1.0},"107":{"tf":1.0},"123":{"tf":1.0},"137":{"tf":1.0},"151":{"tf":1.0},"165":{"tf":1.0},"172":{"tf":1.0},"18":{"tf":1.0},"183":{"tf":1.0},"196":{"tf":1.0},"2":{"tf":1.0},"216":{"tf":1.0},"230":{"tf":1.0},"248":{"tf":1.0},"264":{"tf":1.0},"269":{"tf":1.0},"280":{"tf":1.0},"295":{"tf":1.0},"312":{"tf":1.0},"367":{"tf":1.0},"387":{"tf":1.0},"401":{"tf":1.0},"411":{"tf":1.0},"431":{"tf":1.0},"452":{"tf":1.0},"466":{"tf":1.0},"482":{"tf":1.0},"496":{"tf":1.0},"514":{"tf":1.0},"536":{"tf":1.0},"550":{"tf":1.0},"564":{"tf":1.0},"57":{"tf":1.0},"585":{"tf":1.0},"599":{"tf":1.0},"614":{"tf":1.0},"628":{"tf":1.0},"650":{"tf":1.0},"665":{"tf":1.0},"679":{"tf":1.0},"693":{"tf":1.0},"710":{"tf":1.0},"731":{"tf":1.0},"742":{"tf":1.0},"758":{"tf":1.0},"772":{"tf":1.0},"783":{"tf":1.0},"796":{"tf":1.0},"80":{"tf":1.0},"809":{"tf":1.0},"828":{"tf":1.0},"842":{"tf":1.0},"858":{"tf":1.0},"872":{"tf":1.0},"892":{"tf":1.0},"909":{"tf":1.0},"927":{"tf":1.0},"94":{"tf":1.0},"941":{"tf":1.0},"958":{"tf":1.0},"975":{"tf":1.0},"989":{"tf":1.0}}}}},"df":0,"docs":{}}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"326":{"tf":1.0}}}}}}}},"y":{"df":0,"docs":{},"n":{"c":{"df":1,"docs":{"988":{"tf":1.0}}},"df":0,"docs":{},"t":{"df":0,"docs":{},"h":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"729":{"tf":1.0}}}}}}},"s":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"m":{"a":{"df":0,"docs":{},"t":{"df":2,"docs":{"435":{"tf":1.0},"437":{"tf":1.0}}}},"df":5,"docs":{"198":{"tf":1.0},"229":{"tf":1.0},"268":{"tf":1.0},"386":{"tf":1.0},"777":{"tf":1.0}}}}}}}},"t":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"723":{"tf":1.0}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"m":{"df":1,"docs":{"417":{"tf":1.0}}}},"s":{"df":0,"docs":{},"t":{"df":60,"docs":{"1008":{"tf":1.0},"115":{"tf":1.0},"128":{"tf":1.0},"142":{"tf":1.0},"156":{"tf":1.0},"174":{"tf":1.0},"188":{"tf":1.0},"211":{"tf":1.0},"225":{"tf":1.0},"237":{"tf":1.0},"255":{"tf":1.0},"275":{"tf":1.0},"286":{"tf":1.0},"30":{"tf":1.0},"304":{"tf":1.0},"317":{"tf":1.0},"354":{"tf":1.0},"378":{"tf":1.0},"392":{"tf":1.0},"419":{"tf":1.0},"442":{"tf":1.0},"457":{"tf":1.0},"474":{"tf":1.0},"487":{"tf":1.0},"505":{"tf":1.0},"528":{"tf":1.0},"53":{"tf":1.0},"541":{"tf":1.0},"555":{"tf":1.0},"578":{"tf":1.0},"590":{"tf":1.0},"605":{"tf":1.0},"619":{"tf":1.0},"639":{"tf":1.0},"656":{"tf":1.0},"670":{"tf":1.0},"684":{"tf":1.0},"69":{"tf":1.0},"701":{"tf":1.0},"724":{"tf":1.0},"763":{"tf":1.0},"788":{"tf":1.0},"801":{"tf":1.0},"819":{"tf":1.0},"833":{"tf":1.0},"85":{"tf":1.0},"850":{"tf":1.0},"864":{"tf":1.0},"883":{"tf":1.0},"9":{"tf":1.0},"900":{"tf":1.0},"917":{"tf":1.0},"935":{"tf":1.0},"946":{"tf":1.0},"947":{"tf":1.0},"963":{"tf":1.0},"964":{"tf":1.0},"980":{"tf":1.0},"99":{"tf":1.0},"994":{"tf":1.0}},"n":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":1,"docs":{"678":{"tf":1.0}}}}}}}},"i":{"c":{"df":0,"docs":{},"k":{"df":0,"docs":{},"e":{"df":0,"docs":{},"t":{"df":8,"docs":{"336":{"tf":1.0},"337":{"tf":1.0},"338":{"tf":1.0},"339":{"tf":1.0},"346":{"tf":1.0},"347":{"tf":1.0},"348":{"tf":1.0},"365":{"tf":1.0}}}}}},"df":0,"docs":{},"m":{"df":0,"docs":{},"e":{"df":1,"docs":{"549":{"tf":1.0}}}},"p":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"182":{"tf":1.0}}}}}},"t":{"df":1,"docs":{"723":{"tf":1.0}}}},"o":{"d":{"df":0,"docs":{},"o":{"df":1,"docs":{"1002":{"tf":1.0}}}},"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":2,"docs":{"645":{"tf":1.0},"848":{"tf":1.0}}}}},"r":{"a":{"c":{"df":0,"docs":{},"k":{"df":8,"docs":{"136":{"tf":1.0},"182":{"tf":1.0},"841":{"tf":1.0},"846":{"tf":1.0},"847":{"tf":1.0},"857":{"tf":1.0},"861":{"tf":1.0},"862":{"tf":1.0}}}},"df":0,"docs":{},"n":{"df":0,"docs":{},"s":{"a":{"c":{"df":0,"docs":{},"t":{"df":5,"docs":{"171":{"tf":1.0},"481":{"tf":1.0},"535":{"tf":1.0},"584":{"tf":1.0},"613":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"f":{"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":3,"docs":{"48":{"tf":1.0},"603":{"tf":1.0},"692":{"tf":1.0}}}}},"i":{"df":0,"docs":{},"t":{"df":1,"docs":{"879":{"tf":1.0}}}},"p":{"df":0,"docs":{},"o":{"df":0,"docs":{},"r":{"df":0,"docs":{},"t":{"df":1,"docs":{"633":{"tf":1.0}}}}}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"e":{"df":1,"docs":{"525":{"tf":1.0}}}},"u":{"df":0,"docs":{},"s":{"df":0,"docs":{},"t":{"df":1,"docs":{"697":{"tf":1.0}}}}}},"y":{"df":0,"docs":{},"p":{"df":0,"docs":{},"e":{"df":9,"docs":{"208":{"tf":1.0},"221":{"tf":1.0},"222":{"tf":1.0},"332":{"tf":1.0},"334":{"tf":1.0},"522":{"tf":1.0},"523":{"tf":1.0},"603":{"tf":1.0},"61":{"tf":1.0}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"f":{"df":1,"docs":{"524":{"tf":1.0}}}}}}}}},"u":{"df":0,"docs":{},"m":{"df":0,"docs":{},"p":{"df":3,"docs":{"221":{"tf":1.0},"61":{"tf":1.0},"633":{"tf":1.0}}}},"n":{"b":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"d":{"df":1,"docs":{"563":{"tf":1.0}}},"df":0,"docs":{}}},"r":{"df":0,"docs":{},"i":{"c":{"df":0,"docs":{},"k":{"df":2,"docs":{"106":{"tf":1.0},"112":{"tf":1.0}}}},"df":0,"docs":{}}}},"df":0,"docs":{},"k":{"df":0,"docs":{},"n":{"df":0,"docs":{},"o":{"df":0,"docs":{},"w":{"df":0,"docs":{},"n":{"df":3,"docs":{"213":{"tf":1.0},"227":{"tf":1.0},"55":{"tf":1.0}}}}}}},"r":{"df":0,"docs":{},"e":{"df":0,"docs":{},"l":{"df":1,"docs":{"523":{"tf":1.0}}},"s":{"df":0,"docs":{},"o":{"df":0,"docs":{},"l":{"df":0,"docs":{},"v":{"df":55,"docs":{"1000":{"tf":1.0},"1014":{"tf":1.0},"121":{"tf":1.0},"134":{"tf":1.0},"148":{"tf":1.0},"15":{"tf":1.0},"162":{"tf":1.0},"180":{"tf":1.0},"193":{"tf":1.0},"245":{"tf":1.0},"261":{"tf":1.0},"278":{"tf":1.0},"292":{"tf":1.0},"309":{"tf":1.0},"320":{"tf":1.0},"36":{"tf":1.0},"360":{"tf":1.0},"384":{"tf":1.0},"398":{"tf":1.0},"425":{"tf":1.0},"448":{"tf":1.0},"463":{"tf":1.0},"480":{"tf":1.0},"493":{"tf":1.0},"511":{"tf":1.0},"533":{"tf":1.0},"547":{"tf":1.0},"561":{"tf":1.0},"596":{"tf":1.0},"611":{"tf":1.0},"625":{"tf":1.0},"647":{"tf":1.0},"662":{"tf":1.0},"676":{"tf":1.0},"690":{"tf":1.0},"707":{"tf":1.0},"727":{"tf":1.0},"739":{"tf":1.0},"75":{"tf":1.0},"769":{"tf":1.0},"781":{"tf":1.0},"794":{"tf":1.0},"806":{"tf":1.0},"825":{"tf":1.0},"839":{"tf":1.0},"856":{"tf":1.0},"870":{"tf":1.0},"889":{"tf":1.0},"906":{"tf":1.0},"91":{"tf":1.0},"924":{"tf":1.0},"938":{"tf":1.0},"955":{"tf":1.0},"972":{"tf":1.0},"986":{"tf":1.0}}}}}}}},"u":{"df":0,"docs":{},"s":{"df":1,"docs":{"632":{"tf":1.0}}}}},"p":{"d":{"a":{"df":0,"docs":{},"t":{"df":1,"docs":{"472":{"tf":1.0}}}},"df":0,"docs":{}},"df":0,"docs":{},"g":{"df":0,"docs":{},"r":{"a":{"d":{"df":2,"docs":{"440":{"tf":1.0},"64":{"tf":1.0}}},"df":0,"docs":{}},"df":0,"docs":{}}}},"s":{"a":{"df":0,"docs":{},"g":{"df":2,"docs":{"223":{"tf":1.0},"603":{"tf":1.0}}}},"d":{"(":{"df":0,"docs":{},"x":{"df":1,"docs":{"429":{"tf":1.0}}}},"df":0,"docs":{}},"df":1,"docs":{"876":{"tf":1.0}},"e":{"df":0,"docs":{},"r":{"df":1,"docs":{"29":{"tf":1.0}}}}},"t":{"df":0,"docs":{},"i":{"df":0,"docs":{},"l":{"df":1,"docs":{"400":{"tf":1.0}}}}},"x":{"/":{"df":0,"docs":{},"u":{"df":0,"docs":{},"i":{"df":1,"docs":{"574":{"tf":1.0}}}}},"df":0,"docs":{}}},"v":{"a":{"df":0,"docs":{},"l":{"df":0,"docs":{},"i":{"d":{"df":10,"docs":{"337":{"tf":1.0},"347":{"tf":1.0},"38":{"tf":1.0},"430":{"tf":1.0},"46":{"tf":1.0},"63":{"tf":1.0},"636":{"tf":1.0},"644":{"tf":1.0},"65":{"tf":1.0},"709":{"tf":1.0}}},"df":0,"docs":{}},"u":{"df":2,"docs":{"429":{"tf":1.0},"891":{"tf":1.0}}}}},"df":0,"docs":{},"e":{"df":0,"docs":{},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"f":{"df":1,"docs":{"350":{"tf":1.0}},"i":{"df":1,"docs":{"93":{"tf":1.0}}}}},"s":{"df":0,"docs":{},"i":{"df":0,"docs":{},"o":{"df":0,"docs":{},"n":{"df":5,"docs":{"164":{"tf":1.0},"170":{"tf":1.0},"172":{"tf":1.0},"386":{"tf":1.0},"584":{"tf":1.0}}}}}}}},"o":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":2,"docs":{"575":{"tf":1.0},"795":{"tf":1.0}}}}},"r":{"df":0,"docs":{},"f":{"df":2,"docs":{"340":{"tf":1.0},"341":{"tf":1.0}}}}},"w":{"df":0,"docs":{},"e":{"a":{"df":0,"docs":{},"k":{"df":1,"docs":{"427":{"tf":1.0}}}},"df":0,"docs":{}},"r":{"df":0,"docs":{},"i":{"df":0,"docs":{},"t":{"df":0,"docs":{},"t":{"df":0,"docs":{},"e":{"df":0,"docs":{},"n":{"df":1,"docs":{"243":{"tf":1.0}}}}}}}}},"x":{"c":{"df":0,"docs":{},"m":{"df":10,"docs":{"1":{"tf":1.0},"598":{"tf":1.0},"613":{"tf":1.0},"649":{"tf":1.0},"664":{"tf":1.0},"678":{"tf":1.0},"692":{"tf":1.0},"698":{"tf":1.0},"782":{"tf":1.0},"974":{"tf":1.0}}},"q":{"(":{"c":{"df":0,"docs":{},"r":{"df":0,"docs":{},"o":{"df":0,"docs":{},"s":{"df":0,"docs":{},"s":{"df":1,"docs":{"17":{"tf":1.0}}}}}}},"df":0,"docs":{}},"df":5,"docs":{"22":{"tf":1.0},"23":{"tf":1.0},"24":{"tf":1.0},"25":{"tf":1.0},"26":{"tf":1.0}}}},"df":2,"docs":{"841":{"tf":1.0},"847":{"tf":1.0}}},"z":{"df":0,"docs":{},"k":{"df":1,"docs":{"364":{"tf":1.0}}}}}}},"lang":"English","pipeline":["trimmer","stopWordFilter","stemmer"],"ref":"id","version":"0.9.5"},"results_options":{"limit_results":30,"teaser_word_count":30},"search_options":{"bool":"OR","expand":true,"fields":{"body":{"boost":1},"breadcrumbs":{"boost":1},"title":{"boost":2}}}});
\ No newline at end of file
+Object.assign(window.search, {"doc_urls":["introduction.html#introduction","new/0125-xcm-asset-metadata.html#rfc-0125-xcm-asset-metadata","new/0125-xcm-asset-metadata.html#summary","new/0125-xcm-asset-metadata.html#motivation","new/0125-xcm-asset-metadata.html#stakeholders","new/0125-xcm-asset-metadata.html#explanation","new/0125-xcm-asset-metadata.html#new-instructions","new/0125-xcm-asset-metadata.html#repurposing-assetinstanceundefined","new/0125-xcm-asset-metadata.html#drawbacks","new/0125-xcm-asset-metadata.html#testing-security-and-privacy","new/0125-xcm-asset-metadata.html#performance-ergonomics-and-compatibility","new/0125-xcm-asset-metadata.html#performance","new/0125-xcm-asset-metadata.html#ergonomics","new/0125-xcm-asset-metadata.html#compatibility","new/0125-xcm-asset-metadata.html#prior-art-and-references","new/0125-xcm-asset-metadata.html#unresolved-questions","new/0125-xcm-asset-metadata.html#future-directions-and-related-material","new/0126-introduce-xcq.html#rfc-0126-introduce-xcqcross-consensus-query","new/0126-introduce-xcq.html#summary","new/0126-introduce-xcq.html#motivation","new/0126-introduce-xcq.html#stakeholders","new/0126-introduce-xcq.html#explanation","new/0126-introduce-xcq.html#xcq-runtime-api","new/0126-introduce-xcq.html#xcq-executor","new/0126-introduce-xcq.html#xcq-extension","new/0126-introduce-xcq.html#xcq-program-structure","new/0126-introduce-xcq.html#xcq-program-execution-flow","new/0126-introduce-xcq.html#drawbacks","new/0126-introduce-xcq.html#performance-issues","new/0126-introduce-xcq.html#user-experience-issues","new/0126-introduce-xcq.html#testing-security-and-privacy","new/0126-introduce-xcq.html#performance-ergonomics-and-compatibility","new/0126-introduce-xcq.html#performance","new/0126-introduce-xcq.html#ergonomics","new/0126-introduce-xcq.html#compatibility","new/0126-introduce-xcq.html#prior-art-and-references","new/0126-introduce-xcq.html#unresolved-questions","new/0126-introduce-xcq.html#future-directions-and-related-material","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#rfc-0127-jam-service-for-validating-ethereum-optimistic-rollups","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#background","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#motivation","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#requirements","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#stakeholders","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#jam-service-design","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#overview","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#refine","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#key-validation-process-storage-proofs","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#accumulate","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#transfer","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#beefy","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#service-poc-implementation","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#gas--storage-considerations","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#compatibility","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#testing-security-and-privacy","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#future-directions-and-related-material","new/0127-JAM-Service-for-Validating-Ethereum-Optimistic-Rollups.html#drawbacks-alternatives-and-unknowns","proposed/0102-offchain-parachain-runtime-upgrades.html#rfc-0000-feature-name-here","proposed/0102-offchain-parachain-runtime-upgrades.html#summary","proposed/0102-offchain-parachain-runtime-upgrades.html#motivation","proposed/0102-offchain-parachain-runtime-upgrades.html#stakeholders","proposed/0102-offchain-parachain-runtime-upgrades.html#explanation","proposed/0102-offchain-parachain-runtime-upgrades.html#introduce-a-new-ump-message-type-requestcodeupgrade","proposed/0102-offchain-parachain-runtime-upgrades.html#handle-requestcodeupgrade-on-backers","proposed/0102-offchain-parachain-runtime-upgrades.html#get-the-new-code-to-all-validators","proposed/0102-offchain-parachain-runtime-upgrades.html#on-chain-code-upgrade-process","proposed/0102-offchain-parachain-runtime-upgrades.html#handling-new-validators","proposed/0102-offchain-parachain-runtime-upgrades.html#how-do-other-parties-get-hold-of-the-pvf","proposed/0102-offchain-parachain-runtime-upgrades.html#pruning","proposed/0102-offchain-parachain-runtime-upgrades.html#drawbacks","proposed/0102-offchain-parachain-runtime-upgrades.html#testing-security-and-privacy","proposed/0102-offchain-parachain-runtime-upgrades.html#performance-ergonomics-and-compatibility","proposed/0102-offchain-parachain-runtime-upgrades.html#performance","proposed/0102-offchain-parachain-runtime-upgrades.html#ergonomics","proposed/0102-offchain-parachain-runtime-upgrades.html#compatibility","proposed/0102-offchain-parachain-runtime-upgrades.html#prior-art-and-references","proposed/0102-offchain-parachain-runtime-upgrades.html#unresolved-questions","proposed/0102-offchain-parachain-runtime-upgrades.html#future-directions-and-related-material","proposed/0102-offchain-parachain-runtime-upgrades.html#further-hardening","proposed/0102-offchain-parachain-runtime-upgrades.html#generalize-this-off-chain-storage-mechanism","proposed/0111-pure-proxy-replication.html#rfc-0111-pure-proxy-replication","proposed/0111-pure-proxy-replication.html#summary","proposed/0111-pure-proxy-replication.html#motivation","proposed/0111-pure-proxy-replication.html#stakeholders","proposed/0111-pure-proxy-replication.html#explanation","proposed/0111-pure-proxy-replication.html#drawbacks","proposed/0111-pure-proxy-replication.html#testing-security-and-privacy","proposed/0111-pure-proxy-replication.html#performance-ergonomics-and-compatibility","proposed/0111-pure-proxy-replication.html#performance","proposed/0111-pure-proxy-replication.html#ergonomics","proposed/0111-pure-proxy-replication.html#compatibility","proposed/0111-pure-proxy-replication.html#prior-art-and-references","proposed/0111-pure-proxy-replication.html#unresolved-questions","proposed/0111-pure-proxy-replication.html#future-directions-and-related-material","proposed/0114-secp256r1-hostfunction.html#rfc-0114-introduce-secp256r1_ecdsa_verify_prehashed-host-function-to-verify-nist-p256-elliptic-curve-signatures","proposed/0114-secp256r1-hostfunction.html#summary","proposed/0114-secp256r1-hostfunction.html#motivation","proposed/0114-secp256r1-hostfunction.html#stakeholders","proposed/0114-secp256r1-hostfunction.html#explanation","proposed/0114-secp256r1-hostfunction.html#drawbacks","proposed/0114-secp256r1-hostfunction.html#testing-security-and-privacy","proposed/0114-secp256r1-hostfunction.html#security","proposed/0114-secp256r1-hostfunction.html#performance-ergonomics-and-compatibility","proposed/0114-secp256r1-hostfunction.html#performance","proposed/0114-secp256r1-hostfunction.html#ergonomics","proposed/0114-secp256r1-hostfunction.html#compatibility","proposed/0114-secp256r1-hostfunction.html#prior-art-and-references","proposed/0117-unbrick-collective.html#rfc-0117-the-unbrick-collective","proposed/0117-unbrick-collective.html#summary","proposed/0117-unbrick-collective.html#motivation","proposed/0117-unbrick-collective.html#stakeholders","proposed/0117-unbrick-collective.html#explanation","proposed/0117-unbrick-collective.html#the-collective","proposed/0117-unbrick-collective.html#the-unbrick-process","proposed/0117-unbrick-collective.html#belonging-to-the-collective","proposed/0117-unbrick-collective.html#drawbacks","proposed/0117-unbrick-collective.html#testing-security-and-privacy","proposed/0117-unbrick-collective.html#performance-ergonomics-and-compatibility","proposed/0117-unbrick-collective.html#performance","proposed/0117-unbrick-collective.html#ergonomics","proposed/0117-unbrick-collective.html#compatibility","proposed/0117-unbrick-collective.html#prior-art-and-references","proposed/0117-unbrick-collective.html#unresolved-questions","proposed/0121-iterable-referenda-tracks.html#rfc-0121-iterable-referenda-tracks","proposed/0121-iterable-referenda-tracks.html#summary","proposed/0121-iterable-referenda-tracks.html#motivation","proposed/0121-iterable-referenda-tracks.html#stakeholders","proposed/0121-iterable-referenda-tracks.html#explanation","proposed/0121-iterable-referenda-tracks.html#drawbacks","proposed/0121-iterable-referenda-tracks.html#testing-security-and-privacy","proposed/0121-iterable-referenda-tracks.html#performance-ergonomics-and-compatibility","proposed/0121-iterable-referenda-tracks.html#performance","proposed/0121-iterable-referenda-tracks.html#ergonomics","proposed/0121-iterable-referenda-tracks.html#compatibility","proposed/0121-iterable-referenda-tracks.html#prior-art-and-references","proposed/0121-iterable-referenda-tracks.html#unresolved-questions","proposed/0121-iterable-referenda-tracks.html#future-directions-and-related-material","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#rfc-0123-introduce-pending_code-as-intermediate-storage-key-for-the-runtime-code","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#summary","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#motivation","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#stakeholders","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#explanation","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#drawbacks","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#testing-security-and-privacy","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#performance-ergonomics-and-compatibility","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#performance","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#ergonomics","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#compatibility","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#prior-art-and-references","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#unresolved-questions","proposed/0123-pending-code-as-storage-location-for-runtime-upgrades.html#future-directions-and-related-material","proposed/0124-extrinsic-version-5.html#rfc-0124-extrinsic-version-5","proposed/0124-extrinsic-version-5.html#summary","proposed/0124-extrinsic-version-5.html#motivation","proposed/0124-extrinsic-version-5.html#stakeholders","proposed/0124-extrinsic-version-5.html#explanation","proposed/0124-extrinsic-version-5.html#changes-to-extrinsic-authorization","proposed/0124-extrinsic-version-5.html#encoding-format-for-version-5","proposed/0124-extrinsic-version-5.html#signatures-on-polkadot-in-general-transactions","proposed/0124-extrinsic-version-5.html#summary-of-changes-in-version-5","proposed/0124-extrinsic-version-5.html#drawbacks","proposed/0124-extrinsic-version-5.html#testing-security-and-privacy","proposed/0124-extrinsic-version-5.html#performance-ergonomics-and-compatibility","proposed/0124-extrinsic-version-5.html#performance","proposed/0124-extrinsic-version-5.html#ergonomics","proposed/0124-extrinsic-version-5.html#compatibility","proposed/0124-extrinsic-version-5.html#prior-art-and-references","proposed/0124-extrinsic-version-5.html#unresolved-questions","proposed/0124-extrinsic-version-5.html#future-directions-and-related-material","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#rfc-114-adjust-tipper-track-confirmation-periods","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#summary","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#motivation","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#stakeholders","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#explanation","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#drawbacks","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#testing-security-and-privacy","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#performance-ergonomics-and-compatibility","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#performance","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#ergonomics--compatibility","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#prior-art-and-references","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#unresolved-questions","proposed/RFC-114 Adjust Tipper Track Confirmation Periods.html#future-directions-and-related-material","approved/0001-agile-coretime.html#rfc-1-agile-coretime","approved/0001-agile-coretime.html#summary","approved/0001-agile-coretime.html#motivation","approved/0001-agile-coretime.html#present-system","approved/0001-agile-coretime.html#problems","approved/0001-agile-coretime.html#requirements","approved/0001-agile-coretime.html#stakeholders","approved/0001-agile-coretime.html#explanation","approved/0001-agile-coretime.html#overview","approved/0001-agile-coretime.html#detail","approved/0001-agile-coretime.html#specific-functions-of-the-coretime-chain","approved/0001-agile-coretime.html#notes-on-the-instantaneous-coretime-market","approved/0001-agile-coretime.html#notes-on-economics","approved/0001-agile-coretime.html#notes-on-types","approved/0001-agile-coretime.html#rollout","approved/0001-agile-coretime.html#performance-ergonomics-and-compatibility","approved/0001-agile-coretime.html#testing-security-and-privacy","approved/0001-agile-coretime.html#future-directions-and-related-material","approved/0001-agile-coretime.html#drawbacks-alternatives-and-unknowns","approved/0001-agile-coretime.html#prior-art-and-references","approved/0005-coretime-interface.html#rfc-5-coretime-interface","approved/0005-coretime-interface.html#summary","approved/0005-coretime-interface.html#motivation","approved/0005-coretime-interface.html#requirements","approved/0005-coretime-interface.html#stakeholders","approved/0005-coretime-interface.html#explanation","approved/0005-coretime-interface.html#ump-message-types","approved/0005-coretime-interface.html#dmp-message-types","approved/0005-coretime-interface.html#realistic-limits-of-the-usage","approved/0005-coretime-interface.html#performance-ergonomics-and-compatibility","approved/0005-coretime-interface.html#testing-security-and-privacy","approved/0005-coretime-interface.html#future-directions-and-related-material","approved/0005-coretime-interface.html#drawbacks-alternatives-and-unknowns","approved/0005-coretime-interface.html#prior-art-and-references","approved/0007-system-collator-selection.html#rfc-0007-system-collator-selection","approved/0007-system-collator-selection.html#summary","approved/0007-system-collator-selection.html#motivation","approved/0007-system-collator-selection.html#requirements","approved/0007-system-collator-selection.html#stakeholders","approved/0007-system-collator-selection.html#explanation","approved/0007-system-collator-selection.html#set-size","approved/0007-system-collator-selection.html#drawbacks","approved/0007-system-collator-selection.html#testing-security-and-privacy","approved/0007-system-collator-selection.html#performance-ergonomics-and-compatibility","approved/0007-system-collator-selection.html#performance","approved/0007-system-collator-selection.html#ergonomics","approved/0007-system-collator-selection.html#compatibility","approved/0007-system-collator-selection.html#prior-art-and-references","approved/0007-system-collator-selection.html#written-discussions","approved/0007-system-collator-selection.html#prior-feedback-and-input-from","approved/0007-system-collator-selection.html#unresolved-questions","approved/0007-system-collator-selection.html#future-directions-and-related-material","approved/0008-parachain-bootnodes-dht.html#rfc-0008-store-parachain-bootnodes-in-relay-chain-dht","approved/0008-parachain-bootnodes-dht.html#summary","approved/0008-parachain-bootnodes-dht.html#motivation","approved/0008-parachain-bootnodes-dht.html#stakeholders","approved/0008-parachain-bootnodes-dht.html#explanation","approved/0008-parachain-bootnodes-dht.html#dht-provider-registration","approved/0008-parachain-bootnodes-dht.html#new-networking-protocol","approved/0008-parachain-bootnodes-dht.html#drawbacks","approved/0008-parachain-bootnodes-dht.html#testing-security-and-privacy","approved/0008-parachain-bootnodes-dht.html#performance-ergonomics-and-compatibility","approved/0008-parachain-bootnodes-dht.html#performance","approved/0008-parachain-bootnodes-dht.html#ergonomics","approved/0008-parachain-bootnodes-dht.html#compatibility","approved/0008-parachain-bootnodes-dht.html#prior-art-and-references","approved/0008-parachain-bootnodes-dht.html#unresolved-questions","approved/0008-parachain-bootnodes-dht.html#future-directions-and-related-material","approved/0010-burn-coretime-revenue.html#rfc-0010-burn-coretime-revenue","approved/0010-burn-coretime-revenue.html#summary","approved/0010-burn-coretime-revenue.html#motivation","approved/0010-burn-coretime-revenue.html#stakeholders","approved/0010-burn-coretime-revenue.html#explanation","approved/0012-process-for-adding-new-collectives.html#rfc-0012-process-for-adding-new-system-collectives","approved/0012-process-for-adding-new-collectives.html#summary","approved/0012-process-for-adding-new-collectives.html#motivation","approved/0012-process-for-adding-new-collectives.html#stakeholders","approved/0012-process-for-adding-new-collectives.html#explanation","approved/0012-process-for-adding-new-collectives.html#removing-collectives","approved/0012-process-for-adding-new-collectives.html#drawbacks","approved/0012-process-for-adding-new-collectives.html#testing-security-and-privacy","approved/0012-process-for-adding-new-collectives.html#performance-ergonomics-and-compatibility","approved/0012-process-for-adding-new-collectives.html#prior-art-and-references","approved/0012-process-for-adding-new-collectives.html#unresolved-questions","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#rfc-0013-prepare-core-runtime-api-for-mbms","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#summary","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#motivation","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#stakeholders","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#explanation","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#coreinitialize_block","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#drawbacks","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#testing-security-and-privacy","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#performance-ergonomics-and-compatibility","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#performance","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#ergonomics","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#compatibility","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#prior-art-and-references","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#unresolved-questions","approved/0013-prepare-blockbuilder-and-core-runtime-apis-for-mbms.html#future-directions-and-related-material","approved/0014-improve-locking-mechanism-for-parachains.html#rfc-0014-improve-locking-mechanism-for-parachains","approved/0014-improve-locking-mechanism-for-parachains.html#summary","approved/0014-improve-locking-mechanism-for-parachains.html#motivation","approved/0014-improve-locking-mechanism-for-parachains.html#requirements","approved/0014-improve-locking-mechanism-for-parachains.html#stakeholders","approved/0014-improve-locking-mechanism-for-parachains.html#explanation","approved/0014-improve-locking-mechanism-for-parachains.html#status-quo","approved/0014-improve-locking-mechanism-for-parachains.html#proposed-changes","approved/0014-improve-locking-mechanism-for-parachains.html#migration","approved/0014-improve-locking-mechanism-for-parachains.html#drawbacks","approved/0014-improve-locking-mechanism-for-parachains.html#testing-security-and-privacy","approved/0014-improve-locking-mechanism-for-parachains.html#performance","approved/0014-improve-locking-mechanism-for-parachains.html#ergonomics","approved/0014-improve-locking-mechanism-for-parachains.html#compatibility","approved/0014-improve-locking-mechanism-for-parachains.html#prior-art-and-references","approved/0014-improve-locking-mechanism-for-parachains.html#unresolved-questions","approved/0014-improve-locking-mechanism-for-parachains.html#future-directions-and-related-material","approved/0022-adopt-encointer-runtime.html#rfc-0022-adopt-encointer-runtime","approved/0022-adopt-encointer-runtime.html#summary","approved/0022-adopt-encointer-runtime.html#motivation","approved/0022-adopt-encointer-runtime.html#stakeholders","approved/0022-adopt-encointer-runtime.html#explanation","approved/0022-adopt-encointer-runtime.html#drawbacks","approved/0022-adopt-encointer-runtime.html#testing-security-and-privacy","approved/0022-adopt-encointer-runtime.html#performance-ergonomics-and-compatibility","approved/0022-adopt-encointer-runtime.html#prior-art-and-references","approved/0022-adopt-encointer-runtime.html#unresolved-questions","approved/0022-adopt-encointer-runtime.html#future-directions-and-related-material","approved/0026-sassafras-consensus.html#rfc-0026-sassafras-consensus-protocol","approved/0026-sassafras-consensus.html#abstract","approved/0026-sassafras-consensus.html#1-motivation","approved/0026-sassafras-consensus.html#11-relevance-to-implementors","approved/0026-sassafras-consensus.html#12-supporting-sassafras-for-polkadot","approved/0026-sassafras-consensus.html#2-stakeholders","approved/0026-sassafras-consensus.html#21-blockchain-core-developers","approved/0026-sassafras-consensus.html#22-polkadot-ecosystem-contributors","approved/0026-sassafras-consensus.html#3-notation","approved/0026-sassafras-consensus.html#31-data-structures-definitions","approved/0026-sassafras-consensus.html#32-types-alias","approved/0026-sassafras-consensus.html#32-pseudo-code","approved/0026-sassafras-consensus.html#33-incremental-introduction-of-types-and-functions","approved/0026-sassafras-consensus.html#4-protocol-introduction","approved/0026-sassafras-consensus.html#41-submission-of-candidate-tickets","approved/0026-sassafras-consensus.html#42-validation-of-candidate-tickets","approved/0026-sassafras-consensus.html#43-tickets-slots-binding","approved/0026-sassafras-consensus.html#44-claim-of-ticket-ownership","approved/0026-sassafras-consensus.html#5-bandersnatch-vrfs-cryptographic-primitives","approved/0026-sassafras-consensus.html#51-bare-vrf-interface","approved/0026-sassafras-consensus.html#6-sassafras-protocol","approved/0026-sassafras-consensus.html#62-header-digest-log","approved/0026-sassafras-consensus.html#63-on-chain-randomness","approved/0026-sassafras-consensus.html#64-epoch-change-signal","approved/0026-sassafras-consensus.html#65-tickets-creation-and-submission","approved/0026-sassafras-consensus.html#66-on-chain-tickets-validation","approved/0026-sassafras-consensus.html#67-ticket-slot-binding","approved/0026-sassafras-consensus.html#68-slot-claim","approved/0026-sassafras-consensus.html#69-slot-claim-verification","approved/0026-sassafras-consensus.html#691-primary-method","approved/0026-sassafras-consensus.html#610-randomness-accumulator","approved/0026-sassafras-consensus.html#7-drawbacks","approved/0026-sassafras-consensus.html#8-testing-security-and-privacy","approved/0026-sassafras-consensus.html#9-performance-ergonomics-and-compatibility","approved/0026-sassafras-consensus.html#91-performance","approved/0026-sassafras-consensus.html#92-ergonomics","approved/0026-sassafras-consensus.html#93-compatibility","approved/0026-sassafras-consensus.html#10-prior-art-and-references","approved/0026-sassafras-consensus.html#11-unresolved-questions","approved/0026-sassafras-consensus.html#12-future-directions-and-related-material","approved/0026-sassafras-consensus.html#121-interactions-with-on-chain-code","approved/0026-sassafras-consensus.html#122-deployment-strategies","approved/0026-sassafras-consensus.html#123-zk-snark-parameters","approved/0026-sassafras-consensus.html#124-anonymous-submission-of-tickets","approved/0032-minimal-relay.html#rfc-0032-minimal-relay","approved/0032-minimal-relay.html#summary","approved/0032-minimal-relay.html#motivation","approved/0032-minimal-relay.html#stakeholders","approved/0032-minimal-relay.html#explanation","approved/0032-minimal-relay.html#migrations","approved/0032-minimal-relay.html#interfaces","approved/0032-minimal-relay.html#functional-architecture","approved/0032-minimal-relay.html#resource-allocation","approved/0032-minimal-relay.html#deployment","approved/0032-minimal-relay.html#kusama","approved/0032-minimal-relay.html#drawbacks","approved/0032-minimal-relay.html#testing-security-and-privacy","approved/0032-minimal-relay.html#performance-ergonomics-and-compatibility","approved/0032-minimal-relay.html#performance","approved/0032-minimal-relay.html#ergonomics","approved/0032-minimal-relay.html#compatibility","approved/0032-minimal-relay.html#prior-art-and-references","approved/0032-minimal-relay.html#unresolved-questions","approved/0032-minimal-relay.html#future-directions-and-related-material","approved/0042-extrinsics-state-version.html#rfc-0042-add-system-version-that-replaces-stateversion-on-runtimeversion","approved/0042-extrinsics-state-version.html#summary","approved/0042-extrinsics-state-version.html#motivation","approved/0042-extrinsics-state-version.html#stakeholders","approved/0042-extrinsics-state-version.html#explanation","approved/0042-extrinsics-state-version.html#drawbacks","approved/0042-extrinsics-state-version.html#testing-security-and-privacy","approved/0042-extrinsics-state-version.html#performance-ergonomics-and-compatibility","approved/0042-extrinsics-state-version.html#performance","approved/0042-extrinsics-state-version.html#ergonomics","approved/0042-extrinsics-state-version.html#compatibility","approved/0042-extrinsics-state-version.html#prior-art-and-references","approved/0042-extrinsics-state-version.html#unresolved-questions","approved/0042-extrinsics-state-version.html#future-directions-and-related-material","approved/0043-storage-proof-size-hostfunction.html#rfc-0043-introduce-storage_proof_size-host-function-for-improved-parachain-block-utilization","approved/0043-storage-proof-size-hostfunction.html#summary","approved/0043-storage-proof-size-hostfunction.html#motivation","approved/0043-storage-proof-size-hostfunction.html#stakeholders","approved/0043-storage-proof-size-hostfunction.html#explanation","approved/0043-storage-proof-size-hostfunction.html#performance-ergonomics-and-compatibility","approved/0043-storage-proof-size-hostfunction.html#performance","approved/0043-storage-proof-size-hostfunction.html#ergonomics","approved/0043-storage-proof-size-hostfunction.html#compatibility","approved/0043-storage-proof-size-hostfunction.html#prior-art-and-references","approved/0045-nft-deposits-asset-hub.html#rfc-0045-lowering-nft-deposits-on-asset-hub","approved/0045-nft-deposits-asset-hub.html#summary","approved/0045-nft-deposits-asset-hub.html#motivation","approved/0045-nft-deposits-asset-hub.html#requirements","approved/0045-nft-deposits-asset-hub.html#stakeholders","approved/0045-nft-deposits-asset-hub.html#explanation","approved/0045-nft-deposits-asset-hub.html#enhanced-approach-to-further-lower-barriers-for-entry","approved/0045-nft-deposits-asset-hub.html#short--and-long-term-plans","approved/0045-nft-deposits-asset-hub.html#drawbacks","approved/0045-nft-deposits-asset-hub.html#testing-security-and-privacy","approved/0045-nft-deposits-asset-hub.html#security-concerns","approved/0045-nft-deposits-asset-hub.html#performance-ergonomics-and-compatibility","approved/0045-nft-deposits-asset-hub.html#performance","approved/0045-nft-deposits-asset-hub.html#ergonomics","approved/0045-nft-deposits-asset-hub.html#compatibility","approved/0045-nft-deposits-asset-hub.html#unresolved-questions","approved/0045-nft-deposits-asset-hub.html#addendum","approved/0045-nft-deposits-asset-hub.html#enhanced-weak-governance-origin-model","approved/0045-nft-deposits-asset-hub.html#function-based-pricing-model","approved/0045-nft-deposits-asset-hub.html#linking-deposit-to-usdx-value","approved/0047-assignment-of-availability-chunks.html#rfc-0047-assignment-of-availability-chunks-to-validators","approved/0047-assignment-of-availability-chunks.html#summary","approved/0047-assignment-of-availability-chunks.html#motivation","approved/0047-assignment-of-availability-chunks.html#stakeholders","approved/0047-assignment-of-availability-chunks.html#explanation","approved/0047-assignment-of-availability-chunks.html#systematic-erasure-codes","approved/0047-assignment-of-availability-chunks.html#availability-recovery-at-present","approved/0047-assignment-of-availability-chunks.html#availability-recovery-from-systematic-chunks","approved/0047-assignment-of-availability-chunks.html#chunk-assignment-function","approved/0047-assignment-of-availability-chunks.html#network-protocol","approved/0047-assignment-of-availability-chunks.html#upgrade-path","approved/0047-assignment-of-availability-chunks.html#drawbacks","approved/0047-assignment-of-availability-chunks.html#testing-security-and-privacy","approved/0047-assignment-of-availability-chunks.html#performance-ergonomics-and-compatibility","approved/0047-assignment-of-availability-chunks.html#performance","approved/0047-assignment-of-availability-chunks.html#ergonomics","approved/0047-assignment-of-availability-chunks.html#compatibility","approved/0047-assignment-of-availability-chunks.html#prior-art-and-references","approved/0047-assignment-of-availability-chunks.html#unresolved-questions","approved/0047-assignment-of-availability-chunks.html#future-directions-and-related-material","approved/0047-assignment-of-availability-chunks.html#appendix-a","approved/0048-session-keys-runtime-api.html#rfc-0048-generate-ownership-proof-for-sessionkeys","approved/0048-session-keys-runtime-api.html#summary","approved/0048-session-keys-runtime-api.html#motivation","approved/0048-session-keys-runtime-api.html#stakeholders","approved/0048-session-keys-runtime-api.html#explanation","approved/0048-session-keys-runtime-api.html#drawbacks","approved/0048-session-keys-runtime-api.html#testing-security-and-privacy","approved/0048-session-keys-runtime-api.html#performance-ergonomics-and-compatibility","approved/0048-session-keys-runtime-api.html#performance","approved/0048-session-keys-runtime-api.html#ergonomics","approved/0048-session-keys-runtime-api.html#compatibility","approved/0048-session-keys-runtime-api.html#prior-art-and-references","approved/0048-session-keys-runtime-api.html#unresolved-questions","approved/0048-session-keys-runtime-api.html#future-directions-and-related-material","approved/0050-fellowship-salaries.html#rfc-0050-fellowship-salaries","approved/0050-fellowship-salaries.html#summary","approved/0050-fellowship-salaries.html#motivation","approved/0050-fellowship-salaries.html#stakeholders","approved/0050-fellowship-salaries.html#explanation","approved/0050-fellowship-salaries.html#salary-asset","approved/0050-fellowship-salaries.html#projections","approved/0050-fellowship-salaries.html#updates","approved/0050-fellowship-salaries.html#drawbacks","approved/0050-fellowship-salaries.html#testing-security-and-privacy","approved/0050-fellowship-salaries.html#performance-ergonomics-and-compatibility","approved/0050-fellowship-salaries.html#performance","approved/0050-fellowship-salaries.html#ergonomics","approved/0050-fellowship-salaries.html#compatibility","approved/0050-fellowship-salaries.html#prior-art-and-references","approved/0050-fellowship-salaries.html#unresolved-questions","approved/0056-one-transaction-per-notification.html#rfc-0056-enforce-only-one-transaction-per-notification","approved/0056-one-transaction-per-notification.html#summary","approved/0056-one-transaction-per-notification.html#motivation","approved/0056-one-transaction-per-notification.html#stakeholders","approved/0056-one-transaction-per-notification.html#explanation","approved/0056-one-transaction-per-notification.html#drawbacks","approved/0056-one-transaction-per-notification.html#testing-security-and-privacy","approved/0056-one-transaction-per-notification.html#performance-ergonomics-and-compatibility","approved/0056-one-transaction-per-notification.html#performance","approved/0056-one-transaction-per-notification.html#ergonomics","approved/0056-one-transaction-per-notification.html#compatibility","approved/0056-one-transaction-per-notification.html#prior-art-and-references","approved/0056-one-transaction-per-notification.html#unresolved-questions","approved/0056-one-transaction-per-notification.html#future-directions-and-related-material","approved/0059-nodes-capabilities-discovery.html#rfc-0059-add-a-discovery-mechanism-for-nodes-based-on-their-capabilities","approved/0059-nodes-capabilities-discovery.html#summary","approved/0059-nodes-capabilities-discovery.html#motivation","approved/0059-nodes-capabilities-discovery.html#stakeholders","approved/0059-nodes-capabilities-discovery.html#explanation","approved/0059-nodes-capabilities-discovery.html#capabilities","approved/0059-nodes-capabilities-discovery.html#dht-provider-registration","approved/0059-nodes-capabilities-discovery.html#secondary-dhts","approved/0059-nodes-capabilities-discovery.html#head-of-the-chain-providers","approved/0059-nodes-capabilities-discovery.html#drawbacks","approved/0059-nodes-capabilities-discovery.html#testing-security-and-privacy","approved/0059-nodes-capabilities-discovery.html#performance-ergonomics-and-compatibility","approved/0059-nodes-capabilities-discovery.html#performance","approved/0059-nodes-capabilities-discovery.html#ergonomics","approved/0059-nodes-capabilities-discovery.html#compatibility","approved/0059-nodes-capabilities-discovery.html#prior-art-and-references","approved/0059-nodes-capabilities-discovery.html#unresolved-questions","approved/0059-nodes-capabilities-discovery.html#future-directions-and-related-material","approved/0078-merkleized-metadata.html#rfc-0078-merkleized-metadata","approved/0078-merkleized-metadata.html#summary","approved/0078-merkleized-metadata.html#motivation","approved/0078-merkleized-metadata.html#requirements","approved/0078-merkleized-metadata.html#reduce-metadata-size","approved/0078-merkleized-metadata.html#stakeholders","approved/0078-merkleized-metadata.html#explanation","approved/0078-merkleized-metadata.html#metadata-digest","approved/0078-merkleized-metadata.html#extrinsic-metadata","approved/0078-merkleized-metadata.html#type-information","approved/0078-merkleized-metadata.html#prune-unrelated-types","approved/0078-merkleized-metadata.html#generating-typeref","approved/0078-merkleized-metadata.html#building-the-merkle-tree-root","approved/0078-merkleized-metadata.html#inclusion-in-an-extrinsic","approved/0078-merkleized-metadata.html#drawbacks","approved/0078-merkleized-metadata.html#testing-security-and-privacy","approved/0078-merkleized-metadata.html#performance-ergonomics-and-compatibility","approved/0078-merkleized-metadata.html#performance","approved/0078-merkleized-metadata.html#ergonomics--compatibility","approved/0078-merkleized-metadata.html#prior-art-and-references","approved/0078-merkleized-metadata.html#unresolved-questions","approved/0078-merkleized-metadata.html#future-directions-and-related-material","approved/0084-general-transaction-extrinsic-format.html#rfc-0084-general-transactions-in-extrinsic-format","approved/0084-general-transaction-extrinsic-format.html#summary","approved/0084-general-transaction-extrinsic-format.html#motivation","approved/0084-general-transaction-extrinsic-format.html#stakeholders","approved/0084-general-transaction-extrinsic-format.html#explanation","approved/0084-general-transaction-extrinsic-format.html#drawbacks","approved/0084-general-transaction-extrinsic-format.html#testing-security-and-privacy","approved/0084-general-transaction-extrinsic-format.html#performance-ergonomics-and-compatibility","approved/0084-general-transaction-extrinsic-format.html#performance","approved/0084-general-transaction-extrinsic-format.html#ergonomics","approved/0084-general-transaction-extrinsic-format.html#compatibility","approved/0084-general-transaction-extrinsic-format.html#prior-art-and-references","approved/0084-general-transaction-extrinsic-format.html#unresolved-questions","approved/0084-general-transaction-extrinsic-format.html#future-directions-and-related-material","approved/0091-dht-record-creation-time.html#rfc-0091-dht-authority-discovery-record-creation-time","approved/0091-dht-record-creation-time.html#summary","approved/0091-dht-record-creation-time.html#motivation","approved/0091-dht-record-creation-time.html#stakeholders","approved/0091-dht-record-creation-time.html#explanation","approved/0091-dht-record-creation-time.html#drawbacks","approved/0091-dht-record-creation-time.html#testing-security-and-privacy","approved/0091-dht-record-creation-time.html#performance-ergonomics-and-compatibility","approved/0091-dht-record-creation-time.html#performance","approved/0091-dht-record-creation-time.html#ergonomics","approved/0091-dht-record-creation-time.html#compatibility","approved/0091-dht-record-creation-time.html#prior-art-and-references","approved/0091-dht-record-creation-time.html#unresolved-questions","approved/0091-dht-record-creation-time.html#future-directions-and-related-material","approved/0097-unbonding_queue.html#rfc-0097-unbonding-queue","approved/0097-unbonding_queue.html#summary","approved/0097-unbonding_queue.html#motivation","approved/0097-unbonding_queue.html#stakeholders","approved/0097-unbonding_queue.html#explanation","approved/0097-unbonding_queue.html#mechanism","approved/0097-unbonding_queue.html#proposed-parameters","approved/0097-unbonding_queue.html#rebonding","approved/0097-unbonding_queue.html#empirical-analysis","approved/0097-unbonding_queue.html#additional-considerations","approved/0097-unbonding_queue.html#deferred-slashing","approved/0097-unbonding_queue.html#uxui","approved/0097-unbonding_queue.html#conviction-voting","approved/0097-unbonding_queue.html#potential-extension","approved/0097-unbonding_queue.html#drawbacks","approved/0097-unbonding_queue.html#testing-security-and-privacy","approved/0097-unbonding_queue.html#performance-ergonomics-and-compatibility","approved/0097-unbonding_queue.html#performance","approved/0097-unbonding_queue.html#ergonomics","approved/0097-unbonding_queue.html#compatibility","approved/0097-unbonding_queue.html#prior-art-and-references","approved/0099-transaction-extension-version.html#rfc-0099-introduce-a-transaction-extension-version","approved/0099-transaction-extension-version.html#summary","approved/0099-transaction-extension-version.html#motivation","approved/0099-transaction-extension-version.html#stakeholders","approved/0099-transaction-extension-version.html#explanation","approved/0099-transaction-extension-version.html#drawbacks","approved/0099-transaction-extension-version.html#testing-security-and-privacy","approved/0099-transaction-extension-version.html#performance-ergonomics-and-compatibility","approved/0099-transaction-extension-version.html#performance","approved/0099-transaction-extension-version.html#ergonomics","approved/0099-transaction-extension-version.html#compatibility","approved/0099-transaction-extension-version.html#prior-art-and-references","approved/0099-transaction-extension-version.html#unresolved-questions","approved/0099-transaction-extension-version.html#future-directions-and-related-material","approved/0100-xcm-multi-type-asset-transfer.html#rfc-0100-new-xcm-instruction-initiateassetstransfer","approved/0100-xcm-multi-type-asset-transfer.html#summary","approved/0100-xcm-multi-type-asset-transfer.html#motivation","approved/0100-xcm-multi-type-asset-transfer.html#stakeholders","approved/0100-xcm-multi-type-asset-transfer.html#explanation","approved/0100-xcm-multi-type-asset-transfer.html#example-usage-transferring-2-different-asset-types-across-3-chains","approved/0100-xcm-multi-type-asset-transfer.html#drawbacks","approved/0100-xcm-multi-type-asset-transfer.html#testing-security-and-privacy","approved/0100-xcm-multi-type-asset-transfer.html#performance-ergonomics-and-compatibility","approved/0100-xcm-multi-type-asset-transfer.html#performance","approved/0100-xcm-multi-type-asset-transfer.html#ergonomics","approved/0100-xcm-multi-type-asset-transfer.html#compatibility","approved/0100-xcm-multi-type-asset-transfer.html#prior-art-and-references","approved/0100-xcm-multi-type-asset-transfer.html#unresolved-questions","approved/0100-xcm-multi-type-asset-transfer.html#future-directions-and-related-material","approved/0101-xcm-transact-remove-max-weight-param.html#rfc-0101-xcm-transact-remove-require_weight_at_most-parameter","approved/0101-xcm-transact-remove-max-weight-param.html#summary","approved/0101-xcm-transact-remove-max-weight-param.html#motivation","approved/0101-xcm-transact-remove-max-weight-param.html#stakeholders","approved/0101-xcm-transact-remove-max-weight-param.html#explanation","approved/0101-xcm-transact-remove-max-weight-param.html#drawbacks","approved/0101-xcm-transact-remove-max-weight-param.html#testing-security-and-privacy","approved/0101-xcm-transact-remove-max-weight-param.html#performance-ergonomics-and-compatibility","approved/0101-xcm-transact-remove-max-weight-param.html#performance","approved/0101-xcm-transact-remove-max-weight-param.html#ergonomics","approved/0101-xcm-transact-remove-max-weight-param.html#compatibility","approved/0101-xcm-transact-remove-max-weight-param.html#prior-art-and-references","approved/0101-xcm-transact-remove-max-weight-param.html#unresolved-questions","approved/0101-xcm-transact-remove-max-weight-param.html#future-directions-and-related-material","approved/0103-introduce-core-index-commitment.html#rfc-0103--introduce-a-coreindex-commitment-and-a-sessionindex-field-in-candidate-receipts","approved/0103-introduce-core-index-commitment.html#summary","approved/0103-introduce-core-index-commitment.html#motivation","approved/0103-introduce-core-index-commitment.html#stakeholders","approved/0103-introduce-core-index-commitment.html#explanation","approved/0103-introduce-core-index-commitment.html#reclaiming-unused-space-in-the-descriptor","approved/0103-introduce-core-index-commitment.html#ump-transport","approved/0103-introduce-core-index-commitment.html#polkadot-primitive-changes","approved/0103-introduce-core-index-commitment.html#backwards-compatibility","approved/0103-introduce-core-index-commitment.html#parachain-block-validation","approved/0103-introduce-core-index-commitment.html#on-chain-backing","approved/0103-introduce-core-index-commitment.html#drawbacks","approved/0103-introduce-core-index-commitment.html#testing-security-and-privacy","approved/0103-introduce-core-index-commitment.html#performance","approved/0103-introduce-core-index-commitment.html#ergonomics","approved/0103-introduce-core-index-commitment.html#compatibility","approved/0103-introduce-core-index-commitment.html#relay-chain-runtime","approved/0103-introduce-core-index-commitment.html#validators","approved/0103-introduce-core-index-commitment.html#tooling","approved/0103-introduce-core-index-commitment.html#prior-art-and-references","approved/0103-introduce-core-index-commitment.html#unresolved-questions","approved/0103-introduce-core-index-commitment.html#future-directions-and-related-material","approved/0105-xcm-improved-fee-mechanism.html#rfc-0105-xcm-improved-fee-mechanism","approved/0105-xcm-improved-fee-mechanism.html#summary","approved/0105-xcm-improved-fee-mechanism.html#motivation","approved/0105-xcm-improved-fee-mechanism.html#stakeholders","approved/0105-xcm-improved-fee-mechanism.html#explanation","approved/0105-xcm-improved-fee-mechanism.html#examples","approved/0105-xcm-improved-fee-mechanism.html#drawbacks","approved/0105-xcm-improved-fee-mechanism.html#testing-security-and-privacy","approved/0105-xcm-improved-fee-mechanism.html#performance-ergonomics-and-compatibility","approved/0105-xcm-improved-fee-mechanism.html#performance","approved/0105-xcm-improved-fee-mechanism.html#ergonomics","approved/0105-xcm-improved-fee-mechanism.html#compatibility","approved/0105-xcm-improved-fee-mechanism.html#prior-art-and-references","approved/0105-xcm-improved-fee-mechanism.html#unresolved-questions","approved/0105-xcm-improved-fee-mechanism.html#future-directions-and-related-material","approved/0107-xcm-execution-hints.html#rfc-0107-xcm-execution-hints","approved/0107-xcm-execution-hints.html#summary","approved/0107-xcm-execution-hints.html#motivation","approved/0107-xcm-execution-hints.html#stakeholders","approved/0107-xcm-execution-hints.html#explanation","approved/0107-xcm-execution-hints.html#drawbacks","approved/0107-xcm-execution-hints.html#testing-security-and-privacy","approved/0107-xcm-execution-hints.html#performance-ergonomics-and-compatibility","approved/0107-xcm-execution-hints.html#performance","approved/0107-xcm-execution-hints.html#ergonomics","approved/0107-xcm-execution-hints.html#compatibility","approved/0107-xcm-execution-hints.html#prior-art-and-references","approved/0107-xcm-execution-hints.html#unresolved-questions","approved/0107-xcm-execution-hints.html#future-directions-and-related-material","approved/0108-xcm-remove-testnet-ids.html#rfc-0108-remove-xcm-testnet-networkids","approved/0108-xcm-remove-testnet-ids.html#summary","approved/0108-xcm-remove-testnet-ids.html#motivation","approved/0108-xcm-remove-testnet-ids.html#stakeholders","approved/0108-xcm-remove-testnet-ids.html#explanation","approved/0108-xcm-remove-testnet-ids.html#drawbacks","approved/0108-xcm-remove-testnet-ids.html#testing-security-and-privacy","approved/0108-xcm-remove-testnet-ids.html#performance-ergonomics-and-compatibility","approved/0108-xcm-remove-testnet-ids.html#performance","approved/0108-xcm-remove-testnet-ids.html#ergonomics","approved/0108-xcm-remove-testnet-ids.html#compatibility","approved/0108-xcm-remove-testnet-ids.html#prior-art-and-references","approved/0108-xcm-remove-testnet-ids.html#unresolved-questions","approved/0108-xcm-remove-testnet-ids.html#future-directions-and-related-material","approved/0122-alias-origin-on-asset-transfers.html#rfc-0122-asset-transfers-can-alias-xcm-origin-on-destination-to-original-origin","approved/0122-alias-origin-on-asset-transfers.html#summary","approved/0122-alias-origin-on-asset-transfers.html#motivation","approved/0122-alias-origin-on-asset-transfers.html#stakeholders","approved/0122-alias-origin-on-asset-transfers.html#explanation","approved/0122-alias-origin-on-asset-transfers.html#trust-assumptions","approved/0122-alias-origin-on-asset-transfers.html#xcm-initiateassetstransfer-instruction-changes","approved/0122-alias-origin-on-asset-transfers.html#example-scenarios","approved/0122-alias-origin-on-asset-transfers.html#drawbacks","approved/0122-alias-origin-on-asset-transfers.html#testing-security-and-privacy","approved/0122-alias-origin-on-asset-transfers.html#performance-ergonomics-and-compatibility","approved/0122-alias-origin-on-asset-transfers.html#performance","approved/0122-alias-origin-on-asset-transfers.html#ergonomics","approved/0122-alias-origin-on-asset-transfers.html#compatibility","approved/0122-alias-origin-on-asset-transfers.html#prior-art-and-references","approved/0122-alias-origin-on-asset-transfers.html#unresolved-questions","approved/0122-alias-origin-on-asset-transfers.html#future-directions-and-related-material","stale/0000-rewards.html#rfc-0000-validator-rewards","stale/0000-rewards.html#summary","stale/0000-rewards.html#motivation","stale/0000-rewards.html#stakeholders","stale/0000-rewards.html#logic","stale/0000-rewards.html#categories","stale/0000-rewards.html#collection","stale/0000-rewards.html#messages","stale/0000-rewards.html#rewards-compoutation","stale/0000-rewards.html#strategies","stale/0000-rewards.html#explanation","stale/0000-rewards.html#backing","stale/0000-rewards.html#approvals","stale/0000-rewards.html#availability-redistribution","stale/0000-rewards.html#tit-for-tat","stale/0000-rewards.html#concerns-drawbacks-testing-security-and-privacy","stale/0000-rewards.html#performance-ergonomics-and-compatibility","stale/0000-rewards.html#prior-art-and-references","stale/0000-rewards.html#unresolved-questions","stale/0000-rewards.html#future-directions-and-related-material","stale/0000-rewards.html#synthetic-parachain-flag","stale/0004-remove-unnecessary-allocator-usage.html#rfc-0004-remove-the-host-side-runtime-memory-allocator","stale/0004-remove-unnecessary-allocator-usage.html#summary","stale/0004-remove-unnecessary-allocator-usage.html#motivation","stale/0004-remove-unnecessary-allocator-usage.html#stakeholders","stale/0004-remove-unnecessary-allocator-usage.html#explanation","stale/0004-remove-unnecessary-allocator-usage.html#new-host-functions","stale/0004-remove-unnecessary-allocator-usage.html#other-changes","stale/0004-remove-unnecessary-allocator-usage.html#drawbacks","stale/0004-remove-unnecessary-allocator-usage.html#prior-art","stale/0004-remove-unnecessary-allocator-usage.html#unresolved-questions","stale/0004-remove-unnecessary-allocator-usage.html#future-possibilities","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#rfc-0006-dynamic-pricing-for-bulk-coretime-sales","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#summary","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#motivation","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#requirements","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#stakeholders","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#explanation","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#overview","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#parameters","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#function","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#pseudo-code","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#properties-of-the-curve","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#example-configurations","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#drawbacks","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#prior-art-and-references","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#future-possibilities","stale/0006-dynamic-pricing-for-bulk-coretime-sales.html#references","stale/0009-improved-net-light-client-requests.html#rfc-0009-improved-light-client-requests-networking-protocol","stale/0009-improved-net-light-client-requests.html#summary","stale/0009-improved-net-light-client-requests.html#motivation","stale/0009-improved-net-light-client-requests.html#stakeholders","stale/0009-improved-net-light-client-requests.html#explanation","stale/0009-improved-net-light-client-requests.html#drawbacks","stale/0009-improved-net-light-client-requests.html#testing-security-and-privacy","stale/0009-improved-net-light-client-requests.html#performance-ergonomics-and-compatibility","stale/0009-improved-net-light-client-requests.html#performance","stale/0009-improved-net-light-client-requests.html#ergonomics","stale/0009-improved-net-light-client-requests.html#compatibility","stale/0009-improved-net-light-client-requests.html#prior-art-and-references","stale/0009-improved-net-light-client-requests.html#unresolved-questions","stale/0009-improved-net-light-client-requests.html#future-directions-and-related-material","stale/0015-market-design-revisit.html#rfc-0015-market-design-revisit","stale/0015-market-design-revisit.html#summary","stale/0015-market-design-revisit.html#motivation","stale/0015-market-design-revisit.html#stakeholders","stale/0015-market-design-revisit.html#explanation","stale/0015-market-design-revisit.html#bulk-markets","stale/0015-market-design-revisit.html#benefits-of-this-system","stale/0015-market-design-revisit.html#further-discussion-points","stale/0015-market-design-revisit.html#drawbacks","stale/0015-market-design-revisit.html#prior-art-and-references","stale/0015-market-design-revisit.html#unresolved-questions","stale/0034-xcm-absolute-location-account-derivation.html#rfc-34-xcm-absolute-location-account-derivation","stale/0034-xcm-absolute-location-account-derivation.html#summary","stale/0034-xcm-absolute-location-account-derivation.html#motivation","stale/0034-xcm-absolute-location-account-derivation.html#stakeholders","stale/0034-xcm-absolute-location-account-derivation.html#explanation","stale/0034-xcm-absolute-location-account-derivation.html#drawbacks","stale/0034-xcm-absolute-location-account-derivation.html#testing-security-and-privacy","stale/0034-xcm-absolute-location-account-derivation.html#performance-ergonomics-and-compatibility","stale/0034-xcm-absolute-location-account-derivation.html#performance","stale/0034-xcm-absolute-location-account-derivation.html#ergonomics","stale/0034-xcm-absolute-location-account-derivation.html#compatibility","stale/0034-xcm-absolute-location-account-derivation.html#prior-art-and-references","stale/0034-xcm-absolute-location-account-derivation.html#unresolved-questions","stale/0035-conviction-voting-delegation-modifications.html#rfc-0035-conviction-voting-delegation-modifications","stale/0035-conviction-voting-delegation-modifications.html#summary","stale/0035-conviction-voting-delegation-modifications.html#motivation","stale/0035-conviction-voting-delegation-modifications.html#stakeholders","stale/0035-conviction-voting-delegation-modifications.html#explanation","stale/0035-conviction-voting-delegation-modifications.html#drawbacks","stale/0035-conviction-voting-delegation-modifications.html#testing-security-and-privacy","stale/0035-conviction-voting-delegation-modifications.html#performance-ergonomics-and-compatibility","stale/0035-conviction-voting-delegation-modifications.html#performance","stale/0035-conviction-voting-delegation-modifications.html#ergonomics--compatibility","stale/0035-conviction-voting-delegation-modifications.html#prior-art-and-references","stale/0035-conviction-voting-delegation-modifications.html#unresolved-questions","stale/0035-conviction-voting-delegation-modifications.html#future-directions-and-related-material","stale/0044-rent-based-registration.html#rfc-0044-rent-based-registration-model","stale/0044-rent-based-registration.html#summary","stale/0044-rent-based-registration.html#motivation","stale/0044-rent-based-registration.html#requirements","stale/0044-rent-based-registration.html#stakeholders","stale/0044-rent-based-registration.html#explanation","stale/0044-rent-based-registration.html#registering-an-on-demand-parachain","stale/0044-rent-based-registration.html#on-demand-parachain-pruning","stale/0044-rent-based-registration.html#ensuring-rent-is-paid","stale/0044-rent-based-registration.html#on-demand-para-re-registration","stale/0044-rent-based-registration.html#drawbacks","stale/0044-rent-based-registration.html#testing-security-and-privacy","stale/0044-rent-based-registration.html#performance-ergonomics-and-compatibility","stale/0044-rent-based-registration.html#performance","stale/0044-rent-based-registration.html#ergonomics","stale/0044-rent-based-registration.html#compatibility","stale/0044-rent-based-registration.html#prior-art-and-references","stale/0044-rent-based-registration.html#unresolved-questions","stale/0044-rent-based-registration.html#future-directions-and-related-material","stale/0054-remove-heap-pages.html#rfc-0054-remove-the-concept-of-heap-pages-from-the-client","stale/0054-remove-heap-pages.html#summary","stale/0054-remove-heap-pages.html#motivation","stale/0054-remove-heap-pages.html#stakeholders","stale/0054-remove-heap-pages.html#explanation","stale/0054-remove-heap-pages.html#drawbacks","stale/0054-remove-heap-pages.html#testing-security-and-privacy","stale/0054-remove-heap-pages.html#performance-ergonomics-and-compatibility","stale/0054-remove-heap-pages.html#performance","stale/0054-remove-heap-pages.html#ergonomics","stale/0054-remove-heap-pages.html#compatibility","stale/0054-remove-heap-pages.html#prior-art-and-references","stale/0054-remove-heap-pages.html#unresolved-questions","stale/0054-remove-heap-pages.html#future-directions-and-related-material","stale/0070-x-track-kusamanetwork.html#rfc-0070-x-track-for--kusamanetwork","stale/0070-x-track-kusamanetwork.html#summary","stale/0070-x-track-kusamanetwork.html#motivation","stale/0070-x-track-kusamanetwork.html#stakeholders","stale/0070-x-track-kusamanetwork.html#explanation","stale/0070-x-track-kusamanetwork.html#phase-1---track-configurations","stale/0070-x-track-kusamanetwork.html#phase-2---establish-specs-for-x-post-track-referenda","stale/0070-x-track-kusamanetwork.html#phase-3---release-tooling--documentation","stale/0070-x-track-kusamanetwork.html#drawbacks","stale/0070-x-track-kusamanetwork.html#testing-security-and-privacy","stale/0070-x-track-kusamanetwork.html#performance-ergonomics-and-compatibility","stale/0070-x-track-kusamanetwork.html#performance","stale/0070-x-track-kusamanetwork.html#ergonomics","stale/0070-x-track-kusamanetwork.html#compatibility","stale/0070-x-track-kusamanetwork.html#references","stale/0070-x-track-kusamanetwork.html#unresolved-questions","stale/0073-referedum-deposit-track.html#rfc-0073-decision-deposit-referendum-track","stale/0073-referedum-deposit-track.html#summary","stale/0073-referedum-deposit-track.html#motivation","stale/0073-referedum-deposit-track.html#explanation","stale/0073-referedum-deposit-track.html#referendum-track-parameters---polkadot","stale/0073-referedum-deposit-track.html#referendum-track-parameters---kusama","stale/0073-referedum-deposit-track.html#drawbacks","stale/0073-referedum-deposit-track.html#testing-security-and-privacy","stale/0073-referedum-deposit-track.html#performance-ergonomics-and-compatibility","stale/0073-referedum-deposit-track.html#performance","stale/0073-referedum-deposit-track.html#ergonomics","stale/0073-referedum-deposit-track.html#compatibility","stale/0073-referedum-deposit-track.html#prior-art-and-references","stale/0073-referedum-deposit-track.html#unresolved-questions","stale/0074-stateful-multisig-pallet.html#rfc-0074-stateful-multisig-pallet","stale/0074-stateful-multisig-pallet.html#summary","stale/0074-stateful-multisig-pallet.html#motivation","stale/0074-stateful-multisig-pallet.html#problem","stale/0074-stateful-multisig-pallet.html#requirements","stale/0074-stateful-multisig-pallet.html#use-cases","stale/0074-stateful-multisig-pallet.html#stakeholders","stale/0074-stateful-multisig-pallet.html#explanation","stale/0074-stateful-multisig-pallet.html#state-transition-functions","stale/0074-stateful-multisig-pallet.html#storagestate","stale/0074-stateful-multisig-pallet.html#considerations--edge-cases","stale/0074-stateful-multisig-pallet.html#drawbacks","stale/0074-stateful-multisig-pallet.html#testing-security-and-privacy","stale/0074-stateful-multisig-pallet.html#performance-ergonomics-and-compatibility","stale/0074-stateful-multisig-pallet.html#performance","stale/0074-stateful-multisig-pallet.html#ergonomics","stale/0074-stateful-multisig-pallet.html#compatibility","stale/0074-stateful-multisig-pallet.html#prior-art-and-references","stale/0074-stateful-multisig-pallet.html#unresolved-questions","stale/0074-stateful-multisig-pallet.html#future-directions-and-related-material","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#rfc-0077-increase-maximum-length-of-identity-pgp-fingerprint-values-from-20-bytes","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#summary","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#motivation","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#background","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#problem","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#solution-requirements","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#stakeholders","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#explanation","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#drawbacks","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#testing-security-and-privacy","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#performance-ergonomics-and-compatibility","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#performance","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#ergonomics","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#compatibility","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#prior-art-and-references","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#unresolved-questions","stale/0077-increase-max-length-of-identity-pgp-fingerprint-value.html#future-directions-and-related-material","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#rfc-0088-add-slashable-locked-deposit-purchaser-reputation-and-reserved-cores-for-on-chain-identities-to-broker-pallet","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#summary","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#motivation","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#background","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#problem","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#solution-requirements","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#stakeholders","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#drawbacks","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#testing-security-and-privacy","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance-ergonomics-and-compatibility","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#performance-1","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#ergonomics","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#compatibility","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#prior-art-and-references","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#prior-art","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#unresolved-questions","stale/0088-broker-pallet-slashable-deposit-purchaser-reputation-reserved-cores.html#future-directions-and-related-material","stale/0089-flexible-inflation.html#rfc-0089-flexible-inflation","stale/0089-flexible-inflation.html#summary","stale/0089-flexible-inflation.html#motivation","stale/0089-flexible-inflation.html#stakeholders","stale/0089-flexible-inflation.html#explanation","stale/0089-flexible-inflation.html#existing-order","stale/0089-flexible-inflation.html#new-order","stale/0089-flexible-inflation.html#proposed-implementation","stale/0089-flexible-inflation.html#drawbacks","stale/0089-flexible-inflation.html#testing-security-and-privacy","stale/0089-flexible-inflation.html#performance-ergonomics-and-compatibility","stale/0089-flexible-inflation.html#prior-art-and-references","stale/0089-flexible-inflation.html#unresolved-questions","stale/0089-flexible-inflation.html#future-directions-and-related-material","stale/00xx-secondary-marketplace-for-regions.html#rfc-0001-secondary-market-for-regions","stale/00xx-secondary-marketplace-for-regions.html#summary","stale/00xx-secondary-marketplace-for-regions.html#motivation","stale/00xx-secondary-marketplace-for-regions.html#stakeholders","stale/00xx-secondary-marketplace-for-regions.html#explanation","stale/00xx-secondary-marketplace-for-regions.html#drawbacks","stale/00xx-secondary-marketplace-for-regions.html#testing-security-and-privacy","stale/00xx-secondary-marketplace-for-regions.html#testing","stale/00xx-secondary-marketplace-for-regions.html#security","stale/00xx-secondary-marketplace-for-regions.html#privacy","stale/00xx-secondary-marketplace-for-regions.html#performance-ergonomics-and-compatibility","stale/00xx-secondary-marketplace-for-regions.html#performance","stale/00xx-secondary-marketplace-for-regions.html#ergonomics","stale/00xx-secondary-marketplace-for-regions.html#compatibility","stale/00xx-secondary-marketplace-for-regions.html#prior-art-and-references","stale/00xx-secondary-marketplace-for-regions.html#unresolved-questions","stale/00xx-secondary-marketplace-for-regions.html#future-directions-and-related-material","stale/00xx-smart-contracts-coretime-chain.html#rfc-0002-smart-contracts-on-the-coretime-chain","stale/00xx-smart-contracts-coretime-chain.html#summary","stale/00xx-smart-contracts-coretime-chain.html#motivation","stale/00xx-smart-contracts-coretime-chain.html#stakeholders","stale/00xx-smart-contracts-coretime-chain.html#explanation","stale/00xx-smart-contracts-coretime-chain.html#drawbacks","stale/00xx-smart-contracts-coretime-chain.html#testing-security-and-privacy","stale/00xx-smart-contracts-coretime-chain.html#testing","stale/00xx-smart-contracts-coretime-chain.html#security","stale/00xx-smart-contracts-coretime-chain.html#privacy","stale/00xx-smart-contracts-coretime-chain.html#performance-ergonomics-and-compatibility","stale/00xx-smart-contracts-coretime-chain.html#performance","stale/00xx-smart-contracts-coretime-chain.html#ergonomics","stale/00xx-smart-contracts-coretime-chain.html#compatibility","stale/00xx-smart-contracts-coretime-chain.html#prior-art-and-references","stale/00xx-smart-contracts-coretime-chain.html#unresolved-questions","stale/00xx-smart-contracts-coretime-chain.html#future-directions-and-related-material","stale/0106-xcm-remove-fees-mode.html#rfc-0106-remove-xcm-fees-mode","stale/0106-xcm-remove-fees-mode.html#summary","stale/0106-xcm-remove-fees-mode.html#motivation","stale/0106-xcm-remove-fees-mode.html#stakeholders","stale/0106-xcm-remove-fees-mode.html#explanation","stale/0106-xcm-remove-fees-mode.html#drawbacks","stale/0106-xcm-remove-fees-mode.html#testing-security-and-privacy","stale/0106-xcm-remove-fees-mode.html#performance-ergonomics-and-compatibility","stale/0106-xcm-remove-fees-mode.html#performance","stale/0106-xcm-remove-fees-mode.html#ergonomics","stale/0106-xcm-remove-fees-mode.html#compatibility","stale/0106-xcm-remove-fees-mode.html#prior-art-and-references","stale/0106-xcm-remove-fees-mode.html#unresolved-questions","stale/0106-xcm-remove-fees-mode.html#future-directions-and-related-material","stale/0112-compress-state-response-message-in-state-sync.html#rfc-0112-compress-the-state-response-message-in-state-sync","stale/0112-compress-state-response-message-in-state-sync.html#summary","stale/0112-compress-state-response-message-in-state-sync.html#motivation","stale/0112-compress-state-response-message-in-state-sync.html#stakeholders","stale/0112-compress-state-response-message-in-state-sync.html#explanation","stale/0112-compress-state-response-message-in-state-sync.html#drawbacks","stale/0112-compress-state-response-message-in-state-sync.html#testing-security-and-privacy","stale/0112-compress-state-response-message-in-state-sync.html#performance-ergonomics-and-compatibility","stale/0112-compress-state-response-message-in-state-sync.html#performance","stale/0112-compress-state-response-message-in-state-sync.html#ergonomics","stale/0112-compress-state-response-message-in-state-sync.html#compatibility","stale/0112-compress-state-response-message-in-state-sync.html#prior-art-and-references","stale/0112-compress-state-response-message-in-state-sync.html#unresolved-questions","stale/0112-compress-state-response-message-in-state-sync.html#future-directions-and-related-material","stale/0120-referenda-confirmation-by-candle-mechanism.html#rfc-0120-referenda-confirmation-by-candle-mechanism","stale/0120-referenda-confirmation-by-candle-mechanism.html#summary","stale/0120-referenda-confirmation-by-candle-mechanism.html#motivation","stale/0120-referenda-confirmation-by-candle-mechanism.html#stakeholders","stale/0120-referenda-confirmation-by-candle-mechanism.html#explanation","stale/0120-referenda-confirmation-by-candle-mechanism.html#drawbacks","stale/0120-referenda-confirmation-by-candle-mechanism.html#testing-security-and-privacy","stale/0120-referenda-confirmation-by-candle-mechanism.html#performance-ergonomics-and-compatibility","stale/0120-referenda-confirmation-by-candle-mechanism.html#performance","stale/0120-referenda-confirmation-by-candle-mechanism.html#ergonomics","stale/0120-referenda-confirmation-by-candle-mechanism.html#compatibility","stale/0120-referenda-confirmation-by-candle-mechanism.html#prior-art-and-references","stale/0120-referenda-confirmation-by-candle-mechanism.html#unresolved-questions","stale/0120-referenda-confirmation-by-candle-mechanism.html#future-directions-and-related-material","stale/TODO-stale-nomination-reward-curve.html#rfc-todo-stale-nomination-reward-curve","stale/TODO-stale-nomination-reward-curve.html#summary","stale/TODO-stale-nomination-reward-curve.html#motivation","stale/TODO-stale-nomination-reward-curve.html#stakeholders","stale/TODO-stale-nomination-reward-curve.html#explanation","stale/TODO-stale-nomination-reward-curve.html#drawbacks","stale/TODO-stale-nomination-reward-curve.html#testing-security-and-privacy","stale/TODO-stale-nomination-reward-curve.html#performance-ergonomics-and-compatibility","stale/TODO-stale-nomination-reward-curve.html#performance","stale/TODO-stale-nomination-reward-curve.html#ergonomics","stale/TODO-stale-nomination-reward-curve.html#compatibility","stale/TODO-stale-nomination-reward-curve.html#prior-art-and-references","stale/TODO-stale-nomination-reward-curve.html#unresolved-questions","stale/TODO-stale-nomination-reward-curve.html#future-directions-and-related-material"],"index":{"documentStore":{"docInfo":{"0":{"body":16,"breadcrumbs":2,"title":1},"1":{"body":52,"breadcrumbs":10,"title":5},"10":{"body":0,"breadcrumbs":8,"title":3},"100":{"body":10,"breadcrumbs":13,"title":1},"1000":{"body":13,"breadcrumbs":8,"title":2},"1001":{"body":6,"breadcrumbs":10,"title":4},"1002":{"body":48,"breadcrumbs":12,"title":6},"1003":{"body":34,"breadcrumbs":7,"title":1},"1004":{"body":101,"breadcrumbs":7,"title":1},"1005":{"body":4,"breadcrumbs":7,"title":1},"1006":{"body":22,"breadcrumbs":7,"title":1},"1007":{"body":16,"breadcrumbs":7,"title":1},"1008":{"body":22,"breadcrumbs":9,"title":3},"1009":{"body":6,"breadcrumbs":9,"title":3},"101":{"body":0,"breadcrumbs":15,"title":3},"1010":{"body":8,"breadcrumbs":7,"title":1},"1011":{"body":11,"breadcrumbs":7,"title":1},"1012":{"body":13,"breadcrumbs":7,"title":1},"1013":{"body":8,"breadcrumbs":9,"title":3},"1014":{"body":19,"breadcrumbs":8,"title":2},"1015":{"body":17,"breadcrumbs":10,"title":4},"102":{"body":1,"breadcrumbs":13,"title":1},"103":{"body":17,"breadcrumbs":13,"title":1},"104":{"body":7,"breadcrumbs":13,"title":1},"105":{"body":16,"breadcrumbs":15,"title":3},"106":{"body":53,"breadcrumbs":8,"title":4},"107":{"body":29,"breadcrumbs":5,"title":1},"108":{"body":110,"breadcrumbs":5,"title":1},"109":{"body":8,"breadcrumbs":5,"title":1},"11":{"body":2,"breadcrumbs":6,"title":1},"110":{"body":0,"breadcrumbs":5,"title":1},"111":{"body":107,"breadcrumbs":5,"title":1},"112":{"body":116,"breadcrumbs":6,"title":2},"113":{"body":72,"breadcrumbs":6,"title":2},"114":{"body":32,"breadcrumbs":5,"title":1},"115":{"body":19,"breadcrumbs":7,"title":3},"116":{"body":0,"breadcrumbs":7,"title":3},"117":{"body":4,"breadcrumbs":5,"title":1},"118":{"body":12,"breadcrumbs":5,"title":1},"119":{"body":5,"breadcrumbs":5,"title":1},"12":{"body":25,"breadcrumbs":6,"title":1},"120":{"body":14,"breadcrumbs":7,"title":3},"121":{"body":96,"breadcrumbs":6,"title":2},"122":{"body":53,"breadcrumbs":10,"title":5},"123":{"body":37,"breadcrumbs":6,"title":1},"124":{"body":56,"breadcrumbs":6,"title":1},"125":{"body":17,"breadcrumbs":6,"title":1},"126":{"body":88,"breadcrumbs":6,"title":1},"127":{"body":32,"breadcrumbs":6,"title":1},"128":{"body":48,"breadcrumbs":8,"title":3},"129":{"body":0,"breadcrumbs":8,"title":3},"13":{"body":6,"breadcrumbs":6,"title":1},"130":{"body":31,"breadcrumbs":6,"title":1},"131":{"body":23,"breadcrumbs":6,"title":1},"132":{"body":25,"breadcrumbs":6,"title":1},"133":{"body":33,"breadcrumbs":8,"title":3},"134":{"body":35,"breadcrumbs":7,"title":2},"135":{"body":30,"breadcrumbs":9,"title":4},"136":{"body":49,"breadcrumbs":18,"title":9},"137":{"body":132,"breadcrumbs":10,"title":1},"138":{"body":72,"breadcrumbs":10,"title":1},"139":{"body":8,"breadcrumbs":10,"title":1},"14":{"body":4,"breadcrumbs":8,"title":3},"140":{"body":126,"breadcrumbs":10,"title":1},"141":{"body":107,"breadcrumbs":10,"title":1},"142":{"body":12,"breadcrumbs":12,"title":3},"143":{"body":0,"breadcrumbs":12,"title":3},"144":{"body":14,"breadcrumbs":10,"title":1},"145":{"body":14,"breadcrumbs":10,"title":1},"146":{"body":37,"breadcrumbs":10,"title":1},"147":{"body":10,"breadcrumbs":12,"title":3},"148":{"body":1,"breadcrumbs":11,"title":2},"149":{"body":38,"breadcrumbs":13,"title":4},"15":{"body":10,"breadcrumbs":7,"title":2},"150":{"body":60,"breadcrumbs":10,"title":5},"151":{"body":12,"breadcrumbs":6,"title":1},"152":{"body":47,"breadcrumbs":6,"title":1},"153":{"body":6,"breadcrumbs":6,"title":1},"154":{"body":0,"breadcrumbs":6,"title":1},"155":{"body":58,"breadcrumbs":8,"title":3},"156":{"body":115,"breadcrumbs":9,"title":4},"157":{"body":113,"breadcrumbs":9,"title":4},"158":{"body":34,"breadcrumbs":9,"title":4},"159":{"body":19,"breadcrumbs":6,"title":1},"16":{"body":37,"breadcrumbs":9,"title":4},"160":{"body":4,"breadcrumbs":8,"title":3},"161":{"body":37,"breadcrumbs":8,"title":3},"162":{"body":2,"breadcrumbs":6,"title":1},"163":{"body":28,"breadcrumbs":6,"title":1},"164":{"body":25,"breadcrumbs":6,"title":1},"165":{"body":5,"breadcrumbs":8,"title":3},"166":{"body":44,"breadcrumbs":7,"title":2},"167":{"body":13,"breadcrumbs":9,"title":4},"168":{"body":49,"breadcrumbs":14,"title":7},"169":{"body":25,"breadcrumbs":8,"title":1},"17":{"body":67,"breadcrumbs":12,"title":6},"170":{"body":111,"breadcrumbs":8,"title":1},"171":{"body":27,"breadcrumbs":8,"title":1},"172":{"body":50,"breadcrumbs":8,"title":1},"173":{"body":37,"breadcrumbs":8,"title":1},"174":{"body":26,"breadcrumbs":10,"title":3},"175":{"body":0,"breadcrumbs":10,"title":3},"176":{"body":15,"breadcrumbs":8,"title":1},"177":{"body":45,"breadcrumbs":9,"title":2},"178":{"body":1,"breadcrumbs":10,"title":3},"179":{"body":24,"breadcrumbs":9,"title":2},"18":{"body":78,"breadcrumbs":7,"title":1},"180":{"body":30,"breadcrumbs":11,"title":4},"181":{"body":65,"breadcrumbs":8,"title":4},"182":{"body":50,"breadcrumbs":5,"title":1},"183":{"body":0,"breadcrumbs":5,"title":1},"184":{"body":124,"breadcrumbs":6,"title":2},"185":{"body":153,"breadcrumbs":5,"title":1},"186":{"body":90,"breadcrumbs":5,"title":1},"187":{"body":54,"breadcrumbs":5,"title":1},"188":{"body":0,"breadcrumbs":5,"title":1},"189":{"body":438,"breadcrumbs":5,"title":1},"19":{"body":90,"breadcrumbs":7,"title":1},"190":{"body":562,"breadcrumbs":5,"title":1},"191":{"body":630,"breadcrumbs":8,"title":4},"192":{"body":103,"breadcrumbs":8,"title":4},"193":{"body":410,"breadcrumbs":6,"title":2},"194":{"body":905,"breadcrumbs":6,"title":2},"195":{"body":52,"breadcrumbs":5,"title":1},"196":{"body":33,"breadcrumbs":7,"title":3},"197":{"body":40,"breadcrumbs":7,"title":3},"198":{"body":35,"breadcrumbs":8,"title":4},"199":{"body":49,"breadcrumbs":7,"title":3},"2":{"body":18,"breadcrumbs":6,"title":1},"20":{"body":4,"breadcrumbs":7,"title":1},"200":{"body":34,"breadcrumbs":7,"title":3},"201":{"body":55,"breadcrumbs":8,"title":4},"202":{"body":43,"breadcrumbs":5,"title":1},"203":{"body":37,"breadcrumbs":5,"title":1},"204":{"body":73,"breadcrumbs":5,"title":1},"205":{"body":21,"breadcrumbs":5,"title":1},"206":{"body":39,"breadcrumbs":5,"title":1},"207":{"body":235,"breadcrumbs":7,"title":3},"208":{"body":86,"breadcrumbs":7,"title":3},"209":{"body":32,"breadcrumbs":7,"title":3},"21":{"body":40,"breadcrumbs":7,"title":1},"210":{"body":2,"breadcrumbs":7,"title":3},"211":{"body":11,"breadcrumbs":7,"title":3},"212":{"body":20,"breadcrumbs":8,"title":4},"213":{"body":2,"breadcrumbs":7,"title":3},"214":{"body":1,"breadcrumbs":7,"title":3},"215":{"body":53,"breadcrumbs":10,"title":5},"216":{"body":40,"breadcrumbs":6,"title":1},"217":{"body":203,"breadcrumbs":6,"title":1},"218":{"body":34,"breadcrumbs":6,"title":1},"219":{"body":8,"breadcrumbs":6,"title":1},"22":{"body":175,"breadcrumbs":9,"title":3},"220":{"body":176,"breadcrumbs":6,"title":1},"221":{"body":18,"breadcrumbs":7,"title":2},"222":{"body":11,"breadcrumbs":6,"title":1},"223":{"body":25,"breadcrumbs":8,"title":3},"224":{"body":14,"breadcrumbs":8,"title":3},"225":{"body":21,"breadcrumbs":6,"title":1},"226":{"body":16,"breadcrumbs":6,"title":1},"227":{"body":8,"breadcrumbs":6,"title":1},"228":{"body":0,"breadcrumbs":8,"title":3},"229":{"body":16,"breadcrumbs":7,"title":2},"23":{"body":42,"breadcrumbs":8,"title":2},"230":{"body":21,"breadcrumbs":8,"title":3},"231":{"body":2,"breadcrumbs":7,"title":2},"232":{"body":13,"breadcrumbs":9,"title":4},"233":{"body":57,"breadcrumbs":16,"title":8},"234":{"body":29,"breadcrumbs":9,"title":1},"235":{"body":185,"breadcrumbs":9,"title":1},"236":{"body":15,"breadcrumbs":9,"title":1},"237":{"body":60,"breadcrumbs":9,"title":1},"238":{"body":110,"breadcrumbs":11,"title":3},"239":{"body":153,"breadcrumbs":11,"title":3},"24":{"body":293,"breadcrumbs":8,"title":2},"240":{"body":96,"breadcrumbs":9,"title":1},"241":{"body":144,"breadcrumbs":11,"title":3},"242":{"body":0,"breadcrumbs":11,"title":3},"243":{"body":110,"breadcrumbs":9,"title":1},"244":{"body":1,"breadcrumbs":9,"title":1},"245":{"body":1,"breadcrumbs":9,"title":1},"246":{"body":1,"breadcrumbs":11,"title":3},"247":{"body":21,"breadcrumbs":10,"title":2},"248":{"body":11,"breadcrumbs":12,"title":4},"249":{"body":23,"breadcrumbs":10,"title":5},"25":{"body":83,"breadcrumbs":9,"title":3},"250":{"body":36,"breadcrumbs":6,"title":1},"251":{"body":21,"breadcrumbs":6,"title":1},"252":{"body":4,"breadcrumbs":6,"title":1},"253":{"body":290,"breadcrumbs":6,"title":1},"254":{"body":44,"breadcrumbs":14,"title":7},"255":{"body":43,"breadcrumbs":8,"title":1},"256":{"body":81,"breadcrumbs":8,"title":1},"257":{"body":10,"breadcrumbs":8,"title":1},"258":{"body":101,"breadcrumbs":8,"title":1},"259":{"body":70,"breadcrumbs":9,"title":2},"26":{"body":83,"breadcrumbs":10,"title":4},"260":{"body":16,"breadcrumbs":8,"title":1},"261":{"body":1,"breadcrumbs":10,"title":3},"262":{"body":39,"breadcrumbs":10,"title":3},"263":{"body":7,"breadcrumbs":10,"title":3},"264":{"body":2,"breadcrumbs":9,"title":2},"265":{"body":51,"breadcrumbs":14,"title":7},"266":{"body":15,"breadcrumbs":8,"title":1},"267":{"body":50,"breadcrumbs":8,"title":1},"268":{"body":27,"breadcrumbs":8,"title":1},"269":{"body":0,"breadcrumbs":8,"title":1},"27":{"body":0,"breadcrumbs":7,"title":1},"270":{"body":117,"breadcrumbs":8,"title":1},"271":{"body":14,"breadcrumbs":8,"title":1},"272":{"body":15,"breadcrumbs":10,"title":3},"273":{"body":0,"breadcrumbs":10,"title":3},"274":{"body":19,"breadcrumbs":8,"title":1},"275":{"body":17,"breadcrumbs":8,"title":1},"276":{"body":16,"breadcrumbs":8,"title":1},"277":{"body":26,"breadcrumbs":10,"title":3},"278":{"body":30,"breadcrumbs":9,"title":2},"279":{"body":35,"breadcrumbs":11,"title":4},"28":{"body":46,"breadcrumbs":8,"title":2},"280":{"body":48,"breadcrumbs":12,"title":6},"281":{"body":35,"breadcrumbs":7,"title":1},"282":{"body":152,"breadcrumbs":7,"title":1},"283":{"body":32,"breadcrumbs":7,"title":1},"284":{"body":4,"breadcrumbs":7,"title":1},"285":{"body":0,"breadcrumbs":7,"title":1},"286":{"body":92,"breadcrumbs":8,"title":2},"287":{"body":52,"breadcrumbs":8,"title":2},"288":{"body":32,"breadcrumbs":7,"title":1},"289":{"body":111,"breadcrumbs":7,"title":1},"29":{"body":32,"breadcrumbs":9,"title":3},"290":{"body":19,"breadcrumbs":9,"title":3},"291":{"body":4,"breadcrumbs":7,"title":1},"292":{"body":8,"breadcrumbs":7,"title":1},"293":{"body":5,"breadcrumbs":7,"title":1},"294":{"body":26,"breadcrumbs":9,"title":3},"295":{"body":2,"breadcrumbs":8,"title":2},"296":{"body":34,"breadcrumbs":10,"title":4},"297":{"body":48,"breadcrumbs":10,"title":5},"298":{"body":20,"breadcrumbs":6,"title":1},"299":{"body":30,"breadcrumbs":6,"title":1},"3":{"body":243,"breadcrumbs":6,"title":1},"30":{"body":93,"breadcrumbs":9,"title":3},"300":{"body":52,"breadcrumbs":6,"title":1},"301":{"body":73,"breadcrumbs":6,"title":1},"302":{"body":38,"breadcrumbs":6,"title":1},"303":{"body":7,"breadcrumbs":8,"title":3},"304":{"body":1,"breadcrumbs":8,"title":3},"305":{"body":4,"breadcrumbs":8,"title":3},"306":{"body":2,"breadcrumbs":7,"title":2},"307":{"body":4,"breadcrumbs":9,"title":4},"308":{"body":168,"breadcrumbs":10,"title":5},"309":{"body":38,"breadcrumbs":6,"title":1},"31":{"body":0,"breadcrumbs":9,"title":3},"310":{"body":34,"breadcrumbs":7,"title":2},"311":{"body":22,"breadcrumbs":8,"title":3},"312":{"body":23,"breadcrumbs":9,"title":4},"313":{"body":9,"breadcrumbs":7,"title":2},"314":{"body":10,"breadcrumbs":9,"title":4},"315":{"body":9,"breadcrumbs":9,"title":4},"316":{"body":9,"breadcrumbs":7,"title":2},"317":{"body":21,"breadcrumbs":9,"title":4},"318":{"body":67,"breadcrumbs":8,"title":3},"319":{"body":99,"breadcrumbs":8,"title":3},"32":{"body":7,"breadcrumbs":7,"title":1},"320":{"body":11,"breadcrumbs":10,"title":5},"321":{"body":36,"breadcrumbs":8,"title":3},"322":{"body":19,"breadcrumbs":9,"title":4},"323":{"body":17,"breadcrumbs":9,"title":4},"324":{"body":18,"breadcrumbs":9,"title":4},"325":{"body":19,"breadcrumbs":9,"title":4},"326":{"body":68,"breadcrumbs":10,"title":5},"327":{"body":167,"breadcrumbs":9,"title":4},"328":{"body":98,"breadcrumbs":8,"title":3},"329":{"body":117,"breadcrumbs":9,"title":4},"33":{"body":32,"breadcrumbs":7,"title":1},"330":{"body":89,"breadcrumbs":8,"title":3},"331":{"body":130,"breadcrumbs":9,"title":4},"332":{"body":372,"breadcrumbs":9,"title":4},"333":{"body":171,"breadcrumbs":9,"title":4},"334":{"body":100,"breadcrumbs":9,"title":4},"335":{"body":262,"breadcrumbs":8,"title":3},"336":{"body":117,"breadcrumbs":9,"title":4},"337":{"body":43,"breadcrumbs":8,"title":3},"338":{"body":23,"breadcrumbs":8,"title":3},"339":{"body":1,"breadcrumbs":7,"title":2},"34":{"body":9,"breadcrumbs":7,"title":1},"340":{"body":16,"breadcrumbs":9,"title":4},"341":{"body":0,"breadcrumbs":9,"title":4},"342":{"body":31,"breadcrumbs":7,"title":2},"343":{"body":2,"breadcrumbs":7,"title":2},"344":{"body":23,"breadcrumbs":7,"title":2},"345":{"body":28,"breadcrumbs":9,"title":4},"346":{"body":1,"breadcrumbs":8,"title":3},"347":{"body":14,"breadcrumbs":10,"title":5},"348":{"body":43,"breadcrumbs":9,"title":4},"349":{"body":19,"breadcrumbs":8,"title":3},"35":{"body":69,"breadcrumbs":9,"title":3},"350":{"body":30,"breadcrumbs":9,"title":4},"351":{"body":26,"breadcrumbs":9,"title":4},"352":{"body":54,"breadcrumbs":8,"title":4},"353":{"body":22,"breadcrumbs":5,"title":1},"354":{"body":85,"breadcrumbs":5,"title":1},"355":{"body":16,"breadcrumbs":5,"title":1},"356":{"body":42,"breadcrumbs":5,"title":1},"357":{"body":62,"breadcrumbs":5,"title":1},"358":{"body":62,"breadcrumbs":5,"title":1},"359":{"body":127,"breadcrumbs":6,"title":2},"36":{"body":0,"breadcrumbs":8,"title":2},"360":{"body":101,"breadcrumbs":6,"title":2},"361":{"body":324,"breadcrumbs":5,"title":1},"362":{"body":117,"breadcrumbs":5,"title":1},"363":{"body":12,"breadcrumbs":5,"title":1},"364":{"body":13,"breadcrumbs":7,"title":3},"365":{"body":6,"breadcrumbs":7,"title":3},"366":{"body":12,"breadcrumbs":5,"title":1},"367":{"body":35,"breadcrumbs":5,"title":1},"368":{"body":17,"breadcrumbs":5,"title":1},"369":{"body":7,"breadcrumbs":7,"title":3},"37":{"body":10,"breadcrumbs":10,"title":4},"370":{"body":14,"breadcrumbs":6,"title":2},"371":{"body":23,"breadcrumbs":8,"title":4},"372":{"body":49,"breadcrumbs":16,"title":8},"373":{"body":33,"breadcrumbs":9,"title":1},"374":{"body":94,"breadcrumbs":9,"title":1},"375":{"body":6,"breadcrumbs":9,"title":1},"376":{"body":97,"breadcrumbs":9,"title":1},"377":{"body":11,"breadcrumbs":9,"title":1},"378":{"body":4,"breadcrumbs":11,"title":3},"379":{"body":8,"breadcrumbs":11,"title":3},"38":{"body":126,"breadcrumbs":16,"title":8},"380":{"body":4,"breadcrumbs":9,"title":1},"381":{"body":3,"breadcrumbs":9,"title":1},"382":{"body":3,"breadcrumbs":9,"title":1},"383":{"body":12,"breadcrumbs":11,"title":3},"384":{"body":4,"breadcrumbs":10,"title":2},"385":{"body":9,"breadcrumbs":12,"title":4},"386":{"body":42,"breadcrumbs":20,"title":10},"387":{"body":28,"breadcrumbs":11,"title":1},"388":{"body":121,"breadcrumbs":11,"title":1},"389":{"body":15,"breadcrumbs":11,"title":1},"39":{"body":119,"breadcrumbs":9,"title":1},"390":{"body":70,"breadcrumbs":11,"title":1},"391":{"body":0,"breadcrumbs":13,"title":3},"392":{"body":26,"breadcrumbs":11,"title":1},"393":{"body":26,"breadcrumbs":11,"title":1},"394":{"body":7,"breadcrumbs":11,"title":1},"395":{"body":19,"breadcrumbs":13,"title":3},"396":{"body":78,"breadcrumbs":14,"title":7},"397":{"body":37,"breadcrumbs":8,"title":1},"398":{"body":101,"breadcrumbs":8,"title":1},"399":{"body":8,"breadcrumbs":8,"title":1},"4":{"body":8,"breadcrumbs":6,"title":1},"40":{"body":72,"breadcrumbs":9,"title":1},"400":{"body":67,"breadcrumbs":8,"title":1},"401":{"body":98,"breadcrumbs":8,"title":1},"402":{"body":111,"breadcrumbs":13,"title":6},"403":{"body":112,"breadcrumbs":11,"title":4},"404":{"body":154,"breadcrumbs":8,"title":1},"405":{"body":0,"breadcrumbs":10,"title":3},"406":{"body":19,"breadcrumbs":9,"title":2},"407":{"body":0,"breadcrumbs":10,"title":3},"408":{"body":35,"breadcrumbs":8,"title":1},"409":{"body":20,"breadcrumbs":8,"title":1},"41":{"body":17,"breadcrumbs":9,"title":1},"410":{"body":7,"breadcrumbs":8,"title":1},"411":{"body":10,"breadcrumbs":9,"title":2},"412":{"body":26,"breadcrumbs":8,"title":1},"413":{"body":77,"breadcrumbs":12,"title":5},"414":{"body":60,"breadcrumbs":11,"title":4},"415":{"body":87,"breadcrumbs":11,"title":4},"416":{"body":67,"breadcrumbs":12,"title":6},"417":{"body":20,"breadcrumbs":7,"title":1},"418":{"body":66,"breadcrumbs":7,"title":1},"419":{"body":5,"breadcrumbs":7,"title":1},"42":{"body":27,"breadcrumbs":9,"title":1},"420":{"body":0,"breadcrumbs":7,"title":1},"421":{"body":77,"breadcrumbs":9,"title":3},"422":{"body":94,"breadcrumbs":9,"title":3},"423":{"body":82,"breadcrumbs":10,"title":4},"424":{"body":99,"breadcrumbs":9,"title":3},"425":{"body":261,"breadcrumbs":8,"title":2},"426":{"body":172,"breadcrumbs":8,"title":2},"427":{"body":59,"breadcrumbs":7,"title":1},"428":{"body":11,"breadcrumbs":9,"title":3},"429":{"body":0,"breadcrumbs":9,"title":3},"43":{"body":0,"breadcrumbs":11,"title":3},"430":{"body":45,"breadcrumbs":7,"title":1},"431":{"body":1,"breadcrumbs":7,"title":1},"432":{"body":19,"breadcrumbs":7,"title":1},"433":{"body":6,"breadcrumbs":9,"title":3},"434":{"body":1,"breadcrumbs":8,"title":2},"435":{"body":13,"breadcrumbs":10,"title":4},"436":{"body":217,"breadcrumbs":7,"title":1},"437":{"body":51,"breadcrumbs":12,"title":6},"438":{"body":82,"breadcrumbs":7,"title":1},"439":{"body":73,"breadcrumbs":7,"title":1},"44":{"body":123,"breadcrumbs":9,"title":1},"440":{"body":8,"breadcrumbs":7,"title":1},"441":{"body":136,"breadcrumbs":7,"title":1},"442":{"body":21,"breadcrumbs":7,"title":1},"443":{"body":17,"breadcrumbs":9,"title":3},"444":{"body":0,"breadcrumbs":9,"title":3},"445":{"body":39,"breadcrumbs":7,"title":1},"446":{"body":8,"breadcrumbs":7,"title":1},"447":{"body":46,"breadcrumbs":7,"title":1},"448":{"body":1,"breadcrumbs":9,"title":3},"449":{"body":1,"breadcrumbs":8,"title":2},"45":{"body":224,"breadcrumbs":9,"title":1},"450":{"body":3,"breadcrumbs":10,"title":4},"451":{"body":48,"breadcrumbs":8,"title":4},"452":{"body":16,"breadcrumbs":5,"title":1},"453":{"body":70,"breadcrumbs":5,"title":1},"454":{"body":4,"breadcrumbs":5,"title":1},"455":{"body":78,"breadcrumbs":5,"title":1},"456":{"body":92,"breadcrumbs":6,"title":2},"457":{"body":67,"breadcrumbs":5,"title":1},"458":{"body":12,"breadcrumbs":5,"title":1},"459":{"body":13,"breadcrumbs":5,"title":1},"46":{"body":199,"breadcrumbs":13,"title":5},"460":{"body":1,"breadcrumbs":7,"title":3},"461":{"body":0,"breadcrumbs":7,"title":3},"462":{"body":1,"breadcrumbs":5,"title":1},"463":{"body":1,"breadcrumbs":5,"title":1},"464":{"body":1,"breadcrumbs":5,"title":1},"465":{"body":12,"breadcrumbs":7,"title":3},"466":{"body":2,"breadcrumbs":6,"title":2},"467":{"body":51,"breadcrumbs":14,"title":7},"468":{"body":44,"breadcrumbs":8,"title":1},"469":{"body":100,"breadcrumbs":8,"title":1},"47":{"body":211,"breadcrumbs":9,"title":1},"470":{"body":3,"breadcrumbs":8,"title":1},"471":{"body":121,"breadcrumbs":8,"title":1},"472":{"body":33,"breadcrumbs":8,"title":1},"473":{"body":1,"breadcrumbs":10,"title":3},"474":{"body":0,"breadcrumbs":10,"title":3},"475":{"body":1,"breadcrumbs":8,"title":1},"476":{"body":1,"breadcrumbs":8,"title":1},"477":{"body":19,"breadcrumbs":8,"title":1},"478":{"body":1,"breadcrumbs":10,"title":3},"479":{"body":1,"breadcrumbs":9,"title":2},"48":{"body":53,"breadcrumbs":9,"title":1},"480":{"body":4,"breadcrumbs":11,"title":4},"481":{"body":60,"breadcrumbs":16,"title":8},"482":{"body":32,"breadcrumbs":9,"title":1},"483":{"body":98,"breadcrumbs":9,"title":1},"484":{"body":9,"breadcrumbs":9,"title":1},"485":{"body":23,"breadcrumbs":9,"title":1},"486":{"body":232,"breadcrumbs":9,"title":1},"487":{"body":125,"breadcrumbs":11,"title":3},"488":{"body":44,"breadcrumbs":10,"title":2},"489":{"body":65,"breadcrumbs":11,"title":3},"49":{"body":68,"breadcrumbs":9,"title":1},"490":{"body":2,"breadcrumbs":9,"title":1},"491":{"body":94,"breadcrumbs":11,"title":3},"492":{"body":0,"breadcrumbs":11,"title":3},"493":{"body":91,"breadcrumbs":9,"title":1},"494":{"body":1,"breadcrumbs":9,"title":1},"495":{"body":1,"breadcrumbs":9,"title":1},"496":{"body":1,"breadcrumbs":11,"title":3},"497":{"body":21,"breadcrumbs":10,"title":2},"498":{"body":74,"breadcrumbs":12,"title":4},"499":{"body":72,"breadcrumbs":8,"title":4},"5":{"body":124,"breadcrumbs":6,"title":1},"50":{"body":57,"breadcrumbs":11,"title":3},"500":{"body":165,"breadcrumbs":5,"title":1},"501":{"body":189,"breadcrumbs":5,"title":1},"502":{"body":86,"breadcrumbs":5,"title":1},"503":{"body":69,"breadcrumbs":7,"title":3},"504":{"body":29,"breadcrumbs":5,"title":1},"505":{"body":106,"breadcrumbs":5,"title":1},"506":{"body":143,"breadcrumbs":6,"title":2},"507":{"body":222,"breadcrumbs":6,"title":2},"508":{"body":401,"breadcrumbs":6,"title":2},"509":{"body":87,"breadcrumbs":7,"title":3},"51":{"body":79,"breadcrumbs":11,"title":3},"510":{"body":152,"breadcrumbs":6,"title":2},"511":{"body":196,"breadcrumbs":8,"title":4},"512":{"body":130,"breadcrumbs":6,"title":2},"513":{"body":6,"breadcrumbs":5,"title":1},"514":{"body":92,"breadcrumbs":7,"title":3},"515":{"body":0,"breadcrumbs":7,"title":3},"516":{"body":25,"breadcrumbs":5,"title":1},"517":{"body":28,"breadcrumbs":6,"title":2},"518":{"body":48,"breadcrumbs":7,"title":3},"519":{"body":1,"breadcrumbs":6,"title":2},"52":{"body":50,"breadcrumbs":9,"title":1},"520":{"body":68,"breadcrumbs":8,"title":4},"521":{"body":48,"breadcrumbs":12,"title":6},"522":{"body":11,"breadcrumbs":7,"title":1},"523":{"body":166,"breadcrumbs":7,"title":1},"524":{"body":6,"breadcrumbs":7,"title":1},"525":{"body":85,"breadcrumbs":7,"title":1},"526":{"body":18,"breadcrumbs":7,"title":1},"527":{"body":4,"breadcrumbs":9,"title":3},"528":{"body":15,"breadcrumbs":9,"title":3},"529":{"body":2,"breadcrumbs":7,"title":1},"53":{"body":40,"breadcrumbs":11,"title":3},"530":{"body":13,"breadcrumbs":7,"title":1},"531":{"body":16,"breadcrumbs":7,"title":1},"532":{"body":9,"breadcrumbs":9,"title":3},"533":{"body":1,"breadcrumbs":8,"title":2},"534":{"body":13,"breadcrumbs":10,"title":4},"535":{"body":51,"breadcrumbs":16,"title":8},"536":{"body":19,"breadcrumbs":9,"title":1},"537":{"body":85,"breadcrumbs":9,"title":1},"538":{"body":3,"breadcrumbs":9,"title":1},"539":{"body":177,"breadcrumbs":9,"title":1},"54":{"body":92,"breadcrumbs":12,"title":4},"540":{"body":36,"breadcrumbs":9,"title":1},"541":{"body":31,"breadcrumbs":11,"title":3},"542":{"body":1,"breadcrumbs":11,"title":3},"543":{"body":1,"breadcrumbs":9,"title":1},"544":{"body":1,"breadcrumbs":9,"title":1},"545":{"body":42,"breadcrumbs":9,"title":1},"546":{"body":5,"breadcrumbs":11,"title":3},"547":{"body":1,"breadcrumbs":10,"title":2},"548":{"body":1,"breadcrumbs":12,"title":4},"549":{"body":81,"breadcrumbs":8,"title":4},"55":{"body":48,"breadcrumbs":11,"title":3},"550":{"body":183,"breadcrumbs":5,"title":1},"551":{"body":124,"breadcrumbs":5,"title":1},"552":{"body":3,"breadcrumbs":5,"title":1},"553":{"body":231,"breadcrumbs":5,"title":1},"554":{"body":146,"breadcrumbs":5,"title":1},"555":{"body":70,"breadcrumbs":6,"title":2},"556":{"body":63,"breadcrumbs":5,"title":1},"557":{"body":206,"breadcrumbs":6,"title":2},"558":{"body":0,"breadcrumbs":6,"title":2},"559":{"body":219,"breadcrumbs":6,"title":2},"56":{"body":73,"breadcrumbs":10,"title":5},"560":{"body":54,"breadcrumbs":5,"title":1},"561":{"body":110,"breadcrumbs":6,"title":2},"562":{"body":141,"breadcrumbs":6,"title":2},"563":{"body":89,"breadcrumbs":5,"title":1},"564":{"body":1,"breadcrumbs":7,"title":3},"565":{"body":1,"breadcrumbs":7,"title":3},"566":{"body":5,"breadcrumbs":5,"title":1},"567":{"body":12,"breadcrumbs":5,"title":1},"568":{"body":8,"breadcrumbs":5,"title":1},"569":{"body":13,"breadcrumbs":7,"title":3},"57":{"body":27,"breadcrumbs":6,"title":1},"570":{"body":45,"breadcrumbs":12,"title":6},"571":{"body":9,"breadcrumbs":7,"title":1},"572":{"body":75,"breadcrumbs":7,"title":1},"573":{"body":6,"breadcrumbs":7,"title":1},"574":{"body":73,"breadcrumbs":7,"title":1},"575":{"body":7,"breadcrumbs":7,"title":1},"576":{"body":4,"breadcrumbs":9,"title":3},"577":{"body":8,"breadcrumbs":9,"title":3},"578":{"body":2,"breadcrumbs":7,"title":1},"579":{"body":25,"breadcrumbs":7,"title":1},"58":{"body":88,"breadcrumbs":6,"title":1},"580":{"body":20,"breadcrumbs":7,"title":1},"581":{"body":1,"breadcrumbs":9,"title":3},"582":{"body":1,"breadcrumbs":8,"title":2},"583":{"body":1,"breadcrumbs":10,"title":4},"584":{"body":61,"breadcrumbs":12,"title":6},"585":{"body":56,"breadcrumbs":7,"title":1},"586":{"body":187,"breadcrumbs":7,"title":1},"587":{"body":8,"breadcrumbs":7,"title":1},"588":{"body":509,"breadcrumbs":7,"title":1},"589":{"body":222,"breadcrumbs":15,"title":9},"59":{"body":11,"breadcrumbs":6,"title":1},"590":{"body":2,"breadcrumbs":7,"title":1},"591":{"body":61,"breadcrumbs":9,"title":3},"592":{"body":32,"breadcrumbs":9,"title":3},"593":{"body":2,"breadcrumbs":7,"title":1},"594":{"body":21,"breadcrumbs":7,"title":1},"595":{"body":53,"breadcrumbs":7,"title":1},"596":{"body":1,"breadcrumbs":9,"title":3},"597":{"body":1,"breadcrumbs":8,"title":2},"598":{"body":1,"breadcrumbs":10,"title":4},"599":{"body":47,"breadcrumbs":14,"title":7},"6":{"body":331,"breadcrumbs":7,"title":2},"60":{"body":111,"breadcrumbs":6,"title":1},"600":{"body":39,"breadcrumbs":8,"title":1},"601":{"body":90,"breadcrumbs":8,"title":1},"602":{"body":6,"breadcrumbs":8,"title":1},"603":{"body":35,"breadcrumbs":8,"title":1},"604":{"body":8,"breadcrumbs":8,"title":1},"605":{"body":94,"breadcrumbs":10,"title":3},"606":{"body":0,"breadcrumbs":10,"title":3},"607":{"body":2,"breadcrumbs":8,"title":1},"608":{"body":6,"breadcrumbs":8,"title":1},"609":{"body":4,"breadcrumbs":8,"title":1},"61":{"body":49,"breadcrumbs":11,"title":6},"610":{"body":1,"breadcrumbs":10,"title":3},"611":{"body":1,"breadcrumbs":9,"title":2},"612":{"body":1,"breadcrumbs":11,"title":4},"613":{"body":69,"breadcrumbs":18,"title":9},"614":{"body":43,"breadcrumbs":10,"title":1},"615":{"body":93,"breadcrumbs":10,"title":1},"616":{"body":15,"breadcrumbs":10,"title":1},"617":{"body":40,"breadcrumbs":10,"title":1},"618":{"body":74,"breadcrumbs":13,"title":4},"619":{"body":218,"breadcrumbs":11,"title":2},"62":{"body":57,"breadcrumbs":8,"title":3},"620":{"body":164,"breadcrumbs":12,"title":3},"621":{"body":60,"breadcrumbs":11,"title":2},"622":{"body":34,"breadcrumbs":12,"title":3},"623":{"body":39,"breadcrumbs":11,"title":2},"624":{"body":9,"breadcrumbs":10,"title":1},"625":{"body":26,"breadcrumbs":12,"title":3},"626":{"body":46,"breadcrumbs":10,"title":1},"627":{"body":32,"breadcrumbs":10,"title":1},"628":{"body":36,"breadcrumbs":10,"title":1},"629":{"body":28,"breadcrumbs":12,"title":3},"63":{"body":168,"breadcrumbs":8,"title":3},"630":{"body":61,"breadcrumbs":10,"title":1},"631":{"body":20,"breadcrumbs":10,"title":1},"632":{"body":12,"breadcrumbs":12,"title":3},"633":{"body":1,"breadcrumbs":11,"title":2},"634":{"body":39,"breadcrumbs":13,"title":4},"635":{"body":47,"breadcrumbs":12,"title":6},"636":{"body":57,"breadcrumbs":7,"title":1},"637":{"body":77,"breadcrumbs":7,"title":1},"638":{"body":6,"breadcrumbs":7,"title":1},"639":{"body":109,"breadcrumbs":7,"title":1},"64":{"body":62,"breadcrumbs":9,"title":4},"640":{"body":28,"breadcrumbs":7,"title":1},"641":{"body":9,"breadcrumbs":7,"title":1},"642":{"body":8,"breadcrumbs":9,"title":3},"643":{"body":0,"breadcrumbs":9,"title":3},"644":{"body":17,"breadcrumbs":7,"title":1},"645":{"body":21,"breadcrumbs":7,"title":1},"646":{"body":34,"breadcrumbs":7,"title":1},"647":{"body":15,"breadcrumbs":9,"title":3},"648":{"body":1,"breadcrumbs":8,"title":2},"649":{"body":25,"breadcrumbs":10,"title":4},"65":{"body":38,"breadcrumbs":8,"title":3},"650":{"body":46,"breadcrumbs":10,"title":5},"651":{"body":32,"breadcrumbs":6,"title":1},"652":{"body":32,"breadcrumbs":6,"title":1},"653":{"body":4,"breadcrumbs":6,"title":1},"654":{"body":48,"breadcrumbs":6,"title":1},"655":{"body":13,"breadcrumbs":6,"title":1},"656":{"body":33,"breadcrumbs":8,"title":3},"657":{"body":0,"breadcrumbs":8,"title":3},"658":{"body":1,"breadcrumbs":6,"title":1},"659":{"body":35,"breadcrumbs":6,"title":1},"66":{"body":20,"breadcrumbs":8,"title":3},"660":{"body":1,"breadcrumbs":6,"title":1},"661":{"body":15,"breadcrumbs":8,"title":3},"662":{"body":1,"breadcrumbs":7,"title":2},"663":{"body":1,"breadcrumbs":9,"title":4},"664":{"body":44,"breadcrumbs":12,"title":6},"665":{"body":11,"breadcrumbs":7,"title":1},"666":{"body":22,"breadcrumbs":7,"title":1},"667":{"body":4,"breadcrumbs":7,"title":1},"668":{"body":6,"breadcrumbs":7,"title":1},"669":{"body":8,"breadcrumbs":7,"title":1},"67":{"body":49,"breadcrumbs":6,"title":1},"670":{"body":1,"breadcrumbs":9,"title":3},"671":{"body":0,"breadcrumbs":9,"title":3},"672":{"body":1,"breadcrumbs":7,"title":1},"673":{"body":9,"breadcrumbs":7,"title":1},"674":{"body":5,"breadcrumbs":7,"title":1},"675":{"body":7,"breadcrumbs":9,"title":3},"676":{"body":1,"breadcrumbs":8,"title":2},"677":{"body":1,"breadcrumbs":10,"title":4},"678":{"body":62,"breadcrumbs":20,"title":10},"679":{"body":42,"breadcrumbs":11,"title":1},"68":{"body":22,"breadcrumbs":6,"title":1},"680":{"body":88,"breadcrumbs":11,"title":1},"681":{"body":8,"breadcrumbs":11,"title":1},"682":{"body":117,"breadcrumbs":11,"title":1},"683":{"body":213,"breadcrumbs":12,"title":2},"684":{"body":56,"breadcrumbs":14,"title":4},"685":{"body":44,"breadcrumbs":12,"title":2},"686":{"body":68,"breadcrumbs":11,"title":1},"687":{"body":84,"breadcrumbs":13,"title":3},"688":{"body":0,"breadcrumbs":13,"title":3},"689":{"body":1,"breadcrumbs":11,"title":1},"69":{"body":73,"breadcrumbs":8,"title":3},"690":{"body":14,"breadcrumbs":11,"title":1},"691":{"body":107,"breadcrumbs":11,"title":1},"692":{"body":12,"breadcrumbs":13,"title":3},"693":{"body":1,"breadcrumbs":12,"title":2},"694":{"body":0,"breadcrumbs":14,"title":4},"695":{"body":57,"breadcrumbs":8,"title":4},"696":{"body":51,"breadcrumbs":5,"title":1},"697":{"body":145,"breadcrumbs":5,"title":1},"698":{"body":66,"breadcrumbs":5,"title":1},"699":{"body":0,"breadcrumbs":5,"title":1},"7":{"body":50,"breadcrumbs":7,"title":2},"70":{"body":0,"breadcrumbs":8,"title":3},"700":{"body":74,"breadcrumbs":5,"title":1},"701":{"body":125,"breadcrumbs":5,"title":1},"702":{"body":44,"breadcrumbs":5,"title":1},"703":{"body":88,"breadcrumbs":6,"title":2},"704":{"body":25,"breadcrumbs":5,"title":1},"705":{"body":0,"breadcrumbs":5,"title":1},"706":{"body":164,"breadcrumbs":5,"title":1},"707":{"body":252,"breadcrumbs":5,"title":1},"708":{"body":239,"breadcrumbs":6,"title":2},"709":{"body":149,"breadcrumbs":6,"title":2},"71":{"body":68,"breadcrumbs":6,"title":1},"710":{"body":139,"breadcrumbs":9,"title":5},"711":{"body":74,"breadcrumbs":7,"title":3},"712":{"body":1,"breadcrumbs":7,"title":3},"713":{"body":19,"breadcrumbs":6,"title":2},"714":{"body":0,"breadcrumbs":8,"title":4},"715":{"body":67,"breadcrumbs":7,"title":3},"716":{"body":45,"breadcrumbs":16,"title":8},"717":{"body":10,"breadcrumbs":9,"title":1},"718":{"body":156,"breadcrumbs":9,"title":1},"719":{"body":4,"breadcrumbs":9,"title":1},"72":{"body":70,"breadcrumbs":6,"title":1},"720":{"body":0,"breadcrumbs":9,"title":1},"721":{"body":1723,"breadcrumbs":11,"title":3},"722":{"body":52,"breadcrumbs":9,"title":1},"723":{"body":12,"breadcrumbs":9,"title":1},"724":{"body":10,"breadcrumbs":10,"title":2},"725":{"body":71,"breadcrumbs":10,"title":2},"726":{"body":26,"breadcrumbs":10,"title":2},"727":{"body":54,"breadcrumbs":14,"title":7},"728":{"body":68,"breadcrumbs":8,"title":1},"729":{"body":87,"breadcrumbs":8,"title":1},"73":{"body":84,"breadcrumbs":6,"title":1},"730":{"body":59,"breadcrumbs":8,"title":1},"731":{"body":18,"breadcrumbs":8,"title":1},"732":{"body":0,"breadcrumbs":8,"title":1},"733":{"body":64,"breadcrumbs":8,"title":1},"734":{"body":66,"breadcrumbs":8,"title":1},"735":{"body":142,"breadcrumbs":8,"title":1},"736":{"body":19,"breadcrumbs":9,"title":2},"737":{"body":104,"breadcrumbs":9,"title":2},"738":{"body":151,"breadcrumbs":9,"title":2},"739":{"body":2,"breadcrumbs":8,"title":1},"74":{"body":26,"breadcrumbs":8,"title":3},"740":{"body":28,"breadcrumbs":10,"title":3},"741":{"body":7,"breadcrumbs":9,"title":2},"742":{"body":10,"breadcrumbs":8,"title":1},"743":{"body":52,"breadcrumbs":16,"title":8},"744":{"body":16,"breadcrumbs":9,"title":1},"745":{"body":224,"breadcrumbs":9,"title":1},"746":{"body":5,"breadcrumbs":9,"title":1},"747":{"body":482,"breadcrumbs":9,"title":1},"748":{"body":87,"breadcrumbs":9,"title":1},"749":{"body":137,"breadcrumbs":11,"title":3},"75":{"body":68,"breadcrumbs":7,"title":2},"750":{"body":0,"breadcrumbs":11,"title":3},"751":{"body":23,"breadcrumbs":9,"title":1},"752":{"body":1,"breadcrumbs":9,"title":1},"753":{"body":11,"breadcrumbs":9,"title":1},"754":{"body":6,"breadcrumbs":11,"title":3},"755":{"body":1,"breadcrumbs":10,"title":2},"756":{"body":17,"breadcrumbs":12,"title":4},"757":{"body":48,"breadcrumbs":10,"title":5},"758":{"body":65,"breadcrumbs":6,"title":1},"759":{"body":190,"breadcrumbs":6,"title":1},"76":{"body":0,"breadcrumbs":9,"title":4},"760":{"body":25,"breadcrumbs":6,"title":1},"761":{"body":0,"breadcrumbs":6,"title":1},"762":{"body":367,"breadcrumbs":7,"title":2},"763":{"body":218,"breadcrumbs":7,"title":2},"764":{"body":80,"breadcrumbs":8,"title":3},"765":{"body":46,"breadcrumbs":6,"title":1},"766":{"body":23,"breadcrumbs":8,"title":3},"767":{"body":4,"breadcrumbs":7,"title":2},"768":{"body":45,"breadcrumbs":14,"title":7},"769":{"body":22,"breadcrumbs":8,"title":1},"77":{"body":86,"breadcrumbs":7,"title":2},"770":{"body":37,"breadcrumbs":8,"title":1},"771":{"body":2,"breadcrumbs":8,"title":1},"772":{"body":202,"breadcrumbs":8,"title":1},"773":{"body":3,"breadcrumbs":8,"title":1},"774":{"body":26,"breadcrumbs":10,"title":3},"775":{"body":0,"breadcrumbs":10,"title":3},"776":{"body":8,"breadcrumbs":8,"title":1},"777":{"body":6,"breadcrumbs":8,"title":1},"778":{"body":8,"breadcrumbs":8,"title":1},"779":{"body":10,"breadcrumbs":10,"title":3},"78":{"body":158,"breadcrumbs":9,"title":4},"780":{"body":7,"breadcrumbs":9,"title":2},"781":{"body":40,"breadcrumbs":12,"title":6},"782":{"body":61,"breadcrumbs":7,"title":1},"783":{"body":101,"breadcrumbs":7,"title":1},"784":{"body":15,"breadcrumbs":7,"title":1},"785":{"body":187,"breadcrumbs":7,"title":1},"786":{"body":17,"breadcrumbs":7,"title":1},"787":{"body":12,"breadcrumbs":9,"title":3},"788":{"body":0,"breadcrumbs":9,"title":3},"789":{"body":11,"breadcrumbs":7,"title":1},"79":{"body":47,"breadcrumbs":10,"title":5},"790":{"body":40,"breadcrumbs":8,"title":2},"791":{"body":1,"breadcrumbs":9,"title":3},"792":{"body":1,"breadcrumbs":8,"title":2},"793":{"body":39,"breadcrumbs":10,"title":4},"794":{"body":61,"breadcrumbs":12,"title":6},"795":{"body":34,"breadcrumbs":7,"title":1},"796":{"body":92,"breadcrumbs":7,"title":1},"797":{"body":67,"breadcrumbs":7,"title":1},"798":{"body":4,"breadcrumbs":7,"title":1},"799":{"body":77,"breadcrumbs":7,"title":1},"8":{"body":32,"breadcrumbs":6,"title":1},"80":{"body":37,"breadcrumbs":6,"title":1},"800":{"body":237,"breadcrumbs":9,"title":3},"801":{"body":124,"breadcrumbs":9,"title":3},"802":{"body":41,"breadcrumbs":9,"title":3},"803":{"body":106,"breadcrumbs":10,"title":4},"804":{"body":51,"breadcrumbs":7,"title":1},"805":{"body":27,"breadcrumbs":9,"title":3},"806":{"body":0,"breadcrumbs":9,"title":3},"807":{"body":4,"breadcrumbs":7,"title":1},"808":{"body":13,"breadcrumbs":7,"title":1},"809":{"body":3,"breadcrumbs":7,"title":1},"81":{"body":177,"breadcrumbs":6,"title":1},"810":{"body":5,"breadcrumbs":9,"title":3},"811":{"body":2,"breadcrumbs":8,"title":2},"812":{"body":37,"breadcrumbs":10,"title":4},"813":{"body":49,"breadcrumbs":14,"title":7},"814":{"body":14,"breadcrumbs":8,"title":1},"815":{"body":113,"breadcrumbs":8,"title":1},"816":{"body":6,"breadcrumbs":8,"title":1},"817":{"body":180,"breadcrumbs":8,"title":1},"818":{"body":91,"breadcrumbs":8,"title":1},"819":{"body":25,"breadcrumbs":10,"title":3},"82":{"body":8,"breadcrumbs":6,"title":1},"820":{"body":0,"breadcrumbs":10,"title":3},"821":{"body":44,"breadcrumbs":8,"title":1},"822":{"body":13,"breadcrumbs":8,"title":1},"823":{"body":31,"breadcrumbs":8,"title":1},"824":{"body":1,"breadcrumbs":10,"title":3},"825":{"body":1,"breadcrumbs":9,"title":2},"826":{"body":12,"breadcrumbs":11,"title":4},"827":{"body":60,"breadcrumbs":10,"title":5},"828":{"body":55,"breadcrumbs":6,"title":1},"829":{"body":103,"breadcrumbs":6,"title":1},"83":{"body":223,"breadcrumbs":6,"title":1},"830":{"body":28,"breadcrumbs":6,"title":1},"831":{"body":7,"breadcrumbs":6,"title":1},"832":{"body":125,"breadcrumbs":9,"title":4},"833":{"body":83,"breadcrumbs":13,"title":8},"834":{"body":149,"breadcrumbs":10,"title":5},"835":{"body":148,"breadcrumbs":6,"title":1},"836":{"body":52,"breadcrumbs":8,"title":3},"837":{"body":0,"breadcrumbs":8,"title":3},"838":{"body":61,"breadcrumbs":6,"title":1},"839":{"body":22,"breadcrumbs":6,"title":1},"84":{"body":128,"breadcrumbs":6,"title":1},"840":{"body":6,"breadcrumbs":6,"title":1},"841":{"body":38,"breadcrumbs":6,"title":1},"842":{"body":11,"breadcrumbs":7,"title":2},"843":{"body":50,"breadcrumbs":12,"title":6},"844":{"body":37,"breadcrumbs":7,"title":1},"845":{"body":18,"breadcrumbs":7,"title":1},"846":{"body":42,"breadcrumbs":7,"title":1},"847":{"body":29,"breadcrumbs":10,"title":4},"848":{"body":29,"breadcrumbs":10,"title":4},"849":{"body":43,"breadcrumbs":7,"title":1},"85":{"body":86,"breadcrumbs":8,"title":3},"850":{"body":10,"breadcrumbs":9,"title":3},"851":{"body":0,"breadcrumbs":9,"title":3},"852":{"body":3,"breadcrumbs":7,"title":1},"853":{"body":7,"breadcrumbs":7,"title":1},"854":{"body":2,"breadcrumbs":7,"title":1},"855":{"body":14,"breadcrumbs":9,"title":3},"856":{"body":21,"breadcrumbs":8,"title":2},"857":{"body":58,"breadcrumbs":10,"title":5},"858":{"body":77,"breadcrumbs":6,"title":1},"859":{"body":0,"breadcrumbs":6,"title":1},"86":{"body":0,"breadcrumbs":8,"title":3},"860":{"body":185,"breadcrumbs":6,"title":1},"861":{"body":60,"breadcrumbs":6,"title":1},"862":{"body":63,"breadcrumbs":7,"title":2},"863":{"body":4,"breadcrumbs":6,"title":1},"864":{"body":121,"breadcrumbs":6,"title":1},"865":{"body":865,"breadcrumbs":8,"title":3},"866":{"body":224,"breadcrumbs":6,"title":1},"867":{"body":139,"breadcrumbs":8,"title":3},"868":{"body":3,"breadcrumbs":6,"title":1},"869":{"body":4,"breadcrumbs":8,"title":3},"87":{"body":14,"breadcrumbs":6,"title":1},"870":{"body":0,"breadcrumbs":8,"title":3},"871":{"body":243,"breadcrumbs":6,"title":1},"872":{"body":11,"breadcrumbs":6,"title":1},"873":{"body":14,"breadcrumbs":6,"title":1},"874":{"body":4,"breadcrumbs":8,"title":3},"875":{"body":14,"breadcrumbs":7,"title":2},"876":{"body":23,"breadcrumbs":9,"title":4},"877":{"body":59,"breadcrumbs":22,"title":11},"878":{"body":13,"breadcrumbs":12,"title":1},"879":{"body":0,"breadcrumbs":12,"title":1},"88":{"body":13,"breadcrumbs":6,"title":1},"880":{"body":37,"breadcrumbs":12,"title":1},"881":{"body":150,"breadcrumbs":12,"title":1},"882":{"body":19,"breadcrumbs":13,"title":2},"883":{"body":18,"breadcrumbs":12,"title":1},"884":{"body":73,"breadcrumbs":12,"title":1},"885":{"body":2,"breadcrumbs":12,"title":1},"886":{"body":18,"breadcrumbs":14,"title":3},"887":{"body":0,"breadcrumbs":14,"title":3},"888":{"body":25,"breadcrumbs":12,"title":1},"889":{"body":4,"breadcrumbs":12,"title":1},"89":{"body":1,"breadcrumbs":6,"title":1},"890":{"body":8,"breadcrumbs":12,"title":1},"891":{"body":3,"breadcrumbs":14,"title":3},"892":{"body":3,"breadcrumbs":13,"title":2},"893":{"body":12,"breadcrumbs":15,"title":4},"894":{"body":67,"breadcrumbs":28,"title":14},"895":{"body":36,"breadcrumbs":15,"title":1},"896":{"body":0,"breadcrumbs":15,"title":1},"897":{"body":49,"breadcrumbs":15,"title":1},"898":{"body":226,"breadcrumbs":15,"title":1},"899":{"body":115,"breadcrumbs":16,"title":2},"9":{"body":18,"breadcrumbs":8,"title":3},"90":{"body":1,"breadcrumbs":8,"title":3},"900":{"body":19,"breadcrumbs":15,"title":1},"901":{"body":0,"breadcrumbs":15,"title":1},"902":{"body":13,"breadcrumbs":15,"title":1},"903":{"body":46,"breadcrumbs":17,"title":3},"904":{"body":0,"breadcrumbs":17,"title":3},"905":{"body":53,"breadcrumbs":15,"title":1},"906":{"body":9,"breadcrumbs":15,"title":1},"907":{"body":8,"breadcrumbs":15,"title":1},"908":{"body":0,"breadcrumbs":17,"title":3},"909":{"body":2,"breadcrumbs":16,"title":2},"91":{"body":1,"breadcrumbs":7,"title":2},"910":{"body":1,"breadcrumbs":16,"title":2},"911":{"body":1,"breadcrumbs":18,"title":4},"912":{"body":52,"breadcrumbs":8,"title":4},"913":{"body":37,"breadcrumbs":5,"title":1},"914":{"body":184,"breadcrumbs":5,"title":1},"915":{"body":42,"breadcrumbs":5,"title":1},"916":{"body":0,"breadcrumbs":5,"title":1},"917":{"body":99,"breadcrumbs":6,"title":2},"918":{"body":287,"breadcrumbs":6,"title":2},"919":{"body":161,"breadcrumbs":6,"title":2},"92":{"body":6,"breadcrumbs":9,"title":4},"920":{"body":80,"breadcrumbs":5,"title":1},"921":{"body":20,"breadcrumbs":7,"title":3},"922":{"body":43,"breadcrumbs":7,"title":3},"923":{"body":12,"breadcrumbs":7,"title":3},"924":{"body":59,"breadcrumbs":6,"title":2},"925":{"body":31,"breadcrumbs":8,"title":4},"926":{"body":51,"breadcrumbs":10,"title":5},"927":{"body":29,"breadcrumbs":6,"title":1},"928":{"body":92,"breadcrumbs":6,"title":1},"929":{"body":21,"breadcrumbs":6,"title":1},"93":{"body":50,"breadcrumbs":24,"title":12},"930":{"body":92,"breadcrumbs":6,"title":1},"931":{"body":55,"breadcrumbs":6,"title":1},"932":{"body":0,"breadcrumbs":8,"title":3},"933":{"body":26,"breadcrumbs":6,"title":1},"934":{"body":16,"breadcrumbs":6,"title":1},"935":{"body":12,"breadcrumbs":6,"title":1},"936":{"body":0,"breadcrumbs":8,"title":3},"937":{"body":20,"breadcrumbs":6,"title":1},"938":{"body":18,"breadcrumbs":6,"title":1},"939":{"body":16,"breadcrumbs":6,"title":1},"94":{"body":43,"breadcrumbs":13,"title":1},"940":{"body":5,"breadcrumbs":8,"title":3},"941":{"body":9,"breadcrumbs":7,"title":2},"942":{"body":37,"breadcrumbs":9,"title":4},"943":{"body":51,"breadcrumbs":12,"title":6},"944":{"body":17,"breadcrumbs":7,"title":1},"945":{"body":71,"breadcrumbs":7,"title":1},"946":{"body":24,"breadcrumbs":7,"title":1},"947":{"body":90,"breadcrumbs":7,"title":1},"948":{"body":40,"breadcrumbs":7,"title":1},"949":{"body":0,"breadcrumbs":9,"title":3},"95":{"body":181,"breadcrumbs":13,"title":1},"950":{"body":22,"breadcrumbs":7,"title":1},"951":{"body":23,"breadcrumbs":7,"title":1},"952":{"body":10,"breadcrumbs":7,"title":1},"953":{"body":0,"breadcrumbs":9,"title":3},"954":{"body":22,"breadcrumbs":7,"title":1},"955":{"body":19,"breadcrumbs":7,"title":1},"956":{"body":15,"breadcrumbs":7,"title":1},"957":{"body":34,"breadcrumbs":9,"title":3},"958":{"body":24,"breadcrumbs":8,"title":2},"959":{"body":62,"breadcrumbs":10,"title":4},"96":{"body":2,"breadcrumbs":13,"title":1},"960":{"body":47,"breadcrumbs":12,"title":6},"961":{"body":26,"breadcrumbs":7,"title":1},"962":{"body":31,"breadcrumbs":7,"title":1},"963":{"body":6,"breadcrumbs":7,"title":1},"964":{"body":7,"breadcrumbs":7,"title":1},"965":{"body":20,"breadcrumbs":7,"title":1},"966":{"body":9,"breadcrumbs":9,"title":3},"967":{"body":0,"breadcrumbs":9,"title":3},"968":{"body":5,"breadcrumbs":7,"title":1},"969":{"body":31,"breadcrumbs":7,"title":1},"97":{"body":40,"breadcrumbs":13,"title":1},"970":{"body":21,"breadcrumbs":7,"title":1},"971":{"body":15,"breadcrumbs":9,"title":3},"972":{"body":1,"breadcrumbs":8,"title":2},"973":{"body":15,"breadcrumbs":10,"title":4},"974":{"body":54,"breadcrumbs":16,"title":8},"975":{"body":14,"breadcrumbs":9,"title":1},"976":{"body":51,"breadcrumbs":9,"title":1},"977":{"body":15,"breadcrumbs":9,"title":1},"978":{"body":54,"breadcrumbs":9,"title":1},"979":{"body":2,"breadcrumbs":9,"title":1},"98":{"body":1,"breadcrumbs":13,"title":1},"980":{"body":20,"breadcrumbs":11,"title":3},"981":{"body":0,"breadcrumbs":11,"title":3},"982":{"body":52,"breadcrumbs":9,"title":1},"983":{"body":1,"breadcrumbs":9,"title":1},"984":{"body":3,"breadcrumbs":9,"title":1},"985":{"body":1,"breadcrumbs":11,"title":3},"986":{"body":1,"breadcrumbs":10,"title":2},"987":{"body":1,"breadcrumbs":12,"title":4},"988":{"body":53,"breadcrumbs":12,"title":6},"989":{"body":22,"breadcrumbs":7,"title":1},"99":{"body":0,"breadcrumbs":15,"title":3},"990":{"body":124,"breadcrumbs":7,"title":1},"991":{"body":38,"breadcrumbs":7,"title":1},"992":{"body":301,"breadcrumbs":7,"title":1},"993":{"body":40,"breadcrumbs":7,"title":1},"994":{"body":30,"breadcrumbs":9,"title":3},"995":{"body":0,"breadcrumbs":9,"title":3},"996":{"body":16,"breadcrumbs":7,"title":1},"997":{"body":18,"breadcrumbs":7,"title":1},"998":{"body":33,"breadcrumbs":7,"title":1},"999":{"body":15,"breadcrumbs":9,"title":3}},"docs":{"0":{"body":"This book contains the Polkadot Fellowship Requests for Comments (RFCs) detailing proposed changes to the technical implementation of the Polkadot network. polkadot-fellows/RFCs","breadcrumbs":"Introduction » Introduction","id":"0","title":"Introduction"},"1":{"body":"(source) Table of Contents RFC-0125: XCM Asset Metadata Summary Motivation Stakeholders Explanation New instructions Repurposing AssetInstance::Undefined Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 22 Oct 2024 Description XCM Asset Metadata definition and a way of communicating it via XCM Authors Daniel Shiposha","breadcrumbs":"RFC-0125: XCM Asset Metadata » RFC-0125: XCM Asset Metadata","id":"1","title":"RFC-0125: XCM Asset Metadata"},"10":{"body":"","breadcrumbs":"RFC-0125: XCM Asset Metadata » Performance, Ergonomics, and Compatibility","id":"10","title":"Performance, Ergonomics, and Compatibility"},"100":{"body":"The changes are not directly affecting the protocol security, parachains are not enforced to use the host function.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Security","id":"100","title":"Security"},"1000":{"body":"How to determine in a statistically meaningful way that a change in the poll status corresponds to an organic behaviour, and not an unwanted, malicious behaviour?","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Unresolved Questions","id":"1000","title":"Unresolved Questions"},"1001":{"body":"A proposed implementation of this change can be seen on this Pull Request .","breadcrumbs":"RFC-0120: Referenda Confirmation by Candle Mechanism » Future Directions and Related Material","id":"1001","title":"Future Directions and Related Material"},"1002":{"body":"(source) Table of Contents RFC-TODO: Stale Nomination Reward Curve Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 10 July 2024 Description Introduce a decaying reward curve for stale nominations in staking. Authors Shawn Tabrizi","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » RFC-TODO: Stale Nomination Reward Curve","id":"1002","title":"RFC-TODO: Stale Nomination Reward Curve"},"1003":{"body":"This is a proposal to reduce the impact of stale nominations in the Polkadot staking system. With this proposal, nominators are incentivized to update or renew their selected validators once per time period. Nominators that do not update or renew their selected validators would be considered stale, and a decaying multiplier would be applied to their nominations, reducing the weight of their nomination and rewards.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Summary","id":"1003","title":"Summary"},"1004":{"body":"Longer motivation behind the content of the RFC, presented as a combination of both problems and requirements for the solution. One of Polkadot's primary utilities is providing a high quality security layer for applications built on top of it. To achieve this, Polkadot runs a Nominated Proof-of-Stake system, allowing nominators to vote on who they think are the best validators for Polkadot. This system functions best when nominators and validators are active participants in the network. Nominators should consistently evaluate the quality and preferences of validators, and adjust their nominations accordingly. Unfortunately, many Polkadot nominators do not play an active role in the NPoS system. For many, they set their nominations, and then seldomly look back at the. This can lead to many negative behaviors: Incumbents who received early nominations basically achieve tenure. Validator quality and performance can decrease without recourse. The validator set are not the optimal for Polkadot. New validators have a harder time entering the active set. Validators are able to \"sneakily\" increase their commission.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Motivation","id":"1004","title":"Motivation"},"1005":{"body":"Primary stakeholders are: Nominators Validators","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Stakeholders","id":"1005","title":"Stakeholders"},"1006":{"body":"Detail-heavy explanation of the RFC, suitable for explanation to an implementer of the changeset. This should address corner cases in detail and provide justification behind decisions, and provide rationale for how the design meets the solution requirements.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Explanation","id":"1006","title":"Explanation"},"1007":{"body":"Description of recognized drawbacks to the approach given in the RFC. Non-exhaustively, drawbacks relating to performance, ergonomics, user experience, security, or privacy.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Drawbacks","id":"1007","title":"Drawbacks"},"1008":{"body":"Describe the the impact of the proposal on these three high-importance areas - how implementations can be tested for adherence, effects that the proposal has on security and privacy per-se, as well as any possible implementation pitfalls which should be clearly avoided.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Testing, Security, and Privacy","id":"1008","title":"Testing, Security, and Privacy"},"1009":{"body":"Describe the impact of the proposal on the exposed functionality of Polkadot.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Performance, Ergonomics, and Compatibility","id":"1009","title":"Performance, Ergonomics, and Compatibility"},"101":{"body":"","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Performance, Ergonomics, and Compatibility","id":"101","title":"Performance, Ergonomics, and Compatibility"},"1010":{"body":"Is this an optimization or a necessary pessimization? What steps have been taken to minimize additional overhead?","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Performance","id":"1010","title":"Performance"},"1011":{"body":"If the proposal alters exposed interfaces to developers or end-users, which types of usage patterns have been optimized for?","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Ergonomics","id":"1011","title":"Ergonomics"},"1012":{"body":"Does this proposal break compatibility with existing interfaces, older versions of implementations? Summarize necessary migrations or upgrade strategies, if any.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Compatibility","id":"1012","title":"Compatibility"},"1013":{"body":"Provide references to either prior art or other relevant research for the submitted design.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Prior Art and References","id":"1013","title":"Prior Art and References"},"1014":{"body":"Provide specific questions to discuss and address before the RFC is voted on by the Fellowship. This should include, for example, alternatives to aspects of the proposed design where the appropriate trade-off to make is unclear.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Unresolved Questions","id":"1014","title":"Unresolved Questions"},"1015":{"body":"Describe future work which could be enabled by this RFC, if it were accepted, as well as related RFCs. This is a place to brain-dump and explore possibilities, which themselves may become their own RFCs.","breadcrumbs":"RFC-TODO: Stale Nomination Reward Curve » Future Directions and Related Material","id":"1015","title":"Future Directions and Related Material"},"102":{"body":"N/A","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Performance","id":"102","title":"Performance"},"103":{"body":"The host function proposed in this RFC allows parachain runtime developers to use a more efficient verification mechanism for \"secp256r1\" elliptic curve signatures.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Ergonomics","id":"103","title":"Ergonomics"},"104":{"body":"Parachain teams will need to include this host function to upgrade.","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Compatibility","id":"104","title":"Compatibility"},"105":{"body":"Pull Request including RIP-7212 in Moonbeam: Add secp256r1 precompile . Pull Request including proposed host function: IN PROGRESS .","breadcrumbs":"RFC-0114: Introduce secp256r1_ecdsa_verify_prehashed Host Function to verify NIST-P256 elliptic curve signatures » Prior Art and References","id":"105","title":"Prior Art and References"},"106":{"body":"(source) Table of Contents RFC-0117: The Unbrick Collective Summary Motivation Stakeholders Explanation The Collective The Unbrick Process Belonging to the Collective Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 22 August 2024 Description The Unbrick Collective aims to help teams rescuing a para once it stops producing blocks Authors Bryan Chen, Pablo Dorado","breadcrumbs":"RFC-0117: The Unbrick Collective » RFC-0117: The Unbrick Collective","id":"106","title":"RFC-0117: The Unbrick Collective"},"107":{"body":"A followup of the RFC-0014 . This RFC proposes adding a new collective to the Polkadot Collectives Chain: The Unbrick Collective, as well as improvements in the mechanisms that will allow teams operating paras that had stopped producing blocks to be assisted, in order to restore the production of blocks of these paras.","breadcrumbs":"RFC-0117: The Unbrick Collective » Summary","id":"107","title":"Summary"},"108":{"body":"Since the initial launch of Polkadot parachains, there has been many incidients causing parachains to stop producing new blocks (therefore, being bricked ) and many occurrences that required Polkadot governance to update the parachain head state/wasm. This can be due to many reasons range from incorrectly registering the initial head state, inability to use sudo key, bad runtime migration, bad weight configuration, and bugs in the development of the Polkadot SDK. Currently, when the para is not unlocked in the paras registrar [1] , the Root origin is required to perform such actions, involving the governance process to invoke this origin, which can be very resource expensive for the teams. The long voting and enactment times also could result significant damage to the parachain and users. Finally, other instances of governance that might enact a call using the Root origin (like the Polkadot Fellowship), due to the nature of their mission, are not fit to carry these kind of tasks. In consequence, the idea of a Unbrick Collective that can provide assistance to para teams when they brick and further protection against future halts is reasonable enough.","breadcrumbs":"RFC-0117: The Unbrick Collective » Motivation","id":"108","title":"Motivation"},"109":{"body":"Parachain teams Parachain users OpenGov users Polkadot Fellowship","breadcrumbs":"RFC-0117: The Unbrick Collective » Stakeholders","id":"109","title":"Stakeholders"},"11":{"body":"No significant impact.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Performance","id":"11","title":"Performance"},"110":{"body":"","breadcrumbs":"RFC-0117: The Unbrick Collective » Explanation","id":"110","title":"Explanation"},"111":{"body":"The Unbrick Collective is defined as an unranked collective of members, not paid by the Polkadot Treasury. Its main goal is to serve as a point of contact and assistance for enacting the actions needed to unbrick a para. Such actions are: Updating the Parachain Verification Function (a.k.a. a new WASM) of a para. Updating the head state of a para. A combination of the above. In order to ensure these changes are safe enough for the network, actions enacted by the Unbrick Collective must be whitelisted via similar mechanisms followed by collectives like the Polkadot Fellowship. This will prevent unintended, not overseen changes on other paras to occur. Also, teams might opt-in to delegate handling their para in the registry to the Collective. This allows to perform similar actions using the paras registrar , allowing for a shorter path to unbrick a para. Initially, the unbrick collective has powers similar to a parachains own sudo, but permits more decentralized control. In the future, Polkadot shall provide functionality like SPREE or JAM that exceeds sudo permissions, so the unbrick collective cannot modify those state roots or code.","breadcrumbs":"RFC-0117: The Unbrick Collective » The Collective","id":"111","title":"The Collective"},"112":{"body":"flowchart TD A[Start] A -- Bricked --> C[Request para unlock via Root] C -- Approved --> Y C -- Rejected --> A D[unbrick call proposal on WhitelistedUnbrickCaller] E[whitelist call proposal on the Unbrick governance] E -- call whitelisted --> F[unbrick call enacted] D -- unbrick called --> F F --> Y A -- Not bricked --> O[Opt-in to the Collective] O -- Bricked --> D O -- Bricked --> E Y[update PVF / head state] -- Unbricked --> Z[End] Initially, a para team has two paths to handle a potential unbrick of their para in the case it stops producing blocks. Opt-in to the Unbrick Collective : This is done by delegating the handling of the para in the paras registrar to an origin related to the Collective. This doesn't require unlocking the para. This way, the collective is enabled to perform changes in the paras module, after the Unbrick Process proceeds. Request a Para Unlock : In case the para hasn't delegated its handling in the paras registrar , it'll be still possible for the para team to submit a proposal to unlock the para, which can be assisted by the Collective. However, this involves submitting a proposal to the Root governance origin.","breadcrumbs":"RFC-0117: The Unbrick Collective » The Unbrick Process","id":"112","title":"The Unbrick Process"},"113":{"body":"The collective will be initially created without members (no seeding). There will be additional governance proposals to setup the seed members. The origins able to modify the members of the collective are: The Fellows track in the Polkadot Fellowship. Root track in the Relay. More than two thirds of the existing Unbrick Collective. The members are responsible to verify the technical details of the unbrick requests (i.e. the hash of the new PVF being set). Therefore, they must have the technical capacity to perform such tasks. Suggested requirements to become a member are the following: Rank 3 or above in the Polkadot Fellowship. Being a CTO or Technical Lead in a para team that has opted-in to delegate the Unbrick Collective to manage the PVF/head state of the para.","breadcrumbs":"RFC-0117: The Unbrick Collective » Belonging to the Collective","id":"113","title":"Belonging to the Collective"},"114":{"body":"The ability to modify the Head State and/or the PVF of a para means a possibility to perform arbitrary modifications of it (i.e. take control the native parachain token or any bridged assets in the para). This could introduce a new attack vector, and therefore, such great power needs to be handled carefully.","breadcrumbs":"RFC-0117: The Unbrick Collective » Drawbacks","id":"114","title":"Drawbacks"},"115":{"body":"The implementation of this RFC will be tested on testnets (Rococo and Westend) first. An audit will be required to ensure the implementation doesn't introduce unwanted side effects. There are no privacy related concerns.","breadcrumbs":"RFC-0117: The Unbrick Collective » Testing, Security, and Privacy","id":"115","title":"Testing, Security, and Privacy"},"116":{"body":"","breadcrumbs":"RFC-0117: The Unbrick Collective » Performance, Ergonomics, and Compatibility","id":"116","title":"Performance, Ergonomics, and Compatibility"},"117":{"body":"This RFC should not introduce any performance impact.","breadcrumbs":"RFC-0117: The Unbrick Collective » Performance","id":"117","title":"Performance"},"118":{"body":"This RFC should improve the experience for new and existing parachain teams, lowering the barrier to unbrick a stalled para.","breadcrumbs":"RFC-0117: The Unbrick Collective » Ergonomics","id":"118","title":"Ergonomics"},"119":{"body":"This RFC is fully compatible with existing interfaces.","breadcrumbs":"RFC-0117: The Unbrick Collective » Compatibility","id":"119","title":"Compatibility"},"12":{"body":"Introducing a standard metadata format and a way of communicating it is a valuable addition to the XCM format that potentially increases cross-chain interoperability without the need to form ad-hoc chain-to-chain integrations via Transact.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Ergonomics","id":"12","title":"Ergonomics"},"120":{"body":"RFC-0014: Improve Locking Mechanisms for Parachains How to Recover a Parachain, Polkadot Forum Unbrick Collective, Polkadot Forum","breadcrumbs":"RFC-0117: The Unbrick Collective » Prior Art and References","id":"120","title":"Prior Art and References"},"121":{"body":"What are the parameters for the WhitelistedUnbrickCaller track? Any other methods that shall be updated to accept Unbrick origin? Any other requirements to become a member? We would like to keep this simple, so no funding support from the Polkadot treasury. But do we want to compensate the members somehow? i.e. Allow parachain teams to donate to the collective. We hope SPREE/JAM would be carefully audited for miss-use risks before being provided to parachain teams, but could the unbrick collective have an elections that warranted trust beyond sudo powers? An auditing framework/collective makes sense parachain code upgrades, but could also strengthen the unbrick collective. Do we want to have this collective offer additional technical support to help bricked parachains? i.e. help debug the code, create the rescue plan, create postmortem report, provide resources on how to avoid getting bricked The paras registrar refers to a pallet in the Relay, responsible to gather registration info of the paras, the locked/unlocked state, and the manager info.","breadcrumbs":"RFC-0117: The Unbrick Collective » Unresolved Questions","id":"121","title":"Unresolved Questions"},"122":{"body":"(source) Table of Contents RFC-0121: Iterable Referenda Tracks Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 17 September 2024 Description Allow dynamic modifications of referenda tracks at runtime without the need for a full runtime upgrade. Authors Pablo Dorado, Daniel Olano","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » RFC-0121: Iterable Referenda Tracks","id":"122","title":"RFC-0121: Iterable Referenda Tracks"},"123":{"body":"The protocol change introduces flexibility in the governance structure by enabling the referenda track list to be modified dynamically at runtime. This is achieved by replacing static slices in TracksInfo with iterators, facilitating storage-based track management. As a result, governance tracks can be modified or added based on real-time decisions and without requiring runtime upgrades.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Summary","id":"123","title":"Summary"},"124":{"body":"Polkadot's governance system is designed to be adaptive and decentralized, but modifying the referenda tracks (which determine decision-making paths for proposals) has historically required runtime upgrades. This poses an operational challenge, delaying governance changes until an upgrade is scheduled and executed. The new system provides the flexibility needed to adjust tracks dynamically, reflecting real-time changes in governance needs without the latency and risks associated with runtime upgrades. This reduces governance bottlenecks and allows for quicker adaptation to emergent scenarios.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Motivation","id":"124","title":"Motivation"},"125":{"body":"Network stakeholders : the change means reduced coordination effort for track adjustments. Governance participants : this enables more responsive decision-making pathways.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Stakeholders","id":"125","title":"Stakeholders"},"126":{"body":"The protocol modification replaces the current static slice method used for storing referenda tracks with an iterator-based approach that allows tracks to be managed dynamically using chain storage. Governance participants can define and modify referenda tracks as needed, which are then accessed through runtime rather than being hardcoded in the protocol. This system ensures that tracks are adjustable at any time, reducing upgrade-related complexities and introducing agility in how governance tracks are applied. This modification does not disrupt existing governance mechanisms but rather enhances them by increasing adaptability. In terms of technical structure, TracksInfo::tracks will now return iterators, making it possible to alter track configurations based on storage data rather than static definitions. This opens up possibilities for new track types and governance configurations to be deployed without the need for upgrades that might take up weeks.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Explanation","id":"126","title":"Explanation"},"127":{"body":"The most significant drawback is the increased complexity for developers managing track configurations via storage-based iterators, which require careful handling to avoid misuse or inefficiencies. Additionally, this flexibility could introduce risks if track configurations are modified improperly during runtime, potentially leading to governance instabilities.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Drawbacks","id":"127","title":"Drawbacks"},"128":{"body":"To ensure security, the change must be tested in testnet environments first (Paseo, Westend), particularly in scenarios where multiple track changes happen concurrently. Potential vulnerabilities in governance adjustments must be addressed to prevent abuse. The proposal doesn't introduce privacy risks but increases the need for ensuring that any runtime changes do not inadvertently lead to insecure governance structures. Comprehensive tests should be conducted to validate correct track modifications in different governance scenarios.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Testing, Security, and Privacy","id":"128","title":"Testing, Security, and Privacy"},"129":{"body":"","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Performance, Ergonomics, and Compatibility","id":"129","title":"Performance, Ergonomics, and Compatibility"},"13":{"body":"This RFC proposes new functionality, so there are no compatibility issues.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Compatibility","id":"13","title":"Compatibility"},"130":{"body":"The proposal optimizes governance track management by avoiding the overhead of runtime upgrades, reducing downtime, and eliminating the need for full consensus on upgrades. However, there is a slight performance cost related to runtime access to storage-based iterators, though this is mitigated by the overall system efficiency gains.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Performance","id":"130","title":"Performance"},"131":{"body":"Developers and governance actors benefit from simplified governance processes but must account for the technical complexity of managing iterator-based track configurations. Tools may need to be developed to help streamline track adjustments in runtime.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Ergonomics","id":"131","title":"Ergonomics"},"132":{"body":"The change is backward compatible with existing governance operations, and does not require developers to adjust how they interact with referenda tracks. A migration is required to convert existing statically-defined tracks to dynamic storage-based configurations without disruption.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Compatibility","id":"132","title":"Compatibility"},"133":{"body":"This dynamic governance track approach builds on previous work around Polkadot's on-chain governance and leverages standard iterator patterns in Rust programming to improve runtime flexibility. Comparable solutions in other governance networks were examined, but this proposal uniquely tailors them to Polkadot’s decentralized, runtime-upgradable architecture.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Prior Art and References","id":"133","title":"Prior Art and References"},"134":{"body":"How to handle governance transitions for currently ongoing referenda when changing configuration parameters of an existing track? Ideally, most tracks should not have to go through this change, but some tactics might be applied (like a proposal that reduces the ongoing queue before a major change and then executes the change, after a reasonable period of time has elapsed and no ongoing referenda exists for that track).","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Unresolved Questions","id":"134","title":"Unresolved Questions"},"135":{"body":"There are already two proposed solutions for both the implementation and This Pull Request proposes changing pallet-referenda's TracksInfo to make tracks return an iterator. There is already a proposed implementation of pallet-referenda-tracks , which stores the configurations, and implements TracksInfo using the iterator approach.","breadcrumbs":"RFC-0121: Iterable Referenda Tracks » Future Directions and Related Material","id":"135","title":"Future Directions and Related Material"},"136":{"body":"(source) Table of Contents RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 14.10.2024 Description Store a runtime upgrade in :pending_code before moving it to :code. Authors Bastian Köcher","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code","id":"136","title":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code"},"137":{"body":"The code of a runtime is stored in its own state, and when performing a runtime upgrade, this code is replaced. The new runtime can contain runtime migrations that adapt the state to the state layout as defined by the runtime code. This runtime migration is executed when building the first block with the new runtime code. Anything that interacts with the runtime state uses the state layout as defined by the runtime code. So, when trying to load something from the state in the block that applied the runtime upgrade, it will use the new state layout but will decode the data from the non-migrated state. In the worst case, the data is incorrectly decoded, which may lead to crashes or halting of the chain. This RFC proposes to store the new runtime code under a different storage key when applying a runtime upgrade. This way, all the off-chain logic can still load the old runtime code under the default storage key and decode the state correctly. The block producer is then required to use this new runtime code to build the next block. While building the next block, the runtime is executing the migrations and moves the new runtime code to the default runtime code location. So, the runtime code found under the default location is always the correct one to decode the state from which the runtime code was loaded.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Summary","id":"137","title":"Summary"},"138":{"body":"While the issue of having undecodable state only exists for the one block in which the runtime upgrade was applied, it still impacts anything that reads state data, like block explorers, UIs, nodes, etc. For block explorers, the issue mainly results in indexing invalid data and UIs may show invalid data to the user. For nodes, reading incorrect data may lead to a performance degradation of the network . There are also ways to prevent certain decoding issues from happening, but it requires that developers are aware of this issue and also requires introducing extra code, which could introduce further bugs down the line. So, this RFC tries to solve these issues by fixing the underlying problem of having temporary undecodable state.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Motivation","id":"138","title":"Motivation"},"139":{"body":"Relay chain/Parachain node developers Relay chain/Parachain node operators","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Stakeholders","id":"139","title":"Stakeholders"},"14":{"body":"RFC: XCM Asset Metadata","breadcrumbs":"RFC-0125: XCM Asset Metadata » Prior Art and References","id":"14","title":"Prior Art and References"},"140":{"body":"The runtime code is stored under the special key :code in the state. Nodes and other tooling read the runtime code under this storage key when they want to interact with the runtime for e.g., building/importing blocks or getting the metadata to read the state. To update the runtime code the runtime overwrites the value at :code, and then from the next block on, the new runtime will be loaded. This RFC proposes to first store the new runtime code under :pending_code in the state for one block. When the next block is being built, the block builder first needs to check if :pending_code is set, and if so, it needs to load the runtime from this storage key. While building the block the runtime will move :pending_code to :code to have the runtime code at the default location. Nodes importing the block will also need to load :pending_code if it exists to ensure that the correct runtime code is used. By doing it this way, the runtime code found at :code in the state of a block will always be able to decode the state. Furthermore, this RFC proposes to introduce system_version: 3. The system_version was introduced in RFC42 . Version 3 would then enable the usage of :pending_code when applying a runtime code upgrade. This way, the feature can be introduced first and enabled later when the majority of the nodes have upgraded.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Explanation","id":"140","title":"Explanation"},"141":{"body":"Because the first block built with the new runtime code will move the runtime code from :pending_code to :code, the runtime code will need to be loaded. This means the runtime code will appear in the proof of validity of a parachain for the first block built with the new runtime code. Generally this is not a problem as the runtime code is also loaded by the parachain when setting the new runtime code. There is still the possibility of having state that is not migrated even when following the proposal as presented by this RFC. The issue is that if the amount of data to be migrated is too big, not all of it can be migrated in one block, because either it takes more time than there is assigned for a block or parachains for example have a fixed budget for their proof of validity. To solve this issue there already exist multi-block migrations that can chunk the migration across multiple blocks. Consensus-critical data needs to be migrated in the first block to ensure that block production etc., can continue. For the other data being migrated by multi-block migrations the migrations could for example expose to the outside which keys are being migrated and should not be indexed until the migration is finished.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Drawbacks","id":"141","title":"Drawbacks"},"142":{"body":"Testing should be straightforward and most of the existing testing should already be good enough. Extending with some checks that :pending_code is moved to :code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Testing, Security, and Privacy","id":"142","title":"Testing, Security, and Privacy"},"143":{"body":"","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Performance, Ergonomics, and Compatibility","id":"143","title":"Performance, Ergonomics, and Compatibility"},"144":{"body":"The performance should not be impacted besides requiring loading the runtime code in the first block being built with the new runtime code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Performance","id":"144","title":"Performance"},"145":{"body":"It only alters the way blocks are produced and imported after applying a runtime upgrade. This means that only nodes need to be adapted to the changes of this RFC.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Ergonomics","id":"145","title":"Ergonomics"},"146":{"body":"The change will require that the nodes are upgraded before the runtime starts using this feature. Otherwise they will fail to import the block build by :pending_code. For Polkadot/Kusama this means that also the parachain nodes need to be running with a relay chain node version that supports this new feature. Otherwise the parachains will stop producing/finalizing nodes as they can not sync the relay chain any more.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Compatibility","id":"146","title":"Compatibility"},"147":{"body":"The issue initially reported a bug that led to this RFC. It also discusses multiple solutions for the problem.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Prior Art and References","id":"147","title":"Prior Art and References"},"148":{"body":"None","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Unresolved Questions","id":"148","title":"Unresolved Questions"},"149":{"body":"Solve the issue of requiring loading the entire runtime code to move it into a different location by introducing a low-level move function. When using the V1 trie layout every value bigger than 32 bytes is put into the db separately. This means a low level move function would only need to move the hash of the runtime code from :code to :pending_code.","breadcrumbs":"RFC-0123: Introduce :pending_code as intermediate storage key for the runtime code » Future Directions and Related Material","id":"149","title":"Future Directions and Related Material"},"15":{"body":"Should the MetadataMap and MetadataKeys be bounded, or is it enough to rely on the fact that every XCM message is itself bounded?","breadcrumbs":"RFC-0125: XCM Asset Metadata » Unresolved Questions","id":"15","title":"Unresolved Questions"},"150":{"body":"(source) Table of Contents RFC-0124: Extrinsic version 5 Summary Motivation Stakeholders Explanation Changes to extrinsic authorization Encoding format for version 5 Signatures on Polkadot in General transactions Summary of changes in version 5 Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 18 October 2024 Description Definition and specification of version 5 extrinsics Authors George Pisaltu","breadcrumbs":"RFC-0124: Extrinsic version 5 » RFC-0124: Extrinsic version 5","id":"150","title":"RFC-0124: Extrinsic version 5"},"151":{"body":"This RFC proposes the definition of version 5 extrinsics along with changes to the specification and encoding from version 4.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Summary","id":"151","title":"Summary"},"152":{"body":"RFC84 introduced the specification of General transactions, a new type of extrinsic besides the Signed and Unsigned variants available previously in version 4. Additionally, RFC99 introduced versioning of transaction extensions through an extra byte in the extrinsic encoding. Both of these changes require an extrinsic format version bump as both the semantics around extensions as well as the actual encoding of extrinsics need to change to accommodate these new features.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Motivation","id":"152","title":"Motivation"},"153":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0124: Extrinsic version 5 » Stakeholders","id":"153","title":"Stakeholders"},"154":{"body":"","breadcrumbs":"RFC-0124: Extrinsic version 5 » Explanation","id":"154","title":"Explanation"},"155":{"body":"The introduction of General transactions allows the authorization of any and all origins through extensions. This means that, with the appropriate extension, General transactions are capable of replicating the same behavior present day v4 Signed transactions. Specifically for Polkadot chains, an example implementation for such an extension is VerifySignature , introduced in the Transaction Extension PR3685 . Other extensions can be inserted into the extension pipeline to authorize different custom origins. Therefore, a Signed extrinsic variant is redundant to a General one strictly in terms of functionality available to users and would eventually need to be deprecated and removed.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Changes to extrinsic authorization","id":"155","title":"Changes to extrinsic authorization"},"156":{"body":"As with version 4, the encoded v5 extrinsics will still be an array of SCALE encoded bytes, starting with the encoded length of the following bytes. The leading byte will determine the version and type of extrinsic, as specified by RFC84 , with the addition that the Signed variant will not be supported for v5 extrinsics, for reasons mentioned above. NOTE: For Bare extrinsics, the following bytes will just be the encoded call and nothing else. For General transactions, as stated in RFC99 , an extension version byte must be added in the next extrinsic version. This byte should allow runtimes to expose more than one set of extensions which can be used for a transaction. As far as the v5 extrinsic encoding is concerned, this extension byte should be encoded immediately after the leading encoding byte. The extension version byte should be included in payloads to be signed by all extensions configured by runtime devs to ensure a user's extension version choice cannot be altered by third parties. After the extension version byte, the extensions will be encoded next, followed by the call itself. A quick visualization of the encoding: Bare extrinsics: (extrinsic_encoded_len, 0b0000_0101, call) General transactions: (extrinsic_encoded_len, , 0b0100_0101, extension_version_byte, extension, call)","breadcrumbs":"RFC-0124: Extrinsic version 5 » Encoding format for version 5","id":"156","title":"Encoding format for version 5"},"157":{"body":"As stated before, PR3685 comes with a Transaction Extension which replicates the current Signed transactions in v5 extrinsics, namely VerifySignature . This extension leverages the new inherited implication functionality introduced in TransactionExtension and creates a payload to be signed using the data of all extensions after itself in the extension pipeline. In order to run a transaction with a signed origin, a user must create the transaction with an instance of the extension which provides a signature. Alternatively, if users want to use some other origin, they should create the transaction with this particular extension disabled. More on this behavior in the extension documentation. This extension can be configured to accept a MultiSignature, which makes it compatible with all signature types currently used in Polkadot. To generate the payload to be signed: The extension version byte, call, extension and extension implicit should be encoded; The result of the encoding should then be hashed using the BLAKE2_256 hasher; The result of the hash should then be signed with the signature type specified in the extension definition. // Step 1: encode the bytes\nlet encoded = (extension_version_byte, call, transaction_extension, transaction_extension_implicit).encode();\n// Step 2: hash them\nlet payload = blake2_256(&encoded[..]);\n// Step 3: sign the payload\nlet signature = keyring.sign(&payload[..]);","breadcrumbs":"RFC-0124: Extrinsic version 5 » Signatures on Polkadot in General transactions","id":"157","title":"Signatures on Polkadot in General transactions"},"158":{"body":"In order to minimize the number of changes to the extrinsic format version and also to help all consumers downstream in the transition period between these extrinsic versions, we should: Remove the Signed variant starting with v5 extrinsics Add the General variant starting with v5 extrinsics Enable runtimes to support both v4 and v5 extrinsics","breadcrumbs":"RFC-0124: Extrinsic version 5 » Summary of changes in version 5","id":"158","title":"Summary of changes in version 5"},"159":{"body":"The metadata will have to accommodate two distinct extrinsic format versions at a given point in time in order to provide the new functionality in a non-breaking way for users and tooling.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Drawbacks","id":"159","title":"Drawbacks"},"16":{"body":"The original RFC draft contained additional metadata instructions. Though they could be useful, they're clearly outside the basic logic. So, this RFC version omits them to make the metadata discussion more focused on the core things. Nonetheless, there is hope that metadata approval instructions might be useful in the future, so they are mentioned here. You can read about the details in the original draft .","breadcrumbs":"RFC-0125: XCM Asset Metadata » Future Directions and Related Material","id":"16","title":"Future Directions and Related Material"},"160":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Testing, Security, and Privacy","id":"160","title":"Testing, Security, and Privacy"},"161":{"body":"This change makes the authorization through signatures configurable by runtime devs in version 5 extrinsics, as opposed to version 4 where the signing payload algorithm and signatures were hardcoded. This moves the responsibility of ensuring proper authentication through TransactionExtension to the runtime devs, but a sensible default which closely resembles the present day behavior will be provided in VerifySignature.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Performance, Ergonomics, and Compatibility","id":"161","title":"Performance, Ergonomics, and Compatibility"},"162":{"body":"There is no performance impact.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Performance","id":"162","title":"Performance"},"163":{"body":"Tooling will have to adapt to be able to tell which authorization scheme is used by a particular transaction by decoding the extension and checking which particular TransactionExtension in the pipeline is enabled to do the origin authorization. Previously, this was done by simply checking whether the transaction is signed or unsigned, as there was only one method of authentication.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Ergonomics","id":"163","title":"Ergonomics"},"164":{"body":"As long as extrinsic version 4 is still exposed in the metadata when version 5 will be introduced, the changes will not break existing infrastructure. This should give enough time for tooling to support version 5 and to remove version 4 in the future.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Compatibility","id":"164","title":"Compatibility"},"165":{"body":"This is a result of the work in Extrinsic Horizon and RFC99 .","breadcrumbs":"RFC-0124: Extrinsic version 5 » Prior Art and References","id":"165","title":"Prior Art and References"},"166":{"body":"There is no clear way to expose two different extrinsic versions in the current metadata framework. A non-exhaustive list of options discussed so far: Change the ExtrinsicMetadata trait to specify a list of versions instead of a single version. Use the custom fields in the metadata to specify the details of the version 5. Create a new trait similar to ExtrinsicMetadata, but for future versions of the extrinsic format and add it to the metadata.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Unresolved Questions","id":"166","title":"Unresolved Questions"},"167":{"body":"Following this change, extrinsic version 5 will be introduced as part of the Extrinsic Horizon effort, which will shape future work.","breadcrumbs":"RFC-0124: Extrinsic version 5 » Future Directions and Related Material","id":"167","title":"Future Directions and Related Material"},"168":{"body":"(source) Table of Contents RFC-114: Adjust Tipper Track Confirmation Periods Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics & Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 17-Aug-24 Description Big and Small Tipper Track Conformation Period Modification Authors Leemo / ChaosDAO","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » RFC-114: Adjust Tipper Track Confirmation Periods","id":"168","title":"RFC-114: Adjust Tipper Track Confirmation Periods"},"169":{"body":"This RFC proposes to change the duration of the Confirmation Period for the Big Tipper and Small Tipper tracks in Polkadot OpenGov: Small Tipper: 10 Minutes -> 12 Hours Big Tipper: 1 Hour -> 1 Day","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Summary","id":"169","title":"Summary"},"17":{"body":"(source) Table of Contents RFC-0126: Introduce XCQ(Cross Consensus Query) Summary Motivation Stakeholders Explanation XCQ Runtime API XCQ Executor XCQ Extension XCQ Program Structure XCQ Program Execution Flow Drawbacks Performance issues User experience issues Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date Oct 25 2024 Description Introduce XCQ (Cross Consensus Query) Authors Bryan Chen, Jiyuan Zheng","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » RFC-0126: Introduce XCQ(Cross Consensus Query)","id":"17","title":"RFC-0126: Introduce XCQ(Cross Consensus Query)"},"170":{"body":"Currently, these are the durations of treasury tracks in Polkadot OpenGov. Confirmation periods for the Spender tracks were adjusted based on RFC20 and its related conversation. Track Description Confirmation Period Duration Treasurer 7 Days Big Spender 7 Days Medium Spender 4 Days Small Spender 2 Days Big Tipper 1 Hour Small Tipper 10 Minutes You can see that there is a general trend on the Spender track that when the privilege level (the amount the track can spend) the confirmation period approximately doubles. I believe that the Big Tipper and Small Tipper track's confirmation periods should be adjusted to match this trend. In the current state it is possible to somewhat positively snipe these tracks, and whilst the power/privilege level of these tracks is very low (they cannot spend a large amount of funds), I believe we should increase the confirmation periods to something higher. This is backed up by the recent sentiment in the greater community regarding referendums submitted on these tracks. The parameters of Polkadot OpenGov can be adjusted based on the general sentiment of token holders when necessary.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Motivation","id":"170","title":"Motivation"},"171":{"body":"The primary stakeholders of this RFC are: – DOT token holders – as this affects the protocol's treasury – Entities wishing to submit a referendum on these tracks – as this affects the referendum's timeline – Projects with governance app integrations – see Performance, Ergonomics and Compatibility section below","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Stakeholders","id":"171","title":"Stakeholders"},"172":{"body":"This RFC proposes to change the duration of the confirmation period for both the Big Tipper and Small Tipper tracks. To achieve this the confirm_period parameter for those tracks should be changed. You can see the lines of code that need to be adjusted here: Big Tipper: https://github.com/polkadot-fellows/runtimes/blob/f4c5d272d4672387771fb038ef52ca36f3429096/relay/polkadot/src/governance/tracks.rs#L245 Small Tipper: https://github.com/polkadot-fellows/runtimes/blob/f4c5d272d4672387771fb038ef52ca36f3429096/relay/polkadot/src/governance/tracks.rs#L231 This RFC proposes to change the confirm_period for the Big Tipper track to DAYS (i.e. 1 Day) and the confirm_period for the Small Tipper track to 12 * HOURS (i.e. 12 Hours).","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Explanation","id":"172","title":"Explanation"},"173":{"body":"The drawback of changing these confirmation periods is that the lifecycle of referenda submitted on those tracks would be ultimately longer, and it would add a greater potential to negatively \"snipe\" referenda on those tracks by knocking the referendum out of its confirmation period once the decision period has ended. This can be a good or a bad thing depending on your outlook of positive vs negative sniping.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Drawbacks","id":"173","title":"Drawbacks"},"174":{"body":"This referendum will enhance the security of the protocol as it relates to its treasury. The confirmation period is one of the last lines of defense for the Polkadot token holder DAO to react to a potentially bad referendum and vote NAY in order for its confirmation period to be aborted.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Testing, Security, and Privacy","id":"174","title":"Testing, Security, and Privacy"},"175":{"body":"","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Performance, Ergonomics, and Compatibility","id":"175","title":"Performance, Ergonomics, and Compatibility"},"176":{"body":"This is a simple change (code wise) that should not affect the performance of the Polkadot protocol, outside of increasing the duration of the confirmation periods for these 2 tracks.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Performance","id":"176","title":"Performance"},"177":{"body":"As per the implementation of changes described in RFC-20, it was identified that governance UIs automatically update to meet the new parameters: Nova Wallet - directly uses on-chain data, and change will be automatically reflected. Polkassembly - directly uses on-chain data via rpc to fetch trackInfo so the change will be automatically reflected. SubSquare - scan script will update their app to the latest parameters and it will be automatically reflected in their app.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Ergonomics & Compatibility","id":"177","title":"Ergonomics & Compatibility"},"178":{"body":"N/A","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Prior Art and References","id":"178","title":"Prior Art and References"},"179":{"body":"Some token holders may want these confirmation periods to remain as they are currently and for them not to increase. If this is something that the Polkadot Technical Fellowship considers to be an issue to implement into a runtime upgrade then I can create a Wish For Change to obtain token holder approval.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Unresolved Questions","id":"179","title":"Unresolved Questions"},"18":{"body":"This proposal introduces XCQ (Cross Consensus Query), which aims to serve as an intermediary layer between different chain runtime implementations and tools/UIs, to provide a unified interface for cross-chain queries. XCQ abstracts away concrete implementations across chains and supports custom query computations. Use cases benefiting from XCQ include: XCM bridge UI: Query asset balances Query XCM weight and fee from hop and dest chains Wallets: Query asset balances Query weights and fees for operations across chains Universal dApp that supports all the parachains: Perform Feature discovery Query pallet-specific features Construct extrinsics by querying pallet index, call index, etc","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Summary","id":"18","title":"Summary"},"180":{"body":"The parameters of Polkadot OpenGov will likely continue to change over time, there are additional discussions in the community regarding adjusting the min_support for some tracks so that it does not trend towards 0%, similar to the current state of the Whitelisted Caller track. This is outside of the scope of this RFC and requires a lot more discussion.","breadcrumbs":"RFC-114: Adjust Tipper Track Confirmation Periods » Future Directions and Related Material","id":"180","title":"Future Directions and Related Material"},"181":{"body":"(source) Table of Contents RFC-1: Agile Coretime Summary Motivation Present System Problems Requirements Stakeholders Explanation Overview Detail Specific functions of the Coretime-chain Notes on the Instantaneous Coretime Market Notes on Economics Notes on Types Rollout Performance, Ergonomics and Compatibility Testing, Security and Privacy Future Directions and Related Material Drawbacks, Alternatives and Unknowns Prior Art and References Start Date 30 June 2023 Description Agile periodic-sale-based model for assigning Coretime on the Polkadot Ubiquitous Computer. Authors Gavin Wood","breadcrumbs":"RFC-1: Agile Coretime » RFC-1: Agile Coretime","id":"181","title":"RFC-1: Agile Coretime"},"182":{"body":"This proposes a periodic, sale-based method for assigning Polkadot Coretime, the analogue of \"block space\" within the Polkadot Network. The method takes into account the need for long-term capital expenditure planning for teams building on Polkadot, yet also provides a means to allow Polkadot to capture long-term value in the resource which it sells. It supports the possibility of building rich and dynamic secondary markets to optimize resource allocation and largely avoids the need for parameterization.","breadcrumbs":"RFC-1: Agile Coretime » Summary","id":"182","title":"Summary"},"183":{"body":"","breadcrumbs":"RFC-1: Agile Coretime » Motivation","id":"183","title":"Motivation"},"184":{"body":"The Polkadot Ubiquitous Computer , or just Polkadot UC , represents the public service provided by the Polkadot Network. It is a trust-free, WebAssembly-based, multicore, internet-native omnipresent virtual machine which is highly resilient to interference and corruption. The present system of allocating the limited resources of the Polkadot Ubiquitous Computer is through a process known as parachain slot auctions . This is a parachain-centric paradigm whereby a single core is long-term allocated to a single parachain which itself implies a Substrate/Cumulus-based chain secured and connected via the Relay-chain. Slot auctions are on-chain candle auctions which proceed for several days and result in the core being assigned to the parachain for six months at a time up to 24 months in advance. Practically speaking, we only see two year periods being bid upon and leased. Funds behind the bids made in the slot auctions are merely locked, they are not consumed or paid and become unlocked and returned to the bidder on expiry of the lease period. A means of sharing the deposit trustlessly known as a crowdloan is available allowing token holders to contribute to the overall deposit of a chain without any counterparty risk.","breadcrumbs":"RFC-1: Agile Coretime » Present System","id":"184","title":"Present System"},"185":{"body":"The present system is based on a model of one-core-per-parachain. This is a legacy interpretation of the Polkadot platform and is not a reflection of its present capabilities. By restricting ownership and usage to this model, more dynamic and resource-efficient means of utilizing the Polkadot Ubiquitous Computer are lost. More specifically, it is impossible to lease out cores at anything less than six months, and apparently unrealistic to do so at anything less than two years. This removes the ability to dynamically manage the underlying resource, and generally experimentation, iteration and innovation suffer. It bakes into the platform an assumption of permanence for anything deployed into it and restricts the market's ability to find a more optimal allocation of the finite resource. There is no ability to determine capital requirements for hosting a parachain beyond two years from the point of its initial deployment onto Polkadot. While it would be unreasonable to have perfect and indefinite cost predictions for any real-world platform, not having any clarity whatsoever beyond \"market rates\" two years hence can be a very off-putting prospect for teams to buy into. However, quite possibly the most substantial problem is both a perceived and often real high barrier to entry of the Polkadot ecosystem. By forcing innovators to either raise seven-figure sums through investors or appeal to the wider token-holding community, Polkadot makes it difficult for a small band of innovators to deploy their technology into Polkadot. While not being actually permissioned, it is also far from the barrierless, permissionless ideal which an innovation platform such as Polkadot should be striving for.","breadcrumbs":"RFC-1: Agile Coretime » Problems","id":"185","title":"Problems"},"186":{"body":"The solution SHOULD provide an acceptable value-capture mechanism for the Polkadot network. The solution SHOULD allow parachains and other projects deployed on to the Polkadot UC to make long-term capital expenditure predictions for the cost of ongoing deployment. The solution SHOULD minimize the barriers to entry in the ecosystem. The solution SHOULD work well when the Polkadot UC has up to 1,000 cores. The solution SHOULD work when the number of cores which the Polkadot UC can support changes over time. The solution SHOULD facilitate the optimal allocation of work to cores of the Polkadot UC, including by facilitating the trade of regular core assignment at various intervals and for various spans. The solution SHOULD avoid creating additional dependencies on functionality which the Relay-chain need not strictly provide for the delivery of the Polkadot UC. Furthermore, the design SHOULD be implementable and deployable in a timely fashion; three months from the acceptance of this RFC should not be unreasonable.","breadcrumbs":"RFC-1: Agile Coretime » Requirements","id":"186","title":"Requirements"},"187":{"body":"Primary stakeholder sets are: Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division. Polkadot Parachain teams both present and future, and their users. Polkadot DOT token holders. Socialization: The essensials of this proposal were presented at Polkadot Decoded 2023 Copenhagen on the Main Stage. A small amount of socialization at the Parachain Summit preceeded it and some substantial discussion followed it. Parity Ecosystem team is currently soliciting views from ecosystem teams who would be key stakeholders.","breadcrumbs":"RFC-1: Agile Coretime » Stakeholders","id":"187","title":"Stakeholders"},"188":{"body":"","breadcrumbs":"RFC-1: Agile Coretime » Explanation","id":"188","title":"Explanation"},"189":{"body":"Upon implementation of this proposal, the parachain-centric slot auctions and associated crowdloans cease. Instead, Coretime on the Polkadot UC is sold by the Polkadot System in two separate formats: Bulk Coretime and Instantaneous Coretime . When a Polkadot Core is utilized, we say it is dedicated to a Task rather than a \"parachain\". The Task to which a Core is dedicated may change at every Relay-chain block and while one predominant type of Task is to secure a Cumulus-based blockchain (i.e. a parachain), other types of Tasks are envisioned. Bulk Coretime is sold periodically on a specialised system chain known as the Coretime-chain and allocated in advance of its usage, whereas Instantaneous Coretime is sold on the Relay-chain immediately prior to usage on a block-by-block basis. This proposal does not fix what should be done with revenue from sales of Coretime and leaves it for a further RFC process. Owners of Bulk Coretime are tracked on the Coretime-chain and the ownership status and properties of the owned Coretime are exposed over XCM as a non-fungible asset. At the request of the owner, the Coretime-chain allows a single Bulk Coretime asset, known as a Region , to be used in various ways including transferal to another owner, allocated to a particular task (e.g. a parachain) or placed in the Instantaneous Coretime Pool. Regions can also be split out, either into non-overlapping sub-spans or exactly-overlapping spans with less regularity. The Coretime-Chain periodically instructs the Relay-chain to assign its cores to alternative tasks as and when Core allocations change due to new Regions coming into effect. Renewal and Migration There is a renewal system which allows a Bulk Coretime assignment of a single core to be renewed unchanged with a known price increase from month to month. Renewals are processed in a period prior to regular purchases, effectively giving them precedence over a fixed number of cores available. Renewals are only enabled when a core's assignment does not include an Instantaneous Coretime allocation and has not been split into shorter segments. Thus, renewals are designed to ensure only that committed parachains get some guarantees about price for predicting future costs. This price-capped renewal system only allows cores to be reused for their same tasks from month to month. In any other context, Bulk Coretime would need to be purchased regularly. As a migration mechanism, pre-existing leases (from the legacy lease/slots/crowdloan framework) are initialized into the Coretime-chain and cores assigned to them prior to Bulk Coretime sales. In the sale where the lease expires, the system offers a renewal, as above, to allow a priority sale of Bulk Coretime and ensure that the Parachain suffers no downtime when transitioning from the legacy framework. Instantaneous Coretime Processing of Instantaneous Coretime happens in part on the Polkadot Relay-chain. Credit is purchased on the Coretime-chain for regular DOT tokens, and this results in a DOT-denominated Instantaneous Coretime Credit account on the Relay-chain being credited for the same amount. Though the Instantaneous Coretime Credit account records a balance for an account identifier (very likely controlled by a collator), it is non-transferable and non-refundable . It can only be consumed in order to purchase some Instantaneous Coretime with immediate availability. The Relay-chain reports this usage back to the Coretime-chain in order to allow it to reward the providers of the underlying Coretime, either the Polkadot System or owners of Bulk Coretime who contributed to the Instantaneous Coretime Pool. Specifically the Relay-chain is expected to be responsible for: holding non-transferable, non-refundable DOT-denominated Instantaneous Coretime Credit balance information. setting and adjusting the price of Instantaneous Coretime based on usage. allowing collators to consume their Instantaneous Coretime Credit at the current pricing in exchange for the ability to schedule one PoV for near-immediate usage. ensuring the Coretime-Chain has timely accounting information on Instantaneous Coretime Sales revenue. Coretime-chain The Coretime-chain is a new system parachain. It has the responsibility of providing the Relay-chain via UMP with information of: The number of cores which should be made available. Which tasks should be running on which cores and in what ratios. Accounting information for Instantaneous Coretime Credit. It also expects information from the Relay-chain via DMP: The number of cores available to be scheduled. Account information on Instantaneous Coretime Sales. The specific interface is properly described in RFC-5.","breadcrumbs":"RFC-1: Agile Coretime » Overview","id":"189","title":"Overview"},"19":{"body":"In Substrate, runtime APIs facilitate off-chain clients in reading the state of the consensus system. However, different chains may expose different APIs for a similar query or have varying data types, such as doing custom transformations on direct data, or differing AccountId types. This diversity also extends to client-side, which may require custom computations over runtime APIs in various use cases. Therefore, tools and UI developers often access storage directly and reimplement custom computations to convert data into user-friendly representations, leading to duplicated code between Rust runtime logic and UI JS/TS logic. This duplication increases workload and potential for bugs. Therefore, A system is needed to serve as an intermediary layer between concrete chain runtime implementations and tools/UIs, to provide a unified interface for cross-chain queries.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Motivation","id":"19","title":"Motivation"},"190":{"body":"Parameters This proposal includes a number of parameters which need not necessarily be fixed. Their usage is explained below, but their values are suggested or specified in the later section Parameter Values . Reservations and Leases The Coretime-chain includes some governance-set reservations of Coretime; these cover every System-chain. Additionally, governance is expected to initialize details of the pre-existing leased chains. Regions A Region is an assignable period of Coretime with a known regularity. All Regions are associated with a unique Core Index , to identify which core the assignment of which ownership of the Region controls. All Regions are also associated with a Core Mask , an 80-bit bitmap, to denote the regularity at which it may be scheduled on the core. If all bits are set in the Core Mask value, it is said to be Complete . 80 is selected since this results in the size of the datatype used to identify any Region of Polkadot Coretime to be a very convenient 128-bit. Additionally, if TIMESLICE (the number of Relay-chain blocks in a Timeslice) is 80, then a single bit in the Core Mask bitmap represents exactly one Core for one Relay-chain block in one Timeslice. All Regions have a span. Region spans are quantized into periods of TIMESLICE blocks; BULK_PERIOD divides into TIMESLICE a whole number of times. The Timeslice type is a u32 which can be multiplied by TIMESLICE to give a BlockNumber value representing the same quantity in terms of Relay-chain blocks. Regions can be tasked to a TaskId (aka ParaId) or pooled into the Instantaneous Coretime Pool. This process can be Provisional or Final . If done only provisionally or not at all then they are fresh and have an Owner which is able to manipulate them further including reassignment. Once Final , then all ownership information is discarded and they cannot be manipulated further. Renewal is not possible when only provisionally tasked/pooled. Bulk Sales A sale of Bulk Coretime occurs on the Coretime-chain every BULK_PERIOD blocks. In every sale, a BULK_LIMIT of individual Regions are offered for sale. Each Region offered for sale has a different Core Index, ensuring that they each represent an independently allocatable resource on the Polkadot UC. The Regions offered for sale have the same span: they last exactly BULK_PERIOD blocks, and begin immediately following the span of the previous Sale's Regions. The Regions offered for sale also have the complete, non-interlaced, Core Mask. The Sale Period ends immediately as soon as span of the Coretime Regions that are being sold begins. At this point, the next Sale Price is set according to the previous Sale Price together with the number of Regions sold compared to the desired and maximum amount of Regions to be sold. See Price Setting for additional detail on this point. Following the end of the previous Sale Period, there is an Interlude Period lasting INTERLUDE_PERIOD of blocks. After this period is elapsed, regular purchasing begins with the Purchasing Period . This is designed to give at least two weeks worth of time for the purchased regions to be partitioned, interlaced, traded and allocated. The Interlude The Interlude period is a period prior to Regular Purchasing where renewals are allowed to happen. This has the effect of ensuring existing long-term tasks/parachains have a chance to secure their Bulk Coretime for a well-known price prior to general sales. Regular Purchasing Any account may purchase Regions of Bulk Coretime if they have the appropriate funds in place during the Purchasing Period, which is from INTERLUDE_PERIOD blocks after the end of the previous sale until the beginning of the Region of the Bulk Coretime which is for sale as long as there are Regions of Bulk Coretime left for sale (i.e. no more than BULK_LIMIT have already been sold in the Bulk Coretime Sale). The Purchasing Period is thus roughly BULK_PERIOD - INTERLUDE_PERIOD blocks in length. The Sale Price varies during an initial portion of the Purchasing Period called the Leadin Period and then stays stable for the remainder. This initial portion is LEADIN_PERIOD blocks in duration. During the Leadin Period the price decreases towards the Sale Price, which it lands at by the end of the Leadin Period. The actual curve by which the price starts and descends to the Sale Price is outside the scope of this RFC, though a basic suggestion is provided in the Price Setting Notes, below. Renewals At any time when there are remaining Regions of Bulk Coretime to be sold, including during the Interlude Period , then certain Bulk Coretime assignmnents may be Renewed . This is similar to a purchase in that funds must be paid and it consumes one of the Regions of Bulk Coretime which would otherwise be placed for purchase. However there are two key differences. Firstly, the price paid is the minimum of RENEWAL_PRICE_CAP more than what the purchase/renewal price was in the previous renewal and the current (or initial, if yet to begin) regular Sale Price. Secondly, the purchased Region comes preassigned with exactly the same workload as before. It cannot be traded, repartitioned, interlaced or exchanged. As such unlike regular purchasing the Region never has an owner. Renewal is only possible for either cores which have been assigned as a result of a previous renewal, which are migrating from legacy slot leases, or which fill their Bulk Coretime with an unsegmented, fully and finally assigned workload which does not include placement in the Instantaneous Coretime Pool. The renewed workload will be the same as this initial workload. Manipulation Regions may be manipulated in various ways by its owner: Transferred in ownership. Partitioned into quantized, non-overlapping segments of Bulk Coretime with the same ownership. Interlaced into multiple Regions over the same period whose eventual assignments take turns to be scheduled. Assigned to a single, specific task (identified by TaskId aka ParaId). This may be either provisional or final . Pooled into the Instantaneous Coretime Pool, in return for a pro-rata amount of the revenue from the Instantaneous Coretime Sales over its period. Enactment","breadcrumbs":"RFC-1: Agile Coretime » Detail","id":"190","title":"Detail"},"191":{"body":"Several functions of the Coretime-chain SHALL be exposed through dispatchables and/or a nonfungible trait implementation integrated into XCM: 1. transfer Regions may have their ownership transferred. A transfer(region: RegionId, new_owner: AccountId) dispatchable shall have the effect of altering the current owner of the Region identified by region from the signed origin to new_owner. An implementation of the nonfungible trait SHOULD include equivalent functionality. RegionId SHOULD be used for the AssetInstance value. 2. partition Regions may be split apart into two non-overlapping interior Regions of the same Core Mask which together concatenate to the original Region. A partition(region: RegionId, pivot: Timeslice) dispatchable SHALL have the effect of removing the Region identified by region and adding two new Regions of the same owner and Core Mask. One new Region will begin at the same point of the old Region but end at pivot timeslices into the Region, whereas the other will begin at this point and end at the end point of the original Region. Also: owner field of region must the equal to the Signed origin. pivot must equal neither the begin nor end fields of the region. 3. interlace Regions may be decomposed into two Regions of the same span whose eventual assignments take turns on the core by virtue of having complementary Core Masks. An interlace(region: RegionId, mask: CoreMask) dispatchable shall have the effect of removing the Region identified by region and creating two new Regions. The new Regions will each have the same span and owner of the original Region, but one Region will have a Core Mask equal to mask and the other will have Core Mask equal to the XOR of mask and the Core Mask of the original Region. Also: owner field of region must the equal to the Signed origin. mask must have some bits set AND must not equal the Core Mask of the old Region AND must only have bits set which are also set in the old Region's' Core Mask. 4. assign Regions may be assigned to a core. A assign(region: RegionId, target: TaskId, finality: Finality) dispatchable shall have the effect of placing an item in the workplan corresponding to the region's properties and assigned to the target task. If the region's end has already passed (taking into account any advance notice requirements) then this operation is a no-op. If the region's begining has already passed, then it is effectively altered to become the next schedulable timeslice. finality may have the value of either Final or Provisional. If Final, then the operation is free, the region record is removed entirely from storage and renewal may be possible: if the Region's span is the entire BULK_PERIOD, then the Coretime-chain records in storage that the allocation happened during this period in order to facilitate the possibility for a renewal. (Renewal only becomes possible when the full Core Mask of a core is finally assigned for the full BULK_PERIOD.) Also: owner field of region must the equal to the Signed origin. 5. pool Regions may be consumed in exchange for a pro rata portion of the Instantaneous Coretime Sales Revenue from its period and regularity. A pool(region: RegionId, beneficiary: AccountId, finality: Finality) dispatchable shall have the effect of placing an item in the workplan corresponding to the region's properties and assigned to the Instantaneous Coretime Pool. The details of the region will be recorded in order to allow for a pro rata share of the Instantaneous Coretime Sales Revenue at the time of the Region relative to any other providers in the Pool. If the region's end has already passed (taking into account any advance notice requirements) then this operation is a no-op. If the region's begining has already passed, then it is effectively altered to become the next schedulable timeslice. finality may have the value of either Final or Provisional. If Final, then the operation is free and the region record is removed entirely from storage. Also: owner field of region must the equal to the Signed origin. 6. Purchases A dispatchable purchase(price_limit: Balance) shall be provided. Any account may call purchase to purchase Bulk Coretime at the maximum price of price_limit. This may be called successfully only: during the regular Purchasing Period; when the caller is a Signed origin and their account balance is reducible by the current sale price; when the current sale price is no greater than price_limit; and when the number of cores already sold is less than BULK_LIMIT. If successful, the caller's account balance is reduced by the current sale price and a new Region item for the following Bulk Coretime span is issued with the owner equal to the caller's account. 7. Renewals A dispatchable renew(core: CoreIndex) shall be provided. Any account may call renew to purchase Bulk Coretime and renew an active allocation for the given core. This may be called during the Interlude Period as well as the regular Purchasing Period and has the same effect as purchase followed by assign, except that: The price of the sale is the Renewal Price (see next). The Region is allocated exactly the given core is currently allocated for the present Region. Renewal is only valid where a Region's span is assigned to Tasks (not placed in the Instantaneous Coretime Pool) for the entire unsplit BULK_PERIOD over all of the Core Mask and with Finality. There are thus three possibilities of a renewal being allowed: Purchased unsplit Coretime with final assignment to tasks over the full Core Mask. Renewed Coretime. A legacy lease which is ending. Renewal Price The Renewal Price is the minimum of the current regular Sale Price (or the initial Sale Price if in the Interlude Period) and: If the workload being renewed came to be through the Purchase and Assignment of Bulk Coretime, then the price paid during that Purchase operation. If the workload being renewed was previously renewed, then the price paid during this previous Renewal operation plus RENEWAL_PRICE_CAP. If the workload being renewed is a migation from a legacy slot auction lease, then the nominal price for a Regular Purchase (outside of the Lead-in Period) of the Sale during which the legacy lease expires. 8. Instantaneous Coretime Credits A dispatchable purchase_credit(amount: Balance, beneficiary: RelayChainAccountId) shall be provided. Any account with at least amount spendable funds may call this. This increases the Instantaneous Coretime Credit balance on the Relay-chain of the beneficiary by the given amount. This Credit is consumable on the Relay-chain as part of the Task scheduling system and its specifics are out of the scope of this proposal. When consumed, revenue is recorded and provided to the Coretime-chain for proper distribution. The API for doing this is specified in RFC-5.","breadcrumbs":"RFC-1: Agile Coretime » Specific functions of the Coretime-chain","id":"191","title":"Specific functions of the Coretime-chain"},"192":{"body":"For an efficient market to form around the provision of Bulk-purchased Cores into the pool of cores available for Instantaneous Coretime purchase, it is crucial to ensure that price changes for the purchase of Instantaneous Coretime are reflected well in the revenues of private Coretime providers during the same period. In order to ensure this, then it is crucial that Instantaneous Coretime, once purchased, cannot be held indefinitely prior to eventual use since, if this were the case, a nefarious collator could purchase Coretime when cheap and utilize it some time later when expensive and deprive private Coretime providers of their revenue. It must therefore be assumed that Instantaneous Coretime, once purchased, has a definite and short \"shelf-life\", after which it becomes unusable. This incentivizes collators to avoid purchasing Coretime unless they expect to utilize it imminently and thus helps create an efficient market-feedback mechanism whereby a higher price will actually result in material revenues for private Coretime providers who contribute to the pool of Cores available to service Instantaneous Coretime purchases.","breadcrumbs":"RFC-1: Agile Coretime » Notes on the Instantaneous Coretime Market","id":"192","title":"Notes on the Instantaneous Coretime Market"},"193":{"body":"The specific pricing mechanisms are out of scope for the present proposal. Proposals on economics should be properly described and discussed in another RFC. However, for the sake of completeness, I provide some basic illustration of how price setting could potentially work. Bulk Price Progression The present proposal assumes the existence of a price-setting mechanism which takes into account several parameters: OLD_PRICE: The price of the previous sale. BULK_TARGET: the target number of cores to be purchased as Bulk Coretime Regions or renewed during the previous sale. BULK_LIMIT: the maximum number of cores which could have been purchased/renewed during the previous sale. CORES_SOLD: the actual number of cores purchased/renewed in the previous sale. SELLOUT_PRICE: the price at which the most recent Bulk Coretime was purchased ( not renewed) prior to selling more cores than BULK_TARGET (or immediately after, if none were purchased before). This may not have a value if no Bulk Coretime was purchased. In general we would expect the price to increase the closer CORES_SOLD gets to BULK_LIMIT and to decrease the closer it gets to zero. If it is exactly equal to BULK_TARGET, then we would expect the price to remain the same. In the edge case that no cores were purchased yet more cores were sold (through renewals) than the target, then we would also avoid altering the price. A simple example of this would be the formula: IF SELLOUT_PRICE == NULL AND CORES_SOLD > BULK_TARGET THEN RETURN OLD_PRICE\nEND IF\nEFFECTIVE_PRICE := IF CORES_SOLD > BULK_TARGET THEN SELLOUT_PRICE\nELSE OLD_PRICE\nEND IF\nNEW_PRICE := IF CORES_SOLD < BULK_TARGET THEN EFFECTIVE_PRICE * MAX(CORES_SOLD, 1) / BULK_TARGET\nELSE EFFECTIVE_PRICE + EFFECTIVE_PRICE * (CORES_SOLD - BULK_TARGET) / (BULK_LIMIT - BULK_TARGET)\nEND IF This exists only as a trivial example to demonstrate a basic solution exists, and should not be intended as a concrete proposal. Intra-Leadin Price-decrease During the Leadin Period of a sale, the effective price starts higher than the Sale Price and falls to end at the Sale Price at the end of the Leadin Period. The price can thus be defined as a simple factor above one on which the Sale Price is multiplied. A function which returns this factor would accept a factor between zero and one specifying the portion of the Leadin Period which has passed. Thus we assume SALE_PRICE, then we can define PRICE as: PRICE := SALE_PRICE * FACTOR((NOW - LEADIN_BEGIN) / LEADIN_PERIOD) We can define a very simple progression where the price decreases monotonically from double the Sale Price at the beginning of the Leadin Period. FACTOR(T) := 2 - T Parameter Values Parameters are either suggested or specified . If suggested , it is non-binding and the proposal should not be judged on the value since other RFCs and/or the governance mechanism of Polkadot is expected to specify/maintain it. If specified , then the proposal should be judged on the merit of the value as-is. Name Value BULK_PERIOD 28 * DAYS specified INTERLUDE_PERIOD 7 * DAYS specified LEADIN_PERIOD 7 * DAYS specified TIMESLICE 8 * MINUTES specified BULK_TARGET 30 suggested BULK_LIMIT 45 suggested RENEWAL_PRICE_CAP Perbill::from_percent(2) suggested Instantaneous Price Progression This proposal assumes the existence of a Relay-chain-based price-setting mechanism for the Instantaneous Coretime Market which alters from block to block, taking into account several parameters: the last price, the size of the Instantaneous Coretime Pool (in terms of cores per Relay-chain block) and the amount of Instantaneous Coretime waiting for processing (in terms of Core-blocks queued). The ideal situation is to have the size of the Instantaneous Coretime Pool be equal to some factor of the Instantaneous Coretime waiting. This allows all Instantaneous Coretime sales to be processed with some limited latency while giving limited flexibility over ordering to the Relay-chain apparatus which is needed for efficient operation. If we set a factor of three, and thus aim to retain a queue of Instantaneous Coretime Sales which can be processed within three Relay-chain blocks, then we would increase the price if the queue goes above three times the amount of cores available, and decrease if it goes under. Let us assume the values OLD_PRICE, FACTOR, QUEUE_SIZE and POOL_SIZE. A simple definition of the NEW_PRICE would be thus: NEW_PRICE := IF QUEUE_SIZE < POOL_SIZE * FACTOR THEN OLD_PRICE * 0.95\nELSE OLD_PRICE / 0.95\nEND IF This exists only as a trivial example to demonstrate a basic solution exists, and should not be intended as a concrete proposal.","breadcrumbs":"RFC-1: Agile Coretime » Notes on Economics","id":"193","title":"Notes on Economics"},"194":{"body":"This exists only as a short illustration of a potential technical implementation and should not be treated as anything more. Regions This data schema achieves a number of goals: Coretime can be individually traded at a level of a single usage of a single core. Coretime Regions, of arbitrary span and up to 1/80th interlacing can be exposed as NFTs and exchanged. Any Coretime Region can be contributed to the Instantaneous Coretime Pool. Unlimited number of individual Coretime contributors to the Instantaneous Coretime Pool. (Effectively limited only in number of cores and interlacing level; with current values this would allow 80,000 individual payees per timeslice). All keys are self-describing. Workload to communicate core (re-)assignments is well-bounded and low in weight. All mandatory bookkeeping workload is well-bounded in weight. type Timeslice = u32; // 80 block amounts.\ntype CoreIndex = u16;\ntype CoreMask = [u8; 10]; // 80-bit bitmap. // 128-bit (16 bytes)\nstruct RegionId { begin: Timeslice, core: CoreIndex, mask: CoreMask,\n}\n// 296-bit (37 bytes)\nstruct RegionRecord { end: Timeslice, owner: AccountId,\n} map Regions = Map; // 40-bit (5 bytes). Could be 32-bit with a more specialised type.\nenum CoreTask { Off, Assigned { target: TaskId }, InstaPool,\n}\n// 120-bit (15 bytes). Could be 14 bytes with a specialised 32-bit `CoreTask`.\nstruct ScheduleItem { mask: CoreMask, // 80 bit task: CoreTask, // 40 bit\n} /// The work we plan on having each core do at a particular time in the future.\ntype Workplan = Map<(Timeslice, CoreIndex), BoundedVec>;\n/// The current workload of each core. This gets updated with workplan as timeslices pass.\ntype Workload = Map>; enum Contributor { System, Private(AccountId),\n} struct ContributionRecord { begin: Timeslice, end: Timeslice, core: CoreIndex, mask: CoreMask, payee: Contributor,\n}\ntype InstaPoolContribution = Map; type SignedTotalMaskBits = u32;\ntype InstaPoolIo = Map; type PoolSize = Value; /// Counter for the total CoreMask which could be dedicated to a pool. `u32` so we don't ever get\n/// an overflow.\ntype TotalMaskBits = u32;\nstruct InstaPoolHistoryRecord { total_contributions: TotalMaskBits, maybe_payout: Option,\n}\n/// Total InstaPool rewards for each Timeslice and the number of core Mask which contributed.\ntype InstaPoolHistory = Map; CoreMask tracks unique \"parts\" of a single core. It is used with interlacing in order to give a unique identifier to each component of any possible interlacing configuration of a core, allowing for simple self-describing keys for all core ownership and allocation information. It also allows for each core's workload to be tracked and updated progressively, keeping ongoing compute costs well-bounded and low. Regions are issued into the Regions map and can be transferred, partitioned and interlaced as the owner desires. Regions can only be tasked if they begin after the current scheduling deadline (if they have missed this, then the region can be auto-trimmed until it is). Once tasked, they are removed from there and a record is placed in Workplan. In addition, if they are contributed to the Instantaneous Coretime Pool, then an entry is placing in InstaPoolContribution and InstaPoolIo. Each timeslice, InstaPoolIo is used to update the current value of PoolSize. A new entry in InstaPoolHistory is inserted, with the total_contributions field of InstaPoolHistoryRecord being informed by the PoolSize value. Each core's has its Workload mutated according to its Workplan for the upcoming timeslice. When Instantaneous Coretime Market Revenues are reported for a particular timeslice from the Relay-chain, this information gets placed in the maybe_payout field of the relevant record of InstaPoolHistory. Payments can be requested made for any records in InstaPoolContribution whose begin is the key for a value in InstaPoolHistory whose maybe_payout is Some. In this case, the total_contributions is reduced by the ContributionRecord's mask and a pro rata amount paid. The ContributionRecord is mutated by incrementing begin, or removed if begin becomes equal to end. Example: // Simple example with a `u16` `CoreMask` and bulk sold in 100 timeslices.\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// First split @ 50\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_1111_1111u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Share half of first 50 blocks\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Sell half of them to Bob\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob splits first 10 and assigns them to himself.\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1111_1111u16 } => { end: 110u32, owner: Bob };\n{ core: 0u16, begin: 110, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob shares first 10 3 ways and sells smaller shares to Charlie and Dave\nRegions:\n{ core: 0u16, begin: 100, mask: 0b1111_1111_0000_0000u16 } => { end: 150u32, owner: Alice };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_1100_0000u16 } => { end: 110u32, owner: Charlie };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_0011_0000u16 } => { end: 110u32, owner: Dave };\n{ core: 0u16, begin: 100, mask: 0b0000_0000_0000_1111u16 } => { end: 110u32, owner: Bob };\n{ core: 0u16, begin: 110, mask: 0b0000_0000_1111_1111u16 } => { end: 150u32, owner: Bob };\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\n// Bob assigns to his para B, Charlie and Dave assign to their paras C and D; Alice assigns first 50 to A\nRegions:\n{ core: 0u16, begin: 150, mask: 0b1111_1111_1111_1111u16 } => { end: 200u32, owner: Alice };\nWorkplan:\n(100, 0) => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\n(110, 0) => vec![{ mask: 0b0000_0000_1111_1111u16, task: Assigned(B) }]\n// Alice assigns her remaining 50 timeslices to the InstaPool paying herself:\nRegions: (empty)\nWorkplan:\n(100, 0) => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\n(110, 0) => vec![{ mask: 0b0000_0000_1111_1111u16, task: Assigned(B) }]\n(150, 0) => vec![{ mask: 0b1111_1111_1111_1111u16, task: InstaPool }]\nInstaPoolContribution:\n{ begin: 150, end: 200, core: 0, mask: 0b1111_1111_1111_1111u16, payee: Alice }\nInstaPoolIo:\n150 => 16\n200 => -16\n// Actual notifications to relay chain.\n// Assumes:\n// - Timeslice is 10 blocks.\n// - Timeslice 0 begins at block #1000.\n// - Relay needs 10 blocks notice of change.\n//\nWorkload: 0 => vec![]\nPoolSize: 0 // Block 990:\nRelay <= assign_core(core: 0u16, begin: 1000, assignment: vec![(A, 8), (C, 2), (D, 2), (B, 4)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1100_0000u16, task: Assigned(C) }, { mask: 0b0000_0000_0011_0000u16, task: Assigned(D) }, { mask: 0b0000_0000_0000_1111u16, task: Assigned(B) },\n]\nPoolSize: 0 // Block 1090:\nRelay <= assign_core(core: 0u16, begin: 1100, assignment: vec![(A, 8), (B, 8)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_0000_0000u16, task: Assigned(A) }, { mask: 0b0000_0000_1111_1111u16, task: Assigned(B) },\n]\nPoolSize: 0 // Block 1490:\nRelay <= assign_core(core: 0u16, begin: 1500, assignment: vec![(Pool, 16)])\nWorkload: 0 => vec![ { mask: 0b1111_1111_1111_1111u16, task: InstaPool },\n]\nPoolSize: 16\nInstaPoolIo:\n200 => -16\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: None } // Sometime after block 1500:\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: Some(P) } // Sometime after block 1990:\nInstaPoolIo: (empty)\nPoolSize: 0\nInstaPoolHistory:\n150 => { total_contributions: 16, maybe_payout: Some(P0) }\n151 => { total_contributions: 16, maybe_payout: Some(P1) }\n152 => { total_contributions: 16, maybe_payout: Some(P2) }\n...\n199 => { total_contributions: 16, maybe_payout: Some(P49) } // Sometime later still Alice calls for a payout\nInstaPoolContribution: (empty)\nInstaPoolHistory: (empty)\n// Alice gets rewarded P0 + P1 + ... P49.","breadcrumbs":"RFC-1: Agile Coretime » Notes on Types","id":"194","title":"Notes on Types"},"195":{"body":"Rollout of this proposal comes in several phases: Finalise the specifics of implementation; this may be done through a design document or through a well-documented prototype implementation. Implement the design, including all associated aspects such as unit tests, benchmarks and any support software needed. If any new parachain is required, launch of this. Formal audit of the implementation and any manual testing. Announcement to the various stakeholders of the imminent changes. Software integration and release. Governance upgrade proposal(s). Monitoring of the upgrade process.","breadcrumbs":"RFC-1: Agile Coretime » Rollout","id":"195","title":"Rollout"},"196":{"body":"No specific considerations. Parachains already deployed into the Polkadot UC must have a clear plan of action to migrate to an agile Coretime market. While this proposal does not introduce documentable features per se, adequate documentation must be provided to potential purchasers of Polkadot Coretime. This SHOULD include any alterations to the Polkadot-SDK software collection.","breadcrumbs":"RFC-1: Agile Coretime » Performance, Ergonomics and Compatibility","id":"196","title":"Performance, Ergonomics and Compatibility"},"197":{"body":"Regular testing through unit tests, integration tests, manual testnet tests, zombie-net tests and fuzzing SHOULD be conducted. A regular security review SHOULD be conducted prior to deployment through a review by the Web3 Foundation economic research group. Any final implementation MUST pass a professional external security audit. The proposal introduces no new privacy concerns.","breadcrumbs":"RFC-1: Agile Coretime » Testing, Security and Privacy","id":"197","title":"Testing, Security and Privacy"},"198":{"body":"RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain. RFC-5 proposes the API for interacting with Relay-chain. Additional work should specify the interface for the instantaneous market revenue so that the Coretime-chain can ensure Bulk Coretime placed in the instantaneous market is properly compensated.","breadcrumbs":"RFC-1: Agile Coretime » Future Directions and Related Material","id":"198","title":"Future Directions and Related Material"},"199":{"body":"Unknowns include the economic and resource parameterisations: The initial price of Bulk Coretime. The price-change algorithm between Bulk Coretime sales. The price increase per Bulk Coretime period for renewals. The price decrease graph in the Leadin period for Bulk Coretime sales. The initial price of Instantaneous Coretime. The price-change algorithm for Instantaneous Coretime sales. The percentage of cores to be sold as Bulk Coretime. The fate of revenue collected.","breadcrumbs":"RFC-1: Agile Coretime » Drawbacks, Alternatives and Unknowns","id":"199","title":"Drawbacks, Alternatives and Unknowns"},"2":{"body":"This RFC proposes a metadata format for XCM-identifiable assets (i.e., for fungible/non-fungible collections and non-fungible tokens) and a set of instructions to communicate it across chains.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Summary","id":"2","title":"Summary"},"20":{"body":"Runtime Developers Tools/UI Developers","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Stakeholders","id":"20","title":"Stakeholders"},"200":{"body":"Robert Habermeier initially wrote on the subject of Polkadot blockspace-centric in the article Polkadot Blockspace over Blockchains . While not going into details, the article served as an early reframing piece for moving beyond one-slot-per-chain models and building out secondary market infrastructure for resource allocation.","breadcrumbs":"RFC-1: Agile Coretime » Prior Art and References","id":"200","title":"Prior Art and References"},"201":{"body":"(source) Table of Contents RFC-5: Coretime Interface Summary Motivation Requirements Stakeholders Explanation UMP Message Types DMP Message Types Realistic Limits of the Usage Performance, Ergonomics and Compatibility Testing, Security and Privacy Future Directions and Related Material Drawbacks, Alternatives and Unknowns Prior Art and References Start Date 06 July 2023 Description Interface for manipulating the usage of cores on the Polkadot Ubiquitous Computer. Authors Gavin Wood, Robert Habermeier","breadcrumbs":"RFC-5: Coretime Interface » RFC-5: Coretime Interface","id":"201","title":"RFC-5: Coretime Interface"},"202":{"body":"In the Agile Coretime model of the Polkadot Ubiquitous Computer, as proposed in RFC-1 and RFC-3, it is necessary for the allocating parachain (envisioned to be one or more pallets on a specialised Brokerage System Chain) to communicate the core assignments to the Relay-chain, which is responsible for ensuring those assignments are properly enacted. This is a proposal for the interface which will exist around the Relay-chain in order to communicate this information and instructions.","breadcrumbs":"RFC-5: Coretime Interface » Summary","id":"202","title":"Summary"},"203":{"body":"The background motivation for this interface is splitting out coretime allocation functions and secondary markets from the Relay-chain onto System parachains. A well-understood and general interface is necessary for ensuring the Relay-chain receives coretime allocation instructions from one or more System chains without introducing dependencies on the implementation details of either side.","breadcrumbs":"RFC-5: Coretime Interface » Motivation","id":"203","title":"Motivation"},"204":{"body":"The interface MUST allow the Relay-chain to be scheduled on a low-latency basis. Individual cores MUST be schedulable, both in full to a single task (a ParaId or the Instantaneous Coretime Pool) or to many unique tasks in differing ratios. Typical usage of the interface SHOULD NOT overload the VMP message system. The interface MUST allow for the allocating chain to be notified of all accounting information relevant for making accurate rewards for contributing to the Instantaneous Coretime Pool. The interface MUST allow for Instantaneous Coretime Market Credits to be communicated. The interface MUST allow for the allocating chain to instruct changes to the number of cores which it is able to allocate. The interface MUST allow for the allocating chain to be notified of changes to the number of cores which are able to be allocated by the allocating chain.","breadcrumbs":"RFC-5: Coretime Interface » Requirements","id":"204","title":"Requirements"},"205":{"body":"Primary stakeholder sets are: Developers of the Relay-chain core-management logic. Developers of the Brokerage System Chain and its pallets. Socialization: This content of this RFC was discussed in the Polkdot Fellows channel.","breadcrumbs":"RFC-5: Coretime Interface » Stakeholders","id":"205","title":"Stakeholders"},"206":{"body":"The interface has two sections: The messages which the Relay-chain is able to receive from the allocating parachain (the UMP message types ), and messages which the Relay-chain is able to send to the allocating parachain (the DMP message types ). These messages are expected to be able to be implemented in a well-known pallet and called with the XCM Transact instruction. Future work may include these messages being introduced into the XCM standard.","breadcrumbs":"RFC-5: Coretime Interface » Explanation","id":"206","title":"Explanation"},"207":{"body":"request_core_count Prototype: fn request_core_count( count: u16,\n) Requests the Relay-chain to alter the number of schedulable cores to count. Under normal operation, the Relay-chain SHOULD send a notify_core_count(count) message back. request_revenue_info_at Prototype: fn request_revenue_at( when: BlockNumber,\n) Requests that the Relay-chain send a notify_revenue message back at or soon after Relay-chain block number when whose until parameter is equal to when. The period in to the past which when is allowed to be may be limited; if so the limit should be understood on a channel outside of this proposal. In the case that the request cannot be serviced because when is too old a block then a notify_revenue message must still be returned, but its revenue field may be None. credit_account Prototype: fn credit_account( who: AccountId, amount: Balance,\n) Instructs the Relay-chain to add the amount of DOT to the Instantaneous Coretime Market Credit account of who. It is expected that Instantaneous Coretime Market Credit on the Relay-chain is NOT transferrable and only redeemable when used to assign cores in the Instantaneous Coretime Pool. assign_core Prototype: type PartsOf57600 = u16;\nenum CoreAssignment { InstantaneousPool, Task(ParaId),\n}\nfn assign_core( core: CoreIndex, begin: BlockNumber, assignment: Vec<(CoreAssignment, PartsOf57600)>, end_hint: Option,\n) Requirements: assert!(core < core_count);\nassert!(targets.iter().map(|x| x.0).is_sorted());\nassert_eq!(targets.iter().map(|x| x.0).unique().count(), targets.len());\nassert_eq!(targets.iter().map(|x| x.1).sum(), 57600); Where: core_count is assumed to be the sole parameter in the last received notify_core_count message. Instructs the Relay-chain to ensure that the core indexed as core is utilised for a number of assignments in specific ratios given by assignment starting as soon after begin as possible. Core assignments take the form of a CoreAssignment value which can either task the core to a ParaId value or indicate that the core should be used in the Instantaneous Pool. Each assignment comes with a ratio value, represented as the numerator of the fraction with a denominator of 57,600. If end_hint is Some and the inner is greater than the current block number, then the Relay-chain should optimize in the expectation of receiving a new assign_core(core, ...) message at or prior to the block number of the inner value. Specific functionality should remain unchanged regardless of the end_hint value. On the choice of denominator: 57,600 is a very composite number which factors into: 2 ** 8, 3 ** 2, 5 ** 2. By using it as the denominator we allow for various useful fractions to be perfectly represented including thirds, quarters, fifths, tenths, 80ths, percent and 256ths.","breadcrumbs":"RFC-5: Coretime Interface » UMP Message Types","id":"207","title":"UMP Message Types"},"208":{"body":"notify_core_count Prototype: fn notify_core_count( count: u16,\n) Indicate that from this block onwards, the range of acceptable values of the core parameter of assign_core message is [0, count). assign_core will be a no-op if provided with a value for core outside of this range. notify_revenue_info Prototype: fn notify_revenue_info( until: BlockNumber, revenue: Option,\n) Provide the amount of revenue accumulated from Instantaneous Coretime Sales from Relay-chain block number last_until to until, not including until itself. last_until is defined as being the until argument of the last notify_revenue message sent, or zero for the first call. If revenue is None, this indicates that the information is no longer available. This explicitly disregards the possibility of multiple parachains requesting and being notified of revenue information. The Relay-chain must be configured to ensure that only a single revenue information destination exists.","breadcrumbs":"RFC-5: Coretime Interface » DMP Message Types","id":"208","title":"DMP Message Types"},"209":{"body":"For request_revenue_info, a successful request should be possible if when is no less than the Relay-chain block number on arrival of the message less 100,000. For assign_core, a successful request should be possible if begin is no less than the Relay-chain block number on arrival of the message plus 10 and workload contains no more than 100 items.","breadcrumbs":"RFC-5: Coretime Interface » Realistic Limits of the Usage","id":"209","title":"Realistic Limits of the Usage"},"21":{"body":"The overall query pattern of the XCQ consists of three components: Runtime: View-functions across different pallets are amalgamated through an extension-based system. XCQ query: Custom computations over view-function results are encapsulated via PolkaVM programs. XCQ query arguments: Query arguments like accounts to be queried are also passed together with the query program.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Explanation","id":"21","title":"Explanation"},"210":{"body":"No specific considerations.","breadcrumbs":"RFC-5: Coretime Interface » Performance, Ergonomics and Compatibility","id":"210","title":"Performance, Ergonomics and Compatibility"},"211":{"body":"Standard Polkadot testing and security auditing applies. The proposal introduces no new privacy concerns.","breadcrumbs":"RFC-5: Coretime Interface » Testing, Security and Privacy","id":"211","title":"Testing, Security and Privacy"},"212":{"body":"RFC-1 proposes a means of determining allocation of Coretime using this interface. RFC-3 proposes a means of implementing the high-level allocations within the Relay-chain.","breadcrumbs":"RFC-5: Coretime Interface » Future Directions and Related Material","id":"212","title":"Future Directions and Related Material"},"213":{"body":"None at present.","breadcrumbs":"RFC-5: Coretime Interface » Drawbacks, Alternatives and Unknowns","id":"213","title":"Drawbacks, Alternatives and Unknowns"},"214":{"body":"None.","breadcrumbs":"RFC-5: Coretime Interface » Prior Art and References","id":"214","title":"Prior Art and References"},"215":{"body":"(source) Table of Contents RFC-0007: System Collator Selection Summary Motivation Requirements Stakeholders Explanation Set Size Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Written Discussions Prior Feedback and Input From Unresolved Questions Future Directions and Related Material Start Date 07 July 2023 Description Mechanism for selecting collators of system chains. Authors Joe Petrowski","breadcrumbs":"RFC-0007: System Collator Selection » RFC-0007: System Collator Selection","id":"215","title":"RFC-0007: System Collator Selection"},"216":{"body":"As core functionality moves from the Relay Chain into system chains, so increases the reliance on the liveness of these chains for the use of the network. It is not economically scalable, nor necessary from a game-theoretic perspective, to pay collators large rewards. This RFC proposes a mechanism -- part technical and part social -- for ensuring reliable collator sets that are resilient to attemps to stop any subsytem of the Polkadot protocol.","breadcrumbs":"RFC-0007: System Collator Selection » Summary","id":"216","title":"Summary"},"217":{"body":"In order to guarantee access to Polkadot's system, the collators on its system chains must propose blocks (provide liveness) and allow all transactions to eventually be included. That is, some collators may censor transactions, but there must exist one collator in the set who will include a given transaction. In fact, all collators may censor varying subsets of transactions, but as long as no transaction is in the intersection of every subset, it will eventually be included. The objective of this RFC is to propose a mechanism to select such a set on each system chain. While the network as a whole uses staking (and inflationary rewards) to attract validators, collators face different challenges in scale and have lower security assumptions than validators. Regarding scale, there exist many system chains, and it is economically expensive to pay collators a premium. Likewise, any staked DOT for collation is not staked for validation. Since collator sets do not need to meet Byzantine Fault Tolerance criteria, staking as the primary mechanism for collator selection would remove stake that is securing BFT assumptions, making the network less secure. Another problem with economic scalability relates to the increasing number of system chains, and corresponding increase in need for collators (i.e., increase in collator slots). \"Good\" (highly available, non-censoring) collators will not want to compete in elections on many chains when they could use their resources to compete in the more profitable validator election. Such dilution decreases the required bond on each chain, leaving them vulnerable to takeover by hostile collator groups. This RFC proposes a system whereby collation is primarily an infrastructure service, with the on-chain Treasury reimbursing costs of semi-trusted node operators, referred to as \"Invulnerables\". The system need not trust the individual operators, only that as a set they would be resilient to coordinated attempts to stop a single chain from halting or to censor a particular subset of transactions. In the case that users do not trust this set, this RFC also proposes that each chain always have available collator positions that can be acquired by anyone by placing a bond.","breadcrumbs":"RFC-0007: System Collator Selection » Motivation","id":"217","title":"Motivation"},"218":{"body":"System MUST have at least one valid collator for every chain. System MUST allow anyone to become a collator, provided they reserve/hold enough DOT. System SHOULD select a set of collators with reasonable expectation that the set will not collude to censor any subset of transactions. Collators selected by governance SHOULD have a reasonable expectation that the Treasury will reimburse their operating costs.","breadcrumbs":"RFC-0007: System Collator Selection » Requirements","id":"218","title":"Requirements"},"219":{"body":"Infrastructure providers (people who run validator/collator nodes) Polkadot Treasury","breadcrumbs":"RFC-0007: System Collator Selection » Stakeholders","id":"219","title":"Stakeholders"},"22":{"body":"The runtime API for off-chain query usage includes two methods: execute_query: Executes the query and returns the result. It takes the query, input, and weight limit as arguments. The query is the query program in PolkaVM program binary format. The input is the query arguments that is SCALE-encoded. The weight limit is the maximum weight allowed for the query execution. metadata: Return metadata of supported extensions (introduced in later section) and methods, serving as a feature discovery functionality Example XCQ Runtime API : decl_runtime_apis! { pub trait XcqApi { fn execute_query(query: Vec, input: Vec, weight_limit: u64) -> XcqResult; fn metadata() -> Vec; }\n}\ntype XcqResult = Result;\ntype XcqResponse = Vec;\nenum XcqError { Custom(String),\n} Example metadata : Metadata { extensions: vec![ ExtensionMetadata { name: \"ExtensionCore\", methods: vec![MethodMetadata { name: \"has_extension\", inputs: vec![MethodParamMetadata { name: \"id\", ty: XcqType::Primitive(PrimitiveType::U64) }], output: XcqType::Primitive(PrimitiveType::Bool) }] }, ExtensionMetadata { name: \"ExtensionFungibles\", methods: vec![ MethodMetadata { name: \"total_supply\", inputs: vec![MethodParamMetadata { name: \"asset\", ty: XcqType::Primitive(PrimitiveType::U32) }], output: XcqType::Primitive(PrimitiveType::U64) }, MethodMetadata { name: \"balance\", inputs: vec![ MethodParamMetadata { name: \"asset\", ty: XcqType::Primitive(PrimitiveType::U32) }, MethodParamMetadata { name: \"who\", ty: XcqType::Primitive(PrimitiveType::H256) } ], output: XcqType::Primitive(PrimitiveType::U64) } ] } ]\n} Note: ty is represented by a meta-type system called xcq-types xcq-types xcq-types is a meta-type system similar to scale-info but simpler. It enables different chains with different type definitions to work via a common operation. Front-end codes constructs call data to XCQ programs according to metadata provided by different chains.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Runtime API","id":"22","title":"XCQ Runtime API"},"220":{"body":"This protocol builds on the existing Collator Selection pallet and its notion of Invulnerables. Invulnerables are collators (identified by their AccountIds) who will be selected as part of the collator set every session. Operations relating to the management of the Invulnerables are done through privileged, governance origins. The implementation should maintain an API for adding and removing Invulnerable collators. In addition to Invulnerables, there are also open slots for \"Candidates\". Anyone can register as a Candidate by placing a fixed bond. However, with a fixed bond and fixed number of slots, there is an obvious selection problem: The slots fill up without any logic to replace their occupants. This RFC proposes that the collator selection protocol allow Candidates to increase (and decrease) their individual bonds, sort the Candidates according to bond, and select the top N Candidates. The selection and changeover should be coordinated by the session manager. A FRAME pallet already exists for sorting (\"bagging\") \"top N\" groups, the Bags List pallet . This pallet's SortedListProvider should be integrated into the session manager of the Collator Selection pallet. Despite the lack of apparent economic incentives (i.e., inflation), several reasons exist why one may want to bond funds to participate in the Candidates election, for example: They want to build credibility to be selected as Invulnerable; They want to ensure availability of an application, e.g. a stablecoin issuer might run a collator on Asset Hub to ensure transactions in its asset are included in blocks; They fear censorship themselves, e.g. a voter might think their votes are being censored from governance, so they run a collator on the governance chain to include their votes. Unlike the fixed-bond mechanism that fills up its Candidates, the election mechanism ensures that anyone can join the collator set by placing the Nth highest bond.","breadcrumbs":"RFC-0007: System Collator Selection » Explanation","id":"220","title":"Explanation"},"221":{"body":"In order to achieve the requirements listed under Motivation , it is reasonable to have approximately: 20 collators per system chain, of which 15 are Invulnerable, and five are elected by bond.","breadcrumbs":"RFC-0007: System Collator Selection » Set Size","id":"221","title":"Set Size"},"222":{"body":"The primary drawback is a reliance on governance for continued treasury funding of infrastructure costs for Invulnerable collators.","breadcrumbs":"RFC-0007: System Collator Selection » Drawbacks","id":"222","title":"Drawbacks"},"223":{"body":"The vast majority of cases can be covered by unit testing. Integration test should ensure that the Collator Selection UpdateOrigin, which has permission to modify the Invulnerables and desired number of Candidates, can handle updates over XCM from the system's governance location.","breadcrumbs":"RFC-0007: System Collator Selection » Testing, Security, and Privacy","id":"223","title":"Testing, Security, and Privacy"},"224":{"body":"This proposal has very little impact on most users of Polkadot, and should improve the performance of system chains by reducing the number of missed blocks.","breadcrumbs":"RFC-0007: System Collator Selection » Performance, Ergonomics, and Compatibility","id":"224","title":"Performance, Ergonomics, and Compatibility"},"225":{"body":"As chains have strict PoV size limits, care must be taken in the PoV impact of the session manager. Appropriate benchmarking and tests should ensure that conservative limits are placed on the number of Invulnerables and Candidates.","breadcrumbs":"RFC-0007: System Collator Selection » Performance","id":"225","title":"Performance"},"226":{"body":"The primary group affected is Candidate collators, who, after implementation of this RFC, will need to compete in a bond-based election rather than a race to claim a Candidate spot.","breadcrumbs":"RFC-0007: System Collator Selection » Ergonomics","id":"226","title":"Ergonomics"},"227":{"body":"This RFC is compatible with the existing implementation and can be handled via upgrades and migration.","breadcrumbs":"RFC-0007: System Collator Selection » Compatibility","id":"227","title":"Compatibility"},"228":{"body":"","breadcrumbs":"RFC-0007: System Collator Selection » Prior Art and References","id":"228","title":"Prior Art and References"},"229":{"body":"GitHub: Collator Selection Roadmap GitHub: Revisit Collator Selection Mechanism Polkadot Forum: Economic Model for System Para Collators","breadcrumbs":"RFC-0007: System Collator Selection » Written Discussions","id":"229","title":"Written Discussions"},"23":{"body":"An XCQ executor is a runtime module that executes XCQ queries. It has a core method execute that takes a PolkaVM program binary, method name of the exported functions in the PolkaVM program, input arguments, and weight limit that the PolkaVM program can consume. pub fn execute( &mut self, raw_blob: &[u8], method: &str, input: &[u8], weight_limit: u64,\n) -> Result, XcqExecutorError> {...}","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Executor","id":"23","title":"XCQ Executor"},"230":{"body":"Kian Paimani Jeff Burdges Rob Habermeier SR Labs Auditors Current collators including Paranodes, Stake Plus, Turboflakes, Peter Mensik, SIK, and many more.","breadcrumbs":"RFC-0007: System Collator Selection » Prior Feedback and Input From","id":"230","title":"Prior Feedback and Input From"},"231":{"body":"None at this time.","breadcrumbs":"RFC-0007: System Collator Selection » Unresolved Questions","id":"231","title":"Unresolved Questions"},"232":{"body":"There may exist in the future system chains for which this model of collator selection is not appropriate. These chains should be evaluated on a case-by-case basis.","breadcrumbs":"RFC-0007: System Collator Selection » Future Directions and Related Material","id":"232","title":"Future Directions and Related Material"},"233":{"body":"(source) Table of Contents RFC-0008: Store parachain bootnodes in relay chain DHT Summary Motivation Stakeholders Explanation DHT provider registration New networking protocol Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-07-14 Description Parachain bootnodes shall register themselves in the DHT of the relay chain Authors Pierre Krieger","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » RFC-0008: Store parachain bootnodes in relay chain DHT","id":"233","title":"RFC-0008: Store parachain bootnodes in relay chain DHT"},"234":{"body":"The full nodes of the Polkadot peer-to-peer network maintain a distributed hash table (DHT), which is currently used for full nodes discovery and validators discovery purposes. This RFC proposes to extend this DHT to be used to discover full nodes of the parachains of Polkadot.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Summary","id":"234","title":"Summary"},"235":{"body":"The maintenance of bootnodes has long been an annoyance for everyone. When a bootnode is newly-deployed or removed, every chain specification must be updated in order to take the update into account. This has lead to various non-optimal solutions, such as pulling chain specifications from GitHub repositories. When it comes to RPC nodes, UX developers often have trouble finding up-to-date addresses of parachain RPC nodes. With the ongoing migration from RPC nodes to light clients, similar problems would happen with chain specifications as well. Furthermore, there exists multiple different possible variants of a certain chain specification: with the non-raw storage, with the raw storage, with just the genesis trie root hash, with or without checkpoint, etc. All of this creates confusion. Removing the need for parachain developers to be aware of and manage these different versions would be beneficial. Since the PeerId and addresses of bootnodes needs to be stable, extra maintenance work is required from the chain maintainers. For example, they need to be extra careful when migrating nodes within their infrastructure. In some situations, bootnodes are put behind domain names, which also requires maintenance work. Because the list of bootnodes in chain specifications is so annoying to modify, the consequence is that the number of bootnodes is rather low (typically between 2 and 15). In order to better resist downtimes and DoS attacks, a better solution would be to use every node of a certain chain as potential bootnode, rather than special-casing some specific nodes. While this RFC doesn't solve these problems for relay chains, it aims at solving it for parachains by storing the list of all the full nodes of a parachain on the relay chain DHT. Assuming that this RFC is implemented, and that light clients are used, deploying a parachain wouldn't require more work than registering it onto the relay chain and starting the collators. There wouldn't be any need for special infrastructure nodes anymore.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Motivation","id":"235","title":"Motivation"},"236":{"body":"This RFC has been opened on my own initiative because I think that this is a good technical solution to a usability problem that many people are encountering and that they don't realize can be solved.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Stakeholders","id":"236","title":"Stakeholders"},"237":{"body":"The content of this RFC only applies for parachains and parachain nodes that are \"Substrate-compatible\". It is in no way mandatory for parachains to comply to this RFC. Note that \"Substrate-compatible\" is very loosely defined as \"implements the same mechanisms and networking protocols as Substrate\". The author of this RFC believes that \"Substrate-compatible\" should be very precisely specified, but there is controversy on this topic. While a lot of this RFC concerns the implementation of parachain nodes, it makes use of the resources of the Polkadot chain, and as such it is important to describe them in the Polkadot specification. This RFC adds two mechanisms: a registration in the DHT, and a new networking protocol.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Explanation","id":"237","title":"Explanation"},"238":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . Full nodes of a parachain registered on Polkadot should register themselves onto the Polkadot DHT as the providers of a key corresponding to the parachain that they are serving, as described in the Content provider advertisement section of the specification. This uses the ADD_PROVIDER system of libp2p-kademlia. This key is: sha256(concat(scale_compact(para_id), randomness)) where the value of randomness can be found in the randomness field when calling the BabeApi_currentEpoch function. For example, for a para_id equal to 1000, and at the time of writing of this RFC (July 14th 2023 at 09:13 UTC), it is sha(0xa10f12872447958d50aa7b937b0106561a588e0e2628d33f81b5361b13dbcf8df708), which is equal to 0x483dd8084d50dbbbc962067f216c37b627831d9339f5a6e426a32e3076313d87. In order to avoid downtime when the key changes, parachain full nodes should also register themselves as a secondary key that uses a value of randomness equal to the randomness field when calling BabeApi_nextEpoch. Implementers should be aware that their implementation of Kademlia might already hash the key before XOR'ing it. The key is not meant to be hashed twice. The compact SCALE encoding has been chosen in order to avoid problems related to the number of bytes and endianness of the para_id.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » DHT provider registration","id":"238","title":"DHT provider registration"},"239":{"body":"A new request-response protocol should be added, whose name is /91b171bb158e2d3848fa23a9f1c25182fb8e20313b2c1eb49219da7a70ce90c3/paranode (that hexadecimal number is the genesis hash of the Polkadot chain, and should be adjusted appropriately for Kusama and others). The request consists in a SCALE-compact-encoded para_id. For example, for a para_id equal to 1000, this is 0xa10f. Note that because this is a request-response protocol, the request is always prefixed with its length in bytes. While the body of the request is simply the SCALE-compact-encoded para_id, the data actually sent onto the substream is both the length and body. The response consists in a protobuf struct, defined as: syntax = \"proto2\"; message Response { // Peer ID of the node on the parachain side. bytes peer_id = 1; // Multiaddresses of the parachain side of the node. The list and format are the same as for the `listenAddrs` field of the `identify` protocol. repeated bytes addrs = 2; // Genesis hash of the parachain. Used to determine the name of the networking protocol to connect to the parachain. Untrusted. bytes genesis_hash = 3; // So-called \"fork ID\" of the parachain. Used to determine the name of the networking protocol to connect to the parachain. Untrusted. optional string fork_id = 4;\n}; The maximum size of a response is set to an arbitrary 16kiB. The responding side should make sure to conform to this limit. Given that fork_id is typically very small and that the only variable-length field is addrs, this is easily achieved by limiting the number of addresses. Implementers should be aware that addrs might be very large, and are encouraged to limit the number of addrs to an implementation-defined value.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » New networking protocol","id":"239","title":"New networking protocol"},"24":{"body":"An extension-based design is essential for several reasons: Different chains may have different data types for semantically similar queries, making it challenging to standardize function calls across them. An extension-based design with optional associated types allows these diverse data types to be specified and utilized effectively. Function calls distributed across various pallets can be amalgamated into a single extension, simplifying the development process and ensuring a more cohesive and maintainable codebase. New functionalities can be added without upgrading the core part of the XCQ. Ensure the core part is in a minimal scope. Essential components of an XCQ extension system include: A hash-based extension id generation mechanism for addressing and versioning . The hash value derives from the extension name and its method sets. Any update to an extension is treated as a new extension. decl_extension macro: Defines an extension as a Rust trait with optional associated types. Example usage : use xcq_extension::decl_extension; pub trait Config { type AssetId: Codec; type AccountId: Codec; type Balance: Codec;\n}\ndecl_extension! { pub trait ExtensionFungibles { type Config: Config; fn total_supply(asset: ::AssetId) -> ::Balance; fn balance(asset: ::AssetId, who: ::AccountId) -> ::Balance; }\n} impl_extensions macro: Generates extension implementations and extension-level metadata. Example Usage : // ExtensionImpl is an aggregate struct to impl different extensions\nstruct ExtensionImpl;\nimpl extension_fungibles::Config for ExtensionImpl { type AssetId = u32; type AccountId = [u8; 32]; type Balance = u64;\n}\nimpl_extensions! { impl extension_core::ExtensionCore for ExtensionImpl { type Config = ExtensionImpl; fn has_extension(id: ::ExtensionId) -> bool { matches!(id, 0 | 1) } } impl extension_fungibles::ExtensionFungibles for ExtensionImpl { type Config = ExtensionImpl; #[allow(unused_variables)] fn total_supply(asset: ::AssetId) -> ::Balance { 200 } #[allow(unused_variables)] fn balance(asset: ::AssetId, who: ::AccountId) -> ::Balance { 100 } }\n} ExtensionExecutor: Connects extension implementations and xcq-executor. All methods of all extensions that a chain supports are amalgamated into a single host_call entry. Then this entry is registered as a typed function entry in PolkaVM Linker within the xcq-executor. Given the extension ID and call data encoded in SCALE format, call requests from the guest XCQ program are dispatched to corresponding extensions: linker .define_typed( \"host_call\", move |caller: Caller<'_, Self::UserData>, extension_id: u64, call_ptr: u32, call_len: u32| -> Result { ... }); PermController: Filters guest XCQ program calling requests, useful for host chains to disable some queries by filtering invoking sources. pub trait PermController { fn is_allowed(extension_id: ExtensionIdTy, call: &[u8], source: InvokeSource) -> bool;\n}\n#[derive(Copy, Clone)]\npub enum InvokeSource { RuntimeAPI, XCM, Extrinsic, Runtime,\n}","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Extension","id":"24","title":"XCQ Extension"},"240":{"body":"The peer_id and addrs fields are in theory not strictly needed, as the PeerId and addresses could be always equal to the PeerId and addresses of the node being registered as the provider and serving the response. However, the Cumulus implementation currently uses two different networking stacks, one of the parachain and one for the relay chain, using two separate PeerIds and addresses, and as such the PeerId and addresses of the other networking stack must be indicated. Asking them to use only one networking stack wouldn't feasible in a realistic time frame. The values of the genesis_hash and fork_id fields cannot be verified by the requester and are expected to be unused at the moment. Instead, a client that desires connecting to a parachain is expected to obtain the genesis hash and fork ID of the parachain from the parachain chain specification. These fields are included in the networking protocol nonetheless in case an acceptable solution is found in the future, and in order to allow use cases such as discovering parachains in a not-strictly-trusted way.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Drawbacks","id":"240","title":"Drawbacks"},"241":{"body":"Because not all nodes want to be used as bootnodes, implementers are encouraged to provide a way to disable this mechanism. However, it is very much encouraged to leave this mechanism on by default for all parachain nodes. This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms. However, if the principle of chain specification bootnodes is entirely replaced with the mechanism described in this RFC (which is the objective), then it becomes important whether the mechanism in this RFC can be abused in order to make a parachain unreachable. Due to the way Kademlia works, it would become the responsibility of the 20 Polkadot nodes whose sha256(peer_id) is closest to the key (described in the explanations section) to store the list of bootnodes of each parachain. Furthermore, when a large number of providers (here, a provider is a bootnode) are registered, only the providers closest to the key are kept, up to a certain implementation-defined limit. For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target parachain. They are then in control of the parachain bootnodes. Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term. Furthermore, parachain clients are expected to cache a list of known good nodes on their disk. If the mechanism described in this RFC went down, it would only prevent new nodes from accessing the parachain, while clients that have connected before would not be affected.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Testing, Security, and Privacy","id":"241","title":"Testing, Security, and Privacy"},"242":{"body":"","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Performance, Ergonomics, and Compatibility","id":"242","title":"Performance, Ergonomics, and Compatibility"},"243":{"body":"The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours. Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode. Assuming 1000 parachain full nodes, the 20 Polkadot full nodes corresponding to a specific parachain will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a parachain full node registers itself to be the provider of the key corresponding to BabeApi_next_epoch. Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the bootnodes of a parachain. Light clients are generally encouraged to cache the peers that they use between restarts, so they should only query these 20 Polkadot full nodes at their first initialization. If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Performance","id":"243","title":"Performance"},"244":{"body":"Irrelevant.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Ergonomics","id":"244","title":"Ergonomics"},"245":{"body":"Irrelevant.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Compatibility","id":"245","title":"Compatibility"},"246":{"body":"None.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Prior Art and References","id":"246","title":"Prior Art and References"},"247":{"body":"While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Unresolved Questions","id":"247","title":"Unresolved Questions"},"248":{"body":"It is possible that in the future a client could connect to a parachain without having to rely on a trusted parachain specification.","breadcrumbs":"RFC-0008: Store parachain bootnodes in relay chain DHT » Future Directions and Related Material","id":"248","title":"Future Directions and Related Material"},"249":{"body":"(source) Table of Contents RFC-0010: Burn Coretime Revenue Summary Motivation Stakeholders Explanation Start Date 19.07.2023 Description Revenue from Coretime sales should be burned Authors Jonas Gehrlein","breadcrumbs":"RFC-0010: Burn Coretime Revenue » RFC-0010: Burn Coretime Revenue","id":"249","title":"RFC-0010: Burn Coretime Revenue"},"25":{"body":"An XCQ program is structured as a PolkaVM program with the following key components: Imported Functions: host_call: Dispatches call requests to the XCQ Extension Executor. #[polkavm_derive::polkavm_import]\nextern \"C\" { fn host_call(extension_id: u64, call_ptr: u32, call_len: u32) -> u64;\n} Results are SCALE-encoded bytes, with the pointer address (lower 32 bits) and length (higher 32 bits) packed into a u64. return_ty: Returns the type of the function call result. #[polkavm_derive::polkavm_import]\nextern \"C\" { fn return_ty(extension_id: u64, call_index: u32) -> u64;\n} Results are SCALE-encoded bytes, with the pointer address and length packed similarly to host_call. Exported Functions: main: The entry point of the XCQ program. It performs type checking, arguments and results passing and executes the query.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Program Structure","id":"25","title":"XCQ Program Structure"},"250":{"body":"The Polkadot UC will generate revenue from the sale of available Coretime. The question then arises: how should we handle these revenues? Broadly, there are two reasonable paths – burning the revenue and thereby removing it from total issuance or divert it to the Treasury. This Request for Comment (RFC) presents arguments favoring burning as the preferred mechanism for handling revenues from Coretime sales.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Summary","id":"250","title":"Summary"},"251":{"body":"How to handle the revenue accrued from Coretime sales is an important economic question that influences the value of DOT and should be properly discussed before deciding for either of the options. Now is the best time to start this discussion.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Motivation","id":"251","title":"Motivation"},"252":{"body":"Polkadot DOT token holders.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Stakeholders","id":"252","title":"Stakeholders"},"253":{"body":"This RFC discusses potential benefits of burning the revenue accrued from Coretime sales instead of diverting them to Treasury. Here are the following arguments for it. It's in the interest of the Polkadot community to have a consistent and predictable Treasury income, because volatility in the inflow can be damaging, especially in situations when it is insufficient. As such, this RFC operates under the presumption of a steady and sustainable Treasury income flow, which is crucial for the Polkadot community's stability. The assurance of a predictable Treasury income, as outlined in a prior discussion here , or through other equally effective measures, serves as a baseline assumption for this argument. Consequently, we need not concern ourselves with this particular issue here. This naturally begs the question - why should we introduce additional volatility to the Treasury by aligning it with the variable Coretime sales? It's worth noting that Coretime revenues often exhibit an inverse relationship with periods when Treasury spending should ideally be ramped up. During periods of low Coretime utilization (indicated by lower revenue), Treasury should spend more on projects and endeavours to increase the demand for Coretime. This pattern underscores that Coretime sales, by their very nature, are an inconsistent and unpredictable source of funding for the Treasury. Given the importance of maintaining a steady and predictable inflow, it's unnecessary to rely on another volatile mechanism. Some might argue that we could have both: a steady inflow (from inflation) and some added bonus from Coretime sales, but burning the revenue would offer further benefits as described below. Balancing Inflation: While DOT as a utility token inherently profits from a (reasonable) net inflation, it also benefits from a deflationary force that functions as a counterbalance to the overall inflation. Right now, the only mechanism on Polkadot that burns fees is the one for underutilized DOT in the Treasury. Finding other, more direct target for burns makes sense and the Coretime market is a good option. Clear incentives: By burning the revenue accrued on Coretime sales, prices paid by buyers are clearly costs. This removes distortion from the market that might arise when the paid tokens occur on some other places within the network. In that case, some actors might have secondary motives of influencing the price of Coretime sales, because they benefit down the line. For example, actors that actively participate in the Coretime sales are likely to also benefit from a higher Treasury balance, because they might frequently request funds for their projects. While those effects might appear far-fetched, they could accumulate. Burning the revenues makes sure that the prices paid are clearly costs to the actors themselves. Collective Value Accrual: Following the previous argument, burning the revenue also generates some externality, because it reduces the overall issuance of DOT and thereby increases the value of each remaining token. In contrast to the aforementioned argument, this benefits all token holders collectively and equally. Therefore, I'd consider this as the preferrable option, because burns lets all token holders participate at Polkadot's success as Coretime usage increases.","breadcrumbs":"RFC-0010: Burn Coretime Revenue » Explanation","id":"253","title":"Explanation"},"254":{"body":"(source) Table of Contents RFC-0012: Process for Adding New System Collectives Summary Motivation Stakeholders Explanation Removing Collectives Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Start Date 24 July 2023 Description A process for adding new (and removing existing) system collectives. Authors Joe Petrowski","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » RFC-0012: Process for Adding New System Collectives","id":"254","title":"RFC-0012: Process for Adding New System Collectives"},"255":{"body":"Since the introduction of the Collectives parachain, many groups have expressed interest in forming new -- or migrating existing groups into -- on-chain collectives. While adding a new collective is relatively simple from a technical standpoint, the Fellowship will need to merge new pallets into the Collectives parachain for each new collective. This RFC proposes a means for the network to ratify a new collective, thus instructing the Fellowship to instate it in the runtime.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Summary","id":"255","title":"Summary"},"256":{"body":"Many groups have expressed interest in representing collectives on-chain. Some of these include: Parachain technical fellowship (new) Fellowship(s) for media, education, and evangelism (new) Polkadot Ambassador Program (existing) Anti-Scam Team (existing) Collectives that form part of the core Polkadot protocol should have a mandate to serve the Polkadot network. However, as part of the Polkadot protocol, the Fellowship, in its capacity of maintaining system runtimes, will need to include modules and configurations for each collective. Once a group has developed a value proposition for the Polkadot network, it should have a clear path to having its collective accepted on-chain as part of the protocol. Acceptance should direct the Fellowship to include the new collective with a given initial configuration into the runtime. However, the network, not the Fellowship, should ultimately decide which collectives are in the interest of the network.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Motivation","id":"256","title":"Motivation"},"257":{"body":"Polkadot stakeholders who would like to organize on-chain. Technical Fellowship, in its role of maintaining system runtimes.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Stakeholders","id":"257","title":"Stakeholders"},"258":{"body":"The group that wishes to operate an on-chain collective should publish the following information: Charter, including the collective's mandate and how it benefits Polkadot. This would be similar to the Fellowship Manifesto . Seeding recommendation. Member types, i.e. should members be individuals or organizations. Member management strategy, i.e. how do members join and get promoted, if applicable. How much, if at all, members should get paid in salary. Any special origins this Collective should have outside its self. For example, the Fellowship can whitelist calls for referenda via the WhitelistOrigin. This information could all be in a single document or, for example, a GitHub repository. After publication, members should seek feedback from the community and Technical Fellowship, and make any revisions needed. When the collective believes the proposal is ready, they should bring a remark with the text APPROVE_COLLECTIVE(\"{collective name}, {commitment}\") to a Root origin referendum. The proposer should provide instructions for generating commitment. The passing of this referendum would be unequivocal direction to the Fellowship that this collective should be part of the Polkadot runtime. Note: There is no need for a REJECT referendum. Proposals that have not been approved are simply not included in the runtime.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Explanation","id":"258","title":"Explanation"},"259":{"body":"If someone believes that an existing collective is not acting in the interest of the network or in accordance with its charter, they should likewise have a means to instruct the Fellowship to remove that collective from Polkadot. An on-chain remark from the Root origin with the text REMOVE_COLLECTIVE(\"{collective name}, {para ID}, [{pallet indices}]\") would instruct the Fellowship to remove the collective via the listed pallet indices on paraId. Should someone want to construct such a remark, they should have a reasonable expectation that a member of the Fellowship would help them identify the pallet indices associated with a given collective, whether or not the Fellowship member agrees with removal. Collective removal may also come with other governance calls, for example voiding any scheduled Treasury spends that would fund the given collective.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Removing Collectives","id":"259","title":"Removing Collectives"},"26":{"body":"The interaction between an XCQ program and the XCQ Extension Executor follows these steps: Program Loading: The Executor loads the PolkaVM program binary. Environment Setup: The Executor configures the PolkaVM environment, registering host functions like host_call and return_ty. Main Function Execution: The Executor calls the program's main function, passing serialized query arguments. Program Execution: Type Checking: The program uses the return_ty function to ensure compatibility with supported chain extensions. Query Execution: The program executes the query using host_call and performs custom computations. Result Serialization: The program serializes the result, writes it to shared memory, and returns the pointer and length to the executor. Result Retrieval: The Executor reads the result from shared memory and returns it to the caller.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » XCQ Program Execution Flow","id":"26","title":"XCQ Program Execution Flow"},"260":{"body":"Passing a Root origin referendum is slow. However, given the network's investment (in terms of code maintenance and salaries) in a new collective, this is an appropriate step.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Drawbacks","id":"260","title":"Drawbacks"},"261":{"body":"No impacts.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Testing, Security, and Privacy","id":"261","title":"Testing, Security, and Privacy"},"262":{"body":"Generally all new collectives will be in the Collectives parachain. Thus, performance impacts should strictly be limited to this parachain and not affect others. As the majority of logic for collectives is generalized and reusable, we expect most collectives to be instances of similar subsets of modules. That is, new collectives should generally be compatible with UIs and other services that provide collective-related functionality, with little modifications to support new ones.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Performance, Ergonomics, and Compatibility","id":"262","title":"Performance, Ergonomics, and Compatibility"},"263":{"body":"The launch of the Technical Fellowship, see the initial forum post .","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Prior Art and References","id":"263","title":"Prior Art and References"},"264":{"body":"None at this time.","breadcrumbs":"RFC-0012: Process for Adding New System Collectives » Unresolved Questions","id":"264","title":"Unresolved Questions"},"265":{"body":"(source) Table of Contents RFC-0013: Prepare Core runtime API for MBMs Summary Motivation Stakeholders Explanation Core::initialize_block Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date July 24, 2023 Description Prepare the Core Runtime API for Multi-Block-Migrations Authors Oliver Tale-Yazdi","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » RFC-0013: Prepare Core runtime API for MBMs","id":"265","title":"RFC-0013: Prepare Core runtime API for MBMs"},"266":{"body":"Introduces breaking changes to the Core runtime API by letting Core::initialize_block return an enum. The versions of Core is bumped from 4 to 5.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Summary","id":"266","title":"Summary"},"267":{"body":"The main feature that motivates this RFC are Multi-Block-Migrations (MBM); these make it possible to split a migration over multiple blocks. Further it would be nice to not hinder the possibility of implementing a new hook poll, that runs at the beginning of the block when there are no MBMs and has access to AllPalletsWithSystem. This hook can then be used to replace the use of on_initialize and on_finalize for non-deadline critical logic. In a similar fashion, it should not hinder the future addition of a System::PostInherents callback that always runs after all inherents were applied.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Motivation","id":"267","title":"Motivation"},"268":{"body":"Substrate Maintainers: They have to implement this, including tests, audit and maintenance burden. Polkadot Runtime developers: They will have to adapt the runtime files to this breaking change. Polkadot Parachain Teams: They have to adapt to the breaking changes but then eventually have multi-block migrations available.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Stakeholders","id":"268","title":"Stakeholders"},"269":{"body":"","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Explanation","id":"269","title":"Explanation"},"27":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Drawbacks","id":"27","title":"Drawbacks"},"270":{"body":"This runtime API function is changed from returning () to ExtrinsicInclusionMode: fn initialize_block(header: &::Header)\n+ -> ExtrinsicInclusionMode; With ExtrinsicInclusionMode is defined as: enum ExtrinsicInclusionMode { /// All extrinsics are allowed in this block. AllExtrinsics, /// Only inherents are allowed in this block. OnlyInherents,\n} A block author MUST respect the ExtrinsicInclusionMode that is returned by initialize_block. The runtime MUST reject blocks that have non-inherent extrinsics in them while OnlyInherents was returned. Coming back to the motivations and how they can be implemented with this runtime API change: 1. Multi-Block-Migrations : The runtime is being put into lock-down mode for the duration of the migration process by returning OnlyInherents from initialize_block. This ensures that no user provided transaction can interfere with the migration process. It is absolutely necessary to ensure this, otherwise a transaction could call into un-migrated storage and violate storage invariants. 2. poll is possible by using apply_extrinsic as entry-point and not hindered by this approach. It would not be possible to use a pallet inherent like System::last_inherent to achieve this for two reasons: First is that pallets do not have access to AllPalletsWithSystem which is required to invoke the poll hook on all pallets. Second is that the runtime does currently not enforce an order of inherents. 3. System::PostInherents can be done in the same manner as poll.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Core::initialize_block","id":"270","title":"Core::initialize_block"},"271":{"body":"The previous drawback of cementing the order of inherents has been addressed and removed by redesigning the approach. No further drawbacks have been identified thus far.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Drawbacks","id":"271","title":"Drawbacks"},"272":{"body":"The new logic of initialize_block can be tested by checking that the block-builder will skip transactions when OnlyInherents is returned. Security: n/a Privacy: n/a","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Testing, Security, and Privacy","id":"272","title":"Testing, Security, and Privacy"},"273":{"body":"","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Performance, Ergonomics, and Compatibility","id":"273","title":"Performance, Ergonomics, and Compatibility"},"274":{"body":"The performance overhead is minimal in the sense that no clutter was added after fulfilling the requirements. The only performance difference is that initialize_block also returns an enum that needs to be passed through the WASM boundary. This should be negligible.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Performance","id":"274","title":"Performance"},"275":{"body":"The new interface allows for more extensible runtime logic. In the future, this will be utilized for multi-block-migrations which should be a huge ergonomic advantage for parachain developers.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Ergonomics","id":"275","title":"Ergonomics"},"276":{"body":"The advice here is OPTIONAL and outside of the RFC. To not degrade user experience, it is recommended to ensure that an updated node can still import historic blocks.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Compatibility","id":"276","title":"Compatibility"},"277":{"body":"The RFC is currently being implemented in polkadot-sdk#1781 (formerly substrate#14275 ). Related issues and merge requests: Simple multi block migrations Execute a hook after inherent but before transactions There is no module hook after inherents and before transactions","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Prior Art and References","id":"277","title":"Prior Art and References"},"278":{"body":"Please suggest a better name for BlockExecutiveMode. We already tried: RuntimeExecutiveMode, ExtrinsicInclusionMode. The names of the modes Normal and Minimal were also called AllExtrinsics and OnlyInherents, so if you have naming preferences; please post them. => renamed to ExtrinsicInclusionMode Is post_inherents more consistent instead of last_inherent? Then we should change it. => renamed to last_inherent","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Unresolved Questions","id":"278","title":"Unresolved Questions"},"279":{"body":"The long-term future here is to move the block building logic into the runtime. Currently there is a tight dance between the block author and the runtime; the author has to call into different runtime functions in quick succession and exact order. Any misstep causes the block to be invalid. This can be unified and simplified by moving both parts into the runtime.","breadcrumbs":"RFC-0013: Prepare Core runtime API for MBMs » Future Directions and Related Material","id":"279","title":"Future Directions and Related Material"},"28":{"body":"XCQ Query Program Size: The size of XCQ query programs should be optimized to ensure efficient storage and transmission via XCMP/HRMP. Some strategies to address this issue include: Exploring modular program structures that allow for separate storage and transmission of core logic and supporting elements. PolkaVM supports spliting the program into multiple modules. Establishing guidelines for optimizing dynamic memory usage within query programs","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance issues","id":"28","title":"Performance issues"},"280":{"body":"(source) Table of Contents RFC-0014: Improve locking mechanism for parachains Summary Motivation Requirements Stakeholders Explanation Status quo Proposed changes Migration Drawbacks Testing, Security, and Privacy Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date July 25, 2023 Description Improve locking mechanism for parachains Authors Bryan Chen","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » RFC-0014: Improve locking mechanism for parachains","id":"280","title":"RFC-0014: Improve locking mechanism for parachains"},"281":{"body":"This RFC proposes a set of changes to the parachain lock mechanism. The goal is to allow a parachain manager to self-service the parachain without root track governance action. This is achieved by remove existing lock conditions and only lock a parachain when: A parachain manager explicitly lock the parachain OR a parachain block is produced successfully","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Summary","id":"281","title":"Summary"},"282":{"body":"The manager of a parachain has permission to manage the parachain when the parachain is unlocked. Parachains are by default locked when onboarded to a slot. This requires the parachain wasm/genesis must be valid, otherwise a root track governance action on relaychain is required to update the parachain. The current reliance on root track governance actions for managing parachains can be time-consuming and burdensome. This RFC aims to address this technical difficulty by allowing parachain managers to take self-service actions, rather than relying on general public voting. The key scenarios this RFC seeks to improve are: Rescue a parachain with invalid wasm/genesis. While we have various resources and templates to build a new parachain, it is still not a trivial task. It is very easy to make a mistake and resulting an invalid wasm/genesis. With lack of tools to help detect those issues [1] , it is very likely that the issues are only discovered after the parachain is onboarded on a slot. In this case, the parachain is locked and the parachain team has to go through a lengthy governance process to rescue the parachain. Perform lease renewal for an existing parachain. One way to perform lease renewal for a parachain is by doing a least swap with another parachain with a longer lease. This requires the other parachain must be operational and able to perform XCM transact call into relaychain to dispatch the swap call. Combined with the overhead of setting up a new parachain, this is an time consuming and expensive process. Ideally, the parachain manager should be able to perform the lease swap call without having a running parachain [2] .","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Motivation","id":"282","title":"Motivation"},"283":{"body":"A parachain manager SHOULD be able to rescue a parachain by updating the wasm/genesis without root track governance action. A parachain manager MUST NOT be able to update the wasm/genesis if the parachain is locked. A parachain SHOULD be locked when it successfully produced the first block. A parachain manager MUST be able to perform lease swap without having a running parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Requirements","id":"283","title":"Requirements"},"284":{"body":"Parachain teams Parachain users","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Stakeholders","id":"284","title":"Stakeholders"},"285":{"body":"","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Explanation","id":"285","title":"Explanation"},"286":{"body":"A parachain can either be locked or unlocked [3] . With parachain locked, the parachain manager does not have any privileges. With parachain unlocked, the parachain manager can perform following actions with the paras_registrar pallet: deregister: Deregister a Para Id, freeing all data and returning any deposit. swap: Initiate or confirm lease swap with another parachain. add_lock: Lock the parachain. schedule_code_upgrade: Schedule a parachain upgrade to update parachain wasm. set_current_head: Set the parachain's current head. Currently, a parachain can be locked with following conditions: From add_lock call, which can be dispatched by relaychain Root origin, the parachain, or the parachain manager. When a parachain is onboarded on a slot [4] . When a crowdloan is created. Only the relaychain Root origin or the parachain itself can unlock the lock [5] . This creates an issue that if the parachain is unable to produce block, the parachain manager is unable to do anything and have to rely on relaychain Root origin to manage the parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Status quo","id":"286","title":"Status quo"},"287":{"body":"This RFC proposes to change the lock and unlock conditions. A parachain can be locked only with following conditions: Relaychain governance MUST be able to lock any parachain. A parachain MUST be able to lock its own lock. A parachain manager SHOULD be able to lock the parachain. A parachain SHOULD be locked when it successfully produced a block for the first time. A parachain can be unlocked only with following conditions: Relaychain governance MUST be able to unlock any parachain. A parachain MUST be able to unlock its own lock. Note that create crowdloan MUST NOT lock the parachain and onboard a parachain SHOULD NOT lock it until a new block is successfully produced.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Proposed changes","id":"287","title":"Proposed changes"},"288":{"body":"A one off migration is proposed in order to apply this change retrospectively so that existing parachains can also be benefited from this RFC. This migration will unlock parachains that confirms with following conditions: Parachain is locked. Parachain never produced a block. Including from expired leases. Parachain manager never explicitly lock the parachain.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Migration","id":"288","title":"Migration"},"289":{"body":"Parachain locks are designed in such way to ensure the decentralization of parachains. If parachains are not locked when it should be, it could introduce centralization risk for new parachains. For example, one possible scenario is that a collective may decide to launch a parachain fully decentralized. However, if the parachain is unable to produce block, the parachain manager will be able to replace the wasm and genesis without the consent of the collective. It is considered this risk is tolerable as it requires the wasm/genesis to be invalid at first place. It is not yet practically possible to develop a parachain without any centralized risk currently. Another case is that a parachain team may decide to use crowdloan to help secure a slot lease. Previously, creating a crowdloan will lock a parachain. This means crowdloan participants will know exactly the genesis of the parachain for the crowdloan they are participating. However, this actually providers little assurance to crowdloan participants. For example, if the genesis block is determined before a crowdloan is started, it is not possible to have onchain mechanism to enforce reward distributions for crowdloan participants. They always have to rely on the parachain team to fulfill the promise after the parachain is alive. Existing operational parachains will not be impacted.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Drawbacks","id":"289","title":"Drawbacks"},"29":{"body":"Debugging: Currently, there is no full-fledged debuggers for PolkaVM programs. The only debugging approach is to set the PolkaVM backend in interpreter mode and then log the operations at the assembly level, which is too low-level to debug efficiently. Gas computation: According to this issue , the gas cost model of PolkaVM is not accurate for now.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » User experience issues","id":"29","title":"User experience issues"},"290":{"body":"The implementation of this RFC will be tested on testnets (Rococo and Westend) first. An audit maybe required to ensure the implementation does not introduce unwanted side effects. There is no privacy related concerns.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Testing, Security, and Privacy","id":"290","title":"Testing, Security, and Privacy"},"291":{"body":"This RFC should not introduce any performance impact.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Performance","id":"291","title":"Performance"},"292":{"body":"This RFC should improve the developer experiences for new and existing parachain teams","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Ergonomics","id":"292","title":"Ergonomics"},"293":{"body":"This RFC is fully compatibility with existing interfaces.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Compatibility","id":"293","title":"Compatibility"},"294":{"body":"Parachain Slot Extension Story: https://github.com/paritytech/polkadot/issues/4758 Allow parachain to renew lease without actually run another parachain: https://github.com/paritytech/polkadot/issues/6685 Always treat parachain that never produced block for a significant amount of time as unlocked: https://github.com/paritytech/polkadot/issues/7539","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Prior Art and References","id":"294","title":"Prior Art and References"},"295":{"body":"None at this stage.","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Unresolved Questions","id":"295","title":"Unresolved Questions"},"296":{"body":"This RFC is only intended to be a short term solution. Slots will be removed in future and lock mechanism is likely going to be replaced with a more generalized parachain manage & recovery system in future. Therefore long term impacts of this RFC are not considered. https://github.com/paritytech/cumulus/issues/377 [2] : https://github.com/paritytech/polkadot/issues/6685 [3] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L51-L52C15 [4] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L473-L475 [5] : https://github.com/paritytech/polkadot/blob/994af3de79af25544bf39644844cbe70a7b4d695/runtime/common/src/paras_registrar.rs#L333-L340","breadcrumbs":"RFC-0014: Improve locking mechanism for parachains » Future Directions and Related Material","id":"296","title":"Future Directions and Related Material"},"297":{"body":"(source) Table of Contents RFC-0022: Adopt Encointer Runtime Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date Aug 22nd 2023 Description Permanently move the Encointer runtime into the Fellowship runtimes repo. Authors @brenzi for Encointer Association, 8000 Zurich, Switzerland","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » RFC-0022: Adopt Encointer Runtime","id":"297","title":"RFC-0022: Adopt Encointer Runtime"},"298":{"body":"Encointer is a system chain on Kusama since Jan 2022 and has been developed and maintained by the Encointer association. This RFC proposes to treat Encointer like any other system chain and include it in the fellowship repo with this PR .","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Summary","id":"298","title":"Summary"},"299":{"body":"Encointer does not seek to be in control of its runtime repository. As a decentralized system, the fellowship has a more suitable structure to maintain a system chain runtime repo than the Encointer association does. Also, Encointer aims to update its runtime in batches with other system chains in order to have consistency for interoperability across system chains.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Motivation","id":"299","title":"Motivation"},"3":{"body":"Currently, there is no way to communicate metadata of an asset (or an asset instance) via XCM. The ability to query and modify the metadata is useful for two kinds of entities: Asset collections (both fungible and nonfungible). Any collection has some metadata, such as the name of the collection. The standard way of communicating metadata could help with registering foreign assets within a consensus system. Therefore, this RFC could complement or supersede the RFC for initializing fully-backed derivatives (note that this RFC is related to the old XCM RFC process; it's not the Fellowship RFC and hasn't been migrated yet). NFTs (i.e., asset instances). The metadata is the crucial aspect of any nonfungible object since metadata assigns meaning to such an object. The metadata for NFTs is just as important as the notion of \"amount\" for fungibles (there is no sense in fungibles if they have no amount). An NFT is always a representation of some object. The metadata describes the object represented by the NFT. NFTs can be transferred to another chain via XCM. However, there are limitations due to the inability to communicate its metadata: Teleports are inherently impossible because they imply the complete transfer of an NFT, including its metadata, which can't be done via XCM now. Reserve-based transfers currently have limited use-case scenarios if the reserve chain provides a way of modifying metadata for its users (usually, the token's owner has privileged rights to modify a specific metadata subset). When a user transfers an NFT using this model to another chain, the NFT owner-related metadata can't be updated anymore because another chain's sovereign account owns the original token, and another chain cannot modify the metadata. However, if it were possible to update NFT metadata in the standard XCM way, another chain could offer additional metadata-related logic. For instance, it could provide a facade logic to metadata modification (i.e., provide permission-based modification authorization, new value format check, etc.). Besides metadata modification, the ability to read it is also valuable. On-chain logic can interpret the NFT metadata, i.e., the metadata could have not only the media meaning but also a utility function within a consensus system. Currently, such a way of using NFT metadata is possible only within one consensus system. This RFC proposes making it possible between different systems via XCM so different chains can fetch and analyze the asset metadata from other chains.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Motivation","id":"3","title":"Motivation"},"30":{"body":"Testing: A comprehensive test suite should be developed to cover various scenarios: Positive test cases: Basic queries with various extensions, data types, return values, custom computations, etc. Accurate conversion between given weight limit and the gas limit of PolkaVM Negative test cases: Queries exceeding weight limits Invoking queries from unauthorized sources Edge cases: Queries with minimal or maximum allowed input sizes Integration tests to ensure proper interaction with off-chain wallets/UI and on-chain XCM, including the aforementioned use cases in Motivation section. Security: The XCQ system must enforce a strict read-only policy for all query operations. A mechanism should be implemented to prevent any state-changing operations within XCQ queries. Clear guidelines and best practices should be provided for parachain developers to ensure secure implementation.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Testing, Security, and Privacy","id":"30","title":"Testing, Security, and Privacy"},"300":{"body":"Fellowship: Will continue to take upon them the review and auditing work for the Encointer runtime, but the process is streamlined with other system chains and therefore less time-consuming compared to the separate repo and CI process we currently have. Kusama Network: Tokenholders can easily see the changes of all system chains in one place. Encointer Association: Further decentralization of the Encointer Network necessities like devops. Encointer devs: Being able to work directly in the Fellowship runtimes repo to streamline and synergize with other developers.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Stakeholders","id":"300","title":"Stakeholders"},"301":{"body":"Our PR has all details about our runtime and how we would move it into the fellowship repo. Noteworthy: All Encointer-specific pallets will still be located in encointer's repo for the time being: https://github.com/encointer/pallets It will still be the duty of the Encointer team to keep its runtime up to date and provide adequate test fixtures. Frequent dependency bumps with Polkadot releases would be beneficial for interoperability and could be streamlined with other system chains but that will not be a duty of fellowship. Whenever possible, all system chains could be upgraded jointly (including Encointer) with a batch referendum. Further notes: Encointer will publish all its crates crates.io Encointer does not carry out external auditing of its runtime nor pallets. It would be beneficial but not a requirement from our side if Encointer could join the auditing process of other system chains.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Explanation","id":"301","title":"Explanation"},"302":{"body":"Other than all other system chains, development and maintenance of the Encointer Network is mainly financed by the KSM Treasury and possibly the DOT Treasury in the future. Encointer is dedicated to maintaining its network and runtime code for as long as possible, but there is a dependency on funding which is not in the hands of the fellowship. The only risk in the context of funding, however, is that the Encointer runtime will see less frequent updates if there's less funding.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Drawbacks","id":"302","title":"Drawbacks"},"303":{"body":"No changes to the existing system are proposed. Only changes to how maintenance is organized.","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Testing, Security, and Privacy","id":"303","title":"Testing, Security, and Privacy"},"304":{"body":"No changes","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Performance, Ergonomics, and Compatibility","id":"304","title":"Performance, Ergonomics, and Compatibility"},"305":{"body":"Existing Encointer runtime repo","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Prior Art and References","id":"305","title":"Prior Art and References"},"306":{"body":"None identified","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Unresolved Questions","id":"306","title":"Unresolved Questions"},"307":{"body":"More info on Encointer: encointer.org","breadcrumbs":"RFC-0022: Adopt Encointer Runtime » Future Directions and Related Material","id":"307","title":"Future Directions and Related Material"},"308":{"body":"(source) Table of Contents RFC-0026: Sassafras Consensus Protocol Abstract 1. Motivation 1.1. Relevance to Implementors 1.2. Supporting Sassafras for Polkadot 2. Stakeholders 2.1. Blockchain Core Developers 2.2. Polkadot Ecosystem Contributors 3. Notation 3.1. Data Structures Definitions 3.2. Types Alias 3.2. Pseudo-Code 3.3. Incremental Introduction of Types and Functions 4. Protocol Introduction 4.1. Submission of Candidate Tickets 4.2. Validation of Candidate Tickets 4.3. Tickets Slots Binding 4.4. Claim of Ticket Ownership 5. Bandersnatch VRFs Cryptographic Primitives 5.1 Bare VRF Interface 6. Sassafras Protocol 6.2. Header Digest Log 6.3. On-Chain Randomness 6.4. Epoch Change Signal 6.5. Tickets Creation and Submission 6.6. On-chain Tickets Validation 6.7. Ticket-Slot Binding 6.8. Slot Claim 6.9. Slot Claim Verification 6.9.1. Primary Method 6.10. Randomness Accumulator 7. Drawbacks 8. Testing, Security, and Privacy 9. Performance, Ergonomics, and Compatibility 9.1. Performance 9.2. Ergonomics 9.3. Compatibility 10. Prior Art and References 11. Unresolved Questions 12. Future Directions and Related Material 12.1. Interactions with On-Chain Code 12.2. Deployment Strategies 12.3. ZK-SNARK Parameters 12.4. Anonymous Submission of Tickets. Start Date September 06, 2023 Description Sassafras consensus protocol specification Authors Davide Galassi","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » RFC-0026: Sassafras Consensus Protocol","id":"308","title":"RFC-0026: Sassafras Consensus Protocol"},"309":{"body":"Sassafras is a novel consensus protocol designed to address the recurring fork-related challenges encountered in other lottery-based protocols. The protocol aims to create a mapping between each epoch's slots and the authorities set while ensuring that the identity of authorities assigned to the slots remains undisclosed until the slot is actively claimed during block production.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » Abstract","id":"309","title":"Abstract"},"31":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance, Ergonomics, and Compatibility","id":"31","title":"Performance, Ergonomics, and Compatibility"},"310":{"body":"Sassafras Protocol has been rigorously described in a comprehensive research paper authored by the Web3 Foundation research team. This RFC is primarily intended to detail the critical implementation aspects vital for ensuring interoperability and to clarify certain aspects that are left open by the research paper and thus subject to interpretation during implementation.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1. Motivation","id":"310","title":"1. Motivation"},"311":{"body":"This RFC focuses on providing implementors with the necessary insights into the core protocol's operation. In instances of inconsistency between this document and the research paper, this RFC should be considered authoritative to eliminate ambiguities and ensure interoperability.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1.1. Relevance to Implementors","id":"311","title":"1.1. Relevance to Implementors"},"312":{"body":"Beyond promoting interoperability, this RFC also aims to facilitate the implementation of Sassafras within the greater Polkadot ecosystem. Although the specifics of deployment strategies are beyond the scope of this document, it lays the groundwork for the integration of Sassafras.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 1.2. Supporting Sassafras for Polkadot","id":"312","title":"1.2. Supporting Sassafras for Polkadot"},"313":{"body":"The protocol has a central role in the next generation block authoring consensus systems.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2. Stakeholders","id":"313","title":"2. Stakeholders"},"314":{"body":"Developers responsible for creating blockchains who intend to leverage the benefits offered by the Sassafras Protocol.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2.1. Blockchain Core Developers","id":"314","title":"2.1. Blockchain Core Developers"},"315":{"body":"Developers contributing to the Polkadot ecosystem, both relay-chain and para-chains.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 2.2. Polkadot Ecosystem Contributors","id":"315","title":"2.2. Polkadot Ecosystem Contributors"},"316":{"body":"This section outlines the notation adopted throughout this document to ensure clarity and consistency.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3. Notation","id":"316","title":"3. Notation"},"317":{"body":"Data structures are mostly defined using standard ASN.1 syntax with few exceptions. To ensure interoperability of serialized structures, the order of the fields must match the definitions found within this specification.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.1. Data Structures Definitions","id":"317","title":"3.1. Data Structures Definitions"},"318":{"body":"Unsigned integer: Unsigned ::= INTEGER (0..MAX) n-bit unsigned integer: Unsigned ::= INTEGER (0..2^n - 1) 8-bit unsigned integer (octet) Unsigned8 ::= Unsigned<8> 32-bit unsigned integer: Unsigned32 ::= Unsigned<32> 64-bit unsigned integer: Unsigned64 ::= Unsigned<64> Non-homogeneous sequence (struct/tuple): Sequence ::= SEQUENCE Variable length homogeneous sequence (vector): Sequence ::= SEQUENCE OF T Fixed length homogeneous sequence (array): Sequence ::= Sequence (SIZE(n)) Variable length octet-string: OctetString ::= Sequence Fixed length octet-string: OctetString ::= Sequence","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.2. Types Alias","id":"318","title":"3.2. Types Alias"},"319":{"body":"It is convenient to make use of code snippets as part of the protocol description. As a convention, the code is formatted in a style similar to Rust , and can make use of the following set of predefined procedures: Sequences CONCAT(x₀: OctetString, ..., xₖ: OctetString) -> OctetString: Concatenates the input octet-strings as a new octet string. LENGTH(s: Sequence) -> Unsigned: The number of elements in the sequence s. GET(s: Sequence, i: Unsigned) -> T: The i-th element of the sequence s. PUSH(s: Sequence, x: T): Appends x as the new last element of the sequence s. POP(s: Sequence) -> T: extract and returns the last element of the sequence s. Codec ENCODE(x: T) -> OctetString: Encodes x as an OctetString according to SCALE codec. DECODE(x: OctetString) -> T: Decodes x as a type T object according to SCALE codec. Other BLAKE2(x: OctetString) -> OctetString<32>: Standard Blake2b hash of x with 256-bit digest.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.2. Pseudo-Code","id":"319","title":"3.2. Pseudo-Code"},"32":{"body":"It's a new functionality, which doesn't modify the existing implementations.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Performance","id":"32","title":"Performance"},"320":{"body":"More types and helper functions are introduced incrementally as they become relevant within the document's context.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 3.3. Incremental Introduction of Types and Functions","id":"320","title":"3.3. Incremental Introduction of Types and Functions"},"321":{"body":"The timeline is segmented into a sequentially ordered sequence of slots . This entire sequence of slots is further partitioned into distinct segments known as epochs . Sassafras aims to map each slot within a target epoch to the authorities scheduled for that epoch, utilizing a ticketing system. The core protocol operation can be roughly divided into four phases.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4. Protocol Introduction","id":"321","title":"4. Protocol Introduction"},"322":{"body":"Each authority scheduled for the target epoch generates and shares a set of candidate tickets. Every ticket has an unbiasable pseudo random score and is bundled with an anonymous proof of validity.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.1. Submission of Candidate Tickets","id":"322","title":"4.1. Submission of Candidate Tickets"},"323":{"body":"Each candidate ticket undergoes a validation process for the associated validity proof and compliance with other protocol-specific constraints. Valid tickets are persisted on-chain.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.2. Validation of Candidate Tickets","id":"323","title":"4.2. Validation of Candidate Tickets"},"324":{"body":"After collecting all valid candidate tickets and before the beginning of the target epoch , a deterministic method is used to uniquely associate a subset of these tickets to the slots of the target epoch .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.3. Tickets Slots Binding","id":"324","title":"4.3. Tickets Slots Binding"},"325":{"body":"During block production phase of target epoch , the author is required to prove ownership of the ticket associated to the block's slot. This step discloses the identity of the ticket owner.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 4.4. Claim of Ticket Ownership","id":"325","title":"4.4. Claim of Ticket Ownership"},"326":{"body":"This section is not intended to serve as an exhaustive exploration of the mathematically intensive foundations of the cryptographic primitive. Rather, its primary aim is to offer a concise and accessible explanation of the primitives role and interface which is relevant within the scope of the protocol. For a more detailed explanation, refer to the Bandersnatch VRFs technical specification Bandersnatch VRF comes in two variants: Bare VRF: Extension to the IETF ECVRF RFC 9381 , Ring VRF: Anonymous signatures leveraging zk-SNARK . Together with the input , which determines the VRF output , both variants offer the capability to sign some arbitrary additional data ( extra ) which doesn't contribute to the VRF output.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 5. Bandersnatch VRFs Cryptographic Primitives","id":"326","title":"5. Bandersnatch VRFs Cryptographic Primitives"},"327":{"body":"VRF signature construction. fn vrf_sign( secret: SecretKey, input: OctetString, extra: OctetString, ) -> VrfSignature VRF signature verification. Returns a Boolean indicating the validity of the signature (1 on success). fn vrf_verify( public: PublicKey, input: OctetString, extra: OctetString, signature: VrfSignature ) -> Unsigned<1>; VRF output derivation from input and secret . fn vrf_output( secret: SecretKey, input: OctetString, ) -> OctetString<32>; VRF output derivation from a VRF signature. fn vrf_signed_output( signature: VrfSignature, ) -> OctetString<32>; The following condition is always satisfied: let signature = vrf_sign(secret, input, extra); vrf_output(secret, input) == vrf_signed_output(signature) SecretKey, PublicKey and VrfSignature types are intentionally left undefined. Their definitions can be found in the Bandersnatch VRF specification and related documents. 5.4.2. Ring VRF Interface Ring VRF signature construction. fn ring_vrf_sign( secret: SecretKey, prover: RingProver, input: OctetString, extra: OctetString, ) -> RingVrfSignature; Ring VRF signature verification. Returns a Boolean indicating the validity of the signature (1 on success). Note that verification doesn't require the signer's public key. fn ring_vrf_verify( verifier: RingVerifier, input: OctetString, extra: OctetString, signature: RingVrfSignature, ) -> Unsigned<1>; VRF output derivation from a ring VRF signature . fn ring_vrf_signed_output( signature: RingVrfSignature, ) -> OctetString<32>; The following condition is always satisfied: let signature = vrf_sign(secret, input, extra); let ring_signature = ring_vrf_sign(secret, prover, input, extra); vrf_signed_output(signature) == ring_vrf_signed_output(ring_signature); RingProver, RingVerifier, and RingVrfSignature are intentionally left undefined. Their definitions can be found in the Bandersnatch VRF specification and related documents.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 5.1 Bare VRF Interface","id":"327","title":"5.1 Bare VRF Interface"},"328":{"body":"6.1. Protocol Configuration The ProtocolConfiguration type contains some parameters to tweak the protocol behavior and primarily influences certain checks carried out during tickets validation. It is defined as: ProtocolConfiguration ::= Sequence { epoch_length: Unsigned32, attempts_number: Unsigned8, redundancy_factor: Unsigned8, } Where: epoch_length: Number of slots for each epoch. attempts_number: Maximum number of tickets that each authority is allowed to submit. redundancy_factor: Expected ratio between the cumulative number of valid tickets which can be submitted by the scheduled authorities and the epoch's duration in slots. The attempts_number influences the anonymity of block producers. As all published tickets have a public attempt number less than attempts_number, all the tickets which share the attempt number value must belong to different block producers, which reduces anonymity late as we approach the epoch tail. Bigger values guarantee more anonymity but also more computation. Details about how these parameters drive the tickets validity probability can be found in section 6.5.2 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6. Sassafras Protocol","id":"328","title":"6. Sassafras Protocol"},"329":{"body":"Each block header contains a Digest log, which is defined as an ordered sequence of DigestItems: DigestItem ::= Sequence { id: OctetString<4>, data: OctetString } Digest ::= Sequence The Digest sequence is used to propagate information required for the correct protocol progress. Outside the protocol's context, the information within each DigestItem is opaque and maps to some SCALE-encoded protocol-specific structure. For Sassafras related items, the DiegestItems id is set to the ASCII string \"SASS\" Possible digest items for Sassafras: Epoch change signal: Information about next epoch. This is mandatory for the first block of a new epoch. Epoch tickets signal: Sequence of tickets for claiming slots in the next epoch. This is mandatory for the first block in the epoch's tail Slot claim info: Additional data required for block verification. This is mandatory for each block and must be the second-to-last entry in the log. Seal: Block signature added by the block author. This is mandatory for each block and must be the last entry in the log. If any digest entry is unexpected, not found where mandatory or found in the wrong position, then the block is considered invalid.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.2. Header Digest Log","id":"329","title":"6.2. Header Digest Log"},"33":{"body":"The proposal facilitate the wallets and dApps developers. Developers no longer need to examine every concrete implementation to support conceptually similar operations across different chains. Additionally, they gain a more modular development experience through encapsulating custom computations over the exposed APIs in PolkaVM programs.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Ergonomics","id":"33","title":"Ergonomics"},"330":{"body":"A sequence of four randomness entries is maintained on-chain. RandomnessBuffer ::= Sequence, 4> During epoch N: The first entry is the current randomness accumulator and incorporates verifiable random elements from all previously executed blocks. The accumulation procedure is described in section 6.10 . The second entry is the snapshot of the accumulator before the execution of the first block of epoch N. This is the randomness used for tickets targeting epoch N+2. The third entry is the snapshot of the accumulator before the execution of the first block of epoch N-1. This is the randomness used for tickets targeting epoch N+1 (the next epoch). The third entry is the snapshot of the accumulator before the execution of the first block of epoch N-2. This is the randomness used for tickets targeting epoch N (the current epoch). The buffer's entries are updated after each block execution.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.3. On-Chain Randomness","id":"330","title":"6.3. On-Chain Randomness"},"331":{"body":"The first block produced during epoch N must include a descriptor for some of the parameters to be used by the subsequent epoch (N+1). This signal descriptor is defined as: NextEpochDescriptor ::= Sequence { randomness: OctetString<32>, authorities: Sequence, } Where: randomness: Randomness accumulator snapshot relevant for validation of next epoch blocks. In other words, randomness used to construct the tickets targeting epoch N+1. authorities: List of authorities scheduled for next epoch. This descriptor is SCALE encoded and embedded in a DigestItem. 6.4.1. Startup Parameters Some of the initial parameters used by the first epoch (#0), are set through the genesis configuration, which is defined as: GenesisConfig ::= Sequence { authorities: Sequence, } The on-chain RandomnessBuffer is initialized after the genesis block construction. The first buffer entry is set as the Blake2b hash of the genesis block, each of the other entries is set as the Blake2b hash of the previous entry. Since block #0 is generated by each node as part of the genesis process, the first block that an authority explicitly produces for epoch #0 is block #1. Therefore, block #1 is required to contain the NextEpochDescriptor for the following epoch. NextEpochDescriptor for epoch #1: randomness: Third entry (index 2) of the randomness buffer. authorities: The same sequence as specified in the genesis configuration.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.4. Epoch Change Signal","id":"331","title":"6.4. Epoch Change Signal"},"332":{"body":"During epoch N, each authority scheduled for epoch N+2 constructs a set of tickets which may be eligible ( 6.5.2 ) for on-chain submission. These tickets are constructed using the on-chain randomness snapshot taken before the execution of the first block of epoch N together with other parameters and aims to secure ownership of one or more slots of epoch N+2 ( target epoch ). Each authority is allowed to submit a maximum number of tickets, constrained by attempts_number field of the ProtocolConfiguration. The ideal timing for the candidate authority to start constructing the tickets is subject to strategy. A recommended approach is to initiate tickets creation once the last block of epoch N-1 is either probabilistically or, even better, deterministically finalized. This delay is suggested to prevent wasting resources creating tickets that will be unusable if a different chain branch is chosen as canonical. Tickets generated during epoch N are shared with the tickets relayers , which are the authorities scheduled for epoch N+1. Relayers validate and collect (off-chain) the tickets targeting epoch N+2. When epoch N+1 starts, collected tickets are submitted on-chain by relayers as inherent extrinsics , a special type of transaction inserted by the block author at the beginning of the block's transactions sequence. 6.5.1. Ticket Identifier Each ticket has an associated identifier defined as: TicketId ::= OctetString<32>; The value of TicketId is completely determined by the output of Bandersnatch VRFs given the following unbiasable input: let ticket_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(attempt) ); let ticket_id = vrf_output(authority_secret_key, ticket_vrf_input); Where: target_epoch_randomness: element of RandomnessBuffer which contains the randomness for the epoch the ticket is targeting. attempt: value going from 0 to the configured attempts_number - 1. 6.5.2. Tickets Threshold A ticket is valid for on-chain submission if its TicketId value, when interpreted as a big-endian 256-bit integer normalized as a float within the range [0..1], is less than the ticket threshold computed as: T = (r·s)/(a·v) Where: v: epoch's authorities number s: epoch's slots number r: redundancy factor a: attempts number In an epoch with s slots, the goal is to achieve an expected number of valid tickets equal to r·s. It's crucial to ensure that the probability of having fewer than s winning tickets is very low, even in scenarios where up to 1/3 of the authorities might be offline. To accomplish this, we first define the winning probability of a single ticket as T = (r·s)/(a·v). Let n be the actual number of participating authorities, where v·2/3 ≤ n ≤ v. These n authorities each make a attempts, for a total of a·n attempts. Let X be the random variable associated to the number of winning tickets, then its expected value is E[X] = T·a·n = (r·s·n)/v. By setting r = 2, we get s·4/3 ≤ E[X] ≤ s·2. Using Bernestein's inequality we get Pr[X < s] ≤ e^(-s/21). For instance, with s = 600 this results in Pr[X < s] < 4·10⁻¹³. Consequently, this approach offers considerable tolerance for offline nodes and ensures that all slots are likely to be filled with tickets. For more details about threshold formula refer to probabilities and parameters paragraph in the Web3 Foundation description of the protocol. 6.5.3. Ticket Envelope Each ticket candidate is represented by a TicketEnvelope: TicketEnvelope ::= Sequence { attempt: Unsigned8, extra: OctetString, signature: RingVrfSignature } Where: attempt: Index associated to the ticket. extra: Additional data available for user-defined applications. signature: Ring VRF signature of the envelope data (attempt and extra). Envelope data is signed using Bandersnatch Ring VRF ( 5.4.2 ). let signature = ring_vrf_sign( secret_key, ring_prover ticket_vrf_input, extra, ); With ticket_vrf_input defined as in 6.5.1 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.5. Tickets Creation and Submission","id":"332","title":"6.5. Tickets Creation and Submission"},"333":{"body":"Validation rules: Ring VRF signature is verified using the ring_verifier derived by the constant ring context parameters (SNARK SRS) and the next epoch authorities public keys. TicketId is locally computed from the RingVrfSignature and its value is checked to be less than tickets' threshold. On-chain tickets submission can't occur within a block part of the epoch's tail , which encompasses a configurable number of slots at the end of the epoch. This constraint is to give time to persisted on-chain tickets to be probabilistically (or even better deterministically) finalized and thus to further reduce the fork chances at the beginning of the target epoch. All tickets which are proposed within a block must be valid and all of them must end up being persisted on-chain. Because the total number of tickets persisted on-chain is limited by to the epoch's length, this may require to drop some of the previously persisted tickets. We remove tickets with greater TicketId value first. No tickets duplicates are allowed. If at least one of the checks fails then the block must be considered invalid. Pseudo-code for ticket validation for steps 1 and 2: let ticket_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(envelope.attempt) ); let result = ring_vrf_verify( ring_verifier, ticket_vrf_input, envelope.extra, envelope.ring_signature ); ASSERT(result == 1); let ticket_id = ring_vrf_signed_output(envelope.ring_signature); ASSERT(ticket_id < ticket_threshold); Valid tickets are persisted on-chain in a bounded sorted sequence of TicketBody objects. Items within this sequence are sorted according to their TicketId, interpreted as a 256-bit big-endian unsigned integer. TicketBody ::= Sequence { id: TicketId, attempt: Unsigned8, extra: OctetString, } Tickets ::= Sequence The on-chain tickets sequence length bound is set equal to the epoch length in slots according to the protocol configuration.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.6. On-chain Tickets Validation","id":"333","title":"6.6. On-chain Tickets Validation"},"334":{"body":"Before the beginning of the target epoch , the on-chain sequence of tickets must be associated to epoch's slots such that there is at most one ticket per slot. Given an ordered sequence of tickets [t₀, t₁, ..., tₙ], the tickets are associated according to the following outside-in strategy: slot_index : [ 0, 1, 2, 3 , ... ] tickets : [ t₀, tₙ, t₁, tₙ₋₁, ... ] Here slot_index is the slot number relative to the epoch's first slot: slot_index = slot - epoch_first_slot. The association between tickets and a slots is recorded on-chain and thus is public. What remains confidential is the ticket's author identity, and consequently, who is enabled to claim the corresponding slot. This information is known only to the ticket's author. If the number of published tickets is less than the number of epoch's slots, some orphan slots at the end of the epoch will remain unbounded to any ticket. For orphan slots claiming strategy refer to 6.8.2 . Note that this fallback situation always apply to the first two epochs after genesis.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.7. Ticket-Slot Binding","id":"334","title":"6.7. Ticket-Slot Binding"},"335":{"body":"With tickets bounded to the target epoch slots, every designated authority acquires the information about the slots for which they are required to produce a block. The procedure for slot claiming depends on whether a given slot has an associated ticket according to the on-chain state. If a slot has an associated ticket, then the primary authoring method is used. Conversely, the protocol resorts to the secondary method as a fallback. 6.8.1. Primary Method An authority, can claim a slot using the primary method if it is the legit owner of the ticket associated to the given slot. Let target_epoch_randomness be the entry in RandomnessBuffer relative to the epoch the block is targeting and attempt be the attempt used to construct the ticket associated to the slot to claim, the VRF input for slot claiming is constructed as: let seal_vrf_input = CONCAT( BYTES(\"sassafras_ticket_seal\"), target_epoch_randomness, BYTES(attempt) ); The seal_vrf_input, when signed with the correct authority secret key, must generate the same TicketId which has been associated to the target slot according to the on-chain state. 6.8.2. Secondary Method Given that the authorities scheduled for the target epoch are kept on-chain in an ordered sequence, the index of the authority which has the privilege to claim an orphan slot is given by the following procedure: let hash_input = CONCAT( target_epoch_randomness, ENCODE(relative_slot_index), ); let hash = BLAKE2(hash_input); let index_bytes = CONCAT(GET(hash, 0), GET(hash, 1), GET(hash, 2), GET(hash, 3)); let index = DECODE(index_bytes) % LENGTH(authorities); With relative_slot_index the slot offset relative to the target epoch's start and authorities the sequence of target epoch authorities. let seal_vrf_input = CONCAT( BYTES(\"sassafras_fallback_seal\"), target_epoch_randomness ); 6.8.3. Claim Data ClaimData is a digest entry which contains additional information required by the protocol to verify the block: ClaimData ::= Sequence { slot: Unsigned32, authority_index: Unsigned32, randomness_source: VrfSignature, } slot: The slot number authority_index: Block's author index relative to the on-chain authorities sequence. randomness_source: VRF signature used to generate per-block randomness. Given the seal_vrf_input constructed using the primary or secondary method, the randomness source signature is generated as follows: let randomness_vrf_input = CONCAT( BYTES(\"sassafras_randomness\"), vrf_output(authority_secret_key, seal_vrf_input) ); let randomness_source = vrf_sign( authority_secret_key, randomness_vrf_input, [] ); let claim = SlotClaim { slot, authority_index, randomness_source }; PUSH(block_header.digest, ENCODE(claim)); The ClaimData object is SCALE encoded and pushed as the second-to-last element of the header digest log. 6.8.4. Block Seal A block is finally sealed as follows: let unsealed_header_byets = ENCODE(block_header); let seal = vrf_sign( authority_secret_key, seal_vrf_input, unsealed_header_bytes ); PUSH(block_header.digest, ENCODE(seal)); With block_header the block's header without the seal digest log entry. The seal object is a VrfSignature, which is SCALE encoded and pushed as the last entry of the header digest log.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.8. Slot Claim","id":"335","title":"6.8. Slot Claim"},"336":{"body":"The last entry is extracted from the header digest log, and is SCALE decoded as a VrfSignature object. The unsealed header is then SCALE encoded in order to be verified. The next entry is extracted from the header digest log, and is SCALE decoded as a ClaimData object. The validity of the two signatures is assessed using as the authority public key corresponding to the authority_index found in the ClaimData, together with the VRF input (which depends on primary/secondary method) and additional data used by the block author. let seal_signature = DECODE(POP(header.digest)); let unsealed_header_bytes = ENCODE(header); let claim_data = DECODE(POP(header.digest)); let authority_public_key = GET(authorities, claim_data.authority_index); // Verify seal signature let result = vrf_verify( authority_public_key, seal_vrf_input, unsealed_header_bytes, seal_signature ); ASSERT(result == 1); let randomness_vrf_input = CONCAT( BYTES(\"sassafras_randomness\"), vrf_signed_output(seal_signature) ); // Verify per-block entropy source signature let result = vrf_verify( authority_public_key, randomness_vrf_input, [], claim_data.randomness_source ); ASSERT(result == 1); With: header: The block's header. authorities: Sequence of authorities for the target epoch, as recorded on-chain. seal_vrf_input: VRF input data constructed as specified in 6.8 . If signatures verification is successful, then the verification process diverges based on whether the slot is associated with a ticket according to the on-chain state.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.9. Slot Claim Verification","id":"336","title":"6.9. Slot Claim Verification"},"337":{"body":"For slots tied to a ticket, the primary verification method is employed. This method verifies ticket ownership using the TicketId associated to the slot. let ticket_id = vrf_signed_output(seal_signature); ASSERT(ticket_id == expected_ticket_id); With expected_ticket_id the ticket identifier committed on-chain in the associated TicketBody. 6.9.2. Secondary Method If the slot doesn't have any associated ticket, then the authority_index contained in the ClaimData must match the one returned by the procedure outlined in section 6.8.2 .","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.9.1. Primary Method","id":"337","title":"6.9.1. Primary Method"},"338":{"body":"The randomness accumulator is updated using the randomness_source signature found within the ClaimData object. In particular, fresh randomness is derived and accumulated after block execution as follows: let fresh_randomness = vrf_signed_output(claim.randomness_source); randomness_buffer[0] = BLAKE2(CONCAT(randomness_buffer[0], fresh_randomness));","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 6.10. Randomness Accumulator","id":"338","title":"6.10. Randomness Accumulator"},"339":{"body":"None","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 7. Drawbacks","id":"339","title":"7. Drawbacks"},"34":{"body":"The proposal defines new apis, which doesn't break compatibility with existing interfaces.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Compatibility","id":"34","title":"Compatibility"},"340":{"body":"It is critical that implementations of this RFC undergo thorough rigorous testing. A security audit may be desirable to ensure the implementation does not introduce emergent side effects.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 8. Testing, Security, and Privacy","id":"340","title":"8. Testing, Security, and Privacy"},"341":{"body":"","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9. Performance, Ergonomics, and Compatibility","id":"341","title":"9. Performance, Ergonomics, and Compatibility"},"342":{"body":"Adopting Sassafras consensus marks a significant improvement in reducing the frequency of short-lived forks which are eliminated by design. Forks may only result from network disruption or protocol attacks. In such cases, the choice of which fork to follow upon recovery is clear-cut, with only one valid option.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.1. Performance","id":"342","title":"9.1. Performance"},"343":{"body":"No specific considerations.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.2. Ergonomics","id":"343","title":"9.2. Ergonomics"},"344":{"body":"The adoption of Sassafras affects the native client and thus can't be introduced via a \"simple\" runtime upgrade. A deployment strategy should be carefully engineered for live networks. This subject is left open for a dedicated RFC.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 9.3. Compatibility","id":"344","title":"9.3. Compatibility"},"345":{"body":"Sassafras layman introduction Sassafras research paper Bandersnatch VRFs specification Bandersnatch VRFs reference implementation W3F Ring VRF research paper Sassafras reference implementation tracking issue Sassafras reference implementation main PR","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 10. Prior Art and References","id":"345","title":"10. Prior Art and References"},"346":{"body":"None","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 11. Unresolved Questions","id":"346","title":"11. Unresolved Questions"},"347":{"body":"While this RFC lays the groundwork and outlines the core aspects of the protocol, several crucial topics remain to be addressed in future RFCs.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12. Future Directions and Related Material","id":"347","title":"12. Future Directions and Related Material"},"348":{"body":"Storage : Types, organization and genesis configuration. Host interface : Interface that the hosting environment exposes to on-chain code (also known as host functions ). Unrecorded on-chain interface . Interface that on-chain code exposes to the hosting environment (also known as runtime API ). Transactional on-chain interface . Interface that on-chain code exposes to the World to alter the state (also known as transactions or extrinsics in the Polkadot ecosystem).","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.1. Interactions with On-Chain Code","id":"348","title":"12.1. Interactions with On-Chain Code"},"349":{"body":"Protocol Migration . Investigate of how Sassafras can seamlessly replace an already operational instance of another protocol. Future RFCs may focus on deployment strategies to facilitate a smooth transition.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.2. Deployment Strategies","id":"349","title":"12.2. Deployment Strategies"},"35":{"body":"There are several discussions related to the proposal, including: https://forum.polkadot.network/t/wasm-view-functions/1045 is the original discussion about having a mechanism to avoid code duplications between the runtime and front-ends/wallets. In the original design, the custom computations are compiled as a wasm function. https://github.com/paritytech/polkadot-sdk/issues/216 is the issue tracking the view functions implementation in runtime implementations https://github.com/paritytech/polkadot-sdk/pull/4722 is the on-going view function pull request. It works at pallet level. If two chains use two different pallets to provide similar functionalities, like pallet-assets and pallet-erc20, we still need to have different codes to support. Therefore, it doesn't conflict with XCQ, and can be utilized by XCQ.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Prior Art and References","id":"35","title":"Prior Art and References"},"350":{"body":"Parameters Setup : Determine the setup procedure for the zk-SNARK SRS (Structured Reference String) initialization. Future RFCs may provide insights into whether this process should include an ad-hoc initialization ceremony or if we can reuse an SRS from another ecosystem (e.g. Zcash or Ethereum).","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.3. ZK-SNARK Parameters","id":"350","title":"12.3. ZK-SNARK Parameters"},"351":{"body":"Mixnet Integration : Submitting tickets directly to the relay can pose a risk of potential deanonymization through traffic analysis. Subsequent RFCs may investigate the potential for incorporating mix network protocol or other privacy-enhancing mechanisms to address this concern.","breadcrumbs":"RFC-0026: Sassafras Consensus Protocol » 12.4. Anonymous Submission of Tickets.","id":"351","title":"12.4. Anonymous Submission of Tickets."},"352":{"body":"(source) Table of Contents RFC-0032: Minimal Relay Summary Motivation Stakeholders Explanation Migrations Interfaces Functional Architecture Resource Allocation Deployment Kusama Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 20 September 2023 Description Proposal to minimise Relay Chain functionality. Authors Joe Petrowski, Gavin Wood","breadcrumbs":"RFC-0032: Minimal Relay » RFC-0032: Minimal Relay","id":"352","title":"RFC-0032: Minimal Relay"},"353":{"body":"The Relay Chain contains most of the core logic for the Polkadot network. While this was necessary prior to the launch of parachains and development of XCM, most of this logic can exist in parachains. This is a proposal to migrate several subsystems into system parachains.","breadcrumbs":"RFC-0032: Minimal Relay » Summary","id":"353","title":"Summary"},"354":{"body":"Polkadot's scaling approach allows many distinct state machines (known generally as parachains) to operate with common guarantees about the validity and security of their state transitions. Polkadot provides these common guarantees by executing the state transitions on a strict subset (a backing group) of the Relay Chain's validator set. However, state transitions on the Relay Chain need to be executed by all validators. If any of those state transitions can occur on parachains, then the resources of the complement of a single backing group could be used to offer more cores. As in, they could be offering more coretime (a.k.a. blockspace) to the network. By minimising state transition logic on the Relay Chain by migrating it into \"system chains\" -- a set of parachains that, with the Relay Chain, make up the Polkadot protocol -- the Polkadot Ubiquitous Computer can maximise its primary offering: secure blockspace.","breadcrumbs":"RFC-0032: Minimal Relay » Motivation","id":"354","title":"Motivation"},"355":{"body":"Parachains that interact with affected logic on the Relay Chain; Core protocol and XCM format developers; Tooling, block explorer, and UI developers.","breadcrumbs":"RFC-0032: Minimal Relay » Stakeholders","id":"355","title":"Stakeholders"},"356":{"body":"The following pallets and subsystems are good candidates to migrate from the Relay Chain: Identity Balances Staking Staking Election Provider Bags List NIS Nomination Pools Fast Unstake Governance Treasury and Bounties Conviction Voting Referenda Note: The Auctions and Crowdloan pallets will be replaced by Coretime, its system chain and interface described in RFC-1 and RFC-5, respectively.","breadcrumbs":"RFC-0032: Minimal Relay » Explanation","id":"356","title":"Explanation"},"357":{"body":"Some subsystems are simpler to move than others. For example, migrating Identity can be done by simply preventing state changes in the Relay Chain, using the Identity-related state as the genesis for a new chain, and launching that new chain with the genesis and logic (pallet) needed. Other subsystems cannot experience any downtime like this because they are essential to the network's functioning, like Staking and Governance. However, these can likely coexist with a similarly-permissioned system chain for some time, much like how \"Gov1\" and \"OpenGov\" coexisted at the latter's introduction. Specific migration plans will be included in release notes of runtimes from the Polkadot Fellowship when beginning the work of migrating a particular subsystem.","breadcrumbs":"RFC-0032: Minimal Relay » Migrations","id":"357","title":"Migrations"},"358":{"body":"The Relay Chain, in many cases, will still need to interact with these subsystems, especially Staking and Governance. These subsystems will require making some APIs available either via dispatchable calls accessible to XCM Transact or possibly XCM Instructions in future versions. For example, Staking provides a pallet-API to register points (e.g. for block production) and offences (e.g. equivocation). With Staking in a system chain, that chain would need to allow the Relay Chain to update validator points periodically so that it can correctly calculate rewards. A pub-sub protocol may also lend itself to these types of interactions.","breadcrumbs":"RFC-0032: Minimal Relay » Interfaces","id":"358","title":"Interfaces"},"359":{"body":"This RFC proposes that system chains form individual components within the system's architecture and that these components are chosen as functional groups. This approach allows synchronous composibility where it is most valuable, but isolates logic in such a way that provides flexibility for optimal resource allocation (see Resource Allocation ). For the subsystems discussed in this RFC, namely Identity, Governance, and Staking, this would mean: People Chain, for identity and personhood logic, providing functionality related to the attributes of single actors; Governance Chain, for governance and system collectives, providing functionality for pluralities to express their voices within the system; Staking Chain, for Polkadot's staking system, including elections, nominations, reward distribution, slashing, and non-interactive staking; and Asset Hub, for fungible and non-fungible assets, including DOT. The Collectives chain and Asset Hub already exist, so implementation of this RFC would mean two new chains (People and Staking), with Governance moving to the currently-known-as Collectives chain and Asset Hub being increasingly used for DOT over the Relay Chain. Note that one functional group will likely include many pallets, as we do not know how pallet configurations and interfaces will evolve over time.","breadcrumbs":"RFC-0032: Minimal Relay » Functional Architecture","id":"359","title":"Functional Architecture"},"36":{"body":"","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Unresolved Questions","id":"36","title":"Unresolved Questions"},"360":{"body":"The system should minimise wasted blockspace. These three (and other) subsystems may not each consistently require a dedicated core. However, core scheduling is far more agile than functional grouping. While migrating functionality from one chain to another can be a multi-month endeavour, cores can be rescheduled almost on-the-fly. Migrations are also breaking changes to some use cases, for example other parachains that need to route XCM programs to particular chains. It is thus preferable to do them a single time in migrating off the Relay Chain, reducing the risk of needing parachain splits in the future. Therefore, chain boundaries should be based on functional grouping where synchronous composibility is most valuable; and efficient resource allocation should be managed by the core scheduling protocol. Many of these system chains (including Asset Hub) could often share a single core in a semi-round robin fashion (the coretime may not be uniform). When needed, for example during NPoS elections or slashing events, the scheduler could allocate a dedicated core to the chain in need of more throughput.","breadcrumbs":"RFC-0032: Minimal Relay » Resource Allocation","id":"360","title":"Resource Allocation"},"361":{"body":"Actual migrations should happen based on some prioritization. This RFC proposes to migrate Identity, Staking, and Governance as the systems to work on first. A brief discussion on the factors involved in each one: Identity Identity will be one of the simpler pallets to migrate into a system chain, as its logic is largely self-contained and it does not \"share\" balances with other subsystems. As in, any DOT is held in reserve as a storage deposit and cannot be simultaneously used the way locked DOT can be locked for multiple purposes. Therefore, migration can take place as follows: The pallet can be put in a locked state, blocking most calls to the pallet and preventing updates to identity info. The frozen state will form the genesis of a new system parachain. Functions will be added to the pallet that allow migrating the deposit to the parachain. The parachain deposit is on the order of 1/100th of the Relay Chain's. Therefore, this will result in freeing up Relay State as well as most of each user's reserved balance. The pallet and any leftover state can be removed from the Relay Chain. User interfaces that render Identity information will need to source their data from the new system parachain. Note: In the future, it may make sense to decommission Kusama's Identity chain and do all account identities via Polkadot's. However, the Kusama chain will serve as a dress rehearsal for Polkadot. Staking Migrating the staking subsystem will likely be the most complex technical undertaking, as the Staking system cannot stop (the system MUST always have a validator set) nor run in parallel (the system MUST have only one validator set) and the subsystem itself is made up of subsystems in the runtime and the node. For example, if offences are reported to the Staking parachain, validator nodes will need to submit their reports there. Handling balances also introduces complications. The same balance can be used for staking and governance. Ideally, all balances stay on Asset Hub, and only report \"credits\" to system chains like Staking and Governance. However, staking mutates balances by issuing new DOT on era changes and for rewards. Allowing DOT directly on the Staking parachain would simplify staking changes. Given the complexity, it would be pragmatic to include the Balances pallet in the Staking parachain in its first version. Any other systems that use overlapping locks, most notably governance, will need to recognise DOT held on both Asset Hub and the Staking parachain. There is more discussion about staking in a parachain in Moving Staking off the Relay Chain . Governance Migrating governance into a parachain will be less complicated than staking. Most of the primitives needed for the migration already exist. The Treasury supports spending assets on remote chains and collectives like the Polkadot Technical Fellowship already function in a parachain. That is, XCM already provides the ability to express system origins across chains. Therefore, actually moving the governance logic into a parachain will be simple. It can run in parallel with the Relay Chain's governance, which can be removed when the parachain has demonstrated sufficient functionality. It's possible that the Relay Chain maintain a Root-level emergency track for situations like parachains halting . The only complication arises from the fact that both Asset Hub and the Staking parachain will have DOT balances; therefore, the Governance chain will need to be able to credit users' voting power based on balances from both locations. This is not expected to be difficult to handle.","breadcrumbs":"RFC-0032: Minimal Relay » Deployment","id":"361","title":"Deployment"},"362":{"body":"Although Polkadot and Kusama both have system chains running, they have to date only been used for introducing new features or bodies, for example fungible assets or the Technical Fellowship. There has not yet been a migration of logic/state from the Relay Chain into a parachain. Given its more realistic network conditions than testnets, Kusama is the best stage for rehearsal. In the case of identity, Polkadot's system may be sufficient for the ecosystem. Therefore, Kusama should be used to test the migration of logic and state from Relay Chain to parachain, but these features may be (at the will of Kusama's governance) dropped from Kusama entirely after a successful migration on Polkadot. For Governance, Polkadot already has the Collectives parachain, which would become the Governance parachain. The entire group of DOT holders is itself a collective (the legislative body), and governance provides the means to express voice. Launching a Kusama Governance chain would be sensible to rehearse a migration. The Staking subsystem is perhaps where Kusama would provide the most value in its canary capacity. Staking is the subsystem most constrained by PoV limits. Ensuring that elections, payouts, session changes, offences/slashes, etc. work in a parachain on Kusama -- with its larger validator set -- will give confidence to the chain's robustness on Polkadot.","breadcrumbs":"RFC-0032: Minimal Relay » Kusama","id":"362","title":"Kusama"},"363":{"body":"These subsystems will have reduced resources in cores than on the Relay Chain. Staking in particular may require some optimizations to deal with constraints.","breadcrumbs":"RFC-0032: Minimal Relay » Drawbacks","id":"363","title":"Drawbacks"},"364":{"body":"Standard audit/review requirements apply. More powerful multi-chain integration test tools would be useful in developement.","breadcrumbs":"RFC-0032: Minimal Relay » Testing, Security, and Privacy","id":"364","title":"Testing, Security, and Privacy"},"365":{"body":"Describe the impact of the proposal on the exposed functionality of Polkadot.","breadcrumbs":"RFC-0032: Minimal Relay » Performance, Ergonomics, and Compatibility","id":"365","title":"Performance, Ergonomics, and Compatibility"},"366":{"body":"This is an optimization. The removal of public/user transactions on the Relay Chain ensures that its primary resources are allocated to system performance.","breadcrumbs":"RFC-0032: Minimal Relay » Performance","id":"366","title":"Performance"},"367":{"body":"This proposal alters very little for coretime users (e.g. parachain developers). Application developers will need to interact with multiple chains, making ergonomic light client tools particularly important for application development. For existing parachains that interact with these subsystems, they will need to configure their runtimes to recognize the new locations in the network.","breadcrumbs":"RFC-0032: Minimal Relay » Ergonomics","id":"367","title":"Ergonomics"},"368":{"body":"Implementing this proposal will require some changes to pallet APIs and/or a pub-sub protocol. Application developers will need to interact with multiple chains in the network.","breadcrumbs":"RFC-0032: Minimal Relay » Compatibility","id":"368","title":"Compatibility"},"369":{"body":"Transactionless Relay-chain Moving Staking off the Relay Chain","breadcrumbs":"RFC-0032: Minimal Relay » Prior Art and References","id":"369","title":"Prior Art and References"},"37":{"body":"Since XCQ are supported both in off-chain and on-chain, a related XCM-Format RFC should be proposed.","breadcrumbs":"RFC-0126: Introduce XCQ(Cross Consensus Query) » Future Directions and Related Material","id":"37","title":"Future Directions and Related Material"},"370":{"body":"There remain some implementation questions, like how to use balances for both Staking and Governance. See, for example, Moving Staking off the Relay Chain .","breadcrumbs":"RFC-0032: Minimal Relay » Unresolved Questions","id":"370","title":"Unresolved Questions"},"371":{"body":"Ideally the Relay Chain becomes transactionless, such that not even balances are represented there. With Staking and Governance off the Relay Chain, this is not an unreasonable next step. With Identity on Polkadot, Kusama may opt to drop its People Chain.","breadcrumbs":"RFC-0032: Minimal Relay » Future Directions and Related Material","id":"371","title":"Future Directions and Related Material"},"372":{"body":"(source) Table of Contents RFC-0042: Add System version that replaces StateVersion on RuntimeVersion Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 25th October 2023 Description Add System Version and remove State Version Authors Vedhavyas Singareddi","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » RFC-0042: Add System version that replaces StateVersion on RuntimeVersion","id":"372","title":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion"},"373":{"body":"At the moment, we have system_version field on RuntimeVersion that derives which state version is used for the Storage. We have a use case where we want extrinsics root is derived using StateVersion::V1. Without defining a new field under RuntimeVersion, we would like to propose adding system_version that can be used to derive both storage and extrinsic state version.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Summary","id":"373","title":"Summary"},"374":{"body":"Since the extrinsic state version is always StateVersion::V0, deriving extrinsic root requires full extrinsic data. This would be problematic when we need to verify the extrinsics root if the extrinsic sizes are bigger. This problem is further explored in https://github.com/polkadot-fellows/RFCs/issues/19 For Subspace project, we have an enshrined rollups called Domain with optimistic verification and Fraud proofs are used to detect malicious behavior. One of the Fraud proof variant is to derive Domain block extrinsic root on Subspace's consensus chain. Since StateVersion::V0 requires full extrinsic data, we are forced to pass all the extrinsics through the Fraud proof. One of the main challenge here is some extrinsics could be big enough that this variant of Fraud proof may not be included in the Consensus block due to Block's weight restriction. If the extrinsic root is derived using StateVersion::V1, then we do not need to pass the full extrinsic data but rather at maximum, 32 byte of extrinsic data.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Motivation","id":"374","title":"Motivation"},"375":{"body":"Technical Fellowship, in its role of maintaining system runtimes.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Stakeholders","id":"375","title":"Stakeholders"},"376":{"body":"In order to use project specific StateVersion for extrinsic roots, we proposed an implementation that introduced parameter to frame_system::Config but that unfortunately did not feel correct. So we would like to propose adding this change to the RuntimeVersion object. The system version, if introduced, will be used to derive both storage and extrinsic state version. If system version is 0, then both Storage and Extrinsic State version would use V0. If system version is 1, then Storage State version would use V1 and Extrinsic State version would use V0. If system version is 2, then both Storage and Extrinsic State version would use V1. If implemented, the new RuntimeVersion definition would look something similar to /// Runtime version (Rococo).\n#[sp_version::runtime_version]\npub const VERSION: RuntimeVersion = RuntimeVersion { spec_name: create_runtime_str!(\"rococo\"), impl_name: create_runtime_str!(\"parity-rococo-v2.0\"), authoring_version: 0, spec_version: 10020, impl_version: 0, apis: RUNTIME_API_VERSIONS, transaction_version: 22, system_version: 1, };","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Explanation","id":"376","title":"Explanation"},"377":{"body":"There should be no drawbacks as it would replace state_version with same behavior but documentation should be updated so that chains know which system_version to use.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Drawbacks","id":"377","title":"Drawbacks"},"378":{"body":"AFAIK, should not have any impact on the security or privacy.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Testing, Security, and Privacy","id":"378","title":"Testing, Security, and Privacy"},"379":{"body":"These changes should be compatible for existing chains if they use state_version value for system_verision.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Performance, Ergonomics, and Compatibility","id":"379","title":"Performance, Ergonomics, and Compatibility"},"38":{"body":"(source) Table of Contents RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups Background Motivation Requirements Stakeholders JAM Service Design Overview Refine: Key Validation Process: Storage Proofs Accumulate Transfer Beefy Service PoC Implementation Gas + Storage Considerations Compatibility Testing, Security, and Privacy Future Directions and Related Material Drawbacks, Alternatives, and Unknowns Start Date 26 October 2024 Description JAM Service for Securing Ethereum Optimistic Rollups Authors Sourabh Niyogi Abstract JAM's rollup host function can be extended from Polkadot rollups to non-Polkadot rollups. We outline the design of a JAM service capable of securing Ethereum optimistic rollups, such as OP Stack and ArbOS. This service transforms optimistic rollups to cynical rollups, allowing users to benefit from the finality and high throughput of JAM, alongside JAM's anticipated messaging service. This JAM service's competitive advantage enables rollup operators to choose JAM/Polkadot over Ethereum or other rollup providers. A precise design for the service's refine-accumulate function is outlined, using tools already available.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups","id":"38","title":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups"},"380":{"body":"I do not believe there is any performance hit with this change.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Performance","id":"380","title":"Performance"},"381":{"body":"This does not break any exposed Apis.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Ergonomics","id":"381","title":"Ergonomics"},"382":{"body":"This change should not break any compatibility.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Compatibility","id":"382","title":"Compatibility"},"383":{"body":"We proposed introducing a similar change by introducing a parameter to frame_system::Config but did not feel that is the correct way of introducing this change.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Prior Art and References","id":"383","title":"Prior Art and References"},"384":{"body":"I do not have any specific questions about this change at the moment.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Unresolved Questions","id":"384","title":"Unresolved Questions"},"385":{"body":"IMO, this change is pretty self-contained and there won't be any future work necessary.","breadcrumbs":"RFC-0042: Add System version that replaces StateVersion on RuntimeVersion » Future Directions and Related Material","id":"385","title":"Future Directions and Related Material"},"386":{"body":"(source) Table of Contents RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization Summary Motivation Stakeholders Explanation Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Start Date 30 October 2023 Description Host function to provide the storage proof size to runtimes. Authors Sebastian Kunert","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization","id":"386","title":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization"},"387":{"body":"This RFC proposes a new host function for parachains, storage_proof_size. It shall provide the size of the currently recorded storage proof to the runtime. Runtime authors can use the proof size to improve block utilization by retroactively reclaiming unused storage weight.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Summary","id":"387","title":"Summary"},"388":{"body":"The number of extrinsics that are included in a parachain block is limited by two constraints: execution time and proof size. FRAME weights cover both concepts, and block-builders use them to decide how many extrinsics to include in a block. However, these weights are calculated ahead of time by benchmarking on a machine with reference hardware. The execution-time properties of the state-trie and its storage items are unknown at benchmarking time. Therefore, we make some assumptions about the state-trie: Trie Depth: We assume a trie depth to account for intermediary nodes. Storage Item Size: We make a pessimistic assumption based on the MaxEncodedLen trait. These pessimistic assumptions lead to an overestimation of storage weight, negatively impacting block utilization on parachains. In addition, the current model does not account for multiple accesses to the same storage items. While these repetitive accesses will not increase storage-proof size, the runtime-side weight monitoring will account for them multiple times. Since the proof size is completely opaque to the runtime, we can not implement retroactive storage weight correction. A solution must provide a way for the runtime to track the exact storage-proof size consumed on a per-extrinsic basis.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Motivation","id":"388","title":"Motivation"},"389":{"body":"Parachain Teams: They MUST include this host function in their runtime and node. Light-client Implementors: They SHOULD include this host function in their runtime and node.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Stakeholders","id":"389","title":"Stakeholders"},"39":{"body":"The Gray Paper suggests a design for applying the same audit protocol from Polkadot's parachain validation service to ETH rollups: \" Smart-contract state may be held in a coherent format on the JAM chain so long as any updates are made through the 15kb/core/sec work results, which would need to contain only the hashes of the altered contracts’ state roots . \" This proposal concretely addresses two top non-Polkadot optimistic rollup platforms: OP Stack and ArbOS . Optimistic rollups use centralized sequencers and have no forks, creating an illusion of fast finality while actually relying on delayed fraud proofs. Optimistic rollups are termed \"optimistic\" because they assume transactions are valid by default, requiring fraud proofs on Ethereum L1 if a dispute arises. Currently, ORUs store L2 data on ETH L1, using EIP-4844's blob transactions or similar DA alternatives, just long enough to allow for fraud proof submission. This approach, however, incurs a cost: a 7-day exit window to accommodate fraud proofs. JAM Service can eliminate this long exit window by validating optimistic rollups.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Background","id":"39","title":"Background"},"390":{"body":"This RFC proposes a new host function that exposes the storage-proof size to the runtime. As a result, runtimes can implement storage weight reclaiming mechanisms that improve block utilization. This RFC proposes the following host function signature: fn ext_storage_proof_size_version_1() -> u64; The host function MUST return an unsigned 64-bit integer value representing the current proof size. In block-execution and block-import contexts, this function MUST return the current size of the proof. To achieve this, parachain node implementors need to enable proof recording for block imports. In other contexts, this function MUST return 18446744073709551615 (u64::MAX), which represents disabled proof recording.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Explanation","id":"390","title":"Explanation"},"391":{"body":"","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Performance, Ergonomics, and Compatibility","id":"391","title":"Performance, Ergonomics, and Compatibility"},"392":{"body":"Parachain nodes need to enable proof recording during block import to correctly implement the proposed host function. Benchmarking conducted with balance transfers has shown a performance reduction of around 0.6% when proof recording is enabled.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Performance","id":"392","title":"Performance"},"393":{"body":"The host function proposed in this RFC allows parachain runtime developers to keep track of the proof size. Typical usage patterns would be to keep track of the overall proof size or the difference between subsequent calls to the host function.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Ergonomics","id":"393","title":"Ergonomics"},"394":{"body":"Parachain teams will need to include this host function to upgrade.","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Compatibility","id":"394","title":"Compatibility"},"395":{"body":"Pull Request including proposed host function: PoV Reclaim (Clawback) Node Side . Issue with discussion: [FRAME core] Clawback PoV Weights For Dispatchables","breadcrumbs":"RFC-0043: Introduce storage_proof_size Host Function for Improved Parachain Block Utilization » Prior Art and References","id":"395","title":"Prior Art and References"},"396":{"body":"(source) Table of Contents RFC-0045: Lowering NFT Deposits on Asset Hub Summary Motivation Requirements Stakeholders Explanation Enhanced Approach to Further Lower Barriers for Entry Short- and Long-Term Plans Drawbacks Testing, Security, and Privacy Security concerns Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Unresolved Questions Addendum Enhanced Weak Governance Origin Model Function-Based Pricing Model Linking Deposit to USD(x) Value Start Date 2 November 2023 Description A proposal to reduce the minimum deposit required for collection creation on the Polkadot and Kusama Asset Hubs. Authors Aurora Poppyseed , Just_Luuuu , Viki Val , Joe Petrowski","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » RFC-0045: Lowering NFT Deposits on Asset Hub","id":"396","title":"RFC-0045: Lowering NFT Deposits on Asset Hub"},"397":{"body":"This RFC proposes changing the current deposit requirements on the Polkadot and Kusama Asset Hub for creating an NFT collection, minting an individual NFT, and lowering its corresponding metadata and attribute deposits. The objective is to lower the barrier to entry for NFT creators, fostering a more inclusive and vibrant ecosystem while maintaining network integrity and preventing spam.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Summary","id":"397","title":"Summary"},"398":{"body":"The current deposit of 10 DOT for collection creation (along with 0.01 DOT for item deposit and 0.2 DOT for metadata and attribute deposits) on the Polkadot Asset Hub and 0.1 KSM on Kusama Asset Hub presents a significant financial barrier for many NFT creators. By lowering the deposit requirements, we aim to encourage more NFT creators to participate in the Polkadot NFT ecosystem, thereby enriching the diversity and vibrancy of the community and its offerings. The initial introduction of a 10 DOT deposit was an arbitrary starting point that does not consider the actual storage footprint of an NFT collection. This proposal aims to adjust the deposit first to a value based on the deposit function, which calculates a deposit based on the number of keys introduced to storage and the size of corresponding values stored. Further, it suggests a direction for a future of calculating deposits variably based on adoption and/or market conditions. There is a discussion on tradeoffs of setting deposits too high or too low.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Motivation","id":"398","title":"Motivation"},"399":{"body":"Deposits SHOULD be derived from deposit function, adjusted by correspoding pricing mechansim.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Requirements","id":"399","title":"Requirements"},"4":{"body":"Runtime users, Runtime devs, Cross-chain dApps, Wallets.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Stakeholders","id":"4","title":"Stakeholders"},"40":{"body":"JAM is intended to host rollups rather than serve end users directly. A secure JAM service for Optimistic Rollups will expand JAM's service scope to include optimistic rollups and enhance their appeal with JAM's finality. This expanded focus on rollups will increase CoreTime demand, making JAM attractive to both existing and new optimistic rollups by reducing exit windows. This JAM Service converts optimistic rollups into cynical rollups, delivering a user experience advantage that is marketable. With popular CEXes (Coinbase, Kraken) adopting OP Stack, this improvement is highly visible to retail users, turning ORUs into CRUs \"Secured by JAM\" for a competitive edge.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Motivation","id":"40","title":"Motivation"},"400":{"body":"NFT Creators : Primary beneficiaries of the proposed change, particularly those who found the current deposit requirements prohibitive. NFT Platforms : As the facilitator of artists' relations, NFT marketplaces have a vested interest in onboarding new users and making their platforms more accessible. dApp Developers : Making the blockspace more accessible will encourage developers to create and build unique dApps in the Polkadot ecosystem. Polkadot Community : Stands to benefit from an influx of artists, creators, and diverse NFT collections, enhancing the overall ecosystem. Previous discussions have been held within the Polkadot Forum , with artists expressing their concerns about the deposit amounts.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Stakeholders","id":"400","title":"Stakeholders"},"401":{"body":"This RFC proposes a revision of the deposit constants in the configuration of the NFTs pallet on the Polkadot Asset Hub. The new deposit amounts would be determined by a standard deposit formula. As of v1.1.1, the Collection Deposit is 10 DOT and the Item Deposit is 0.01 DOT (see here ). Based on the storage footprint of these items, this RFC proposes changing them to: pub const NftsCollectionDeposit: Balance = system_para_deposit(1, 130);\npub const NftsItemDeposit: Balance = system_para_deposit(1, 164); This results in the following deposits (calculted using this repository ): Polkadot Name Current Rate (DOT) Calculated with Function (DOT) collectionDeposit 10 0.20064 itemDeposit 0.01 0.20081 metadataDepositBase 0.20129 0.20076 attributeDepositBase 0.2 0.2 Similarly, the prices for Kusama were calculated as: Kusama: Name Current Rate (KSM) Calculated with Function (KSM) collectionDeposit 0.1 0.006688 itemDeposit 0.001 0.000167 metadataDepositBase 0.006709666617 0.0006709666617 attributeDepositBase 0.00666666666 0.000666666666","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Explanation","id":"401","title":"Explanation"},"402":{"body":"This RFC proposes further lowering these deposits below the rate normally charged for such a storage footprint. This is based on the economic argument that sub-rate deposits are a subsididy for growth and adoption of a specific technology. If the NFT functionality on Polkadot gains adoption, it makes it more attractive for future entrants, who would be willing to pay the non-subsidized rate because of the existing community. Proposed Rate Adjustments parameter_types! { pub const NftsCollectionDeposit: Balance = system_para_deposit(1, 130); pub const NftsItemDeposit: Balance = system_para_deposit(1, 164) / 40; pub const NftsMetadataDepositBase: Balance = system_para_deposit(1, 129) / 10; pub const NftsAttributeDepositBase: Balance = system_para_deposit(1, 0) / 10; pub const NftsDepositPerByte: Balance = system_para_deposit(0, 1);\n} This adjustment would result in the following DOT and KSM deposit values: Name Proposed Rate Polkadot Proposed Rate Kusama collectionDeposit 0.20064 DOT 0.006688 KSM itemDeposit 0.005 DOT 0.000167 KSM metadataDepositBase 0.002 DOT 0.0006709666617 KSM attributeDepositBase 0.002 DOT 0.000666666666 KSM","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Enhanced Approach to Further Lower Barriers for Entry","id":"402","title":"Enhanced Approach to Further Lower Barriers for Entry"},"403":{"body":"The plan presented above is recommended as an immediate step to make Polkadot a more attractive place to launch NFTs, although one would note that a forty fold reduction in the Item Deposit is just as arbitrary as the value it was replacing. As explained earlier, this is meant as a subsidy to gain more momentum for NFTs on Polkadot. In the long term, an implementation should account for what should happen to the deposit rates assuming that the subsidy is successful and attracts a lot of deployments. Many options are discussed in the Addendum . The deposit should be calculated as a function of the number of existing collections with maximum DOT and stablecoin values limiting the amount. With asset rates available via the Asset Conversion pallet, the system could take the lower value required. A sigmoid curve would make sense for this application to avoid sudden rate changes, as in: $$ minDeposit + \\frac{\\mathrm{min(DotDeposit, StableDeposit) - minDeposit} }{\\mathrm{1 + e^{a - b * x}} }$$ where the constant a moves the inflection to lower or higher x values, the constant b adjusts the rate of the deposit increase, and the independent variable x is the number of collections or items, depending on application.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Short- and Long-Term Plans","id":"403","title":"Short- and Long-Term Plans"},"404":{"body":"Modifying deposit requirements necessitates a balanced assessment of the potential drawbacks. Highlighted below are cogent points extracted from the discourse on the Polkadot Forum conversation , which provide critical perspectives on the implications of such changes. Adjusting NFT deposit requirements on Polkadot and Kusama Asset Hubs involves key challenges: State Growth and Technical Concerns : Lowering deposit requirements can lead to increased blockchain state size, potentially causing state bloat. This growth needs to be managed to prevent strain on the network's resources and maintain operational efficiency. As stated earlier, the deposit levels proposed here are intentionally low with the thesis that future participants would pay the standard rate. Network Security and Market Response : Adapting to the cryptocurrency market's volatility is crucial. The mechanism for setting deposit amounts must be responsive yet stable, avoiding undue complexity for users. Economic Impact on Previous Stakeholders : The change could have varied economic effects on previous (before the change) creators, platform operators, and investors. Balancing these interests is essential to ensure the adjustment benefits the ecosystem without negatively impacting its value dynamics. However in the particular case of Polkadot and Kusama Asset Hub this does not pose a concern since there are very few collections currently and thus previous stakeholders wouldn't be much affected. As of date 9th January 2024 there are 42 collections on Polkadot Asset Hub and 191 on Kusama Asset Hub with a relatively low volume.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Drawbacks","id":"404","title":"Drawbacks"},"405":{"body":"","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Testing, Security, and Privacy","id":"405","title":"Testing, Security, and Privacy"},"406":{"body":"As noted above, state bloat is a security concern. In the case of abuse, governance could adapt by increasing deposit rates and/or using forceDestroy on collections agreed to be spam.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Security concerns","id":"406","title":"Security concerns"},"407":{"body":"","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Performance, Ergonomics, and Compatibility","id":"407","title":"Performance, Ergonomics, and Compatibility"},"408":{"body":"The primary performance consideration stems from the potential for state bloat due to increased activity from lower deposit requirements. It's vital to monitor and manage this to avoid any negative impact on the chain's performance. Strategies for mitigating state bloat, including efficient data management and periodic reviews of storage requirements, will be essential.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Performance","id":"408","title":"Performance"},"409":{"body":"The proposed change aims to enhance the user experience for artists, traders, and utilizers of Kusama and Polkadot Asset Hubs, making Polkadot and Kusama more accessible and user-friendly.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Ergonomics","id":"409","title":"Ergonomics"},"41":{"body":"Securing optimistic rollups with a JAM Service should be practical and require minimal changes by the ORU operator. Securing Polkadot rollups with a JAM Service should not be affected.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Requirements","id":"41","title":"Requirements"},"410":{"body":"The change does not impact compatibility as a redeposit function is already implemented.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Compatibility","id":"410","title":"Compatibility"},"411":{"body":"If this RFC is accepted, there should not be any unresolved questions regarding how to adapt the implementation of deposits for NFT collections.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Unresolved Questions","id":"411","title":"Unresolved Questions"},"412":{"body":"Several innovative proposals have been considered to enhance the network's adaptability and manage deposit requirements more effectively. The RFC recommends a mixture of the function-based model and the stablecoin model, but some tradeoffs of each are maintained here for those interested.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Addendum","id":"412","title":"Addendum"},"413":{"body":"The concept of a weak governance origin, controlled by a consortium like a system collective, has been proposed. This model would allow for dynamic adjustments of NFT deposit requirements in response to market conditions, adhering to storage deposit norms. Responsiveness : To address concerns about delayed responses, the model could incorporate automated triggers based on predefined market indicators, ensuring timely adjustments. Stability vs. Flexibility : Balancing stability with the need for flexibility is challenging. To mitigate the issue of frequent changes in DOT-based deposits, a mechanism for gradual and predictable adjustments could be introduced. Scalability : The model's scalability is a concern, given the numerous deposits across the system. A more centralized approach to deposit management might be needed to avoid constant, decentralized adjustments.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Enhanced Weak Governance Origin Model","id":"413","title":"Enhanced Weak Governance Origin Model"},"414":{"body":"Another proposal is to use a mathematical function to regulate deposit prices, initially allowing low prices to encourage participation, followed by a gradual increase to prevent network bloat. Choice of Function : A logarithmic or sigmoid function is favored over an exponential one, as these functions increase prices at a rate that encourages participation while preventing prohibitive costs. Adjustment of Constants : To finely tune the pricing rise, one of the function's constants could correlate with the total number of NFTs on Asset Hub. This would align the deposit requirements with the actual usage and growth of the network.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Function-Based Pricing Model","id":"414","title":"Function-Based Pricing Model"},"415":{"body":"This approach suggests pegging the deposit value to a stable currency like the USD, introducing predictability and stability for network users. Market Dynamics : One perspective is that fluctuations in native currency value naturally balance user participation and pricing, deterring network spam while encouraging higher-value collections. Conversely, there's an argument for allowing broader participation if the DOT/KSM value increases. Complexity and Risks : Implementing a USD-based pricing system could add complexity and potential risks. The implementation needs to be carefully designed to avoid unintended consequences, such as excessive reliance on external financial systems or currencies. Each of these proposals offers unique advantages and challenges. The optimal approach may involve a combination of these ideas, carefully adjusted to address the specific needs and dynamics of the Polkadot and Kusama networks.","breadcrumbs":"RFC-0045: Lowering NFT Deposits on Asset Hub » Linking Deposit to USD(x) Value","id":"415","title":"Linking Deposit to USD(x) Value"},"416":{"body":"(source) Table of Contents RFC-0047: Assignment of availability chunks to validators Summary Motivation Stakeholders Explanation Systematic erasure codes Availability recovery at present Availability recovery from systematic chunks Chunk assignment function Network protocol Upgrade path Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Appendix A Start Date 03 November 2023 Description An evenly-distributing indirection layer between availability chunks and validators. Authors Alin Dima","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » RFC-0047: Assignment of availability chunks to validators","id":"416","title":"RFC-0047: Assignment of availability chunks to validators"},"417":{"body":"Propose a way of permuting the availability chunk indices assigned to validators, in the context of recovering available data from systematic chunks , with the purpose of fairly distributing network bandwidth usage.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Summary","id":"417","title":"Summary"},"418":{"body":"Currently, the ValidatorIndex is always identical to the ChunkIndex. Since the validator array is only shuffled once per session, naively using the ValidatorIndex as the ChunkIndex would pose an unreasonable stress on the first N/3 validators during an entire session, when favouring availability recovery from systematic chunks. Therefore, the relay chain node needs a deterministic way of evenly distributing the first ~(N_VALIDATORS / 3) systematic availability chunks to different validators, based on the relay chain block and core. The main purpose is to ensure fair distribution of network bandwidth usage for availability recovery in general and in particular for systematic chunk holders.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Motivation","id":"418","title":"Motivation"},"419":{"body":"Relay chain node core developers.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Stakeholders","id":"419","title":"Stakeholders"},"42":{"body":"Optimistic Rollup Operators seeking shorter exit windows, lower costs, higher scalability, and DA. Web3 developers wanting to create applications on cynical rollups secured by JAM. DOT Holders aiming to increase CoreTime demand.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Stakeholders","id":"42","title":"Stakeholders"},"420":{"body":"","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Explanation","id":"420","title":"Explanation"},"421":{"body":"An erasure coding algorithm is considered systematic if it preserves the original unencoded data as part of the resulting code. The implementation of the erasure coding algorithm used for polkadot's availability data is systematic. Roughly speaking, the first N_VALIDATORS/3 chunks of data can be cheaply concatenated to retrieve the original data, without running the resource-intensive and time-consuming reconstruction algorithm. You can find the concatenation procedure of systematic chunks for polkadot's erasure coding algorithm here In a nutshell, it performs a column-wise concatenation with 2-byte chunks. The output could be zero-padded at the end, so scale decoding must be aware of the expected length in bytes and ignore trailing zeros (this assertion is already being made for regular reconstruction).","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Systematic erasure codes","id":"421","title":"Systematic erasure codes"},"422":{"body":"According to the polkadot protocol spec : A validator should request chunks by picking peers randomly and must recover at least f+1 chunks, where n=3f+k and k in {1,2,3}. For parity's polkadot node implementation, the process was further optimised. At this moment, it works differently based on the estimated size of the available data: (a) for small PoVs (up to 128 Kib), sequentially try requesting the unencoded data from the backing group, in a random order. If this fails, fallback to option (b). (b) for large PoVs (over 128 Kib), launch N parallel requests for the erasure coded chunks (currently, N has an upper limit of 50), until enough chunks were recovered. Validators are tried in a random order. Then, reconstruct the original data. All options require that after reconstruction, validators then re-encode the data and re-create the erasure chunks trie in order to check the erasure root.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Availability recovery at present","id":"422","title":"Availability recovery at present"},"423":{"body":"As part of the effort of increasing polkadot's resource efficiency, scalability and performance , work is under way to modify the Availability Recovery protocol by leveraging systematic chunks. See this comment for preliminary performance results. In this scheme, the relay chain node will first attempt to retrieve the ~N/3 systematic chunks from the validators that should hold them, before falling back to recovering from regular chunks, as before. A re-encoding step is still needed for verifying the erasure root, so the erasure coding overhead cannot be completely brought down to 0. Not being able to retrieve even one systematic chunk would make systematic reconstruction impossible. Therefore, backers can be used as a backup to retrieve a couple of missing systematic chunks, before falling back to retrieving regular chunks.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Availability recovery from systematic chunks","id":"423","title":"Availability recovery from systematic chunks"},"424":{"body":"Properties The function that decides the chunk index for a validator will be parameterized by at least (validator_index, core_index) and have the following properties: deterministic relatively quick to compute and resource-efficient. when considering a fixed core_index, the function should describe a permutation of the chunk indices the validators that map to the first N/3 chunk indices should have as little overlap as possible for different cores. In other words, we want a uniformly distributed, deterministic mapping from ValidatorIndex to ChunkIndex per core. It's desirable to not embed this function in the runtime, for performance and complexity reasons. However, this means that the function needs to be kept very simple and with minimal or no external dependencies. Any change to this function could result in parachains being stalled and needs to be coordinated via a runtime upgrade or governance call. Proposed function Pseudocode: pub fn get_chunk_index( n_validators: u32, validator_index: ValidatorIndex, core_index: CoreIndex\n) -> ChunkIndex { let threshold = systematic_threshold(n_validators); // Roughly n_validators/3 let core_start_pos = core_index * threshold; (core_start_pos + validator_index) % n_validators\n}","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Chunk assignment function","id":"424","title":"Chunk assignment function"},"425":{"body":"The request-response /req_chunk protocol will be bumped to a new version (from v1 to v2). For v1, the request and response payloads are: /// Request an availability chunk.\npub struct ChunkFetchingRequest { /// Hash of candidate we want a chunk for. pub candidate_hash: CandidateHash, /// The index of the chunk to fetch. pub index: ValidatorIndex,\n} /// Receive a requested erasure chunk.\npub enum ChunkFetchingResponse { /// The requested chunk data. Chunk(ChunkResponse), /// Node was not in possession of the requested chunk. NoSuchChunk,\n} /// This omits the chunk's index because it is already known by\n/// the requester and by not transmitting it, we ensure the requester is going to use his index\n/// value for validating the response, thus making sure he got what he requested.\npub struct ChunkResponse { /// The erasure-encoded chunk of data belonging to the candidate block. pub chunk: Vec, /// Proof for this chunk's branch in the Merkle tree. pub proof: Proof,\n} Version 2 will add an index field to ChunkResponse: #[derive(Debug, Clone, Encode, Decode)]\npub struct ChunkResponse { /// The erasure-encoded chunk of data belonging to the candidate block. pub chunk: Vec, /// Proof for this chunk's branch in the Merkle tree. pub proof: Proof, /// Chunk index. pub index: ChunkIndex\n} An important thing to note is that in version 1, the ValidatorIndex value is always equal to the ChunkIndex. Until the chunk rotation feature is enabled, this will also be true for version 2. However, after the feature is enabled, this will generally not be true. The requester will send the request to validator with index V. The responder will map the V validator index to the C chunk index and respond with the C-th chunk. This mapping can be seamless, by having each validator store their chunk by ValidatorIndex (just as before). The protocol implementation MAY check the returned ChunkIndex against the expected mapping to ensure that it received the right chunk. In practice, this is desirable during availability-distribution and systematic chunk recovery. However, regular recovery may not check this index, which is particularly useful when participating in disputes that don't allow for easy access to the validator->chunk mapping. See Appendix A for more details. In any case, the requester MUST verify the chunk's proof using the provided index. During availability-recovery, given that the requester may not know (if the mapping is not available) whether the received chunk corresponds to the requested validator index, it has to keep track of received chunk indices and ignore duplicates. Such duplicates should be considered the same as an invalid/garbage response (drop it and move on to the next validator - we can't punish via reputation changes, because we don't know which validator misbehaved).","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Network protocol","id":"425","title":"Network protocol"},"426":{"body":"Step 1: Enabling new network protocol In the beginning, both /req_chunk/1 and /req_chunk/2 will be supported, until all validators and collators have upgraded to use the new version. V1 will be considered deprecated. During this step, the mapping will still be 1:1 (ValidatorIndex == ChunkIndex), regardless of protocol. Once all nodes are upgraded, a new release will be cut that removes the v1 protocol. Only once all nodes have upgraded to this version will step 2 commence. Step 2: Enabling the new validator->chunk mapping Considering that the Validator->Chunk mapping is critical to para consensus, the change needs to be enacted atomically via governance, only after all validators have upgraded the node to a version that is aware of this mapping, functionality-wise. It needs to be explicitly stated that after the governance enactment, validators that run older client versions that don't support this mapping will not be able to participate in parachain consensus. Additionally, an error will be logged when starting a validator with an older version, after the feature was enabled. On the other hand, collators will not be required to upgrade in this step (but are still require to upgrade for step 1), as regular chunk recovery will work as before, granted that version 1 of the networking protocol has been removed. Note that collators only perform availability-recovery in rare, adversarial scenarios, so it is fine to not optimise for this case and let them upgrade at their own pace. To support enabling this feature via the runtime, we will use the NodeFeatures bitfield of the HostConfiguration struct (added in https://github.com/paritytech/polkadot-sdk/pull/2177). Adding and enabling a feature with this scheme does not require a runtime upgrade, but only a referendum that issues a Configuration::set_node_feature extrinsic. Once the feature is enabled and new configuration is live, the validator->chunk mapping ceases to be a 1:1 mapping and systematic recovery may begin.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Upgrade path","id":"426","title":"Upgrade path"},"427":{"body":"Getting access to the core_index that used to be occupied by a candidate in some parts of the dispute protocol is very complicated (See appendix A ). This RFC assumes that availability-recovery processes initiated during disputes will only use regular recovery, as before. This is acceptable since disputes are rare occurrences in practice and is something that can be optimised later, if need be. Adding the core_index to the CandidateReceipt would mitigate this problem and will likely be needed in the future for CoreJam and/or Elastic scaling. Related discussion about updating CandidateReceipt It's a breaking change that requires all validators and collators to upgrade their node version at least once.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Drawbacks","id":"427","title":"Drawbacks"},"428":{"body":"Extensive testing will be conducted - both automated and manual. This proposal doesn't affect security or privacy.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Testing, Security, and Privacy","id":"428","title":"Testing, Security, and Privacy"},"429":{"body":"","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Performance, Ergonomics, and Compatibility","id":"429","title":"Performance, Ergonomics, and Compatibility"},"43":{"body":"","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » JAM Service Design","id":"43","title":"JAM Service Design"},"430":{"body":"This is a necessary data availability optimisation, as reed-solomon erasure coding has proven to be a top consumer of CPU time in polkadot as we scale up the parachain block size and number of availability cores. With this optimisation, preliminary performance results show that CPU time used for reed-solomon coding/decoding can be halved and total POV recovery time decrease by 80% for large POVs. See more here .","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Performance","id":"430","title":"Performance"},"431":{"body":"Not applicable.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Ergonomics","id":"431","title":"Ergonomics"},"432":{"body":"This is a breaking change. See upgrade path section above. All validators and collators need to have upgraded their node versions before the feature will be enabled via a governance call.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Compatibility","id":"432","title":"Compatibility"},"433":{"body":"See comments on the tracking issue and the in-progress PR","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Prior Art and References","id":"433","title":"Prior Art and References"},"434":{"body":"Not applicable.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Unresolved Questions","id":"434","title":"Unresolved Questions"},"435":{"body":"This enables future optimisations for the performance of availability recovery, such as retrieving batched systematic chunks from backers/approval-checkers.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Future Directions and Related Material","id":"435","title":"Future Directions and Related Material"},"436":{"body":"This appendix details the intricacies of getting access to the core index of a candidate in parity's polkadot node. Here, core_index refers to the index of the core that a candidate was occupying while it was pending availability (from backing to inclusion). Availability-recovery can currently be triggered by the following phases in the polkadot protocol: During the approval voting process. By other collators of the same parachain. During disputes. Getting the right core index for a candidate can be troublesome. Here's a breakdown of how different parts of the node implementation can get access to it: The approval-voting process for a candidate begins after observing that the candidate was included. Therefore, the node has easy access to the block where the candidate got included (and also the core that it occupied). The pov_recovery task of the collators starts availability recovery in response to noticing a candidate getting backed, which enables easy access to the core index the candidate started occupying. Disputes may be initiated on a number of occasions: 3.a. is initiated by the validator as a result of finding an invalid candidate while participating in the approval-voting protocol. In this case, availability-recovery is not needed, since the validator already issued their vote. 3.b is initiated by the validator noticing dispute votes recorded on-chain. In this case, we can safely assume that the backing event for that candidate has been recorded and kept in memory. 3.c is initiated as a result of getting a dispute statement from another validator. It is possible that the dispute is happening on a fork that was not yet imported by this validator, so the subsystem may not have seen this candidate being backed. A naive attempt of solving 3.c would be to add a new version for the disputes request-response networking protocol. Blindly passing the core index in the network payload would not work, since there is no way of validating that the reported core_index was indeed the one occupied by the candidate at the respective relay parent. Another attempt could be to include in the message the relay block hash where the candidate was included. This information would be used in order to query the runtime API and retrieve the core index that the candidate was occupying. However, considering it's part of an unimported fork, the validator cannot call a runtime API on that block. Adding the core_index to the CandidateReceipt would solve this problem and would enable systematic recovery for all dispute scenarios.","breadcrumbs":"RFC-0047: Assignment of availability chunks to validators » Appendix A","id":"436","title":"Appendix A"},"437":{"body":"(source) Table of Contents RFC-0048: Generate ownership proof for SessionKeys Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 13 November 2023 Description Change SessionKeys runtime api to support generating an ownership proof for the on chain registration. Authors Bastian Köcher","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » RFC-0048: Generate ownership proof for SessionKeys","id":"437","title":"RFC-0048: Generate ownership proof for SessionKeys"},"438":{"body":"This RFC proposes to changes the SessionKeys::generate_session_keys runtime api interface. This runtime api is used by validator operators to generate new session keys on a node. The public session keys are then registered manually on chain by the validator operator. Before this RFC it was not possible by the on chain logic to ensure that the account setting the public session keys is also in possession of the private session keys. To solve this the RFC proposes to pass the account id of the account doing the registration on chain to generate_session_keys. Further this RFC proposes to change the return value of the generate_session_keys function also to not only return the public session keys, but also the proof of ownership for the private session keys. The validator operator will then need to send the public session keys and the proof together when registering new session keys on chain.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Summary","id":"438","title":"Summary"},"439":{"body":"When submitting the new public session keys to the on chain logic there doesn't exist any verification of possession of the private session keys. This means that users can basically register any kind of public session keys on chain. While the on chain logic ensures that there are no duplicate keys, someone could try to prevent others from registering new session keys by setting them first. While this wouldn't bring the \"attacker\" any kind of advantage, more like disadvantages (potential slashes on their account), it could prevent someone from e.g. changing its session key in the event of a private session key leak. After this RFC this kind of attack would not be possible anymore, because the on chain logic can verify that the sending account is in ownership of the private session keys.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Motivation","id":"439","title":"Motivation"},"44":{"body":"Rollups produce a sequence of blocks ${\\bf B}$ with headers ${\\bf H}$. The header ${\\bf H}$ contains a parent header hash ${\\bf H} p$ and a state root ${\\bf H} {r}$, which represents the global state after applying all block transactions. The transactions trie root is unnecessary here; validating the state trie root alone is sufficient for securing rollups. This JAM Service strategy, as hinted in the JAM Gray Paper, aggregates storage proofs of altered smart account/contract states into a chain of work packages. These validate an uninterrupted chain of an optimistic rollup's blocks against the state root ${\\bf H}_r$. Instead of relying on a promise that the state root is correct unless proven otherwise, JAM validates it using storage proofs for each contract update across $N$ blocks. The rollup operator submits headers and Merkle proofs in a chain of work packages $..., p_{n-1}, p_{n}, p_{n+1}, ...$ corresponding to the rollup chain, grouping $N$ blocks of data in each package. Typically, each work package $p_n$ requires a prerequisite work package $p_{n-1}$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Overview","id":"44","title":"Overview"},"440":{"body":"Polkadot runtime implementors Polkadot node implementors Validator operators","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Stakeholders","id":"440","title":"Stakeholders"},"441":{"body":"We are first going to explain the proof format being used: type Proof = (Signature, Signature, ..); The proof being a SCALE encoded tuple over all signatures of each private session key signing the account_id. The actual type of each signature depends on the corresponding session key cryptographic algorithm. The order of the signatures in the proof is the same as the order of the session keys in the SessionKeys type declared in the runtime. The version of the SessionKeys needs to be bumped to 1 to reflect the changes to the signature of SessionKeys_generate_session_keys: pub struct OpaqueGeneratedSessionKeys { pub keys: Vec, pub proof: Vec,\n} fn SessionKeys_generate_session_keys(account_id: Vec, seed: Option>) -> OpaqueGeneratedSessionKeys; The default calling convention for runtime apis is applied, meaning the parameters passed as SCALE encoded array and the length of the encoded array. The return value being the SCALE encoded return value as u64 (array_ptr | length << 32). So, the actual exported function signature looks like: fn SessionKeys_generate_session_keys(array: *const u8, len: usize) -> u64; The on chain logic for setting the SessionKeys needs to be changed as well. It already gets the proof passed as Vec. This proof needs to be decoded to the actual Proof type as explained above. The proof and the SCALE encoded account_id of the sender are used to verify the ownership of the SessionKeys.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Explanation","id":"441","title":"Explanation"},"442":{"body":"Validator operators need to pass the their account id when rotating their session keys in a node. This will require updating some high level docs and making users familiar with the slightly changed ergonomics.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Drawbacks","id":"442","title":"Drawbacks"},"443":{"body":"Testing of the new changes only requires passing an appropriate owner for the current testing context. The changes to the proof generation and verification got audited to ensure they are correct.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Testing, Security, and Privacy","id":"443","title":"Testing, Security, and Privacy"},"444":{"body":"","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Performance, Ergonomics, and Compatibility","id":"444","title":"Performance, Ergonomics, and Compatibility"},"445":{"body":"The session key generation is an offchain process and thus, doesn't influence the performance of the chain. Verifying the proof is done on chain as part of the transaction logic for setting the session keys. The verification of the proof is a signature verification number of individual session keys times. As setting the session keys is happening quite rarely, it should not influence the overall system performance.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Performance","id":"445","title":"Performance"},"446":{"body":"The interfaces have been optimized to make it as easy as possible to generate the ownership proof.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Ergonomics","id":"446","title":"Ergonomics"},"447":{"body":"Introduces a new version of the SessionKeys runtime api. Thus, nodes should be updated before a runtime is enacted that contains these changes otherwise they will fail to generate session keys. The RPC that exists around this runtime api needs to be updated to support passing the account id and for returning the ownership proof alongside the public session keys. UIs would need to be updated to support the new RPC and the changed on chain logic.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Compatibility","id":"447","title":"Compatibility"},"448":{"body":"None.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Prior Art and References","id":"448","title":"Prior Art and References"},"449":{"body":"None.","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Unresolved Questions","id":"449","title":"Unresolved Questions"},"45":{"body":"Key Input: Work Packages In JAM's refine code, work package content is as follows: JAM Refine Content Work Package $p_n \\in \\mathbb{P}$ Data submitted by ORU operator for validation of blocks $i$ through $j$ Payload ${\\bf y}$ Chain ID (e.g., 10, 42161, etc.), start and end block numbers expected in extrinsics Imported Data Segment ${\\bf i}$ Last ${\\bf H}$ validated by the service in the previous work package $p_{n-1}$ Extrinsics $\\bar{{\\bf x}}$ Header ${\\bf H}$, block hash $H({\\bf B})$, and Merkle proofs $\\Pi$ detailed below Work Items ${\\bf w} \\in \\mathbb{I}$ Summary of the first and last blocks ($i$ to $j$) Exported Data Segment ${\\bf e}$ Last validated ${\\bf H}$, used in the next work package $p_{n+1}$ Work Result ${\\bf r}$ $N$ header hashes $H({\\bf H})$ and $N$ block hashes $H({\\bf B})$ Refine's operations: Check for authorization ${\\bf o}$. Perform historical_lookup to fetch the last on-chain state in the anchor block. Import the last header ${\\bf H}$ and confirm that the imported data segment ${\\bf i}$ matches the historical_lookup. For each extrinsic header in ${\\bf H}$: Ensure that each header forms a chain, with ${\\bf H}_p$ matching the previous extrinsic $H({\\bf H})$, except for the first header, which must match the previous 2. Using the state root ${\\bf H}_r$, validate all Merkle proofs. Export the header of the last extrinsic successfully validated. Output the work result, up to $2(j-i+1)$ hashes: two hashes per extrinsic, $H({\\bf H})$ and $H({\\bf B})$. The refine process uses 3 host functions, with the main computation focused on Merkle proof validation. As detailed in GP, work results in guaranteed work reports are assured, audited, and judged following the ELVES protocol. JAM finalizes its audited blocks via GRANDPA voting, ensuring the rollup’s state can be trusted for subsequent operations.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Refine:","id":"45","title":"Refine:"},"450":{"body":"Substrate implementation of the RFC .","breadcrumbs":"RFC-0048: Generate ownership proof for SessionKeys » Future Directions and Related Material","id":"450","title":"Future Directions and Related Material"},"451":{"body":"(source) Table of Contents RFC-0050: Fellowship Salaries Summary Motivation Stakeholders Explanation Salary Asset Projections Updates Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 15 November 2023 Description Proposal to set rank-based Fellowship salary levels. Authors Joe Petrowski, Gavin Wood","breadcrumbs":"RFC-0050: Fellowship Salaries » RFC-0050: Fellowship Salaries","id":"451","title":"RFC-0050: Fellowship Salaries"},"452":{"body":"The Fellowship Manifesto states that members should receive a monthly allowance on par with gross income in OECD countries. This RFC proposes concrete amounts.","breadcrumbs":"RFC-0050: Fellowship Salaries » Summary","id":"452","title":"Summary"},"453":{"body":"One motivation for the Technical Fellowship is to provide an incentive mechanism that can induct and retain technical talent for the continued progress of the network. In order for members to uphold their commitment to the network, they should receive support to ensure that their needs are met such that they have the time to dedicate to their work on Polkadot. Given the high expectations of Fellows, it is reasonable to consider contributions and requirements on par with a full-time job. Providing a livable wage to those making such contributions makes it pragmatic to work full-time on Polkadot. Note: Goals of the Fellowship, expectations for each Dan, and conditions for promotion and demotion are all explained in the Manifesto. This RFC is only to propose concrete values for allowances.","breadcrumbs":"RFC-0050: Fellowship Salaries » Motivation","id":"453","title":"Motivation"},"454":{"body":"Fellowship members Polkadot Treasury","breadcrumbs":"RFC-0050: Fellowship Salaries » Stakeholders","id":"454","title":"Stakeholders"},"455":{"body":"This RFC proposes agreeing on salaries relative to a single level, the III Dan. As such, changes to the amount or asset used would only be on a single value, and all others would adjust relatively. A III Dan is someone whose contributions match the expectations of a full-time individual contributor. The salary at this level should be reasonably close to averages in OECD countries. Dan Factor I 0.125 II 0.25 III 1 IV 1.5 V 2.0 VI 2.5 VII 2.5 VIII 2.5 IX 2.5 Note that there is a sizable increase between II Dan (Proficient) and III Dan (Fellow). By the third Dan, it is generally expected that one is working on Polkadot as their primary focus in a full-time capacity.","breadcrumbs":"RFC-0050: Fellowship Salaries » Explanation","id":"455","title":"Explanation"},"456":{"body":"Although the Manifesto (Section 8) specifies a monthly allowance in DOT, this RFC proposes the use of USDT instead. The allowance is meant to provide members stability in meeting their day-to-day needs and recognize contributions. Using USDT provides more stability and less speculation. This RFC proposes that a III Dan earn 80,000 USDT per year. The salary at this level is commensurate with average salaries in OECD countries (note: 77,000 USD in the U.S., with an average engineer at 100,000 USD). The other ranks would thus earn: Dan Annual Salary I 10,000 II 20,000 III 80,000 IV 120,000 V 160,000 VI 200,000 VII 200,000 VIII 200,000 IX 200,000 The salary levels for Architects (IV, V, and VI Dan) are typical of senior engineers. Allowances will be managed by the Salary pallet.","breadcrumbs":"RFC-0050: Fellowship Salaries » Salary Asset","id":"456","title":"Salary Asset"},"457":{"body":"Based on the current membership, the maximum yearly and monthly costs are shown below: Dan Salary Members Yearly Monthly I 10,000 27 270,000 22,500 II 20,000 11 220,000 18,333 III 80,000 8 640,000 53,333 IV 120,000 3 360,000 30,000 V 160,000 5 800,000 66,667 VI 200,000 3 600,000 50,000 > VI 200,000 0 0 0 Total 2,890,000 240,833 Note that these are the maximum amounts; members may choose to take a passive (lower) level. On the other hand, more people will likely join the Fellowship in the coming years.","breadcrumbs":"RFC-0050: Fellowship Salaries » Projections","id":"457","title":"Projections"},"458":{"body":"Updates to these levels, whether relative ratios, the asset used, or the amount, shall be done via RFC.","breadcrumbs":"RFC-0050: Fellowship Salaries » Updates","id":"458","title":"Updates"},"459":{"body":"By not using DOT for payment, the protocol relies on the stability of other assets and the ability to acquire them. However, the asset of choice can be changed in the future.","breadcrumbs":"RFC-0050: Fellowship Salaries » Drawbacks","id":"459","title":"Drawbacks"},"46":{"body":"Optimistic rollups, including OP Stack and ArbOS, use Ethereum's Merkle Patricia Trie to commit to state data on each block. See this architecture diagram for an overview. The state root ${\\bf H}_r$ is a cryptographic commitment to the entire rollup state at that block height. Notably, validation does not calculate the state root ${\\bf H_r}$ based on block transactions , which would necessitate the entire state of the rollup. Instead, storage proofs (or \"witness data\") enable the ORU to prove that specific storage values exist within a particular state root. Only the last witness per contract address is needed in a work package of $N$ blocks. The central assumption is that if the work package proves all account/contract storage items over $N$ of blocks, which are guaranteed/assured/audited by a subset of JAM validators, then the sequence of state transitions in these blocks is valid. This chaining of state roots ensures continuity and trust in the rollup secured by this JAM Service: Each block’s state root can be verified against the previous state, allowing nodes to validate state changes trustlessly. Inclusion in Parent Block Hash: Since each block header ${\\bf H}$ includes the previous header hash ${\\bf H}_p$ and indirectly references the previous state root ${\\bf H}_r$, each block and header also serves as a cryptographic reference to the prior state. The core operation verifies proofs against the state root, enabling efficient, trustless block sequence validation based solely on headers, which are much smaller than full transaction blocks. For now, we consider 100% of storage keys and values output by the trace of a block. A more sophisticated approach to sample the set of storage keys based on JAM's public entropy $\\eta_3$ may be warranted to limit work packages to within JAM's limits, made available through historical_lookup operations.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Key Validation Process: Storage Proofs","id":"46","title":"Key Validation Process: Storage Proofs"},"460":{"body":"N/A.","breadcrumbs":"RFC-0050: Fellowship Salaries » Testing, Security, and Privacy","id":"460","title":"Testing, Security, and Privacy"},"461":{"body":"","breadcrumbs":"RFC-0050: Fellowship Salaries » Performance, Ergonomics, and Compatibility","id":"461","title":"Performance, Ergonomics, and Compatibility"},"462":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Performance","id":"462","title":"Performance"},"463":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Ergonomics","id":"463","title":"Ergonomics"},"464":{"body":"N/A","breadcrumbs":"RFC-0050: Fellowship Salaries » Compatibility","id":"464","title":"Compatibility"},"465":{"body":"The Polkadot Fellowship Manifesto OECD Average Wages Indeed: Average Salary for Engineers, United States","breadcrumbs":"RFC-0050: Fellowship Salaries » Prior Art and References","id":"465","title":"Prior Art and References"},"466":{"body":"None at present.","breadcrumbs":"RFC-0050: Fellowship Salaries » Unresolved Questions","id":"466","title":"Unresolved Questions"},"467":{"body":"(source) Table of Contents RFC-0056: Enforce only one transaction per notification Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-11-30 Description Modify the transactions notifications protocol to always send only one transaction at a time Authors Pierre Krieger","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » RFC-0056: Enforce only one transaction per notification","id":"467","title":"RFC-0056: Enforce only one transaction per notification"},"468":{"body":"When two peers connect to each other, they open (amongst other things) a so-called \"notifications protocol\" substream dedicated to gossiping transactions to each other. Each notification on this substream currently consists in a SCALE-encoded Vec where Transaction is defined in the runtime. This RFC proposes to modify the format of the notification to become (Compact(1), Transaction). This maintains backwards compatibility, as this new format decodes as a Vec of length equal to 1.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Summary","id":"468","title":"Summary"},"469":{"body":"There exists three motivations behind this change: It is technically impossible to decode a SCALE-encoded Vec into a list of SCALE-encoded transactions without knowing how to decode a Transaction. That's because a Vec consists in several Transactions one after the other in memory, without any delimiter that indicates the end of a transaction and the start of the next. Unfortunately, the format of a Transaction is runtime-specific. This means that the code that receives notifications is necessarily tied to a specific runtime, and it is not possible to write runtime-agnostic code. Notifications protocols are already designed to be optimized to send many items. Currently, when it comes to transactions, each item is a Vec that consists in multiple sub-items of type Transaction. This two-steps hierarchy is completely unnecessary, and was originally written at a time when the networking protocol of Substrate didn't have proper multiplexing. It makes the implementation way more straight-forward by not having to repeat code related to back-pressure. See explanations below.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Motivation","id":"469","title":"Motivation"},"47":{"body":"The accumulate process ensures that all rollup data necessary to validate the rollup is available in JAM DA. Accumulate is an entirely synchronous on-chain operation performed by all JAM Validators (rather than in-core as with Refine). Computation is carried out first by the JAM Block Author and the newly authored block sent to all Validators. On-chain Storage of Rollup State The service maintains a summary of fully validated blocks of each chain in 3 service storage keys: the first block number $a$ validated with data fully available the last block number $b$ validated with data fully available a window parameter $w$, modeling the maximum $b-a$ For every block number in this range, the block number has its own key to store the header hash and the block hash. The function of this data storage represents both of the following: the refine validation has been completed and the block and header preimages are available in JAM's DA Key Process JAM Accumulate Content Wrangled Work Results Chain ID (e.g., 10, 42161, etc.), block number start $i$ and end $j$ followed by pairs of $H({\\bf H})$ and $H({\\bf B})$ read fetch $a, b, w$ based on Chain ID. Validate that $i=b+1$. solicit is called for both hashes in the wrangled work results. Advance $b$ by 1 if: both ${\\bf a}_l(H({\\bf B}))$ and ${\\bf a}_l(H({\\bf H}))$ are \"available\" the header ${\\bf H}$ is contained with ${\\bf B}$ If $b-a$ exceeds the window $w$, advance $a$ by 1 if both ${\\bf a}_l(H({\\bf B}))$ and ${\\bf a}_l(H({\\bf H}))$ are \"forget\". write $a$ and $b$ back to storage. Necessarily, the ORU operator must provide both preimages for the chain to be considered valid. If any block or header is not made available by the ORU operator, $b$ will not advance. Under normal operations, the above process will result in a full set of blocks and header preimages being in JAM's DA layer. Moreover, the forget operation ensures that storage is bounded by $w$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Accumulate","id":"47","title":"Accumulate"},"470":{"body":"Low-level developers.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Stakeholders","id":"470","title":"Stakeholders"},"471":{"body":"To give an example, if you send one notification with three transactions, the bytes that are sent on the wire are: concat( leb128(total-size-in-bytes-of-the-rest), scale(compact(3)), scale(transaction1), scale(transaction2), scale(transaction3)\n) But you can also send three notifications of one transaction each, in which case it is: concat( leb128(size(scale(transaction1)) + 1), scale(compact(1)), scale(transaction1), leb128(size(scale(transaction2)) + 1), scale(compact(1)), scale(transaction2), leb128(size(scale(transaction3)) + 1), scale(compact(1)), scale(transaction3)\n) Right now the sender can choose which of the two encoding to use. This RFC proposes to make the second encoding mandatory. The format of the notification would become a SCALE-encoded (Compact(1), Transaction). A SCALE-compact encoded 1 is one byte of value 4. In other words, the format of the notification would become concat(&[4], scale_encoded_transaction). This is equivalent to forcing the Vec to always have a length of 1, and I expect the Substrate implementation to simply modify the sending side to add a for loop that sends one notification per item in the Vec. As explained in the motivation section, this allows extracting scale(transaction) items without having to know how to decode them. By \"flattening\" the two-steps hierarchy, an implementation only needs to back-pressure individual notifications rather than back-pressure notifications and transactions within notifications.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Explanation","id":"471","title":"Explanation"},"472":{"body":"This RFC chooses to maintain backwards compatibility at the cost of introducing a very small wart (the Compact(1)). An alternative could be to introduce a new version of the transactions notifications protocol that sends one Transaction per notification, but this is significantly more complicated to implement and can always be done later in case the Compact(1) is bothersome.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Drawbacks","id":"472","title":"Drawbacks"},"473":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Testing, Security, and Privacy","id":"473","title":"Testing, Security, and Privacy"},"474":{"body":"","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Performance, Ergonomics, and Compatibility","id":"474","title":"Performance, Ergonomics, and Compatibility"},"475":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Performance","id":"475","title":"Performance"},"476":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Ergonomics","id":"476","title":"Ergonomics"},"477":{"body":"The change is backwards compatible if done in two steps: modify the sender to always send one transaction per notification, then, after a while, modify the receiver to enforce the new format.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Compatibility","id":"477","title":"Compatibility"},"478":{"body":"Irrelevant.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Prior Art and References","id":"478","title":"Prior Art and References"},"479":{"body":"None.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Unresolved Questions","id":"479","title":"Unresolved Questions"},"48":{"body":"Transfer details concerning fees of storage balance are not considered at this time. A full model appears to necessitate a clear interface between JAM and CoreTime as well as a model of how this service can support a single vs. multiple Chain IDs. Naturally, all service fees would be in DOT rather than ETH on L2. Multiple service instantiations under different CoreTime leases may be envisioned for each rollup, but a set of homogenous ORU rollups to support sync/async models by the same ORU operator could also be supported.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Transfer","id":"48","title":"Transfer"},"480":{"body":"None. This is a simple isolated change.","breadcrumbs":"RFC-0056: Enforce only one transaction per notification » Future Directions and Related Material","id":"480","title":"Future Directions and Related Material"},"481":{"body":"(source) Table of Contents RFC-0059: Add a discovery mechanism for nodes based on their capabilities Summary Motivation Stakeholders Explanation Capabilities DHT provider registration Secondary DHTs Head of the chain providers Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-12-18 Description Nodes having certain capabilities register themselves in the DHT to be discoverable Authors Pierre Krieger","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » RFC-0059: Add a discovery mechanism for nodes based on their capabilities","id":"481","title":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities"},"482":{"body":"This RFC proposes to make the mechanism of RFC #8 more generic by introducing the concept of \"capabilities\". Implementations can implement certain \"capabilities\", such as serving old block headers or being a parachain bootnode. The discovery mechanism of RFC #8 is extended to be able to discover nodes of specific capabilities.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Summary","id":"482","title":"Summary"},"483":{"body":"The Polkadot peer-to-peer network is made of nodes. Not all these nodes are equal. Some nodes store only the headers of recent blocks, some nodes store all the block headers and bodies since the genesis, some nodes store the storage of all blocks since the genesis, and so on. It is currently not possible to know ahead of time (without connecting to it and asking) which nodes have which data available, and it is not easily possible to build a list of nodes that have a specific piece of data available. If you want to download for example the header of block 500, you have to connect to a randomly-chosen node, ask it for block 500, and if it says that it doesn't have the block, disconnect and try another randomly-chosen node. In certain situations such as downloading the storage of old blocks, nodes that have the information are relatively rare, and finding through trial and error a node that has the data can take a long time. This RFC attempts to solve this problem by giving the possibility to build a list of nodes that are capable of serving specific data.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Motivation","id":"483","title":"Motivation"},"484":{"body":"Low-level client developers. People interested in accessing the archive of the chain.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Stakeholders","id":"484","title":"Stakeholders"},"485":{"body":"Reading RFC #8 first might help with comprehension, as this RFC is very similar. Please keep in mind while reading that everything below applies for both relay chains and parachains, except mentioned otherwise.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Explanation","id":"485","title":"Explanation"},"486":{"body":"This RFC defines a list of so-called capabilities : Head of chain provider . An implementation with this capability must be able to serve to other nodes block headers, block bodies, justifications, calls proofs, and storage proofs of \"recent\" (see below) blocks, and, for relay chains, to serve to other nodes warp sync proofs where the starting block is a session change block and must participate in Grandpa and Beefy gossip. History provider . An implementation with this capability must be able to serve to other nodes block headers and block bodies of any block since the genesis, and must be able to serve to other nodes justifications of any session change block since the genesis up until and including their currently finalized block. Archive provider . This capability is a superset of History provider . In addition to the requirements of History provider , an implementation with this capability must be able to serve call proofs and storage proof requests of any block since the genesis up until and including their currently finalized block. Parachain bootnode (only for relay chains). An implementation with this capability must be able to serve the network request described in RFC 8. More capabilities might be added in the future. In the context of the head of chain provider , the word \"recent\" means: any not-finalized-yet block that is equal to or an ancestor of a block that it has announced through a block announce, and any finalized block whose height is superior to its current finalized block minus 16 . This does not include blocks that have been pruned because they're not a descendant of its current finalized block. In other words, blocks that aren't a descendant of the current finalized block can be thrown away. A gap of blocks is required due to race conditions: when a node finalizes a block, it takes some time for its peers to be made aware of this, during which they might send requests concerning older blocks. The choice of the number of blocks in this gap is arbitrary. Substrate is currently by default a head of chain provider provider. After it has finished warp syncing, it downloads the list of old blocks, after which it becomes a history provider . If Substrate is instead configured as an archive node, then it downloads all blocks since the genesis and builds their state, after which it becomes an archive provider , history provider , and head of chain provider . If blocks pruning is enabled and the chain is a relay chain, then Substrate unfortunately doesn't implement any of these capabilities, not even head of chain provider . This is considered as a bug that should be fixed, see https://github.com/paritytech/polkadot-sdk/issues/2733 .","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Capabilities","id":"486","title":"Capabilities"},"487":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . Implementations that have the history provider capability should register themselves as providers under the key sha256(concat(\"history\", randomness)). Implementations that have the archive provider capability should register themselves as providers under the key sha256(concat(\"archive\", randomness)). Implementations that have the parachain bootnode capability should register themselves as provider under the key sha256(concat(scale_compact(para_id), randomness)), as described in RFC 8. \"Register themselves as providers\" consists in sending ADD_PROVIDER requests to nodes close to the key, as described in the Content provider advertisement section of the specification. The value of randomness can be found in the randomness field when calling the BabeApi_currentEpoch function. In order to avoid downtimes when the key changes, nodes should also register themselves as a secondary key that uses a value of randomness equal to the randomness field when calling BabeApi_nextEpoch. Implementers should be aware that their implementation of Kademlia might already hash the key before XOR'ing it. The key is not meant to be hashed twice. Implementations must not register themselves if they don't fulfill the capability yet . For example, a node configured to be an archive node but that is still building its archive state in the background must register itself only after it has finished building its archive.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » DHT provider registration","id":"487","title":"DHT provider registration"},"488":{"body":"Implementations that have the history provider capability must also participate in a secondary DHT that comprises only of nodes with that capability. The protocol name of that secondary DHT must be //kad/history. Similarly, implementations that have the archive provider capability must also participate in a secondary DHT that comprises only of nodes with that capability and whose protocol name is //kad/archive. Just like implementations must not register themselves if they don't fulfill their capability yet, they must also not participate in the secondary DHT if they don't fulfill their capability yet.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Secondary DHTs","id":"488","title":"Secondary DHTs"},"489":{"body":"Implementations that have the head of the chain provider capability do not register themselves as providers, but instead are the nodes that participate in the main DHT. In other words, they are the nodes that serve requests of the //kad protocol. Any implementation that isn't a head of the chain provider (read: light clients) must not participate in the main DHT. This is already presently the case. Implementations must not participate in the main DHT if they don't fulfill the capability yet. For example, a node that is still in the process of warp syncing must not participate in the main DHT. However, assuming that warp syncing doesn't last more than a few seconds, it is acceptable to ignore this requirement in order to avoid complicating implementations too much.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Head of the chain providers","id":"489","title":"Head of the chain providers"},"49":{"body":"Following the BEEFY protocol, JAM's own state trie aggregates work packages' accumulate roots into its own recent history $\\beta$, signed by JAM validators. BEEFY’s model allows JAM's state to be verified on Ethereum and other external chains without needing all JAM Chain data on the external chain. All rollups, whether built on Substrate or optimistic turned cynical, are committed into this state, supporting cross-ecosystem proofs using Merkle trees as today. To support this goal, the accumulate result is the last block hash, last header hash, or last state root as suitable to match Polkadot rollup behavior.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Beefy","id":"49","title":"Beefy"},"490":{"body":"None that I can see.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Drawbacks","id":"490","title":"Drawbacks"},"491":{"body":"The content of this section is basically the same as the one in RFC 8. This mechanism doesn't add or remove any security by itself, as it relies on existing mechanisms. Due to the way Kademlia works, it would become the responsibility of the 20 Polkadot nodes whose sha256(peer_id) is closest to the key (described in the explanations section) to store the list of nodes that have specific capabilities. Furthermore, when a large number of providers are registered, only the providers closest to the key are kept, up to a certain implementation-defined limit. For this reason, an attacker can abuse this mechanism by randomly generating libp2p PeerIds until they find the 20 entries closest to the key representing the target capability. They are then in control of the list of nodes with that capability. While doing this can in no way be actually harmful, it could lead to eclipse attacks. Because the key changes periodically and isn't predictable, and assuming that the Polkadot DHT is sufficiently large, it is not realistic for an attack like this to be maintained in the long term.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Testing, Security, and Privacy","id":"491","title":"Testing, Security, and Privacy"},"492":{"body":"","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Performance, Ergonomics, and Compatibility","id":"492","title":"Performance, Ergonomics, and Compatibility"},"493":{"body":"The DHT mechanism generally has a low overhead, especially given that publishing providers is done only every 24 hours. Doing a Kademlia iterative query then sending a provider record shouldn't take more than around 50 kiB in total of bandwidth for the parachain bootnode. Assuming 1000 nodes with a specific capability, the 20 Polkadot full nodes corresponding to that capability will each receive a sudden spike of a few megabytes of networking traffic when the key rotates. Again, this is relatively negligible. If this becomes a problem, one can add a random delay before a node registers itself to be the provider of the key corresponding to BabeApi_next_epoch. Maybe the biggest uncertainty is the traffic that the 20 Polkadot full nodes will receive from light clients that desire knowing the nodes with a capability. If this every becomes a problem, this value of 20 is an arbitrary constant that can be increased for more redundancy.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Performance","id":"493","title":"Performance"},"494":{"body":"Irrelevant.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Ergonomics","id":"494","title":"Ergonomics"},"495":{"body":"Irrelevant.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Compatibility","id":"495","title":"Compatibility"},"496":{"body":"Unknown.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Prior Art and References","id":"496","title":"Prior Art and References"},"497":{"body":"While it fundamentally doesn't change much to this RFC, using BabeApi_currentEpoch and BabeApi_nextEpoch might be inappropriate. I'm not familiar enough with good practices within the runtime to have an opinion here. Should it be an entirely new pallet?","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Unresolved Questions","id":"497","title":"Unresolved Questions"},"498":{"body":"This RFC would make it possible to reliably discover archive nodes, which would make it possible to reliably send archive node requests, something that isn't currently possible. This could solve the problem of finding archive RPC node providers by migrating archive-related request to using the native peer-to-peer protocol rather than JSON-RPC. If we ever decide to break backwards compatibility, we could divide the \"history\" and \"archive\" capabilities in two, between nodes capable of serving older blocks and nodes capable of serving newer blocks. We could even add to the peer-to-peer network nodes that are only capable of serving older blocks (by reading from a database) but do not participate in the head of the chain, and that just exist for historical purposes.","breadcrumbs":"RFC-0059: Add a discovery mechanism for nodes based on their capabilities » Future Directions and Related Material","id":"498","title":"Future Directions and Related Material"},"499":{"body":"(source) Table of Contents RFC-0078: Merkleized Metadata Summary Motivation Requirements Reduce metadata size Stakeholders Explanation Metadata digest Extrinsic metadata Type Information Prune unrelated Types Generating TypeRef Building the Merkle Tree Root Inclusion in an Extrinsic Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics & Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 22 February 2024 Description Include merkleized metadata hash in extrinsic signature for trust-less metadata verification. Authors Zondax AG, Parity Technologies","breadcrumbs":"RFC-0078: Merkleized Metadata » RFC-0078: Merkleized Metadata","id":"499","title":"RFC-0078: Merkleized Metadata"},"5":{"body":"The Asset Metadata is information bound to an asset class (fungible or NFT collection) or an asset instance (an NFT). The Asset Metadata could be represented differently on different chains (or in other consensus entities). However, to communicate metadata between consensus entities via XCM, we need a general format so that any consensus entity can make sense of such information. We can name this format \"XCM Asset Metadata\". This RFC proposes: Using key-value pairs as XCM Asset Metadata since it is a general concept useful for both structured and unstructured data. Both key and value can be raw bytes with interpretation up to the communicating entities. The XCM Asset Metadata should be represented as a map SCALE-encoded equivalent to the BTreeMap. Let's call the type of the XCM Asset Metadata map MetadataMap. Communicating only the demanded part of the metadata, not the whole metadata. A consensus entity should be able to query the values of interested keys to read the metadata. To specify the keys to read, we need a set-like type. Let's call that type MetadataKeys and make its instance a SCALE-encoded equivalent to the BTreeSet. A consensus entity should be able to write the values for specified keys. New XCM instructions to communicate the metadata.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Explanation","id":"5","title":"Explanation"},"50":{"body":"This JAM Service can be implemented in Rust using polkatool and tested on a JAM Testnet by JAM implementers. A Keccak256 host function is used for expedience, and the preimage hash function will be adjusted to this for PoC. Real-world work packages can be developed for OP Stack chains like Base and Optimism (currently with 30 blocks/minute) and Arbitrum, which operates at 150 blocks/minute. The results of \"trace_block\" JSON-RPC calls enable 3 x 1440 work packages per day for these top 3 ETH rollups. This is ample for PoC.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Service PoC Implementation","id":"50","title":"Service PoC Implementation"},"500":{"body":"To interact with chains in the Polkadot ecosystem it is required to know how transactions are encoded and how to read state. For doing this, Polkadot-SDK, the framework used by most of the chains in the Polkadot ecosystem, exposes metadata about the runtime to the outside. UIs, wallets, and others can use this metadata to interact with these chains. This makes the metadata a crucial piece of the transaction encoding as users are relying on the interacting software to encode the transactions in the correct format. It gets even more important when the user signs the transaction in an offline wallet, as the device by its nature cannot get access to the metadata without relying on the online wallet to provide it. This makes it so that the offline wallet needs to trust an online party, deeming the security assumptions of the offline devices, mute. This RFC proposes a way for offline wallets to leverage metadata, within the constraints of these. The design idea is that the metadata is chunked and these chunks are put into a merkle tree. The root hash of this merkle tree represents the metadata. The offline wallets can use the root hash to decode transactions by getting proofs for the individual chunks of the metadata. This root hash is also included in the signed data of the transaction (but not sent as part of the transaction). The runtime is then including its known metadata root hash when verifying the transaction. If the metadata root hash known by the runtime differs from the one that the offline wallet used, it very likely means that the online wallet provided some fake data and the verification of the transaction fails. Users depend on offline wallets to correctly display decoded transactions before signing. With merkleized metadata, they can be assured of the transaction's legitimacy, as incorrect transactions will be rejected by the runtime.","breadcrumbs":"RFC-0078: Merkleized Metadata » Summary","id":"500","title":"Summary"},"501":{"body":"Polkadot's innovative design (both relay chain and parachains) present the ability to developers to upgrade their network as frequently as they need. These systems manage to have integrations working after the upgrades with the help of FRAME Metadata. This Metadata, which is in the order of half a MiB for most Polkadot-SDK chains, completely describes chain interfaces and properties. Securing this metadata is key for users to be able to interact with the Polkadot-SDK chain in the expected way. On the other hand, offline wallets provide a secure way for Blockchain users to hold their own keys (some do a better job than others). These devices seldomly get upgraded, usually account for one particular network and hold very small internal memories. Currently in the Polkadot ecosystem there is no secure way of having these offline devices know the latest Metadata of the Polkadot-SDK chain they are interacting with. This results in a plethora of similar yet slightly different offline wallets for all different Polkadot-SDK chains, as well as the impediment of keeping these regularly updated, thus not fully leveraging Polkadot-SDK’s unique forkless upgrade feature. The two main reasons why this is not possible today are: Metadata is too large for offline devices . Currently Polkadot-SDK metadata is on average 500 KiB, which is more than what the mostly adopted offline devices can hold. Metadata is not authenticated . Even if there was enough space on offline devices to hold the metadata, the user would be trusting the entity providing this metadata to the hardware wallet. In the Polkadot ecosystem, this is how currently Polkadot Vault works. This RFC proposes a solution to make FRAME Metadata compatible with offline signers in a secure way. As it leverages FRAME Metadata, it does not only ensure that offline devices can always keep up to date with every FRAME based chain, but also that every offline wallet will be compatible with all FRAME based chains, avoiding the need of per-chain implementations.","breadcrumbs":"RFC-0078: Merkleized Metadata » Motivation","id":"501","title":"Motivation"},"502":{"body":"Metadata's integrity MUST be preserved. If any compromise were to happen, extrinsics sent with compromised metadata SHOULD fail. Metadata information that could be used in signable extrinsic decoding MAY be included in digest, yet its inclusion MUST be indicated in signed extensions. Digest MUST be deterministic with respect to metadata. Digest MUST be cryptographically strong against pre-image, both first (finding an input that results in given digest) and second (finding an input that results in same digest as some other input given). Extra-metadata information necessary for extrinsic decoding and constant within runtime version MUST be included in digest. It SHOULD be possible to quickly withdraw offline signing mechanism without access to cold signing devices. Digest format SHOULD be versioned. Work necessary for proving metadata authenticity MAY be omitted at discretion of signer device design (to support automation tools).","breadcrumbs":"RFC-0078: Merkleized Metadata » Requirements","id":"502","title":"Requirements"},"503":{"body":"Metadata should be stripped from parts that are not necessary to parse a signable extrinsic, then it should be separated into a finite set of self-descriptive chunks. Thus, a subset of chunks necessary for signable extrinsic decoding and rendering could be sent, possibly in small portions (ultimately, one at a time), to cold devices together with the proof. Single chunk with proof payload size SHOULD fit within few kB; Chunks handling mechanism SHOULD support chunks being sent in any order without memory utilization overhead; Unused enum variants MUST be stripped (this has great impact on transmitted metadata size; examples: era enum, enum with all calls for call batching).","breadcrumbs":"RFC-0078: Merkleized Metadata » Reduce metadata size","id":"503","title":"Reduce metadata size"},"504":{"body":"Runtime implementors UI/wallet implementors Offline wallet implementors The idea for this RFC was brought up by runtime implementors and was extensively discussed with offline wallet implementors. It was designed in such a way that it can work easily with the existing offline wallet solutions in the Polkadot ecosystem.","breadcrumbs":"RFC-0078: Merkleized Metadata » Stakeholders","id":"504","title":"Stakeholders"},"505":{"body":"The FRAME metadata provides a wide range of information about a FRAME based runtime. It contains information about the pallets, the calls per pallet, the storage entries per pallet, runtime APIs, and type information about most of the types that are used in the runtime. For decoding extrinsics on an offline wallet, what is mainly required is type information. Most of the other information in the FRAME metadata is actually not required for decoding extrinsics and thus it can be removed. Therefore, the following is a proposal on a custom representation of the metadata and how this custom metadata is chunked, ensuring that only the needed chunks required for decoding a particular extrinsic are sent to the offline wallet. The necessary information to transform the FRAME metadata type information into the type information presented in this RFC will be provided. However, not every single detail on how to convert from FRAME metadata into the RFC type information is described. First, the MetadataDigest is introduced. After that, ExtrinsicMetadata is covered and finally the actual format of the type information. Then pruning of unrelated type information is covered and how to generate the TypeRefs. In the latest step, merkle tree calculation is explained.","breadcrumbs":"RFC-0078: Merkleized Metadata » Explanation","id":"505","title":"Explanation"},"506":{"body":"The metadata digest is the compact representation of the metadata. The hash of this digest is the metadata hash . Below the type declaration of the Hash type and the MetadataDigest itself can be found: type Hash = [u8; 32]; enum MetadataDigest { #[index = 1] V1 { type_information_tree_root: Hash, extrinsic_metadata_hash: Hash, spec_version: u32, spec_name: String, base58_prefix: u16, decimals: u8, token_symbol: String, },\n} The Hash is 32 bytes long and blake3 is used for calculating it. The hash of the MetadataDigest is calculated by blake3(SCALE(MetadataDigest)). Therefore, MetadataDigest is at first SCALE encoded, and then those bytes are hashed. The MetadataDigest itself is represented as an enum. This is done to make it future proof, because a SCALE encoded enum is prefixed by the index of the variant. This index represents the version of the digest. As seen above, there is no index zero and it starts directly with one. Version one of the digest contains the following elements: type_information_tree_root: The root of the merkleized type information tree. extrinsic_metadata_hash: The hash of the extrinsic metadata . spec_version: The spec_version of the runtime as found in the RuntimeVersion when generating the metadata. While this information can also be found in the metadata, it is hidden in a big blob of data. To avoid transferring this big blob of data, we directly add this information here. spec_name: Similar to spec_version, but being the spec_name found in the RuntimeVersion. ss58_prefix: The SS58 prefix used for address encoding. decimals: The number of decimals for the token. token_symbol: The symbol of the token.","breadcrumbs":"RFC-0078: Merkleized Metadata » Metadata digest","id":"506","title":"Metadata digest"},"507":{"body":"For decoding an extrinsic, more information on what types are being used is required. The actual format of the extrinsic is the format as described in the Polkadot specification . The metadata for an extrinsic is as follows: struct ExtrinsicMetadata { version: u8, address_ty: TypeRef, call_ty: TypeRef, signature_ty: TypeRef, signed_extensions: Vec,\n} struct SignedExtensionMetadata { identifier: String, included_in_extrinsic: TypeRef, included_in_signed_data: TypeRef,\n} To begin with, TypeRef. This is a unique identifier for a type as found in the type information. Using this TypeRef, it is possible to look up the type in the type information tree. More details on this process can be found in the section Generating TypeRef . The actual ExtrinsicMetadata contains the following information: version: The version of the extrinsic format. As of writing this, the latest version is 4. address_ty: The address type used by the chain. call_ty: The call type used by the chain. The call in FRAME based runtimes represents the type of transaction being executed on chain. It references the actual function to execute and the parameters of this function. signature_ty: The signature type used by the chain. signed_extensions: FRAME based runtimes can extend the base extrinsic with extra information. This extra information that is put into an extrinsic is called \"signed extensions\". These extensions offer the runtime developer the possibility to include data directly into the extrinsic, like nonce, tip, amongst others. This means that the this data is sent alongside the extrinsic to the runtime. The other possibility these extensions offer is to include extra information only in the signed data that is signed by the sender. This means that this data needs to be known by both sides, the signing side and the verification side. An example for this kind of data is the genesis hash that ensures that extrinsics are unique per chain. Another example is the metadata hash itself that will also be included in the signed data. The offline wallets need to know which signed extensions are present in the chain and this is communicated to them using this field. The SignedExtensionMetadata provides information about a signed extension: identifier: The identifier of the signed extension. An identifier is required to be unique in the Polkadot ecosystem as otherwise extrinsics are maybe built incorrectly. included_in_extrinsic: The type that will be included in the extrinsic by this signed extension. included_in_signed_data: The type that will be included in the signed data by this signed extension.","breadcrumbs":"RFC-0078: Merkleized Metadata » Extrinsic metadata","id":"507","title":"Extrinsic metadata"},"508":{"body":"As SCALE is not self descriptive like JSON, a decoder always needs to know the format of the type to decode it properly. This is where the type information comes into play. The format of the extrinsic is fixed as described above and ExtrinsicMetadata provides information on which type information is required for which part of the extrinsic. So, offline wallets only need access to the actual type information. It is a requirement that the type information can be chunked into logical pieces to reduce the amount of data that is sent to the offline wallets for decoding the extrinsics. So, the type information is structured in the following way: struct Type { path: Vec, type_def: TypeDef, type_id: Compact,\n} enum TypeDef { Composite(Vec), Enumeration(EnumerationVariant), Sequence(TypeRef), Array(Array), Tuple(Vec), BitSequence(BitSequence),\n} struct Field { name: Option, ty: TypeRef, type_name: Option,\n} struct Array { len: u32, type_param: TypeRef,\n} struct BitSequence { num_bytes: u8, least_significant_bit_first: bool,\n} struct EnumerationVariant { name: String, fields: Vec, index: Compact,\n} enum TypeRef { Bool, Char, Str, U8, U16, U32, U64, U128, U256, I8, I16, I32, I64, I128, I256, CompactU8, CompactU16, CompactU32, CompactU64, CompactU128, CompactU256, Void, PerId(Compact),\n} The Type declares the structure of a type. The type has the following fields: path: A path declares the position of a type locally to the place where it is defined. The path is not globally unique, this means that there can be multiple types with the same path. type_def: The high-level type definition, e.g. the type is a composition of fields where each field has a type, the type is a composition of different types as tuple etc. type_id: The unique identifier of this type. Every Type is composed of multiple different types. Each of these \"sub types\" can reference either a full Type again or reference one of the primitive types. This is where TypeRef becomes relevant as the type referencing information. To reference a Type in the type information, a unique identifier is used. As primitive types can be represented using a single byte, they are not put as separate types into the type information. Instead the primitive types are directly part of TypeRef to not require the overhead of referencing them in an extra Type. The special primitive type Void represents a type that encodes to nothing and can be decoded from nothing. As FRAME doesn't support Compact as primitive type it requires a more involved implementation to convert a FRAME type to a Compact primitive type. SCALE only supports u8, u16, u32, u64 and u128 as Compact which maps onto the primitive type declaration in the RFC. One special case is a Compact that wraps an empty Tuple which is expressed as primitive type Void. The TypeDef variants have the following meaning: Composite: A struct like type that is composed of multiple different fields. Each Field can have its own type. The order of the fields is significant. A Composite with no fields is expressed as primitive type Void. Enumeration: Stores a EnumerationVariant. A EnumerationVariant is a struct that is described by a name, an index and a vector of Fields, each of which can have it's own type. Typically Enumerations have more than just one variant, and in those cases Enumeration will appear multiple times, each time with a different variant, in the type information. Enumerations can become quite large, yet usually for decoding a type only one variant is required, therefore this design brings optimizations and helps reduce the size of the proof. An Enumeration with no variants is expressed as primitive type Void. Sequence: A vector like type wrapping the given type. BitSequence: A vector storing bits. num_bytes represents the size in bytes of the internal storage. If least_significant_bit_first is true the least significant bit is first, otherwise the most significant bit is first. Array: A fixed-length array of a specific type. Tuple: A composition of multiple types. A Tuple that is composed of no types is expressed as primitive type Void. Using the type information together with the SCALE specification provides enough information on how to decode types.","breadcrumbs":"RFC-0078: Merkleized Metadata » Type Information","id":"508","title":"Type Information"},"509":{"body":"The FRAME metadata contains not only the type information for decoding extrinsics, but it also contains type information about storage types. The scope of the RFC is only about decoding transactions on offline wallets. Thus, a lot of type information can be pruned. To know which type information are required to decode all possible extrinsics, ExtrinsicMetadata has been defined. The extrinsic metadata contains all the types that define the layout of an extrinsic. Therefore, all the types that are accessible from the types declared in the extrinsic metadata can be collected. To collect all accessible types, it requires to recursively iterate over all types starting from the types in ExtrinsicMetadata. Note that some types are accessible, but they don't appear in the final type information and thus, can be pruned as well. These are for example inner types of Compact or the types referenced by BitSequence. The result of collecting these accessible types is a list of all the types that are required to decode each possible extrinsic.","breadcrumbs":"RFC-0078: Merkleized Metadata » Prune unrelated Types","id":"509","title":"Prune unrelated Types"},"51":{"body":"JAM's gas parameters for PVM instructions and host calls have not been fully developed yet. Combining Polkadot and non-Polkadot rollup services will provide valuable data for determining these parameters. The gas required for refine is proportional to the number of storage proofs submitted in a work package and the average size of each proof. To upper-bound storage proofs, sampling using an entropy state variable $\\eta_3$ may be necessary, although accessing it remains unclear. The gas required for accumulate is proportional to the number of solicit and forget operations. It is believed that accumulate's gas cost is nominal and poses no significant issue. However, the storage rent model common to all blockchain storage applies to the preimage, which is explicitly tallied. Fortunately, this is upper-bounded by $w$.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Gas + Storage Considerations","id":"51","title":"Gas + Storage Considerations"},"510":{"body":"Each TypeRef basically references one of the following types: One of the primitive types. All primitive types can be represented by 1 byte and thus, they are directly part of the TypeRef itself to remove an extra level of indirection. A Type using its unique identifier. In FRAME metadata a primitive type is represented like any other type. So, the first step is to remove all the primitive only types from the list of types that were generated in the previous section. The resulting list of types is sorted using the id provided by FRAME metadata. In the last step the TypeRefs are created. Each reference to a primitive type is replaced by one of the corresponding TypeRef primitive type variants and every other reference is replaced by the type's unique identifier. The unique identifier of a type is the index of the type in our sorted list. For Enumerations all variants have the same unique identifier, while they are represented as multiple type information. All variants need to have the same unique identifier as the reference doesn't know which variant will appear in the actual encoded data. let pruned_types = get_pruned_types(); for ty in pruned_types { if ty.is_primitive_type() { pruned_types.remove(ty); }\n} pruned_types.sort(|(left, right)| if left.frame_metadata_id() == right.frame_metadata_id() { left.variant_index() < right.variant_index() } else { left.frame_metadata_id() < right.frame_metadata_id() }\n); fn generate_type_ref(ty, ty_list) -> TypeRef { if ty.is_primitive_type() { TypeRef::primtive_from_ty(ty) } TypeRef::from_id( // Determine the id by using the position of the type in the // list of unique frame metadata ids. ty_list.position_by_frame_metadata_id(ty.frame_metadata_id()) )\n} fn replace_all_sub_types_with_type_refs(ty, ty_list) -> Type { for sub_ty in ty.sub_types() { replace_all_sub_types_with_type_refs(sub_ty, ty_list); sub_ty = generate_type_ref(sub_ty, ty_list) } ty\n} let final_ty_list = Vec::new();\nfor ty in pruned_types { final_ty_list.push(replace_all_sub_types_with_type_refs(ty, ty_list))\n}","breadcrumbs":"RFC-0078: Merkleized Metadata » Generating TypeRef","id":"510","title":"Generating TypeRef"},"511":{"body":"A complete binary merkle tree with blake3 as the hashing function is proposed. For building the merkle tree root, the initial data has to be hashed as a first step. This initial data is referred to as the leaves of the merkle tree. The leaves need to be sorted to make the tree root deterministic. The type information is sorted using their unique identifiers and for the Enumeration, variants are sort using their index. After sorting and hashing all leaves, two leaves have to be combined to one hash. The combination of these of two hashes is referred to as a node . let nodes = leaves;\nwhile nodes.len() > 1 { let right = nodes.pop_back(); let left = nodes.pop_back(); nodes.push_front(blake3::hash(scale::encode((left, right))));\n} let merkle_tree_root = if nodes.is_empty() { [0u8; 32] } else { nodes.back() }; The merkle_tree_root in the end is the last node left in the list of nodes. If there are no nodes in the list left, it means that the initial data set was empty. In this case, all zeros hash is used to represent the empty tree. Building a tree with 5 leaves (numbered 0 to 4): nodes: 0 1 2 3 4 nodes: [3, 4] 0 1 2 nodes: [1, 2] [3, 4] 0 nodes: [[3, 4], 0] [1, 2] nodes: [[[3, 4], 0], [1, 2]] The resulting tree visualized: [root] / \\ * * / \\ / \\ * 0 1 2 / \\\n3 4 Building a tree with 6 leaves (numbered 0 to 5): nodes: 0 1 2 3 4 5 nodes: [4, 5] 0 1 2 3 nodes: [2, 3] [4, 5] 0 1 nodes: [0, 1] [2, 3] [4, 5] nodes: [[2, 3], [4, 5]] [0, 1] nodes: [[[2, 3], [4, 5]], [0, 1]] The resulting tree visualized: [root] / \\ * * / \\ / \\ * * 0 1 / \\ / \\\n2 3 4 5","breadcrumbs":"RFC-0078: Merkleized Metadata » Building the Merkle Tree Root","id":"511","title":"Building the Merkle Tree Root"},"512":{"body":"To ensure that the offline wallet used the correct metadata to show the extrinsic to the user the metadata hash needs to be included in the extrinsic. The metadata hash is generated by hashing the SCALE encoded MetadataDigest: blake3::hash(SCALE::encode(MetadataDigest::V1 { .. })) For the runtime the metadata hash is generated at compile time. Wallets will have to generate the hash using the FRAME metadata. The signing side should control whether it wants to add the metadata hash or if it wants to omit it. To accomplish this it is required to add one extra byte to the extrinsic itself. If this byte is 0 the metadata hash is not required and if the byte is 1 the metadata hash is added using V1 of the MetadataDigest. This leaves room for future versions of the MetadataDigest format. When the metadata hash should be included, it is only added to the data that is signed. This brings the advantage of not requiring to include 32 bytes into the extrinsic itself, because the runtime knows the metadata hash as well and can add it to the signed data as well if required. This is similar to the genesis hash, while this isn't added conditionally to the signed data. So, to recap: Included in the extrinsic is u8, the \"mode\". The mode is either 0 which means to not include the metadata hash in the signed data or the mode is 1 to include the metadata hash in V1. Included in the signed data is an Option<[u8; 32]>. Depending on the mode the value is either None or Some(metadata_hash).","breadcrumbs":"RFC-0078: Merkleized Metadata » Inclusion in an Extrinsic","id":"512","title":"Inclusion in an Extrinsic"},"513":{"body":"The chunking may not be the optimal case for every kind of offline wallet.","breadcrumbs":"RFC-0078: Merkleized Metadata » Drawbacks","id":"513","title":"Drawbacks"},"514":{"body":"All implementations are required to strictly follow the RFC to generate the metadata hash. This includes which hash function to use and how to construct the metadata types tree. So, all implementations are following the same security criteria. As the chains will calculate the metadata hash at compile time, the build process needs to be trusted. However, this is already a solved problem in the Polkadot ecosystem by using reproducible builds. So, anyone can rebuild a chain runtime to ensure that a proposal is actually containing the changes as advertised. Implementations can also be tested easily against each other by taking some metadata and ensuring that they all come to the same metadata hash. Privacy of users should also not be impacted. This assumes that wallets will generate the metadata hash locally and don't leak any information to third party services about which chunks a user will send to their offline wallet. Besides that, there is no leak of private information as getting the raw metadata from the chain is an operation that is done by almost everyone.","breadcrumbs":"RFC-0078: Merkleized Metadata » Testing, Security, and Privacy","id":"514","title":"Testing, Security, and Privacy"},"515":{"body":"","breadcrumbs":"RFC-0078: Merkleized Metadata » Performance, Ergonomics, and Compatibility","id":"515","title":"Performance, Ergonomics, and Compatibility"},"516":{"body":"There should be no measurable impact on performance to Polkadot or any other chain using this feature. The metadata root hash is calculated at compile time and at runtime it is optionally used when checking the signature of a transaction. This means that at runtime no performance heavy operations are done.","breadcrumbs":"RFC-0078: Merkleized Metadata » Performance","id":"516","title":"Performance"},"517":{"body":"The proposal alters the way a transaction is built, signed, and verified. So, this imposes some required changes to any kind of developer who wants to construct transactions for Polkadot or any chain using this feature. As the developer can pass 0 for disabling the verification of the metadata root hash, it can be easily ignored.","breadcrumbs":"RFC-0078: Merkleized Metadata » Ergonomics & Compatibility","id":"517","title":"Ergonomics & Compatibility"},"518":{"body":"RFC 46 produced by the Alzymologist team is a previous work reference that goes in this direction as well. On other ecosystems, there are other solutions to the problem of trusted signing. Cosmos for example has a standardized way of transforming a transaction into some textual representation and this textual representation is included in the signed data. Basically achieving the same as what the RFC proposes, but it requires that for every transaction applied in a block, every node in the network always has to generate this textual representation to ensure the transaction signature is valid.","breadcrumbs":"RFC-0078: Merkleized Metadata » Prior Art and References","id":"518","title":"Prior Art and References"},"519":{"body":"None.","breadcrumbs":"RFC-0078: Merkleized Metadata » Unresolved Questions","id":"519","title":"Unresolved Questions"},"52":{"body":"CoreTime Instead of ETH, rollups would require DOT for CoreTime to secure their rollup. However, rollups are not locked into JAM and may freely enter and exit the JAM ecosystem since work packages do not need to start at genesis. Different rollups may need to scale their core usage based on rollup activity. JAM's connectivity to CoreTime is expected to handle this effectively. Hashing Currently, preimages are specified to use the Blake2b hash, while Ethereum rollup block hashes utilize Keccak256.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Compatibility","id":"52","title":"Compatibility"},"520":{"body":"Does it work with all kind of offline wallets? Generic types currently appear multiple times in the metadata with each instantiation. It could be may be useful to have generic type only once in the metadata and declare the generic parameters at their instantiation. The metadata doesn't contain any kind of semantic information. This means that the offline wallet for example doesn't know what is a balance etc. The current solution for this problem is to match on the type name, but this isn't a sustainable solution. MetadataDigest only provides one token and decimal. However, chains support a lot of chains support multiple tokens for paying fees etc. Probably more a question of having semantic information as mentioned above.","breadcrumbs":"RFC-0078: Merkleized Metadata » Future Directions and Related Material","id":"520","title":"Future Directions and Related Material"},"521":{"body":"(source) Table of Contents RFC-0084: General transactions in extrinsic format Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 12 March 2024 Description Support more extrinsic types by updating the extrinsic format Authors George Pisaltu","breadcrumbs":"RFC-0084: General transactions in extrinsic format » RFC-0084: General transactions in extrinsic format","id":"521","title":"RFC-0084: General transactions in extrinsic format"},"522":{"body":"This RFC proposes a change to the extrinsic format to incorporate a new transaction type, the \"general\" transaction.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Summary","id":"522","title":"Summary"},"523":{"body":"\"General\" transactions, a new type of transaction that this RFC aims to support, are transactions which obey the runtime's extensions and have according extension data yet do not have hard-coded signatures. They are first described in Extrinsic Horizon and supported in 3685 . They enable users to authorize origins in new, more flexible ways (e.g. ZK proofs, mutations over pre-authenticated origins). As of now, all transactions are limited to the account signing model for origin authorization and any additional origin changes happen in extrinsic logic, which cannot leverage the validation process of extensions. An example of a use case for such an extension would be sponsoring the transaction fee for some other user. A new extension would be put in place to verify that a part of the initial payload was signed by the author under who the extrinsic should run and change the origin, but the payment for the whole transaction should be handled under a sponsor's account. A POC for this can be found in 3712 . The new \"general\" transaction type would coexist with both current transaction types for a while and, therefore, the current number of supported transaction types, capped at 2, is insufficient. A new extrinsic type must be introduced alongside the current signed and unsigned types. Currently, an encoded extrinsic's first byte indicate the type of extrinsic using the most significant bit - 0 for unsigned, 1 for signed - and the 7 following bits indicate the extrinsic format version , which has been equal to 4 for a long time. By taking one bit from the extrinsic format version encoding, we can support 2 additional extrinsic types while also having a minimal impact on our capability to extend and change the extrinsic format in the future.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Motivation","id":"523","title":"Motivation"},"524":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Stakeholders","id":"524","title":"Stakeholders"},"525":{"body":"An extrinsic is currently encoded as one byte to identify the extrinsic type and version. This RFC aims to change the interpretation of this byte regarding the reserved bits for the extrinsic type and version. In the following explanation, bits represented using T make up the extrinsic type and bits represented using V make up the extrinsic version. Currently, the bit allocation within the leading encoded byte is 0bTVVV_VVVV. In practice in the Polkadot ecosystem, the leading byte would be 0bT000_0100 as the version has been equal to 4 for a long time. This RFC proposes for the bit allocation to change to 0bTTVV_VVVV. As a result, the extrinsic format version will be bumped to 5 and the extrinsic type bit representation would change as follows: bits type 00 unsigned 10 signed 01 reserved 11 reserved","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Explanation","id":"525","title":"Explanation"},"526":{"body":"This change would reduce the maximum possible transaction version from the current 127 to 63. In order to bypass the new, lower limit, the extrinsic format would have to change again.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Drawbacks","id":"526","title":"Drawbacks"},"527":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Testing, Security, and Privacy","id":"527","title":"Testing, Security, and Privacy"},"528":{"body":"This change would allow Polkadot to support new types of transactions, with the specific \"general\" transaction type in mind at the time of writing this proposal.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Performance, Ergonomics, and Compatibility","id":"528","title":"Performance, Ergonomics, and Compatibility"},"529":{"body":"There is no performance impact.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Performance","id":"529","title":"Performance"},"53":{"body":"The described service requires expert attention from security experts familiar with JAM, ELVES, and Ethereum. The ELVES and JAM protocols are expected to undergo audit with the 1.0 ratification of JAM. The proposal introduces no new privacy concerns. Raw PVM assembly may be preferred in a production implementation, along with a host function for Keccak256 to minimize issues related to compiler bugs.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Testing, Security, and Privacy","id":"53","title":"Testing, Security, and Privacy"},"530":{"body":"The impact to developers and end-users is minimal as it would just be a bitmask update on their part for parsing the extrinsic type along with the version.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Ergonomics","id":"530","title":"Ergonomics"},"531":{"body":"This change breaks backwards compatiblity because any transaction that is neither signed nor unsigned, but a new transaction type, would be interpreted as having a future extrinsic format version.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Compatibility","id":"531","title":"Compatibility"},"532":{"body":"The original design was originally proposed in the TransactionExtension PR , which is also the motivation behind this effort.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Prior Art and References","id":"532","title":"Prior Art and References"},"533":{"body":"None.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Unresolved Questions","id":"533","title":"Unresolved Questions"},"534":{"body":"Following this change, the \"general\" transaction type will be introduced as part of the Extrinsic Horizon effort, which will shape future work.","breadcrumbs":"RFC-0084: General transactions in extrinsic format » Future Directions and Related Material","id":"534","title":"Future Directions and Related Material"},"535":{"body":"(source) Table of Contents RFC-0091: DHT Authority discovery record creation time Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2024-05-20 Description Add creation time for DHT authority discovery records Authors Alex Gheorghe (alexggh)","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » RFC-0091: DHT Authority discovery record creation time","id":"535","title":"RFC-0091: DHT Authority discovery record creation time"},"536":{"body":"Extend the DHT authority discovery records with a signed creation time, so that nodes can determine which record is newer and always decide to prefer the newer records to the old ones.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Summary","id":"536","title":"Summary"},"537":{"body":"Currently, we use the Kademlia DHT for storing records regarding the p2p address of an authority discovery key, the problem is that if the nodes decide to change its PeerId/Network key it will publish a new record, however because of the distributed and replicated nature of the DHT there is no way to tell which record is newer so both old PeerId and the new PeerId will live in the network until the old one expires(36h), that creates all sort of problem and leads to the node changing its address not being properly connected for up to 36h. After this RFC, nodes are extended to decide to keep the new record and propagate the new record to nodes that have the old record stored, so in the end all the nodes will converge faster to the new record(in the order of minutes, not 36h) Implementation of the rfc: https://github.com/paritytech/polkadot-sdk/pull/3786. Current issue without this enhacement: https://github.com/paritytech/polkadot-sdk/issues/3673","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Motivation","id":"537","title":"Motivation"},"538":{"body":"Polkadot node developers.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Stakeholders","id":"538","title":"Stakeholders"},"539":{"body":"This RFC heavily relies on the functionalities of the Kademlia DHT already in use by Polkadot. You can find a link to the specification here . In a nutshell, on a specific node the current authority-discovery protocol publishes Kademila DHT records at startup and periodically. The records contain the full address of the node for each authorithy key it owns. The node tries also to find the full address of all authorities in the network by querying the DHT and picking up the first record it finds for each of the authority id it found on chain. The authority discovery DHT records use the protobuf protocol and the current format is specified here . This RFC proposese extending the schema in a backwards compatible manner by adding a new optional creation_time field to AuthorityRecord and nodes can use this information to determine which of the record is newer. Diff of dht-v3.proto vs dht-v2.proto @@ -1,10 +1,10 @@ syntax = \"proto3\"; -package authority_discovery_v2;\n+package authority_discovery_v3; // First we need to serialize the addresses in order to be able to sign them. message AuthorityRecord { repeated bytes addresses = 1;\n+\t// Time since UNIX_EPOCH in nanoseconds, scale encoded\n+\tTimestampInfo creation_time = 2; } message PeerSignature {\n@@ -13,11 +15,17 @@ bytes public_key = 2; } +// Information regarding the creation data of the record\n+message TimestampInfo {\n+ // Time since UNIX_EPOCH in nanoseconds, scale encoded\n+ bytes timestamp = 1;\n+}\n+ Each time a node wants to resolve an authorithy ID it will issue a query with a certain redundancy factor, and from all the results it receives it will decide to pick only the newest record. Additionally, in order to speed up the time until all nodes have the newest record, nodes can optionaly implement a logic where they send the new record to nodes that answered with the older record.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Explanation","id":"539","title":"Explanation"},"54":{"body":"Solutions to model other elements in the state trie (account balances and nonces) are not covered in this service design yet. As JAM implementers move towards conformant implementations in 2025, which support gas modeling and justify performance improvements, a proper model of storage costs and fees will be necessary. JAM enables a semi-coherent model for non-Polkadot rollups, starting with optimistic rollups as described here. A similar service may be envisioned for mature ZK rollup ecosystems. An interoperable JAM messaging service between both kinds of non-Polkadot rollups and Polkadot rollups would be highly desirable. The growth of optimistic rollup platforms, led by OP Stack with CEXes (Coinbase and Kraken) and ArbOS, threatens JAM's viability as a rollup host. Achieving JAM's rollup host goals may require urgency to match the speed at which these network effects emerge.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Future Directions and Related Material","id":"54","title":"Future Directions and Related Material"},"540":{"body":"In theory the new protocol creates a bit more traffic on the DHT network, because it waits for DHT records to be received from more than one node, while in the current implementation we just take the first record that we receive and cancel all in-flight requests to other peers. However, because the redundancy factor will be relatively small and this operation happens rarerly, every 10min, this cost is negligible.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Drawbacks","id":"540","title":"Drawbacks"},"541":{"body":"This RFC's implementation https://github.com/paritytech/polkadot-sdk/pull/3786 had been tested on various local test networks and versi. With regard to security the creation time is wrapped inside SignedAuthorityRecord wo it will be signed with the authority id key, so there is no way for other malicious nodes to manipulate this field without the received node observing.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Testing, Security, and Privacy","id":"541","title":"Testing, Security, and Privacy"},"542":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Performance, Ergonomics, and Compatibility","id":"542","title":"Performance, Ergonomics, and Compatibility"},"543":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Performance","id":"543","title":"Performance"},"544":{"body":"Irrelevant.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Ergonomics","id":"544","title":"Ergonomics"},"545":{"body":"The changes are backwards compatible with the existing protocol, so nodes with both the old protocol and newer protocol can exist in the network, this is achieved by the fact that we use protobuf for serializing and deserializing the records, so new fields will be ignore when deserializing with the older protocol and vice-versa when deserializing an old record with the new protocol the new field will be None and the new code accepts this record as being valid.","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Compatibility","id":"545","title":"Compatibility"},"546":{"body":"The enhancements have been inspired by the algorithm specified in here","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Prior Art and References","id":"546","title":"Prior Art and References"},"547":{"body":"N/A","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Unresolved Questions","id":"547","title":"Unresolved Questions"},"548":{"body":"N/A","breadcrumbs":"RFC-0091: DHT Authority discovery record creation time » Future Directions and Related Material","id":"548","title":"Future Directions and Related Material"},"549":{"body":"(source) Table of Contents RFC-0097: Unbonding Queue Summary Motivation Stakeholders Explanation Mechanism Proposed Parameters Rebonding Empirical Analysis Additional Considerations Deferred slashing UX/UI Conviction voting Potential Extension Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Date 19.06.2024 Description This RFC proposes a safe mechanism to scale the unbonding time from staking on the Relay Chain proportionally to the overall unbonding stake. This approach significantly reduces the expected duration for unbonding, while ensuring that a substantial portion of the stake is always available to slash of validators behaving maliciously within a 28-day window. Authors Jonas Gehrlein & Alistair Stewart","breadcrumbs":"RFC-0097: Unbonding Queue » RFC-0097: Unbonding Queue","id":"549","title":"RFC-0097: Unbonding Queue"},"55":{"body":"Alongside Ethereum DA (via EIP-4844), numerous DA alternatives for rollups exist: Avail, Celestia, Eigenlayer. ORUs rely primarily on fraud proofs, but they require a lengthy 7-day window for these \"fraud proofs.\" The cynical rollup model offers significant UX improvements by eliminating this \"exit window,\" commonly 7 days. None of these alternatives provide the same UX enhancement enabled by \"cynical\" rollups.","breadcrumbs":"RFC-0127: JAM Service for Validating Ethereum Optimistic Rollups » Drawbacks, Alternatives, and Unknowns","id":"55","title":"Drawbacks, Alternatives, and Unknowns"},"550":{"body":"This RFC proposes a flexible unbonding mechanism for tokens that are locked from staking on the Relay Chain (DOT/KSM), aiming to enhance user convenience without compromising system security. Locking tokens for staking ensures that Polkadot is able to slash tokens backing misbehaving validators. With changing the locking period, we still need to make sure that Polkadot can slash enough tokens to deter misbehaviour. This means that not all tokens can be unbonded immediately, however we can still allow some tokens to be unbonded quickly. The new mechanism leads to a signficantly reduced unbonding time on average, by queuing up new unbonding requests and scaling their unbonding duration relative to the size of the queue. New requests are executed with a minimum of 2 days, when the queue is comparatively empty, to the conventional 28 days, if the sum of requests (in terms of stake) exceed some threshold. In scenarios between these two bounds, the unbonding duration scales proportionately. The new mechanism will never be worse than the current fixed 28 days. In this document we also present an empirical analysis by retrospectively fitting the proposed mechanism to the historic unbonding timeline and show that the average unbonding duration would drastically reduce, while still being sensitive to large unbonding events. Additionally, we discuss implications for UI, UX, and conviction voting. Note: Our proposition solely focuses on the locks imposed from staking. Other locks, such as governance, remain unchanged. Also, this mechanism should not be confused with the already existing feature of FastUnstake , which lets users unstake tokens immediately that have not received rewards for 28 days or longer. As an initial step to gauge its effectiveness and stability, it is recommended to implement and test this model on Kusama before considering its integration into Polkadot, with appropriate adjustments to the parameters. In the following, however, we limit our discussion to Polkadot.","breadcrumbs":"RFC-0097: Unbonding Queue » Summary","id":"550","title":"Summary"},"551":{"body":"Polkadot has one of the longest unbonding periods among all Proof-of-Stake protocols, because security is the most important goal. Staking on Polkadot is still attractive compared to other protocols because of its above-average staking APY. However the long unbonding period harms usability and deters potential participants that want to contribute to the security of the network. The current length of the unbonding period imposes significant costs for any entity that even wants to perform basic tasks such as a reorganization / consolidation of their stashes, or updating their private key infrastructure. It also limits participation of users that have a large preference for liquidity. The combination of long unbonding periods and high returns has lead to the proliferation of liquid staking , where parachains or centralised exchanges offer users their staked tokens before the 28 days unbonding period is over either in original DOT/KSM form or derivative tokens. Liquid staking is harmless if few tokens are involved but it could result in many validators being selected by a few entities if a large fraction of DOTs were involved. This may lead to centralization (see here for more discussion on threats of liquid staking) and an opportunity for attacks. The new mechanism greatly increases the competitiveness of Polkadot, while maintaining sufficient security.","breadcrumbs":"RFC-0097: Unbonding Queue » Motivation","id":"551","title":"Motivation"},"552":{"body":"Every DOT/KSM token holder","breadcrumbs":"RFC-0097: Unbonding Queue » Stakeholders","id":"552","title":"Stakeholders"},"553":{"body":"Before diving into the details of how to implement the unbonding queue, we give readers context about why Polkadot has a 28-day unbonding period in the first place. The reason for it is to prevent long-range attacks (LRA) that becomes theoretically possible if more than 1/3 of validators collude. In essence, a LRA describes the inability of users, who disconnect from the consensus at time t0 and reconnects later, to realize that validators which were legitimate at a certain time, say t0 but dropped out in the meantime, are not to be trusted anymore. That means, for example, a user syncing the state could be fooled by trusting validators that fell outside the active set of validators after t0, and are building a competitive and malicious chain (fork). LRAs of longer than 28 days are mitigated by the use of trusted checkpoints, which are assumed to be no more than 28 days old. A new node that syncs Polkadot will start at the checkpoint and look for proofs of finality of later blocks, signed by 2/3 of the validators. In an LRA fork, some of the validator sets may be different but only if 2/3 of some validator set in the last 28 days signed something incorrect. If we detect an LRA of no more than 28 days with the current unbonding period, then we should be able to detect misbehaviour from over 1/3 of validators whose nominators are still bonded. The stake backing these validators is considerable fraction of the total stake (empirically it is 0.287 or so). If we allowed more than this stake to unbond, without checking who it was backing, then the LRA attack might be free of cost for an attacker. The proposed mechansim allows up to half this stake to unbond within 28 days. This halves the amount of tokens that can be slashed, but this is still very high in absolute terms. For example, at the time of writing (19.06.2024) this would translate to around 120 millions DOTs. Attacks other than an LRA, such as backing incorrect parachain blocks, should be detected and slashed within 2 days. This is why the mechanism has a minimum unbonding period. In practice an LRA does not affect clients who follow consensus more frequently than every 2 days, such as running nodes or bridges. However any time a node syncs Polkadot if an attacker is able to connect to it first, it could be misled. In short, in the light of the huge benefits obtained, we are fine by only keeping a fraction of the total stake of validators slashable against LRAs at any given time.","breadcrumbs":"RFC-0097: Unbonding Queue » Explanation","id":"553","title":"Explanation"},"554":{"body":"When a user ( nominator or validator) decides to unbond their tokens, they don't become instantly available. Instead, they enter an unbonding queue . The following specification illustrates how the queue works, given a user wants to unbond some portion of their stake denoted as new_unbonding_stake. We also store a variable, max_unstake that tracks how much stake we allow to unbond potentially earlier than 28 eras (28 days on Polkadot and 7 days on Kusama). To calculate max_unstake, we record for each era how much stake was used to back the lowest-backed 1/3 of validators. We store this information for the last 28 eras and let min_lowest_third_stake be the minimum of this over the last 28 eras. max_unstake is determined by MIN_SLASHABLE_SHARE x min_lowest_third_stake. In addition, we can use UPPER_BOUND and LOWER_BOUND as variables to scale the unbonding duration of the queue. At any time we store back_of_unbonding_queue_block_number which expresses the block number when all the existing unbonders have unbonded. Let's assume a user wants to unbond some of their stake, i.e., new_unbonding_stake, and issues the request at some arbitrary block number denoted as current_block. Then: unbonding_time_delta = new_unbonding_stake / max_unstake * UPPER_BOUND This number needs to be added to the back_of_unbonding_queue_block_number under the conditions that it does not undercut current_block + LOWER_BOUND or exceed current_block + UPPER_BOUND. back_of_unbonding_queue_block_number = max(current_block_number, back_of_unbonding_queue_block_number) + unbonding_time_delta This determines at which block the user has their tokens unbonded, making sure that it is in the limit of LOWER_BOUND and UPPER_BOUND. unbonding_block_number = min(UPPER_BOUND, max(back_of_unbonding_queue_block_number - current_block_number, LOWER_BOUND)) + current_block_number Ultimately, the user's token are unbonded at unbonding_block_number.","breadcrumbs":"RFC-0097: Unbonding Queue » Mechanism","id":"554","title":"Mechanism"},"555":{"body":"There are a few constants to be exogenously set. They are up for discussion, but we make the following recommendation: MIN_SLASHABLE_SHARE: 1/2 - This is the share of stake backing the lowest 1/3 of validators that is slashable at any point in time. It offers a trade-off between security and unbonding time. Half is a sensible choice. Here, we have sufficient stake to slash while allowing for a short average unbonding time. LOWER_BOUND: 28800 blocks (or 2 eras): This value resembles a minimum unbonding time for any stake of 2 days. UPPER_BOUND: 403200 blocks (or 28 eras): This value resembles the maximum time a user faces in their unbonding time. It equals to the current unbonding time and should be familiar to users.","breadcrumbs":"RFC-0097: Unbonding Queue » Proposed Parameters","id":"555","title":"Proposed Parameters"},"556":{"body":"Users that chose to unbond might want to cancel their request and rebond. There is no security loss in doing this, but with the scheme above, it could imply that a large unbond increases the unbonding time for everyone else later in the queue. When the large stake is rebonded, however, the participants later in the queue move forward and can unbond more quickly than originally estimated. It would require an additional extrinsic by the user though. Thus, we should store the unbonding_time_delta with the unbonding account. If it rebonds when it is still unbonding, then this value should be subtracted from back_of_unbonding_queue_block_number. So unbonding and rebonding leaves this number unaffected. Note that we must store unbonding_time_delta, because in later eras max_unstake might have changed and we cannot recompute it.","breadcrumbs":"RFC-0097: Unbonding Queue » Rebonding","id":"556","title":"Rebonding"},"557":{"body":"We can use the proposed unbonding queue calculation, with the recommended parameters, and simulate the queue over the course of Polkadot's unbonding history. Instead of doing the analysis on a per-block basis, we calculate it on a daily basis. To simulate the unbonding queue, we require the ratio between the daily total stake of the lowest third backed validators and the daily total stake (which determines the max_unstake) and the sum of daily and newly unbonded tokens. Due to the NPoS algorithm , the first number has only small variations and we used a constant as approximation (0.287) determined by sampling a bunch of empirical eras. At this point, we want to thank Parity's Data team for allowing us to leverage their data infrastructure in these analyses. The following graph plots said statistics. The abovementioned graph combines two metrics into a single graph. Unbonded Amount: The number of daily and newly unbonded token over time scaled to the y-axis of 28 days. In particular its normalized by daily_unbonded / max(daily_unbonded) * 28. Unbonding Days: The daily expected unbonding days given the history of daily_unbonded. We can observe that historical unbonds only trigger an unbonding time larger than LOWER_BOUND in situations with extensive and/or clustered unbonding amounts. The average unbonding time across the whole timeseries is ~2.67 days. We can, however, see it taking effect pushing unbonding times up during large unbonding events. In the largest events, we hit a maximum of 28 days. This gives us reassurance that it is sufficiently sensitive and it makes sense to match the UPPER_BOUND with the historically largest unbonds. The main parameter affecting the situation is the max_unstake. The relationship is obvious: decreasing the max_unstake makes the queue more sensitive, i.e., having it spike more quickly and higher with unbonding events. Given that these events historically were mostly associated with parachain auctions, we can assume that, in the absence of major systemic events, users will experience drastically reduced unbonding times. The analysis can be reproduced or changed to other parameters using this repository .","breadcrumbs":"RFC-0097: Unbonding Queue » Empirical Analysis","id":"557","title":"Empirical Analysis"},"558":{"body":"","breadcrumbs":"RFC-0097: Unbonding Queue » Additional Considerations","id":"558","title":"Additional Considerations"},"559":{"body":"Currently we defer applying many slashes until around 28 days have passed. This was implemented so we can conveniently cancel slashes via governance in the case that the slashing was due to a bug. While rare on Polkadot, such bugs cause a significant fraction of slashes. This includes slashing for attacks other than LRAs for which we've assumed that 2 days is enough to slash. But 2 days in not enough to cancel slashes via OpenGov. Owing to the way exposures, which nominators back validators with how many tokens, are stored, it is hard to search for whether a nominator has deferred slashes that need to be applied to them on chain as of now. So we cannot simply check when a nominator attempts to withdraw their bond. We can solve this by freezing the unbonding queue while there are pending slashes in the staking system. In the worst case, where the slash is applied, we would forced all members of the queue to unbond with 28 days minus the days since they are in the queue (i.e., nobody ever needs to wait more than 28 days) and pause the unbonding queue until there are no deferred slashes in the system. This solution is potentially easier to implement but could cause disruptions for unbonding stakers that are not slashed, because they do not benefit from the queue. It is crucial to note that unbonding is still always possible for all stakers in the usual 28 days. Since slashes should occur rarely, this should not cause distruptions in reality too often. In addition, we could further complement the solution by adding a new extrinsic where any account is allowed to point out the unbonding accounts with the deferred slashes. Then, the chain would set the unbonding_block_number of the affected accounts to after the time when the slash would be applied, which will be no more than 28 days from the time the staker unbonded. After removing the offenders from the queue, we could unfreeze the unbonding queue and restore operation for unslashed accounts immediately. To find nominators with deferred slashes it is required, however, to iterate through all nominators, which is only feasible to do off chain. There should be plenty of incentive to do so by the non-slashed unbonding accounts that seek to reduce the opportunity costs of being forced wait potentially much longer than necessary. This solution achieves resolve the situation securely and, in the worst case where no user submits the extrinsic, no staker would exceed an unbonding duration of the usual 28 days and apply all slashes as intended.","breadcrumbs":"RFC-0097: Unbonding Queue » Deferred slashing","id":"559","title":"Deferred slashing"},"56":{"body":"(source) Table of Contents RFC-0000: Feature Name Here Summary Motivation Stakeholders Explanation Introduce a new UMP message type RequestCodeUpgrade Handle RequestCodeUpgrade on backers Get the new code to all validators On-chain code upgrade process Handling new validators How do other parties get hold of the PVF? Pruning Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Further Hardening Generalize this off-chain storage mechanism? Start Date 13 July 2024 Description Implement off-chain parachain runtime upgrades Authors eskimor","breadcrumbs":"RFC-0000: Feature Name Here » RFC-0000: Feature Name Here","id":"56","title":"RFC-0000: Feature Name Here"},"560":{"body":"As per the nature of the unbonding queue, the more a user slices up their stake to be unbonded, the quicker they find their expected unbonding time. This, however, comes at the cost of creating more and/or larger transactions, i.e., incurring higher transactions costs. We leave it to UI implementations to provide a good UX to inform users about this trade-off and help them find their individual willingness to pay to unbond even faster. For most users, splitting up their stake will not lead to any meaningful advantage because their effect on the queue is neglible.","breadcrumbs":"RFC-0097: Unbonding Queue » UX/UI","id":"560","title":"UX/UI"},"561":{"body":"Changing the (expected) unbonding period has an indirect impact on conviction voting, because the governance locks do not stack with the staking locks. In other words, if a user is already being locked in staking, they can, for free, choose a conviction vote that is lower or equal to that locking time. Currently and with an unbonding period of a fixed 28 days, that means, the 3x conviction vote comes essentially for free. There has been discussions to rescale the conviction weights to improved parametrization. But, the transition between the old locks and new locks pose significant challenges. We argue, that under our unbonding queue, the current conviction voting scheme logically better aligns with their impact on governance, avoiding an expensive solution to migrate existing locks to a new scheme. For example, if the average unbonding period is around 2 days from staking, locking tokens for an additional 26 days justifies a higher weight (in that regard of3x). Voters that seek maximum liquidity are free to do so but it is fair to be weighted less in governance decisions that are naturally affecting the long-term success of Polkadot.","breadcrumbs":"RFC-0097: Unbonding Queue » Conviction voting","id":"561","title":"Conviction voting"},"562":{"body":"In addition to a simple queue, we could add a market component that lets users always unbond from staking at the minimum possible waiting time)(== LOWER_BOUND, e.g., 2 days), by paying a variable fee. To achieve this, it is reasonable to split the total unbonding capacity into two chunks, with the first capacity for the simple queue and the remaining capacity for the fee-based unbonding. By doing so, we allow users to choose whether they want the quickest unbond and paying a dynamic fee or join the simple queue. Setting a capacity restriction for both queues enables us to guarantee a predictable unbonding time in the simple queue, while allowing users with the respective willingness to pay to get out even earlier. The fees are dynamically adjusted and are proportional to the unbonding stake (and thereby expressed in a percentage of the requested unbonding stake). In contrast to a unified queue, this prevents the issue that users paying a fee jump in front of other users not paying a fee, pushing their unbonding time back (which would be bad for UX). The revenue generated could be burned. This extension and further specifications are left out of this RFC, because it adds further complexity and the empirical analysis above suggests that average unbonding times will already be close the LOWER_BOUND, making a more complex design unnecessary. We advise to first implement the discussed mechanism and assess after some experience whether an extension is desirable.","breadcrumbs":"RFC-0097: Unbonding Queue » Potential Extension","id":"562","title":"Potential Extension"},"563":{"body":"Lower security for LRAs: Without a doubt, the theoretical security against LRAs decreases. But, as we argue, the attack is still costly enough to deter attacks and the attack is sufficiently theoretical. Here, the benefits outweigh the costs. Griefing attacks: A large holder could pretend to unbond a large amount of their tokens to prevent other users to exit the network earlier. This would, however be costly due to the fact that the holder loses out on staking rewards. The larger the impact on the queue, the higher the costs. In any case it must be noted that the UPPER_BOUND is still 28 days, which means that nominators are never left with a longer unbonding period than currently. There is not enough gain for the attacker to endure this cost. Challenge for Custodians and Liquid Staking Providers : Changing the unbonding time, especially making it flexible, requires entities that offer staking derivatives to rethink and rework their products.","breadcrumbs":"RFC-0097: Unbonding Queue » Drawbacks","id":"563","title":"Drawbacks"},"564":{"body":"NA","breadcrumbs":"RFC-0097: Unbonding Queue » Testing, Security, and Privacy","id":"564","title":"Testing, Security, and Privacy"},"565":{"body":"NA","breadcrumbs":"RFC-0097: Unbonding Queue » Performance, Ergonomics, and Compatibility","id":"565","title":"Performance, Ergonomics, and Compatibility"},"566":{"body":"The authors cannot see any potential impact on performance.","breadcrumbs":"RFC-0097: Unbonding Queue » Performance","id":"566","title":"Performance"},"567":{"body":"The authors cannot see any potential impact on ergonomics for developers. We discussed potential impact on UX/UI for users above.","breadcrumbs":"RFC-0097: Unbonding Queue » Ergonomics","id":"567","title":"Ergonomics"},"568":{"body":"The authors cannot see any potential impact on compatibility. This should be assessed by the technical fellows.","breadcrumbs":"RFC-0097: Unbonding Queue » Compatibility","id":"568","title":"Compatibility"},"569":{"body":"Ethereum proposed a similar solution Alistair did some initial write-up There are other solutions that further mitigate the risk of LRAs.","breadcrumbs":"RFC-0097: Unbonding Queue » Prior Art and References","id":"569","title":"Prior Art and References"},"57":{"body":"Change the upgrade process of a parachain runtime upgrade to become an off-chain process with regards to the relay chain. Upgrades are still contained in parachain blocks, but will no longer need to end up in relay chain blocks nor in relay chain state.","breadcrumbs":"RFC-0000: Feature Name Here » Summary","id":"57","title":"Summary"},"570":{"body":"(source) Table of Contents RFC-0099: Introduce a transaction extension version Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 03 July 2024 Description Introduce a versioning for transaction extensions. Authors Bastian Köcher","breadcrumbs":"RFC-0099: Introduce a transaction extension version » RFC-0099: Introduce a transaction extension version","id":"570","title":"RFC-0099: Introduce a transaction extension version"},"571":{"body":"This RFC proposes a change to the extrinsic format to include a transaction extension version.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Summary","id":"571","title":"Summary"},"572":{"body":"The extrinsic format supports to be extended with transaction extensions. These transaction extensions are runtime specific and can be different per chain. Each transaction extension can add data to the extrinsic itself or extend the signed payload. This means that adding a transaction extension is breaking the chain specific extrinsic format. A recent example was the introduction of the CheckMetadatHash to Polkadot and all its system chains. As the extension was adding one byte to the extrinsic, it broke a lot of tooling. By introducing an extra version for the transaction extensions it will be possible to introduce changes to these transaction extensions while still being backwards compatible. Based on the version of the transaction extensions, each chain runtime could decode the extrinsic correctly and also create the correct signed payload.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Motivation","id":"572","title":"Motivation"},"573":{"body":"Runtime users Runtime devs Wallet devs","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Stakeholders","id":"573","title":"Stakeholders"},"574":{"body":"RFC84 introduced the extrinsic format 5. The idea is to piggyback onto this change of the extrinsic format to add the extra version for the transaction extensions. If required, this could also come as extrinsic format 6, but 5 is not yet deployed anywhere. The extrinsic format supports the following types of transactions: Bare: Does not add anything to the extrinsic. Signed: (Address, Signature, Extensions) General: Extensions The Signed and General transaction would change to: Signed: (Address, Signature, Version, Extensions) General: (Version, Extensions) The Version being a SCALE encoded u8 representing the version of the transaction extensions. In the chain runtime the version can be used to determine which set of transaction extensions should be used to decode and to validate the transaction.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Explanation","id":"574","title":"Explanation"},"575":{"body":"This adds one byte more to each signed transaction.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Drawbacks","id":"575","title":"Drawbacks"},"576":{"body":"There is no impact on testing, security or privacy.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Testing, Security, and Privacy","id":"576","title":"Testing, Security, and Privacy"},"577":{"body":"This will ensure that changes to the transactions extensions can be done in a backwards compatible way.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Performance, Ergonomics, and Compatibility","id":"577","title":"Performance, Ergonomics, and Compatibility"},"578":{"body":"There is no performance impact.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Performance","id":"578","title":"Performance"},"579":{"body":"Runtime developers need to take care of the versioning and ensure to bump as required, so that there are no compatibility breaking changes without a bump of the version. It will also add a little bit more code in the runtime to decode these old versions, but this should be neglectable.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Ergonomics","id":"579","title":"Ergonomics"},"58":{"body":"Having parachain runtime upgrades go through the relay chain has always been seen as a scalability concern. Due to optimizations in statement distribution and asynchronous backing it became less crucial and got de-prioritized, the original issue can be found here . With the introduction of Agile Coretime and in general our efforts to reduce barrier to entry more for Polkadot more, the issue becomes more relevant again: We would like to reduce the required storage deposit for PVF registration, with the aim to not only make it cheaper to run a parachain (bulk + on-demand coretime), but also reduce the amount of capital required for the deposit. With this we would hope for far more parachains to get registered, thousands potentially even ten thousands. With so many PVFs registered, updates are expected to become more frequent and even attacks on service quality for other parachains would become a higher risk.","breadcrumbs":"RFC-0000: Feature Name Here » Motivation","id":"58","title":"Motivation"},"580":{"body":"When introduced together with extrinsic format version 5 from RFC84 , it can be implemented in a backwards compatible way. So, transactions can still be send using the old extrinsic format and decoded by the runtime.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Compatibility","id":"580","title":"Compatibility"},"581":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Prior Art and References","id":"581","title":"Prior Art and References"},"582":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Unresolved Questions","id":"582","title":"Unresolved Questions"},"583":{"body":"None.","breadcrumbs":"RFC-0099: Introduce a transaction extension version » Future Directions and Related Material","id":"583","title":"Future Directions and Related Material"},"584":{"body":"(source) Table of Contents RFC-0100: New XCM instruction: InitiateAssetsTransfer Summary Motivation Stakeholders Explanation Example usage: transferring 2 different asset types across 3 chains Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 11 July 2024 Description Add new XCM instruction: InitiateAssetsTransfer for mixing asset transfer types in same XCM Authors Adrian Catangiu","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » RFC-0100: New XCM instruction: InitiateAssetsTransfer","id":"584","title":"RFC-0100: New XCM instruction: InitiateAssetsTransfer"},"585":{"body":"This RFC proposes a new instruction that provides a way to initiate on remote chains, asset transfers which transfer multiple types (teleports, local-reserve, destination-reserve) of assets, using XCM alone. The currently existing instructions are too opinionated and force each XCM asset transfer to a single transfer type (teleport, local-reserve, destination-reserve). This results in inability to combine different types of transfers in single transfer which results in overall poor UX when trying to move assets across chains.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Summary","id":"585","title":"Summary"},"586":{"body":"XCM is the de-facto cross-chain messaging protocol within the Polkadot ecosystem, and cross-chain assets transfers is one of its main use-cases. Unfortunately, in its current spec, it does not support initiating on a remote chain, one or more transfers that combine assets with different transfer types. For example, ParachainA cannot instruct AssetHub to teleport ForeignAssetX to ParachainX alongside USDT (which has to be reserve transferred) using current XCM specification. There currently exist DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions that initiate asset transfers on execution, but they are opinionated in the type of transfer to use. Combining them is also not possible, because as a result of their individual execution, a message containing a ClearOrigin instruction is sent to the destination chain, making subsequent transfers impossible after the first instruction is executed. The new instruction proposed by this RFC allows an XCM program to describe multiple asset transfer types, then execute them in one shot with a single remote_xcm program sent to the target chain to effect the transfer and subsequently clear origin. Multi-hop asset transfers will benefit from this change by allowing single XCM program to handle multiple types of transfers and reduce complexity. Bridge asset transfers greatly benefit from this change by allowing building XCM programs to transfer multiple assets across multiple hops in a single pseudo-atomic action. For example, allows single XCM program execution to transfer multiple assets from ParaK on Kusama, through Kusama Asset Hub, over the bridge through Polkadot Asset Hub with final destination ParaP on Polkadot. With current XCM, we are limited to doing multiple independent transfers for each individual hop in order to move both \"interesting\" assets, but also \"supporting\" assets (used to pay fees).","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Motivation","id":"586","title":"Motivation"},"587":{"body":"Runtime users Runtime devs Wallet devs dApps devs","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Stakeholders","id":"587","title":"Stakeholders"},"588":{"body":"A new instruction InitiateAssetsTransfer is introduced that initiates an assets transfer from the chain it is executed on, to another chain. The executed transfer is point-to-point (chain-to-chain) with all of the transfer properties specified in the instruction parameters. The instruction also allows specifying another XCM program to be executed on the remote chain. If a transfer requires going through multiple hops, an XCM program can compose this instruction to be used at every chain along the path, on each hop describing that specific leg of the transfer. Note: Transferring assets that require different paths (chains along the way) is not supported within same XCM because of the async nature of cross chain messages. This new instruction, however, enables initiating transfers for multiple assets that take the same path even if they require different transfer types along that path. The usage and composition model of InitiateAssetsTransfer is the same as with existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions. The main difference comes from the ability to handle assets that have different point-to-point transfer type between A and B. The other benefit is that it also allows specifying remote fee payment and transparently appends the required remote fees logic to the remote XCM. We can specify the desired transfer type for some asset(s) using: /// Specify which type of asset transfer is required for a particular `(asset, dest)` combination.\npub enum AssetTransferFilter { /// teleport assets matching `AssetFilter` to `dest` Teleport(AssetFilter), /// reserve-transfer assets matching `AssetFilter` to `dest`, using the local chain as reserve ReserveDeposit(AssetFilter), /// reserve-transfer assets matching `AssetFilter` to `dest`, using `dest` as reserve ReserveWithdraw(AssetFilter),\n} This RFC proposes 1 new XCM instruction: /// Cross-chain transfer matching `assets` in the holding register as follows:\n///\n/// Assets in the holding register are matched using the given list of `AssetTransferFilter`s,\n/// they are then transferred based on their specified transfer type:\n///\n/// - teleport: burn local assets and append a `ReceiveTeleportedAsset` XCM instruction to\n/// the XCM program to be sent onward to the `dest` location,\n///\n/// - reserve deposit: place assets under the ownership of `dest` within this consensus system\n/// (i.e. its sovereign account), and append a `ReserveAssetDeposited` XCM instruction\n/// to the XCM program to be sent onward to the `dest` location,\n///\n/// - reserve withdraw: burn local assets and append a `WithdrawAsset` XCM instruction\n/// to the XCM program to be sent onward to the `dest` location,\n///\n/// The onward XCM is then appended a `ClearOrigin` to allow safe execution of any following\n/// custom XCM instructions provided in `remote_xcm`.\n///\n/// The onward XCM also potentially contains a `BuyExecution` instruction based on the presence\n/// of the `remote_fees` parameter (see below).\n///\n/// If a transfer requires going through multiple hops, an XCM program can compose this instruction\n/// to be used at every chain along the path, describing that specific leg of the transfer.\n///\n/// Parameters:\n/// - `dest`: The location of the transfer next hop.\n/// - `remote_fees`: If set to `Some(asset_xfer_filter)`, the single asset matching\n/// `asset_xfer_filter` in the holding register will be transferred first in the remote XCM\n/// program, followed by a `BuyExecution(fee)`, then rest of transfers follow.\n/// This guarantees `remote_xcm` will successfully pass a `AllowTopLevelPaidExecutionFrom` barrier.\n/// - `remote_xcm`: Custom instructions that will be executed on the `dest` chain. Note that\n/// these instructions will be executed after a `ClearOrigin` so their origin will be `None`.\n///\n/// Safety: No concerns.\n///\n/// Kind: *Command*.\n///\nInitiateAssetsTransfer { destination: Location, assets: Vec, remote_fees: Option, remote_xcm: Xcm<()>,\n} An InitiateAssetsTransfer { .. } instruction shall transfer to dest, all assets in the holding register that match the provided assets and remote_fees filters. These filters identify the assets to be transferred as well as the transfer type to be used for transferring them. It shall handle the local side of the transfer, then forward an onward XCM to dest for handling the remote side of the transfer. It should do so using same mechanisms as existing DepositReserveAsset, InitiateReserveWithdraw, InitiateTeleport instructions but practically combining all required XCM instructions to be remotely executed into a single remote XCM program to be sent over to dest. Furthermore, through remote_fees: Option, it shall allow specifying a single asset to be used for fees on dest chain. This single asset shall be remotely handled/received by the first instruction in the onward XCM and shall be followed by a BuyExecution instruction using it. If remote_fees is set to None, the first instruction in the onward XCM shall be a UnpaidExecution instruction. The rest of the assets shall be handled by subsequent instructions, thus also finally allowing single asset buy execution barrier security recommendation. The BuyExecution appended to the onward XCM specifies WeightLimit::Unlimited, thus being limited only by the remote_fees asset \"amount\". This is a deliberate decision for enhancing UX - in practice, people/dApps care about limiting the amount of fee asset used and not the actually used weight. The onward XCM, following the assets transfers instructions, ClearOrigin or DescendOrigin instructions shall be appended to stop acting on behalf of the source chain, then the caller-provided remote_xcm shall also be appended, allowing the caller to control what to do with the transferred assets.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Explanation","id":"588","title":"Explanation"},"589":{"body":"Transferring ROCs as the native asset of RococoAssetHub and PENs as the native asset of Penpal, Transfer origin is Penpal (on Rococo) and the destination is WestendAssetHub (across the bridge), ROCs are native to RococoAssetHub and are registered as trust-backed assets on Penpal and WestendAssetHub, PENs are native to Penpal and are registered as teleportable assets on RococoAssetHub and as foreign assets on WestendAssetHub, Fees on RococoAssetHub and WestendAssetHub are paid using ROCs. We can transfer them from Penpal (Rococo), through RococoAssetHub, over the bridge to WestendAssetHub by executing a single XCM message, even though we'll be mixing multiple types of transfers along the path: 1st leg of the transfer: Penpal -> Rococo Asset Hub: teleport PENs reserve withdraw ROCs 2nd leg of the transfer: Rococo Asset Hub -> Westend Asset Hub: reserve deposit both PENs and ROCs Penpal::execute_with(|| { let destination = Location::new(2, (GlobalConsensus(Westend), Parachain(1000)).into()); let rocs_id: AssetId = Parent.into(); let rocs: Asset = (rocs_id.clone(), rocs_amount).into(); let pens: Asset = (pens_id, pens_amount).into(); let assets: Assets = vec![rocs.clone(), pens.clone()].into(); // XCM to be executed at dest (Westend Asset Hub) let xcm_on_dest = Xcm(vec![DepositAsset { assets: Wild(All), beneficiary: beneficiary.clone() }]); // XCM to be executed at Rococo Asset Hub let context = PenpalUniversalLocation::get(); let reanchored_assets = assets.clone().reanchored(&local_asset_hub, &context).unwrap(); let reanchored_dest = destination.clone().reanchored(&local_asset_hub, &context).unwrap(); let reanchored_rocs_id = rocs_id.clone().reanchored(&local_asset_hub, &context).unwrap(); // from AHR, both ROCs and PENs are local-reserve transferred to Westend Asset Hub let assets_filter = vec![ AssetTransferFilter::ReserveDeposit(reanchored_assets.clone().into()) ]; // we want to pay with ROCs on WAH let remote_fees = Some(AssetTransferFilter::ReserveDeposit( AssetFilter::Wild(AllOf { id: reanchored_rocs_id.into(), fun: WildFungibility::Fungible })) ); let xcm_on_ahr = Xcm(vec![ InitiateAssetsTransfer { dest: reanchored_dest, assets: assets_filter, remote_fees: Some(), remote_xcm: xcm_on_dest, }, ]); // pay remote fees with ROCs let remote_fees = Some( AssetTransferFilter::ReserveWithdraw( AssetFilter::Wild(AllOf { id: rocs_id.into(), fun: WildFungibility::Fungible }) ) ); // XCM to be executed locally let xcm = Xcm::(vec![ // Withdraw both ROCs and PENs from origin account WithdrawAsset(assets.clone().into()), // Execute the transfers while paying remote fees with ROCs InitiateAssetsTransfer { dest: local_asset_hub, assets: vec![ // ROCs are reserve-withdrawn on AHR ReserveWithdraw(rocs.into()), // PENs are teleported to AHR Teleport(pens.into()), ], remote_fees, remote_xcm: xcm_on_ahr, }, ]); ::PolkadotXcm::execute( signed_origin, bx!(xcm::VersionedXcm::V4(xcm.into())), Weight::MAX, ).unwrap();\n})","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Example usage: transferring 2 different asset types across 3 chains","id":"589","title":"Example usage: transferring 2 different asset types across 3 chains"},"59":{"body":"Parachain Teams Relay Chain Node implementation teams Relay Chain runtime developers","breadcrumbs":"RFC-0000: Feature Name Here » Stakeholders","id":"59","title":"Stakeholders"},"590":{"body":"No drawbacks identified.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Drawbacks","id":"590","title":"Drawbacks"},"591":{"body":"There should be no security risks related to the new instruction from the XCVM perspective. It follows the same pattern as with single-type asset transfers, only now it allows combining multiple types at once. Improves security by enabling enforcement of single asset for buying execution , which minimizes the potential free/unpaid work that a receiving chain has to do. It does so, by making the required execution fee payment, part of the instruction logic through the remote_fees: Option parameter, which will make sure the remote XCM starts with a single-asset-holding-loading-instruction, immediately followed by a BuyExecution using said asset.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Testing, Security, and Privacy","id":"591","title":"Testing, Security, and Privacy"},"592":{"body":"This brings no impact to the rest of the XCM spec. It is a new, independent instruction, no changes to existing instructions. Enhances the exposed functionality of Polkadot. Will allow multi-chain transfers that are currently forced to happen in multiple programs per asset per \"hop\", to be possible in a single XCM program.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Performance, Ergonomics, and Compatibility","id":"592","title":"Performance, Ergonomics, and Compatibility"},"593":{"body":"No performance changes/implications.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Performance","id":"593","title":"Performance"},"594":{"body":"The proposal enhances developers' and users' cross-chain asset transfer capabilities. This enhancement is optimized for XCM programs transferring multiple assets, needing to run their logic across multiple chains.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Ergonomics","id":"594","title":"Ergonomics"},"595":{"body":"Does this proposal break compatibility with existing interfaces, older versions of implementations? Summarize necessary migrations or upgrade strategies, if any. This enhancement is compatible with all existing XCM programs and versions. New (XCMv5) programs using this instruction shall be best-effort downgraded to an older XCM version, but cannot guarantee success. A program where the new instruction is used to initiate multiple types of asset transfers, cannot be downgraded to older XCM versions, because there is no equivalent capability there. Such conversion attempts will explicitly fail.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Compatibility","id":"595","title":"Compatibility"},"596":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Prior Art and References","id":"596","title":"Prior Art and References"},"597":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Unresolved Questions","id":"597","title":"Unresolved Questions"},"598":{"body":"None.","breadcrumbs":"RFC-0100: New XCM instruction: InitiateAssetsTransfer » Future Directions and Related Material","id":"598","title":"Future Directions and Related Material"},"599":{"body":"(source) Table of Contents RFC-0101: XCM Transact remove require_weight_at_most parameter Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 12 July 2024 Description Remove require_weight_at_most parameter from XCM Transact Authors Adrian Catangiu","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » RFC-0101: XCM Transact remove require_weight_at_most parameter","id":"599","title":"RFC-0101: XCM Transact remove require_weight_at_most parameter"},"6":{"body":"ReportMetadata The ReportMetadata is a new instruction to query metadata information. It can be used to query metadata key list or to query values of interested keys. This instruction allows querying the metadata of: a collection (fungible or nonfungible) an NFT If an asset (or an asset instance) for which the query is made doesn't exist, the Response::Null should be reported via the existing QueryResponse instruction. The ReportMetadata can be used without origin (i.e., following the ClearOrigin instruction) since it only reads state. Safety: The reporter origin should be trusted to hold the true metadata. If the reserve-based model is considered, the asset's reserve location must be viewed as the only source of truth about the metadata. The use case for this instruction is when the metadata information of a foreign asset (or asset instance) is used in the logic of a consensus entity that requested it. /// An instruction to query metadata of an asset or an asset instance.\nReportMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the metadata of the collection is reported. instance: AssetInstance, /// See `MetadataQueryKind` below. query_kind: MetadataQueryKind, /// The usual field for Report XCM instructions. /// /// Information regarding the query response. /// The `QueryResponseInfo` type is already defined in the XCM spec. response_info: QueryResponseInfo,\n} Where the MetadataQueryKind is: enum MetadataQueryKind { /// Query metadata key list. KeyList, /// Query values of the specified keys. Values(MetadataKeys),\n} The QueryMetadata works in conjunction with the existing QueryResponse instruction. The Response type should be modified accordingly: we need to add a new AssetMetadata variant to it. /// The struct used in the existing `QueryResponse` instruction.\npub enum Response { // ... snip, existing variants ... /// The metadata info. AssetMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the reported metadata is related to the collection, not a token. instance: AssetInstance, /// See `MetadataResponseData` below. data: MetadataResponseData, }\n} pub enum MetadataResponseData { /// The metadata key list to be reported /// in response to the `KeyList` metadata query kind. KeyList(MetadataKeys), /// The values of the keys that were specified in the /// `Values` variant of the metadata query kind. Values(MetadataMap),\n} ModifyMetadata The ModifyMetadata is a new instruction to request a remote chain to modify the values of the specified keys. This instruction can be used to update the metadata of a collection (fungible or nonfungible) or of an NFT. The remote chain handles the modification request and may reject it based on its internal rules. The request can only be executed or rejected in its entirety. It must not be executed partially. To execute the ModifyMetadata, an origin is required so that the handling logic can authorize the metadata modification request from a known source. Since this instruction requires an origin, the assets used to cover the execution fees must be transferred in a way that preserves the origin. For instance, one can use the approach described in RFC #122 if the handling chain configured aliasing rules accordingly. The example use case of this instruction is to ask the reserve location of the asset to modify the metadata. So that, the original asset's metadata is updated according to the reserve location's rules. ModifyMetadata { /// The ID of an asset (a collection, fungible or nonfungible). asset_id: AssetId, /// The ID of an asset instance. /// /// If the value is `Undefined`, the modification request targets the collection, not a token. instance: AssetInstance, /// The map contains the keys mapped to the requested new values. modification: MetadataMap,\n}","breadcrumbs":"RFC-0125: XCM Asset Metadata » New instructions","id":"6","title":"New instructions"},"60":{"body":"The issues with on-chain runtime upgrades are: Needlessly costly. A single runtime upgrade more or less occupies an entire relay chain block, thus it might affect also other parachains, especially if their candidates are also not negligible due to messages for example or they want to uprade their runtime at the same time. The signalling of the parachain to notify the relay chain of an upcoming runtime upgrade already contains the upgrade. Therefore the only way to rate limit upgrades is to drop an already distributed update in the size of megabytes: With the result that the parachain missed a block and more importantly it will try again with the very next block, until it finally succeeds. If we imagine to reduce capacity of runtime upgrades to let's say 1 every 100 relay chain blocks, this results in lot's of wasted effort and lost blocks. We discussed introducing a separate signalling before submitting the actual runtime, but I think we should just go one step further and make upgrades fully off-chain. Which also helps bringing down deposit costs in a secure way, as we are also actually reducing costs for the network.","breadcrumbs":"RFC-0000: Feature Name Here » Explanation","id":"60","title":"Explanation"},"600":{"body":"The Transact XCM instruction currently forces the user to set a specific maximum weight allowed to the inner call and then also pay for that much weight regardless of how much the call actually needs in practice. This RFC proposes improving the usability of Transact by removing that parameter and instead get and charge the actual weight of the inner call from its dispatch info on the remote chain.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Summary","id":"600","title":"Summary"},"601":{"body":"The UX of using Transact is poor because of having to guess/estimate the require_weight_at_most weight used by the inner call on the target. We've seen multiple Transact on-chain failures caused by guessing wrong values for this require_weight_at_most even though the rest of the XCM program would have worked. In practice, this parameter only adds UX overhead with no real practical value. Use cases fall in one of two categories: Unpaid execution of Transacts - in these cases the require_weight_at_most is not really useful, caller doesn't have to pay for it, and on the call site it either fits the block or not; Paid execution of single Transact - the weight to be spent by the Transact is already covered by the BuyExecution weight limit parameter. We've had multiple OpenGov root/whitelisted_caller proposals initiated by core-devs completely or partially fail because of incorrect configuration of require_weight_at_most parameter. This is a strong indication that the instruction is hard to use.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Motivation","id":"601","title":"Motivation"},"602":{"body":"Runtime Users, Runtime Devs, Wallets, dApps,","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Stakeholders","id":"602","title":"Stakeholders"},"603":{"body":"The proposed enhancement is simple: remove require_weight_at_most parameter from the instruction: - Transact { origin_kind: OriginKind, require_weight_at_most: Weight, call: DoubleEncoded },\n+ Transact { origin_kind: OriginKind, call: DoubleEncoded }, The XCVM implementation shall no longer use require_weight_at_most for weighing. Instead, it shall weigh the Transact instruction by decoding and weighing the inner call.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Explanation","id":"603","title":"Explanation"},"604":{"body":"No drawbacks, existing scenarios work as before, while this also allows new/easier flows.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Drawbacks","id":"604","title":"Drawbacks"},"605":{"body":"Currently, an XCVM implementation can weigh a message just by looking at the decoded instructions without decoding the Transact's call, but assuming require_weight_at_most weight for it. With the new version it has to decode the inner call to know its actual weight. But this does not actually change the security considerations, as can be seen below. With the new Transact the weighing happens after decoding the inner call. The entirety of the XCM program containing this Transact needs to be either covered by enough bought weight using a BuyExecution, or the origin has to be allowed to do free execution. The security considerations around how much can someone execute for free are the same for both this new version and the old. In both cases, an \"attacker\" can do the XCM decoding (including Transact inner calls) for free by adding a large enough BuyExecution without actually having the funds available. In both cases, decoding is done for free, but in both cases execution fails early on BuyExecution.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Testing, Security, and Privacy","id":"605","title":"Testing, Security, and Privacy"},"606":{"body":"","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Performance, Ergonomics, and Compatibility","id":"606","title":"Performance, Ergonomics, and Compatibility"},"607":{"body":"No performance change.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Performance","id":"607","title":"Performance"},"608":{"body":"Ergonomics are slightly improved by simplifying Transact API.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Ergonomics","id":"608","title":"Ergonomics"},"609":{"body":"Compatible with previous XCM programs.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Compatibility","id":"609","title":"Compatibility"},"61":{"body":"As part of elastic scaling we are already planning to increase flexibility of UMP messages , we can now use this to our advantage and introduce another UMP message: enum UMPSignal { // For elastic scaling OnCore(CoreIndex), // For off-chain upgrades RequestCodeUpgrade(Hash),\n} We could also make that new message a regular XCM, calling an extrinsic on the relay chain, but we will want to look into that message right after validation on the backers on the node side, making a straight forward semantic message more apt for the purpose.","breadcrumbs":"RFC-0000: Feature Name Here » Introduce a new UMP message type RequestCodeUpgrade","id":"61","title":"Introduce a new UMP message type RequestCodeUpgrade"},"610":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Prior Art and References","id":"610","title":"Prior Art and References"},"611":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Unresolved Questions","id":"611","title":"Unresolved Questions"},"612":{"body":"None.","breadcrumbs":"RFC-0101: XCM Transact remove require_weight_at_most parameter » Future Directions and Related Material","id":"612","title":"Future Directions and Related Material"},"613":{"body":"(source) Table of Contents RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts Summary Motivation Stakeholders Explanation Reclaiming unused space in the descriptor UMP transport Polkadot Primitive changes Backwards compatibility Parachain block validation On-chain backing Drawbacks Testing, Security, and Privacy Performance Ergonomics Compatibility Relay chain runtime Validators Tooling Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 15 July 2024 Description Constrain parachain block validity to a specific core and session Authors Andrei Sandu","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts","id":"613","title":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts"},"614":{"body":"Elastic scaling is not resilient against griefing attacks without a way for a PoV (Proof of Validity) to commit to the particular core index it was intended for. This RFC proposes a way to include core index information in the candidate commitments and the CandidateDescriptor data structure in a backward compatible way. Additionally, it proposes the addition of a SessionIndex field in the CandidateDescriptor to make dispute resolution more secure and robust.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Summary","id":"614","title":"Summary"},"615":{"body":"This RFC proposes a way to solve two different problems: For Elastic Scaling, it prevents anyone who has acquired a valid collation to DoS the parachain by providing the same collation to all backing groups assigned to the parachain. This can happen before the next valid parachain block is authored and will prevent the chain of candidates from being formed, reducing the throughput of the parachain to a single core. The dispute protocol relies on validators trusting the session index provided by other validators when initiating and participating in disputes. It is used to look up validator keys and check dispute vote signatures. By adding a SessionIndex in the CandidateDescriptor, validators no longer have to trust the Sessionindex provided by the validator raising a dispute. The dispute may concern a relay chain block not yet imported by a validator. In this case, validators can safely assume the session index refers to the session the candidate has appeared in, otherwise, the chain would have rejected the candidate.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Motivation","id":"615","title":"Motivation"},"616":{"body":"Polkadot core developers. Cumulus node developers. Tooling, block explorer developers. This approach and alternatives have been considered and discussed in this issue .","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Stakeholders","id":"616","title":"Stakeholders"},"617":{"body":"The approach proposed below was chosen primarily because it minimizes the number of breaking changes, the complexity and takes less implementation and testing time. The proposal is to change the existing primitives while keeping binary compatibility with the older versions. We repurpose unused fields to introduce core index and a session index information in the CandidateDescriptor and extend the UMP to transport non-XCM messages.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Explanation","id":"617","title":"Explanation"},"618":{"body":"The CandidateDescriptor includes collator and signature fields. The collator includes a signature on the following descriptor fields: parachain id, relay parent, validation data hash, validation code hash, and the PoV hash. However, in practice, having a collator signature in the receipt on the relay chain does not provide any benefits as there is no mechanism to punish or reward collators that have provided bad parachain blocks. This proposal aims to remove the collator signature and all the logic that checks the collator signatures of candidate receipts. We use the first 7 reclaimed bytes to represent the version, the core, session index, and fill the rest with zeroes. So, there is no change in the layout and length of the receipt. The new primitive is binary-compatible with the old one.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Reclaiming unused space in the descriptor","id":"618","title":"Reclaiming unused space in the descriptor"},"619":{"body":"CandidateCommitments remains unchanged as we will store scale encoded UMPSignal messages directly in the parachain UMP queue by outputting them in upward_messages . The UMP queue layout is changed to allow the relay chain to receive both the XCM messages and UMPSignal messages. An empty message (empty Vec) is used to mark the end of XCM messages and the start of UMPSignal messages. The UMPSignal is optional and can be omitted by parachains not using elastic scaling. This way of representing the new messages has been chosen over introducing an enum wrapper to minimize breaking changes of XCM message decoding in tools like Subscan for example. Example: [ XCM message1, XCM message2, ..., EMPTY message, UMPSignal::SelectCore ] UMPSignal messages /// The selector that determines the core index.\npub struct CoreSelector(pub u8); /// The offset in the relay chain claim queue.\n///\n/// The state of the claim queue is given by the relay chain block\n/// that is used as context for the `PoV`. pub struct ClaimQueueOffset(pub u8); /// Signals sent by a parachain to the relay chain.\npub enum UMPSignal { /// A message sent by a parachain to select the core the candidate is committed to. /// Relay chain validators, in particular backers, use the `CoreSelector` and `ClaimQueueOffset` /// to compute the index of the core the candidate has committed to. SelectCore(CoreSelector, ClaimQueueOffset),\n} The CoreSelector together with the ClaimQueueOffset are used to index the claim queue. This way the validators can compute the CoreIndex and ensure that the collator put the correct CoreIndex into the CandidateDescriptor. Example: cq_offset = 1 and core_selector = 3 The table below represents a snapshot of the claim queue: offset = 0 offset = 1 offset = 2 Core 1 Para A Para A Para A Core 2 Para A Para B Para A Core 3 Para B Para A Para A The purpose of ClaimQueueOffset is to select the column from the above table. For cq_offset = 1 we get [Para A, Para B, Para A] and use as input to create a sorted vec with the cores A is assigned to: [Core 1, Core 3] and call it para_assigned_cores. We use core_selector and determine the committed core index is Core 3 like this: let committed_core_index = para_assigned_cores[core_selector % para_assigned_cores.len()];","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » UMP transport","id":"619","title":"UMP transport"},"62":{"body":"We will introduce a new request/response protocol for both collators and validators, with the following request/response: struct RequestBlob { blob_hash: Hash,\n} struct BlobResponse { blob: Vec\n} This protocol will be used by backers to request the PVF from collators in the following conditions: They received a collation sending RequestCodeUpgrade. They received a collation, but they don't yet have the code that was previously registered on the relaychain. (E.g. disk pruned, new validator) In case they received the collation via PoV distribution instead of from the collator itself, they will use the exact same message to fetch from the valiator they got the PoV from.","breadcrumbs":"RFC-0000: Feature Name Here » Handle RequestCodeUpgrade on backers","id":"62","title":"Handle RequestCodeUpgrade on backers"},"620":{"body":"New CandidateDescriptor reclaim 32 bytes from collator: CollatorId and 64 bytes from signature: CollatorSignature and rename to reserved1 and reserved2 fields. take 1 bytes from reserved1 for a new version: u8 field. take 2 bytes from reserved1 for a new core_index: u16 field. take 4 bytes from reserved1 for a new session_index: u32 field. the remaining reserved1 and reserved2 fields are zeroed The new primitive will look like this: pub struct CandidateDescriptorV2 { /// The ID of the para this is a candidate for. para_id: ParaId, /// The hash of the relay-chain block this is executed in the context of. relay_parent: H, /// Version field. The raw value here is not exposed, instead, it is used /// to determine the `CandidateDescriptorVersion` version: InternalVersion, /// The core index where the candidate is backed. core_index: u16, /// The session in which the candidate is backed. session_index: SessionIndex, /// Reserved bytes. reserved1: [u8; 25], /// The blake2-256 hash of the persisted validation data. This is extra data derived from /// relay-chain state which may vary based on bitfields included before the candidate. /// Thus it cannot be derived entirely from the relay parent. persisted_validation_data_hash: Hash, /// The blake2-256 hash of the PoV. pov_hash: Hash, /// The root of a block's erasure encoding Merkle tree. erasure_root: Hash, /// Reserved bytes. reserved2: [u8; 64], /// Hash of the para header that is being generated by this candidate. para_head: Hash, /// The blake2-256 hash of the validation code bytes. validation_code_hash: ValidationCodeHash,\n} In future format versions, parts of the reserved1 and reserved2 bytes can be used to include additional information in the descriptor.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Polkadot Primitive changes","id":"620","title":"Polkadot Primitive changes"},"621":{"body":"Two flavors of candidate receipts are used in network protocols, runtime and node implementation: CommittedCandidateReceipt which includes the CandidateDescriptor and the CandidateCommitments CandidateReceipt which includes the CandidateDescriptor and just a hash of the commitments We want to support both the old and new versions in the runtime and node, so the implementation must be able to detect the version of a given candidate receipt. The version of the descriptor is detected by checking the reserved fields. If they are not zeroed, it means it is a version 1 descriptor. Otherwise the version field is used further to determine the version. It should be 0 for version 2 descriptors. If it is not the descriptor has an unknown version and should be considered invalid.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Backwards compatibility","id":"621","title":"Backwards compatibility"},"622":{"body":"If the candidate descriptor is version 1, there are no changes. Backers must check the validity of core_index and session_index fields. A candidate must not be backed if any of the following are true: the core_index in the descriptor does not match the core the backer is assigned to the session_index is not equal to the session index the candidate is backed in the core_index in the descriptor does not match the one determined by the UMPSignal::SelectCore message","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Parachain block validation","id":"622","title":"Parachain block validation"},"623":{"body":"If the candidate descriptor is version 1, there are no changes. For version 2 descriptors the runtime will determine the core_index using the same inputs as backers did off-chain. It currently stores the claim queue at the newest allowed relay parent corresponding to the claim queue offset 0. The runtime needs to be changed to store a claim queue snapshot at all allowed relay parents.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » On-chain backing","id":"623","title":"On-chain backing"},"624":{"body":"The only drawback is that further additions to the descriptor are limited to the amount of remaining unused space.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Drawbacks","id":"624","title":"Drawbacks"},"625":{"body":"Standard testing (unit tests, CI zombienet tests) for functionality and mandatory security audit to ensure the implementation does not introduce any new security issues. Backward compatibility of the implementation will be tested on testnets (Versi and Westend). There is no impact on privacy.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Testing, Security, and Privacy","id":"625","title":"Testing, Security, and Privacy"},"626":{"body":"Overall performance will be improved by not checking the collator signatures in runtime and nodes. The impact on the UMP queue and candidate receipt processing is negligible. The ClaimQueueOffset along with the relay parent choice allows parachains to optimize their block production for either throughput or lower XCM message processing latency. A value of 0 with the newest relay parent provides the best latency while picking older relay parents avoids re-orgs.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Performance","id":"626","title":"Performance"},"627":{"body":"It is mandatory for elastic parachains to switch to the new receipt format and commit to a core by sending the UMPSignal::SelectCore message. It is optional but desired that all parachains switch to the new receipts for providing the session index for disputes. The implementation of this RFC itself must not introduce any breaking changes for the parachain runtime or collator nodes.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Ergonomics","id":"627","title":"Ergonomics"},"628":{"body":"The proposed changes are not fully backward compatible, because older validators verify the collator signature of candidate descriptors. Additional care must be taken before enabling the new descriptors by waiting for at least 2/3 + 1 validators to upgrade. Validators that have not upgraded will not back candidates using the new descriptor format and will also initiate disputes against these candidates.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Compatibility","id":"628","title":"Compatibility"},"629":{"body":"The first step is to remove collator signature checking logic in the runtime but keep the node side collator signature checks. The runtime must be upgraded to support the new primitives before any collator or node is allowed to use the new candidate receipts format.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Relay chain runtime","id":"629","title":"Relay chain runtime"},"63":{"body":"Once the candidate issuing RequestCodeUpgrade got backed on chain, validators will start fetching the code from the backers as part of availability distribution. To mitigate attack vectors we should make sure that serving requests for code can be treated as low priority requests. Thus I am suggesting the following scheme: Validators will notice via a runtime API (TODO: Define) that a new code has been requested, the API will return the Hash and a counter, which starts at some configurable value e.g. 10. The validators are now aware of the new hash and start fetching, but they don't have to wait for the fetch to succeed to sign their bitfield. Then on each further candidate from that chain that counter gets decremented. Validators which have not yet succeeded fetching will now try again. This game continues until the counter reached 0. Now it is mandatory to have to code in order to sign a 1 in the bitfield. PVF pre-checking will happen after the candidate which brought the counter to 0 has been successfully included and thus is also able to assume that 2/3 of the validators have the code. This scheme serves two purposes: Fetching can happen over a longer period of time with low priority. E.g. if we waited for the PVF at the very first avaialbility distribution, this might actually affect liveness of other chains on the same core. Distributing megabytes of data to a thousand validators, might take a bit. Thus this helps isolating parachains from each other. By configuring the initial counter value we can affect how much an upgrade costs. E.g. forcing the parachain to produce 10 blocks, means 10x the cost for issuing an update. If too frequent upgrades ever become a problem for the system, we have a knob to make them more costly.","breadcrumbs":"RFC-0000: Feature Name Here » Get the new code to all validators","id":"63","title":"Get the new code to all validators"},"630":{"body":"To ensure a smooth launch, a new node feature is required. The feature acts as a signal for supporting the new candidate receipts on the node side and can only be safely enabled if at least 2/3 + 1 of the validators are upgraded. Node implementations need to decode the new candidate descriptor once the feature is enabled otherwise they might raise disputes and get slashed. Once the feature is enabled, the validators will skip checking the collator signature when processing the candidate receipts and verify the CoreIndex and SessionIndex fields if present in the receipt. No new implementation of networking protocol versions for collation and validation is required.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Validators","id":"630","title":"Validators"},"631":{"body":"Any tooling that decodes UMP XCM messages needs an update to support or ignore the new UMP messages, but they should be fine to decode the regular XCM messages that come before the separator.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Tooling","id":"631","title":"Tooling"},"632":{"body":"Forum discussion about a new CandidateReceipt format: https://forum.polkadot.network/t/pre-rfc-discussion-candidate-receipt-format-v2/3738","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Prior Art and References","id":"632","title":"Prior Art and References"},"633":{"body":"N/A","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Unresolved Questions","id":"633","title":"Unresolved Questions"},"634":{"body":"The implementation is extensible and future-proof to some extent. With minimal or no breaking changes, additional fields can be added in the candidate descriptor until the reserved space is exhausted At this point, there is a simple way to determine the version of the receipt, by testing for zeroed reserved bytes in the descriptor. Future versions of the receipt can be implemented and identified by using the version field of the descriptor introduced in this RFC.","breadcrumbs":"RFC-0103: Introduce a CoreIndex commitment and a SessionIndex field in candidate receipts » Future Directions and Related Material","id":"634","title":"Future Directions and Related Material"},"635":{"body":"(source) Table of Contents RFC-0105: XCM improved fee mechanism Summary Motivation Stakeholders Explanation Examples Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Allow multiple types of fees to be paid Authors Francisco Aguirre","breadcrumbs":"RFC-0105: XCM improved fee mechanism » RFC-0105: XCM improved fee mechanism","id":"635","title":"RFC-0105: XCM improved fee mechanism"},"636":{"body":"XCM already handles execution fees in an effective and efficient manner using the BuyExecution instruction. However, other types of fees are not handled as effectively -- for example, delivery fees. Fees exist that can't be measured using Weight -- as execution fees can -- so a new method should be thought up for those cases. This RFC proposes making the fee handling system simpler and more general, by doing two things: Adding a fees register Deprecating BuyExecution and adding a new instruction PayFees with new semantics to ultimately replace it.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Summary","id":"636","title":"Summary"},"637":{"body":"Execution fees are handled correctly by XCM right now. However, the addition of extra fees, like for message delivery, result in awkward ways of integrating them into the XCVM implementation. This is because these types of fees are not included in the language. The standard should have a way to correctly deal with these implementation specific fees, that might not exist in every system that uses XCM. The new instruction moves the specified amount of fees from the holding register to a dedicated fees register that the XCVM can use in flexible ways depending on its implementation. The XCVM implementation is free to use these fees to pay for execution fees, transport fees, or any other type of fee that might be necessary. This moves the specifics of fees further away from the XCM standard, and more into the actual underlying XCVM implementation, which is a good thing.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Motivation","id":"637","title":"Motivation"},"638":{"body":"Runtime Users Runtime Devs Wallets dApps","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Stakeholders","id":"638","title":"Stakeholders"},"639":{"body":"The new instruction that will replace BuyExecution is a much simpler and general version: PayFees. This instruction takes one Asset, takes it from the holding register, and puts it into a new fees register. The XCVM implementation can now use this Asset to make sure every necessary fee is paid for, this includes execution fees, delivery fees, and any other type of fee necessary for the program to execute successfully. PayFees { asset: Asset } This new instruction will reserve the entirety of the asset operand for fee payment. There is not concept of returning the leftover fees to the holding register, to allow for the implementation to charge fees at different points during execution. Because of this, the asset passed in can't be used for anything else during the entirety of the program. This is different from the current semantics of BuyExecution. If not all Asset in the fees register is used when the execution ends, then we trap them alongside any possible leftover assets from the holding register. RefundSurplus can be used to move all leftover fees from the fees register to the holding register. Care must be taken that this is used only after all possible instructions which might charge fees, else execution will fail.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Explanation","id":"639","title":"Explanation"},"64":{"body":"First when a candidate is backed we need to make the new hash available (together with a counter) via a runtime API so validators in availability distribution can check for it and fetch it if changed (see previous section). For performance reasons, I think we should not do an additional call, but replace the existing one with one containing the new additional information (Option<(Hash, Counter)>). Once the candidate gets included (counter 0), the hash is given to pre-checking and only after pre-checking succeeded (and a full session passed) it is finally enacted and the parachain can switch to the new code. (Same process as it used to be.)","breadcrumbs":"RFC-0000: Feature Name Here » On-chain code upgrade process","id":"64","title":"On-chain code upgrade process"},"640":{"body":"Most XCM programs that pay for execution are written like so: // Instruction that loads the holding register\nBuyExecution { asset, weight_limit }\n// ...rest With this RFC, the structure would be the same, but using the new instruction, that has different semantics: // Instruction that loads the holding register\nPayFees { asset }\n// ...rest","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Examples","id":"640","title":"Examples"},"641":{"body":"There needs to be an explicit change from BuyExecution to PayFees, most often accompanied by a reduction in the assets passed in.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Drawbacks","id":"641","title":"Drawbacks"},"642":{"body":"It might become a security concern if leftover fees are trapped, since a lot of them are expected.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Testing, Security, and Privacy","id":"642","title":"Testing, Security, and Privacy"},"643":{"body":"","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Performance, Ergonomics, and Compatibility","id":"643","title":"Performance, Ergonomics, and Compatibility"},"644":{"body":"There should be no performance downsides to this approach. The fees register is a simplification that may actually result in better performance, in the case an implementation is doing a workaround to achieve what this RFC proposes.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Performance","id":"644","title":"Performance"},"645":{"body":"The interface is going to be very similar to the already existing one. Even simpler since PayFees will only receive one asset. That asset will allow users to limit the amount of fees they are willing to pay.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Ergonomics","id":"645","title":"Ergonomics"},"646":{"body":"This RFC can't just change the semantics of the BuyExecution instruction since that instruction accepts any funds, uses what it needs and returns the rest immediately. The new proposed instruction, PayFees, doesn't return the leftover immediately, it keeps it in the fees register. In practice, the deprecated BuyExecution needs to be slowly rolled out in favour of PayFees.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Compatibility","id":"646","title":"Compatibility"},"647":{"body":"The closed RFC PR on the xcm-format repository, before XCM RFCs got moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/53.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Prior Art and References","id":"647","title":"Prior Art and References"},"648":{"body":"None","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Unresolved Questions","id":"648","title":"Unresolved Questions"},"649":{"body":"This proposal would greatly benefit from an improved asset trapping system. CustomAssetClaimer is also related, as it directly improves the ergonomics of this proposal. LeftoverAssetsDestination execution hint would also similarly improve the ergonomics. Removal of JIT fees is also related, they are useless with this proposal.","breadcrumbs":"RFC-0105: XCM improved fee mechanism » Future Directions and Related Material","id":"649","title":"Future Directions and Related Material"},"65":{"body":"Backers If a backer receives a collation for a parachain it does not yet have the code as enacted on chain (see \"On-chain code upgrade process\"), it will use above request/response protocol to fetch it from whom it received the collation. Availablity Distribution Validators in availability distribution will be changed to only sign a 1 in the bitfield of a candidate if they not only have the chunk, but also the currently active PVF. They will fetch it from backers in case they don't have it yet.","breadcrumbs":"RFC-0000: Feature Name Here » Handling new validators","id":"65","title":"Handling new validators"},"650":{"body":"(source) Table of Contents RFC-0107: XCM Execution hints Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Add a mechanism for configuring particular XCM executions Authors Francisco Aguirre","breadcrumbs":"RFC-0107: XCM Execution hints » RFC-0107: XCM Execution hints","id":"650","title":"RFC-0107: XCM Execution hints"},"651":{"body":"A previous XCM RFC (https://github.com/polkadot-fellows/xcm-format/pull/37) introduced a SetAssetClaimer instruction. This idea of instructing the XCVM to change some implementation-specific behavior is useful. In order to generalize this mechanism, this RFC introduces a new instruction SetHints and makes the SetAssetClaimer be just one of many possible execution hints.","breadcrumbs":"RFC-0107: XCM Execution hints » Summary","id":"651","title":"Summary"},"652":{"body":"There is a need for specifying how certain implementation-specific things should behave. Things like who can claim the assets or what can be done instead of trapping assets. Another idea for a hint: AssetForFees: to signify to the executor what asset the user prefers to use for fees. LeftoverAssetsDestination: for depositing leftover assets to a destination instead of trapping them","breadcrumbs":"RFC-0107: XCM Execution hints » Motivation","id":"652","title":"Motivation"},"653":{"body":"Runtime devs Wallets dApps","breadcrumbs":"RFC-0107: XCM Execution hints » Stakeholders","id":"653","title":"Stakeholders"},"654":{"body":"A new instruction, SetHints, will be added. This instruction will take a single parameter of type Hint, an enumeration. The first variant for this enum is AssetClaimer, which allows to specify a location that should be able to claim trapped assets. This means the instruction SetAssetClaimer would also be removed, in favor of this. In Rust, the new definitions would look as follows: enum Instruction { // ...snip... SetHints(BoundedVec), // ...snip...\n} enum Hint { AssetClaimer(Location), // more can be added\n} type NumVariants = /* Number of variants of the `Hint` enum */;","breadcrumbs":"RFC-0107: XCM Execution hints » Explanation","id":"654","title":"Explanation"},"655":{"body":"The SetHints instruction might be hard to benchmark, since we should look into the actual hints being set to know how much weight to attribute to it.","breadcrumbs":"RFC-0107: XCM Execution hints » Drawbacks","id":"655","title":"Drawbacks"},"656":{"body":"Hints are specified on a per-message basis, so they have to be specified at the beginning of a message. If they were to be specified at the end, hints like AssetClaimer would be useless if an error occurs beforehand and assets get trapped before ever reaching the hint. The instruction takes a bounded vector of hints so as to not force barriers to allow an arbitrary number of SetHint instructions.","breadcrumbs":"RFC-0107: XCM Execution hints » Testing, Security, and Privacy","id":"656","title":"Testing, Security, and Privacy"},"657":{"body":"","breadcrumbs":"RFC-0107: XCM Execution hints » Performance, Ergonomics, and Compatibility","id":"657","title":"Performance, Ergonomics, and Compatibility"},"658":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Performance","id":"658","title":"Performance"},"659":{"body":"The SetHints instruction provides a better integration with barriers. If we had to add one barrier for SetAssetClaimer and another for each new hint that's added, barriers would need to be changed all the time. Also, this instruction would make it simpler to write XCM programs. You only need to specify the hints you want in one single instruction at the top of your program.","breadcrumbs":"RFC-0107: XCM Execution hints » Ergonomics","id":"659","title":"Ergonomics"},"66":{"body":"Two ways: Discover collators via relay chain DHT and request from them: Preferred way, as it is less load on validators. Request from validators, which will serve on a best effort basis.","breadcrumbs":"RFC-0000: Feature Name Here » How do other parties get hold of the PVF?","id":"66","title":"How do other parties get hold of the PVF?"},"660":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Compatibility","id":"660","title":"Compatibility"},"661":{"body":"The previous RFC PR in the xcm-format repository before XCM RFCs moved to fellowship RFCs: https://github.com/polkadot-fellows/xcm-format/pull/59.","breadcrumbs":"RFC-0107: XCM Execution hints » Prior Art and References","id":"661","title":"Prior Art and References"},"662":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Unresolved Questions","id":"662","title":"Unresolved Questions"},"663":{"body":"None.","breadcrumbs":"RFC-0107: XCM Execution hints » Future Directions and Related Material","id":"663","title":"Future Directions and Related Material"},"664":{"body":"(source) Table of Contents RFC-0108: Remove XCM testnet NetworkIds Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 23 July 2024 Description Remove the NetworkIds for testnets Westend and Rococo Authors","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » RFC-0108: Remove XCM testnet NetworkIds","id":"664","title":"RFC-0108: Remove XCM testnet NetworkIds"},"665":{"body":"This RFC aims to remove the NetworkIds of Westend and Rococo, arguing that testnets shouldn't go in the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Summary","id":"665","title":"Summary"},"666":{"body":"We've already seen the plans to phase out Rococo and Paseo has appeared. Instead of constantly changing the testnets included in the language, we should favor specifying them via their genesis hash, using NetworkId::ByGenesis.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Motivation","id":"666","title":"Motivation"},"667":{"body":"Runtime devs Wallets dApps","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Stakeholders","id":"667","title":"Stakeholders"},"668":{"body":"Remove Westend and Rococo from the included NetworkIds in the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Explanation","id":"668","title":"Explanation"},"669":{"body":"This RFC will make it less convenient to specify a testnet, but not by a large amount.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Drawbacks","id":"669","title":"Drawbacks"},"67":{"body":"We covered how validators get hold of new code, but when can they prune old ones? In principle it is not an issue, if some validors prune code, because: We changed it so that a candidate is not deemed available if validators were not able to fetch the PVF. Backers can always fetch the PVF from collators as part of the collation fetching. But the majority of validators should always keep the latest code of any parachain and only prune the previous one, once the first candidate using the new code got finalized. This ensures that disputes will always be able to resolve.","breadcrumbs":"RFC-0000: Feature Name Here » Pruning","id":"67","title":"Pruning"},"670":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Testing, Security, and Privacy","id":"670","title":"Testing, Security, and Privacy"},"671":{"body":"","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Performance, Ergonomics, and Compatibility","id":"671","title":"Performance, Ergonomics, and Compatibility"},"672":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Performance","id":"672","title":"Performance"},"673":{"body":"It will very slightly reduce the ergonomics of testnet developers but improve the stability of the language.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Ergonomics","id":"673","title":"Ergonomics"},"674":{"body":"NetworkId::Rococo and NetworkId::Westend can just use NetworkId::ByGenesis, as can other testnets.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Compatibility","id":"674","title":"Compatibility"},"675":{"body":"A previous attempt to add NetworkId::Paseo: https://github.com/polkadot-fellows/xcm-format/pull/58.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Prior Art and References","id":"675","title":"Prior Art and References"},"676":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Unresolved Questions","id":"676","title":"Unresolved Questions"},"677":{"body":"None.","breadcrumbs":"RFC-0108: Remove XCM testnet NetworkIds » Future Directions and Related Material","id":"677","title":"Future Directions and Related Material"},"678":{"body":"(source) Table of Contents RFC-0122: Asset transfers can alias XCM origin on destination to original origin Summary Motivation Stakeholders Explanation Trust assumptions XCM InitiateAssetsTransfer instruction changes Example scenarios Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 01 Sep 2024. Description Single and Multi-hop asset transfers should be able to carry over original origin Authors Adrian Catangiu","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » RFC-0122: Asset transfers can alias XCM origin on destination to original origin","id":"678","title":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin"},"679":{"body":"XCM programs generated by the InitiateAssetTransfer instruction shall have the option to carry over the original origin all the way to the final destination. They shall do so by internally making use of AliasOrigin or ClearOrigin depending on given parameters. This allows asset transfers to retain their original origin even across multiple hops. Ecosystem chains would have to change their trusted aliasing rules to effectively make use of this feature.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Summary","id":"679","title":"Summary"},"68":{"body":"The major drawback of this solution is the same as any solution the moves work off-chain, it adds complexity to the node. E.g. nodes needing the PVF, need to store them separately, together with their own pruning strategy as well.","breadcrumbs":"RFC-0000: Feature Name Here » Drawbacks","id":"68","title":"Drawbacks"},"680":{"body":"Currently, all XCM asset transfer instructions ultimately clear the origin in the remote XCM message by use of the ClearOrigin instruction. This is done for security considerations to ensure that subsequent (user-controlled) instructions cannot command the authority of the sending chain. The problem with this approach is that it limits what can be achieved on remote chains through XCM. Most XCM operations require having an origin, and following any asset transfer the origin is lost, meaning not much can be done other than depositing the transferred assets to some local account or transferring them onward to another chain. For example, we cannot transfer some funds for buying execution, then do a Transact (all in the same XCM message). The above example is a basic, core building block for cross-chain interactions and we should support it. Transact XCM programs today require a two step process: And we want to be able to do it using a single XCM program.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Motivation","id":"680","title":"Motivation"},"681":{"body":"Runtime Users, Runtime Devs, wallets, cross-chain dApps.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Stakeholders","id":"681","title":"Stakeholders"},"682":{"body":"In the case of XCM programs going from source-chain directly to dest-chain without an intermediary hop, we can enable scenarios such as above by using the AliasOrigin instruction instead of the ClearOrigin instruction. Instead of clearing the source-chain origin, the destination chain shall attempt to alias source-chain to \"original origin\" on the source chain. Most common such origin aliasing would be X1(Parachain(source-chain)) -> X2(Parachain(source-chain), AccountId32(origin-account)) for the case of a single hop transfer where the initiator is a (signed/pure/proxy) account origin-account on source-chain. This is equivalent to using the DescendOrigin instruction in this case, but also usable in the multi hop case. This allows an actor on chain A to Transact on chain B without having to prefund its SA account on chain B, instead they can simply transfer the required fees in the same XCM program as the Transact. As long as the asset transfer has the same XCM route/hops as the rest of the program, this pattern of usage can be composed across multiple hops, to ultimately Transact on the final hop using the original origin on the source chain, effectively abstracting away any intermediary hops.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Explanation","id":"682","title":"Explanation"},"683":{"body":"The model described above works between chains that configure certain aliasing rules. Origin aliasing is highly customizable at the runtime level, so that chains can define coarse filters or granular pairs of (source, target) locations aliasing. This RFC suggests a coarse set of aliasing rules that chains can use for allowing the vast majority of Transact usecases in a \"one-click\" manner (single user signature), without practically lowering their security posture. Suggested Aliasing Rules: Any chain allows aliasing origin into a child location. Equivalent to DescendOrigin into an interior location. Parachains allow Asset Hub root location to alias into any other origin. The first rule is allowing use of AliasOrigin with same effect as doing a DescendOrigin, so it is absolutely not controversial. Now, the second rule as defined above in its most generic form might seem \"dangerous\" at first, but in practical terms if Asset Hub Root gets compromised and can access arbitrary sovereign accounts on Asset Hub and/or send arbitrary XCMs, the blast radius and potential damage to other chains is already so large that it is not relevantly impacted by this aliasing rule. A compromised system chain root would already be by itself an \"apocalypse\" scenario for the whole Polkadot Ecosystem. It's important noting that the aliasing rules above are a suggestion only, ultimately they are chain specific configuration. Therefore, each chain can tighten them to their own liking. For example, use stricter range of locations that Asset Hub can alias like: \"allow Asset Hub root to alias Ethereum locations\" - which enables support for Transact over the Ethereum Snowbridge (but doesn't support sibling parachain to Transact through Asset Hub), \"allow Asset Hub root to alias Kusama locations\" \"allow Asset Hub root to alias specific pallet or smart contract on Chain X\" Please note that Bridge Hub already does something similar today: Bridge Hub root is allowed/trusted to UniversalOrigin+DescendOrigin into any external location in order to impersonate/proxy external locations.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Trust assumptions","id":"683","title":"Trust assumptions"},"684":{"body":"A new parameter preserve_origin to be added to the InitiateAssetsTransfer XCM instruction that specifies if the original origin should be preserved or cleared. InitiateAssetsTransfer { destination: Location, assets: Vec, remote_fees: Option,\n+\tpreserve_origin: bool, remote_xcm: Xcm<()>,\n} This parameter is explicitly necessary because the instruction should be usable between any two chains regardless of their origin-aliasing trust relationship. Preserving the origin requires some level of trust, while clearing it works regardless of that relationship. Specifying preserve_origin: false will always work regardless of the configured alias filters of the involved chains.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » XCM InitiateAssetsTransfer instruction changes","id":"684","title":"XCM InitiateAssetsTransfer instruction changes"},"685":{"body":"Transact within the ecosytem: between two chains using an asset native to either one of them for paying for Transact, between two chains using an Asset Hub asset (e.g. USDT) for paying for Transact, Transact over Snowbridge (same for other bridges): user on Ethereum calls function in Parachain A on Polkadot, pays with ETH, user on ParaA on Polkdaot calls function on Ethereum, pays with ETH,","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Example scenarios","id":"685","title":"Example scenarios"},"686":{"body":"In terms of ergonomics and user experience, this support for combining an asset transfer with a subsequent action (like Transact) is a net positive. In terms of performance, and privacy, this is neutral with no changes. In terms of security, the feature by itself is also neutral because it allows preserve_origin: false usage for operating with no extra trust assumptions. When wanting to support preserving origin, chains need to configure secure origin aliasing filters. The one suggested in this RFC should be the right choice for the majority of chains, but each chain will ultimately choose depending on their business model and logic (e.g. chain does not plan to integrate with Asset Hub). It is up to the individual chains to configure accordingly.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Drawbacks","id":"686","title":"Drawbacks"},"687":{"body":"Barriers should now allow AliasOrigin, DescendOrigin or ClearOrigin. Normally, XCM program builders should audit their programs and eliminate assumptions of \"no origin\" on remote side of this instruction. In this case, the InitiateAssetsTransfer has not been released yet, it will be part of XCMv5, and we can make this change part of the same XCMv5 so that there isn't even the possibility of someone in the wild having built XCM programs using this instruction on those wrong assumptions. The working assumption going forward is that the origin on the remote side can either be cleared or it can be the local origin's reanchored location. This assumption is in line with the current behavior of remote XCM programs sent over using pallet_xcm::send. The existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear origin same as before for compatibility reasons.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Testing, Security, and Privacy","id":"687","title":"Testing, Security, and Privacy"},"688":{"body":"","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Performance, Ergonomics, and Compatibility","id":"688","title":"Performance, Ergonomics, and Compatibility"},"689":{"body":"No impact.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Performance","id":"689","title":"Performance"},"69":{"body":"Implementations adhering to this RFC, will respond to PVF requests with the actual PVF, if they have it. Requesters will persist received PVFs on disk for as long as they are replaced by a new one. Implementations must not be lazy here, if validators only fetched the PVF when needed, they can be prevented from participating in disputes. Validators should treat incoming requests for PVFs in general with rather low priority, but should prefer fetches from other validators over requests from random peers. Given that we are altering what set bits in the availability bitfields mean (not only chunk, but also PVF available), it is important to have enough validators upgraded, before we allow collators to make use of the new runtime upgrade mechanism. Otherwise we would risk disputes to not being able to succeed. This RFC has no impact on privacy.","breadcrumbs":"RFC-0000: Feature Name Here » Testing, Security, and Privacy","id":"69","title":"Testing, Security, and Privacy"},"690":{"body":"Improves ergonomics by allowing the local origin to operate on the remote chain even when the XCM program includes an asset transfer.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Ergonomics","id":"690","title":"Ergonomics"},"691":{"body":"At the executor-level this change is backwards and forwards compatible. Both types of programs can be executed on new and old versions of XCM with no changes in behavior. New version of the InitiateAssetsTransfer instruction acts same as before when used with preserve_origin: false. For using the new capabilities, the XCM builder has to verify that the involved chains have the required origin-aliasing filters configured and use some new version of Barriers aware of AliasOrigin as an allowed alternative to ClearOrigin. For compatibility reasons, this RFC proposes this mechanism be added as an enhancement to the yet unreleased InitiateAssetsTransfer instruction, thus eliminating possibilities of XCM logic breakages in the wild. Following the same logic, the existing DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport cross chain asset transfer instructions will not attempt to do origin aliasing and will always clear the origin same as before for compatibility reasons. Any one of DepositReserveAsset, InitiateReserveWithdraw and InitiateTeleport instructions can be replaced with a InitiateAssetsTransfer instruction with or without origin aliasing, thus providing a clean and clear upgrade path for opting-in this new feature.","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Compatibility","id":"691","title":"Compatibility"},"692":{"body":"RFC: InitiateAssetsTransfer for complex asset transfers RFC: Descend XCM origin instead of clearing it where possible","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Prior Art and References","id":"692","title":"Prior Art and References"},"693":{"body":"None","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Unresolved Questions","id":"693","title":"Unresolved Questions"},"694":{"body":"","breadcrumbs":"RFC-0122: Asset transfers can alias XCM origin on destination to original origin » Future Directions and Related Material","id":"694","title":"Future Directions and Related Material"},"695":{"body":"(source) Table of Contents RFC-0000: Validator Rewards Summary Motivation Stakeholders Logic Categories Collection Messages Rewards compoutation Strategies Explanation Backing Approvals Availability redistribution Tit-for-tat Concerns: Drawbacks, Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Synthetic parachain flag Start Date Date of initial proposal Description Rewards protocol for Polkadot validators Authors Jeff Burdges, ...","breadcrumbs":"RFC-0000: Validator Rewards » RFC-0000: Validator Rewards","id":"695","title":"RFC-0000: Validator Rewards"},"696":{"body":"An off-chain approximation protocol should assign rewards based upon the approvals and availability work done by validators. All validators track which approval votes they actually use, reporting the aggregate, after which an on-chain median computation gives a good approximation under byzantine assumptions. Approval checkers report aggregate information about which availability chunks they use too, but in availability we need a tit-for-tat game to enforce honesty, because approval committees could often bias results thanks to their small size.","breadcrumbs":"RFC-0000: Validator Rewards » Summary","id":"696","title":"Summary"},"697":{"body":"We want all polkadot subsystems be profitable for validataors, because otherwise operators might profit from running modified code. In particular, almost all rewards in Kusama/Polkadot should come from work done securing parachains, primarily approval checking, but also backing, availability, and support of XCMP. Among these task, our highest priorities must be approval checks, which ensure soundness, and sending availability chunks to approval checkers. We prove backers must be paid strictly less than approval checkers. At present though, validators' rewards have relatively little relationship to validators operating costs, in terms of bandwidth and CPU time. Worse, polkadot's scaling makes us particular vulnerable \"no-shows\" caused by validators skipping their approval checks. We're particularly concernned about hardware specks impact upon the number of parachain cores. We've requested relatively low spec machines so far, only four physical CPU cores, although some run even lower specs like only two physical CPU cores. Alone, rewards cannot fix our low speced validator problem, but rewards and outreach together should far more impact than either alone. In future, we'll further increase validator spec requirements, which directly improve polkadot's throughput, and which repeats this dynamic of purging underspeced nodes, except outreach becomes more important because de facto too many slow validators can \"out vote\" the faster ones","breadcrumbs":"RFC-0000: Validator Rewards » Motivation","id":"697","title":"Motivation"},"698":{"body":"We alter the validators rewards protocol, but with negligable impact upon rewards for honest validators who comply with hardware and bandwidth recommendations. We shall still reward participation in relay chain concensus of course, which de facto means block production but not finality, but these current reward levels shall wind up greatly reduced. Any validators who manipulate block rewards now could lose rewards here, simply because of rewards being shifted from block production to availability, but this sounds desirable. We've discussed roughly this rewards protocol in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF and https://github.com/paritytech/polkadot-sdk/issues/1811 as well as related topics like https://github.com/paritytech/polkadot-sdk/issues/5122","breadcrumbs":"RFC-0000: Validator Rewards » Stakeholders","id":"698","title":"Stakeholders"},"699":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Logic","id":"699","title":"Logic"},"7":{"body":"As the new instructions show, this RFC reframes the purpose of the Undefined variant of the AssetInstance enum. This RFC proposes to use the Undefined variant of a collection identified by an AssetId as a synonym of the collection itself. I.e., an asset Asset { id: , fun: Undefined } is considered an NFT representing the collection itself. As a singleton non-fungible instance is barely distinguishable from its collection, this convention shouldn't cause any problems. Thus, the AssetInstance docs must be updated accordingly in the implementations.","breadcrumbs":"RFC-0125: XCM Asset Metadata » Repurposing AssetInstance::Undefined","id":"7","title":"Repurposing AssetInstance::Undefined"},"70":{"body":"","breadcrumbs":"RFC-0000: Feature Name Here » Performance, Ergonomics, and Compatibility","id":"70","title":"Performance, Ergonomics, and Compatibility"},"700":{"body":"We alter the current rewards scheme by reducing to roughly these proportions of total rewards: 15-20% - Relay chain block production and uncle logic 5% - Rnything else related to relay chain finality, primarily beefy proving, but maybe other tasts exist. Any existing rewards for on-chain validity statements would only cover backers, so those rewards must be removed. We add roughly these proportions of total rewards covering parachain work: 70-75% - approval and backing validity checks, with the backing rewards being required to be less than approval rewards. 5-10% - Availability redistribution from availability providers to approval checkers. We do not reward for availability distribution from backers to availability providers.","breadcrumbs":"RFC-0000: Validator Rewards » Categories","id":"700","title":"Categories"},"701":{"body":"We track this data for each candidate during the approvals process: /// Our subjective record of out availability transfers for this candidate.\nCandidateRewards { /// Anyone who backed this parablock backers: [AuthorityId; NumBackers], /// Anyone who sent us chunks for this candidate downloaded_from: HashMap, /// Anyone to whome we sent chunks for this candidate uploaded_to: HashMap,\n} We no longer require this data during disputes. After we approve a relay chain block, then we collect all its CandidateRewards into an ApprovalsTally, with one ApprovalTallyRecord for each validator. In this, we compute approval_usages from the final run of the approvals loop, plus 0.8 for each backer. /// Our subjective record of what we used from, and provided to, all other validators on the finalized chain\npub struct ApprovalsTally(Vec); /// Our subjective record of what we used from, and provided to, all one other validators on the finalized chain\npub struct ApprovalTallyLine { /// Approvals by this validator which our approvals gadget used in marking candidates approved. approval_usages: u32, /// Availability chunks we downloaded from this validator for our approval checks we used. used_downloads: u32, /// Availability chunks we uploaded to this validator which whose approval checks we used. used_uploads: u32,\n} At finality we sum these ApprovalsTally for one for the whole epoch so far, into another ApprovalsTally. We can optionally sum them earlier at chain heads, but this requires mutablity.","breadcrumbs":"RFC-0000: Validator Rewards » Collection","id":"701","title":"Collection"},"702":{"body":"After the epoch is finalized, we share the first two lines of its ApprovalTally. /// Our subjective record of what we used from some other validator on the finalized chain\npub struct ApprovalTallyMessageLine { /// Approvals by this validator which our approvals gadget used in marking candidates approved. approval_usages: u32, /// Availability chunks we downloaded from this validator for our approval checks we used. used_downloads: u32,\n} /// Our subjective record of what we used from all other validators on the finalized chain\npub struct ApprovalsTallyMessage(Vec);","breadcrumbs":"RFC-0000: Validator Rewards » Messages","id":"702","title":"Messages"},"703":{"body":"We compute the approvals rewards by taking the median of the approval_usages fields for each validator across all validators ApprovalsTallyMessages. let mut approval_usages_medians = Vec::new(); for i in 0..num_validators { let mut v: Vec = approvals_tally_messages.iter().map(|atm| atm.0[i].approval_usages); v.sort(); approval_usages_medians.push(v[num_validators/2]);\n} Assuming more than 50% honersty, these median tell us how many approval votes form each validator We re-weight the used_downloads from the ith validator by their median times their expected f+1 chunks and divided by how many chunks downloads they claimed, and sum them #[cfg(offchain)]\nlet mut my_missing_uploads = my_approvals_tally.iter().map(|l| l.used_uploads).collect();\nlet mut reweighted_total_used_downloads = vec[0u64; num_validators];\nfor (mmu,atm) in my_missing_uploads.iter_mut().zip(approvals_tally_messages) { let d = atm.0.iter().map(|l| l.used_downloads).sum(); for i in 0..num_validators { let atm_from_i = approval_usages_medians[i] * (f+1) / d; #[cfg(offchain)] if i == me { mmu -= atm_from_i }; reweighted_total_used_downloads[i] += atm_from_i; }\n} We distribute rewards on-chain using approval_usages_medians and reweighted_total_used_downloads. Approval checkers could later change from who they download chunks using my_missing_uploads.","breadcrumbs":"RFC-0000: Validator Rewards » Rewards compoutation","id":"703","title":"Rewards compoutation"},"704":{"body":"In theory, validators could adopt whatever strategy they like to penalize validators who stiff them on availability redistribution rewards, except they should not stiff back, only choose other availability providers. We discuss one good strategy below, but initially this could go unimplemented.","breadcrumbs":"RFC-0000: Validator Rewards » Strategies","id":"704","title":"Strategies"},"705":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Explanation","id":"705","title":"Explanation"},"706":{"body":"Polkadot's efficency creates subtle liveness concerns: Anytime one node cannot perform one of its approval checks then Polkadot loses in expectation 3.25 approval checks, or 0.10833 parablocks. This makes back pressure essential. We cannot throttle approval checks securely either, so reactive off-chain back pressure only makes sense during or before the backing phase. In other words, if nodes feel overworked themselves, or perhaps beleive others to be, then they should drop backing checks, never approval checks. It follows backing work must be rewarded less well and less reliably than approvals, as otherwise validators could benefit from behavior that harms the network. We propose that one backing statement be rewarded at 80% of one approval statement, so backers earn only 80% of what approval checkers earn. We omit rewards for availability distribution, so backers spend more on bandwidth too. Approval checkers always fetch chunks first from backers though, so good backers earn roughly 7% there, meaning backing checks earn roughly 13% less than approval checks. We should lower this 80% if we ever increase availability redistribution rewards. Although imperfect, we believe this simplifies implementation, and provides robustness against mistakes elsewhere, including by governance mistakes, but incurs minimal risk. In principle, backer might not distribute systemic chunks, but approval checkers fetch systemic chunks from backers first anyways, so likely this yields negligable gains. As always we require that backers' rewards covers their operational costs plus some profit, but approval checks must be more profitable.","breadcrumbs":"RFC-0000: Validator Rewards » Backing","id":"706","title":"Backing"},"707":{"body":"In polkadot, all validators run an approval assignment loop for each candidate, in which the validator listens to other approval checkers assignments and approval statements/votes, with which it marks checkers no-show or done, and marks candidates approved. Also, this loop determines and announces validators' own approval checker assignments. Any validator should always conclude whatever approval checks it begins, but our approval assignment loop ignore some approval checks, either because they were announced too soon or because an earlier no-show delivered its approval vote before the final approval. We say a validator $u$ uses an approval vote by a validator $v$ on a candidate $c$ if the approval assignments loop by $u$ counted the vote by $v$ towards approving the candidate $c$. We should not rewards votes announced too soon, so we unavoidably omit rewards for some honest no-show replacements too. We expect the 80% discount for backing covers these losses, so approval checks remain more profitable than backing. We propose a simple approximate solution based upon computing medians across validators for used votes. In an epoch $e$, each validator $u$ counts of the number $\\alpha_{u,v}$ of votes they used from each validator $v$, including themselves. Any time a validator marks a candidate approved, they increment these counts appropriately. After epoch $e$'s last block gets finalized, all validators of epoch $e$ submit an approvals tally message ApprovalsTallyMessage that reveals their number $\\alpha_{u,v}$ of useful approvals they saw from each validator $v$ on candidates that became available in epoch $n$. We do not send $\\alpha_{u,u}$ for tit-for-tat reasons discussed below, not for bias concerns. We record these approvals tally messages on-chain. After some delay, we compute on-chain the median $\\alpha_v := \\textrm{median} { \\alpha_{u,v} : u }$ used approvals statements for each validator $v$. As discussed in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF we could compute these medians using the on-line algorithm if substrate had a nice priority queue. We never achieve true consensus on approval checkers and their approval votes. Yet, our approval assignment loop gives a rough concensus, under our Byzantine assumption and some synchrony assumption. It then follows that miss-reporting by malicious validators should not appreciably alter the median $\\alpha_v$ and hence rewards. We never tally used approval assignments to candidate equivocations or other forks. Any validator should always conclude whatever approval checks it begins, even on other forks, but we expect relay chain equivocations should be vanishingly rare, and sassafras should make forks uncommon.","breadcrumbs":"RFC-0000: Validator Rewards » Approvals","id":"707","title":"Approvals"},"708":{"body":"As approval checkers could easily perform useless checks, we shall reward availability providers for the availability chunks they provide that resulted in useful approval checks. We enforce honesty using a tit-for-tat mechanism because chunk transfers are inherently subjective. An approval checker reconstructs the full parachain block by downloading distinct $f+1$ chunks from other validators, where at most $f$ validators are byzantine, out of the $n \\ge 3 f + 1$ total validators. In downloading chunks, validators prefer the $f+1$ systemic chunks over the non-systemic chunks, and prefer fetching from validators who already voted valid, like backing checkers. It follows some validators should recieve credit for more than one chunk per candidate. We expect a validator $v$ has actually performed more approval checks $\\omega_v$ than the median $\\alpha_v$ for which they actually received credit. In fact, approval checkers even ignore some of their own approval checks, meaning $\\alpha_{v,v} \\le \\omega_v$ too. Alongside approvals count for epoch $e$, approval checker $v$ computes the counts $\\beta_{u,v}$ of the number of chunks they downloaded from each availability provider $u$, excluding themselves, for which they percieve the approval check turned out useful, meaning their own approval counts in $\\alpha_{v,v}$. Approval checkers publish $\\beta_{u,v}$ alongside $\\alpha_{u,v}$ in the approvals tally message ApprovalsTallyMessage. We originally proposed include the self availability usage $\\beta_{v,v}$ here, but this should not matter, and excluding simplifies the code. Symmetrically, availability provider $u$ computes the counts $\\gamma_{u,v}$ of the number of chunks they uploaded to each approval checker $v$, again including themselves, again for which they percieve the approval check turned out useful. Availability provider $u$ never reveal its $\\gamma_{u,v}$ however. At this point, $\\alpha_v$, $\\alpha_{v,v}$, and $\\alpha_{u,v}$ all potentially differ. We established consensus upon $\\alpha_v$ above however, with which we avoid approval checkers printing unearned availability provider rewards: After receiving \"all\" pairs $(\\alpha_{u,v},\\beta_{u,v})$, validator $w$ re-weights the $\\beta_{u,v}$ and their own $\\gamma_{w,v}$. $$ \\begin{aligned} \\beta\\prime_{w,v} &= {(f+1) \\alpha_v \\over \\sum_u \\beta_{u,v}} \\beta_{w,v} \\ \\gamma\\prime_{w,v} &= {(f+1) \\alpha_w \\over \\sum_v \\gamma_{w,v}} \\gamma_{w,v} \\ \\end{aligned} $$ At this point, we compute $\\beta\\prime_w = \\sum_v \\beta\\prime_{w,v}$ on-chain for each $w$ and reward $w$ proportionally.","breadcrumbs":"RFC-0000: Validator Rewards » Availability redistribution","id":"708","title":"Availability redistribution"},"709":{"body":"We employ a tit-for-tat strategy to punish validators who lie about from whome they obtain availability chunks. We only alter validators future choices in from whom they obtain availability chunks, and never punish by lying ourselves, so nothing here breaks polkadot, but not having roughly this strategy enables cheating. An availability provider $w$ defines $\\delta\\prime_{w,v} := \\gamma\\prime_{w,v} - \\beta\\prime_{w,v}$ to be the re-weighted number of chunks by which $v$ stiffed $w$. Now $w$ increments their cumulative stiffing perception $\\eta_{w,v}$ from $v$ by the value $\\delta\\prime_{w,v}$, so $\\eta_{w,v} \\mathrel{+}= \\delta\\prime_{w,v}$ In future, anytime $w$ seeks chunks in reconstruction $w$ skips $v$ proportional to $\\eta_{w,v} / \\sum_u \\eta_{w,u}$, with each skip reducing $\\eta_{w,u}$ by 1. We expect honest accedental availability stiffs have only small $\\delta\\prime_{w,v}$, so they clear out quickly, but intentional skips add up more quickly. We keep $\\gamma_{w,v}$ and $\\alpha_{u,u}$ secret so that approval checkers cannot really know others stiffing perceptions, although $\\alpha_{u,v}$ leaks some relevant information. We expect this secrecy keeps skips secret and thus prevents the tit-for-tat escalating beyond one round, which hopefully creates a desirable Nash equilibrium. We favor skiping systematic chunks to reduce reconstructon costs, so we face costs when skipping them. We could however fetch systematic chunks from availability providers as well as backers, or even other approval checkers, so this might not become problematic in practice.","breadcrumbs":"RFC-0000: Validator Rewards » Tit-for-tat","id":"709","title":"Tit-for-tat"},"71":{"body":"This proposal lightens the load on the relay chain and is thus in general beneficial for the performance of the network, this is achieved by the following: Code upgrades are still propagated to all validators, but only once, not twice (First statements, then via the containing relay chain block). Code upgrades are only communicated to validators and other nodes which are interested, not any full node as it has been before. Relay chain block space is preserved. Previously we could only do one runtime upgrade per relay chain block, occupying almost all of the blockspace. Signalling an upgrade no longer contains the upgrade, hence if we need to push back on an upgrade for whatever reason, no network bandwidth and core time gets wasted because of this.","breadcrumbs":"RFC-0000: Feature Name Here » Performance","id":"71","title":"Performance"},"710":{"body":"We do not pay backers individually for availability distribution per se. We could only do so by including this information into the availability bitfields, which complicates on-chain computation. Also, if one of the two backers does not distribute then the availability core should remain occupied longer, meaning the lazy backer loses some rewards too. It's likely future protocol improbvements change this, so we should monitor for lazy backers outside the rewards system. We discuss approvals being considered by the tit-for-tat in earlier drafts. An adversary who successfuly manipulates the rewards median votes would've alraedy violated polkadot's security assumptions though, which requires a hard fork and correcting the dot allocation. Incorrect report wrong approval_usages remain interesting statistics though. Adversarial validators could manipulates their availability votes though, even without being a supermajority. If they still download honestly, then this costs them more rewards than they earn. We do not prevent validators from preferentially obtaining their pieces from their friends though. We should analyze, or at least observe, the long-term consequences. A priori, whale nominator's validators could stiff validators but then rotate their validators quickly enough so that they never suffered being skipped back. We discuss several possible solution, and their difficulties, under \"Rob's nominator-wise skipping\" in https://hackmd.io/@rgbPIkIdTwSICPuAq67Jbw/S1fHcvXSF but overall less seems like more here. Also frequent validator rotation could be penalized elsewhere.","breadcrumbs":"RFC-0000: Validator Rewards » Concerns: Drawbacks, Testing, Security, and Privacy","id":"710","title":"Concerns: Drawbacks, Testing, Security, and Privacy"},"711":{"body":"We operate off-chain except for final rewards votes and median tallies. We expect lower overhead rewards protocols would lack information, thereby admitting easier cheating. Initially, we designed the ELVES approval gadget to allow on-chain operation, in part for rewards computation, but doing so looks expensive. Also, on-chain rewards computaiton remains only an approximation too, but could even be biased more easily than our off-chain protocol presented here. We alraedy teach validators about missed parachain blocks, but we'll teach approval checking more going forwards, because current efforts focus more upon backing. JAM's block exports should not complicate availability rewards, but could impact some alternative schemes.","breadcrumbs":"RFC-0000: Validator Rewards » Performance, Ergonomics, and Compatibility","id":"711","title":"Performance, Ergonomics, and Compatibility"},"712":{"body":"None","breadcrumbs":"RFC-0000: Validator Rewards » Prior Art and References","id":"712","title":"Prior Art and References"},"713":{"body":"Provide specific questions to discuss and address before the RFC is voted on by the Fellowship. This should include, for example, alternatives to aspects of the proposed design where the appropriate trade-off to make is unclear.","breadcrumbs":"RFC-0000: Validator Rewards » Unresolved Questions","id":"713","title":"Unresolved Questions"},"714":{"body":"","breadcrumbs":"RFC-0000: Validator Rewards » Future Directions and Related Material","id":"714","title":"Future Directions and Related Material"},"715":{"body":"Any rewards protocol could simply be \"out voted\" by too many slow validators: An increase the number of parachain cores increases more workload, but this creates no-shows if too few validators could handle this workload. We could add a synthetic parachain flag, only settable by governance, which treats no-shows as positive approval votes for that parachain, but without adding rewards. We should never enable this for real parachains, only for synthetic ones like gluttons. We should not enable the synthetic parachain flag long-term even for gluttonsm, because validators could easily modify their code. Yet, synthetic approval checks might enable pushing the hardware upgrades more agressively over the short-term.","breadcrumbs":"RFC-0000: Validator Rewards » Synthetic parachain flag","id":"715","title":"Synthetic parachain flag"},"716":{"body":"(source) Table of Contents RFC-0004: Remove the host-side runtime memory allocator Summary Motivation Stakeholders Explanation New host functions Other changes Drawbacks Prior Art Unresolved Questions Future Possibilities Start Date 2023-07-04 Description Update the runtime-host interface to no longer make use of a host-side allocator Authors Pierre Krieger","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » RFC-0004: Remove the host-side runtime memory allocator","id":"716","title":"RFC-0004: Remove the host-side runtime memory allocator"},"717":{"body":"Update the runtime-host interface to no longer make use of a host-side allocator.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Summary","id":"717","title":"Summary"},"718":{"body":"The heap allocation of the runtime is currently controlled by the host using a memory allocator on the host side. The API of many host functions consists in allocating a buffer. For example, when calling ext_hashing_twox_256_version_1, the host allocates a 32 bytes buffer using the host allocator, and returns a pointer to this buffer to the runtime. The runtime later has to call ext_allocator_free_version_1 on this pointer in order to free the buffer. Even though no benchmark has been done, it is pretty obvious that this design is very inefficient. To continue with the example of ext_hashing_twox_256_version_1, it would be more efficient to instead write the output hash to a buffer that was allocated by the runtime on its stack and passed by pointer to the function. Allocating a buffer on the stack in the worst case scenario simply consists in decreasing a number, and in the best case scenario is free. Doing so would save many Wasm memory reads and writes by the allocator, and would save a function call to ext_allocator_free_version_1. Furthermore, the existence of the host-side allocator has become questionable over time. It is implemented in a very naive way, and for determinism and backwards compatibility reasons it needs to be implemented exactly identically in every client implementation. Runtimes make substantial use of heap memory allocations, and each allocation needs to go twice through the runtime <-> host boundary (once for allocating and once for freeing). Moving the allocator to the runtime side, while it would increase the size of the runtime, would be a good idea. But before the host-side allocator can be deprecated, all the host functions that make use of it need to be updated to not use it.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Motivation","id":"718","title":"Motivation"},"719":{"body":"No attempt was made at convincing stakeholders.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Stakeholders","id":"719","title":"Stakeholders"},"72":{"body":"End users are only affected by better performance and more stable block times. Parachains will need to implement the introduced request/response protocol and adapt to the new signalling mechanism via an UMP message, instead of sending the code upgrade directly. For parachain operators we should emit events on initiated runtime upgrade and each block reporting the current counter and how many blocks to go until the upgrade gets passed to pre-checking. This is especially important for on-demand chains or bulk users not occupying a full core. Further more that behaviour of requiring multiple blocks to fully initiate a runtime upgrade needs to be well documented.","breadcrumbs":"RFC-0000: Feature Name Here » Ergonomics","id":"72","title":"Ergonomics"},"720":{"body":"","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Explanation","id":"720","title":"Explanation"},"721":{"body":"This section contains a list of new host functions to introduce. (func $ext_storage_read_version_2 (param $key i64) (param $value_out i64) (param $offset i32) (result i64))\n(func $ext_default_child_storage_read_version_2 (param $child_storage_key i64) (param $key i64) (param $value_out i64) (param $offset i32) (result i64)) The signature and behaviour of ext_storage_read_version_2 and ext_default_child_storage_read_version_2 is identical to their version 1 counterparts, but the return value has a different meaning. The new functions directly return the number of bytes that were written in the value_out buffer. If the entry doesn't exist, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in value_out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. The runtime execution stops with an error if value_out is outside of the range of the memory of the virtual machine, even if the size of the buffer is 0 or if the amount of data to write would be 0 bytes. (func $ext_storage_next_key_version_2 (param $key i64) (param $out i64) (return i32))\n(func $ext_default_child_storage_next_key_version_2 (param $child_storage_key i64) (param $key i64) (param $out i64) (return i32)) The behaviour of these functions is identical to their version 1 counterparts. Instead of allocating a buffer, writing the next key to it, and returning a pointer to it, the new version of these functions accepts an out parameter containing a pointer-size to the memory location where the host writes the output. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. These functions return the size, in bytes, of the next key, or 0 if there is no next key. If the size of the next key is larger than the buffer in out, the bytes of the key that fit the buffer are written to out and any extra byte that doesn't fit is discarded. Some notes: It is never possible for the next key to be an empty buffer, because an empty key has no preceding key. For this reason, a return value of 0 can unambiguously be used to indicate the lack of next key. The ext_storage_next_key_version_2 and ext_default_child_storage_next_key_version_2 are typically used in order to enumerate keys that starts with a certain prefix. Given that storage keys are constructed by concatenating hashes, the runtime is expected to know the size of the next key and can allocate a buffer that can fit said key. When the next key doesn't belong to the desired prefix, it might not fit the buffer, but given that the start of the key is written to the buffer anyway this can be detected in order to avoid calling the function a second time with a larger buffer. (func $ext_hashing_keccak_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_keccak_512_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_sha2_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_blake2_128_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_blake2_256_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_64_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_128_version_2 (param $data i64) (param $out i32))\n(func $ext_hashing_twox_256_version_2 (param $data i64) (param $out i32))\n(func $ext_trie_blake2_256_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_blake2_256_ordered_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_keccak_256_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_trie_keccak_256_ordered_root_version_3 (param $data i64) (param $version i32) (param $out i32))\n(func $ext_default_child_storage_root_version_3 (param $child_storage_key i64) (param $out i32))\n(func $ext_crypto_ed25519_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32))\n(func $ext_crypto_sr25519_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32) (return i32))\n(func $ext_crypto_ecdsa_generate_version_2 (param $key_type_id i32) (param $seed i64) (param $out i32) (return i32)) The behaviour of these functions is identical to their version 1 or version 2 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new version of these functions accepts an out parameter containing the memory location where the host writes the output. The output is always of a size known at compilation time. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. (func $ext_default_child_storage_root_version_3 (param $child_storage_key i64) (param $out i32))\n(func $ext_storage_root_version_3 (param $out i32)) The behaviour of these functions is identical to their version 1 and version 2 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new versions of these functions accepts an out parameter containing the memory location where the host writes the output. The output is always of a size known at compilation time. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. I have taken the liberty to take the version 1 of these functions as a base rather than the version 2, as a PPP deprecating the version 2 of these functions has previously been accepted: https://github.com/w3f/PPPs/pull/6 . (func $ext_storage_clear_prefix_version_3 (param $prefix i64) (param $limit i64) (param $removed_count_out i32) (return i32))\n(func $ext_default_child_storage_clear_prefix_version_3 (param $child_storage_key i64) (param $prefix i64) (param $limit i64) (param $removed_count_out i32) (return i32))\n(func $ext_default_child_storage_kill_version_4 (param $child_storage_key i64) (param $limit i64) (param $removed_count_out i32) (return i32)) The behaviour of these functions is identical to their version 2 and 3 counterparts. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the version 3 and 4 of these functions accepts a removed_count_out parameter containing the memory location to a 8 bytes buffer where the host writes the number of keys that were removed in little endian. The runtime execution stops with an error if removed_count_out is outside of the range of the memory of the virtual machine. The functions return 1 to indicate that there are keys remaining, and 0 to indicate that all keys have been removed. Note that there is an alternative proposal to add new host functions with the same names: https://github.com/w3f/PPPs/pull/7 . This alternative doesn't conflict with this one except for the version number. One proposal or the other will have to use versions 4 and 5 rather than 3 and 4. (func $ext_crypto_ed25519_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\n(func $ext_crypto_sr25519_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\nfunc $ext_crypto_ecdsa_sign_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i32))\n(func $ext_crypto_ecdsa_sign_prehashed_version_2 (param $key_type_id i32) (param $key i32) (param $msg i64) (param $out i32) (return i64)) The behaviour of these functions is identical to their version 1 counterparts. The new versions of these functions accept an out parameter containing the memory location where the host writes the signature. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. The signatures are always of a size known at compilation time. On success, these functions return 0. If the public key can't be found in the keystore, these functions return 1 and do not write anything to out. Note that the return value is 0 on success and 1 on failure, while the previous version of these functions write 1 on success (as it represents a SCALE-encoded Some) and 0 on failure (as it represents a SCALE-encoded None). Returning 0 on success and non-zero on failure is consistent with common practices in the C programming language and is less surprising than the opposite. (func $ext_crypto_secp256k1_ecdsa_recover_version_3 (param $sig i32) (param $msg i32) (param $out i32) (return i64))\n(func $ext_crypto_secp256k1_ecdsa_recover_compressed_version_3 (param $sig i32) (param $msg i32) (param $out i32) (return i64)) The behaviour of these functions is identical to their version 2 counterparts. The new versions of these functions accept an out parameter containing the memory location where the host writes the signature. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. The signatures are always of a size known at compilation time. On success, these functions return 0. On failure, these functions return a non-zero value and do not write anything to out. The non-zero value written on failure is: 1: incorrect value of R or S 2: incorrect value of V 3: invalid signature These values are equal to the values returned on error by the version 2 (see https://spec.polkadot.network/chap-host-api#defn-ecdsa-verify-error ), but incremented by 1 in order to reserve 0 for success. (func $ext_crypto_ed25519_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_ed25519_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32))\n(func $ext_crypto_sr25519_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_sr25519_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32))\n(func $ext_crypto_ecdsa_num_public_keys_version_1 (param $key_type_id i32) (return i32))\n(func $ext_crypto_ecdsa_public_key_version_2 (param $key_type_id i32) (param $key_index i32) (param $out i32)) The functions superceded the ext_crypto_ed25519_public_key_version_1, ext_crypto_sr25519_public_key_version_1, and ext_crypto_ecdsa_public_key_version_1 host functions. Instead of calling ext_crypto_ed25519_public_key_version_1 in order to obtain the list of all keys at once, the runtime should instead call ext_crypto_ed25519_num_public_keys_version_1 in order to obtain the number of public keys available, then ext_crypto_ed25519_public_key_version_2 repeatedly. The ext_crypto_ed25519_public_key_version_2 function writes the public key of the given key_index to the memory location designated by out. The key_index must be between 0 (included) and n (excluded), where n is the value returned by ext_crypto_ed25519_num_public_keys_version_1. Execution must trap if n is out of range. The same explanations apply for ext_crypto_sr25519_public_key_version_1 and ext_crypto_ecdsa_public_key_version_1. Host implementers should be aware that the list of public keys (including their ordering) must not change while the runtime is running. This is most likely done by copying the list of all available keys either at the start of the execution or the first time the list is accessed. (func $ext_offchain_http_request_start_version_2 (param $method i64) (param $uri i64) (param $meta i64) (result i32)) The behaviour of this function is identical to its version 1 counterpart. Instead of allocating a buffer, writing the request identifier in it, and returning a pointer to it, the version 2 of this function simply returns the newly-assigned identifier to the HTTP request. On failure, this function returns -1. An identifier of -1 is invalid and is reserved to indicate failure. (func $ext_offchain_http_request_write_body_version_2 (param $method i64) (param $uri i64) (param $meta i64) (result i32))\n(func $ext_offchain_http_response_read_body_version_2 (param $request_id i32) (param $buffer i64) (param $deadline i64) (result i64)) The behaviour of these functions is identical to their version 1 counterpart. Instead of allocating a buffer, writing two bytes in it, and returning a pointer to it, the new version of these functions simply indicates what happened: For ext_offchain_http_request_write_body_version_2, 0 on success. For ext_offchain_http_response_read_body_version_2, 0 or a non-zero number of bytes on success. -1 if the deadline was reached. -2 if there was an I/O error while processing the request. -3 if the identifier of the request is invalid. These values are equal to the values returned on error by the version 1 (see https://spec.polkadot.network/chap-host-api#defn-http-error ), but tweaked in order to reserve positive numbers for success. When it comes to ext_offchain_http_response_read_body_version_2, the host implementers must not read too much data at once in order to not create ambiguity in the returned value. Given that the size of the buffer is always inferior or equal to 4 GiB, this is not a problem. (func $ext_offchain_http_response_wait_version_2 (param $ids i64) (param $deadline i64) (param $out i32)) The behaviour of this function is identical to its version 1 counterpart. Instead of allocating a buffer, writing the output to it, and returning a pointer to it, the new version of this function accepts an out parameter containing the memory location where the host writes the output. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. The encoding of the response code is also modified compared to its version 1 counterpart and each response code now encodes to 4 little endian bytes as described below: 100-999: the request has finished with the given HTTP status code. -1 if the deadline was reached. -2 if there was an I/O error while processing the request. -3 if the identifier of the request is invalid. The buffer passed to out must always have a size of 4 * n where n is the number of elements in the ids. (func $ext_offchain_http_response_header_name_version_1 (param $request_id i32) (param $header_index i32) (param $out i64) (result i64))\n(func $ext_offchain_http_response_header_value_version_1 (param $request_id i32) (param $header_index i32) (param $out i64) (result i64)) These functions supercede the ext_offchain_http_response_headers_version_1 host function. Contrary to ext_offchain_http_response_headers_version_1, only one header indicated by header_index can be read at a time. Instead of calling ext_offchain_http_response_headers_version_1 once, the runtime should call ext_offchain_http_response_header_name_version_1 and ext_offchain_http_response_header_value_version_1 multiple times with an increasing header_index, until a value of -1 is returned. These functions accept an out parameter containing a pointer-size to the memory location where the header name or value should be written. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine, even if the function wouldn't write anything to out. These functions return the size, in bytes, of the header name or header value. If request doesn't exist or is in an invalid state (as documented for ext_offchain_http_response_headers_version_1) or the header_index is out of range, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. If the buffer in out is too small to fit the entire header name of value, only the bytes that fit are written and the rest are discarded. (func $ext_offchain_submit_transaction_version_2 (param $data i64) (return i32))\n(func $ext_offchain_http_request_add_header_version_2 (param $request_id i32) (param $name i64) (param $value i64) (result i32)) Instead of allocating a buffer, writing 1 or 0 in it, and returning a pointer to it, the version 2 of these functions return 0 or 1, where 0 indicates success and 1 indicates failure. The runtime must interpret any non-0 value as failure, but the client must always return 1 in case of failure. (func $ext_offchain_local_storage_read_version_1 (param $kind i32) (param $key i64) (param $value_out i64) (param $offset i32) (result i64)) This function supercedes the ext_offchain_local_storage_get_version_1 host function, and uses an API and logic similar to ext_storage_read_version_2. It reads the offchain local storage key indicated by kind and key starting at the byte indicated by offset, and writes the value to the pointer-size indicated by value_out. The function returns the number of bytes that were written in the value_out buffer. If the entry doesn't exist, a value of -1 is returned. Given that the host must never write more bytes than the size of the buffer in value_out, and that the size of this buffer is expressed as a 32 bits number, a 64bits value of -1 is not ambiguous. The runtime execution stops with an error if value_out is outside of the range of the memory of the virtual machine, even if the size of the buffer is 0 or if the amount of data to write would be 0 bytes. (func $ext_offchain_network_peer_id_version_1 (param $out i64)) This function writes the PeerId of the local node to the memory location indicated by out. A PeerId is always 38 bytes long. The runtime execution stops with an error if out is outside of the range of the memory of the virtual machine. (func $ext_input_size_version_1 (return i64))\n(func $ext_input_read_version_1 (param $offset i64) (param $out i64)) When a runtime function is called, the host uses the allocator to allocate memory within the runtime where to write some input data. These two new host functions provide an alternative way to access the input that doesn't make use of the allocator. The ext_input_size_version_1 host function returns the size in bytes of the input data. The ext_input_read_version_1 host function copies some data from the input data to the memory of the runtime. The offset parameter indicates the offset within the input data where to start copying, and must be inferior or equal to the value returned by ext_input_size_version_1. The out parameter is a pointer-size containing the buffer where to write to. The runtime execution stops with an error if offset is strictly superior to the size of the input data, or if out is outside of the range of the memory of the virtual machine, even if the amount of data to copy would be 0 bytes.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » New host functions","id":"721","title":"New host functions"},"722":{"body":"In addition to the new host functions, this RFC proposes two changes to the runtime-host interface: The following function signature is now also accepted for runtime entry points: (func (result i64)). Runtimes no longer need to expose a constant named __heap_base. All the host functions that are being superceded by new host functions are now considered deprecated and should no longer be used. The following other host functions are similarly also considered deprecated: ext_storage_get_version_1 ext_default_child_storage_get_version_1 ext_allocator_malloc_version_1 ext_allocator_free_version_1 ext_offchain_network_state_version_1","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Other changes","id":"722","title":"Other changes"},"723":{"body":"This RFC might be difficult to implement in Substrate due to the internal code design. It is not clear to the author of this RFC how difficult it would be.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Drawbacks","id":"723","title":"Drawbacks"},"724":{"body":"The API of these new functions was heavily inspired by API used by the C programming language.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Prior Art","id":"724","title":"Prior Art"},"725":{"body":"The changes in this RFC would need to be benchmarked. This involves implementing the RFC and measuring the speed difference. It is expected that most host functions are faster or equal speed to their deprecated counterparts, with the following exceptions: ext_input_size_version_1/ext_input_read_version_1 is inherently slower than obtaining a buffer with the entire data due to the two extra function calls and the extra copying. However, given that this only happens once per runtime call, the cost is expected to be negligible. The ext_crypto_*_public_keys, ext_offchain_network_state, and ext_offchain_http_* host functions are likely slightly slower than their deprecated counterparts, but given that they are used only in offchain workers this is acceptable. It is unclear how replacing ext_storage_get with ext_storage_read and ext_default_child_storage_get with ext_default_child_storage_read will impact performances. It is unclear how the changes to ext_storage_next_key and ext_default_child_storage_next_key will impact performances.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Unresolved Questions","id":"725","title":"Unresolved Questions"},"726":{"body":"After this RFC, we can remove from the source code of the host the allocator altogether in a future version, by removing support for all the deprecated host functions. This would remove the possibility to synchronize older blocks, which is probably controversial and requires a some preparations that are out of scope of this RFC.","breadcrumbs":"RFC-0004: Remove the host-side runtime memory allocator » Future Possibilities","id":"726","title":"Future Possibilities"},"727":{"body":"(source) Table of Contents RFC-0006: Dynamic Pricing for Bulk Coretime Sales Summary Motivation Requirements Stakeholders Explanation Overview Parameters Function Pseudo-code Properties of the Curve Example Configurations Drawbacks Prior Art and References Future Possibilities References Start Date July 09, 2023 Description A dynamic pricing model to adapt the regular price for bulk coretime sales Authors Tommi Enenkel (Alice und Bob) License MIT","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » RFC-0006: Dynamic Pricing for Bulk Coretime Sales","id":"727","title":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales"},"728":{"body":"This RFC proposes a dynamic pricing model for the sale of Bulk Coretime on the Polkadot UC. The proposed model updates the regular price of cores for each sale period, by taking into account the number of cores sold in the previous sale, as well as a limit of cores and a target number of cores sold. It ensures a minimum price and limits price growth to a maximum price increase factor, while also giving govenance control over the steepness of the price change curve. It allows governance to address challenges arising from changing market conditions and should offer predictable and controlled price adjustments. Accompanying visualizations are provided at [1].","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Summary","id":"728","title":"Summary"},"729":{"body":"RFC-1 proposes periodic Bulk Coretime Sales as a mechanism to sell continouos regions of blockspace (suggested to be 4 weeks in length). A number of Blockspace Regions (compare RFC-1 & RFC-3) are provided for sale to the Broker-Chain each period and shall be sold in a way that provides value-capture for the Polkadot network. The exact pricing mechanism is out of scope for RFC-1 and shall be provided by this RFC. A dynamic pricing model is needed. A limited number of Regions are offered for sale each period. The model needs to find the price for a period based on supply and demand of the previous period. The model shall give Coretime consumers predictability about upcoming price developments and confidence that Polkadot governance can adapt the pricing model to changing market conditions.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Motivation","id":"729","title":"Motivation"},"73":{"body":"We will continue to support the old mechanism for code upgrades for a while, but will start to impose stricter limits over time, with the number of registered parachains going up. With those limits in place parachains not migrating to the new scheme might be having a harder time upgrading and will miss more blocks. I guess we can be lenient for a while still, so the upgrade path for parachains should be rather smooth. In total the protocol changes we need are: For validators and collators: New request/response protocol for fetching PVF data from collators and validators. New UMP message type for signalling a runtime upgrade. Only for validators: New runtime API for determining to be enacted code upgrades. Different behaviour of bitfields (only sign a 1 bit, if validator has chunk + \"hot\" PVF). Altered behaviour in availability-distribution: Fetch missing PVFS.","breadcrumbs":"RFC-0000: Feature Name Here » Compatibility","id":"73","title":"Compatibility"},"730":{"body":"The solution SHOULD provide a dynamic pricing model that increases price with growing demand and reduces price with shrinking demand. The solution SHOULD have a slow rate of change for price if the number of Regions sold is close to a given sales target and increase the rate of change as the number of sales deviates from the target. The solution SHOULD provide the possibility to always have a minimum price per Region. The solution SHOULD provide a maximum factor of price increase should the limit of Regions sold per period be reached. The solution should allow governance to control the steepness of the price function","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Requirements","id":"730","title":"Requirements"},"731":{"body":"The primary stakeholders of this RFC are: Protocol researchers and evelopers Polkadot DOT token holders Polkadot parachains teams Brokers involved in the trade of Bulk Coretime","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Stakeholders","id":"731","title":"Stakeholders"},"732":{"body":"","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Explanation","id":"732","title":"Explanation"},"733":{"body":"The dynamic pricing model sets the new price based on supply and demand in the previous period. The model is a function of the number of Regions sold, piecewise-defined by two power functions. The left side ranges from 0 to the target. It represents situations where demand was lower than the target. The right side ranges from the target to limit. It represents situations where demand was higher than the target. The curve of the function forms a plateau around the target and then falls off to the left and rises up to the right. The shape of the plateau can be controlled via a scale factor for the left side and right side of the function respectively.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Overview","id":"733","title":"Overview"},"734":{"body":"From here on, we will also refer to Regions sold as 'cores' to stay congruent with RFC-1. Name Suggested Value Description Constraints BULK_LIMIT 45 The maximum number of cores being sold 0 < BULK_LIMIT BULK_TARGET 30 The target number of cores being sold 0 < BULK_TARGET <= BULK_LIMIT MIN_PRICE 1 The minimum price a core will always cost. 0 < MIN_PRICE MAX_PRICE_INCREASE_FACTOR 2 The maximum factor by which the price can change. 1 < MAX_PRICE_INCREASE_FACTOR SCALE_DOWN 2 The steepness of the left side of the function. 0 < SCALE_DOWN SCALE_UP 2 The steepness of the right side of the function. 0 < SCALE_UP","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Parameters","id":"734","title":"Parameters"},"735":{"body":"P(n) = \\begin{cases} (P_{\\text{old}} - P_{\\text{min}}) \\left(1 - \\left(\\frac{T - n}{T}\\right)^d\\right) + P_{\\text{min}} & \\text{if } n \\leq T \\\\ ((F - 1) \\cdot P_{\\text{old}} \\cdot \\left(\\frac{n - T}{L - T}\\right)^u) + P_{\\text{old}} & \\text{if } n > T \\end{cases} $P_{\\text{old}}$ is the old_price, the price of a core in the previous period. $P_{\\text{min}}$ is the MIN_PRICE, the minimum price a core will always cost. $F$ is the MAX_PRICE_INCREASE_FACTOR, the factor by which the price maximally can change from one period to another. $d$ is the SCALE_DOWN, the steepness of the left side of the function. $u$ is the SCALE_UP, the steepness of the right side of the function. $T$ is the BULK_TARGET, the target number of cores being sold. $L$ is the BULK_LIMIT, the maximum number of cores being sold. $n$ is cores_sold, the number of cores being sold. Left side The left side is a power function that describes an increasing concave downward curvature that approaches old_price. We realize this by using the form $y = a(1 - x^d)$, usually used as a downward sloping curve, but in our case flipped horizontally by letting the argument $x = \\frac{T-n}{T}$ decrease with $n$, doubly inversing the curve. This approach is chosen over a decaying exponential because it let's us a better control the shape of the plateau, especially allowing us to get a straight line by setting SCALE_DOWN to $1$. Ride side The right side is a power function of the form $y = a(x^u)$.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Function","id":"735","title":"Function"},"736":{"body":"NEW_PRICE := IF CORES_SOLD <= BULK_TARGET THEN (OLD_PRICE - MIN_PRICE) * (1 - ((BULK_TARGET - CORES_SOLD)^SCALE_DOWN / BULK_TARGET^SCALE_DOWN)) + MIN_PRICE\nELSE ((MAX_PRICE_INCREASE_FACTOR - 1) * OLD_PRICE * ((CORES_SOLD - BULK_TARGET)^SCALE_UP / (BULK_LIMIT - BULK_TARGET)^SCALE_UP)) + OLD_PRICE\nEND IF","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Pseudo-code","id":"736","title":"Pseudo-code"},"737":{"body":"Minimum Price We introduce MIN_PRICE to control the minimum price. The left side of the function shall be allowed to come close to 0 if cores sold approaches 0. The rationale is that if there are actually 0 cores sold, the previous sale price was too high and the price needs to adapt quickly. Price forms a plateau around the target If the number of cores is close to BULK_TARGET, less extreme price changes might be sensible. This ensures that a drop in sold cores or an increase doesn’t lead to immediate price changes, but rather slowly adapts. Only if more extreme changes in the number of sold cores occur, does the price slope increase. We introduce SCALE_DOWN and SCALE_UP to control for the steepness of the left and the right side of the function respectively. Max price increase factor We introduce MAX_PRICE_INCREASE_FACTOR as the factor that controls how much the price may increase from one period to another. Introducing this variable gives governance an additional control lever and avoids the necessity for a future runtime upgrade.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Properties of the Curve","id":"737","title":"Properties of the Curve"},"738":{"body":"Baseline This example proposes the baseline parameters. If not mentioned otherwise, other examples use these values. The minimum price of a core is 1 DOT, the price can double every 4 weeks. Price change around BULK_TARGET is dampened slightly. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 2\nSCALE_DOWN = 2\nSCALE_UP = 2\nOLD_PRICE = 1000 More aggressive pricing We might want to have a more aggressive price growth, allowing the price to triple every 4 weeks and have a linear increase in price on the right side. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 3\nSCALE_DOWN = 2\nSCALE_UP = 1\nOLD_PRICE = 1000 Conservative pricing to ensure quick corrections in an affluent market If governance considers the risk that a sudden surge in DOT price might price chains out from bulk coretime markets, it can ensure the model quickly reacts to a quick drop in demand, by setting 0 < SCALE_DOWN < 1 and setting the max price increase factor more conservatively. BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 1.5\nSCALE_DOWN = 0.5\nSCALE_UP = 2\nOLD_PRICE = 1000 Linear pricing By setting the scaling factors to 1 and potentially adapting the max price increase, we can achieve a linear function BULK_TARGET = 30\nBULK_LIMIT = 45\nMIN_PRICE = 1\nMAX_PRICE_INCREASE_FACTOR = 1.5\nSCALE_DOWN = 1\nSCALE_UP = 1\nOLD_PRICE = 1000","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Example Configurations","id":"738","title":"Example Configurations"},"739":{"body":"None at present.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Drawbacks","id":"739","title":"Drawbacks"},"74":{"body":"Off-chain runtime upgrades have been discussed before, the architecture described here is simpler though as it piggybacks on already existing features, namely: availability-distribution: No separate I have code messages anymore. Existing pre-checking. https://github.com/paritytech/polkadot-sdk/issues/971","breadcrumbs":"RFC-0000: Feature Name Here » Prior Art and References","id":"74","title":"Prior Art and References"},"740":{"body":"This pricing model is based on the requirements from the basic linear solution proposed in RFC-1, which is a simple dynamic pricing model and only used as proof. The present model adds additional considerations to make the model more adaptable under real conditions.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Prior Art and References","id":"740","title":"Prior Art and References"},"741":{"body":"This RFC, if accepted, shall be implemented in conjunction with RFC-1.","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » Future Possibilities","id":"741","title":"Future Possibilities"},"742":{"body":"[1] Polkadot forum post with visualizations: Dynamic Pricing for Bulk Coretime Sales","breadcrumbs":"RFC-0006: Dynamic Pricing for Bulk Coretime Sales » References","id":"742","title":"References"},"743":{"body":"(source) Table of Contents RFC-0009: Improved light client requests networking protocol Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Future Directions and Related Material Start Date 2023-07-19 Description Modify the networking storage read requests to solve some problems with the existing one Authors Pierre Krieger","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » RFC-0009: Improved light client requests networking protocol","id":"743","title":"RFC-0009: Improved light client requests networking protocol"},"744":{"body":"Improve the networking messages that query storage items from the remote, in order to reduce the bandwidth usage and number of round trips of light clients.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Summary","id":"744","title":"Summary"},"745":{"body":"Clients on the Polkadot peer-to-peer network can be divided into two categories: full nodes and light clients. So-called full nodes are nodes that store the content of the chain locally on their disk, while light clients are nodes that don't. In order to access for example the balance of an account, a full node can do a disk read, while a light client needs to send a network message to a full node and wait for the full node to reply with the desired value. This reply is in the form of a Merkle proof, which makes it possible for the light client to verify the exactness of the value. Unfortunately, this network protocol is suffering from some issues: It is not possible for the querier to check whether a key exists in the storage of the chain except by querying the value of that key. The reply will thus include the value of the key, only for that value to be discarded by the querier that isn't interested by it. This is a waste of bandwidth. It is not possible for the querier to know whether a value in the storage of the chain has been modified between two blocks except by querying this value for both blocks and comparing them. Only a few storage values get modified in a block, and thus most of the time the comparison will be equal. This leads to a waste of bandwidth as the values have to be transferred. While it is possible to ask for multiple specific storage keys at the same time, it is not possible to ask for a list of keys that start with a certain prefix. Due to the way FRAME works, storage keys are grouped by \"prefix\", for example all account balances start with the same prefix. It is thus a common necessity for a light client to obtain the list of all keys (and possibly their values) that start with a specific prefix. This is currently not possible except by performing multiple queries serially that \"walk down\" the trie. Once Polkadot and Kusama will have transitioned to state_version = 1, which modifies the format of the trie entries, it will be possible to generate Merkle proofs that contain only the hashes of values in the storage. Thanks to this, it is already possible to prove the existence of a key without sending its entire value (only its hash), or to prove that a value has changed or not between two blocks (by sending just their hashes). Thus, the only reason why aforementioned issues exist is because the existing networking messages don't give the possibility for the querier to query this. This is what this proposal aims at fixing.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Motivation","id":"745","title":"Motivation"},"746":{"body":"This is the continuation of https://github.com/w3f/PPPs/pull/10, which itself is the continuation of https://github.com/w3f/PPPs/pull/5.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Stakeholders","id":"746","title":"Stakeholders"},"747":{"body":"The protobuf schema of the networking protocol can be found here: https://github.com/paritytech/substrate/blob/5b6519a7ff4a2d3cc424d78bc4830688f3b184c0/client/network/light/src/schema/light.v1.proto The proposal is to modify this protocol in this way: @@ -11,6 +11,7 @@ message Request { RemoteReadRequest remote_read_request = 2; RemoteReadChildRequest remote_read_child_request = 4; // Note: ids 3 and 5 were used in the past. It would be preferable to not re-use them.\n+ RemoteReadRequestV2 remote_read_request_v2 = 6; } } @@ -48,6 +49,21 @@ message RemoteReadRequest { repeated bytes keys = 3; } +message RemoteReadRequestV2 {\n+ required bytes block = 1;\n+ optional ChildTrieInfo child_trie_info = 2; // Read from the main trie if missing.\n+ repeated Key keys = 3;\n+ optional bytes onlyKeysAfter = 4;\n+ optional bool onlyKeysAfterIgnoreLastNibble = 5;\n+}\n+\n+message ChildTrieInfo {\n+ enum ChildTrieNamespace {\n+ DEFAULT = 1;\n+ }\n+\n+ required bytes hash = 1;\n+ required ChildTrieNamespace namespace = 2;\n+}\n+ // Remote read response. message RemoteReadResponse { // Read proof. If missing, indicates that the remote couldn't answer, for example because\n@@ -65,3 +81,8 @@ message RemoteReadChildRequest { // Storage keys. repeated bytes keys = 6; }\n+\n+message Key {\n+ required bytes key = 1;\n+ optional bool skipValue = 2; // Defaults to `false` if missing\n+ optional bool includeDescendants = 3; // Defaults to `false` if missing\n+} Note that the field names aren't very important as they are not sent over the wire. They can be changed at any time without any consequence. I would invite people to not discuss these field names as they are implementation details. This diff adds a new type of request (RemoteReadRequestV2). The new child_trie_info field in the request makes it possible to specify which trie is concerned by the request. The current networking protocol uses two different structs (RemoteReadRequest and RemoteReadChildRequest) for main trie and child trie queries, while this new request would make it possible to query either. This change doesn't fix any of the issues mentioned in the previous section, but is a side change that has been done for simplicity. An alternative could have been to specify the child_trie_info for each individual Key. However this would make it necessary to send the child trie hash many times over the network, which leads to a waste of bandwidth, and in my opinion makes things more complicated for no actual gain. If a querier would like to access more than one trie at the same time, it is always possible to send one query per trie. If skipValue is true for a Key, then the value associated with this key isn't important to the querier, and the replier is encouraged to replace the value with its hash provided that the storage item has a state_version equal to 1. If the storage value has a state_version equal to 0, then the optimization isn't possible and the replier should behave as if skipValue was false. If includeDescendants is true for a Key, then the replier must also include in the proof all keys that are descendant of the given key (in other words, its children, children of children, children of children of children, etc.). It must do so even if key itself doesn't have any storage value associated to it. The values of all of these descendants are replaced with their hashes if skipValue is true, similarly to key itself. The optional onlyKeysAfter and onlyKeysAfterIgnoreLastNibble fields can provide a lower bound for the keys contained in the proof. The responder must not include in its proof any node whose key is strictly inferior to the value in onlyKeysAfter. If onlyKeysAfterIgnoreLastNibble is provided, then the last 4 bits for onlyKeysAfter must be ignored. This makes it possible to represent a trie branch node that doesn't have an even number of nibbles. If no onlyKeysAfter is provided, it is equivalent to being empty, meaning that the response must start with the root node of the trie. If onlyKeysAfterIgnoreLastNibble is missing, it is equivalent to false. If onlyKeysAfterIgnoreLastNibble is true and onlyKeysAfter is missing or empty, then the request is invalid. For the purpose of this networking protocol, it should be considered as if the main trie contained an entry for each default child trie whose key is concat(\":child_storage:default:\", child_trie_hash) and whose value is equal to the trie root hash of that default child trie. This behavior is consistent with what the host functions observe when querying the storage. This behavior is present in the existing networking protocol, in other words this proposal doesn't change anything to the situation, but it is worth mentioning. Also note that child tries aren't considered as descendants of the main trie when it comes to the includeDescendants flag. In other words, if the request concerns the main trie, no content coming from child tries is ever sent back. This protocol keeps the same maximum response size limit as currently exists (16 MiB). It is not possible for the querier to know in advance whether its query will lead to a reply that exceeds the maximum size. If the reply is too large, the replier should send back only a limited number (but at least one) of requested items in the proof. The querier should then send additional requests for the rest of the items. A response containing none of the requested items is invalid. The server is allowed to silently discard some keys of the request if it judges that the number of requested keys is too high. This is in line with the fact that the server might truncate the response.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Explanation","id":"747","title":"Explanation"},"748":{"body":"This proposal doesn't handle one specific situation: what if a proof containing a single specific item would exceed the response size limit? For example, if the response size limit was 1 MiB, querying the runtime code (which is typically 1.0 to 1.5 MiB) would be impossible as it's impossible to generate a proof less than 1 MiB. The response size limit is currently 16 MiB, meaning that no single storage item must exceed 16 MiB. Unfortunately, because it's impossible to verify a Merkle proof before having received it entirely, parsing the proof in a streaming way is also not possible. A way to solve this issue would be to Merkle-ize large storage items, so that a proof could include only a portion of a large storage item. Since this would require a change to the trie format, it is not realistically feasible in a short time frame.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Drawbacks","id":"748","title":"Drawbacks"},"749":{"body":"The main security consideration concerns the size of replies and the resources necessary to generate them. It is for example easily possible to ask for all keys and values of the chain, which would take a very long time to generate. Since responses to this networking protocol have a maximum size, the replier should truncate proofs that would lead to the response being too large. Note that it is already possible to send a query that would lead to a very large reply with the existing network protocol. The only thing that this proposal changes is that it would make it less complicated to perform such an attack. Implementers of the replier side should be careful to detect early on when a reply would exceed the maximum reply size, rather than inconditionally generate a reply, as this could take a very large amount of CPU, disk I/O, and memory. Existing implementations might currently be accidentally protected from such an attack thanks to the fact that requests have a maximum size, and thus that the list of keys in the query was bounded. After this proposal, this accidental protection would no longer exist. Malicious server nodes might truncate Merkle proofs even when they don't strictly need to, and it is not possible for the client to (easily) detect this situation. However, malicious server nodes can already do undesirable things such as throttle down their upload bandwidth or simply not respond. There is no need to handle unnecessarily truncated Merkle proofs any differently than a server simply not answering the request.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Testing, Security, and Privacy","id":"749","title":"Testing, Security, and Privacy"},"75":{"body":"What about the initial runtime, shall we make that off-chain as well? Good news, at least after the first upgrade, no code will be stored on chain any more, this means that we also have to redefine the storage deposit now. We no longer charge for chain storage, but validator disk storage -> Should be cheaper. Solution to this: Not only store the hash on chain, but also the size of the data. Then define a price per byte and charge that, but: how do we charge - I guess deposit has to be provided via other means, runtime upgrade fails if not provided. how do we signal to the chain that the code is too large for it to reject the upgrade? Easy: Make available and vote nay in pre-checking. TODO: Fully resolve these questions and incorporate in RFC text.","breadcrumbs":"RFC-0000: Feature Name Here » Unresolved Questions","id":"75","title":"Unresolved Questions"},"750":{"body":"","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Performance, Ergonomics, and Compatibility","id":"750","title":"Performance, Ergonomics, and Compatibility"},"751":{"body":"It is unclear to the author of the RFC what the performance implications are. Servers are supposed to have limits to the amount of resources they use to respond to requests, and as such the worst that can happen is that light client requests become a bit slower than they currently are.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Performance","id":"751","title":"Performance"},"752":{"body":"Irrelevant.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Ergonomics","id":"752","title":"Ergonomics"},"753":{"body":"The prior networking protocol is maintained for now. The older version of this protocol could get removed in a long time.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Compatibility","id":"753","title":"Compatibility"},"754":{"body":"None. This RFC is a clean-up of an existing mechanism.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Prior Art and References","id":"754","title":"Prior Art and References"},"755":{"body":"None","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Unresolved Questions","id":"755","title":"Unresolved Questions"},"756":{"body":"The current networking protocol could be deprecated in a long time. Additionally, the current \"state requests\" protocol (used for warp syncing) could also be deprecated in favor of this one.","breadcrumbs":"RFC-0009: Improved light client requests networking protocol » Future Directions and Related Material","id":"756","title":"Future Directions and Related Material"},"757":{"body":"(source) Table of Contents RFC-0015: Market Design Revisit Summary Motivation Stakeholders Explanation Bulk Markets Benefits of this system Further Discussion Points Drawbacks Prior Art and References Unresolved Questions Start Date 05.08.2023 Description This RFC refines the previously proposed mechanisms involving the various Coretime markets and presents an integrated framework for harmonious interaction between all markets. Authors Jonas Gehrlein","breadcrumbs":"RFC-0015: Market Design Revisit » RFC-0015: Market Design Revisit","id":"757","title":"RFC-0015: Market Design Revisit"},"758":{"body":"This document is a proposal for restructuring the bulk markets in the Polkadot UC's coretime allocation system to improve efficiency and fairness. The proposal suggests separating the BULK_PERIOD into MARKET_PERIOD and RENEWAL_PERIOD, allowing for a market-driven price discovery through a clearing price Dutch auction during the MARKET_PERIOD followed by renewal offers at the MARKET_PRICE during the RENEWAL_PERIOD. The new system ensures synchronicity between renewal and market prices, fairness among all current tenants, and efficient price discovery, while preserving price caps to provide security for current tenants. It seeks to start a discussion about the possibility of long-term leases.","breadcrumbs":"RFC-0015: Market Design Revisit » Summary","id":"758","title":"Summary"},"759":{"body":"While the initial RFC-1 has provided a robust framework for Coretime allocation within the Polkadot UC, this proposal builds upon its strengths and uses many provided building blocks to address some areas that could be further improved. In particular, this proposal introduces the following changes: It introduces a RESERVE_PRICE that anchors all markets, promoting price synchronicity within the Bulk markets (flexible + renewals). This reduces complexity. This makes sure all consumers pay a closely correlated price for coretime within a BULK_PERIOD. It reverses the order of the market and renewal phase. This allows to fine-tune the price through market forces. It exposes the renewal prices, while still being beneficial for longterm tenants, more to market forces. It removes the LeadIn period and introduces a (from the perspective of the coretime systemchain) passive Settlement Phase, that allows the secondary market to exert it's force. The premise of this proposal is to reduce complexity by introducing a common price (that develops releative to capacity consumption of Polkadot UC), while still allowing for market forces to add efficiency. Longterm lease owners still receive priority IF they can pay (close to) the market price. This prevents a situation where the renewal price significantly diverges from renewal prices which allows for core captures. While maximum price increase certainty might seem contradictory to efficient price discovery, the proposed model aims to balance these elements, utilizing market forces to determine the price and allocate cores effectively within certain bounds. It must be stated, that potential price increases remain predictable (in the worst-case) but could be higher than in the originally proposed design. The argument remains, however, that we need to allow market forces to affect all prices for an efficient Coretime pricing and allocation. Ultimately, this the framework proposed here adheres to all requirements stated in RFC-1.","breadcrumbs":"RFC-0015: Market Design Revisit » Motivation","id":"759","title":"Motivation"},"76":{"body":"","breadcrumbs":"RFC-0000: Feature Name Here » Future Directions and Related Material","id":"76","title":"Future Directions and Related Material"},"760":{"body":"Primary stakeholder sets are: Protocol researchers and developers, largely represented by the Polkadot Fellowship and Parity Technologies' Engineering division. Polkadot Parachain teams both present and future, and their users. Polkadot DOT token holders.","breadcrumbs":"RFC-0015: Market Design Revisit » Stakeholders","id":"760","title":"Stakeholders"},"761":{"body":"","breadcrumbs":"RFC-0015: Market Design Revisit » Explanation","id":"761","title":"Explanation"},"762":{"body":"The BULK_PERIOD has been restructured into two primary segments: the MARKET_PERIOD and RENEWAL_PERIOD, along with an auxiliary SETTLEMENT_PERIOD. This latter period doesn't necessitate any actions from the coretime system chain, but it facilitates a more efficient allocation of coretime in secondary markets. A significant departure from the original proposal lies in the timing of renewals, which now occur post-market phase. This adjustment aims to harmonize renewal prices with their market counterparts, ensuring a more consistent and equitable pricing model. Market Period (14 days) During the market period, core sales are conducted through a well-established clearing price Dutch auction that features a RESERVE_PRICE. The price initiates at a premium, designated as PRICE_PREMIUM (for instance, 30%) and descends linearly to the RESERVE_PRICE throughout the duration of the MARKET_PERIOD. Each bidder is expected to submit both their desired price and the quantity (that is, the amount of Coretime) they wish to purchase. To secure these acquisitions, bidders must make a deposit equivalent to their bid multiplied by the chosen quantity, in DOT. The market achieves resolution once all quantities have been sold, or the RESERVE_PRICE has been reached. This situation leads to determining the MARKET_PRICE either by the lowest bid that was successful in clearing the entire market or by the RESERVE_PRICE. This mechanism yields a uniform price, shaped by market forces (refer to the following discussion for an explanation of its benefits). In other words, all buyers pay the same price (per unit of Coretime). Further down the benefits of this variant of a Dutch auction is discussed. Note: In cases where some cores remain unsold in the market, all buyers are obligated to pay the RESERVE_PRICE. Renewal Period (7 days) As the RENEWAL_PERIOD commences, all current tenants are granted the opportunity to renew their cores at a slight discount of MARKET_PRICE * RENEWAL_DISCOUNT (for instance, 10%). This provision affords marginal benefits to existing tenants, balancing out the non-transferability aspect of renewals. At the end of the period, all available cores are allocated to the current tenants who have opted for renewal and the participants who placed bids during the market period. If the demand for cores exceeds supply, the cores left unclaimed from renewals may be awarded to bidders who placed their bids early in the auction, thereby subtly incentivizing early participation. If the supply exceeds the demand, all unsold cores are transferred to the Instantanous Market. Reserve Price Adjustment After all cores are allocated, the RESERVE_PRICE is adjusted following the process described in RFC-1 and serves as baseline price in the next BULK_PERIOD. Note: The particular price curve is outside the scope of the proposal. The MARKET_PRICE (as a function of RESERVE_PRICE), however, is able to capture higher demand very well while being capped downwards. That means, the curve that adjusts the RESERVE_PRICE should be more sensitive to undercapacity. Price Predictability Tasks that are in the \"renewal-pipeline\" can determine the upper bound for the price they will pay in any future period. The main driver of any price increase over time is the adjustment of the RESERVE_PRICE, that occurs at the end of each BULK_PERIOD after determining the capacity fillment of Polkadot UC. To calculate the maximum price in some future period, a task could assume maximum capacity in all upcoming periods and track the resulting price increase of RESERVE_PRICE. In the final period, that price can get a maximum premium of PRICE_PREMIUM and after deducting a potential RENEWAL_DISCOUNT, the maximum price can be determined. Settlement Period (7 days) During the settlement period, participants have ample time to trade Coretime on secondary markets before the onset of the next BULK_PERIOD. This allows for trading with full Coretime availability. Trading transferrable Coretime naturally continues during each BULK_PERIOD, albeit with cores already in use.","breadcrumbs":"RFC-0015: Market Design Revisit » Bulk Markets","id":"762","title":"Bulk Markets"},"763":{"body":"The introduction of a single price, the RESERVE_PRICE, provides an anchor for all Coretime markets. This is a preventative measure against the possible divergence and mismatch of prices, which could inadvertently lead to a situation where existing tenants secure cores at significantly below-market rates. With a more market-responsive pricing system, we can achieve a more efficient price discovery process. Any price increases will be less arbitrary and more dynamic. The ideal strategy for existing tenants is to maintain passivity, i.e., refrain from active market participation and simply accept the offer presented to them during the renewal phase. This approach lessens the organizational overhead for long-term projects. In the two-week market phase, the maximum price increase is known well in advance, providing ample time for tenants to secure necessary funds to meet the potential price escalation. All existing tenants pay an equal amount for Coretime, reflecting our intent to price the Coretime itself and not the relative timing of individual projects. Discussion: Clearing Price Dutch Auctions Having all bidders pay the market clearing price offers some benefits and disadvantages. Advantages: Fairness : All bidders pay the same price. Active participation : Because bidders are protected from overbidding (winner's curse), they are more likely to engage and reveal their true valuations. Simplicity : A single price is easier to work with for pricing renewals later. Truthfulness : There is no need to try to game the market by waiting with bidding. Bidders can just bid their valuations. Disadvantages: (Potentially) Lower Revenue : While the theory predicts revenue-equivalence between a uniform price and pay-as-bid type of auction, slightly lower revenue for the former type is observed empirically. Arguably, revenue maximization (i.e., squeezing out the maximum willingness to pay from bidders) is not the priority for Polkadot UC. Instead, it is interested in efficient allocation and the other benefits illustrated above. (Technical) Complexity : Instead of making a final purchase within the auction, the bid is only a deposit. Some refunds might happen after the auction is finished. This might pose additional challenges from the technical side (e.g., storage requirements).","breadcrumbs":"RFC-0015: Market Design Revisit » Benefits of this system","id":"763","title":"Benefits of this system"},"764":{"body":"Long-term Coretime : The Polkadot UC is undergoing a transition from two-year leases without an instantaneous market to a model encompassing instantaneous and one-month leases. This shift seems to pivot from one extreme to another. While the introduction of short-term leases, both instantaneous and for one month, is a constructive move to lower barriers to entry and promote experimentation, it seems to be the case that established projects might benefit from more extended lease options. We could consider offering another product, such as a six-month Coretime lease, using the same mechanism described herein. Although the majority of leases would still be sold on a one-month basis, the addition of this option would enhance market efficiency as it would strengthen the impact of a secondary market .","breadcrumbs":"RFC-0015: Market Design Revisit » Further Discussion Points","id":"764","title":"Further Discussion Points"},"765":{"body":"There are trade-offs that arise from this proposal, compared to the initial model. The most notable one is that here, I prioritize requirement 6 over requirement 2. The price, in the very \"worst-case\" (meaning a huge explosion in demand for coretime) could lead to a much larger increase of prices in Coretime. From an economic perspective, this (rare edgecase) would also mean that we'd vastly underprice Coretime in the original model, leading to highly inefficient allocations.","breadcrumbs":"RFC-0015: Market Design Revisit » Drawbacks","id":"765","title":"Drawbacks"},"766":{"body":"This RFC builds extensively on the available ideas put forward in RFC-1 . Additionally, I want to express a special thanks to Samuel Haefner and Shahar Dobzinski for fruitful discussions and helping me structure my thoughts.","breadcrumbs":"RFC-0015: Market Design Revisit » Prior Art and References","id":"766","title":"Prior Art and References"},"767":{"body":"The technical feasability needs to be assessed.","breadcrumbs":"RFC-0015: Market Design Revisit » Unresolved Questions","id":"767","title":"Unresolved Questions"},"768":{"body":"(source) Table of Contents RFC-34: XCM Absolute Location Account Derivation Summary Motivation Stakeholders Explanation Drawbacks Testing, Security, and Privacy Performance, Ergonomics, and Compatibility Performance Ergonomics Compatibility Prior Art and References Unresolved Questions Start Date 05 October 2023 Description XCM Absolute Location Account Derivation Authors Gabriel Facco de Arruda","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » RFC-34: XCM Absolute Location Account Derivation","id":"768","title":"RFC-34: XCM Absolute Location Account Derivation"},"769":{"body":"This RFC proposes changes that enable the use of absolute locations in AccountId derivations, which allows protocols built using XCM to have static account derivations in any runtime, regardless of its position in the family hierarchy.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Summary","id":"769","title":"Summary"},"77":{"body":"By no longer having code upgrade go through the relay chain, occupying a full relay chain block, the impact on other parachains is already greatly reduced, if we make distribution and PVF pre-checking low-priority processes on validators. The only thing attackers might be able to do is delay upgrades of other parachains. Which seems like a problem to be solved once we actually see it as a problem in the wild (and can already be mitigated by adjusting the counter). The good thing is that we have all the ingredients to go further if need be. Signalling no longer actually includes the code, hence there is no need to reject the candidate: The parachain can make progress even if we choose not to immediately act on the request and no relay chain resources are wasted either. We could for example introduce another UMP Signalling message RequestCodeUpgradeWithPriority which not just requests a code upgrade, but also offers some DOT to get ranked up in a queue.","breadcrumbs":"RFC-0000: Feature Name Here » Further Hardening","id":"77","title":"Further Hardening"},"770":{"body":"These changes would allow protocol builders to leverage absolute locations to maintain the exact same derived account address across all networks in the ecosystem, thus enhancing user experience. One such protocol, that is the original motivation for this proposal, is InvArch's Saturn Multisig, which gives users a unifying multisig and DAO experience across all XCM connected chains.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Motivation","id":"770","title":"Motivation"},"771":{"body":"Ecosystem developers","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Stakeholders","id":"771","title":"Stakeholders"},"772":{"body":"This proposal aims to make it possible to derive accounts for absolute locations, enabling protocols that require the ability to maintain the same derived account in any runtime. This is done by deriving accounts from the hash of described absolute locations, which are static across different destinations. The same location can be represented in relative form and absolute form like so: // Relative location (from own perspective)\n{ parents: 0, interior: Here\n} // Relative location (from perspective of parent)\n{ parents: 0, interior: [Parachain(1000)]\n} // Relative location (from perspective of sibling)\n{ parents: 1, interior: [Parachain(1000)]\n} // Absolute location\n[GlobalConsensus(Kusama), Parachain(1000)] Using DescribeFamily, the above relative locations would be described like so: // Relative location (from own perspective)\n// Not possible. // Relative location (from perspective of parent)\n(b\"ChildChain\", Compact::::from(*index)).encode() // Relative location (from perspective of sibling)\n(b\"SiblingChain\", Compact::::from(*index)).encode() The proposed description for absolute location would follow the same pattern, like so: ( b\"GlobalConsensus\", network_id, b\"Parachain\", Compact::::from(para_id), tail\n).encode() This proposal requires the modification of two XCM types defined in the xcm-builder crate: The WithComputedOrigin barrier and the DescribeFamily MultiLocation descriptor. WithComputedOrigin The WtihComputedOrigin barrier serves as a wrapper around other barriers, consuming origin modification instructions and applying them to the message origin before passing to the inner barriers. One of the origin modifying instructions is UniversalOrigin, which serves the purpose of signaling that the origin should be a Universal Origin that represents the location as an absolute path prefixed by the GlobalConsensus junction. In it's current state the barrier transforms locations with the UniversalOrigin instruction into relative locations, so the proposed changes aim to make it return absolute locations instead. DescribeFamily The DescribeFamily location descriptor is part of the HashedDescription MultiLocation hashing system and exists to describe locations in an easy format for encoding and hashing, so that an AccountId can be derived from this MultiLocation. This implementation contains a match statement that does not match against absolute locations, so changes to it involve matching against absolute locations and providing appropriate descriptions for hashing.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Explanation","id":"772","title":"Explanation"},"773":{"body":"No drawbacks have been identified with this proposal.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Drawbacks","id":"773","title":"Drawbacks"},"774":{"body":"Tests can be done using simple unit tests, as this is not a change to XCM itself but rather to types defined in xcm-builder. Security considerations should be taken with the implementation to make sure no unwanted behavior is introduced. This proposal does not introduce any privacy considerations.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Testing, Security, and Privacy","id":"774","title":"Testing, Security, and Privacy"},"775":{"body":"","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Performance, Ergonomics, and Compatibility","id":"775","title":"Performance, Ergonomics, and Compatibility"},"776":{"body":"Depending on the final implementation, this proposal should not introduce much overhead to performance.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Performance","id":"776","title":"Performance"},"777":{"body":"The ergonomics of this proposal depend on the final implementation details.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Ergonomics","id":"777","title":"Ergonomics"},"778":{"body":"Backwards compatibility should remain unchanged, although that depend on the final implementation.","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Compatibility","id":"778","title":"Compatibility"},"779":{"body":"DescirbeFamily type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/location_conversion.rs#L122 WithComputedOrigin type: https://github.com/paritytech/polkadot-sdk/blob/master/polkadot/xcm/xcm-builder/src/barriers.rs#L153","breadcrumbs":"RFC-34: XCM Absolute Location Account Derivation » Prior Art and References","id":"779","title":"Prior Art and References"},"78":{"body":"Making this storage mechanism more general purpose is worth thinking about. E.g. by resolving above \"fee\" question, we might also be able to resolve the pruning question in a more generic way and thus could indeed open this storage facility for other purposes as well. E.g. smart contracts, so the PoV would only need to reference contracts by hash and the actual PoV is stored on validators and collators and thus no longer needs to be part of the PoV. A possible avenue would be to change the response to: enum BlobResponse { Blob(Vec 
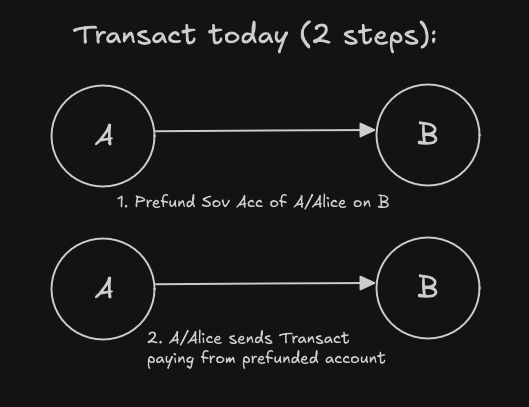
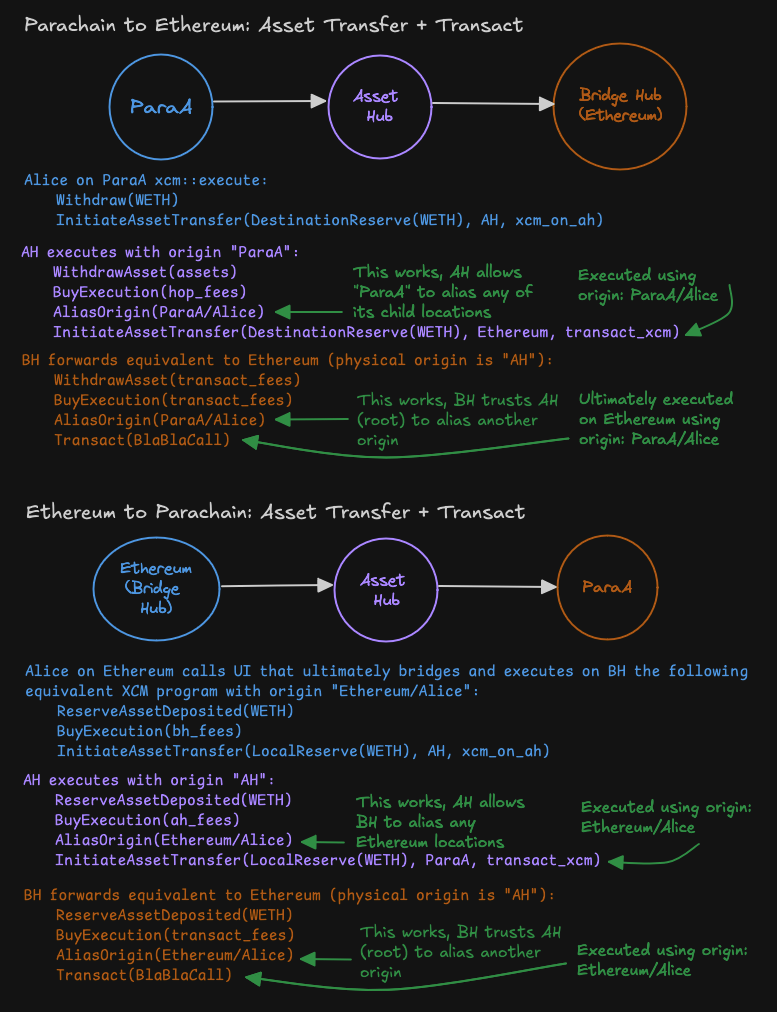 -
-